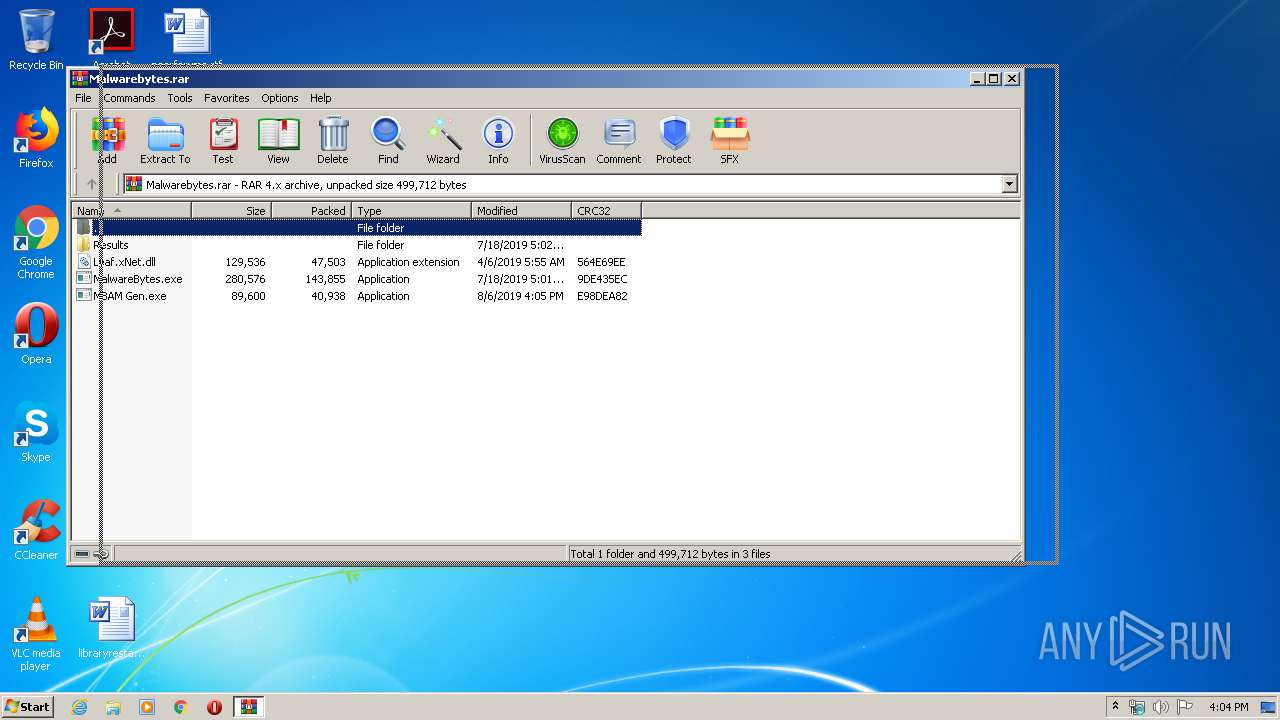
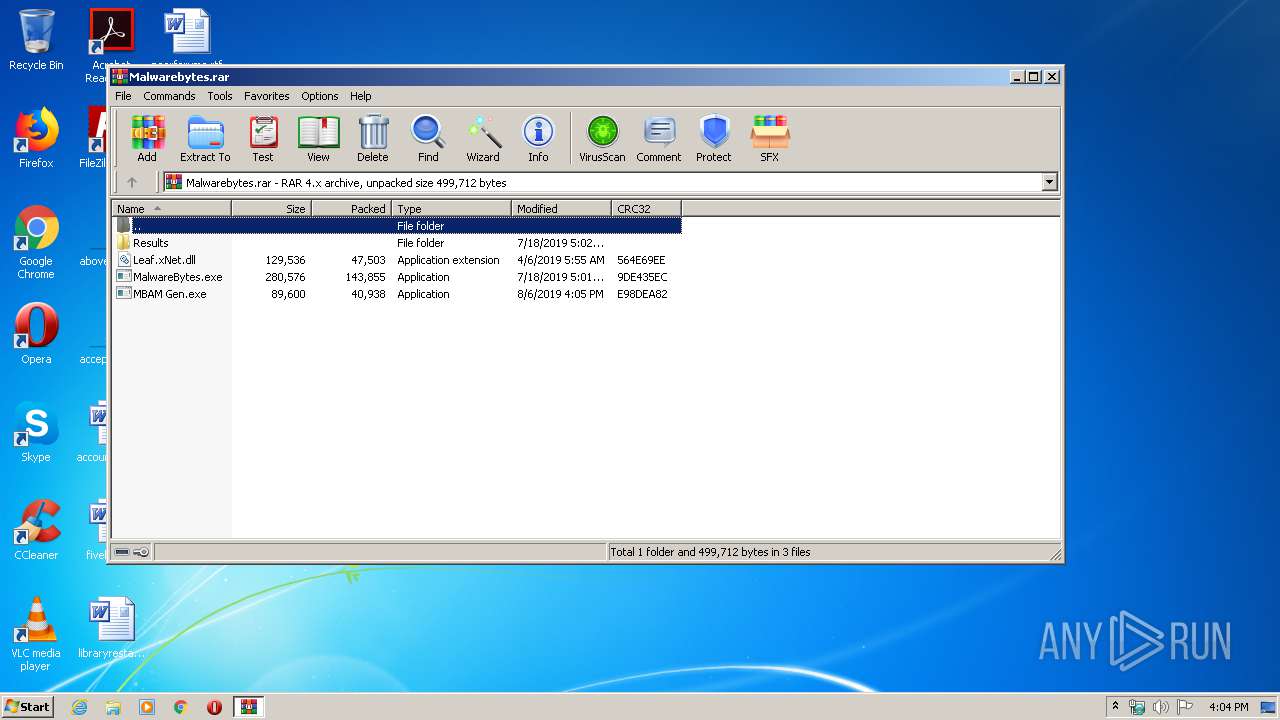
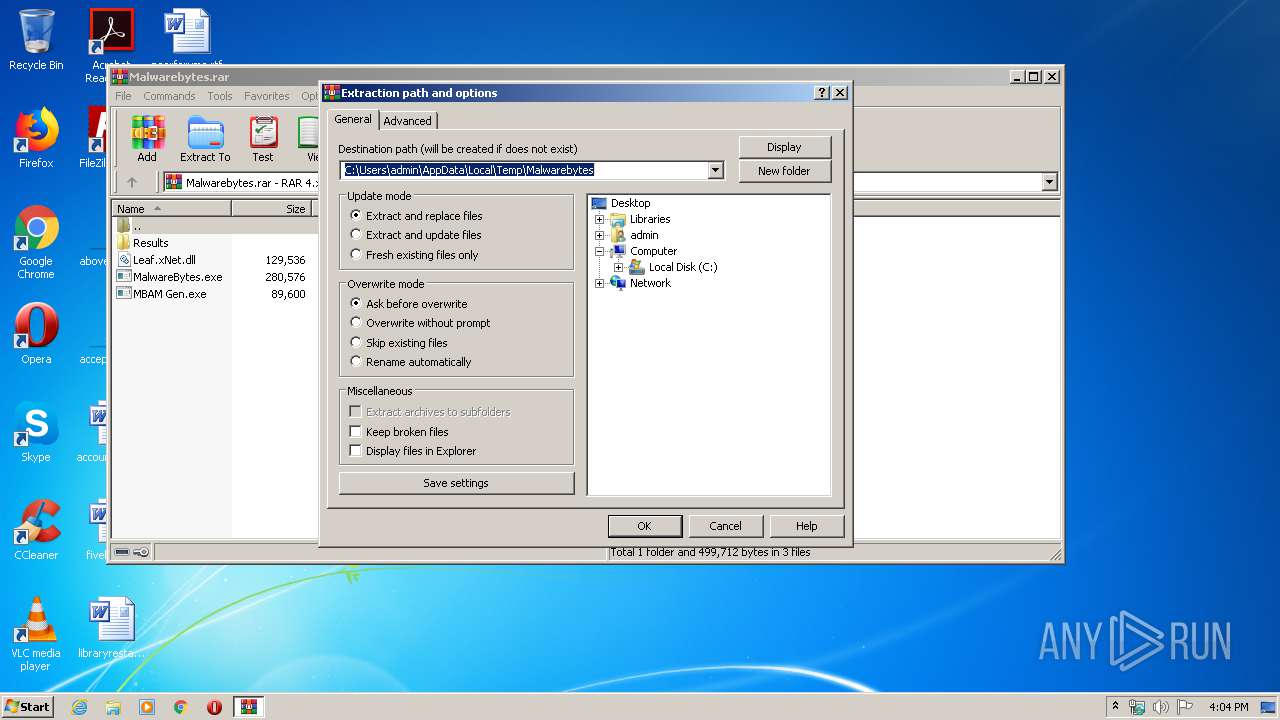
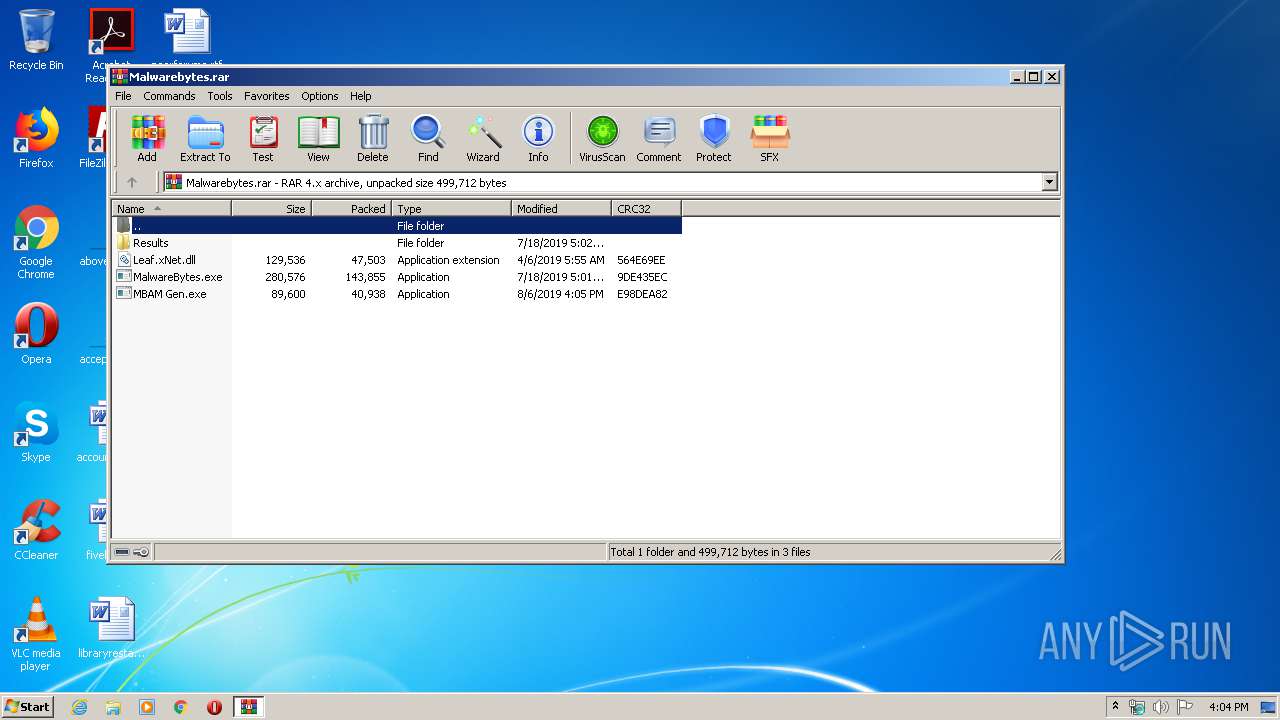
| File name: | Malwarebytes.rar |
| Full analysis: | https://app.any.run/tasks/090b77b2-0fce-466d-a149-2a7aff4b6c05 |
| Verdict: | Malicious activity |
| Analysis date: | February 21, 2020, 16:04:08 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v4, os: Win32 |
| MD5: | 547CF76534193CAF786EE5E140AE2DCA |
| SHA1: | 1F8290AE356EF838CF86C019B657E9894EF43AD0 |
| SHA256: | 87229EF185CEC84CF0227ED4572429206A4EB78C2B04339C08D4BABF7CF97A78 |
| SSDEEP: | 6144:3rdylfgmarzgj7LI+2CV4rAn+E/PFgAujaqVdgusVDkQ:wBYgt2Q+EVTQaCMaQ |
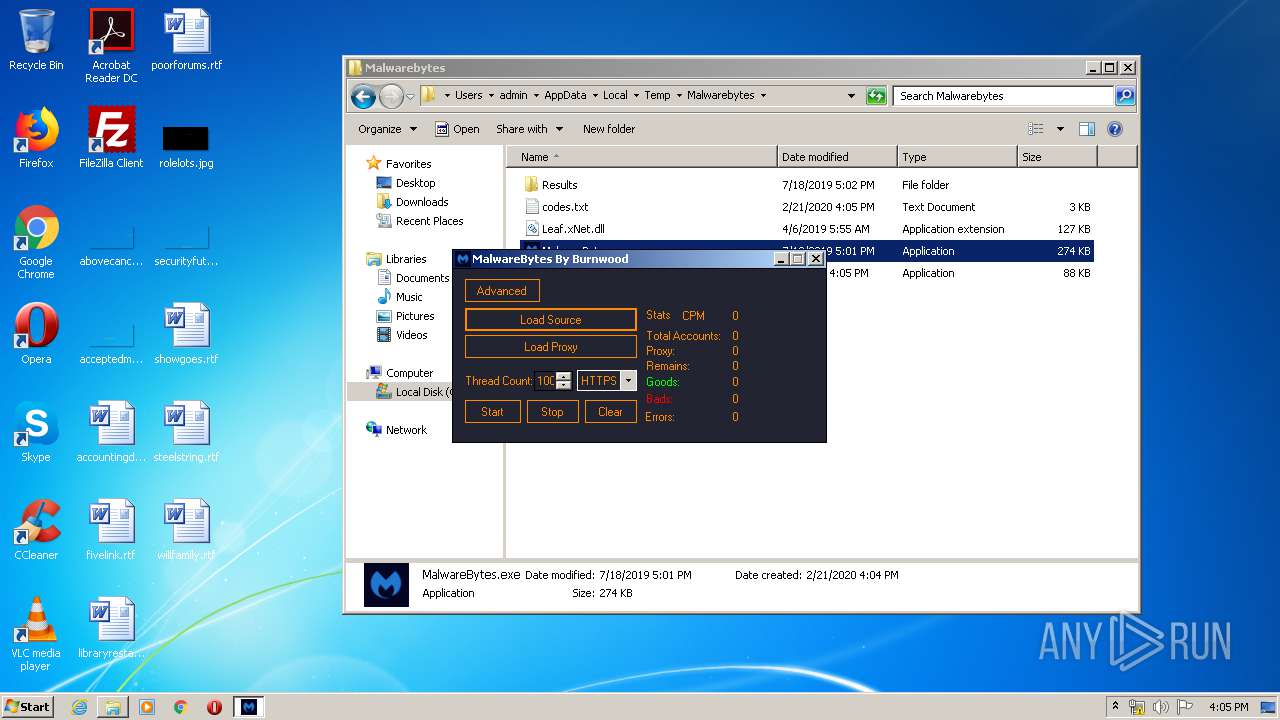
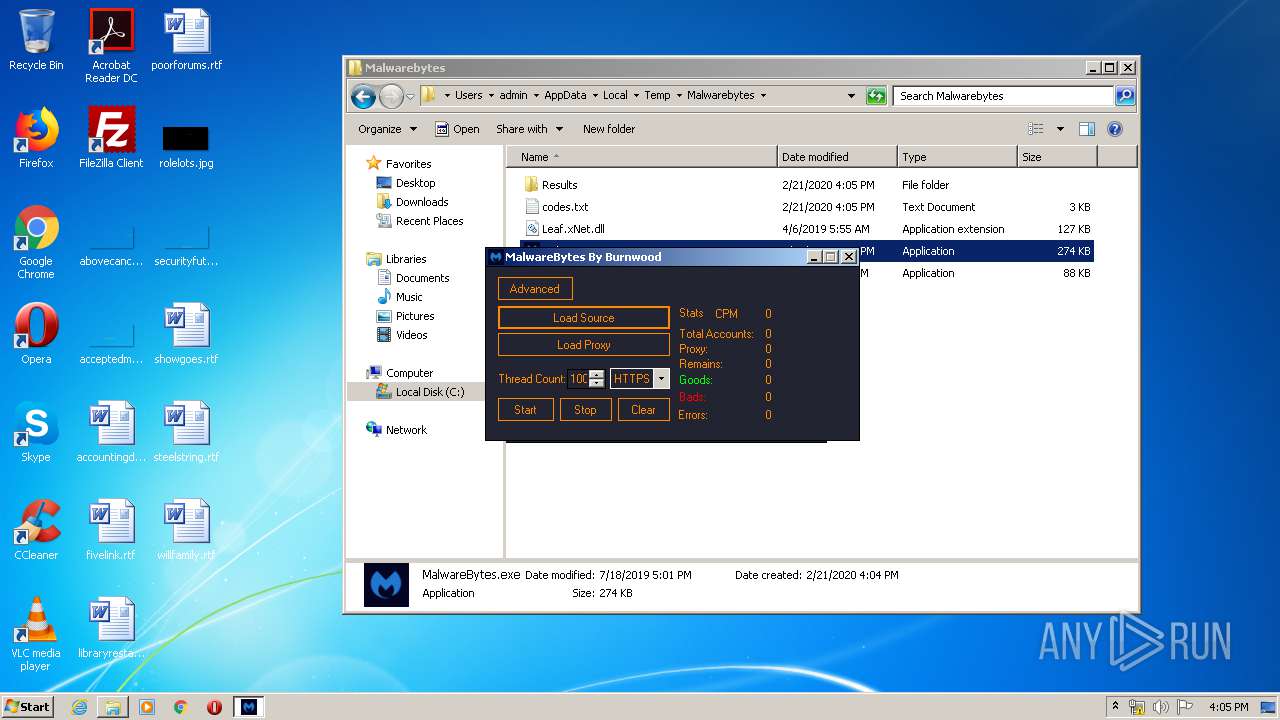
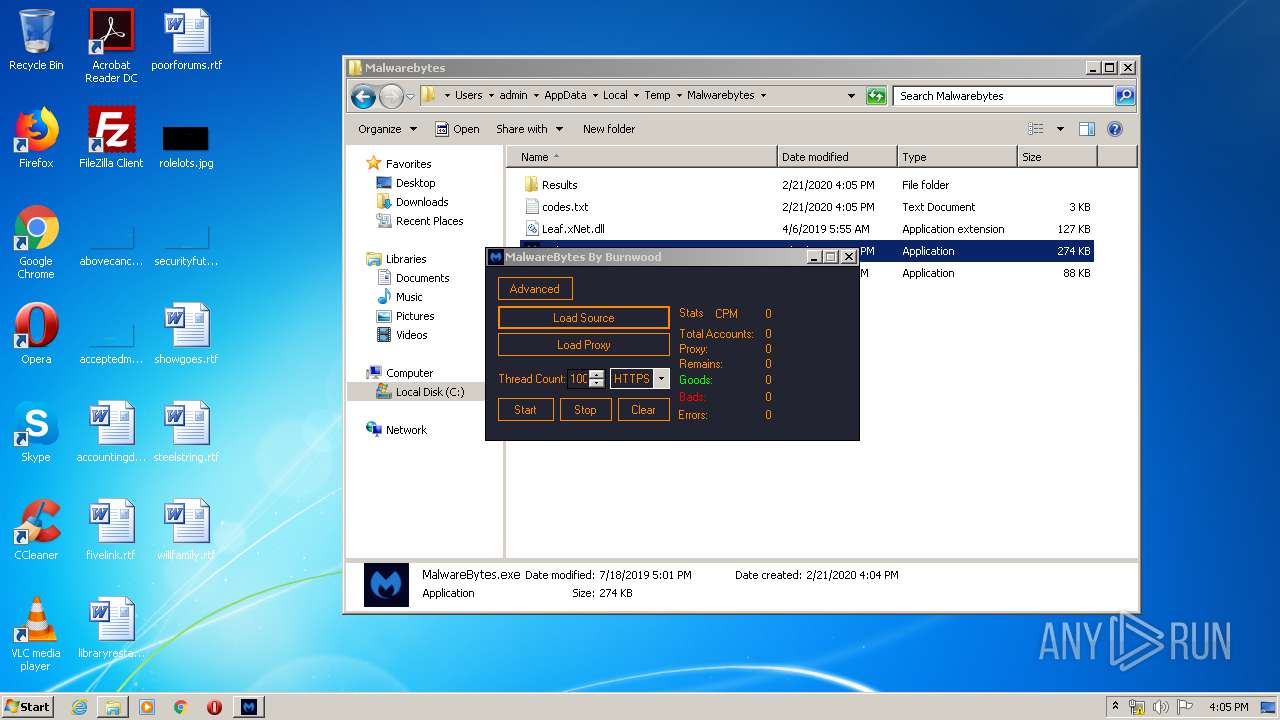
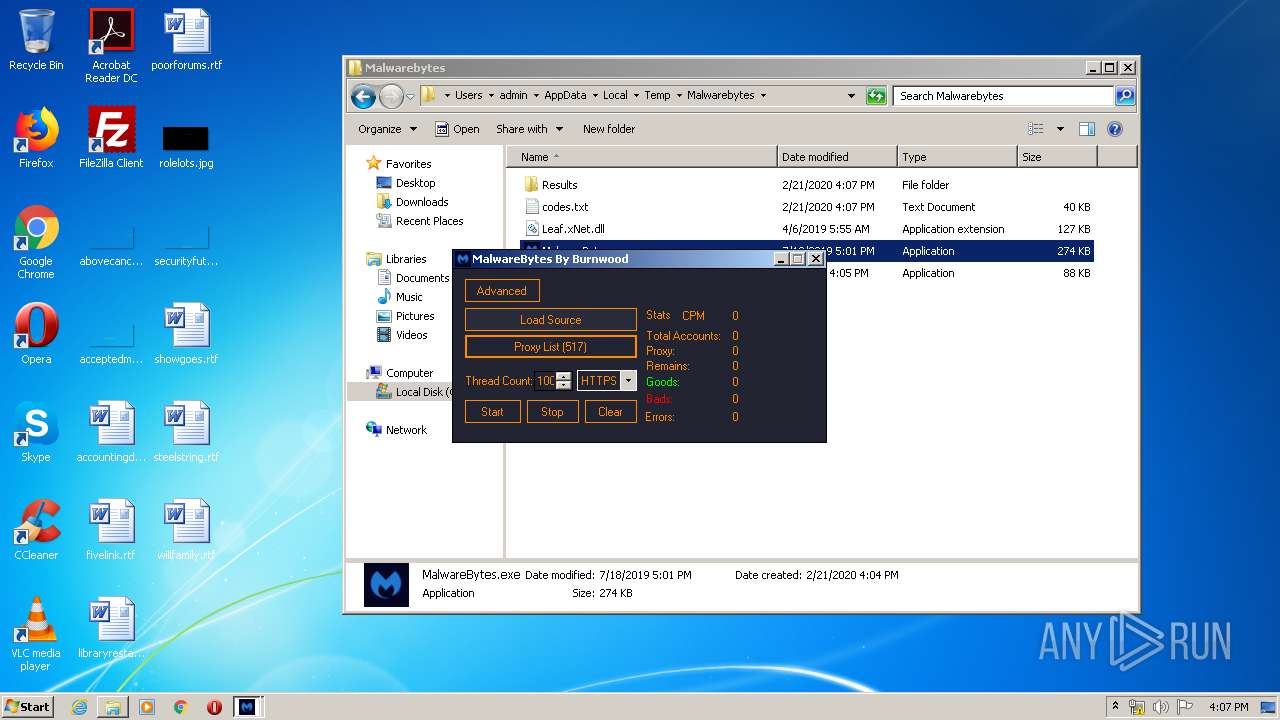
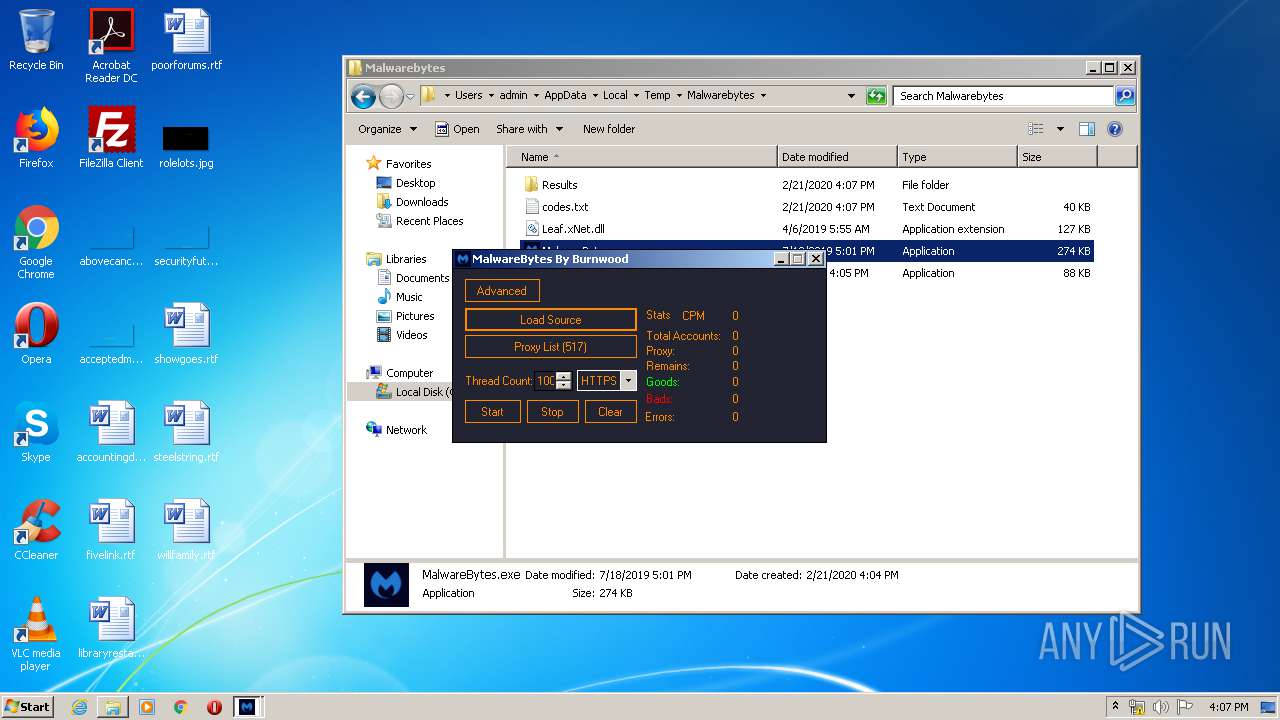
MALICIOUS
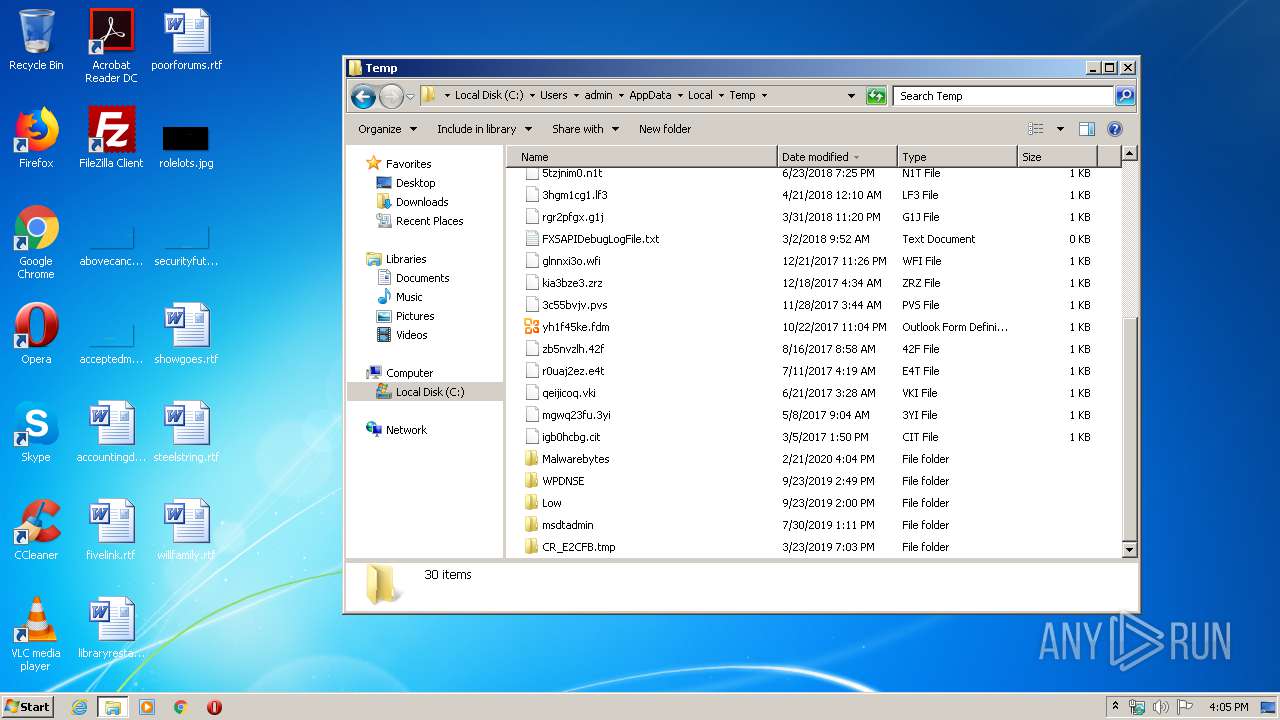
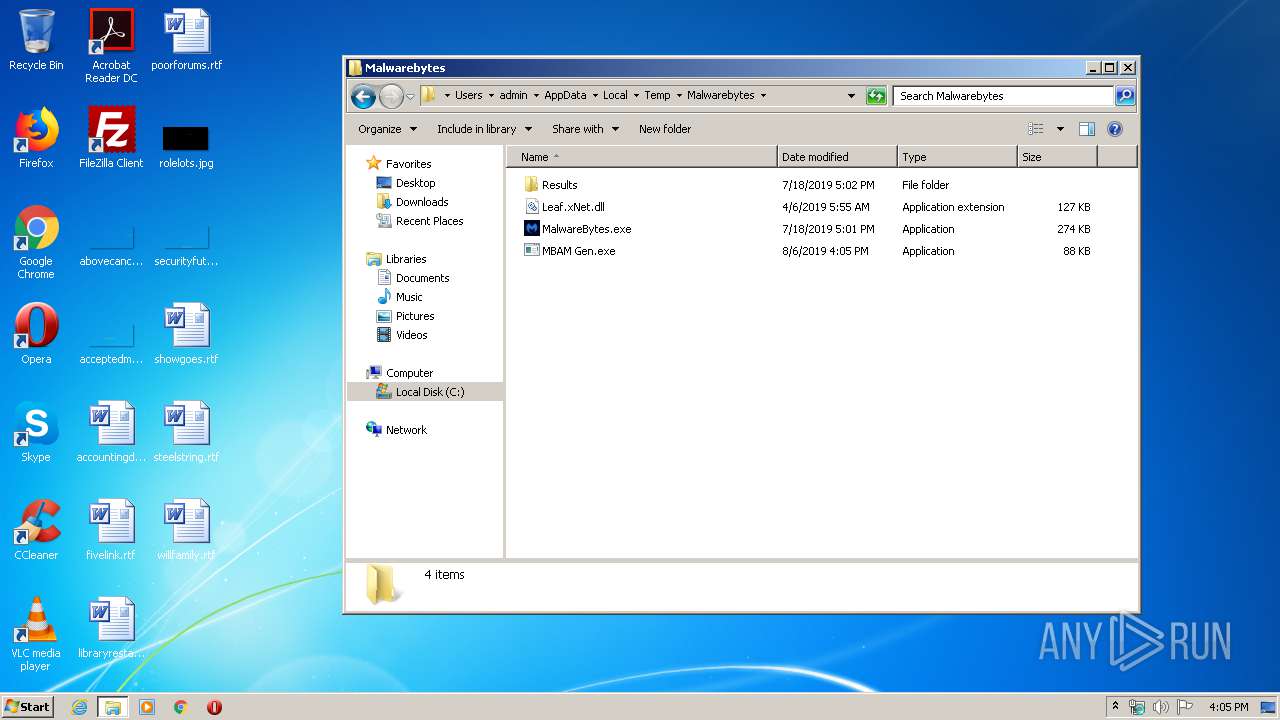
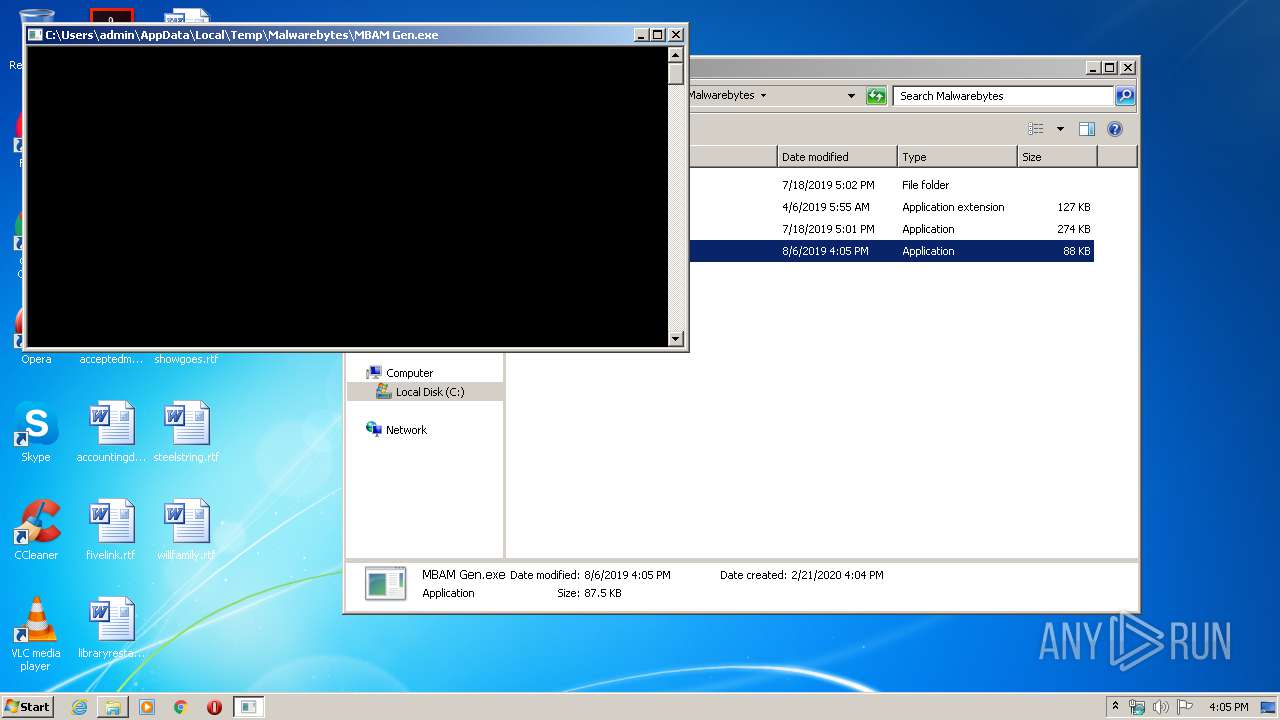
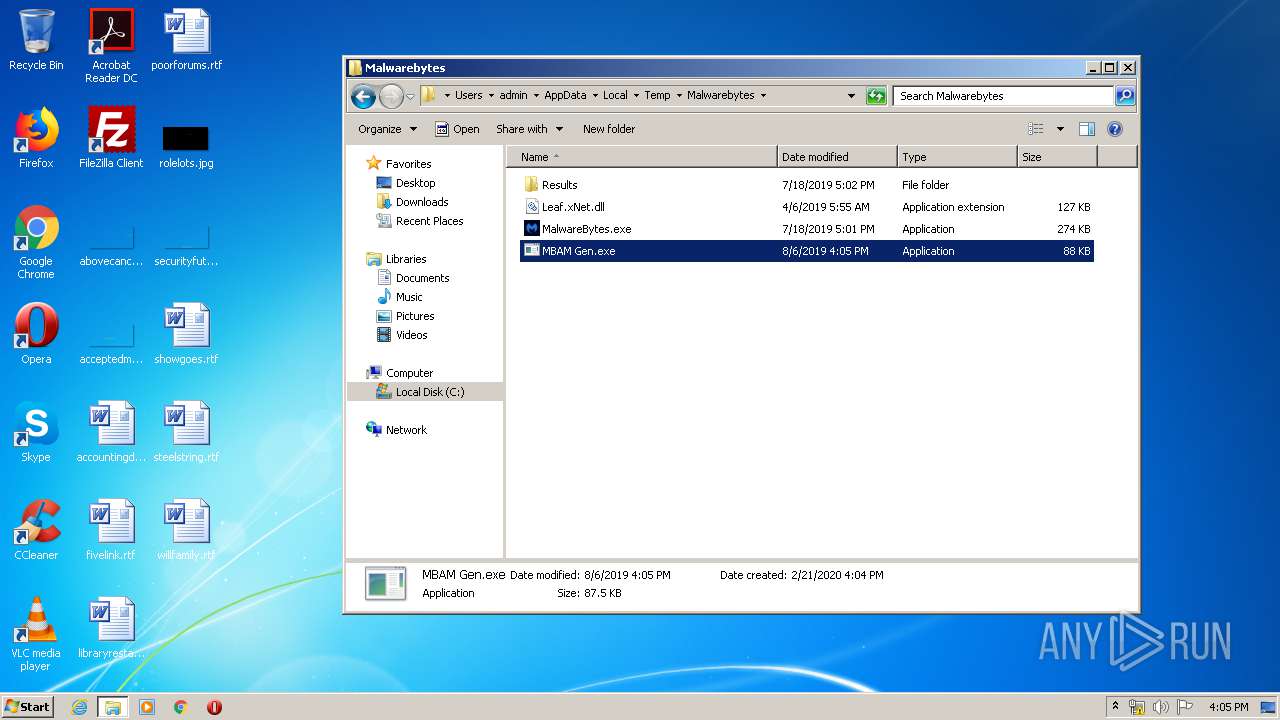
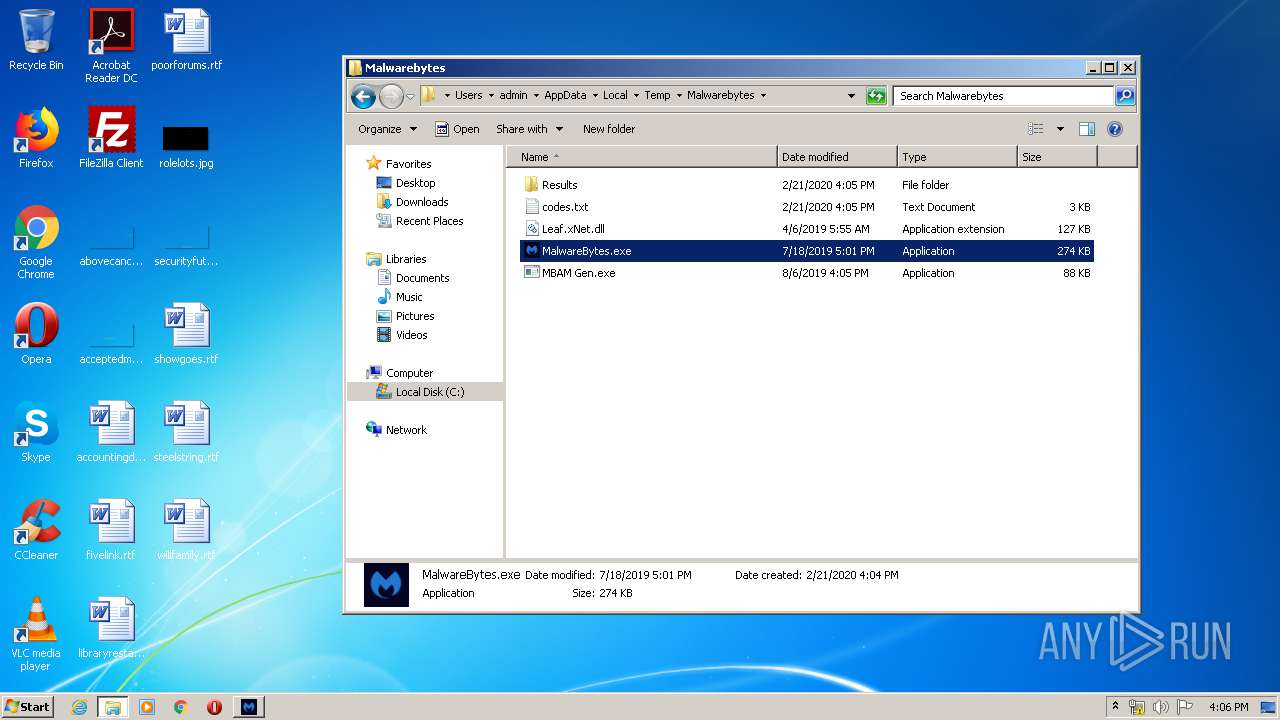
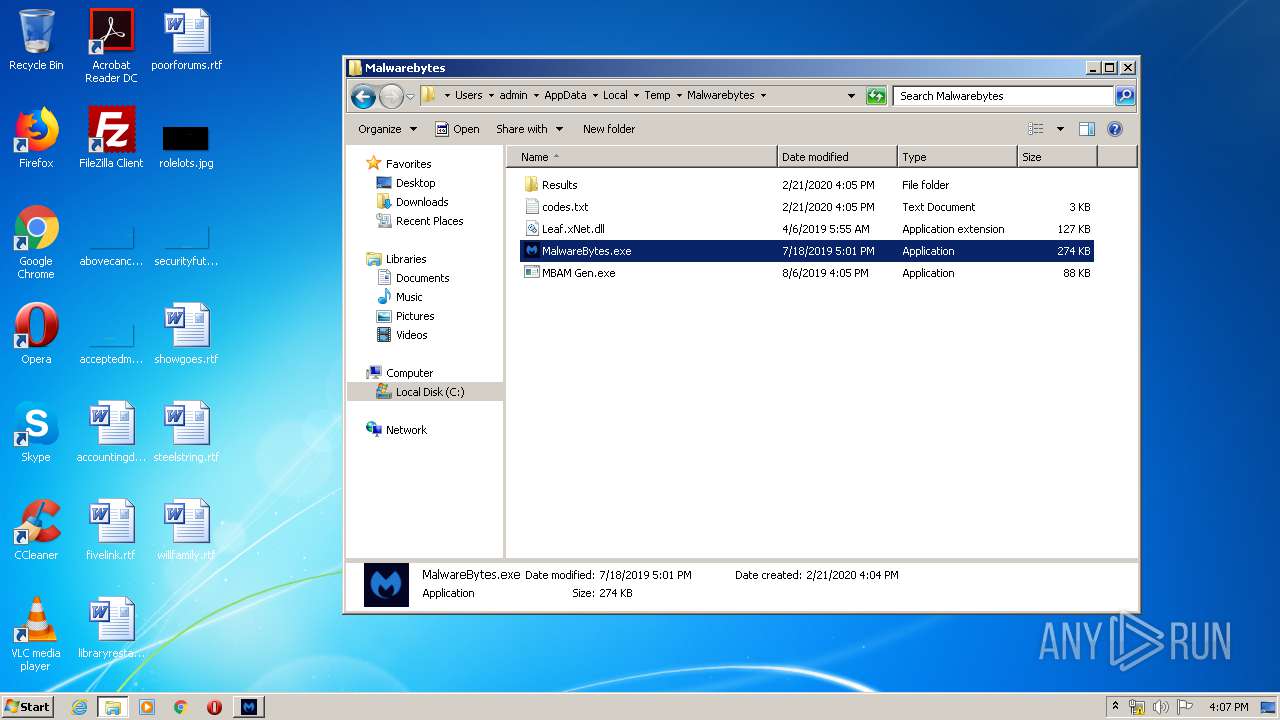
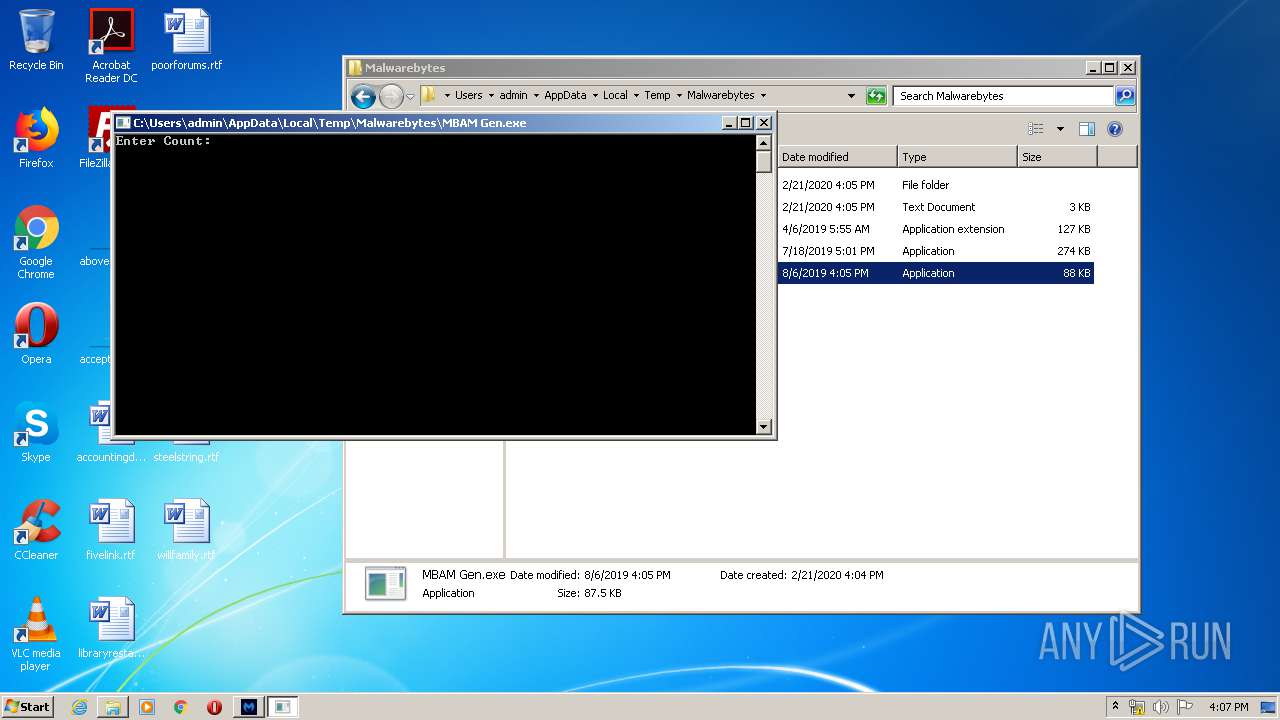
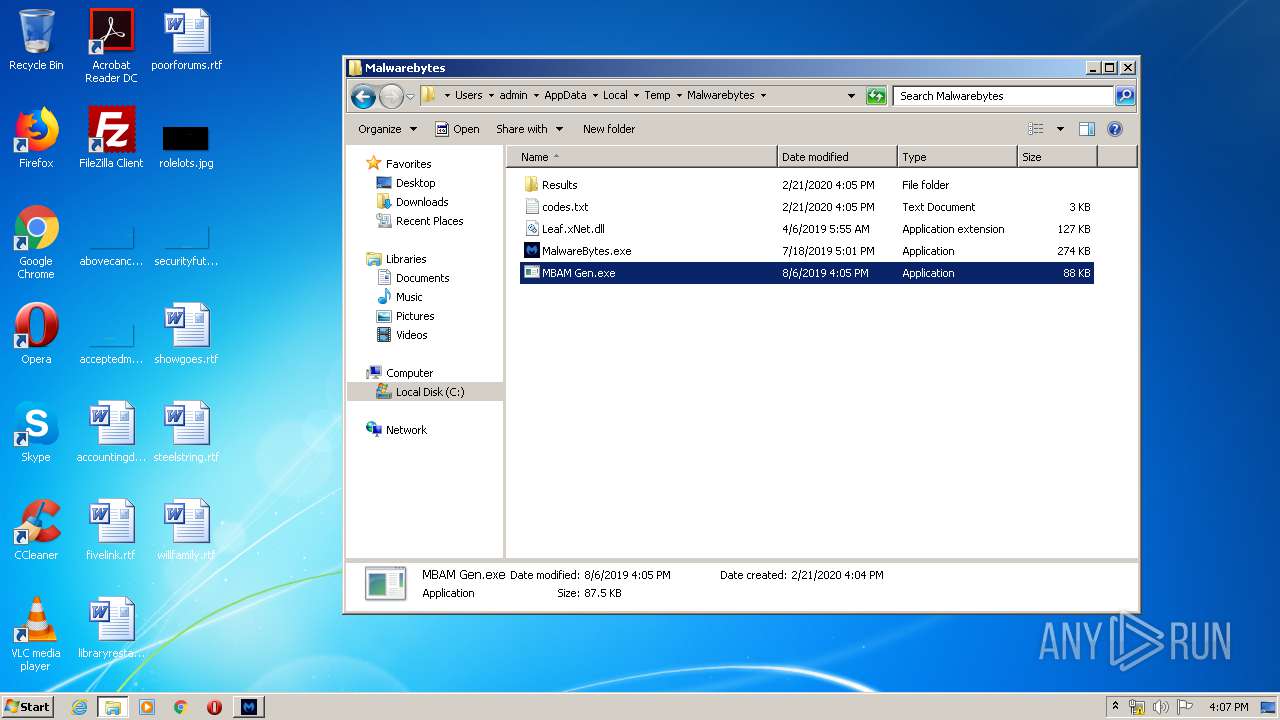
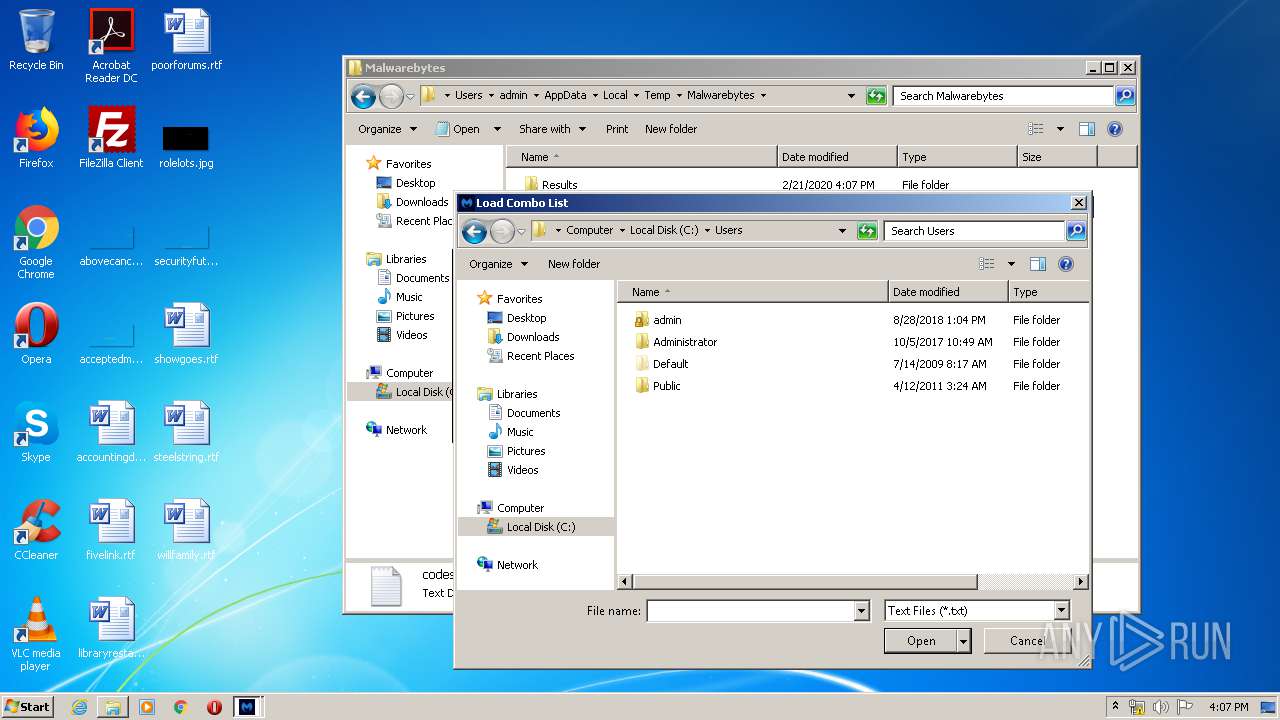
Application was dropped or rewritten from another process
- MBAM Gen.exe (PID: 1688)
- MalwareBytes.exe (PID: 2500)
- MBAM Gen.exe (PID: 3144)
- MalwareBytes.exe (PID: 1780)
Loads dropped or rewritten executable
- MalwareBytes.exe (PID: 2500)
- MalwareBytes.exe (PID: 1780)
SUSPICIOUS
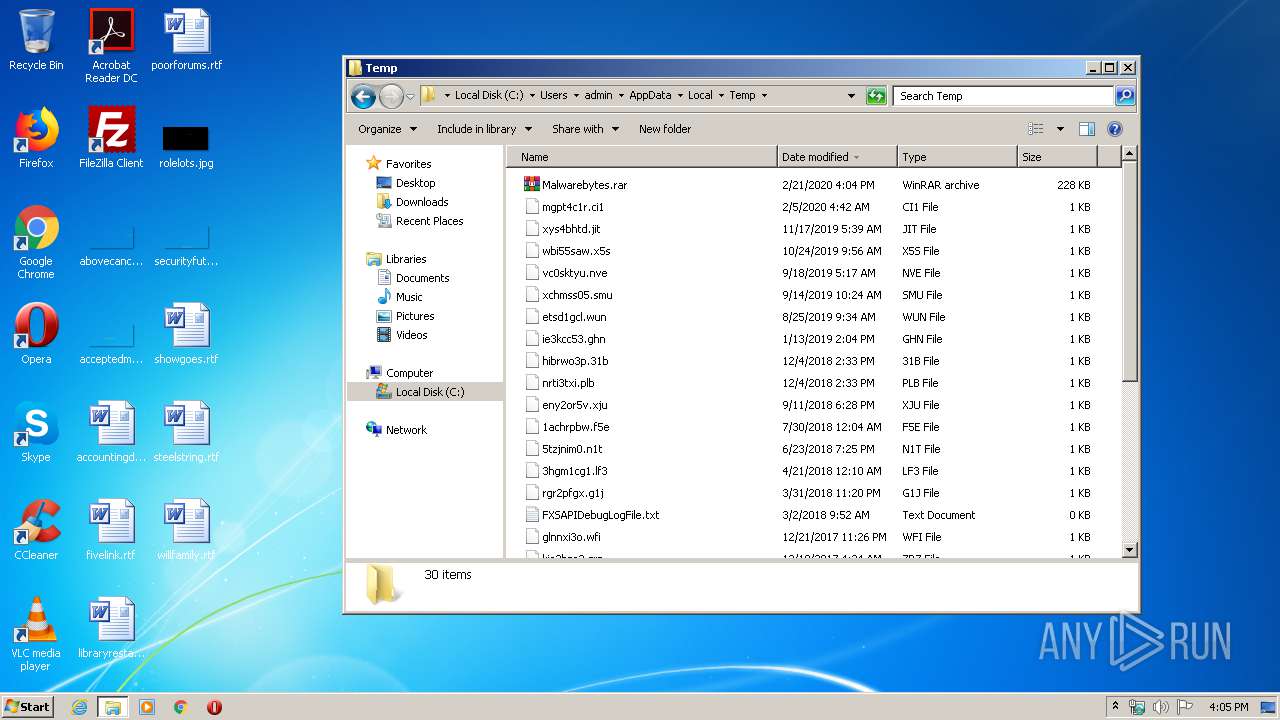
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2884)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3348)
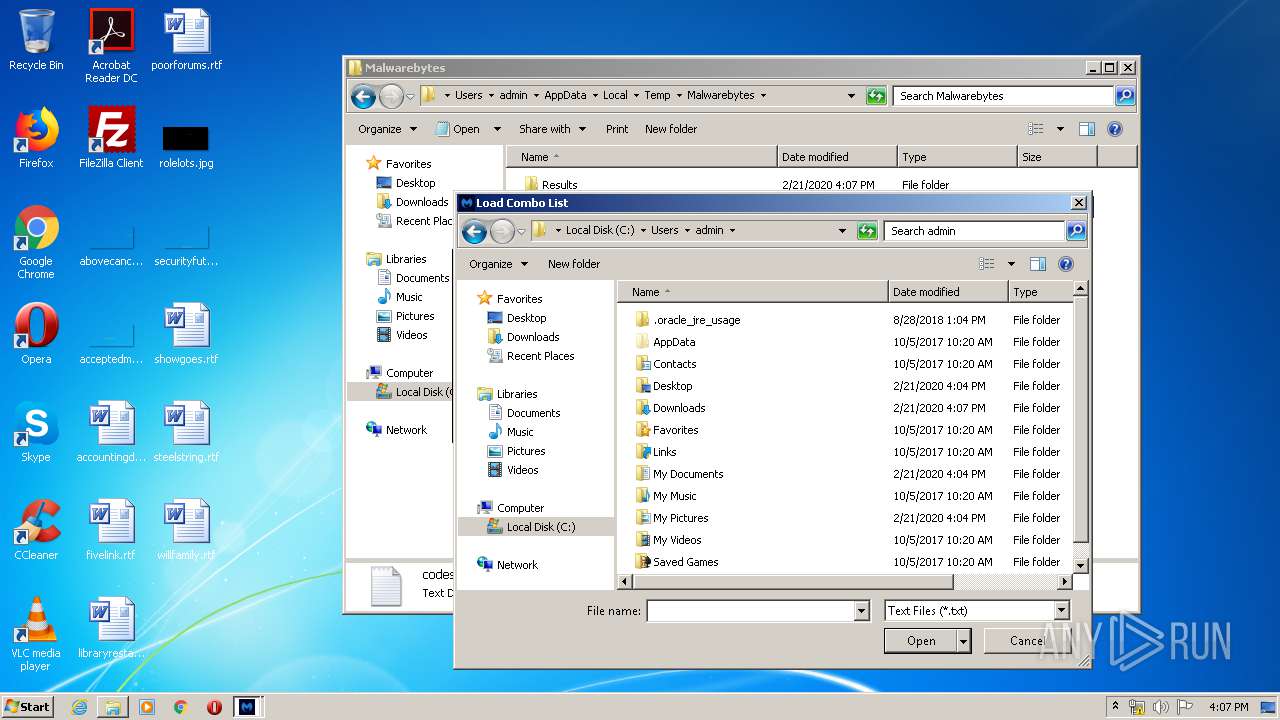
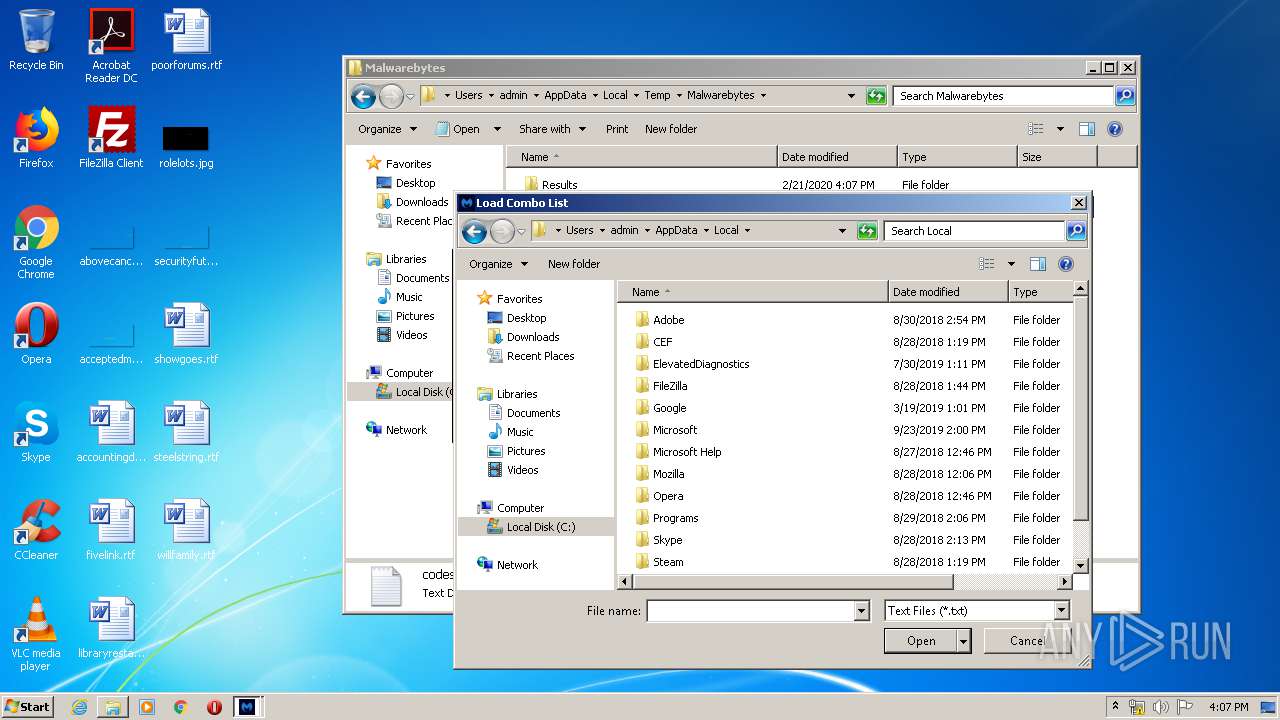
Reads Environment values
- MalwareBytes.exe (PID: 1780)
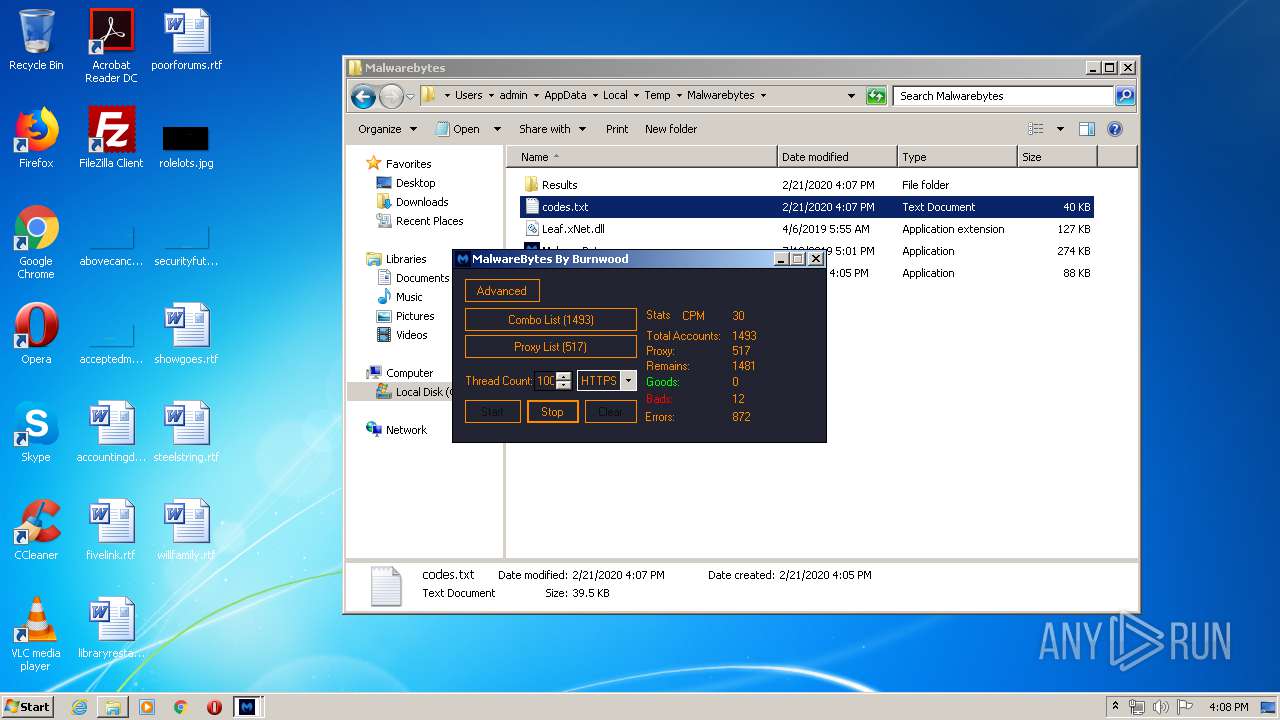
Connects to unusual port
- MalwareBytes.exe (PID: 1780)
INFO
Manual execution by user
- explorer.exe (PID: 3448)
- MBAM Gen.exe (PID: 1688)
- NOTEPAD.EXE (PID: 1928)
- MalwareBytes.exe (PID: 2500)
- chrome.exe (PID: 2056)
- MBAM Gen.exe (PID: 3144)
- chrome.exe (PID: 3348)
- MalwareBytes.exe (PID: 1780)
Reads the hosts file
- chrome.exe (PID: 2056)
- chrome.exe (PID: 2956)
- chrome.exe (PID: 1640)
- chrome.exe (PID: 3348)
Application launched itself
- chrome.exe (PID: 3348)
- chrome.exe (PID: 2056)
Reads settings of System Certificates
- chrome.exe (PID: 2956)
- MalwareBytes.exe (PID: 1780)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v-4.x) (58.3) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (41.6) |
EXIF
ZIP
| CompressedSize: | 47537 |
|---|---|
| UncompressedSize: | 129536 |
| OperatingSystem: | Win32 |
| ModifyDate: | 2019:04:06 05:55:09 |
| PackingMethod: | Normal |
| ArchivedFileName: | Leaf.xNet.dll |
Total processes
100
Monitored processes
53
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 180 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,16941756225788213302,13222807025365886665,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=4699447004621179962 --mojo-platform-channel-handle=2124 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 272 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,16941756225788213302,13222807025365886665,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13798687693843889564 --mojo-platform-channel-handle=3436 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 308 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6a36a9d0,0x6a36a9e0,0x6a36a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 332 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,16941756225788213302,13222807025365886665,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15479202085704178504 --mojo-platform-channel-handle=3188 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 940 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,16941756225788213302,13222807025365886665,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11062250297756703788 --renderer-client-id=28 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2440 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1640 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,16941756225788213302,13222807025365886665,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=17321869680517016227 --mojo-platform-channel-handle=1588 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
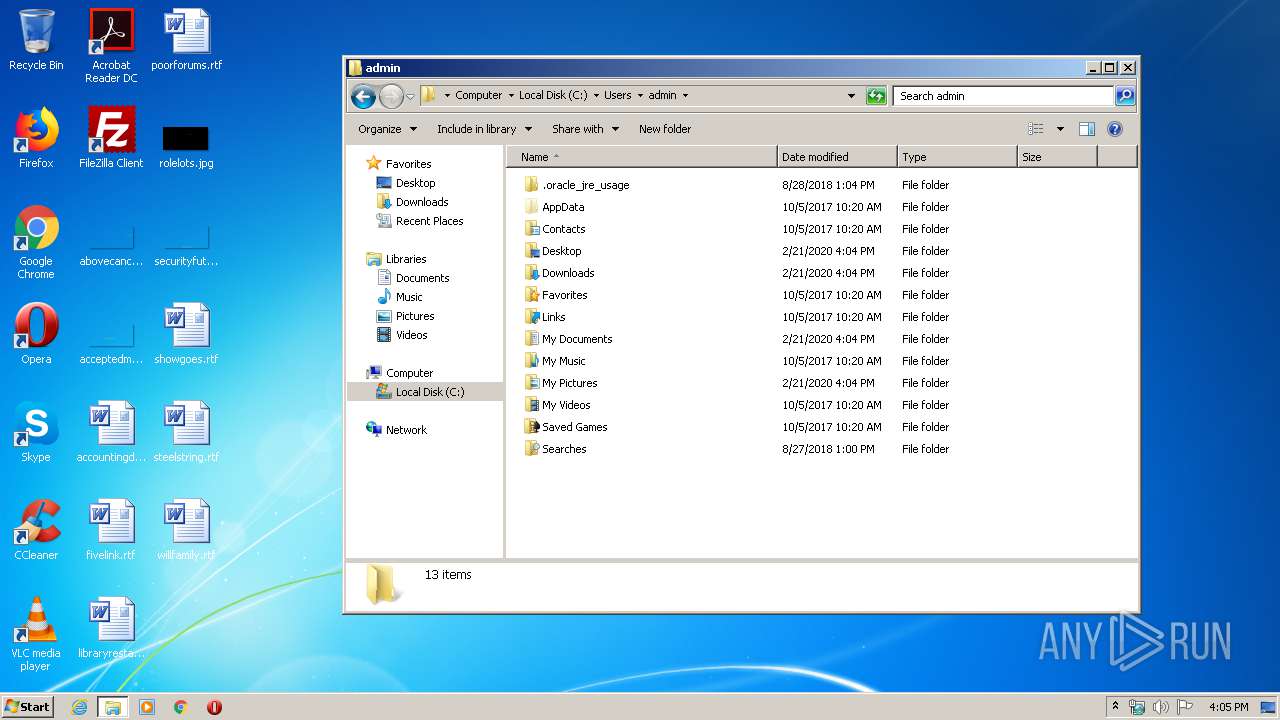
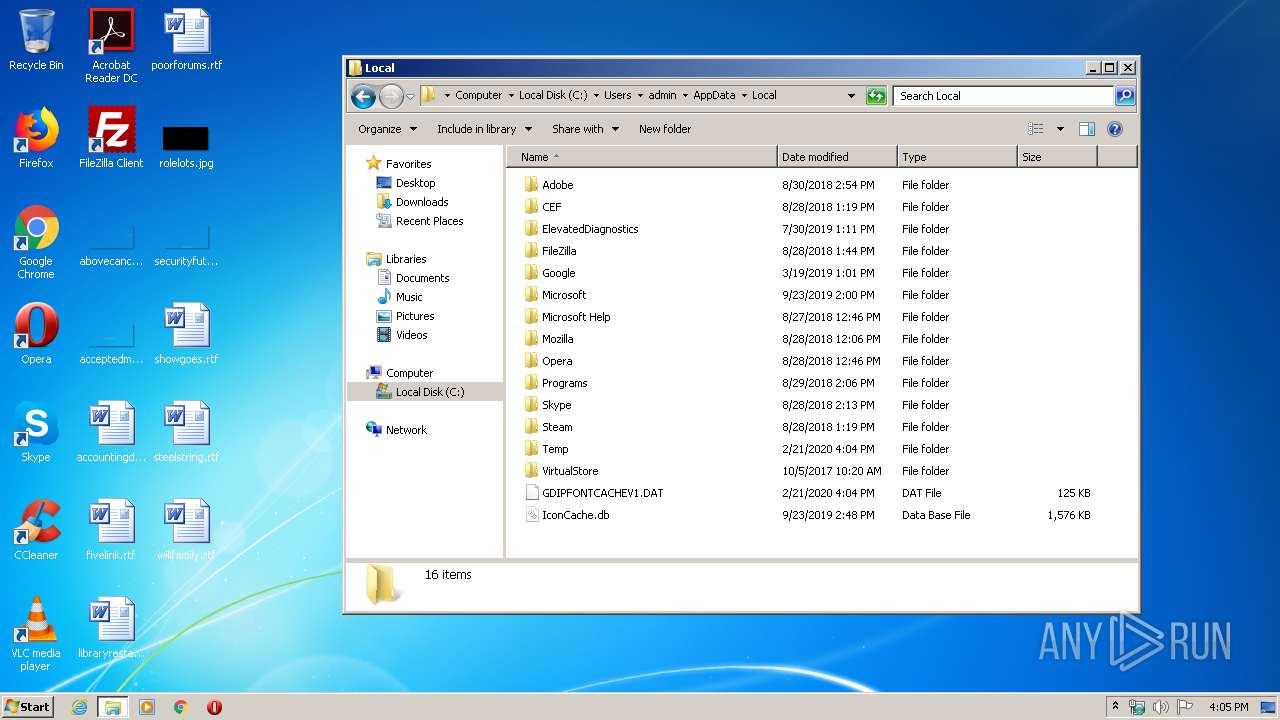
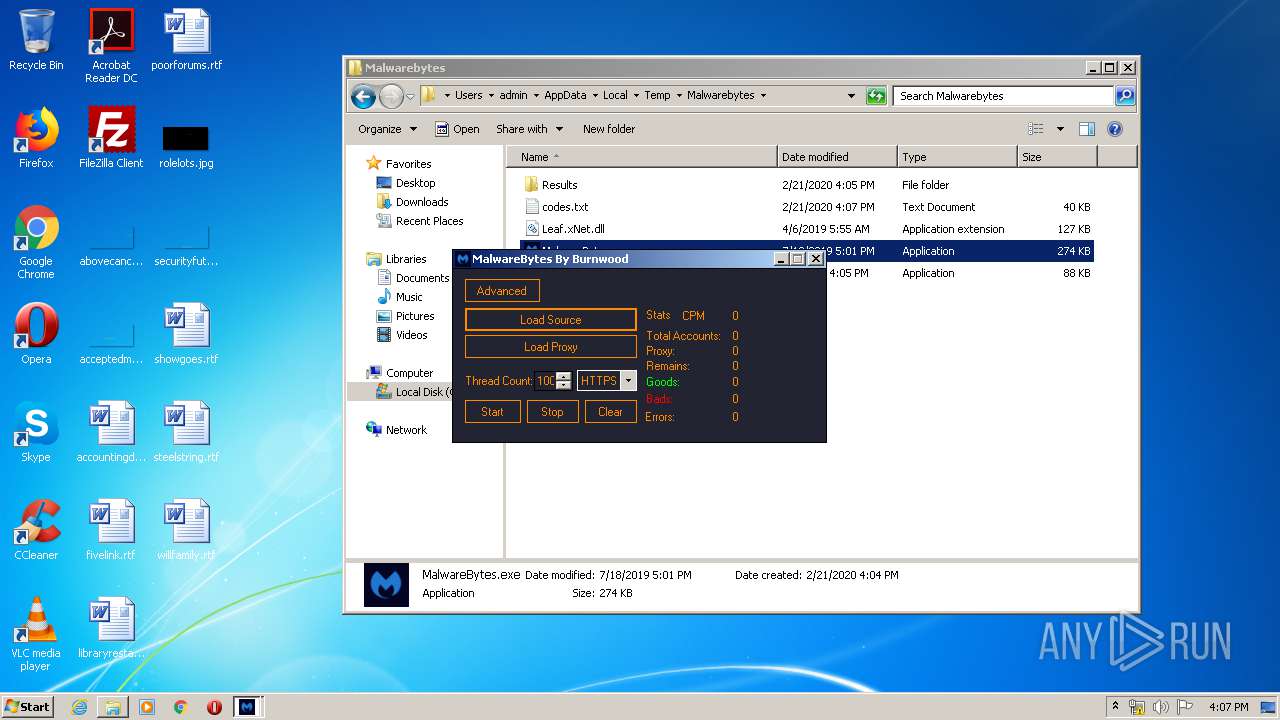
| 1688 | "C:\Users\admin\AppData\Local\Temp\Malwarebytes\MBAM Gen.exe" | C:\Users\admin\AppData\Local\Temp\Malwarebytes\MBAM Gen.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: MBAM Gen Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1724 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,16941756225788213302,13222807025365886665,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12295077563402314745 --renderer-client-id=33 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1332 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
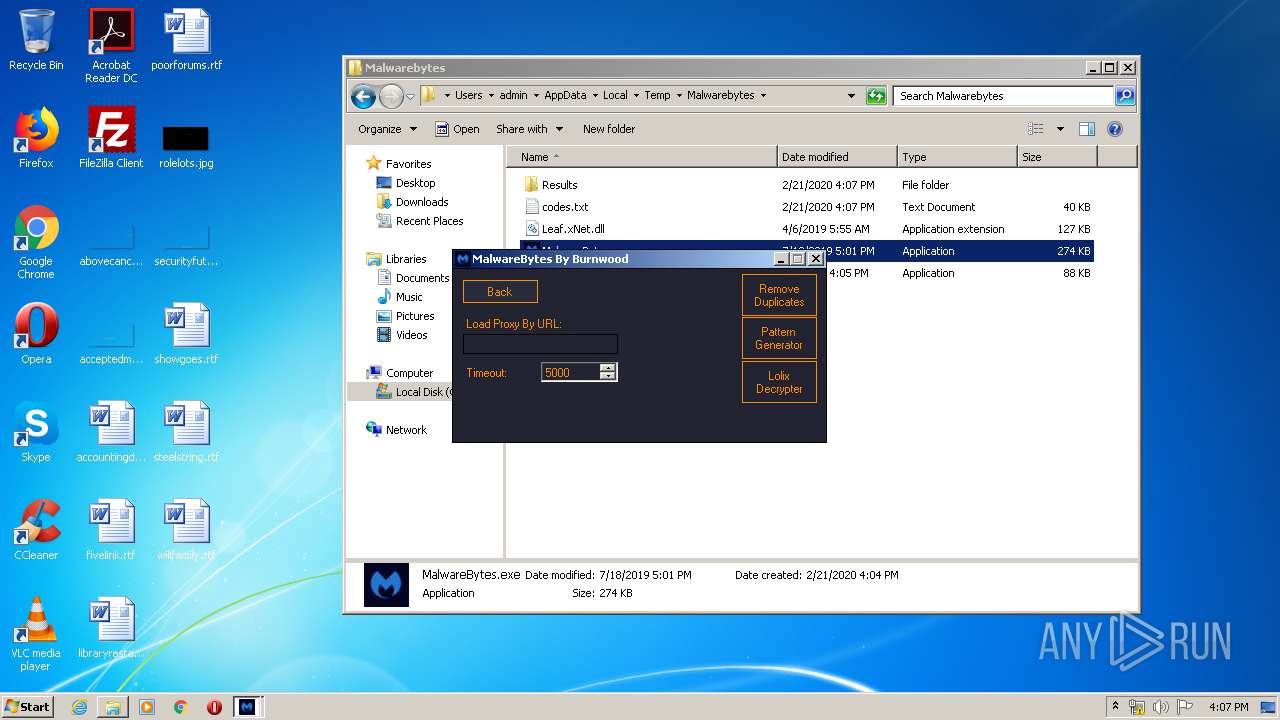
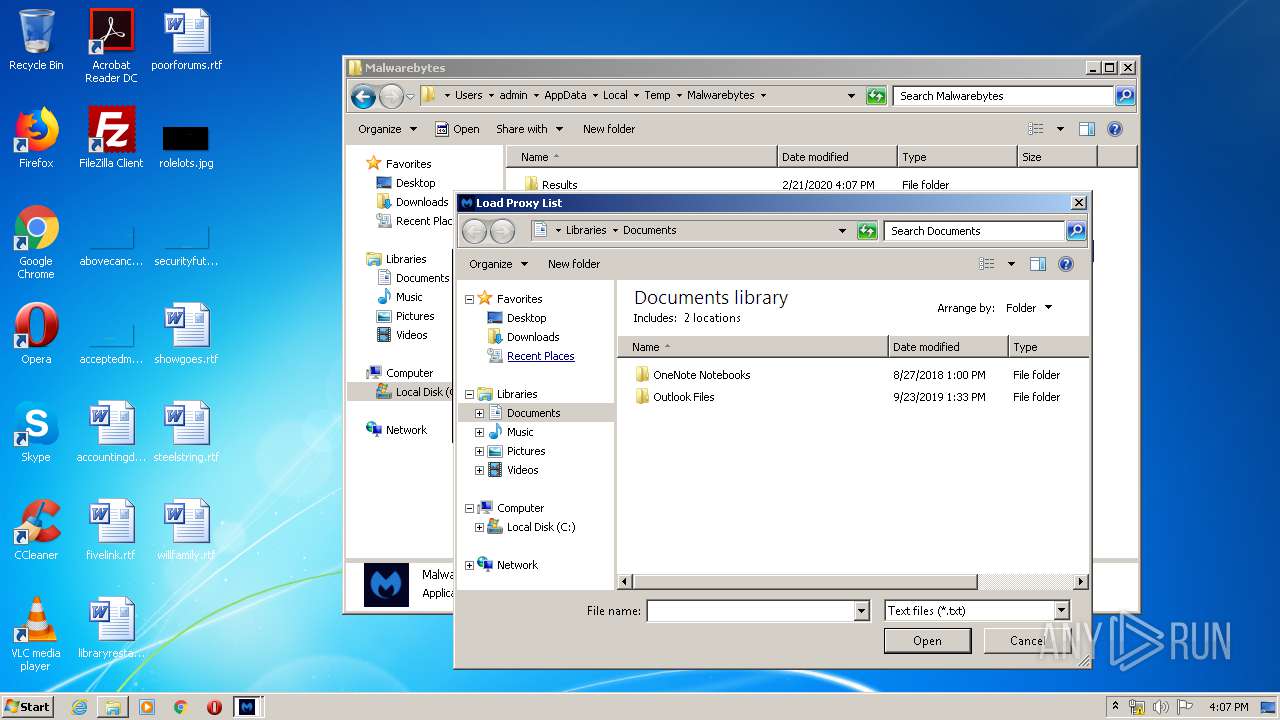
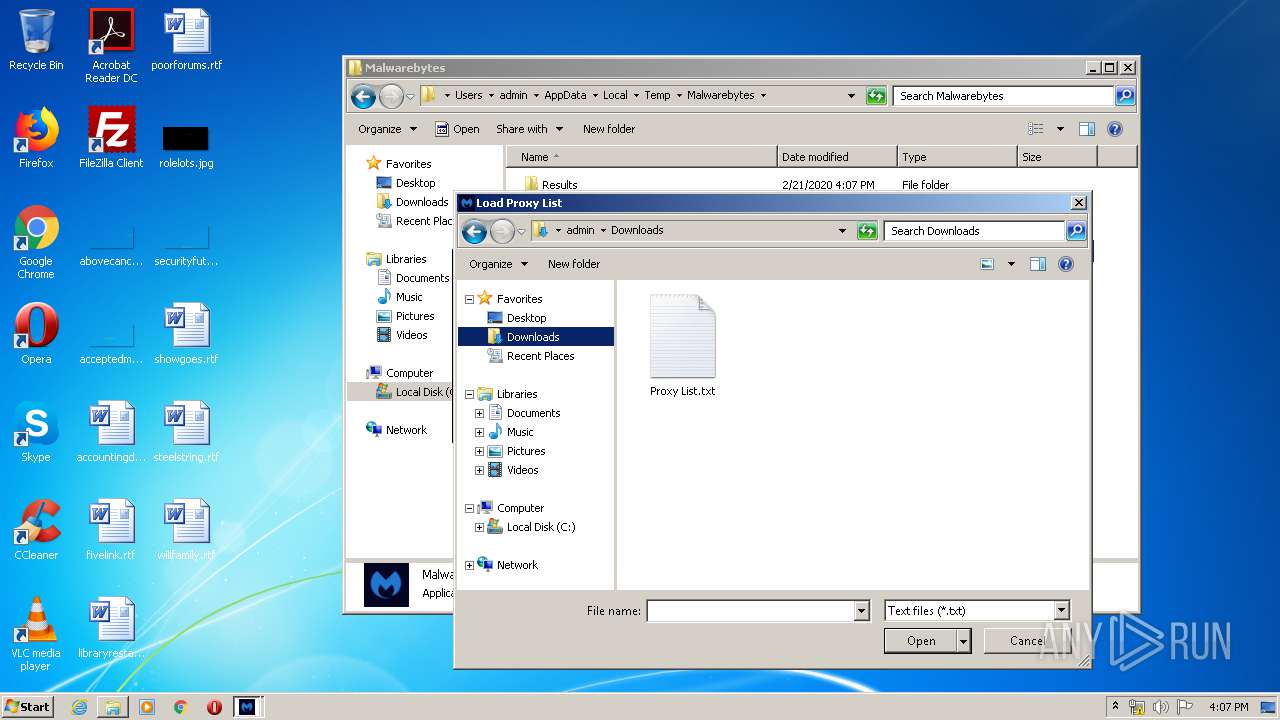
| 1780 | "C:\Users\admin\AppData\Local\Temp\Malwarebytes\MalwareBytes.exe" | C:\Users\admin\AppData\Local\Temp\Malwarebytes\MalwareBytes.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: UiBase Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1904 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,16941756225788213302,13222807025365886665,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3592529691131138437 --mojo-platform-channel-handle=3200 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
8 609
Read events
8 112
Write events
483
Delete events
14
Modification events
| (PID) Process: | (2884) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2884) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2884) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2884) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Malwarebytes.rar | |||
| (PID) Process: | (2884) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2884) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2884) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2884) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2884) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Malwarebytes | |||
| (PID) Process: | (2884) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF6A000000400000002A04000035020000 | |||
Executable files
3
Suspicious files
94
Text files
262
Unknown types
15
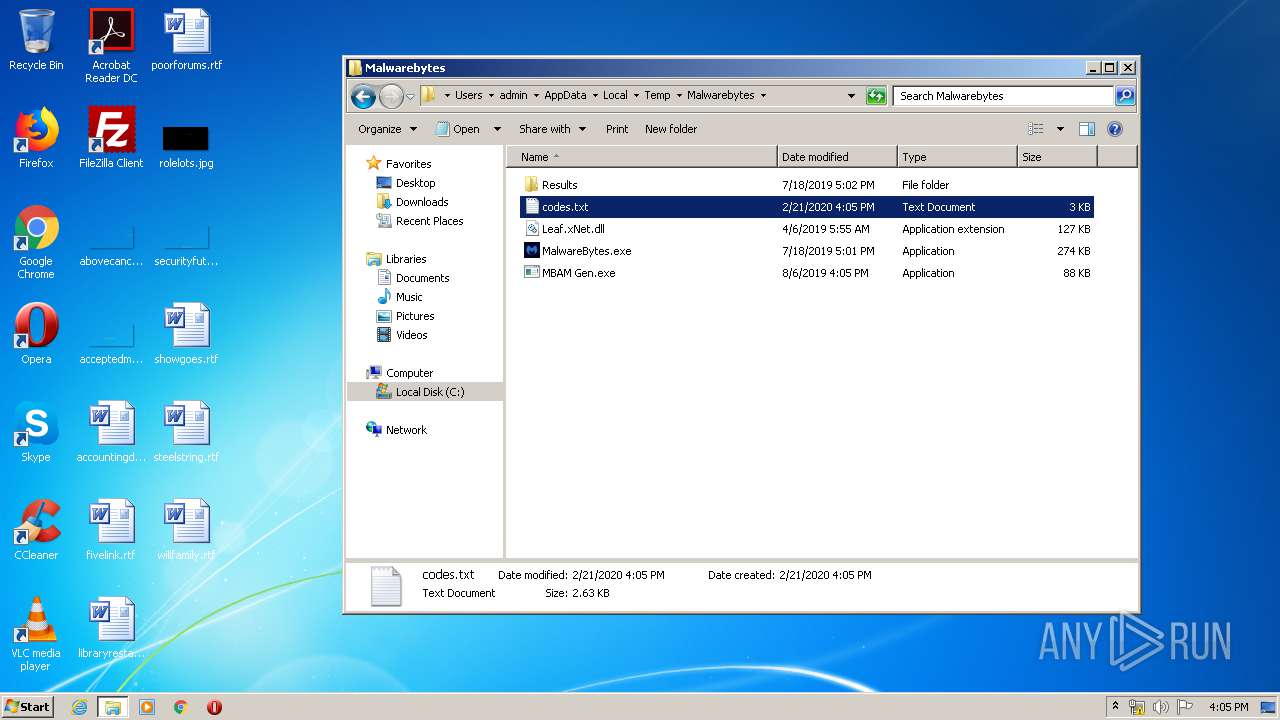
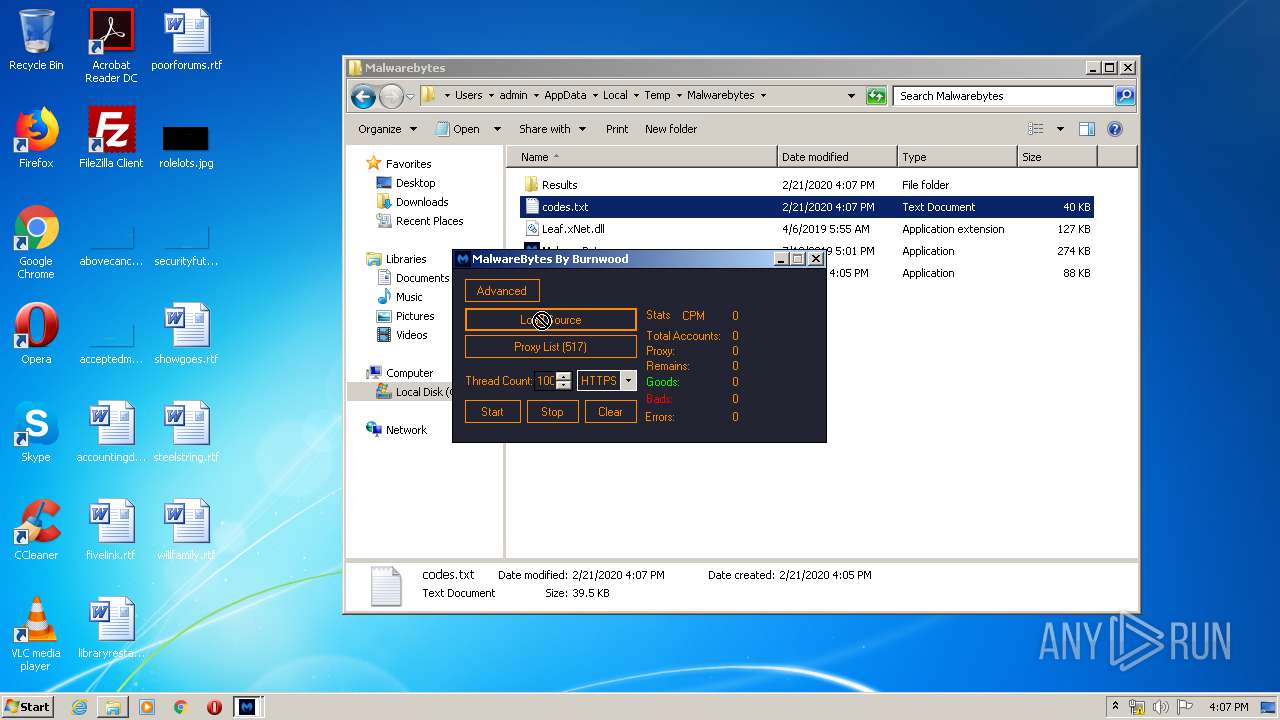
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2056 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5E4FFFD9-808.pma | — | |
MD5:— | SHA256:— | |||
| 2056 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\19c4eae6-abad-4c1d-a868-01509af7934a.tmp | — | |
MD5:— | SHA256:— | |||
| 2056 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2884 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Malwarebytes\MBAM Gen.exe | executable | |
MD5:— | SHA256:— | |||
| 2884 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Malwarebytes\MalwareBytes.exe | executable | |
MD5:— | SHA256:— | |||
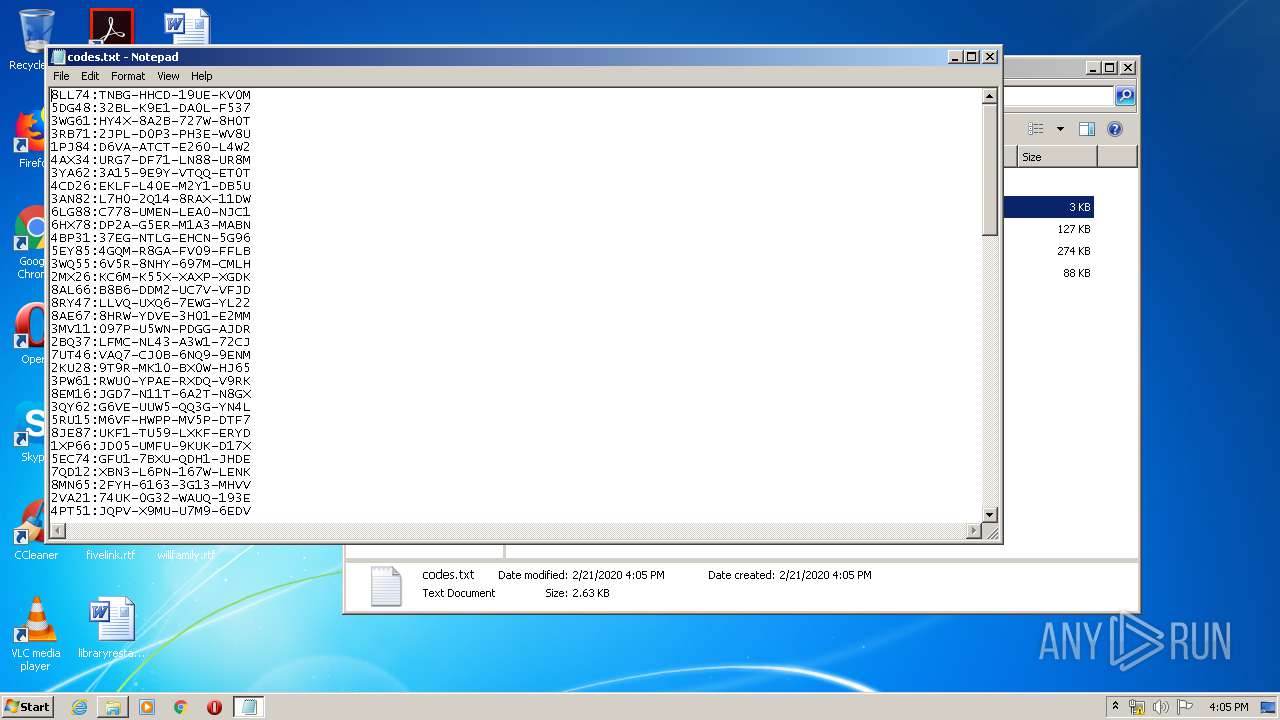
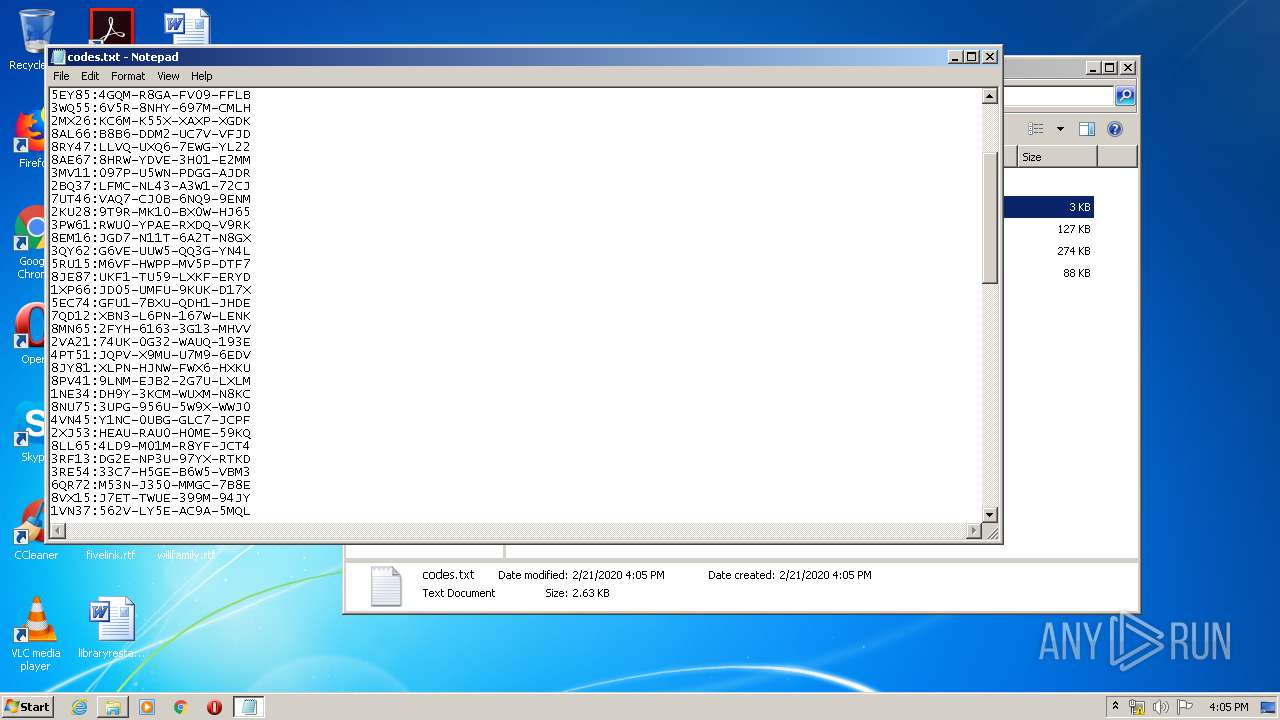
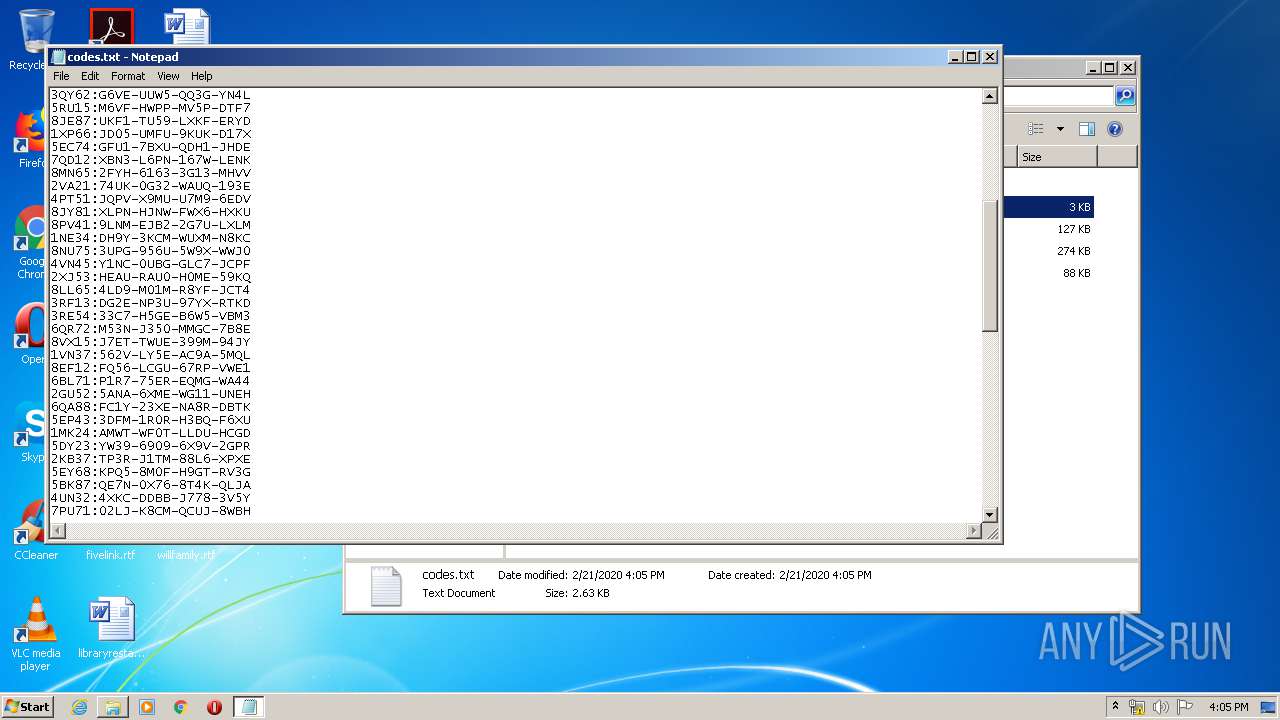
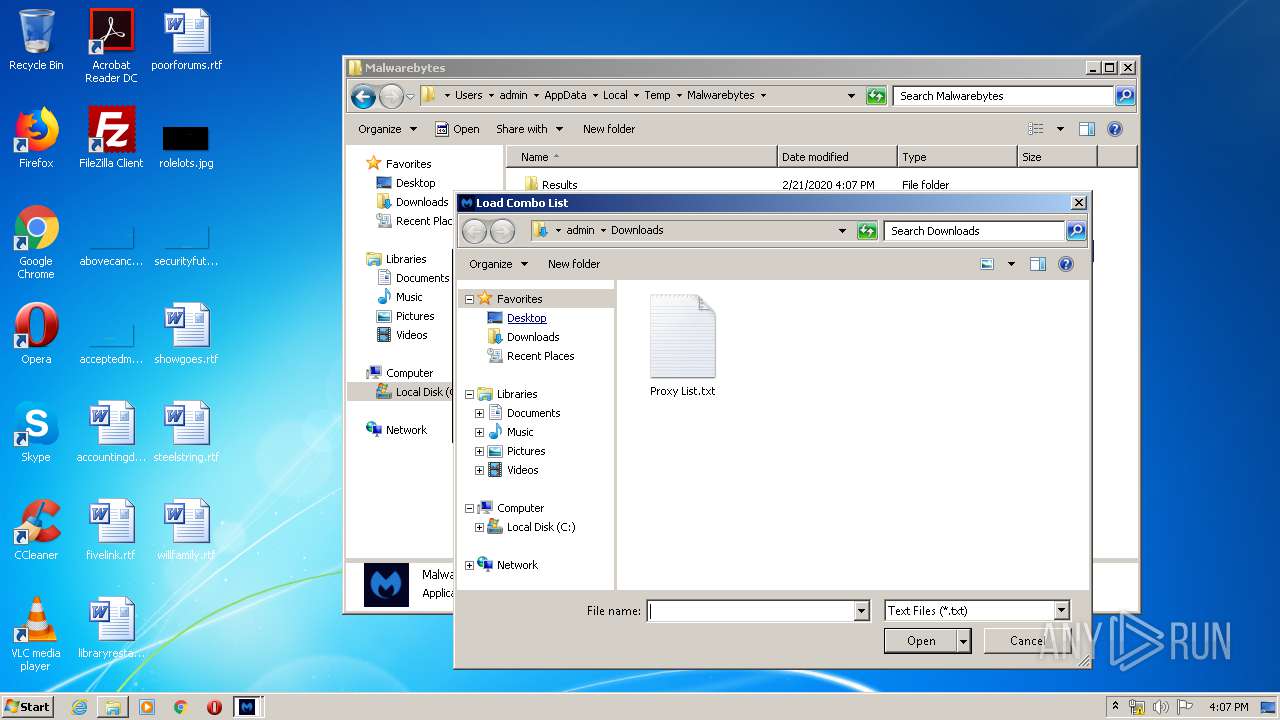
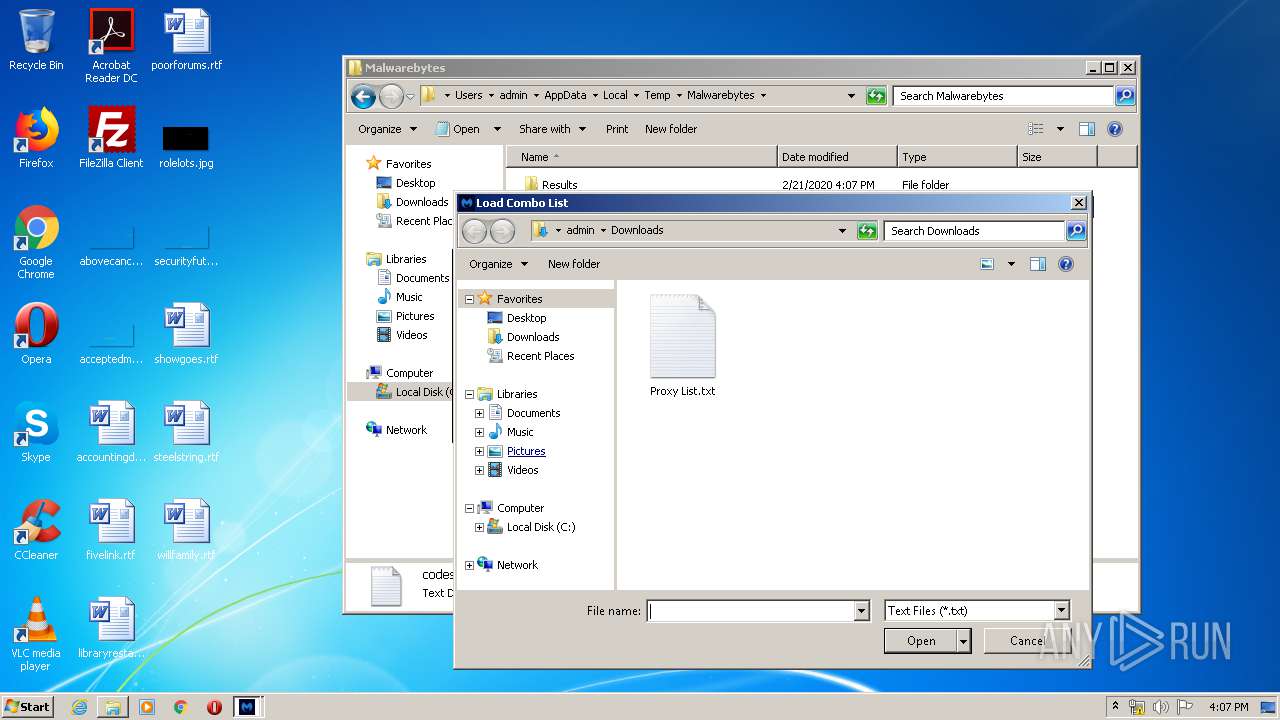
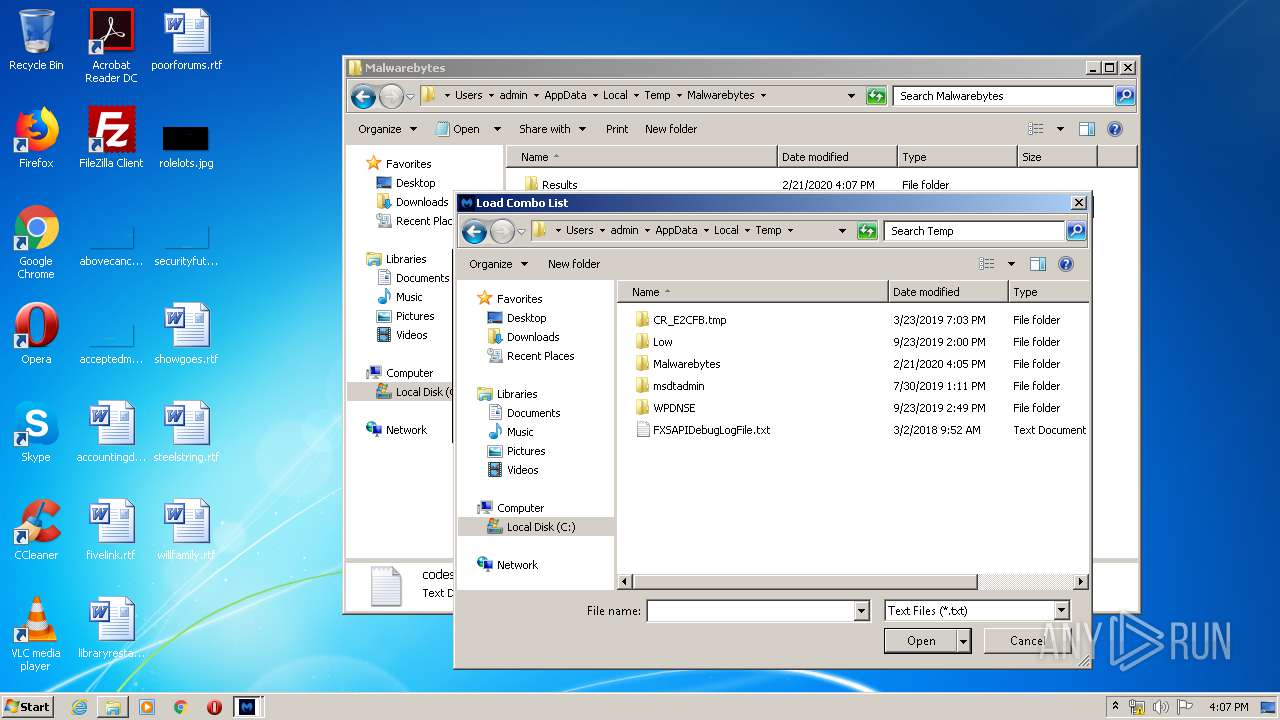
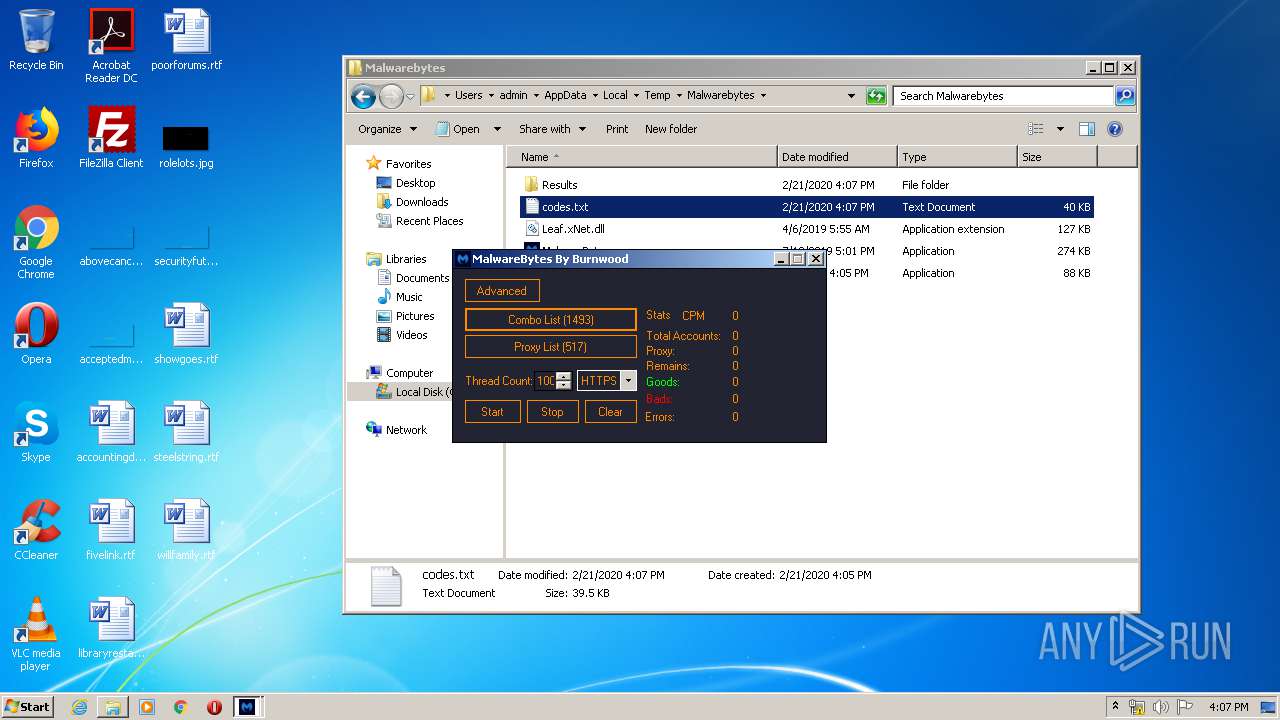
| 1688 | MBAM Gen.exe | C:\Users\admin\AppData\Local\Temp\Malwarebytes\codes.txt | text | |
MD5:— | SHA256:— | |||
| 2056 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2056 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2056 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFa7aa4d.TMP | text | |
MD5:— | SHA256:— | |||
| 2056 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1 837
TCP/UDP connections
2 012
DNS requests
37
Threats
1 819
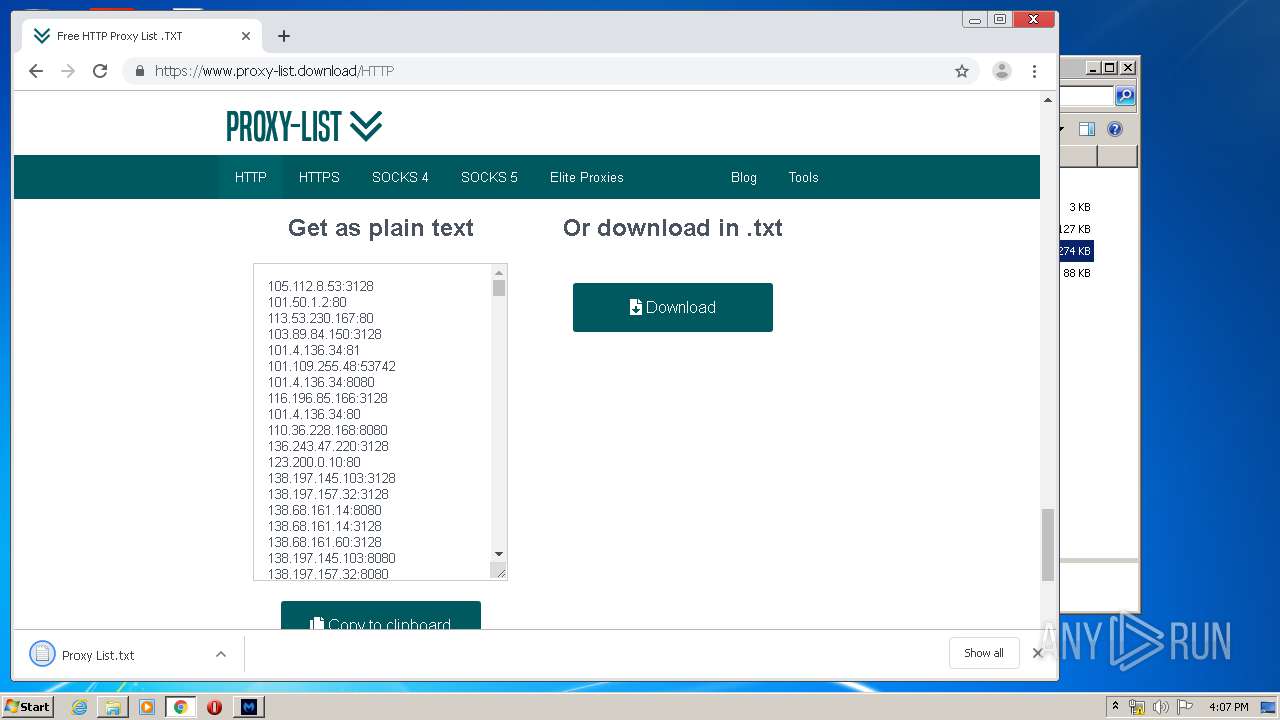
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
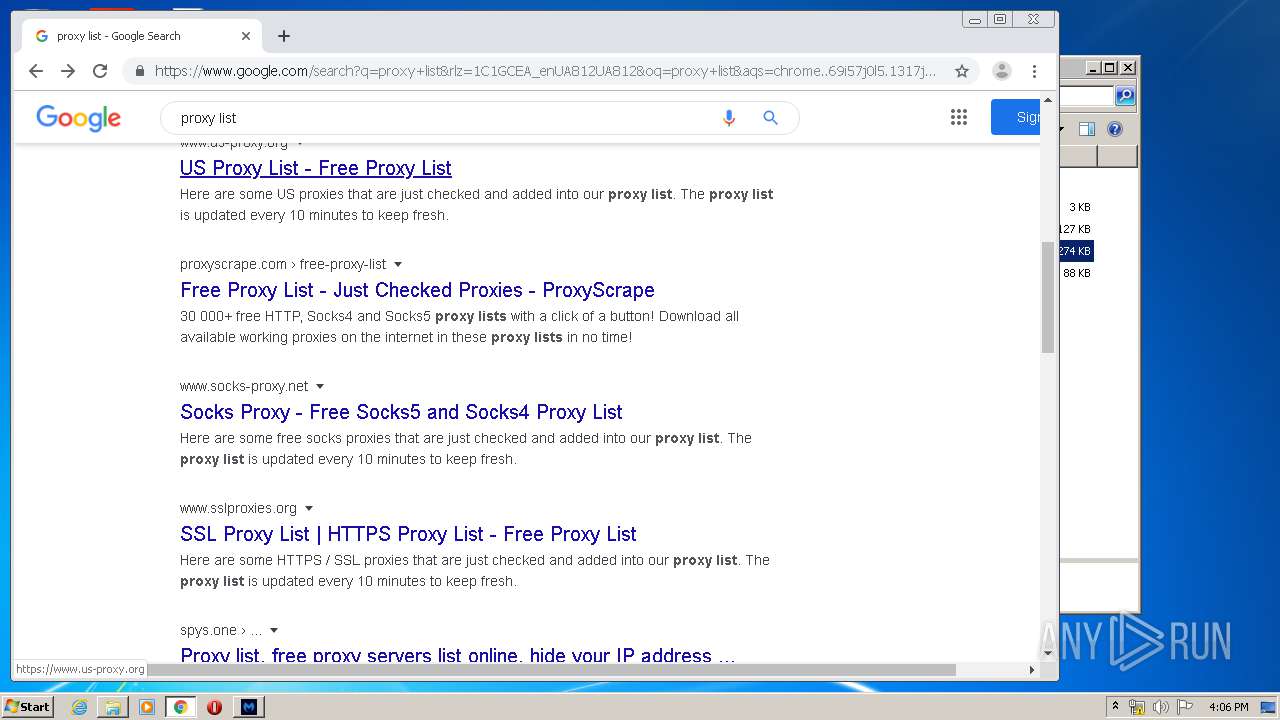
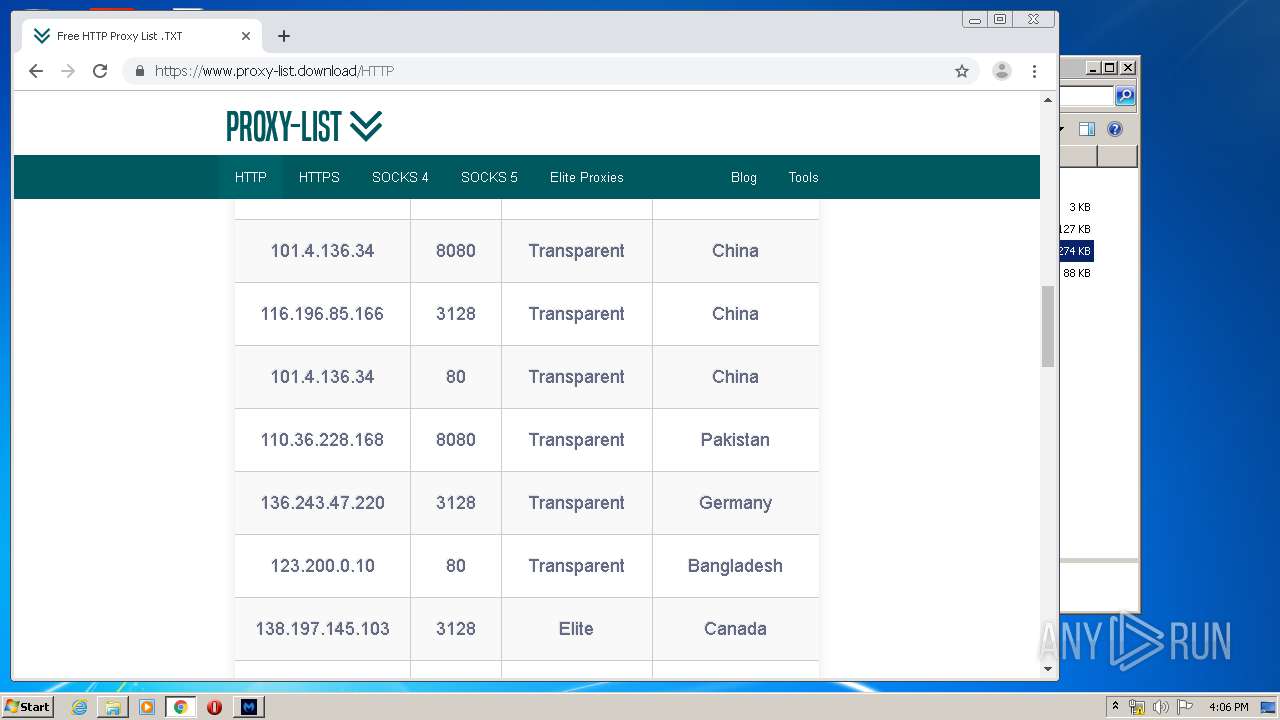
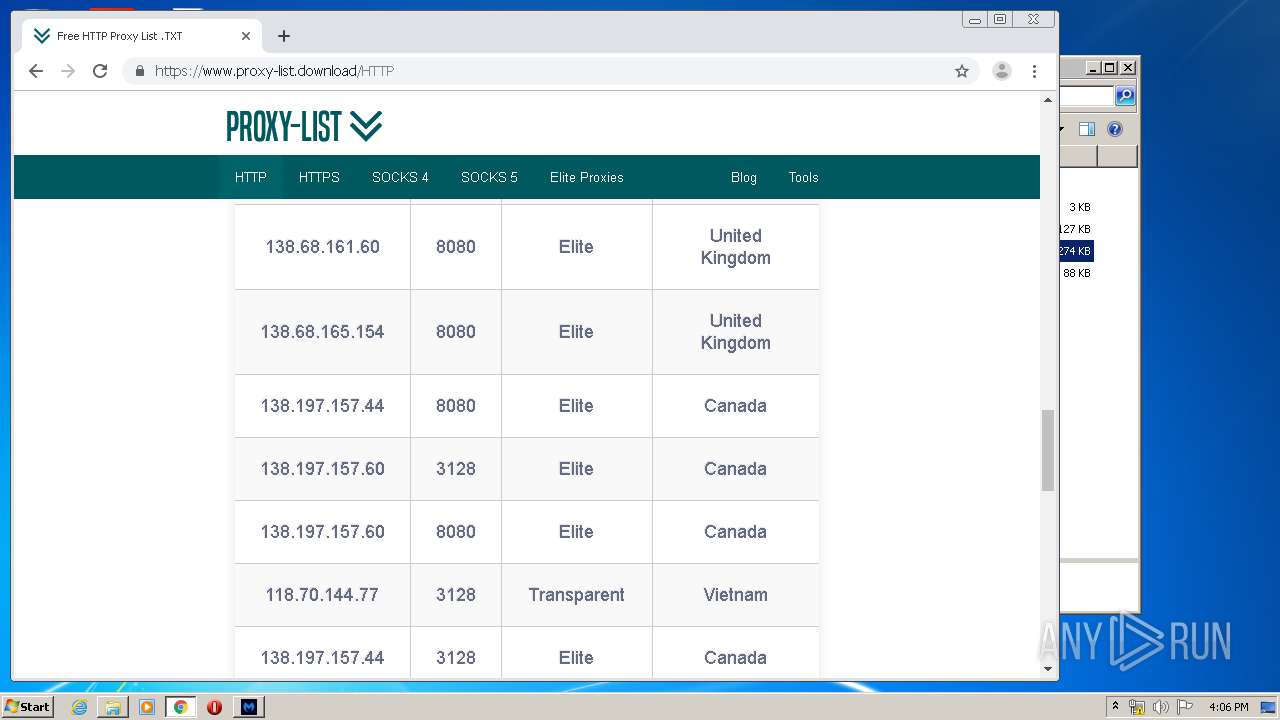
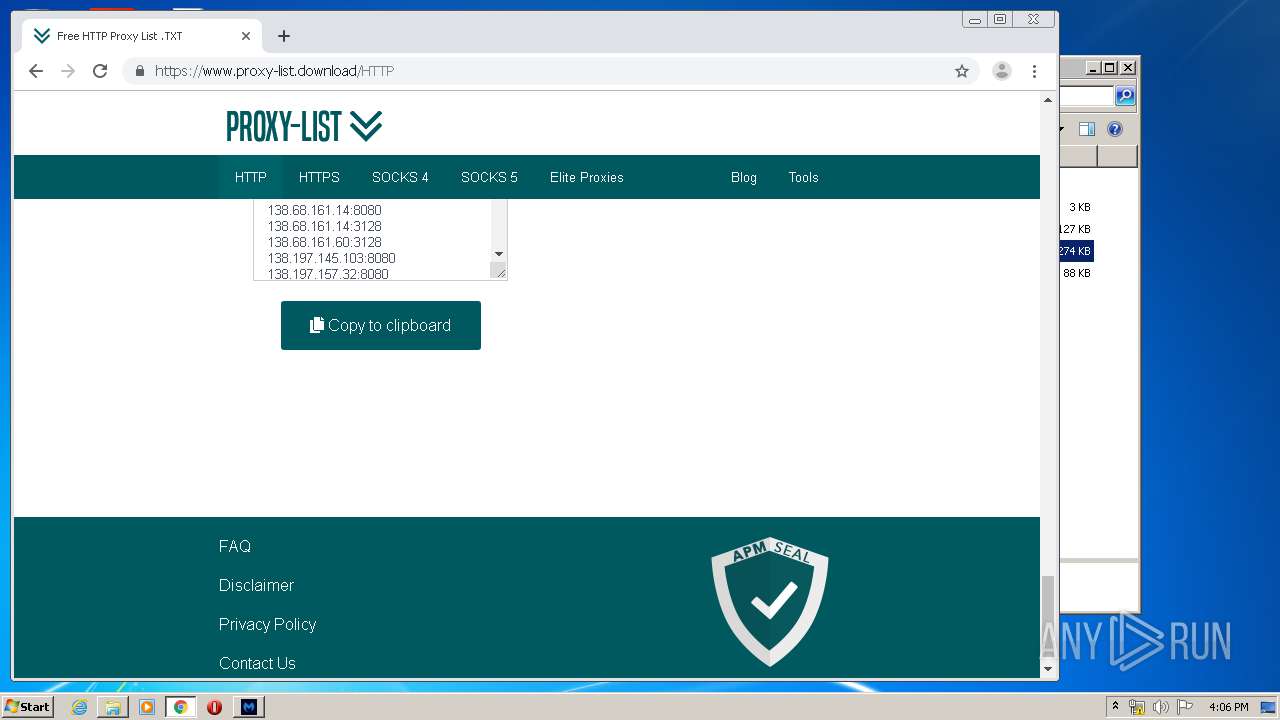
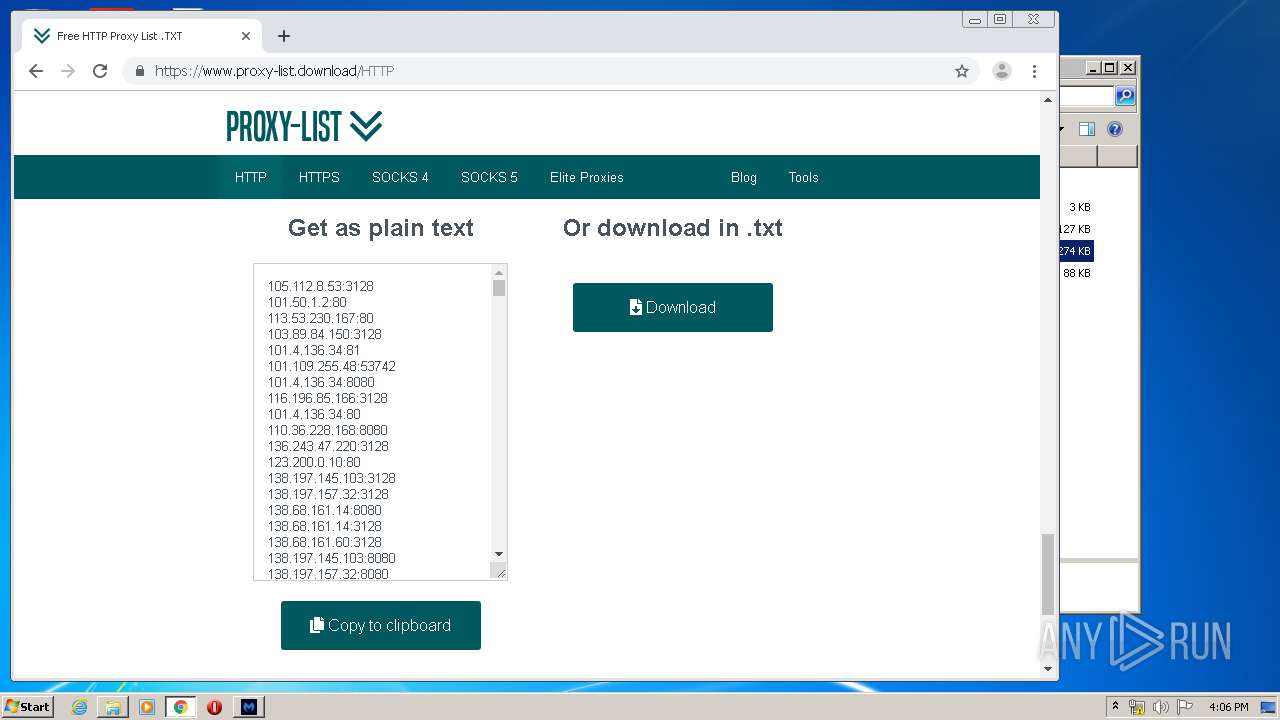
1780 | MalwareBytes.exe | CONNECT | — | 39.137.95.70:8080 | http://39.137.95.70:8080keystone.mwbsys.com:443 | CN | — | — | unknown |
1780 | MalwareBytes.exe | CONNECT | — | 138.68.161.14:8080 | http://138.68.161.14:8080keystone.mwbsys.com:443 | GB | — | — | unknown |
1780 | MalwareBytes.exe | CONNECT | — | 139.59.169.246:3128 | http://139.59.169.246:3128keystone.mwbsys.com:443 | GB | — | — | unknown |
1780 | MalwareBytes.exe | CONNECT | — | 167.172.33.59:3128 | http://167.172.33.59:3128keystone.mwbsys.com:443 | GB | — | — | unknown |
1780 | MalwareBytes.exe | CONNECT | — | 159.203.91.6:8080 | http://159.203.91.6:8080keystone.mwbsys.com:443 | US | — | — | suspicious |
1780 | MalwareBytes.exe | CONNECT | — | 51.158.119.88:8811 | http://51.158.119.88:8811keystone.mwbsys.com:443 | GB | — | — | unknown |
1780 | MalwareBytes.exe | CONNECT | — | 207.154.231.213:8080 | http://207.154.231.213:8080keystone.mwbsys.com:443 | DE | — | — | unknown |
1780 | MalwareBytes.exe | CONNECT | — | 183.89.184.242:8080 | http://183.89.184.242:8080keystone.mwbsys.com:443 | TH | — | — | unknown |
1780 | MalwareBytes.exe | CONNECT | — | 151.237.59.102:8080 | http://151.237.59.102:8080keystone.mwbsys.com:443 | ES | — | — | unknown |
1780 | MalwareBytes.exe | CONNECT | — | 46.101.211.77:8080 | http://46.101.211.77:8080keystone.mwbsys.com:443 | DE | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2956 | chrome.exe | 172.217.22.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2956 | chrome.exe | 172.217.16.195:443 | www.google.com.ua | Google Inc. | US | whitelisted |
2956 | chrome.exe | 172.217.17.106:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2956 | chrome.exe | 172.217.22.14:443 | apis.google.com | Google Inc. | US | whitelisted |
1640 | chrome.exe | 172.217.22.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2956 | chrome.exe | 172.217.18.163:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
1640 | chrome.exe | 172.217.22.14:443 | apis.google.com | Google Inc. | US | whitelisted |
2956 | chrome.exe | 216.58.206.14:443 | ogs.google.com | Google Inc. | US | whitelisted |
1640 | chrome.exe | 172.217.16.195:443 | www.google.com.ua | Google Inc. | US | whitelisted |
1640 | chrome.exe | 172.217.21.238:443 | consent.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com |
| whitelisted |
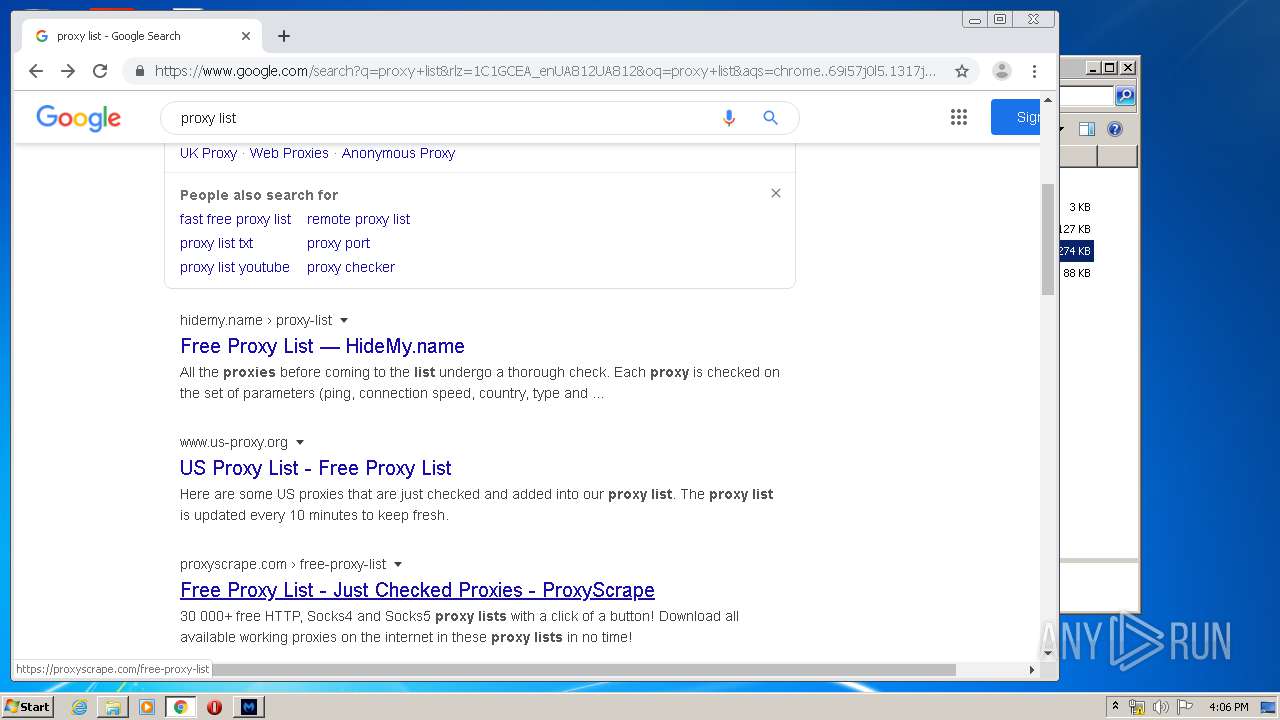
www.google.com |
| malicious |
consent.google.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1780 | MalwareBytes.exe | Generic Protocol Command Decode | SURICATA HTTP missing Host header |
1780 | MalwareBytes.exe | Generic Protocol Command Decode | SURICATA HTTP missing Host header |
1780 | MalwareBytes.exe | Generic Protocol Command Decode | SURICATA HTTP missing Host header |
1780 | MalwareBytes.exe | Generic Protocol Command Decode | SURICATA HTTP missing Host header |
1780 | MalwareBytes.exe | Generic Protocol Command Decode | SURICATA HTTP missing Host header |
1780 | MalwareBytes.exe | Generic Protocol Command Decode | SURICATA HTTP missing Host header |
1780 | MalwareBytes.exe | Generic Protocol Command Decode | SURICATA HTTP missing Host header |
1780 | MalwareBytes.exe | Generic Protocol Command Decode | SURICATA HTTP missing Host header |
1780 | MalwareBytes.exe | Generic Protocol Command Decode | SURICATA HTTP missing Host header |
1780 | MalwareBytes.exe | Generic Protocol Command Decode | SURICATA HTTP missing Host header |