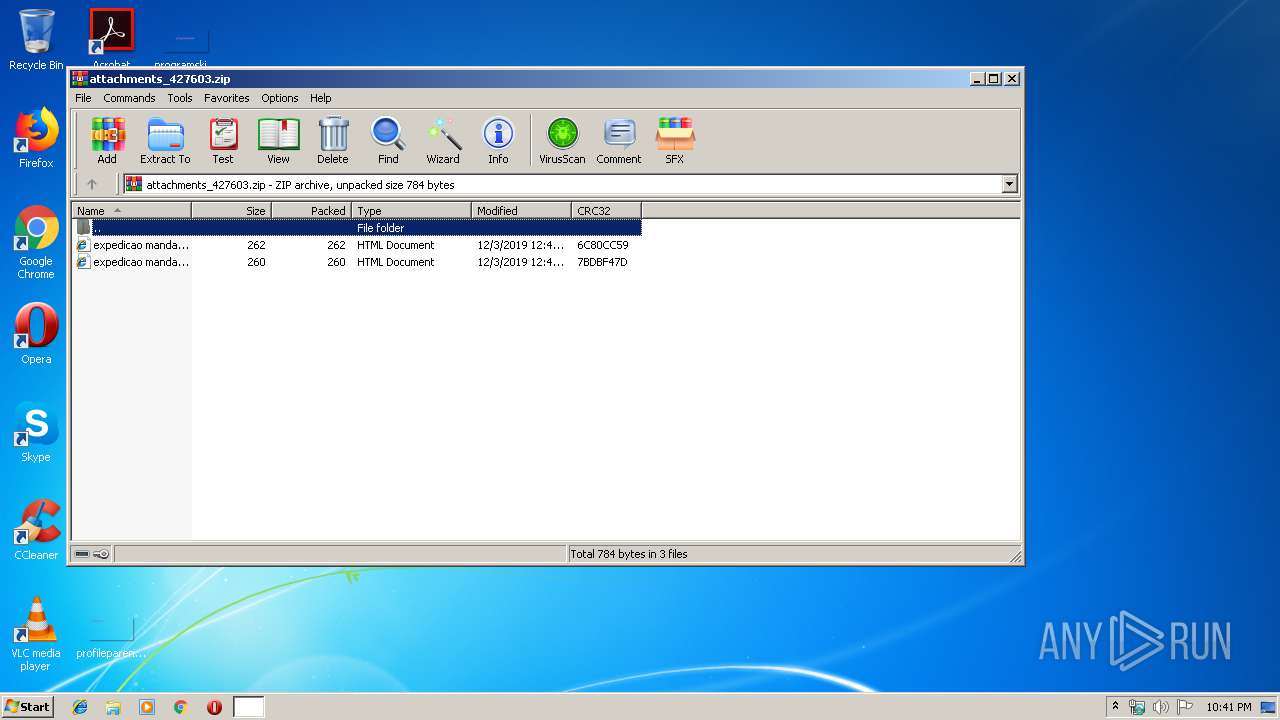
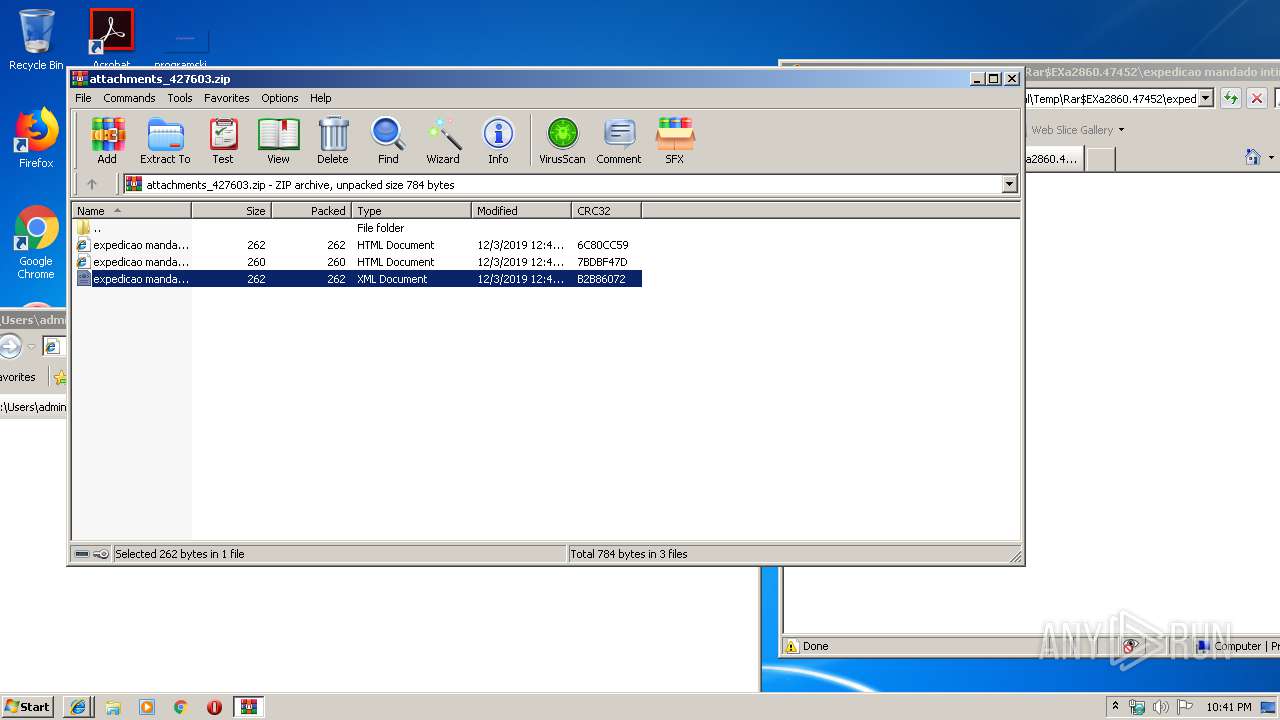
| File name: | attachments_427603.zip |
| Full analysis: | https://app.any.run/tasks/2731e43a-445e-4b23-a516-32aa7a77cc6a |
| Verdict: | Malicious activity |
| Analysis date: | December 02, 2019, 22:40:50 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 89D4962482C75E9690A955677EAEFD39 |
| SHA1: | 6CB612DA6D76813B27C88E6A346367F4F0E0742E |
| SHA256: | 8745BBF77F989B0A5D270DFB8A4B58B6C472D511B4A886E05ABDA283C344053A |
| SSDEEP: | 24:9ap0ND8dLNVMiisyFmeCND8dLNVMiEF+ND8dLNVMiJNrZzpCeeZn:9uLQNmetQdpQ8FNel |
MALICIOUS
No malicious indicators.SUSPICIOUS
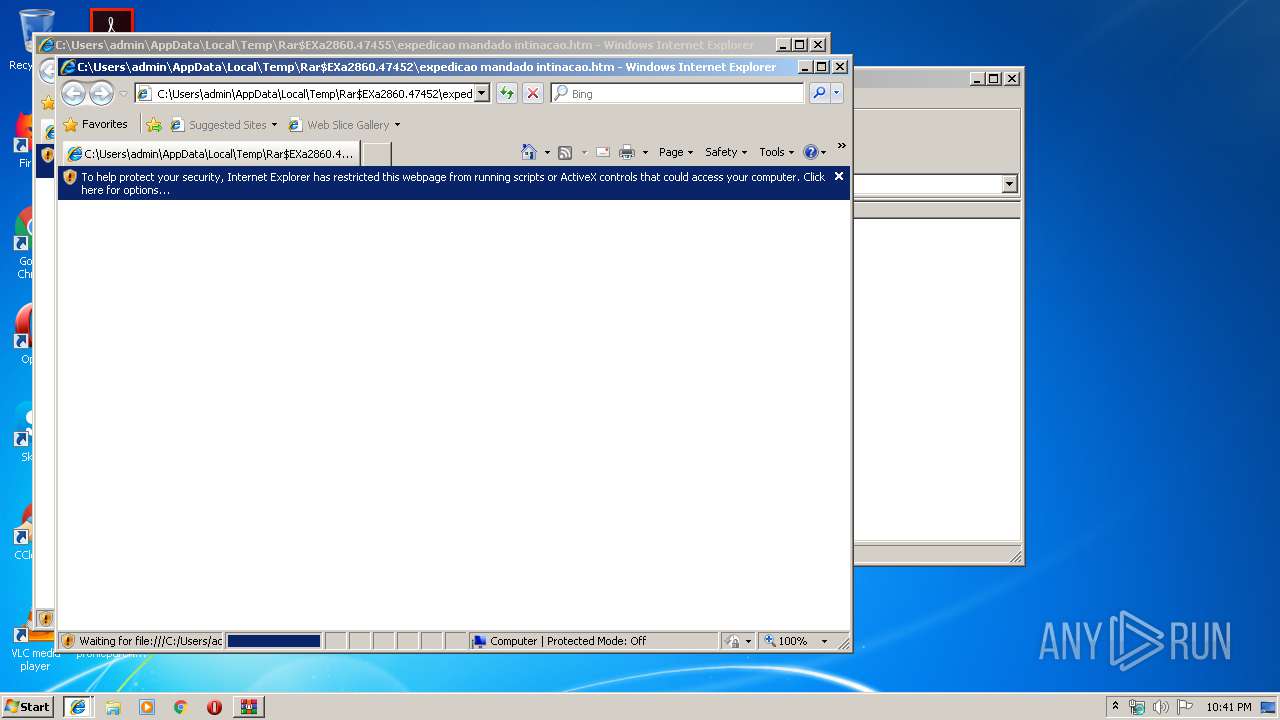
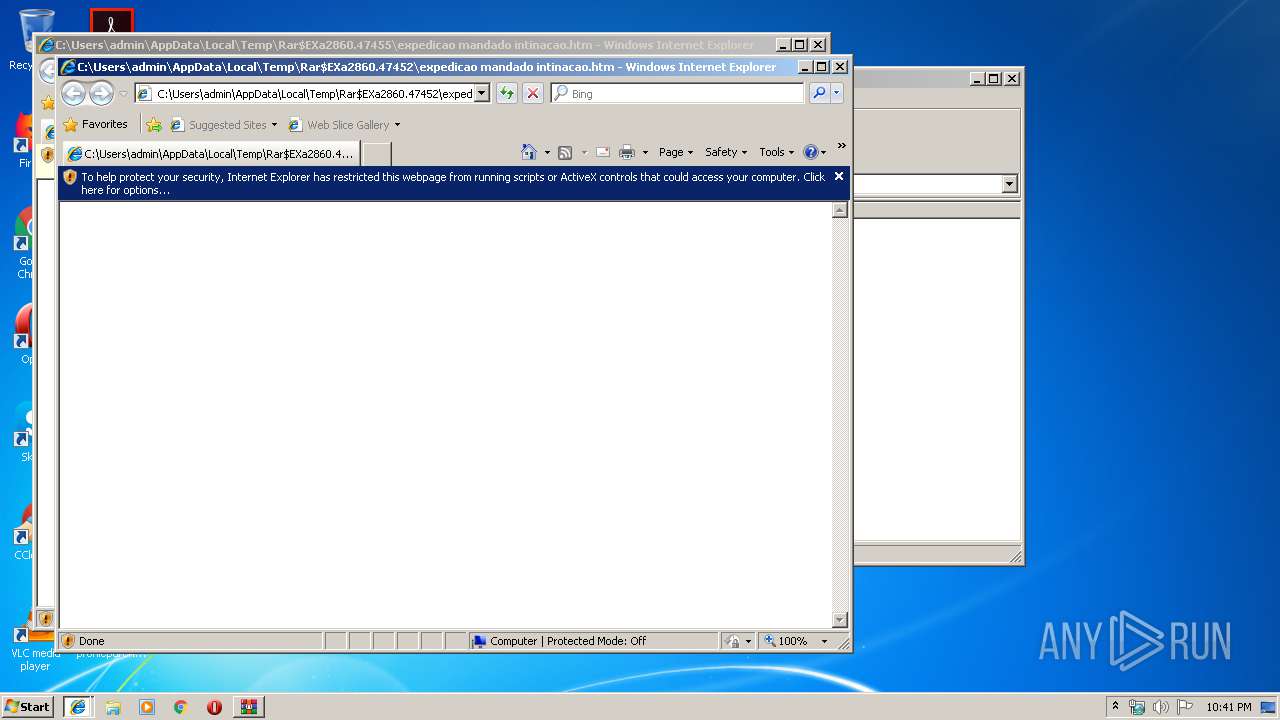
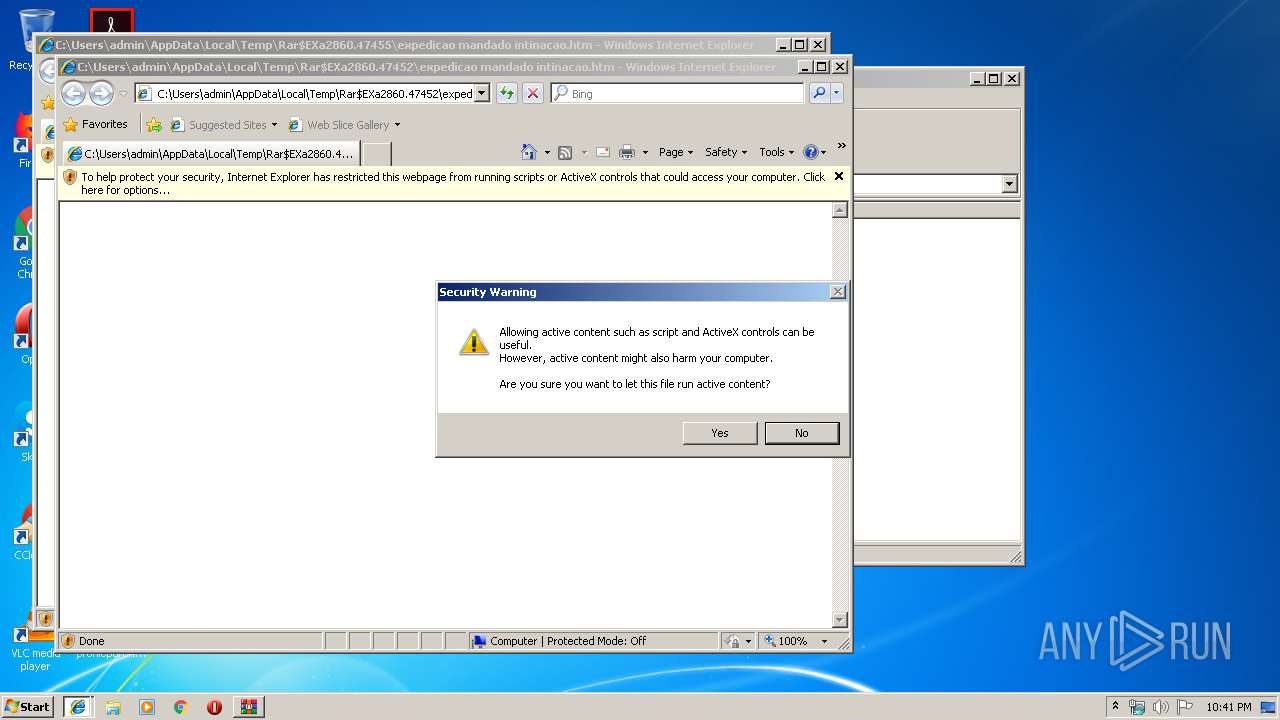
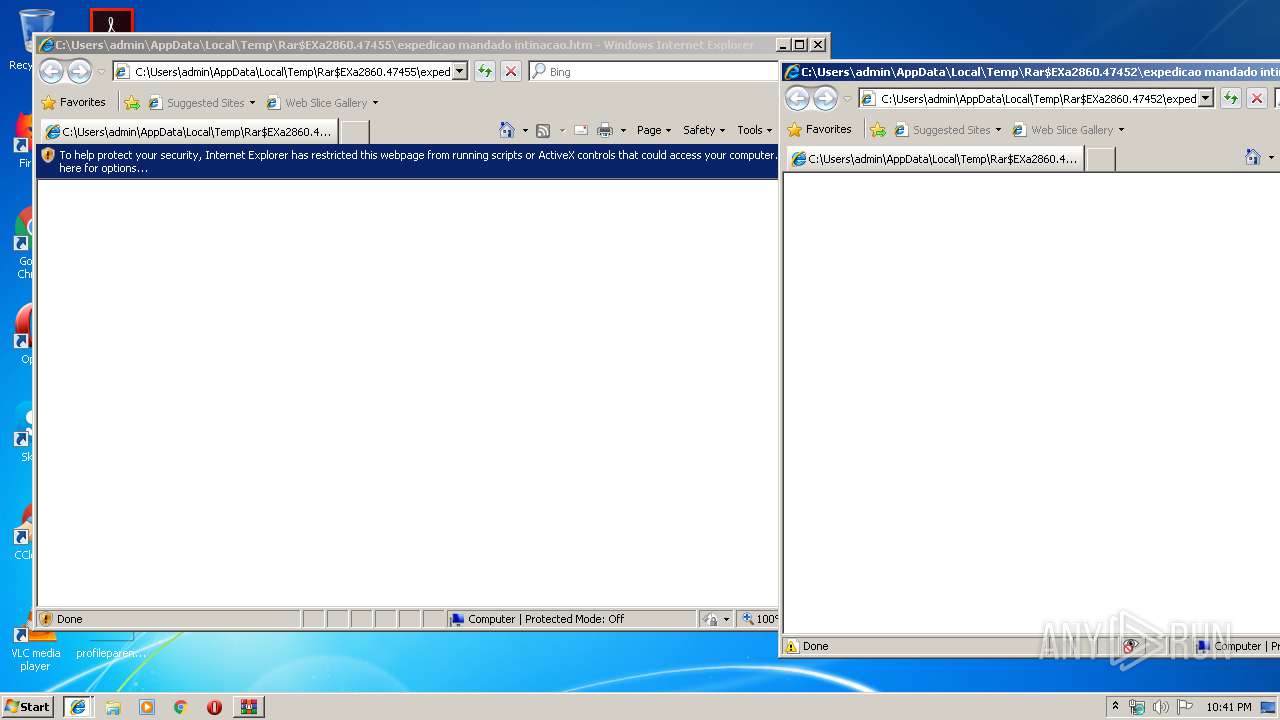
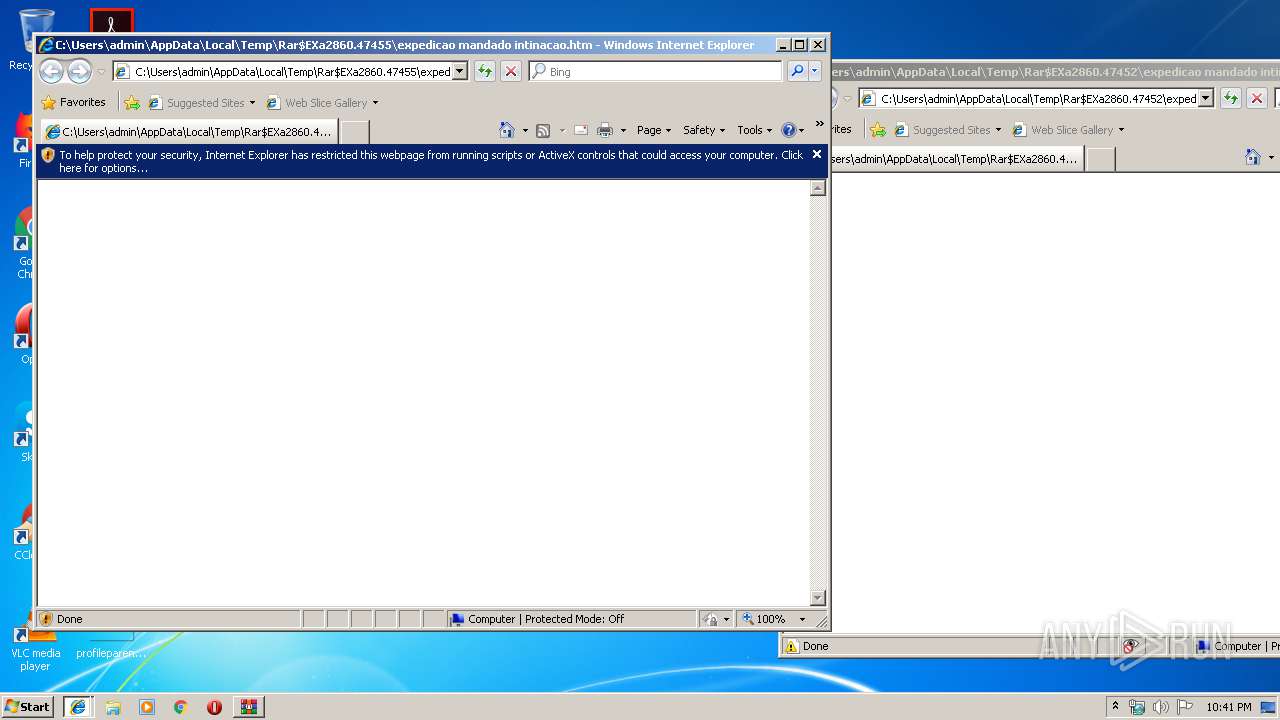
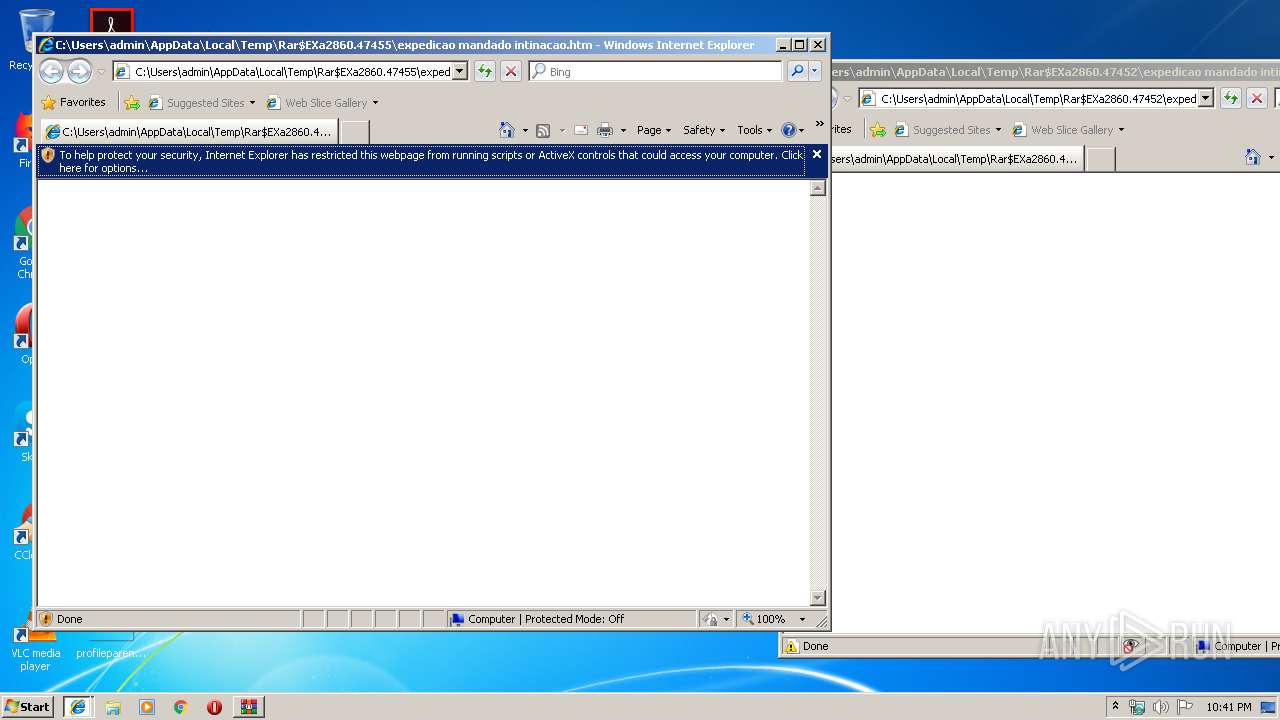
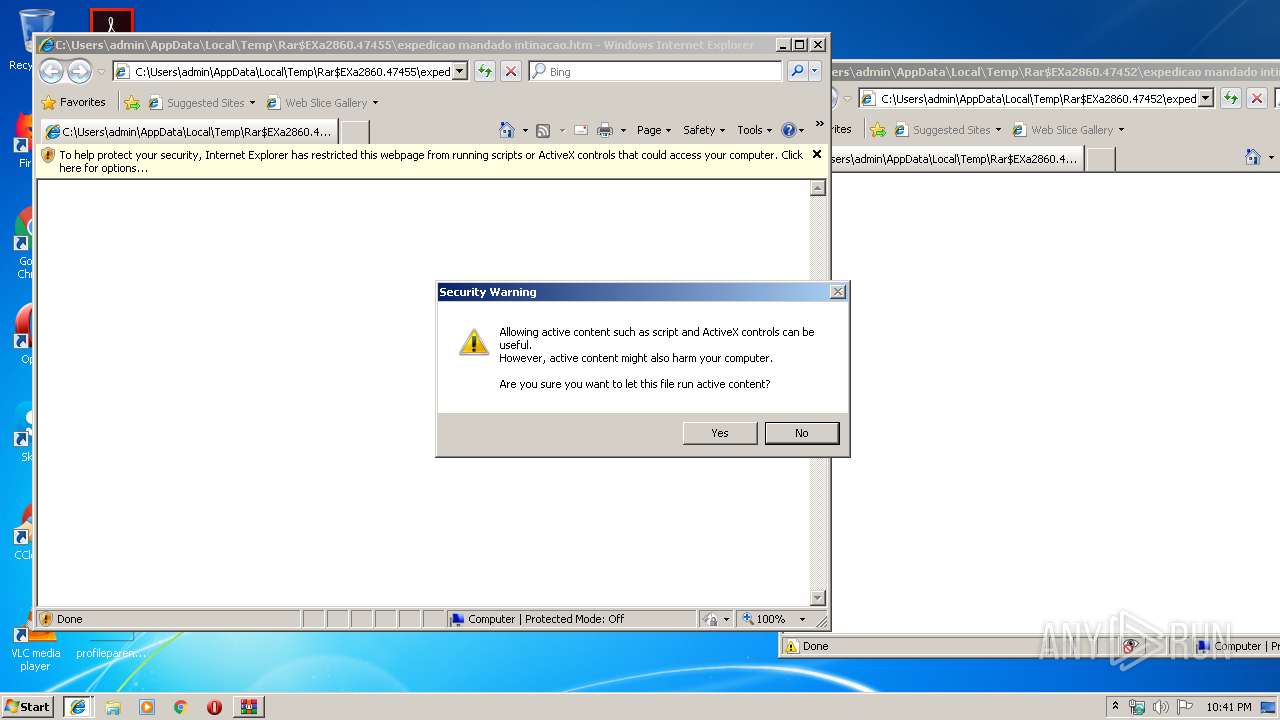
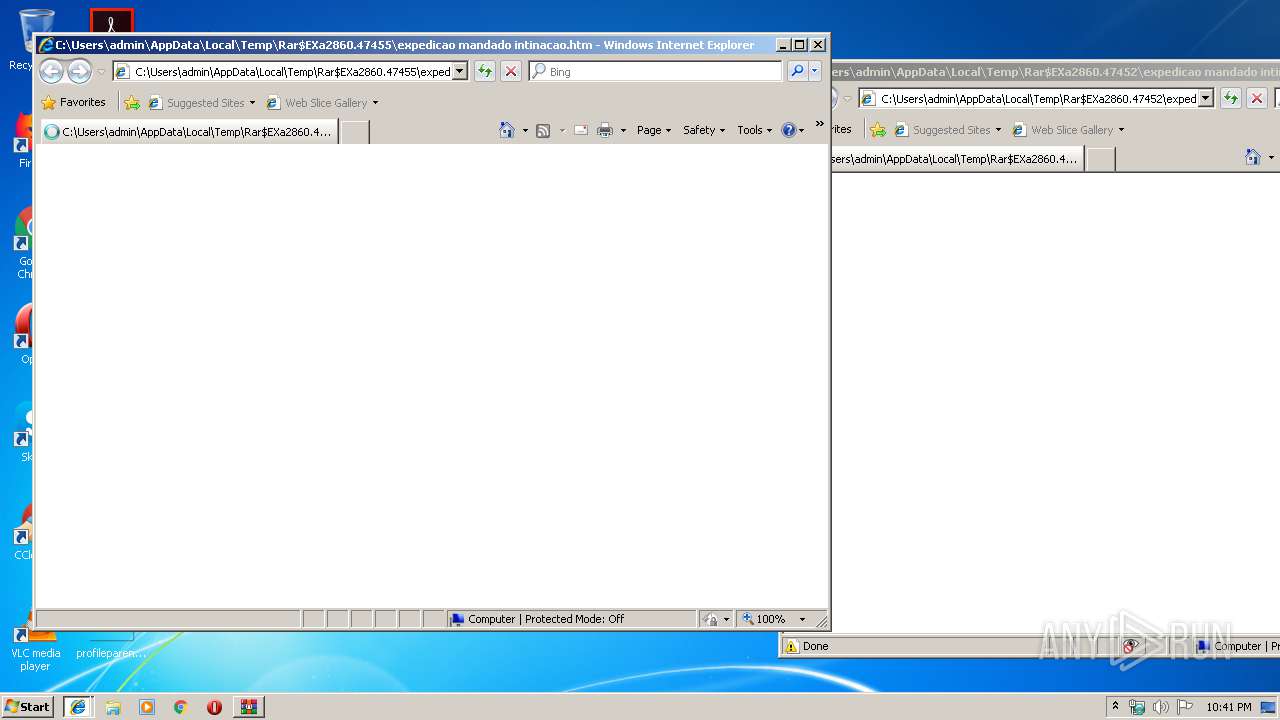
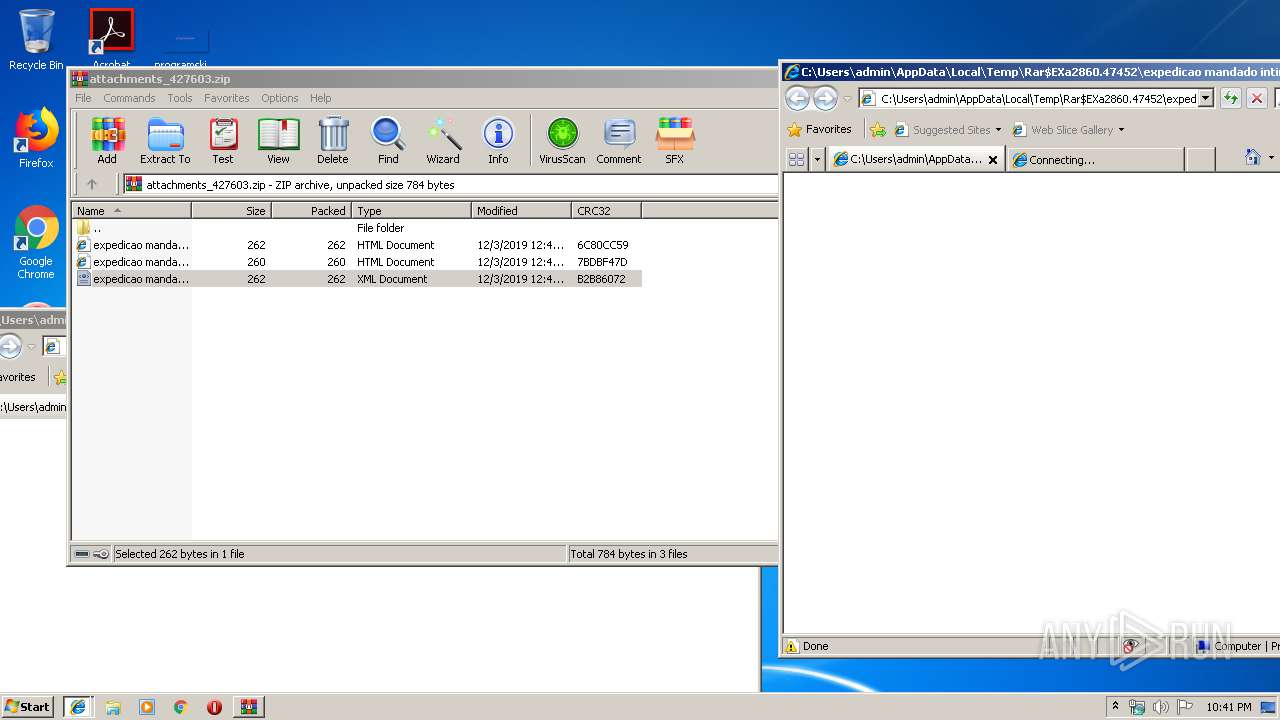
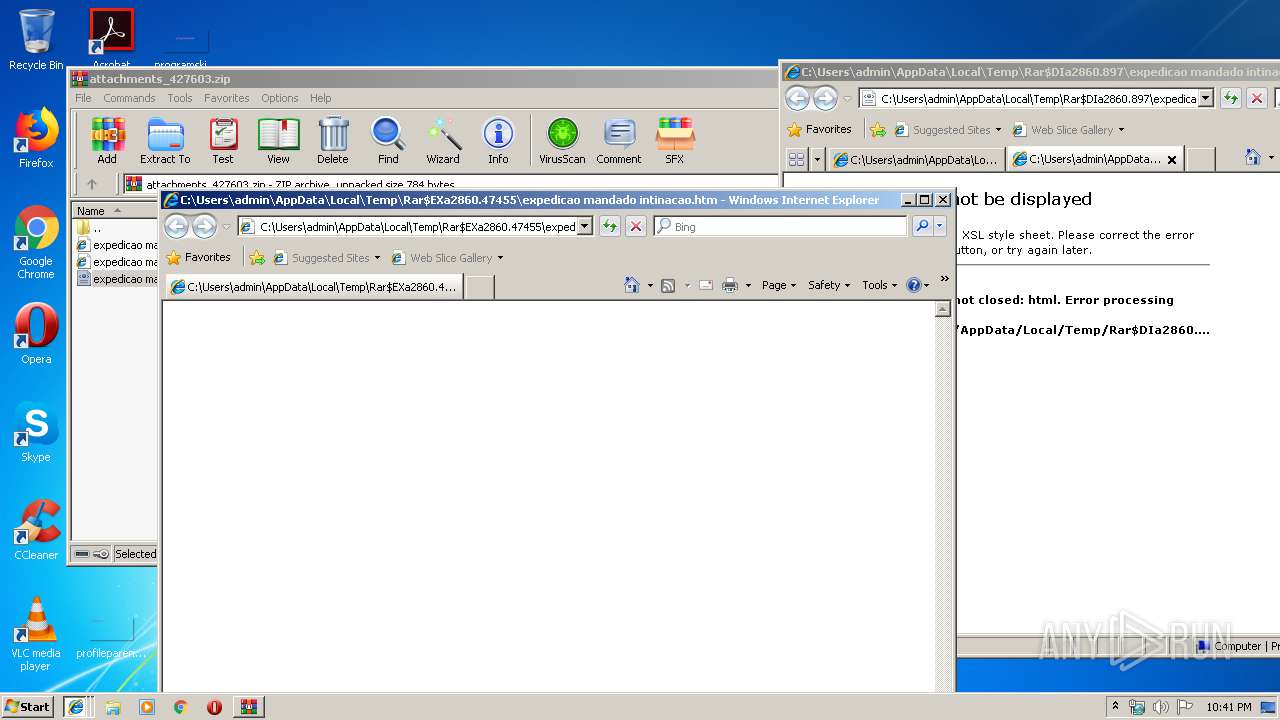
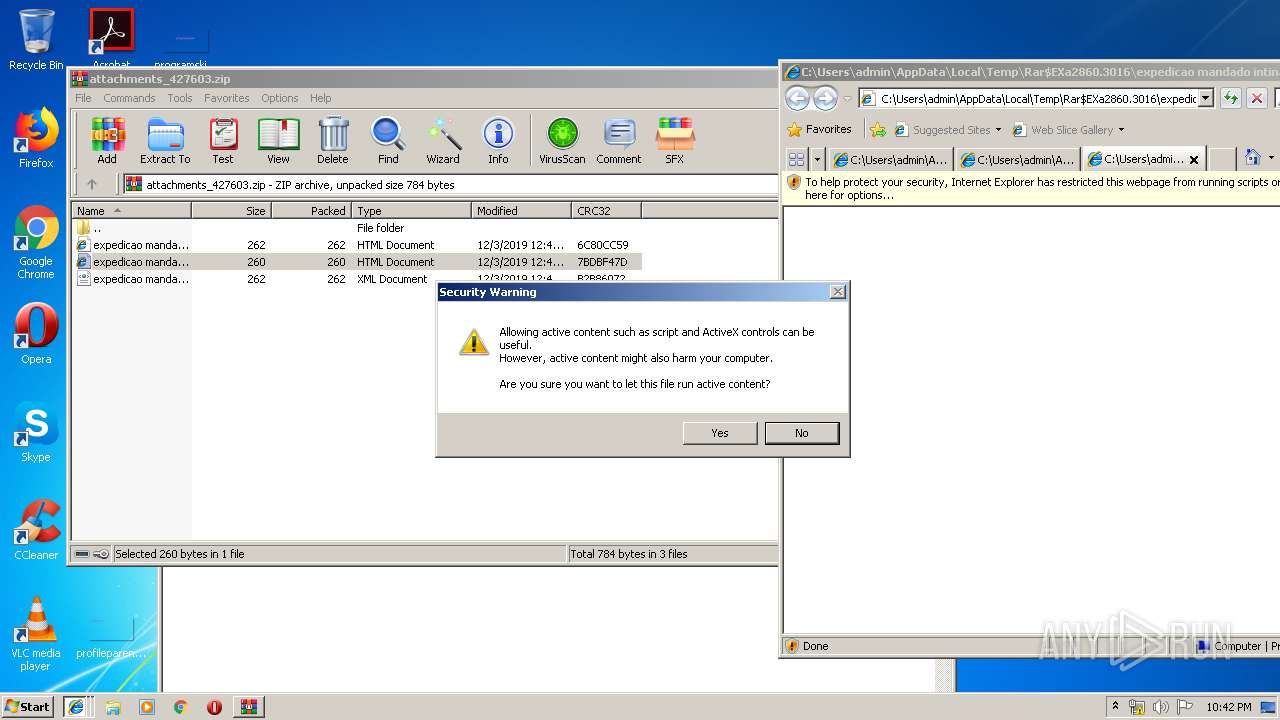
Starts Internet Explorer
- WinRAR.exe (PID: 2860)
INFO
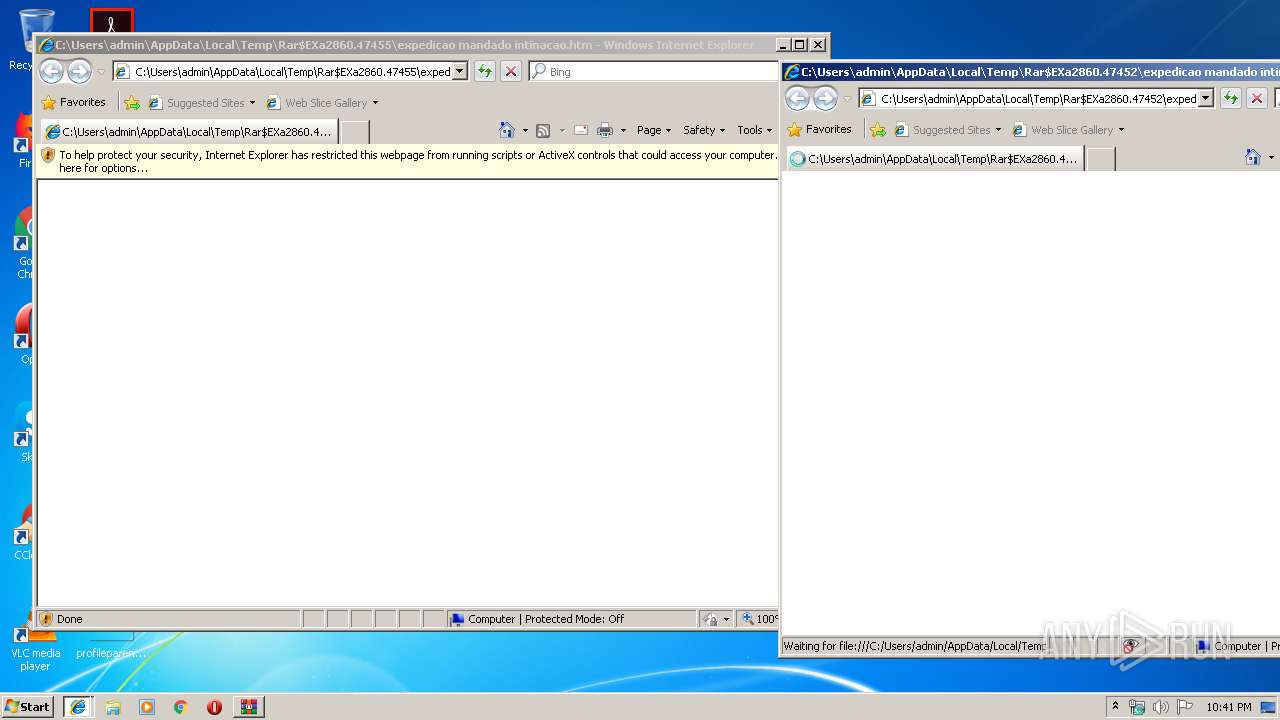
Application launched itself
- iexplore.exe (PID: 3188)
- iexplore.exe (PID: 4080)
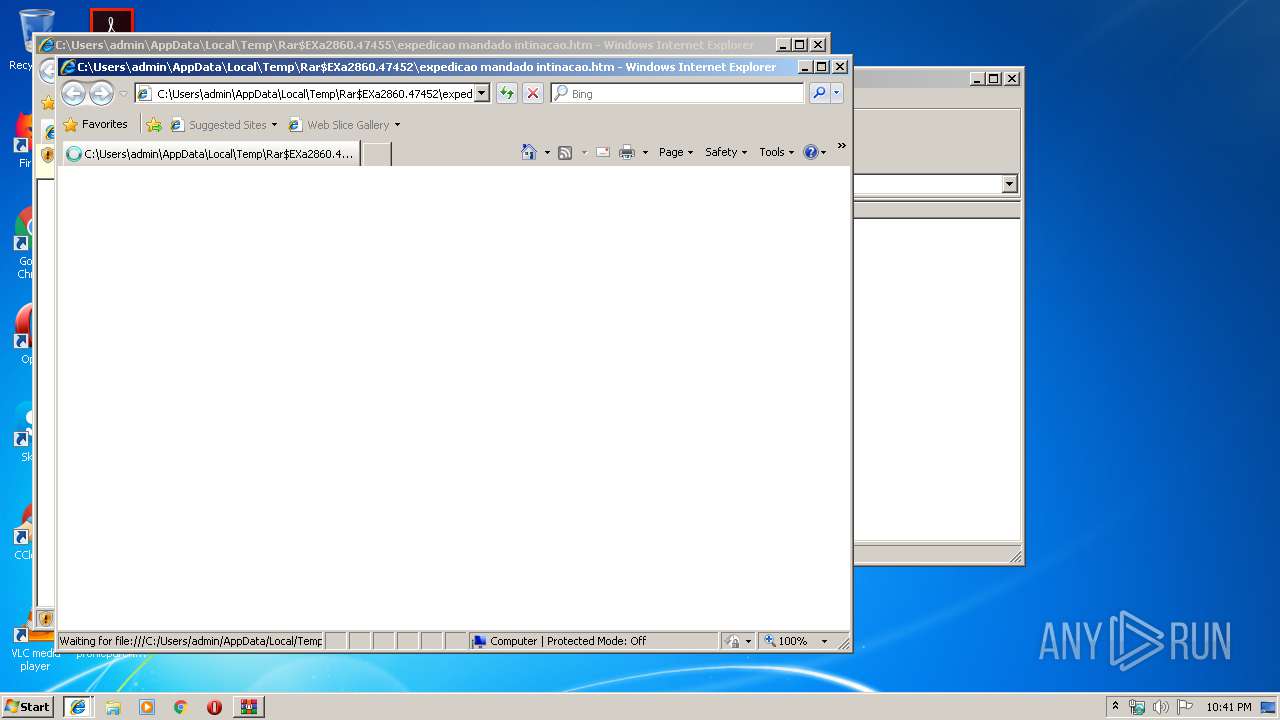
Reads internet explorer settings
- iexplore.exe (PID: 2132)
- iexplore.exe (PID: 3792)
- iexplore.exe (PID: 2604)
Changes internet zones settings
- iexplore.exe (PID: 4080)
- iexplore.exe (PID: 3188)
Creates files in the user directory
- iexplore.exe (PID: 2132)
Reads Internet Cache Settings
- iexplore.exe (PID: 3792)
- iexplore.exe (PID: 2132)
Writes to a desktop.ini file (may be used to cloak folders)
- iexplore.exe (PID: 3188)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
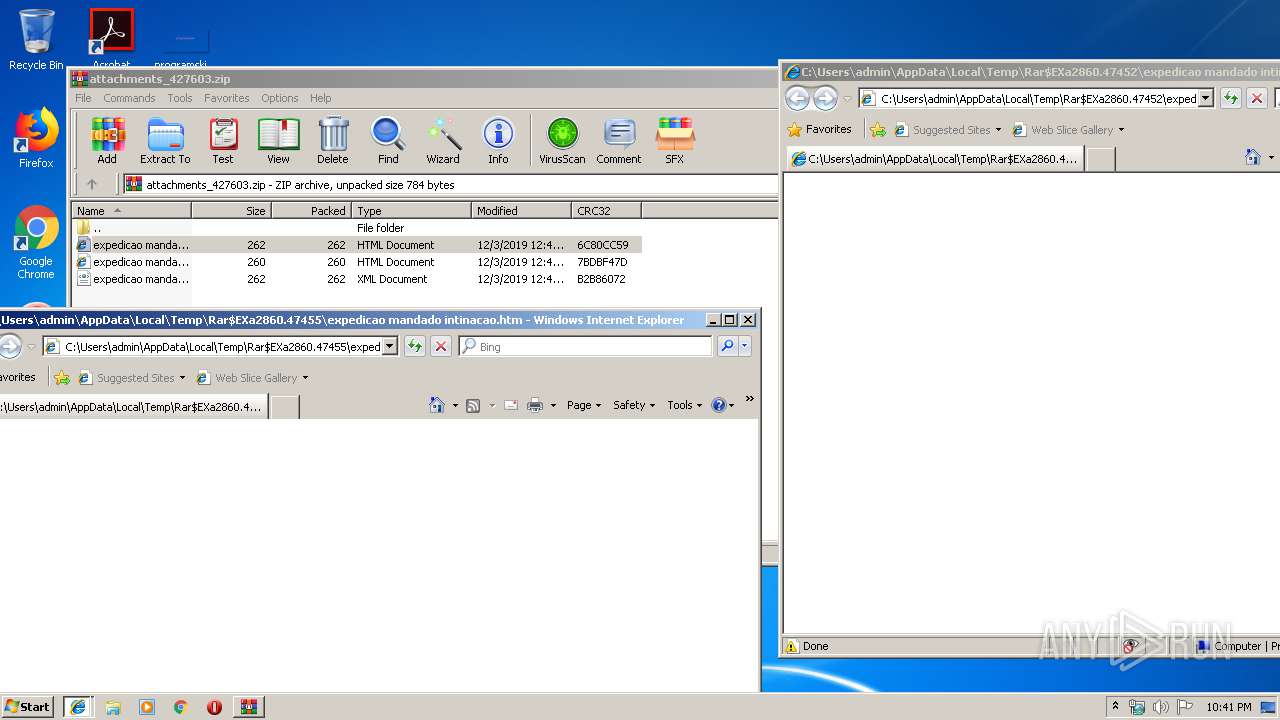
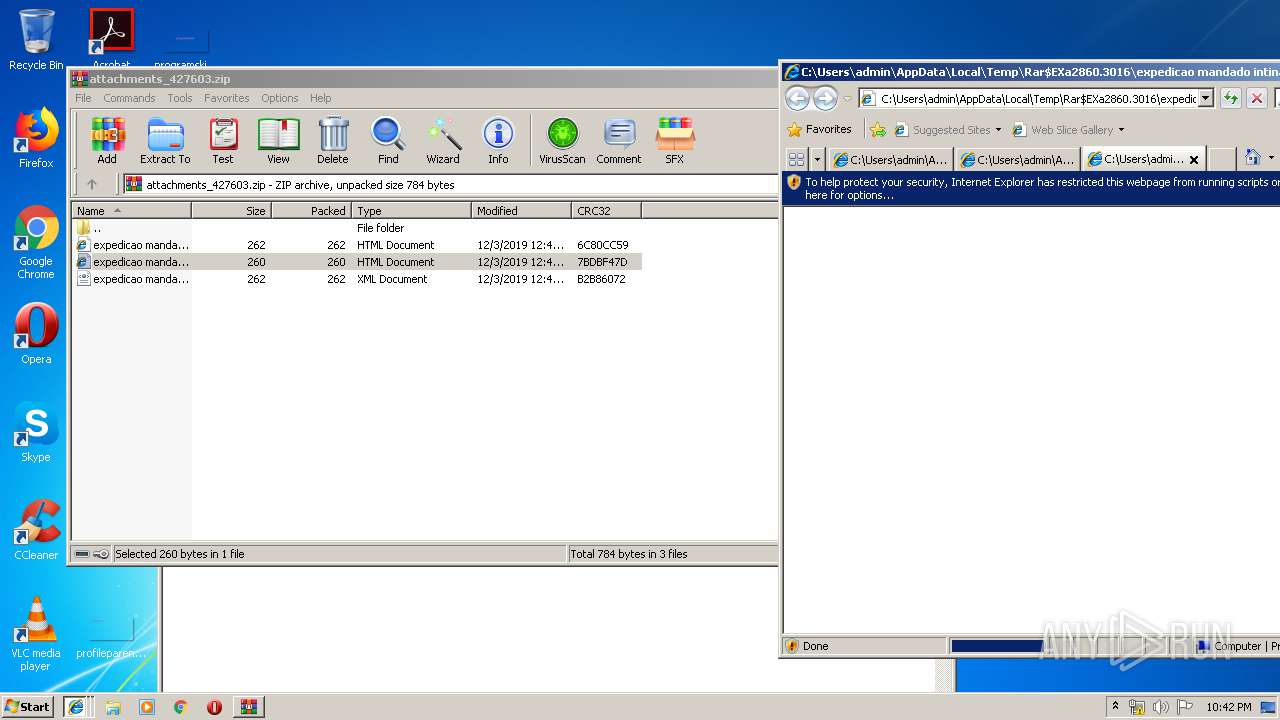
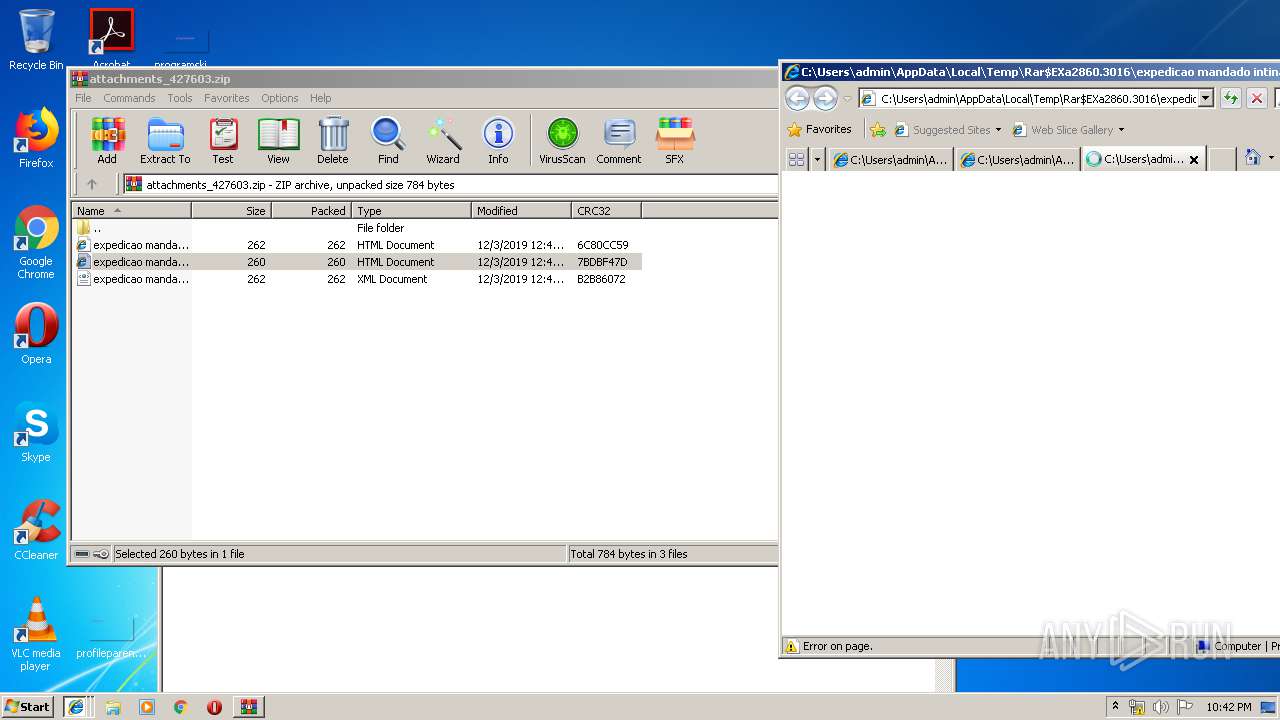
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2019:12:03 00:40:16 |
| ZipCRC: | 0x6c80cc59 |
| ZipCompressedSize: | 262 |
| ZipUncompressedSize: | 262 |
| ZipFileName: | expedicao mandado intinacao.htm |
Total processes
42
Monitored processes
7
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2132 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:4080 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2604 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3188 CREDAT:14341 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
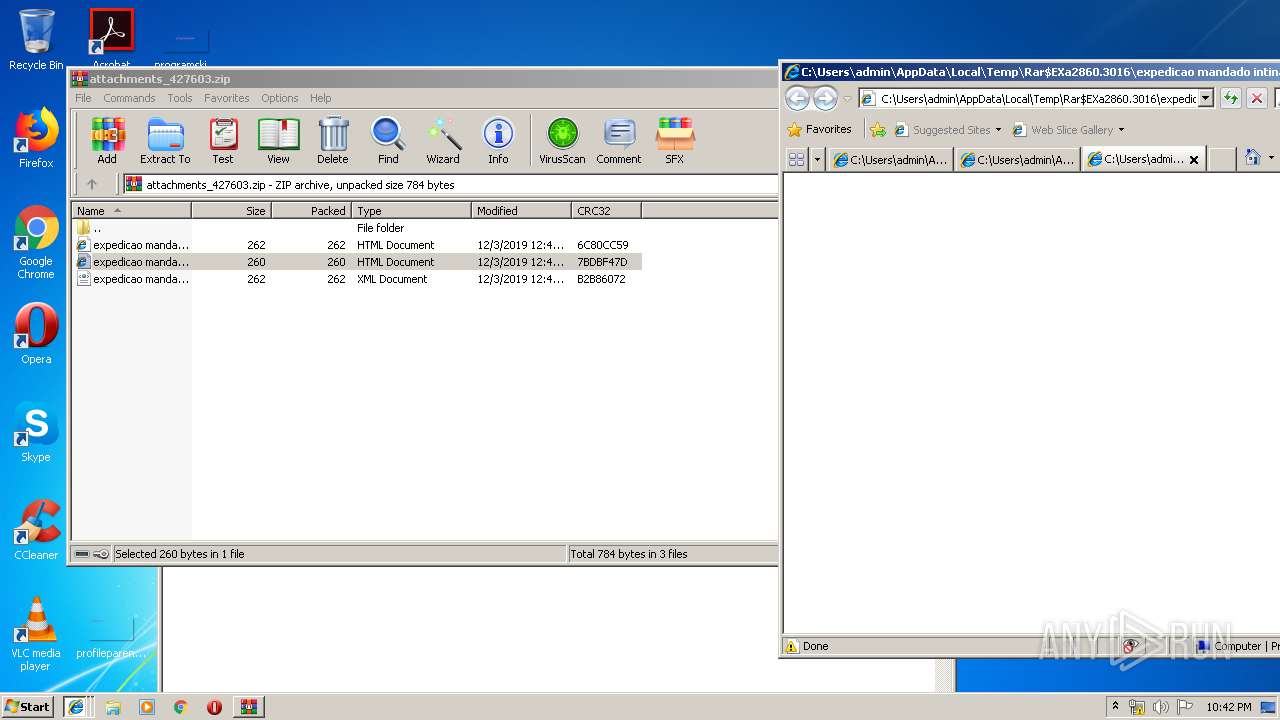
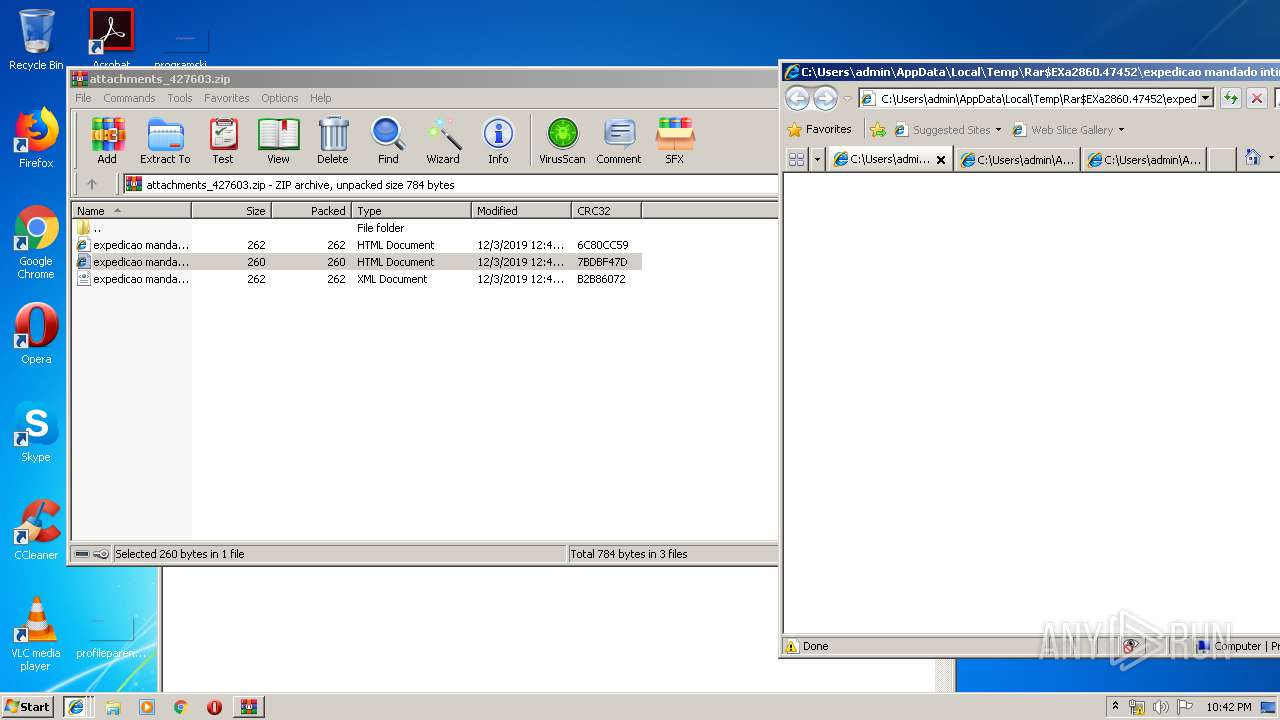
| 2860 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\attachments_427603.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3188 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\admin\AppData\Local\Temp\Rar$EXa2860.47452\expedicao mandado intinacao.htm | C:\Program Files\Internet Explorer\iexplore.exe | WinRAR.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
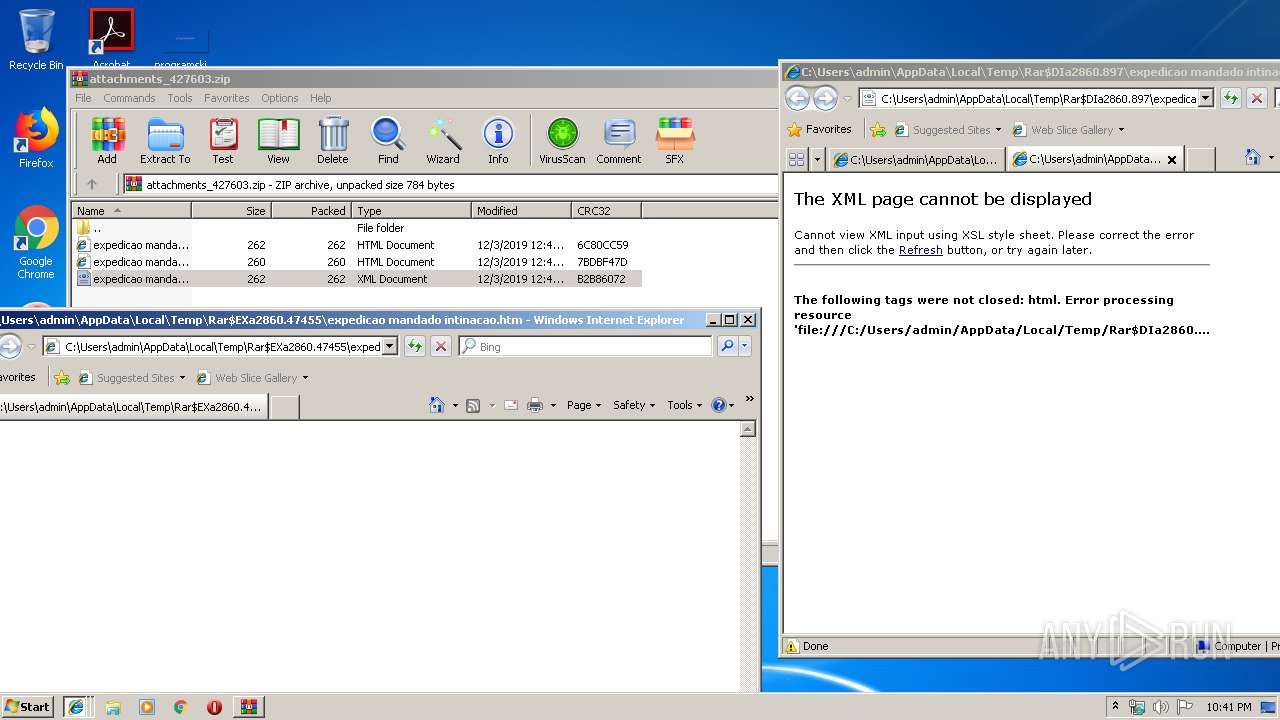
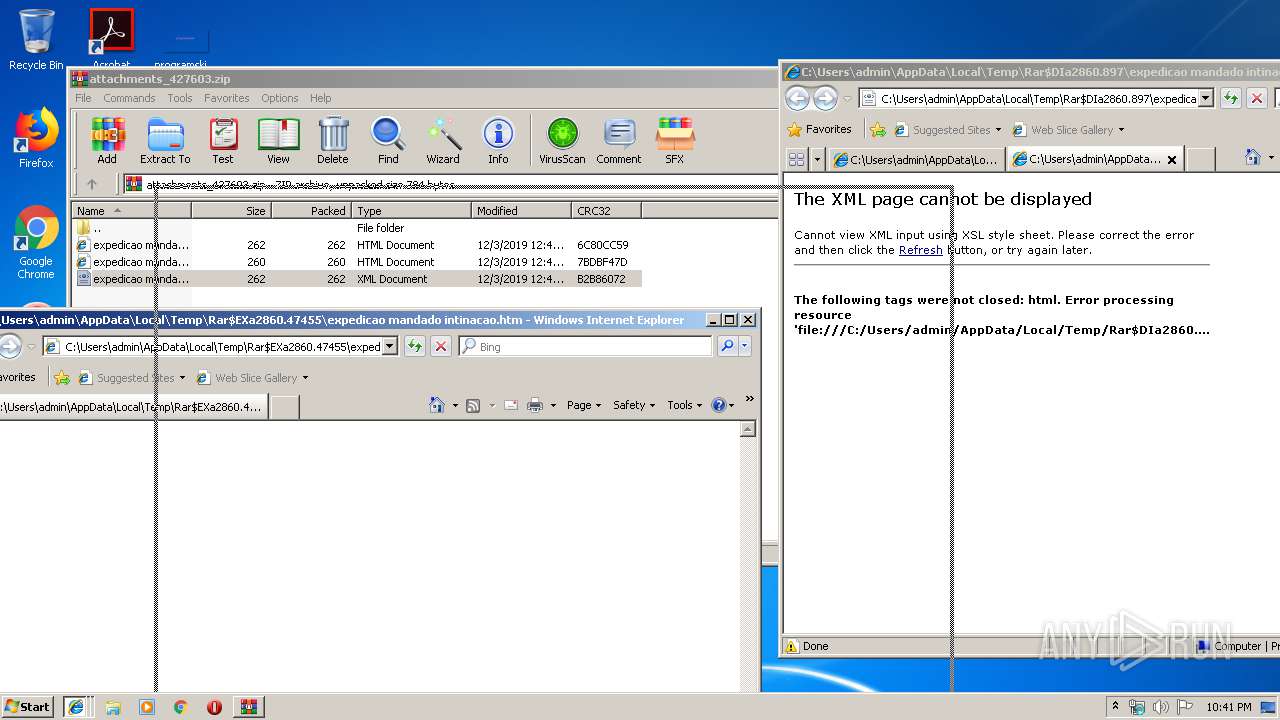
| 3712 | "C:\Program Files\Common Files\Microsoft Shared\OFFICE14\MSOXMLED.EXE" /verb open "C:\Users\admin\AppData\Local\Temp\Rar$DIa2860.897\expedicao mandado intinacao.xml" | C:\Program Files\Common Files\Microsoft Shared\OFFICE14\MSOXMLED.EXE | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: XML Editor Exit code: 0 Version: 14.0.4750.1000 Modules
| |||||||||||||||
| 3792 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3188 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4080 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\admin\AppData\Local\Temp\Rar$EXa2860.47455\expedicao mandado intinacao.htm | C:\Program Files\Internet Explorer\iexplore.exe | WinRAR.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 661
Read events
1 470
Write events
190
Delete events
1
Modification events
| (PID) Process: | (2860) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2860) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2860) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2860) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\NetworkExplorer.dll,-1 |
Value: Network | |||
| (PID) Process: | (2860) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\attachments_427603.zip | |||
| (PID) Process: | (2860) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2860) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2860) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2860) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2860) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\ieframe.dll,-912 |
Value: HTML Document | |||
Executable files
0
Suspicious files
0
Text files
24
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3188 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Temporary Internet Files\Content.IE5\4UCZJNQV\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3188 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 4080 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 4080 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2132 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\jquery.min[1].php | — | |
MD5:— | SHA256:— | |||
| 2860 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2860.47452\expedicao mandado intinacao.xml | html | |
MD5:— | SHA256:— | |||
| 2860 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2860.47455\expedicao mandado intinacao.xml | html | |
MD5:— | SHA256:— | |||
| 2860 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2860.47452\expedicao mandado intinacao.htm | html | |
MD5:— | SHA256:— | |||
| 2860 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2860.47452\expedicao mandado intinacao.html | html | |
MD5:— | SHA256:— | |||
| 2860 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2860.47455\expedicao mandado intinacao.html | html | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
11
DNS requests
6
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3792 | iexplore.exe | GET | — | 104.28.20.217:80 | http://wtei4u6v3a85.uk82ury478fjdi92w.cf/jquery.min.php | US | — | — | suspicious |
3792 | iexplore.exe | GET | 200 | 104.31.91.216:80 | http://cea2ruwka9h.ax23ftw745kvb09s.tk/jquery.min.php | US | text | 632 b | suspicious |
3188 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4080 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3188 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3792 | iexplore.exe | 172.217.22.106:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
2132 | iexplore.exe | 172.217.22.106:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
2132 | iexplore.exe | 104.28.21.217:80 | wtei4u6v3a85.uk82ury478fjdi92w.cf | Cloudflare Inc | US | shared |
3792 | iexplore.exe | 104.28.20.217:80 | wtei4u6v3a85.uk82ury478fjdi92w.cf | Cloudflare Inc | US | suspicious |
3792 | iexplore.exe | 104.31.91.216:80 | cea2ruwka9h.ax23ftw745kvb09s.tk | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
wtei4u6v3a85.uk82ury478fjdi92w.cf |
| suspicious |
cea2ruwka9h.ax23ftw745kvb09s.tk |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .cf Domain |
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a .tk domain - Likely Hostile |
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a .tk domain - Likely Hostile |
3792 | iexplore.exe | Potentially Bad Traffic | ET POLICY HTTP Request to a *.tk domain |