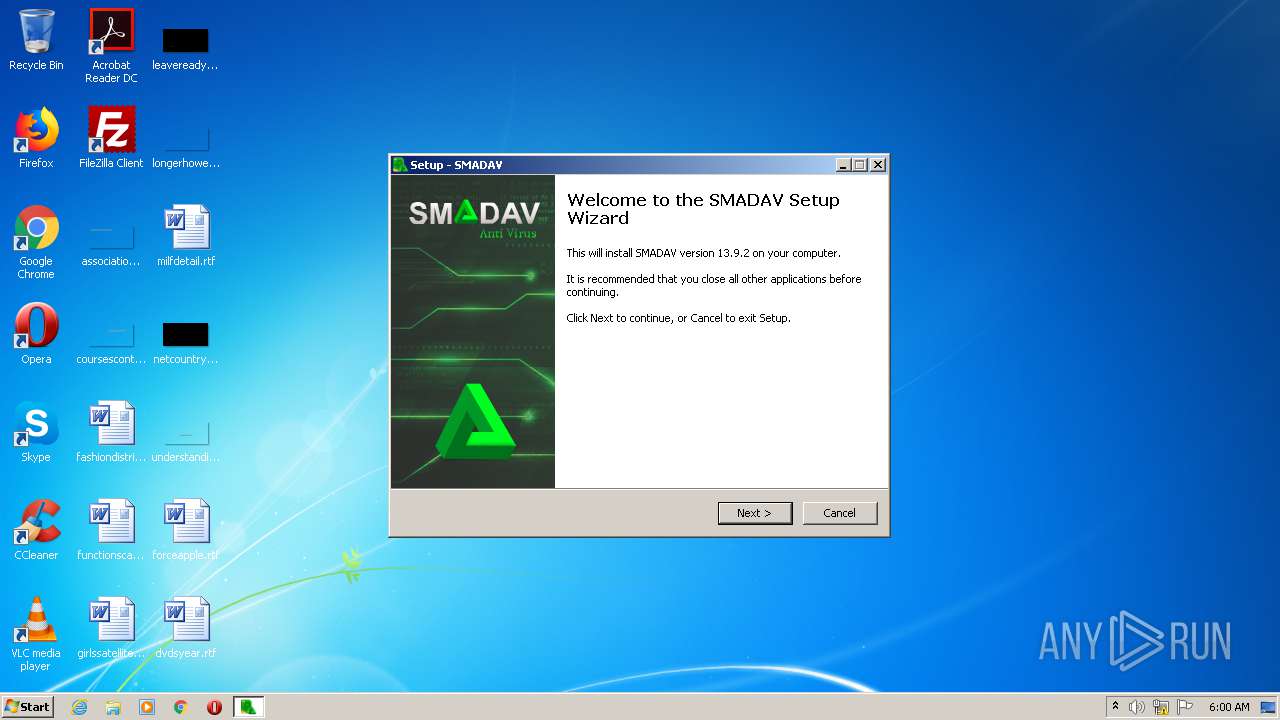
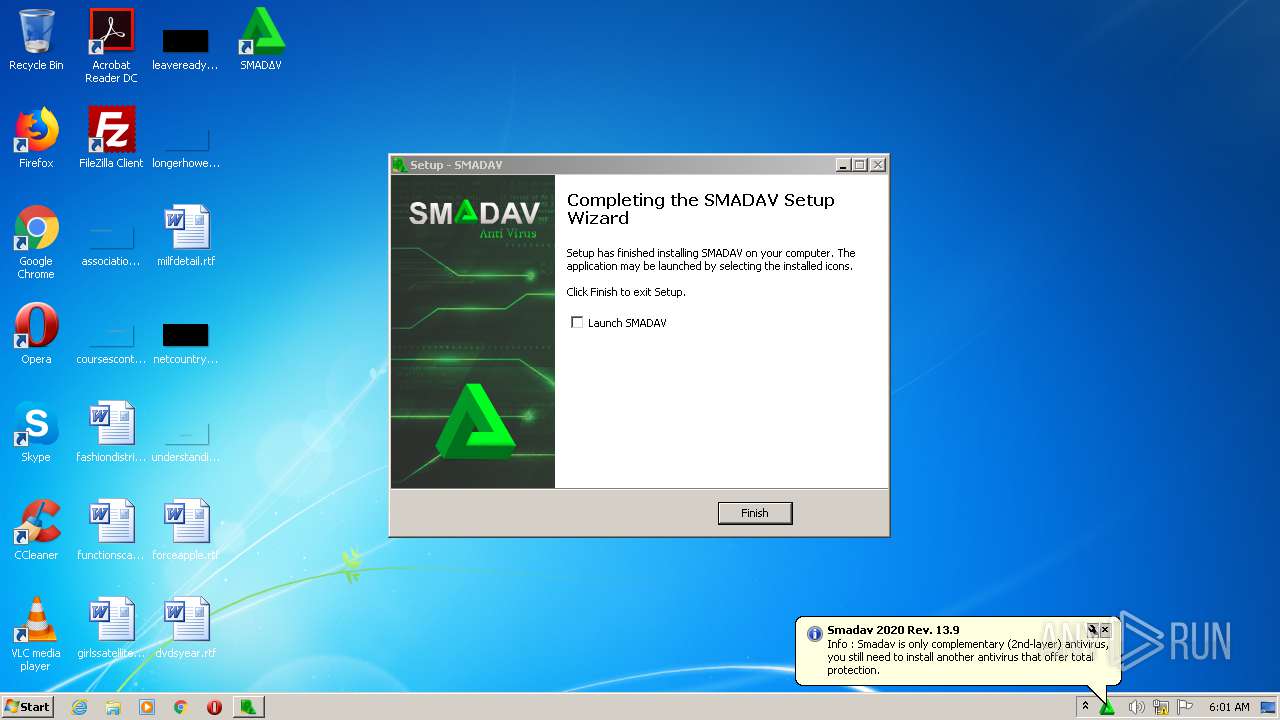
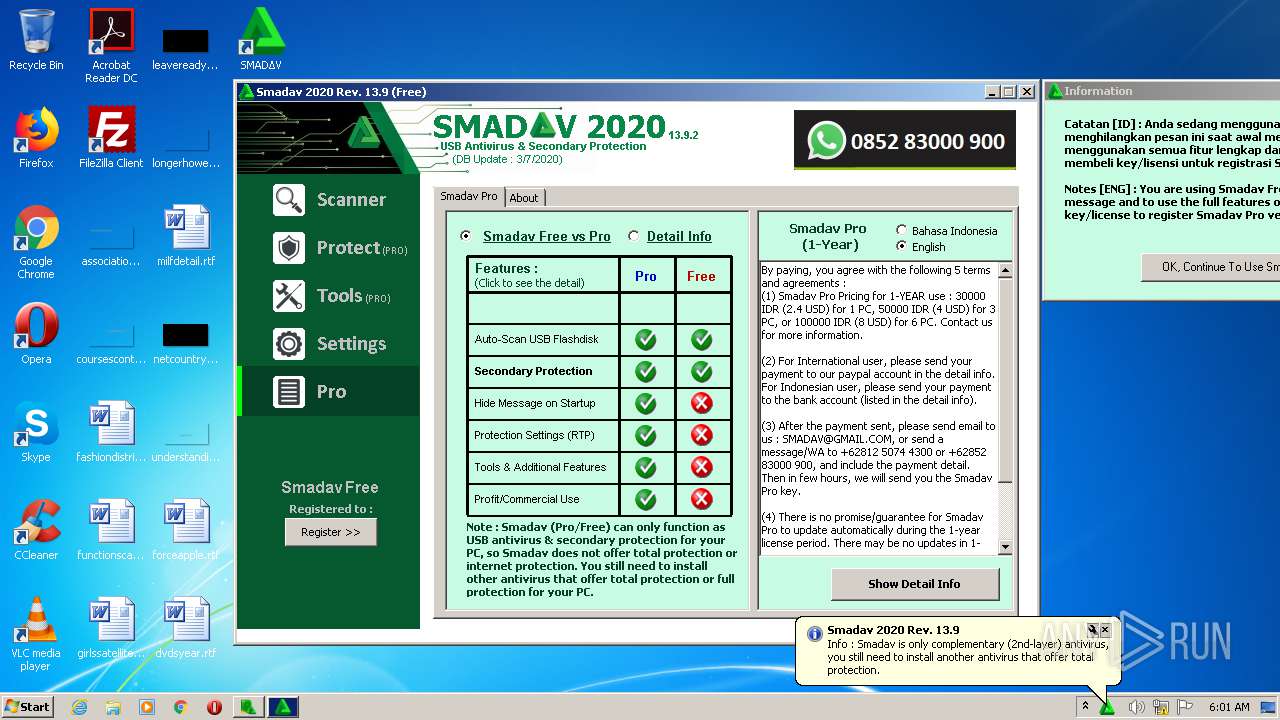
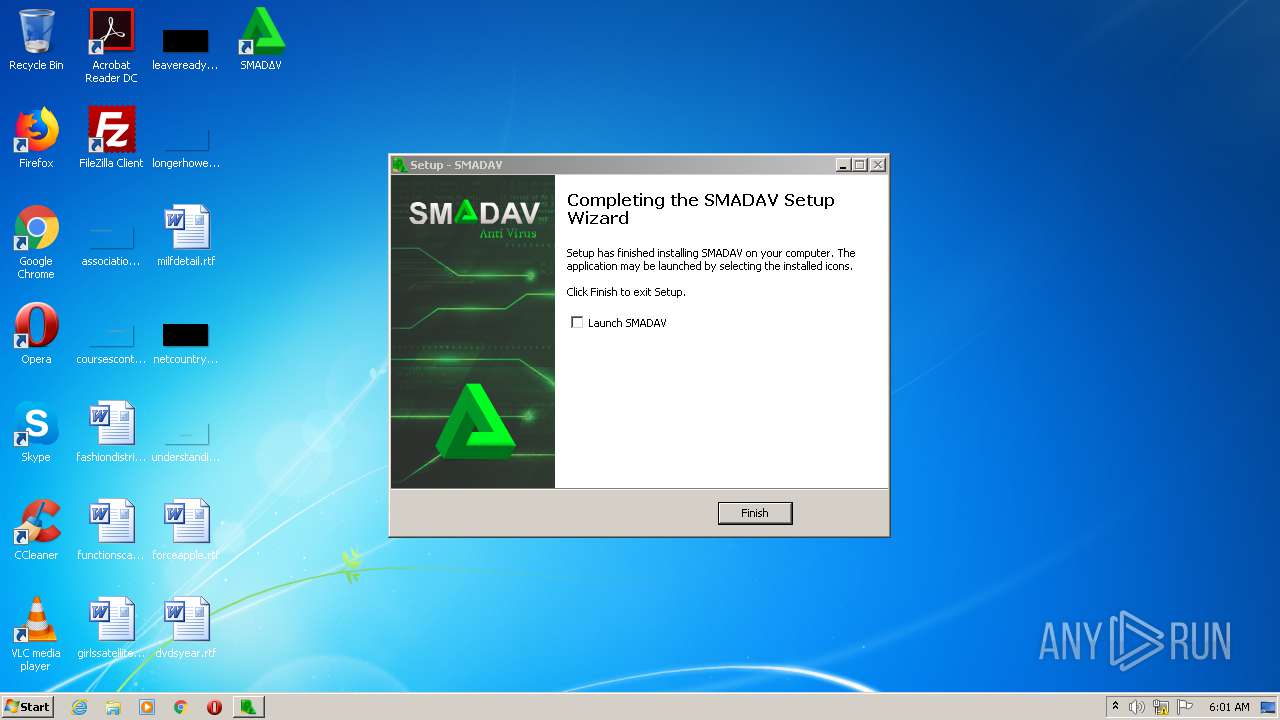
| download: | smadav2020rev139.exe |
| Full analysis: | https://app.any.run/tasks/05560521-8b9c-4b69-9254-033044e99b40 |
| Verdict: | Malicious activity |
| Analysis date: | July 17, 2020, 05:00:04 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | C7C0CDF291719A18265688A736DE6C62 |
| SHA1: | 43B26588E240B148B6C71D4C1FAACCBB2C0358F4 |
| SHA256: | 86EE7FA44AF8D3E7761CDD1B0B42B3DDA07D002332EF47F1C151F4A2E8E0B269 |
| SSDEEP: | 393216:iDorn1kM3NFBeq38ZN5aY0M0uDEI6wqh67o/41n9WW4ReYPk:i0yMNFBeqC5r4I6HU7o/4R9W3xk |
MALICIOUS
Registers / Runs the DLL via REGSVR32.EXE
- smadav2020rev139.tmp (PID: 2556)
Loads dropped or rewritten executable
- regsvr32.exe (PID: 2708)
- SMΔRTP.exe (PID: 4016)
- ctfmon.exe (PID: 292)
- SmadavProtect32.exe (PID: 3732)
- explorer.exe (PID: 288)
- DllHost.exe (PID: 4044)
- SMΔRTP.exe (PID: 4028)
Application was dropped or rewritten from another process
- SMΔRTP.exe (PID: 4016)
- SMΔRTP.exe (PID: 4028)
- SmadavProtect32.exe (PID: 3732)
- SmadavHelper.exe (PID: 1152)
Uses Task Scheduler to run other applications
- SMΔRTP.exe (PID: 4016)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 2484)
Changes the autorun value in the registry
- SMΔRTP.exe (PID: 4016)
Changes settings of System certificates
- SMΔRTP.exe (PID: 4016)
SUSPICIOUS
Executable content was dropped or overwritten
- smadav2020rev139.exe (PID: 3560)
- smadav2020rev139.exe (PID: 296)
- smadav2020rev139.tmp (PID: 2556)
- SMΔRTP.exe (PID: 4016)
Reads Windows owner or organization settings
- smadav2020rev139.tmp (PID: 2556)
Reads the Windows organization settings
- smadav2020rev139.tmp (PID: 2556)
Uses TASKKILL.EXE to kill process
- smadav2020rev139.tmp (PID: 2556)
Creates COM task schedule object
- regsvr32.exe (PID: 2708)
- SMΔRTP.exe (PID: 4016)
Searches for installed software
- smadav2020rev139.tmp (PID: 2556)
Creates files in the user directory
- SMΔRTP.exe (PID: 4016)
Application launched itself
- SMΔRTP.exe (PID: 4016)
Reads Internet Cache Settings
- SMΔRTP.exe (PID: 4016)
- SmadavHelper.exe (PID: 1152)
Adds / modifies Windows certificates
- SMΔRTP.exe (PID: 4016)
INFO
Application was dropped or rewritten from another process
- smadav2020rev139.tmp (PID: 2556)
- smadav2020rev139.tmp (PID: 2272)
Loads dropped or rewritten executable
- smadav2020rev139.tmp (PID: 2556)
Creates files in the program directory
- smadav2020rev139.tmp (PID: 2556)
Creates a software uninstall entry
- smadav2020rev139.tmp (PID: 2556)
Reads settings of System Certificates
- SMΔRTP.exe (PID: 4016)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (42.6) |
|---|---|---|
| .exe | | | Win16/32 Executable Delphi generic (19.5) |
| .exe | | | Generic Win/DOS Executable (18.9) |
| .exe | | | DOS Executable Generic (18.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2013:10:13 10:19:32+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 65024 |
