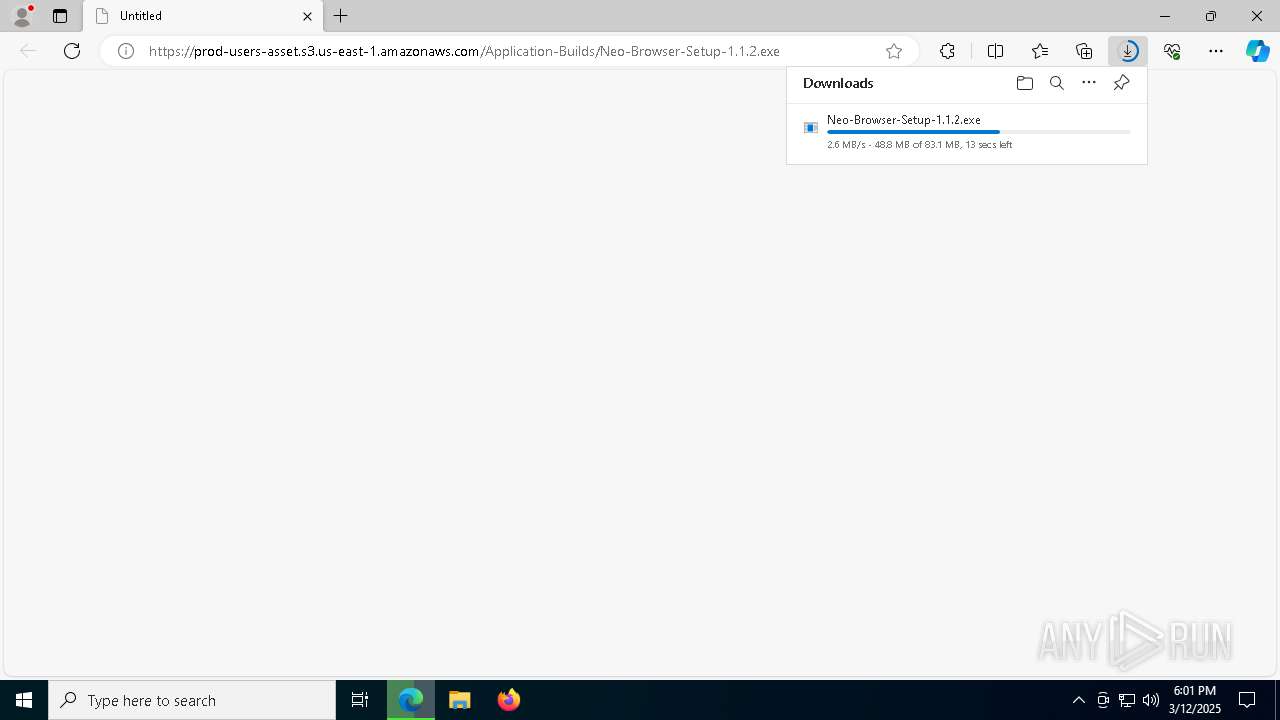
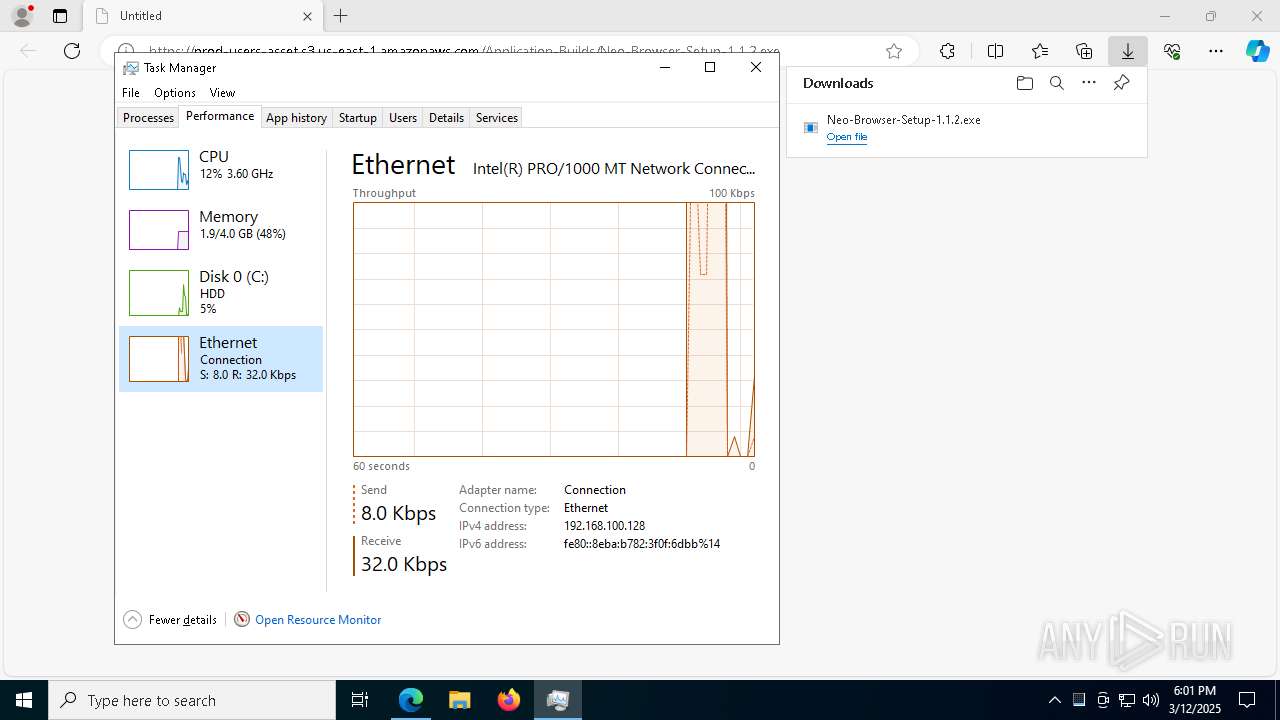
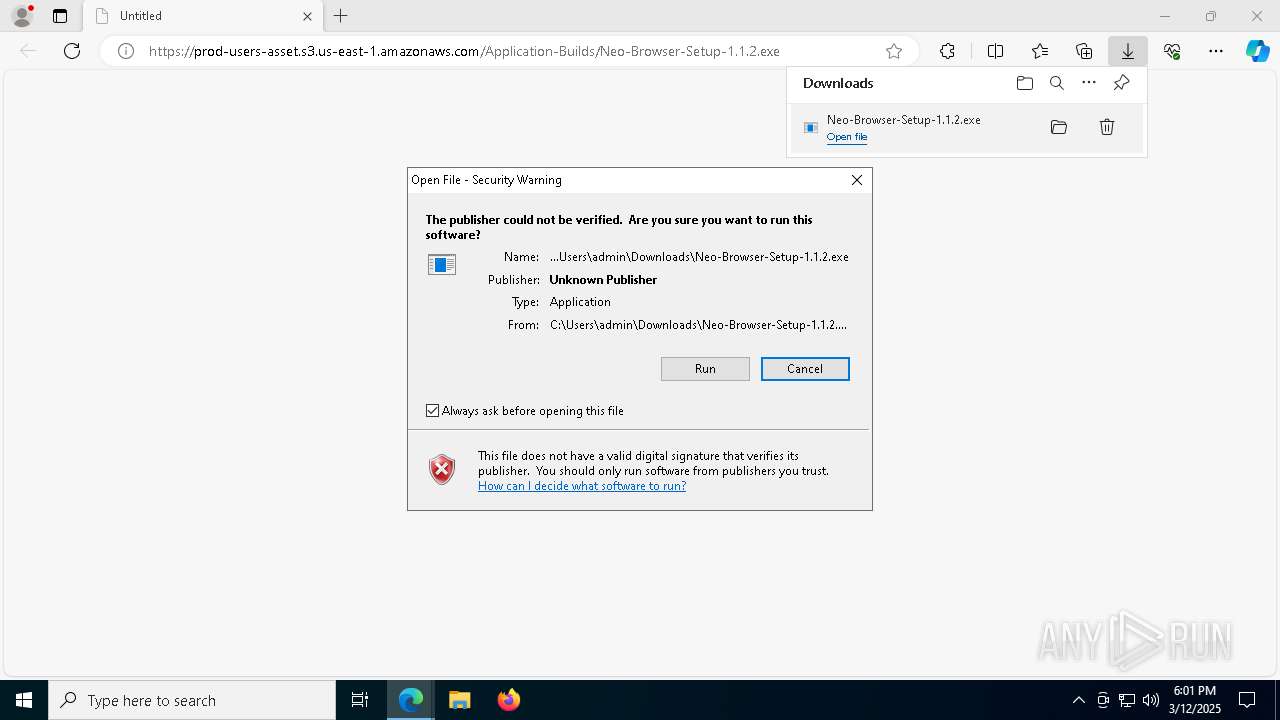
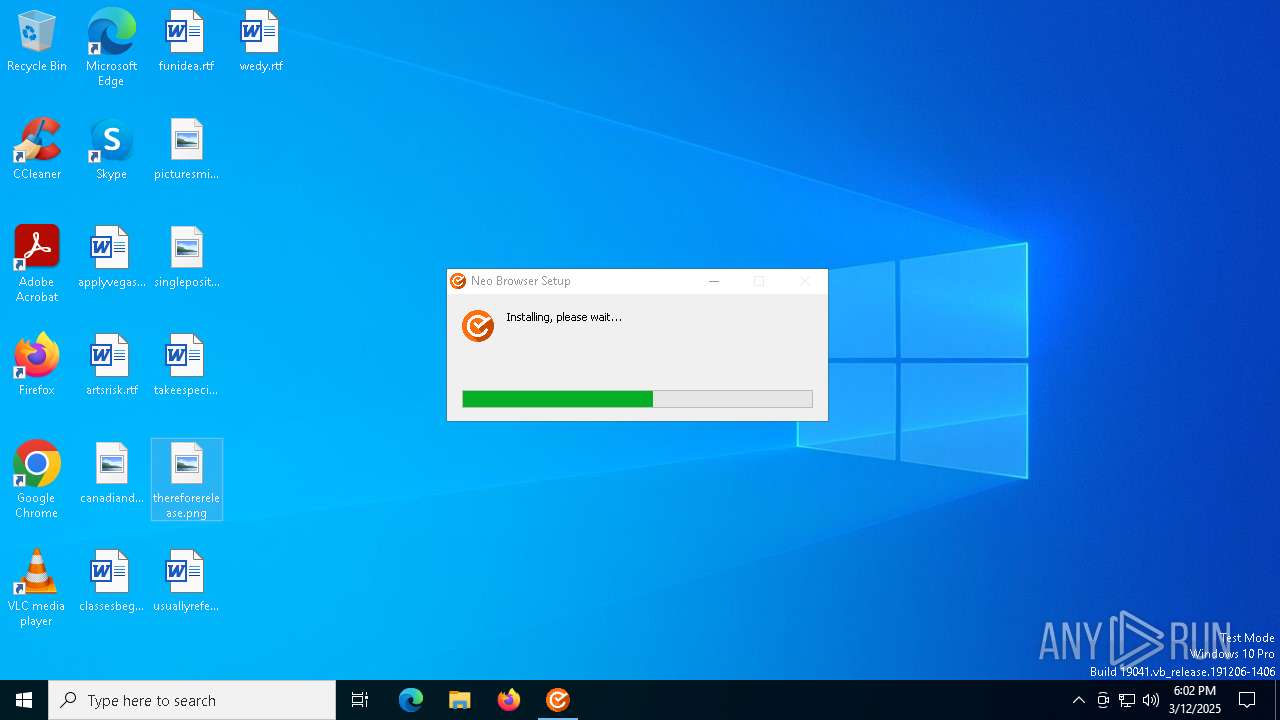
| URL: | https://prod-users-asset.s3.us-east-1.amazonaws.com/Application-Builds/Neo-Browser-Setup-1.1.2.exe |
| Full analysis: | https://app.any.run/tasks/06551a96-958c-422c-94e5-580e20561b9a |
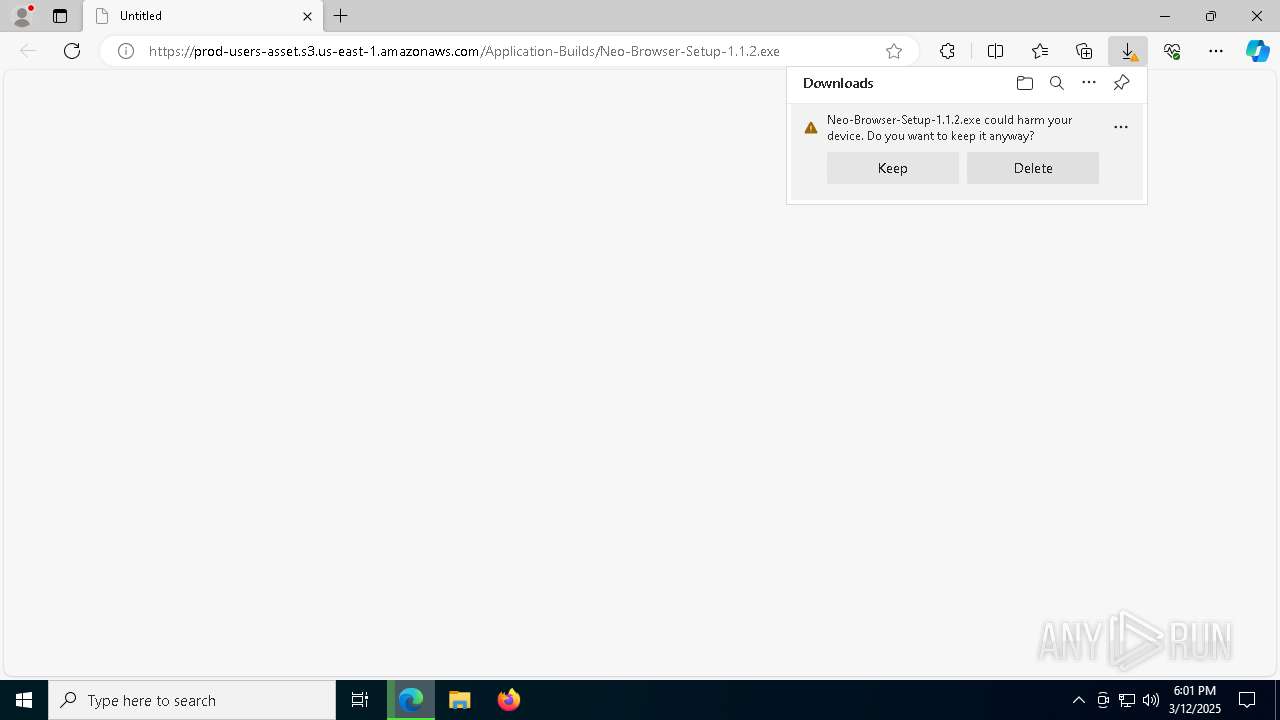
| Verdict: | Malicious activity |
| Analysis date: | March 12, 2025, 18:01:16 |
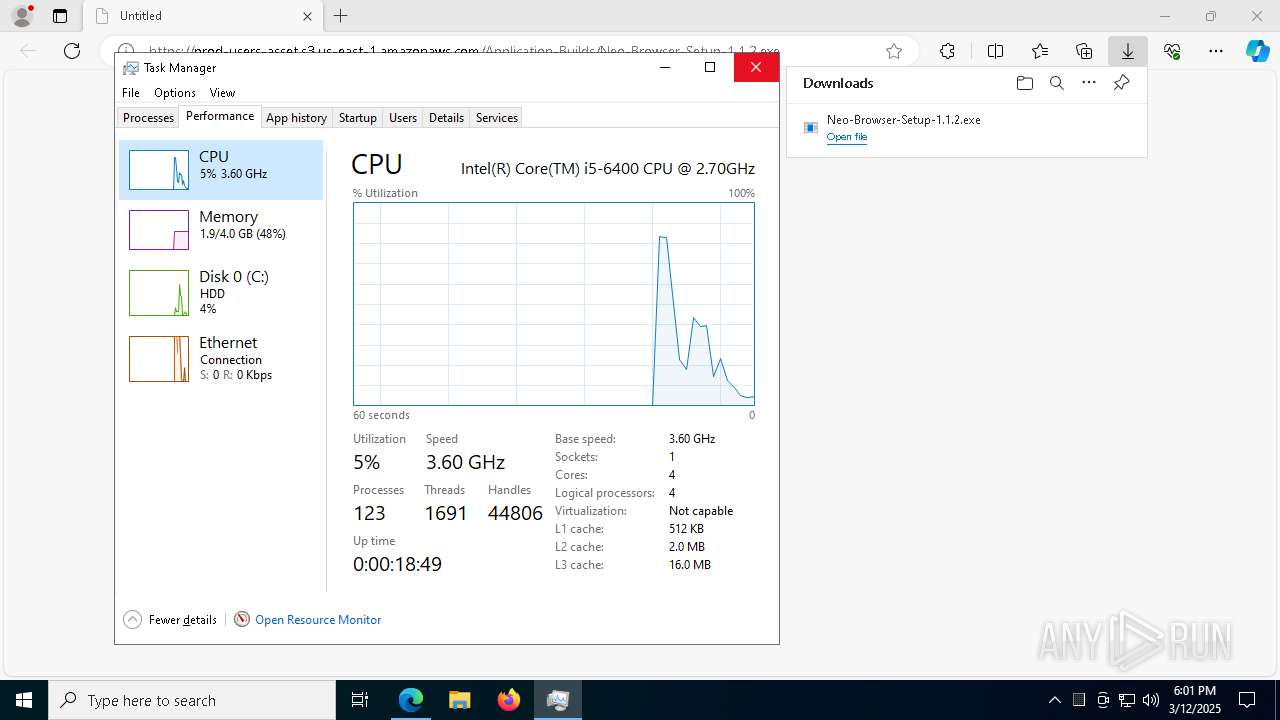
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MD5: | 22A605ECF5A25910494B3DA7F3A00E5C |
| SHA1: | A50187BD4156E4F415C3821D72931296CE56A974 |
| SHA256: | 8707369BB480E23C791F7E39F7E0DC9B0A835C1DB57231FB437C4457968CED89 |
| SSDEEP: | 3:N8TKBt3PERCmPSsQ7WtoERMQa3BWwjSE2VkUA:2oMRCmPRQFj/SEy8 |
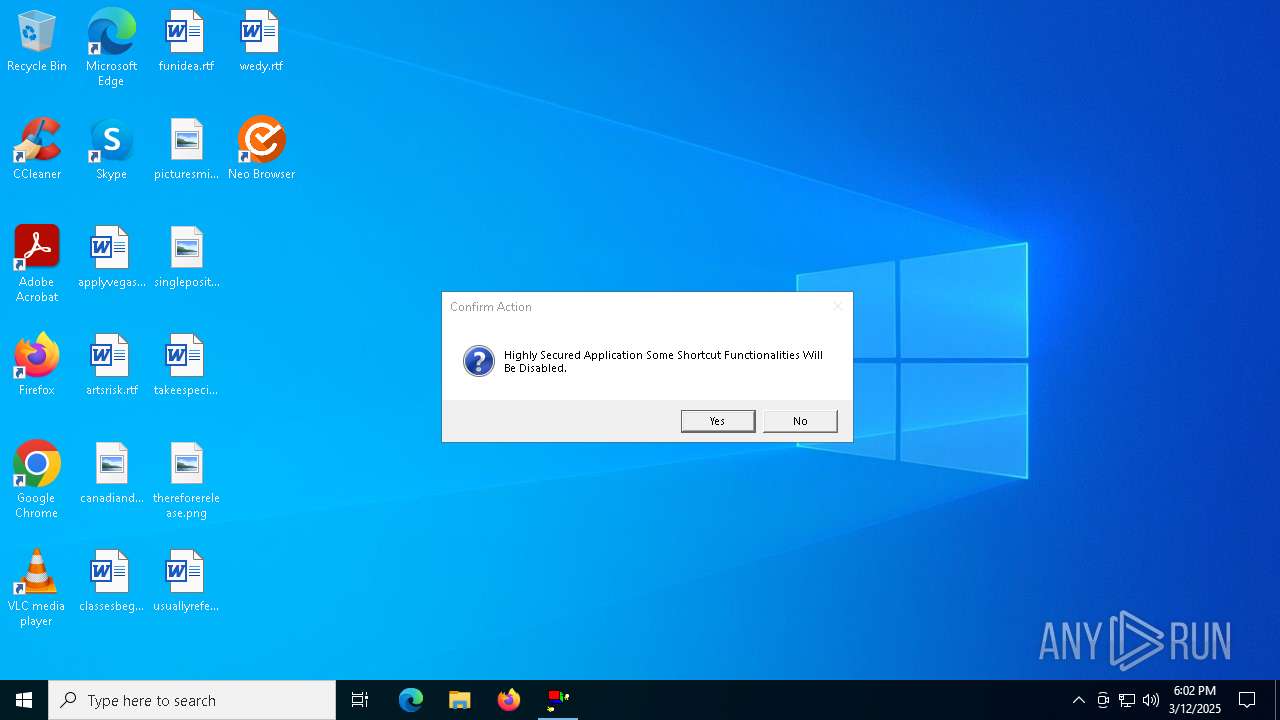
MALICIOUS
No malicious indicators.SUSPICIOUS
Malware-specific behavior (creating "System.dll" in Temp)
- Neo-Browser-Setup-1.1.2.exe (PID: 3304)
Starts CMD.EXE for commands execution
- Neo-Browser-Setup-1.1.2.exe (PID: 3304)
- Neo Browser.exe (PID: 2088)
- cscript.exe (PID: 8660)
Get information on the list of running processes
- Neo-Browser-Setup-1.1.2.exe (PID: 3304)
- cmd.exe (PID: 8660)
Executable content was dropped or overwritten
- Neo-Browser-Setup-1.1.2.exe (PID: 3304)
Process drops legitimate windows executable
- Neo-Browser-Setup-1.1.2.exe (PID: 3304)
Drops 7-zip archiver for unpacking
- Neo-Browser-Setup-1.1.2.exe (PID: 3304)
The process executes VB scripts
- cmd.exe (PID: 5956)
- cmd.exe (PID: 4452)
Runs shell command (SCRIPT)
- cscript.exe (PID: 8660)
Executing commands from a ".bat" file
- cscript.exe (PID: 8660)
Starts NET.EXE to display or manage information about active sessions
- net.exe (PID: 7916)
- cmd.exe (PID: 7964)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 7964)
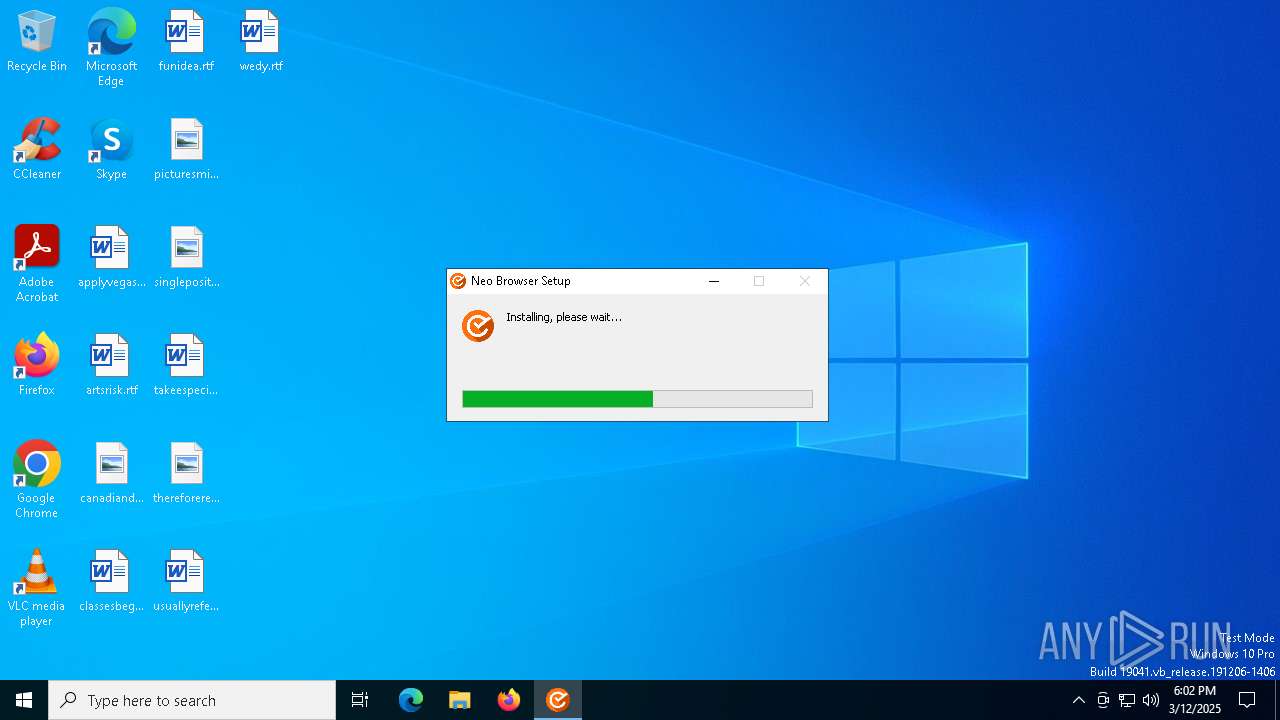
The process executes via Task Scheduler
- explorer.exe (PID: 8044)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 8064)
- cmd.exe (PID: 7828)
- cmd.exe (PID: 6248)
- cmd.exe (PID: 512)
- cmd.exe (PID: 5572)
- cmd.exe (PID: 7112)
- cmd.exe (PID: 6600)
- cmd.exe (PID: 7896)
- cmd.exe (PID: 5188)
- cmd.exe (PID: 8136)
- cmd.exe (PID: 672)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 7964)
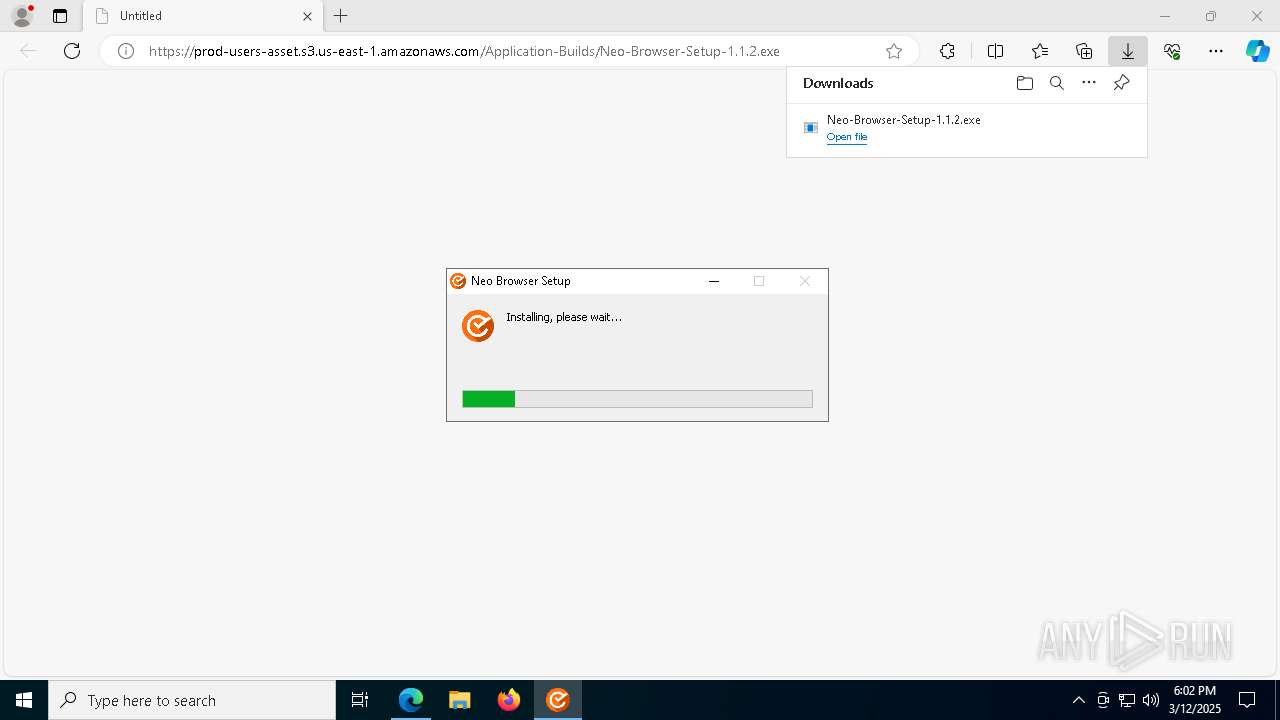
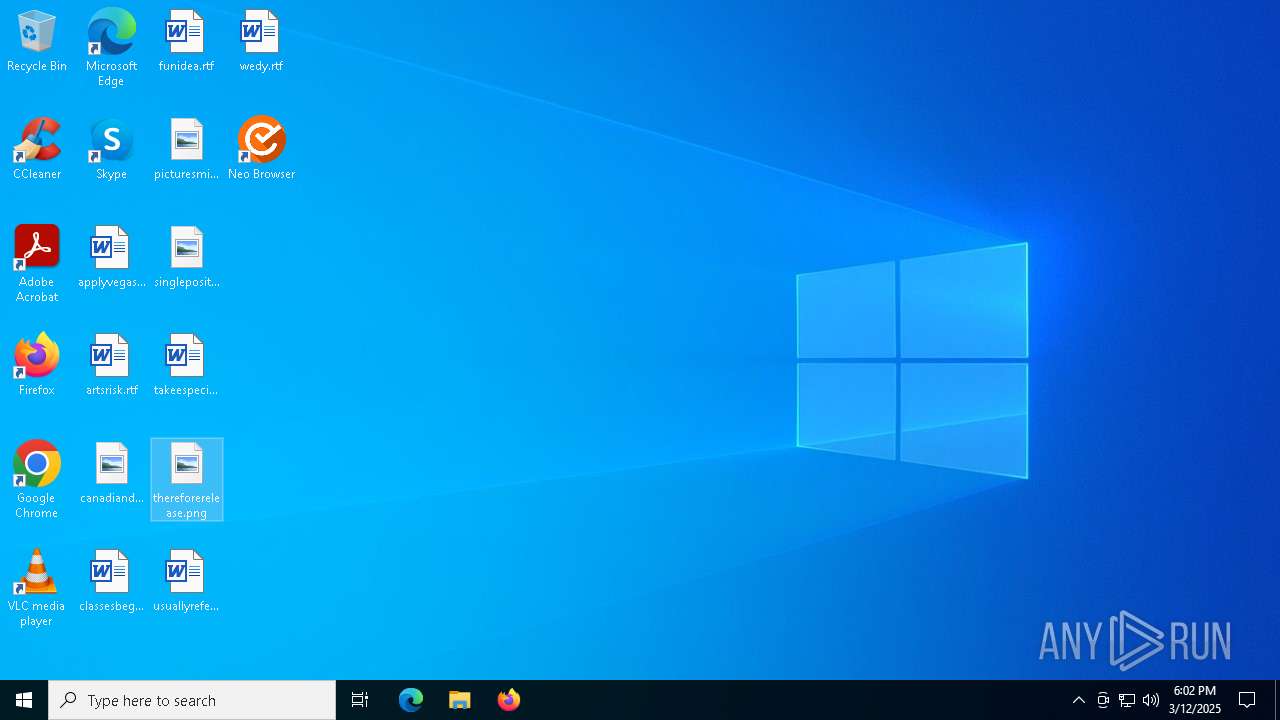
Application launched itself
- Neo Browser.exe (PID: 2088)
INFO
Checks supported languages
- identity_helper.exe (PID: 8296)
Executable content was dropped or overwritten
- msedge.exe (PID: 7280)
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 6184)
Application launched itself
- msedge.exe (PID: 7280)
- msedge.exe (PID: 8780)
Reads the computer name
- identity_helper.exe (PID: 8296)
Reads Environment values
- identity_helper.exe (PID: 8296)
The sample compiled with english language support
- Neo-Browser-Setup-1.1.2.exe (PID: 3304)
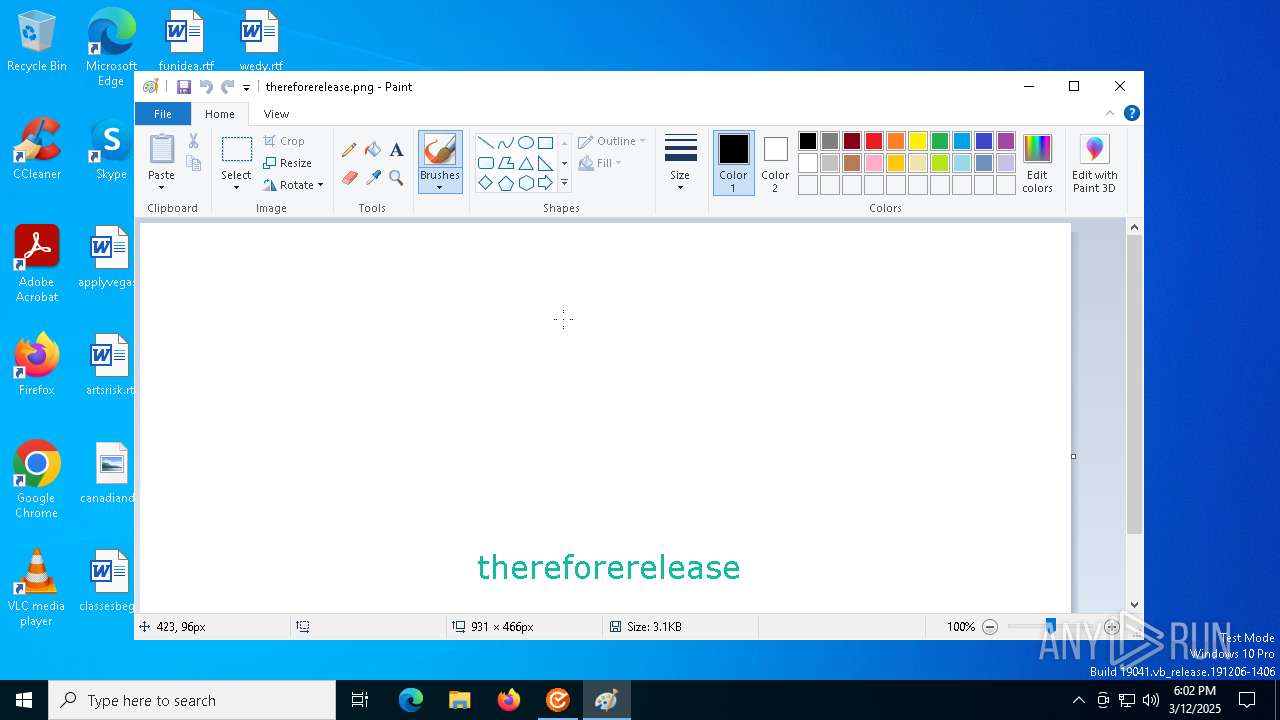
Manual execution by a user
- mspaint.exe (PID: 672)
- Neo Browser.exe (PID: 2088)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 5316)
- powershell.exe (PID: 2972)
- powershell.exe (PID: 6976)
- powershell.exe (PID: 4716)
- powershell.exe (PID: 7344)
- powershell.exe (PID: 8632)
- powershell.exe (PID: 7844)
- powershell.exe (PID: 8236)
- powershell.exe (PID: 4164)
- powershell.exe (PID: 2040)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
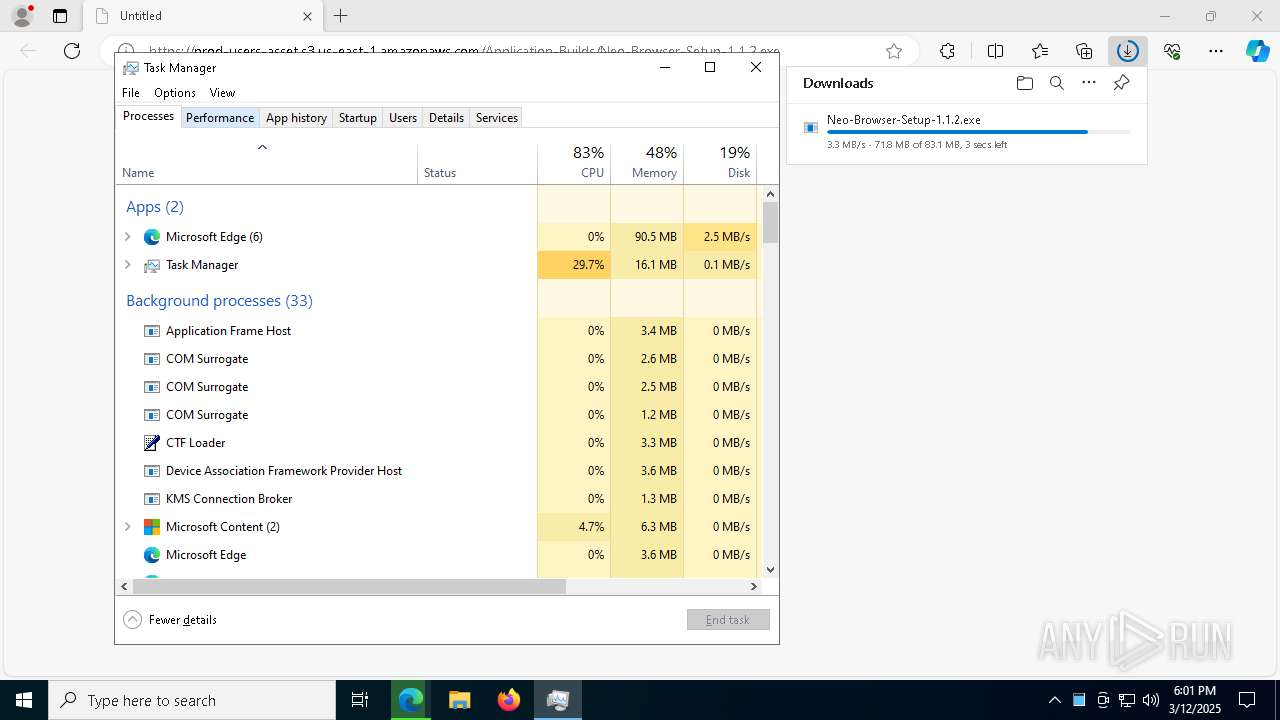
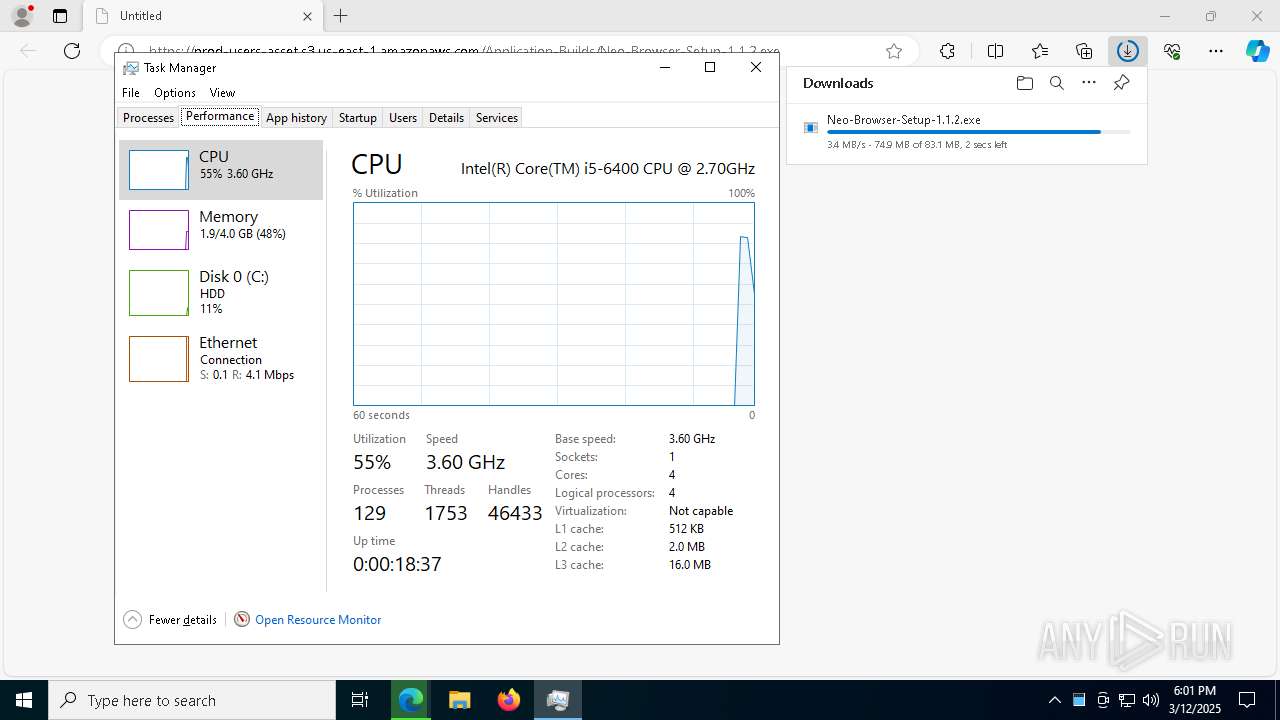
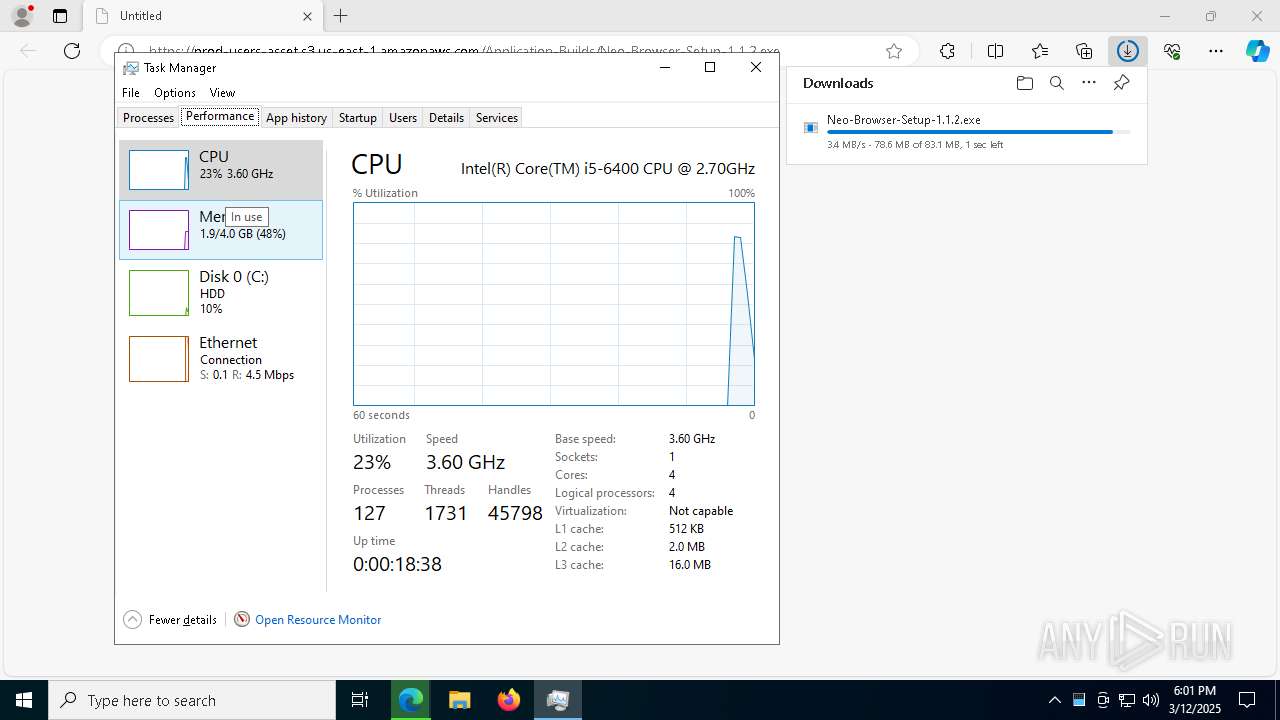
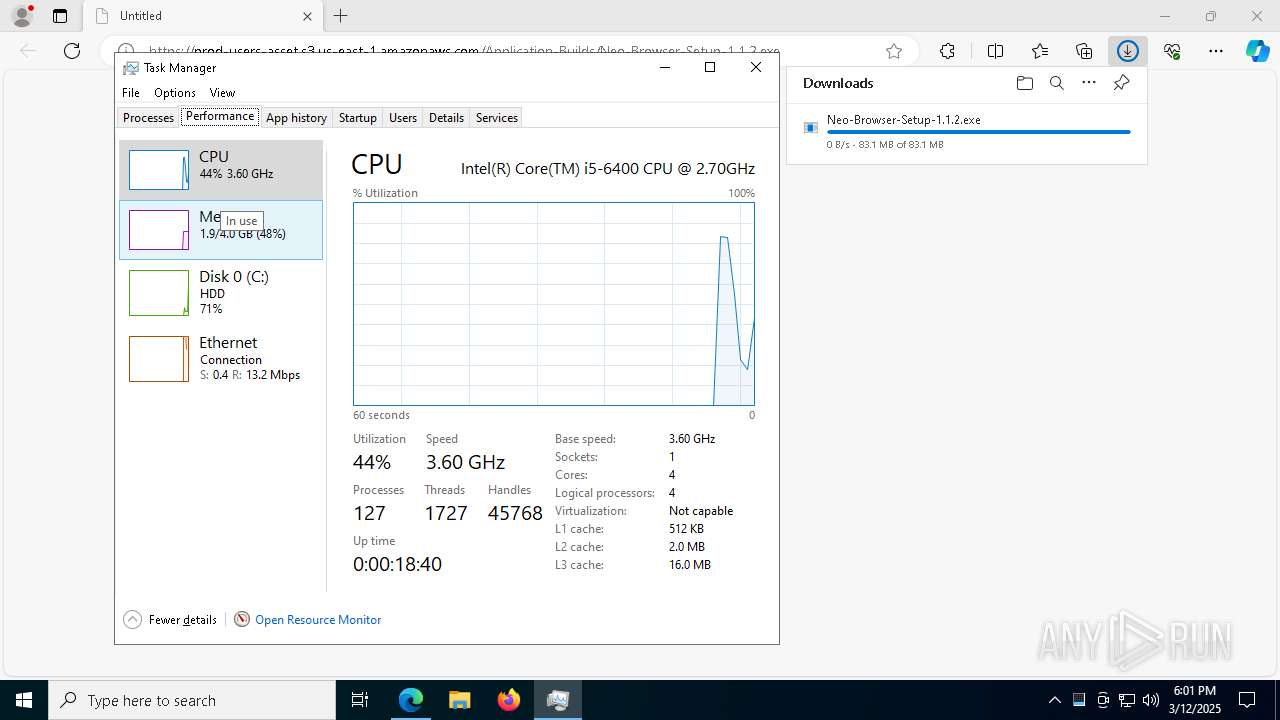
Total processes
277
Monitored processes
127
Malicious processes
2
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 512 | cmd.exe /d /s /c "powershell.exe -command "Get-WmiObject WmiMonitorBasicDisplayParams -Namespace root\wmi | Select-Object Active, InstanceName"" | C:\Windows\System32\cmd.exe | — | Neo Browser.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 544 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 668 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6968 --field-trial-handle=1920,i,12893552887768381201,17917905871986241051,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 672 | "C:\WINDOWS\system32\mspaint.exe" "C:\Users\admin\Desktop\thereforerelease.png" | C:\Windows\System32\mspaint.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Paint Exit code: 0 Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 672 | cmd.exe /d /s /c "powershell.exe -command "Get-WmiObject WmiMonitorBasicDisplayParams -Namespace root\wmi | Select-Object Active, InstanceName"" | C:\Windows\System32\cmd.exe | — | Neo Browser.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1052 | "C:\WINDOWS\SystemApps\Microsoft.Windows.Search_cw5n1h2txyewy\SearchApp.exe" -ServerName:CortanaUI.AppX8z9r6jm96hw4bsbneegw0kyxx296wr9t.mca | C:\Windows\SystemApps\Microsoft.Windows.Search_cw5n1h2txyewy\SearchApp.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Search application Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1240 | "C:\Users\admin\AppData\Local\Programs\neo-browser\Neo Browser.exe" --type=renderer --user-data-dir="C:\Users\admin\AppData\Roaming\neo-browser" --app-path="C:\Users\admin\AppData\Local\Programs\neo-browser\resources\app.asar" --enable-sandbox --enable-blink-features --disable-blink-features --disable-frame-rate-limit --use-fake-ui-for-media-stream --js-flags=--max-old-space-size=4096 --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-zero-copy --enable-main-frame-before-activation --renderer-client-id=8 --field-trial-handle=4084,i,8668027762464479755,17584886699432641895,262144 --enable-features=MediaDevices,WebRTCPipeWireCapturer --disable-features=SpareRendererForSitePerProcess,WinDelaySpellcheckServiceInit,WinRetrieveSuggestionsOnlyOnDemand --variations-seed-version --mojo-platform-channel-handle=3988 /prefetch:1 | C:\Users\admin\AppData\Local\Programs\neo-browser\Neo Browser.exe | — | Neo Browser.exe | |||||||||||
User: admin Company: iamneo.ai Integrity Level: LOW Description: A secure browser that prevents unauthorized activities and ensures exam integrity. Exit code: 0 Version: 1.1.2 Modules
| |||||||||||||||
| 1324 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4416 --field-trial-handle=2332,i,4898020740423737738,16125601041477602916,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1676 | tasklist /FI "USERNAME eq admin" /FI "IMAGENAME eq Neo Browser.exe" /FO csv | C:\Windows\SysWOW64\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Lists the current running tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2040 | powershell.exe -command "Get-WmiObject WmiMonitorBasicDisplayParams -Namespace root\wmi | Select-Object Active, InstanceName" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
87 963
Read events
87 637
Write events
289
Delete events
37
Modification events
| (PID) Process: | (7280) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 5961B346BF8E2F00 | |||
| (PID) Process: | (7280) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328464 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {0F757022-73A8-454E-9F71-72019F28E428} | |||
| (PID) Process: | (7280) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328464 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {E6EE6446-F1DE-4F6C-B96F-457FD64D968A} | |||
| (PID) Process: | (7280) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7280) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7280) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7280) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7280) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: F790AA46BF8E2F00 | |||
| (PID) Process: | (7280) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: F84FDA46BF8E2F00 | |||
| (PID) Process: | (7280) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
Executable files
39
Suspicious files
614
Text files
237
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7280 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b315.TMP | — | |
MD5:— | SHA256:— | |||
| 7280 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7280 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b325.TMP | — | |
MD5:— | SHA256:— | |||
| 7280 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7280 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b325.TMP | — | |
MD5:— | SHA256:— | |||
| 7280 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7280 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b325.TMP | — | |
MD5:— | SHA256:— | |||
| 7280 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7280 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b344.TMP | — | |
MD5:— | SHA256:— | |||
| 7280 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
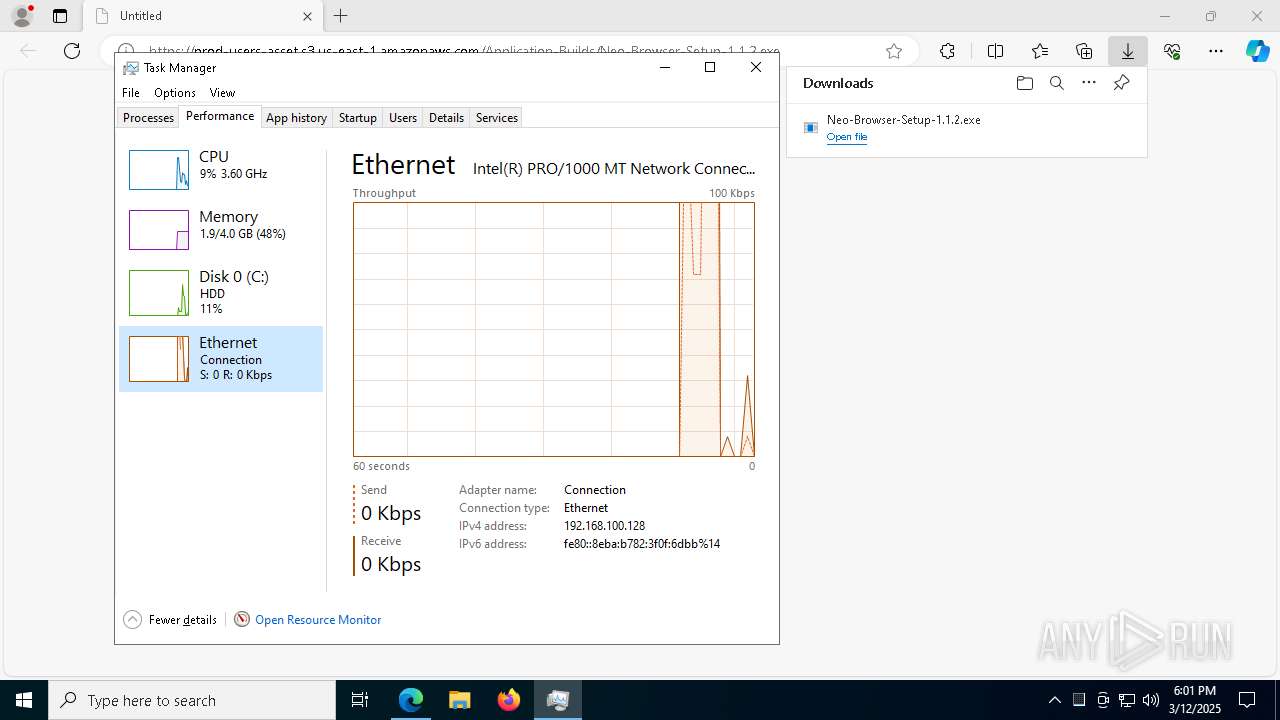
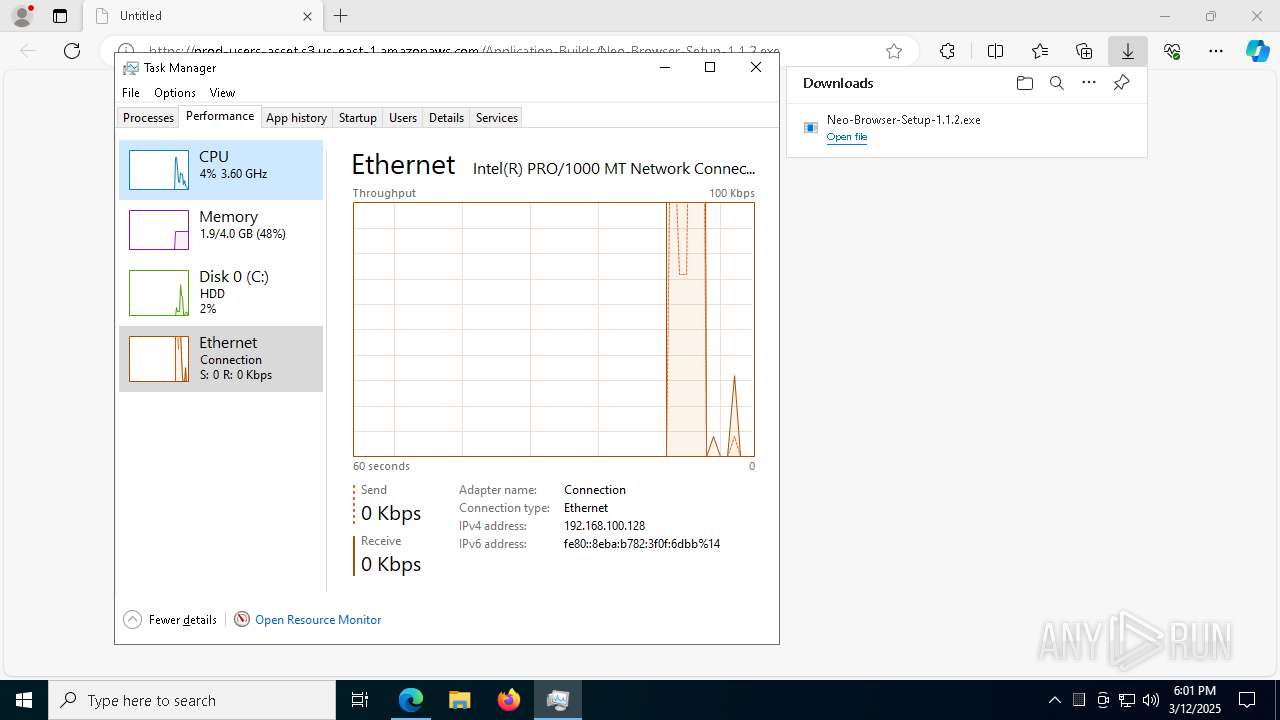
TCP/UDP connections
62
DNS requests
56
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5228 | SIHClient.exe | GET | 200 | 23.75.65.219:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5228 | SIHClient.exe | GET | 200 | 23.75.65.219:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
8852 | svchost.exe | HEAD | 200 | 2.16.10.177:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1741808917&P2=404&P3=2&P4=YnSxUfaYtLNjewNGvBQSs3zCTz6520ue4IuO2KNQ%2fi%2flBZa2SAPbpCW5t7KKXNIsgs0g1gKOEXaFd4f4RHzNpg%3d%3d | unknown | — | — | whitelisted |
8852 | svchost.exe | GET | 206 | 2.16.10.177:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1741808917&P2=404&P3=2&P4=YnSxUfaYtLNjewNGvBQSs3zCTz6520ue4IuO2KNQ%2fi%2flBZa2SAPbpCW5t7KKXNIsgs0g1gKOEXaFd4f4RHzNpg%3d%3d | unknown | — | — | whitelisted |
1052 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
8852 | svchost.exe | GET | 206 | 2.16.10.177:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1741808917&P2=404&P3=2&P4=YnSxUfaYtLNjewNGvBQSs3zCTz6520ue4IuO2KNQ%2fi%2flBZa2SAPbpCW5t7KKXNIsgs0g1gKOEXaFd4f4RHzNpg%3d%3d | unknown | — | — | whitelisted |
8852 | svchost.exe | GET | 206 | 2.16.10.177:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1741808917&P2=404&P3=2&P4=YnSxUfaYtLNjewNGvBQSs3zCTz6520ue4IuO2KNQ%2fi%2flBZa2SAPbpCW5t7KKXNIsgs0g1gKOEXaFd4f4RHzNpg%3d%3d | unknown | — | — | whitelisted |
8852 | svchost.exe | GET | 206 | 2.16.10.177:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1741808917&P2=404&P3=2&P4=YnSxUfaYtLNjewNGvBQSs3zCTz6520ue4IuO2KNQ%2fi%2flBZa2SAPbpCW5t7KKXNIsgs0g1gKOEXaFd4f4RHzNpg%3d%3d | unknown | — | — | whitelisted |
6184 | BackgroundTransferHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
8852 | svchost.exe | GET | — | 2.16.10.177:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1741808917&P2=404&P3=2&P4=YnSxUfaYtLNjewNGvBQSs3zCTz6520ue4IuO2KNQ%2fi%2flBZa2SAPbpCW5t7KKXNIsgs0g1gKOEXaFd4f4RHzNpg%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.48.23.141:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7556 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7280 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7556 | msedge.exe | 52.217.121.42:443 | prod-users-asset.s3.us-east-1.amazonaws.com | — | US | shared |
7556 | msedge.exe | 204.79.197.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7556 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
prod-users-asset.s3.us-east-1.amazonaws.com |
| shared |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
update.googleapis.com |
| whitelisted |