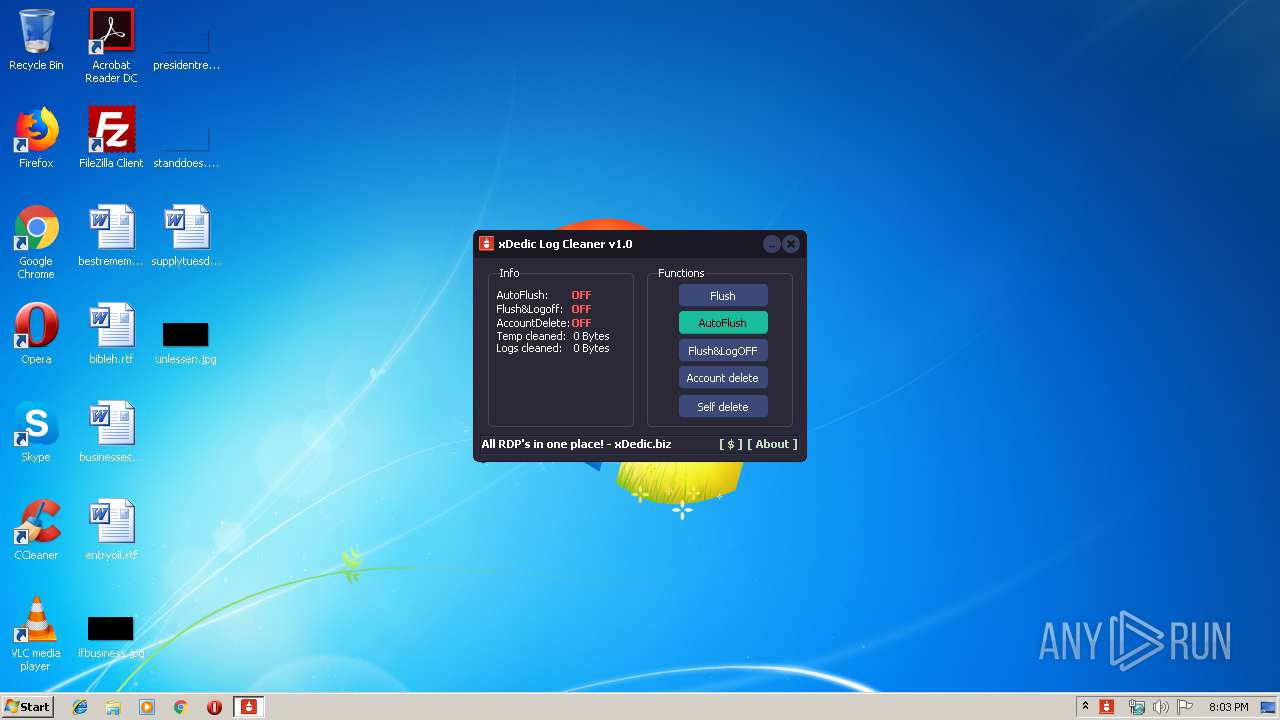
| File name: | logs.exe |
| Full analysis: | https://app.any.run/tasks/0e73ea75-5a3e-47d2-bf17-3974d69020ff |
| Verdict: | Malicious activity |
| Analysis date: | January 07, 2020, 20:02:42 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows |
| MD5: | 0F34AB1E2166CADA2BE7C551E026507C |
| SHA1: | 550B803F22078AD75240011D7B766BD79871B932 |
| SHA256: | 878706CD11B5223C89AAEF08887B92A655A25B7C630950AFFA553574A60B922E |
| SSDEEP: | 49152:xtuNXEZiAjGftDoCRt8aGQRRIpw/JpfFNeBz66Bc:n+XNATCRt8aGiX/j56 |
MALICIOUS
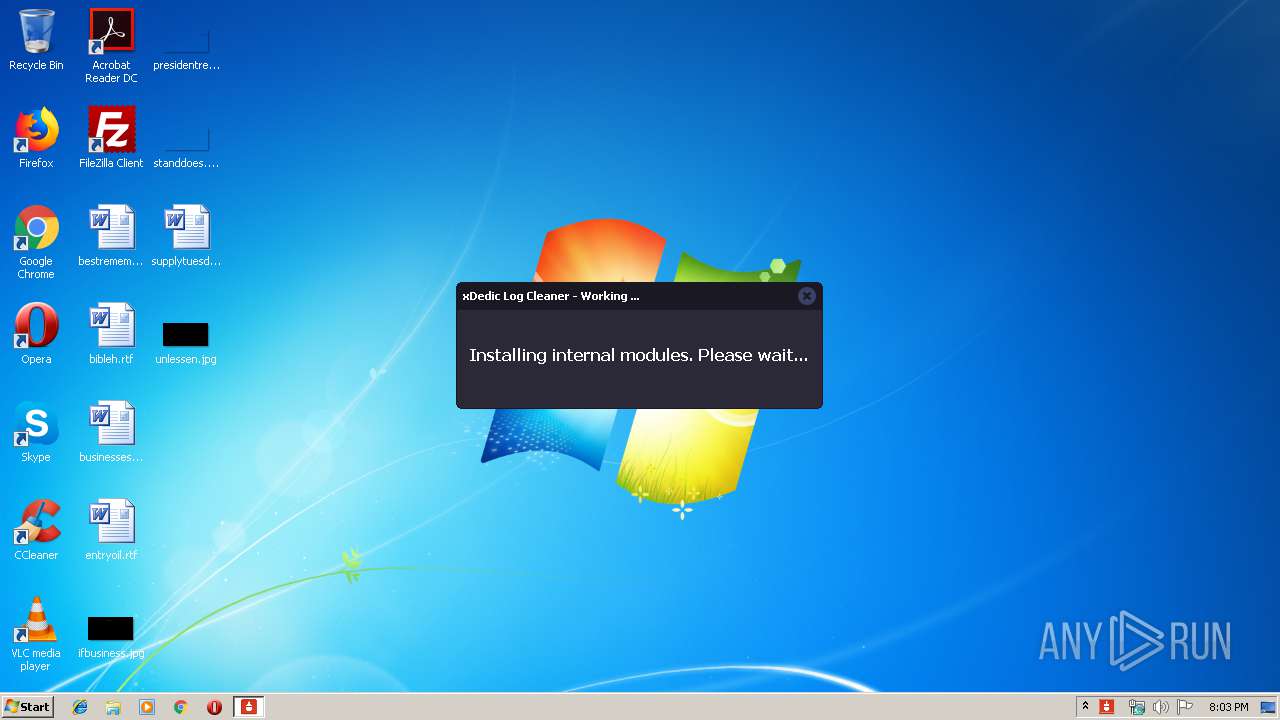
Application was dropped or rewritten from another process
- xDLS.exe (PID: 1648)
- xDLS.exe (PID: 3288)
SUSPICIOUS
Executed as Windows Service
- xDLS.exe (PID: 1648)
Creates files in the Windows directory
- logs.exe (PID: 3820)
Creates or modifies windows services
- xDLS.exe (PID: 3288)
Executable content was dropped or overwritten
- logs.exe (PID: 3820)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (42.6) |
|---|---|---|
| .exe | | | Win16/32 Executable Delphi generic (19.5) |
| .exe | | | Generic Win/DOS Executable (18.9) |
| .exe | | | DOS Executable Generic (18.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:06:10 11:45:56+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 2700288 |
| InitializedDataSize: | 1464832 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x49a001 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.1.19 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | xDedic INC. |
| FileVersion: | 1.0.1.19 |
| ProductVersion: | 1.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 10-Jun-2016 09:45:56 |
| Detected languages: |
|
| CompanyName: | xDedic INC. |
| FileVersion: | 1.0.1.19 |
| ProductVersion: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 12 |
| Time date stamp: | 10-Jun-2016 09:45:56 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00291000 | 0x000AF800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.99967 |
.itext | 0x00292000 | 0x00003000 | 0x00001400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.61244 |
.data | 0x00295000 | 0x0000A000 | 0x00004A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.98505 |
.bss | 0x0029F000 | 0x0009A954 | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0033A000 | 0x00004000 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.89162 |
.didata | 0x0033E000 | 0x00001000 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.1427 |
.edata | 0x0033F000 | 0x00001000 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.222 |
.tls | 0x00340000 | 0x0000004C | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x00341000 | 0x00001000 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.33455 |
.rsrc | 0x00342000 | 0x00158000 | 0x000D5C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.99743 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.8618 | 723 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 7.34082 | 308 | UNKNOWN | English - United States | RT_CURSOR |
3 | 7.24819 | 308 | UNKNOWN | English - United States | RT_CURSOR |
4 | 7.2847 | 308 | UNKNOWN | English - United States | RT_CURSOR |
5 | 7.26894 | 308 | UNKNOWN | English - United States | RT_CURSOR |
6 | 7.37434 | 308 | UNKNOWN | English - United States | RT_CURSOR |
7 | 7.34678 | 308 | UNKNOWN | English - United States | RT_CURSOR |
8 | 7.34527 | 308 | UNKNOWN | English - United States | RT_CURSOR |
4056 | 7.47599 | 408 | UNKNOWN | UNKNOWN | RT_STRING |
4057 | 7.71096 | 860 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
gdi32.dll |
kernel32.dll |
msvcrt.dll |
ole32.dll |
oleacc.dll |
oleaut32.dll |
shell32.dll |
user32.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
TMethodImplementationIntercept | 1 | 0x000564D8 |
Total processes
39
Monitored processes
4
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1648 | C:\Windows\xDLS.exe | C:\Windows\xDLS.exe | — | services.exe | |||||||||||
User: SYSTEM Company: xDedic INC. Integrity Level: SYSTEM Description: Windows Maintenance Exit code: 0 Version: 1.0.1.4 Modules
| |||||||||||||||
| 2428 | "C:\Users\admin\AppData\Local\Temp\logs.exe" | C:\Users\admin\AppData\Local\Temp\logs.exe | — | explorer.exe | |||||||||||
User: admin Company: xDedic INC. Integrity Level: MEDIUM Exit code: 3221226540 Version: 1.0.1.19 Modules
| |||||||||||||||
| 3288 | C:\Windows\xDLS.exe /install /silent | C:\Windows\xDLS.exe | — | logs.exe | |||||||||||
User: admin Company: xDedic INC. Integrity Level: HIGH Description: Windows Maintenance Exit code: 0 Version: 1.0.1.4 Modules
| |||||||||||||||
| 3820 | "C:\Users\admin\AppData\Local\Temp\logs.exe" | C:\Users\admin\AppData\Local\Temp\logs.exe | explorer.exe | ||||||||||||
User: admin Company: xDedic INC. Integrity Level: HIGH Exit code: 0 Version: 1.0.1.19 Modules
| |||||||||||||||
Total events
45
Read events
16
Write events
29
Delete events
0
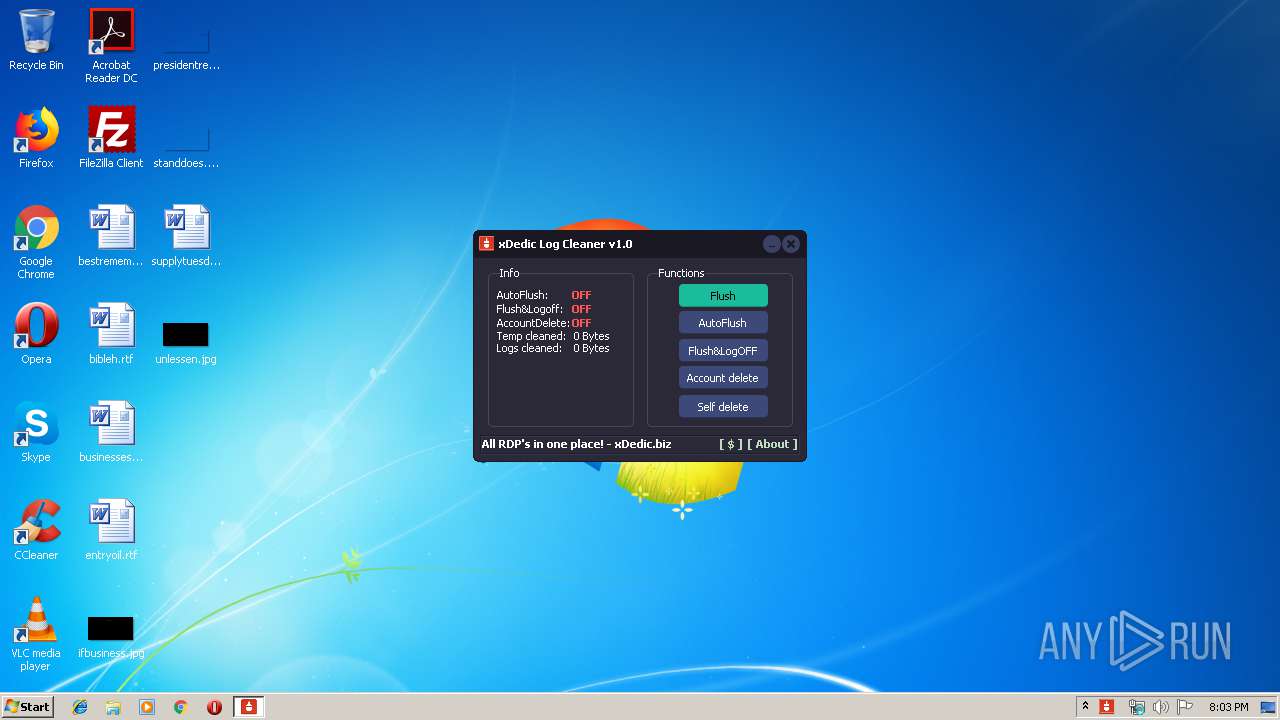
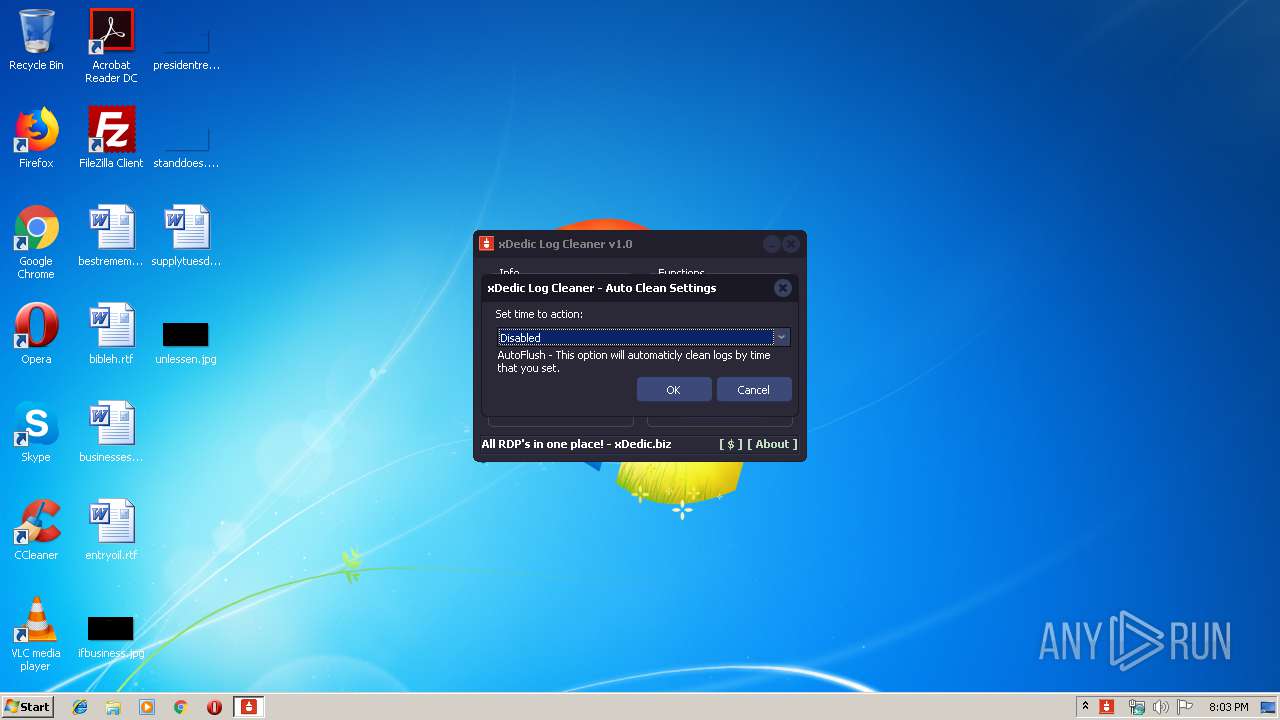
Modification events
| (PID) Process: | (3820) logs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\XDLC Software |
| Operation: | write | Name: | WinAccName |
Value: YWRtaW4= | |||
| (PID) Process: | (3820) logs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\XDLC Software |
| Operation: | write | Name: | AppExeName |
Value: QzpcVXNlcnNcYWRtaW5cQXBwRGF0YVxMb2NhbFxUZW1wXGxvZ3MuZXhl | |||
| (PID) Process: | (3820) logs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\XDLC Software |
| Operation: | write | Name: | AutoFlushTimer |
Value: 0 | |||
| (PID) Process: | (3820) logs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\XDLC Software |
| Operation: | write | Name: | AccFlushLogoff |
Value: 0 | |||
| (PID) Process: | (3820) logs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\XDLC Software |
| Operation: | write | Name: | AccDelete |
Value: 0 | |||
| (PID) Process: | (3820) logs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\XDLC Software |
| Operation: | write | Name: | AccFlushLogoffTime |
Value: 0 | |||
| (PID) Process: | (3820) logs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\XDLC Software |
| Operation: | write | Name: | AccDeleteTime |
Value: 0 | |||
| (PID) Process: | (3820) logs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\XDLC Software |
| Operation: | write | Name: | AccNextFlush |
Value: 0 | |||
| (PID) Process: | (3820) logs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\XDLC Software |
| Operation: | write | Name: | OptAutoFlush |
Value: 0 | |||
| (PID) Process: | (3820) logs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\XDLC Software |
| Operation: | write | Name: | OptFlushLogoff |
Value: 0 | |||
Executable files
1
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3820 | logs.exe | C:\Windows\xDLS.exe | executable | |
MD5:2F9AC709C1419B96771D81E1EDD79E8A | SHA256:D00CFB07692EA3D0533F082A14295F7E18383420C2A940A024030C8BAD67FB3A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report