| InitializedDataSize: | 67072 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x113bc |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
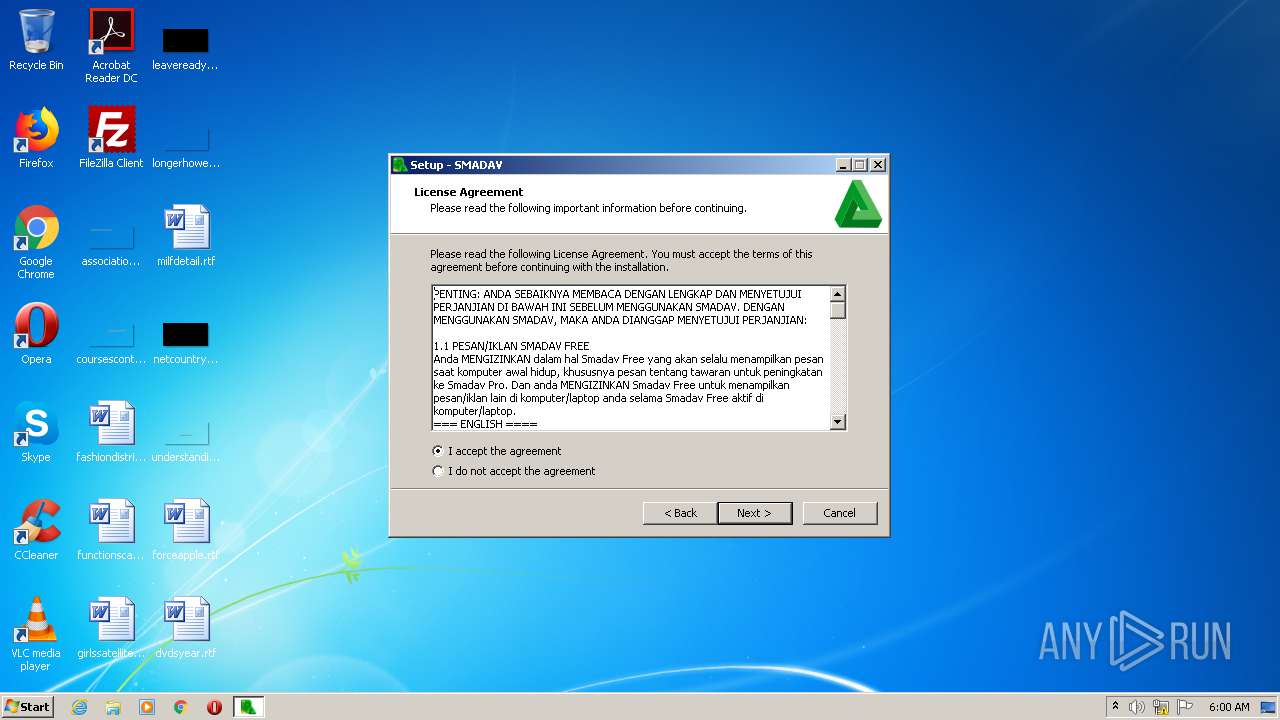
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | Smadsoft |
| FileDescription: | SMADAV Setup |
| FileVersion: | |
| LegalCopyright: | |
| ProductName: | SMADAV |
| ProductVersion: | 13.9.2 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 13-Oct-2013 08:19:32 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | Smadsoft |
| FileDescription: | SMADAV Setup |
| FileVersion: | - |
| LegalCopyright: | - |
| ProductName: | SMADAV |
| ProductVersion: | 13.9.2 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 13-Oct-2013 08:19:32 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000F12C | 0x0000F200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.39148 |
.itext | 0x00011000 | 0x00000B44 | 0x00000C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.73207 |
.data | 0x00012000 | 0x00000C88 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.24631 |
.bss | 0x00013000 | 0x000056B4 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00019000 | 0x00000DD0 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.97188 |
.tls | 0x0001A000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0001B000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.204488 |
.rsrc | 0x0001C000 | 0x0000E71C | 0x0000E800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.77833 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.11919 | 1512 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 5.41348 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 5.14033 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 5.47746 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 5.85188 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
4091 | 2.56031 | 104 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4092 | 3.25287 | 212 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4093 | 3.26919 | 164 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4094 | 3.33268 | 684 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4095 | 3.34579 | 844 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
56
Monitored processes
17
Malicious processes
7
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 288 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 292 | C:\Windows\System32\ctfmon.exe | C:\Windows\System32\ctfmon.exe | — | taskeng.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: CTF Loader Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 296 | "C:\Users\admin\AppData\Local\Temp\smadav2020rev139.exe" /SPAWNWND=$20132 /NOTIFYWND=$20138 | C:\Users\admin\AppData\Local\Temp\smadav2020rev139.exe | smadav2020rev139.tmp | ||||||||||||
User: admin Company: Smadsoft Integrity Level: HIGH Description: SMADAV Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 1152 | "C:\Program Files\Smadav\SmadavHelper.exe" "JZb)toynfjb3djixpSTbunjiaxex|JZb6knvk.pYGtqxjblblaxex|" | C:\Program Files\Smadav\SmadavHelper.exe | SMΔRTP.exe | ||||||||||||
User: admin Company: Smadav Software Integrity Level: HIGH Description: Smadav Helper Assistance Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 1740 | "C:\Windows\System32\taskkill.exe" /f /im SmadavProtect32.exe | C:\Windows\System32\taskkill.exe | — | smadav2020rev139.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2056 | "C:\Windows\System32\taskkill.exe" /f /im SMΔRTP.exe | C:\Windows\System32\taskkill.exe | — | smadav2020rev139.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2272 | "C:\Users\admin\AppData\Local\Temp\is-17ATN.tmp\smadav2020rev139.tmp" /SL5="$20138,16880570,133120,C:\Users\admin\AppData\Local\Temp\smadav2020rev139.exe" | C:\Users\admin\AppData\Local\Temp\is-17ATN.tmp\smadav2020rev139.tmp | — | smadav2020rev139.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 2484 | "C:\Windows\system32\schtasks.exe" /create /tn "smadav" /xml "C:\Users\admin\AppData\Roaming\Smadav\smadav.xml" | C:\Windows\system32\schtasks.exe | — | SMΔRTP.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2556 | "C:\Users\admin\AppData\Local\Temp\is-J0QA8.tmp\smadav2020rev139.tmp" /SL5="$3013C,16880570,133120,C:\Users\admin\AppData\Local\Temp\smadav2020rev139.exe" /SPAWNWND=$20132 /NOTIFYWND=$20138 | C:\Users\admin\AppData\Local\Temp\is-J0QA8.tmp\smadav2020rev139.tmp | smadav2020rev139.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 2708 | "C:\Windows\system32\regsvr32.exe" /s "C:\Program Files\SMADAV\SmadExtMenu.dll" | C:\Windows\system32\regsvr32.exe | — | smadav2020rev139.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 673
Read events
2 525
Write events
142
Delete events
6
Modification events
| (PID) Process: | (2556) smadav2020rev139.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2556) smadav2020rev139.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2556) smadav2020rev139.tmp | Key: | HKEY_CURRENT_USER\Software\SMADΔV |
| Operation: | write | Name: | Language |
Value: 1 | |||
| (PID) Process: | (2556) smadav2020rev139.tmp | Key: | HKEY_CURRENT_USER\Software\SMADΔV |
| Operation: | write | Name: | LanguageSet |
Value: 1 | |||
| (PID) Process: | (2556) smadav2020rev139.tmp | Key: | HKEY_CURRENT_USER\Software\SMADΔV |
| Operation: | write | Name: | Path |
Value: C:\Program Files\SMADAV\ | |||
| (PID) Process: | (2556) smadav2020rev139.tmp | Key: | HKEY_CURRENT_USER\Software\SMADΔV |
| Operation: | write | Name: | AutoScan |
Value: 1 | |||
| (PID) Process: | (2556) smadav2020rev139.tmp | Key: | HKEY_CURRENT_USER\Software\SMADΔV |
| Operation: | write | Name: | Smad-Lock |
Value: 1 | |||
| (PID) Process: | (2556) smadav2020rev139.tmp | Key: | HKEY_CURRENT_USER\Software\SMADΔV |
| Operation: | write | Name: | HideScanner |
Value: 1 | |||
| (PID) Process: | (2556) smadav2020rev139.tmp | Key: | HKEY_CURRENT_USER\Software\SMADΔV |
| Operation: | write | Name: | AllowMacro |
Value: 0 | |||
| (PID) Process: | (2556) smadav2020rev139.tmp | Key: | HKEY_CURRENT_USER\Software\SMADΔV |
| Operation: | write | Name: | AllowUSB |
Value: 0 | |||
Executable files
14
Suspicious files
2
Text files
2
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2556 | smadav2020rev139.tmp | C:\Program Files\SMADAV\is-G4UG3.tmp | — | |
MD5:— | SHA256:— | |||
| 2556 | smadav2020rev139.tmp | C:\Program Files\SMADAV\is-OQPEF.tmp | — | |
MD5:— | SHA256:— | |||
| 2556 | smadav2020rev139.tmp | C:\Program Files\SMADAV\is-4E86I.tmp | — | |
MD5:— | SHA256:— | |||
| 2556 | smadav2020rev139.tmp | C:\Program Files\SMADAV\is-BN208.tmp | — | |
MD5:— | SHA256:— | |||
| 2556 | smadav2020rev139.tmp | C:\Program Files\SMADAV\Smadav.loov | — | |
MD5:— | SHA256:— | |||
| 2556 | smadav2020rev139.tmp | C:\Program Files\SMADAV\is-NHR6U.tmp | — | |
MD5:— | SHA256:— | |||
| 2556 | smadav2020rev139.tmp | C:\Program Files\SMADAV\is-QFQ7I.tmp | — | |
MD5:— | SHA256:— | |||
| 2556 | smadav2020rev139.tmp | C:\Program Files\SMADAV\is-45271.tmp | — | |
MD5:— | SHA256:— | |||
| 2556 | smadav2020rev139.tmp | C:\Program Files\SMADAV\is-8GIHL.tmp | — | |
MD5:— | SHA256:— | |||
| 2556 | smadav2020rev139.tmp | C:\Program Files\SMADAV\is-C5M90.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
7
DNS requests
4
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
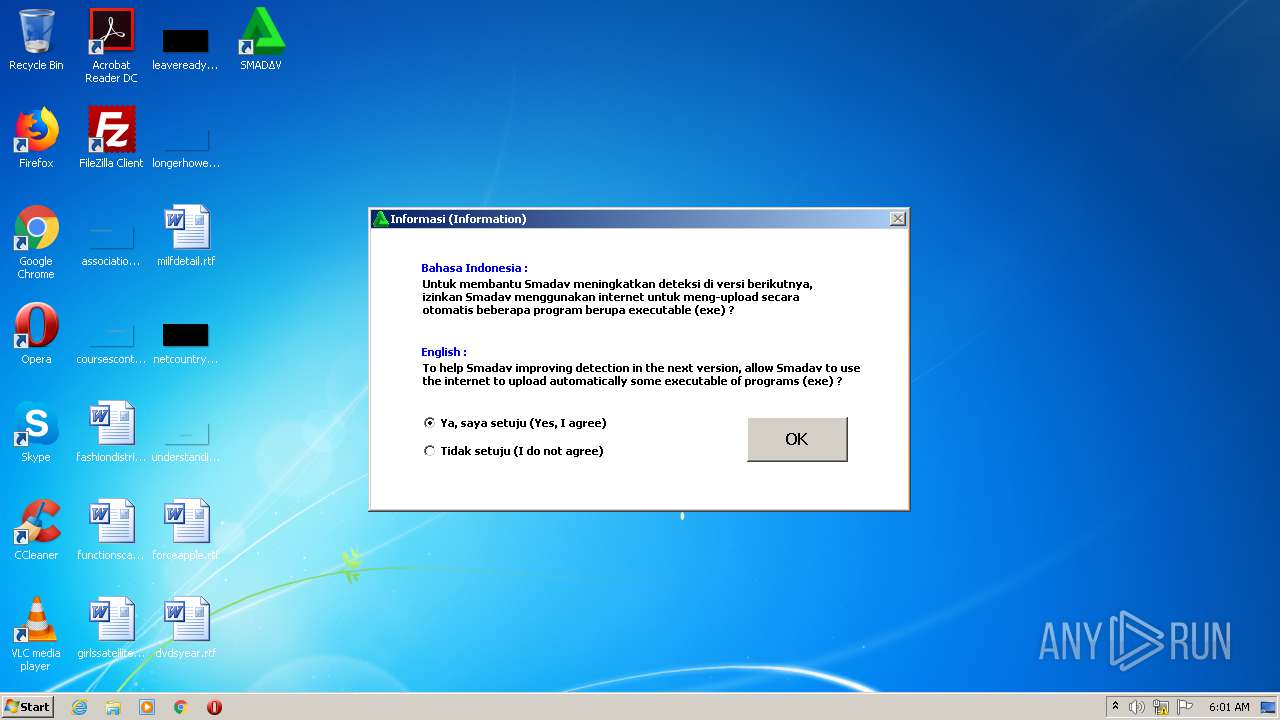
4016 | SMΔRTP.exe | POST | 200 | 139.99.68.140:80 | http://mencapai.com/smadavstats80.php | SG | text | 69 b | suspicious |
4016 | SMΔRTP.exe | GET | 200 | 148.72.212.69:80 | http://www.lempar.com/update/secure-smadav.txt | US | text | 389 b | malicious |
4016 | SMΔRTP.exe | GET | 200 | 148.72.212.69:80 | http://lempar.com/smadstat.php?mac=1994429369A727963&key=0&name=0&os=2%2E6%2E1%2E7601&build=1147&old=-1&mode=0&stat1=777&stat2=1&stat3=0&stat4=3&stat5=8002&stat6=6 | US | binary | 1 b | malicious |
4016 | SMΔRTP.exe | POST | 200 | 147.135.46.101:80 | http://dwres.com/smadavstats27.php | US | text | 3 b | suspicious |
4016 | SMΔRTP.exe | POST | 200 | 147.135.46.101:80 | http://dwres.com/smadavstats15.php | US | text | 3 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4016 | SMΔRTP.exe | 148.72.212.69:80 | lempar.com | — | US | malicious |
4016 | SMΔRTP.exe | 147.135.46.101:80 | dwres.com | OVH SAS | US | suspicious |
— | — | 147.135.46.101:80 | dwres.com | OVH SAS | US | suspicious |
4016 | SMΔRTP.exe | 139.99.68.140:80 | mencapai.com | OVH SAS | SG | unknown |
1152 | SmadavHelper.exe | 139.99.68.140:21 | mencapai.com | OVH SAS | SG | unknown |
1152 | SmadavHelper.exe | 139.99.68.140:30233 | mencapai.com | OVH SAS | SG | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
lempar.com |
| malicious |
dwres.com |
| suspicious |
www.lempar.com |
| malicious |
mencapai.com |
| suspicious |