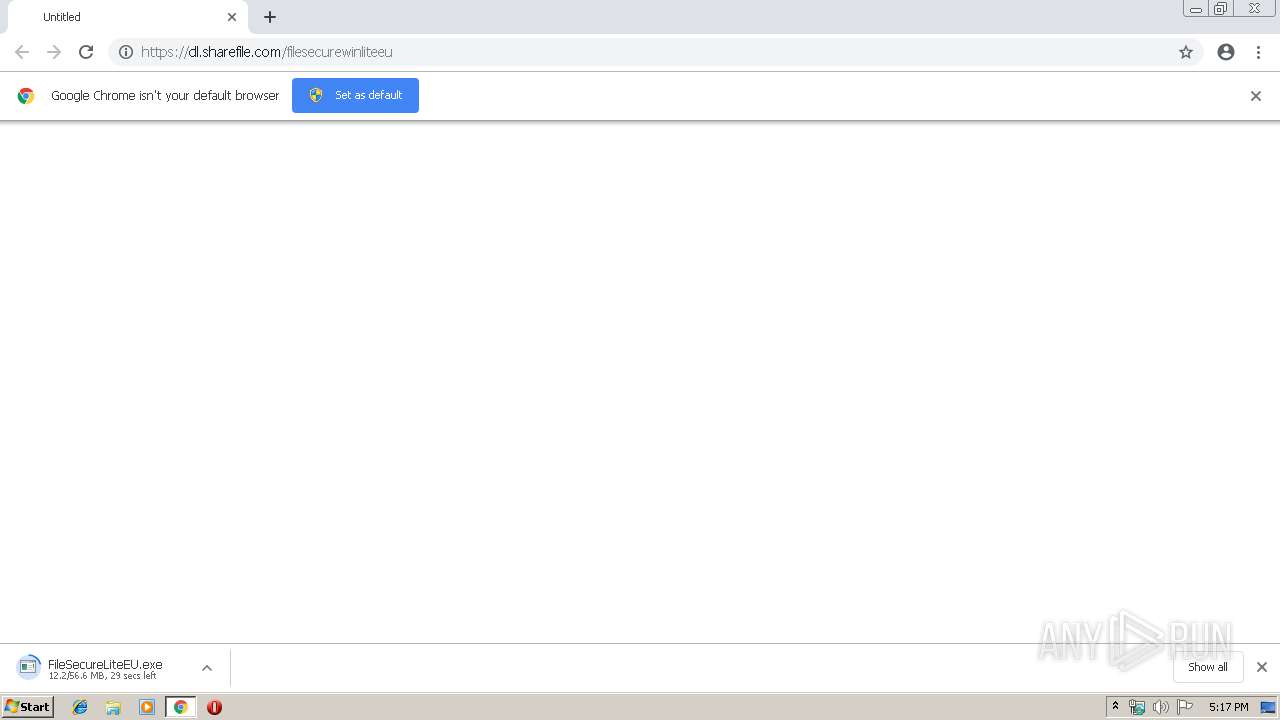
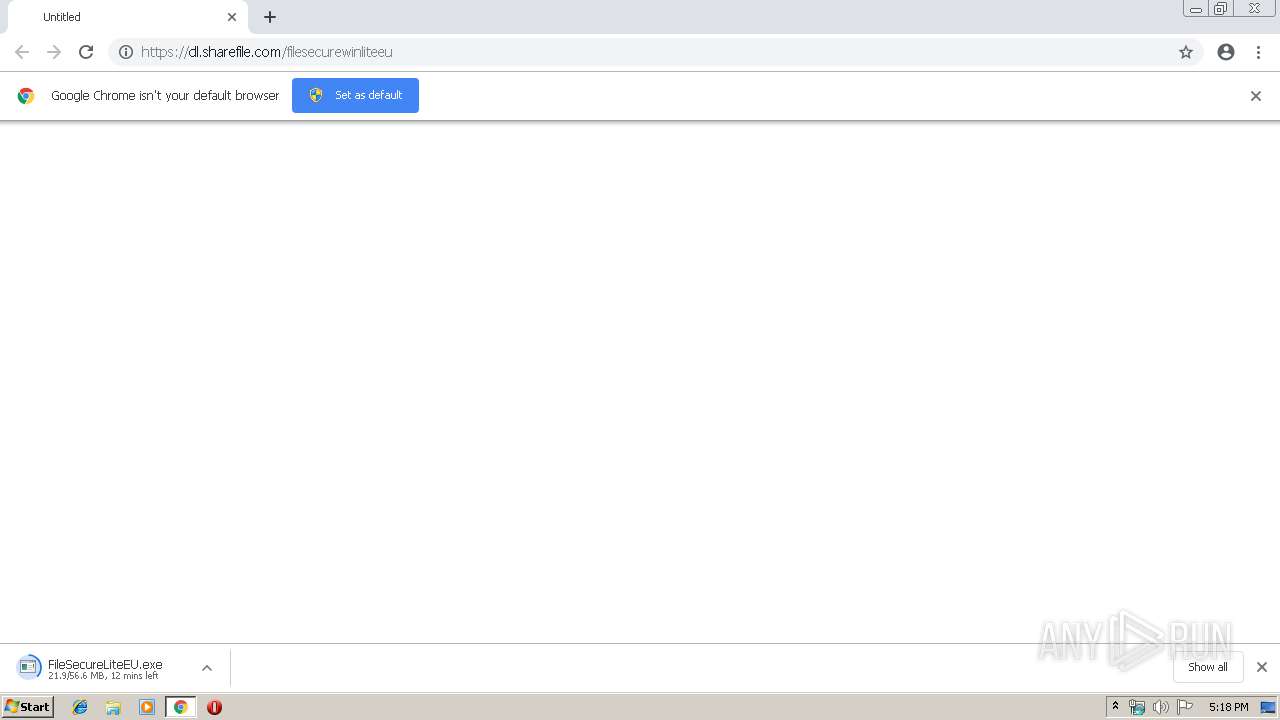
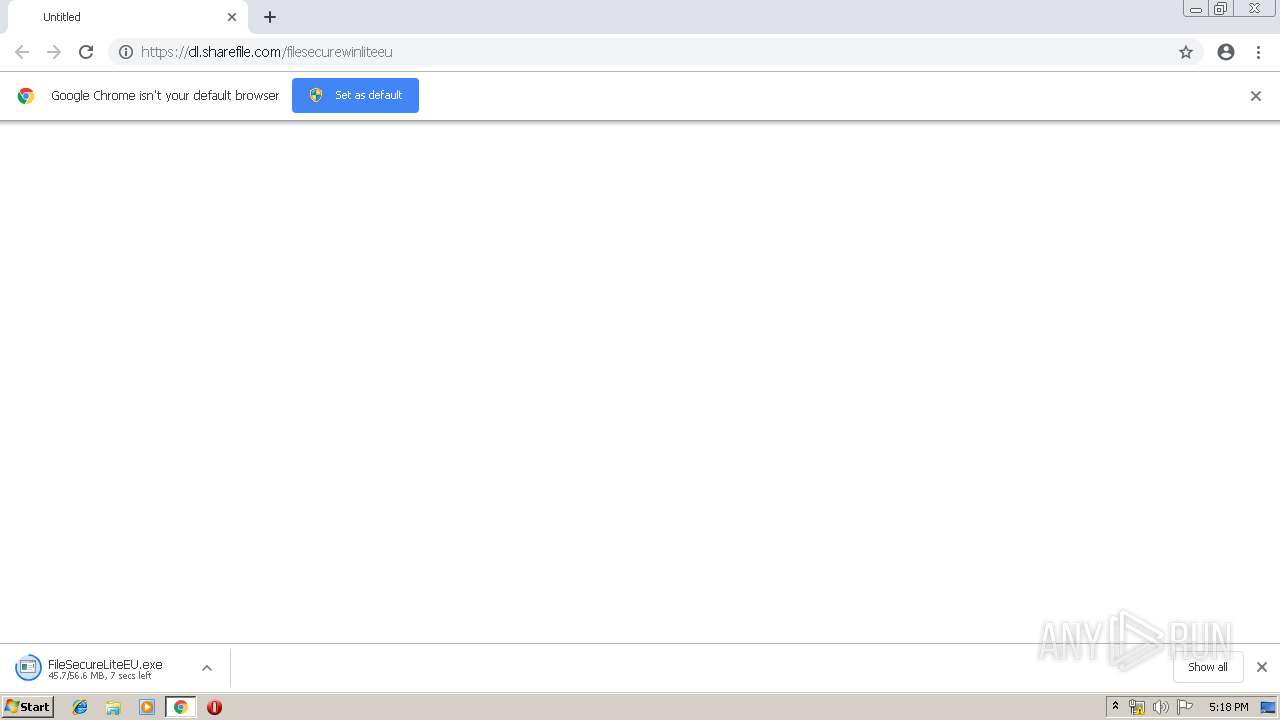
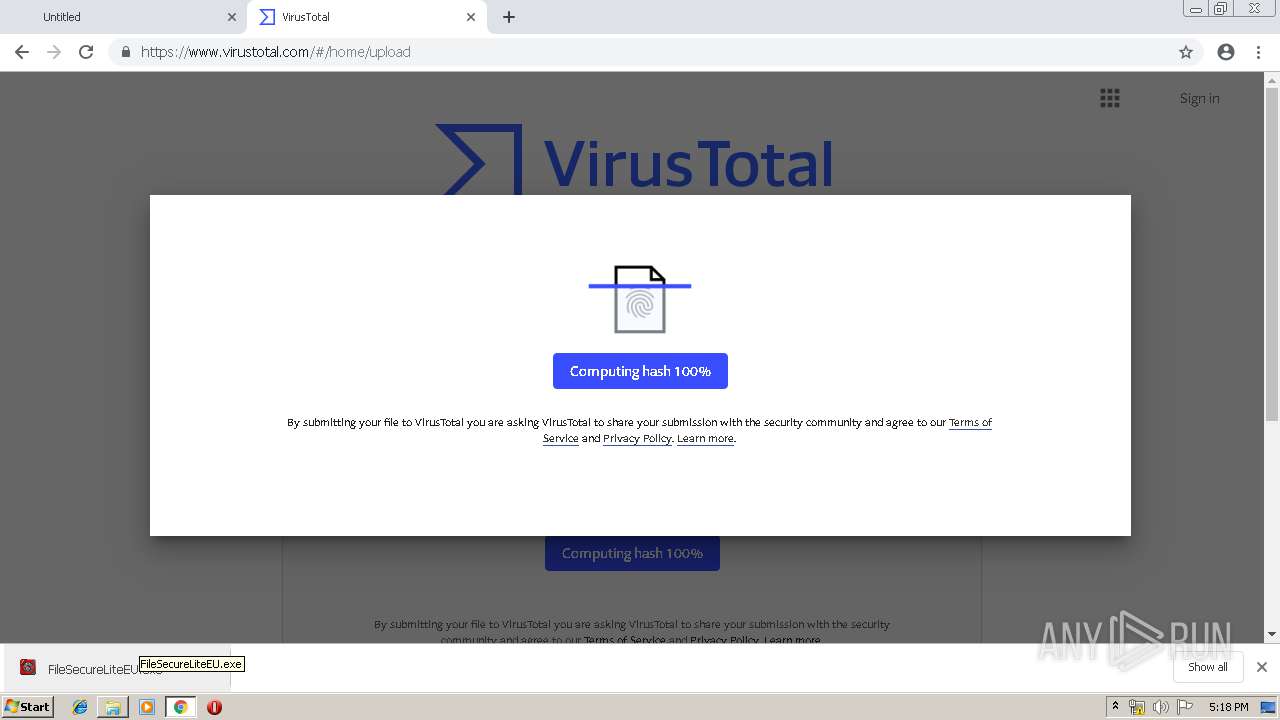
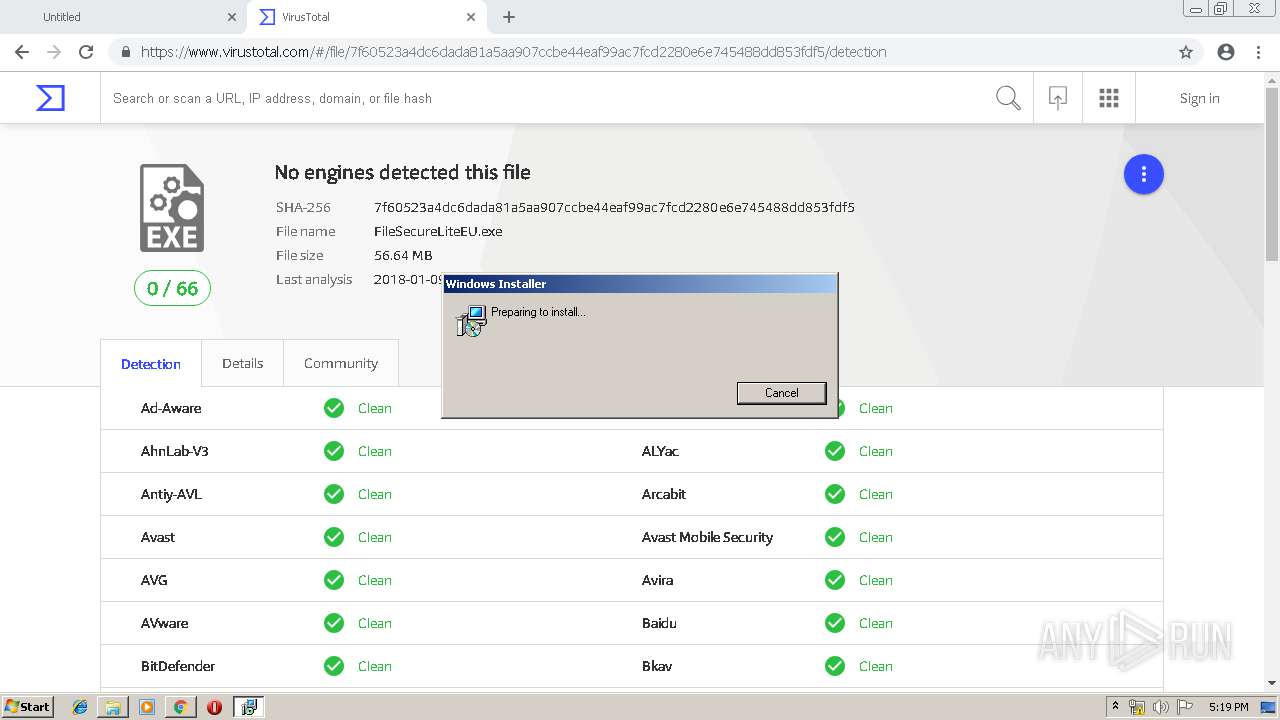
| URL: | https://dl.sharefile.com/filesecurewinliteeu |
| Full analysis: | https://app.any.run/tasks/da51852c-5e90-4984-9d2a-341621ffb848 |
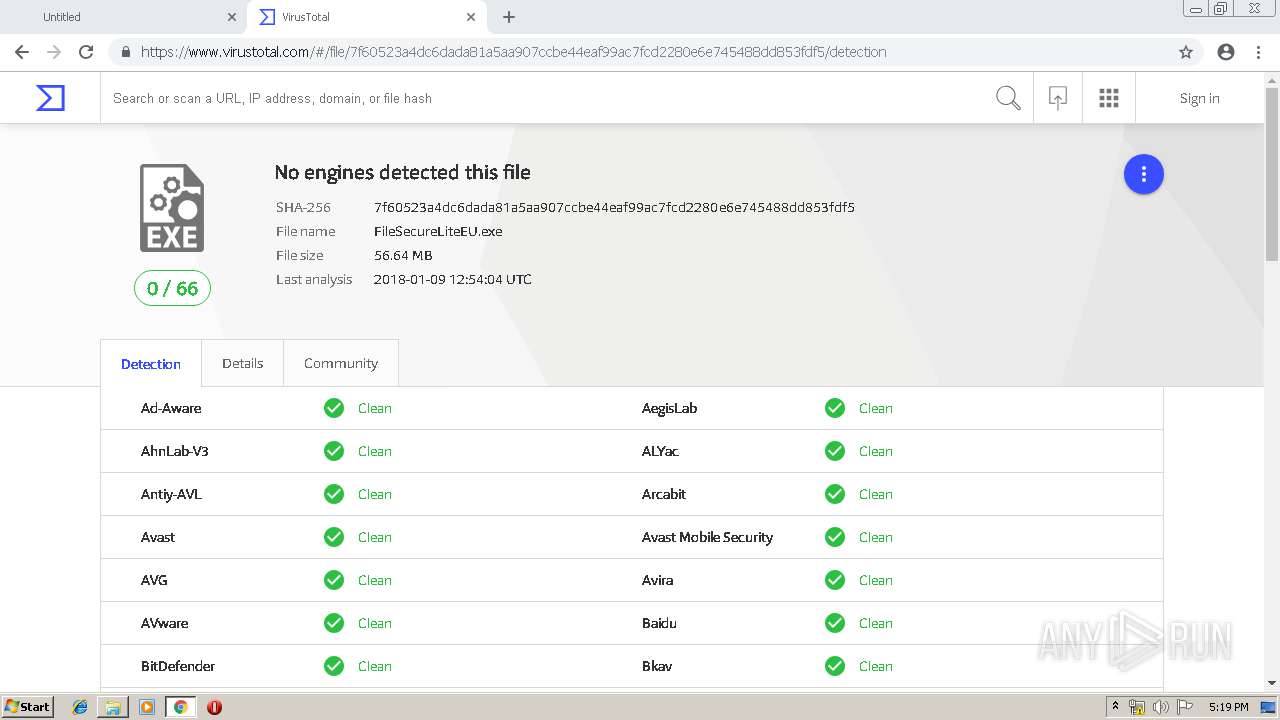
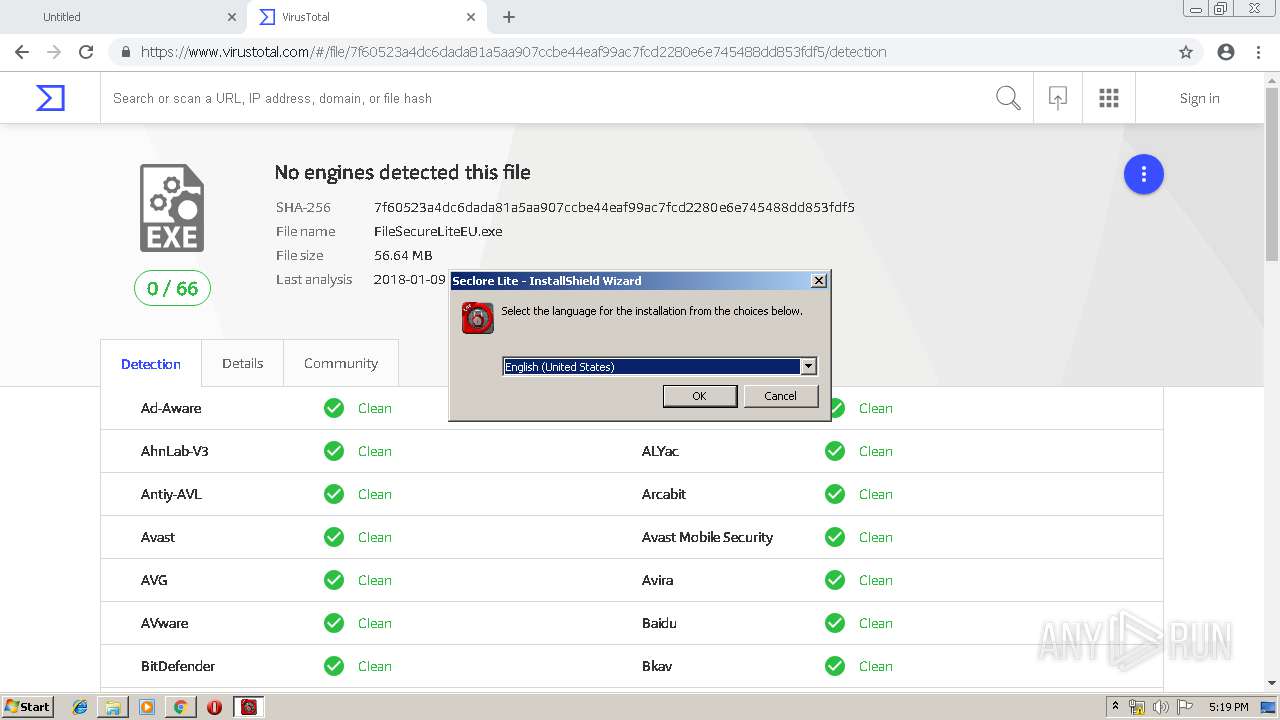
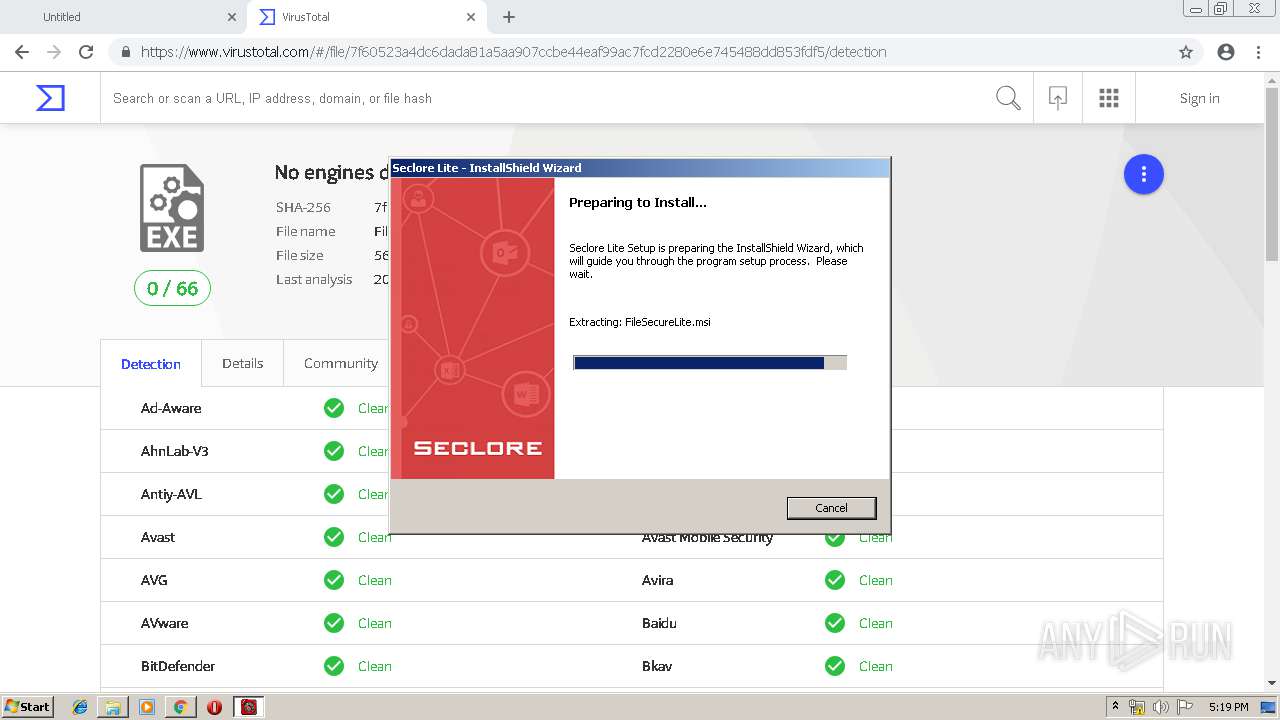
| Verdict: | Malicious activity |
| Analysis date: | March 21, 2019, 17:17:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
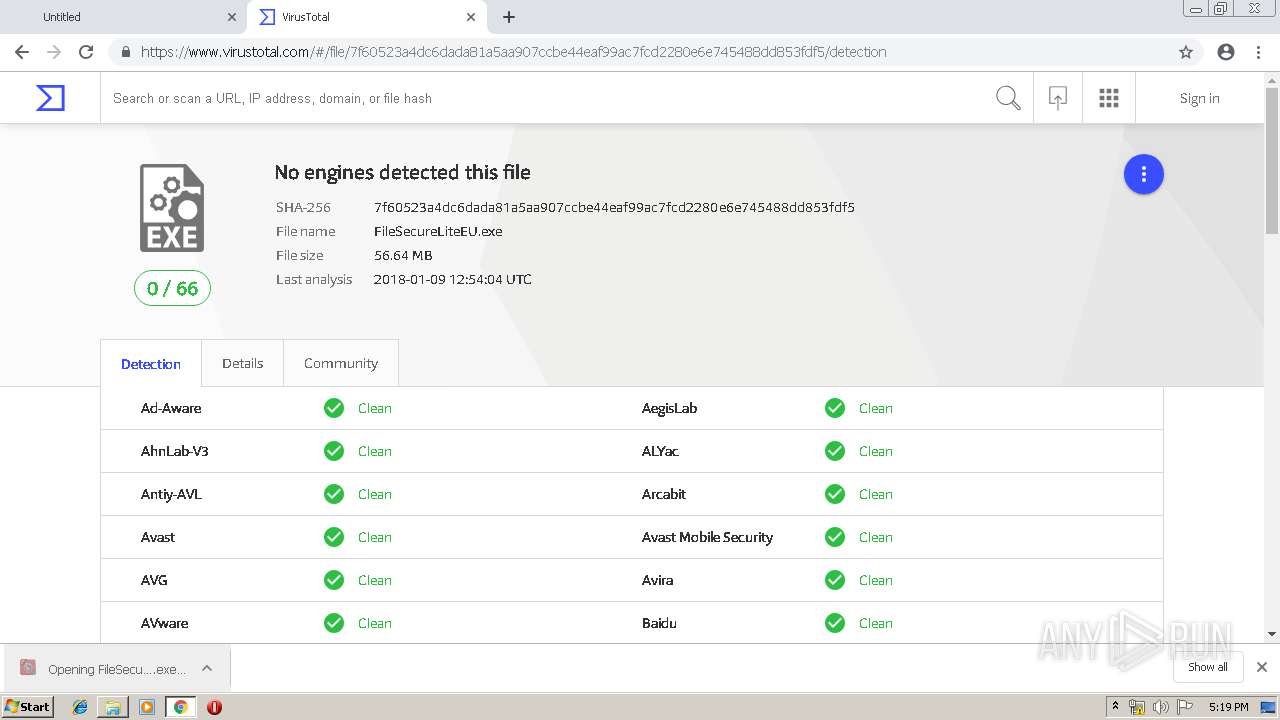
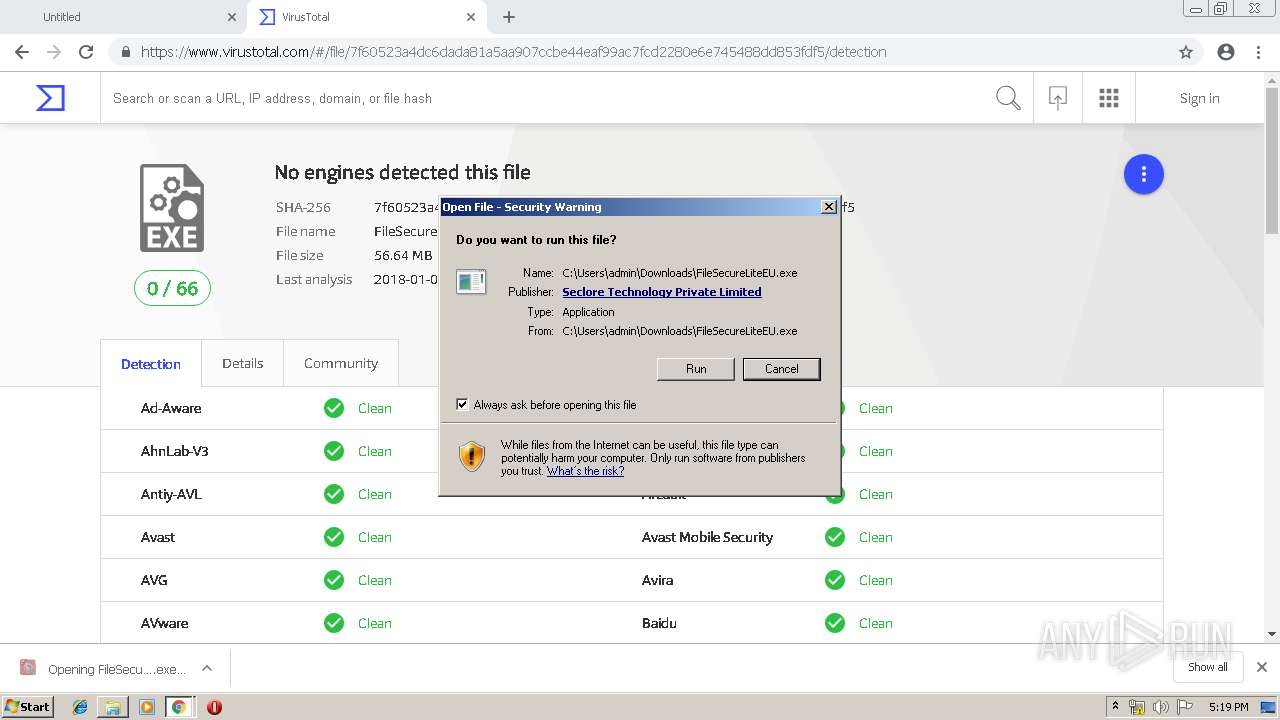
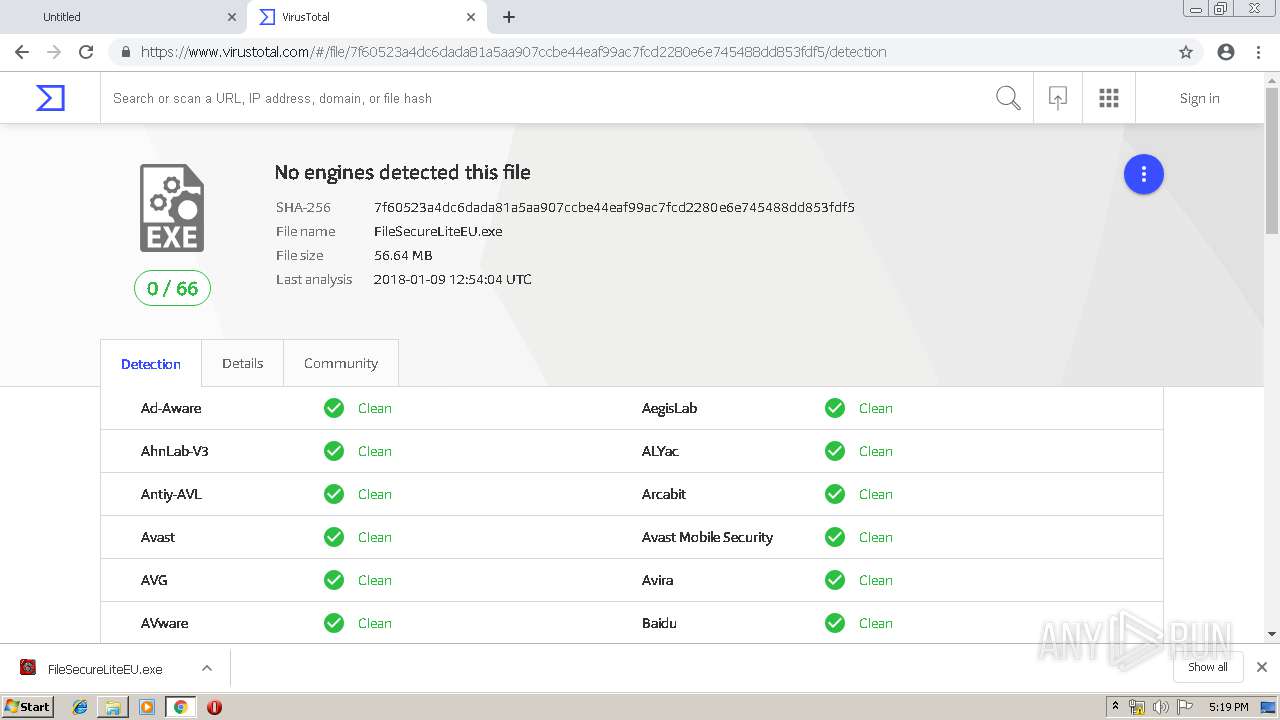
| MD5: | 7D87C1E31AC95FCA2E6F672CF4AAAD3C |
| SHA1: | 58CB7AE9A606AEC5DA666ADDAE295A6E0F9F339A |
| SHA256: | 874D0949D56285AE6C4D7F31218CAF4AE00CFCE47566BB786B3886E06DE7E016 |
| SSDEEP: | 3:N8Ru+7M0sX3Mug:2x0X8ug |
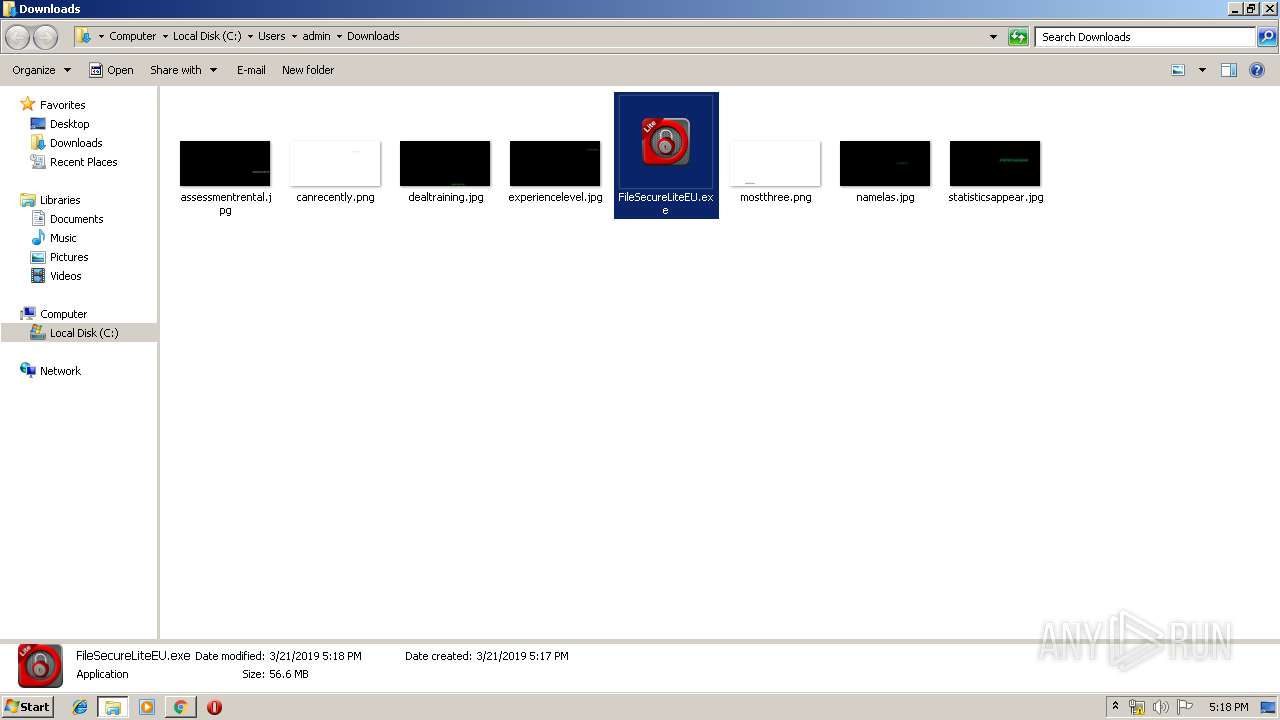
MALICIOUS
Application was dropped or rewritten from another process
- FileSecureLiteEU.exe (PID: 2960)
- FSLiteUpdateLauncher.exe (PID: 2420)
- FSLiteUpdater.exe (PID: 2036)
- FSLiteUpdateLauncher.exe (PID: 1500)
- Troubleshooter.exe (PID: 2700)
- FSLiteTray.exe (PID: 2952)
- FileSecureAssist.exe (PID: 1476)
- Troubleshooter.exe (PID: 2948)
Registers / Runs the DLL via REGSVR32.EXE
- MsiExec.exe (PID: 2428)
- Troubleshooter.exe (PID: 2700)
Loads dropped or rewritten executable
- regsvr32.exe (PID: 3592)
- Troubleshooter.exe (PID: 2700)
- FSLiteUpdateLauncher.exe (PID: 2420)
- regsvr32.exe (PID: 788)
- FSLiteTray.exe (PID: 2952)
- FSLiteUpdater.exe (PID: 2036)
- regsvr32.exe (PID: 2892)
- regsvr32.exe (PID: 3452)
- Troubleshooter.exe (PID: 2948)
- regsvr32.exe (PID: 2832)
- FileSecureAssist.exe (PID: 1476)
- FSLiteUpdateLauncher.exe (PID: 1500)
- regsvr32.exe (PID: 2364)
- regsvr32.exe (PID: 1476)
- regsvr32.exe (PID: 3208)
- regsvr32.exe (PID: 1932)
- regsvr32.exe (PID: 2392)
- regsvr32.exe (PID: 1548)
- regsvr32.exe (PID: 3216)
- regsvr32.exe (PID: 1164)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 1332)
- MSIEXEC.EXE (PID: 2692)
- FileSecureLite.exe (PID: 2156)
- FSLiteUpdateLauncher.exe (PID: 2420)
- msiexec.exe (PID: 3564)
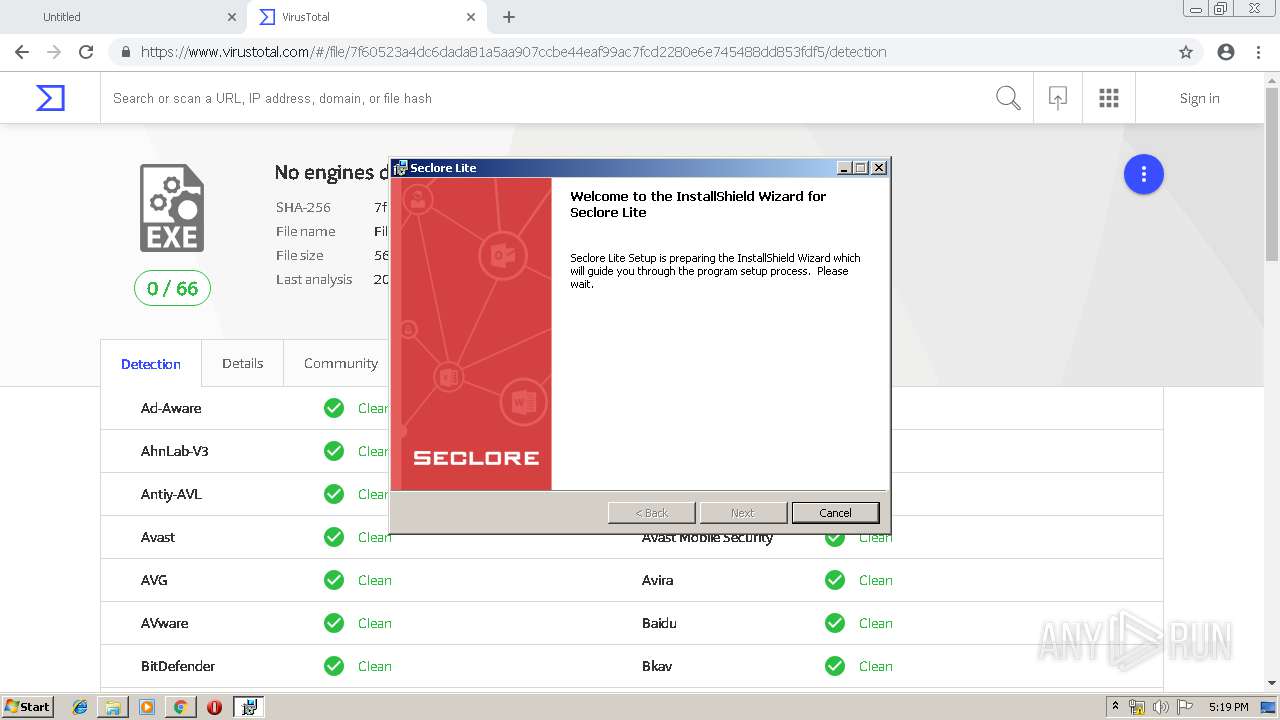
Starts Microsoft Installer
- FileSecureLite.exe (PID: 2156)
Creates files in the user directory
- MsiExec.exe (PID: 3248)
- msiexec.exe (PID: 3564)
- MsiExec.exe (PID: 2428)
- regsvr32.exe (PID: 2832)
- regsvr32.exe (PID: 788)
- FSLiteUpdateLauncher.exe (PID: 2420)
- Troubleshooter.exe (PID: 2700)
- FSLiteUpdater.exe (PID: 2036)
- Troubleshooter.exe (PID: 2948)
- FileSecureAssist.exe (PID: 1476)
- FSLiteUpdateLauncher.exe (PID: 1500)
- regsvr32.exe (PID: 3452)
- FSLiteTray.exe (PID: 2952)
