| File name: | 1570567738.doc |
| Full analysis: | https://app.any.run/tasks/268e7375-8e01-4e35-be2e-6d27b4feff1f |
| Verdict: | Malicious activity |
| Analysis date: | October 14, 2019, 06:52:05 |
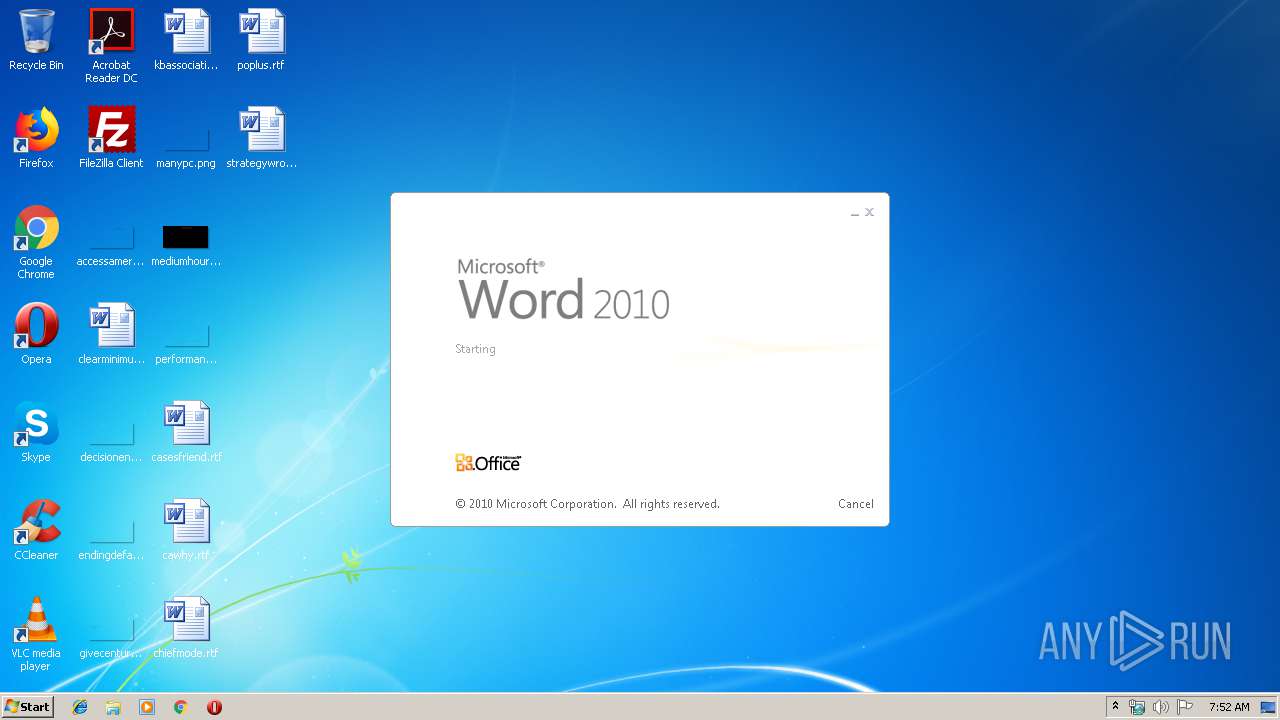
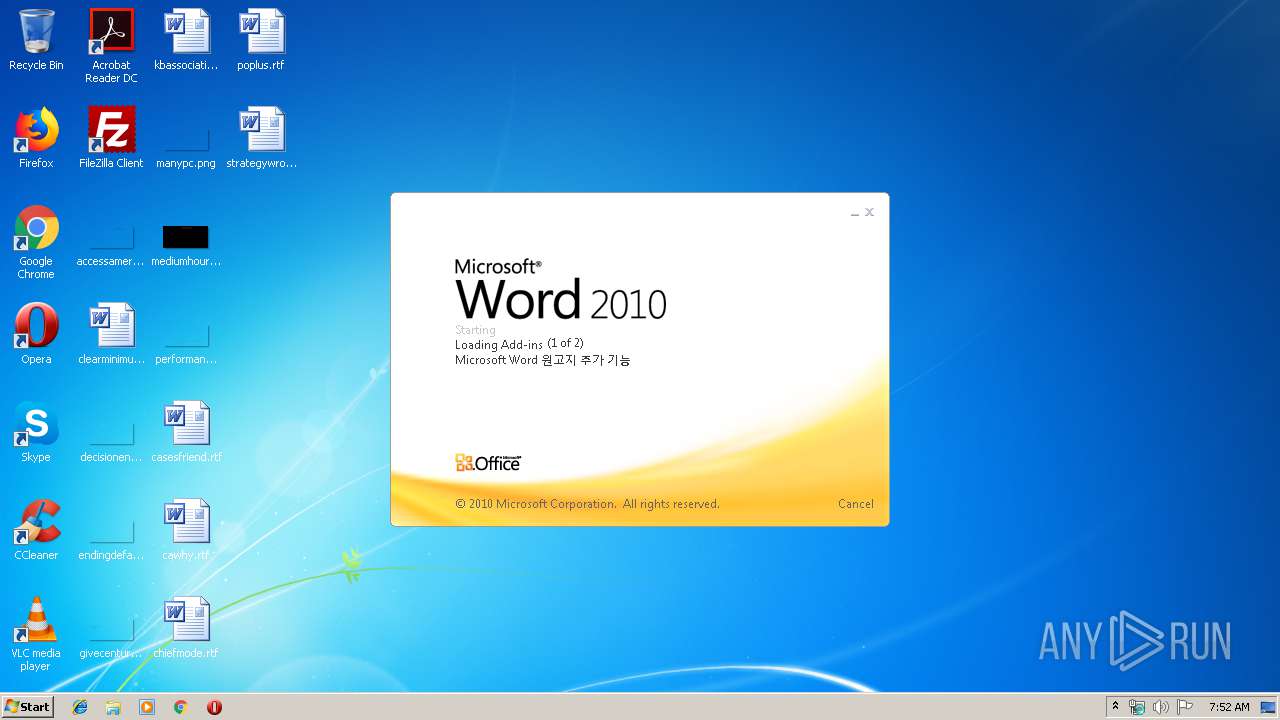
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/rtf |
| File info: | Rich Text Format data, version 1, unknown character set |
| MD5: | 7657F3784B718621C028716FBF6CA3E2 |
| SHA1: | 2AD5A3612738FE4C8BFD6F10A5876ACE434A1181 |
| SHA256: | 876CAA26F9F70FB04C89C4C63C53BDAC1EBD31236E863ED689A865D8CFC5EE6C |
| SSDEEP: | 12288:mpDIrl6nxevhIyXYLVaB9JokEsHDJXe1/ws8G/UHZ2FDIXblnrPb+RkdtXVBBW8:mpDIrlUevhV1DJXRs8G/S2gFBY8 |
MALICIOUS
Application was dropped or rewritten from another process
- ldin.exe (PID: 3872)
- ldin.exe (PID: 3968)
Executable content was dropped or overwritten
- WINWORD.EXE (PID: 2384)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2384)
Writes to a start menu file
- DllHost.exe (PID: 3616)
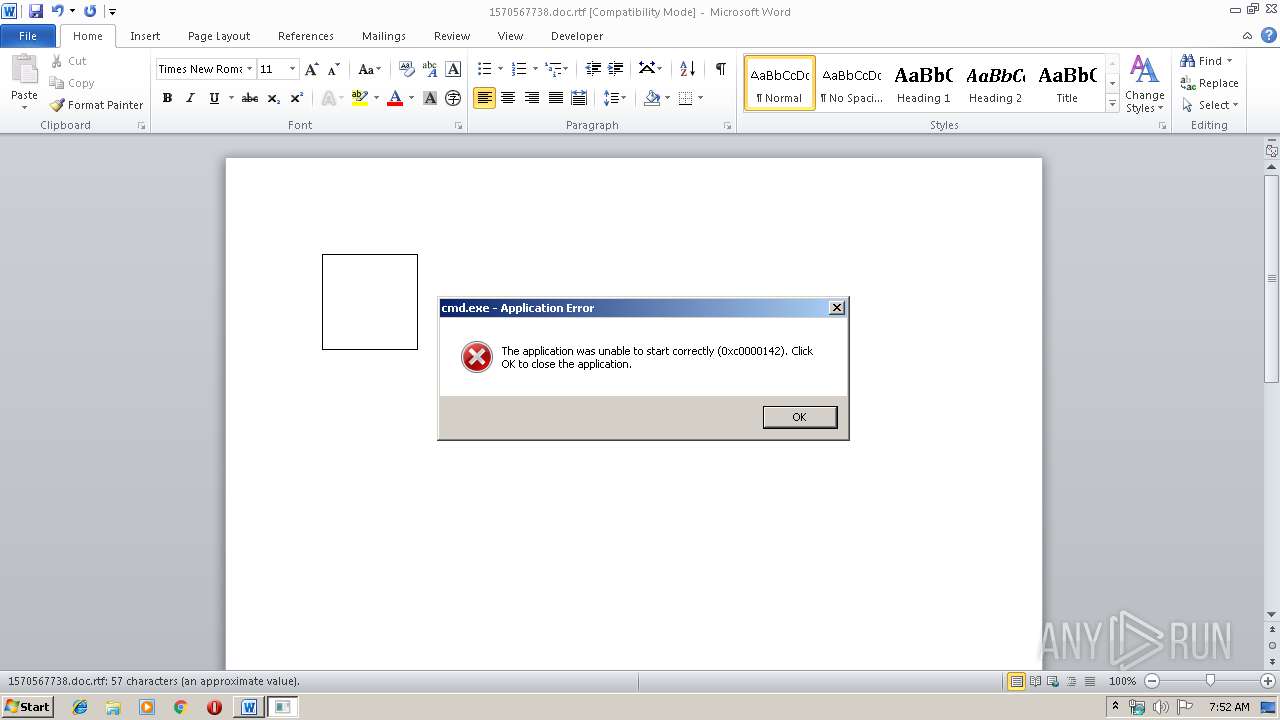
Equation Editor starts application (CVE-2017-11882)
- EQNEDT32.EXE (PID: 2472)
SUSPICIOUS
Starts CMD.EXE for commands execution
- EQNEDT32.EXE (PID: 2472)
Reads internet explorer settings
- EQNEDT32.EXE (PID: 2472)
Executed via COM
- EQNEDT32.EXE (PID: 2472)
- DllHost.exe (PID: 3616)
Application launched itself
- ldin.exe (PID: 3872)
Creates files in the user directory
- DllHost.exe (PID: 3616)
Executable content was dropped or overwritten
- DllHost.exe (PID: 3616)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2384)
Creates files in the user directory
- WINWORD.EXE (PID: 2384)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rtf | | | Rich Text Format (100) |
|---|
Total processes
41
Monitored processes
6
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2384 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\1570567738.doc.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | explorer.exe | ||||||||||||
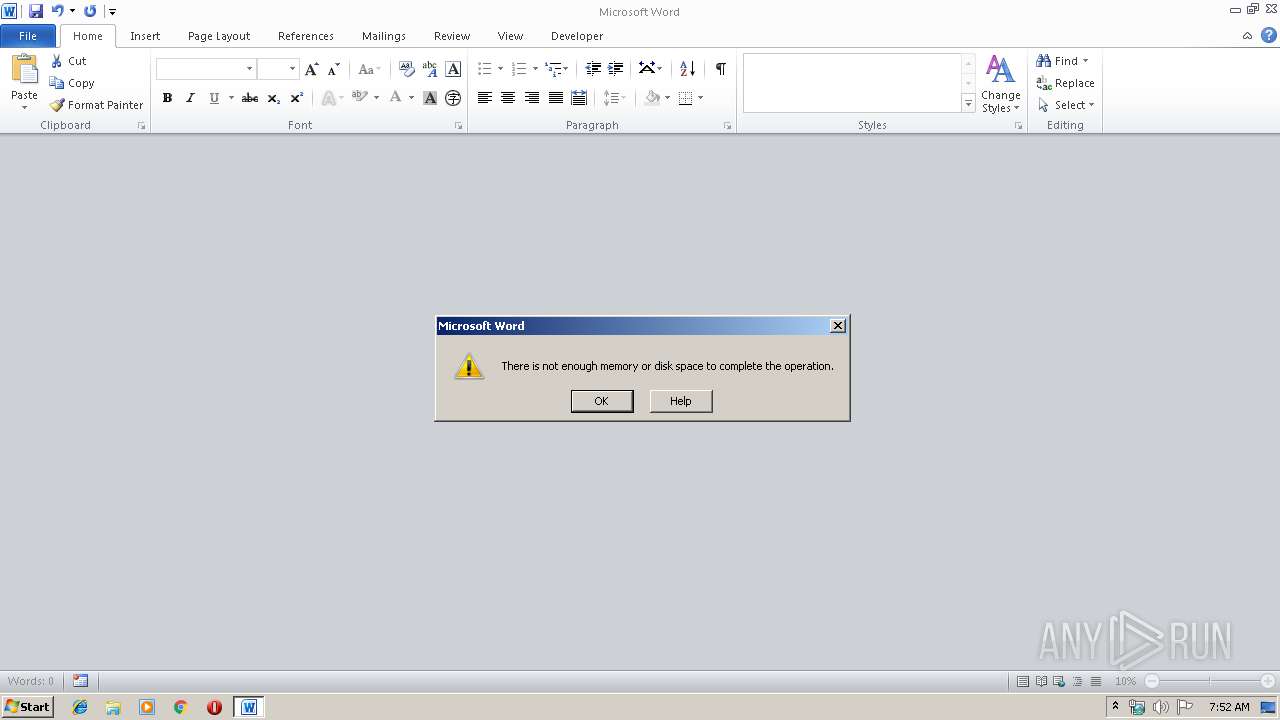
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2472 | "C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE" -Embedding | C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE | — | svchost.exe | |||||||||||
User: admin Company: Design Science, Inc. Integrity Level: MEDIUM Description: Microsoft Equation Editor Exit code: 0 Version: 00110900 Modules
| |||||||||||||||
| 2896 | "C:\Windows\System32\cmd.exe" /c C:\Users\admin\AppData\Local\Temp\ldin.exe | C:\Windows\System32\cmd.exe | — | EQNEDT32.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 3221225794 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3616 | C:\Windows\system32\DllHost.exe /Processid:{3AD05575-8857-4850-9277-11B85BDB8E09} | C:\Windows\system32\DllHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3872 | "C:\Users\admin\AppData\Local\Temp\ldin.exe" | C:\Users\admin\AppData\Local\Temp\ldin.exe | — | WINWORD.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Description: CustomControlDemo MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 3968 | "C:\Users\admin\AppData\Local\Temp\ldin.exe" | C:\Users\admin\AppData\Local\Temp\ldin.exe | ldin.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: CustomControlDemo MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
Total events
2 260
Read events
1 493
Write events
632
Delete events
135
Modification events
| (PID) Process: | (2384) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 5ba |
Value: 3562610050090000010000000000000000000000 | |||
| (PID) Process: | (2384) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2384) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2384) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2384) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2384) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2384) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2384) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2384) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2384) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1330511934 | |||
Executable files
2
Suspicious files
0
Text files
1
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2384 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRAA15.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3872 | ldin.exe | C:\Users\admin\AppData\Local\Temp\Liebert.bmp | — | |
MD5:— | SHA256:— | |||
| 2384 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2384 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\1.a | text | |
MD5:DCD94CFCF3517AA9F1C9F47B75A08C0E | SHA256:0404FFE20E2F5CABC8913E3C9832EF6494D2EF47D5FACE1A78259BF9728BC13C | |||
| 2384 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$70567738.doc.rtf | pgc | |
MD5:— | SHA256:— | |||
| 2384 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\F84D9794.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2384 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\ldin.exe | executable | |
MD5:0D8D8589C01A18BC63B4CEDE2D5386DC | SHA256:2524E1FCA051374E6BDEF56EFBC9D8A0DC28CFE50FC39FCD501AB4A70EE2136A | |||
| 3616 | DllHost.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\Nomem8.exe | executable | |
MD5:0D8D8589C01A18BC63B4CEDE2D5386DC | SHA256:2524E1FCA051374E6BDEF56EFBC9D8A0DC28CFE50FC39FCD501AB4A70EE2136A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
2
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3968 | ldin.exe | 79.134.225.115:3303 | — | Andreas Fink trading as Fink Telecom Services | CH | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dns.msftncsi.com |
| shared |