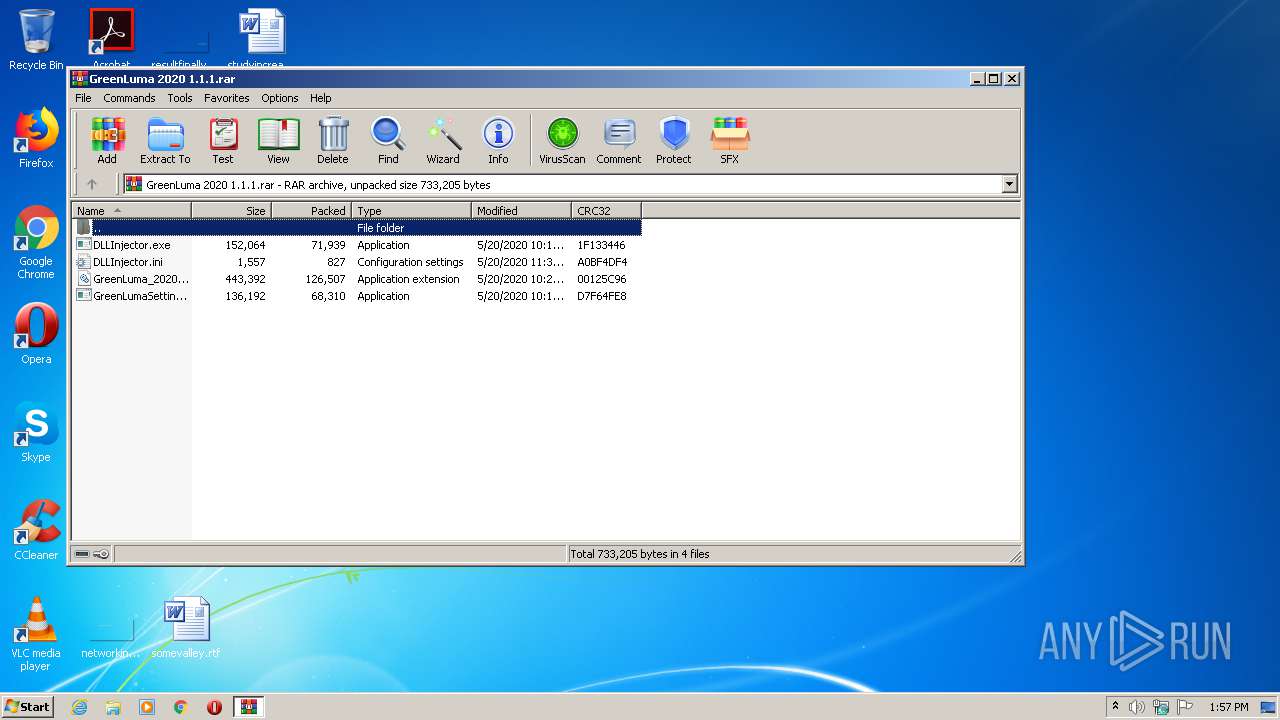
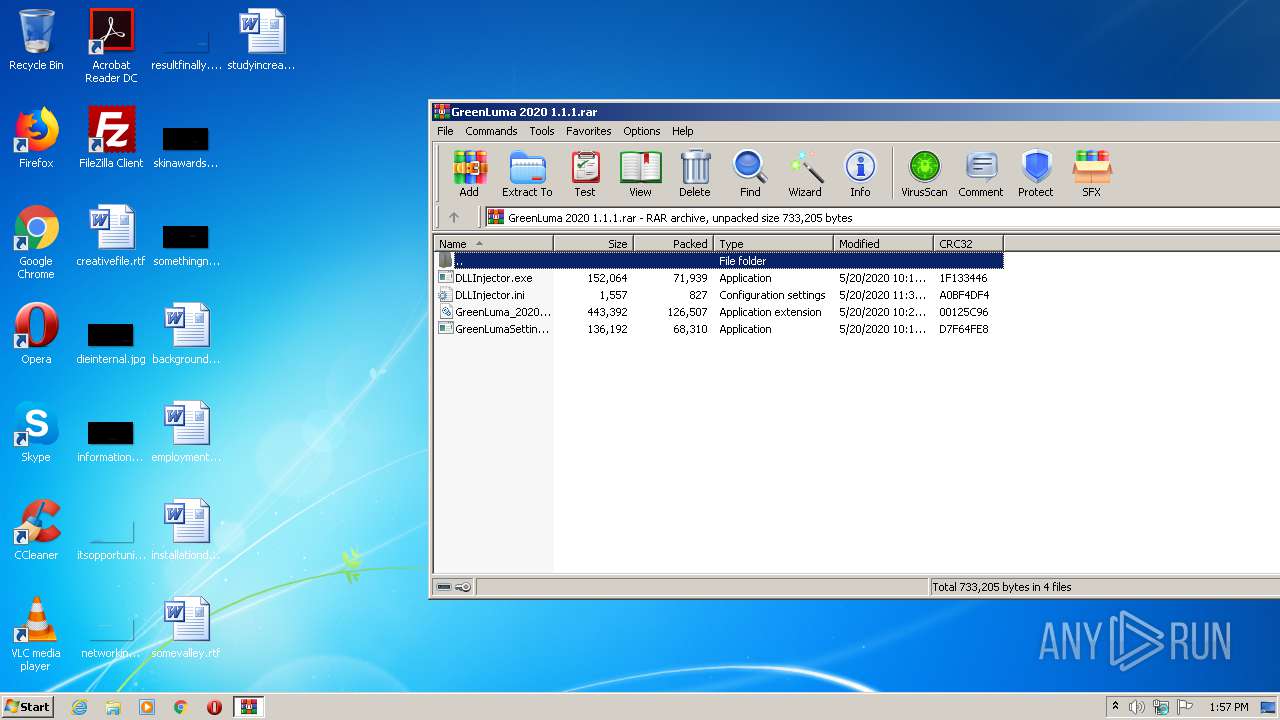
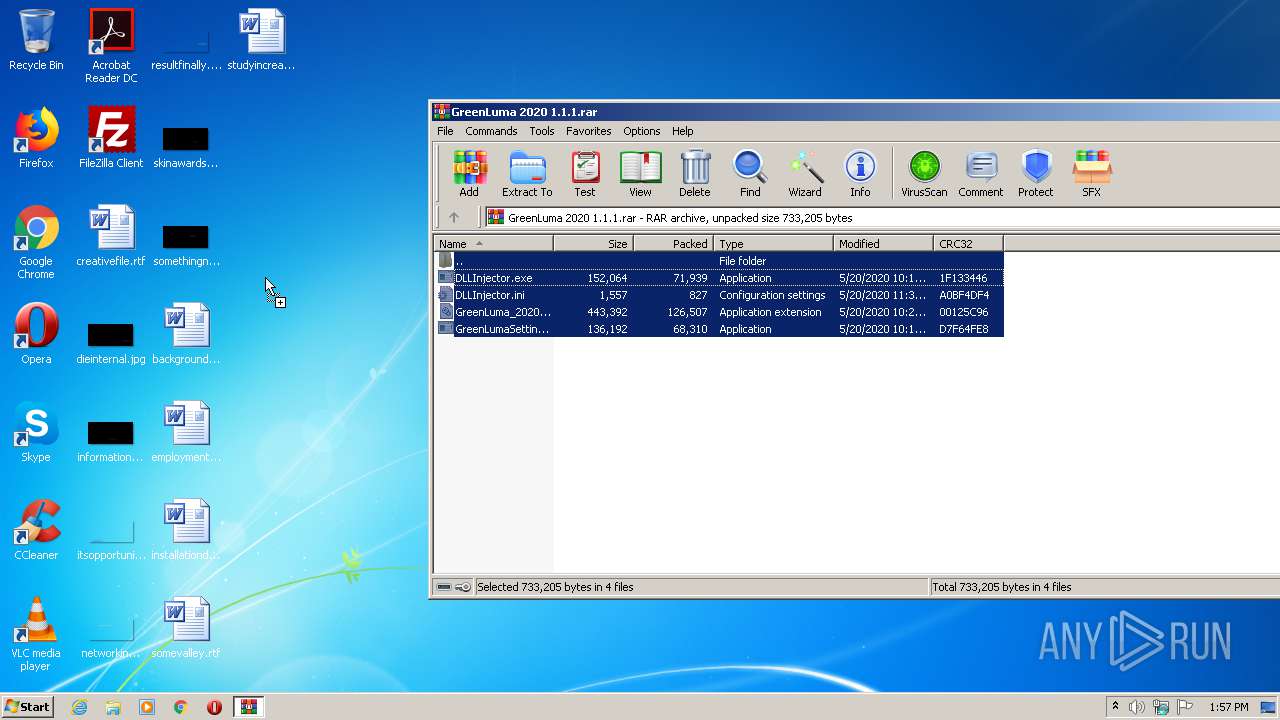
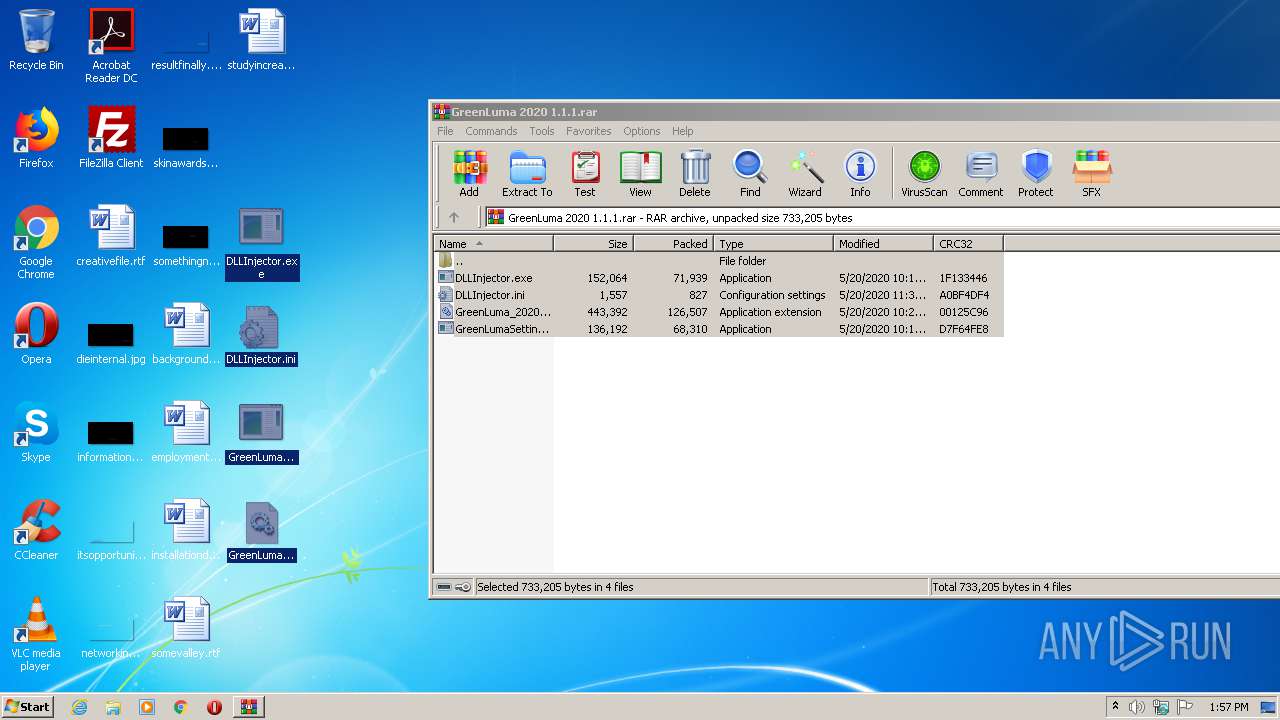
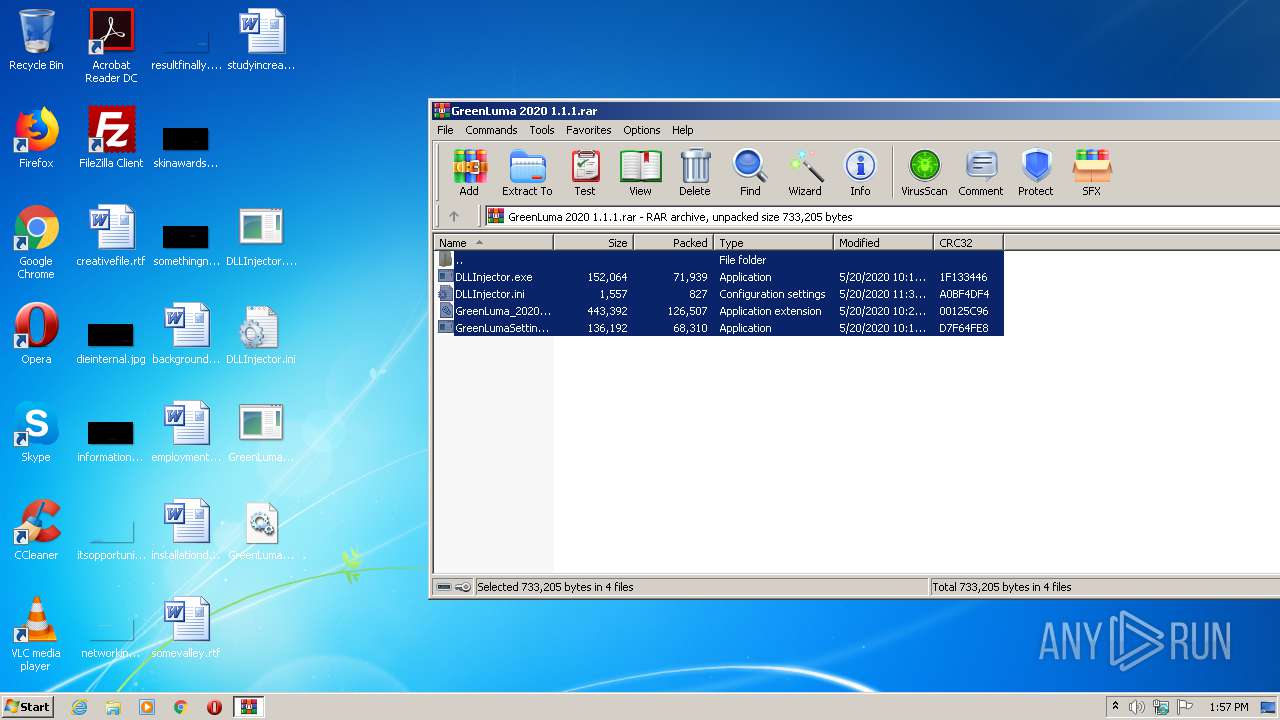
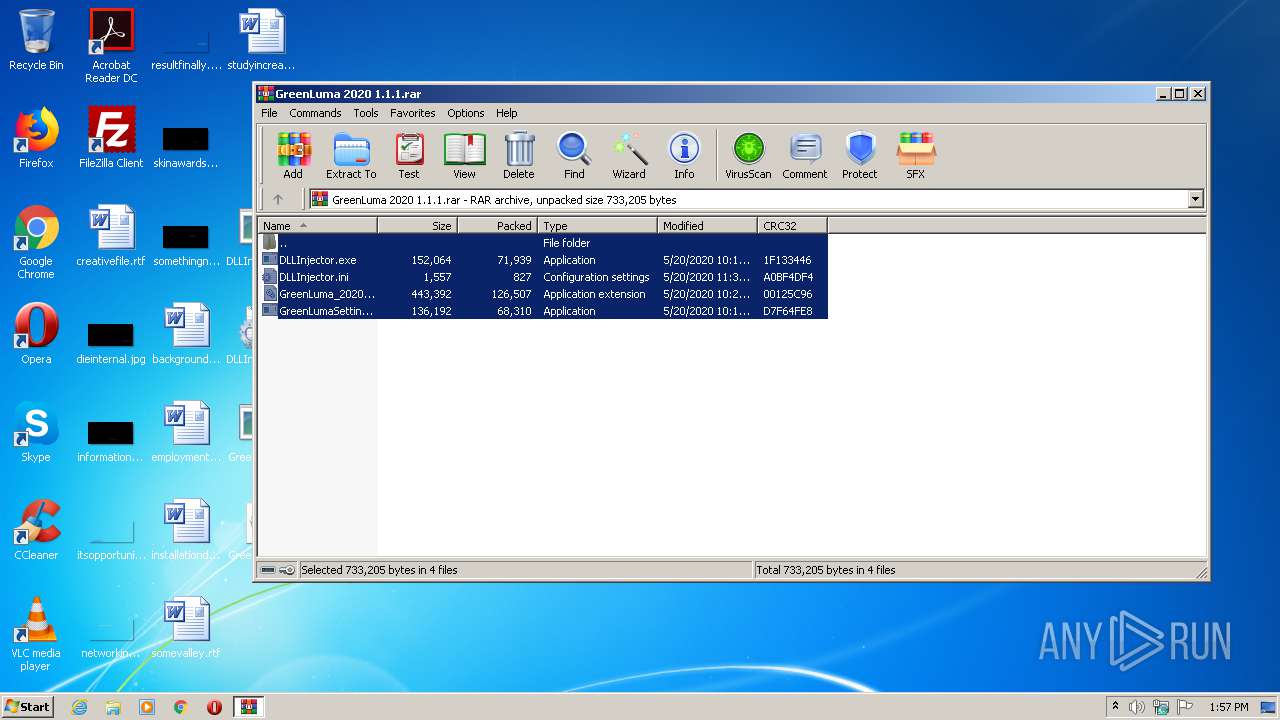
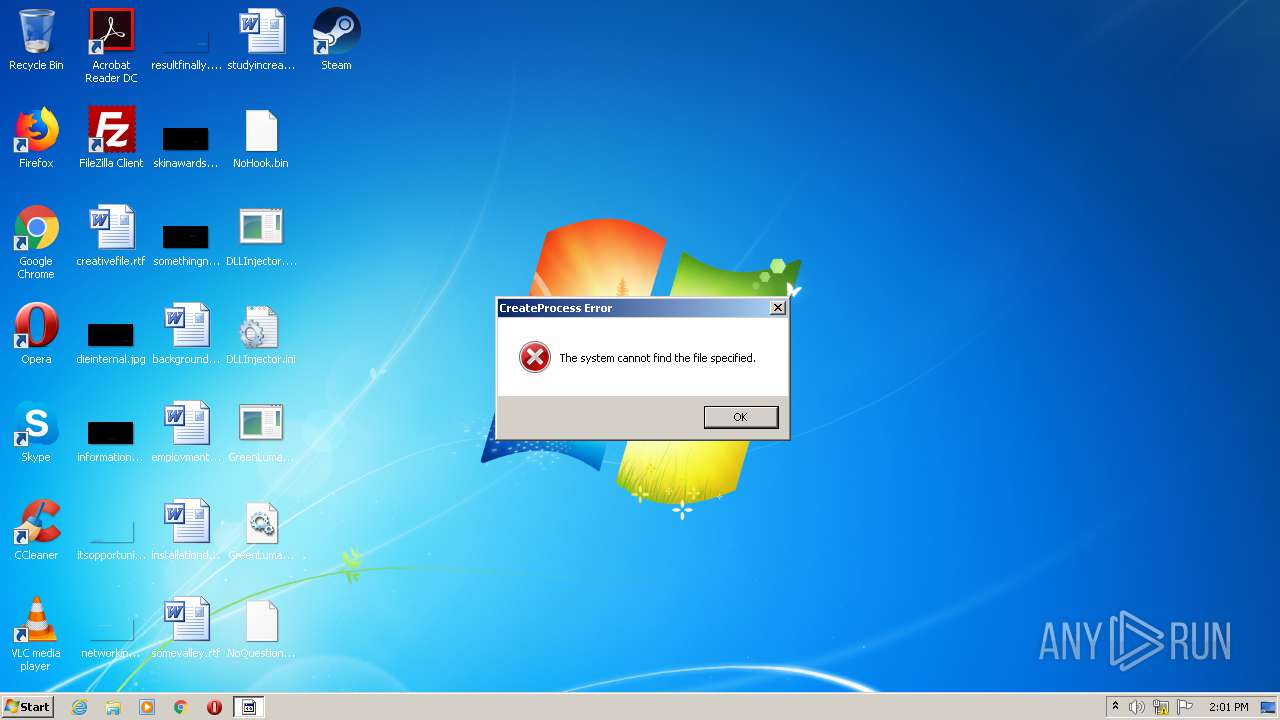
| File name: | GreenLuma 2020 1.1.1.rar |
| Full analysis: | https://app.any.run/tasks/f5d8bb25-f584-4ff3-ad46-9fdc51bac3aa |
| Verdict: | Malicious activity |
| Analysis date: | June 29, 2020, 12:56:44 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | A2DFB2DD730623608AC8871D539DE97F |
| SHA1: | 963304B9EEC45F8020EF5767DA76F0EA6BB92482 |
| SHA256: | 87AC9A5E0609D7DFDC178E5D73119D19901B0E0E667C68A7B0030A6B149B4B35 |
| SSDEEP: | 6144:lJX4OUPQi5icqw6OMTWOQu/6t0iyfbGmzePh1+RN:lJX4OUPQi5RMTWOQu/E0nZePyv |
MALICIOUS
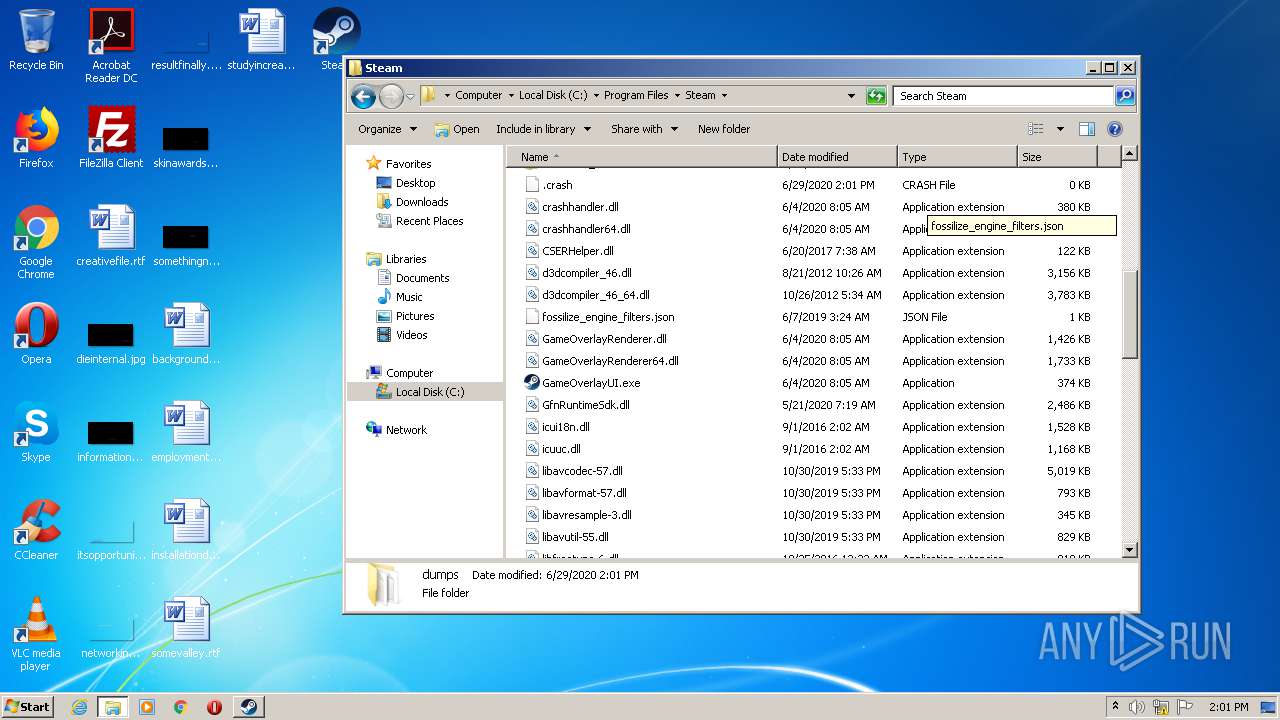
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3460)
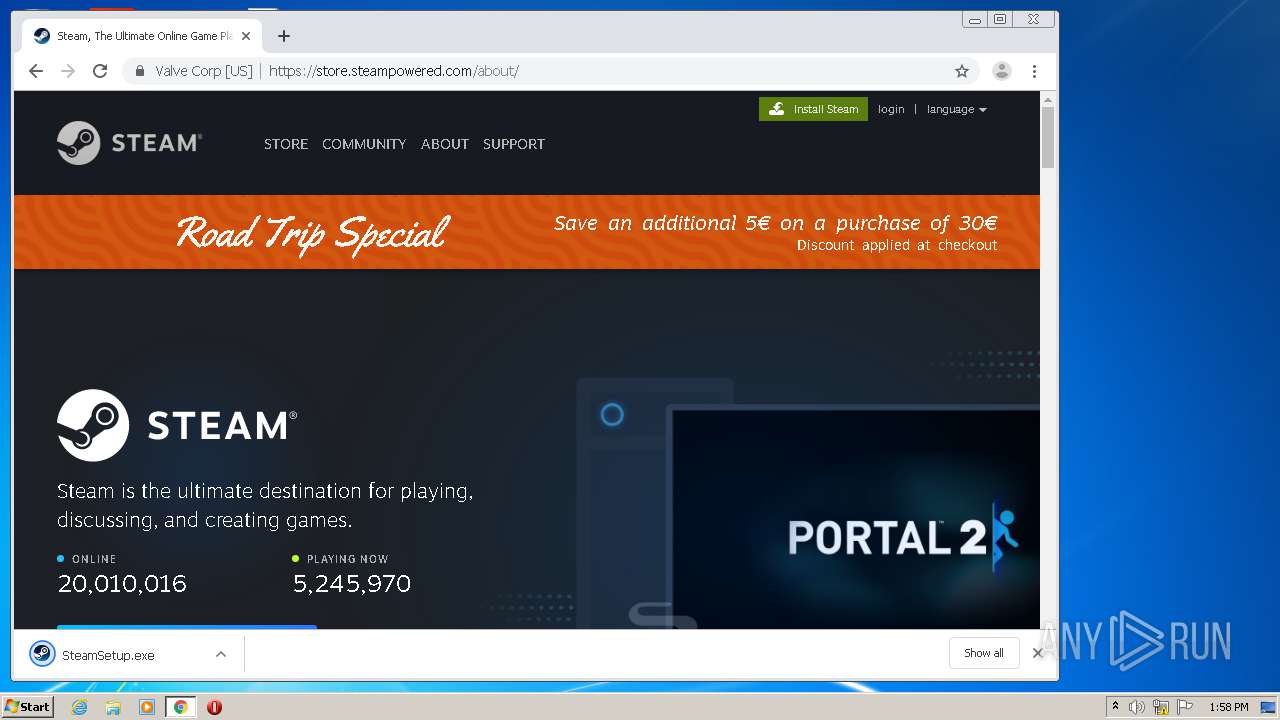
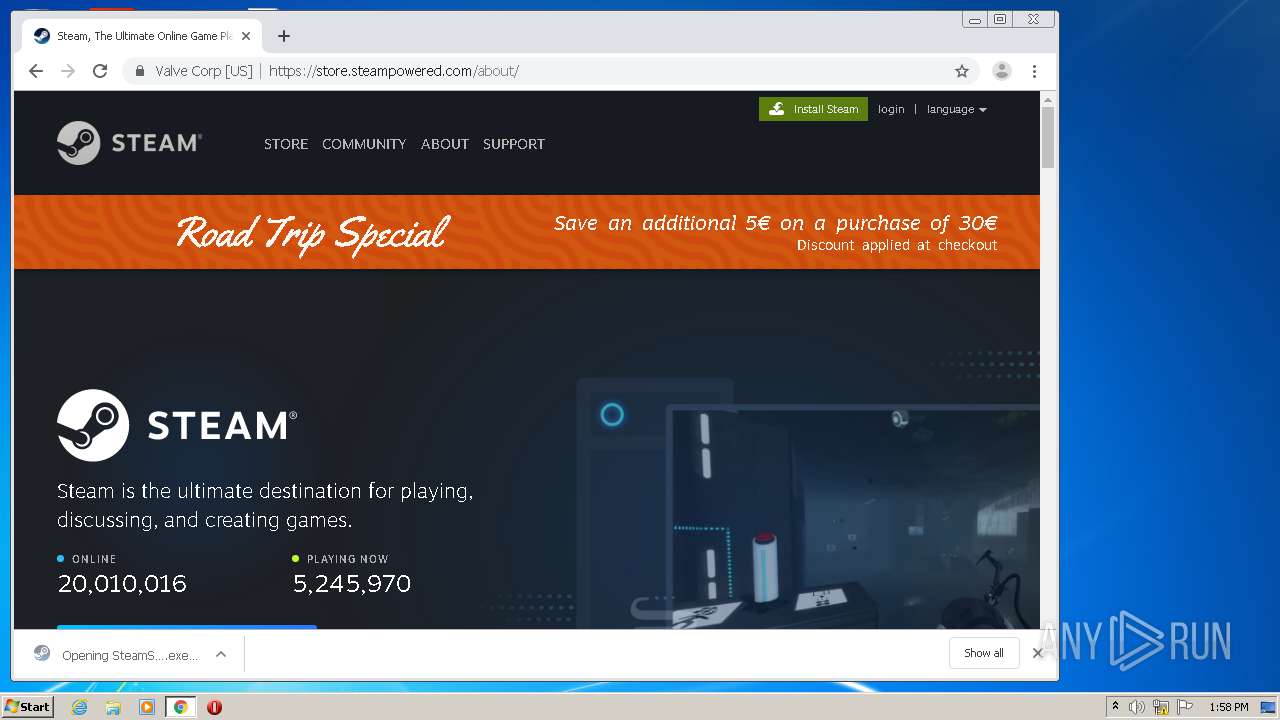
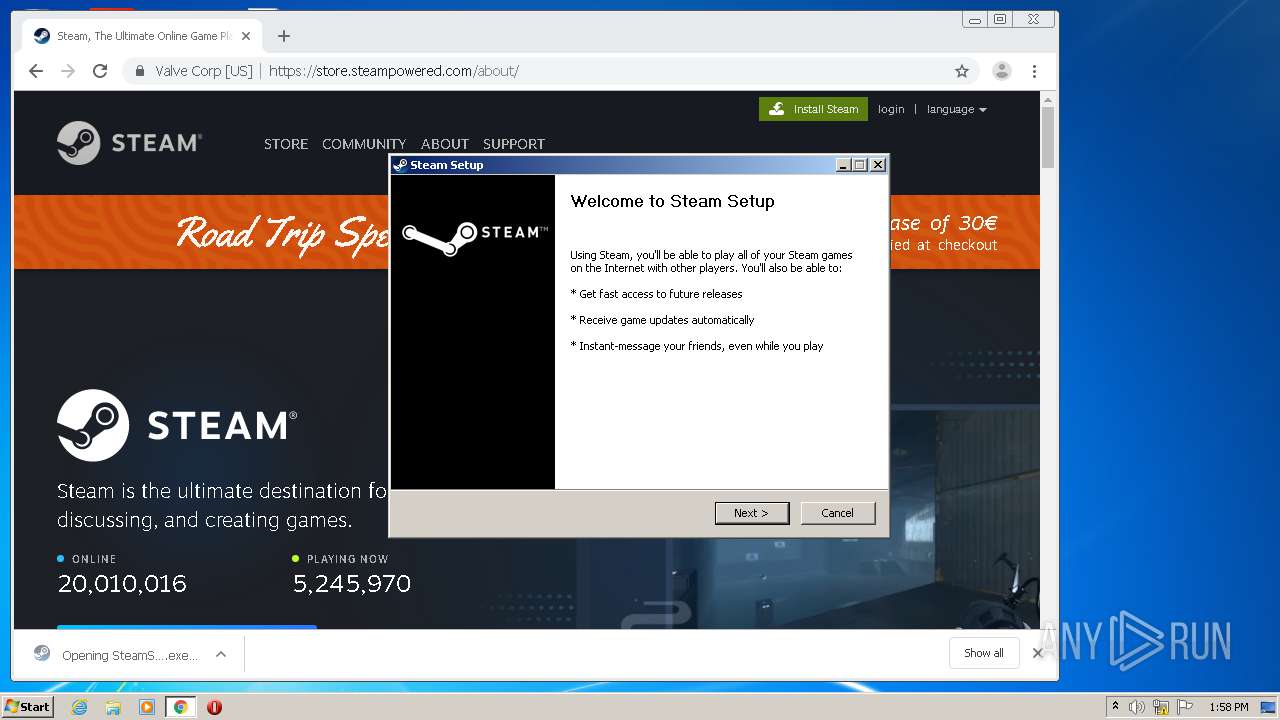
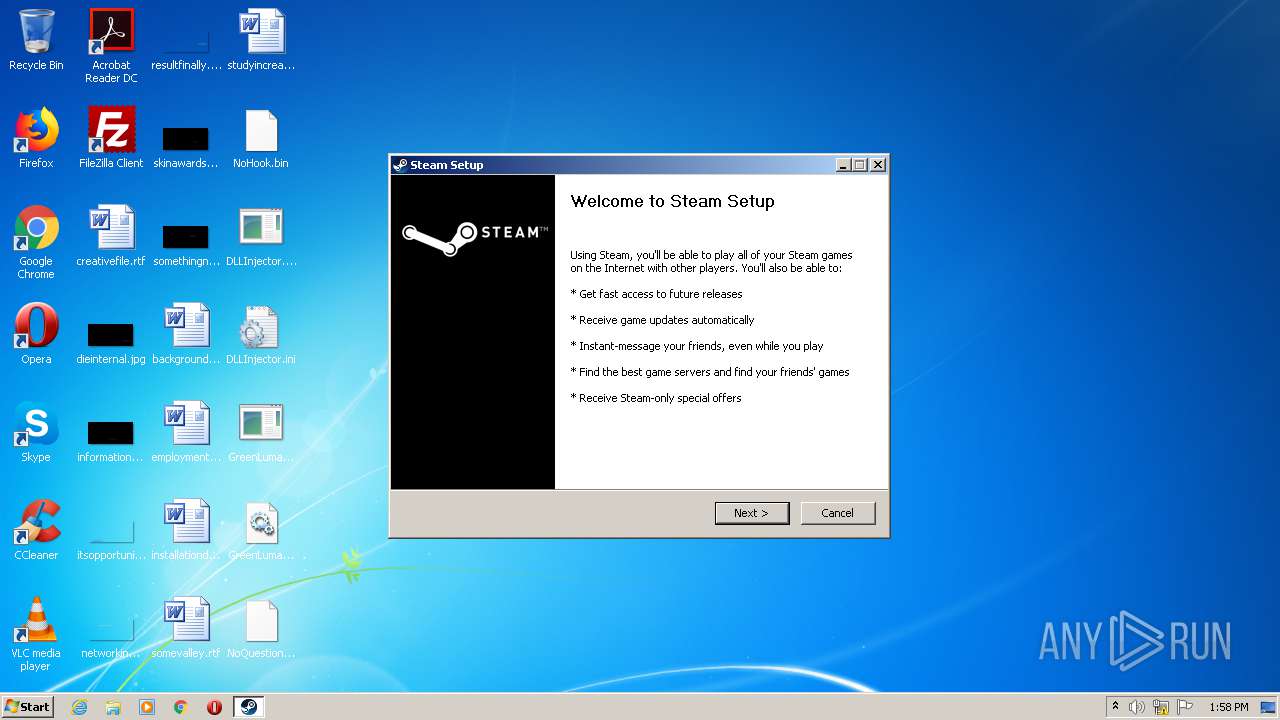
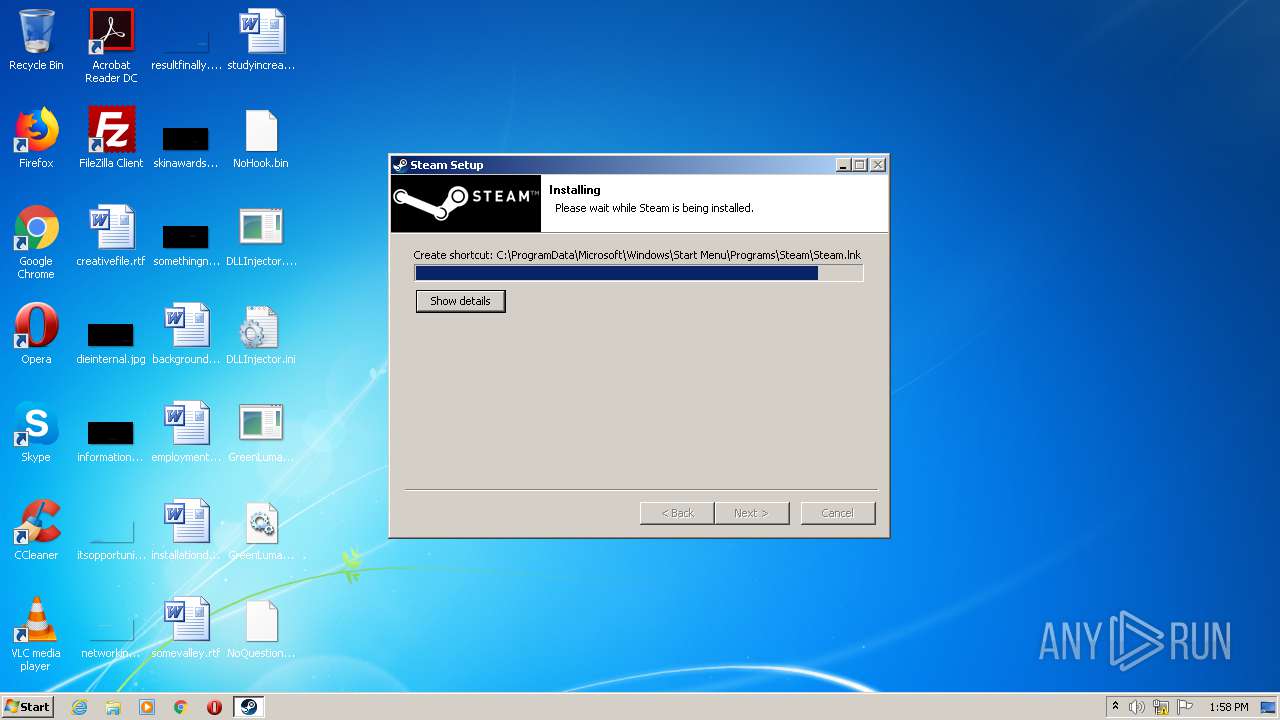
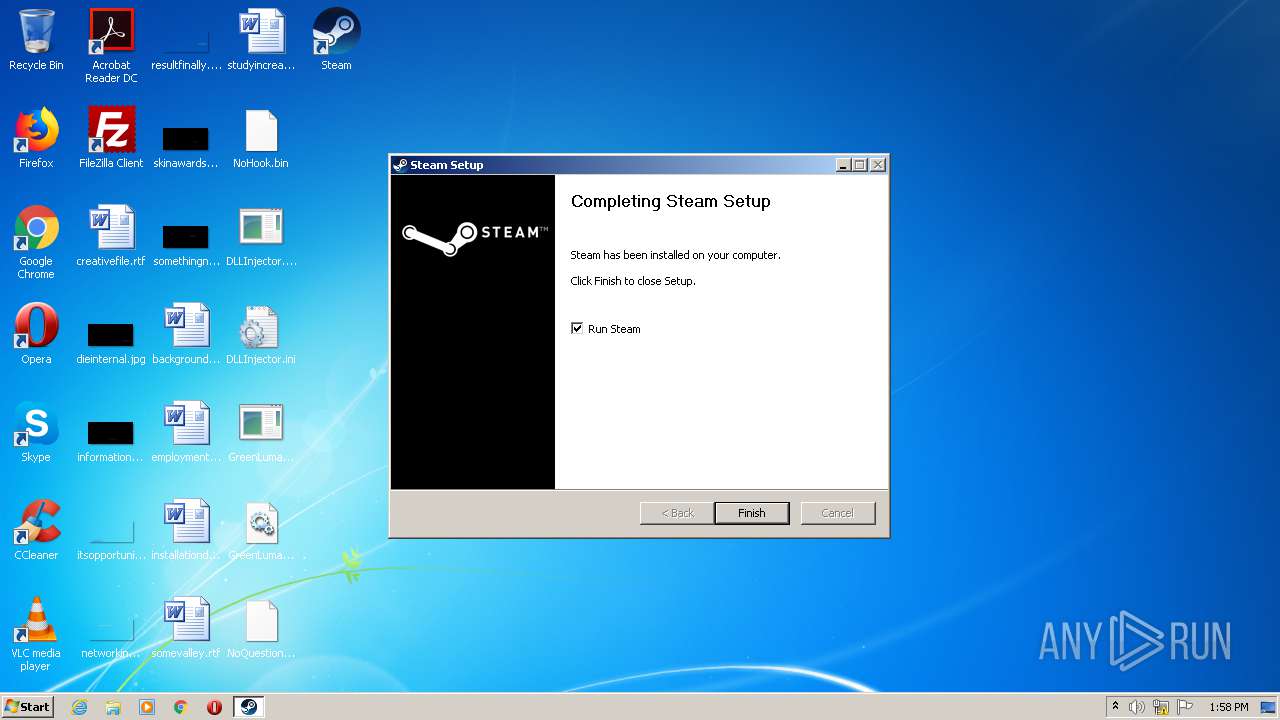
- SteamSetup.exe (PID: 2944)
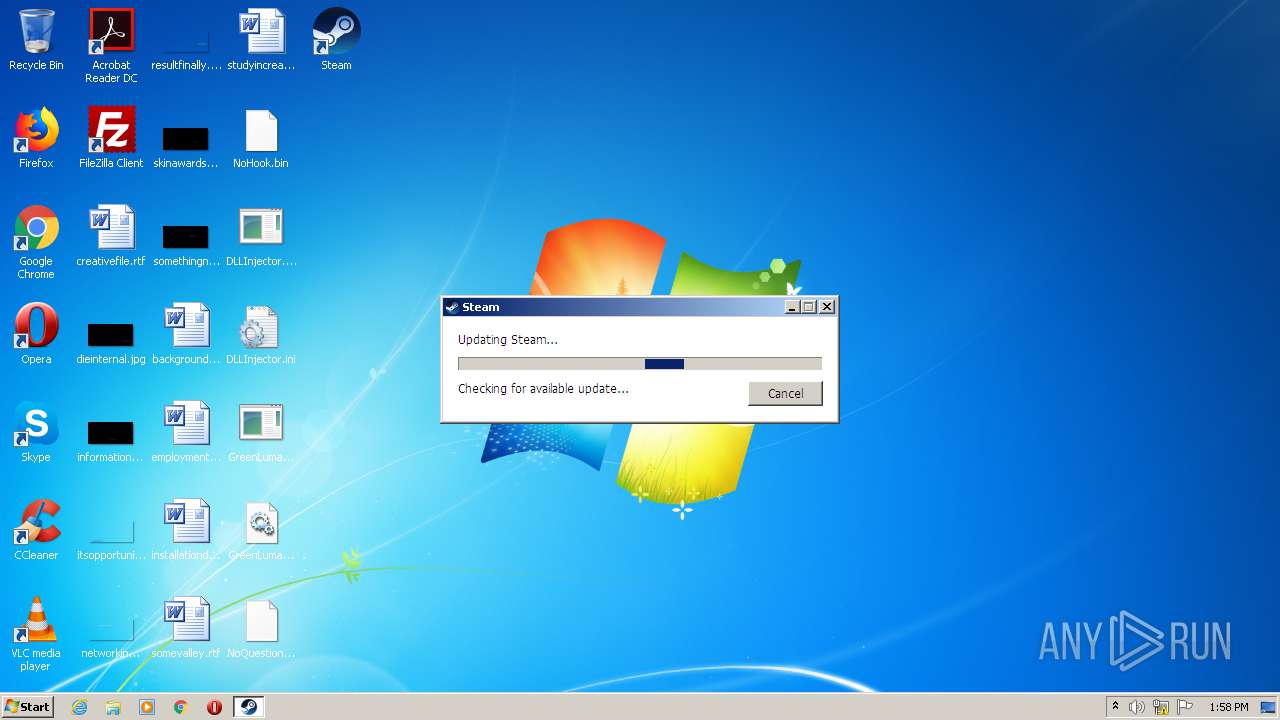
- steam.exe (PID: 852)
- explorer.exe (PID: 348)
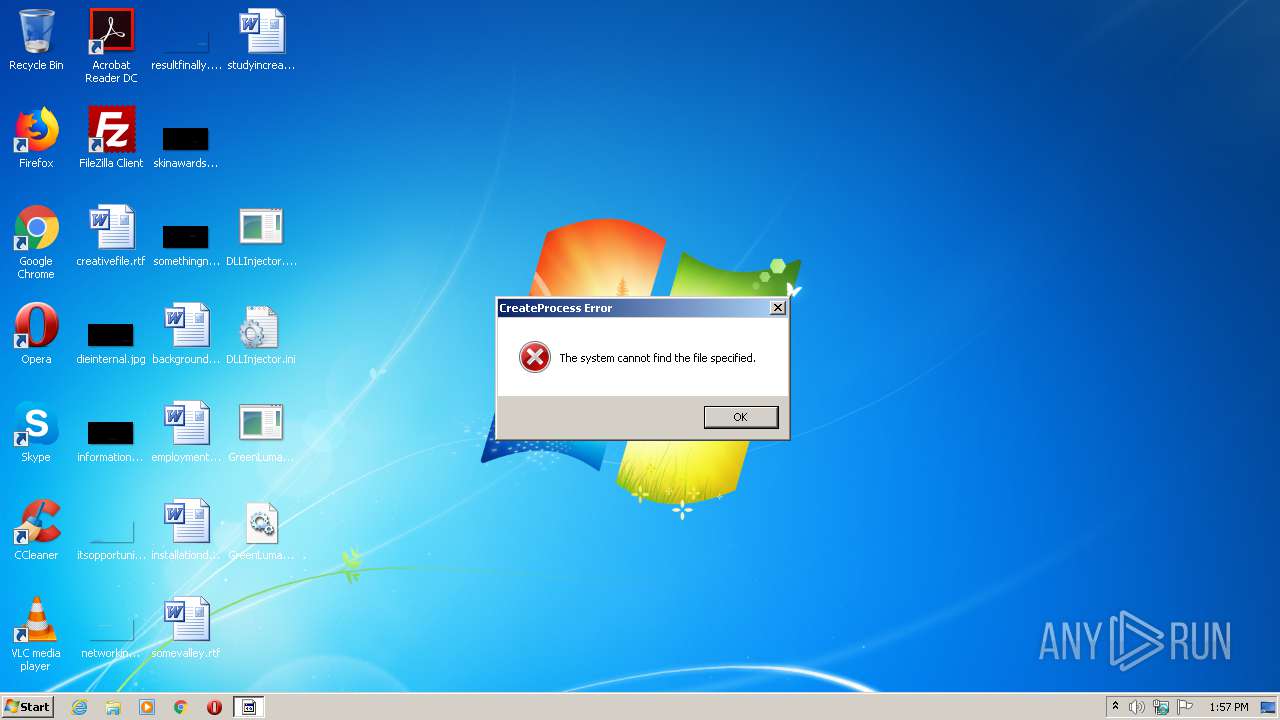
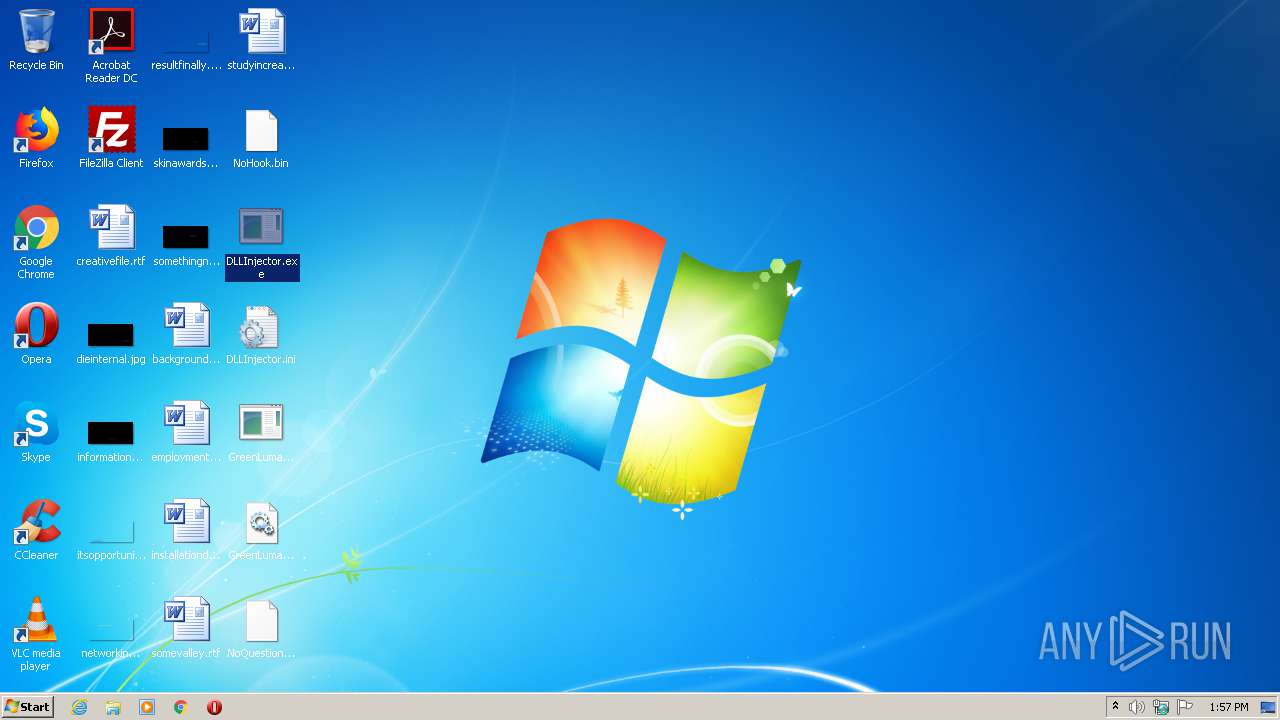
Application was dropped or rewritten from another process
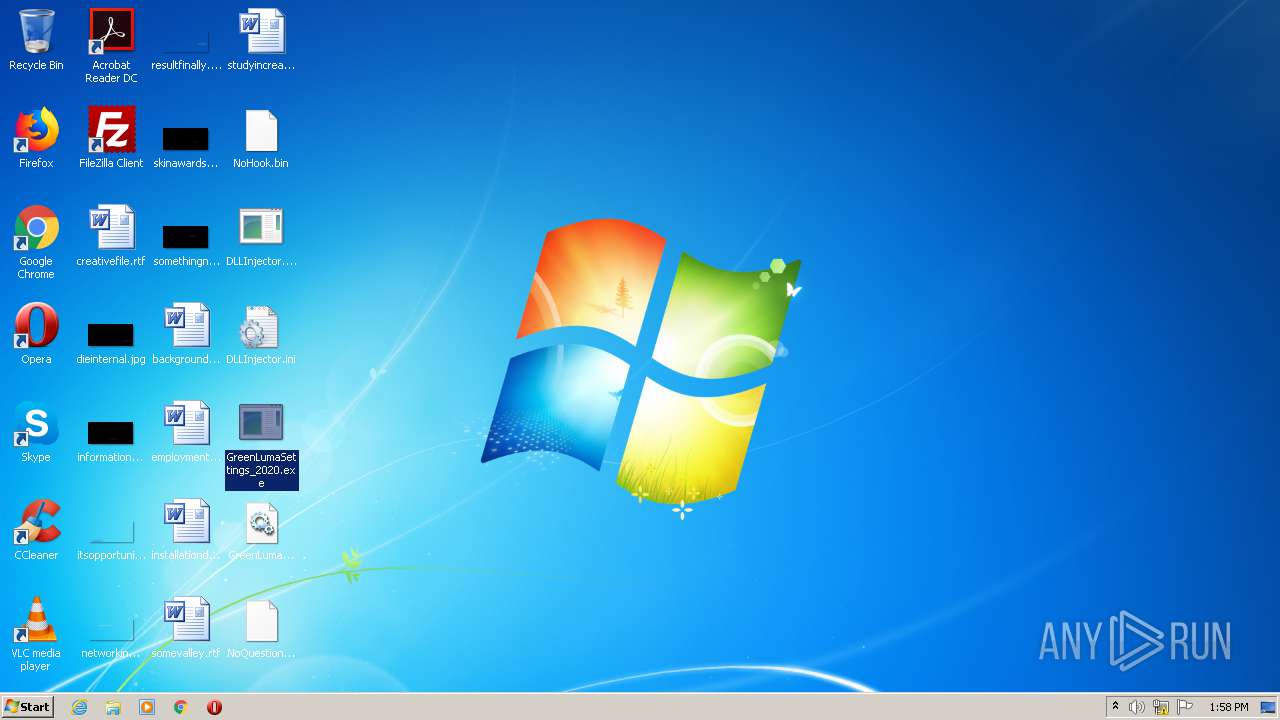
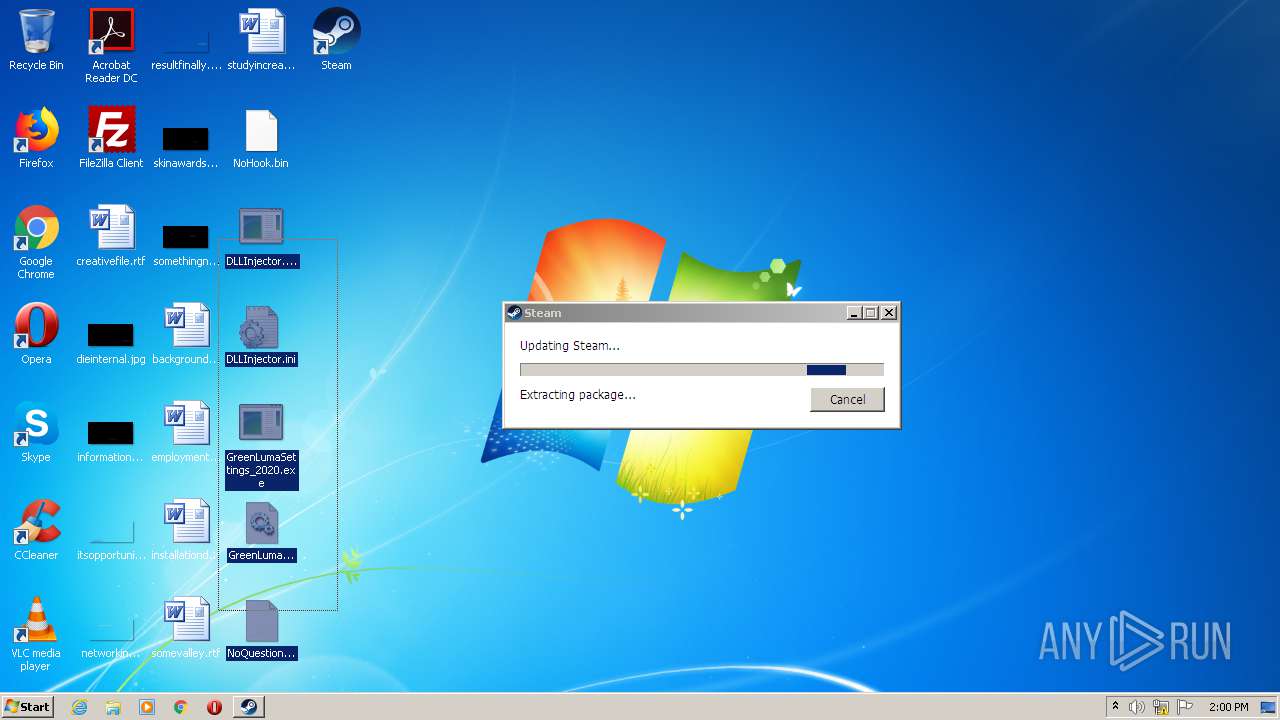
- DLLInjector.exe (PID: 2296)
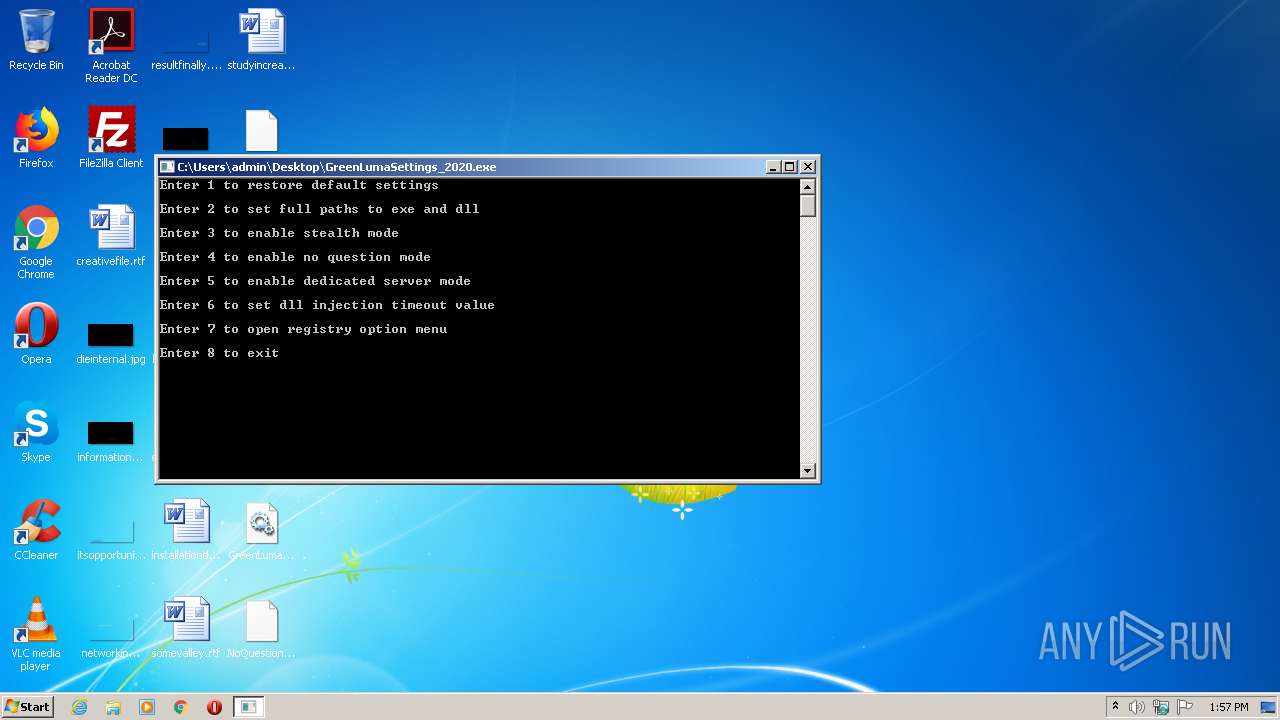
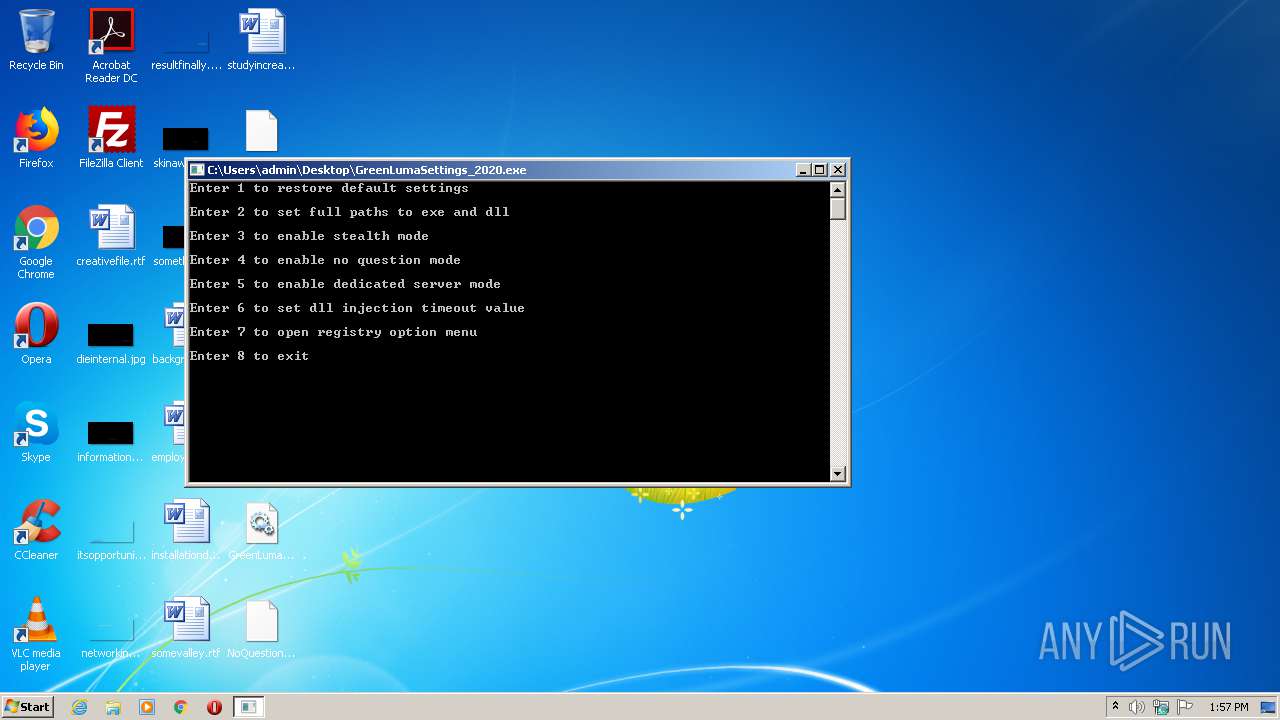
- GreenLumaSettings_2020.exe (PID: 2556)
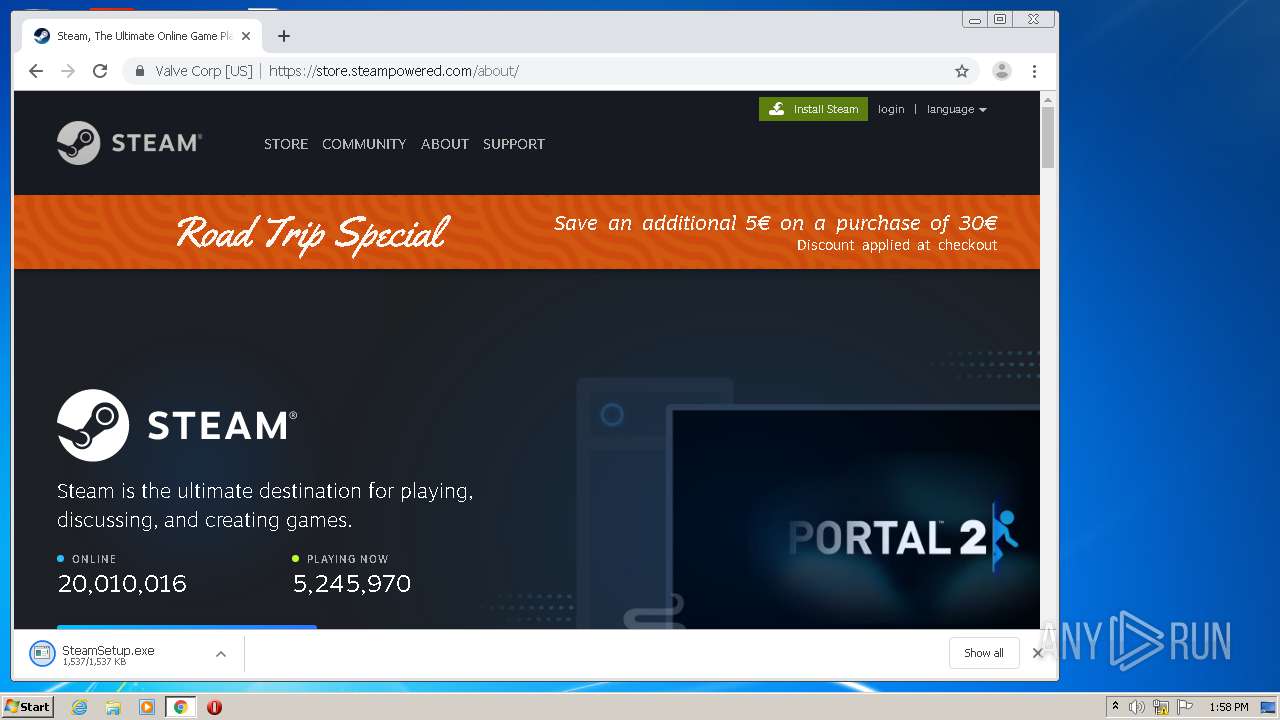
- SteamSetup.exe (PID: 4060)
- SteamSetup.exe (PID: 2944)
- nsE237.tmp (PID: 2604)
- steamservice.exe (PID: 3188)
- SteamService.exe (PID: 2764)
- steam.exe (PID: 3736)
- DLLInjector.exe (PID: 3724)
- SteamService.exe (PID: 956)
- steamwebhelper.exe (PID: 3820)
- steamwebhelper.exe (PID: 2132)
- SteamServiceTmp.exe (PID: 3480)
- steamwebhelper.exe (PID: 2940)
- steamwebhelper.exe (PID: 3908)
- steamwebhelper.exe (PID: 2880)
Changes the autorun value in the registry
- SteamSetup.exe (PID: 2944)
Changes settings of System certificates
- SteamService.exe (PID: 2764)
SUSPICIOUS
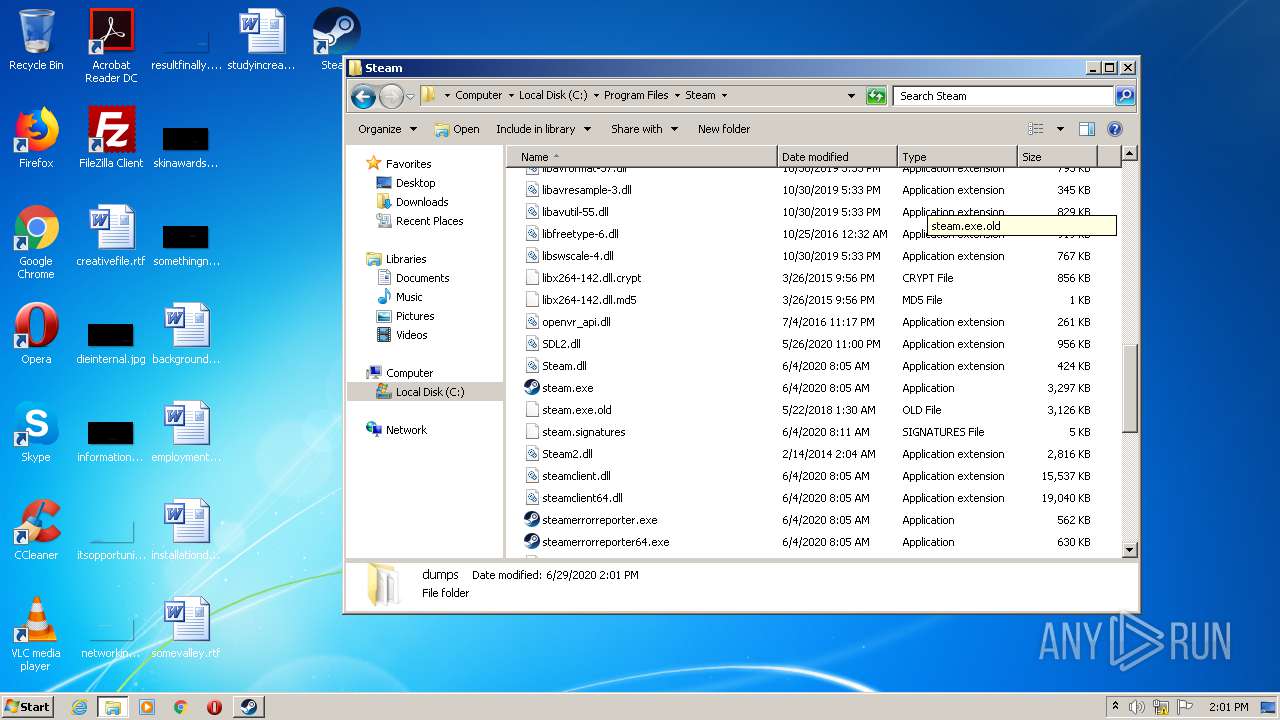
Executable content was dropped or overwritten
- SteamSetup.exe (PID: 2944)
- chrome.exe (PID: 1580)
- chrome.exe (PID: 3756)
- steamservice.exe (PID: 3188)
- steam.exe (PID: 3736)
- SteamService.exe (PID: 2764)
- SteamServiceTmp.exe (PID: 3480)
- SteamService.exe (PID: 956)
- steam.exe (PID: 852)
- explorer.exe (PID: 348)
Modifies files in Chrome extension folder
- chrome.exe (PID: 1580)
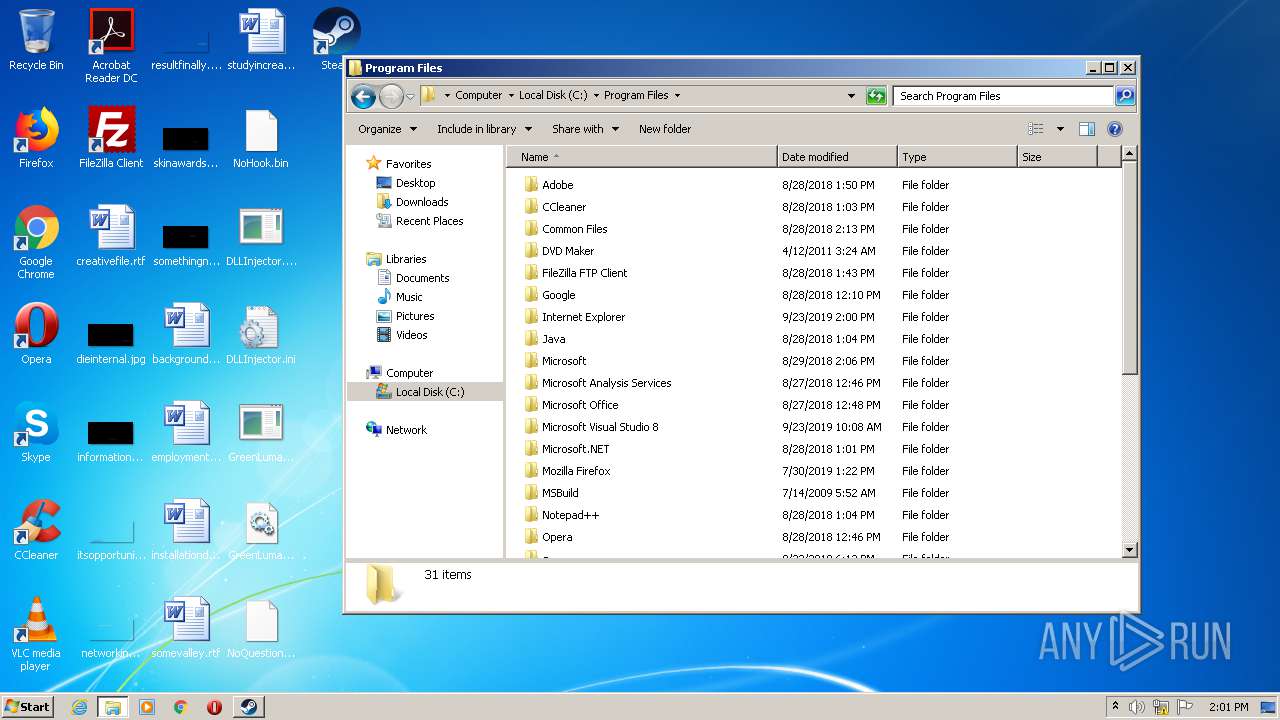
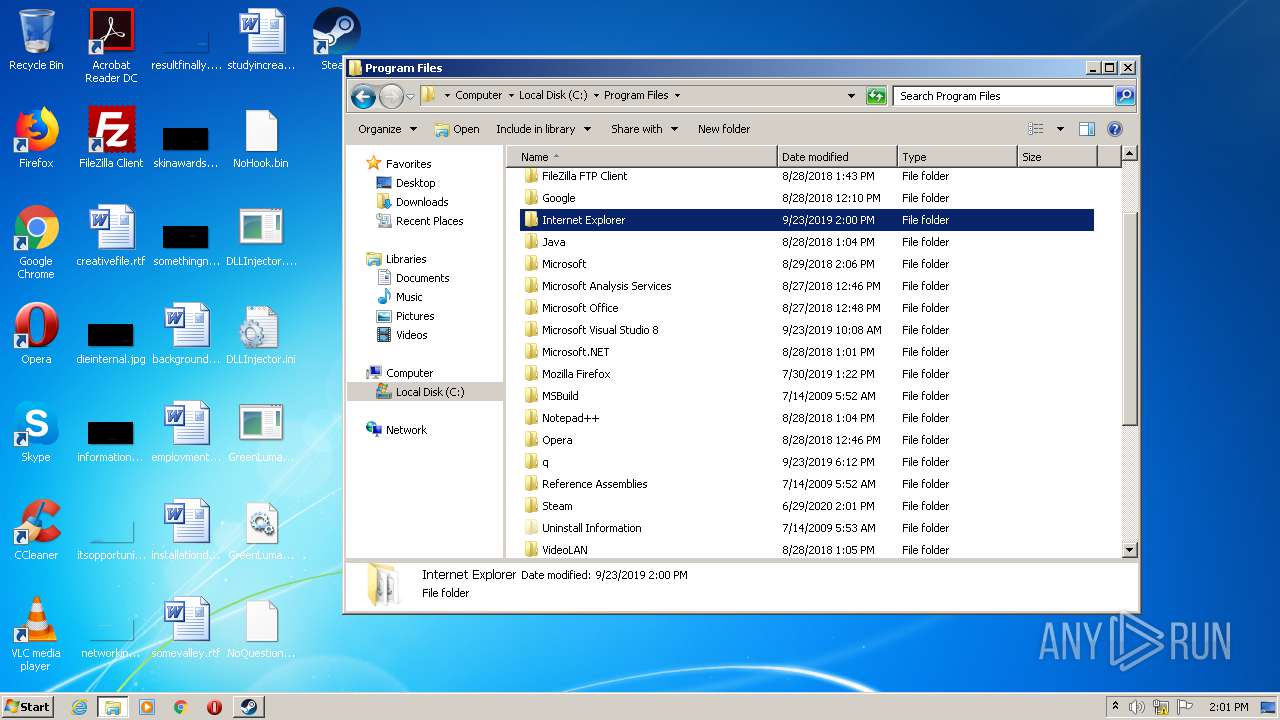
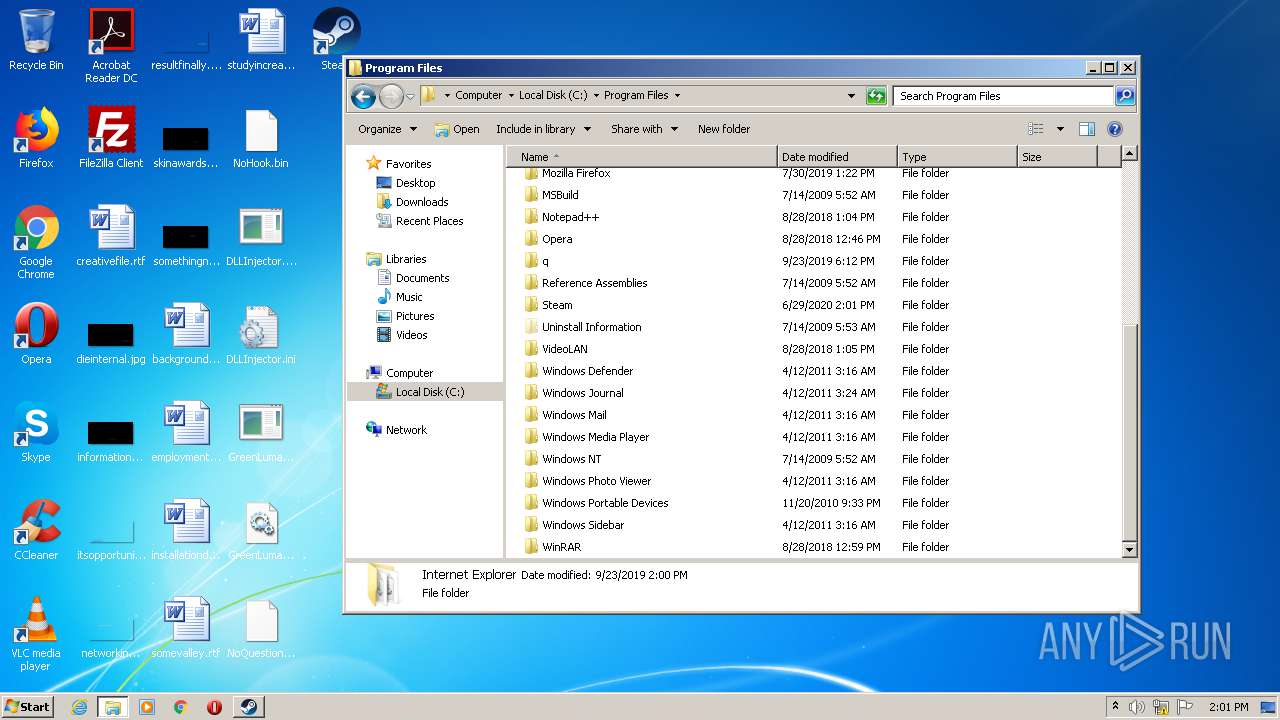
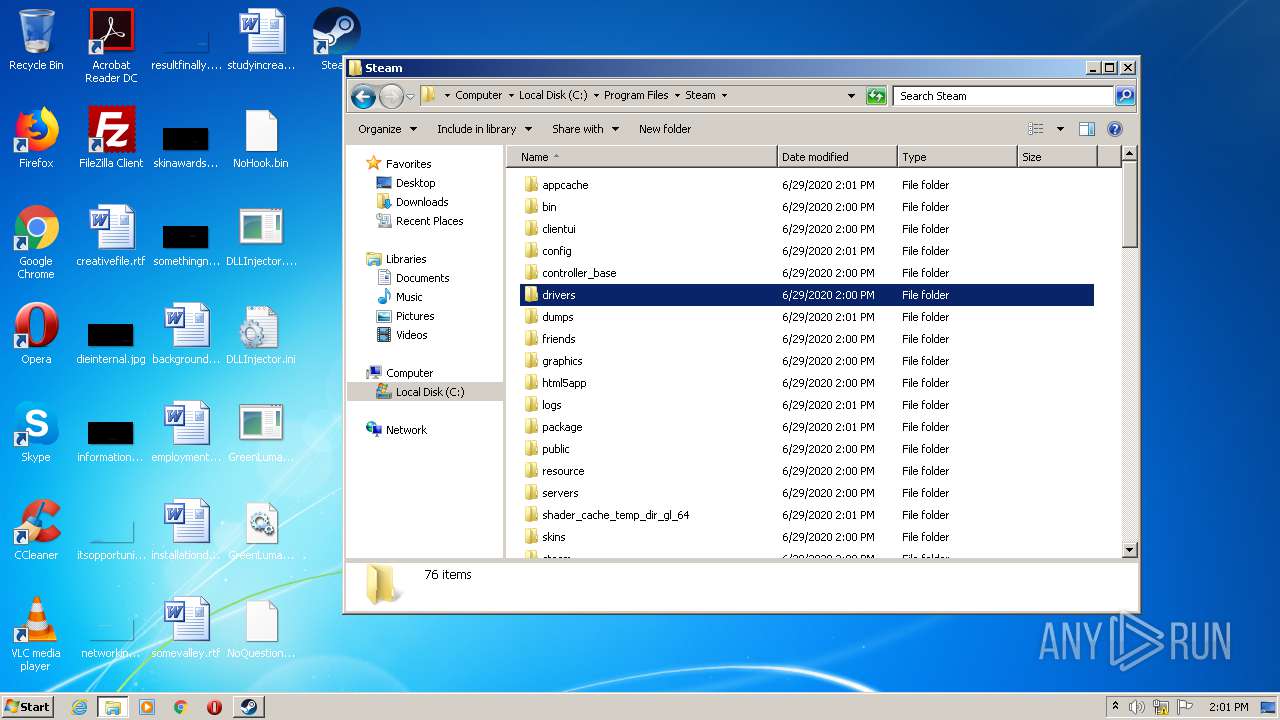
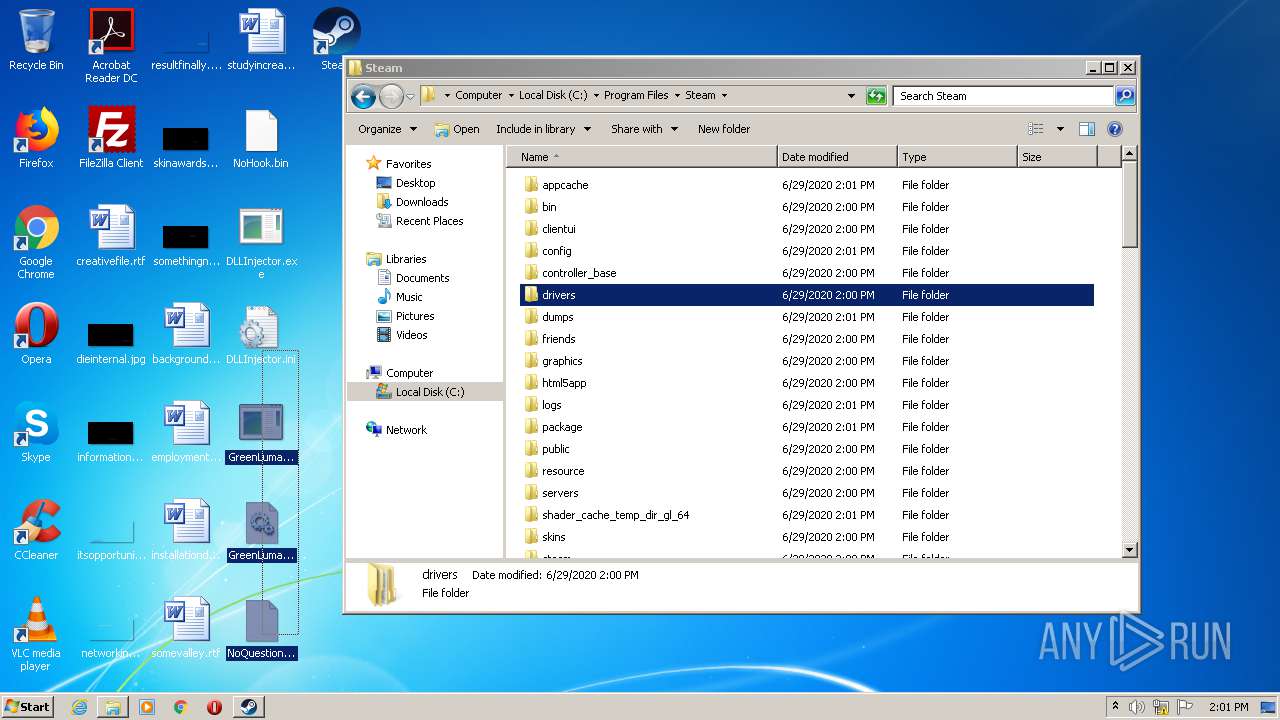
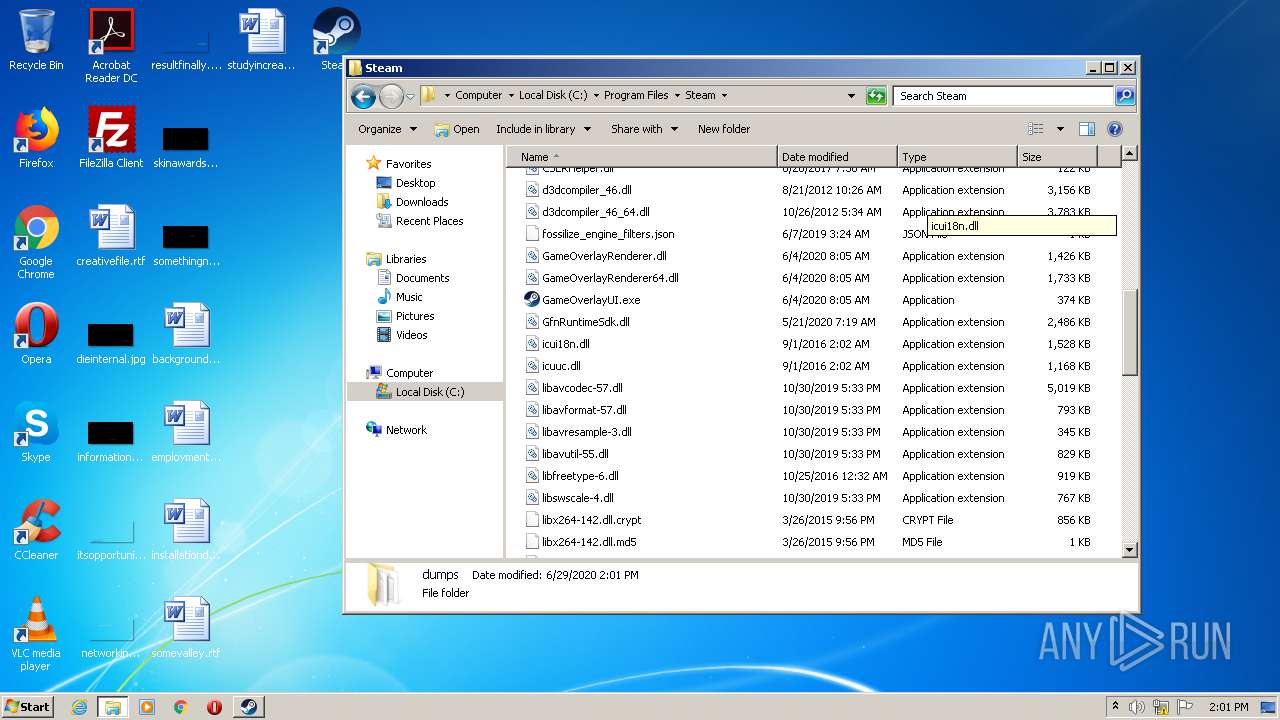
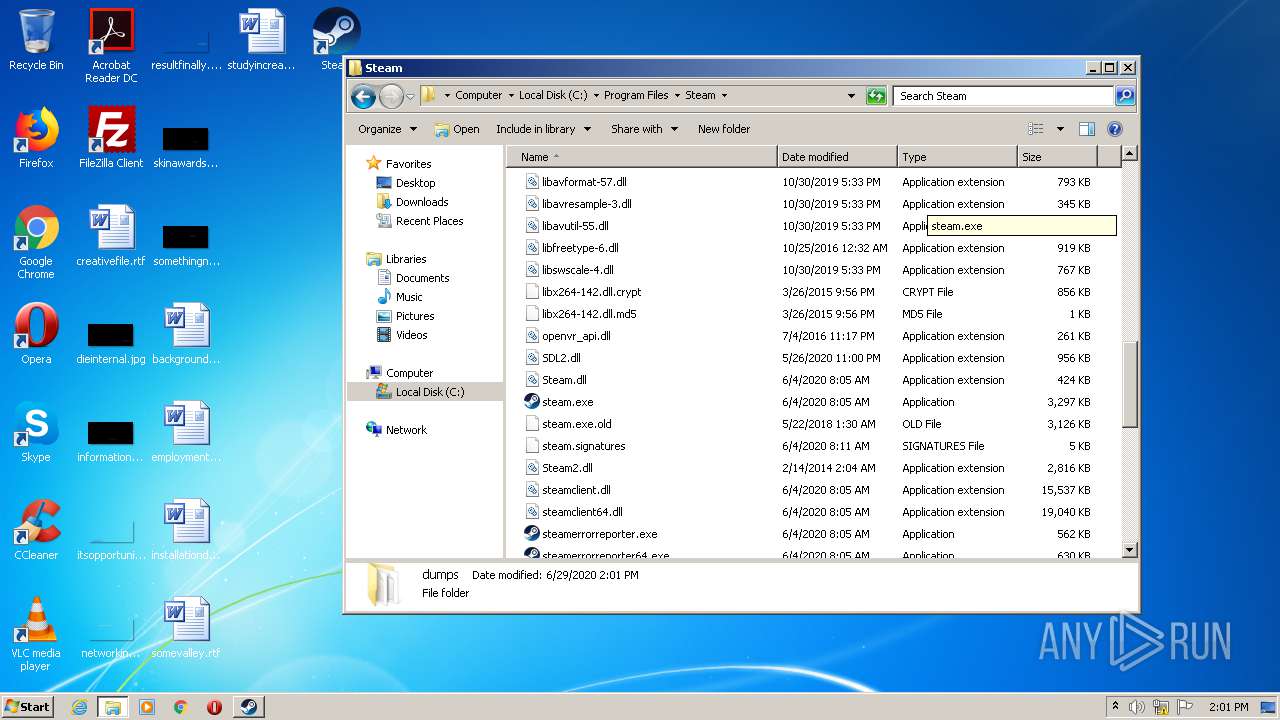
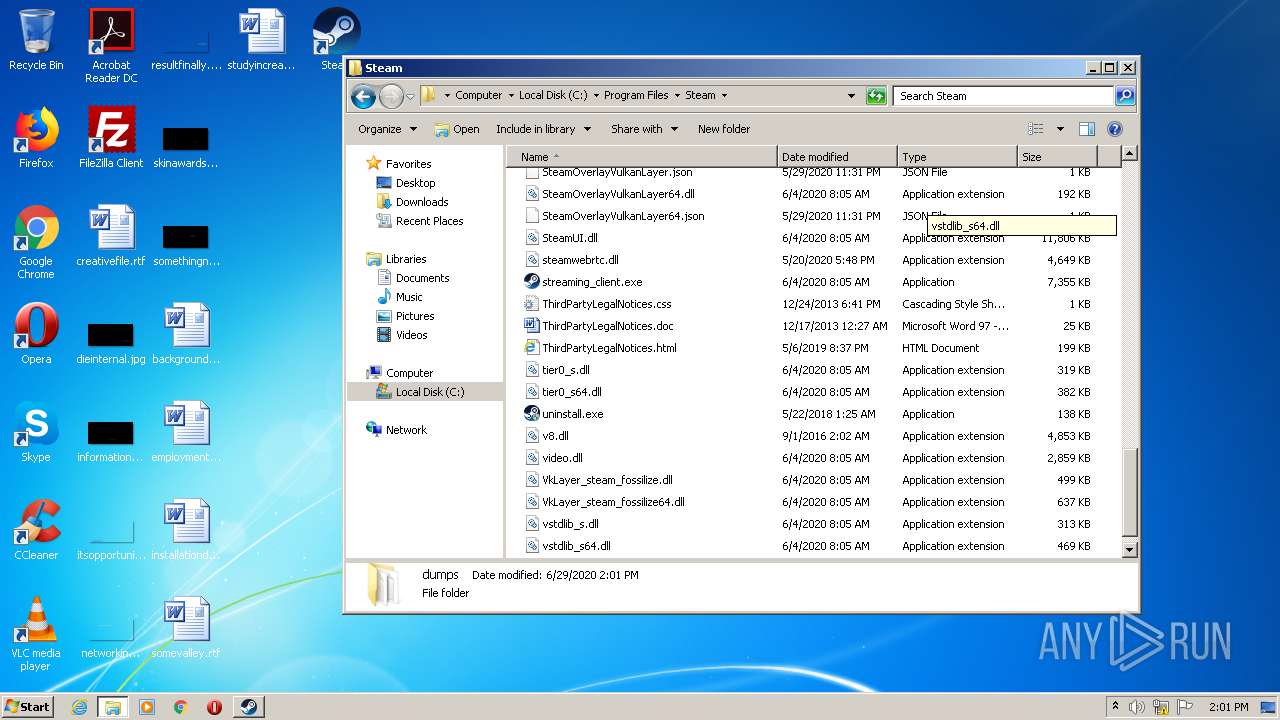
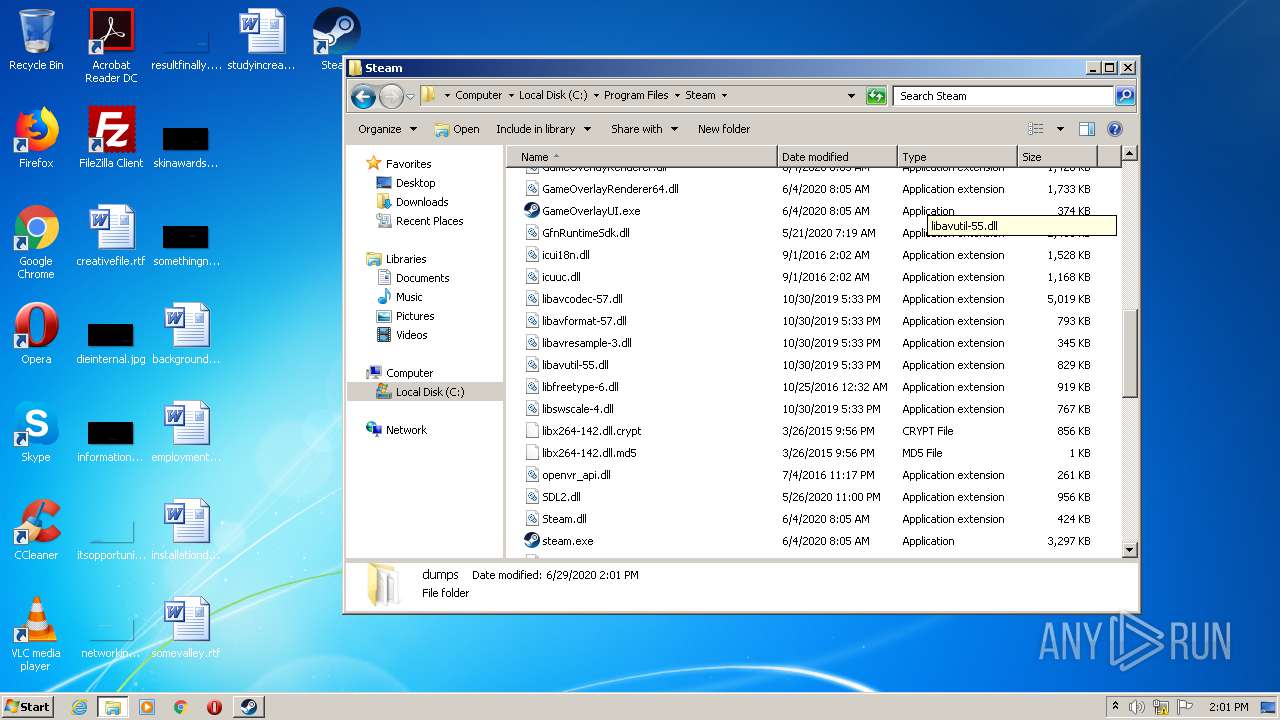
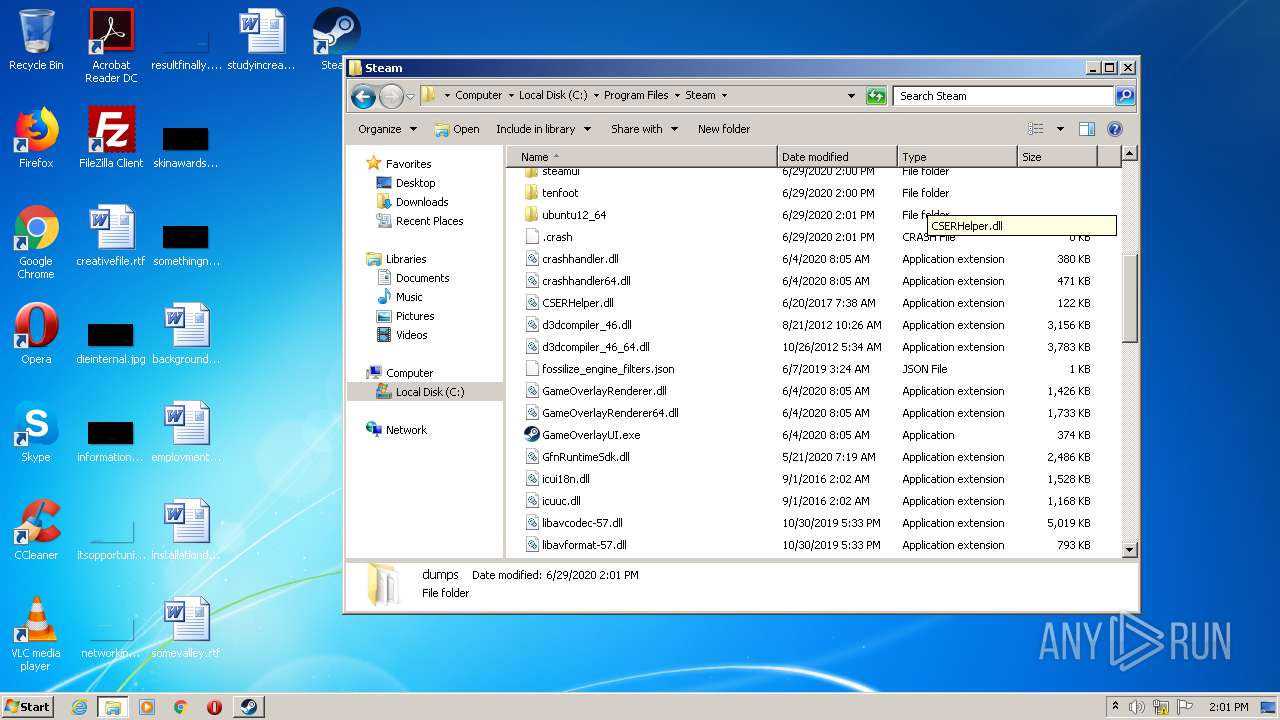
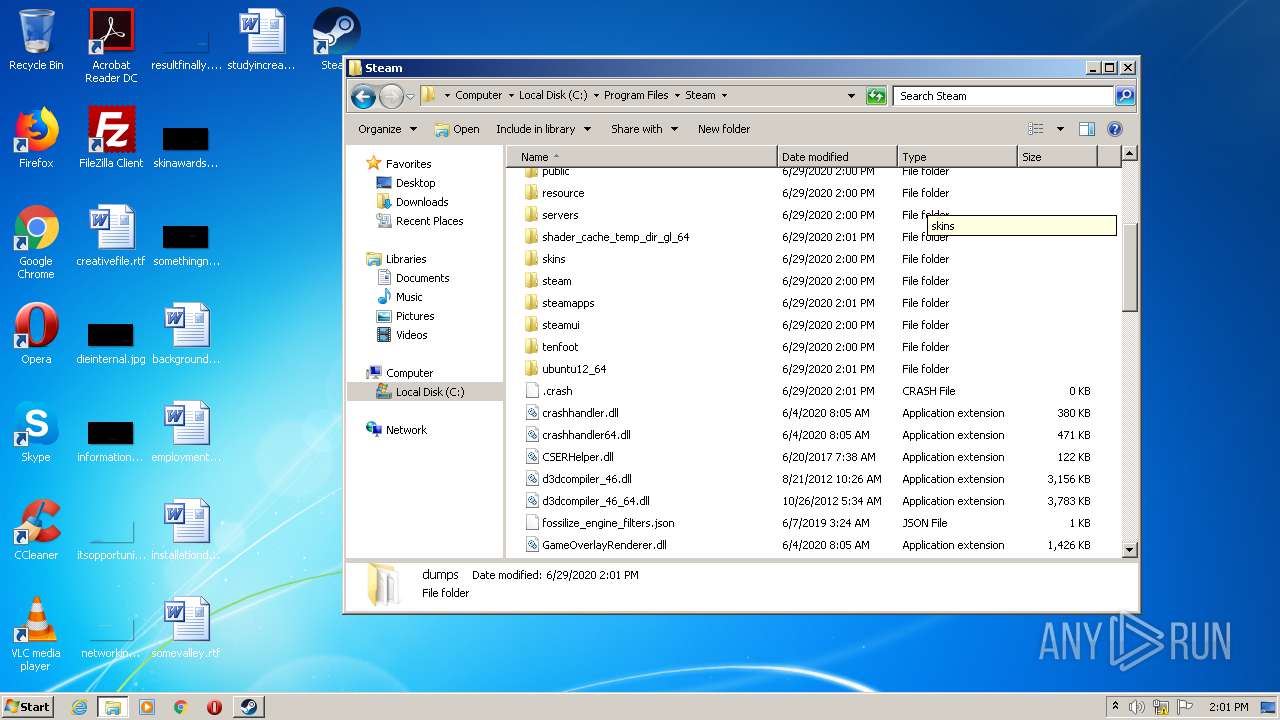
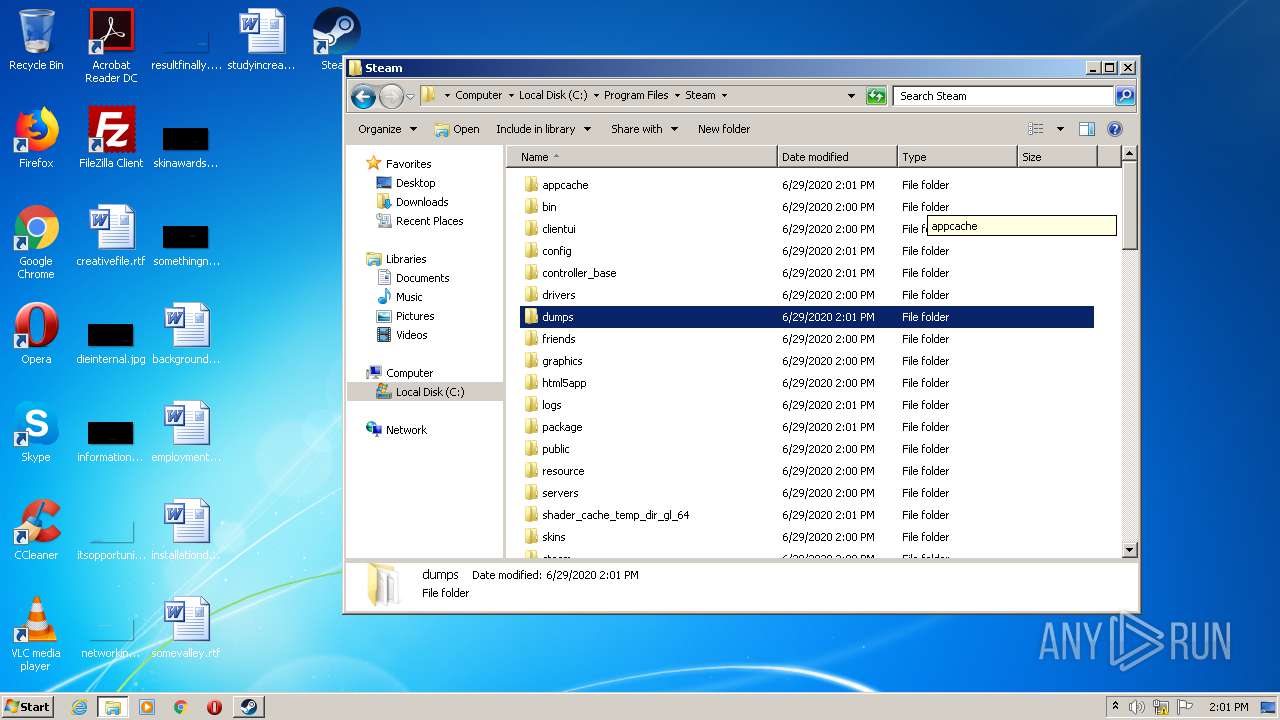
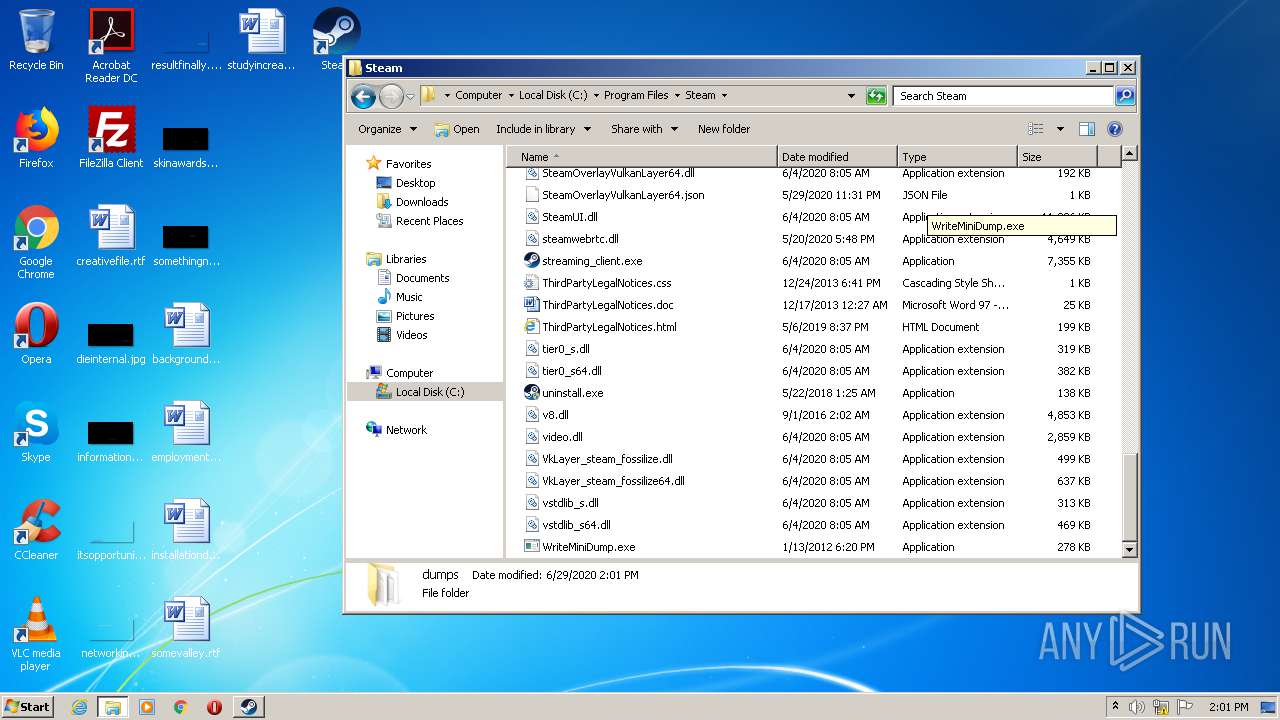
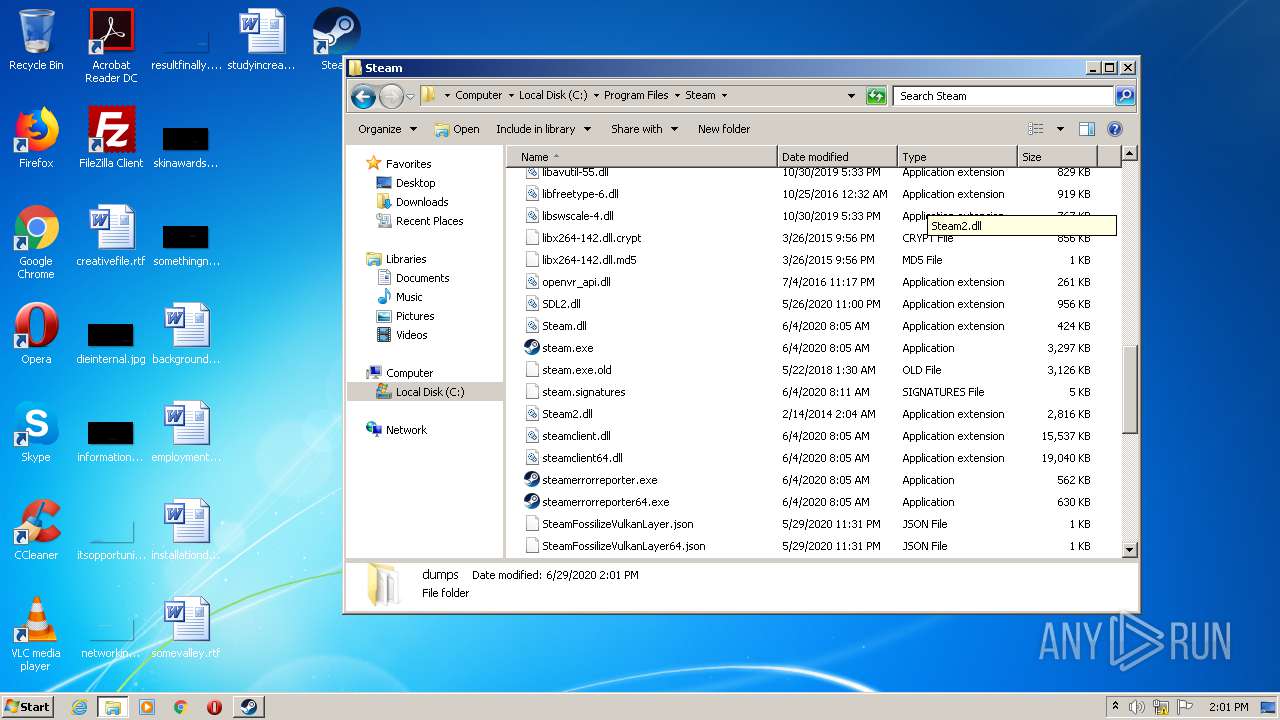
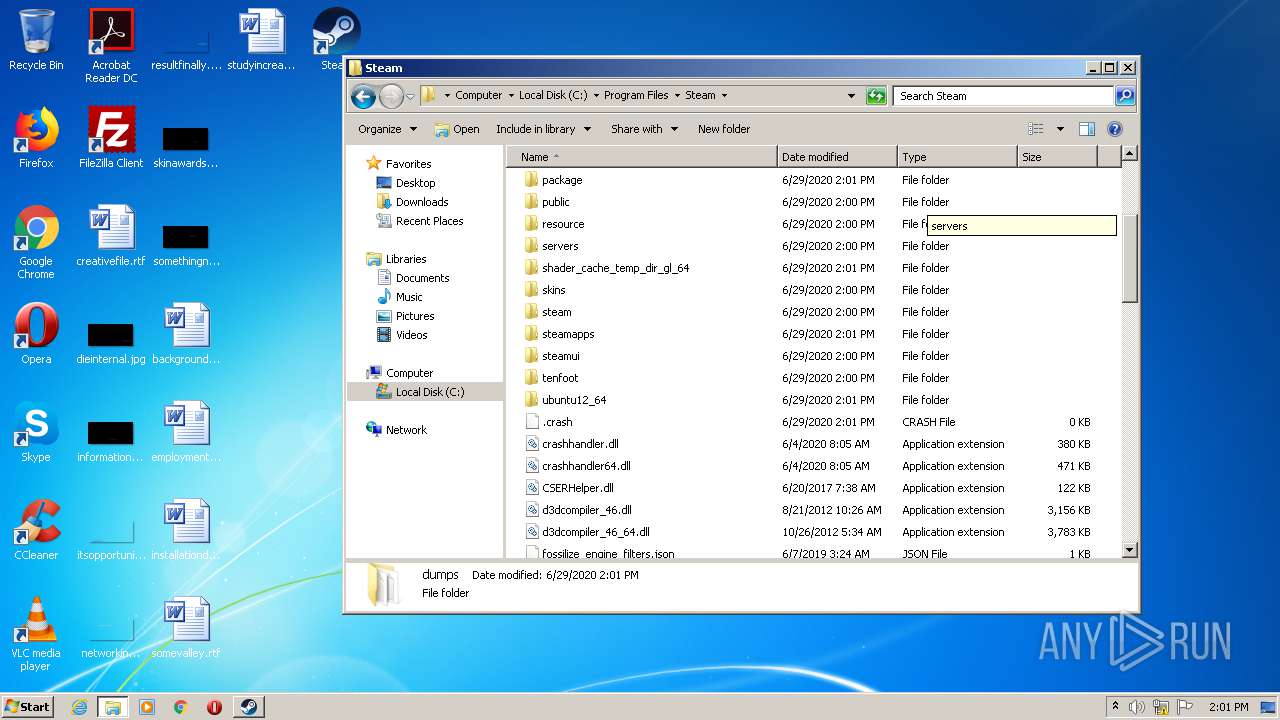
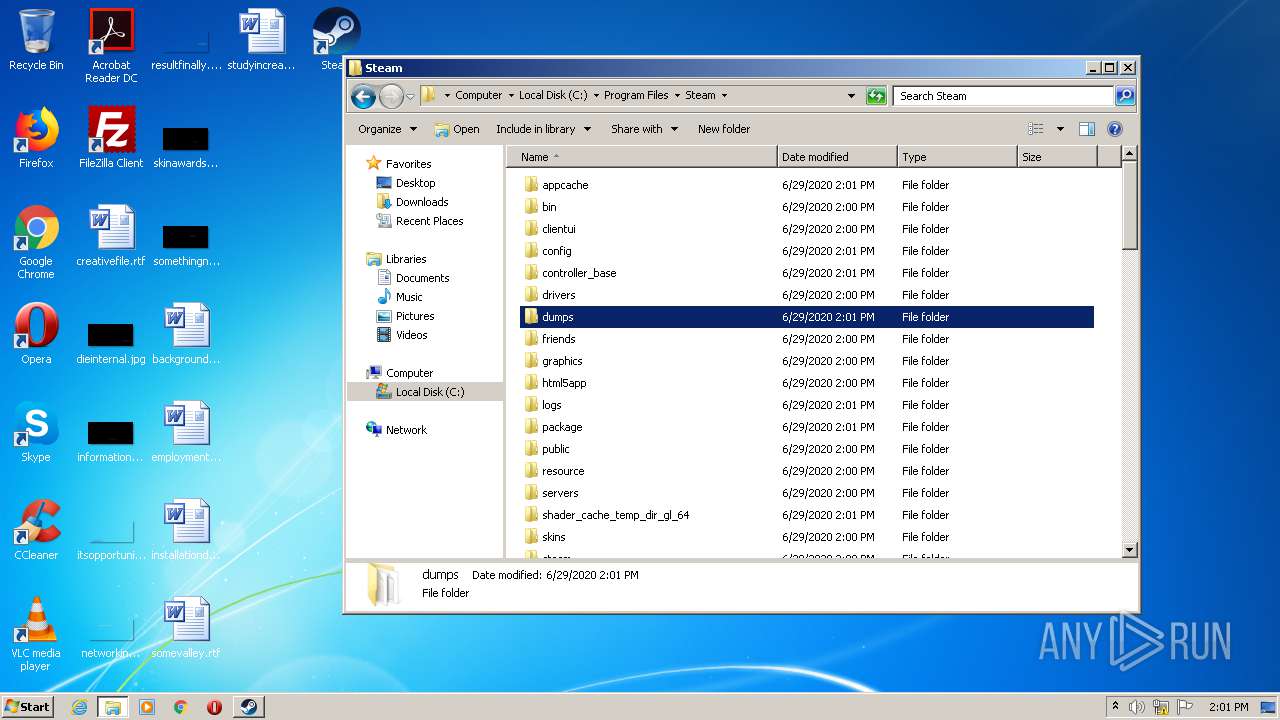
Creates files in the program directory
- SteamSetup.exe (PID: 2944)
- steam.exe (PID: 852)
- steamwebhelper.exe (PID: 2132)
- steamwebhelper.exe (PID: 3820)
- SteamService.exe (PID: 956)
- steam.exe (PID: 3736)
Starts application with an unusual extension
- SteamSetup.exe (PID: 2944)
Modifies the open verb of a shell class
- steamservice.exe (PID: 3188)
- SteamService.exe (PID: 956)
Creates a software uninstall entry
- SteamSetup.exe (PID: 2944)
Executed as Windows Service
- SteamService.exe (PID: 2764)
- SteamService.exe (PID: 956)
Application launched itself
- steamwebhelper.exe (PID: 3820)
Creates files in the Windows directory
- SteamService.exe (PID: 2764)
- SteamService.exe (PID: 956)
Removes files from Windows directory
- SteamService.exe (PID: 2764)
- SteamService.exe (PID: 956)
Adds / modifies Windows certificates
- SteamService.exe (PID: 2764)
INFO
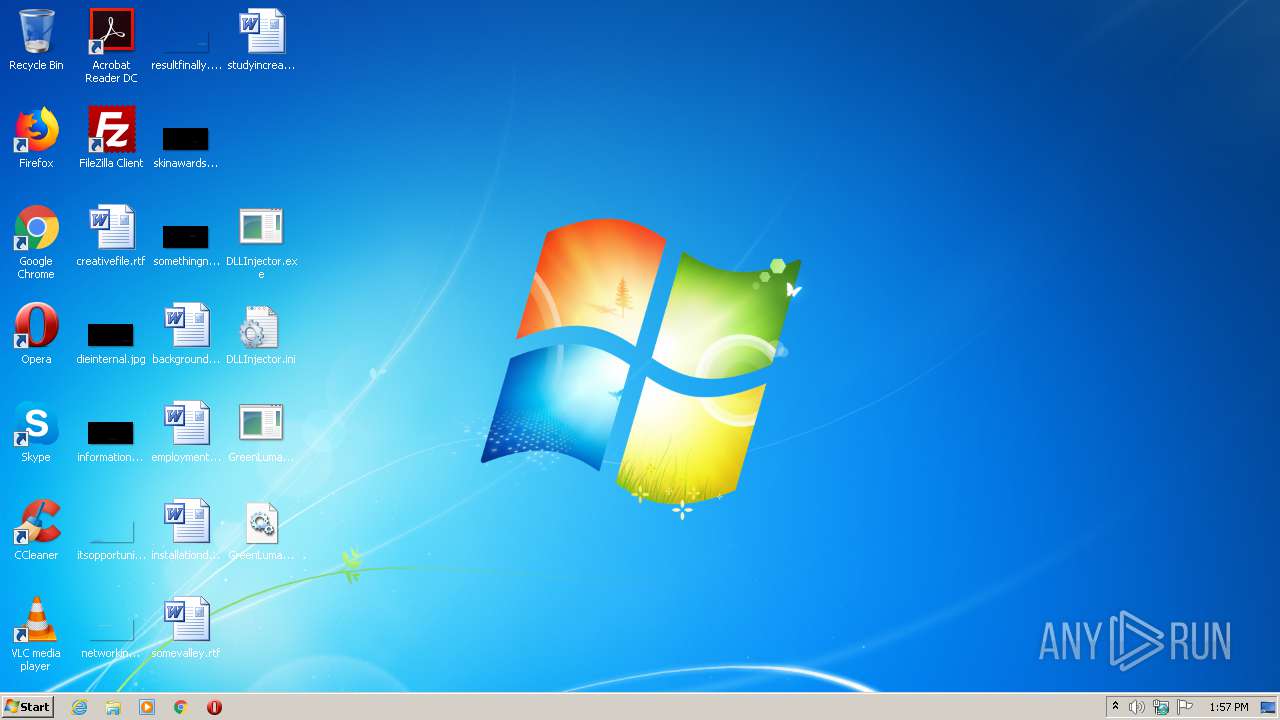
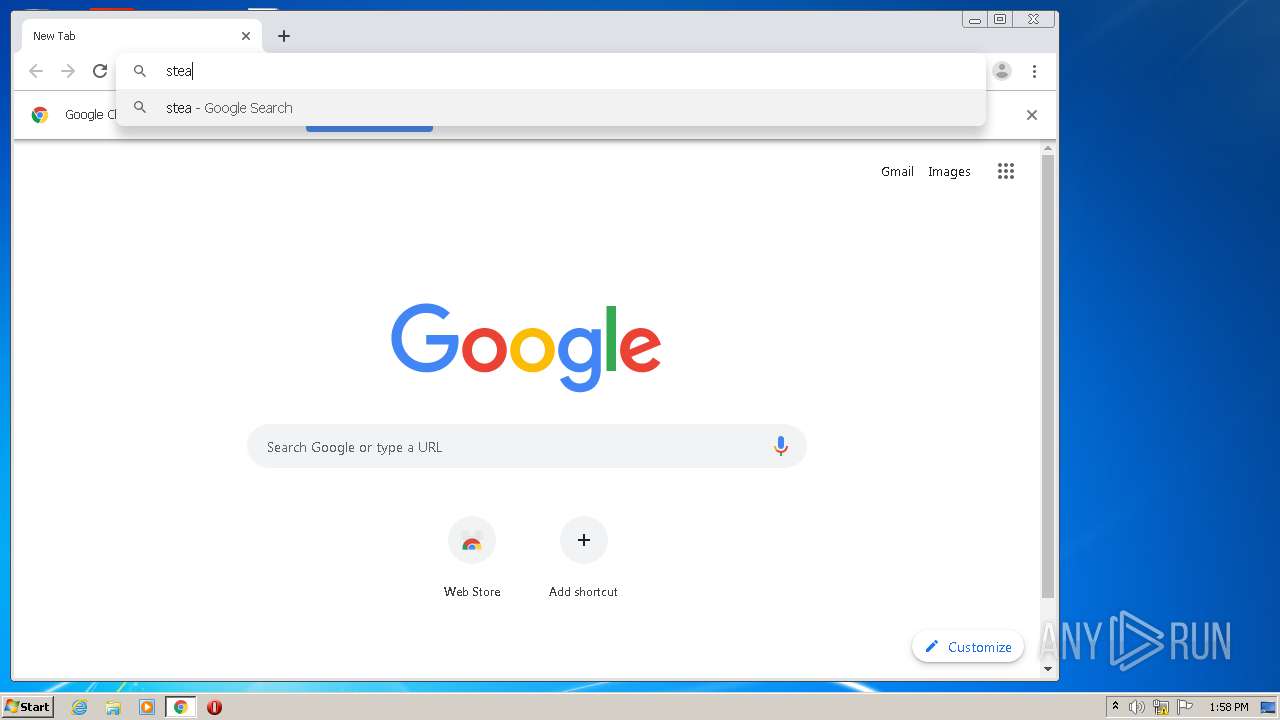
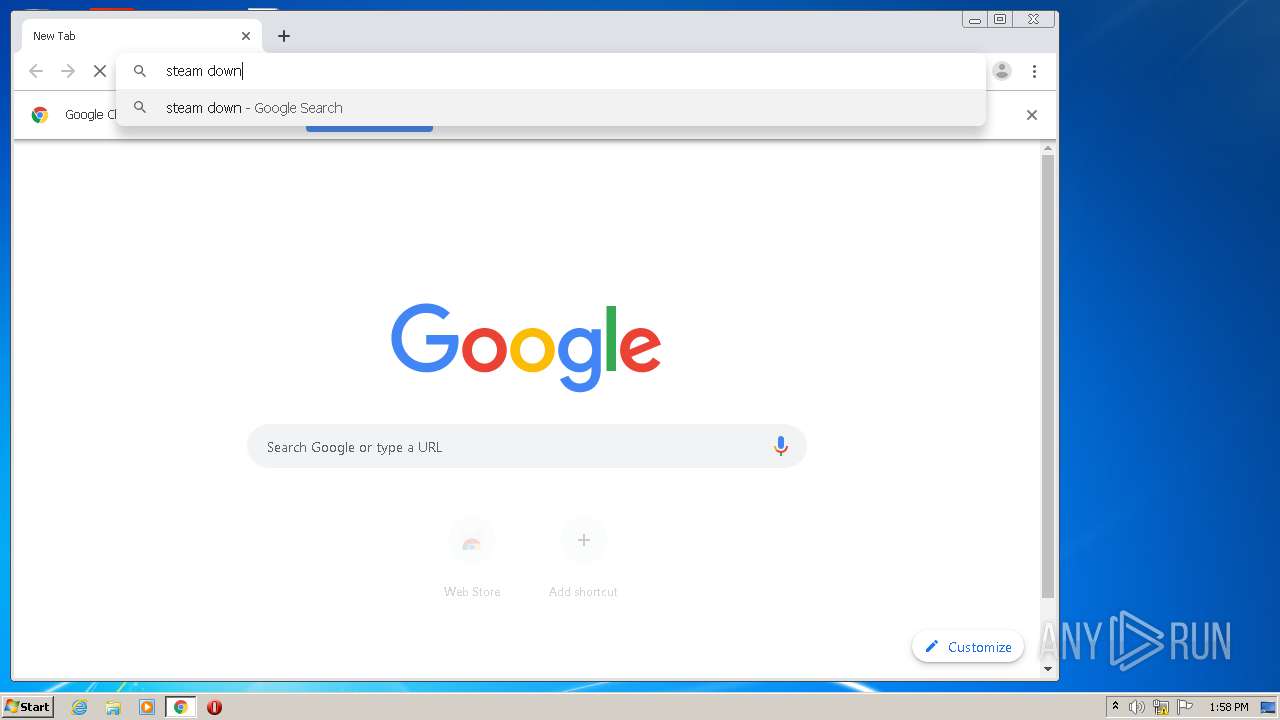
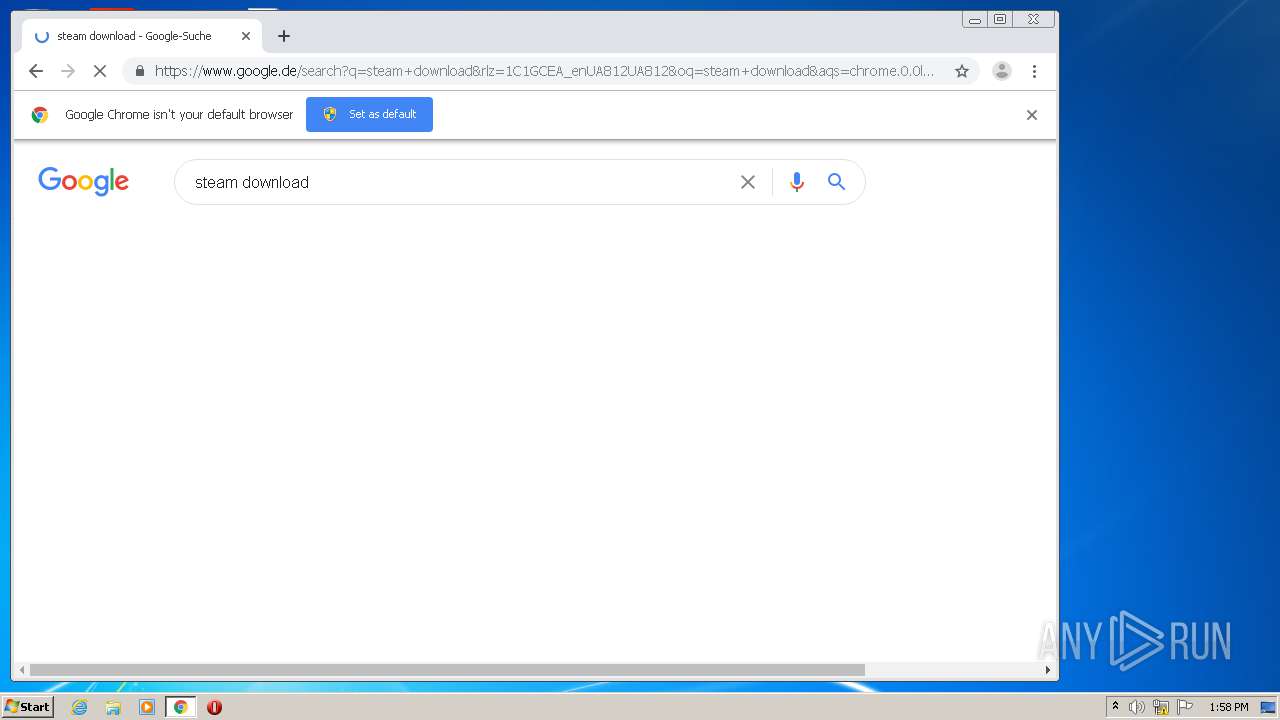
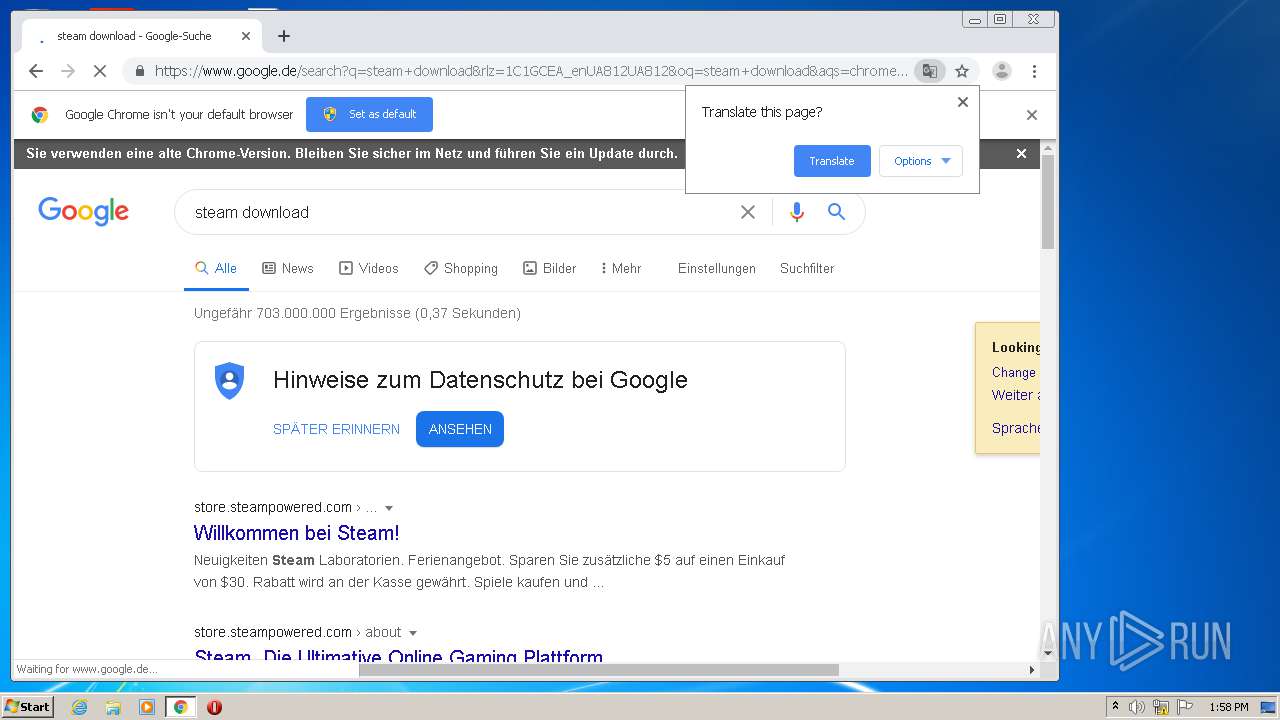
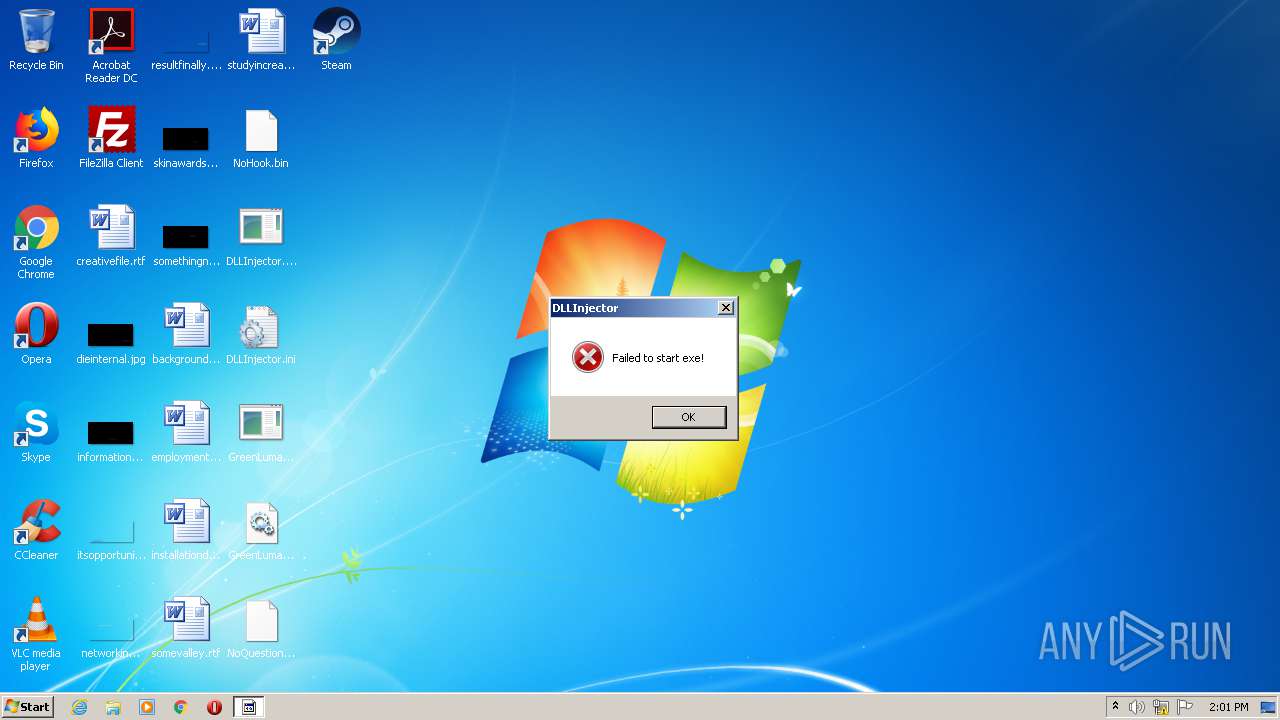
Manual execution by user
- DLLInjector.exe (PID: 2296)
- GreenLumaSettings_2020.exe (PID: 2556)
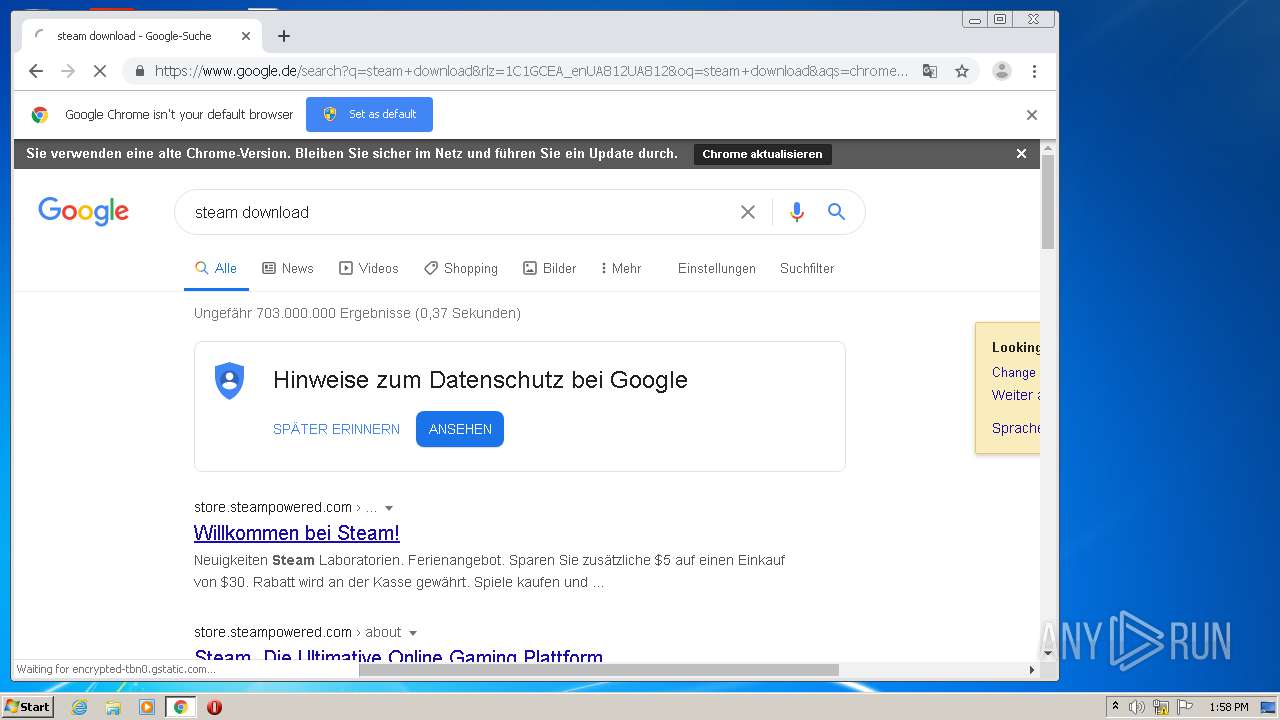
- chrome.exe (PID: 1580)
- steam.exe (PID: 3736)
- DLLInjector.exe (PID: 3724)
Reads the hosts file
- chrome.exe (PID: 1580)
- chrome.exe (PID: 3756)
- steamwebhelper.exe (PID: 3820)
- steamwebhelper.exe (PID: 2940)
Application launched itself
- chrome.exe (PID: 1580)
Reads Internet Cache Settings
- chrome.exe (PID: 1580)
Reads settings of System Certificates
- chrome.exe (PID: 1580)
- chrome.exe (PID: 3756)
- SteamService.exe (PID: 2764)
- steam.exe (PID: 852)
Dropped object may contain Bitcoin addresses
- steam.exe (PID: 3736)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
99
Monitored processes
51
Malicious processes
11
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 124 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,7935491647901104252,11196086287243912083,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13747261847500313152 --mojo-platform-channel-handle=3392 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 348 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 440 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,7935491647901104252,11196086287243912083,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9328032297218904022 --renderer-client-id=15 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3844 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 572 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=1336 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 748 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,7935491647901104252,11196086287243912083,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17418848142536868743 --mojo-platform-channel-handle=3664 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 852 | "C:\Program Files\Steam\steam.exe" | C:\Program Files\Steam\steam.exe | steam.exe | ||||||||||||
User: admin Company: Valve Corporation Integrity Level: MEDIUM Description: Steam Client Bootstrapper Exit code: 0 Version: 05.90.98.72 Modules
| |||||||||||||||
| 956 | "C:\Program Files\Common Files\Steam\SteamService.exe" /RunAsService | C:\Program Files\Common Files\Steam\SteamService.exe | services.exe | ||||||||||||
User: SYSTEM Company: Valve Corporation Integrity Level: SYSTEM Description: Steam Client Service Exit code: 0 Version: 05.90.98.72 Modules
| |||||||||||||||
| 1020 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,7935491647901104252,11196086287243912083,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17384308592663878300 --renderer-client-id=19 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4552 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1264 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,7935491647901104252,11196086287243912083,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12656865937437282047 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2496 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1296 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,7935491647901104252,11196086287243912083,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11470979926920406170 --mojo-platform-channel-handle=1152 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
10 468
Read events
8 733
Write events
1 727
Delete events
8
Modification events
| (PID) Process: | (1340) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1340) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1340) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1340) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\NetworkExplorer.dll,-1 |
Value: Network | |||
| (PID) Process: | (1340) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\GreenLuma 2020 1.1.1.rar | |||
| (PID) Process: | (1340) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1340) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1340) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1340) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (348) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.rar\OpenWithList |
| Operation: | write | Name: | a |
Value: WinRAR.exe | |||
Executable files
155
Suspicious files
150
Text files
4 643
Unknown types
197
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1340 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1340.27308\DLLInjector.exe | — | |
MD5:— | SHA256:— | |||
| 1340 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1340.27308\DLLInjector.ini | — | |
MD5:— | SHA256:— | |||
| 1340 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1340.27308\GreenLuma_2020_x86.dll | — | |
MD5:— | SHA256:— | |||
| 1340 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1340.27308\GreenLumaSettings_2020.exe | — | |
MD5:— | SHA256:— | |||
| 1580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5EF9E55F-62C.pma | — | |
MD5:— | SHA256:— | |||
| 1580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\dc7d7454-849a-4452-942f-887f4abf4d86.tmp | — | |
MD5:— | SHA256:— | |||
| 1580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF106b7d.TMP | text | |
MD5:— | SHA256:— | |||
| 348 | explorer.exe | C:\Users\admin\Desktop\DLLInjector.exe | executable | |
MD5:— | SHA256:— | |||
| 1580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 348 | explorer.exe | C:\Users\admin\Desktop\GreenLumaSettings_2020.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
36
TCP/UDP connections
58
DNS requests
38
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3736 | steam.exe | GET | 302 | 155.133.250.107:80 | http://client-download.steampowered.com/client/steam_client_win32 | PE | — | — | whitelisted |
3756 | chrome.exe | GET | 302 | 172.217.23.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 519 b | whitelisted |
3756 | chrome.exe | GET | 302 | 172.217.23.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvY2Y1QUFXUjZlVjI5UldyLVpDTFJFcEx6QQ/7719.805.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 524 b | whitelisted |
3736 | steam.exe | GET | 200 | 2.16.186.59:80 | http://media4.steampowered.com/client/steam_client_win32?1591402071 | unknown | text | 4.41 Kb | whitelisted |
3756 | chrome.exe | GET | 200 | 173.194.150.249:80 | http://r3---sn-2gb7sn7z.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvY2Y1QUFXUjZlVjI5UldyLVpDTFJFcEx6QQ/7719.805.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=Nf&mip=45.135.187.22&mm=28&mn=sn-2gb7sn7z&ms=nvh&mt=1593435376&mv=m&mvi=2&pl=24&shardbypass=yes | US | crx | 823 Kb | whitelisted |
3736 | steam.exe | GET | 200 | 2.16.186.59:80 | http://media4.steampowered.com/client/tenfoot_ambientsounds_all.zip.89b80bcfdd11b2b99257ddbbdc374e2df54e2738 | unknown | ini | 7.60 Mb | whitelisted |
3736 | steam.exe | GET | 200 | 2.16.186.59:80 | http://media4.steampowered.com/client/tenfoot_misc_all.zip.1ca83d76835b4613170f5cead778b176b11f2b0c | unknown | binary | 12.5 Mb | whitelisted |
3756 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAx5qUSwjBGVIJJhX%2BJrHYM%3D | US | der | 471 b | whitelisted |
3736 | steam.exe | GET | 200 | 2.16.186.59:80 | http://media4.steampowered.com/client/tenfoot_all.zip.vz.a09b31c42a796e3aa29861b512054980f83f4bed_2661761 | unknown | binary | 2.54 Mb | whitelisted |
3736 | steam.exe | GET | 200 | 2.16.186.59:80 | http://media4.steampowered.com/client/tenfoot_fonts_all.zip.vz.7673e4cd32b6752bc621d8bc1a7118a9af19b64a_12077027 | unknown | binary | 11.5 Mb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
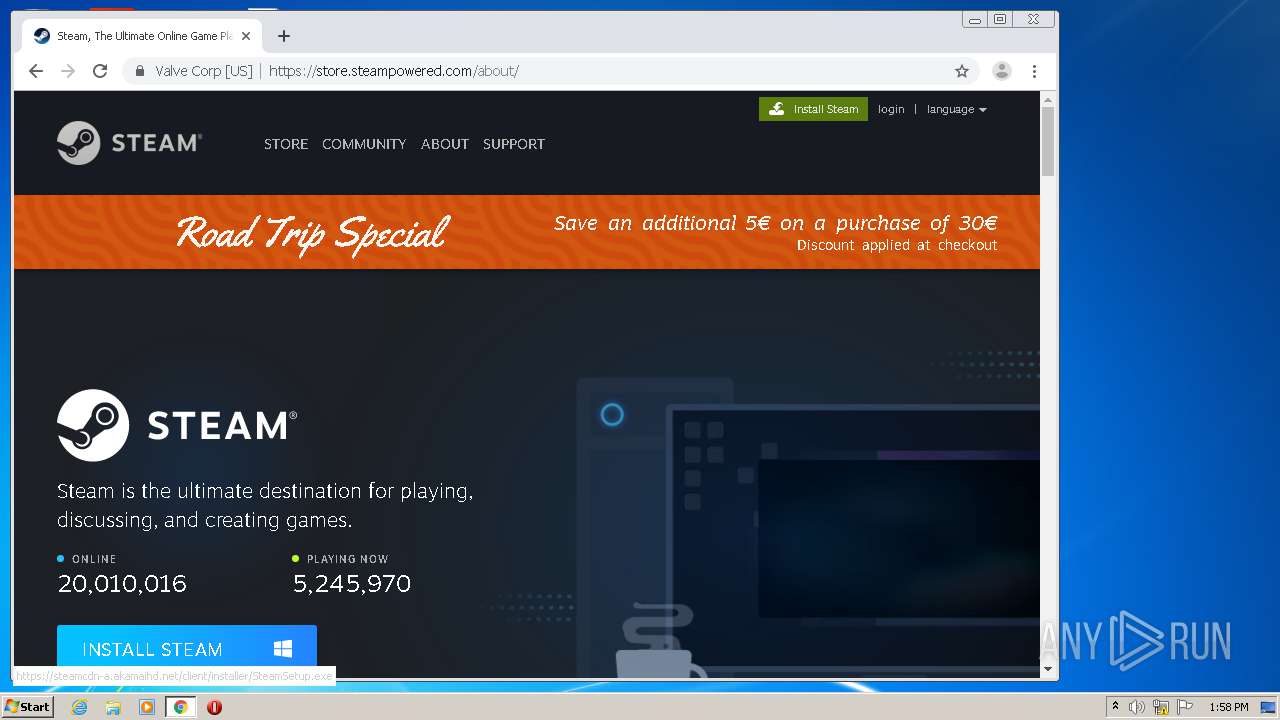
3756 | chrome.exe | 72.247.178.26:443 | steamstore-a.akamaihd.net | Akamai International B.V. | NL | whitelisted |
3756 | chrome.exe | 172.217.23.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3756 | chrome.exe | 216.58.212.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
3756 | chrome.exe | 172.217.22.35:443 | www.google.com.ua | Google Inc. | US | whitelisted |
3756 | chrome.exe | 216.58.210.4:443 | www.google.com | Google Inc. | US | whitelisted |
3756 | chrome.exe | 172.217.18.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3756 | chrome.exe | 216.58.206.3:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3756 | chrome.exe | 172.217.23.110:443 | apis.google.com | Google Inc. | US | whitelisted |
3756 | chrome.exe | 172.217.18.110:443 | ogs.google.com.ua | Google Inc. | US | whitelisted |
3756 | chrome.exe | 172.217.16.206:443 | clients2.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
www.google.com |
| malicious |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com.ua |
| whitelisted |
clients2.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3736 | steam.exe | Potential Corporate Privacy Violation | ET USER_AGENTS Steam HTTP Client User-Agent |
Process | Message |
|---|---|
steam.exe | Loaded SDL version 2.0.13-hg-0:aaaaaaaaaaah
|
steam.exe | C:\Program Files\Steam\steamerrorreporter.exe |
steam.exe | |
steam.exe | |
steam.exe | |
steam.exe | |
steam.exe | |
steamwebhelper.exe | [0629/140102.343:INFO:crash_reporting.cc(247)] Crash reporting enabled for process: browser
|
steamwebhelper.exe | [0629/140102.484:ERROR:widevine_loader.cc(383)] Widevine CDM registration failed; Manifest has no supported x-cdm-interface-versions in '8'
|
steamwebhelper.exe | [0629/140104.218:WARNING:gpu_process_host.cc(1213)] The GPU process has crashed 1 time(s)
|