| File name: | vs_community__582490270.1543589565.exe |
| Full analysis: | https://app.any.run/tasks/224453dd-d656-49b6-a3b4-85cdcfb04b01 |
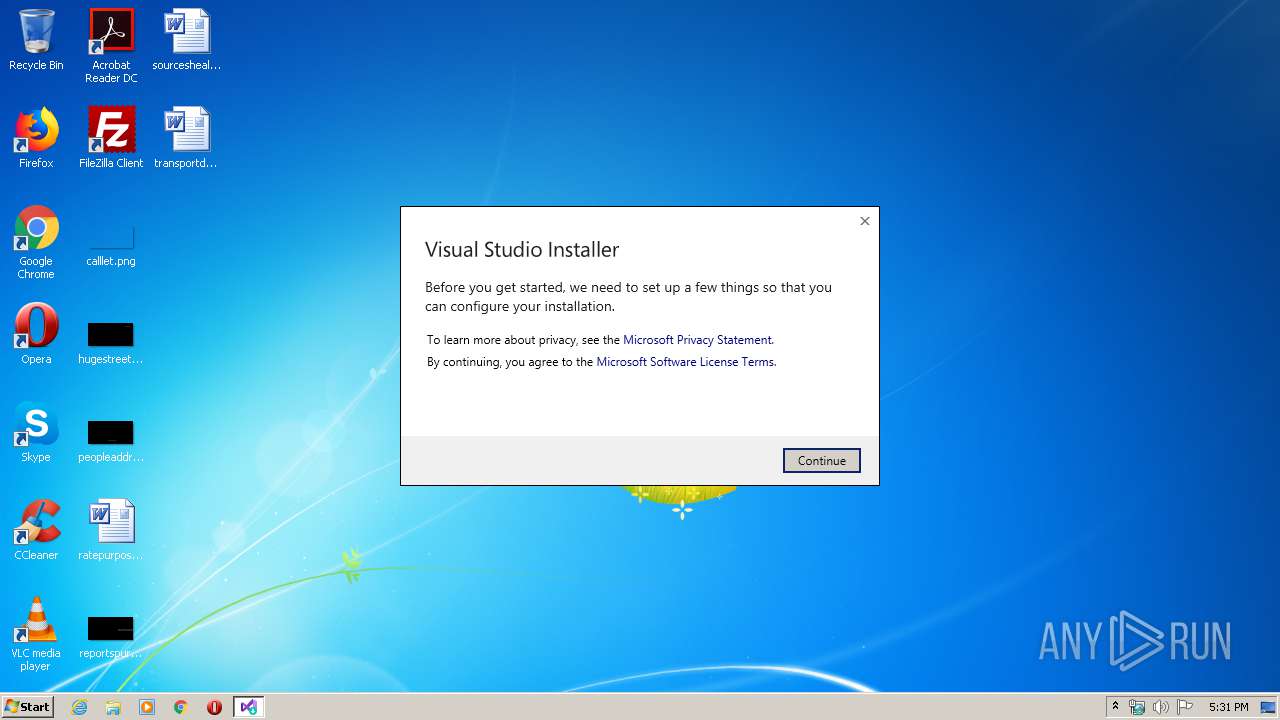
| Verdict: | Malicious activity |
| Analysis date: | February 21, 2020, 17:31:27 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | CAF7131F6CC35996AB8D6E6D21121FAB |
| SHA1: | 7A1CA992015301E0AECE72A019A1BCCB3D2B6648 |
| SHA256: | 8739F26BC097A79F446474BC97F07E75502F3FBAD76633F81121879E03080962 |
| SSDEEP: | 24576:K/2HWxfVfVaerrRs3JafJnYK+cbmlMxq3RkQi4rY0mwXBftjSrTGOA8:u22xfV00RsZ8JV5bcSQTrWcVGF |
MALICIOUS
Loads dropped or rewritten executable
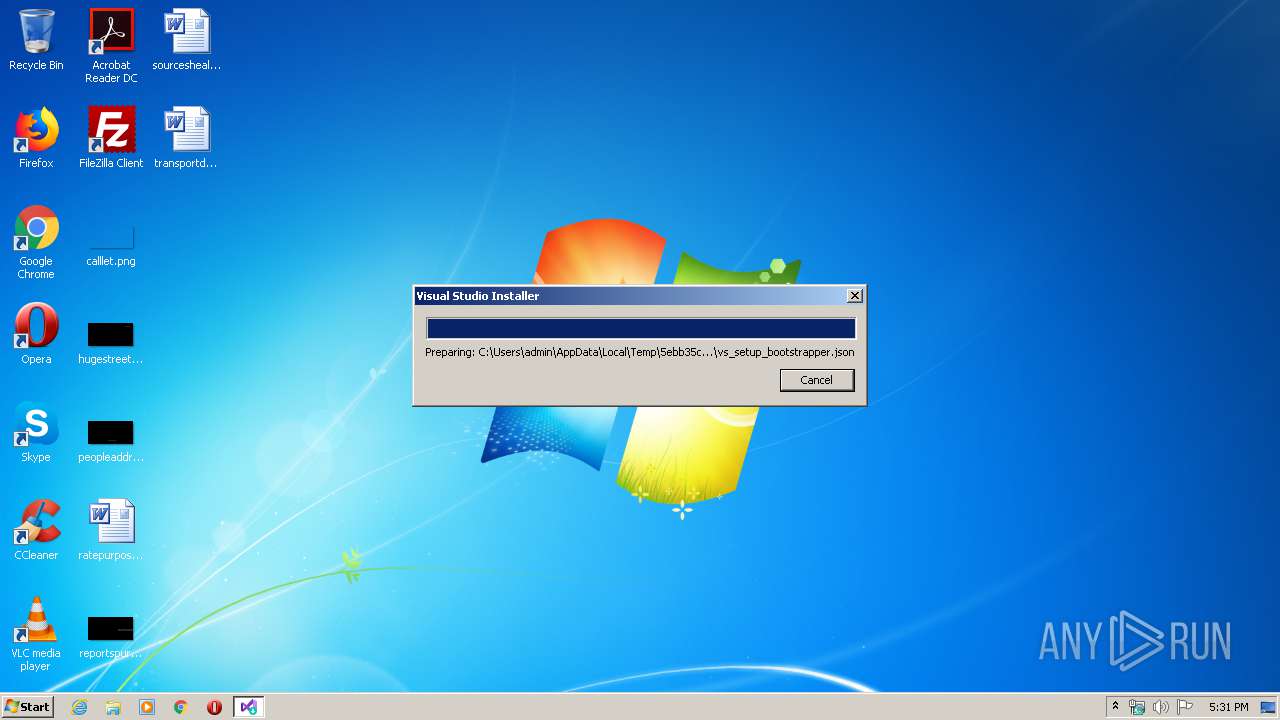
- vs_setup_bootstrapper.exe (PID: 3336)
Application was dropped or rewritten from another process
- vs_setup_bootstrapper.exe (PID: 3336)
Changes settings of System certificates
- vs_setup_bootstrapper.exe (PID: 3336)
SUSPICIOUS
Executable content was dropped or overwritten
- vs_community__582490270.1543589565.exe (PID: 3300)
Creates files in the program directory
- vs_setup_bootstrapper.exe (PID: 3336)
Reads Environment values
- vs_setup_bootstrapper.exe (PID: 3336)
Reads CPU info
- vs_setup_bootstrapper.exe (PID: 3336)
Checks supported languages
- vs_setup_bootstrapper.exe (PID: 3336)
Adds / modifies Windows certificates
- vs_setup_bootstrapper.exe (PID: 3336)
INFO
Reads settings of System Certificates
- vs_setup_bootstrapper.exe (PID: 3336)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:02:27 00:15:42+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 157184 |
| InitializedDataSize: | 104960 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x17fc9 |
| OSVersion: | 5.1 |
| ImageVersion: | 10 |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 16.2.29201.188 |
| ProductVersionNumber: | 16.2.29201.188 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Microsoft Corporation |
| FileDescription: | Visual Studio Installer |
| FileVersion: | 16.2.29201.188 |
| InternalName: | vs_community.exe |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFileName: | vs_community.exe |
| ProductName: | Microsoft Visual Studio Community |
| ProductVersion: | 16.2.29201.188 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 26-Feb-2019 23:15:42 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Microsoft Corporation |
| FileDescription: | Visual Studio Installer |
| FileVersion: | 16.2.29201.188 |
| InternalName: | vs_community.exe |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFilename: | vs_community.exe |
| ProductName: | Microsoft Visual Studio Community |
| ProductVersion: | 16.2.29201.188 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000110 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 26-Feb-2019 23:15:42 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000265DA | 0x00026600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.55151 |
.data | 0x00028000 | 0x00003800 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.59821 |
.idata | 0x0002C000 | 0x00000D58 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.32128 |
.00cfg | 0x0002D000 | 0x00000004 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.0611629 |
.gfids | 0x0002E000 | 0x00000004 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.0611629 |
.boxld01\xb8 | 0x0002F000 | 0x000000B8 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.66528 |
.rsrc | 0x00030000 | 0x000144C4 | 0x00014600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.54374 |
.reloc | 0x00045000 | 0x00002A62 | 0x00002C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 4.85247 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.19777 | 1423 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.24929 | 552 | Latin 1 / Western European | English - United States | RT_STRING |
3 | 4.56189 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 4.62701 | 6760 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 4.81123 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 4.96785 | 2440 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 4.99822 | 1720 | Latin 1 / Western European | English - United States | RT_ICON |
8 | 5.02317 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
32 | 2.08644 | 78 | Latin 1 / Western European | English - United States | RT_STRING |
107 | 2.95799 | 118 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
Imports
ADVAPI32.dll (delay-loaded) |
KERNEL32.dll |
OLEAUT32.dll |
SHLWAPI.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
?dwPlaceholder@@3PAEA | 1 | 0x0002F000 |
_DecodePointerInternal@4 | 2 | 0x0000AA29 |
_EncodePointerInternal@4 | 3 | 0x0000AA0E |
Total processes
42
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2916 | "getmac" | C:\Windows\system32\getmac.exe | — | vs_setup_bootstrapper.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Displays NIC MAC information Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3300 | "C:\Users\admin\AppData\Local\Temp\vs_community__582490270.1543589565.exe" | C:\Users\admin\AppData\Local\Temp\vs_community__582490270.1543589565.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Studio Installer Exit code: 0 Version: 16.2.29201.188 Modules
| |||||||||||||||
| 3336 | "C:\Users\admin\AppData\Local\Temp\5ebb35c6aa38e9191f3e69f91cfa1a\vs_bootstrapper_d15\vs_setup_bootstrapper.exe" --env "_SFX_CAB_EXE_PACKAGE:C:\Users\admin\AppData\Local\Temp\vs_community__582490270.1543589565.exe _SFX_CAB_EXE_ORIGINALWORKINGDIR:C:\Users\admin\AppData\Local\Temp" | C:\Users\admin\AppData\Local\Temp\5ebb35c6aa38e9191f3e69f91cfa1a\vs_bootstrapper_d15\vs_setup_bootstrapper.exe | vs_community__582490270.1543589565.exe | ||||||||||||
User: admin Company: Microsoft Integrity Level: HIGH Description: Visual Studio Installer Exit code: 0 Version: 2.2.3062.31357 Modules
| |||||||||||||||
Total events
2 383
Read events
638
Write events
1 745
Delete events
0
Modification events
| (PID) Process: | (3300) vs_community__582490270.1543589565.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3300) vs_community__582490270.1543589565.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3336) vs_setup_bootstrapper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\vs_setup_bootstrapper_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3336) vs_setup_bootstrapper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\vs_setup_bootstrapper_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3336) vs_setup_bootstrapper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\vs_setup_bootstrapper_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3336) vs_setup_bootstrapper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\vs_setup_bootstrapper_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3336) vs_setup_bootstrapper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\vs_setup_bootstrapper_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3336) vs_setup_bootstrapper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\vs_setup_bootstrapper_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (3336) vs_setup_bootstrapper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\vs_setup_bootstrapper_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3336) vs_setup_bootstrapper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\vs_setup_bootstrapper_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
22
Suspicious files
0
Text files
40
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3300 | vs_community__582490270.1543589565.exe | C:\Users\admin\AppData\Local\Temp\5ebb35c6aa38e9191f3e69f91cfa1a\vs_bootstrapper_d15\Microsoft.VisualStudio.Setup.Download.dll | executable | |
MD5:— | SHA256:— | |||
| 3300 | vs_community__582490270.1543589565.exe | C:\Users\admin\AppData\Local\Temp\5ebb35c6aa38e9191f3e69f91cfa1a\vs_bootstrapper_d15\HelpFile\3082\help.html | html | |
MD5:826BE401E28B2BEEE0E3B8C44095AE3E | SHA256:B5F180DB33609AEA3263816A3F8D273192D73126323D400BF2E6A8F006896857 | |||
| 3300 | vs_community__582490270.1543589565.exe | C:\Users\admin\AppData\Local\Temp\5ebb35c6aa38e9191f3e69f91cfa1a\vs_bootstrapper_d15\HelpFile\1046\help.html | html | |
MD5:8A40B9D3D347E5E5E97B9D7E17006577 | SHA256:3ADFF0EEE03C23C714411D8CF96A560A7F4B89EB74CB0420862C99C90DC256FE | |||
| 3300 | vs_community__582490270.1543589565.exe | C:\Users\admin\AppData\Local\Temp\5ebb35c6aa38e9191f3e69f91cfa1a\vs_bootstrapper_d15\Microsoft.VisualStudio.RemoteControl.dll | executable | |
MD5:— | SHA256:— | |||
| 3300 | vs_community__582490270.1543589565.exe | C:\Users\admin\AppData\Local\Temp\5ebb35c6aa38e9191f3e69f91cfa1a\vs_bootstrapper_d15\Microsoft.VisualStudio.Setup.Common.dll | executable | |
MD5:— | SHA256:— | |||
| 3300 | vs_community__582490270.1543589565.exe | C:\Users\admin\AppData\Local\Temp\5ebb35c6aa38e9191f3e69f91cfa1a\vs_bootstrapper_d15\vs_setup_bootstrapper.exe | executable | |
MD5:— | SHA256:— | |||
| 3300 | vs_community__582490270.1543589565.exe | C:\Users\admin\AppData\Local\Temp\5ebb35c6aa38e9191f3e69f91cfa1a\vs_bootstrapper_d15\HelpFile\2052\help.html | html | |
MD5:64A67F7C1382E29E228C07FC5EE9C5D2 | SHA256:D0073D777B258374E6CFD2CCD9EBE89D1FA0A0C7DE74CC7CE8FF163823FCE414 | |||
| 3300 | vs_community__582490270.1543589565.exe | C:\Users\admin\AppData\Local\Temp\5ebb35c6aa38e9191f3e69f91cfa1a\vs_bootstrapper_d15\HelpFile\1029\help.html | html | |
MD5:B2253798761C179BBF7426DA5A705F2B | SHA256:BDDD5A3295325FE67F0AF2F677A3F12BB7360460EA777D561B06810CE321D4E4 | |||
| 3300 | vs_community__582490270.1543589565.exe | C:\Users\admin\AppData\Local\Temp\5ebb35c6aa38e9191f3e69f91cfa1a\vs_bootstrapper_d15\HelpFile\1040\help.html | html | |
MD5:2C2C6549E9DCA6D00825B1FF78F08BB7 | SHA256:6354092ACDF3A3BEF63366B84E641E8362B15F63EDD198E817D315E35423A2B6 | |||
| 3300 | vs_community__582490270.1543589565.exe | C:\Users\admin\AppData\Local\Temp\5ebb35c6aa38e9191f3e69f91cfa1a\vs_bootstrapper_d15\HelpFile\1028\help.html | html | |
MD5:E4470787BD74BBCCC17CB551EC2BE909 | SHA256:A1812D2A4F939FD486EDB515535457A989366AB7B1446752D7CCCEAC11DCD3FD | |||
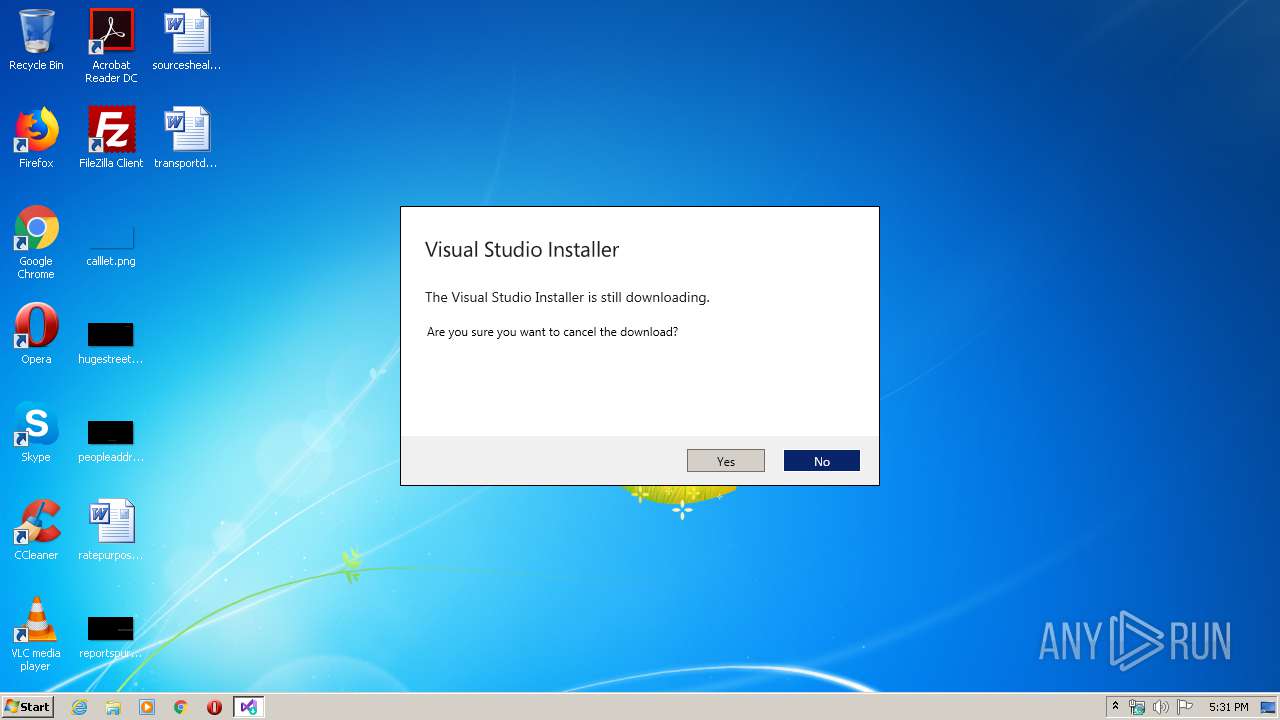
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
10
DNS requests
9
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3336 | vs_setup_bootstrapper.exe | 152.199.19.161:443 | az700632.vo.msecnd.net | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3336 | vs_setup_bootstrapper.exe | 104.211.92.54:443 | dc.services.visualstudio.com | Microsoft Corporation | IN | unknown |
3336 | vs_setup_bootstrapper.exe | 111.221.29.254:443 | vortex.data.microsoft.com | Microsoft Corporation | HK | whitelisted |
3336 | vs_setup_bootstrapper.exe | 104.109.82.33:443 | aka.ms | Akamai International B.V. | NL | unknown |
3336 | vs_setup_bootstrapper.exe | 68.232.34.200:443 | download.visualstudio.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3336 | vs_setup_bootstrapper.exe | 104.214.77.221:443 | targetednotifications-tm.trafficmanager.net | Microsoft Corporation | US | whitelisted |
3336 | vs_setup_bootstrapper.exe | 92.123.10.235:443 | go.microsoft.com | Telia Company AB | FR | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
az700632.vo.msecnd.net |
| whitelisted |
az667904.vo.msecnd.net |
| whitelisted |
go.microsoft.com |
| whitelisted |
aka.ms |
| whitelisted |
targetednotifications-tm.trafficmanager.net |
| suspicious |
download.visualstudio.microsoft.com |
| whitelisted |
vortex.data.microsoft.com |
| whitelisted |
dc.services.visualstudio.com |
| whitelisted |