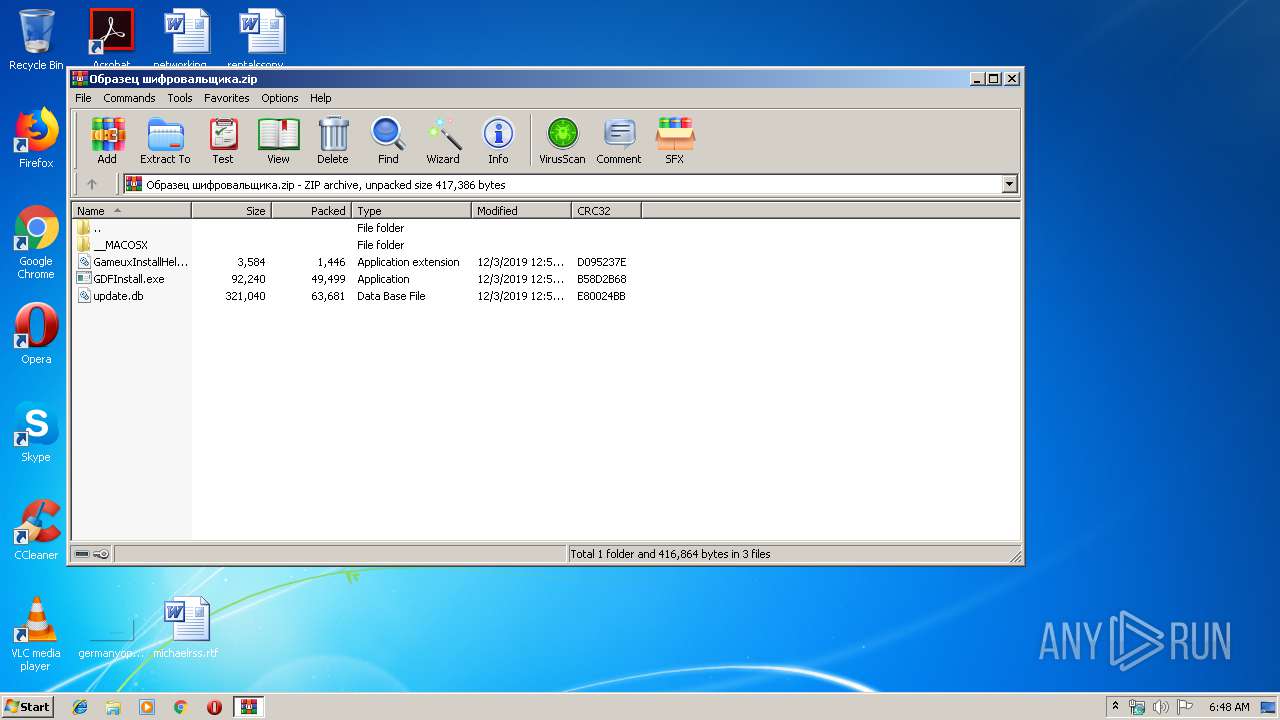
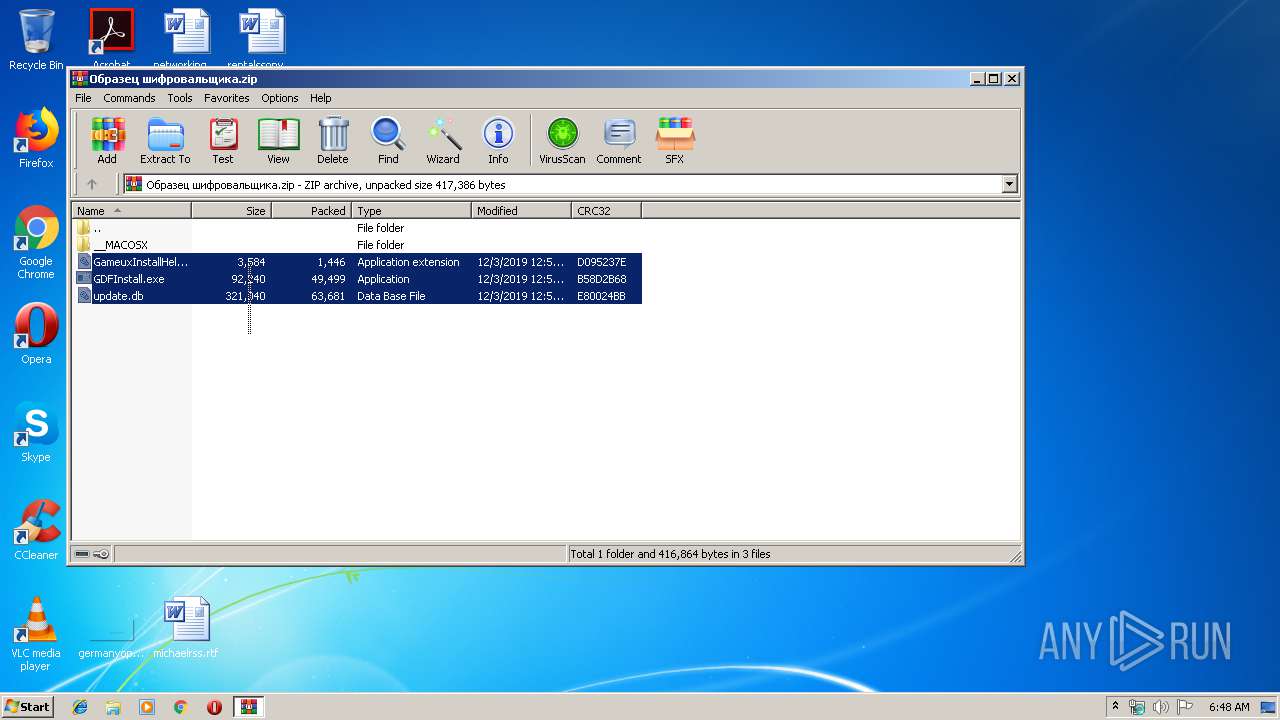
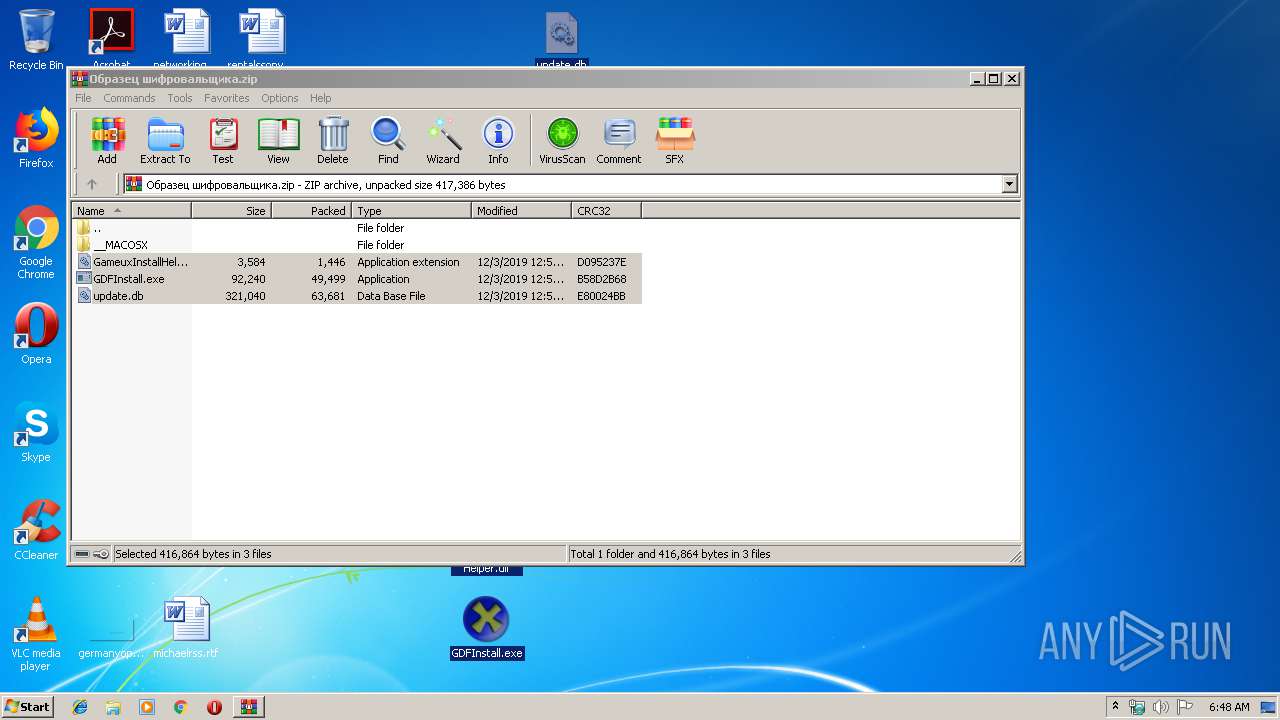
| File name: | Образец шифровальщика.zip |
| Full analysis: | https://app.any.run/tasks/f6dfa857-ca74-4162-a83a-135d47ee5525 |
| Verdict: | Malicious activity |
| Analysis date: | December 04, 2019, 06:48:02 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
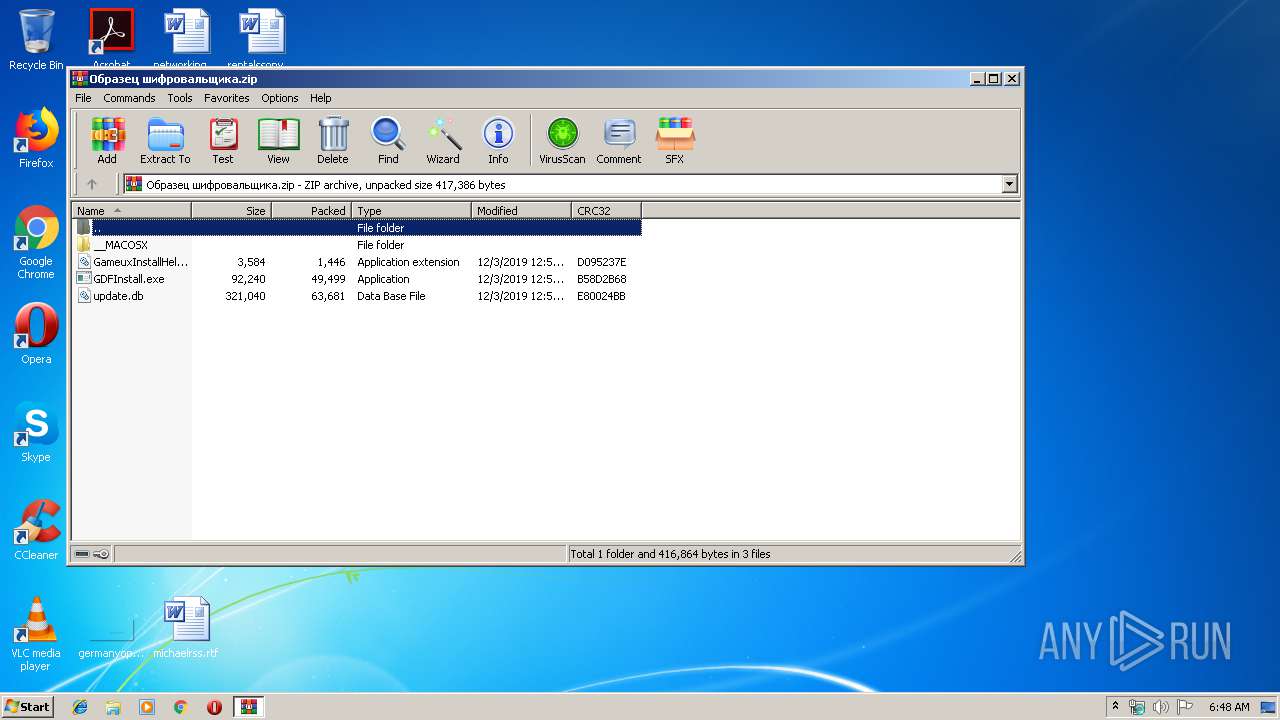
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | A74615DE249B4609F51B826A34DC9492 |
| SHA1: | A7FCE32A4A62808D37EC3C80970F08CC3559F03D |
| SHA256: | 86F69D19F94AD5A44393F0384BDCF3894F1C26609F2EB29FB23604DC820C89B7 |
| SSDEEP: | 3072:hAC5eieOFyGeeRzzKzb5gXLGbagfHsp81BxBkGLe7KS:hAWVeWNeyzeGXrgfs2Bx7Lu |
MALICIOUS
Loads dropped or rewritten executable
- GDFInstall.exe (PID: 2352)
- SearchProtocolHost.exe (PID: 3476)
- GDFInstall.exe (PID: 716)
Application was dropped or rewritten from another process
- GDFInstall.exe (PID: 2352)
- GDFInstall.exe (PID: 716)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2248)
INFO
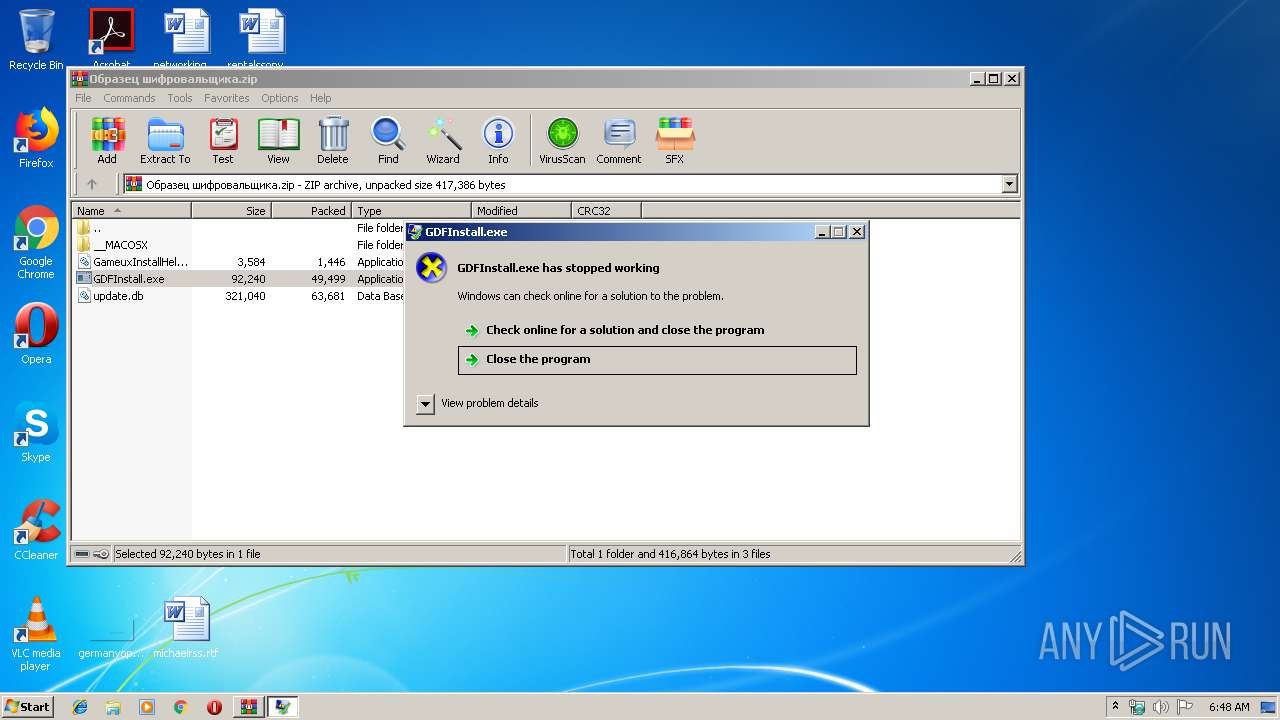
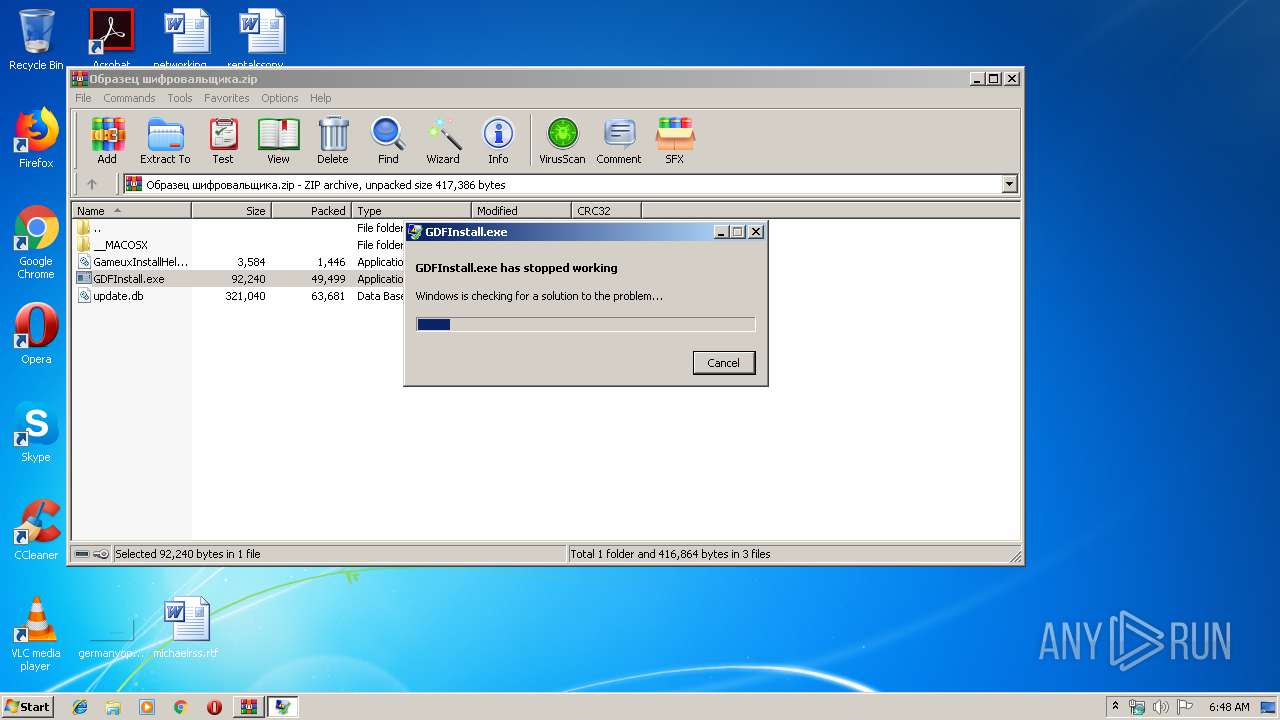
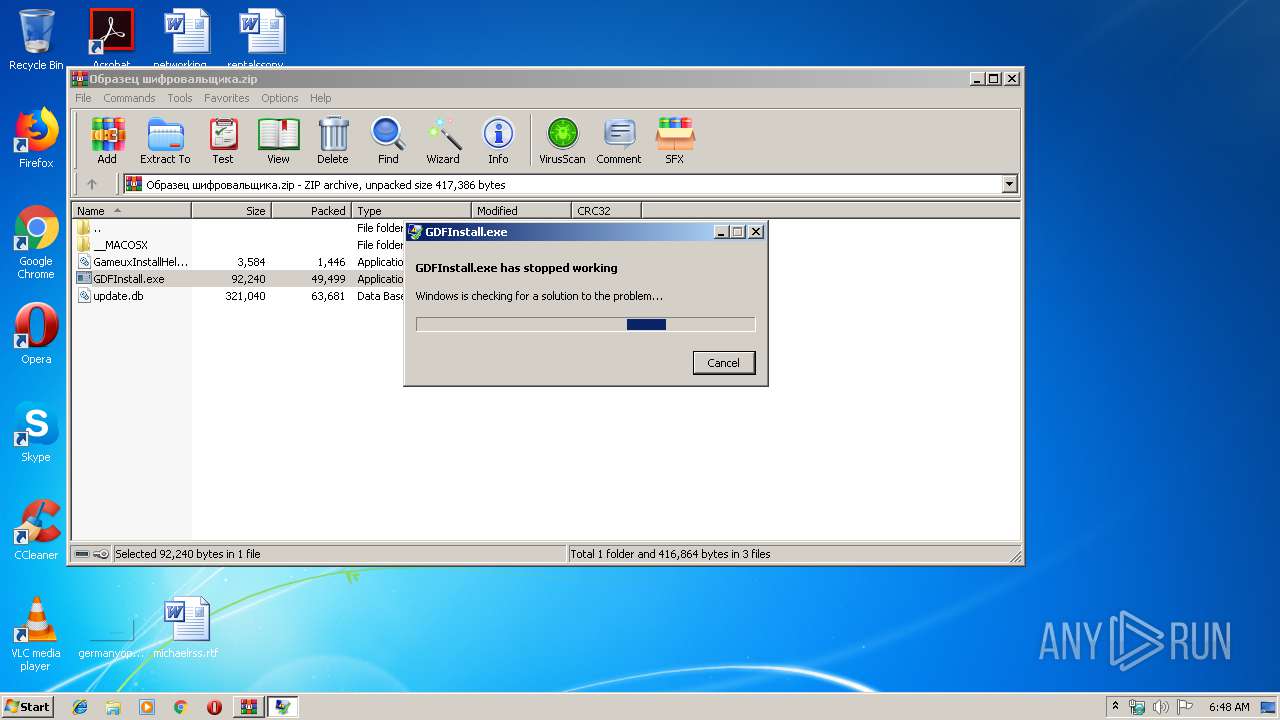
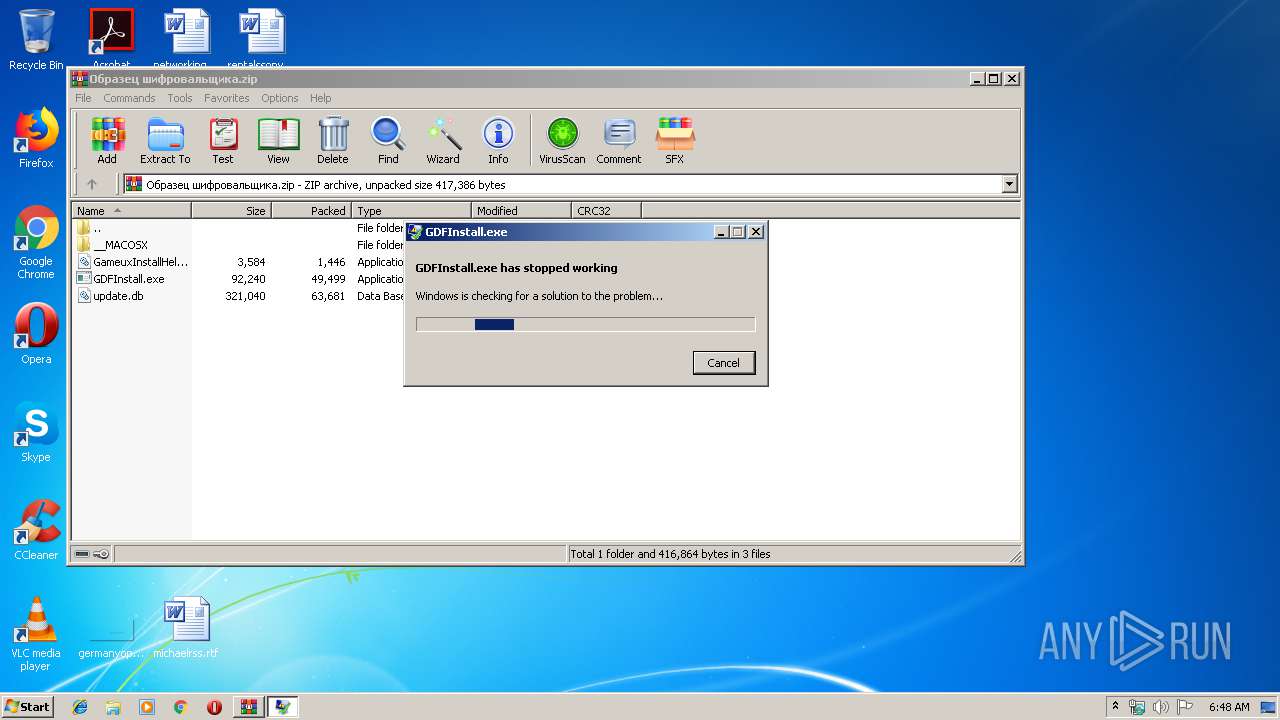
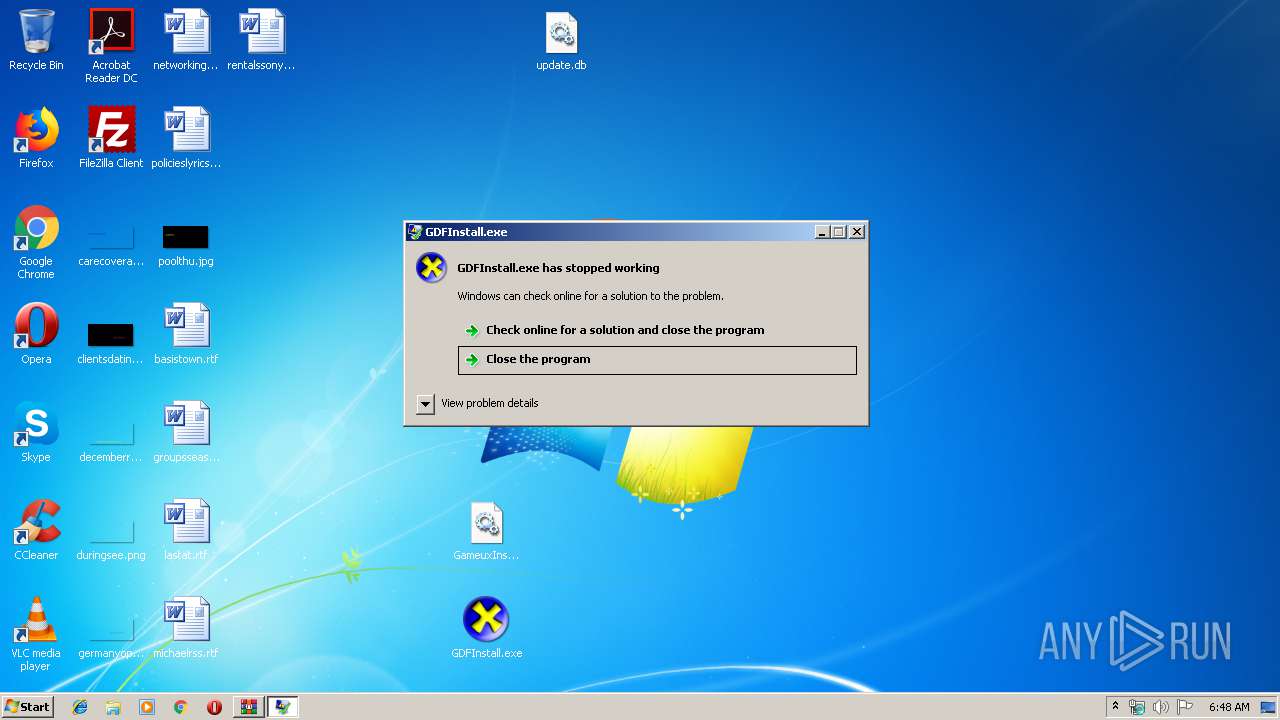
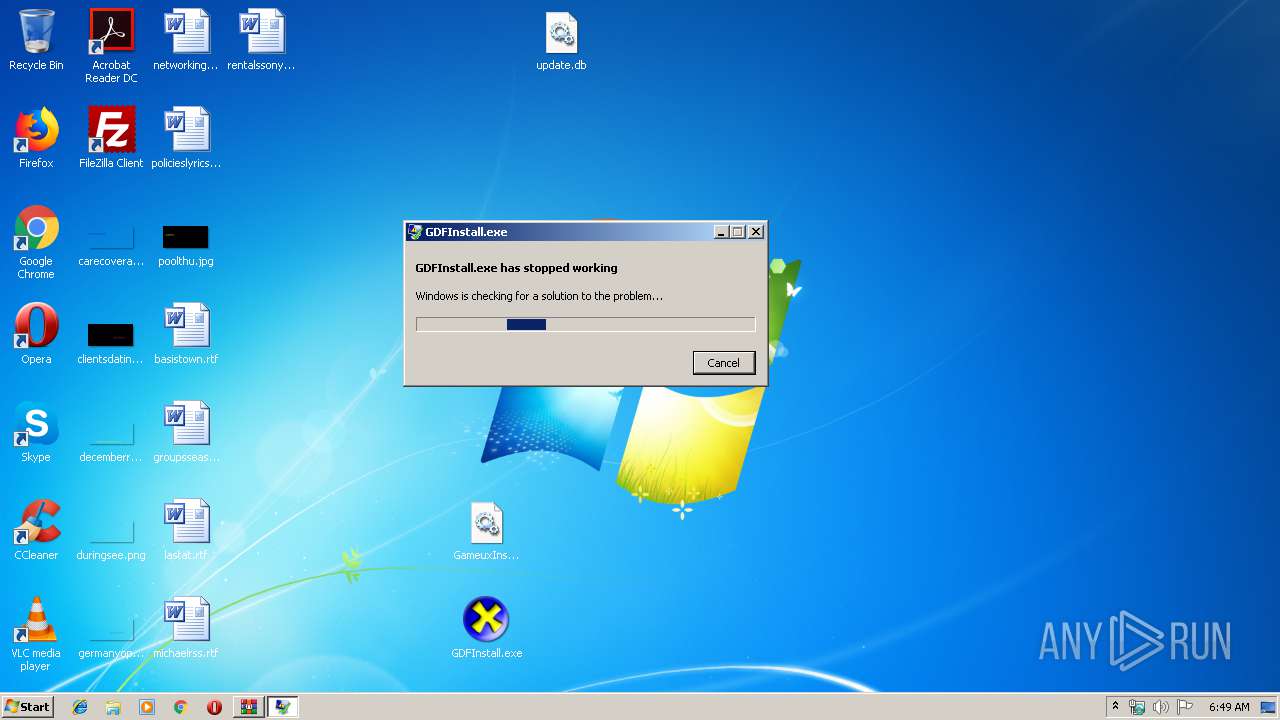
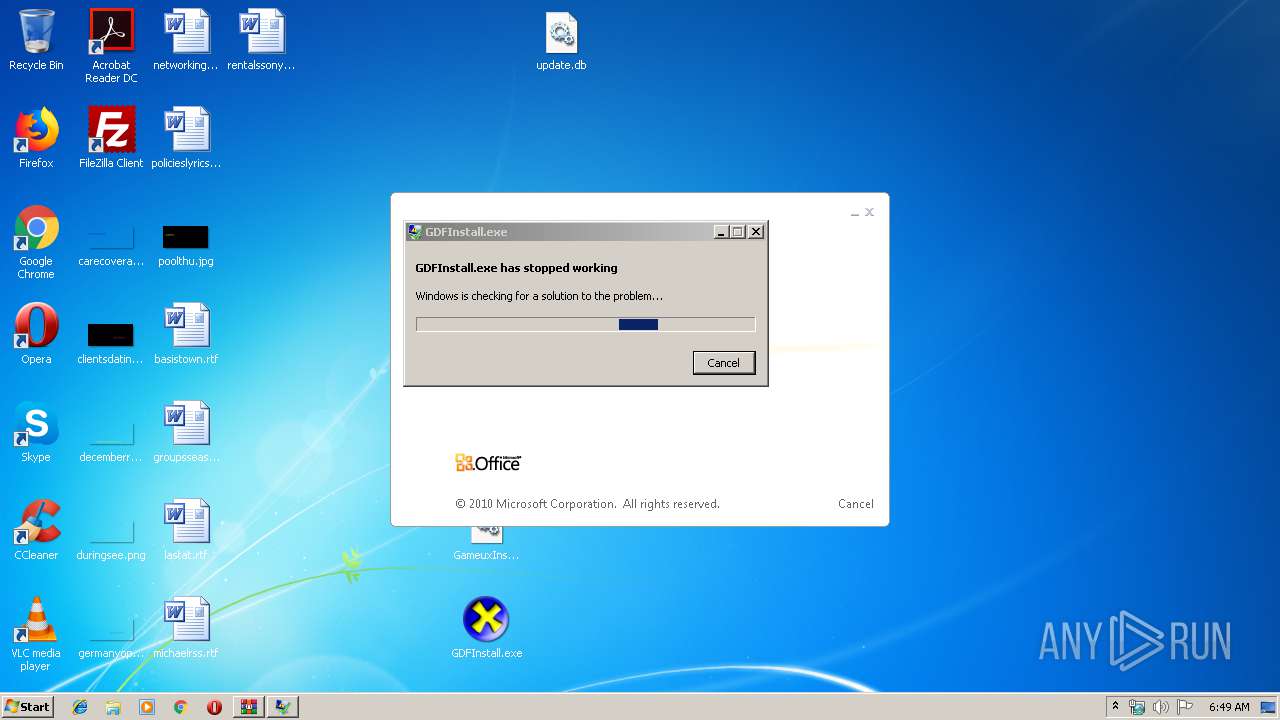
Application was crashed
- GDFInstall.exe (PID: 2352)
- GDFInstall.exe (PID: 716)
Manual execution by user
- GDFInstall.exe (PID: 716)
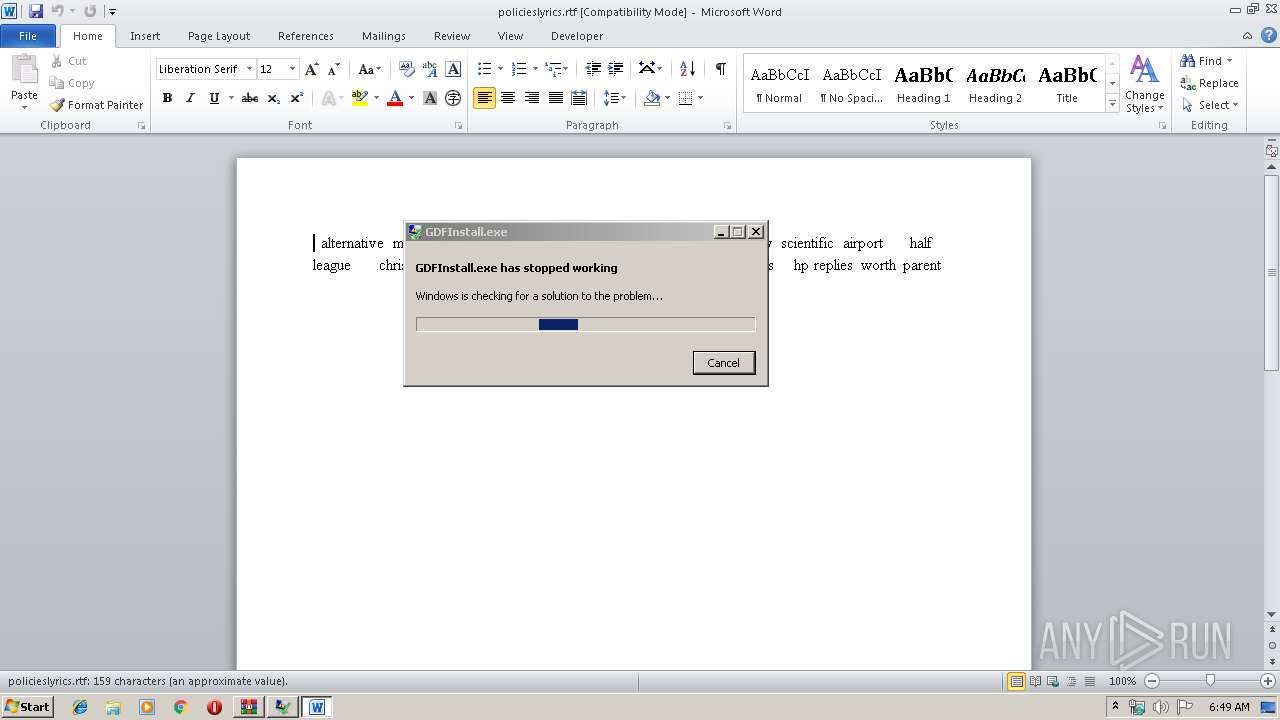
- WINWORD.EXE (PID: 3584)
Creates files in the user directory
- WINWORD.EXE (PID: 3584)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3584)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xpi | | | Mozilla Firefox browser extension (66.6) |
|---|---|---|
| .zip | | | ZIP compressed archive (33.3) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0008 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:12:03 15:51:16 |
| ZipCRC: | 0xe80024bb |
| ZipCompressedSize: | 63681 |
| ZipUncompressedSize: | 321040 |
| ZipFileName: | update.db |
Total processes
41
Monitored processes
7
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 716 | "C:\Users\admin\Desktop\GDFInstall.exe" | C:\Users\admin\Desktop\GDFInstall.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2140 | dw20.exe -x -s 364 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\dw20.exe | GDFInstall.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Error Reporting Shim Exit code: 0 Version: 2.0.50727.4927 (NetFXspW7.050727-4900) Modules
| |||||||||||||||
| 2248 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Образец шифровальщика.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2352 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2248.10926\GDFInstall.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2248.10926\GDFInstall.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3762507597 Modules
| |||||||||||||||
| 3316 | dw20.exe -x -s 364 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\dw20.exe | GDFInstall.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Error Reporting Shim Exit code: 0 Version: 2.0.50727.4927 (NetFXspW7.050727-4900) Modules
| |||||||||||||||
| 3476 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe2_ Global\UsGthrCtrlFltPipeMssGthrPipe2 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3584 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\policieslyrics.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
1 491
Read events
1 164
Write events
183
Delete events
144
Modification events
| (PID) Process: | (2248) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2248) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2248) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2248) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Образец шифровальщика.zip | |||
| (PID) Process: | (2248) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2248) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2248) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2248) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2248) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2248) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
2
Suspicious files
2
Text files
4
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2248 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2248.13112\update.db | — | |
MD5:— | SHA256:— | |||
| 2248 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2248.13112\GDFInstall.exe | — | |
MD5:— | SHA256:— | |||
| 2248 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2248.13112\GameuxInstallHelper.dll | — | |
MD5:— | SHA256:— | |||
| 3584 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR6B91.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2248 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2248.10926\GameuxInstallHelper.dll | executable | |
MD5:— | SHA256:— | |||
| 2248 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2248.10926\__MACOSX\._update.db | ad | |
MD5:— | SHA256:— | |||
| 2248 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2248.10926\__MACOSX\._GDFInstall.exe | ad | |
MD5:— | SHA256:— | |||
| 3316 | dw20.exe | C:\Users\admin\AppData\Local\Temp\WERDBF3.tmp.WERInternalMetadata.xml | xml | |
MD5:— | SHA256:— | |||
| 3316 | dw20.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\WER\ReportArchive\AppCrash_gdfinstall.exe_deae338fd113dcfc22ba63f54d28ca97b0ce2575_0cce0d25\Report.wer | binary | |
MD5:— | SHA256:— | |||
| 2248 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2248.10926\__MACOSX\._GameuxInstallHelper.dll | ad | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
2
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3316 | dw20.exe | GET | — | 52.158.209.219:80 | http://watson.microsoft.com/StageOne/Generic/CLR20r3/gdfinstall_exe/0_0_0_0/4fd77b35/mscorlib/2_0_0_0/4ca2b889/344b/d8/System_IO_FileNotFoundException.htm?LCID=1033&OS=6.1.7601.2.00010100.1.0.48.17514&SM=DELL&SPN=DELL&BV=DELL&MID=3ADE2C42-4AB9-49B7-B142-BE9AEEA69063 | US | — | — | whitelisted |
2140 | dw20.exe | GET | — | 52.158.209.219:80 | http://watson.microsoft.com/StageOne/Generic/CLR20r3/gdfinstall_exe/0_0_0_0/4fd77b35/mscorlib/2_0_0_0/4ca2b889/344b/d8/System_IO_FileNotFoundException.htm?LCID=1033&OS=6.1.7601.2.00010100.1.0.48.17514&SM=DELL&SPN=DELL&BV=DELL&MID=3ADE2C42-4AB9-49B7-B142-BE9AEEA69063 | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3316 | dw20.exe | 52.158.209.219:80 | watson.microsoft.com | Microsoft Corporation | US | suspicious |
— | — | 52.158.209.219:80 | watson.microsoft.com | Microsoft Corporation | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
watson.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3316 | dw20.exe | Potential Corporate Privacy Violation | ET POLICY Application Crash Report Sent to Microsoft |
3316 | dw20.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |