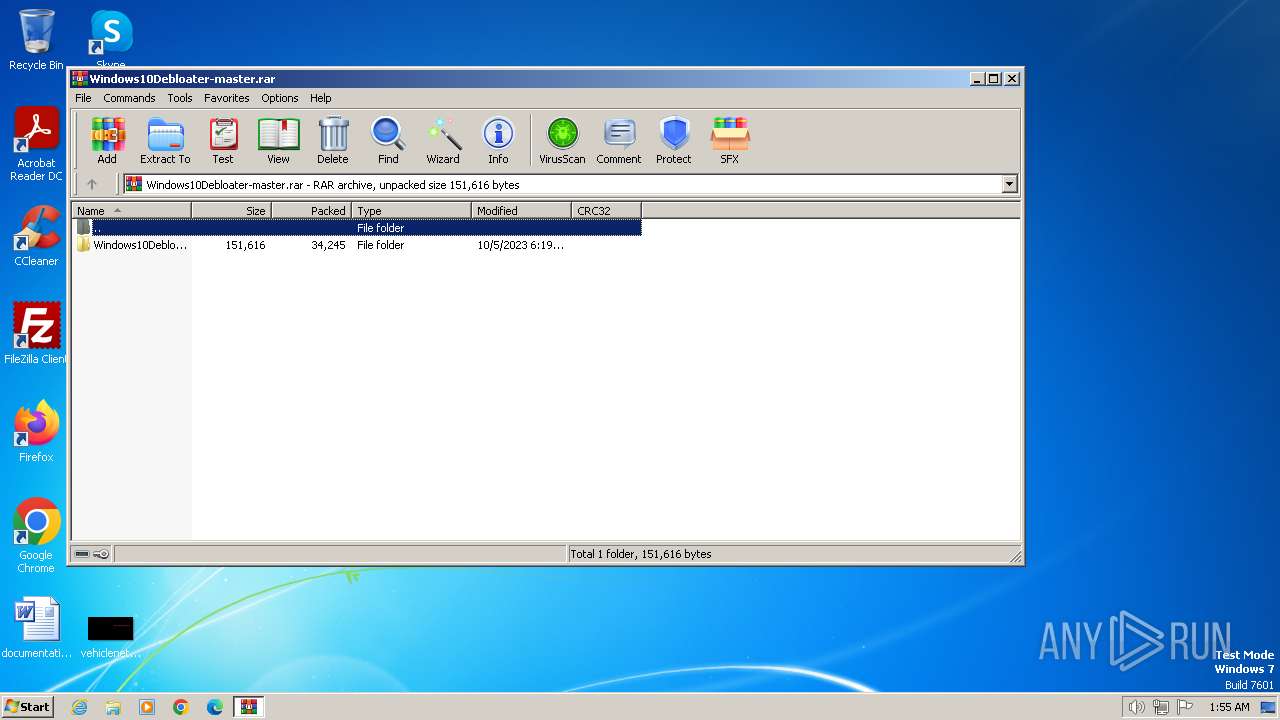
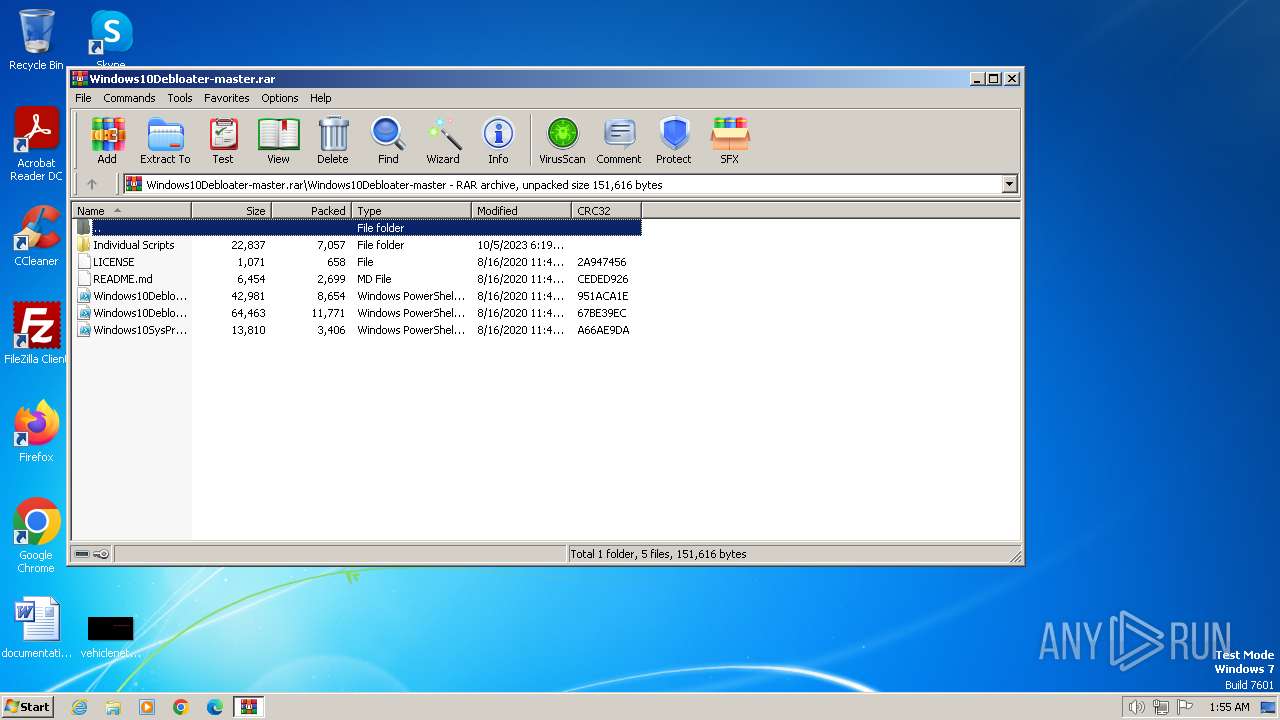
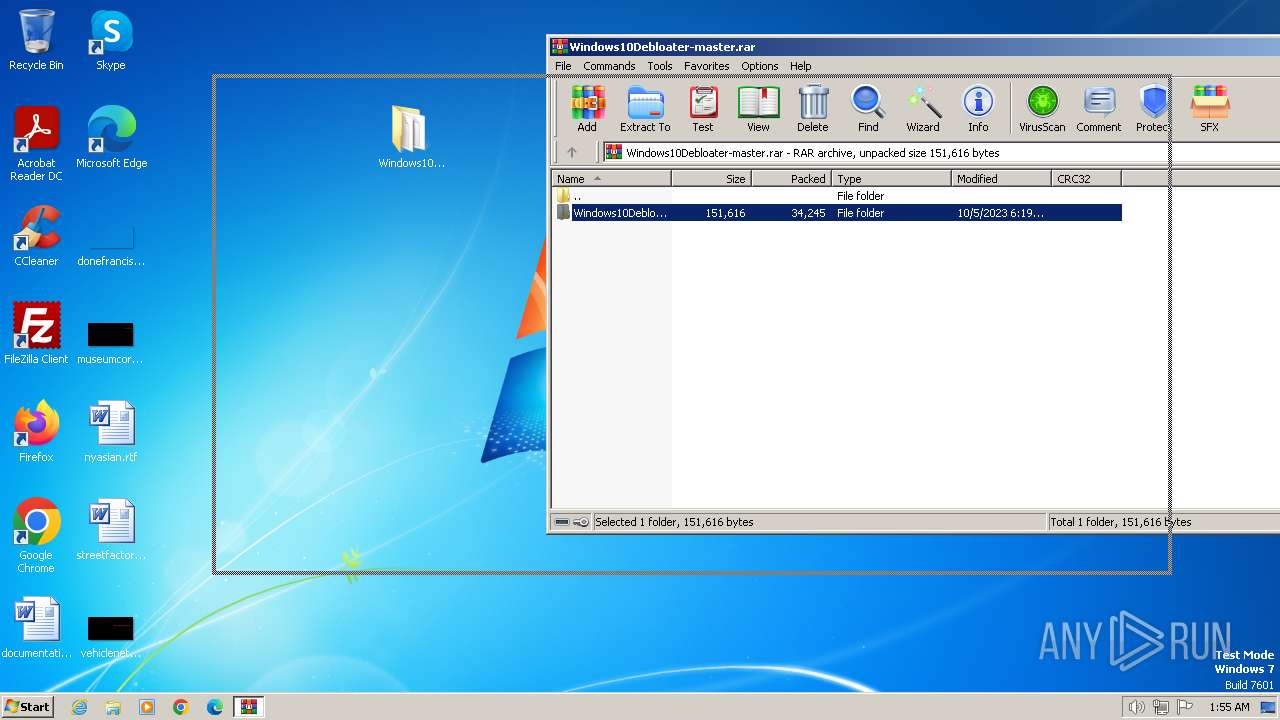
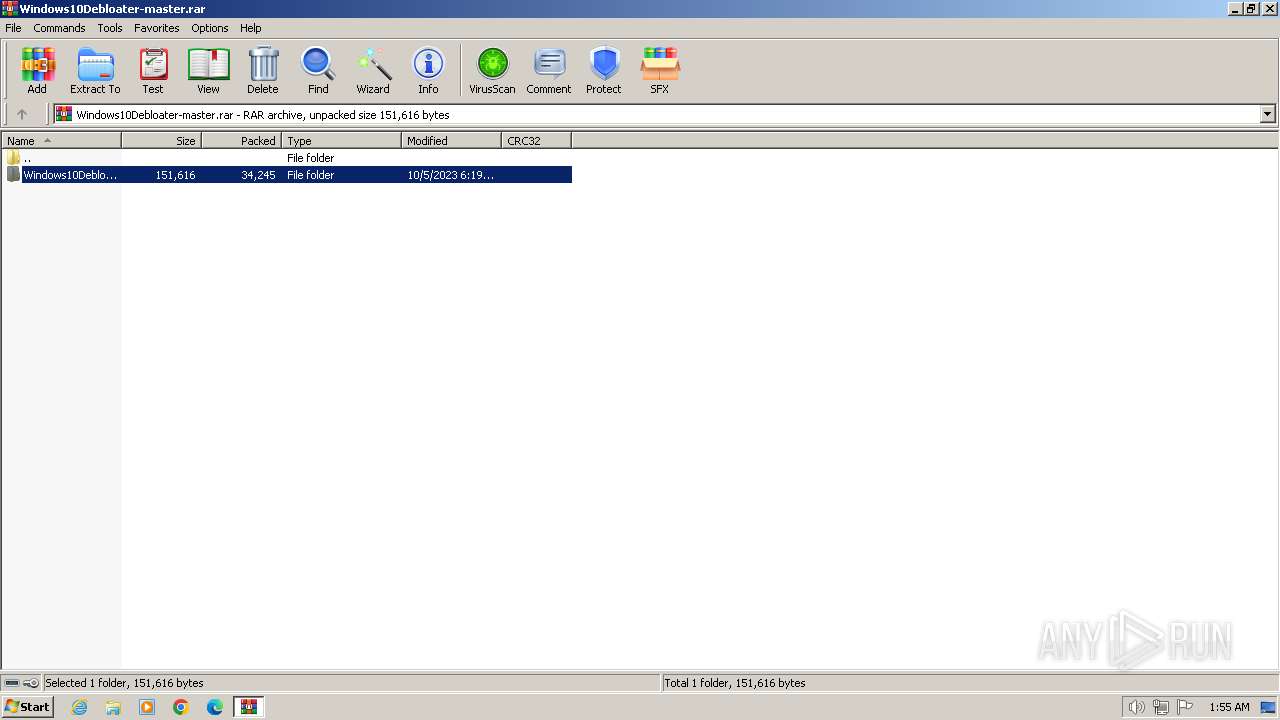
| File name: | Windows10Debloater-master.rar |
| Full analysis: | https://app.any.run/tasks/18b94002-81f0-40a2-9aeb-f31c2c507ab4 |
| Verdict: | Malicious activity |
| Analysis date: | January 14, 2024, 01:55:12 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 12A19025DCC93B54FB4382949BD87F4B |
| SHA1: | B8B95D47E8D4D33A30BE9E2729ED4FF623B216E3 |
| SHA256: | 875168DE3658B9C6C967D132F694666ED75D1ACEFFD28BD71FCAA816303FF711 |
| SSDEEP: | 768:/lpxN+rsxK3argpr+jgAr1ub9nhpKT7eqfdlz32cdWUbTfuITrxx:/3XxK3qgJG71uRhIem2c5T2If |
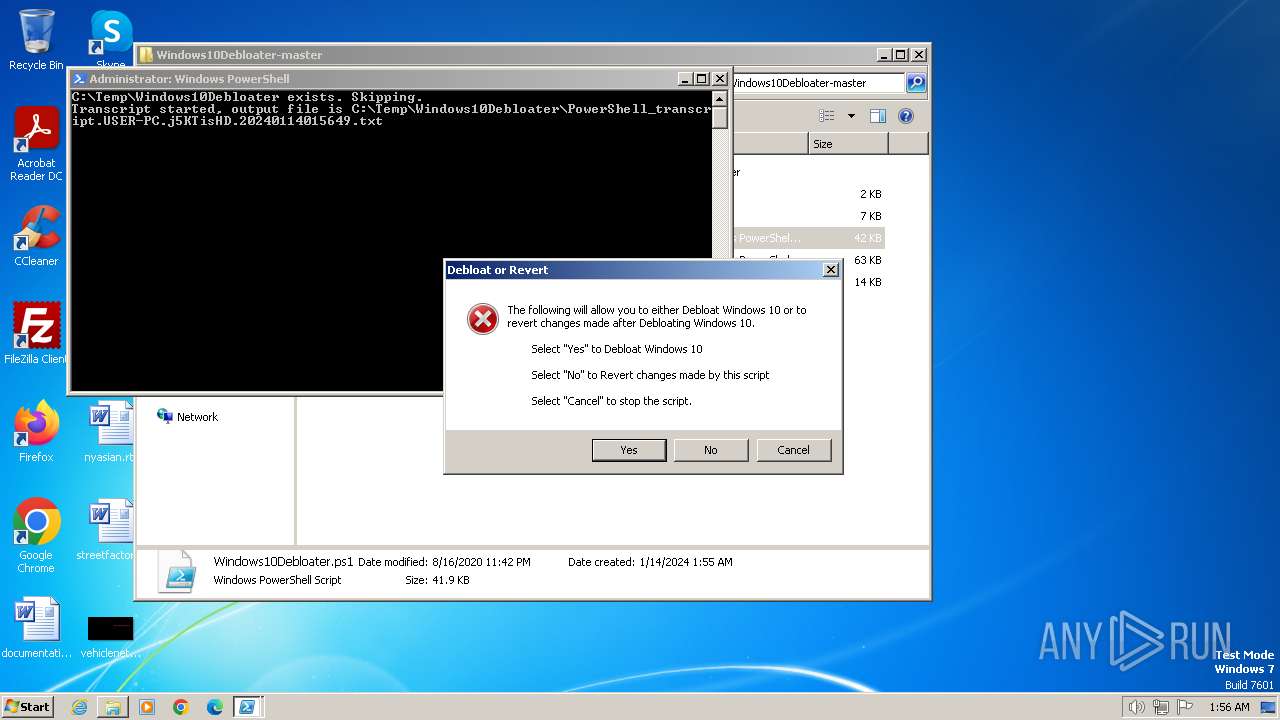
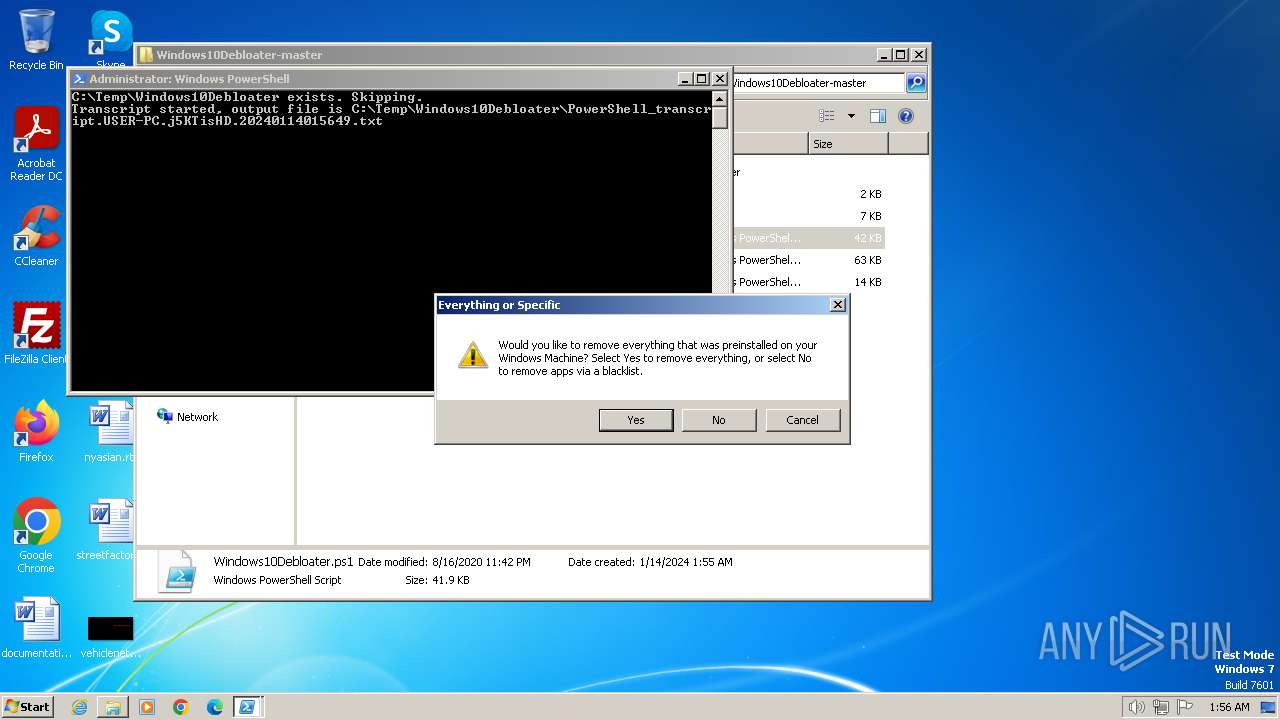
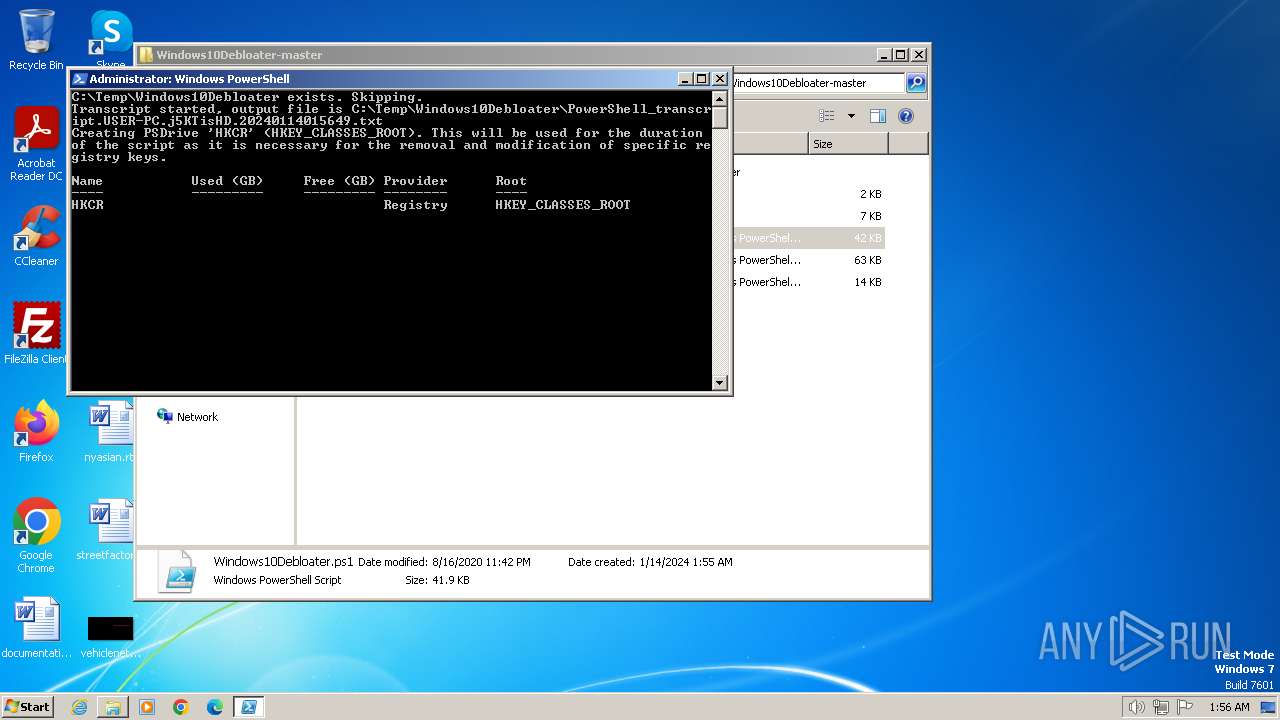
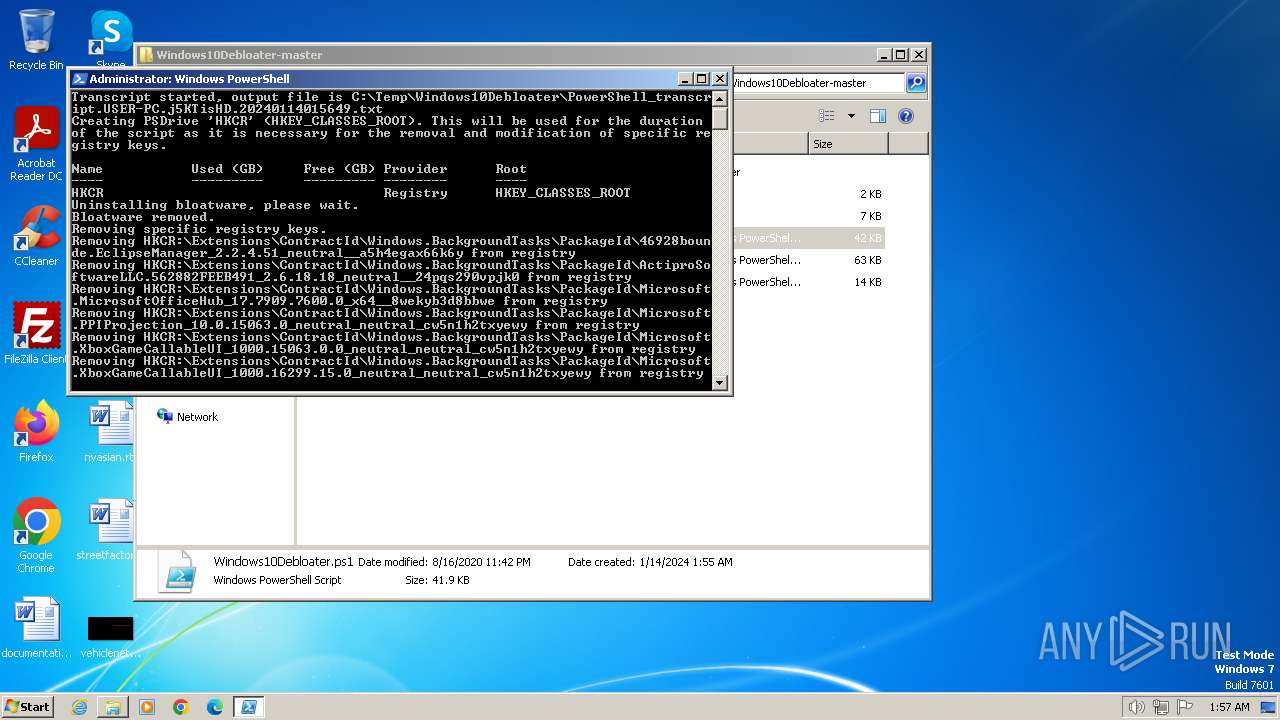
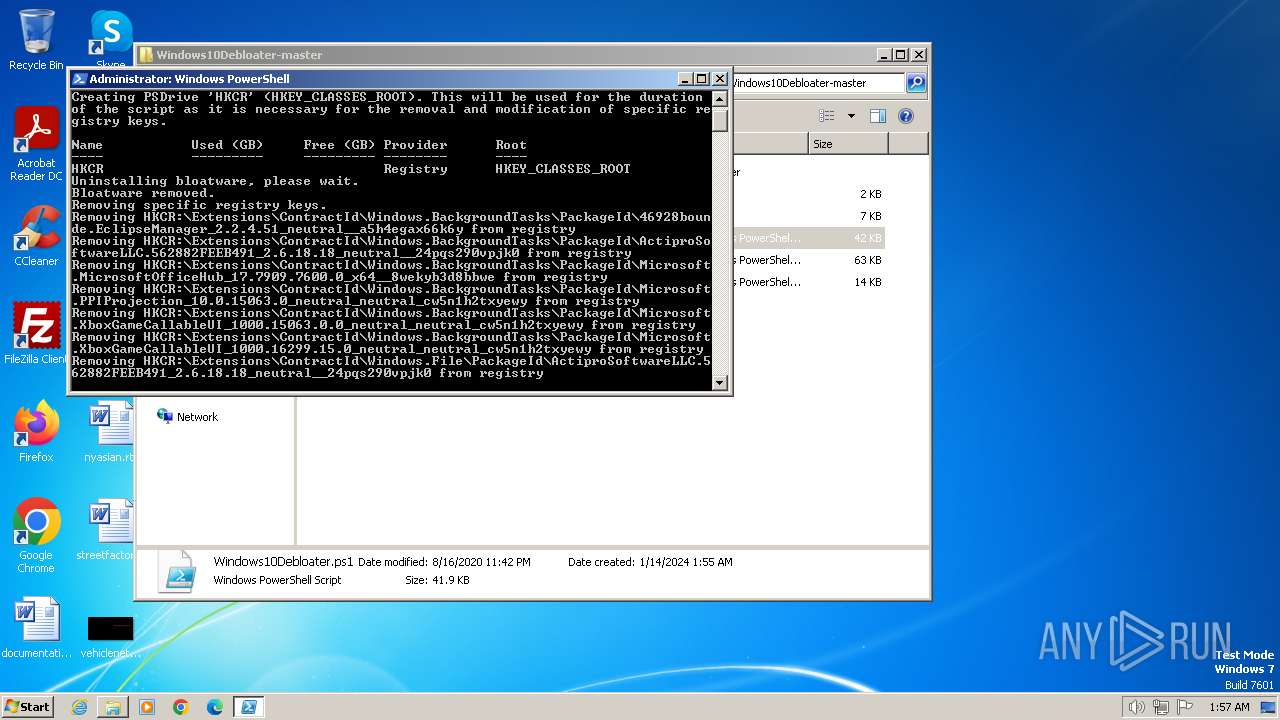
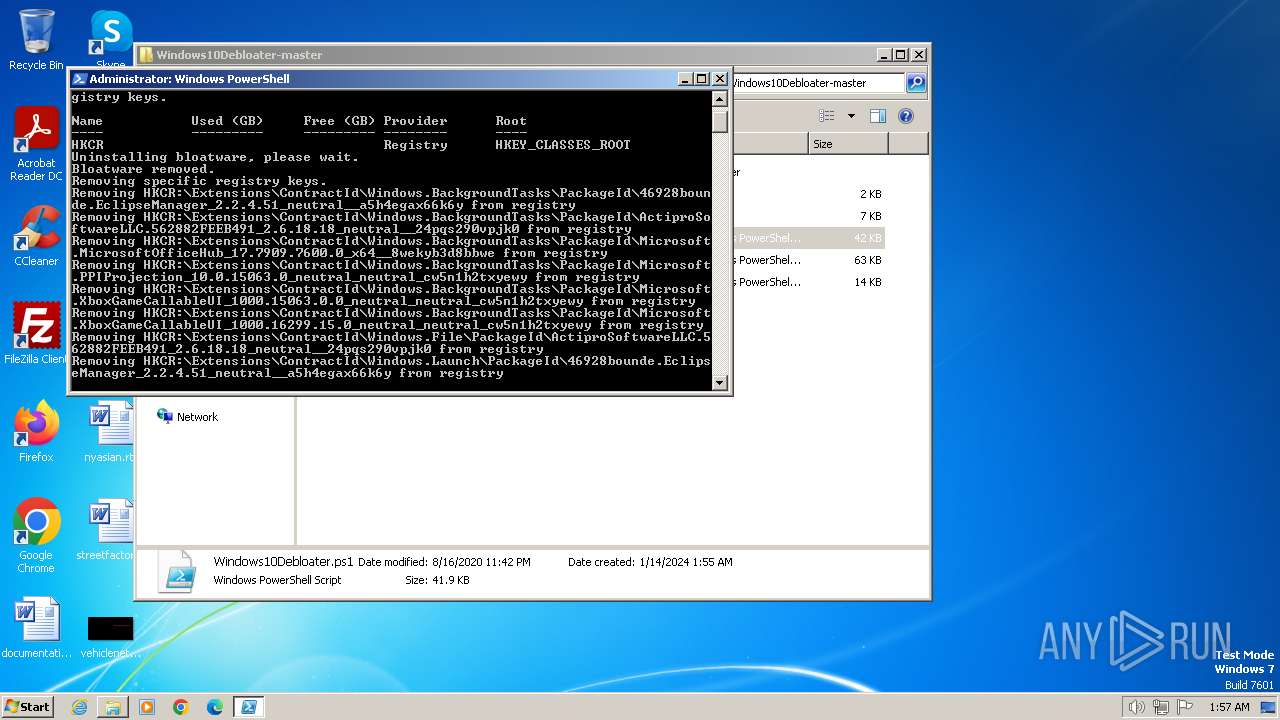
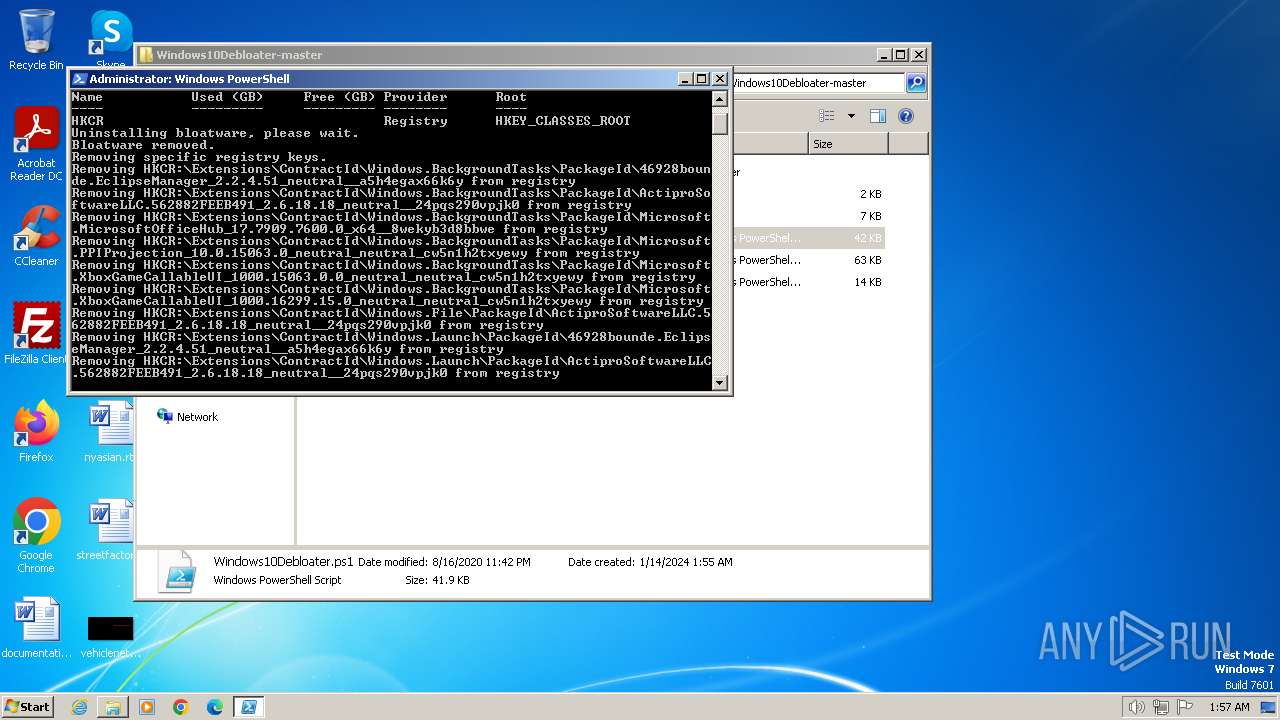
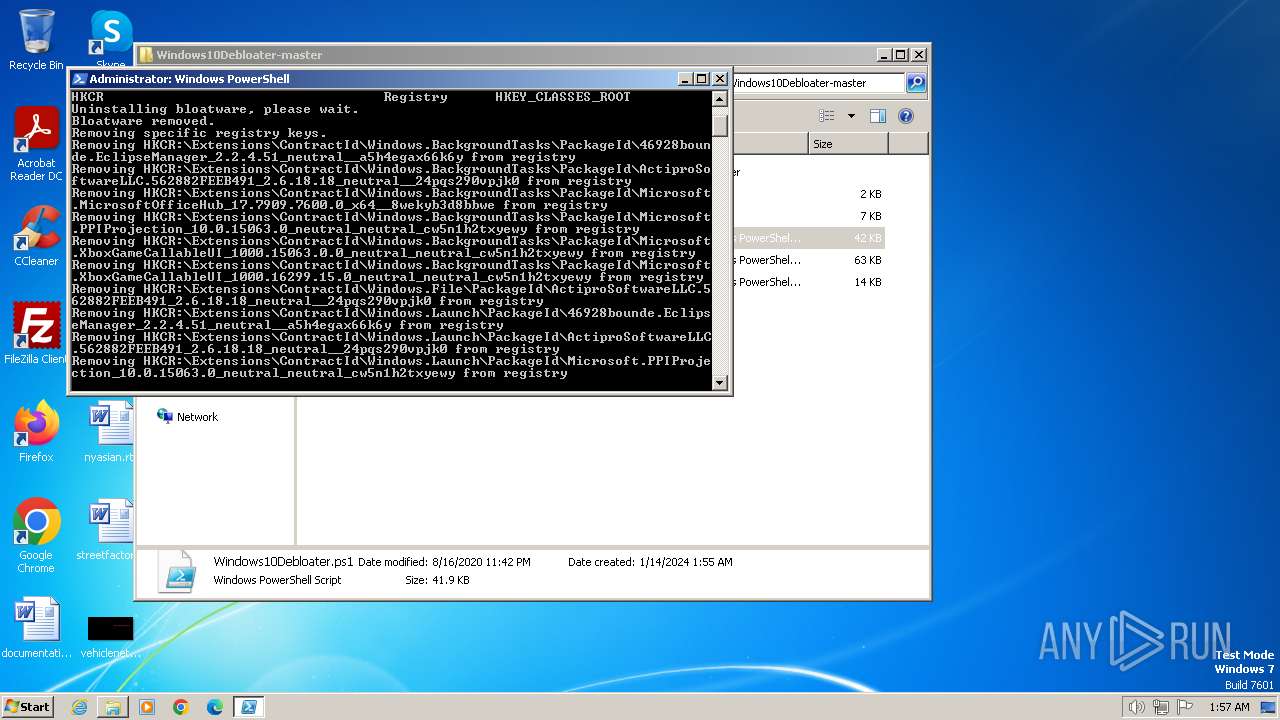
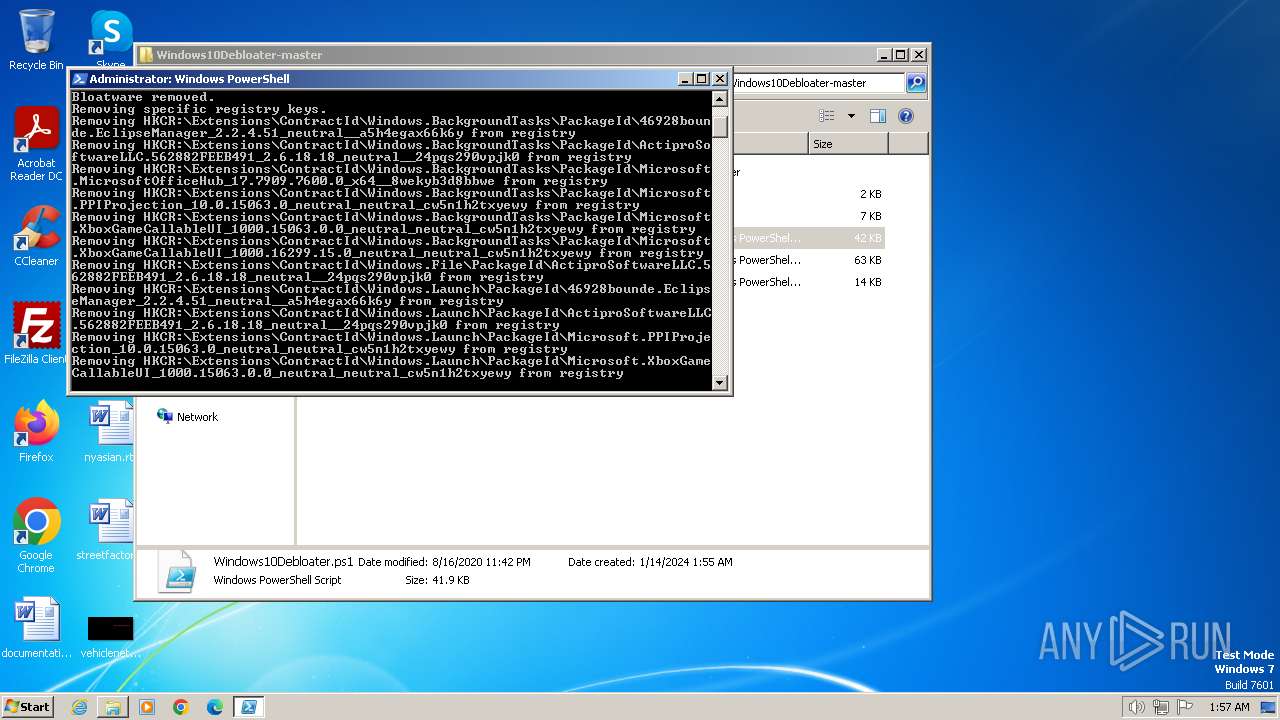
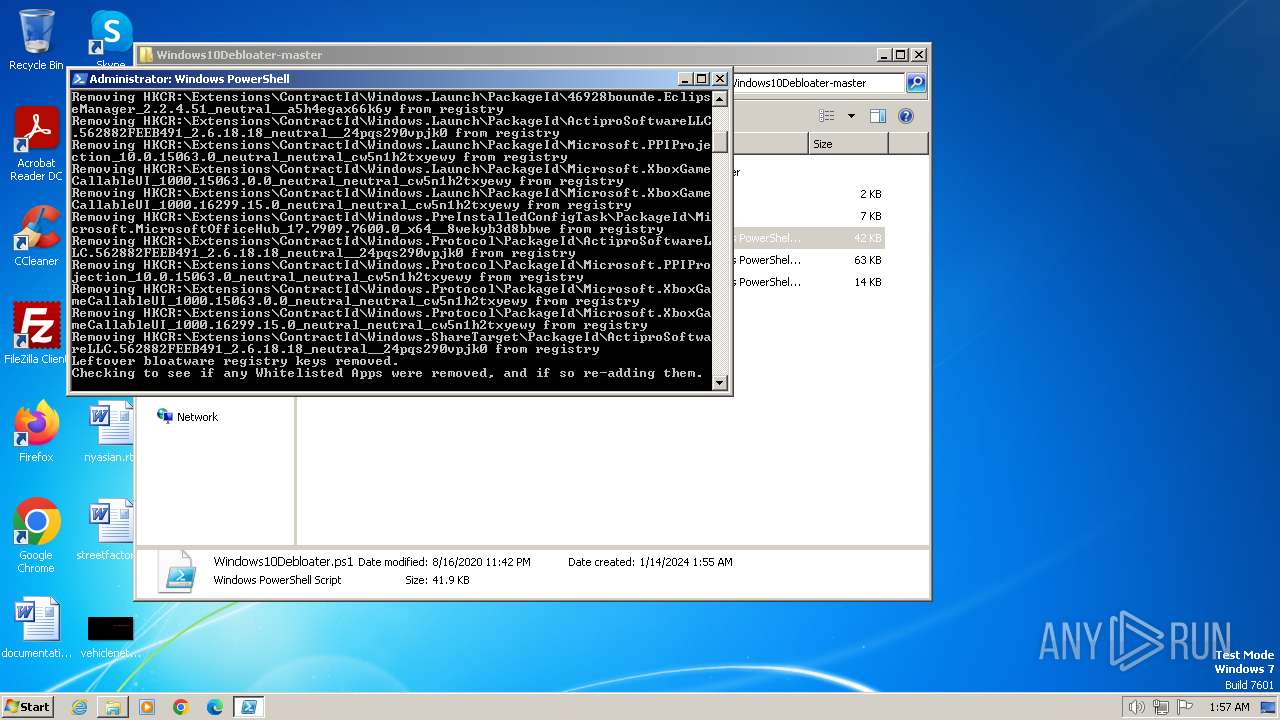
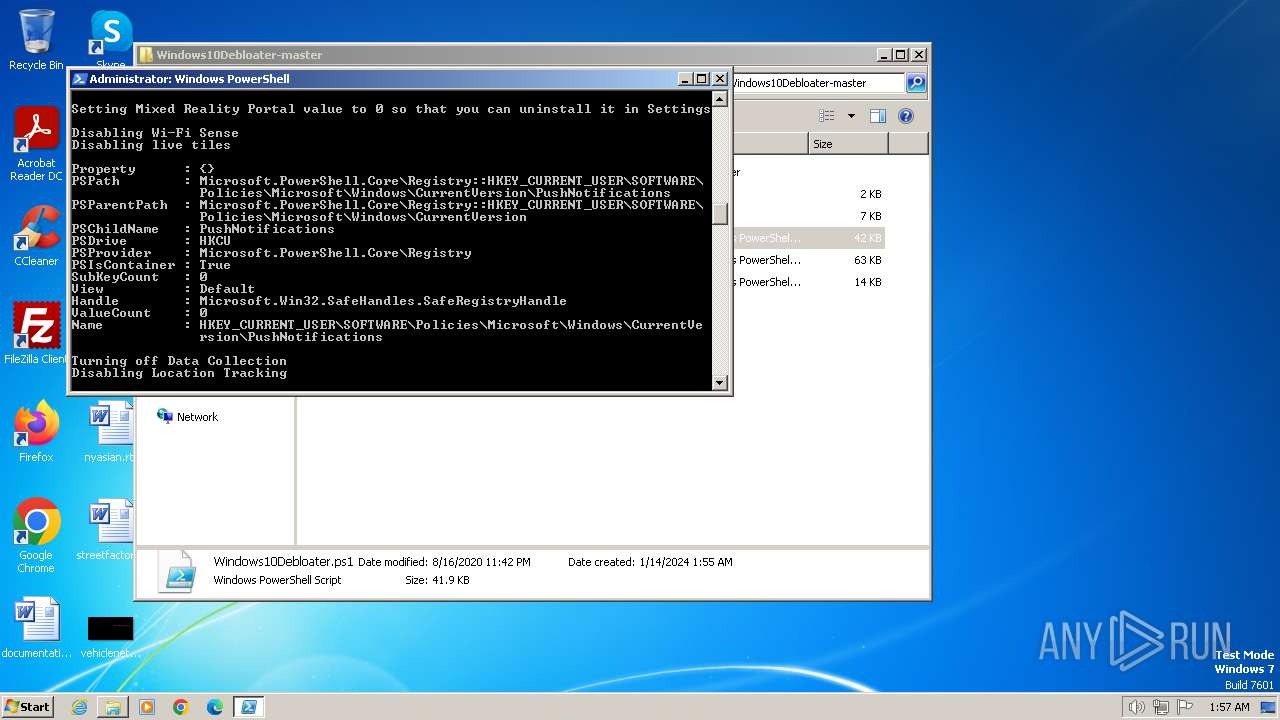
MALICIOUS
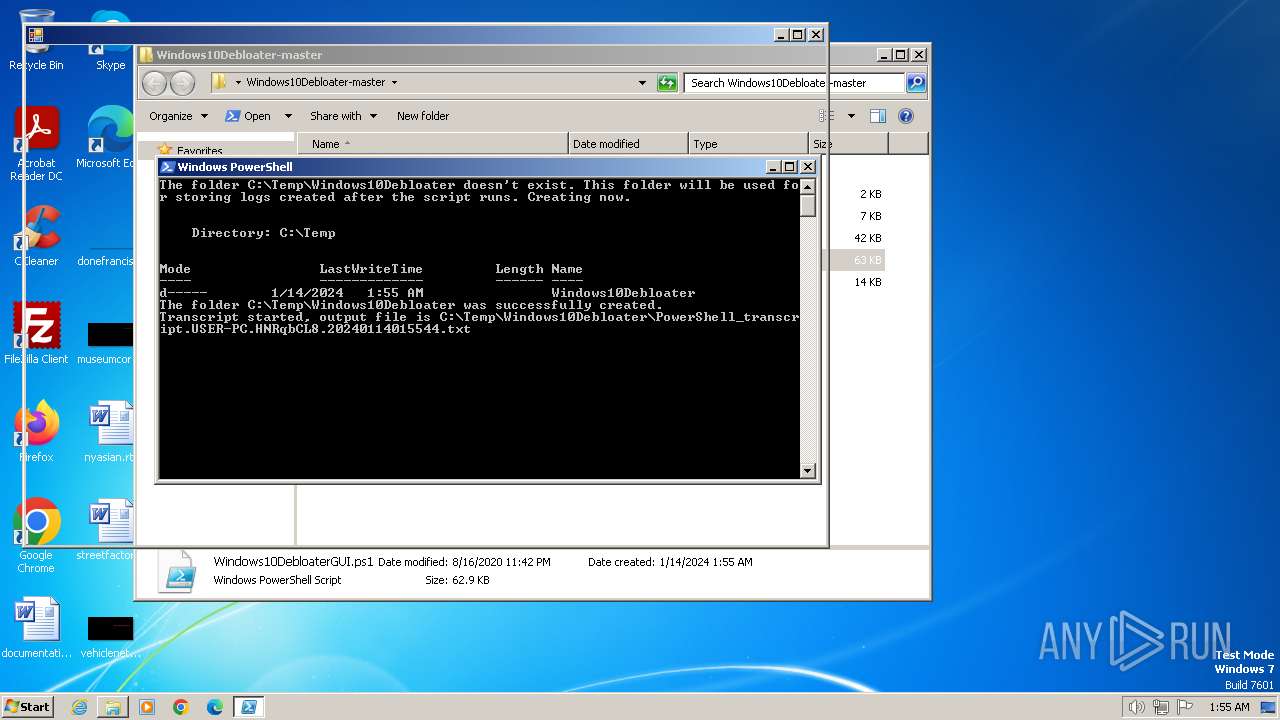
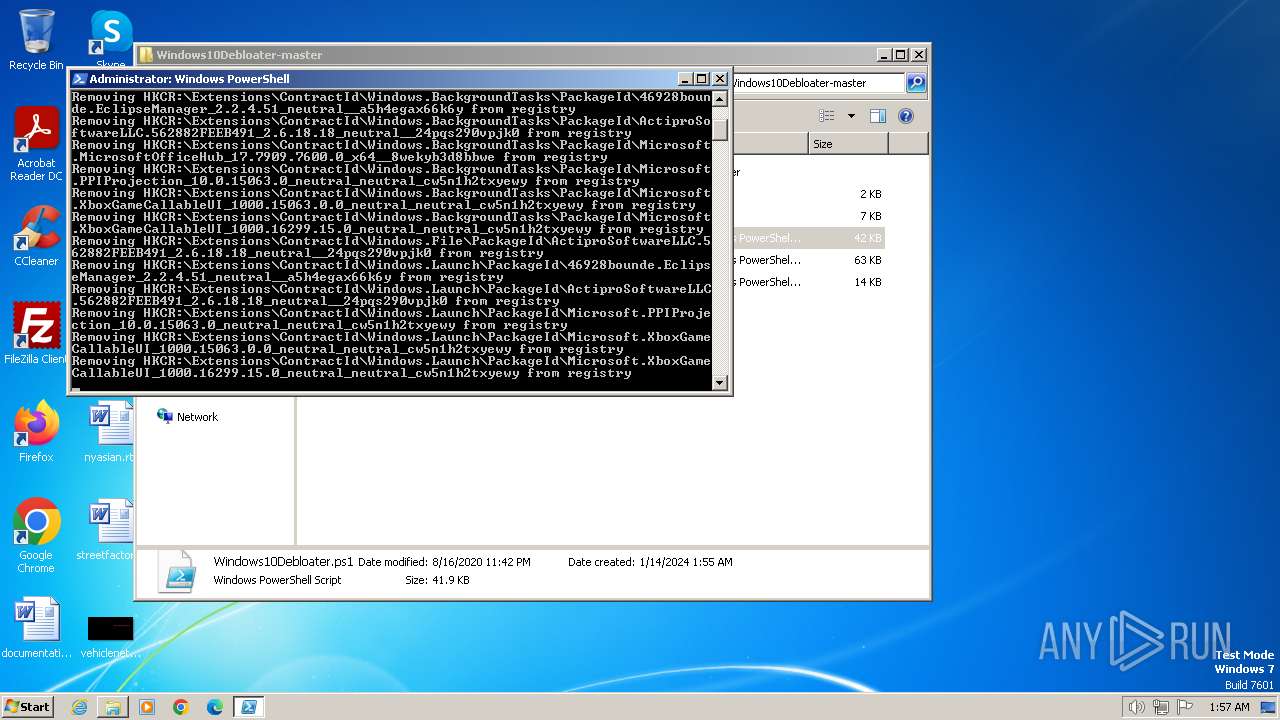
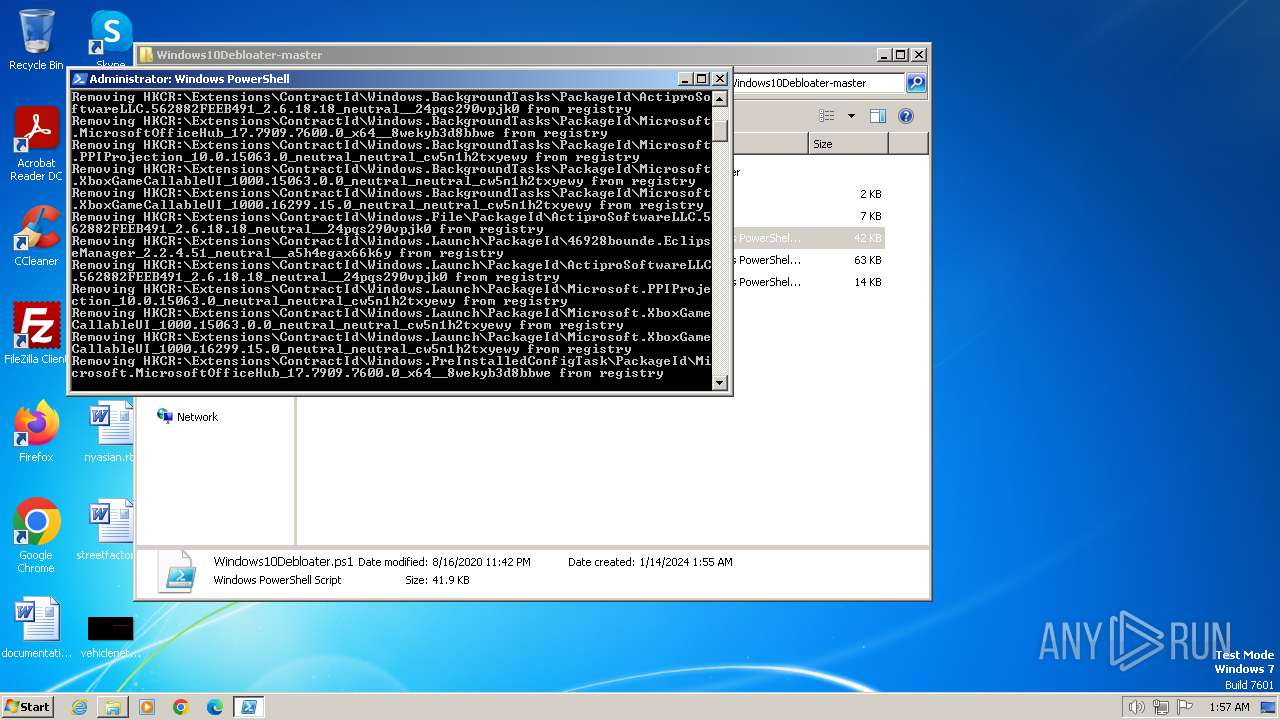
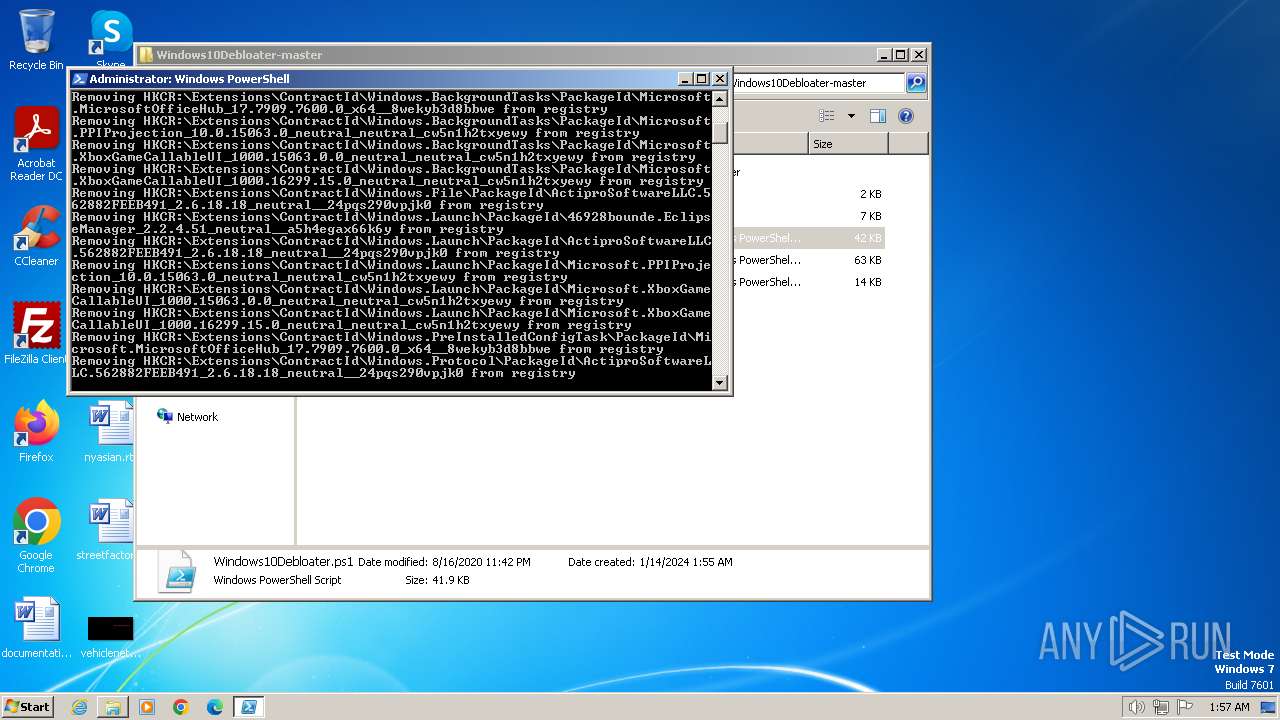
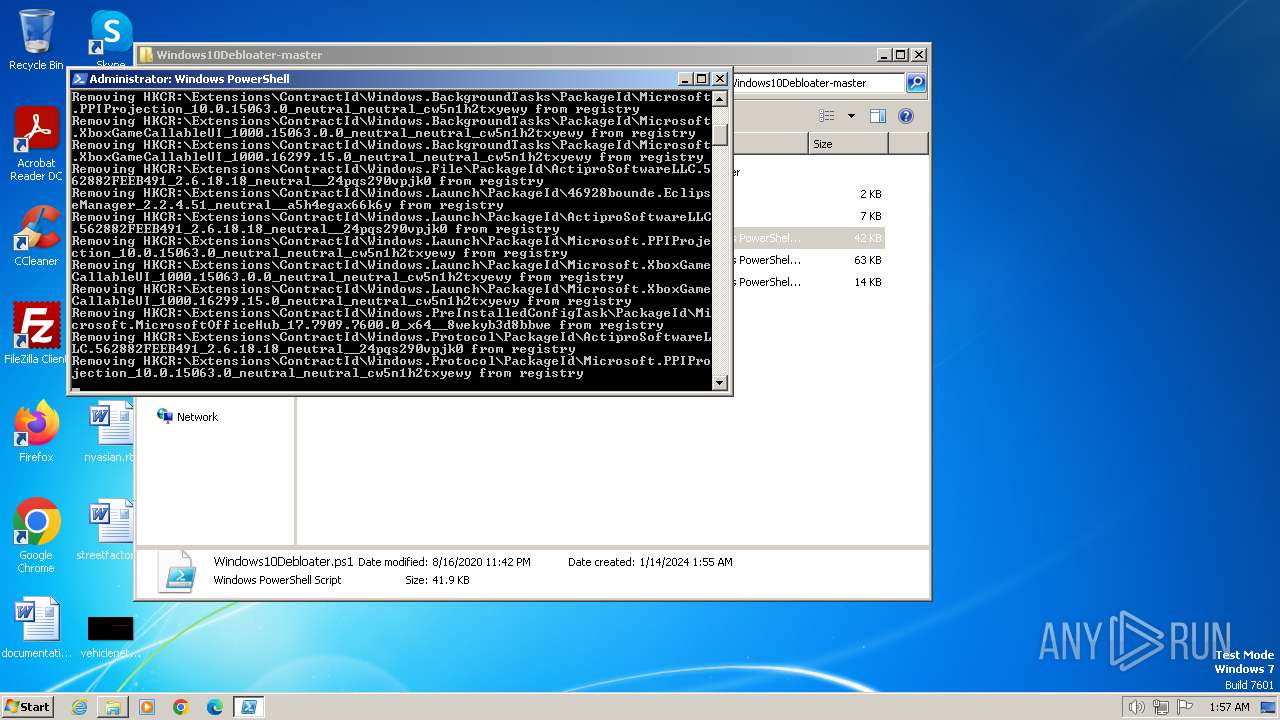
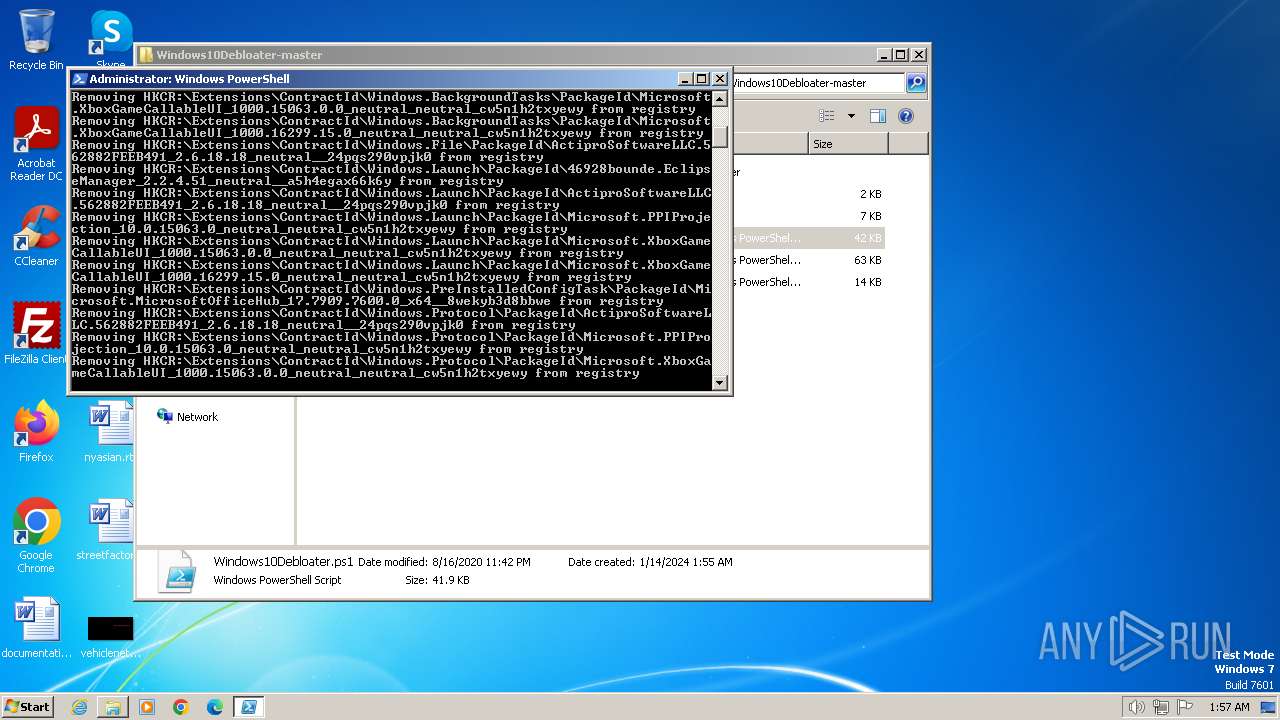
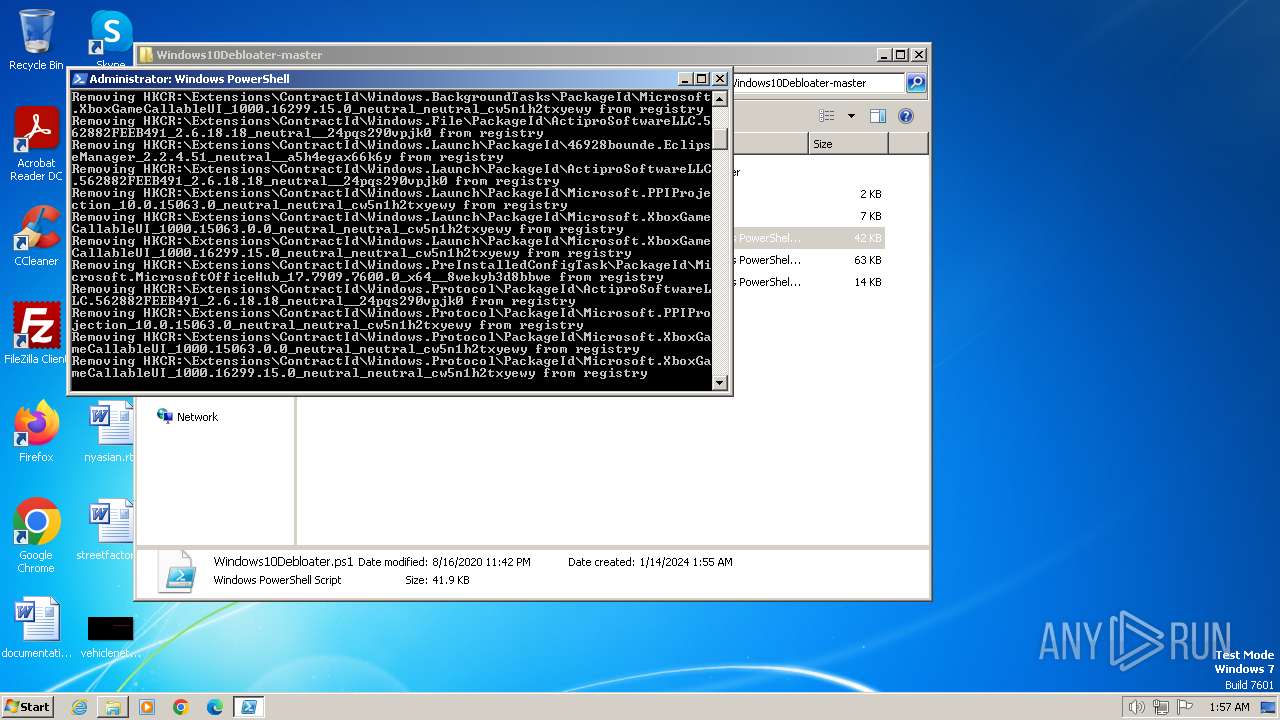
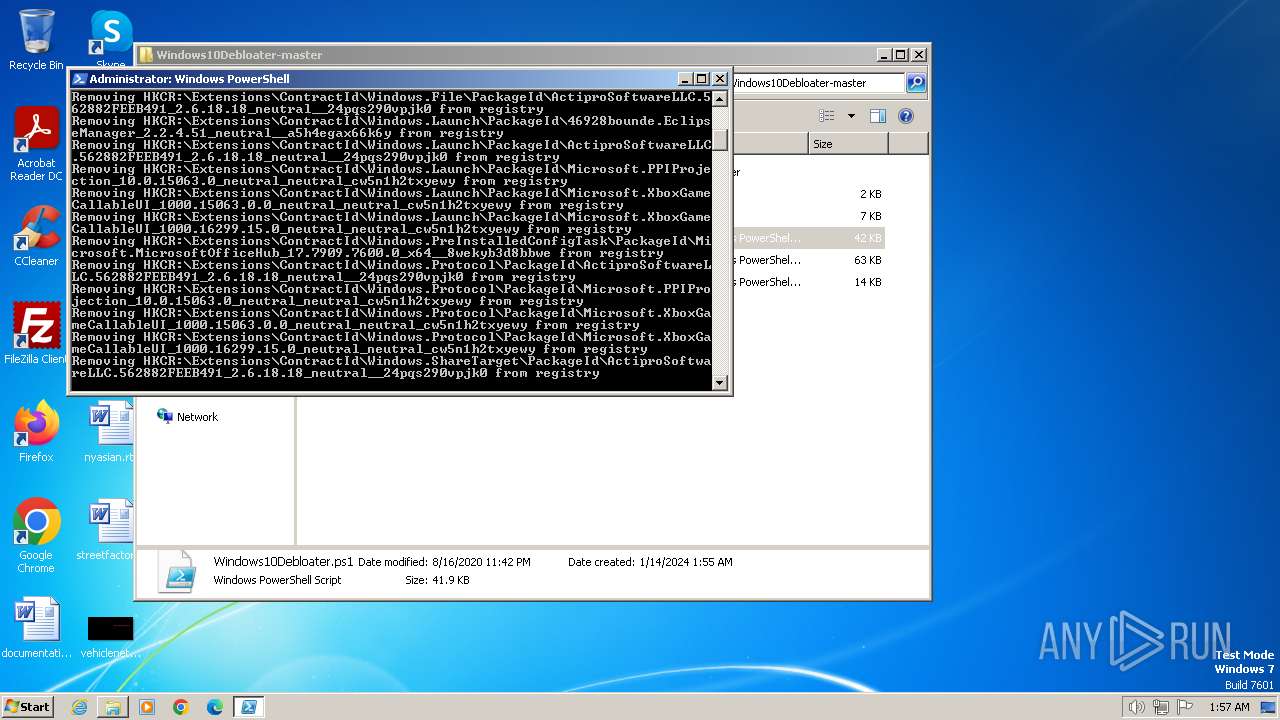
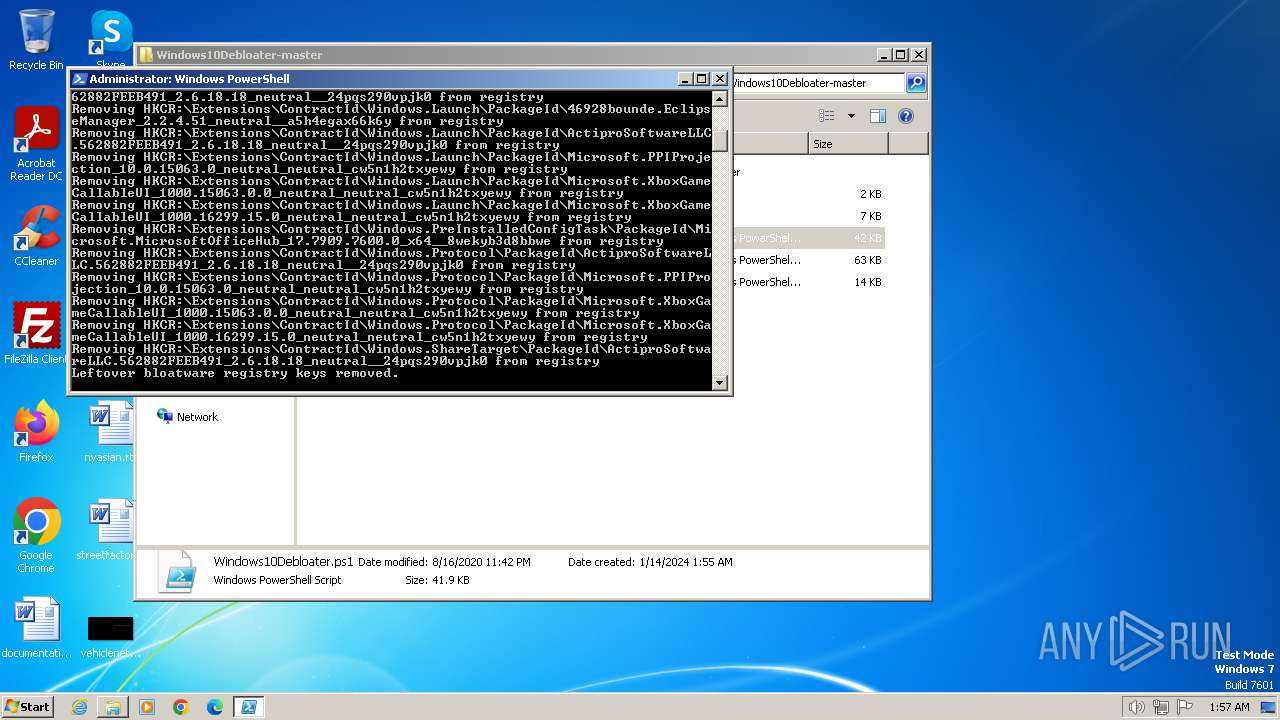
Bypass execution policy to execute commands
- powershell.exe (PID: 1504)
- powershell.exe (PID: 680)
- powershell.exe (PID: 1220)
Changes powershell execution policy (Bypass)
- powershell.exe (PID: 680)
SUSPICIOUS
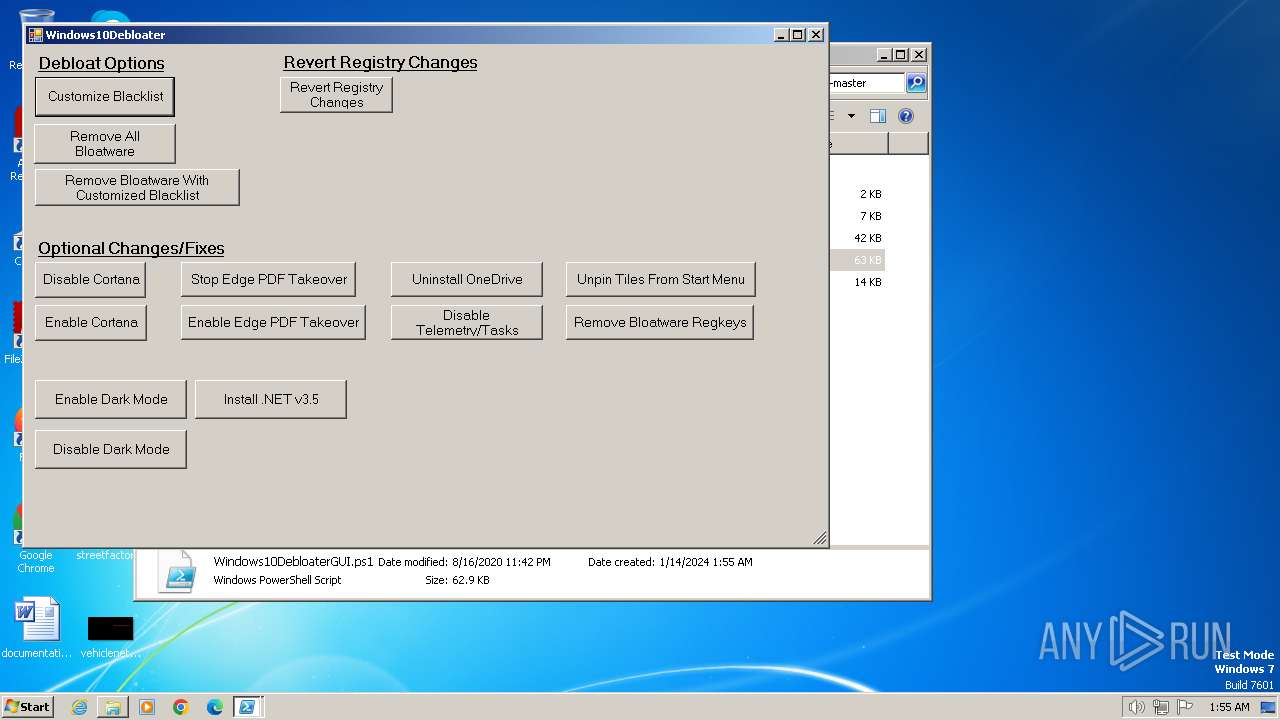
Using PowerShell to operate with local accounts
- powershell.exe (PID: 1504)
Reads the Internet Settings
- powershell.exe (PID: 680)
- powershell.exe (PID: 1504)
The process bypasses the loading of PowerShell profile settings
- powershell.exe (PID: 680)
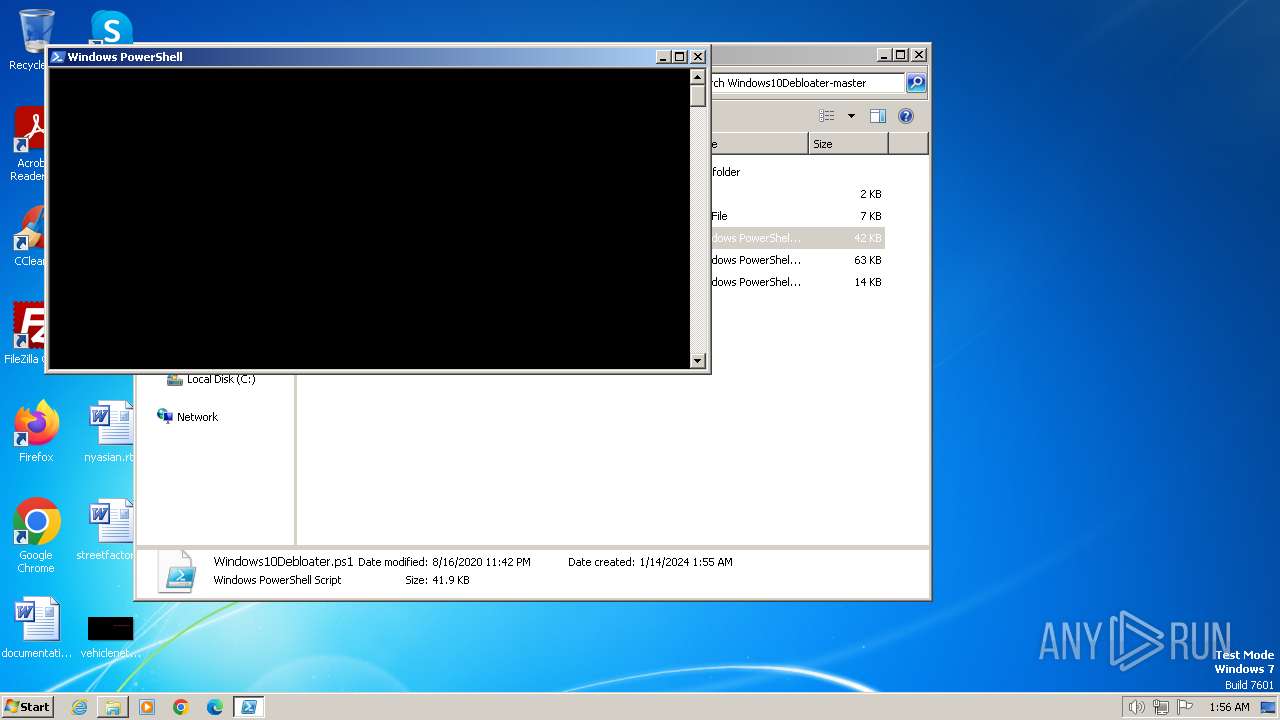
Starts POWERSHELL.EXE for commands execution
- powershell.exe (PID: 680)
The process executes Powershell scripts
- powershell.exe (PID: 680)
Application launched itself
- powershell.exe (PID: 680)
INFO
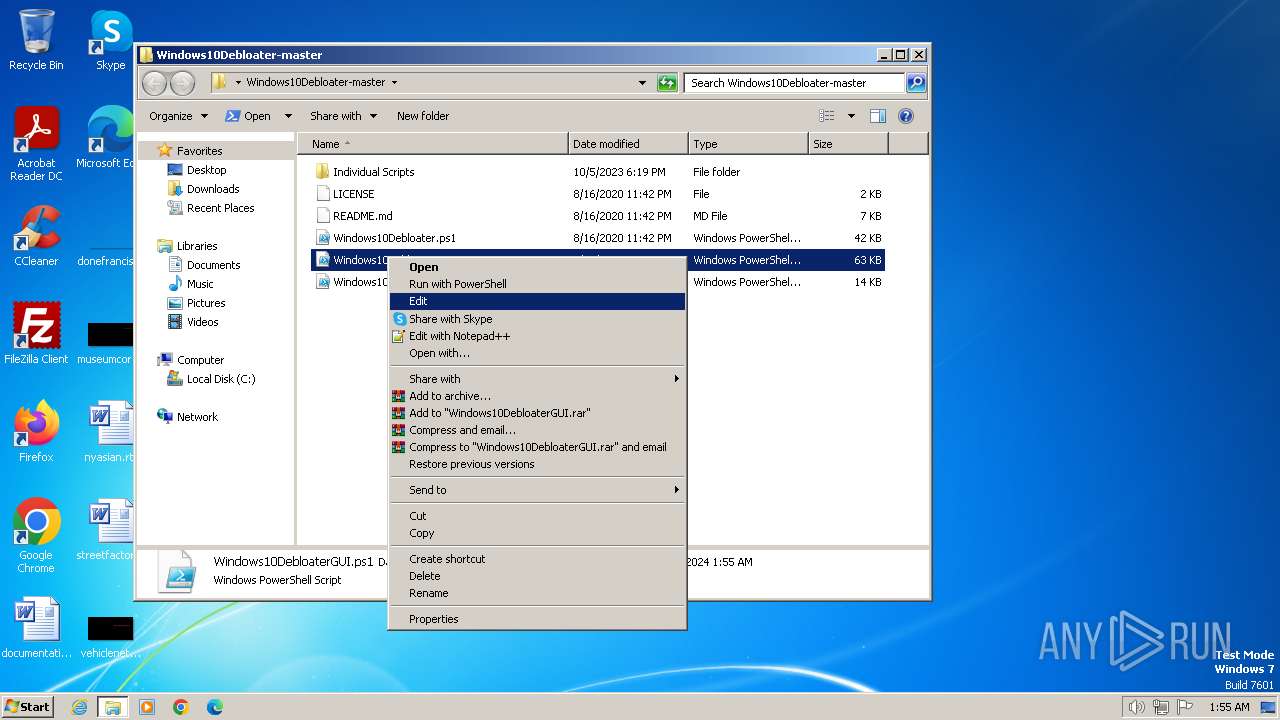
Manual execution by a user
- powershell.exe (PID: 1504)
- powershell.exe (PID: 680)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
52
Monitored processes
4
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
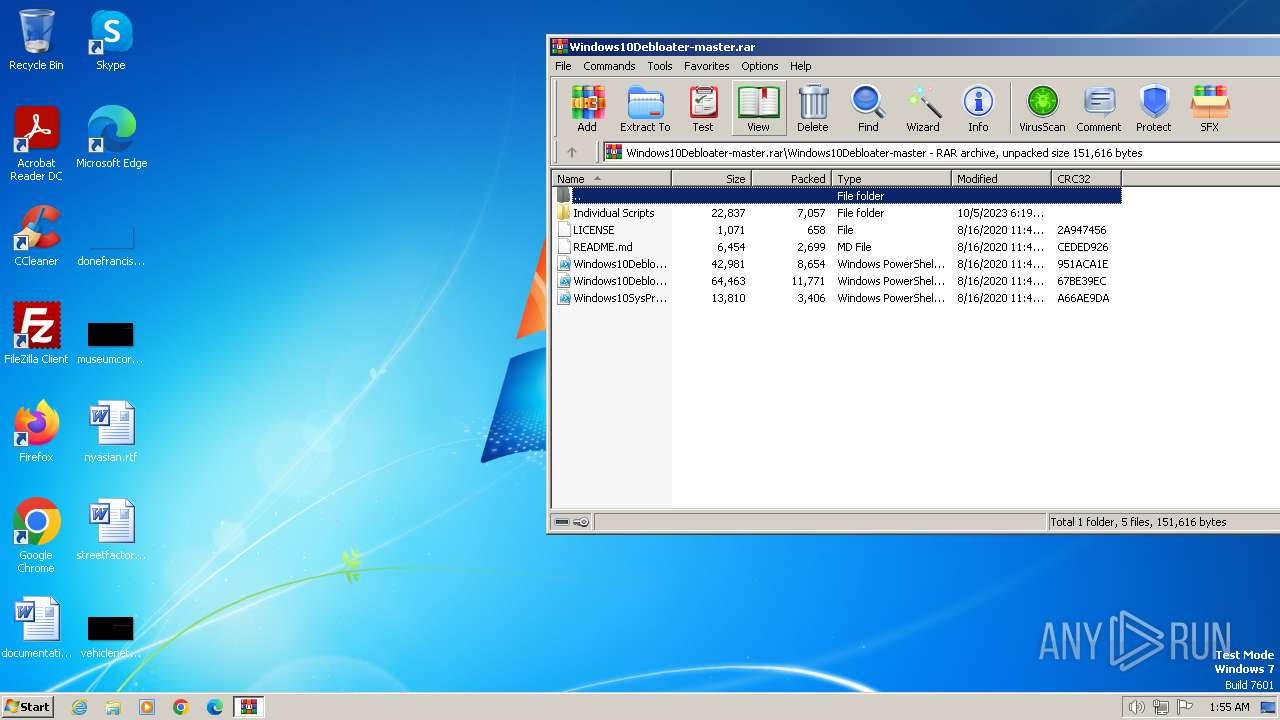
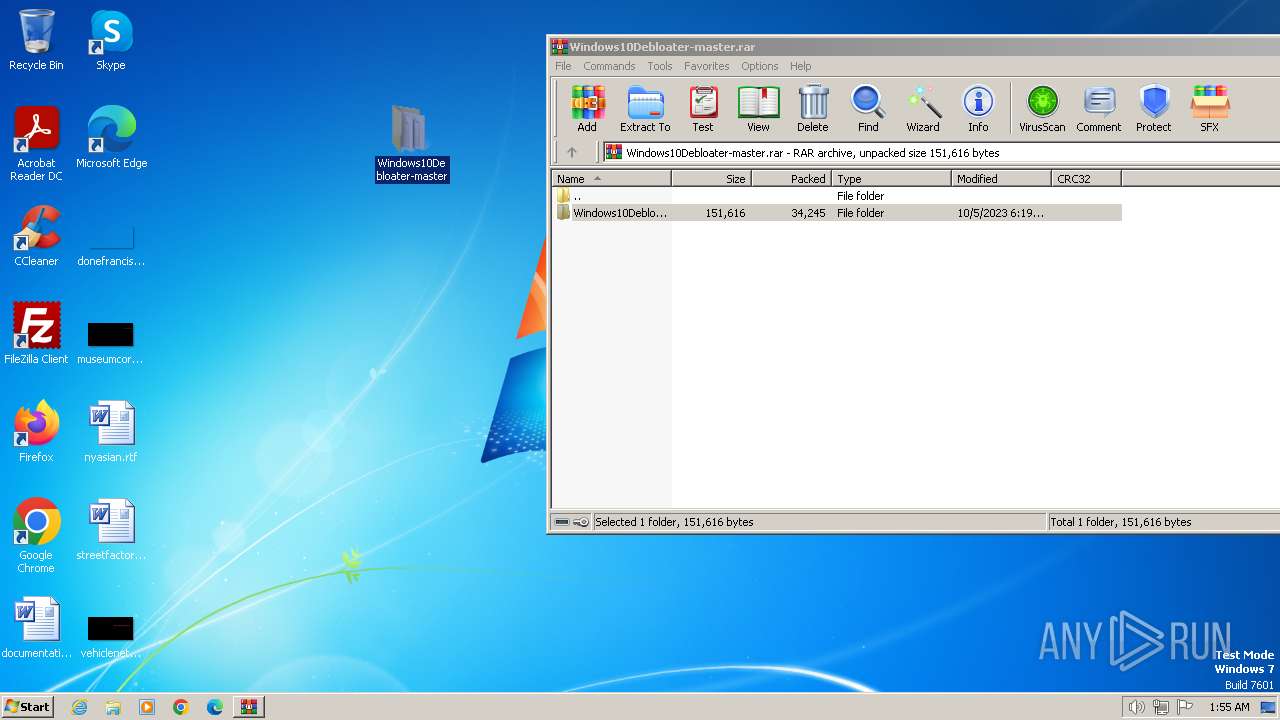
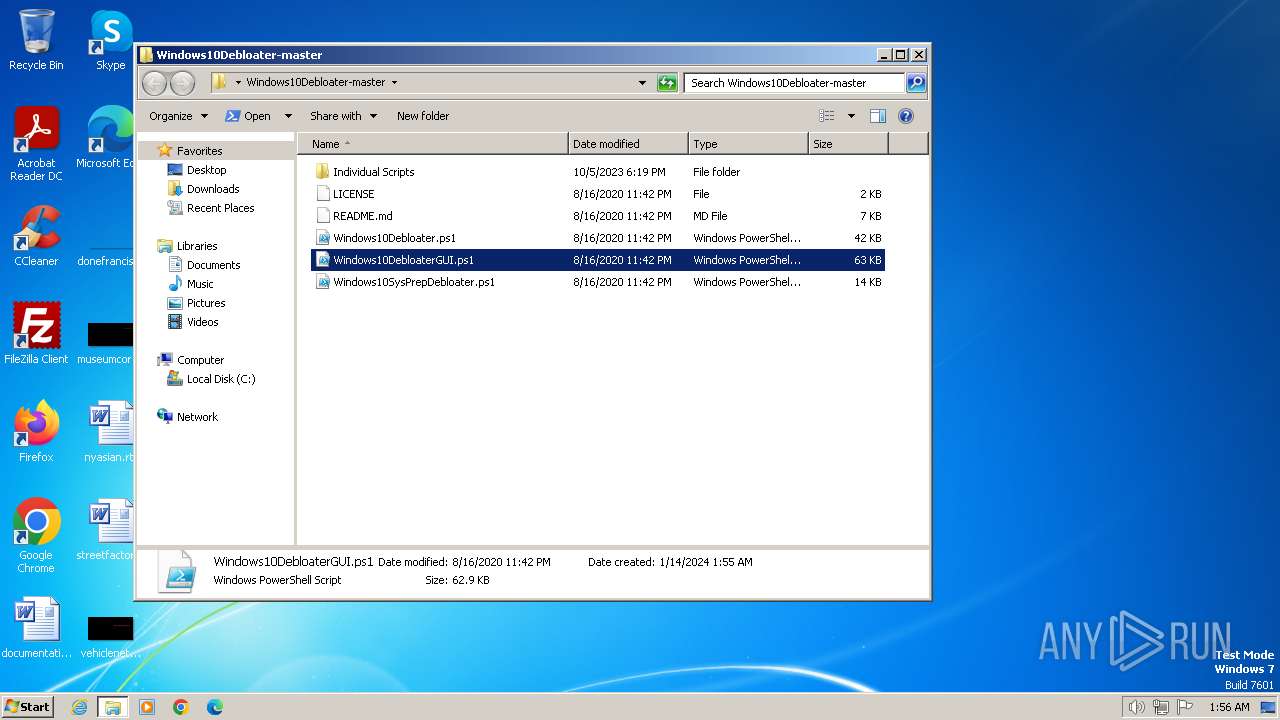
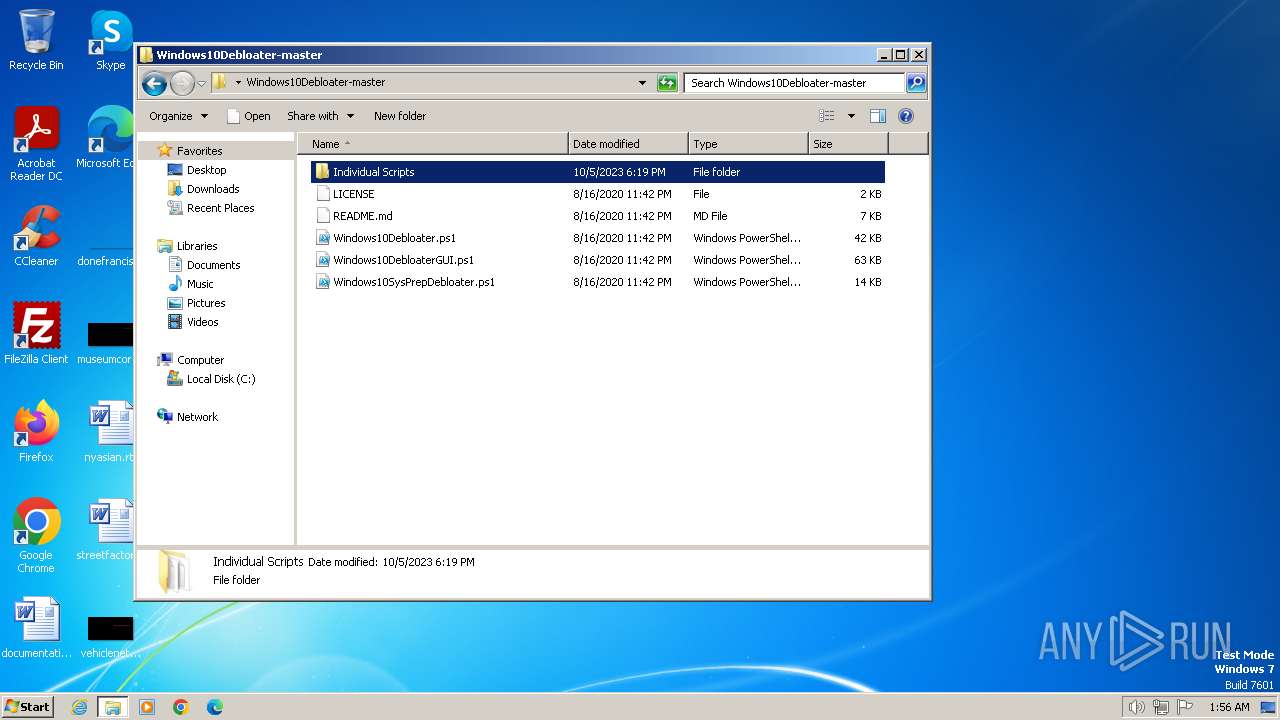
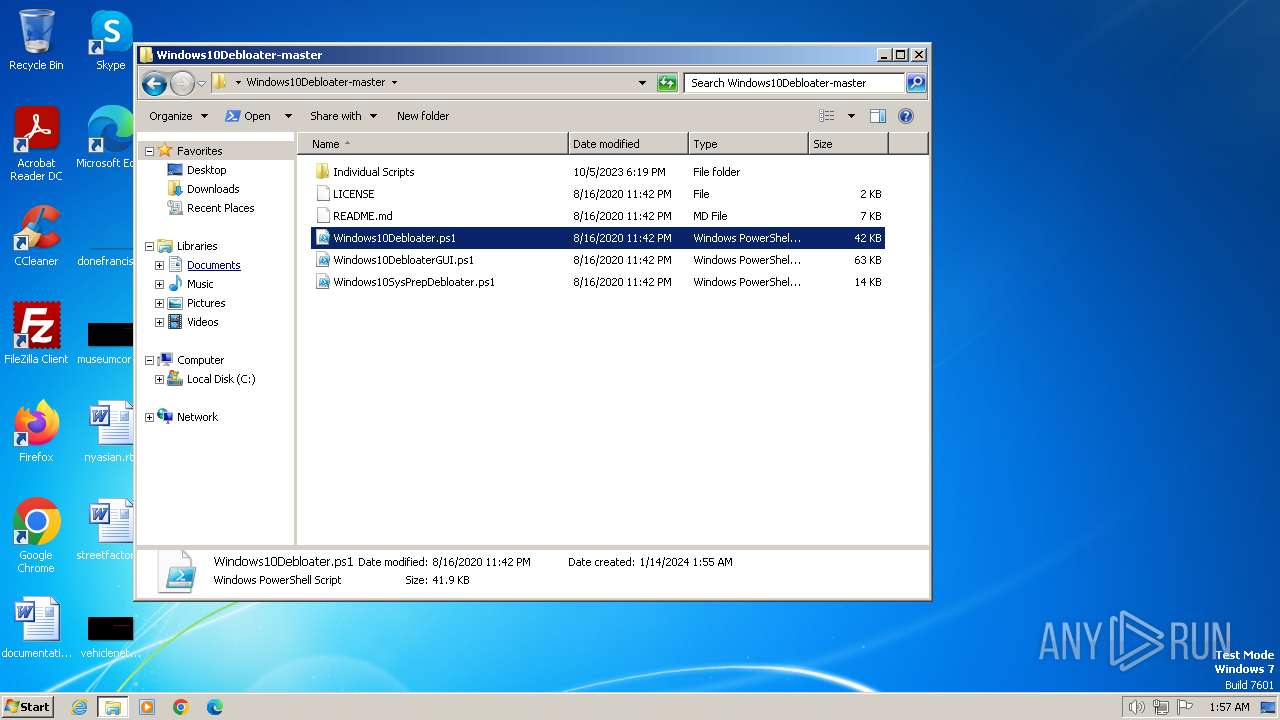
| 128 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Windows10Debloater-master.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
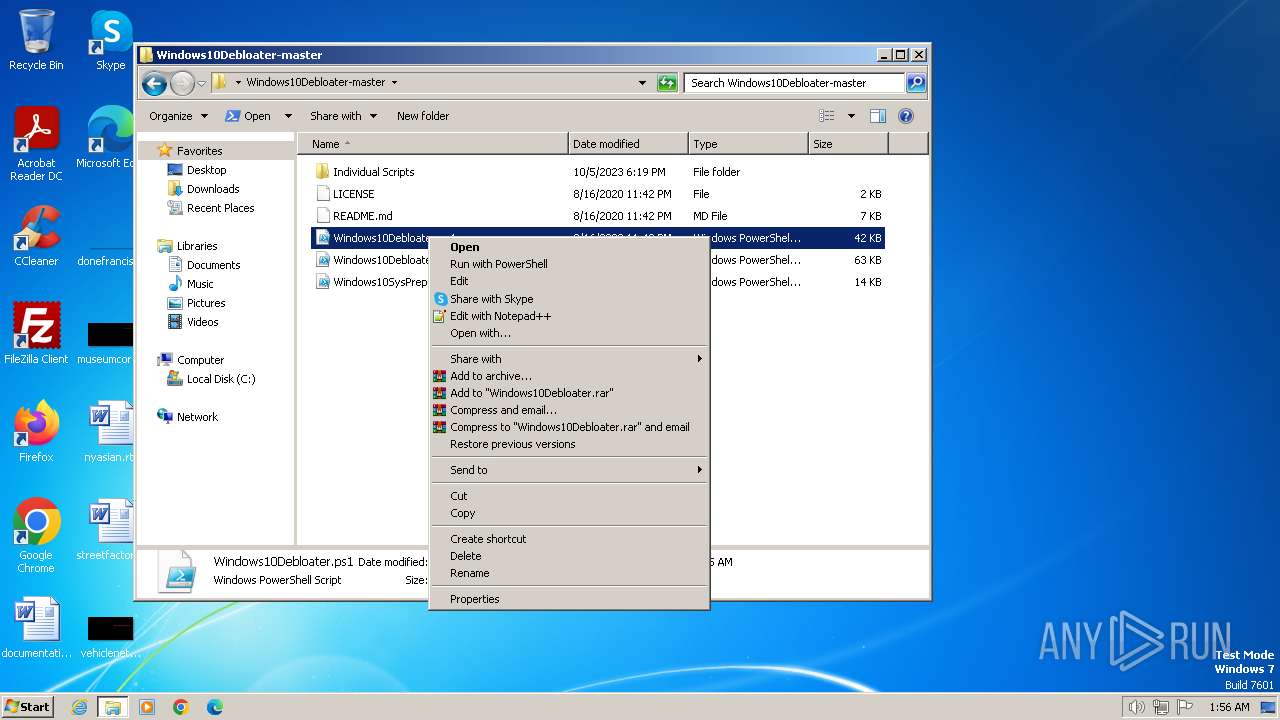
| 680 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" "-file" "C:\Users\admin\Desktop\Windows10Debloater-master\Windows10Debloater.ps1" "-Command" "if((Get-ExecutionPolicy ) -ne AllSigned) { Set-ExecutionPolicy -Scope Process Bypass }" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
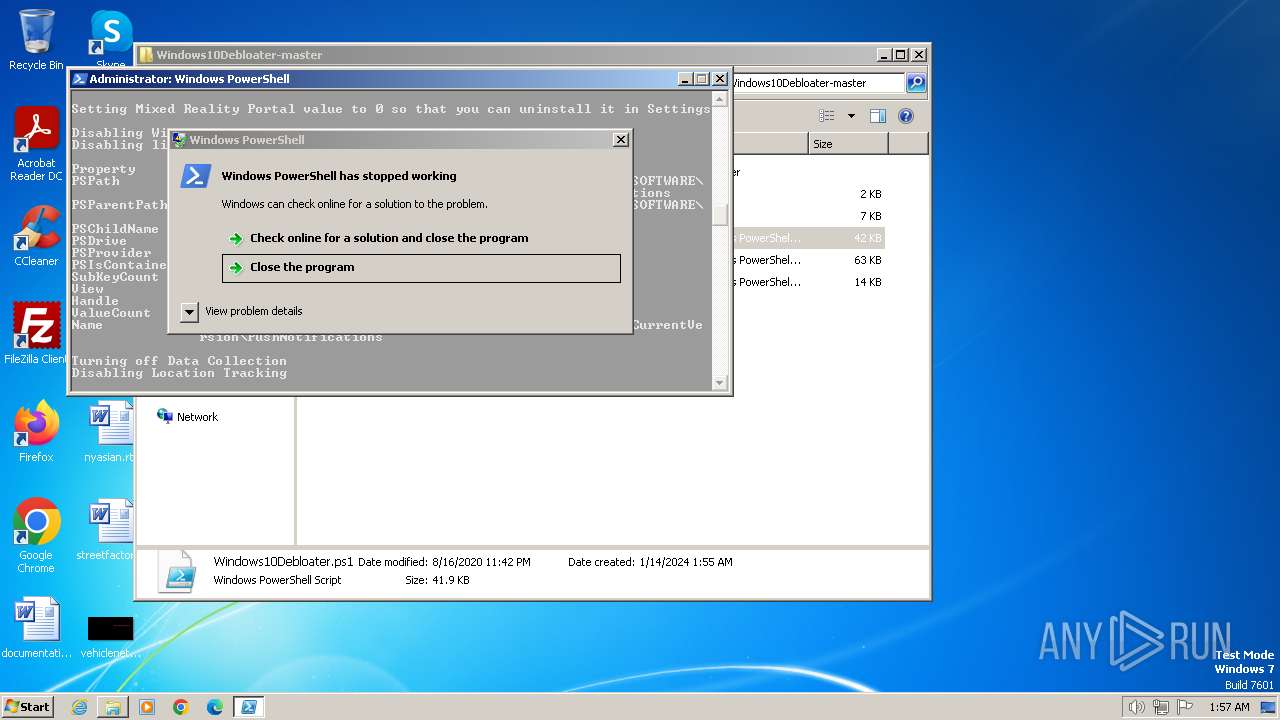
| 1220 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -NoProfile -ExecutionPolicy Bypass -File "C:\Users\admin\Desktop\Windows10Debloater-master\Windows10Debloater.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 3221225477 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
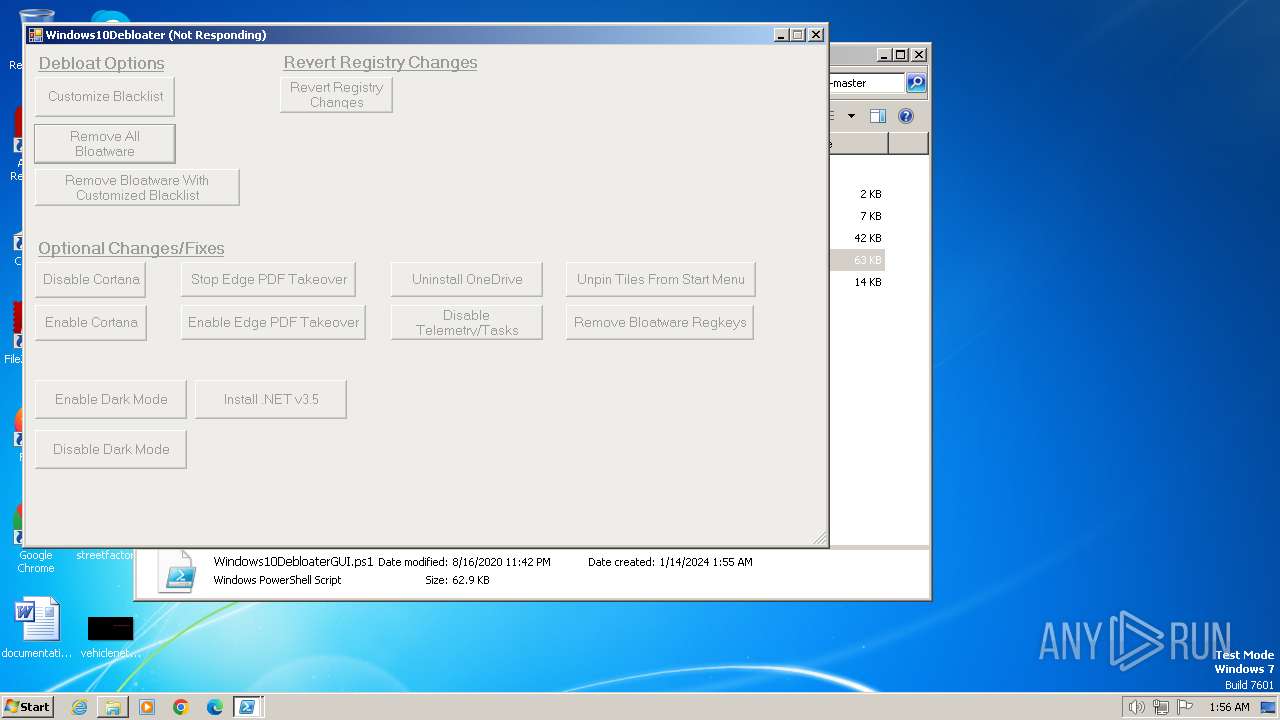
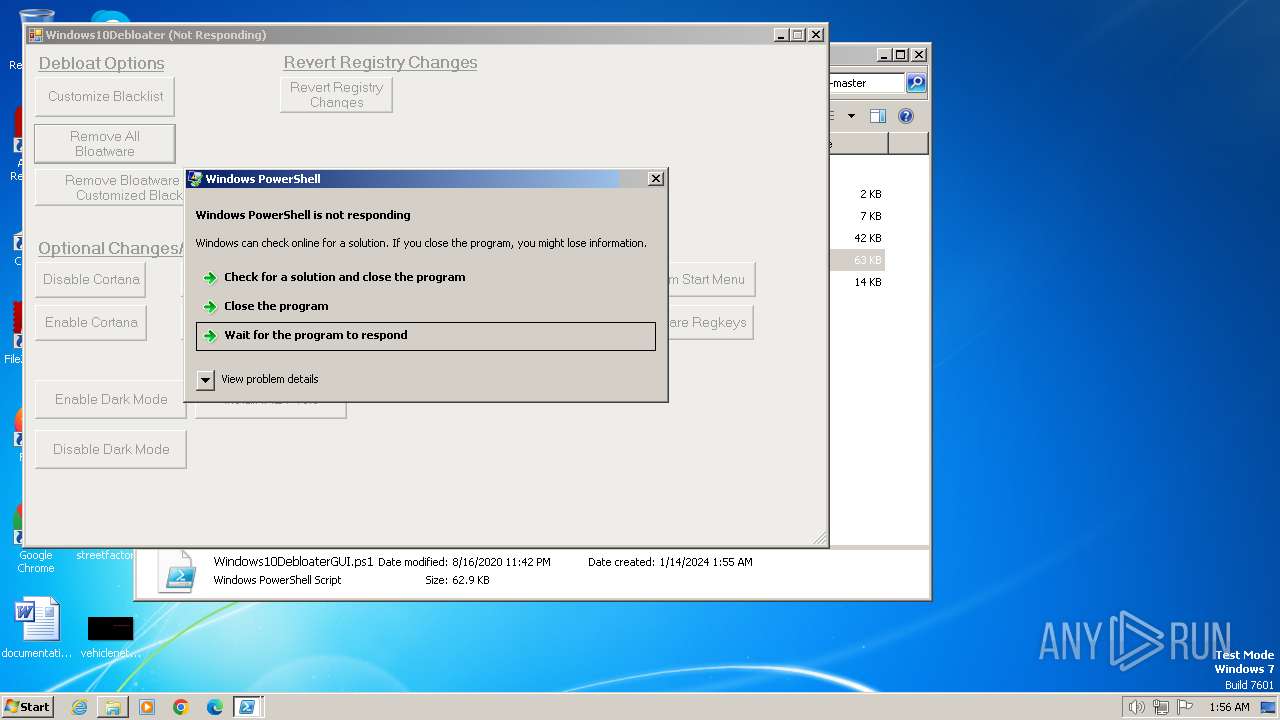
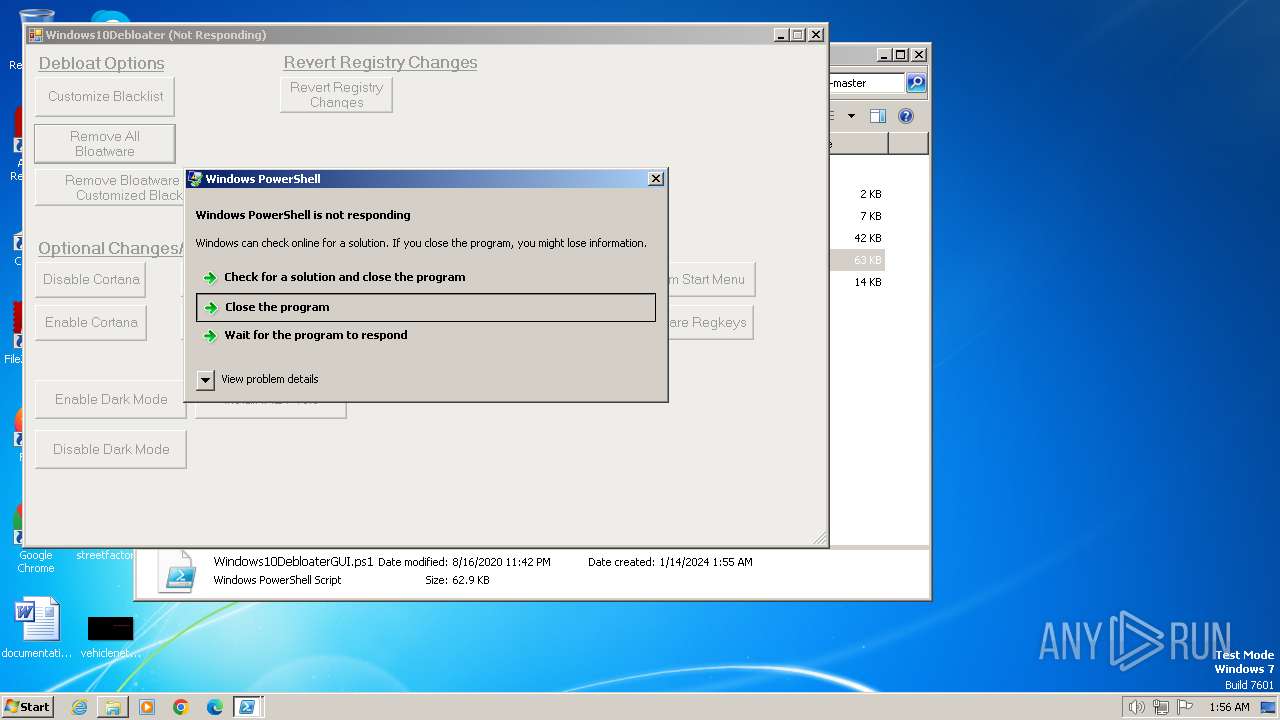
| 1504 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" "-file" "C:\Users\admin\Desktop\Windows10Debloater-master\Windows10DebloaterGUI.ps1" "-Command" "if((Get-ExecutionPolicy ) -ne AllSigned) { Set-ExecutionPolicy -Scope Process Bypass }" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 3489660927 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
Total events
5 649
Read events
5 450
Write events
199
Delete events
0
Modification events
| (PID) Process: | (128) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (128) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (128) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (128) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (128) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (128) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (128) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (128) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (128) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (128) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
Executable files
0
Suspicious files
17
Text files
18
Unknown types
0
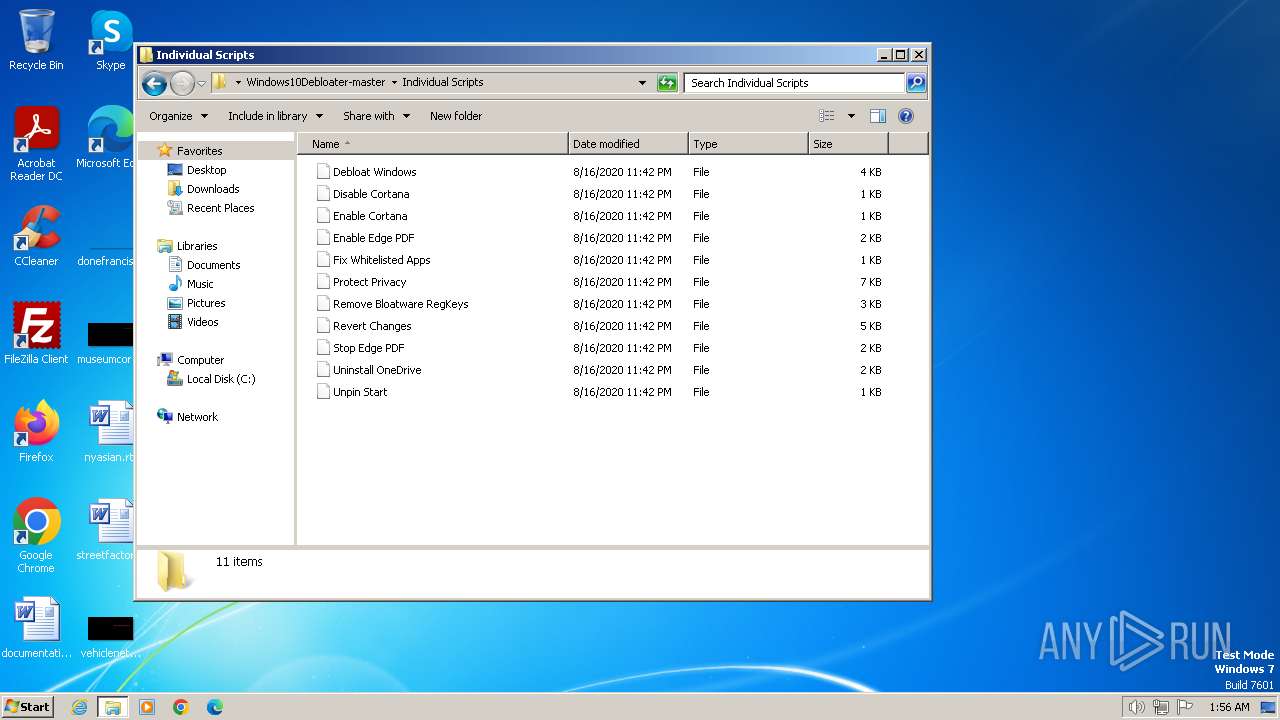
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
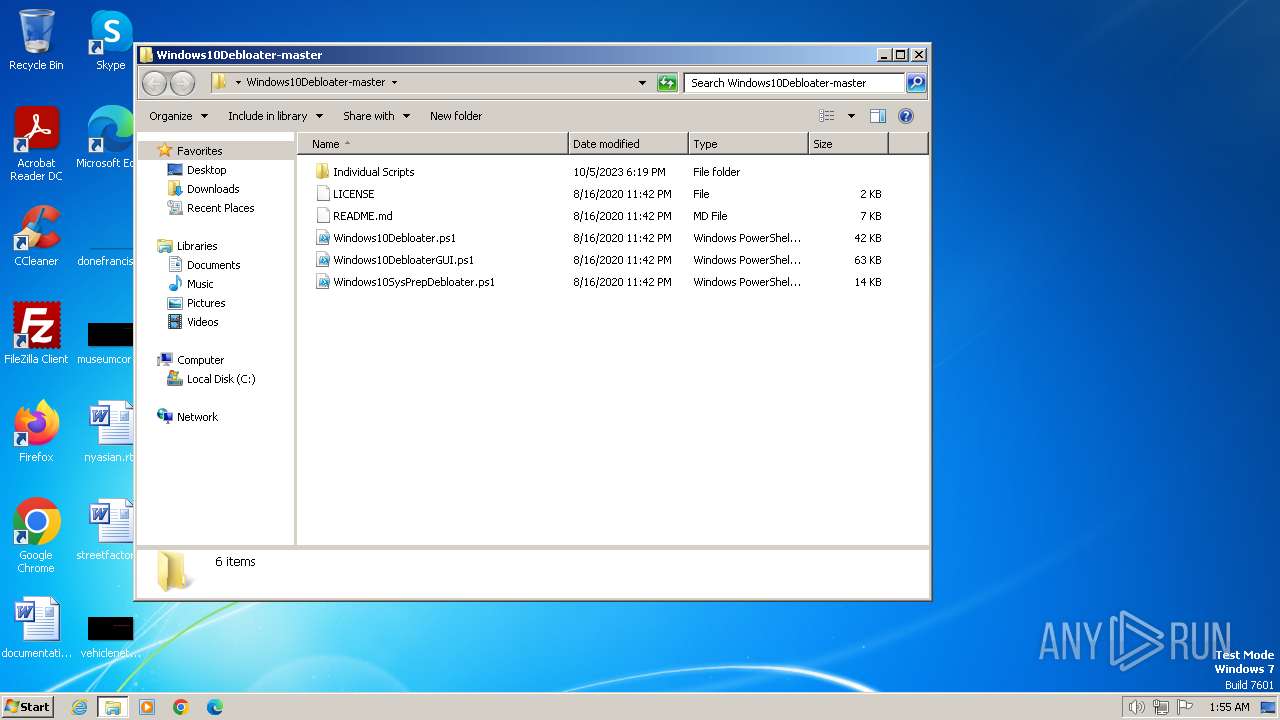
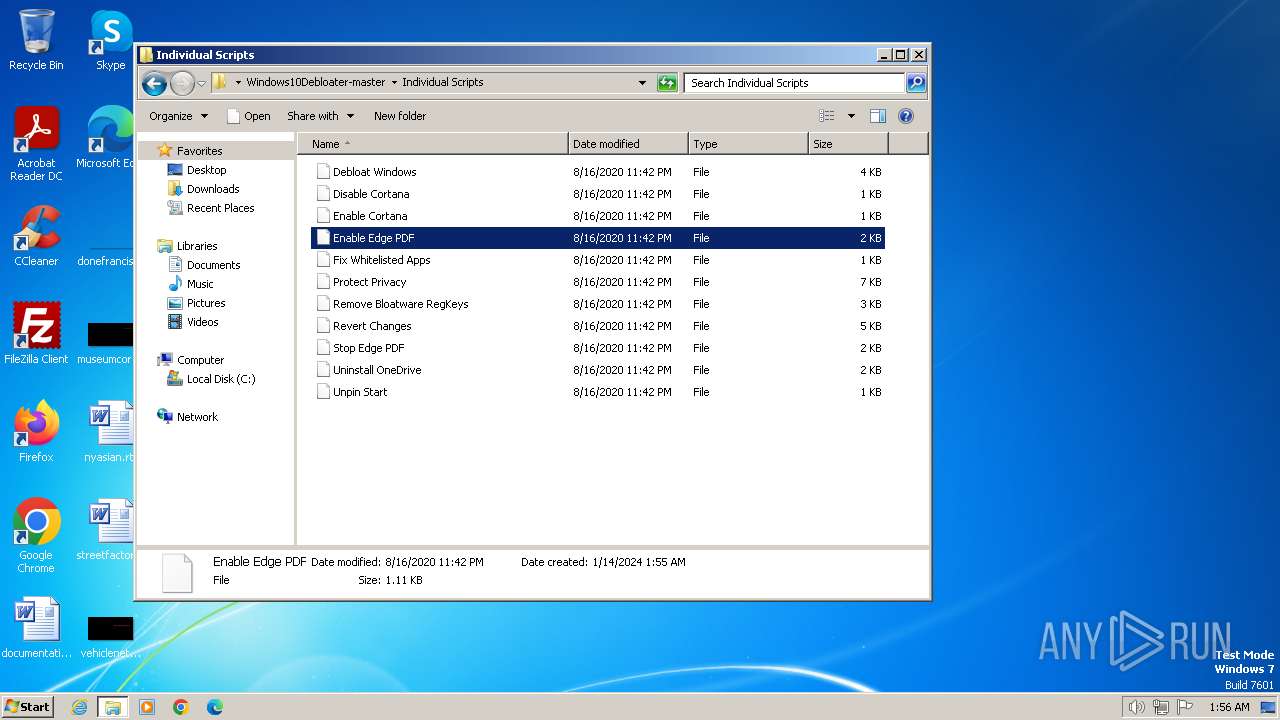
| 128 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa128.31126\Windows10Debloater-master\Individual Scripts\Enable Cortana | text | |
MD5:9C87D755EA8C3D89C465044A67C1D3F5 | SHA256:3A936C1812C16B8843B55A8E48458261438DA509738362827BE33B9FDB44A9E3 | |||
| 128 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa128.31126\Windows10Debloater-master\Individual Scripts\Debloat Windows | text | |
MD5:FE027363EDD3AA71C6A4AE0ECB7CEAAE | SHA256:2152BDD73176E7152A02B79170FE193E0F036B91373F8781937DF67247561DE0 | |||
| 128 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa128.31126\Windows10Debloater-master\Individual Scripts\Stop Edge PDF | text | |
MD5:09F3F884027577977C62455B0846322D | SHA256:02A5B62D5D10A47CD9F5FBCF703AC518B205AA29714CA5B970627829F6519D28 | |||
| 128 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa128.31126\Windows10Debloater-master\Individual Scripts\Protect Privacy | text | |
MD5:0204760E129C125D3B6432E3C55BFBCC | SHA256:3C1E5367AC277EEEDDDFC67B0C350900F6E60251779BB8D4F5C262C4019EC42F | |||
| 128 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa128.31126\Windows10Debloater-master\Individual Scripts\Disable Cortana | text | |
MD5:6323E777A8ADD8E0C94BF73B29C7E493 | SHA256:5F094AE62D81CD7B7A049D3193802CCF58CBDC738DF285C95FF5CBB73B4876D7 | |||
| 128 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa128.31126\Windows10Debloater-master\Individual Scripts\Unpin Start | text | |
MD5:2585B204E5E767E08DF2CE918F5557E2 | SHA256:613E3BEAB6C22759D15E8F6F796F4EC7E2709800CA49C552E8535A65FEA6705C | |||
| 1504 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:F500255BDC0DD45A0934243E38529D10 | SHA256:AD4304402753CEF71770C63692428001309617BDA00D87E229D197721D29496E | |||
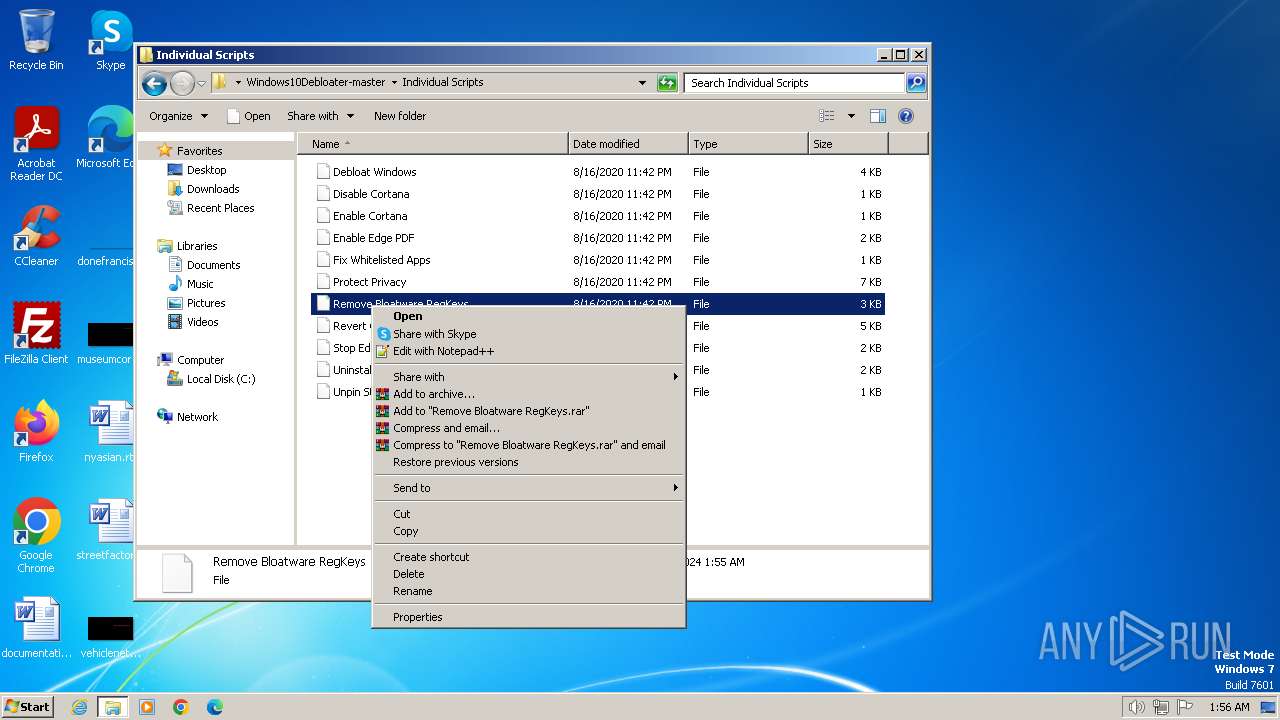
| 128 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa128.31126\Windows10Debloater-master\Individual Scripts\Remove Bloatware RegKeys | text | |
MD5:DBA98A6EEDA78832880BCE9452FB2524 | SHA256:6F04F74E2F2AAE8D8AE8413B514A719B9B8A68D7A1580B93D717A477F539C1D5 | |||
| 1504 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RFe50db.TMP | binary | |
MD5:0268C3470C936E6FBAC2945B9E1C2099 | SHA256:DF2AF58E8879B48826D8A418ED3B02CC8D484BCFC231C5B7A11BD153ED3998E9 | |||
| 128 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa128.31126\Windows10Debloater-master\Individual Scripts\Fix Whitelisted Apps | text | |
MD5:BEB720E264A818EC1C8523B6DE24D705 | SHA256:F9998BFB7DC3FDE2DF313E7E37D22CBEA956CFDD4938BC06D27752974E9C67B8 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |