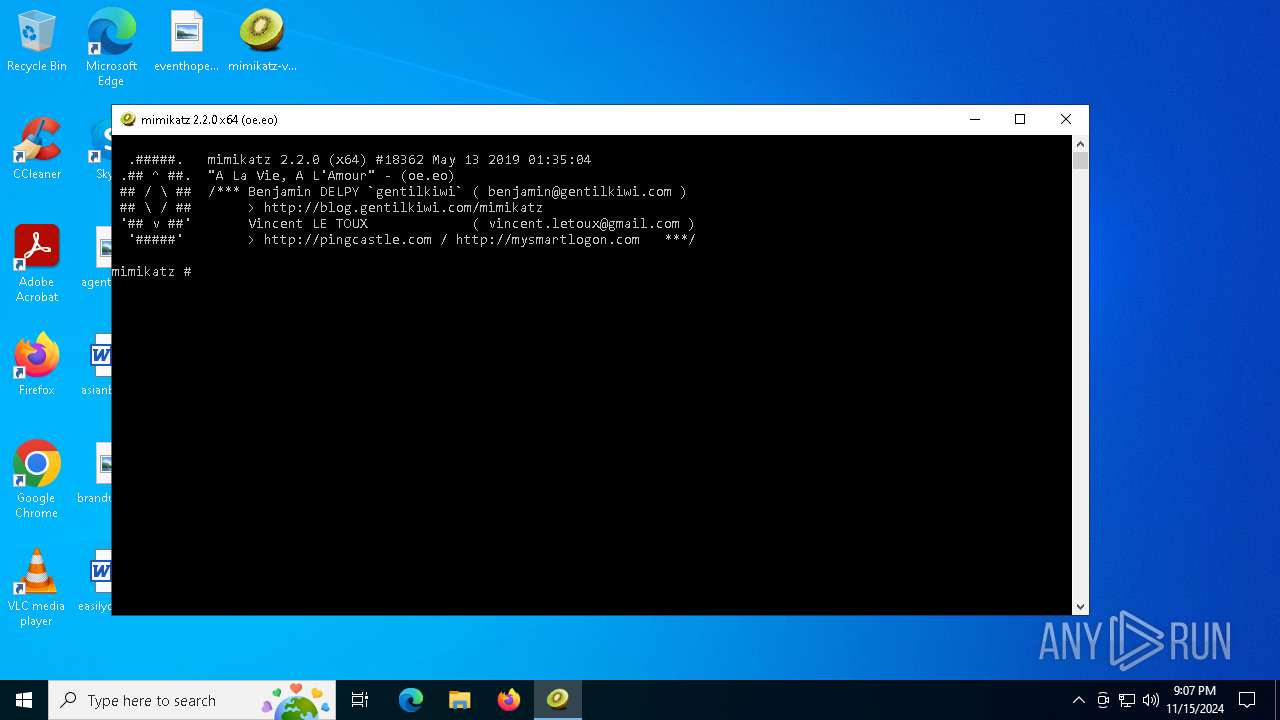
| File name: | mimikatz-vmp.exe |
| Full analysis: | https://app.any.run/tasks/64a7334a-5029-43b3-a623-4f7a81e638ed |
| Verdict: | Malicious activity |
| Analysis date: | November 15, 2024, 21:07:13 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (console) x86-64, for MS Windows, 8 sections |
| MD5: | 5D570DAF6DC6DB5253B789192D6F0C5E |
| SHA1: | BDC8506DF8ACA91AE9F646EDC6E9F8AEB82B02F8 |
| SHA256: | 87A4ADCC8C5C10BDF57E4B5EC13B2D2567437034E908982ED276AA4A62A01EB0 |
| SSDEEP: | 98304:gU7lffZX3U75zMDsY2jNbYo6ktbYxP9utEe+yRd2RQHiue6AShgJ4mCfglh3duHW:wdVgQ+4xvr/t |
MALICIOUS
MIMIKATZ has been detected (YARA)
- mimikatz-vmp.exe (PID: 6660)
SUSPICIOUS
No suspicious indicators.INFO
Checks supported languages
- mimikatz-vmp.exe (PID: 6660)
Reads the computer name
- mimikatz-vmp.exe (PID: 6660)
VMProtect protector has been detected
- mimikatz-vmp.exe (PID: 6660)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2019:05:12 23:35:22+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 9 |
| CodeSize: | 612352 |
| InitializedDataSize: | 386048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x81f307 |
| OSVersion: | 5.2 |
| ImageVersion: | - |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 2.2.0.0 |
| ProductVersionNumber: | 2.2.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Pre-release, Private build, Special build |
| FileOS: | Windows NT |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| ProductName: | mimikatz |
| ProductVersion: | 2.2.0.0 |
| CompanyName: | gentilkiwi (Benjamin DELPY) |
| FileDescription: | mimikatz for Windows |
| FileVersion: | 2.2.0.0 |
| InternalName: | mimikatz |
| LegalCopyright: | Copyright (c) 2007 - 2019 gentilkiwi (Benjamin DELPY) |
| OriginalFileName: | mimikatz.exe |
| PrivateBuild: | Build with love for POC only |
| SpecialBuild: | :) |
Total processes
118
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 5748 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | mimikatz-vmp.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6660 | "C:\Users\admin\Desktop\mimikatz-vmp.exe" | C:\Users\admin\Desktop\mimikatz-vmp.exe | explorer.exe | ||||||||||||
User: admin Company: gentilkiwi (Benjamin DELPY) Integrity Level: MEDIUM Description: mimikatz for Windows Version: 2.2.0.0 Modules
| |||||||||||||||
Total events
52
Read events
52
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
44
TCP/UDP connections
65
DNS requests
17
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6944 | svchost.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6944 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 304 | 4.175.87.197:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | unknown |
— | — | GET | 200 | 104.126.37.155:443 | https://www.bing.com/DSB/search?dsbmr=1&format=dsbjson&client=windowsminiserp&dsbschemaversion=1.1&dsbminiserp=1&q=q&pastMomentsInDays=6&cc=US&setlang=en-us&clientDateTime=11%2F15%2F2024%2C%209%3A07%3A27%20PM | unknown | binary | 153 Kb | whitelisted |
— | — | GET | 200 | 104.126.37.155:443 | https://www.bing.com/DSB/search?dsbmr=1&format=dsbjson&client=windowsminiserp&dsbschemaversion=1.1&dsbminiserp=1&q=q&pastMomentsInDays=6&cc=US&setlang=en-us&clientDateTime=11%2F15%2F2024%2C%209%3A07%3A27%20PM | unknown | binary | 153 Kb | whitelisted |
— | — | POST | 200 | 20.190.159.75:443 | https://login.live.com/RST2.srf | unknown | xml | 1.25 Kb | whitelisted |
— | — | GET | 200 | 104.126.37.178:443 | https://www.bing.com/th?id=ODSWG.6b2ff3e6-3dfc-4f04-8b76-d47fc391cfc9&pid=dsb | unknown | image | 21.6 Kb | whitelisted |
— | — | POST | 204 | 104.126.37.139:443 | https://www.bing.com/threshold/xls.aspx | unknown | — | — | whitelisted |
— | — | POST | 400 | 40.126.31.67:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | unknown | text | 210 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
6944 | svchost.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5488 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
6944 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 2.23.209.158:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4020 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
Threats
2 ETPRO signatures available at the full report