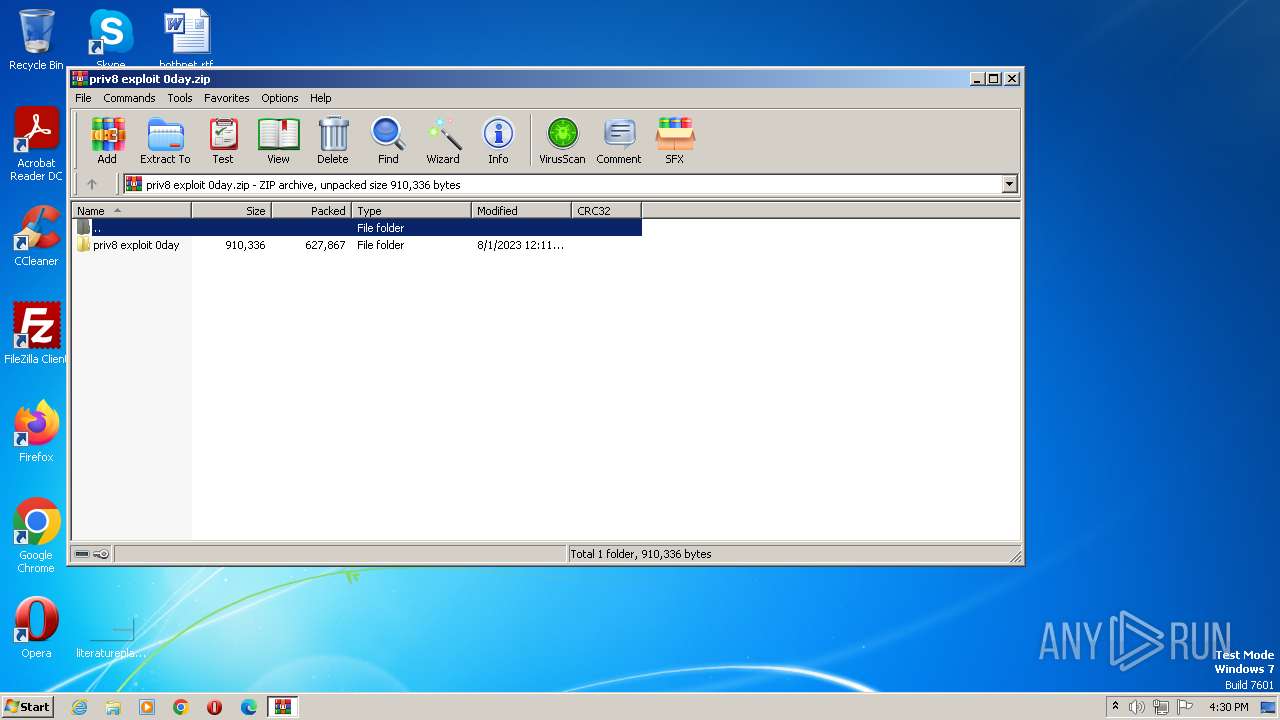
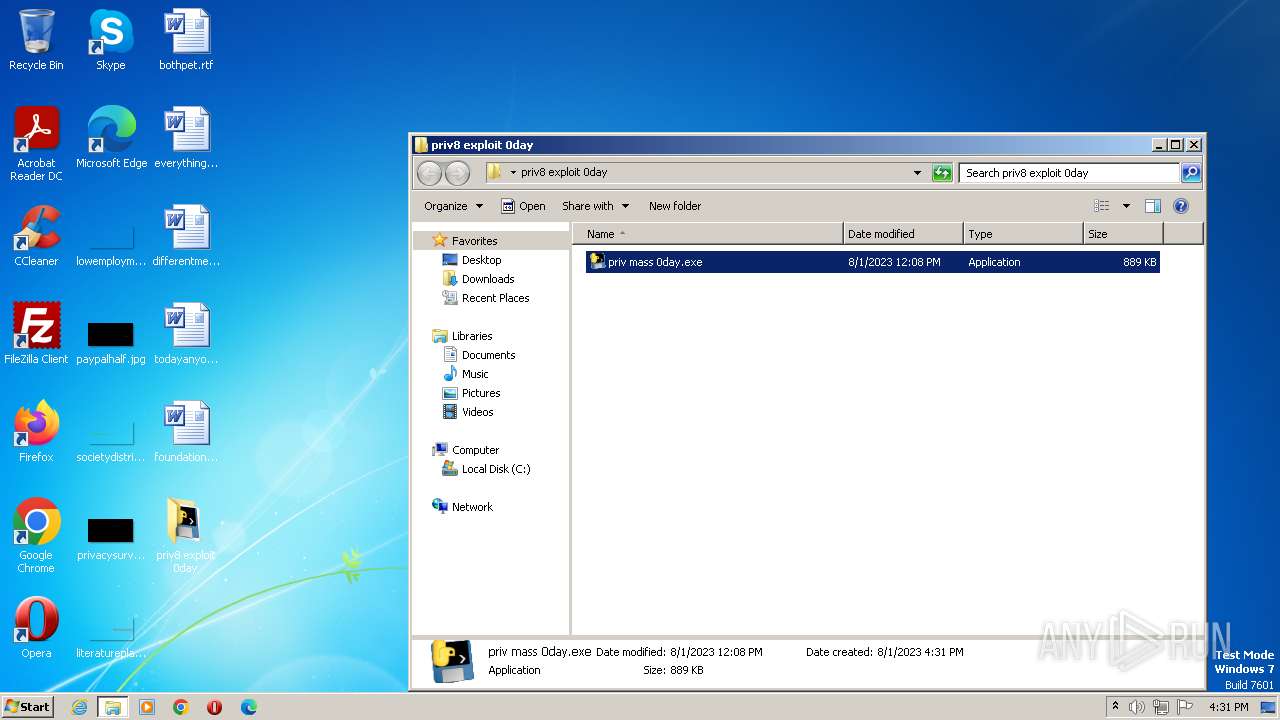
| File name: | priv8 exploit 0day.zip |
| Full analysis: | https://app.any.run/tasks/74334d05-dc06-4a2f-aa34-762572e798cc |
| Verdict: | Malicious activity |
| Analysis date: | August 01, 2023, 15:30:45 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract |
| MD5: | A07CE2810694EC43F0AE4FCA2F8D9ACD |
| SHA1: | 495A9C93BCDE792798E1240D891F30D51D3F0557 |
| SHA256: | 878F0C3BDC14384E12BEF02023FF70CD417615ECF8ED13D32E25D351FC48D714 |
| SSDEEP: | 12288:M6W0z6J2F5b0PlROXggUenkQl74QSaO88LpRuzwWf2wYUfIG9CIskrEHXk:NznF+xJe5Z4QSayLpROwMjYwIOCArGU |
MALICIOUS
Application was dropped or rewritten from another process
- priv mass 0day.exe (PID: 3464)
- priv mass 0day.exe (PID: 1424)
- Microsoft Teams.exe (PID: 2344)
- Microsoft Teams.exe (PID: 3692)
- Microsoft Teams.exe (PID: 324)
Known privilege escalation attack
- dllhost.exe (PID: 2848)
Changes powershell execution policy (Bypass)
- priv mass 0day.exe (PID: 1424)
- Microsoft Teams.exe (PID: 2344)
- Microsoft Teams.exe (PID: 3692)
- Microsoft Teams.exe (PID: 324)
Bypass execution policy to execute commands
- powershell.exe (PID: 2268)
- powershell.exe (PID: 3224)
- powershell.exe (PID: 3624)
- powershell.exe (PID: 2592)
- powershell.exe (PID: 1772)
- powershell.exe (PID: 2908)
- powershell.exe (PID: 2336)
- powershell.exe (PID: 1744)
Adds path to the Windows Defender exclusion list
- priv mass 0day.exe (PID: 1424)
- Microsoft Teams.exe (PID: 2344)
- Microsoft Teams.exe (PID: 3692)
- Microsoft Teams.exe (PID: 324)
Adds process to the Windows Defender exclusion list
- priv mass 0day.exe (PID: 1424)
- Microsoft Teams.exe (PID: 2344)
- Microsoft Teams.exe (PID: 3692)
- Microsoft Teams.exe (PID: 324)
SUSPICIOUS
Reads the Internet Settings
- priv mass 0day.exe (PID: 3464)
- mshta.exe (PID: 1048)
- mshta.exe (PID: 3940)
- priv mass 0day.exe (PID: 1424)
- Microsoft Teams.exe (PID: 2344)
- Microsoft Teams.exe (PID: 3692)
- Microsoft Teams.exe (PID: 324)
Probably UAC bypass using CMSTP.exe (Connection Manager service profile)
- priv mass 0day.exe (PID: 3464)
Starts CMD.EXE for commands execution
- mshta.exe (PID: 1048)
- priv mass 0day.exe (PID: 1424)
- Microsoft Teams.exe (PID: 2344)
- Microsoft Teams.exe (PID: 3692)
- Microsoft Teams.exe (PID: 324)
Uses TASKKILL.EXE to kill process
- mshta.exe (PID: 3940)
Script adds exclusion path to Windows Defender
- priv mass 0day.exe (PID: 1424)
- Microsoft Teams.exe (PID: 2344)
- Microsoft Teams.exe (PID: 3692)
- Microsoft Teams.exe (PID: 324)
Starts POWERSHELL.EXE for commands execution
- priv mass 0day.exe (PID: 1424)
- Microsoft Teams.exe (PID: 2344)
- Microsoft Teams.exe (PID: 3692)
- Microsoft Teams.exe (PID: 324)
Executes as Windows Service
- VSSVC.exe (PID: 3544)
Executing commands from a ".bat" file
- priv mass 0day.exe (PID: 1424)
- Microsoft Teams.exe (PID: 2344)
- Microsoft Teams.exe (PID: 3692)
- Microsoft Teams.exe (PID: 324)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 3276)
- cmd.exe (PID: 1280)
- cmd.exe (PID: 3024)
- cmd.exe (PID: 2992)
The process executes via Task Scheduler
- Microsoft Teams.exe (PID: 2344)
- Microsoft Teams.exe (PID: 3692)
- Microsoft Teams.exe (PID: 324)
Script adds exclusion process to Windows Defender
- priv mass 0day.exe (PID: 1424)
- Microsoft Teams.exe (PID: 2344)
- Microsoft Teams.exe (PID: 3692)
- Microsoft Teams.exe (PID: 324)
Executable content was dropped or overwritten
- priv mass 0day.exe (PID: 1424)
INFO
Executable content was dropped or overwritten
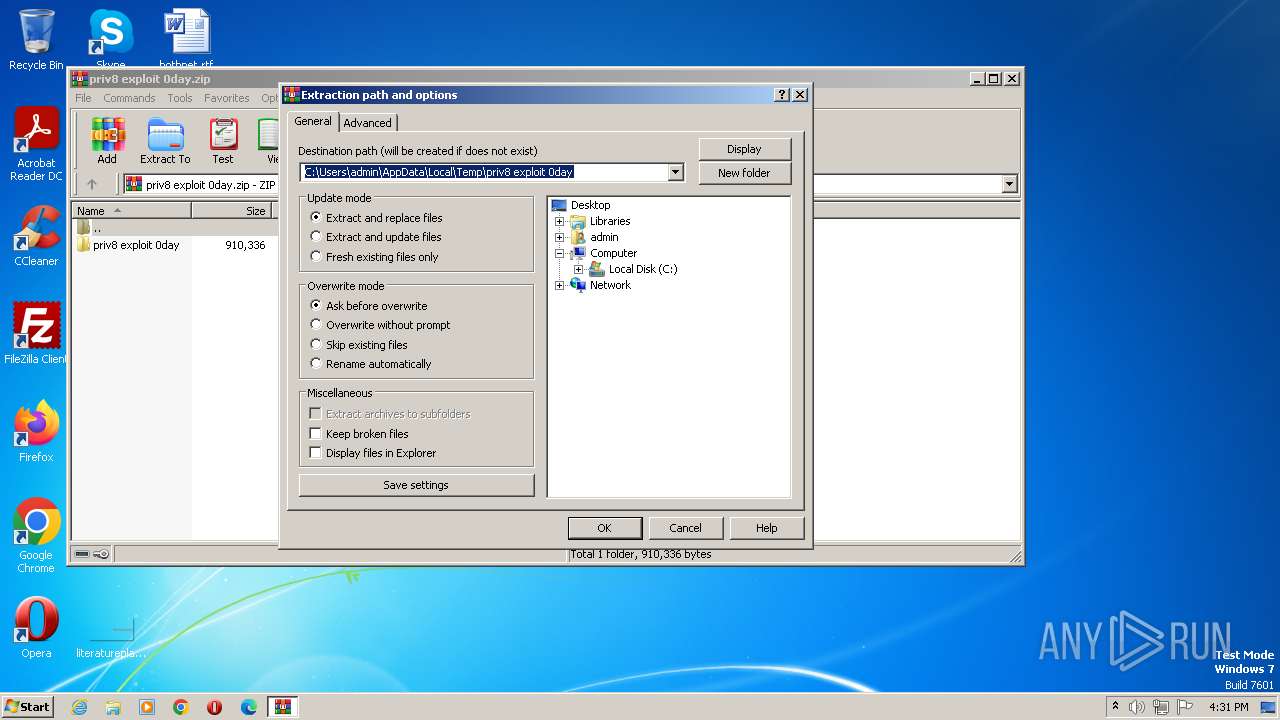
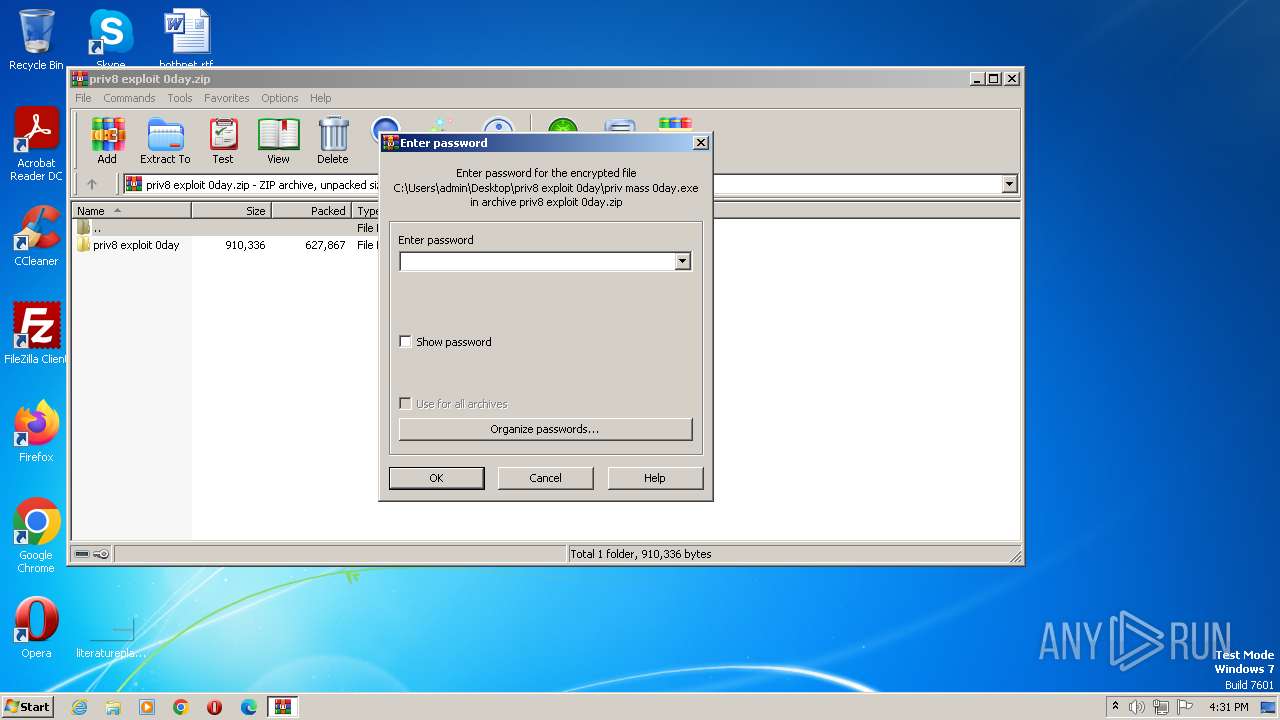
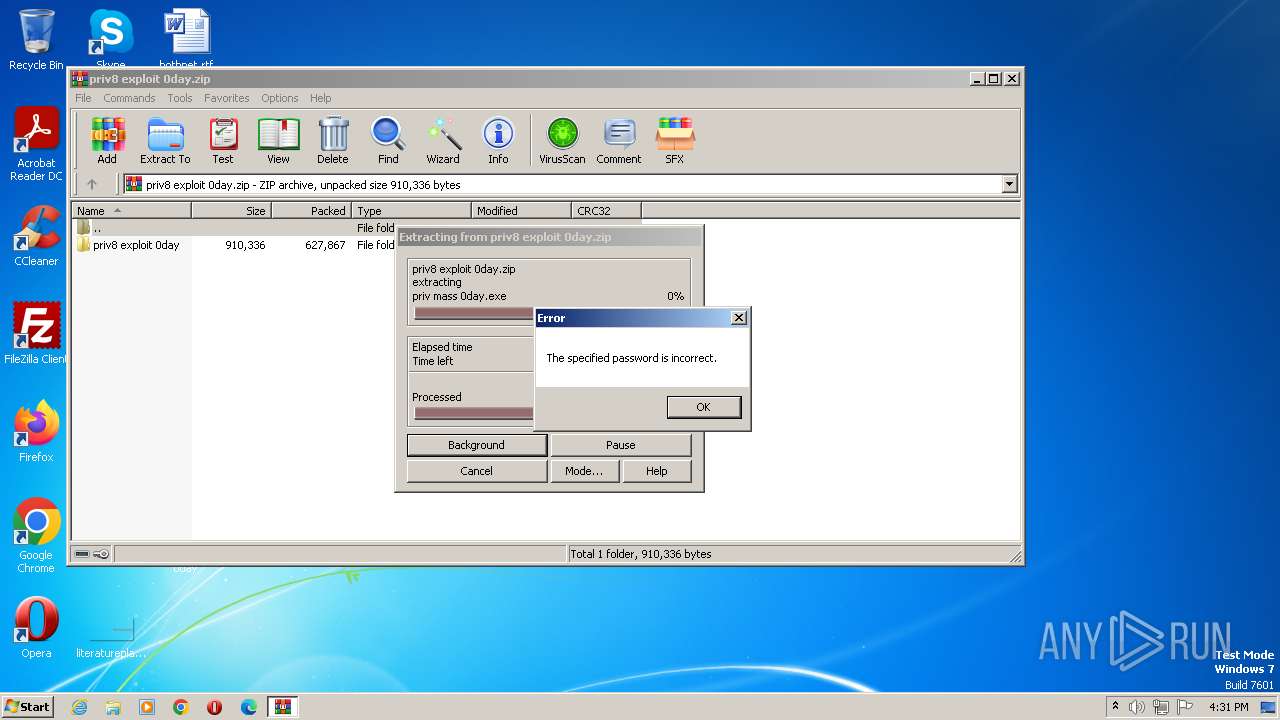
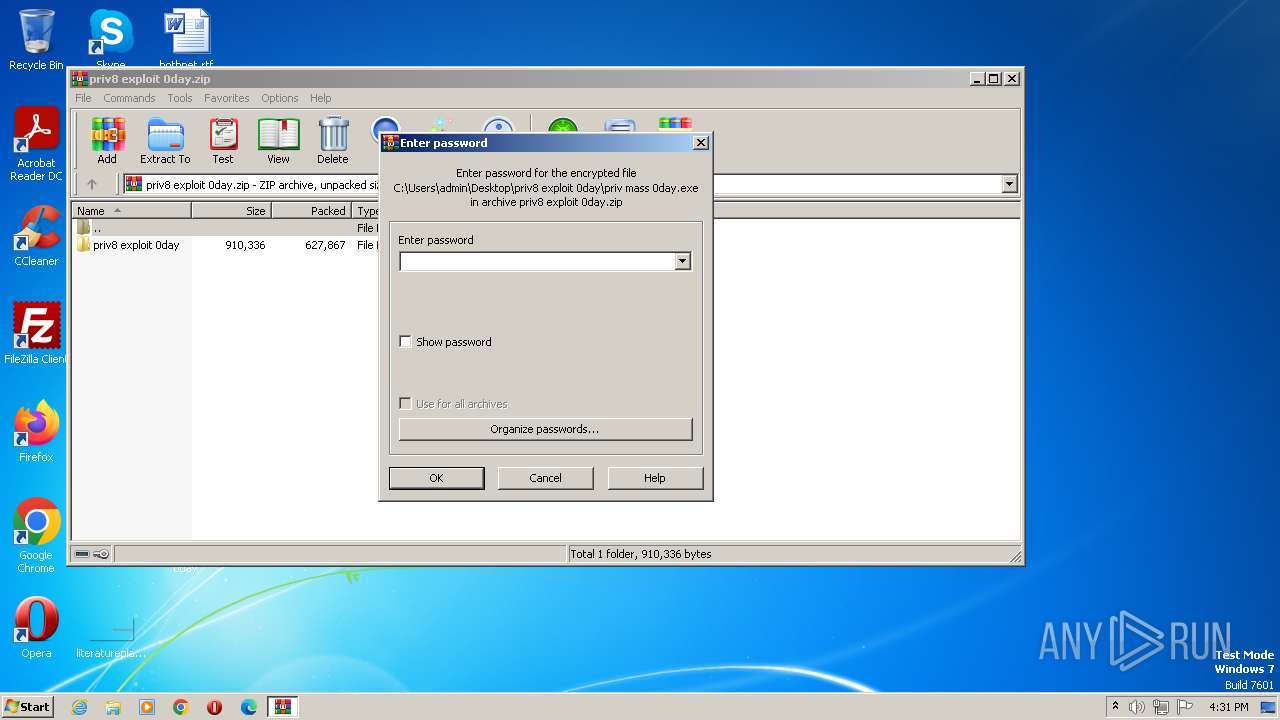
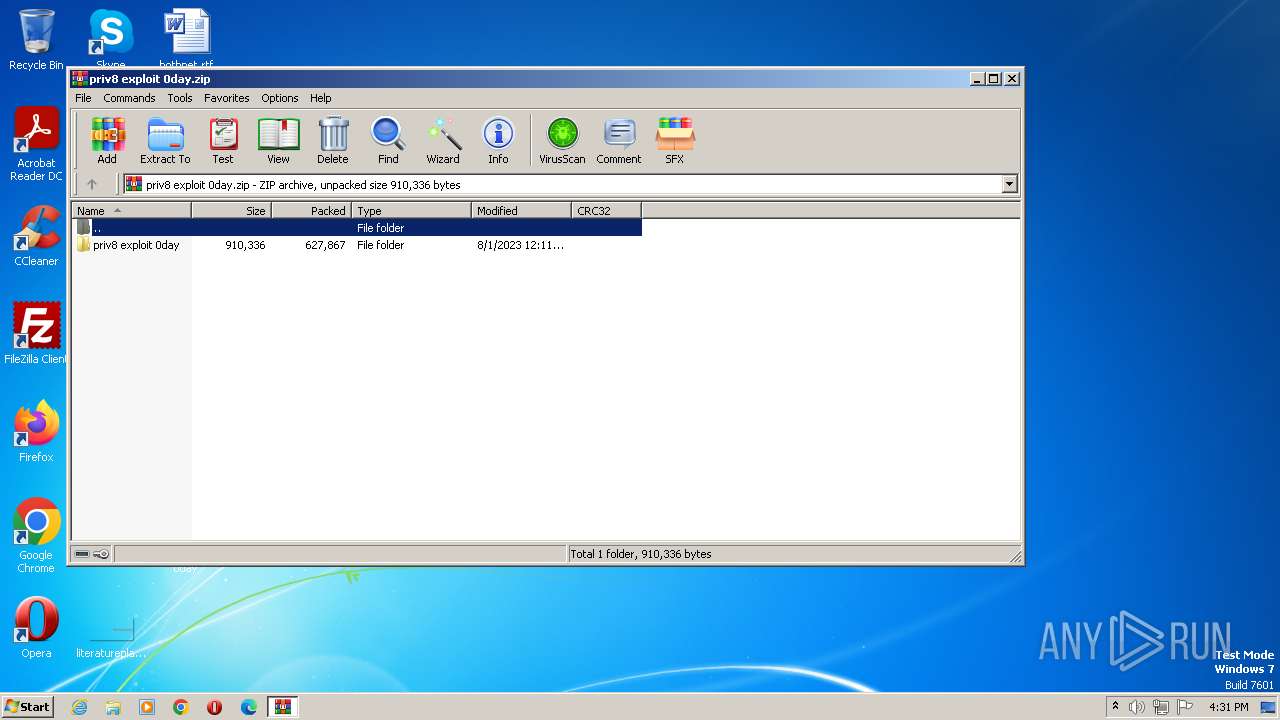
- WinRAR.exe (PID: 3752)
Checks supported languages
- priv mass 0day.exe (PID: 3464)
- priv mass 0day.exe (PID: 1424)
- Microsoft Teams.exe (PID: 2344)
- Microsoft Teams.exe (PID: 3692)
- Microsoft Teams.exe (PID: 324)
Reads the computer name
- priv mass 0day.exe (PID: 3464)
- priv mass 0day.exe (PID: 1424)
- Microsoft Teams.exe (PID: 2344)
- Microsoft Teams.exe (PID: 3692)
- Microsoft Teams.exe (PID: 324)
The process checks LSA protection
- priv mass 0day.exe (PID: 3464)
- cmstp.exe (PID: 3688)
- dllhost.exe (PID: 2848)
- priv mass 0day.exe (PID: 1424)
- taskkill.exe (PID: 3164)
- dllhost.exe (PID: 4028)
- VSSVC.exe (PID: 3544)
- Microsoft Teams.exe (PID: 2344)
- dllhost.exe (PID: 3676)
- Microsoft Teams.exe (PID: 3692)
- dllhost.exe (PID: 2304)
- dllhost.exe (PID: 3600)
- Microsoft Teams.exe (PID: 324)
Reads the machine GUID from the registry
- priv mass 0day.exe (PID: 3464)
- priv mass 0day.exe (PID: 1424)
- Microsoft Teams.exe (PID: 2344)
- Microsoft Teams.exe (PID: 3692)
- Microsoft Teams.exe (PID: 324)
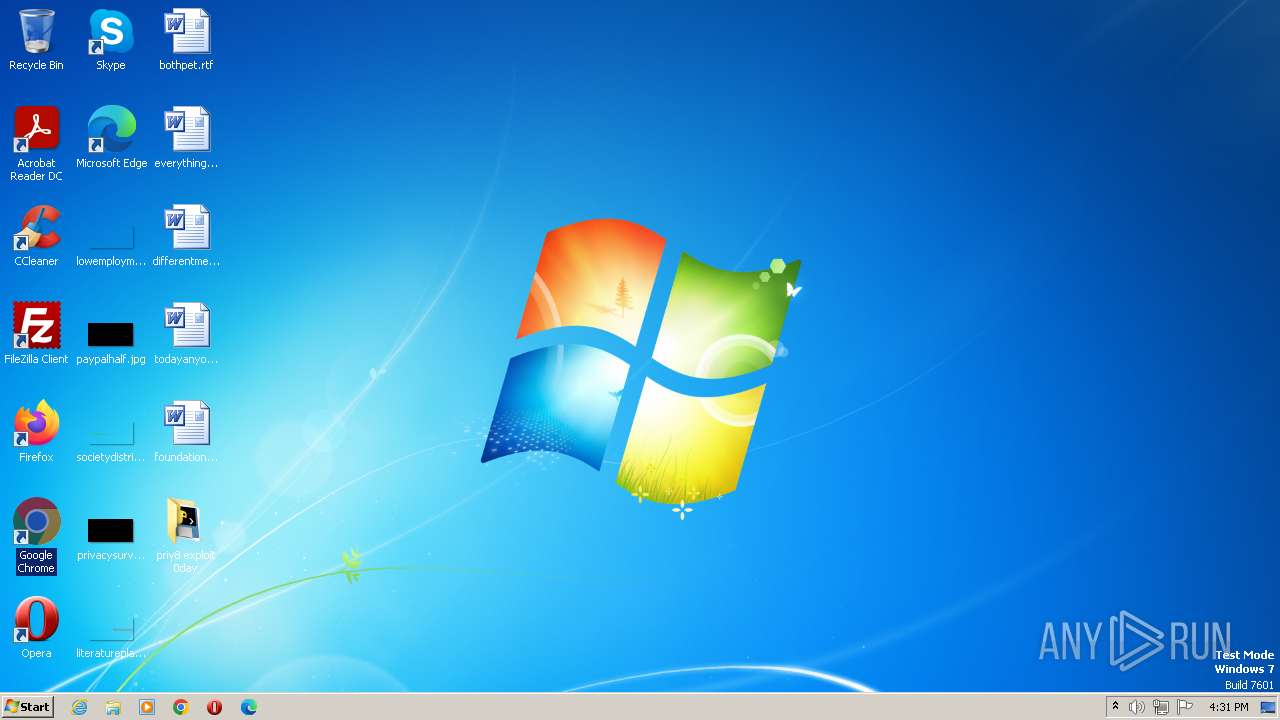
Manual execution by a user
- priv mass 0day.exe (PID: 3464)
Checks transactions between databases Windows and Oracle
- cmstp.exe (PID: 3688)
Creates files in the program directory
- dllhost.exe (PID: 2848)
Reads Internet Explorer settings
- mshta.exe (PID: 1048)
- mshta.exe (PID: 3940)
Create files in a temporary directory
- priv mass 0day.exe (PID: 1424)
- Microsoft Teams.exe (PID: 2344)
- Microsoft Teams.exe (PID: 3692)
- Microsoft Teams.exe (PID: 324)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipFileName: | priv8 exploit 0day/ |
|---|---|
| ZipUncompressedSize: | - |
| ZipCompressedSize: | - |
| ZipCRC: | 0x00000000 |
| ZipModifyDate: | 2023:08:01 04:11:30 |
| ZipCompression: | None |
| ZipBitFlag: | - |
| ZipRequiredVersion: | 10 |
Total processes
88
Monitored processes
33
Malicious processes
7
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 324 | "\Microsoft Teams.exe" | C:\Microsoft Teams.exe | — | taskeng.exe | |||||||||||
User: admin Integrity Level: HIGH Description: Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 488 | timeout 3 | C:\Windows\System32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: timeout - pauses command processing Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1048 | mshta vbscript:Execute("CreateObject(""WScript.Shell"").Run ""cmd.exe /c start """""""" """"C:\Users\admin\Desktop\priv8 exploit 0day\priv mass 0day.exe"""""",0:close") | C:\Windows\System32\mshta.exe | — | dllhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft (R) HTML Application host Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1280 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\tmp5F5C.tmp.bat"" | C:\Windows\System32\cmd.exe | — | Microsoft Teams.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1424 | "C:\Users\admin\Desktop\priv8 exploit 0day\priv mass 0day.exe" | C:\Users\admin\Desktop\priv8 exploit 0day\priv mass 0day.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1744 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ExecutionPolicy Bypass Add-MpPreference -ExclusionPath 'C:\Microsoft Teams.exe' | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | Microsoft Teams.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 1772 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ExecutionPolicy Bypass Add-MpPreference -ExclusionPath 'C:\Microsoft Teams.exe' | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | Microsoft Teams.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 2268 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ExecutionPolicy Bypass Add-MpPreference -ExclusionPath 'C:\Microsoft Teams.exe' | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | priv mass 0day.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 2304 | C:\Windows\system32\DllHost.exe /Processid:{F32D97DF-E3E5-4CB9-9E3E-0EB5B4E49801} | C:\Windows\System32\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2336 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ExecutionPolicy Bypass Add-MpPreference -ExclusionProcess 'Microsoft Teams.exe' | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | Microsoft Teams.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
Total events
7 106
Read events
6 937
Write events
169
Delete events
0
Modification events
| (PID) Process: | (3752) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\178\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3752) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (3752) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (3752) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (3752) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3752) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3752) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3752) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3752) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (3752) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
Executable files
4
Suspicious files
17
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2848 | dllhost.exe | C:\Windows\INF\setupapi.app.log | text | |
MD5:A860567D9E04ADAC1B61C7B13613C17E | SHA256:0EAF1046087A7ADC123AAC16F500E642C28B8520A12068757A3CD7098376EACF | |||
| 2268 | powershell.exe | C:\Users\admin\AppData\Local\Temp\do4fht5v.ysy.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
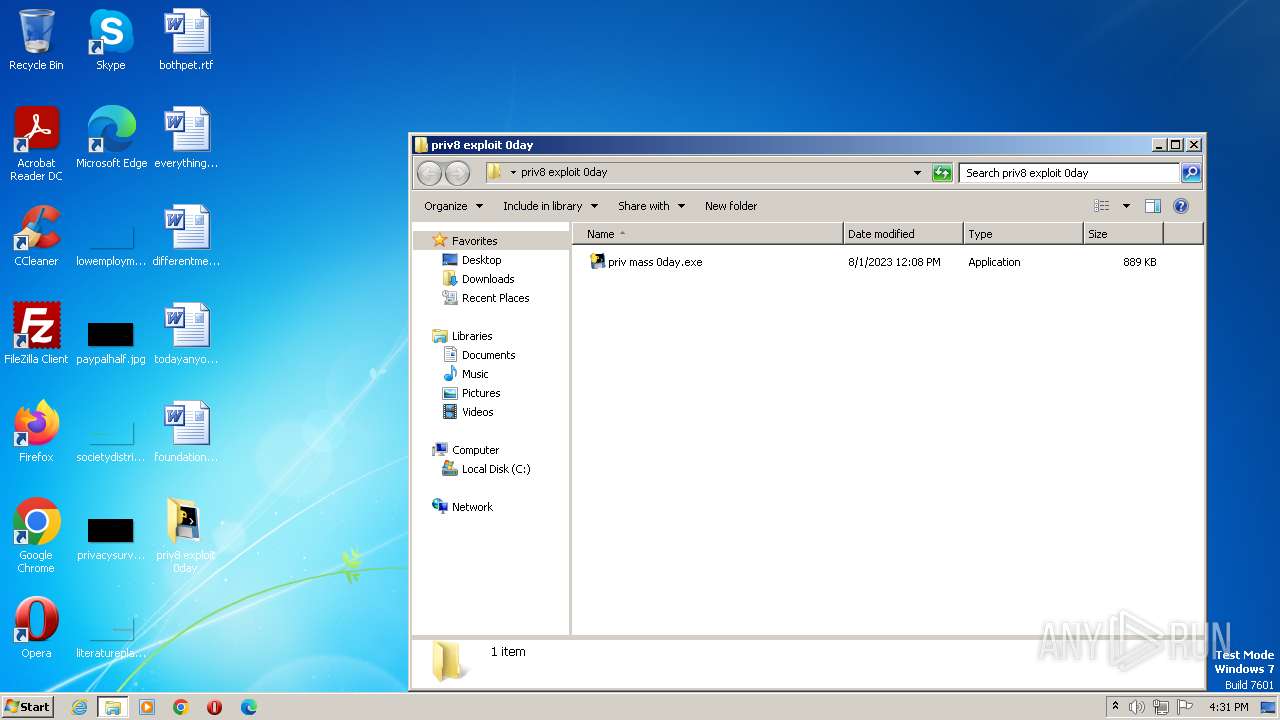
| 3752 | WinRAR.exe | C:\Users\admin\Desktop\priv8 exploit 0day\priv mass 0day.exe | executable | |
MD5:BB8E4B020969CC8B37AD479FEABE059A | SHA256:E15F1AB88571BBB40A75C64BC55CA563A314B937391E49F99C505F51D83D8CA6 | |||
| 3624 | powershell.exe | C:\Users\admin\AppData\Local\Temp\uphiyiqf.hez.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 1424 | priv mass 0day.exe | C:\Microsoft Teams.exe | executable | |
MD5:BB8E4B020969CC8B37AD479FEABE059A | SHA256:E15F1AB88571BBB40A75C64BC55CA563A314B937391E49F99C505F51D83D8CA6 | |||
| 2268 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:446DD1CF97EABA21CF14D03AEBC79F27 | SHA256:A7DE5177C68A64BD48B36D49E2853799F4EBCFA8E4761F7CC472F333DC5F65CF | |||
| 3624 | powershell.exe | C:\Users\admin\AppData\Local\Temp\1tttjhmq.242.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 3224 | powershell.exe | C:\Users\admin\AppData\Local\Temp\svn5vfv4.3wd.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 2908 | powershell.exe | C:\Users\admin\AppData\Local\Temp\1kxt4ghp.t5x.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 2592 | powershell.exe | C:\Users\admin\AppData\Local\Temp\t3fx1e2c.e3p.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2640 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |