analyze malware
- Huge database of samples and IOCs
- Custom VM setup
- Unlimited submissions
- Interactive approach
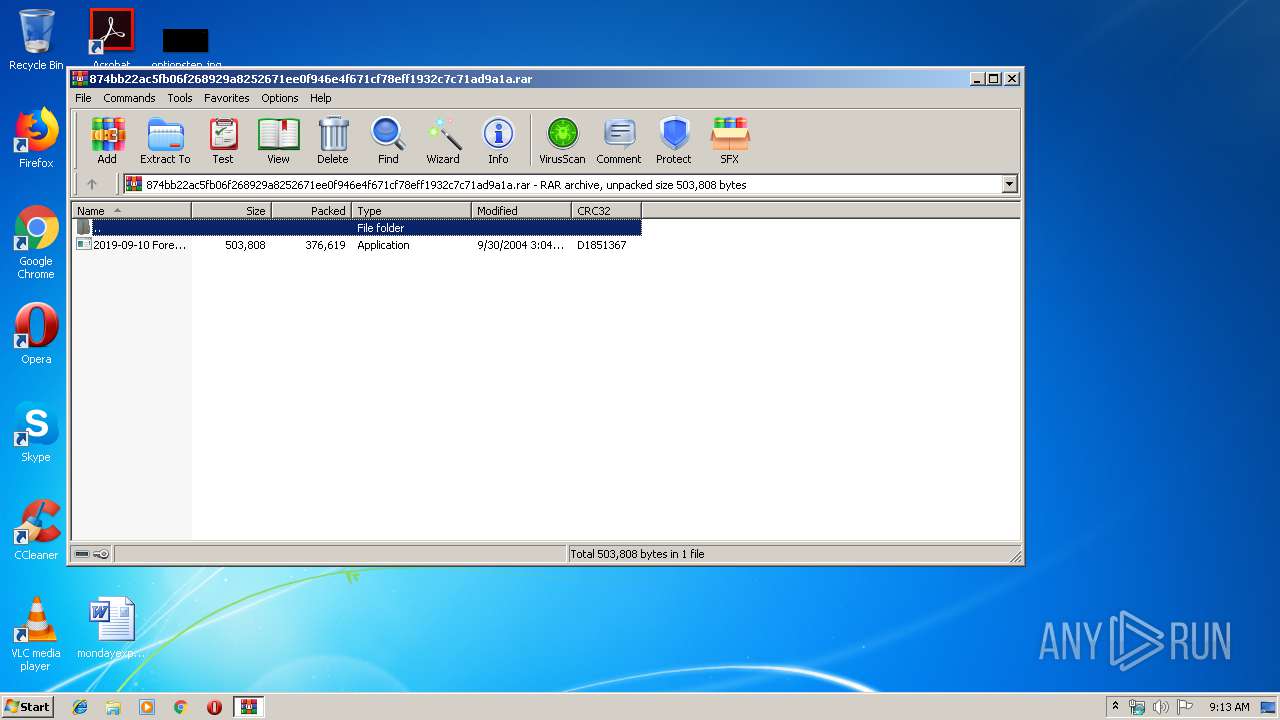
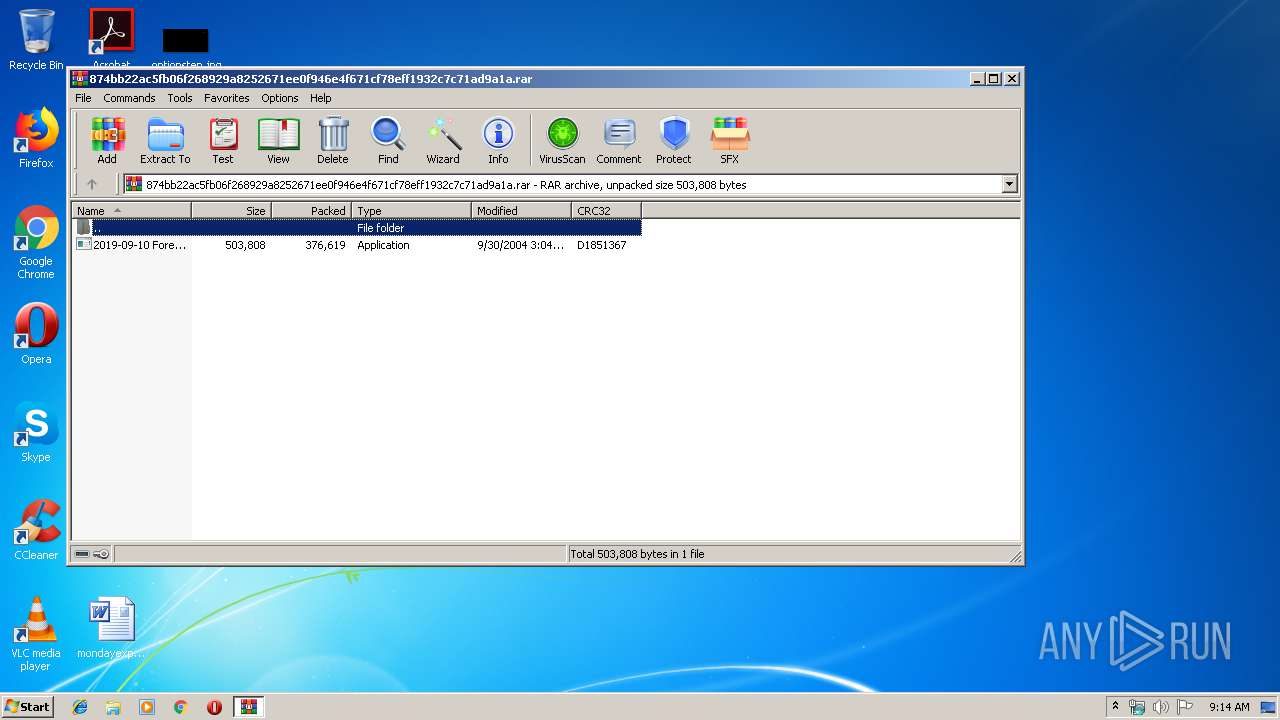
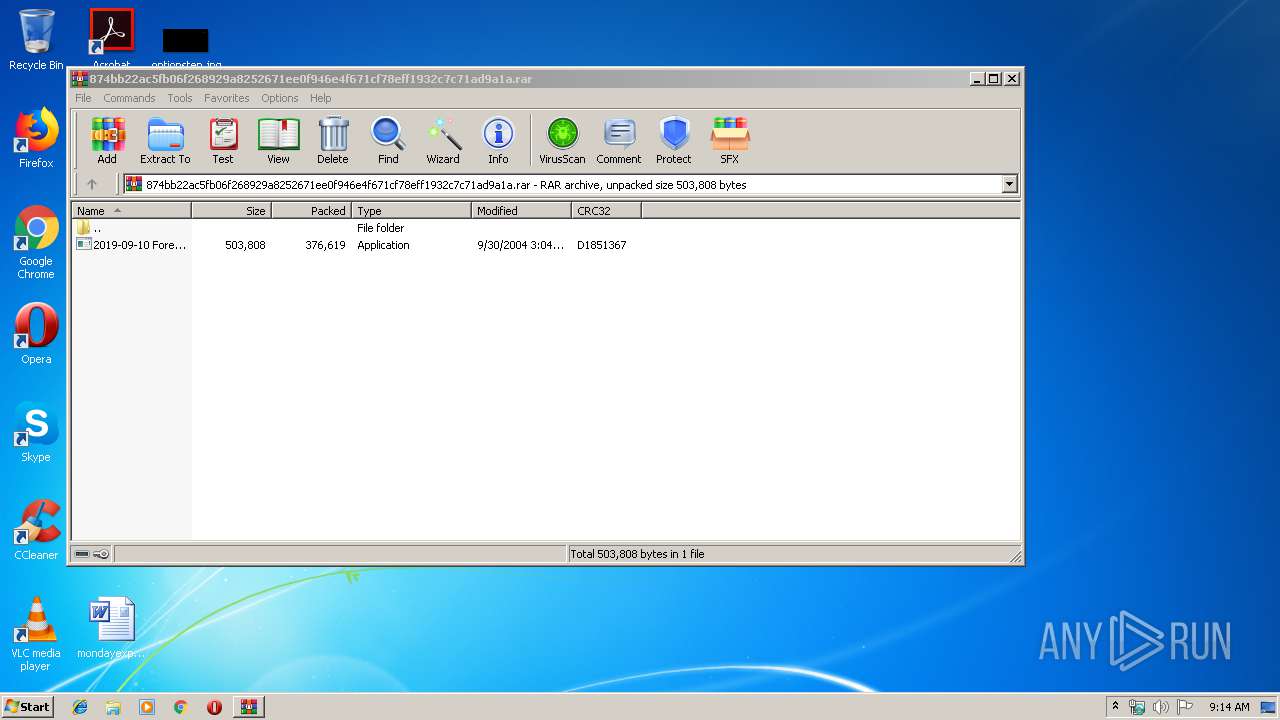
| File name: | 874bb22ac5fb06f268929a8252671ee0f946e4f671cf78eff1932c7c71ad9a1a |
| Full analysis: | https://app.any.run/tasks/d1a42c38-d481-4741-901c-f8dc4d7aee98 |
| Verdict: | Malicious activity |
| Threats: | FormBook is a data stealer that is being distributed as a MaaS. FormBook differs from a lot of competing malware by its extreme ease of use that allows even the unexperienced threat actors to use FormBook virus. |
| Analysis date: | September 11, 2019, 08:13:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 936252726A0262397F44175FFB313C54 |
| SHA1: | F4D7548D70AA3507E92229C4079F675D4543269A |
| SHA256: | 874BB22AC5FB06F268929A8252671EE0F946E4F671CF78EFF1932C7C71AD9A1A |
| SSDEEP: | 6144:xJt0X3sBAU8CptlVFUb+j5+GDCttKg/oYWp2RdoiPhEZKW5DD+lUGQZYnyNOtJS/:xosB58EVFUb1iW6YWp24iPCfDalU5s/4 |
MALICIOUS
Application was dropped or rewritten from another process
- 2019-09-10 Forecast.exe (PID: 3964)
- 2019-09-10 Forecast.exe (PID: 3328)
FORMBOOK was detected
- explorer.exe (PID: 276)
- chkdsk.exe (PID: 2408)
- Firefox.exe (PID: 504)
Changes the autorun value in the registry
- chkdsk.exe (PID: 2408)
Connects to CnC server
- explorer.exe (PID: 276)
Actions looks like stealing of personal data
- chkdsk.exe (PID: 2408)
Stealing of credential data
- chkdsk.exe (PID: 2408)
SUSPICIOUS
Application launched itself
- 2019-09-10 Forecast.exe (PID: 3328)
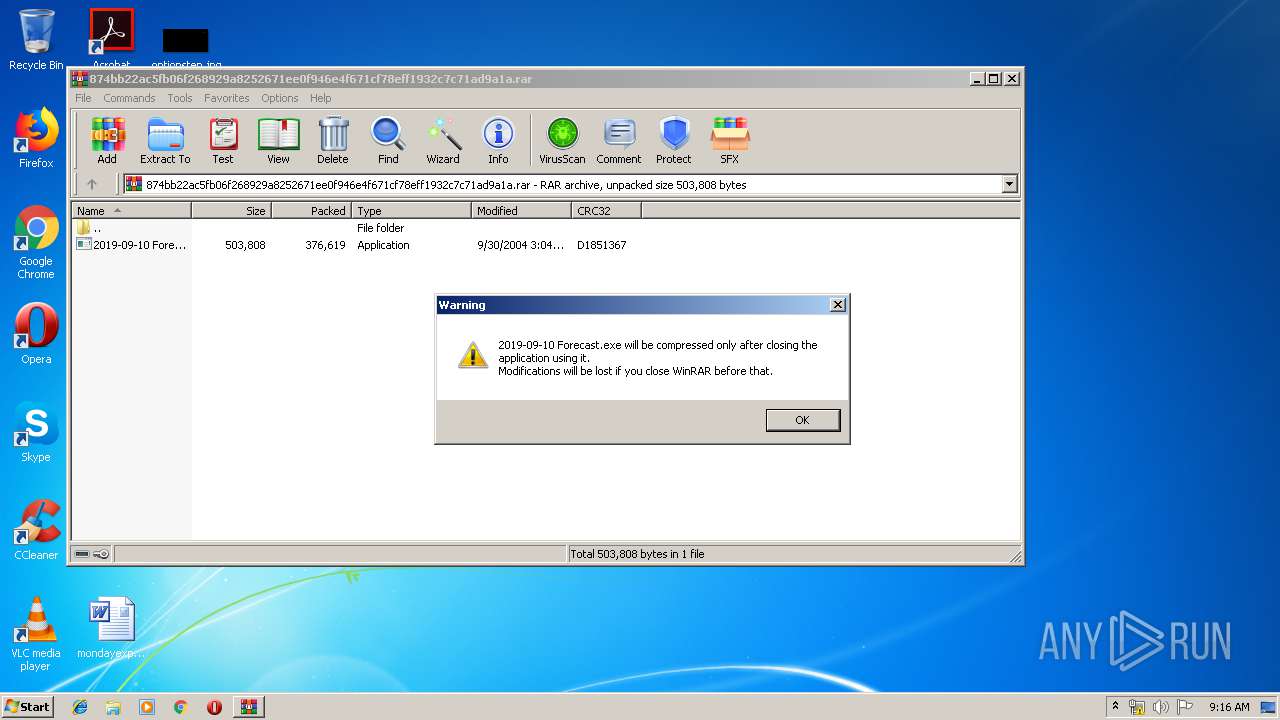
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3632)
Starts CMD.EXE for commands execution
- chkdsk.exe (PID: 2408)
Creates files in the user directory
- chkdsk.exe (PID: 2408)
Loads DLL from Mozilla Firefox
- chkdsk.exe (PID: 2408)
INFO
Manual execution by user
- chkdsk.exe (PID: 2408)
Reads the hosts file
- chkdsk.exe (PID: 2408)
Creates files in the user directory
- Firefox.exe (PID: 504)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
38
Monitored processes
7
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
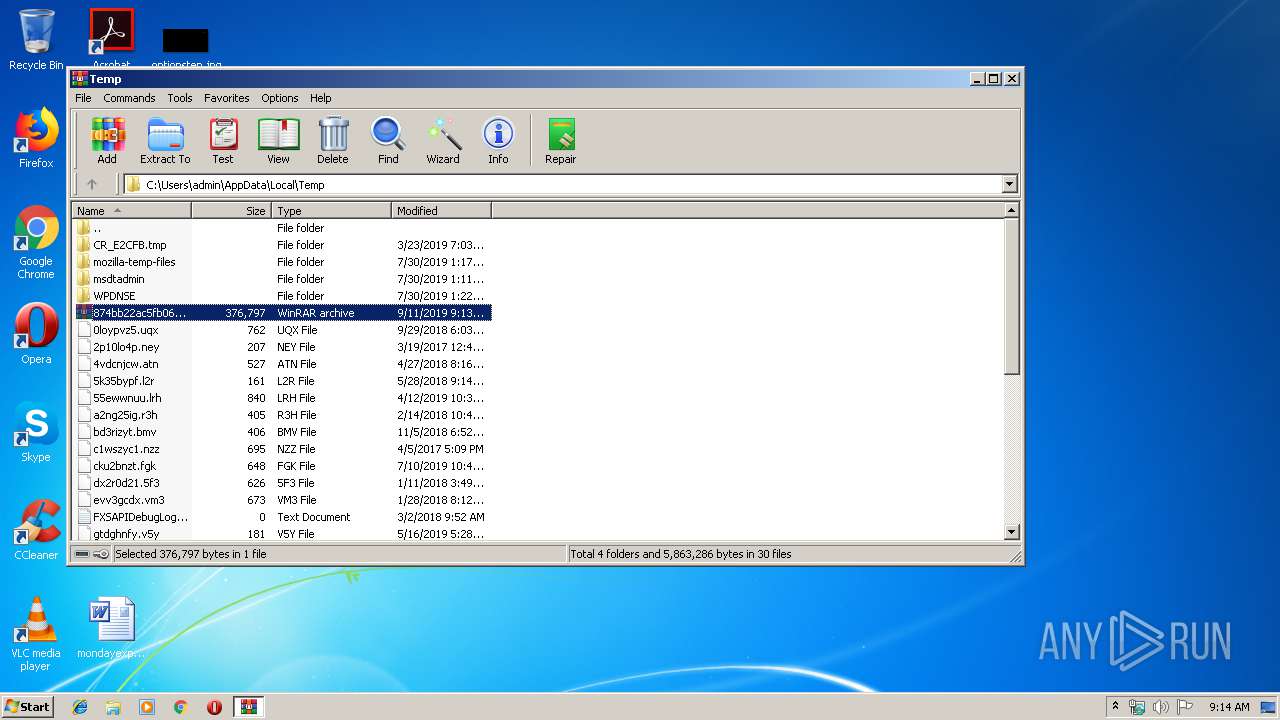
| 3632 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\874bb22ac5fb06f268929a8252671ee0f946e4f671cf78eff1932c7c71ad9a1a.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | |
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.60.0 | ||||
| 3328 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3632.15123\2019-09-10 Forecast.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3632.15123\2019-09-10 Forecast.exe | — | WinRAR.exe |
User: admin Company: WorkmanshipHYPOEOSINOPHILIA Integrity Level: MEDIUM Description: WorkmanshipSedaka Exit code: 0 Version: 1.08.0005 | ||||
| 3964 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3632.15123\2019-09-10 Forecast.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3632.15123\2019-09-10 Forecast.exe | — | 2019-09-10 Forecast.exe |
User: admin Company: WorkmanshipHYPOEOSINOPHILIA Integrity Level: MEDIUM Description: WorkmanshipSedaka Exit code: 0 Version: 1.08.0005 | ||||
| 2408 | "C:\Windows\System32\chkdsk.exe" | C:\Windows\System32\chkdsk.exe | explorer.exe | |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Check Disk Utility Version: 6.1.7600.16385 (win7_rtm.090713-1255) | ||||
| 3076 | /c del "C:\Users\admin\AppData\Local\Temp\Rar$EXa3632.15123\2019-09-10 Forecast.exe" | C:\Windows\System32\cmd.exe | — | chkdsk.exe |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) | ||||
| 276 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Version: 6.1.7600.16385 (win7_rtm.090713-1255) | ||||
| 504 | "C:\Program Files\Mozilla Firefox\Firefox.exe" | C:\Program Files\Mozilla Firefox\Firefox.exe | chkdsk.exe | |
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 | ||||
Total events
505
Read events
473
Write events
32
Delete events
0
Modification events
| (PID) Process: | (3632) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3632) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3632) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3632) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\874bb22ac5fb06f268929a8252671ee0f946e4f671cf78eff1932c7c71ad9a1a.rar | |||
| (PID) Process: | (3632) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3632) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3632) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3632) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (276) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.rar\OpenWithList |
| Operation: | write | Name: | a |
Value: WinRAR.exe | |||
| (PID) Process: | (276) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.rar\OpenWithList |
| Operation: | write | Name: | MRUList |
Value: a | |||
Executable files
1
Suspicious files
73
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3632 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3632.15123\2019-09-10 Forecast.exe | executable | |
MD5:0E3E66454100C0F22D66855AF13C8B8C | SHA256:8CE6131DB6598743C5EF9A1F9DEF3BD5FA214BB6268EE25BF86C3FC9DC7EE5B9 | |||
| 2408 | chkdsk.exe | C:\Users\admin\AppData\Roaming\K8MBO92E\K8Mlogrc.ini | binary | |
MD5:2855A82ECDD565B4D957EC2EE05AED26 | SHA256:88E38DA5B12DD96AFD9DC90C79929EC31D8604B1AFDEBDD5A02B19249C08C939 | |||
| 2408 | chkdsk.exe | C:\Users\admin\AppData\Roaming\K8MBO92E\K8Mlogim.jpeg | image | |
MD5:59C4D8C50D47A5B48562D58918F3AF8B | SHA256:6A9C34D39C28264521868C51B444A4E0185EFA1837D5173BF64153A30097D9E4 | |||
| 504 | Firefox.exe | C:\Users\admin\AppData\Roaming\K8MBO92E\K8Mlogrf.ini | binary | |
MD5:53028481B5B5795F1501241CCC7ABFF6 | SHA256:75B5F3045E20C80F264568707E2D444DC7498DB119D9661AE51A91575960FC5A | |||
| 2408 | chkdsk.exe | C:\Users\admin\AppData\Roaming\K8MBO92E\K8Mlogrv.ini | binary | |
MD5:BA3B6BC807D4F76794C4B81B09BB9BA5 | SHA256:6EEBF968962745B2E9DE2CA969AF7C424916D4E3FE3CC0BB9B3D414ABFCE9507 | |||
| 2408 | chkdsk.exe | C:\Users\admin\AppData\Roaming\K8MBO92E\K8Mlogri.ini | binary | |
MD5:D63A82E5D81E02E399090AF26DB0B9CB | SHA256:EAECE2EBA6310253249603033C744DD5914089B0BB26BDE6685EC9813611BAAE | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
17
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
276 | explorer.exe | GET | 301 | 35.246.6.109:80 | http://www.kingfwb.com/ko/?ChD=NoW+iHFsXPAcHEU69sghMwragBx7ljNPHCXRoNaSAVgZGYeMplENzuGaHHIqNle3gVSmEg==&Ez=ltfXG6h&sql=1 | US | — | — | malicious |
276 | explorer.exe | GET | — | 184.168.221.54:80 | http://www.fundstd.com/ko/?ChD=6jbD5Kzhq5x1jDRWaoH9qnwAYaX5z6/NH+7UAfPDRoAaLH0xqhM9Rv4Ktvj/Ri7oBos1Aw==&Ez=ltfXG6h&sql=1 | US | — | — | malicious |
276 | explorer.exe | POST | — | 35.246.6.109:80 | http://www.kingfwb.com/ko/ | US | — | — | malicious |
276 | explorer.exe | POST | — | 66.34.159.210:80 | http://www.universityofhargeisa.net/ko/ | US | — | — | malicious |
276 | explorer.exe | POST | — | 66.34.159.210:80 | http://www.universityofhargeisa.net/ko/ | US | — | — | malicious |
276 | explorer.exe | POST | — | 66.34.159.210:80 | http://www.universityofhargeisa.net/ko/ | US | — | — | malicious |
276 | explorer.exe | GET | 403 | 104.28.17.15:80 | http://www.massagekr.com/ko/?ChD=NM9mtvc5yT/o7u1maXEuYT9PcymLQS+9pGsd186wqEppOAM0hUXqssp0ycYFIo4wHQR82A==&Ez=ltfXG6h&sql=1 | US | html | 2.99 Kb | malicious |
276 | explorer.exe | GET | 301 | 166.62.10.30:80 | http://www.invytepromotionalproducts.com/ko/?ChD=dK2OkLl8Z8AtrXYr9jiiTl8NXQegSGh73UM0TNt6lAl3Qs0v/oufEY3S4jpKAVUELLEOiA==&Ez=ltfXG6h | US | html | 340 b | malicious |
276 | explorer.exe | POST | — | 35.246.6.109:80 | http://www.kingfwb.com/ko/ | US | — | — | malicious |
276 | explorer.exe | POST | — | 35.246.6.109:80 | http://www.kingfwb.com/ko/ | US | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
276 | explorer.exe | 66.34.159.210:80 | www.universityofhargeisa.net | CoreSpace, Inc. | US | malicious |
276 | explorer.exe | 35.246.6.109:80 | www.kingfwb.com | — | US | malicious |
276 | explorer.exe | 166.62.10.30:80 | www.invytepromotionalproducts.com | GoDaddy.com, LLC | US | malicious |
276 | explorer.exe | 104.28.17.15:80 | www.massagekr.com | Cloudflare Inc | US | shared |
276 | explorer.exe | 184.168.221.54:80 | www.fundstd.com | GoDaddy.com, LLC | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.invytepromotionalproducts.com |
| malicious |
www.kingfwb.com |
| malicious |
www.universityofhargeisa.net |
| malicious |
www.fundstd.com |
| malicious |
www.massagekr.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
276 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
276 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
276 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (POST) |
276 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
276 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (POST) |
276 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
276 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
276 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (POST) |
276 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
276 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (POST) |
11 ETPRO signatures available at the full report