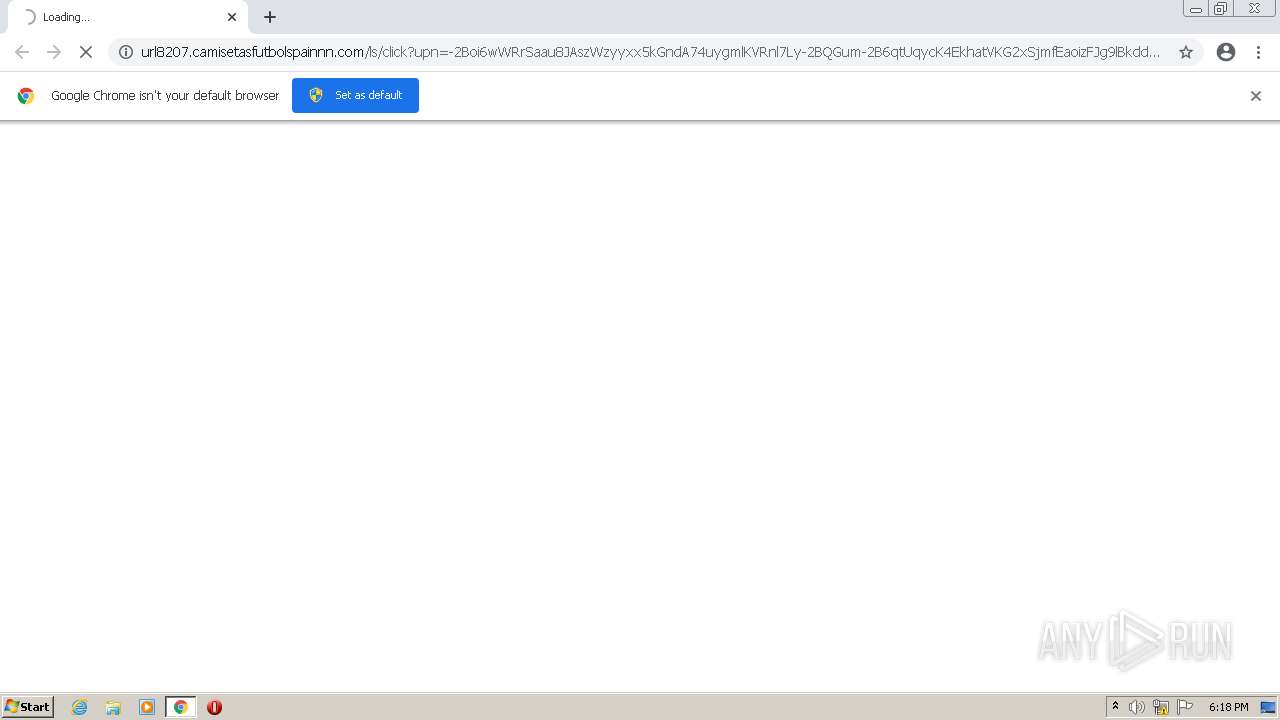
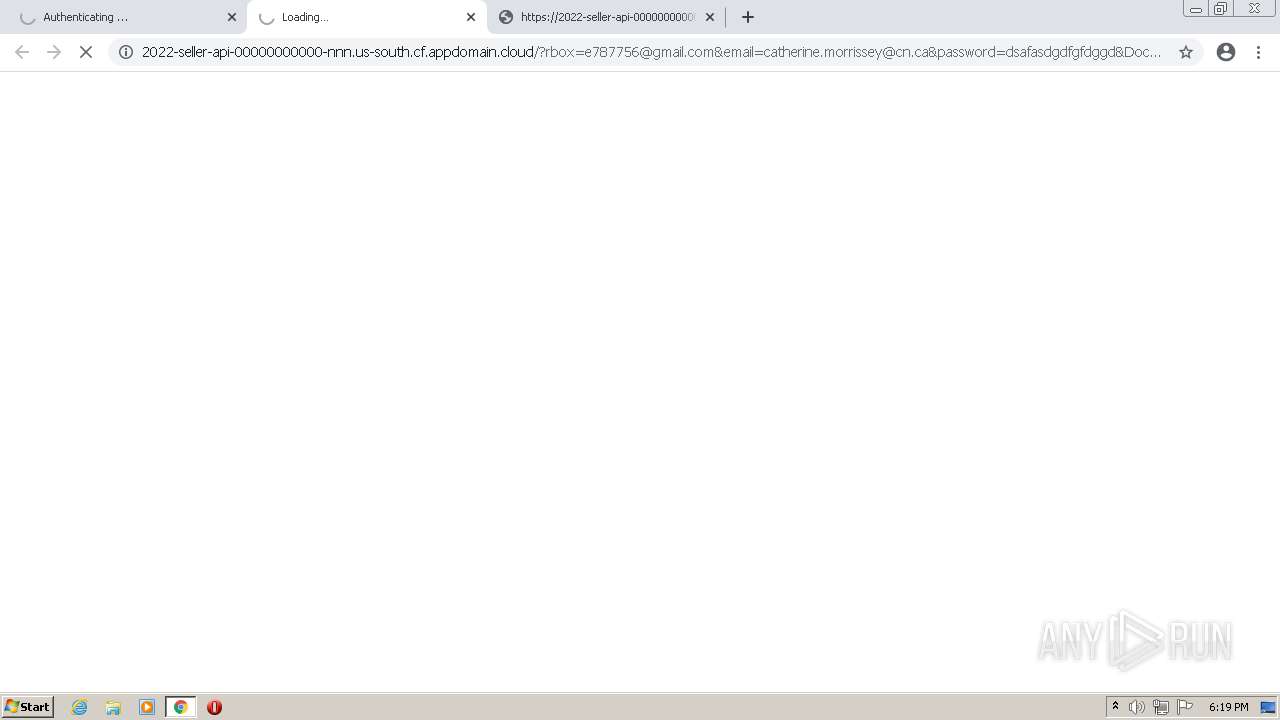
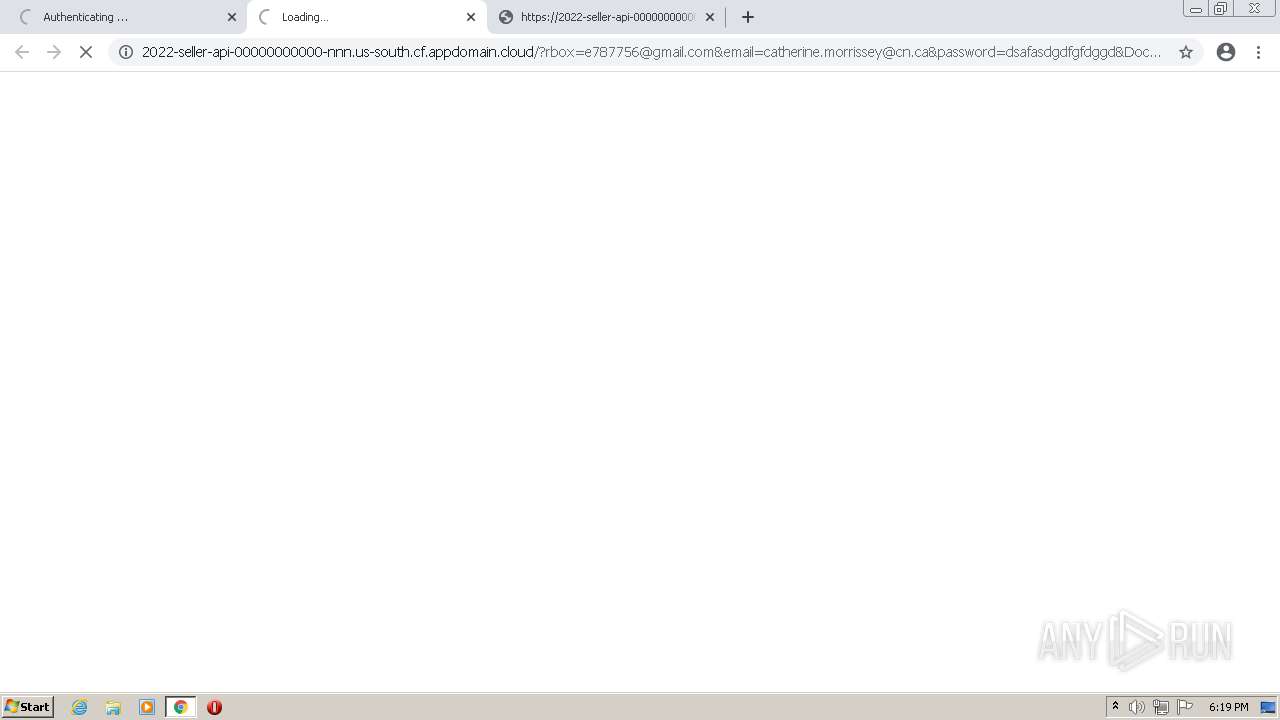
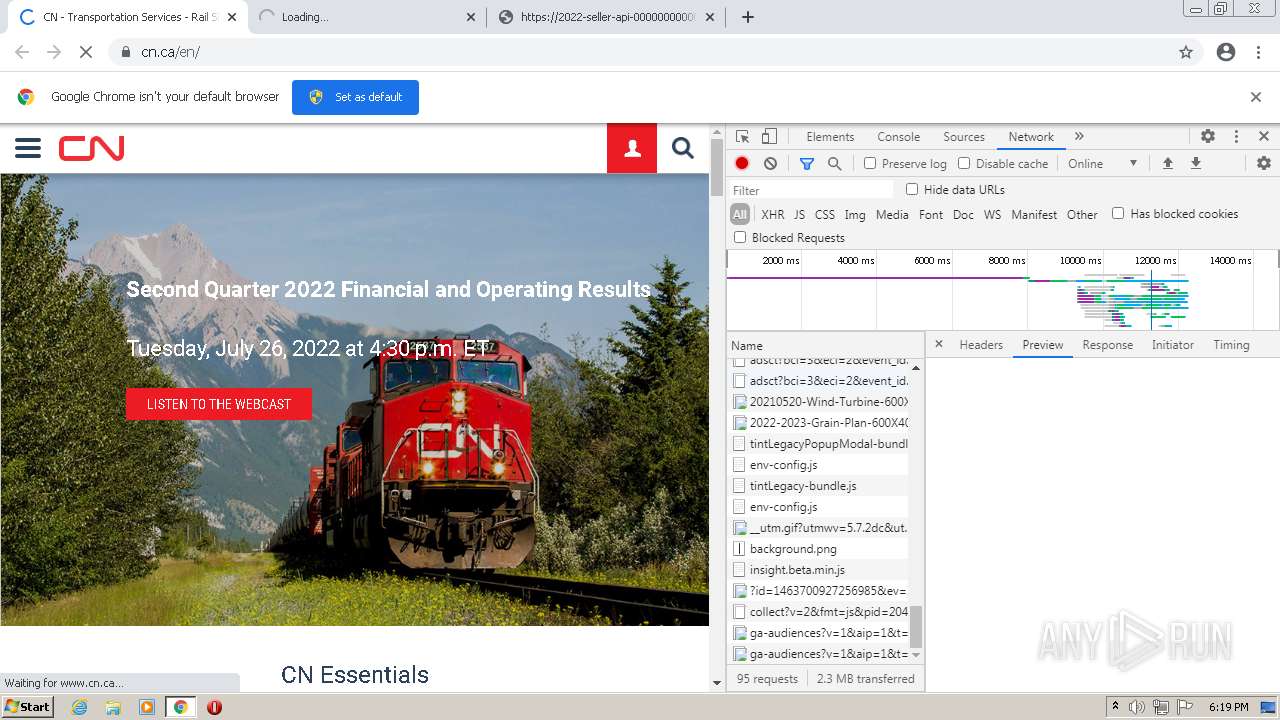
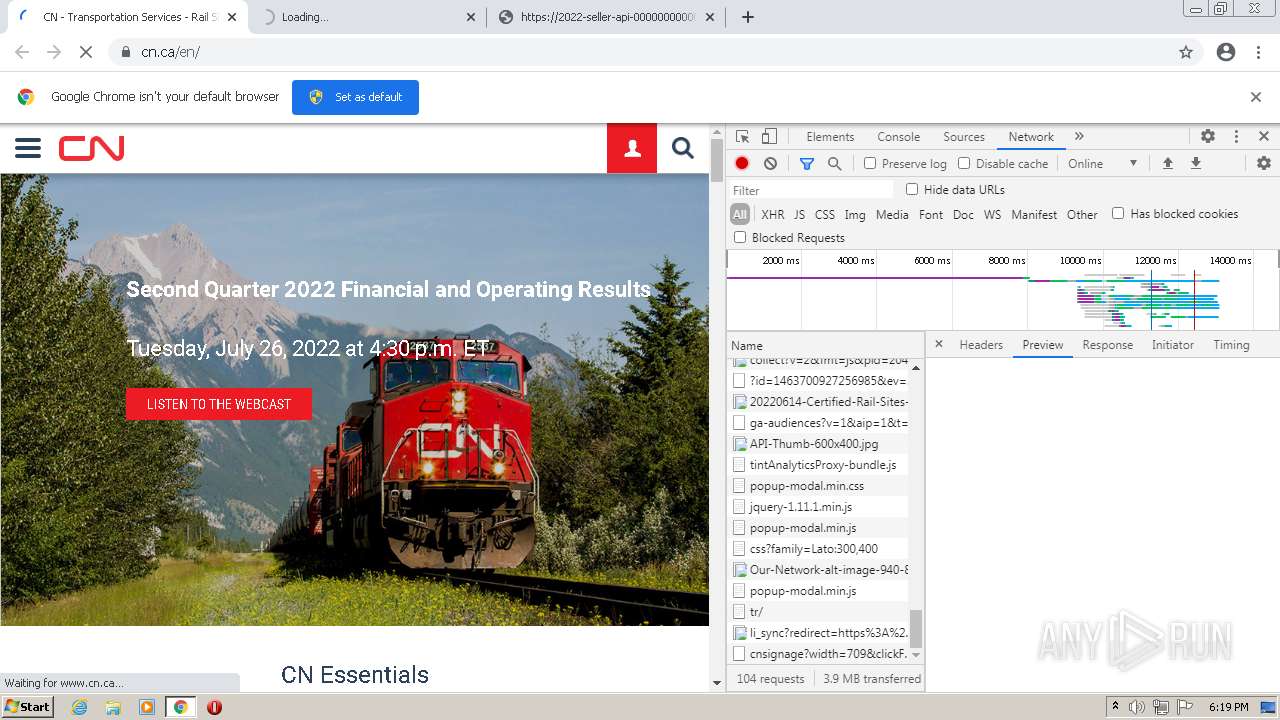
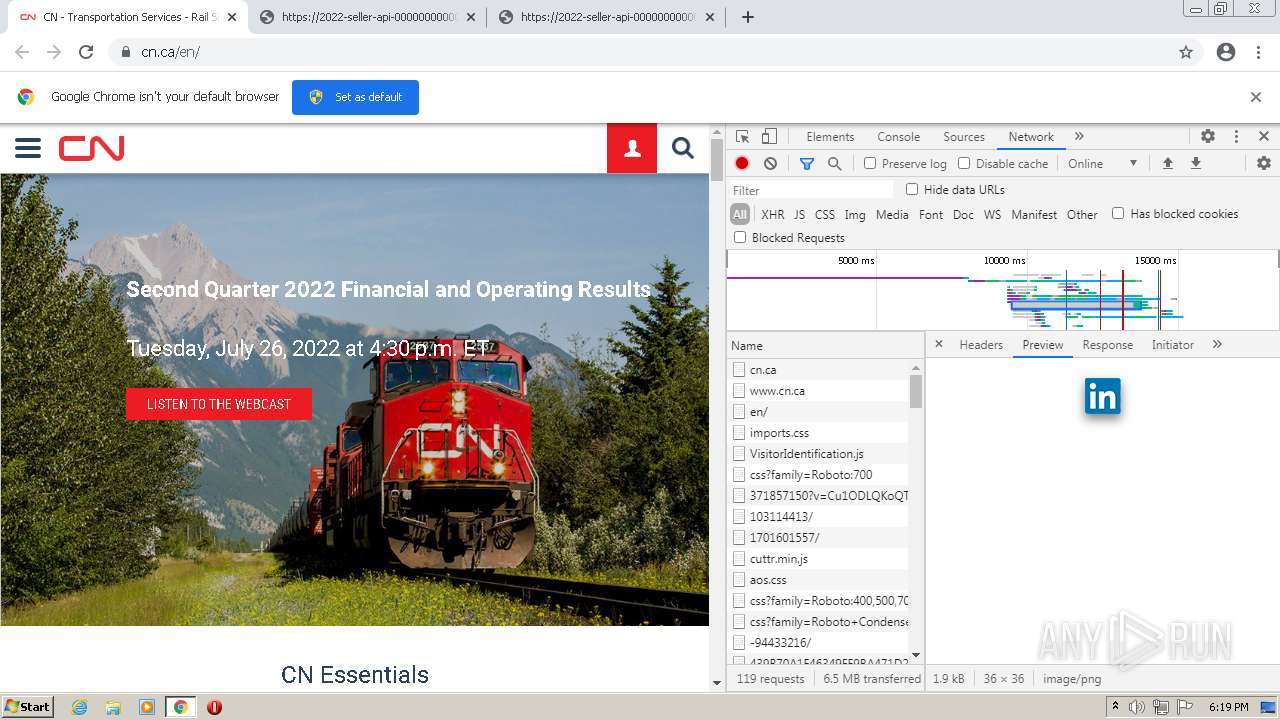
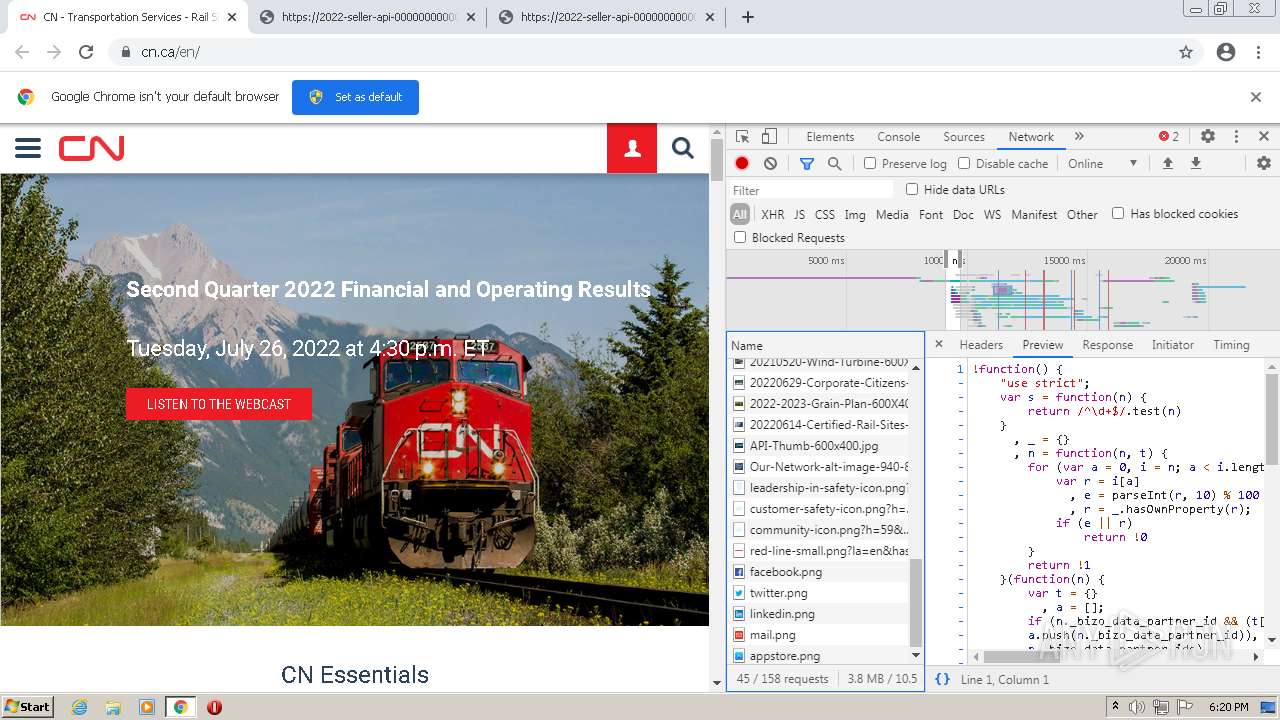
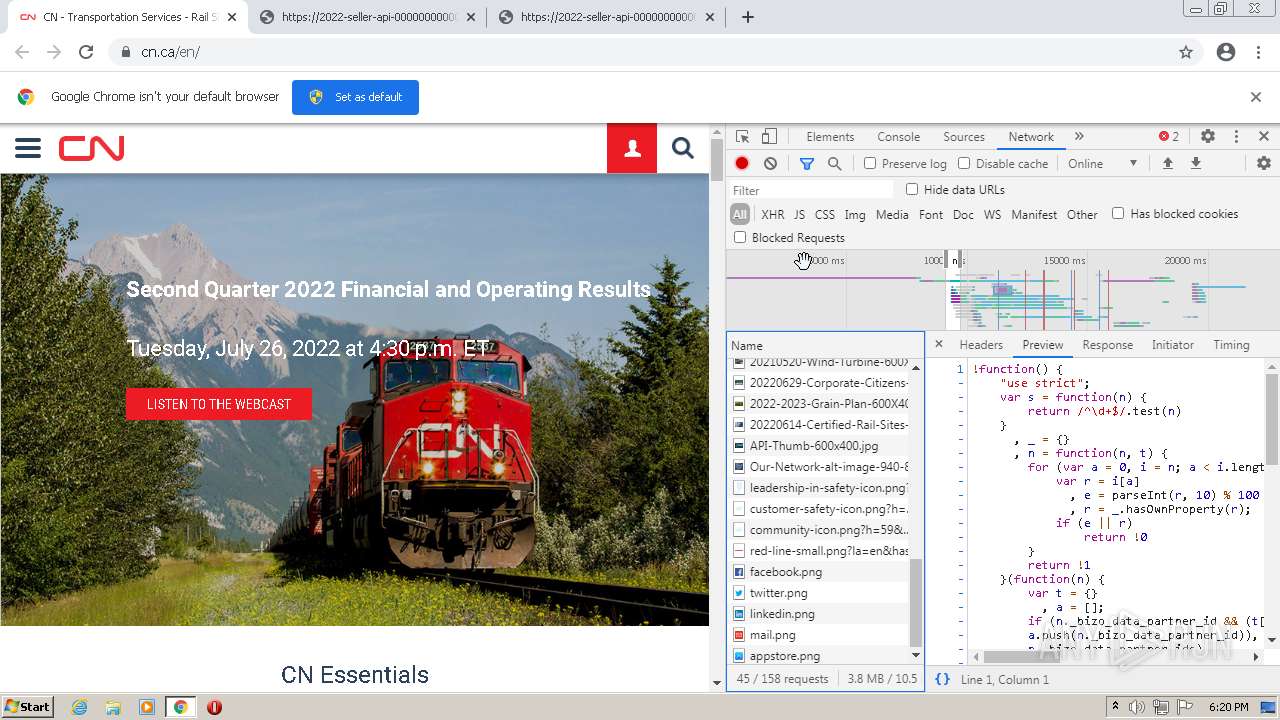
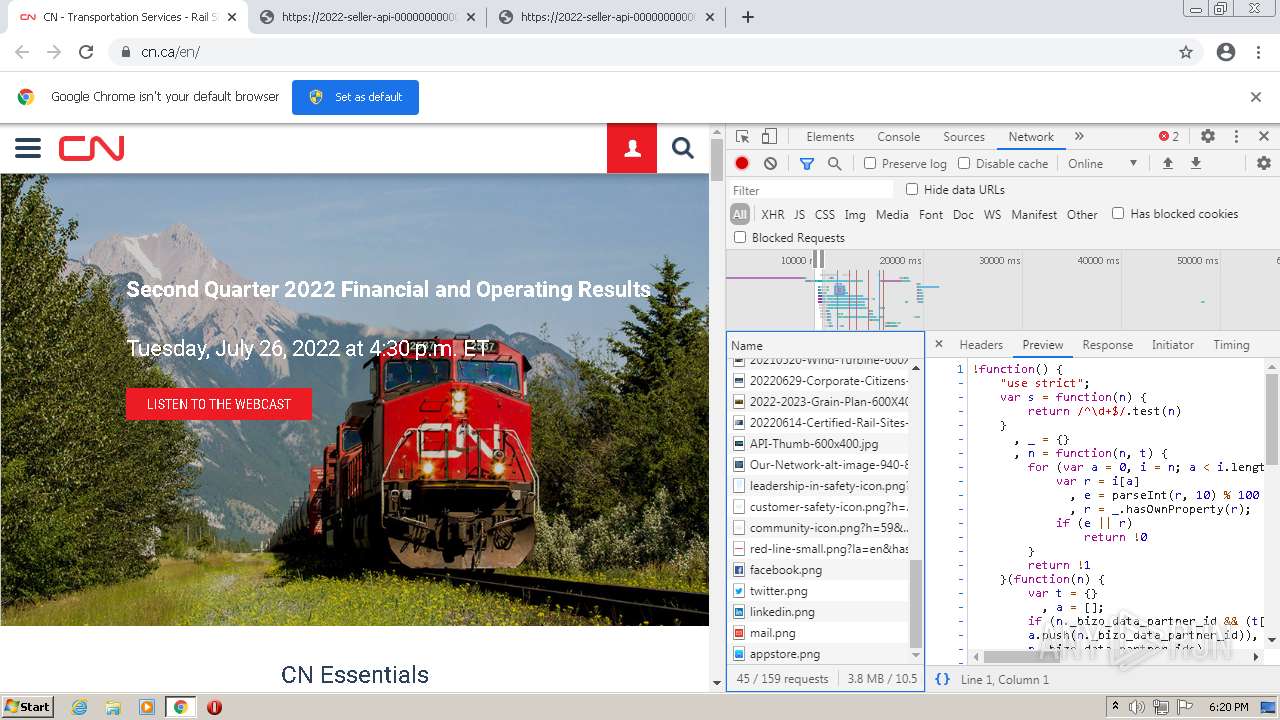
| URL: | http://url8207.camisetasfutbolspainnn.com/ls/click?upn=-2Boi6wWRrSaau8JAszWzyyxx5kGndA74uygmlKVRnl7Ly-2BQGum-2B6qtUqycK4EkhatVKG2xSjmfEaoizFJg9lBkdd8-2FDAkBZyPXAvcpv7qW3mWeH0GeDfucg5rfCX7bq57z8e4Nl3CP3d9aB1eG-2FP3p4m-2FQ7GFyhIfSOCXhCwlGtuNWB94g2YJK081zZeuLXvoFe4YO-2FXIvqiwEG0Ad2IXc1i2zPQcDJ-2BTUUWf0K8pECNfo5WYegmmIfElT7oJ-2BU8gmeEw7cvLhroZSAf4UW3wuVVkQB4csp7u8Jw66MW3zWkJWijcl8eOXPg3NkyqSvPqwCW0yr8g-2Ba0G6KqH6JA6jtIOybVq0iELjhYrZtbRckWvlIk3R78p-2B5PkJSESyFVrG2cNOxlkOg-2B7WnrM7p7gruip-2FBMaBXxpyfyx-2FX1rqjFCyAois4rQrooxse0oErySEn8hU5U-2FBfdoOBoafzmGewcTC8a7kZBKN2O9Cy8CgkuYOsKxKTfgKywq5cmcw7vvLX6g9c8ahphnWKzbNqQbf5-2FtXAdPiBSbYCMYPiPOwVtZMcUdSjIjZ6xqi-2B5o-2F0LNtMcsGwfxr9YnFBbnjRqyQg-3D-3D0gGx_DDU7xl9rzvyPQyt3hm-2Fav1X6wl-2BLoScaqQCO0i0HuHuzKz-2BFeMoRFss6CEklzykJl66Dn0rOcr8n4UFWm0PNFrIuJ1uLwbXnzzOsYfR3aCQolx9Vw8aYFvXFS7GQxqrgGRxyttBgmC6nIB7l29s4HC3OuVDzE4L9pTrhzyeglcy9f6tMIfT8-2BQuY34rYNXpDVHZggZzxYBdsSUwLdISUBV5a1M9paikhTgHyht72aos-3D |
| Full analysis: | https://app.any.run/tasks/bc868946-fc7b-44af-bd65-c472d9f84691 |
| Verdict: | Malicious activity |
| Analysis date: | August 12, 2022, 17:18:18 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | CFBFE50934B38858FAFF99D4DDF31CD9 |
| SHA1: | 63C48BFCA3D54EBCBE5A2611632D555385F96ED6 |
| SHA256: | 872A53056D9BF77EB4CC2D8CF992D6FC751EFB9A39843040CA0C6FB6853F66D2 |
| SSDEEP: | 24:8H/q9XrovFnYjusovgXEpW/Vjphh7O6dp8d1MkdOFt:8fq97ohYi1vgXlVlT9dp8ckUL |
MALICIOUS
Drops executable file immediately after starts
- chrome.exe (PID: 2732)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 3476)
Drops a file with a compile date too recent
- chrome.exe (PID: 2732)
Executable content was dropped or overwritten
- chrome.exe (PID: 2732)
INFO
Checks supported languages
- chrome.exe (PID: 3476)
- chrome.exe (PID: 1484)
- chrome.exe (PID: 1032)
- chrome.exe (PID: 2732)
- chrome.exe (PID: 2740)
- chrome.exe (PID: 1372)
- chrome.exe (PID: 1368)
- chrome.exe (PID: 3068)
- chrome.exe (PID: 1940)
- chrome.exe (PID: 3636)
- chrome.exe (PID: 416)
- chrome.exe (PID: 3648)
- chrome.exe (PID: 2560)
- chrome.exe (PID: 3564)
- chrome.exe (PID: 120)
- chrome.exe (PID: 1376)
- chrome.exe (PID: 1848)
- chrome.exe (PID: 2768)
- chrome.exe (PID: 3032)
- chrome.exe (PID: 1000)
- chrome.exe (PID: 3220)
- chrome.exe (PID: 3156)
- chrome.exe (PID: 3440)
- chrome.exe (PID: 2732)
- chrome.exe (PID: 3860)
Reads the computer name
- chrome.exe (PID: 3476)
- chrome.exe (PID: 1484)
- chrome.exe (PID: 1372)
- chrome.exe (PID: 1368)
- chrome.exe (PID: 3636)
- chrome.exe (PID: 3564)
- chrome.exe (PID: 2560)
- chrome.exe (PID: 1848)
Application launched itself
- chrome.exe (PID: 3476)
Reads settings of System Certificates
- chrome.exe (PID: 1372)
Reads the date of Windows installation
- chrome.exe (PID: 3564)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
60
Monitored processes
25
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 120 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1068,6709775911954246668,6484311519900221412,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2772 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 416 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1068,6709775911954246668,6484311519900221412,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3064 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1000 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1068,6709775911954246668,6484311519900221412,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=1884 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1032 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=86.0.4240.198 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6e9ad988,0x6e9ad998,0x6e9ad9a4 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1368 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1068,6709775911954246668,6484311519900221412,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgACAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --use-gl=swiftshader-webgl --mojo-platform-channel-handle=1140 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1372 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --field-trial-handle=1068,6709775911954246668,6484311519900221412,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --mojo-platform-channel-handle=1248 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1376 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1068,6709775911954246668,6484311519900221412,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=14 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=624 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1484 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1068,6709775911954246668,6484311519900221412,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgACAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --mojo-platform-channel-handle=1052 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1848 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1068,6709775911954246668,6484311519900221412,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3092 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1940 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1068,6709775911954246668,6484311519900221412,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=11 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3052 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
13 339
Read events
13 233
Write events
101
Delete events
5
Modification events
| (PID) Process: | (3476) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3476) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3476) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3476) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3476) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3476) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3476) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3476) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3476) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (3476) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
1
Suspicious files
29
Text files
124
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3476 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-62F68B5E-D94.pma | — | |
MD5:— | SHA256:— | |||
| 3476 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 3476 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\705998e1-2f16-4c0f-aada-c699b047fe19.tmp | text | |
MD5:— | SHA256:— | |||
| 3476 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 3476 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFcd7d7.TMP | text | |
MD5:936EB7280DA791E6DD28EF3A9B46D39C | SHA256:CBAF2AFD831B32F6D1C12337EE5D2F090D6AE1F4DCB40B08BEF49BF52AD9721F | |||
| 3476 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:7721CDA9F5B73CE8A135471EB53B4E0E | SHA256:DD730C576766A46FFC84E682123248ECE1FF1887EC0ACAB22A5CE93A450F4500 | |||
| 3476 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RFcd7f6.TMP | text | |
MD5:81F483F77EE490F35306A4F94DB2286B | SHA256:82434CE3C9D13F509EBEEBE3A7A1A1DE9AB4557629D9FC855761E0CFA45E8BCE | |||
| 3476 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old~RFcd94e.TMP | text | |
MD5:109A25C32EE1132ECD6D9F3ED9ADF01A | SHA256:DA6028DB9485C65E683643658326F02B1D0A1566DE14914EF28E5248EB94F0DD | |||
| 3476 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFcd7e7.TMP | text | |
MD5:64AD8ED3E666540337BA541C549F72F7 | SHA256:BECBDB08B5B37D203A85F2E974407334053BB1D2270F0B3C9A4DB963896F2206 | |||
| 3476 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
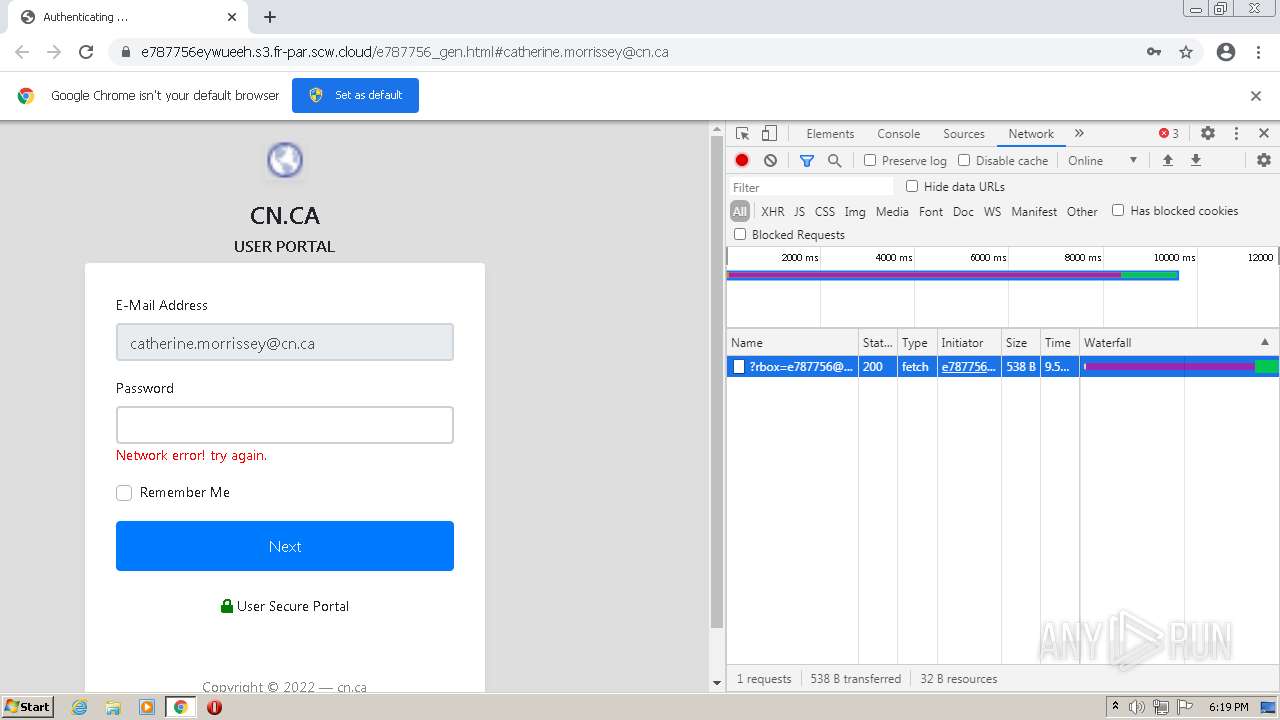
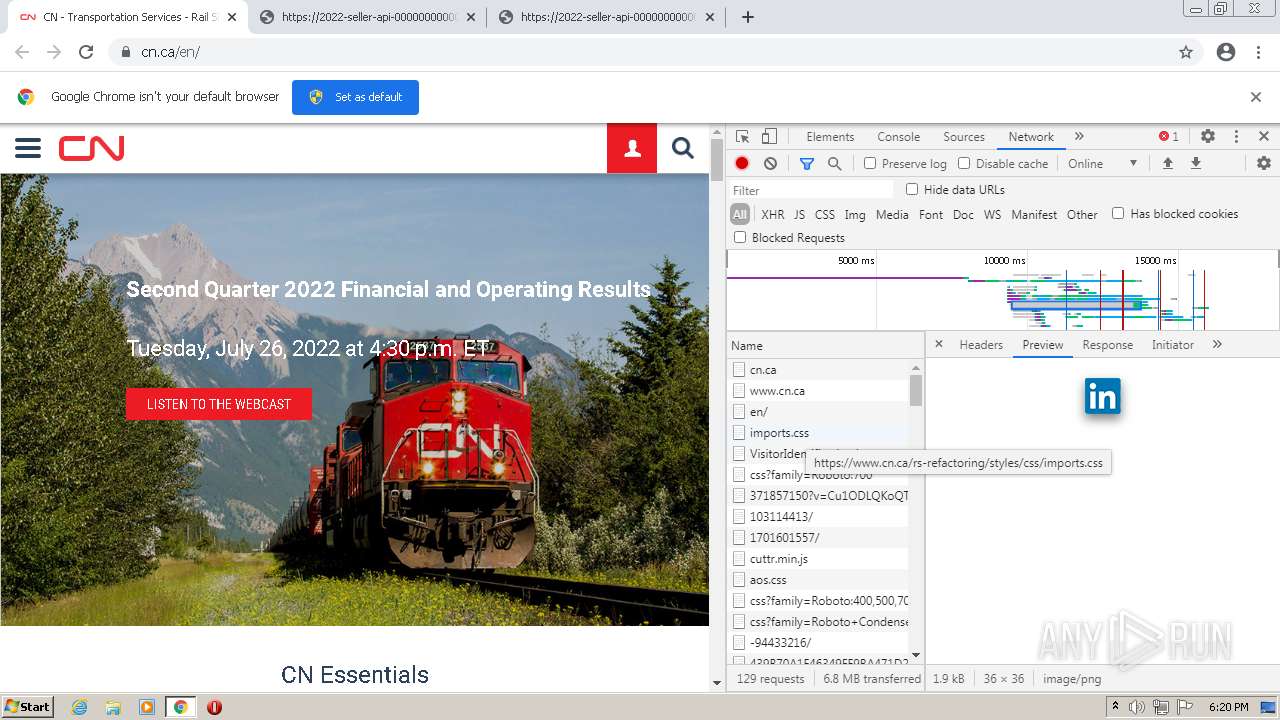
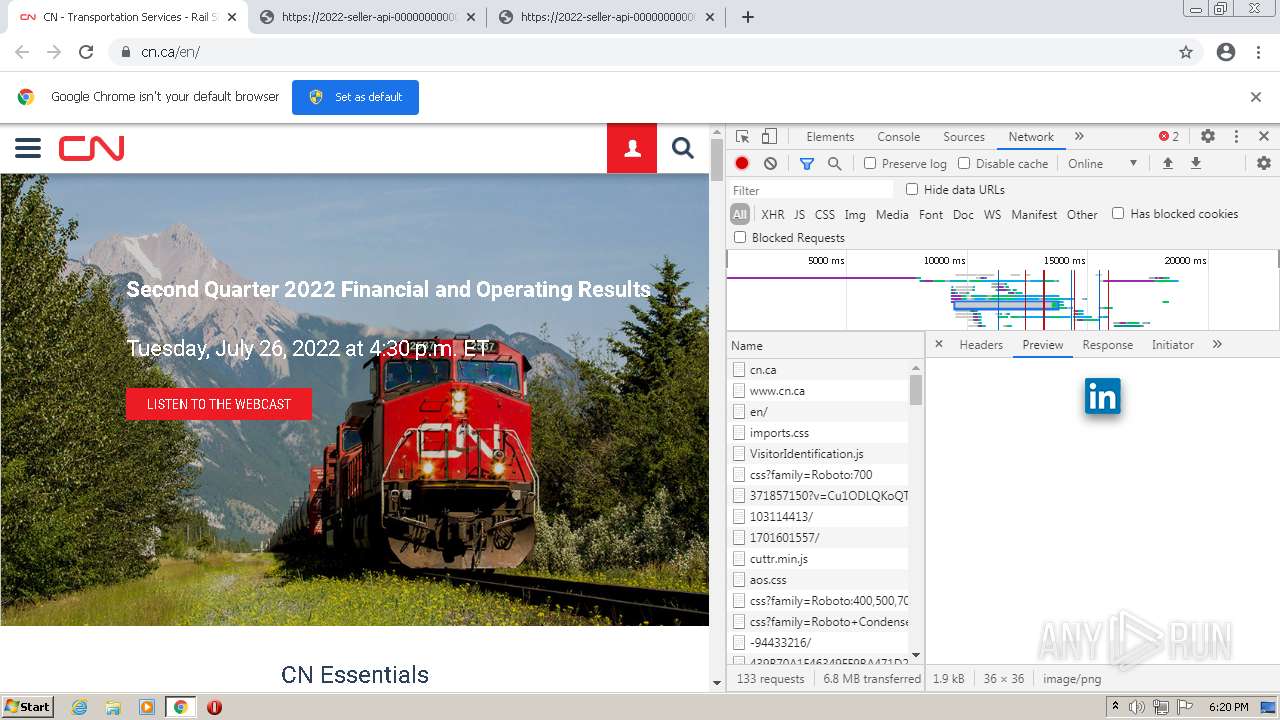
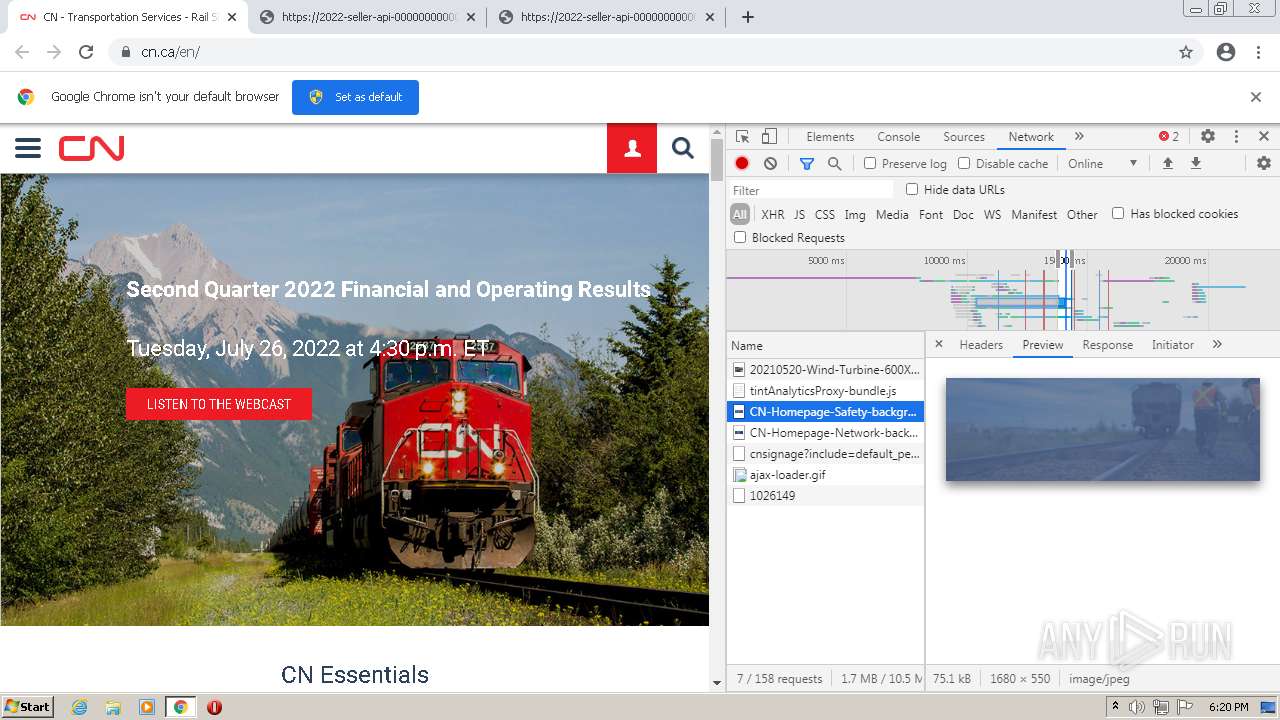
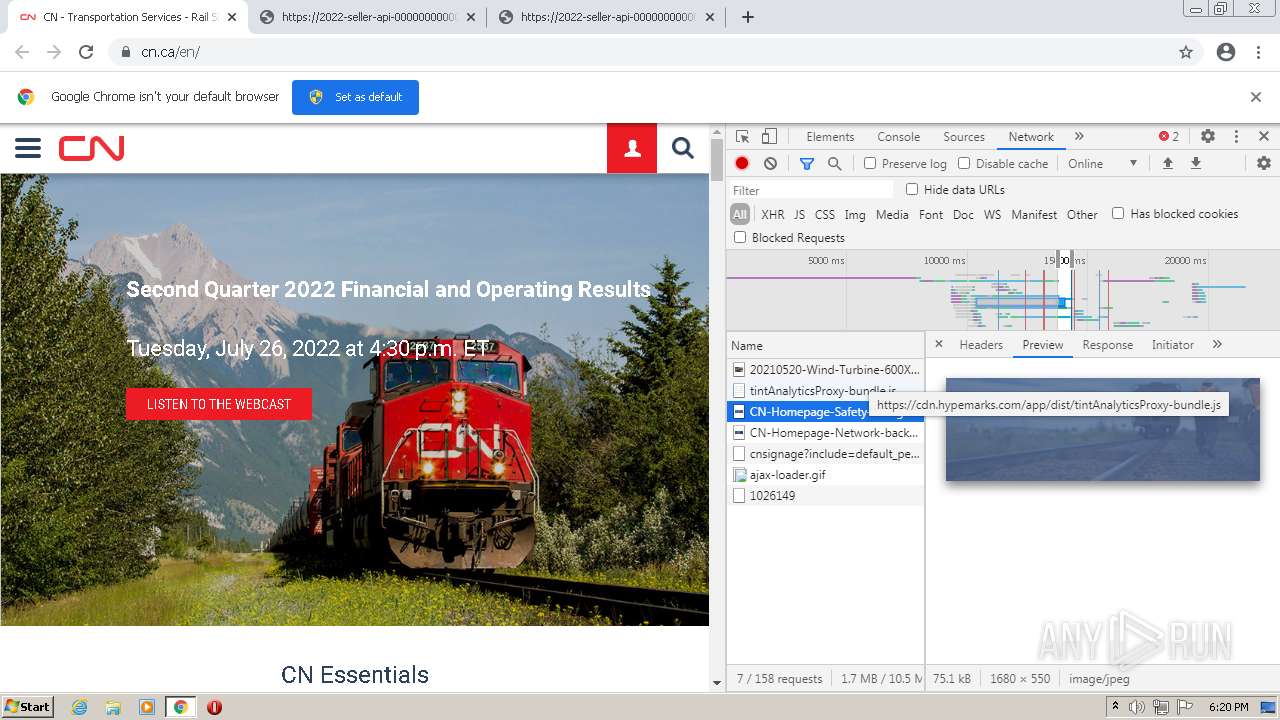
HTTP(S) requests
37
TCP/UDP connections
100
DNS requests
55
Threats
2
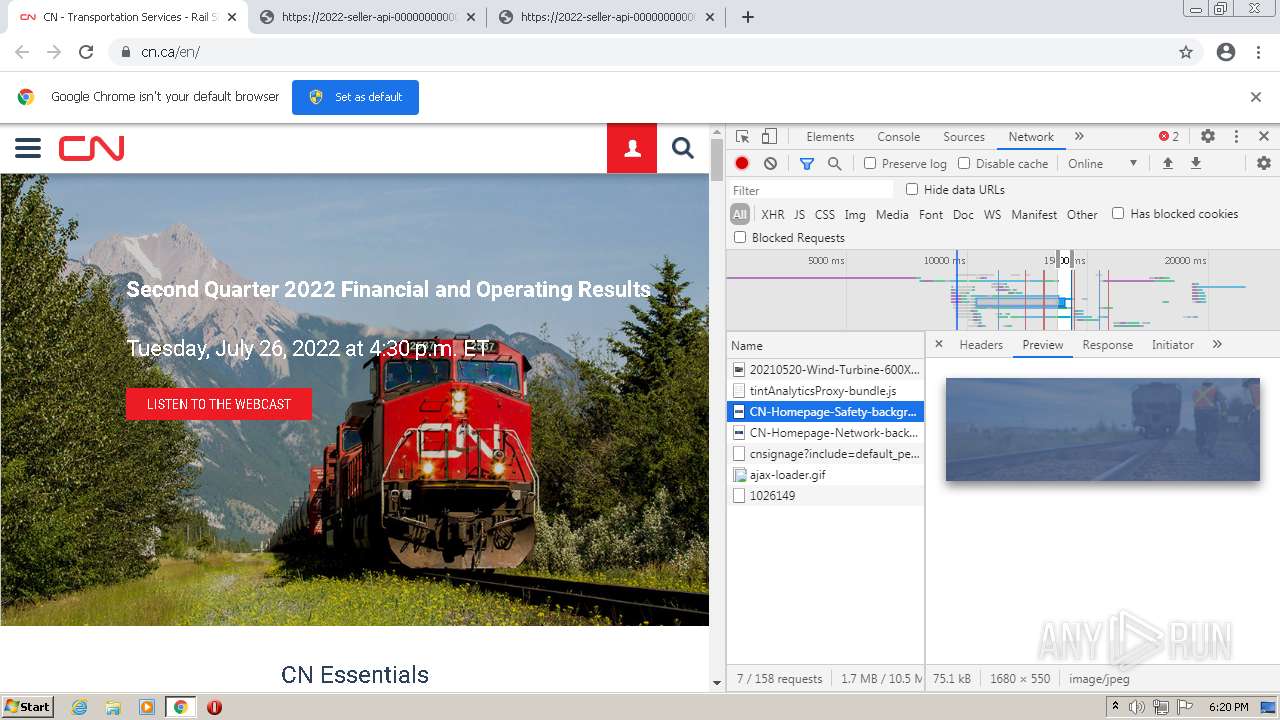
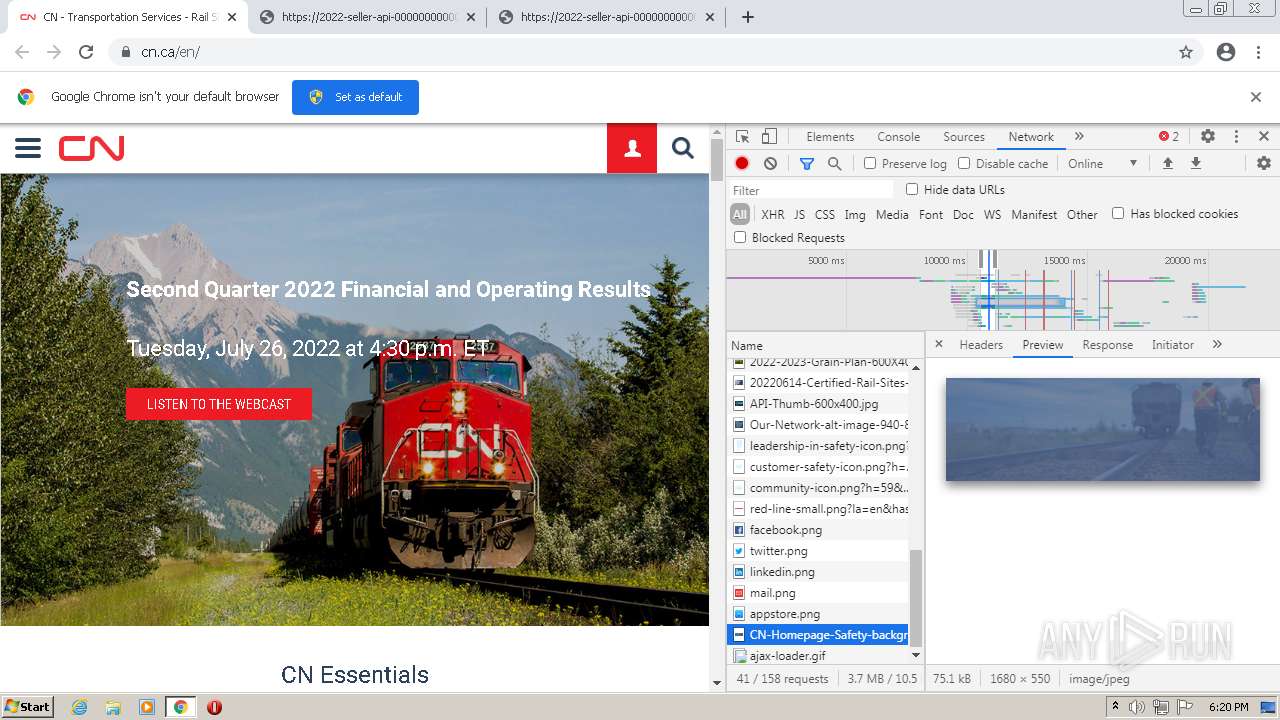
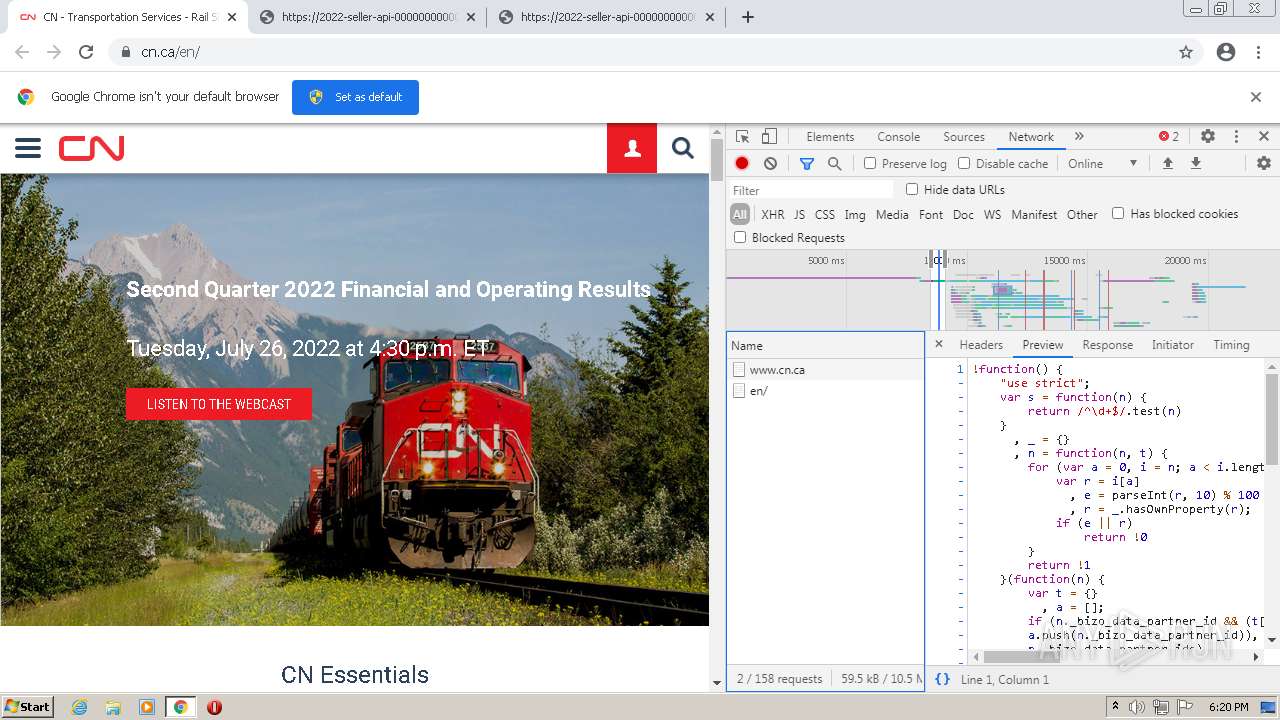
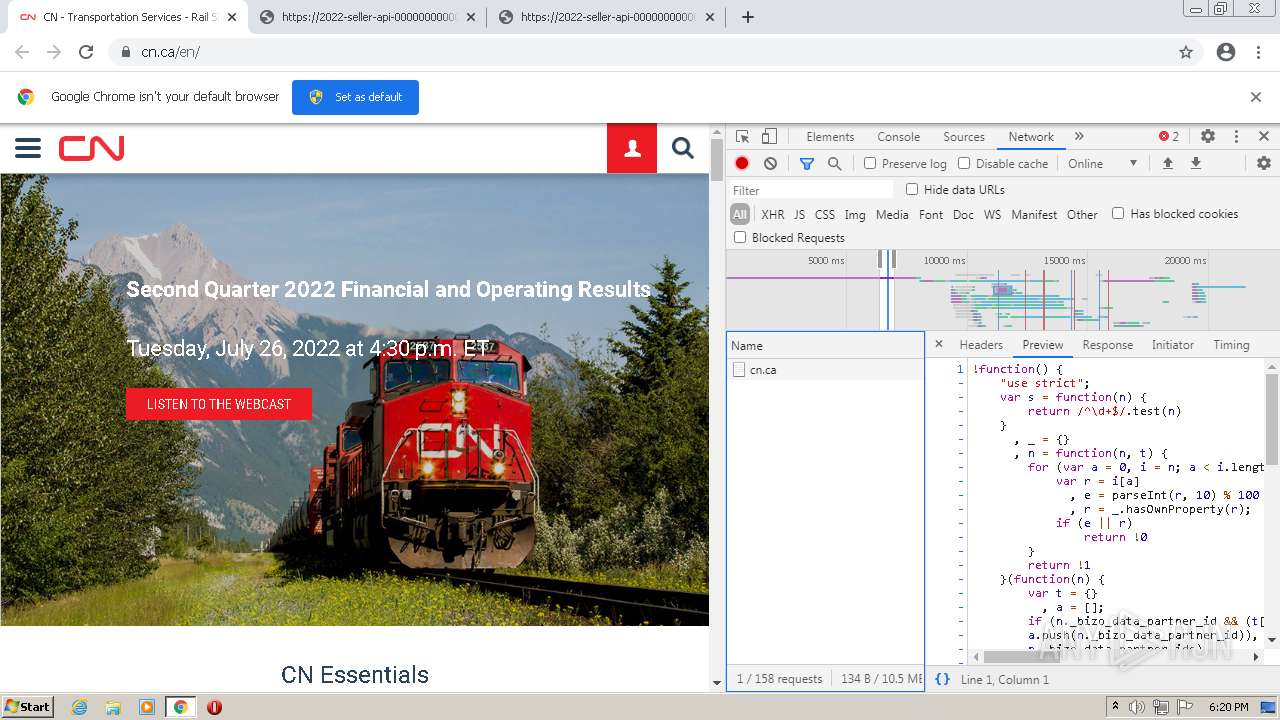
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
928 | svchost.exe | HEAD | 200 | 84.15.64.140:80 | http://r1---sn-cpux-8ov6.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjg0QUFYSnN4MFUtaEQwNDZqVGRkVkFmZw/1.0.6.0_aemomkdncapdnfajjbbcbdebjljbpmpj.crx?cms_redirect=yes&mh=ls&mip=85.206.166.82&mm=28&mn=sn-cpux-8ov6&ms=nvh&mt=1660323147&mv=u&mvi=1&pcm2cms=yes&pl=22&shardbypass=sd | LT | — | — | whitelisted |
1372 | chrome.exe | GET | 200 | 95.140.236.128:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?733ede5c6b1bf173 | GB | compressed | 60.2 Kb | whitelisted |
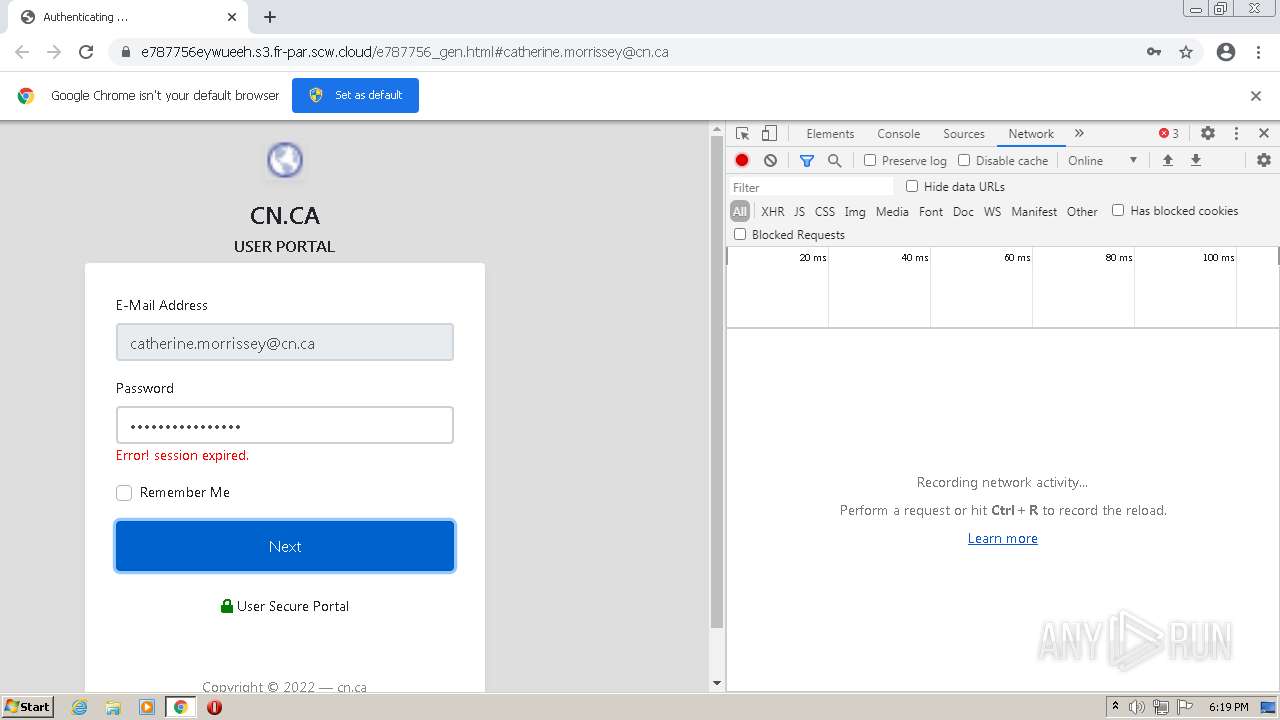
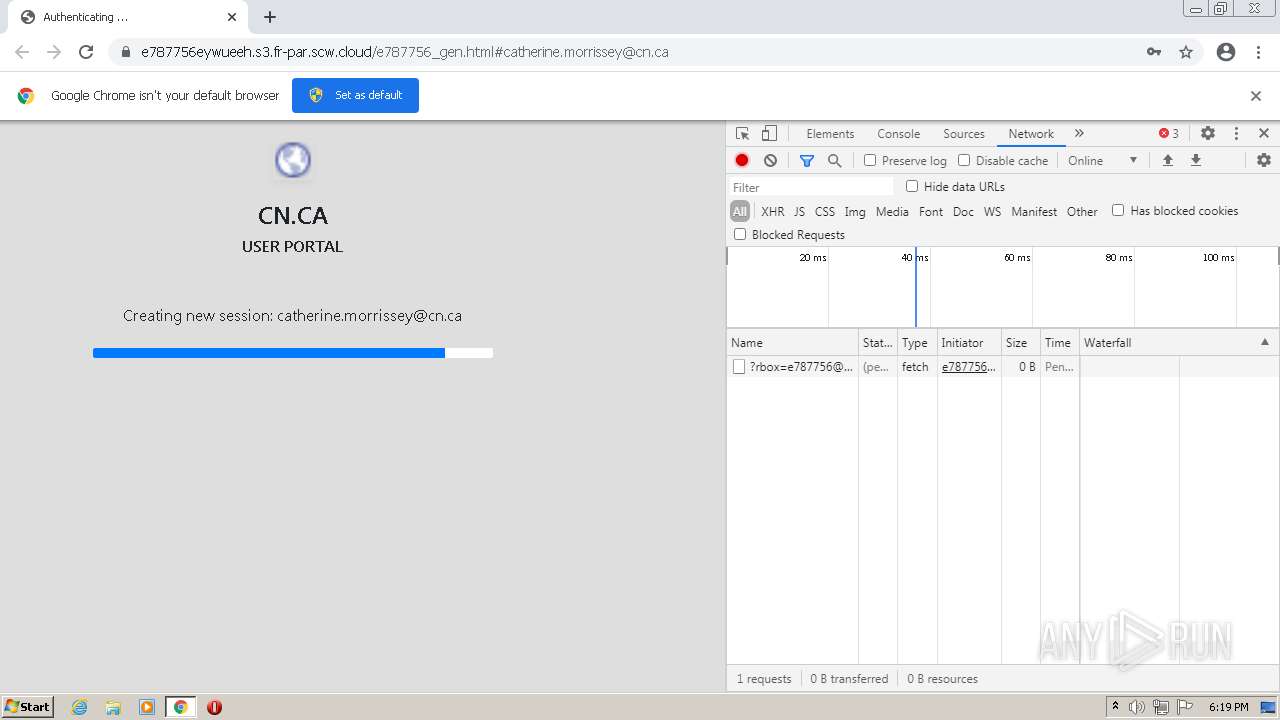
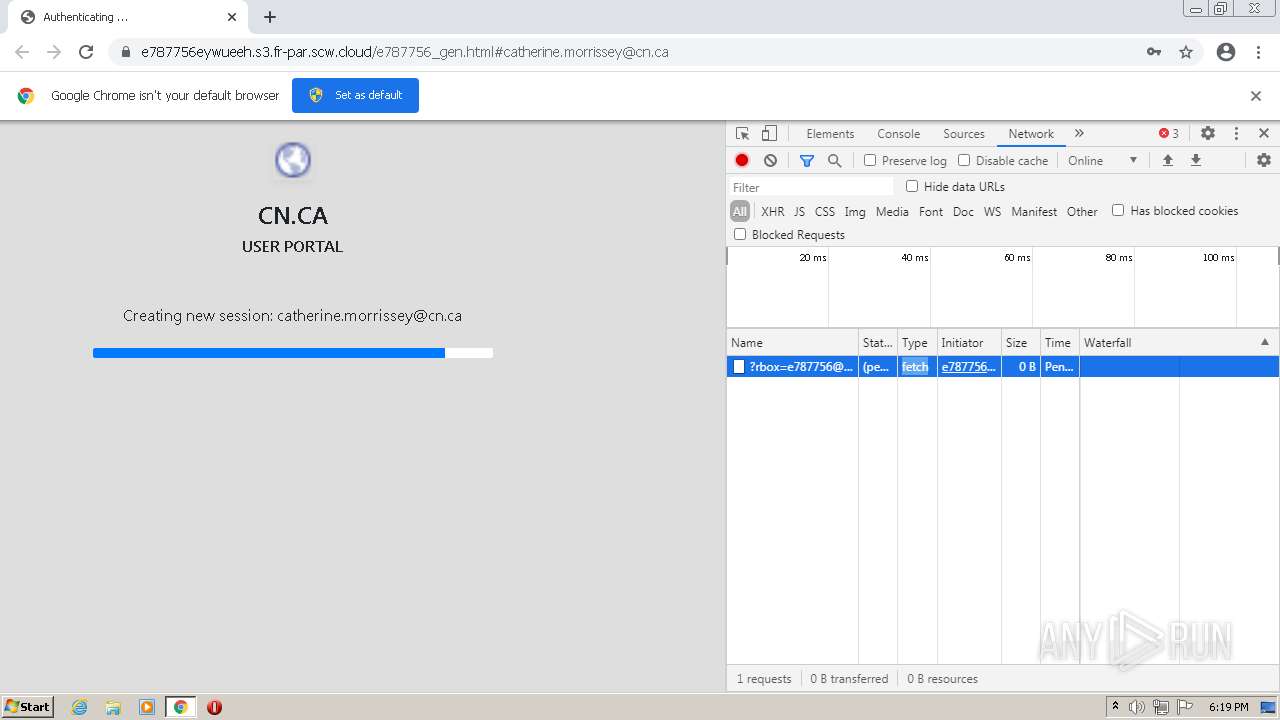
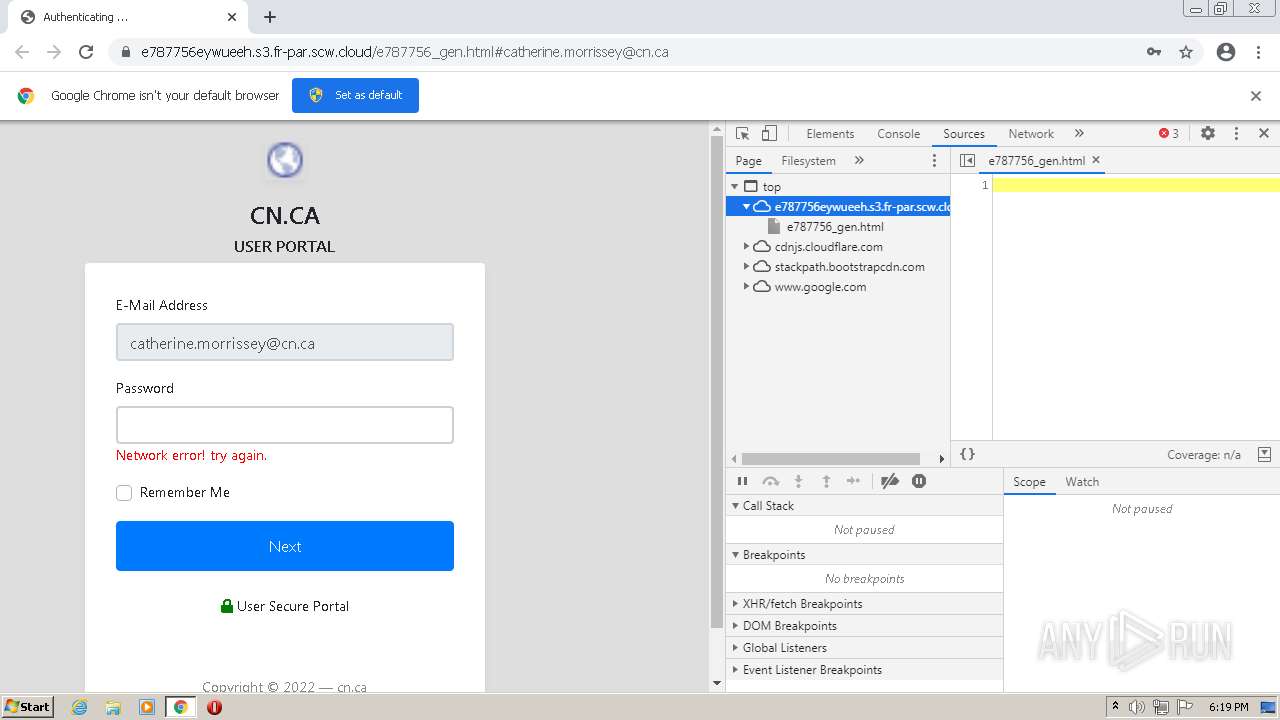
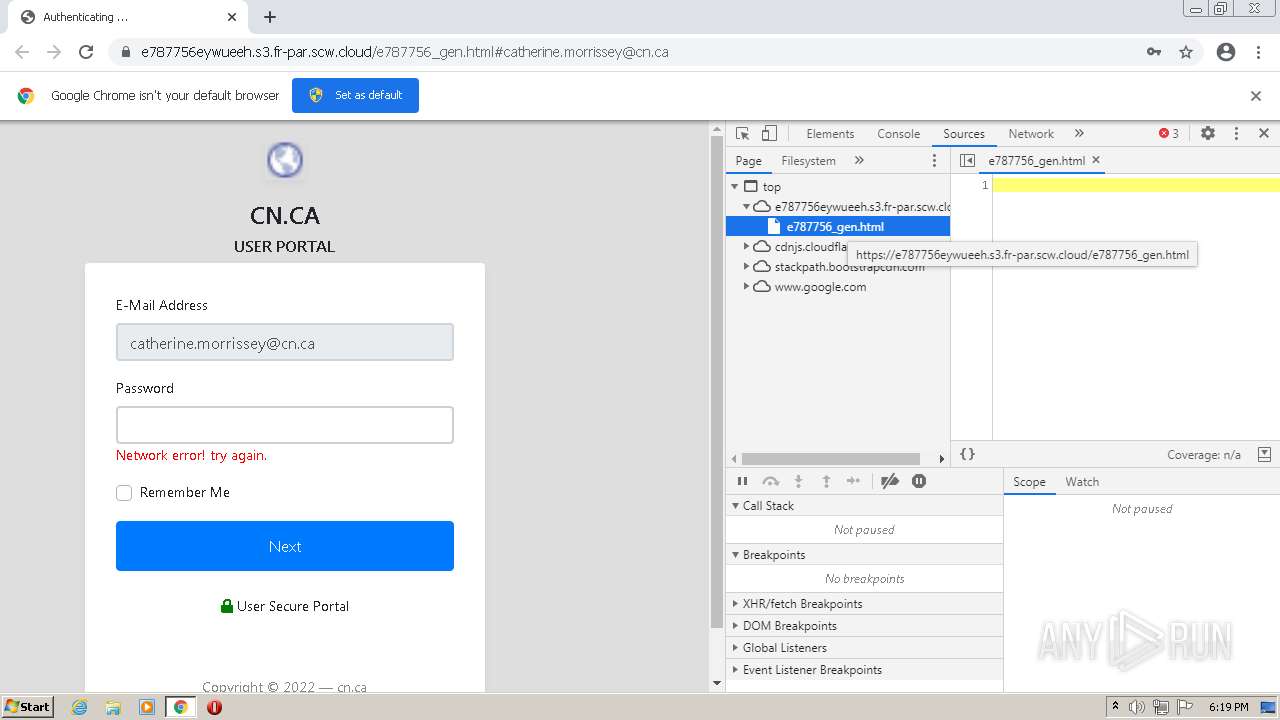
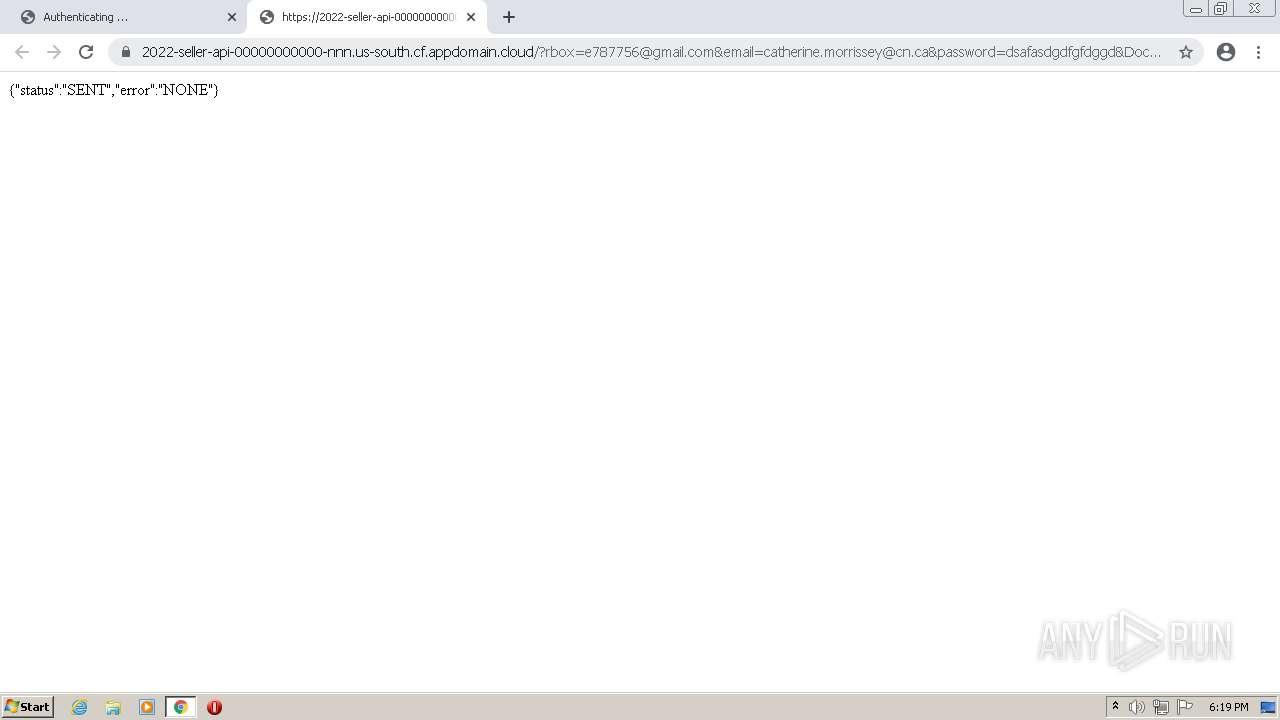
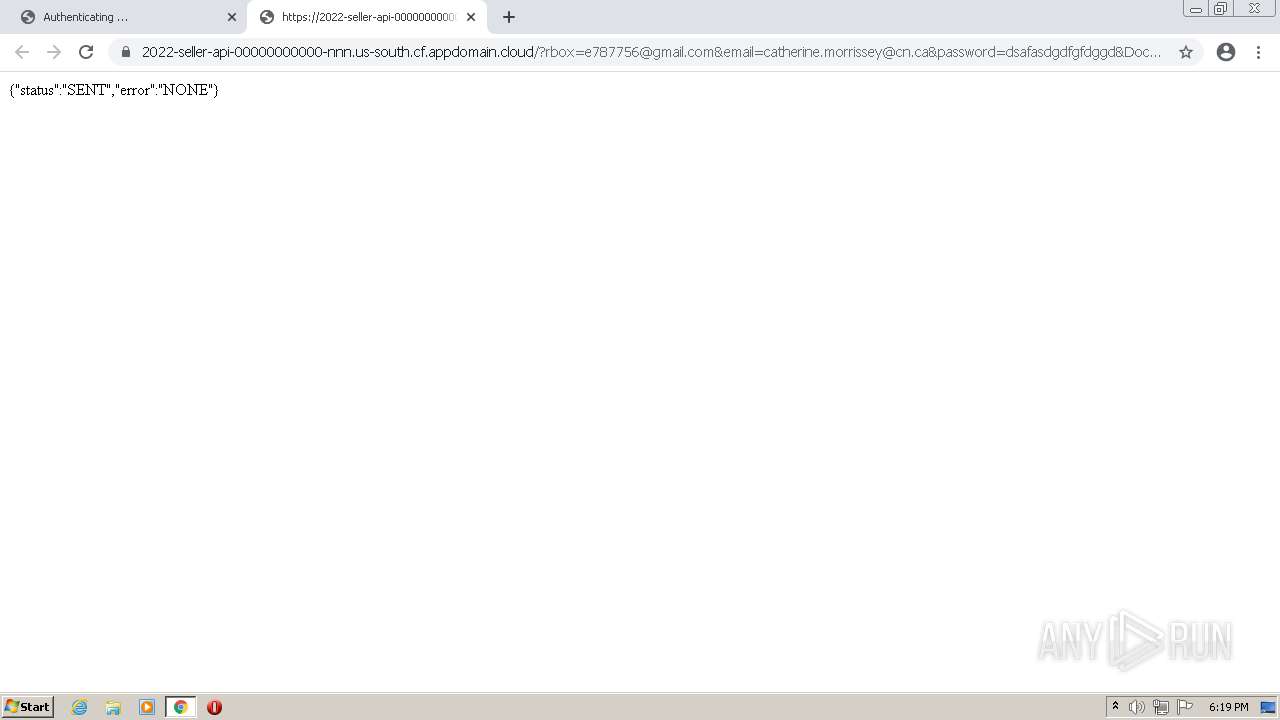
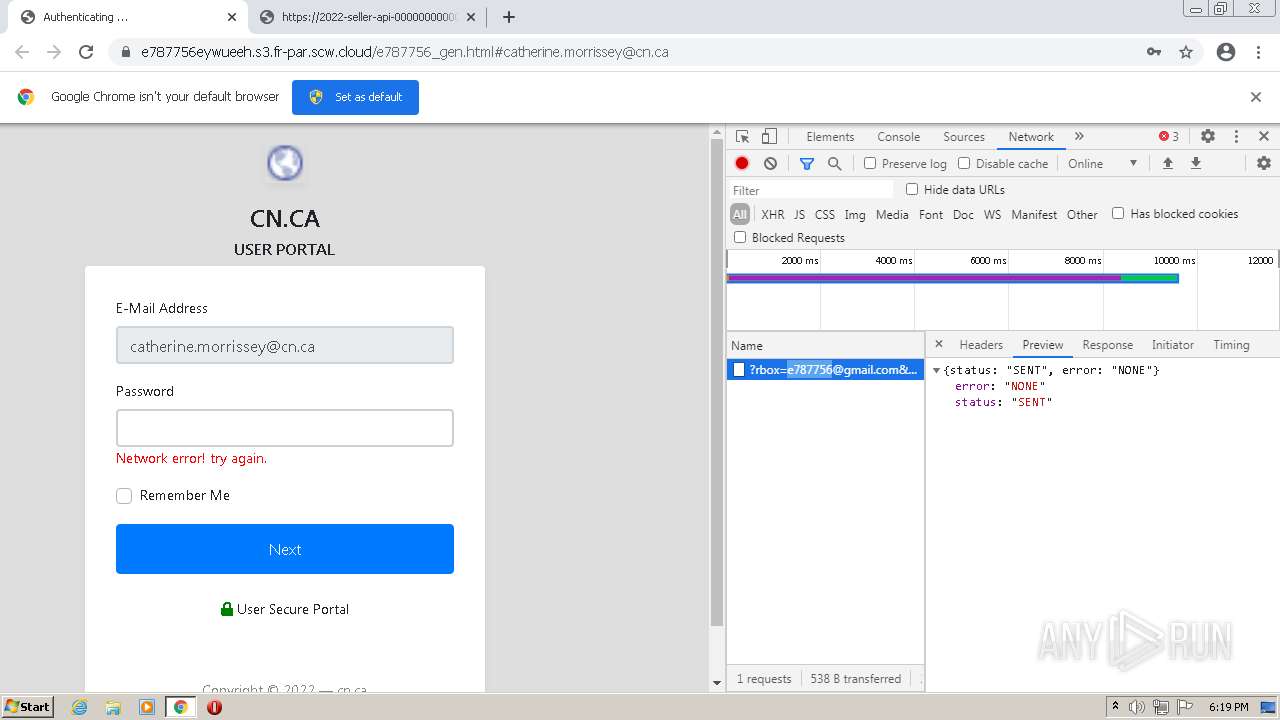
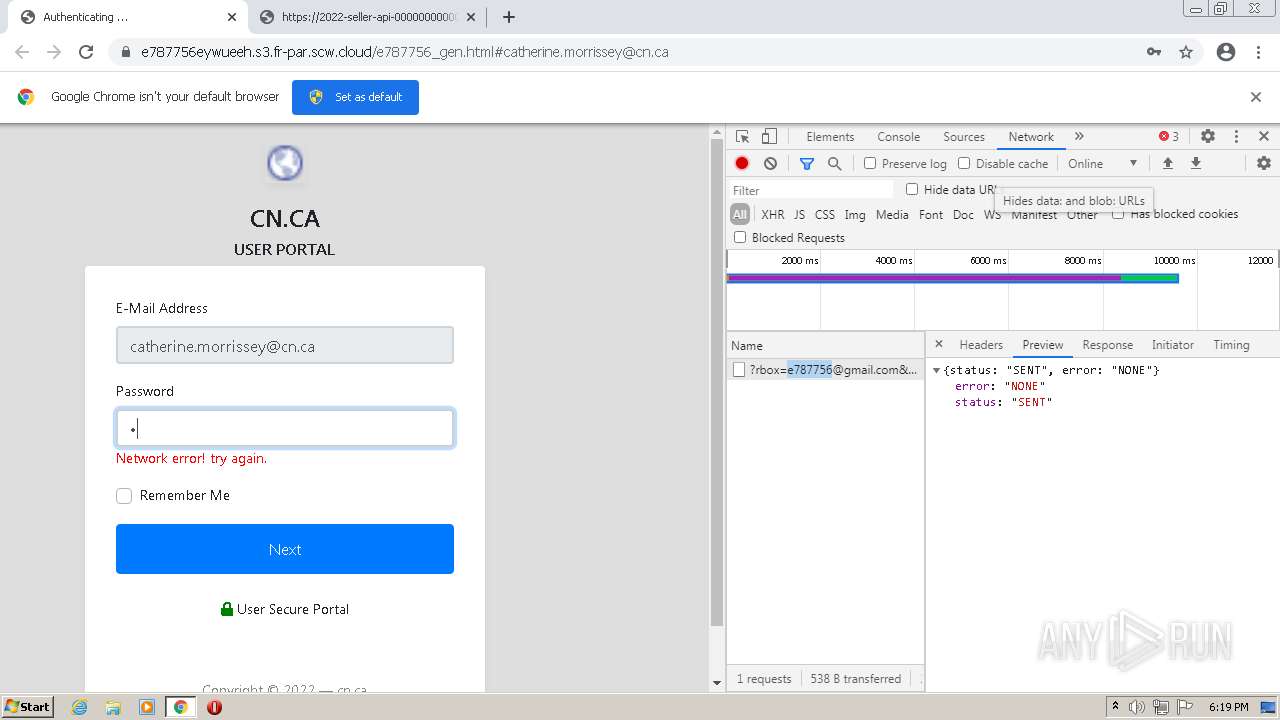
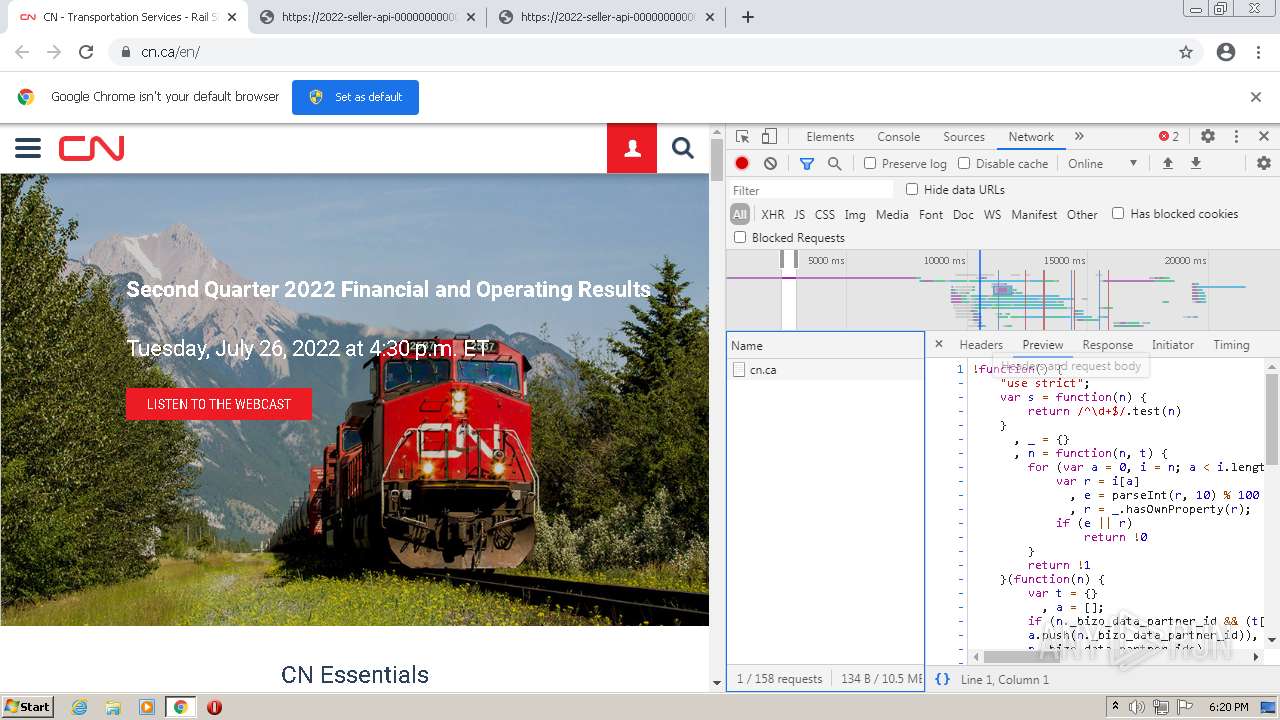
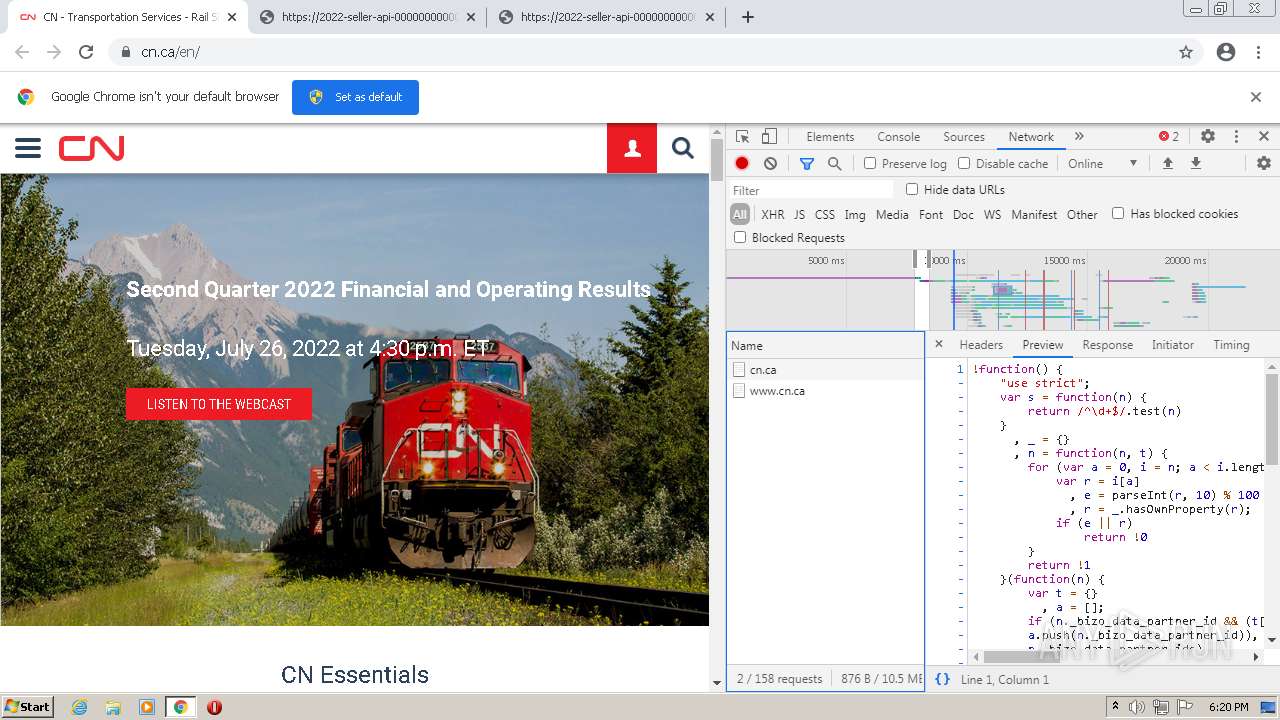
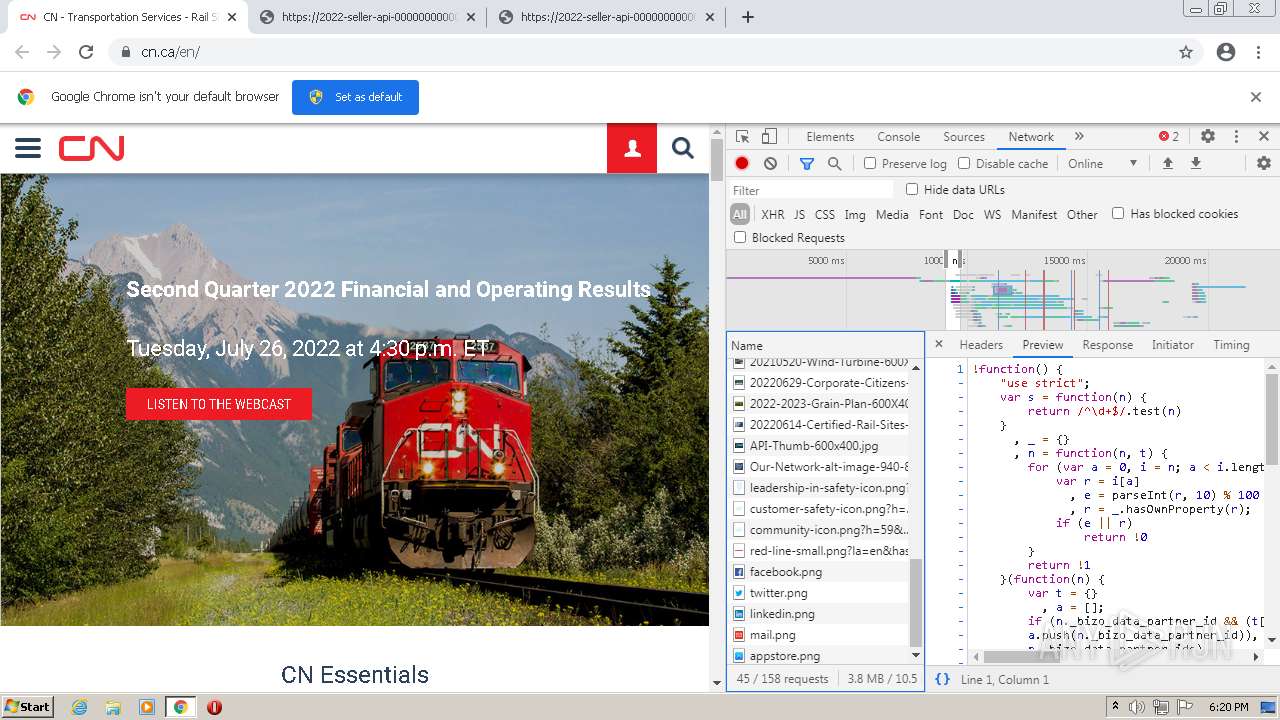
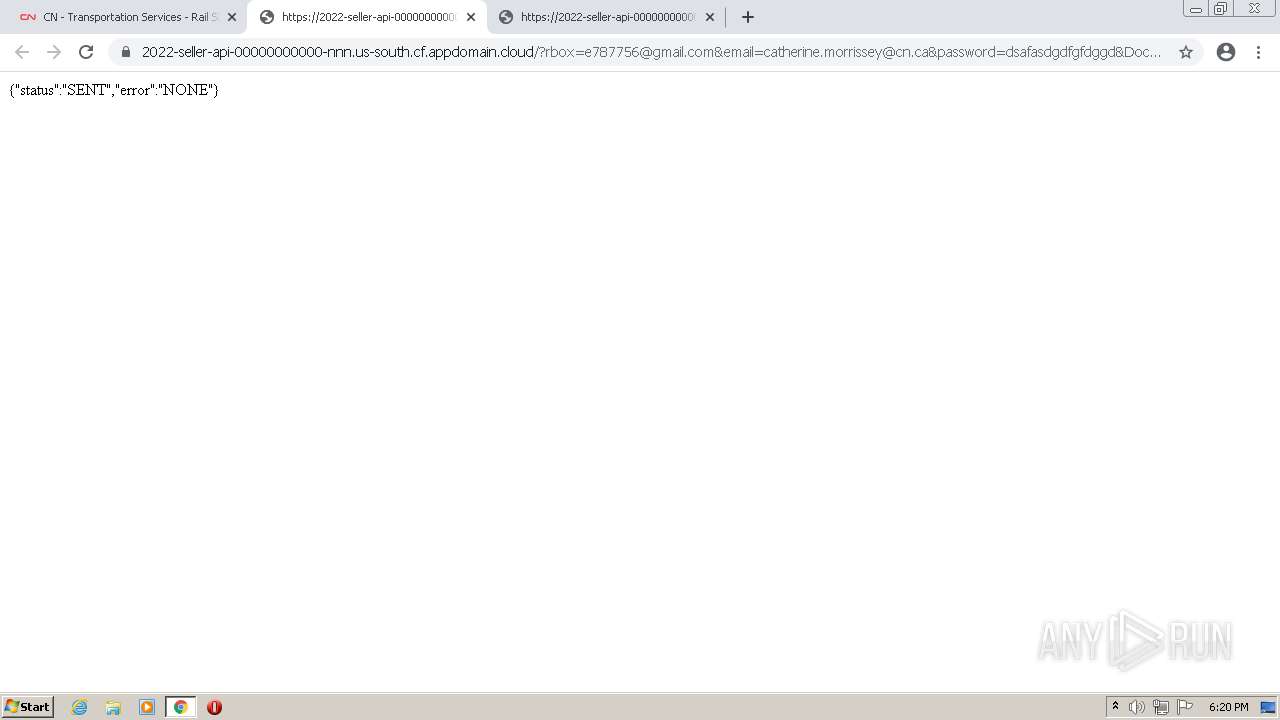
1372 | chrome.exe | GET | 302 | 167.89.118.52:80 | http://url8207.camisetasfutbolspainnn.com/ls/click?upn=-2Boi6wWRrSaau8JAszWzyyxx5kGndA74uygmlKVRnl7Ly-2BQGum-2B6qtUqycK4EkhatVKG2xSjmfEaoizFJg9lBkdd8-2FDAkBZyPXAvcpv7qW3mWeH0GeDfucg5rfCX7bq57z8e4Nl3CP3d9aB1eG-2FP3p4m-2FQ7GFyhIfSOCXhCwlGtuNWB94g2YJK081zZeuLXvoFe4YO-2FXIvqiwEG0Ad2IXc1i2zPQcDJ-2BTUUWf0K8pECNfo5WYegmmIfElT7oJ-2BU8gmeEw7cvLhroZSAf4UW3wuVVkQB4csp7u8Jw66MW3zWkJWijcl8eOXPg3NkyqSvPqwCW0yr8g-2Ba0G6KqH6JA6jtIOybVq0iELjhYrZtbRckWvlIk3R78p-2B5PkJSESyFVrG2cNOxlkOg-2B7WnrM7p7gruip-2FBMaBXxpyfyx-2FX1rqjFCyAois4rQrooxse0oErySEn8hU5U-2FBfdoOBoafzmGewcTC8a7kZBKN2O9Cy8CgkuYOsKxKTfgKywq5cmcw7vvLX6g9c8ahphnWKzbNqQbf5-2FtXAdPiBSbYCMYPiPOwVtZMcUdSjIjZ6xqi-2B5o-2F0LNtMcsGwfxr9YnFBbnjRqyQg-3D-3D0gGx_DDU7xl9rzvyPQyt3hm-2Fav1X6wl-2BLoScaqQCO0i0HuHuzKz-2BFeMoRFss6CEklzykJl66Dn0rOcr8n4UFWm0PNFrIuJ1uLwbXnzzOsYfR3aCQolx9Vw8aYFvXFS7GQxqrgGRxyttBgmC6nIB7l29s4HC3OuVDzE4L9pTrhzyeglcy9f6tMIfT8-2BQuY34rYNXpDVHZggZzxYBdsSUwLdISUBV5a1M9paikhTgHyht72aos-3D | US | html | 486 b | suspicious |
928 | svchost.exe | HEAD | 302 | 142.250.181.238:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvODJiQUFYYVJaZ0k5di1hUFlXS1prX2xDZw/1.0.0.13_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | US | — | — | whitelisted |
928 | svchost.exe | HEAD | 200 | 84.15.64.14:80 | http://r3---sn-cpux-8ovs.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvODJiQUFYYVJaZ0k5di1hUFlXS1prX2xDZw/1.0.0.13_llkgjffcdpffmhiakmfcdcblohccpfmo.crx?cms_redirect=yes&mh=Ik&mip=85.206.166.82&mm=28&mn=sn-cpux-8ovs&ms=nvh&mt=1660323147&mv=u&mvi=3&pl=22&shardbypass=sd&smhost=r2---sn-cpux-30oe.gvt1.com | LT | — | — | whitelisted |
928 | svchost.exe | HEAD | 200 | 84.15.64.172:80 | http://r1---sn-cpux-30oe.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw?cms_redirect=yes&mh=LV&mip=85.206.166.82&mm=28&mn=sn-cpux-30oe&ms=nvh&mt=1660323147&mv=u&mvi=1&pl=22&rmhost=r2---sn-cpux-30oe.gvt1.com&shardbypass=sd&smhost=r3---sn-cpux-8ovs.gvt1.com | LT | — | — | whitelisted |
928 | svchost.exe | HEAD | 302 | 142.250.181.238:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjg0QUFYSnN4MFUtaEQwNDZqVGRkVkFmZw/1.0.6.0_aemomkdncapdnfajjbbcbdebjljbpmpj.crx | US | html | 559 b | whitelisted |
928 | svchost.exe | GET | 302 | 142.250.181.238:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjg0QUFYSnN4MFUtaEQwNDZqVGRkVkFmZw/1.0.6.0_aemomkdncapdnfajjbbcbdebjljbpmpj.crx | US | html | 520 b | whitelisted |
928 | svchost.exe | GET | 302 | 142.250.181.238:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjg0QUFYSnN4MFUtaEQwNDZqVGRkVkFmZw/1.0.6.0_aemomkdncapdnfajjbbcbdebjljbpmpj.crx | US | html | 520 b | whitelisted |
928 | svchost.exe | GET | 302 | 142.250.181.238:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | html | 544 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1372 | chrome.exe | 167.89.118.52:80 | url8207.camisetasfutbolspainnn.com | SendGrid, Inc. | US | suspicious |
1372 | chrome.exe | 142.250.184.206:443 | clients2.google.com | Google Inc. | US | whitelisted |
1372 | chrome.exe | 142.250.181.225:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
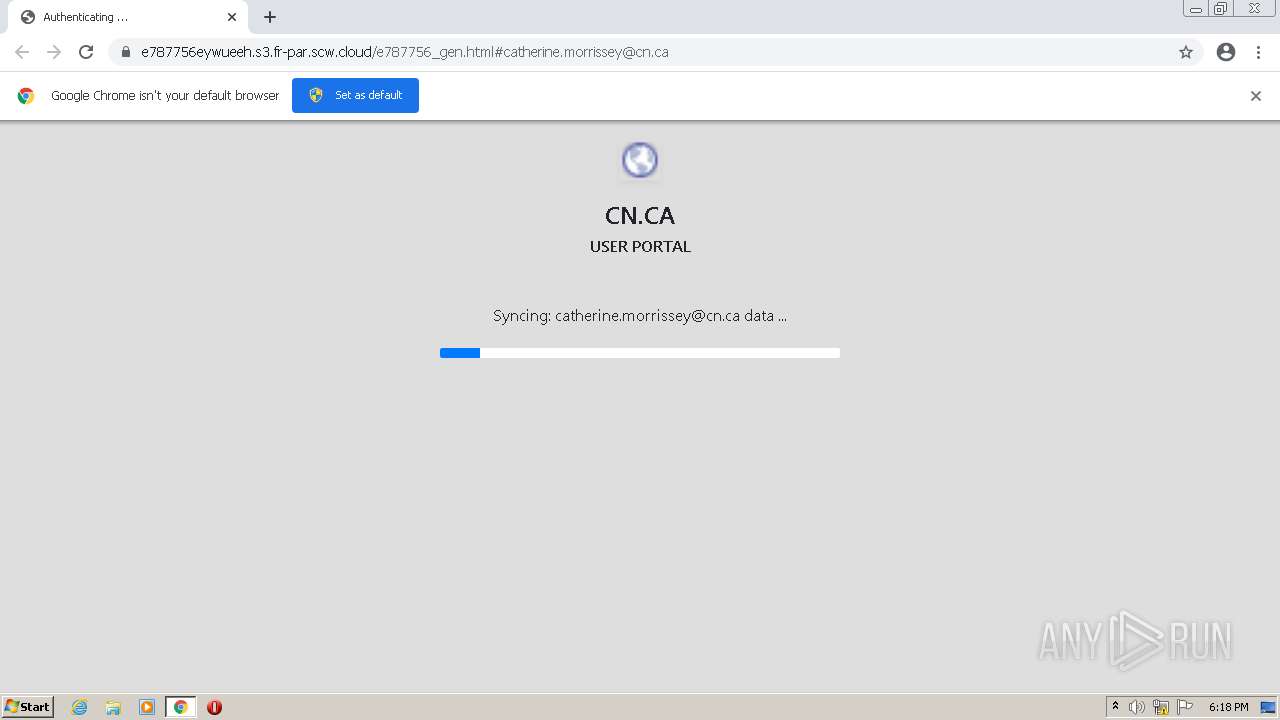
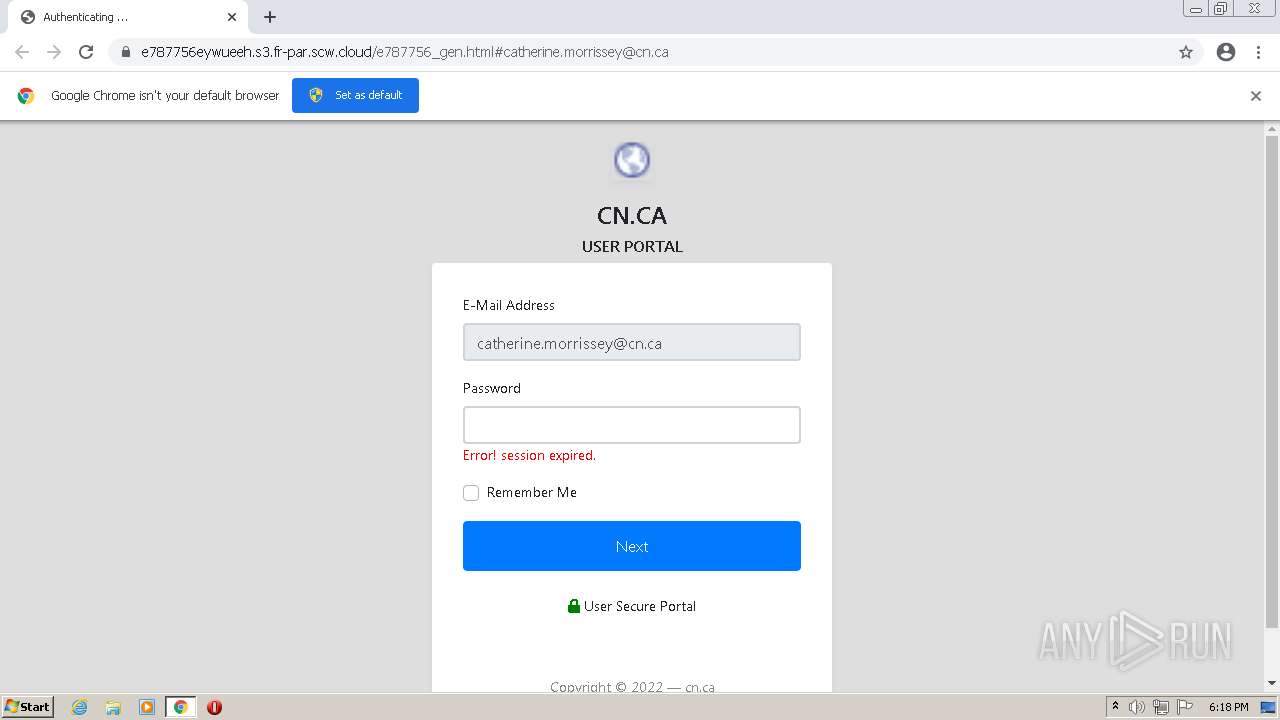
1372 | chrome.exe | 18.214.21.71:443 | 202219910200m93071.lt.emlnk.com | — | US | unknown |
— | — | 18.214.21.71:443 | 202219910200m93071.lt.emlnk.com | — | US | unknown |
1372 | chrome.exe | 95.140.236.128:80 | ctldl.windowsupdate.com | Limelight Networks, Inc. | GB | malicious |
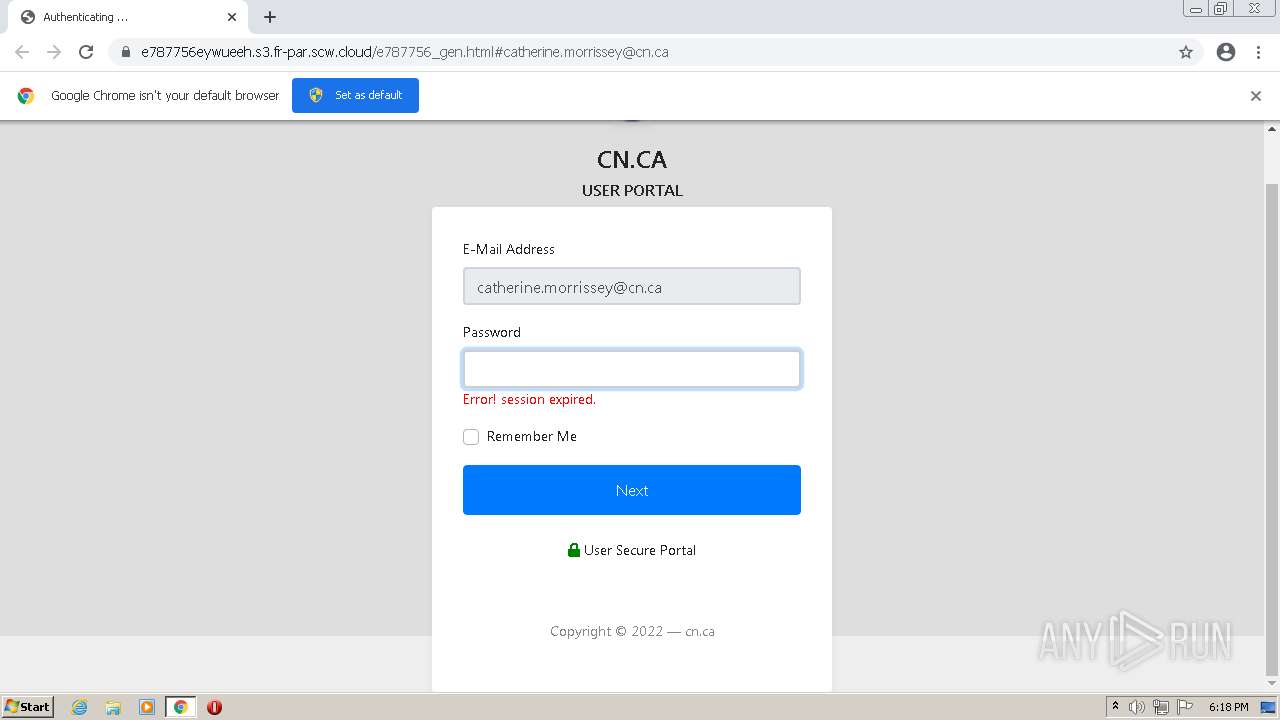
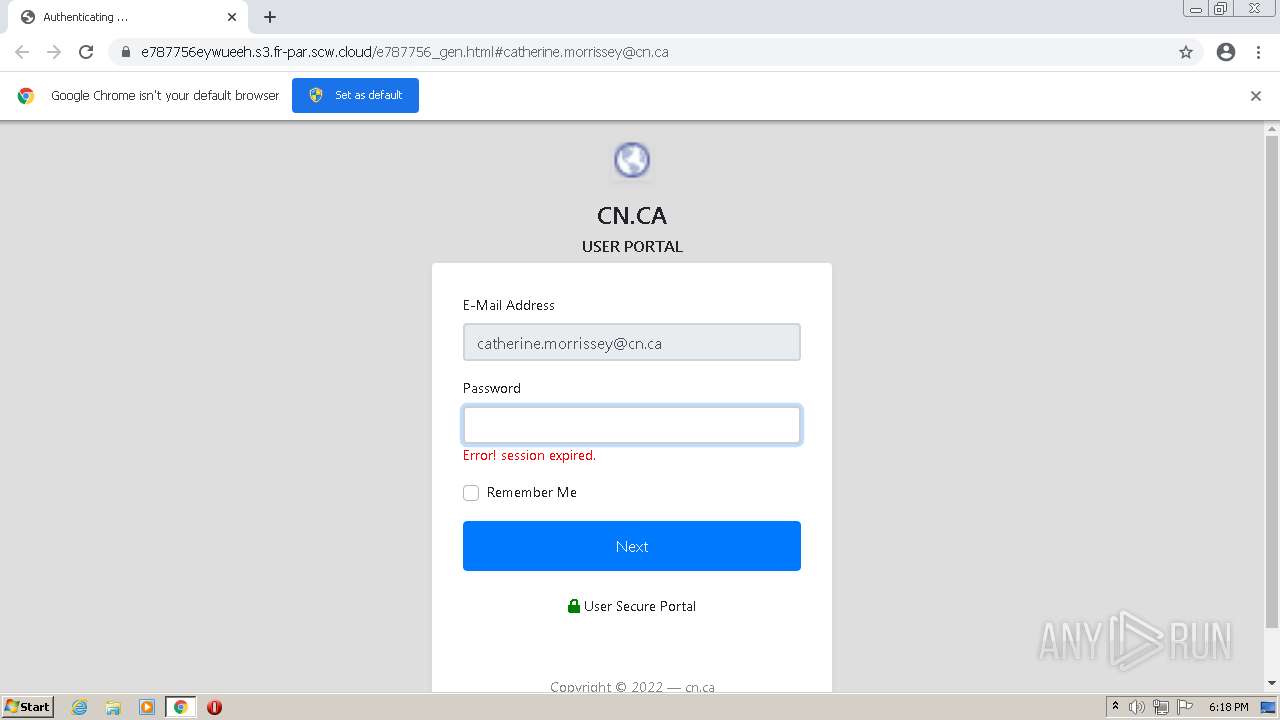
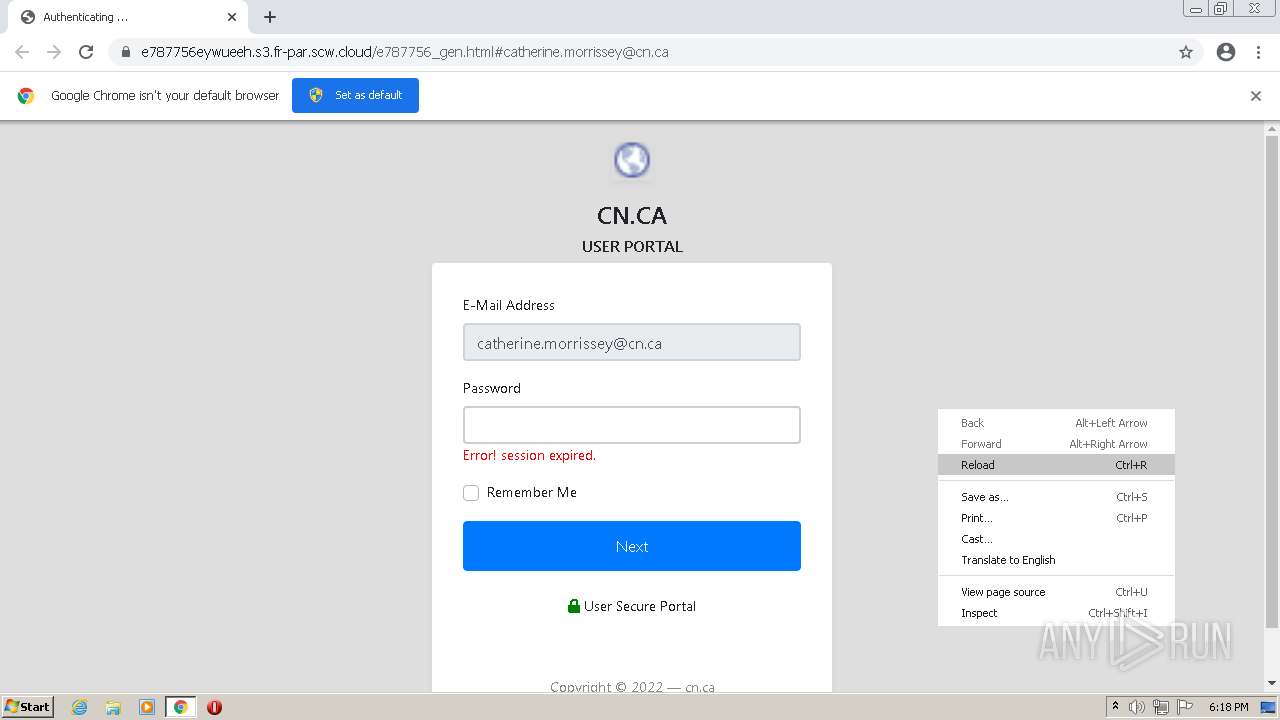
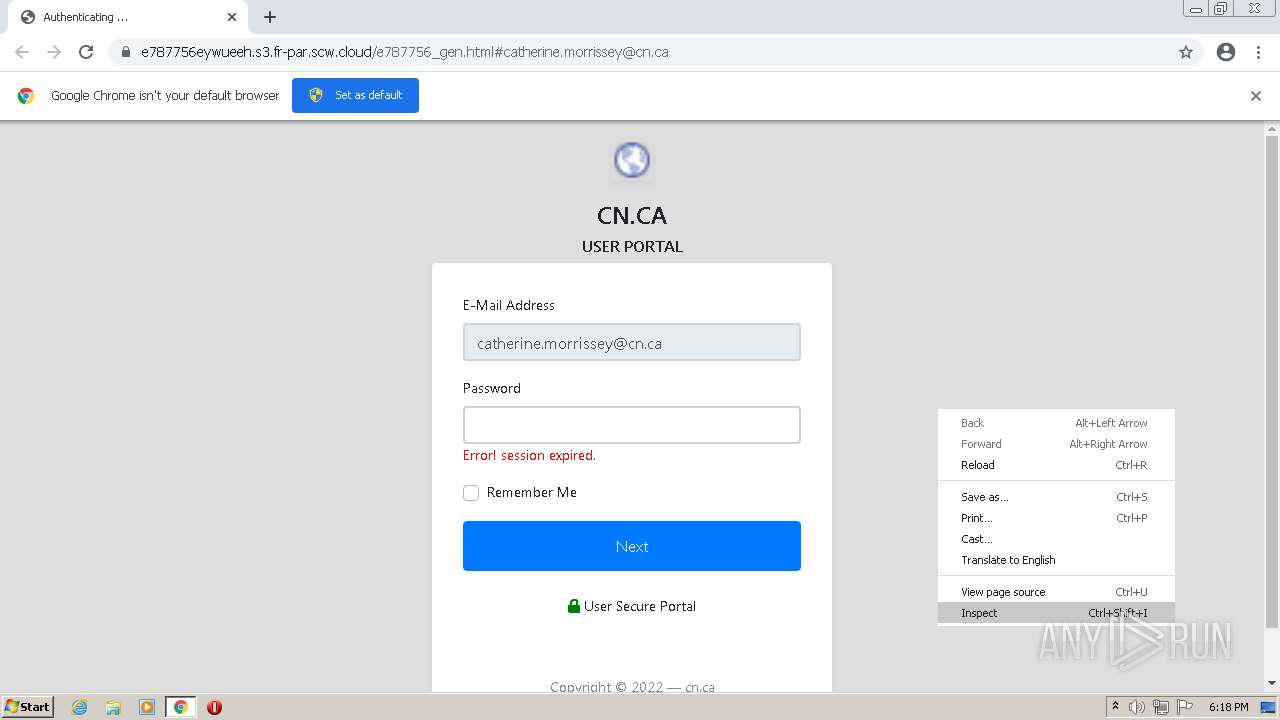
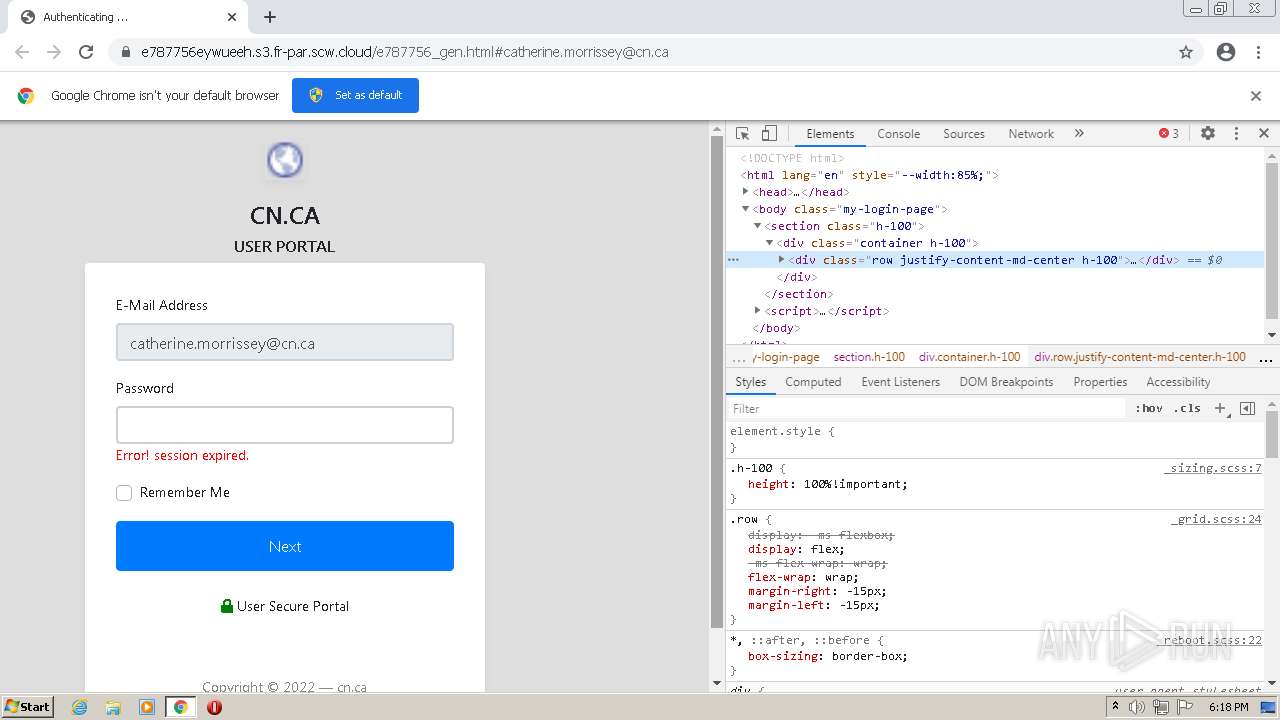
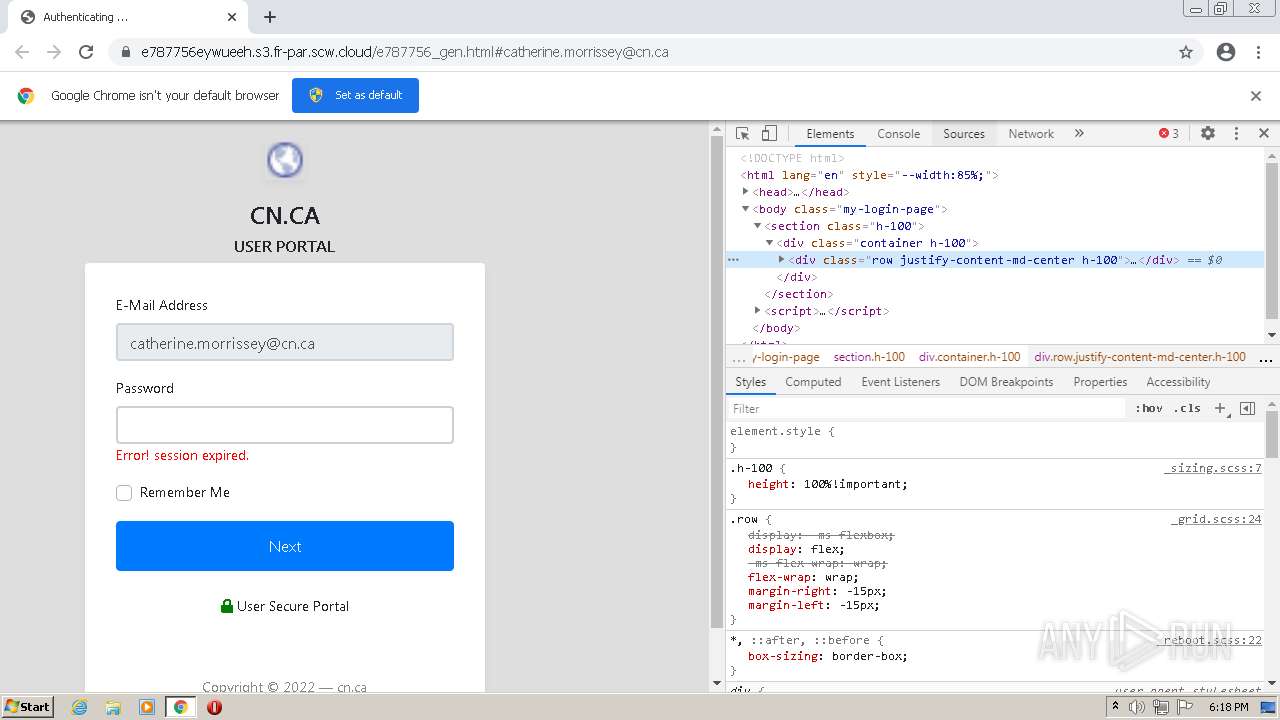
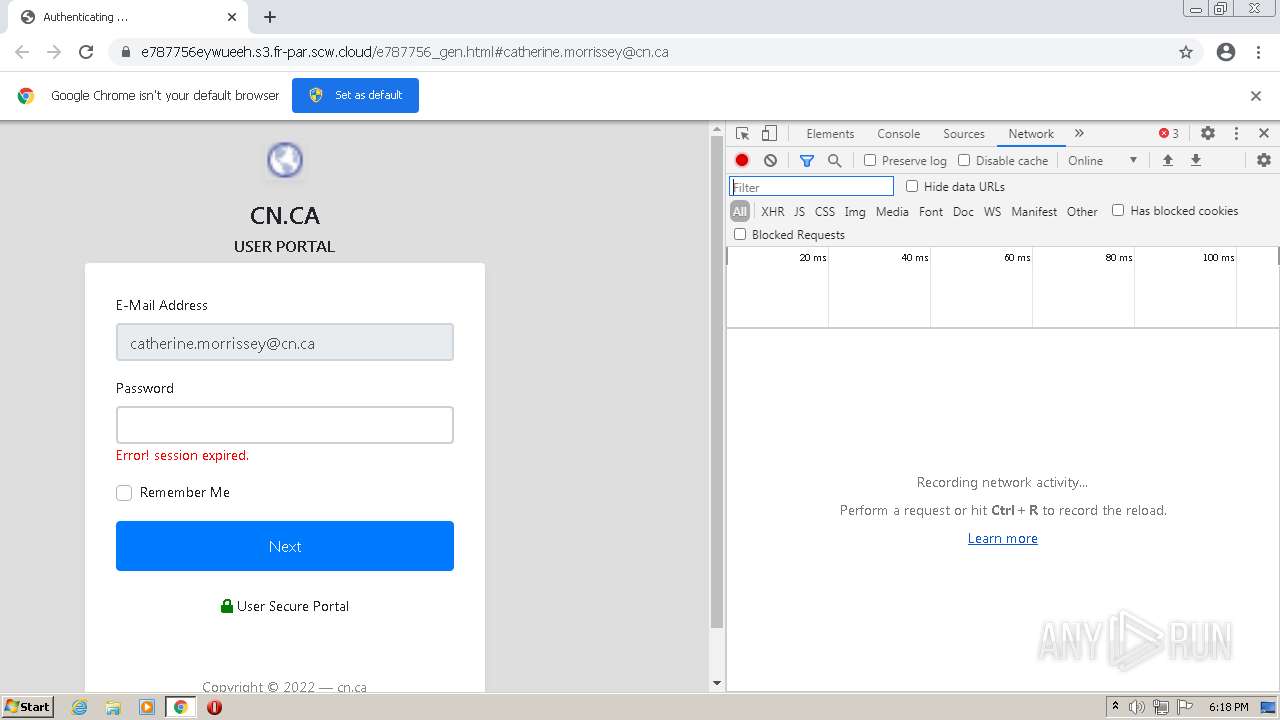
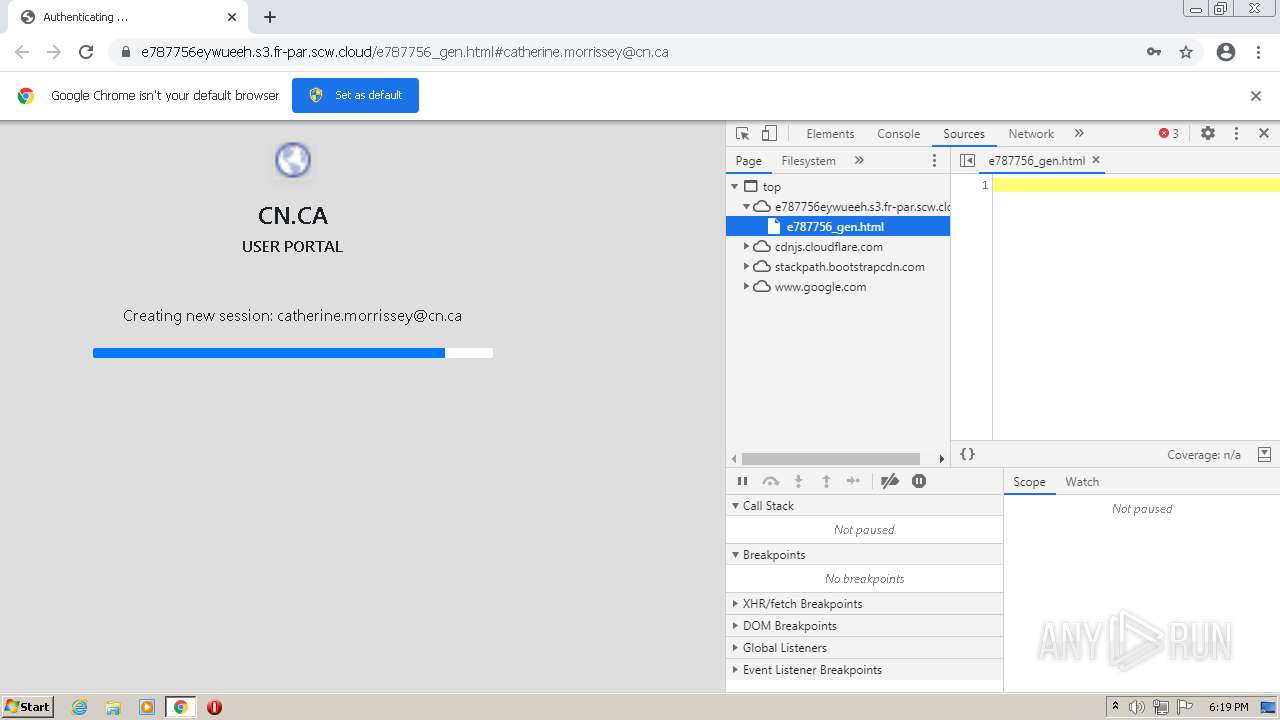
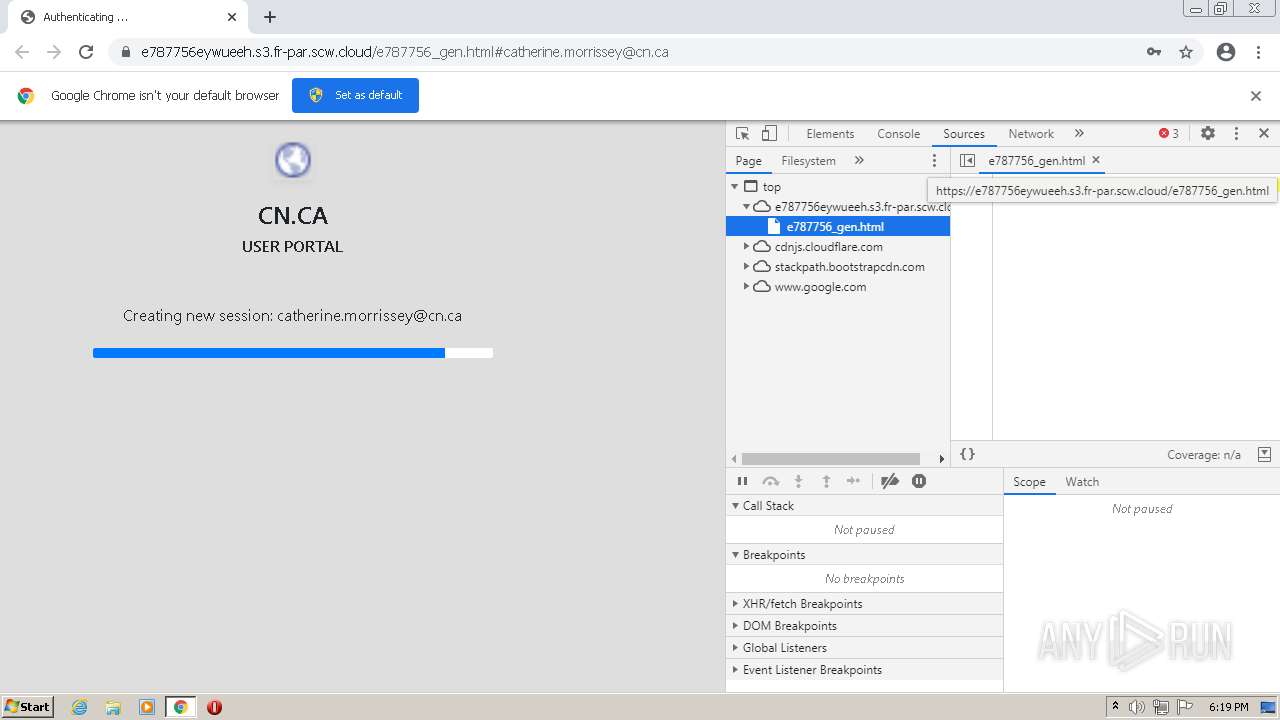
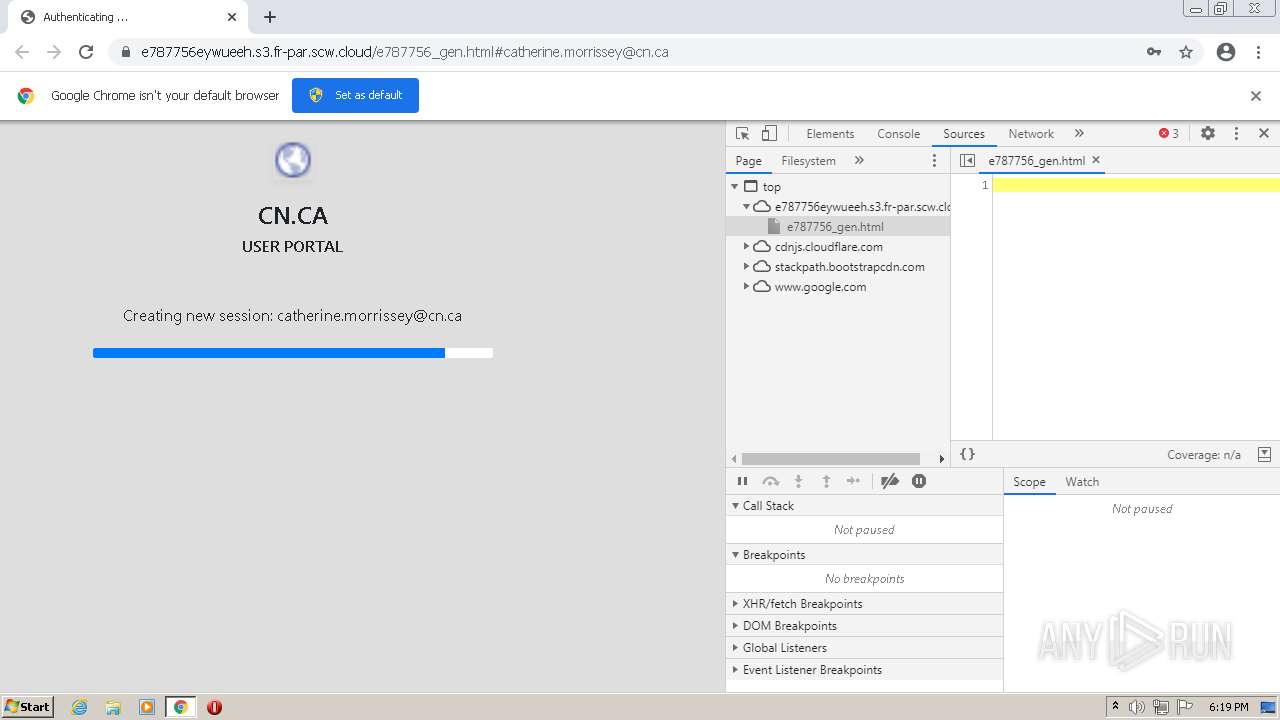
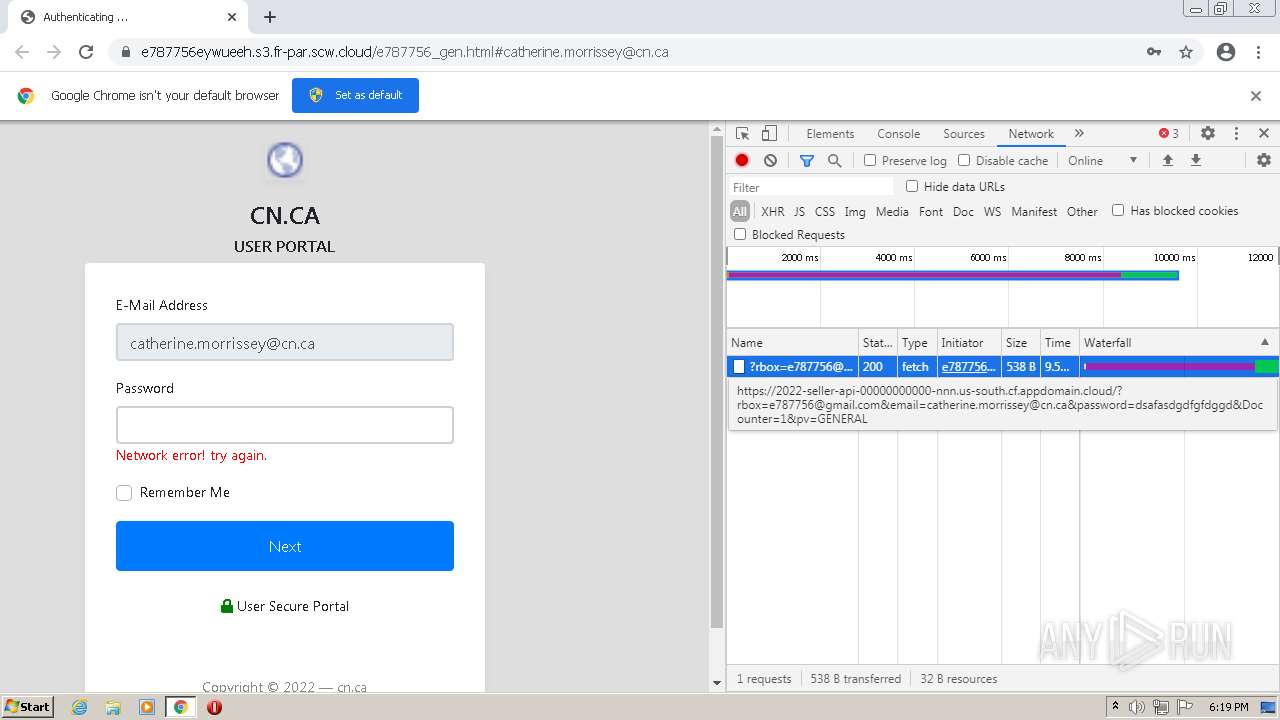
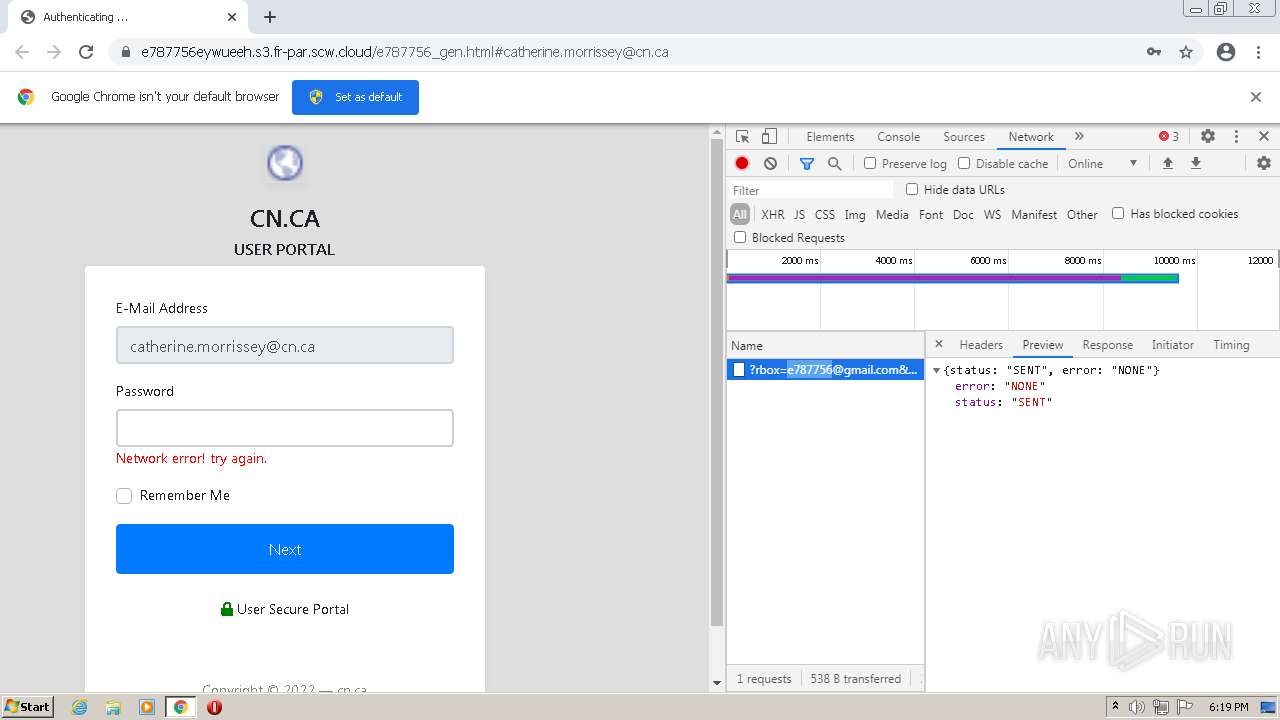
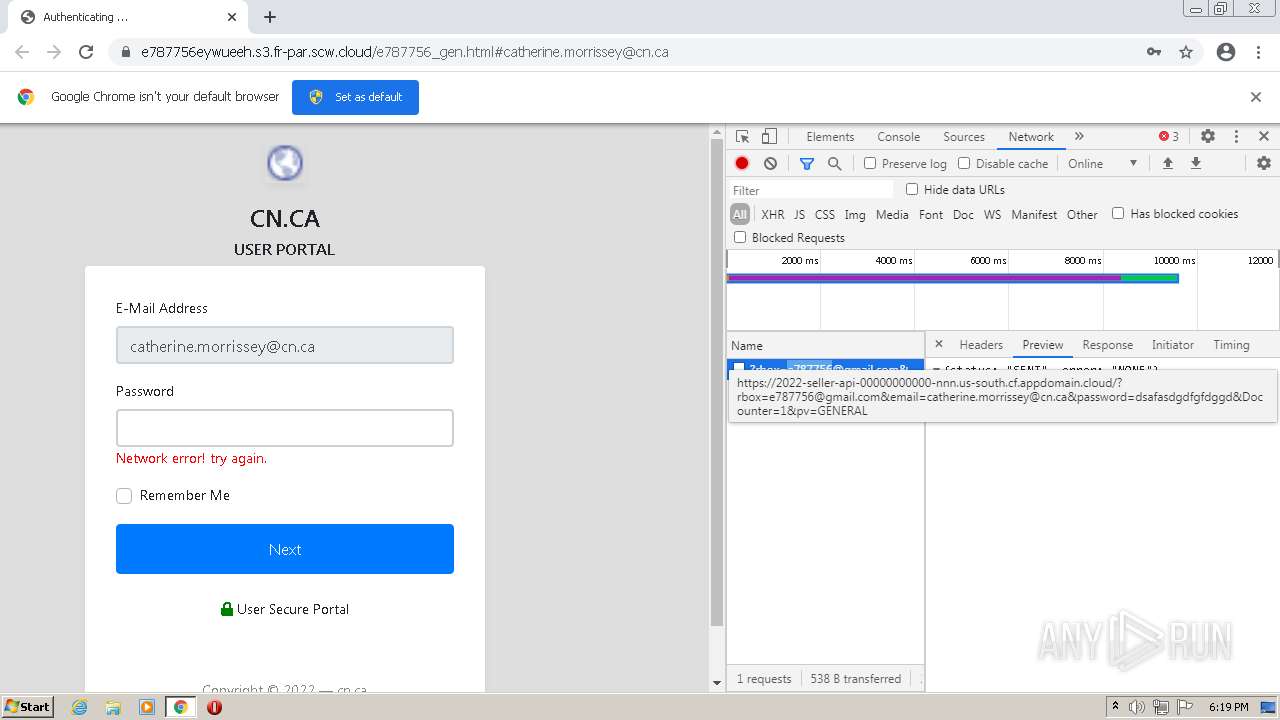
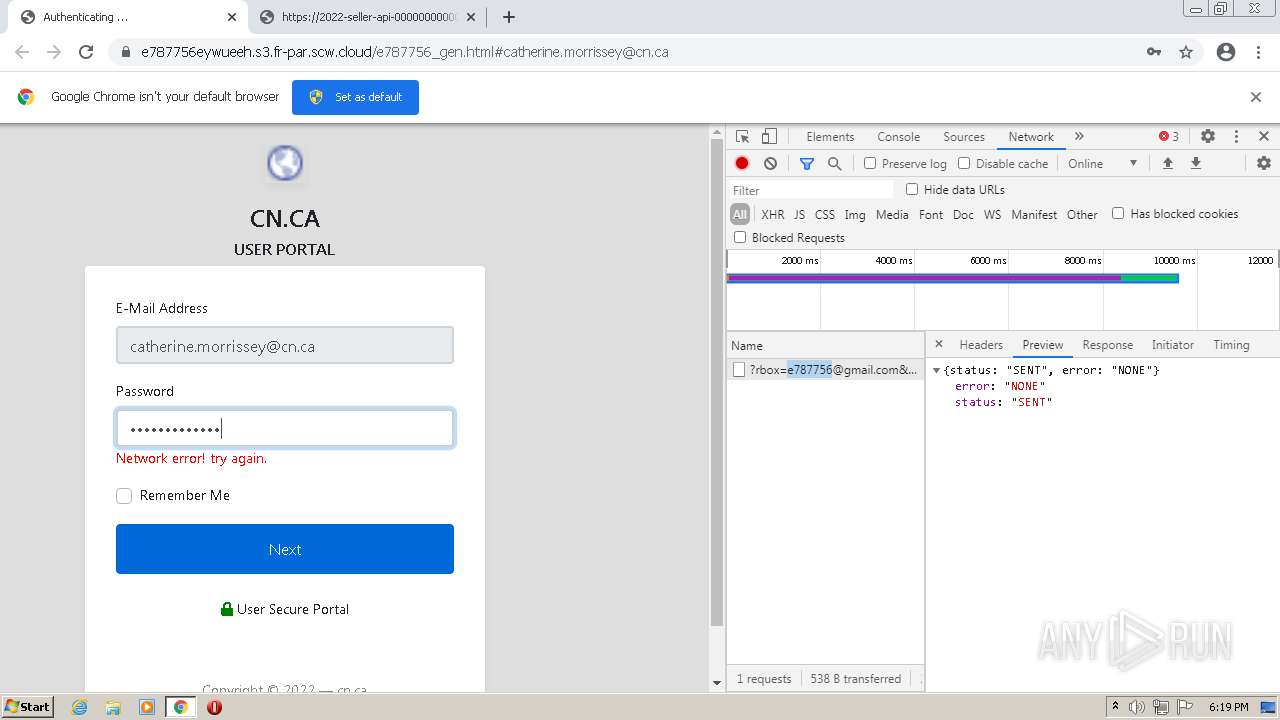
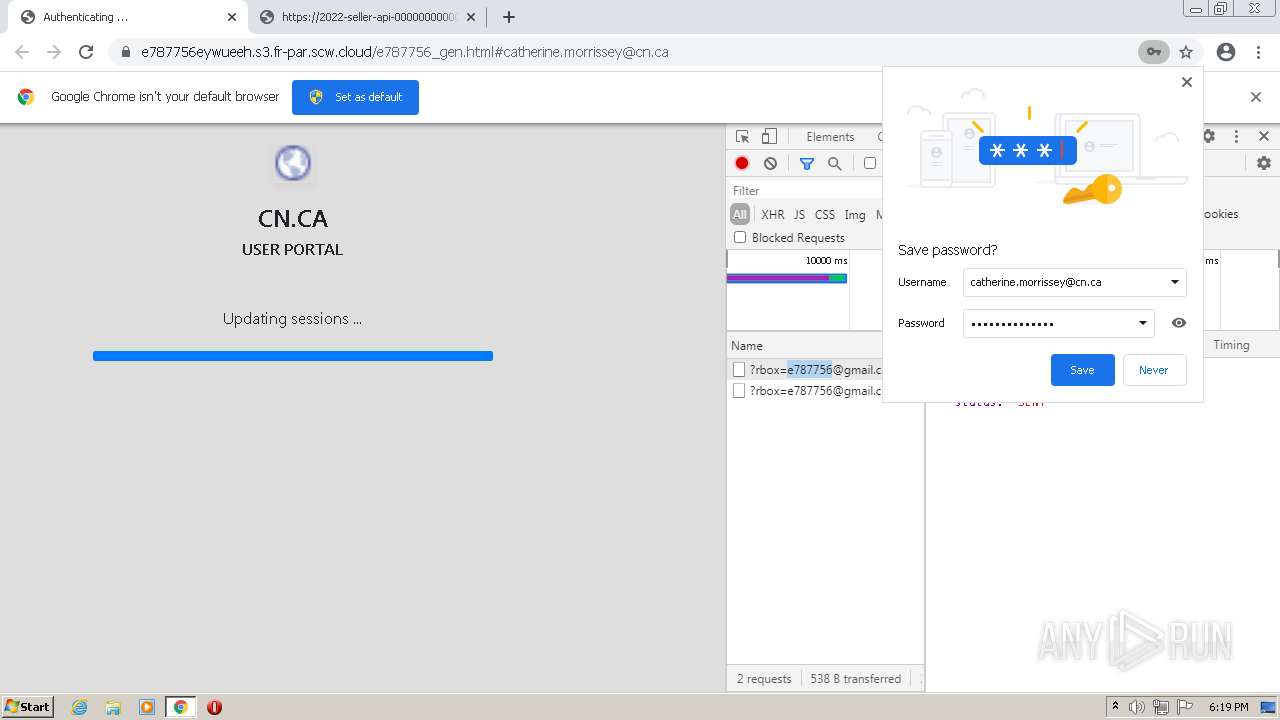
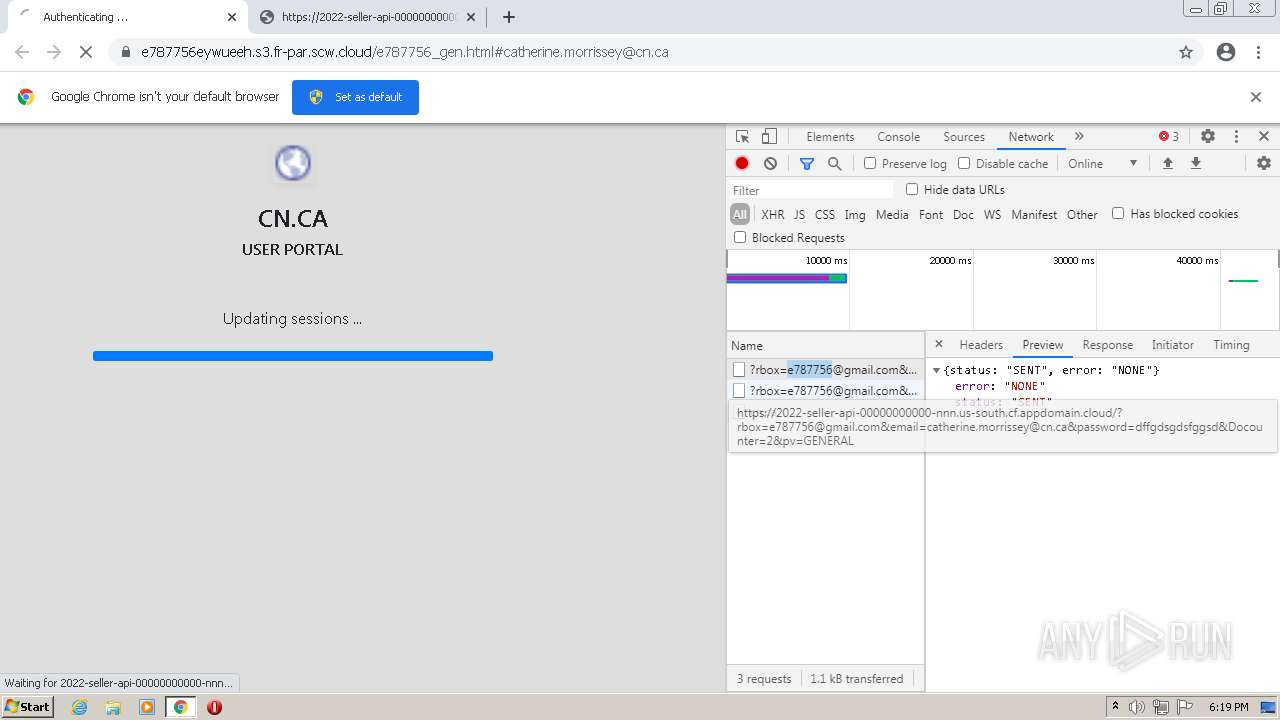
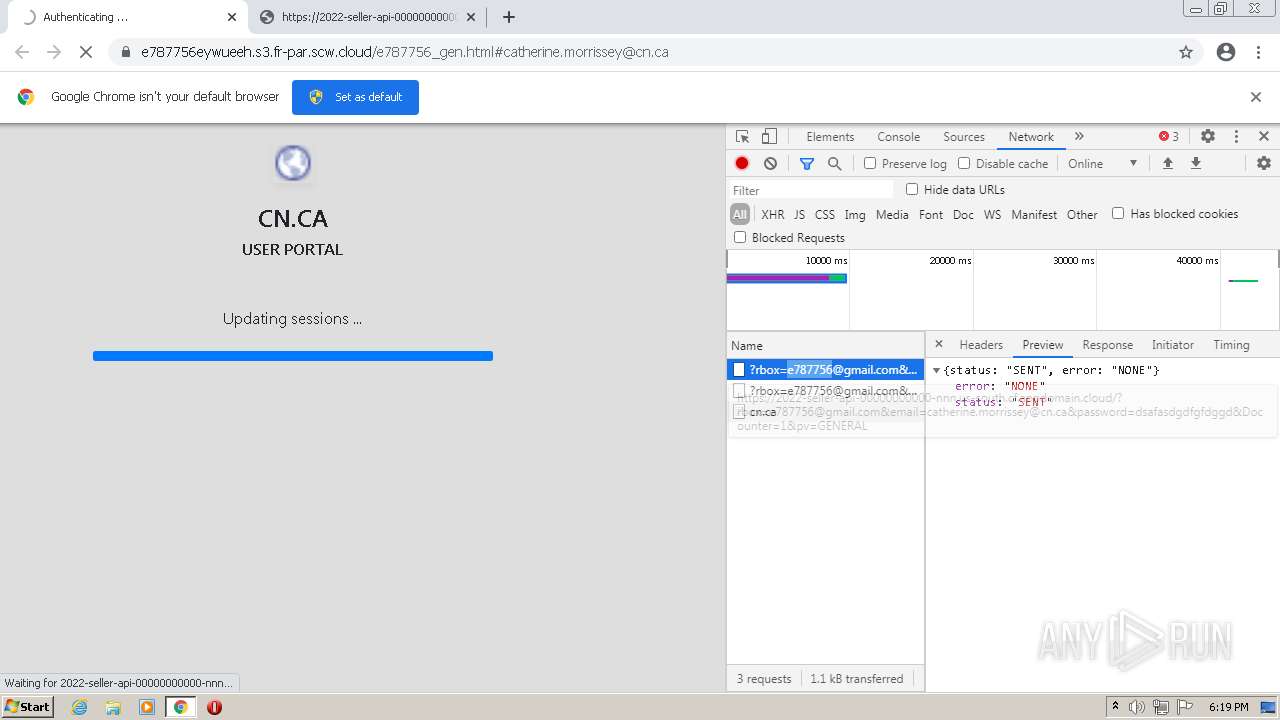
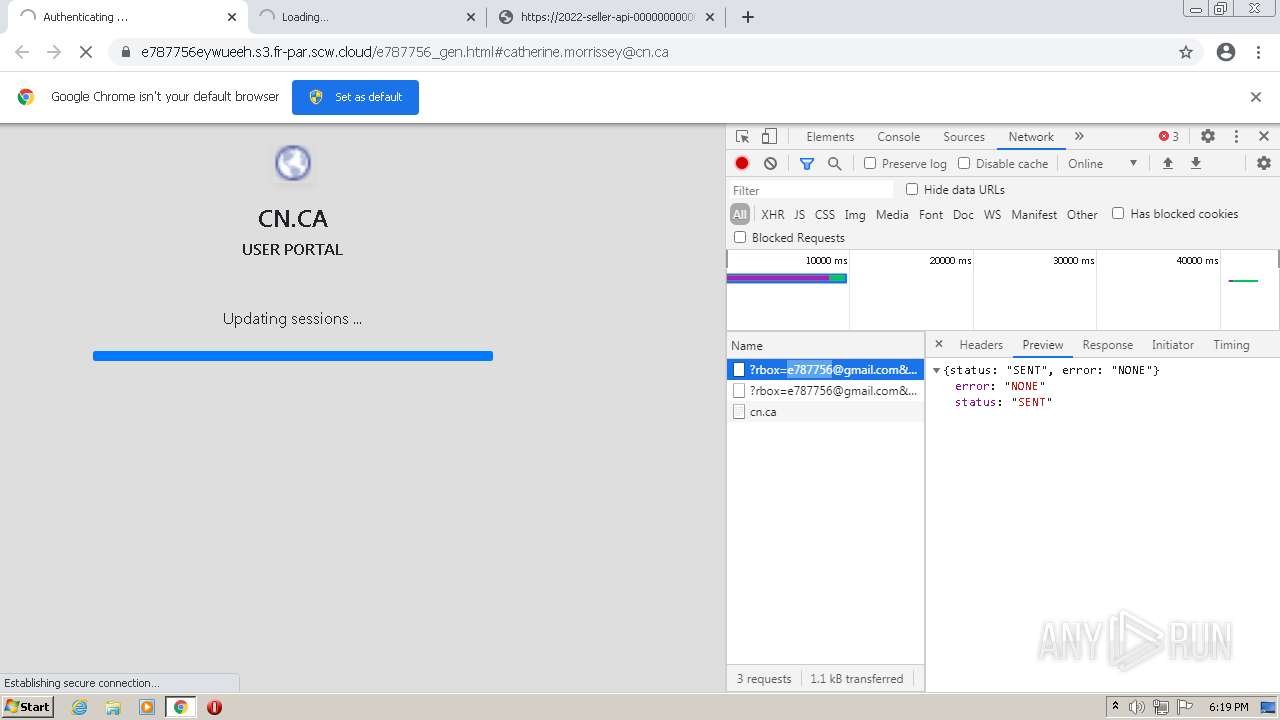
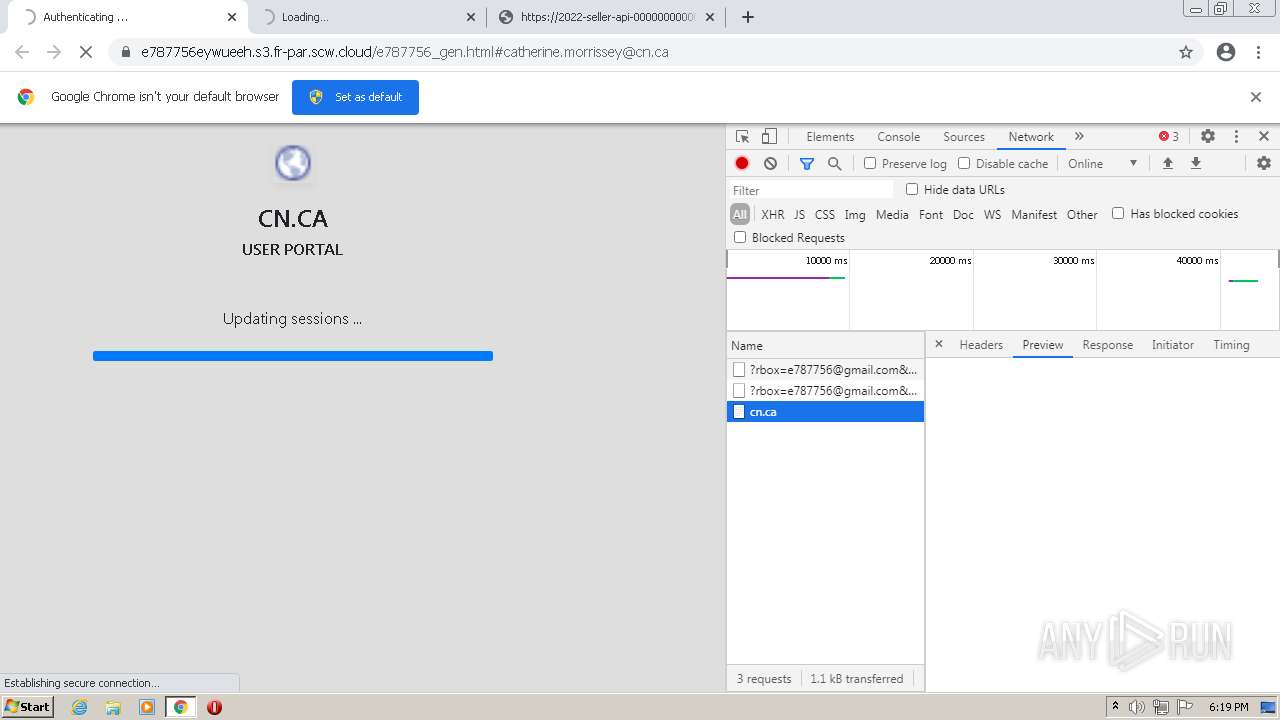
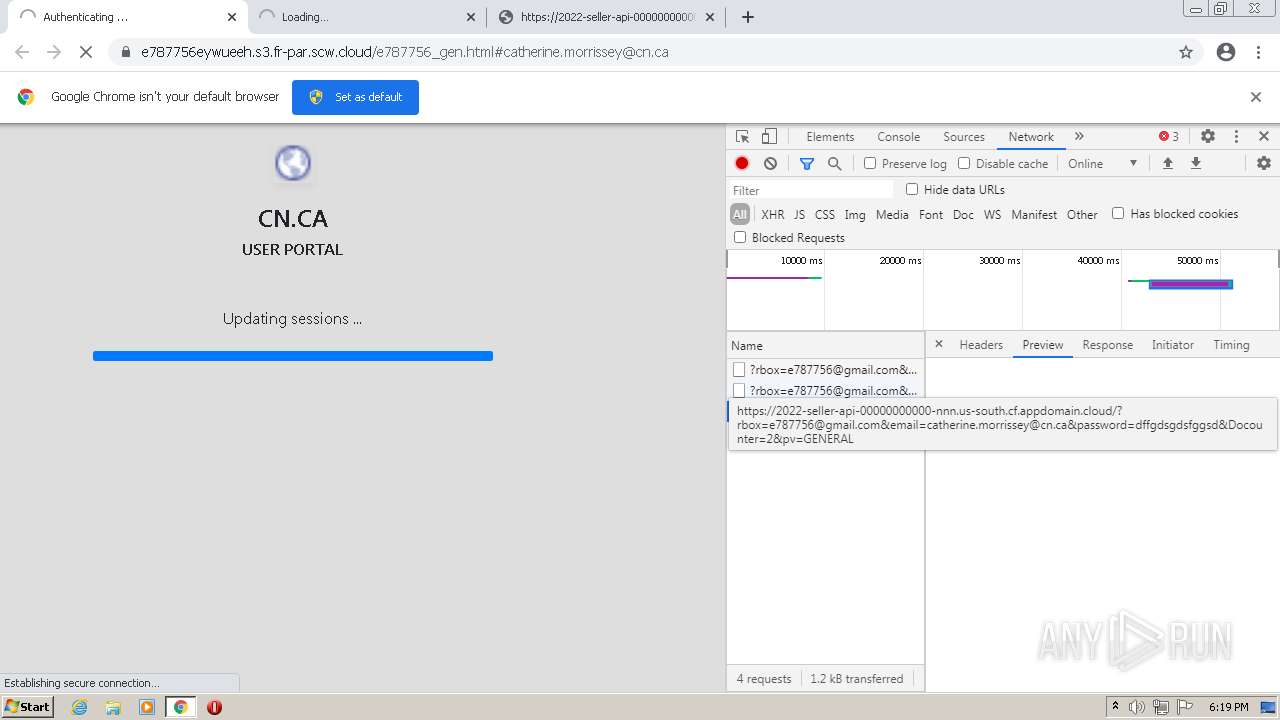
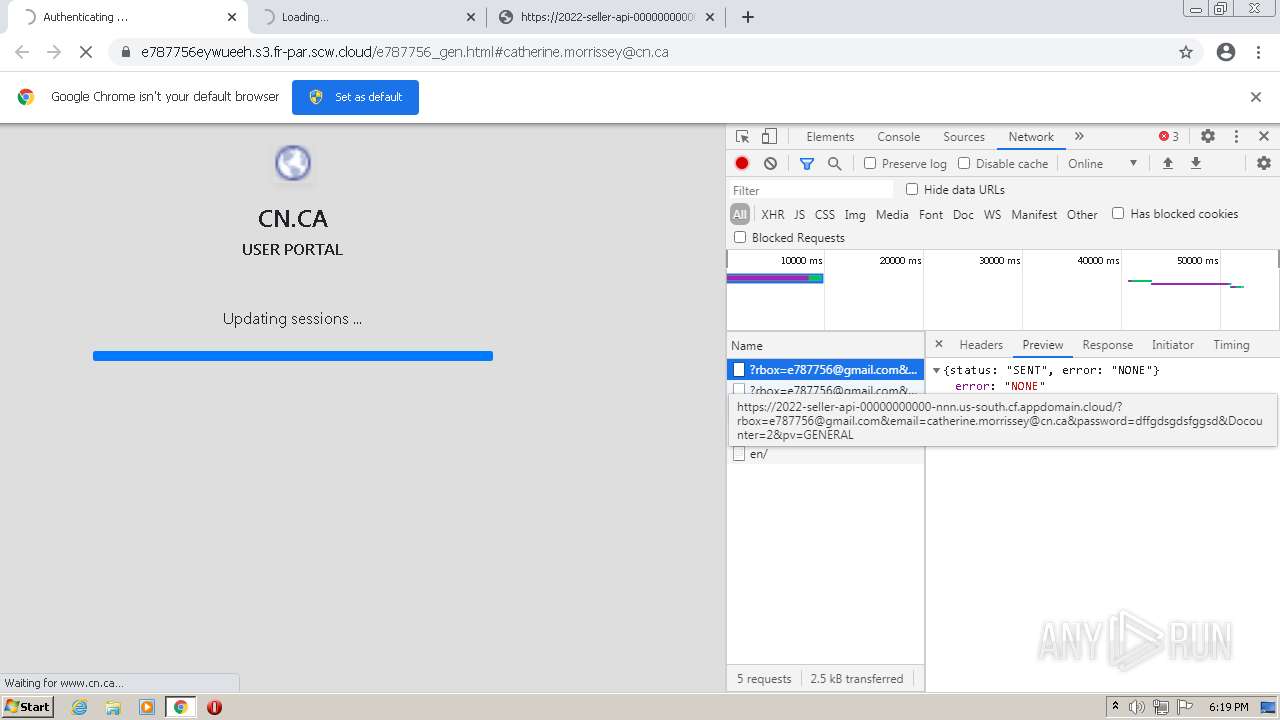
1372 | chrome.exe | 51.159.62.6:443 | e787756eywueeh.s3.fr-par.scw.cloud | — | GB | suspicious |
1372 | chrome.exe | 172.217.18.3:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
1372 | chrome.exe | 172.217.23.100:443 | www.google.com | Google Inc. | US | whitelisted |
1372 | chrome.exe | 104.17.25.14:443 | cdnjs.cloudflare.com | Cloudflare Inc | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clients2.google.com |
| whitelisted |
accounts.google.com |
| shared |
url8207.camisetasfutbolspainnn.com |
| suspicious |
clients2.googleusercontent.com |
| whitelisted |
202219910200m93071.lt.emlnk.com |
| unknown |
e787756eywueeh.s3.fr-par.scw.cloud |
| suspicious |
ctldl.windowsupdate.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
stackpath.bootstrapcdn.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
— | — | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |