| File name: | LBB.exe |
| Full analysis: | https://app.any.run/tasks/1511cf1c-af0e-49c6-adf1-41b967e6942a |
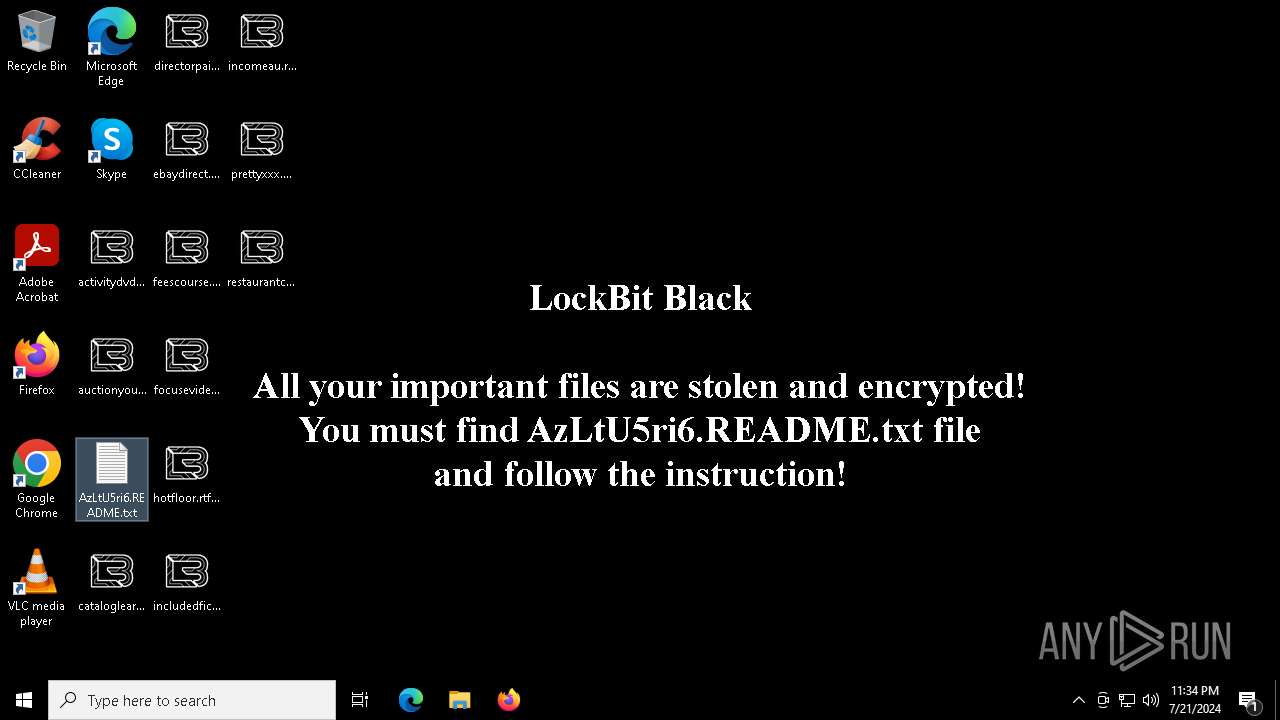
| Verdict: | Malicious activity |
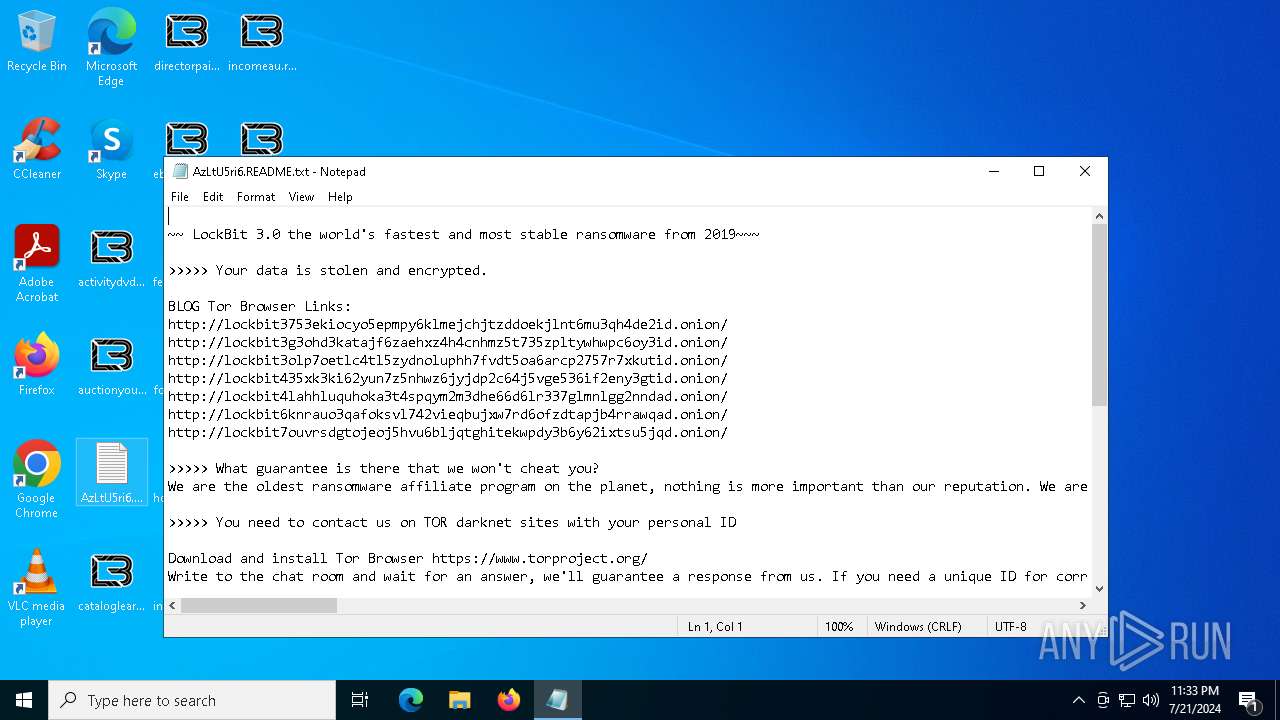
| Threats: | LockBit, a ransomware variant, encrypts data on infected machines, demanding a ransom payment for decryption. Used in targeted attacks, It's a significant risk to organizations. |
| Analysis date: | July 21, 2024, 23:33:34 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | F6490D06C7A3BEA39522B759A3E47D05 |
| SHA1: | F1BFD118062D97CD869E843C6DB1C4CEC0A35CB7 |
| SHA256: | 86FE17D8D2086A8F58BD6C3114A2FFA74577778A990E18B33E556563612CD709 |
| SSDEEP: | 3072:0MMMMMM/MMMMMMTMMMMMM/MMMMMMTMMMMMM/MMMMMOMMMMMM/MMMMM+MMMMMM/Mt:EkEQ8dRoXjzL5VSZmq/n |
MALICIOUS
Drops the executable file immediately after the start
- LBB.exe (PID: 5636)
- LBB.exe (PID: 7244)
Known privilege escalation attack
- dllhost.exe (PID: 6240)
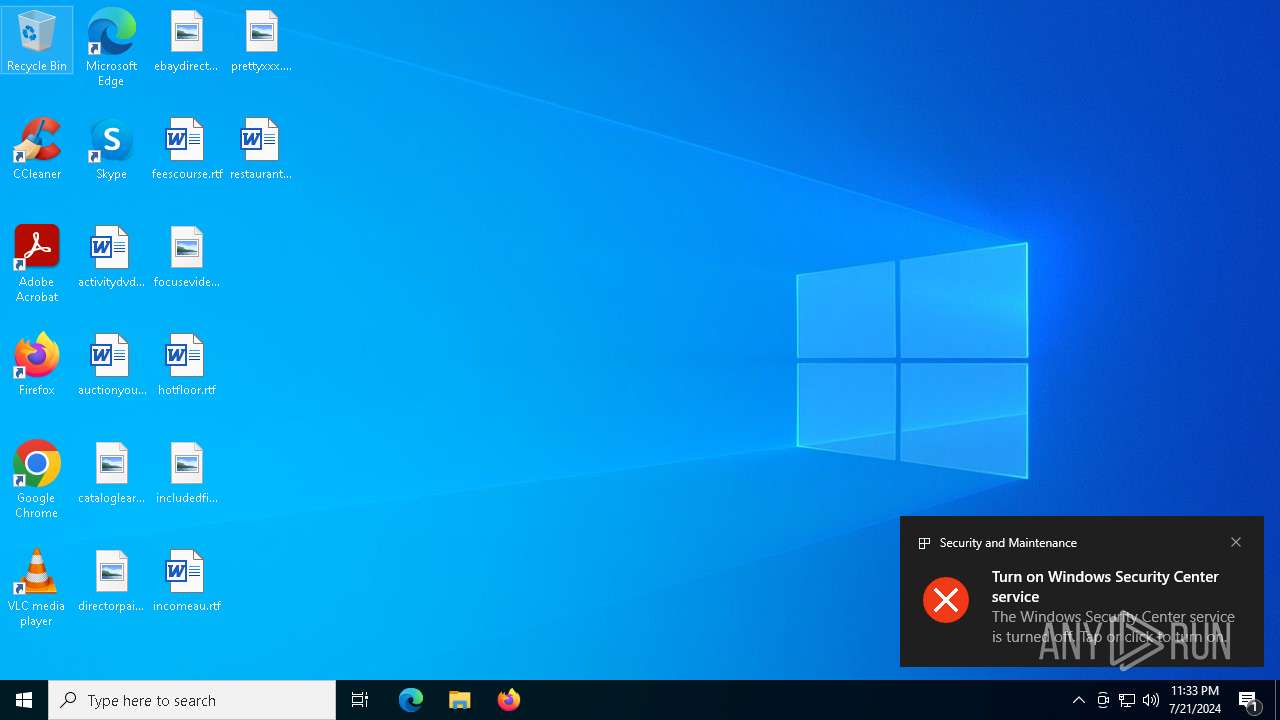
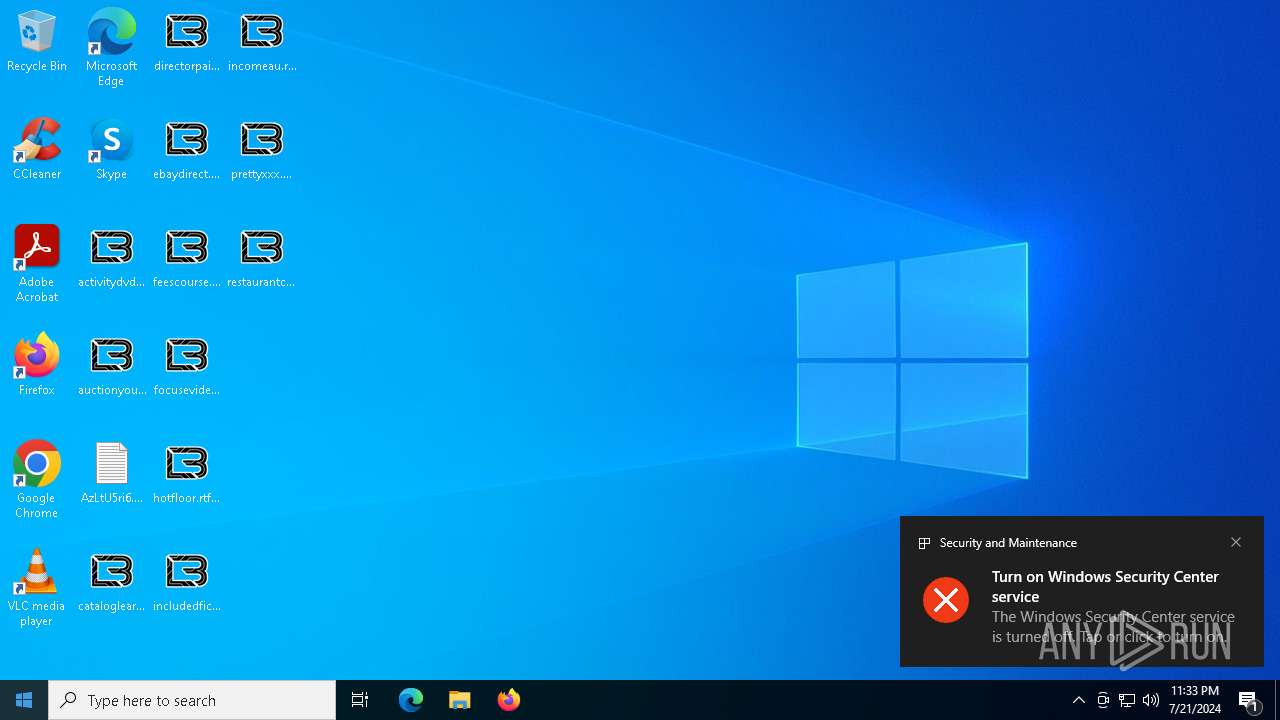
Renames files like ransomware
- LBB.exe (PID: 7244)
[YARA] LockBit is detected
- LBB.exe (PID: 7244)
SUSPICIOUS
Executes as Windows Service
- VSSVC.exe (PID: 5184)
Write to the desktop.ini file (may be used to cloak folders)
- LBB.exe (PID: 7244)
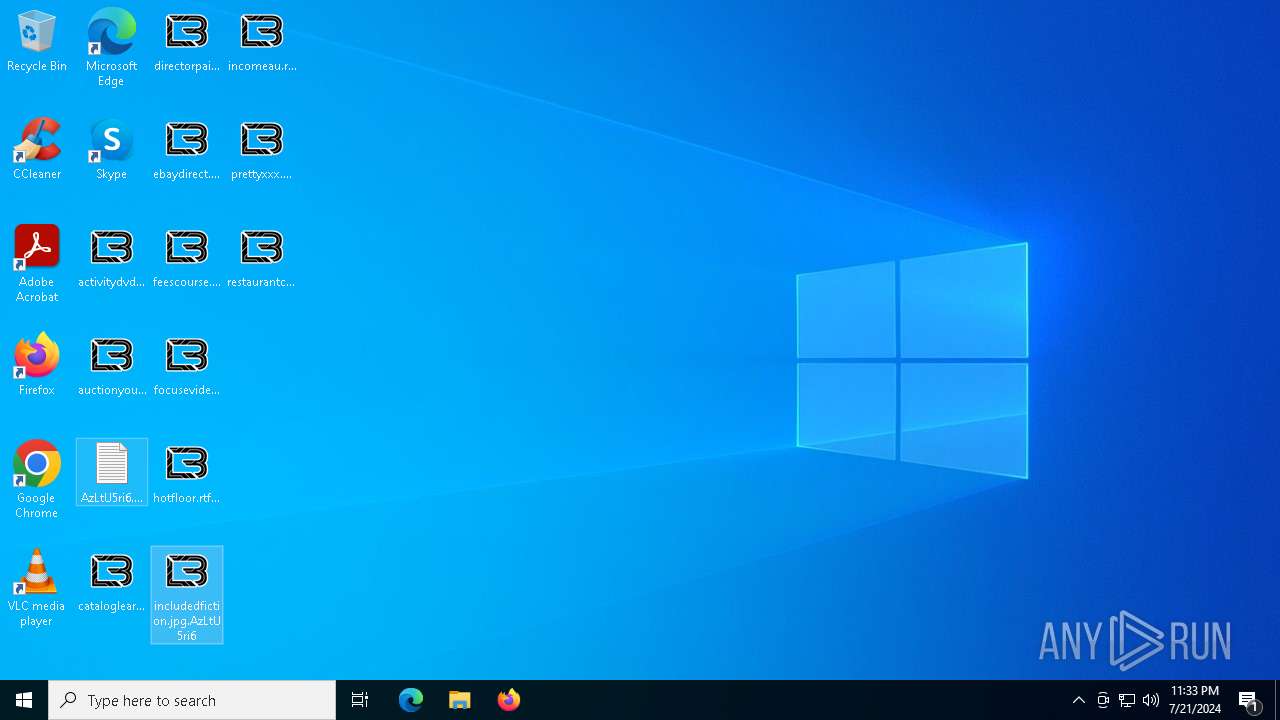
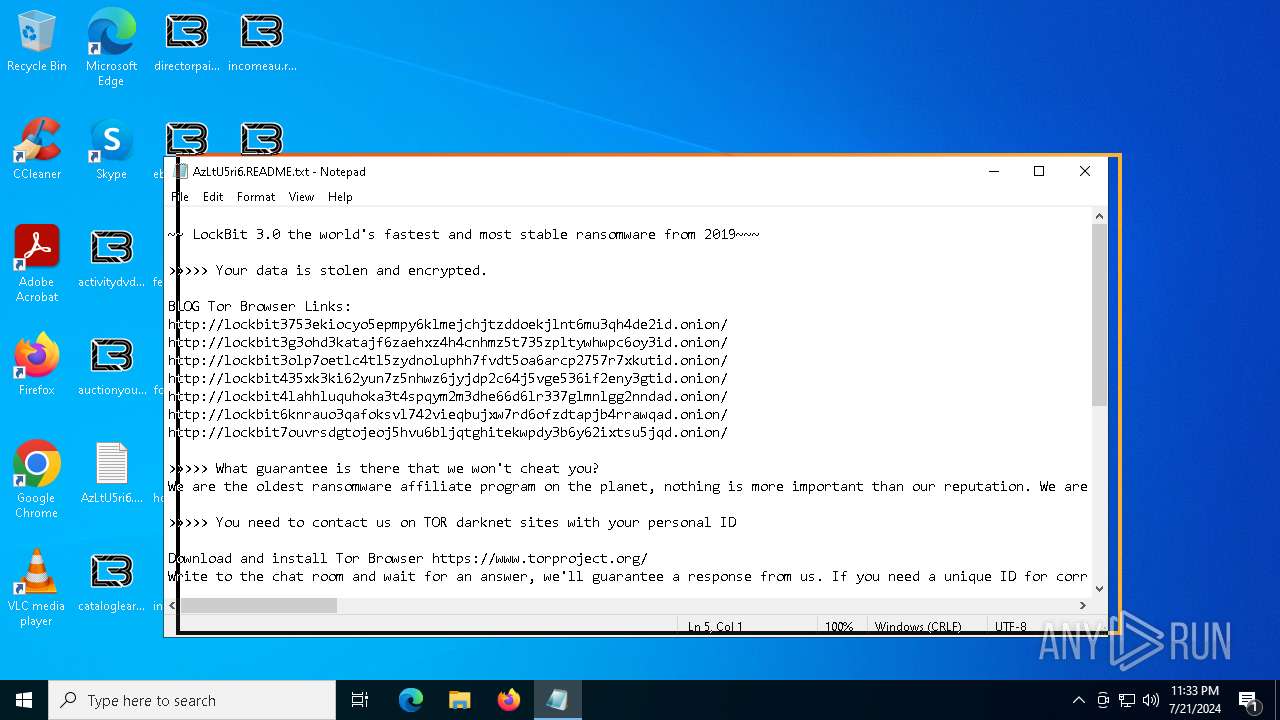
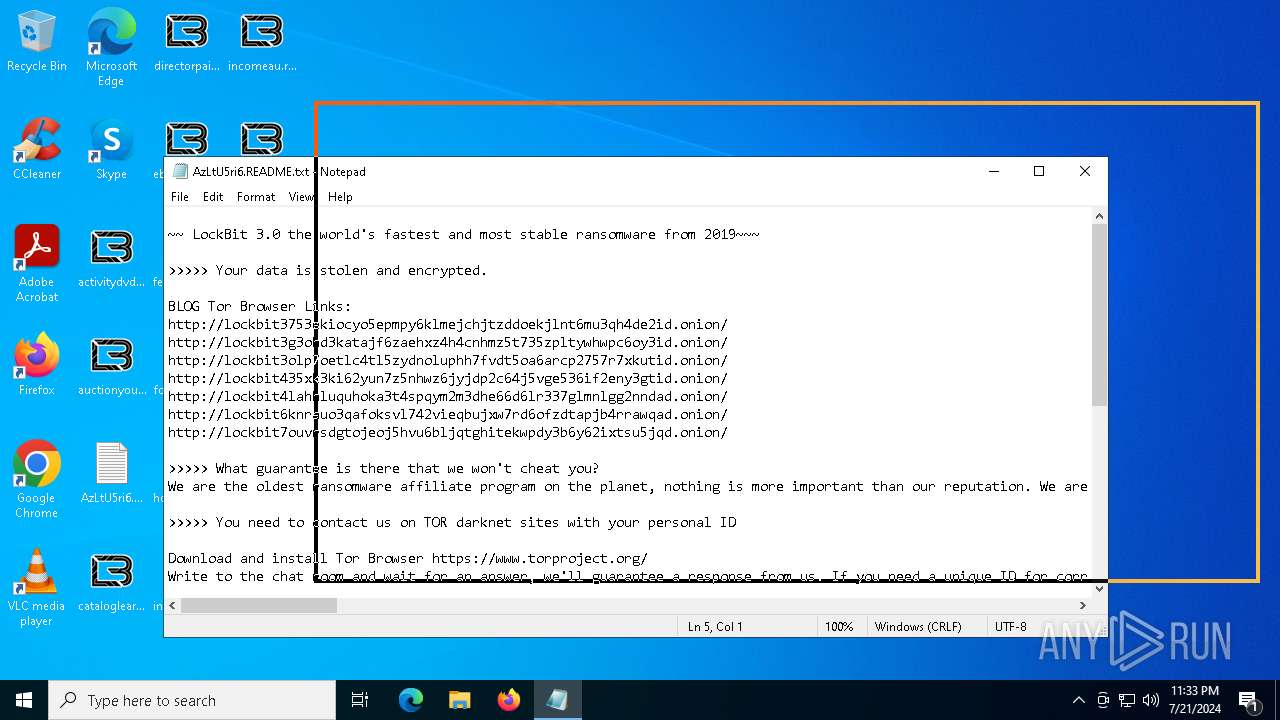
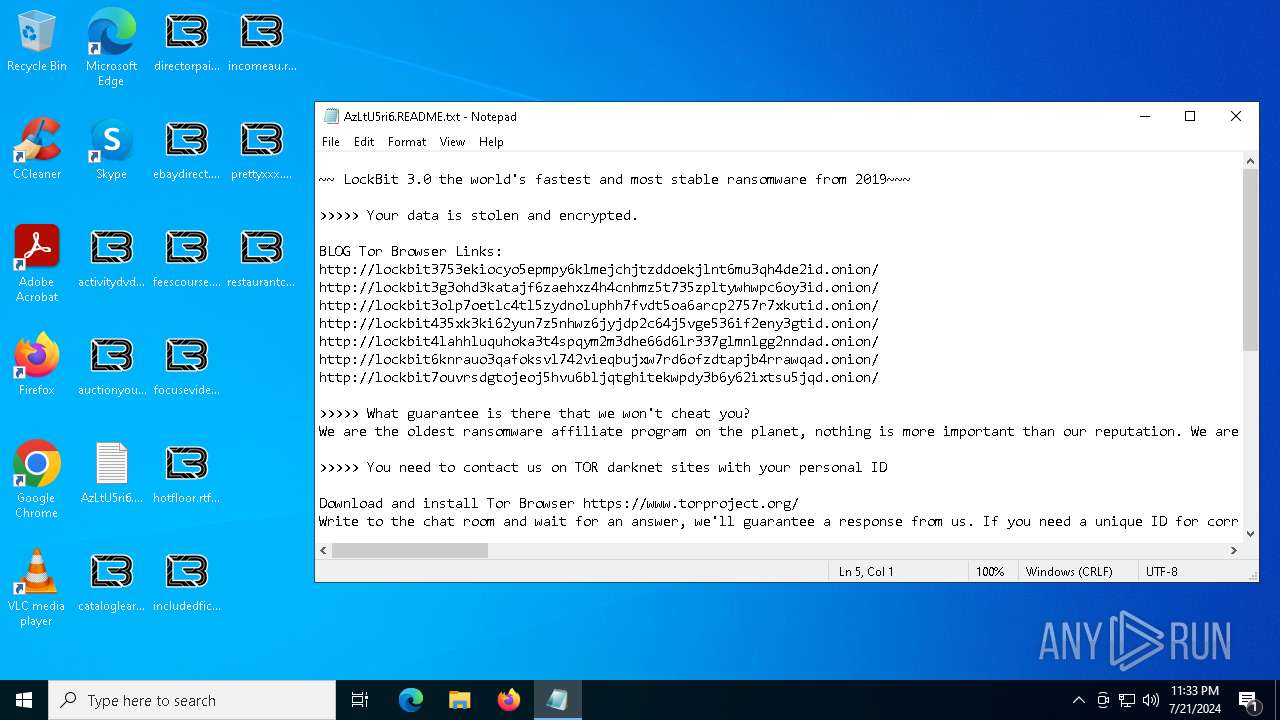
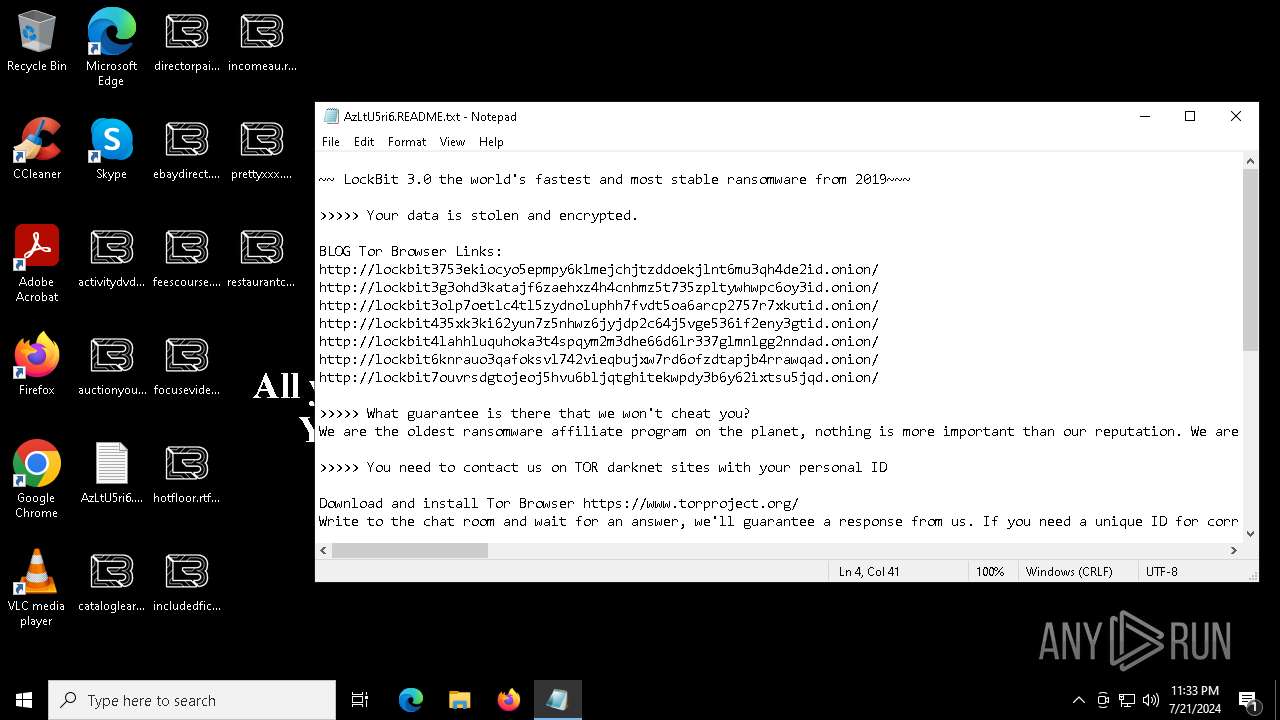
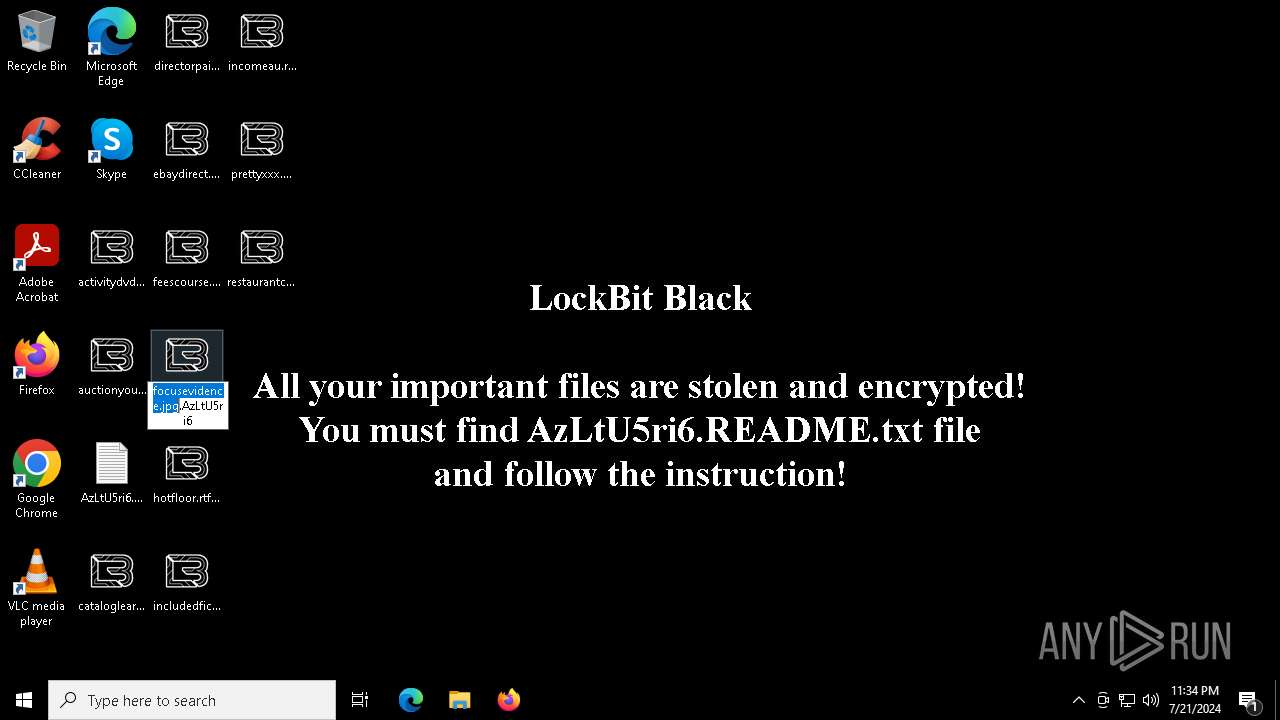
Creates files like ransomware instruction
- LBB.exe (PID: 7244)
Executable content was dropped or overwritten
- LBB.exe (PID: 7244)
Starts application with an unusual extension
- LBB.exe (PID: 7244)
Changes the desktop background image
- LBB.exe (PID: 7244)
INFO
Checks supported languages
- LBB.exe (PID: 5636)
- LBB.exe (PID: 7244)
- D725.tmp (PID: 7332)
Reads security settings of Internet Explorer
- dllhost.exe (PID: 6240)
- notepad.exe (PID: 2020)
- notepad.exe (PID: 5096)
Creates files in the program directory
- LBB.exe (PID: 7244)
Reads the computer name
- LBB.exe (PID: 5636)
- LBB.exe (PID: 7244)
Reads the machine GUID from the registry
- LBB.exe (PID: 5636)
- LBB.exe (PID: 7244)
Manual execution by a user
- notepad.exe (PID: 2020)
- notepad.exe (PID: 5096)
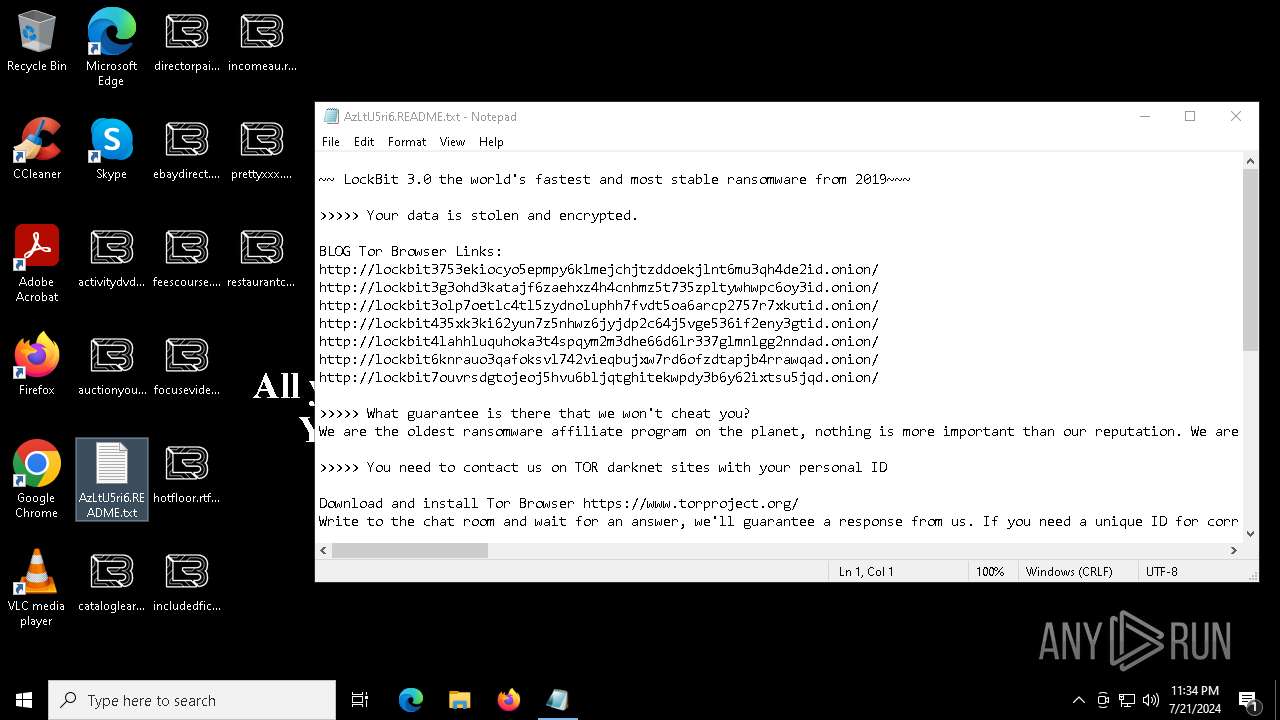
Dropped object may contain TOR URL's
- LBB.exe (PID: 7244)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (38.3) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (26.2) |
| .exe | | | Win16/32 Executable Delphi generic (12) |
| .exe | | | Generic Win/DOS Executable (11.6) |
| .exe | | | DOS Executable Generic (11.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2022:06:11 09:50:55+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.12 |
| CodeSize: | 106496 |
| InitializedDataSize: | 51200 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1b46f |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Total processes
147
Monitored processes
7
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2020 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\AzLtU5ri6.README.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5096 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\AzLtU5ri6.README.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5184 | C:\WINDOWS\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5636 | "C:\Users\admin\AppData\Local\Temp\LBB.exe" | C:\Users\admin\AppData\Local\Temp\LBB.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 6240 | C:\WINDOWS\SysWOW64\DllHost.exe /Processid:{3E5FC7F9-9A51-4367-9063-A120244FBEC7} | C:\Windows\SysWOW64\dllhost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7244 | "C:\Users\admin\AppData\Local\Temp\LBB.exe" | C:\Users\admin\AppData\Local\Temp\LBB.exe | dllhost.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 7332 | "C:\ProgramData\D725.tmp" | C:\ProgramData\D725.tmp | — | LBB.exe | |||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
Total events
8 696
Read events
6 259
Write events
2 436
Delete events
1
Modification events
| (PID) Process: | (6240) dllhost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\3c\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\cmlua.dll,-100 |
Value: Connection Manager | |||
| (PID) Process: | (6240) dllhost.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (6240) dllhost.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (6240) dllhost.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (6240) dllhost.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (7244) LBB.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | GlobalAssocChangedCounter |
Value: 12 | |||
| (PID) Process: | (7244) LBB.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\WINEVT\Channels\AirSpaceChannel |
| Operation: | write | Name: | Enabled |
Value: 0 | |||
| (PID) Process: | (7244) LBB.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\WINEVT\Channels\AirSpaceChannel |
| Operation: | write | Name: | ChannelAccess |
Value: O:BAG:SYD:(A;;0x1;;;SY)(A;;0x5;;;BA)(A;;0x1;;;LA) | |||
| (PID) Process: | (7244) LBB.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\WINEVT\Channels\AMSI/Debug |
| Operation: | write | Name: | Enabled |
Value: 0 | |||
| (PID) Process: | (7244) LBB.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\WINEVT\Channels\AMSI/Debug |
| Operation: | write | Name: | ChannelAccess |
Value: O:BAG:SYD:(A;;0x1;;;SY)(A;;0x5;;;BA)(A;;0x1;;;LA) | |||
Executable files
1
Suspicious files
177
Text files
93
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7244 | LBB.exe | C:\$Recycle.Bin\S-1-5-18\JJJJJJJJJJJ | binary | |
MD5:3DC67C92F44C82732C60A2F7101C7CD6 | SHA256:F007F4E62F2F74C7F39E77B3CB8D0D587357272935E6AC299B410C56BBF3E9A8 | |||
| 7244 | LBB.exe | C:\ProgramData\AzLtU5ri6.ico | image | |
MD5:88D9337C4C9CFE2D9AFF8A2C718EC76B | SHA256:95E059EF72686460884B9AEA5C292C22917F75D56FE737D43BE440F82034F438 | |||
| 7244 | LBB.exe | C:\$Recycle.Bin\S-1-5-18\EEEEEEEEEEE | binary | |
MD5:3DC67C92F44C82732C60A2F7101C7CD6 | SHA256:F007F4E62F2F74C7F39E77B3CB8D0D587357272935E6AC299B410C56BBF3E9A8 | |||
| 7244 | LBB.exe | C:\$Recycle.Bin\S-1-5-18\HHHHHHHHHHH | binary | |
MD5:3DC67C92F44C82732C60A2F7101C7CD6 | SHA256:F007F4E62F2F74C7F39E77B3CB8D0D587357272935E6AC299B410C56BBF3E9A8 | |||
| 7244 | LBB.exe | C:\$Recycle.Bin\S-1-5-18\BBBBBBBBBBB | binary | |
MD5:3DC67C92F44C82732C60A2F7101C7CD6 | SHA256:F007F4E62F2F74C7F39E77B3CB8D0D587357272935E6AC299B410C56BBF3E9A8 | |||
| 7244 | LBB.exe | C:\$Recycle.Bin\S-1-5-18\GGGGGGGGGGG | binary | |
MD5:3DC67C92F44C82732C60A2F7101C7CD6 | SHA256:F007F4E62F2F74C7F39E77B3CB8D0D587357272935E6AC299B410C56BBF3E9A8 | |||
| 7244 | LBB.exe | C:\$Recycle.Bin\S-1-5-18\CCCCCCCCCCC | binary | |
MD5:3DC67C92F44C82732C60A2F7101C7CD6 | SHA256:F007F4E62F2F74C7F39E77B3CB8D0D587357272935E6AC299B410C56BBF3E9A8 | |||
| 7244 | LBB.exe | C:\$Recycle.Bin\S-1-5-18\MMMMMMMMMMM | binary | |
MD5:3DC67C92F44C82732C60A2F7101C7CD6 | SHA256:F007F4E62F2F74C7F39E77B3CB8D0D587357272935E6AC299B410C56BBF3E9A8 | |||
| 7244 | LBB.exe | C:\$Recycle.Bin\S-1-5-18\IIIIIIIIIII | binary | |
MD5:3DC67C92F44C82732C60A2F7101C7CD6 | SHA256:F007F4E62F2F74C7F39E77B3CB8D0D587357272935E6AC299B410C56BBF3E9A8 | |||
| 7244 | LBB.exe | C:\$Recycle.Bin\S-1-5-18\DDDDDDDDDDD | binary | |
MD5:3DC67C92F44C82732C60A2F7101C7CD6 | SHA256:F007F4E62F2F74C7F39E77B3CB8D0D587357272935E6AC299B410C56BBF3E9A8 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
31
DNS requests
11
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4716 | svchost.exe | 20.190.160.14:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
5620 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
7856 | svchost.exe | 4.209.32.198:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
4032 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2760 | svchost.exe | 40.113.110.67:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4716 | svchost.exe | 40.126.32.140:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
3616 | backgroundTaskHost.exe | 20.199.58.43:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | unknown |
6944 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
login.live.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |