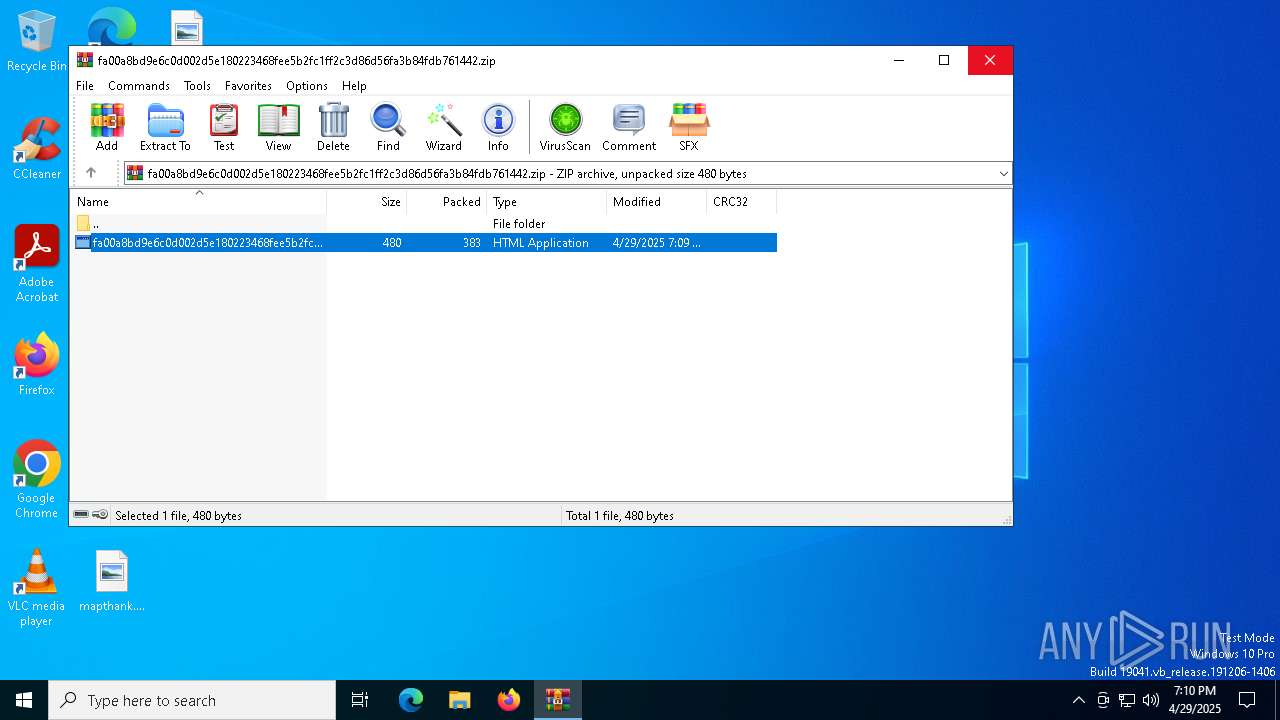
| File name: | fa00a8bd9e6c0d002d5e180223468fee5b2fc1ff2c3d86d56fa3b84fdb761442.zip |
| Full analysis: | https://app.any.run/tasks/d3f98180-0d47-4a7e-9e02-a3aa583657db |
| Verdict: | Malicious activity |
| Analysis date: | April 29, 2025, 19:09:53 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
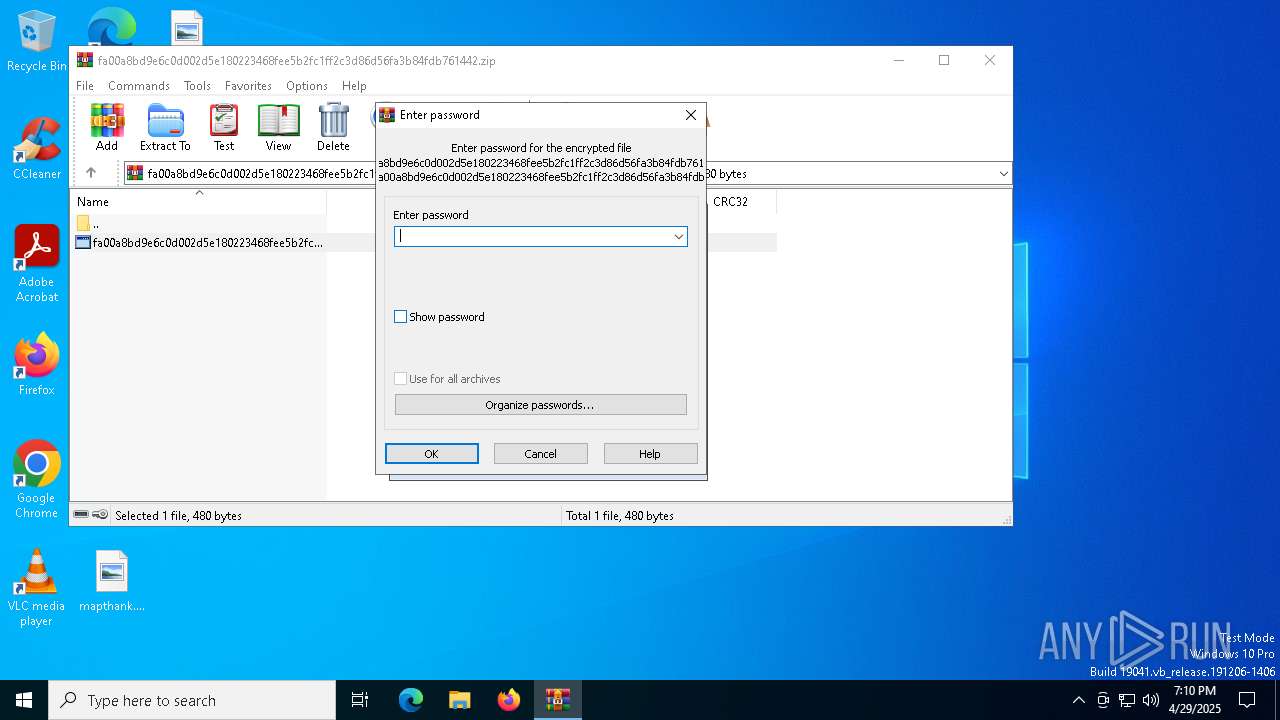
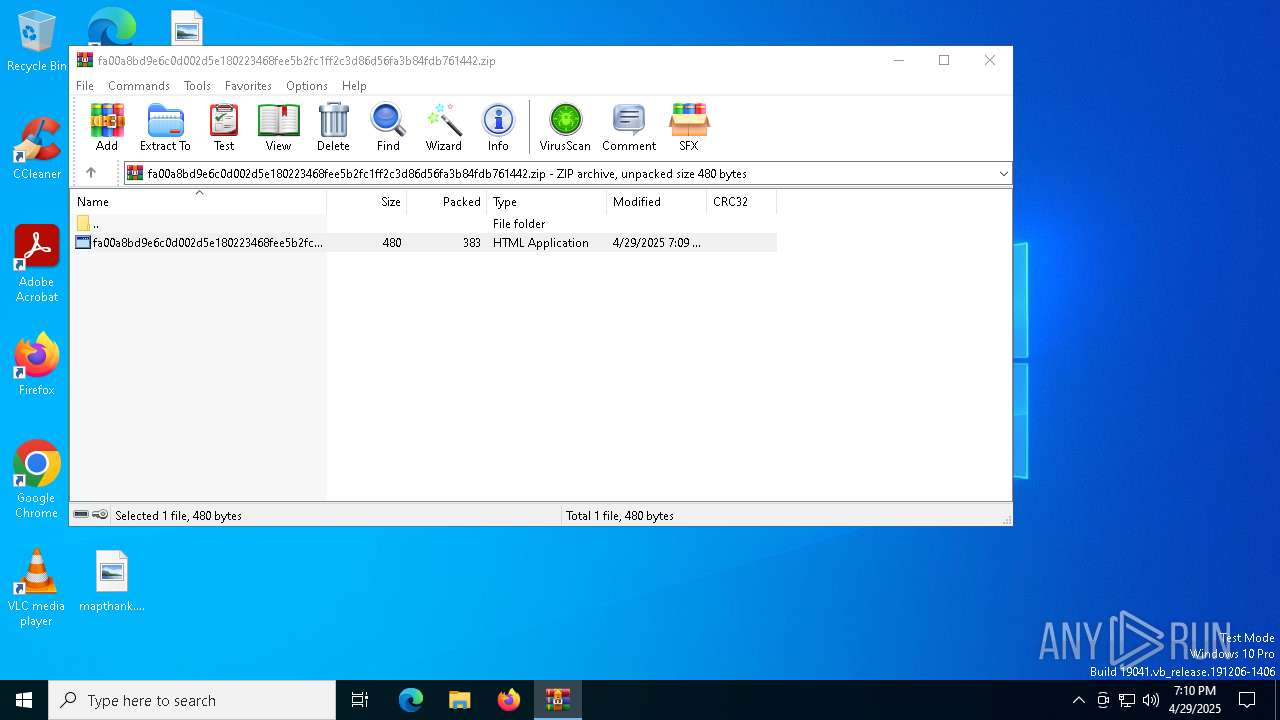
| MIME: | application/zip |
| File info: | Zip archive data, at least v5.1 to extract, compression method=AES Encrypted |
| MD5: | D80BC364E6A9743F2B3F8E0ABF5FA0C1 |
| SHA1: | 86CCD9E08C47639944CCF31D9F37B7A1B15B54AD |
| SHA256: | 8719B900712A9827BC101E5DA0D9125EB6D65BD2E51E4E8DA3F10E0C18D9AE50 |
| SSDEEP: | 12:5fGequD6ttzUku+s/k7i/sFl16IZgS46TnTgQiyDvIrLgVTu8kcWqlyD6ttPatZ:HrYt9u+G0FlEIWx6TTZJDg2uTZkkYtYZ |
MALICIOUS
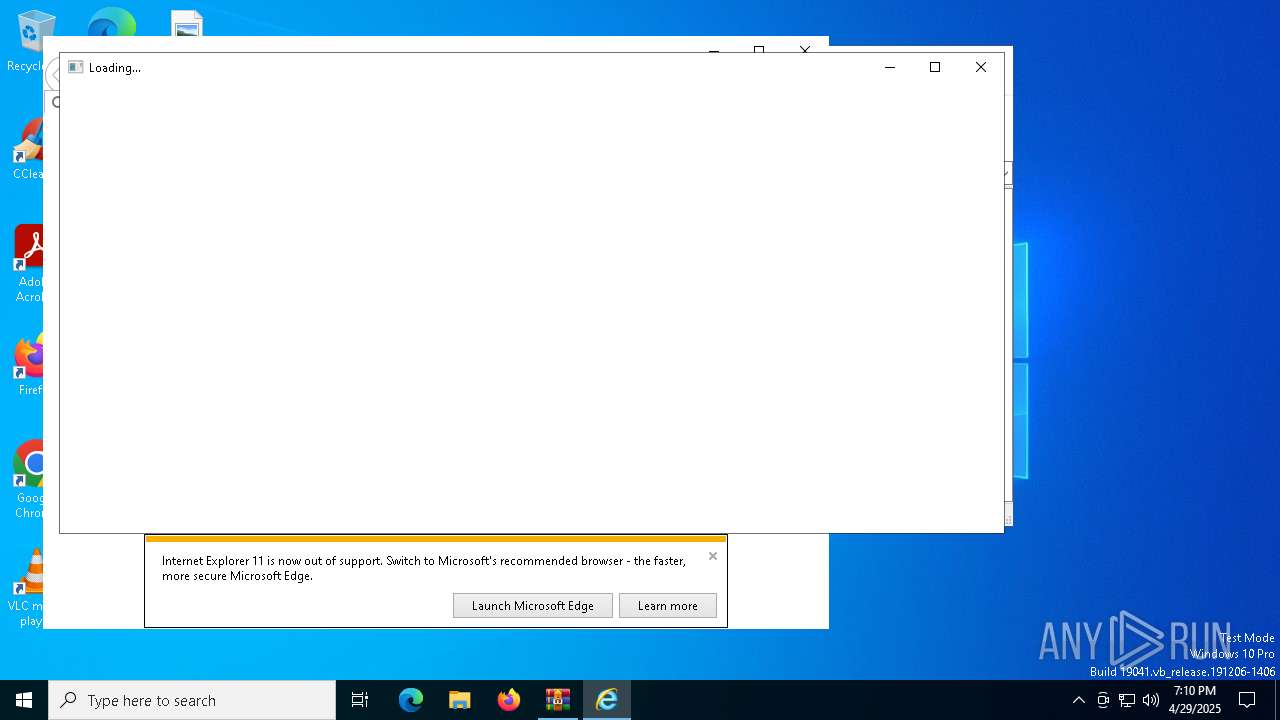
Generic archive extractor
- WinRAR.exe (PID: 7152)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 7152)
INFO
Reads Microsoft Office registry keys
- WinRAR.exe (PID: 7152)
Reads Internet Explorer settings
- mshta.exe (PID: 2320)
Reads the computer name
- ielowutil.exe (PID: 4000)
Checks supported languages
- ielowutil.exe (PID: 4000)
Local mutex for internet shortcut management
- iexplore.exe (PID: 4892)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 51 |
|---|---|
| ZipBitFlag: | 0x0003 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2025:04:29 19:09:28 |
| ZipCRC: | 0x1e5d29d7 |
| ZipCompressedSize: | 383 |
| ZipUncompressedSize: | 480 |
| ZipFileName: | fa00a8bd9e6c0d002d5e180223468fee5b2fc1ff2c3d86d56fa3b84fdb761442.hta |
Total processes
135
Monitored processes
10
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
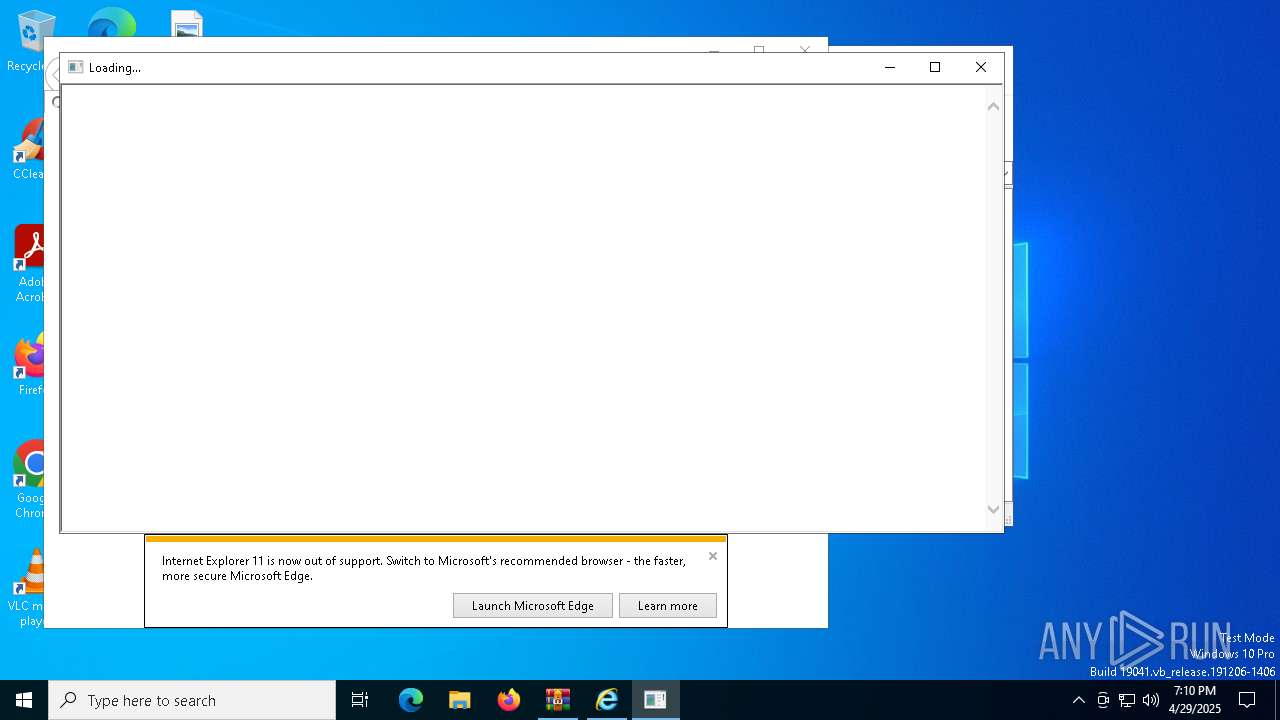
| 2320 | "C:\Windows\SysWOW64\mshta.exe" "C:\Users\admin\AppData\Local\Temp\Rar$DIb7152.11267\fa00a8bd9e6c0d002d5e180223468fee5b2fc1ff2c3d86d56fa3b84fdb761442.hta" {1E460BD7-F1C3-4B2E-88BF-4E770A288AF5}{1E460BD7-F1C3-4B2E-88BF-4E770A288AF5} | C:\Windows\SysWOW64\mshta.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 0 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4000 | "C:\Program Files (x86)\Internet Explorer\ielowutil.exe" -CLSID:{0002DF01-0000-0000-C000-000000000046} -Embedding | C:\Program Files (x86)\Internet Explorer\ielowutil.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Low-Mic Utility Tool Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4172 | "C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE" SCODEF:4892 CREDAT:3413266 /prefetch:2 | C:\Program Files (x86)\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4892 | "C:\Program Files\Internet Explorer\IEXPLORE.EXE" -Embedding | C:\Program Files\Internet Explorer\iexplore.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5380 | "C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE" SCODEF:4892 CREDAT:9476 /prefetch:2 | C:\Program Files (x86)\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5720 | "C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE" SCODEF:4892 CREDAT:9474 /prefetch:2 | C:\Program Files (x86)\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5960 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6264 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7152 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\fa00a8bd9e6c0d002d5e180223468fee5b2fc1ff2c3d86d56fa3b84fdb761442.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
Total events
8 585
Read events
8 500
Write events
76
Delete events
9
Modification events
| (PID) Process: | (7152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\fa00a8bd9e6c0d002d5e180223468fee5b2fc1ff2c3d86d56fa3b84fdb761442.zip | |||
| (PID) Process: | (7152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (7152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.hta\OpenWithProgids |
| Operation: | write | Name: | htafile |
Value: | |||
Executable files
0
Suspicious files
26
Text files
9
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4892 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF33105CA9D6866274.TMP | binary | |
MD5:320B03FD3B225FB342BAD58A465C65FF | SHA256:59ADF0D009DE6FD611622200BA85C1E56FD43E9F7104F959C5E8AB1B1A256B7B | |||
| 5380 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\542326A32EB51C769BA44BE0756E303D | der | |
MD5:C9D50DB6000B2C421758624EDDED30AA | SHA256:356B1FDA4F248385FBACE7BCBAE0293F26E3060BE607737C8F725DA21F06C28B | |||
| 7152 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIb7152.11267\fa00a8bd9e6c0d002d5e180223468fee5b2fc1ff2c3d86d56fa3b84fdb761442.hta | html | |
MD5:1591BA87B1E46EF063AC1B5AFD364673 | SHA256:FA00A8BD9E6C0D002D5E180223468FEE5B2FC1FF2C3D86D56FA3B84FDB761442 | |||
| 5380 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:08B74398C18A48C2D5E97B5867EC4F30 | SHA256:54A2A43A4A894B94BAB8B8A798881F363840F4FE1D46C5929D9C79E41AAE76C1 | |||
| 4892 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{902A95AD-252D-11F0-B4ED-18F7786F96EE}.dat | binary | |
MD5:FA3B7C1C9176E5CFA514151BEBDCE8B4 | SHA256:756282EF6B8CB83B1B9225A7480D4A55D35449A0EE916CA4A2BF275A19FD284C | |||
| 5380 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Low\IE\SG5UMOCJ\AA5S4AX0.htm | html | |
MD5:6DC65E532314CEFA47F9EE5D5D96E5AE | SHA256:575D787B89615ECE8190817763FA7B387728B1C57B669F81B3D6DDEB91F89538 | |||
| 5380 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:E192462F281446B5D1500D474FBACC4B | SHA256:F1BA9F1B63C447682EBF9DE956D0DA2A027B1B779ABEF9522D347D3479139A60 | |||
| 4892 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\26C212D9399727259664BDFCA073966E_F9F7D6A7ECE73106D2A8C63168CDA10D | binary | |
MD5:97394740B451BD8B67A0CCCC43FB4898 | SHA256:4998A16378BA92B1D4A114B1E3B5556393B69713A31CBD8079CB4C65828363BE | |||
| 5380 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\542326A32EB51C769BA44BE0756E303D | binary | |
MD5:349BB739F38859B34343A7A30BEB5AC2 | SHA256:8E3FA3CC7C095AE55CEFFBA71C90FACDE2EA22FA2C565ACFD8E6878DD1FE7A52 | |||
| 5380 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_0FB9553B978E7F00C6B2309507DEB64A | der | |
MD5:7EDCC2F8FD122636E37A34E819B046B8 | SHA256:51C585682EA77A3B985FD3D21409AA320FCAE26793147FCD3DB8A45611040D93 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
16
TCP/UDP connections
44
DNS requests
25
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
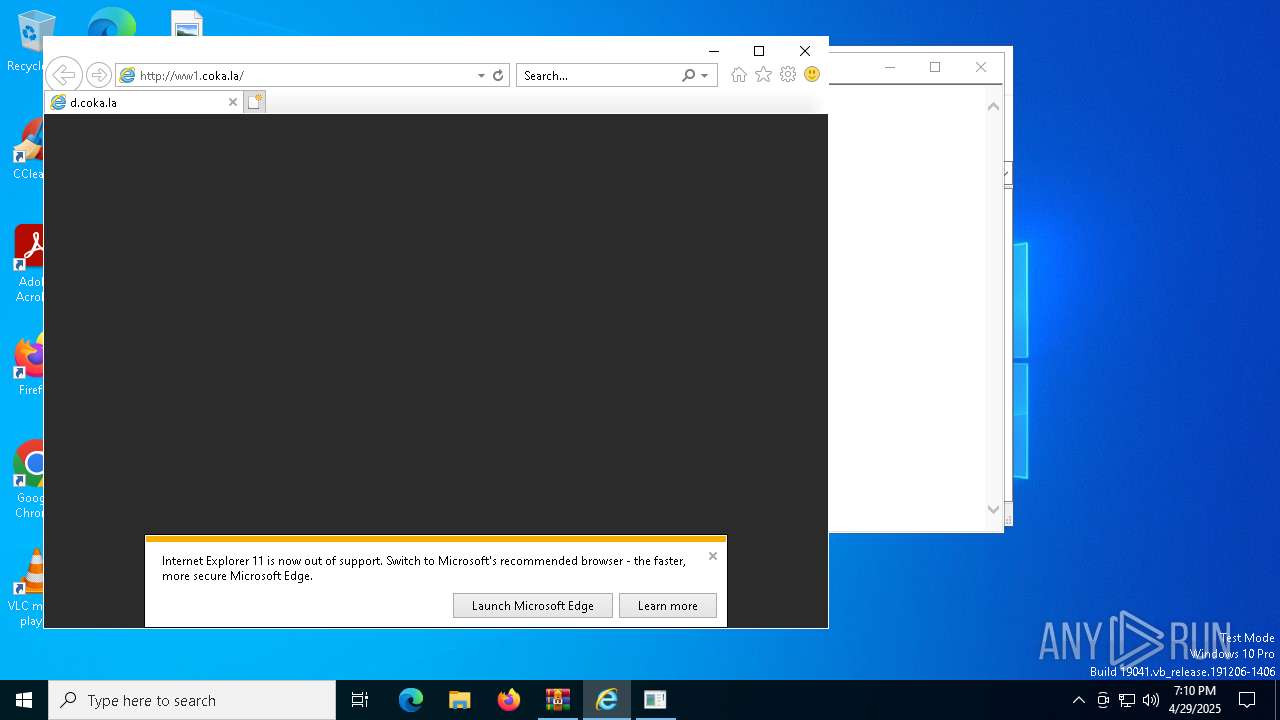
5380 | iexplore.exe | GET | 200 | 199.59.243.228:80 | http://ww1.coka.la/ | unknown | — | — | malicious |
— | — | GET | 200 | 23.216.77.11:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
3896 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
3896 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
4892 | iexplore.exe | GET | 200 | 23.54.109.203:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
5380 | iexplore.exe | GET | 200 | 199.59.243.228:80 | http://ww1.coka.la/ | unknown | — | — | malicious |
5380 | iexplore.exe | GET | 200 | 199.59.243.228:80 | http://ww1.coka.la/bvDUhKXqH.js | unknown | — | — | malicious |
5380 | iexplore.exe | GET | 200 | 199.59.243.228:80 | http://ww1.coka.la/balxYOJmB.js | unknown | — | — | malicious |
4892 | iexplore.exe | GET | 200 | 23.54.109.203:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.216.77.11:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 40.126.31.1:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 23.54.109.203:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5380 | iexplore.exe | 74.63.241.19:443 | d.coka.la | LIMESTONENETWORKS | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
d.coka.la |
| malicious |
x1.c.lencr.org |
| whitelisted |
r11.o.lencr.org |
| whitelisted |