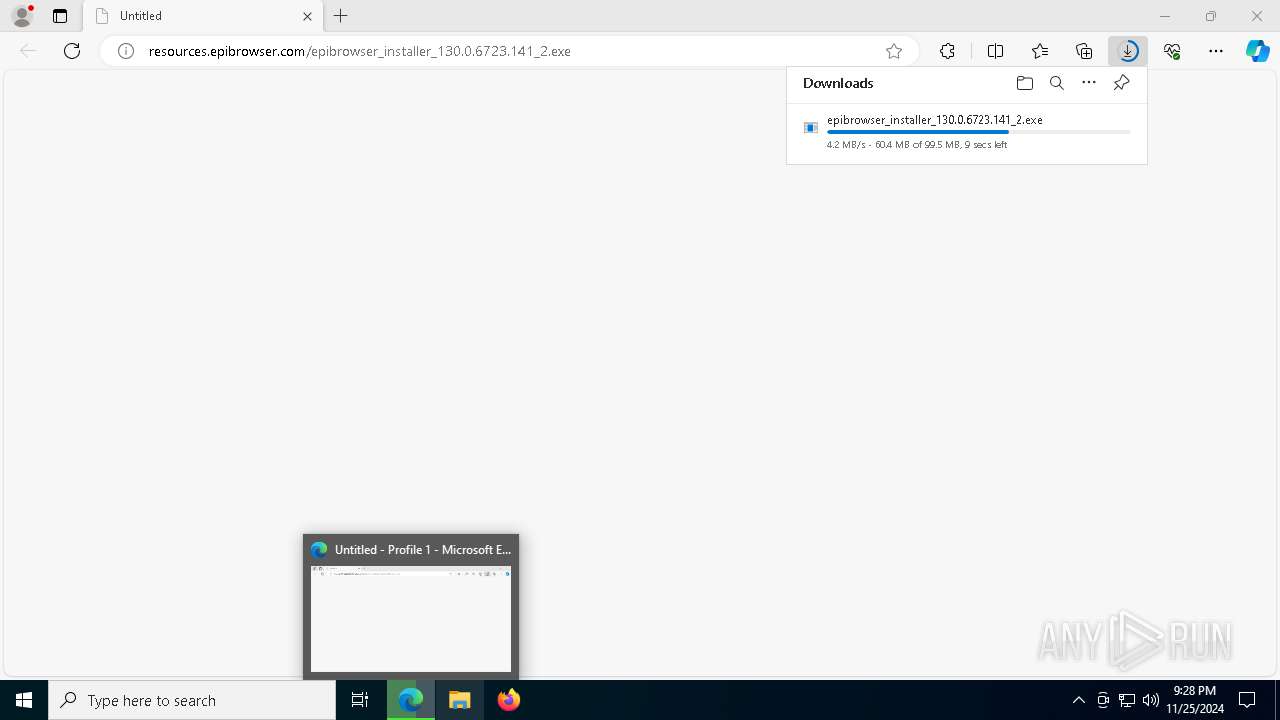
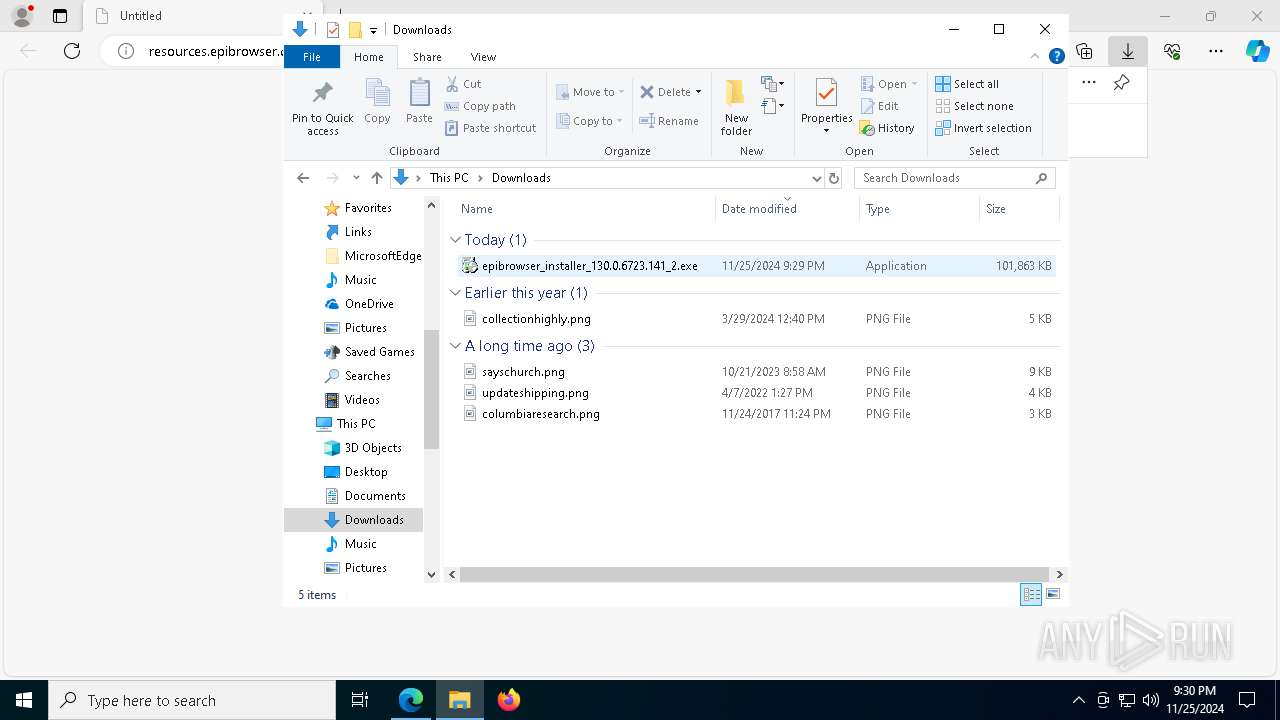
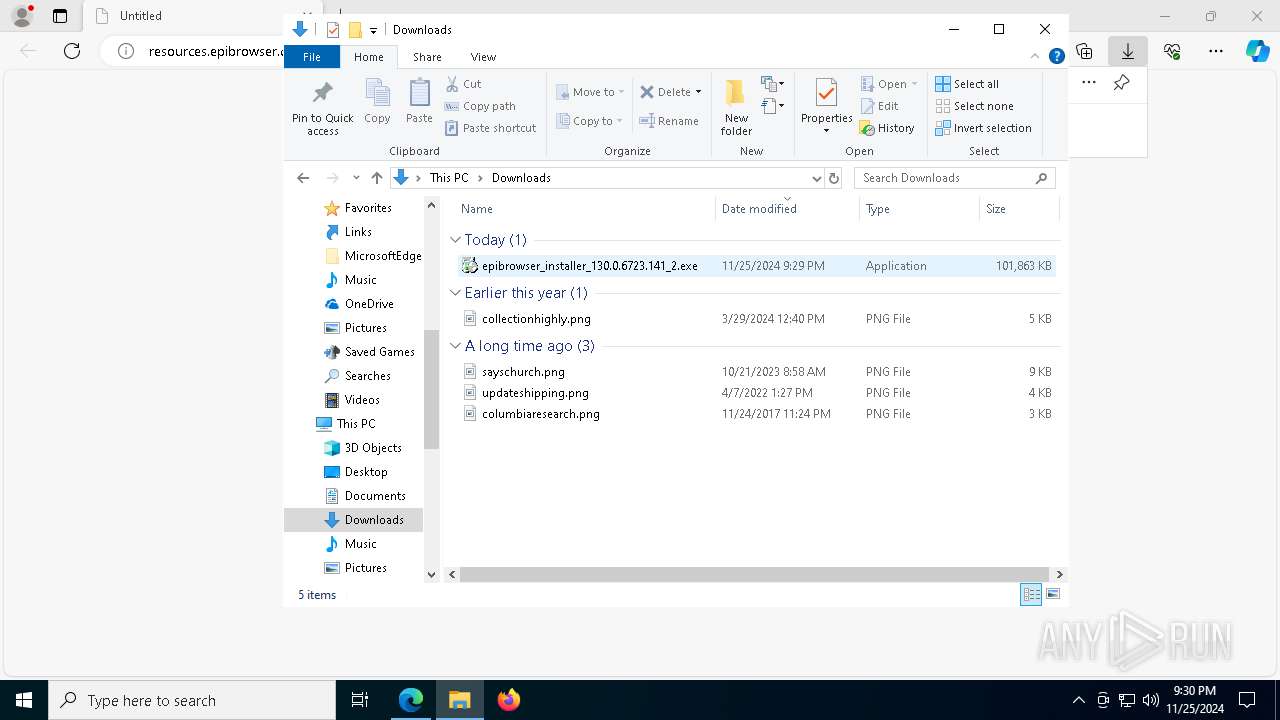
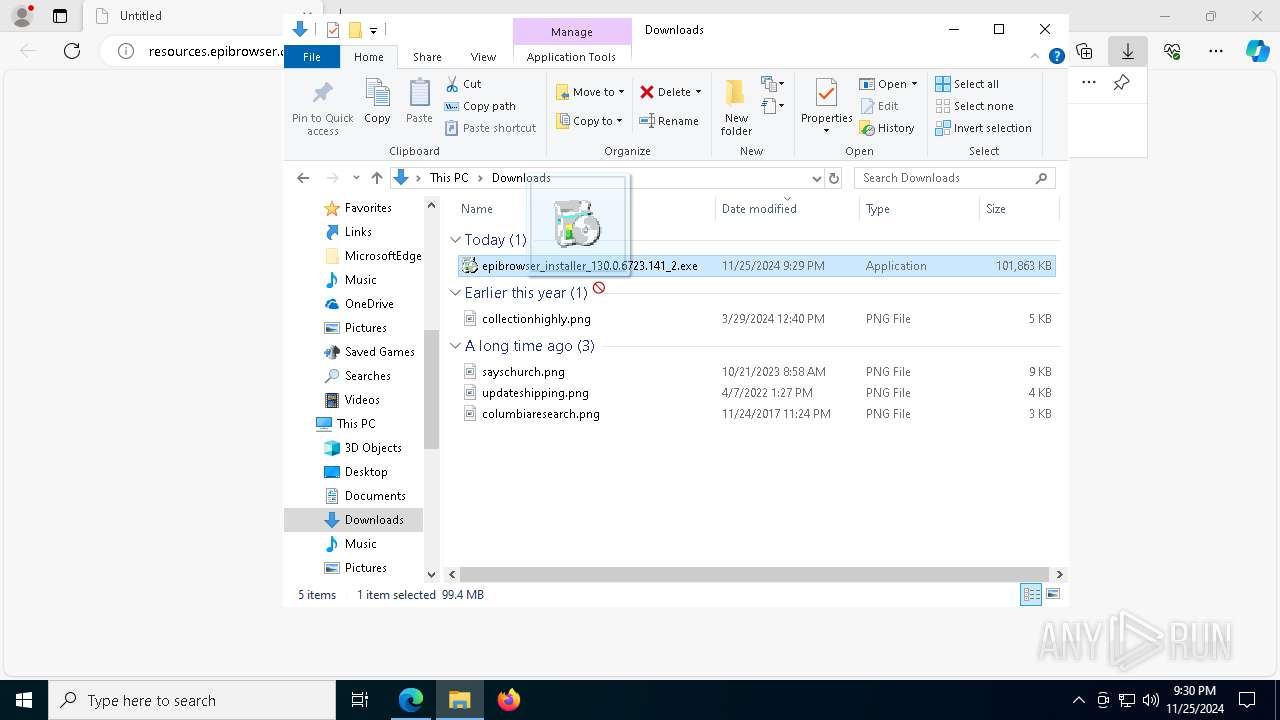
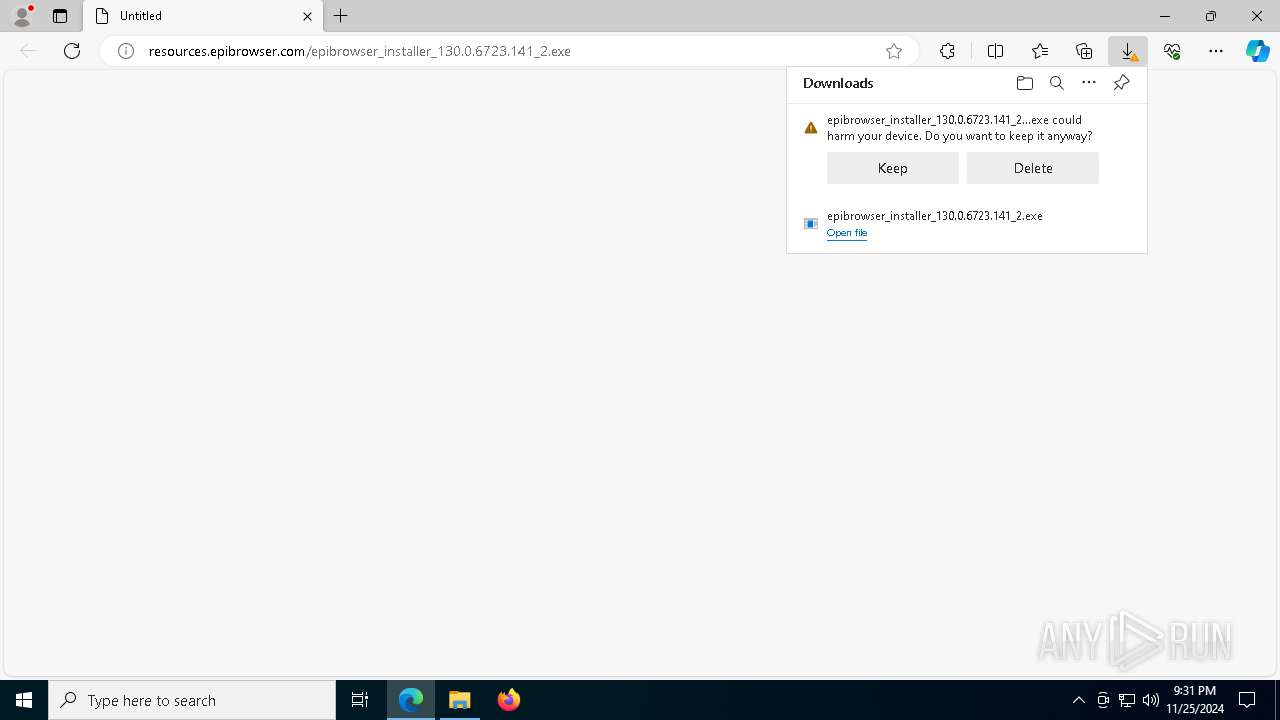
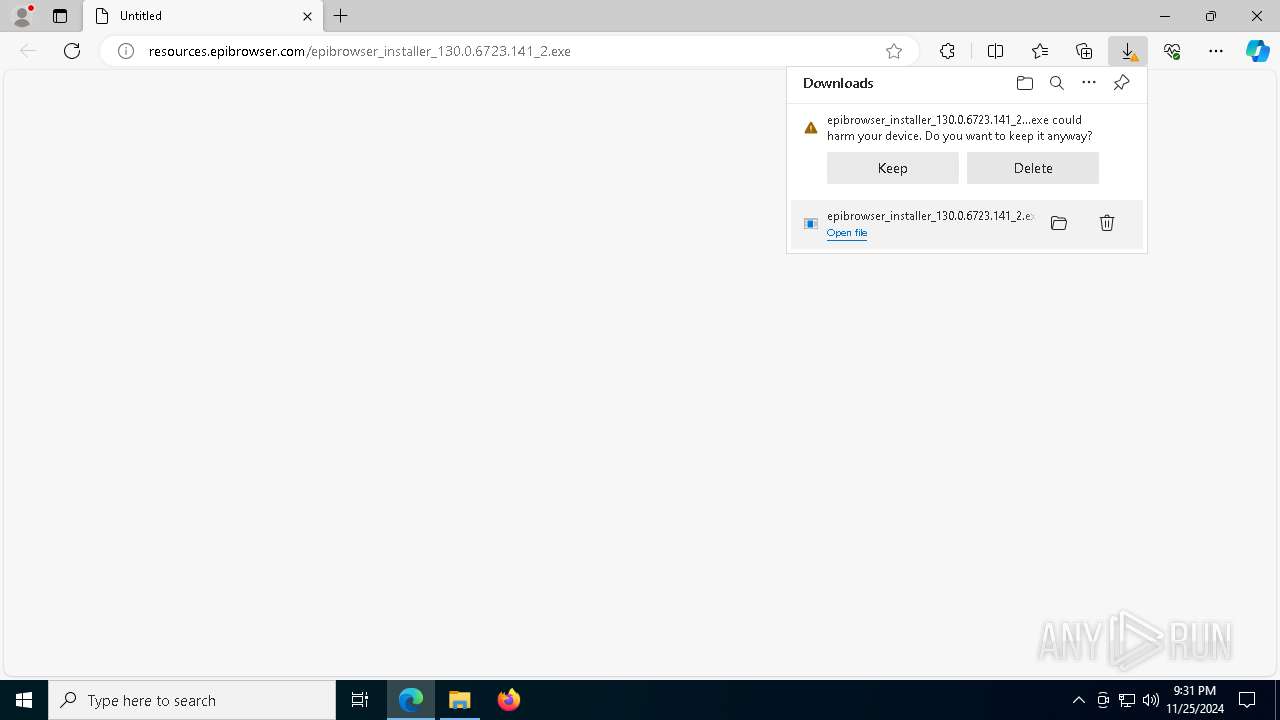
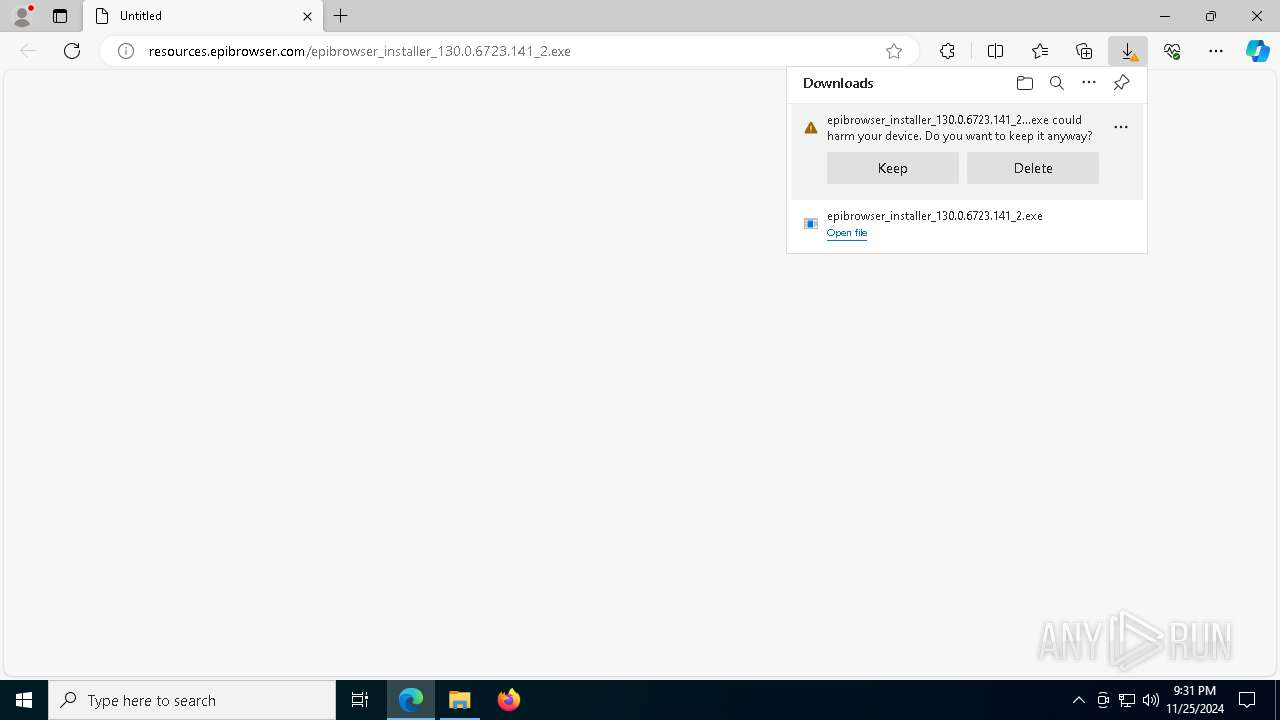
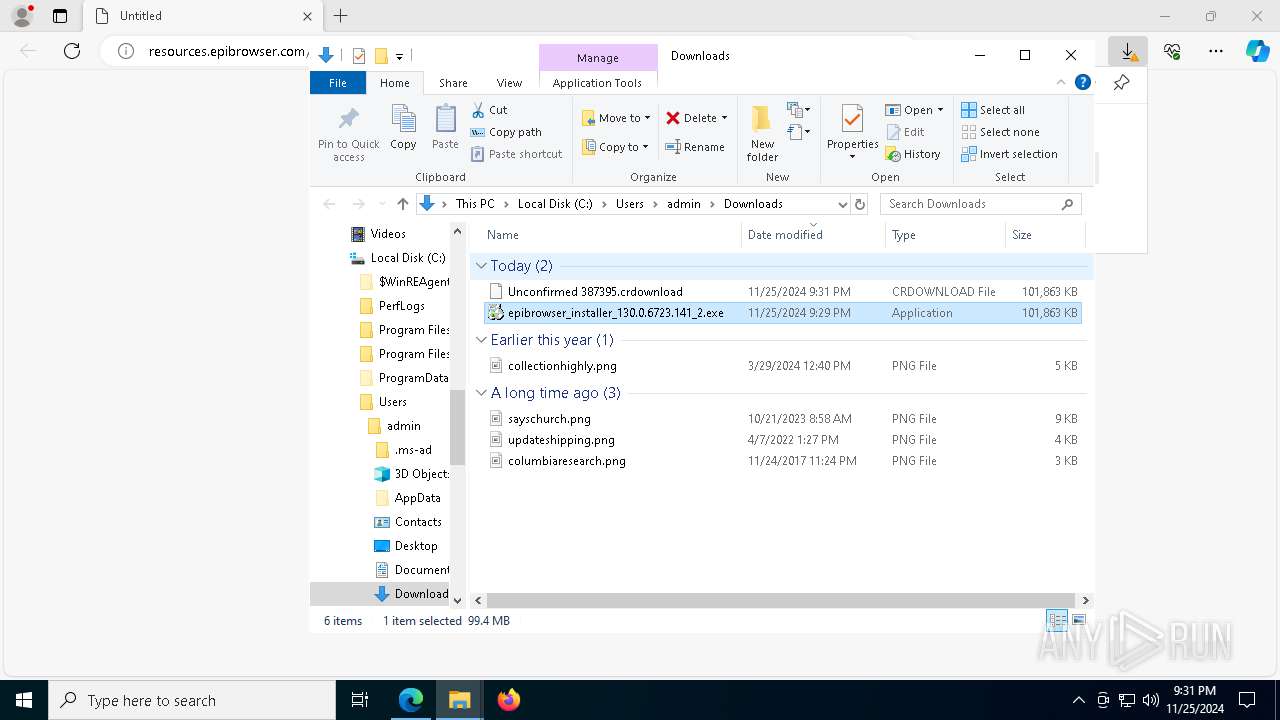
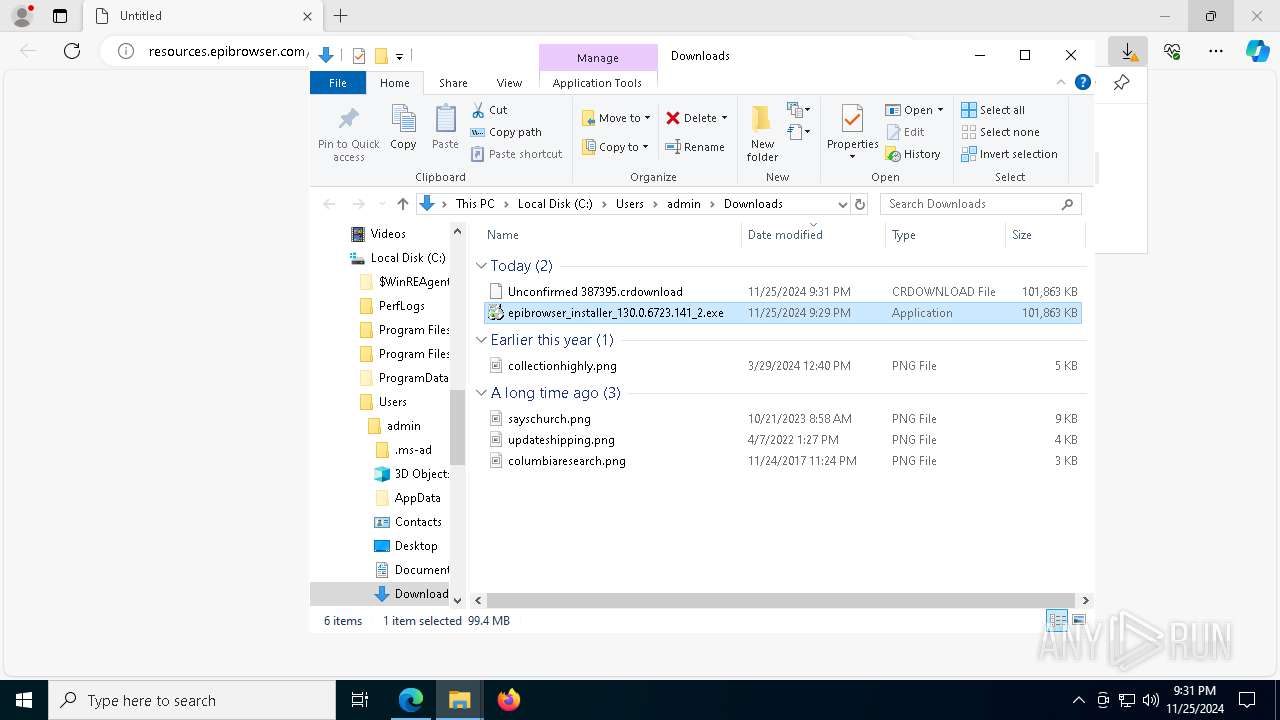
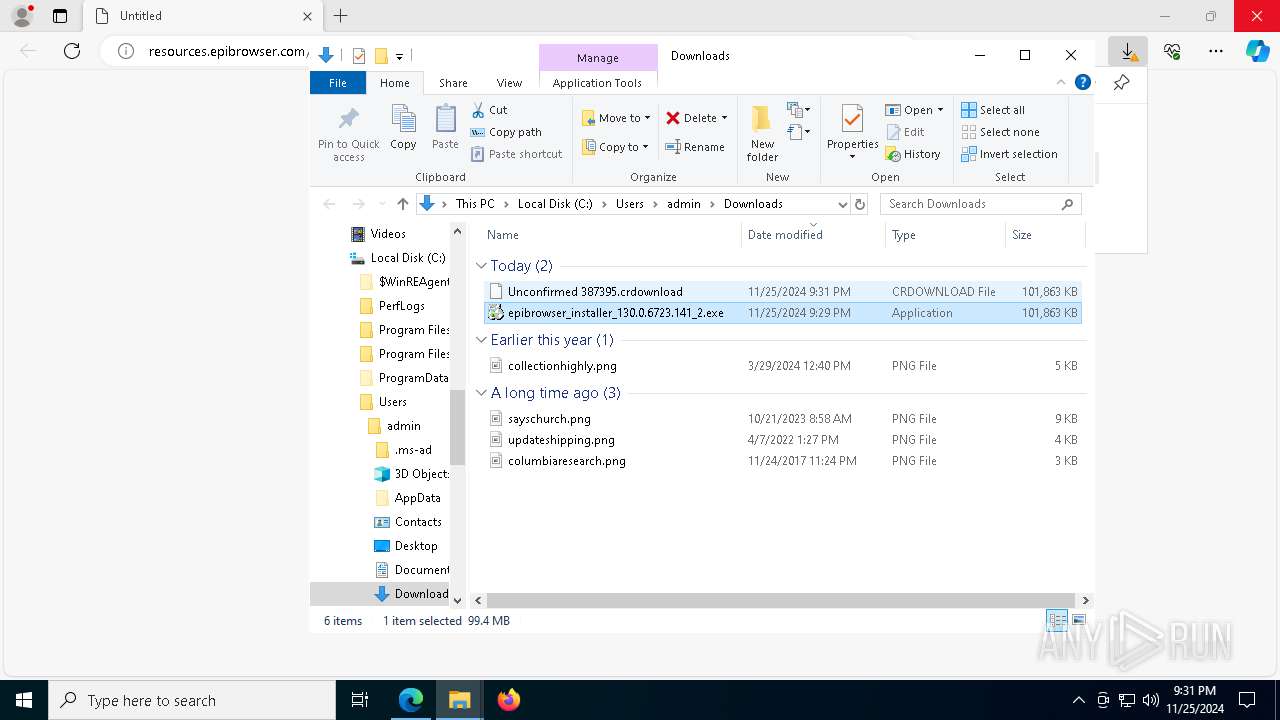
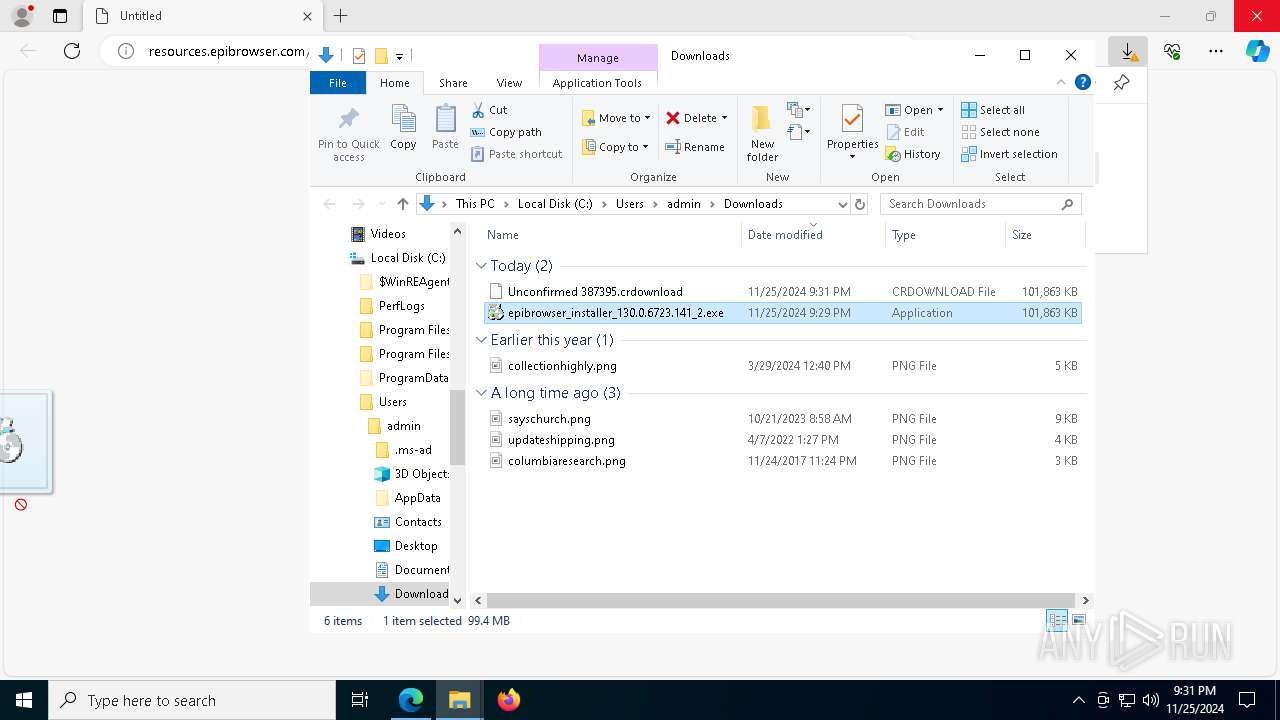
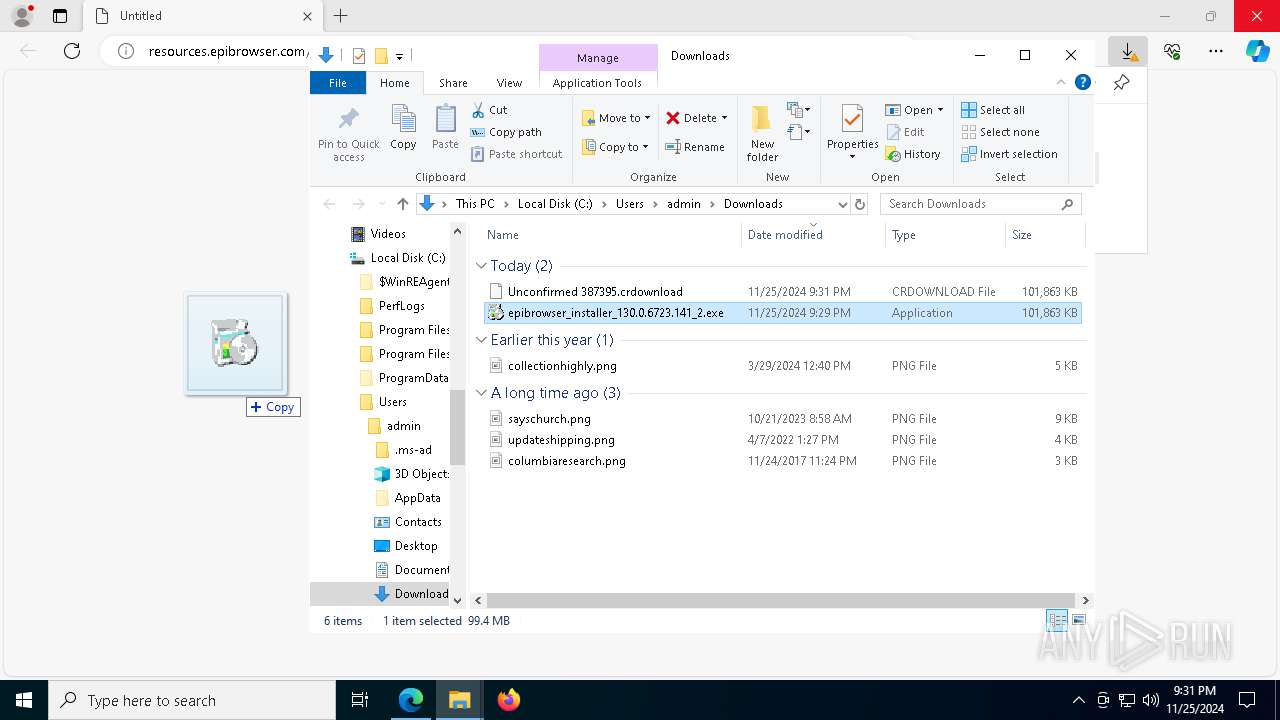
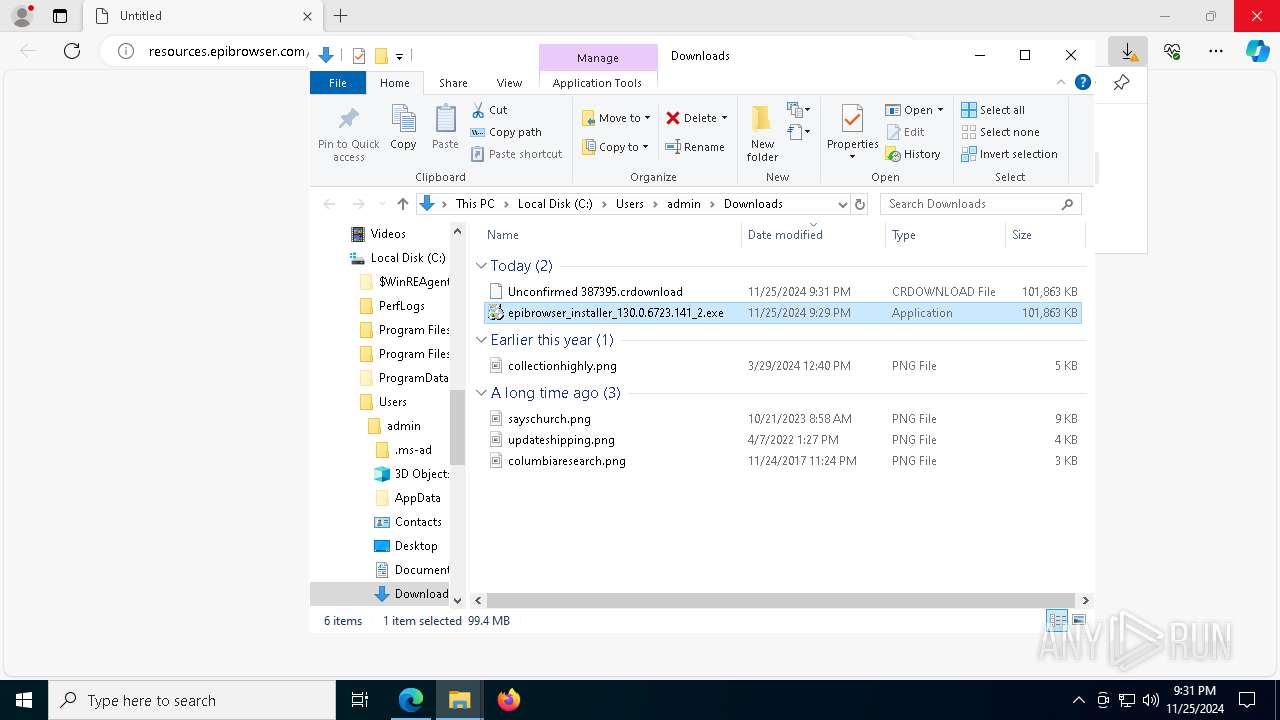
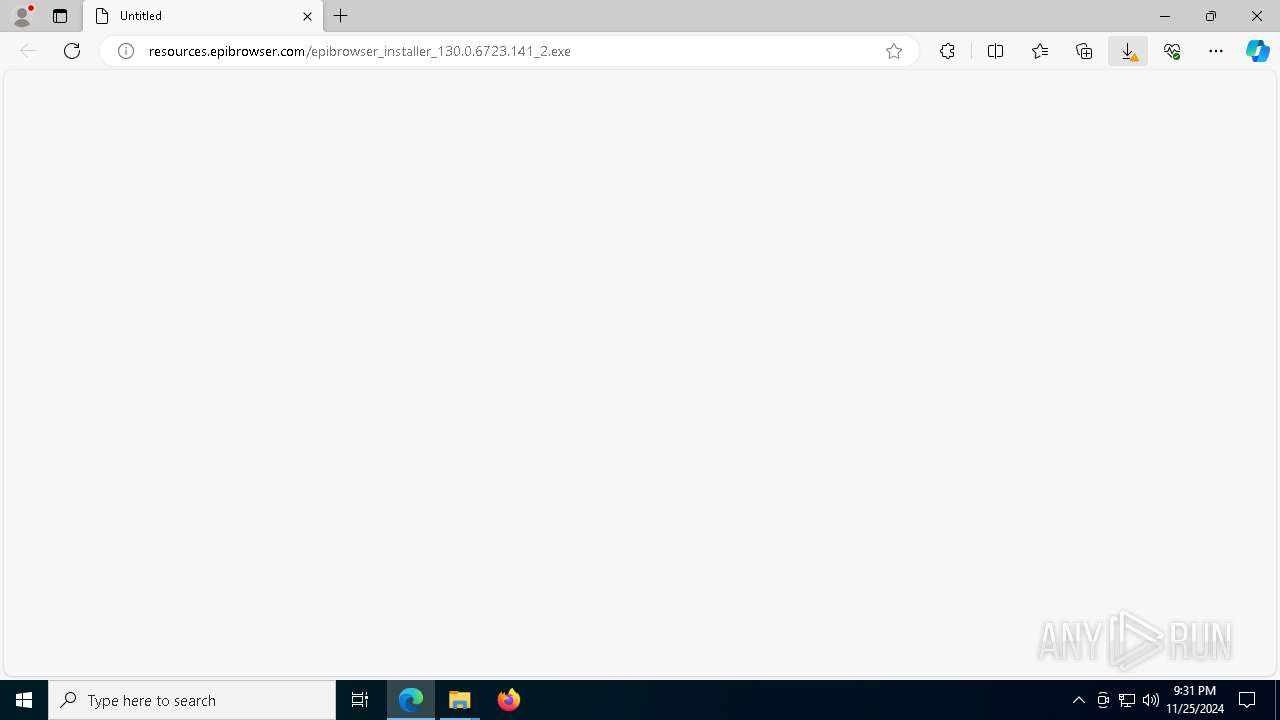
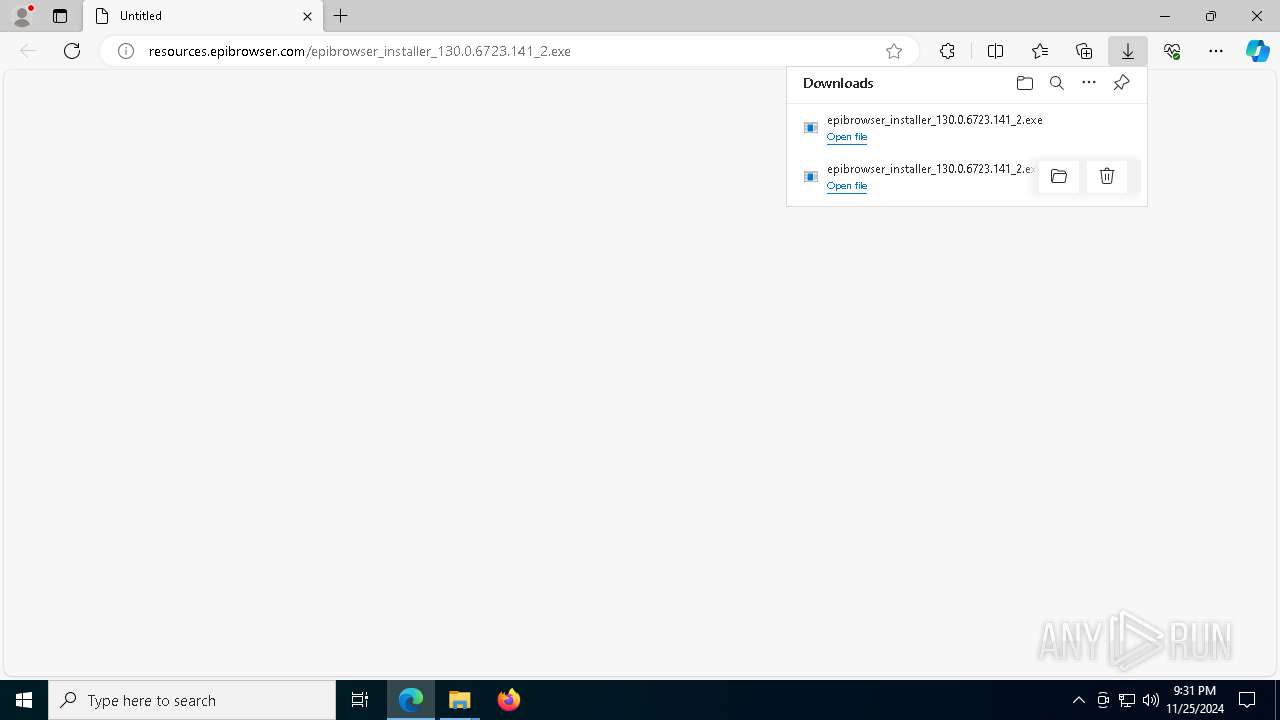
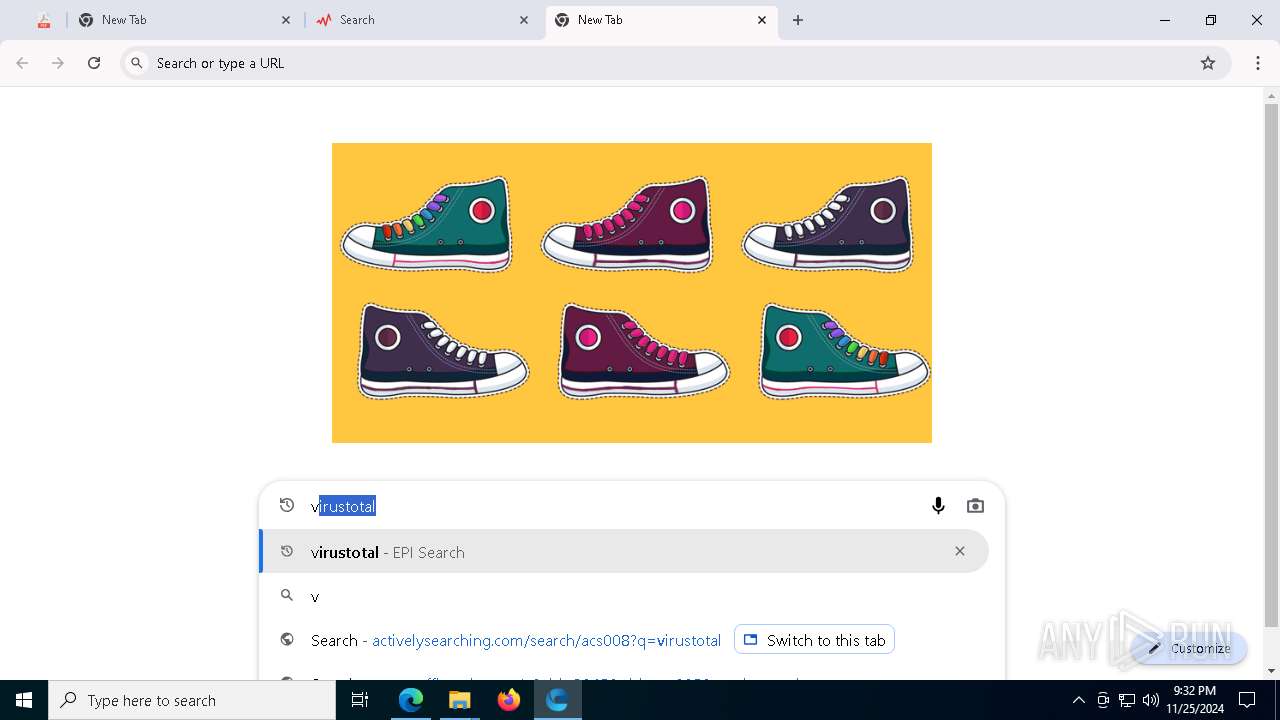
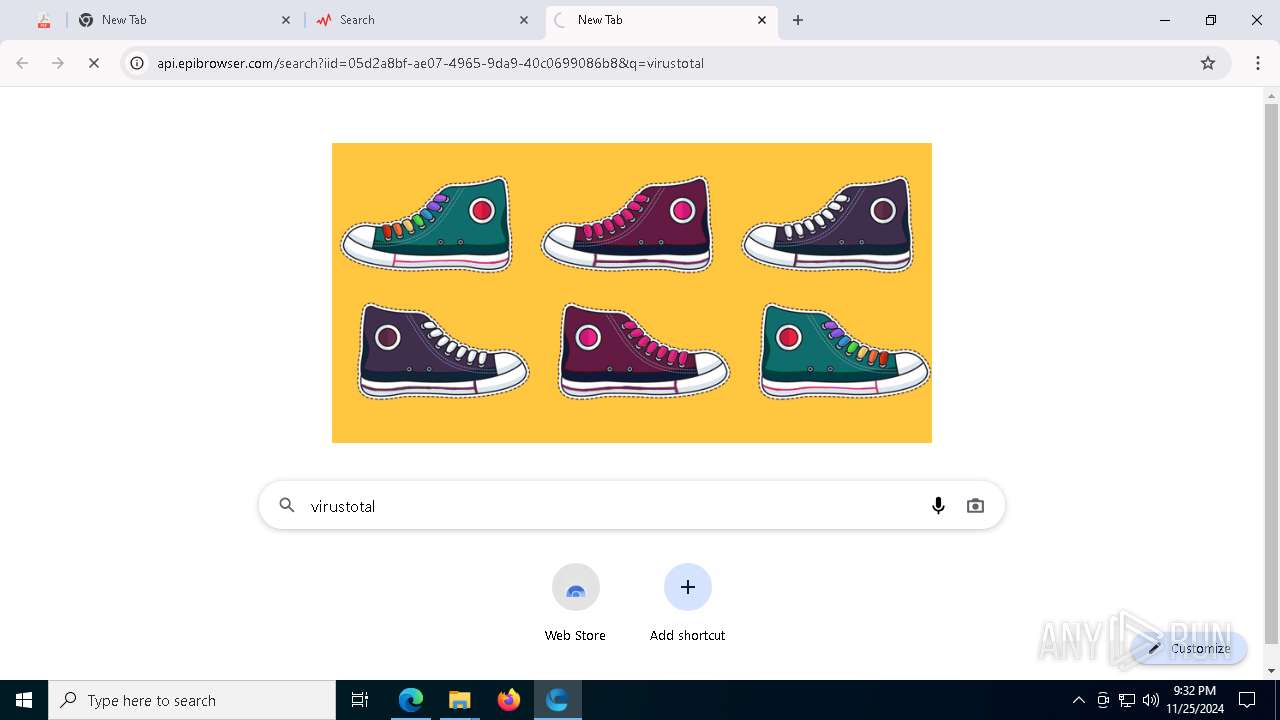
| URL: | resources.epibrowser.com/epibrowser_installer_130.0.6723.141_2.exe |
| Full analysis: | https://app.any.run/tasks/3bd149e6-8a66-4002-a813-94c6368c250a |
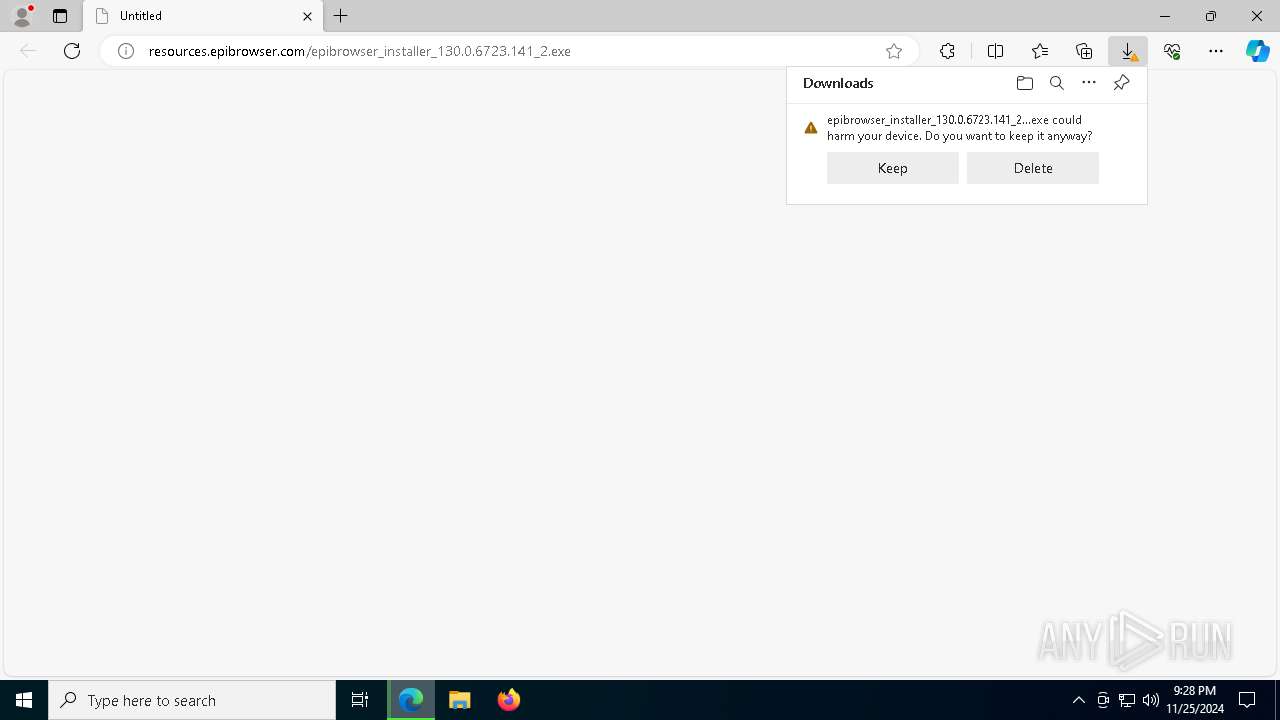
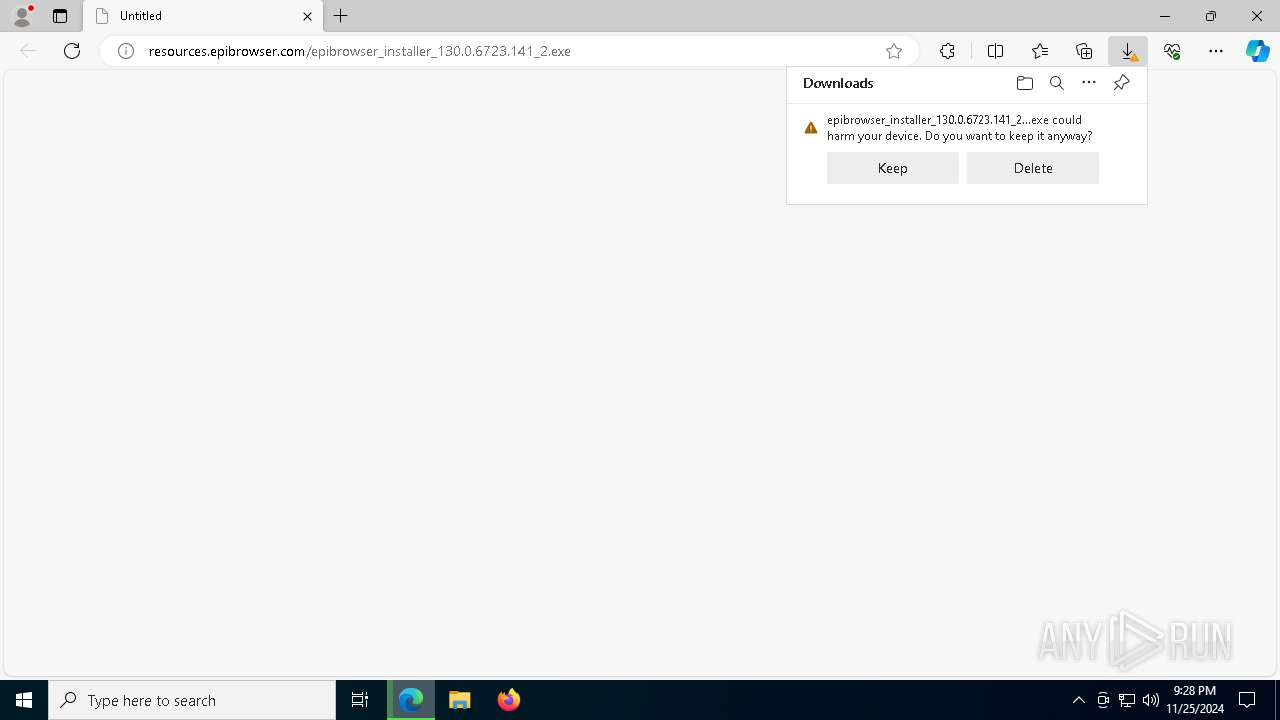
| Verdict: | Malicious activity |
| Analysis date: | November 25, 2024, 21:28:41 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MD5: | CB09898624555C77201161DE43E5652F |
| SHA1: | 4818EA4369DA38858C8F5BF3C141EDB84943B675 |
| SHA256: | 87A04E5CAABE65A43256CCE7BE080230E3CF5BA60BE1455CE1600AC4FE2A4EB4 |
| SSDEEP: | 3:mwM3JWAXyKJ5WAXiRgOXeXIWN6bN:mwNAiKJIASqOXuIWNu |
MALICIOUS
No malicious indicators.SUSPICIOUS
Starts CMD.EXE for commands execution
- epibrowser.exe (PID: 5872)
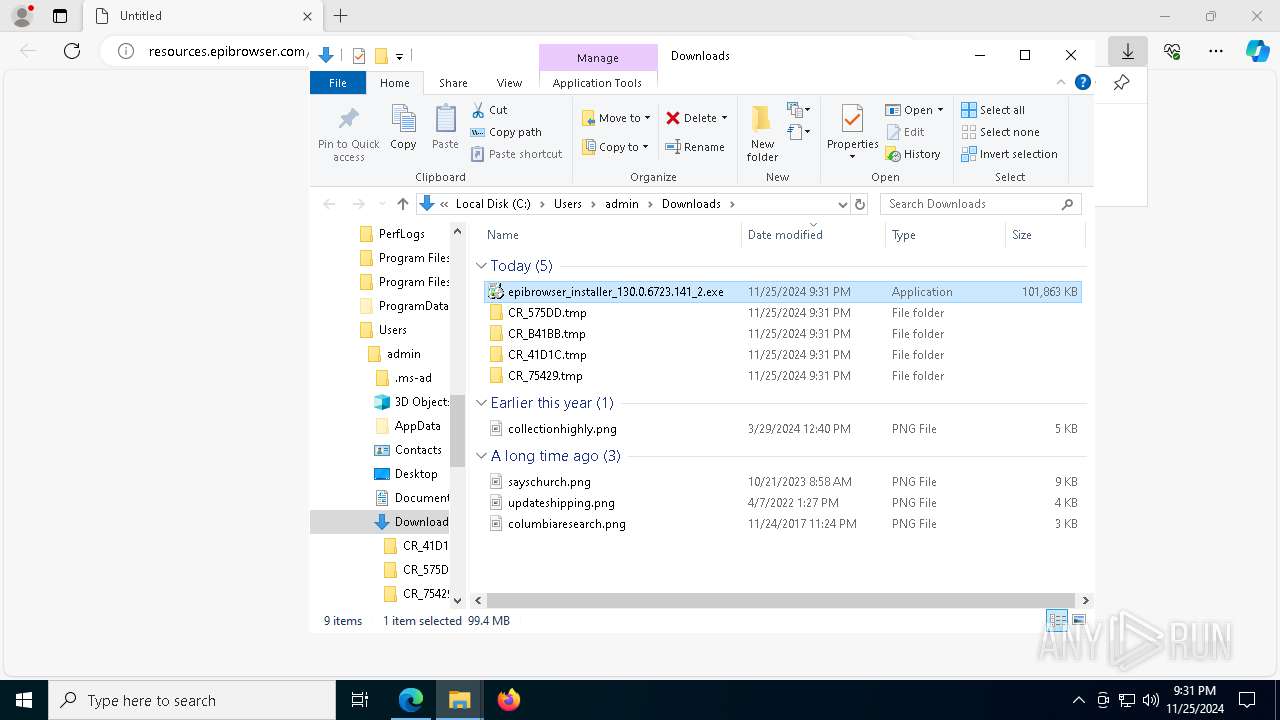
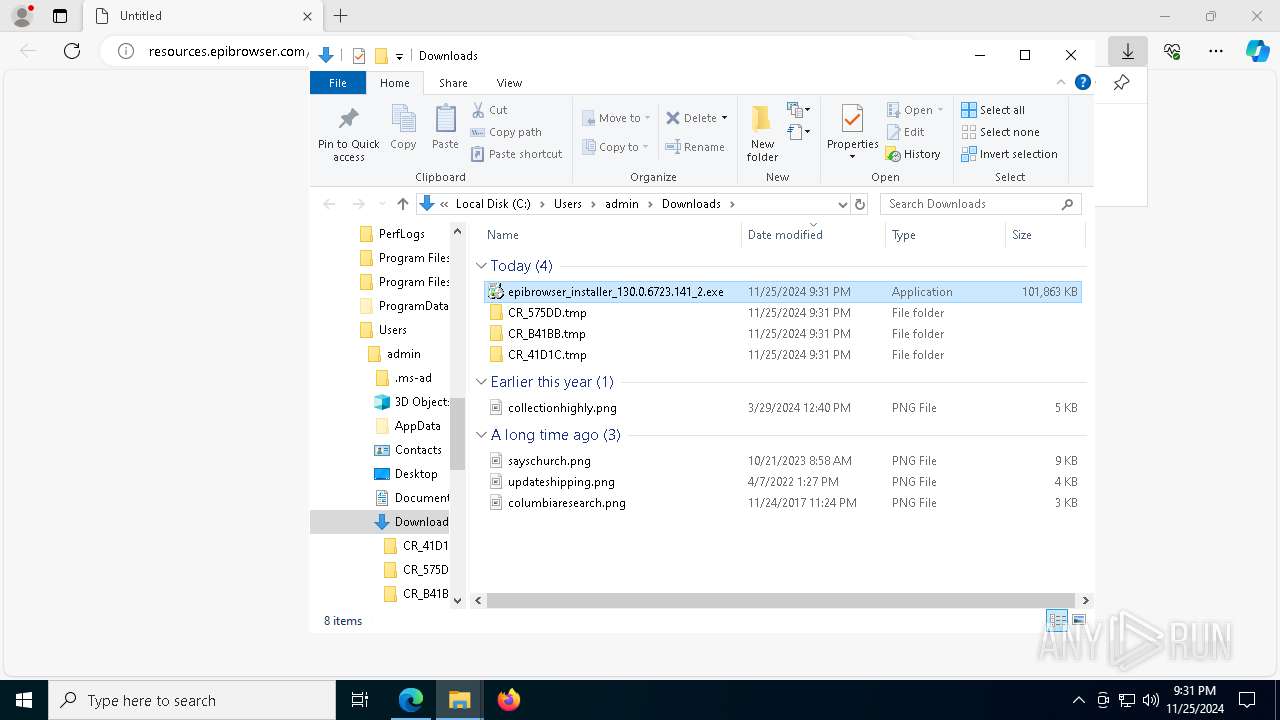
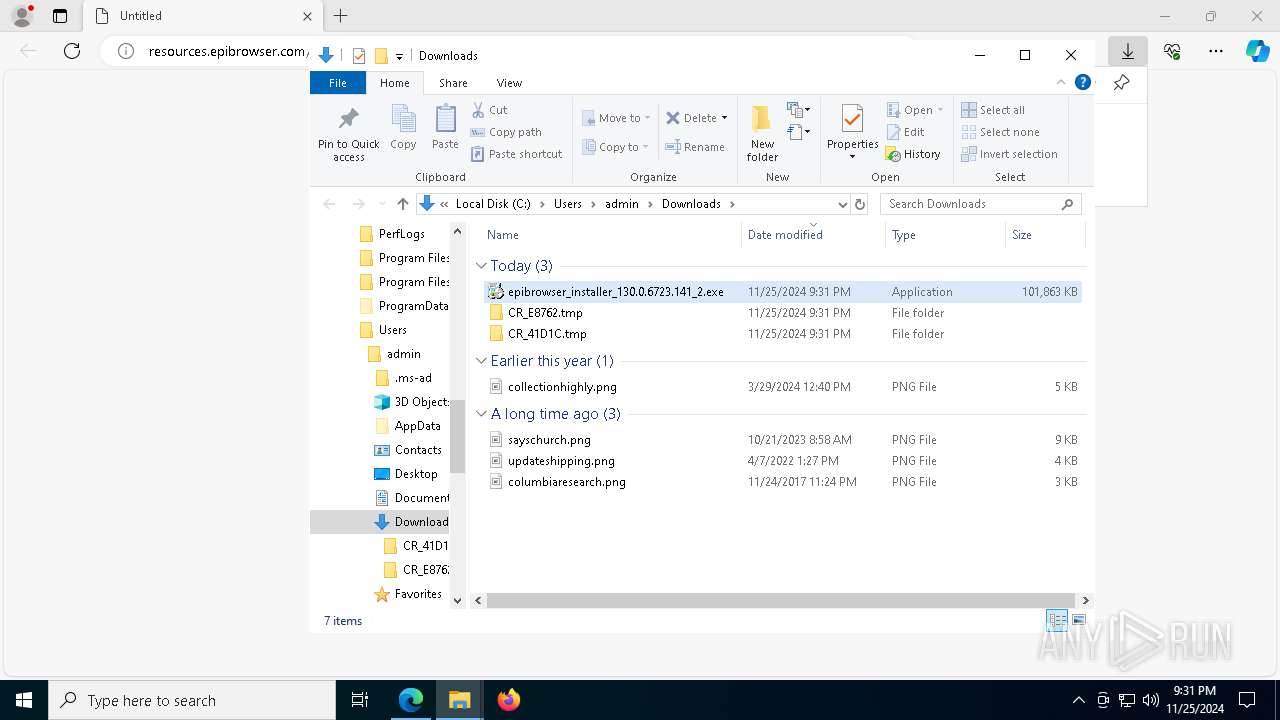
Executable content was dropped or overwritten
- setup.exe (PID: 1220)
- epibrowser_installer_130.0.6723.141_2.exe (PID: 2012)
- epibrowser_installer_130.0.6723.141_2.exe (PID: 776)
- epibrowser_installer_130.0.6723.141_2.exe (PID: 3656)
- epibrowser_installer_130.0.6723.141_2.exe (PID: 6196)
- setup.exe (PID: 7340)
- epibrowser_installer_130.0.6723.141_2.exe (PID: 7132)
Application launched itself
- setup.exe (PID: 4504)
- setup.exe (PID: 7672)
- setup.exe (PID: 7636)
- setup.exe (PID: 1220)
- epibrowser.exe (PID: 5872)
- setup.exe (PID: 7576)
- setup.exe (PID: 7340)
- setup.exe (PID: 3692)
The executable file from the user directory is run by the CMD process
- epibrowser.exe (PID: 7692)
Executes application which crashes
- epibrowser.exe (PID: 5872)
INFO
Executable content was dropped or overwritten
- msedge.exe (PID: 3688)
- msedge.exe (PID: 4320)
Application launched itself
- msedge.exe (PID: 3688)
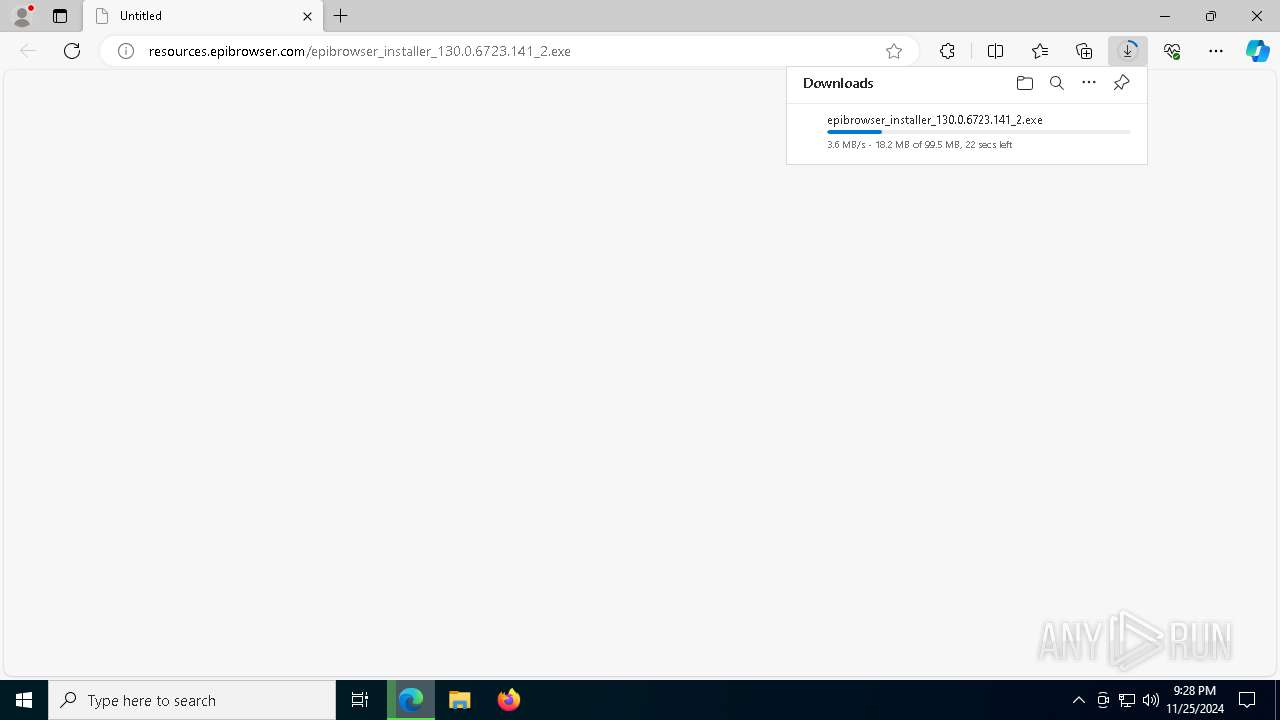
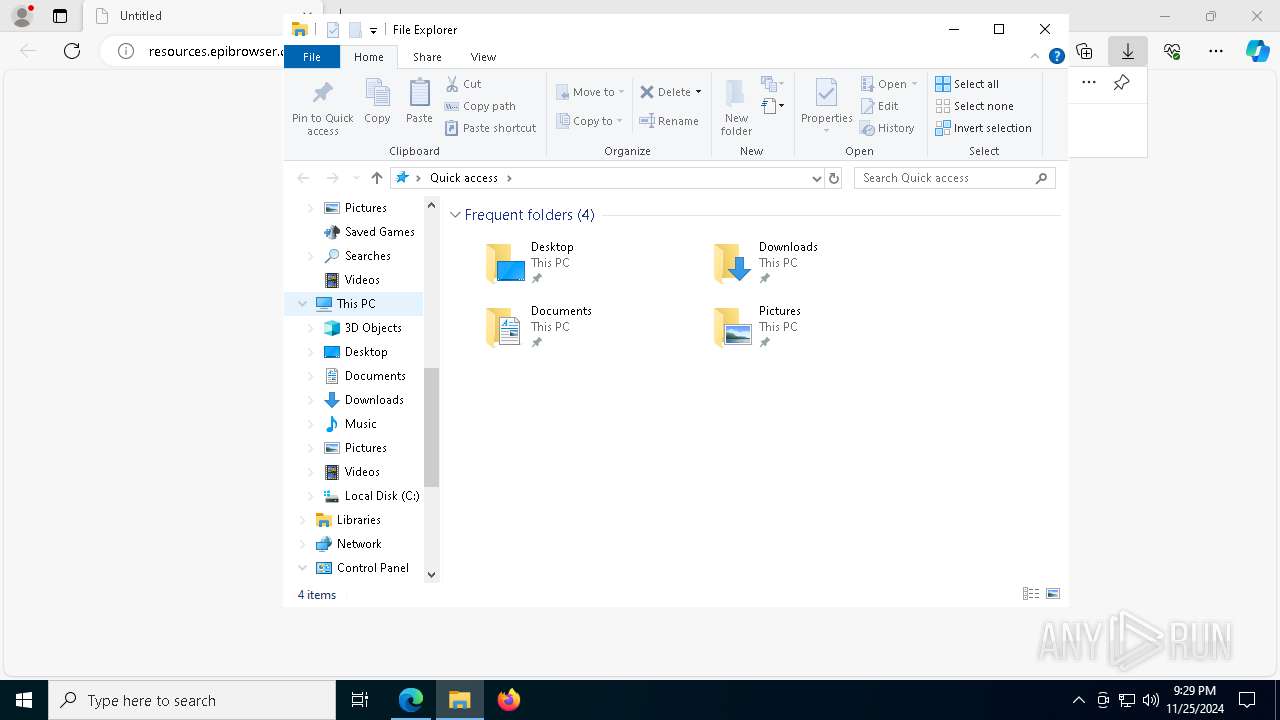
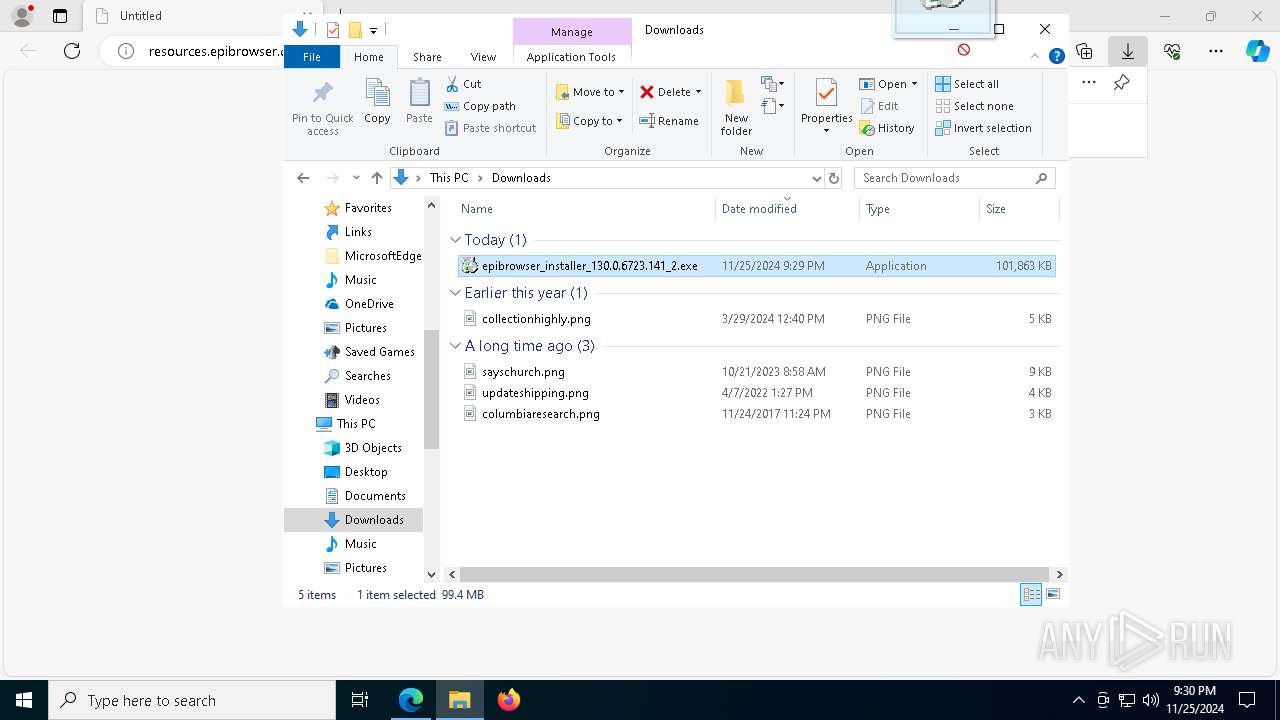
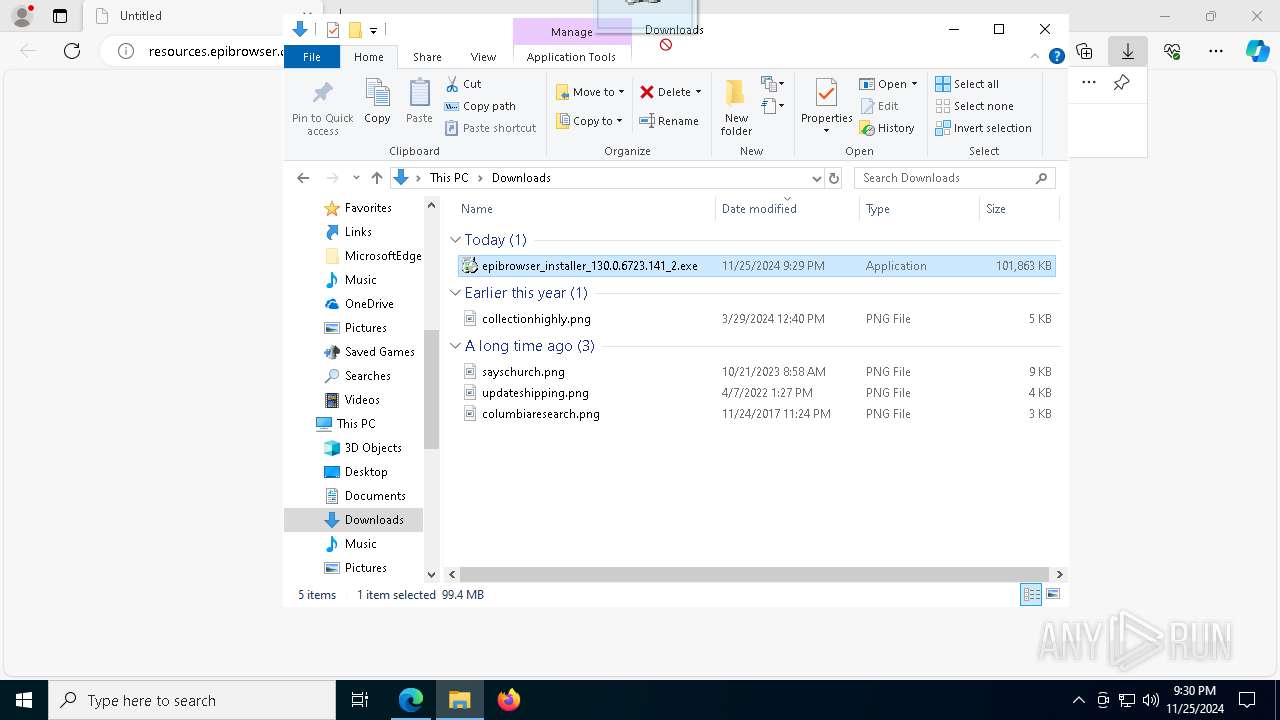
Manual execution by a user
- epibrowser_installer_130.0.6723.141_2.exe (PID: 7132)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
244
Monitored processes
106
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 420 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6260 --field-trial-handle=2328,i,989064737633747548,5829608479692600036,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 520 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_search_indexer.mojom.SearchIndexerInterfaceBroker --lang=en-US --service-sandbox-type=search_indexer --message-loop-type-ui --no-appcompat-clear --mojo-platform-channel-handle=3092 --field-trial-handle=2328,i,989064737633747548,5829608479692600036,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 768 | "C:\WINDOWS\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe" -ServerName:App.AppXtk181tbxbce2qsex02s8tw7hfxa9xb3t.mca | C:\Windows\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Shell Experience Host Version: 10.0.19041.3758 (WinBuild.160101.0800) | |||||||||||||||
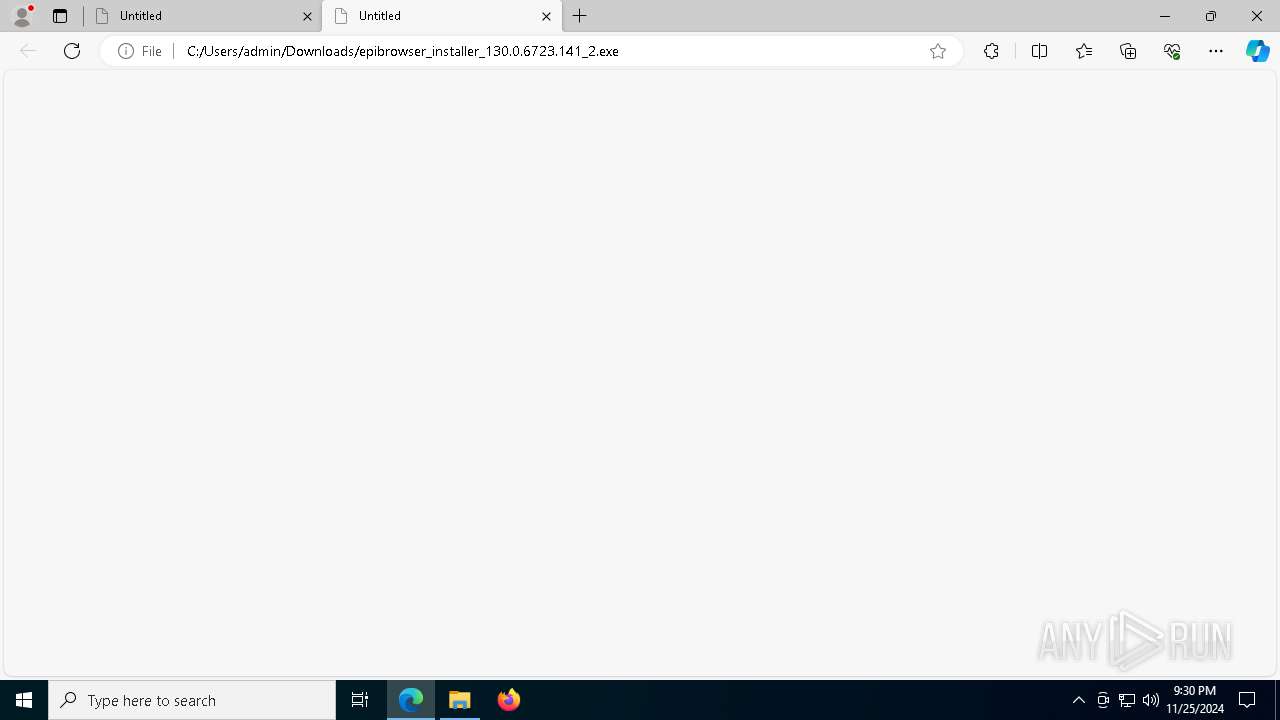
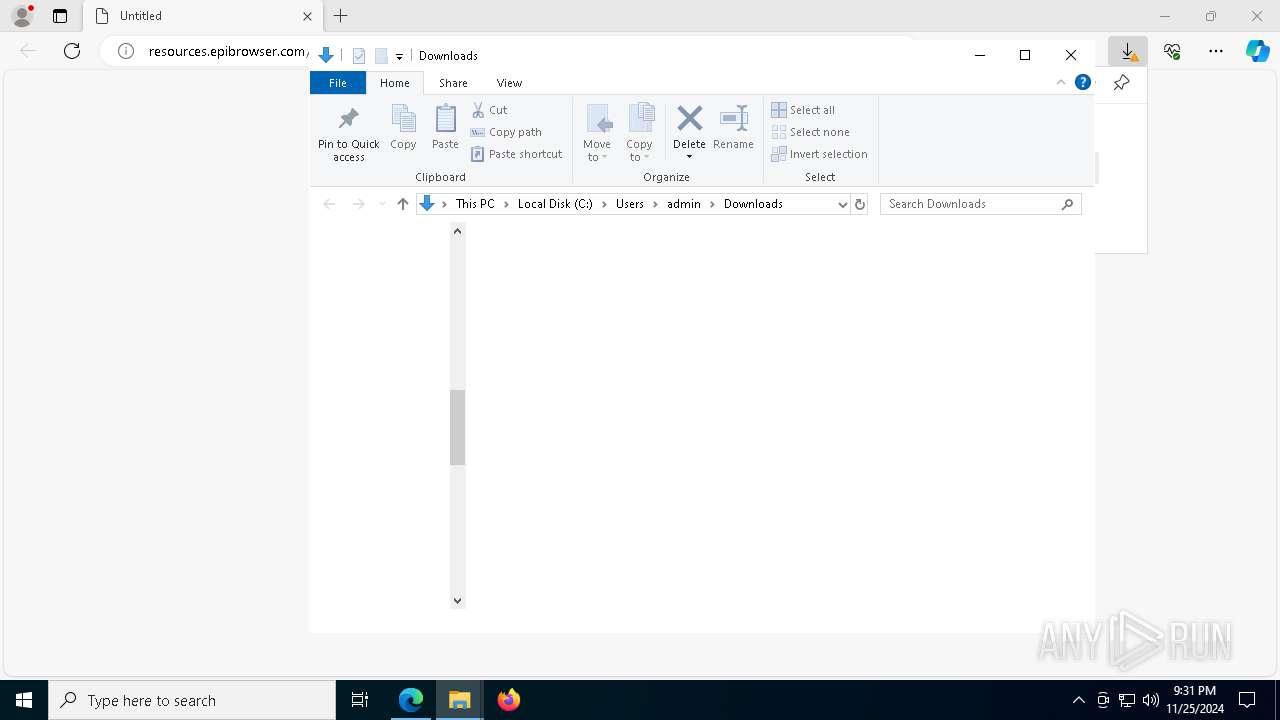
| 776 | "C:\Users\admin\Downloads\epibrowser_installer_130.0.6723.141_2.exe" | C:\Users\admin\Downloads\epibrowser_installer_130.0.6723.141_2.exe | msedge.exe | ||||||||||||
User: admin Company: EPI Software Integrity Level: MEDIUM Description: EpiBrowser Installer Exit code: 60 Version: 130.0.6723.141 Modules
| |||||||||||||||
| 1216 | C:\Users\admin\Downloads\CR_41D1C.tmp\setup.exe --type=crashpad-handler /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\EPISoftware\EpiBrowser\User Data\Crashpad" --annotation=plat=Win64 --annotation=prod=EpiBrowser --annotation=ver=130.0.6723.141 --initial-client-data=0x28c,0x290,0x294,0x268,0x298,0x7ff6269eb088,0x7ff6269eb094,0x7ff6269eb0a0 | C:\Users\admin\Downloads\CR_41D1C.tmp\setup.exe | — | setup.exe | |||||||||||
User: admin Company: EPI Software Integrity Level: MEDIUM Description: EpiBrowser Installer Exit code: 0 Version: 130.0.6723.141 Modules
| |||||||||||||||
| 1220 | "C:\Users\admin\Downloads\CR_41D1C.tmp\setup.exe" --install-archive="C:\Users\admin\Downloads\CR_41D1C.tmp\EPIBROWSER.PACKED.7Z" | C:\Users\admin\Downloads\CR_41D1C.tmp\setup.exe | epibrowser_installer_130.0.6723.141_2.exe | ||||||||||||
User: admin Company: EPI Software Integrity Level: MEDIUM Description: EpiBrowser Installer Exit code: 0 Version: 130.0.6723.141 Modules
| |||||||||||||||
| 1224 | "C:\Users\admin\AppData\Local\EPISoftware\EpiBrowser\Application\epibrowser.exe" --type=renderer --string-annotations=is-enterprise-managed=no --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=9 --field-trial-handle=4928,i,11805249912048443341,9456619627391757512,262144 --variations-seed-version --mojo-platform-channel-handle=4940 /prefetch:1 | C:\Users\admin\AppData\Local\EPISoftware\EpiBrowser\Application\epibrowser.exe | — | epibrowser.exe | |||||||||||
User: admin Company: EPI Software Integrity Level: LOW Description: EpiBrowser Version: 130.0.6723.141 Modules
| |||||||||||||||
| 1448 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win64 --annotation=prod=Chrome --annotation=ver=122.0.6261.70 --initial-client-data=0x210,0x214,0x218,0x1ec,0x21c,0x7ff73f9c35f0,0x7ff73f9c35fc,0x7ff73f9c3608 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | notification_helper.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 | |||||||||||||||
| 2012 | "C:\Users\admin\Downloads\epibrowser_installer_130.0.6723.141_2.exe" | C:\Users\admin\Downloads\epibrowser_installer_130.0.6723.141_2.exe | msedge.exe | ||||||||||||
User: admin Company: EPI Software Integrity Level: MEDIUM Description: EpiBrowser Installer Exit code: 0 Version: 130.0.6723.141 Modules
| |||||||||||||||
| 2136 | "C:\Users\admin\AppData\Local\EPISoftware\EpiBrowser\Application\epibrowser.exe" --type=renderer --string-annotations=is-enterprise-managed=no --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --field-trial-handle=4456,i,11805249912048443341,9456619627391757512,262144 --variations-seed-version --mojo-platform-channel-handle=4500 /prefetch:1 | C:\Users\admin\AppData\Local\EPISoftware\EpiBrowser\Application\epibrowser.exe | — | epibrowser.exe | |||||||||||
User: admin Company: EPI Software Integrity Level: LOW Description: EpiBrowser Version: 130.0.6723.141 Modules
| |||||||||||||||
Total events
15 522
Read events
15 369
Write events
153
Delete events
0
Modification events
| (PID) Process: | (3688) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3688) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3688) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3688) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3688) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 1A5C69B359862F00 | |||
| (PID) Process: | (3688) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: ABB671B359862F00 | |||
| (PID) Process: | (3688) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262892 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {A82ECAA8-28B9-49AE-843F-33432746DB07} | |||
| (PID) Process: | (3688) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: CA7B96B359862F00 | |||
| (PID) Process: | (3688) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
| (PID) Process: | (3688) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\Clients\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\Commands\on-logon-autolaunch |
| Operation: | write | Name: | Enabled |
Value: 0 | |||
Executable files
16
Suspicious files
457
Text files
158
Unknown types
78
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3688 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF13547c.TMP | — | |
MD5:— | SHA256:— | |||
| 3688 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF13547c.TMP | — | |
MD5:— | SHA256:— | |||
| 3688 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3688 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3688 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF13549b.TMP | — | |
MD5:— | SHA256:— | |||
| 3688 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3688 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF1354ca.TMP | — | |
MD5:— | SHA256:— | |||
| 3688 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3688 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF13549b.TMP | — | |
MD5:— | SHA256:— | |||
| 3688 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
65
TCP/UDP connections
129
DNS requests
114
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5448 | svchost.exe | GET | 200 | 23.53.42.18:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5448 | svchost.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6768 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5540 | SIHClient.exe | GET | 200 | 88.221.125.143:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5540 | SIHClient.exe | GET | 200 | 88.221.125.143:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
8160 | svchost.exe | HEAD | 200 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/c08f1970-45bc-4dbe-8166-4ecef7a1f617?P1=1733059312&P2=404&P3=2&P4=aTdb4D6Hl6W4qCLD3xQHF2jYdDBh0ASJ2G0zzwI3s%2bW%2bjY1ky0f0B4vlSS7S6Aztg27sFHAFOSDQTJneOIZTVg%3d%3d | unknown | — | — | whitelisted |
8160 | svchost.exe | GET | 206 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/c08f1970-45bc-4dbe-8166-4ecef7a1f617?P1=1733059312&P2=404&P3=2&P4=aTdb4D6Hl6W4qCLD3xQHF2jYdDBh0ASJ2G0zzwI3s%2bW%2bjY1ky0f0B4vlSS7S6Aztg27sFHAFOSDQTJneOIZTVg%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5448 | svchost.exe | 23.53.42.18:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5448 | svchost.exe | 23.52.120.96:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 23.52.120.96:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 2.16.110.123:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
5064 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 65.9.66.15:80 | resources.epibrowser.com | AMAZON-02 | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
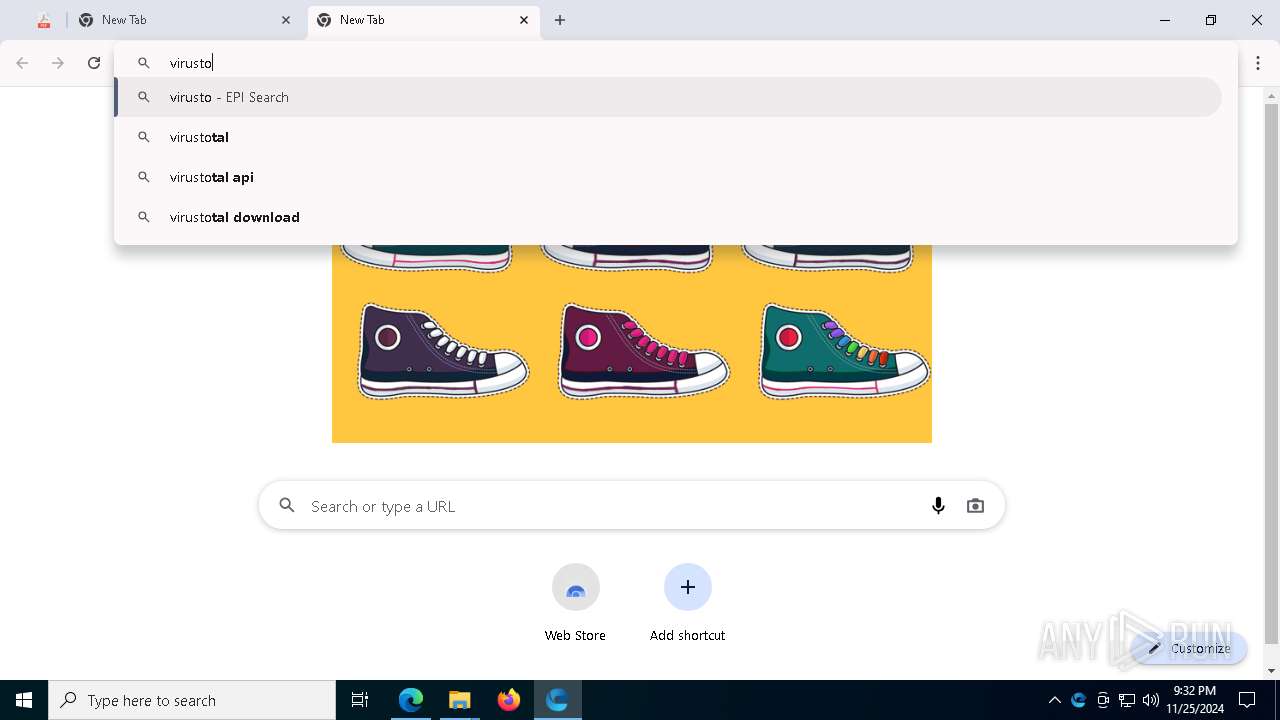
resources.epibrowser.com |
| unknown |
business.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4876 | epibrowser.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
4876 | epibrowser.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
4876 | epibrowser.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
4876 | epibrowser.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
4876 | epibrowser.exe | Not Suspicious Traffic | INFO [ANY.RUN] Global content delivery network (unpkg .com) |
4876 | epibrowser.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
4876 | epibrowser.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |