analyze malware
- Huge database of samples and IOCs
- Custom VM setup
- Unlimited submissions
- Interactive approach
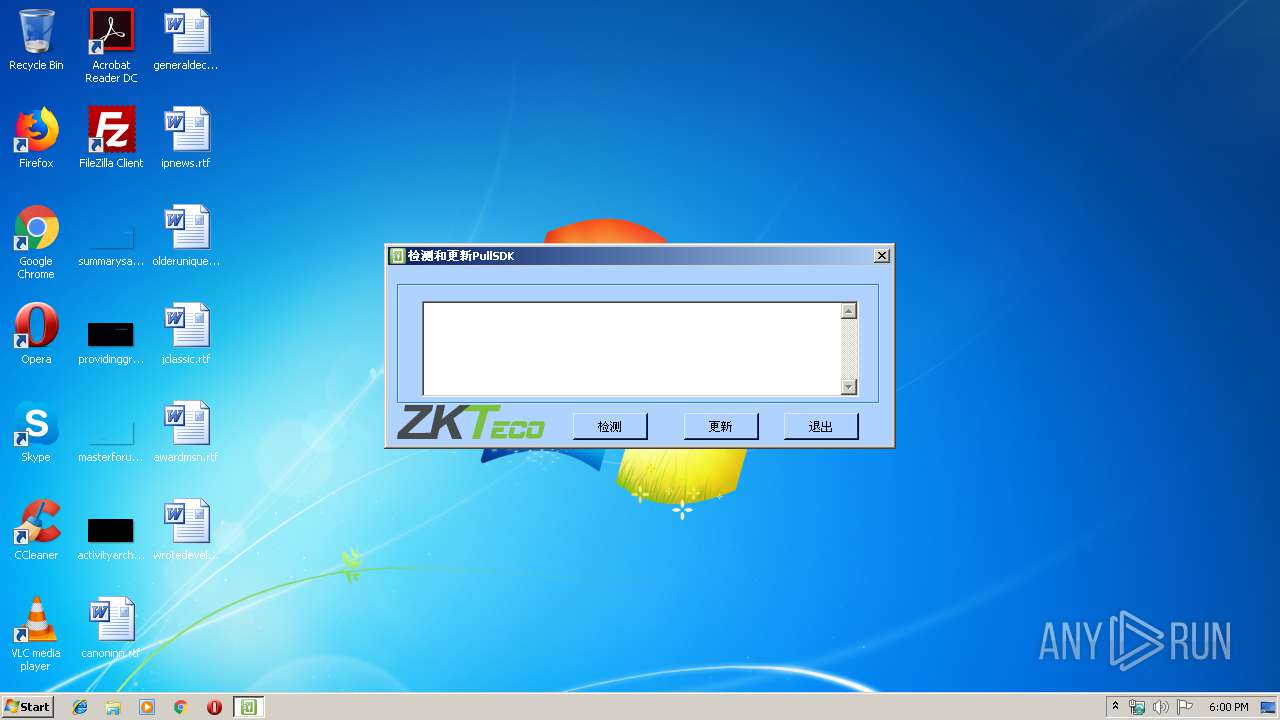
| File name: | Run_RefreshPullSDK.exe |
| Full analysis: | https://app.any.run/tasks/4d2842c4-8043-4786-b101-f8bf53bd2932 |
| Verdict: | Malicious activity |
| Analysis date: | September 18, 2019, 16:59:47 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 682AA868CFE32EB014978F504A4B7D9B |
| SHA1: | 585D4566DFFF9A23C52ED27A35209359806A1FFD |
| SHA256: | 86F8685E944CA441F95C1B93CAFD2822C48DE2544FC4604776B9273EE76DCEA3 |
| SSDEEP: | 24576:lJlh9bDpUnPiMMgKjhfsoK/67ZI2bg9mMN8:lJgKMlEhErsZI289tN8 |
MALICIOUS
Application was dropped or rewritten from another process
- CheckSDK.exe (PID: 3440)
- CheckSDK.exe (PID: 2888)
SUSPICIOUS
Executable content was dropped or overwritten
- Run_RefreshPullSDK.exe (PID: 3000)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 5.1 |
| ImageVersion: | - |
| OSVersion: | 5.1 |
| EntryPoint: | 0x1cab5 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 101376 |
| CodeSize: | 188416 |
| LinkerVersion: | 14 |
| PEType: | PE32 |
| TimeStamp: | 2016:08:14 21:15:49+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 14-Aug-2016 19:15:49 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 14-Aug-2016 19:15:49 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0002DFE8 | 0x0002E000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.71025 |
.rdata | 0x0002F000 | 0x000099D0 | 0x00009A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.15287 |
.data | 0x00039000 | 0x0001F8B8 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.29547 |
.gfids | 0x00059000 | 0x000000F0 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.12367 |
.rsrc | 0x0005A000 | 0x0000C2C8 | 0x0000C400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.05703 |
.reloc | 0x00067000 | 0x00001F8C | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.62986 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.25329 | 1875 | Latin 1 / Western European | Chinese - PRC | RT_MANIFEST |
2 | 6.22742 | 2216 | Latin 1 / Western European | Process Default Language | RT_ICON |
3 | 6.13537 | 1736 | Latin 1 / Western European | Process Default Language | RT_ICON |
4 | 5.70333 | 1384 | Latin 1 / Western European | Process Default Language | RT_ICON |
5 | 5.74548 | 7336 | Latin 1 / Western European | Process Default Language | RT_ICON |
6 | 5.94515 | 3240 | Latin 1 / Western European | Process Default Language | RT_ICON |
7 | 5.24197 | 182 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
8 | 5.27357 | 214 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
9 | 5.38938 | 202 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
10 | 5.11103 | 116 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
Imports
COMCTL32.dll (delay-loaded) |
KERNEL32.dll |
Total processes
36
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 3000 | "C:\Users\admin\AppData\Local\Temp\Run_RefreshPullSDK.exe" | C:\Users\admin\AppData\Local\Temp\Run_RefreshPullSDK.exe | explorer.exe | |
User: admin Integrity Level: MEDIUM | ||||
| 2888 | "C:\Users\admin\AppData\Local\Temp\RarSFX0\CheckSDK.exe" | C:\Users\admin\AppData\Local\Temp\RarSFX0\CheckSDK.exe | — | Run_RefreshPullSDK.exe |
User: admin Company: Microsoft Integrity Level: MEDIUM Description: CheckSDK Exit code: 3221226540 Version: 1.0.0.0 | ||||
| 3440 | "C:\Users\admin\AppData\Local\Temp\RarSFX0\CheckSDK.exe" | C:\Users\admin\AppData\Local\Temp\RarSFX0\CheckSDK.exe | Run_RefreshPullSDK.exe | |
User: admin Company: Microsoft Integrity Level: HIGH Description: CheckSDK Version: 1.0.0.0 | ||||
Total events
353
Read events
349
Write events
4
Delete events
0
Modification events
| (PID) Process: | (3000) Run_RefreshPullSDK.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3000) Run_RefreshPullSDK.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
7
Suspicious files
0
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3000 | Run_RefreshPullSDK.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\ALLSDK\pltcpcomm.dll | executable | |
MD5:3BC93002144302592E3E473A57B0B8B8 | SHA256:09920468395F37D76A3B87BCF3A18FF2D21D48AD07612A8697C77C3B39FD6D26 | |||
| 3000 | Run_RefreshPullSDK.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\CheckSDK.exe | executable | |
MD5:95CF4A350F543F9408B50AD3FDF57A74 | SHA256:28F1936ECE7ED32A3C2738CE324E9193244141B5CD20093122FE89982A0486FA | |||
| 3000 | Run_RefreshPullSDK.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\ALLSDK\plcomms.dll | executable | |
MD5:B4D158B128B49384987BC69AAC004D4A | SHA256:09DBDBC79715B6E216C6B6F1D38522BF6FEB2A45B22EBFFAFEBB29159ADC9D38 | |||
| 3000 | Run_RefreshPullSDK.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\ALLSDK\plrscagent.dll | executable | |
MD5:EEA5A1C1908834177C5C2948EA319F64 | SHA256:D9D2D377B99254D4BD9603FCDD1AB5A95C670044B20F628CC3469970E506BEBC | |||
| 3000 | Run_RefreshPullSDK.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\ALLSDK\plusbcomm.dll | executable | |
MD5:62B12849E2B8FB1DC833B319C922F501 | SHA256:50EA84B6E24660DF1F68B37B5F57C2A959CF0099576BF0166875FC415301578A | |||
| 3000 | Run_RefreshPullSDK.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\ALLSDK\Register_SDK.bat | text | |
MD5:A88EE8EB005901DAA2F907A657D1BA66 | SHA256:DBFBCE26EA395DD3176A88A9DE5362E71FB511E2B3364D5F63D1184499A1D2D6 | |||
| 3000 | Run_RefreshPullSDK.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\ALLSDK\plcommpro.dll | executable | |
MD5:30F4554793148CBCE4DCC3D0749B1195 | SHA256:D0739A97DDBE99152851EF859E15CA375E14BD2DB0C00F471935FF3BDBCC48DB | |||
| 3000 | Run_RefreshPullSDK.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\ALLSDK\plrscomm.dll | executable | |
MD5:6272D43EB151BACFC1000D1E3CCA4C98 | SHA256:666E2B388BCF36C6520C86BCFA44221891927606612B0337650EDB406EA3BD08 | |||
| 3000 | Run_RefreshPullSDK.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\ALLSDK\Delete_SDK.bat | text | |
MD5:5BC74F099A7ADB39DB5C75E4E937E98F | SHA256:9CE9FF3AE668DF89CF3CAA7142964EAB6D28DAF7E21F936DD7E8836DE9D04363 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report