- regsvr32.exe (PID: 2892)
Modifies the open verb of a shell class
- MsiExec.exe (PID: 2428)
- Troubleshooter.exe (PID: 2700)
Changes the autorun value in the registry
- MsiExec.exe (PID: 2428)
Creates COM task schedule object
- regsvr32.exe (PID: 788)
- regsvr32.exe (PID: 2832)
- regsvr32.exe (PID: 1476)
- regsvr32.exe (PID: 1164)
- regsvr32.exe (PID: 3592)
- MsiExec.exe (PID: 2428)
- regsvr32.exe (PID: 3788)
- Troubleshooter.exe (PID: 2700)
- regsvr32.exe (PID: 1548)
- regsvr32.exe (PID: 3452)
- regsvr32.exe (PID: 2364)
- regsvr32.exe (PID: 2892)
- regsvr32.exe (PID: 3208)
Starts itself from another location
- FSLiteUpdateLauncher.exe (PID: 2420)
Application launched itself
- Troubleshooter.exe (PID: 2700)
Changes IE settings (feature browser emulation)
- Troubleshooter.exe (PID: 2700)
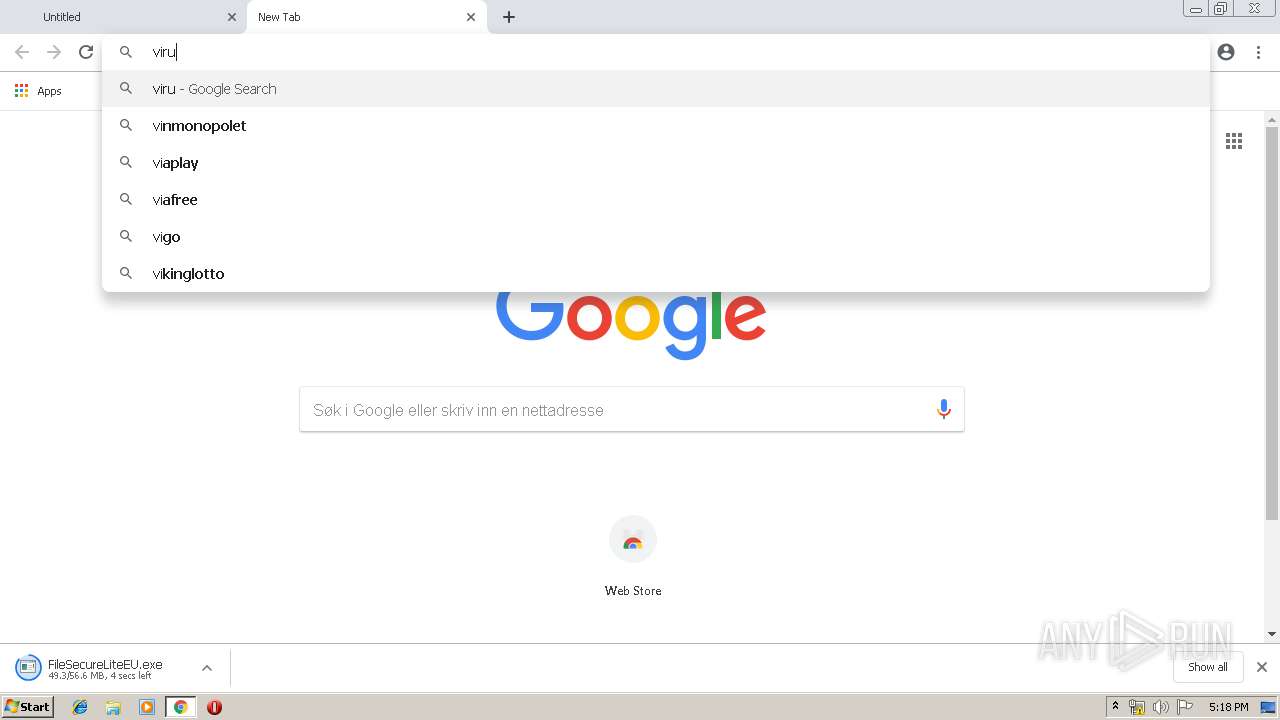
Modifies files in Chrome extension folder
- chrome.exe (PID: 1332)
INFO
Reads settings of System Certificates
- chrome.exe (PID: 3324)
- MsiExec.exe (PID: 2428)
Application launched itself
- chrome.exe (PID: 1332)
- msiexec.exe (PID: 3564)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 3248)
- MsiExec.exe (PID: 2428)
Searches for installed software
- msiexec.exe (PID: 3564)
Low-level read access rights to disk partition
- vssvc.exe (PID: 1624)
Adds / modifies Windows certificates
- DrvInst.exe (PID: 2172)
Changes settings of System certificates
- DrvInst.exe (PID: 2172)
Creates a software uninstall entry
- msiexec.exe (PID: 3564)
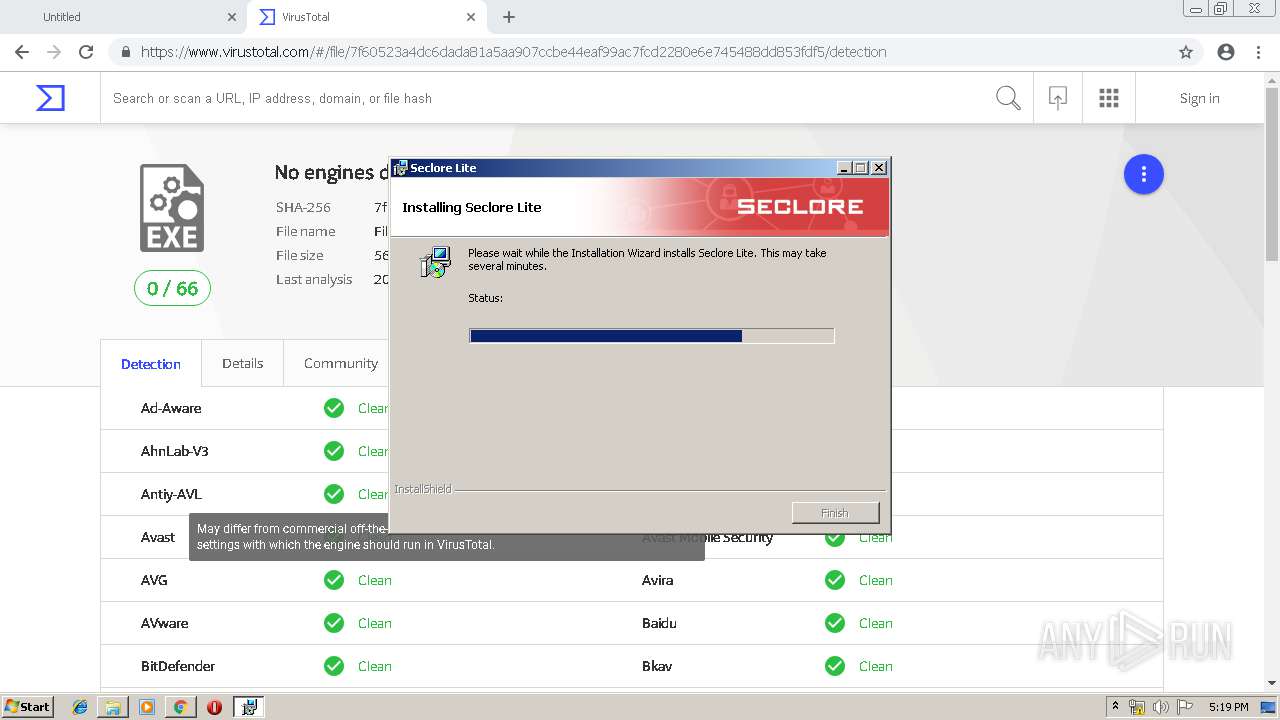
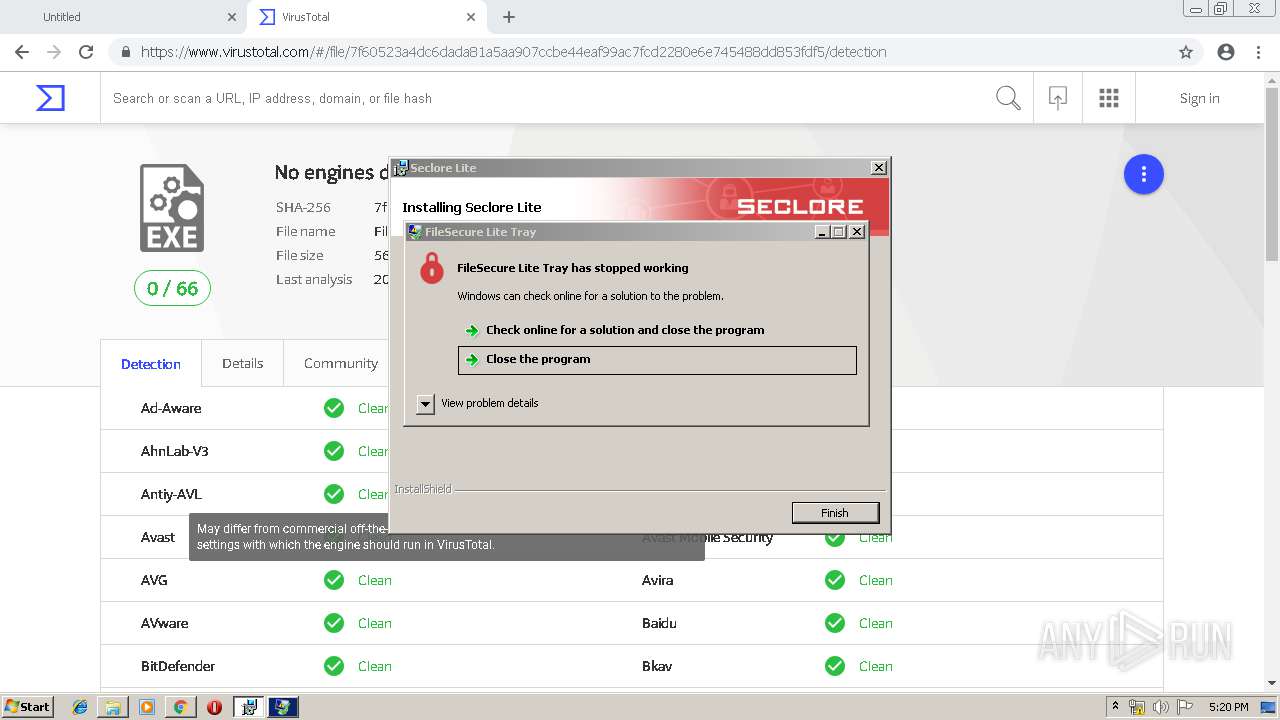
Application was crashed
- FSLiteTray.exe (PID: 2952)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
87
Monitored processes
53
Malicious processes
5
Suspicious processes
8
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 396 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=976,10472020817386206667,17024858077240079286,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5121850753527466732 --mojo-platform-channel-handle=4416 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 788 | regsvr32.exe /s "C:\Users\admin\AppData\Local\Seclore\FileSecure\FileSecure Lite\FSLiteShellExt.dll" | C:\Windows\system32\regsvr32.exe | — | MsiExec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1164 | regsvr32 /s /n /i:user "C:\Users\admin\AppData\Local\Seclore\FileSecure\FileSecure Lite\FSWindowTracker.dll" | C:\Windows\system32\regsvr32.exe | — | MsiExec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1332 | "C:\Program Files\Google\Chrome\Application\chrome.exe" https://dl.sharefile.com/filesecurewinliteeu | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1428 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=976,10472020817386206667,17024858077240079286,131072 --enable-features=PasswordImport --service-pipe-token=14603170214047455772 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14603170214047455772 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2120 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1476 | regsvr32.exe /s "C:\Users\admin\AppData\Local\Seclore\FileSecure\FileSecure Lite\FSIconHandler.dll" | C:\Windows\system32\regsvr32.exe | — | MsiExec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1476 | "C:\Users\admin\AppData\Local\Seclore\FileSecure\FileSecure Lite\FileSecureAssist.exe" | C:\Users\admin\AppData\Local\Seclore\FileSecure\FileSecure Lite\FileSecureAssist.exe | — | Troubleshooter.exe | |||||||||||
User: admin Company: Seclore Technology Pvt. Ltd. Integrity Level: MEDIUM Exit code: 0 Version: 3.1.0.0 Modules
| |||||||||||||||
| 1500 | "C:\Users\admin\AppData\Local\Seclore\FileSecure\FileSecure Lite\FSLiteUpdateLauncher.exe" | C:\Users\admin\AppData\Local\Seclore\FileSecure\FileSecure Lite\FSLiteUpdateLauncher.exe | — | Troubleshooter.exe | |||||||||||
User: admin Company: Seclore Technology Pvt. Ltd. Integrity Level: MEDIUM Description: FileSecure Lite Upgrader Exit code: 1 Version: 3.1.0.0 Modules
| |||||||||||||||
| 1528 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=976,10472020817386206667,17024858077240079286,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=16103353695917792324 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16103353695917792324 --renderer-client-id=21 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4880 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1548 | regsvr32.exe /s "C:\Users\admin\AppData\Local\Seclore\FileSecure\FileSecure Lite\Plugins\FSLiteOfficePlugin.dll" | C:\Windows\system32\regsvr32.exe | — | Troubleshooter.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
4 362
Read events
2 724
Write events
1 481
Delete events
157
Modification events
| (PID) Process: | (1332) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1332) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1332) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1332) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1332) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1928) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1332-13197662251880125 |
Value: 259 | |||
| (PID) Process: | (1332) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1332) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1332) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (1332) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
173
Suspicious files
104
Text files
534
Unknown types
27
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 1332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 1332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 1332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 1332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 1332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\41cd6eff-7bbd-4f1a-b78a-e883069d075d.tmp | — | |
MD5:— | SHA256:— | |||
| 1332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 1332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 1332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
50
DNS requests
24
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3324 | chrome.exe | GET | 302 | 216.239.32.21:80 | http://virustotal.com/ | US | — | — | whitelisted |
3324 | chrome.exe | GET | 200 | 173.194.19.183:80 | http://r1---sn-5go7yn7z.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=82.102.22.104&mm=28&mn=sn-5go7yn7z&ms=nvh&mt=1553188760&mv=m&pl=24&shardbypass=yes | US | crx | 842 Kb | whitelisted |
3324 | chrome.exe | GET | 302 | 216.58.207.78:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 504 b | whitelisted |
3324 | chrome.exe | GET | 200 | 205.185.216.10:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 55.2 Kb | whitelisted |
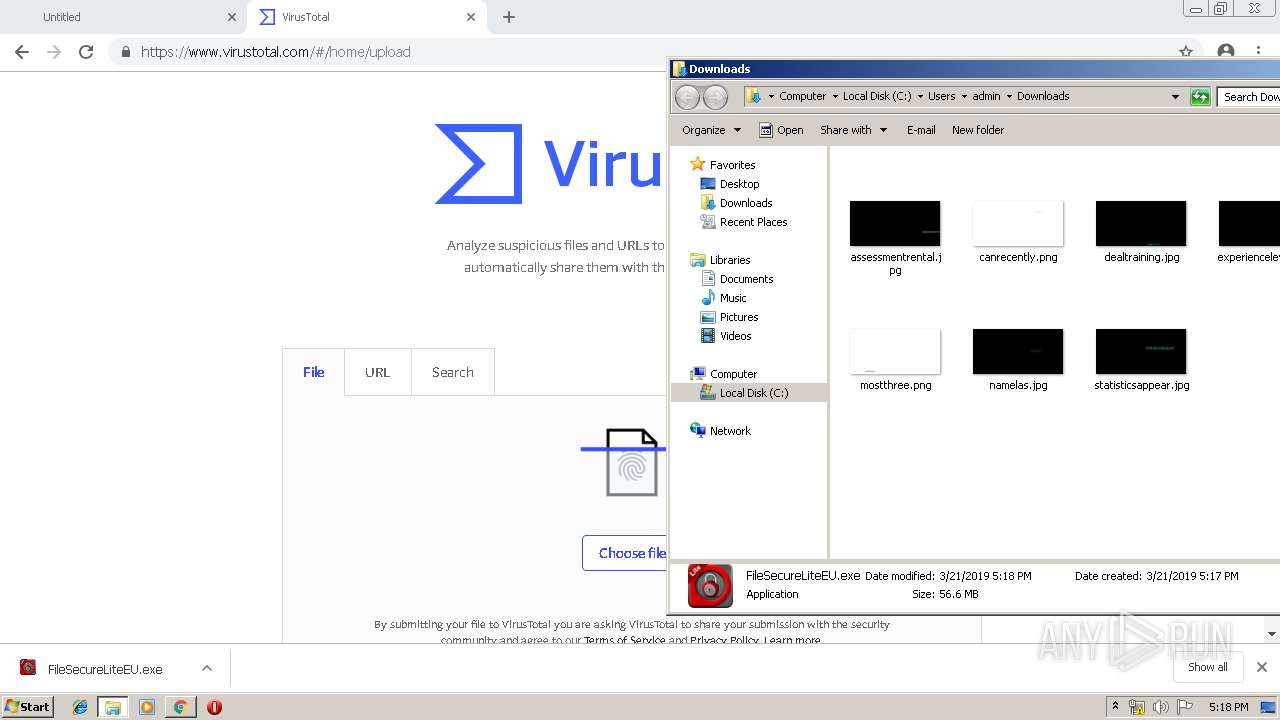
3324 | chrome.exe | GET | 301 | 13.32.219.3:80 | http://dl.sharefile.com/filesecurewinliteeu/FileSecureLiteEU.exe | US | html | 183 b | malicious |
3324 | chrome.exe | GET | 301 | 13.32.219.3:80 | http://dl.sharefile.com/filesecurewinliteeu/ | US | html | 183 b | malicious |
3324 | chrome.exe | GET | 200 | 13.32.222.239:80 | http://x.ss2.us/x.cer | US | der | 1.27 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3324 | chrome.exe | 172.217.16.195:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3324 | chrome.exe | 13.32.219.3:443 | dl.sharefile.com | Amazon.com, Inc. | US | unknown |
3324 | chrome.exe | 13.32.222.239:80 | x.ss2.us | Amazon.com, Inc. | US | whitelisted |
3324 | chrome.exe | 205.185.216.10:80 | www.download.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
3324 | chrome.exe | 13.32.219.3:80 | dl.sharefile.com | Amazon.com, Inc. | US | unknown |
3324 | chrome.exe | 172.217.22.99:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3324 | chrome.exe | 216.58.206.3:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3324 | chrome.exe | 172.217.18.100:443 | www.google.com | Google Inc. | US | whitelisted |
3324 | chrome.exe | 172.217.21.234:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3324 | chrome.exe | 216.58.205.238:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dl.sharefile.com |
| malicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
x.ss2.us |
| whitelisted |
www.download.windowsupdate.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
www.google.com |
| malicious |
apis.google.com |
| whitelisted |
virustotal.com |
| whitelisted |