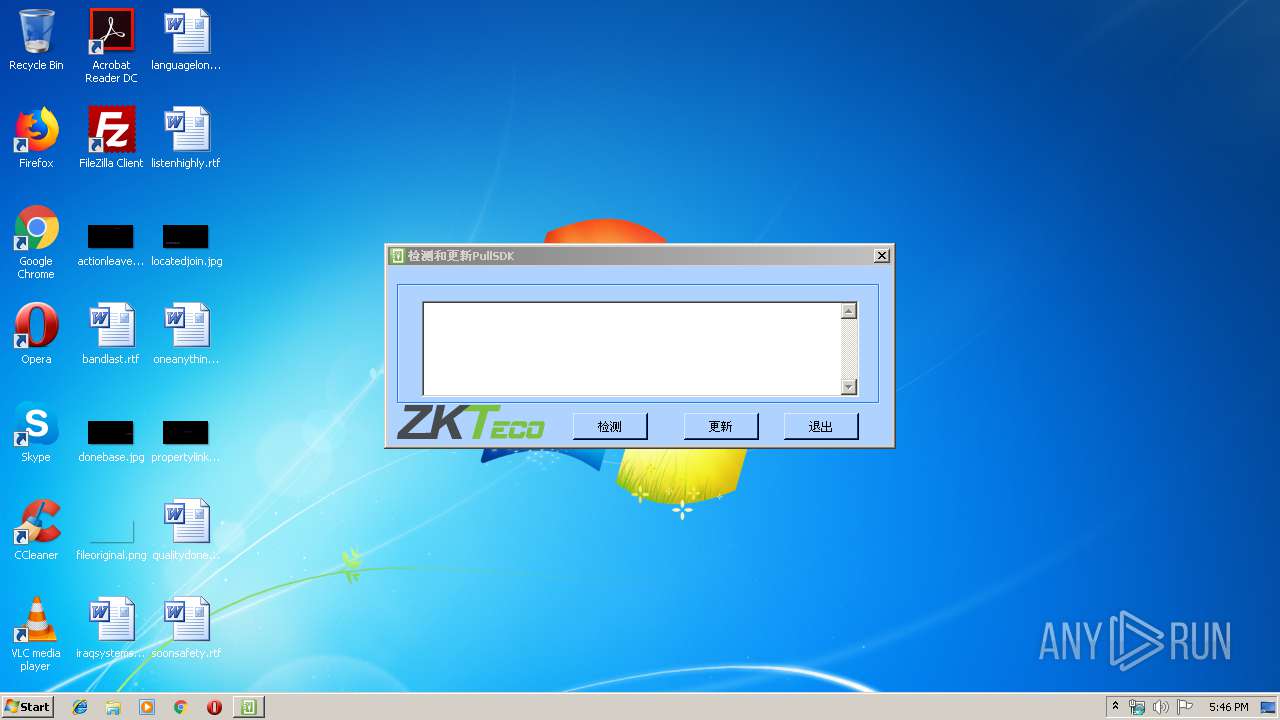
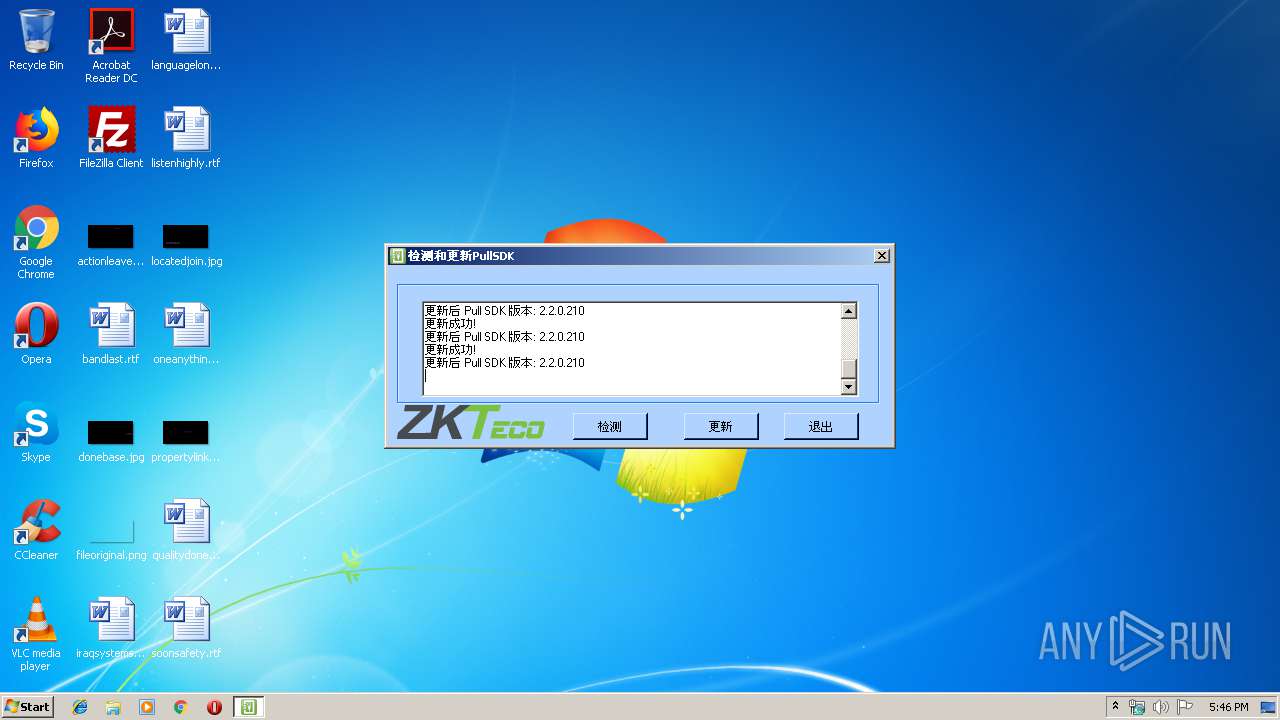
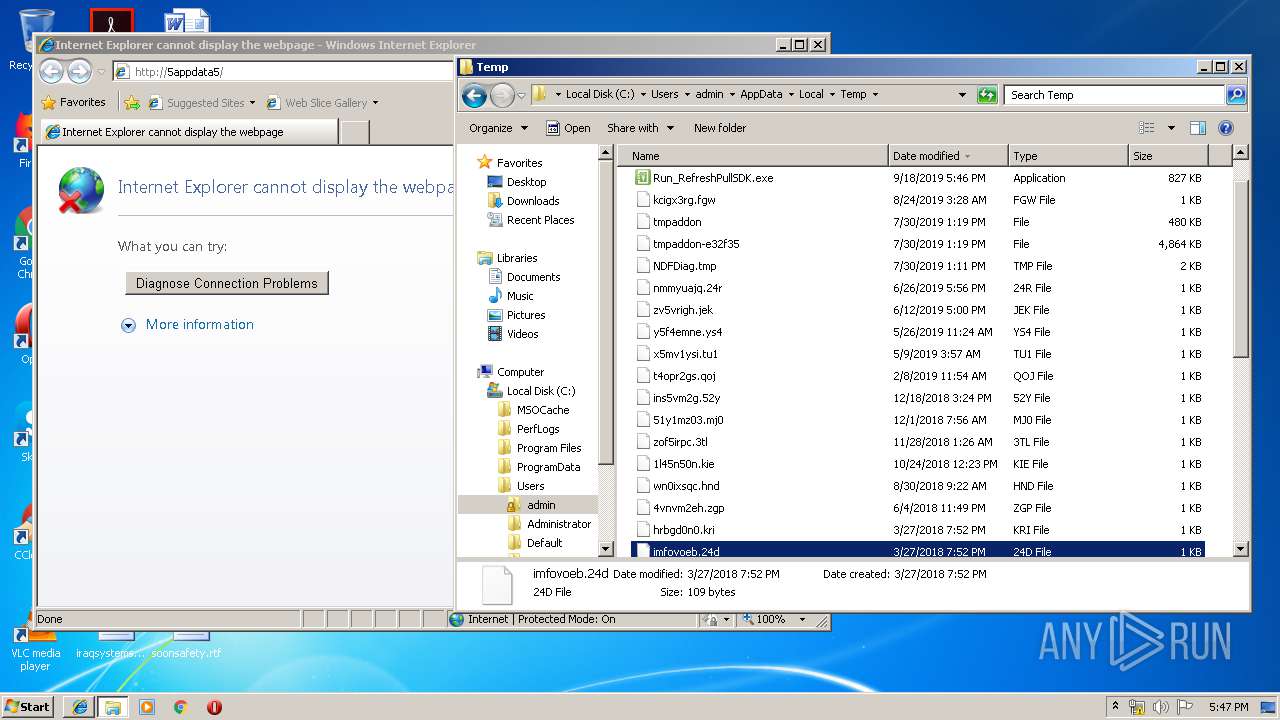
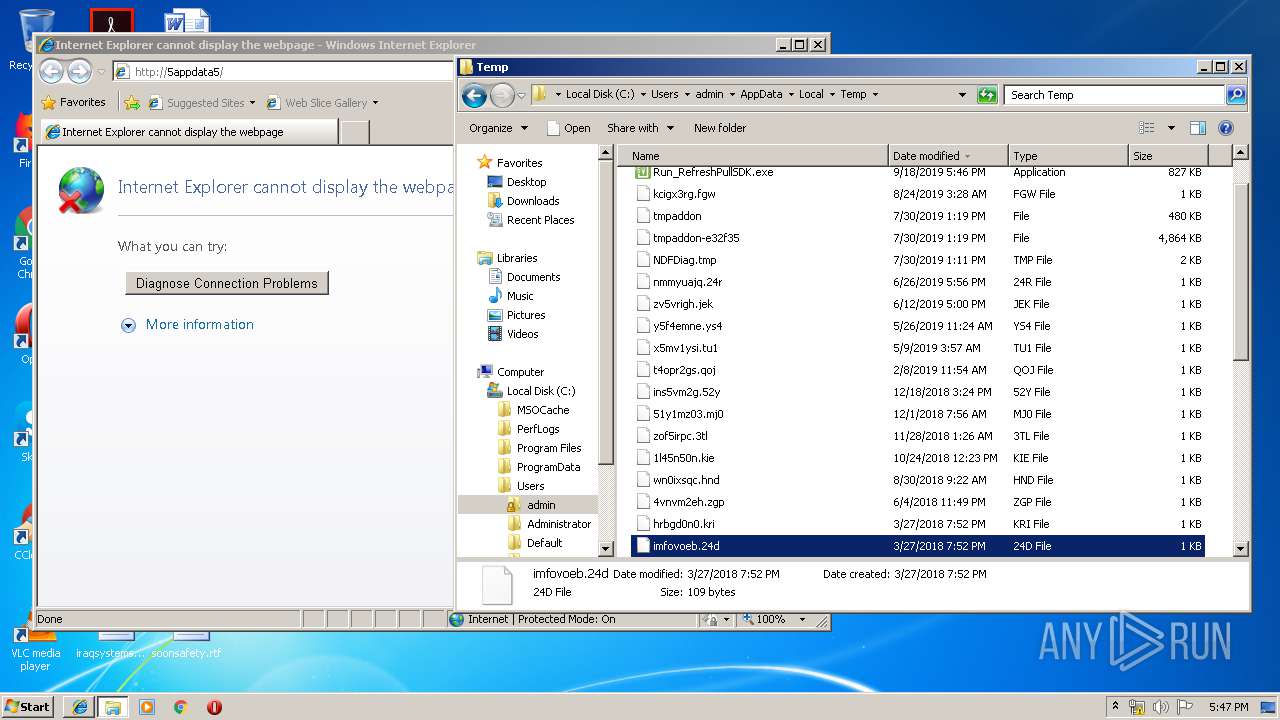
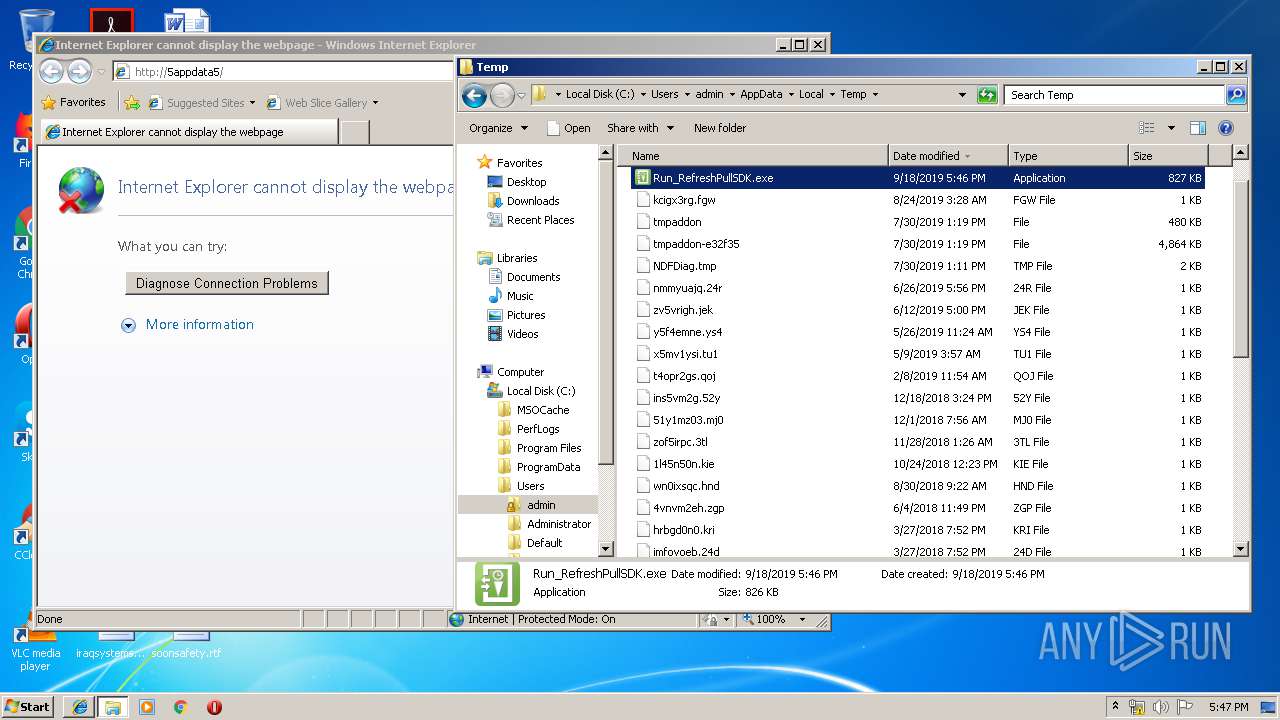
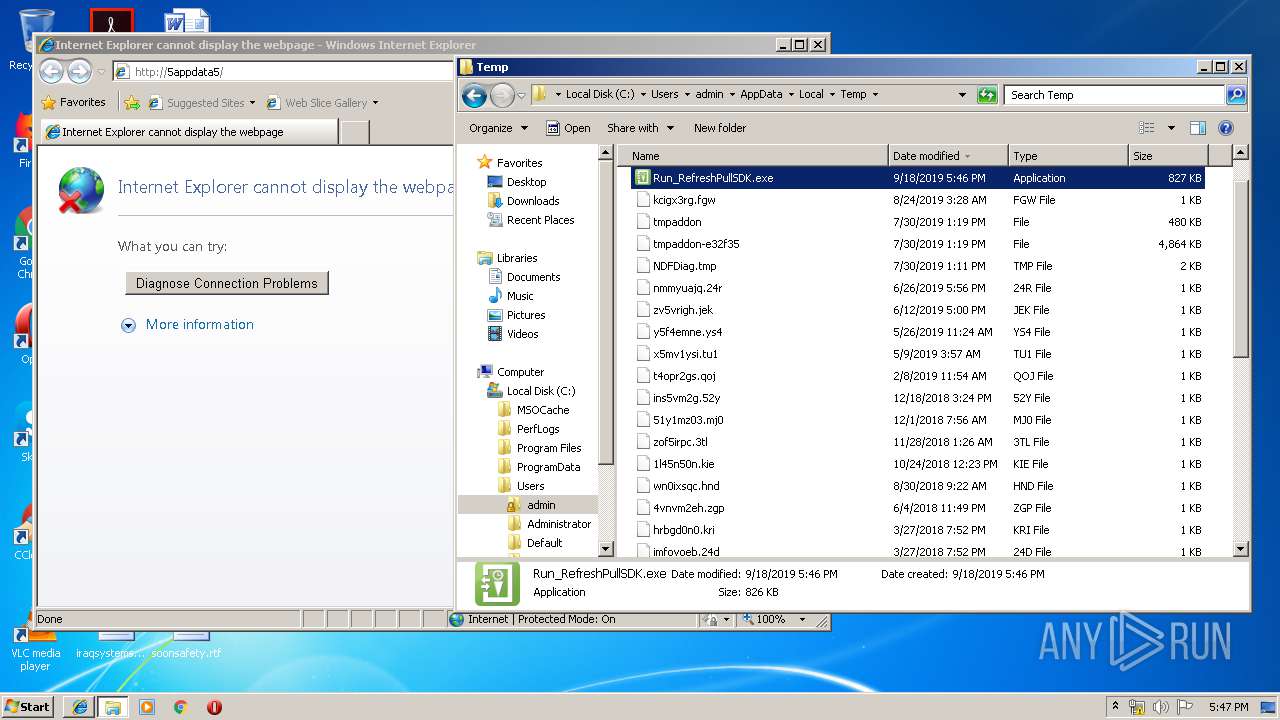
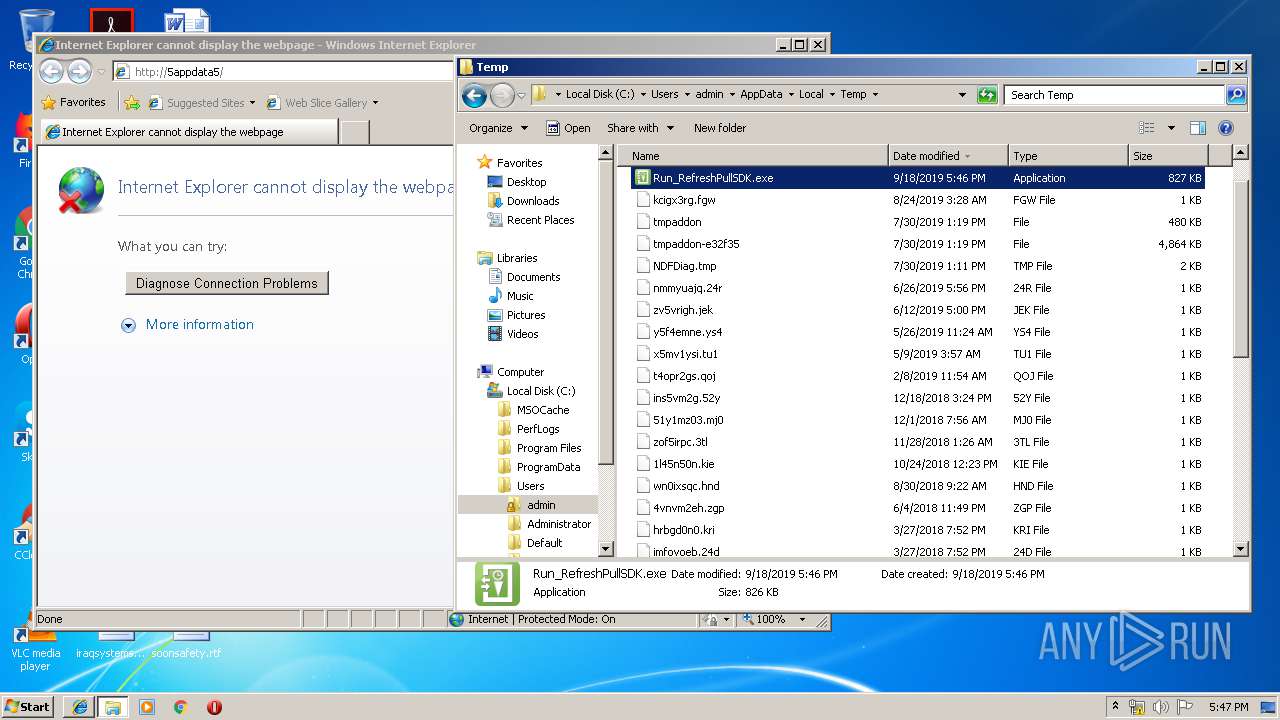
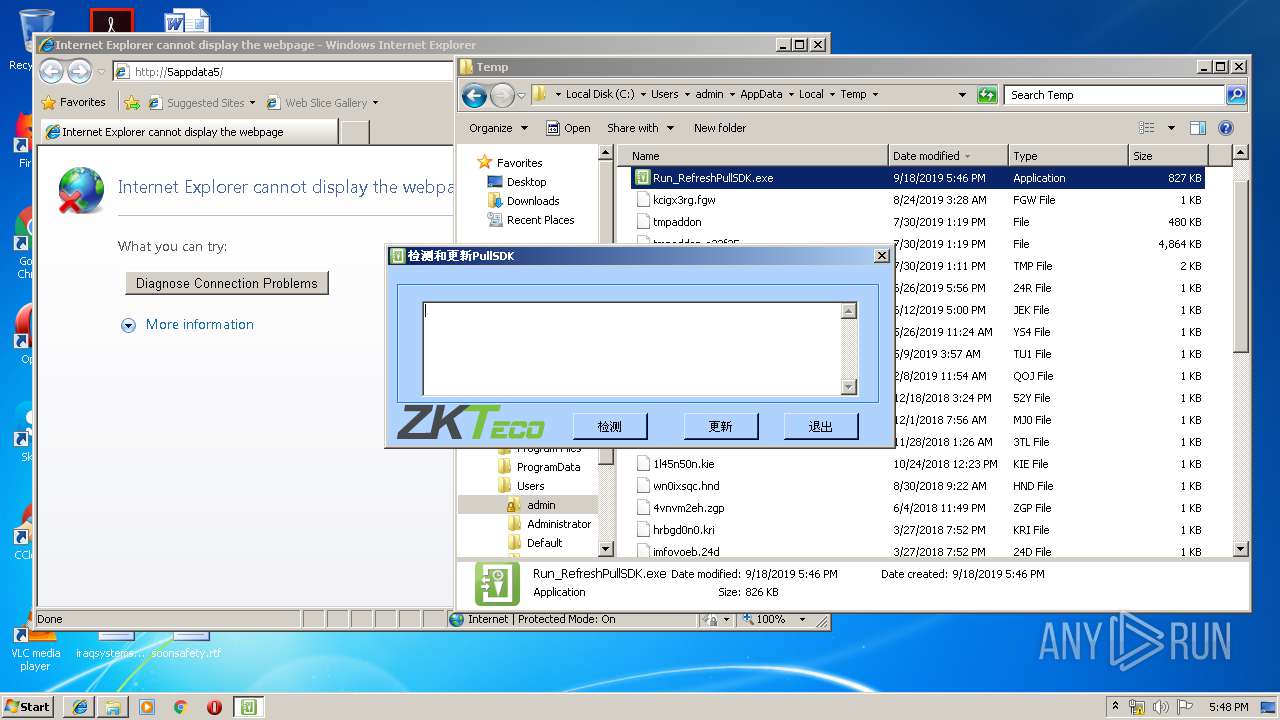
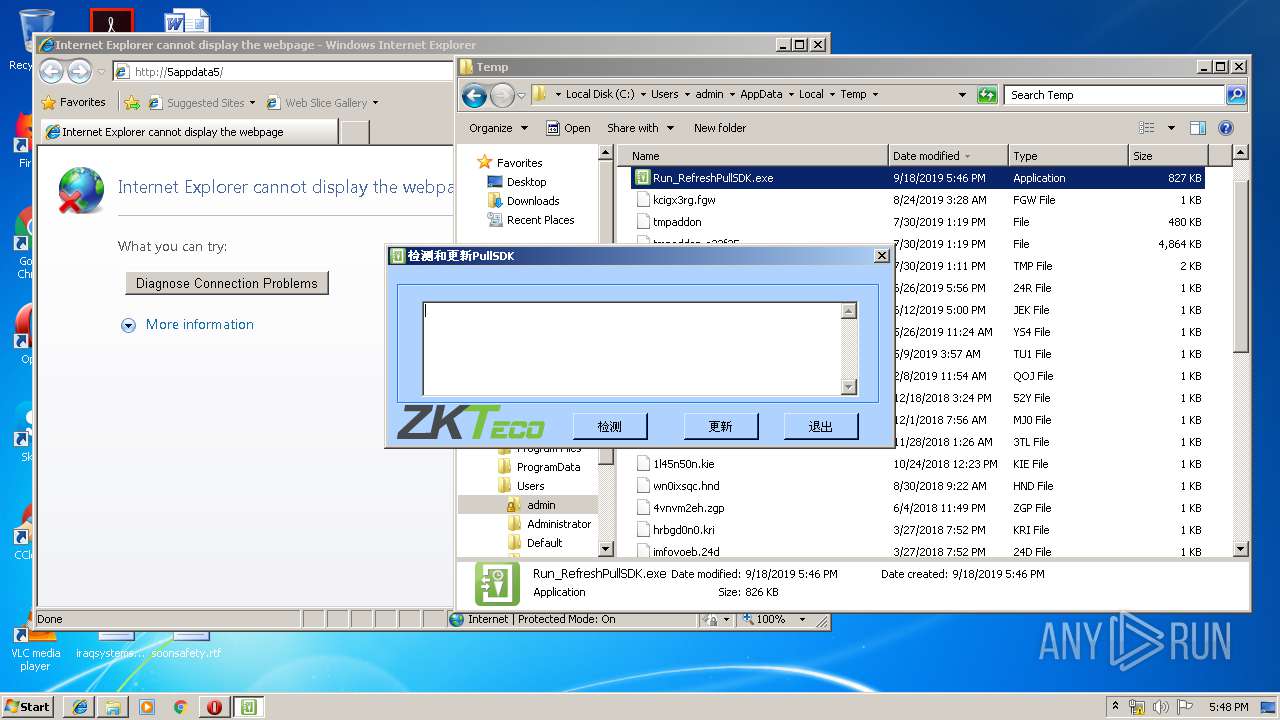
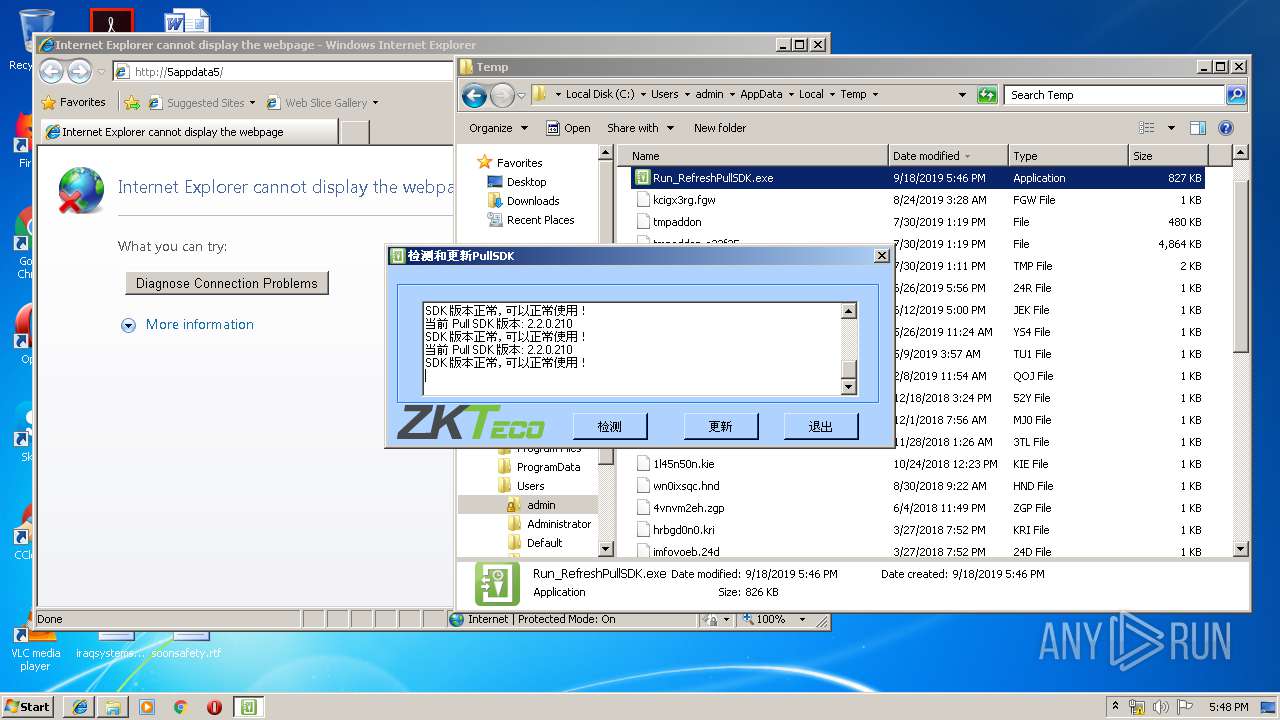
| File name: | Run_RefreshPullSDK.exe |
| Full analysis: | https://app.any.run/tasks/997c91c6-3e14-4240-a895-6f4ab11877f4 |
| Verdict: | Malicious activity |
| Analysis date: | September 18, 2019, 16:46:03 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 682AA868CFE32EB014978F504A4B7D9B |
| SHA1: | 585D4566DFFF9A23C52ED27A35209359806A1FFD |
| SHA256: | 86F8685E944CA441F95C1B93CAFD2822C48DE2544FC4604776B9273EE76DCEA3 |
| SSDEEP: | 24576:lJlh9bDpUnPiMMgKjhfsoK/67ZI2bg9mMN8:lJgKMlEhErsZI289tN8 |
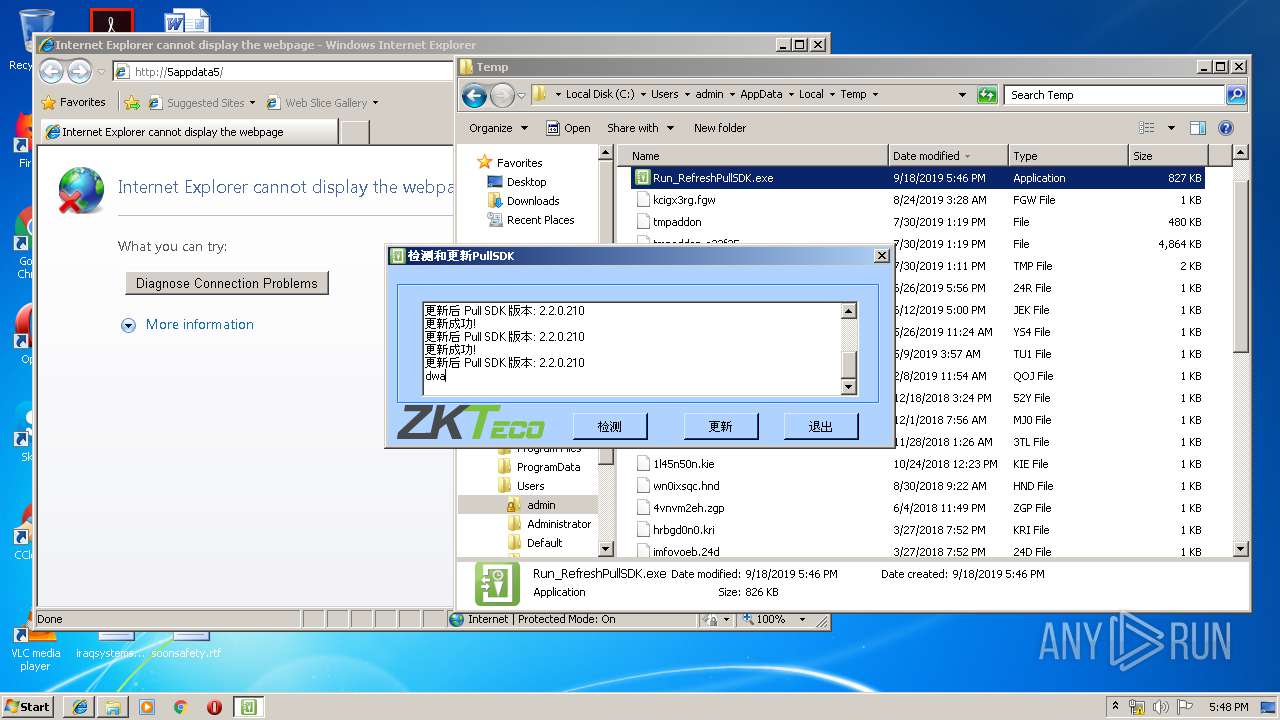
MALICIOUS
Loads dropped or rewritten executable
- CheckSDK.exe (PID: 3976)
- CheckSDK.exe (PID: 3228)
- CheckSDK.exe (PID: 2632)
Application was dropped or rewritten from another process
- CheckSDK.exe (PID: 3524)
- CheckSDK.exe (PID: 2532)
- CheckSDK.exe (PID: 3228)
- CheckSDK.exe (PID: 2632)
- CheckSDK.exe (PID: 2620)
- CheckSDK.exe (PID: 3976)
SUSPICIOUS
Executable content was dropped or overwritten
- Run_RefreshPullSDK.exe (PID: 3664)
- CheckSDK.exe (PID: 3976)
- Run_RefreshPullSDK.exe (PID: 796)
- CheckSDK.exe (PID: 3228)
- Run_RefreshPullSDK.exe (PID: 3392)
Creates files in the Windows directory
- CheckSDK.exe (PID: 3976)
INFO
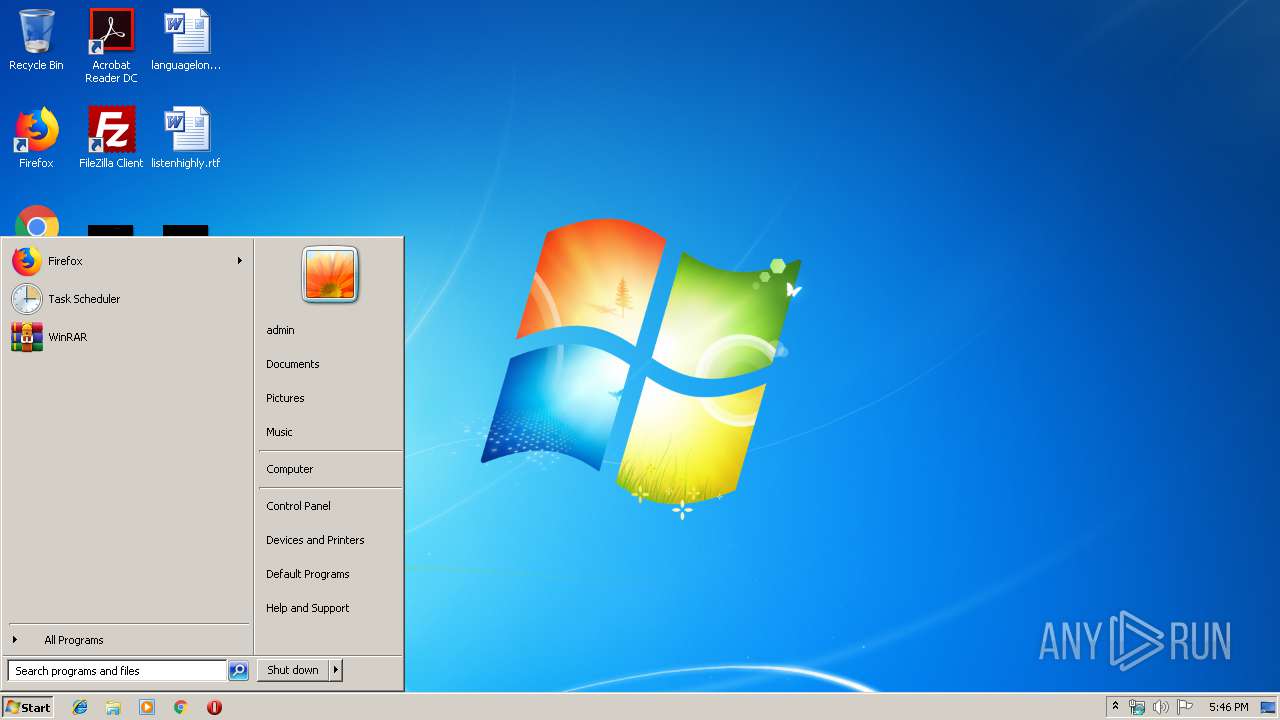
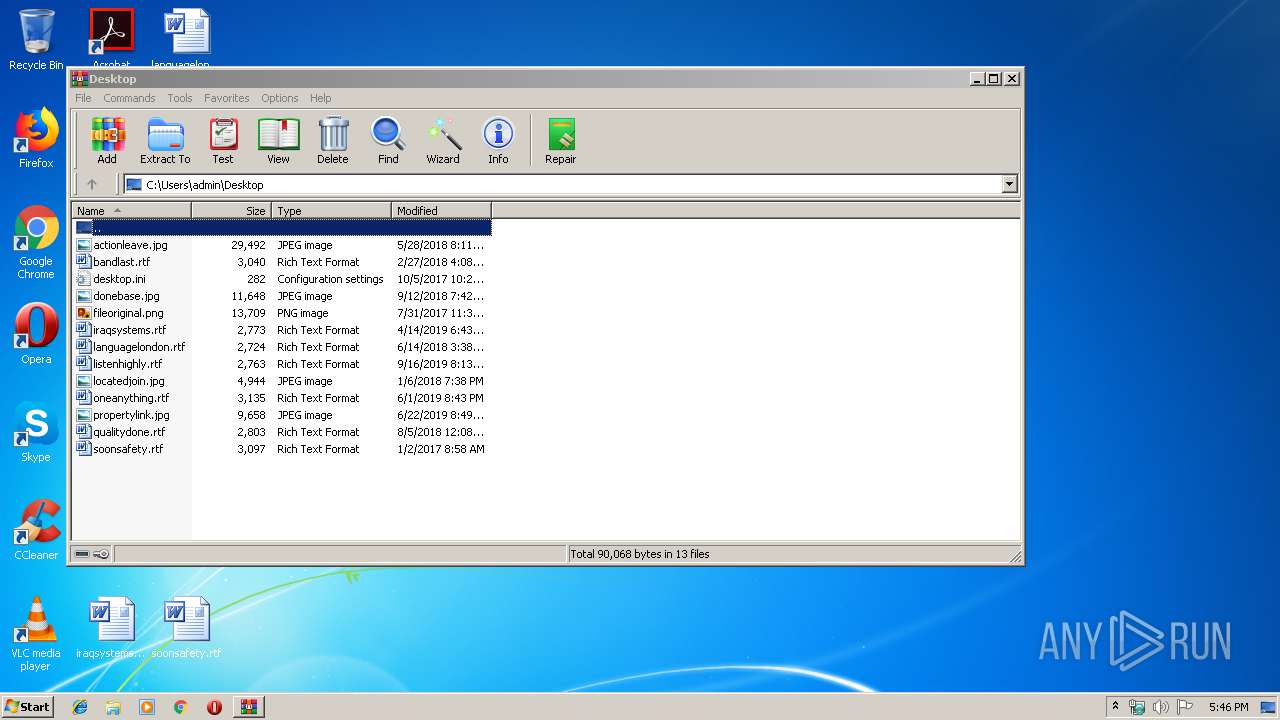
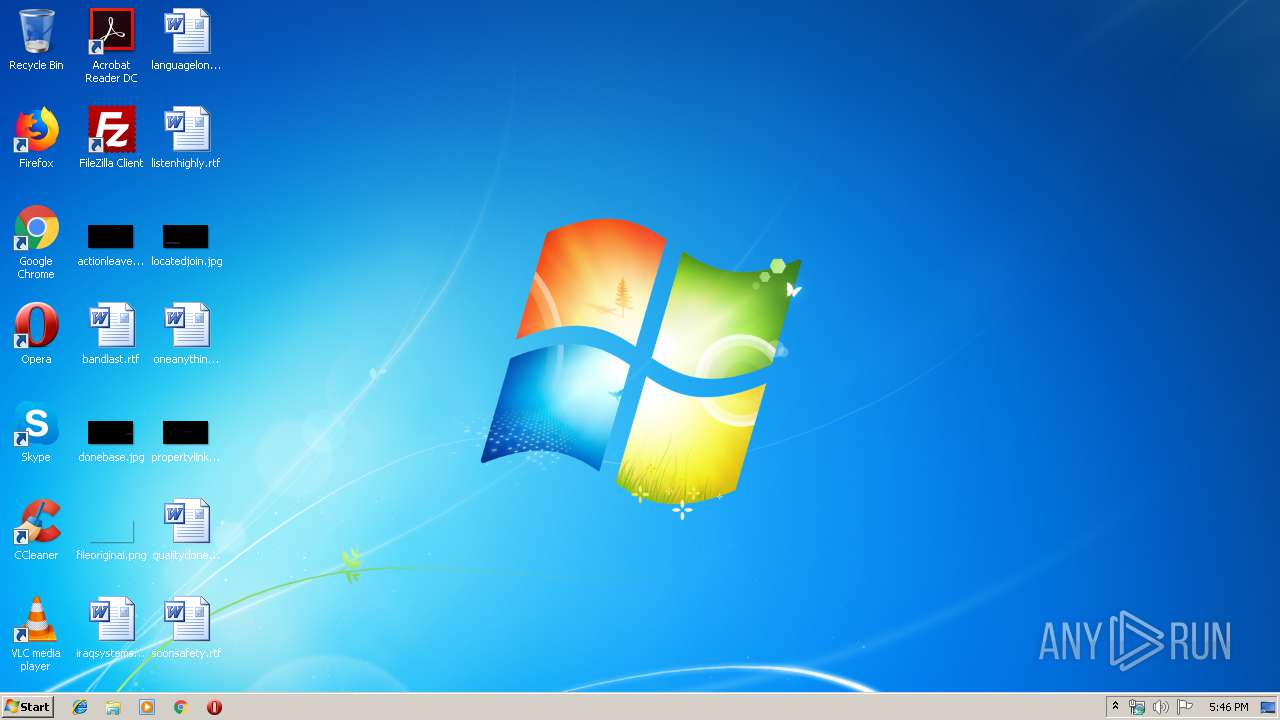
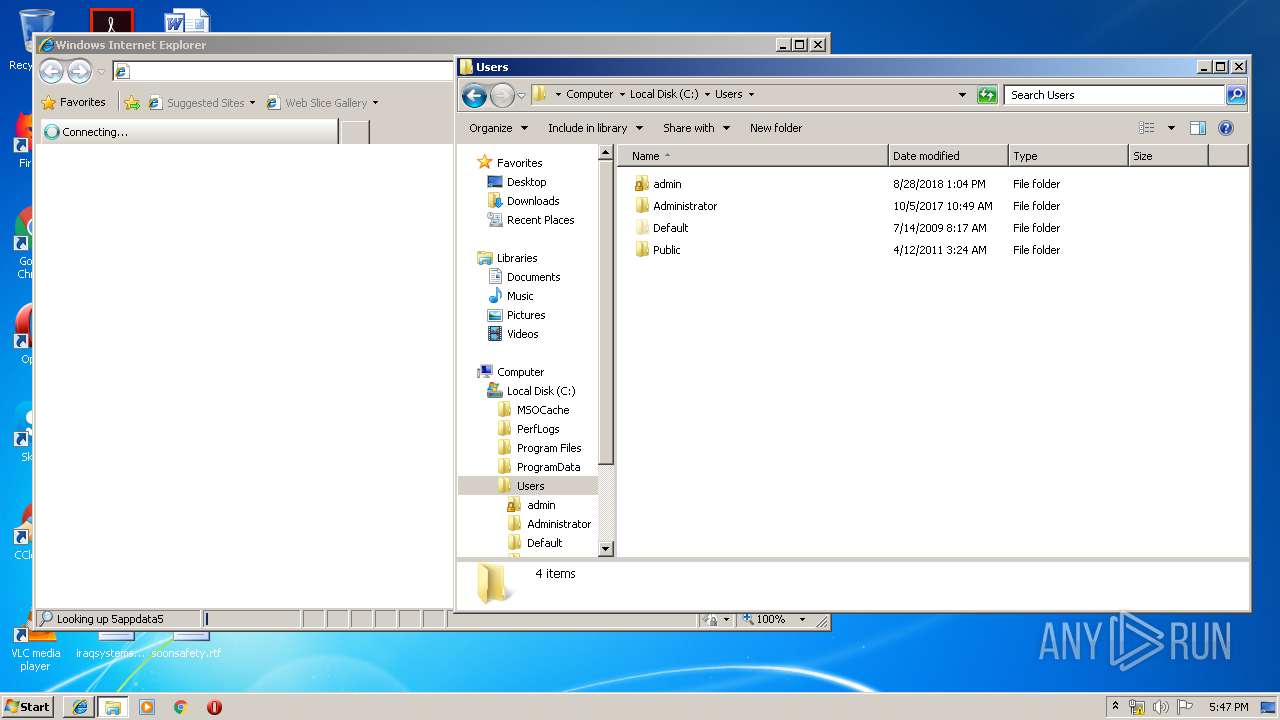
Manual execution by user
- chrome.exe (PID: 2588)
- chrome.exe (PID: 2172)
- WinRAR.exe (PID: 3704)
- explorer.exe (PID: 3264)
- iexplore.exe (PID: 3504)
- Run_RefreshPullSDK.exe (PID: 796)
- Run_RefreshPullSDK.exe (PID: 3392)
- rundll32.exe (PID: 2296)
Reads the hosts file
- chrome.exe (PID: 2932)
- chrome.exe (PID: 2172)
- chrome.exe (PID: 2588)
Application launched itself
- chrome.exe (PID: 2172)
- chrome.exe (PID: 2588)
Reads Internet Cache Settings
- iexplore.exe (PID: 2264)
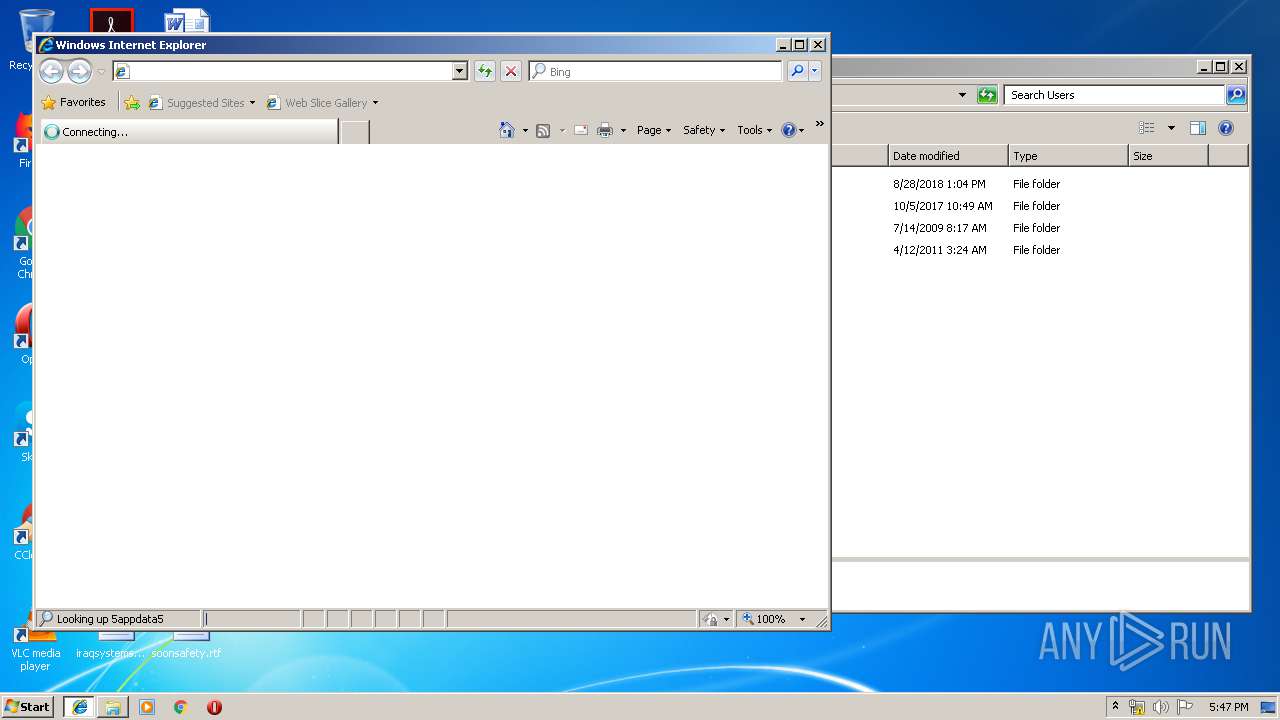
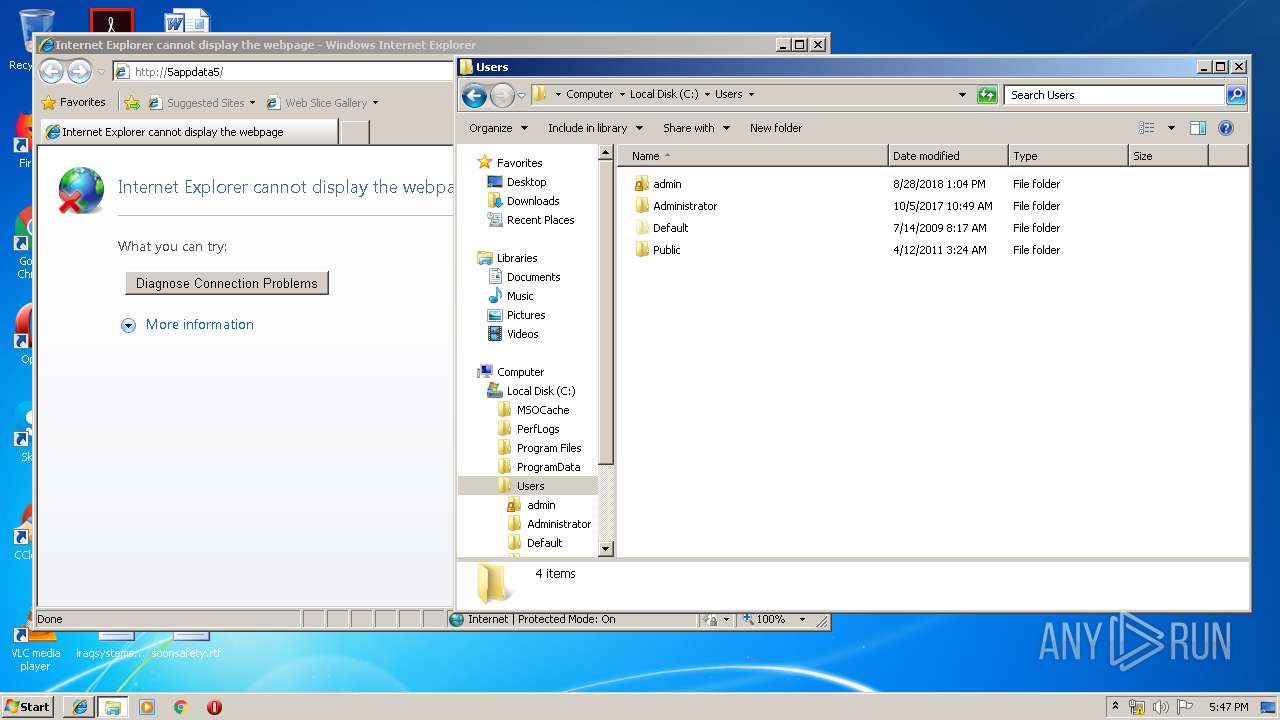
Reads internet explorer settings
- iexplore.exe (PID: 2264)
Changes internet zones settings
- iexplore.exe (PID: 3504)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:08:14 21:15:49+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 188416 |
| InitializedDataSize: | 101376 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1cab5 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 14-Aug-2016 19:15:49 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 14-Aug-2016 19:15:49 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0002DFE8 | 0x0002E000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.71025 |
.rdata | 0x0002F000 | 0x000099D0 | 0x00009A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.15287 |
.data | 0x00039000 | 0x0001F8B8 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.29547 |
.gfids | 0x00059000 | 0x000000F0 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.12367 |
.rsrc | 0x0005A000 | 0x0000C2C8 | 0x0000C400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.05703 |
.reloc | 0x00067000 | 0x00001F8C | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.62986 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.25329 | 1875 | Latin 1 / Western European | Chinese - PRC | RT_MANIFEST |
2 | 6.22742 | 2216 | Latin 1 / Western European | Process Default Language | RT_ICON |
3 | 6.13537 | 1736 | Latin 1 / Western European | Process Default Language | RT_ICON |
4 | 5.70333 | 1384 | Latin 1 / Western European | Process Default Language | RT_ICON |
5 | 5.74548 | 7336 | Latin 1 / Western European | Process Default Language | RT_ICON |
6 | 5.94515 | 3240 | Latin 1 / Western European | Process Default Language | RT_ICON |
7 | 5.24197 | 182 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
8 | 5.27357 | 214 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
9 | 5.38938 | 202 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
10 | 5.11103 | 116 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
Imports
COMCTL32.dll (delay-loaded) |
KERNEL32.dll |
Total processes
86
Monitored processes
39
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 504 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,6612781507074151603,8406826872187279202,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5841390879815155166 --mojo-platform-channel-handle=3340 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 796 | "C:\Users\admin\AppData\Local\Temp\Run_RefreshPullSDK.exe" | C:\Users\admin\AppData\Local\Temp\Run_RefreshPullSDK.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2072 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2220 --on-initialized-event-handle=312 --parent-handle=316 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2084 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,6612781507074151603,8406826872187279202,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8352563499673058144 --mojo-platform-channel-handle=3932 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2132 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,6612781507074151603,8406826872187279202,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=18310511213223511972 --mojo-platform-channel-handle=3208 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2172 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 3221225547 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2264 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3504 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
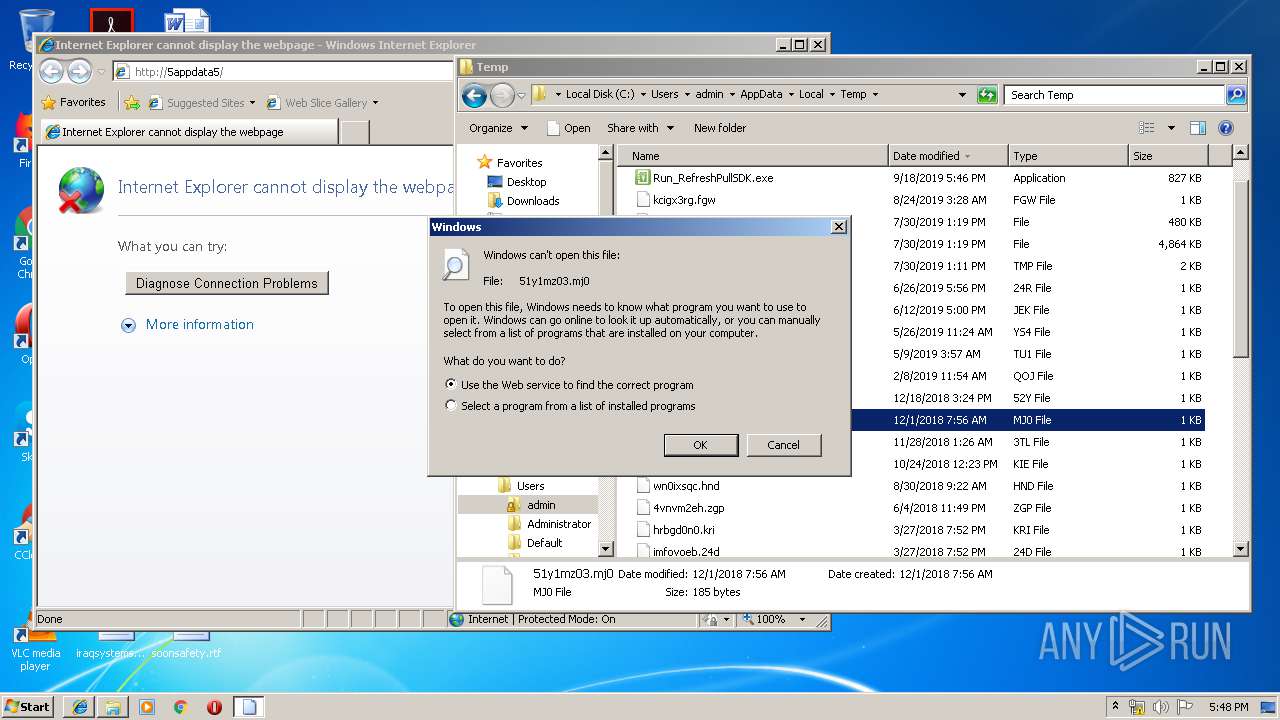
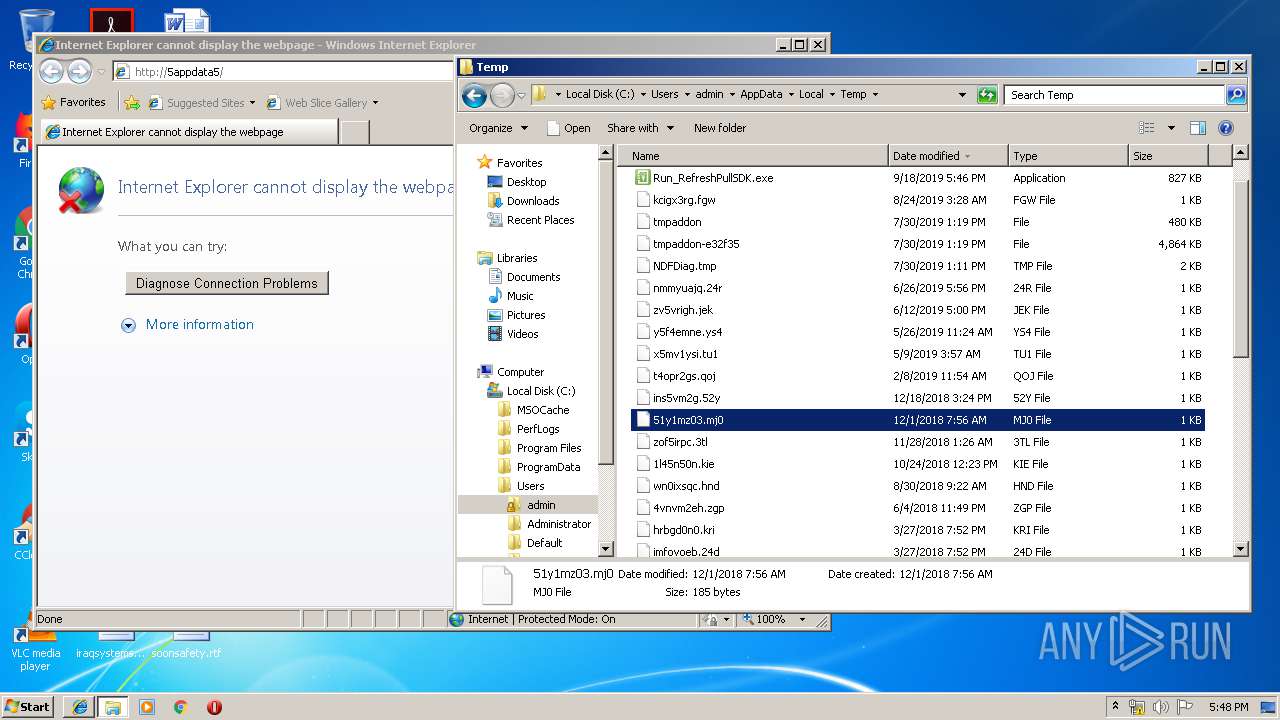
| 2296 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\AppData\Local\Temp\51y1mz03.mj0 | C:\Windows\system32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2424 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,6612781507074151603,8406826872187279202,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11496166024182782960 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2464 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2468 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,6612781507074151603,8406826872187279202,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6738500711717016486 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2480 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 006
Read events
1 867
Write events
133
Delete events
6
Modification events
| (PID) Process: | (3664) Run_RefreshPullSDK.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3664) Run_RefreshPullSDK.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2172) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2172) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2172) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2172) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2172) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2172) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2588) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2588) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
Executable files
33
Suspicious files
27
Text files
200
Unknown types
8
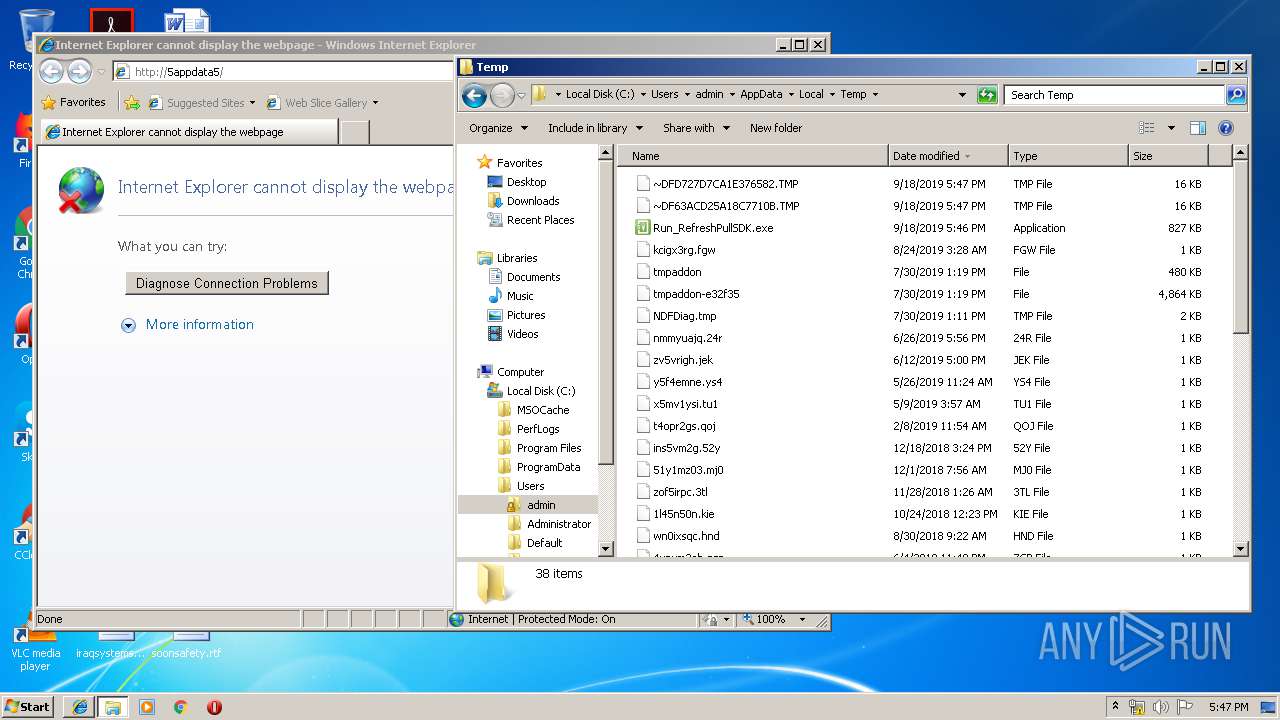
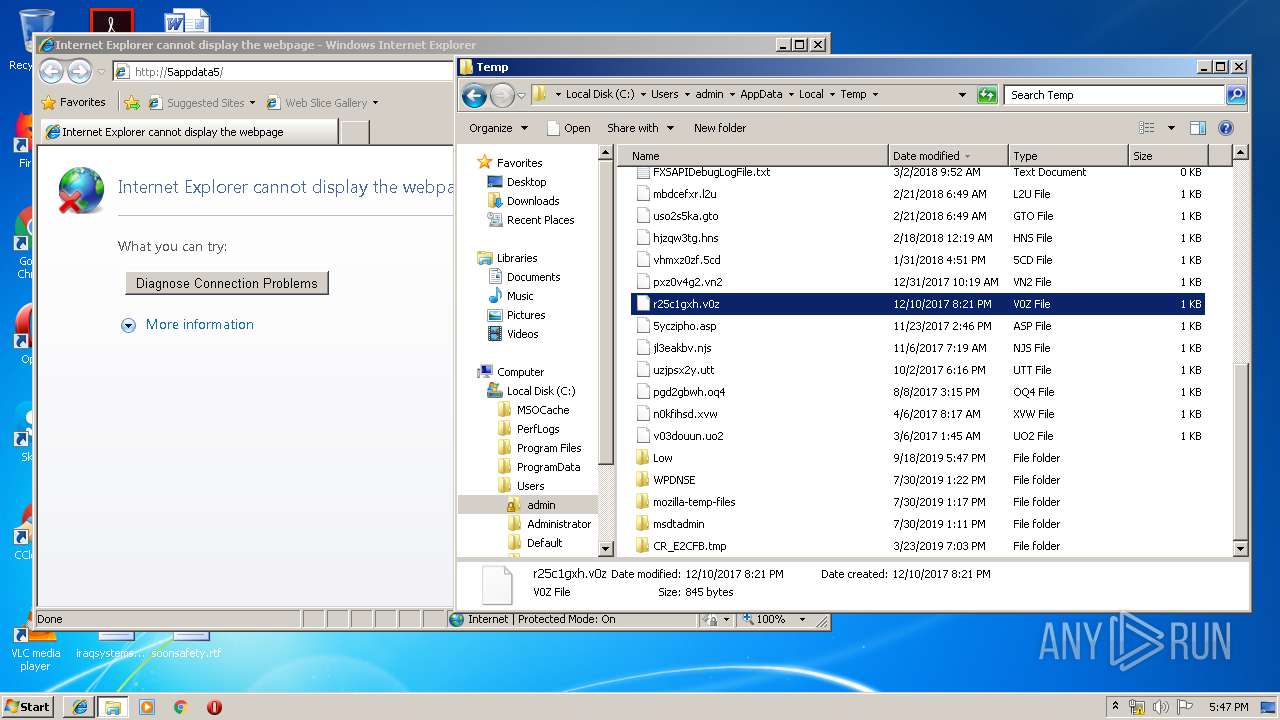
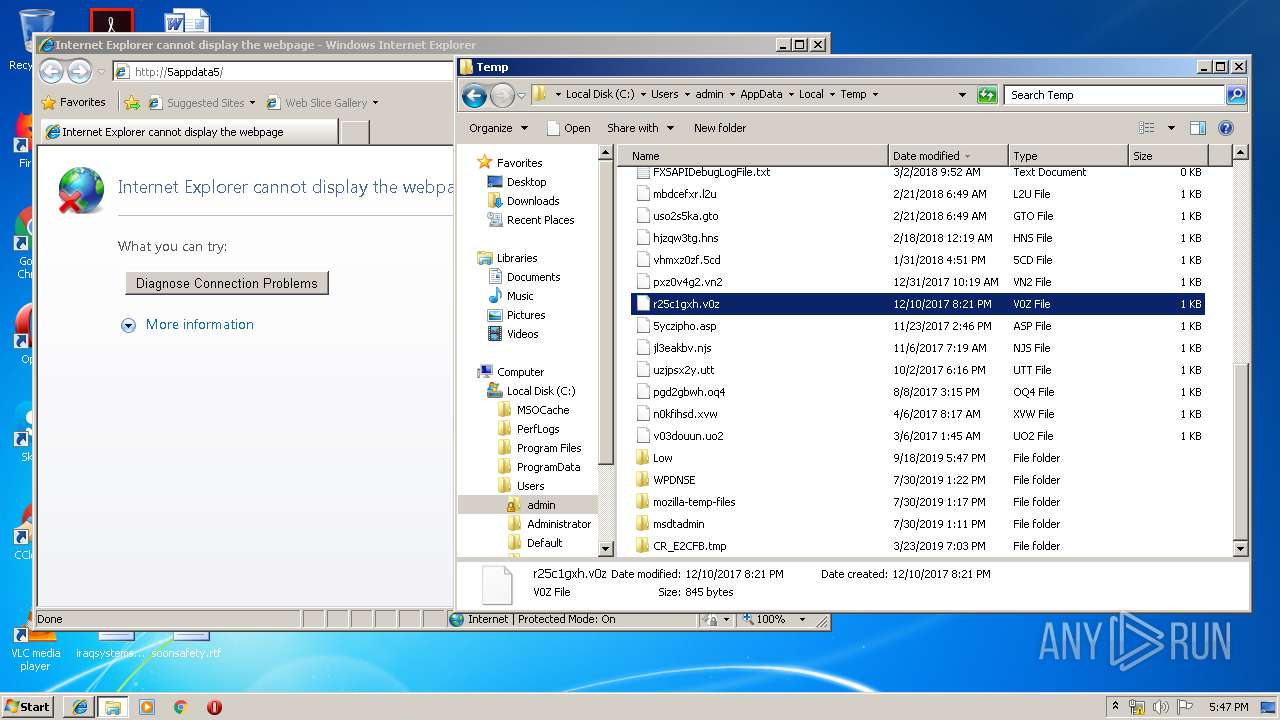
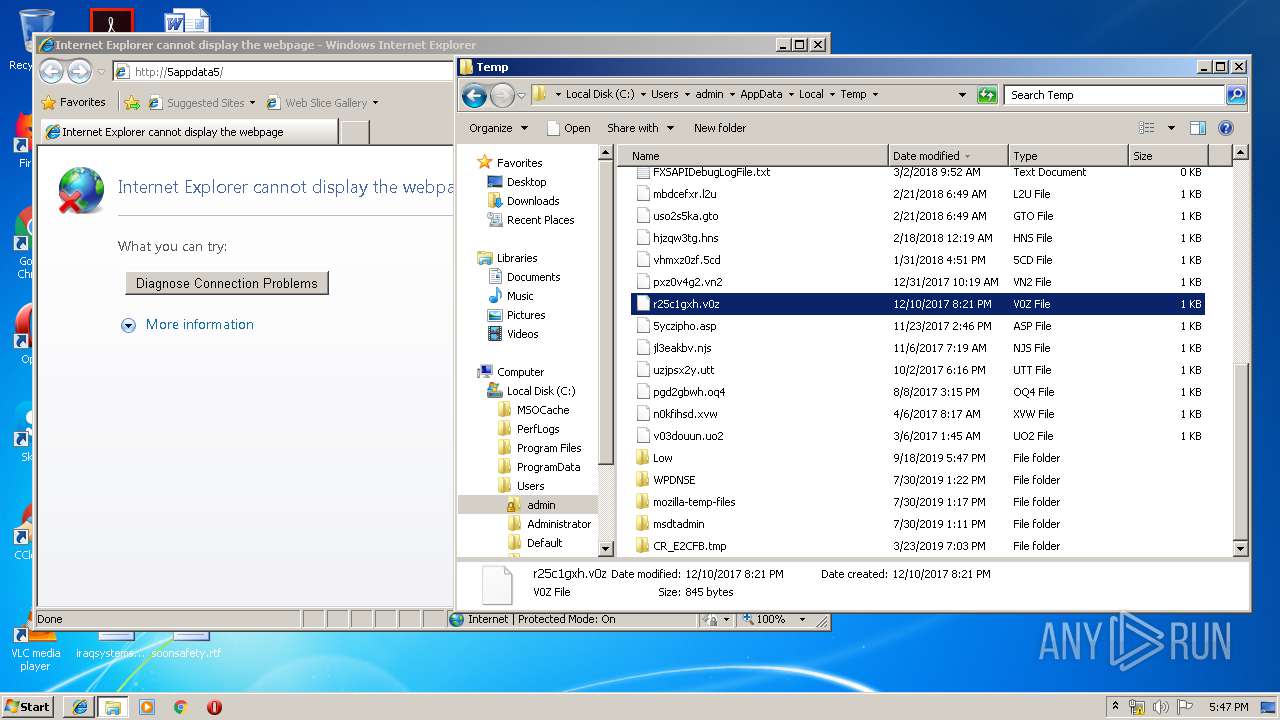
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3664 | Run_RefreshPullSDK.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\CheckSDK.exe | executable | |
MD5:— | SHA256:— | |||
| 3664 | Run_RefreshPullSDK.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\ALLSDK\plcommpro.dll | executable | |
MD5:— | SHA256:— | |||
| 3664 | Run_RefreshPullSDK.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\ALLSDK\plrscagent.dll | executable | |
MD5:— | SHA256:— | |||
| 3664 | Run_RefreshPullSDK.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\ALLSDK\plcomms.dll | executable | |
MD5:— | SHA256:— | |||
| 3664 | Run_RefreshPullSDK.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\ALLSDK\plrscomm.dll | executable | |
MD5:— | SHA256:— | |||
| 3664 | Run_RefreshPullSDK.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\ALLSDK\pltcpcomm.dll | executable | |
MD5:— | SHA256:— | |||
| 3664 | Run_RefreshPullSDK.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\ALLSDK\plusbcomm.dll | executable | |
MD5:— | SHA256:— | |||
| 3976 | CheckSDK.exe | C:\Windows\System32\plcommpro.dll | executable | |
MD5:— | SHA256:— | |||
| 3976 | CheckSDK.exe | C:\Windows\System32\plrscomm.dll | executable | |
MD5:— | SHA256:— | |||
| 3976 | CheckSDK.exe | C:\Windows\System32\pltcpcomm.dll | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
13
DNS requests
13
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2932 | chrome.exe | GET | 302 | 172.217.22.78:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 515 b | whitelisted |
3504 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
2932 | chrome.exe | GET | 200 | 172.217.133.135:80 | http://r2---sn-hpa7znsd.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=185.128.27.133&mm=28&mn=sn-hpa7znsd&ms=nvh&mt=1568825065&mv=m&mvi=1&pl=24&shardbypass=yes | US | crx | 862 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2932 | chrome.exe | 172.217.18.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2932 | chrome.exe | 172.217.23.141:443 | accounts.google.com | Google Inc. | US | whitelisted |
2932 | chrome.exe | 216.58.205.238:443 | clients2.google.com | Google Inc. | US | whitelisted |
2932 | chrome.exe | 172.217.16.195:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2932 | chrome.exe | 172.217.21.225:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
2932 | chrome.exe | 172.217.22.78:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
2932 | chrome.exe | 172.217.133.135:80 | r2---sn-hpa7znsd.gvt1.com | Google Inc. | US | whitelisted |
3504 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2932 | chrome.exe | 216.58.207.35:443 | www.google.com.ua | Google Inc. | US | whitelisted |
2932 | chrome.exe | 172.217.16.142:443 | apis.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
clients2.google.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
apis.google.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
ogs.google.com |
| whitelisted |