| File name: | 86ee53c7d42f9187b734d69bdcde0869932b85992e5fa635ecf0040a933acc96.exe |
| Full analysis: | https://app.any.run/tasks/0bb07fb6-3ebc-4ccc-876f-c8d13406d6d1 |
| Verdict: | Malicious activity |
| Analysis date: | May 26, 2025, 17:12:08 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive, 5 sections |
| MD5: | 8733C89F832C5E011934B72685A34153 |
| SHA1: | D9258906C84ABD12731D9536CB12CCB46C77443E |
| SHA256: | 86EE53C7D42F9187B734D69BDCDE0869932B85992E5FA635ECF0040A933ACC96 |
| SSDEEP: | 24576:b6w26e6KLluvYSE3xjZhzNFx01/LB5gSBClLDlmenrZtUj/zq/8sihKDKlfh/PcD:2w2r6KLluvYSyxjZhzNFx01/LB5gSBCh |
MALICIOUS
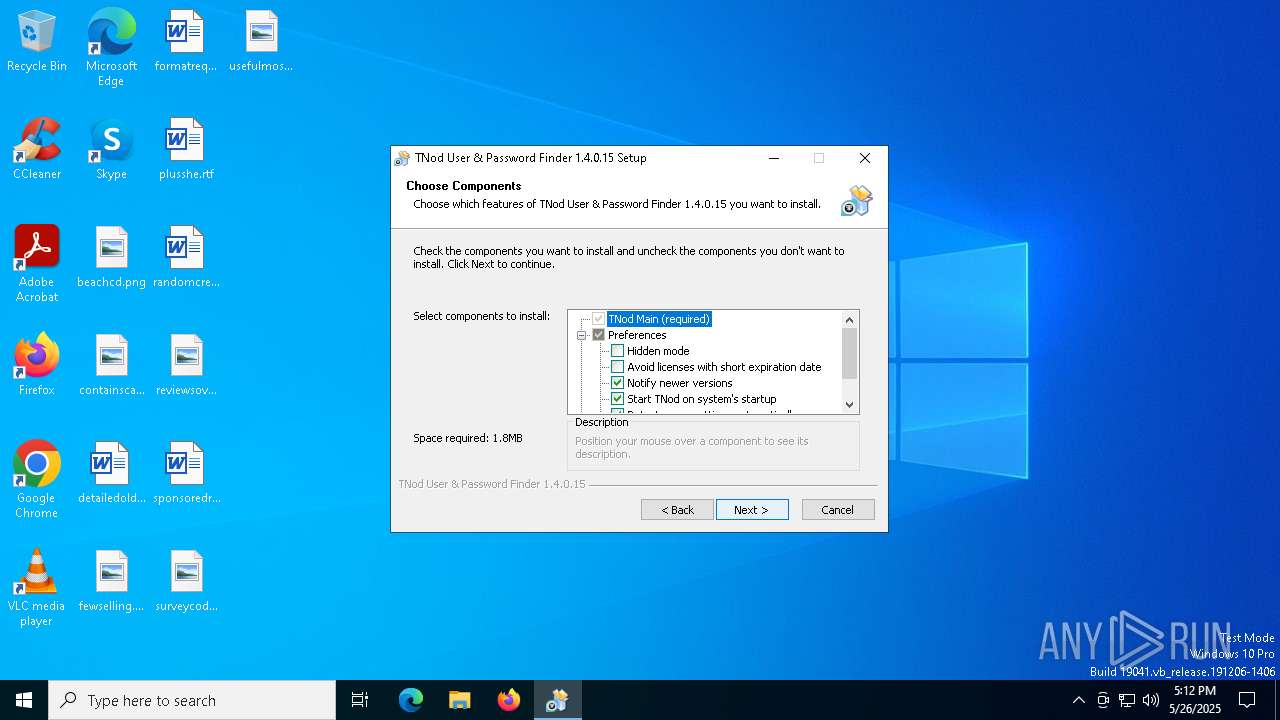
Changes the autorun value in the registry
- 86ee53c7d42f9187b734d69bdcde0869932b85992e5fa635ecf0040a933acc96.exe (PID: 7012)
SUSPICIOUS
Executable content was dropped or overwritten
- 86ee53c7d42f9187b734d69bdcde0869932b85992e5fa635ecf0040a933acc96.exe (PID: 7012)
Malware-specific behavior (creating "System.dll" in Temp)
- 86ee53c7d42f9187b734d69bdcde0869932b85992e5fa635ecf0040a933acc96.exe (PID: 7012)
There is functionality for taking screenshot (YARA)
- 86ee53c7d42f9187b734d69bdcde0869932b85992e5fa635ecf0040a933acc96.exe (PID: 7012)
The process creates files with name similar to system file names
- 86ee53c7d42f9187b734d69bdcde0869932b85992e5fa635ecf0040a933acc96.exe (PID: 7012)
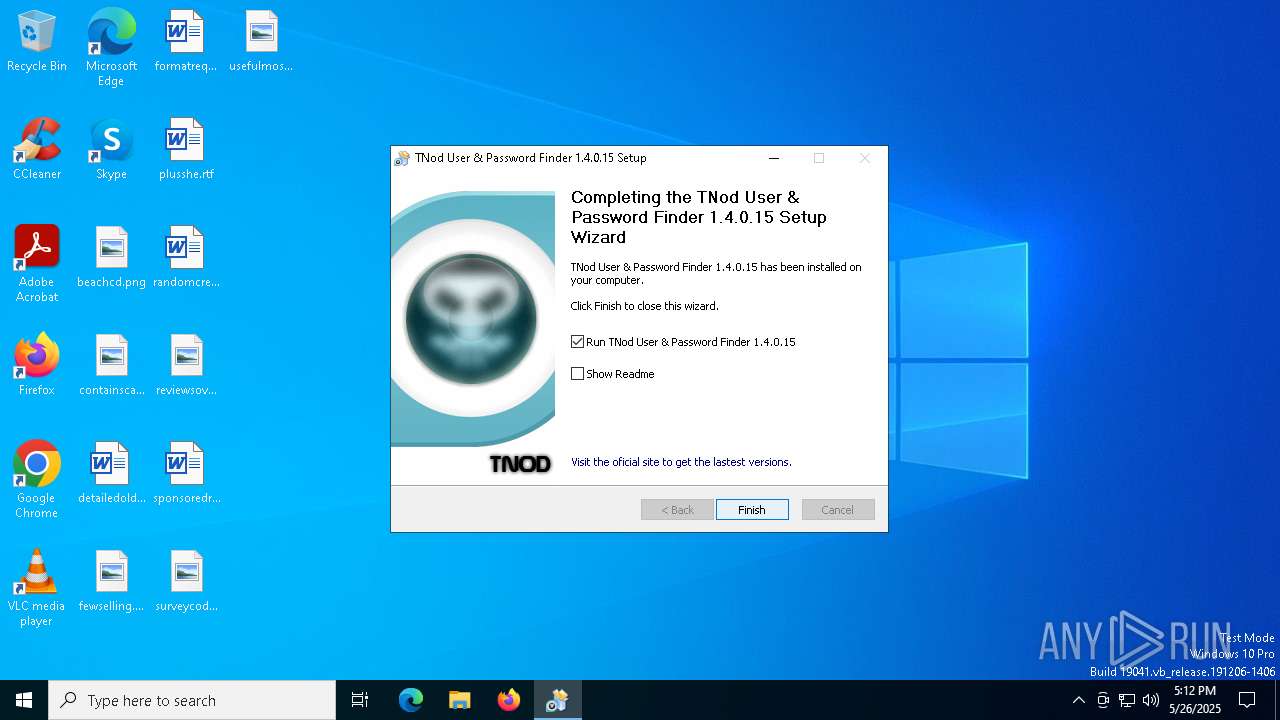
Creates a software uninstall entry
- 86ee53c7d42f9187b734d69bdcde0869932b85992e5fa635ecf0040a933acc96.exe (PID: 7012)
Reads security settings of Internet Explorer
- TNODUP.exe (PID: 4696)
- TNODUP.exe (PID: 1096)
INFO
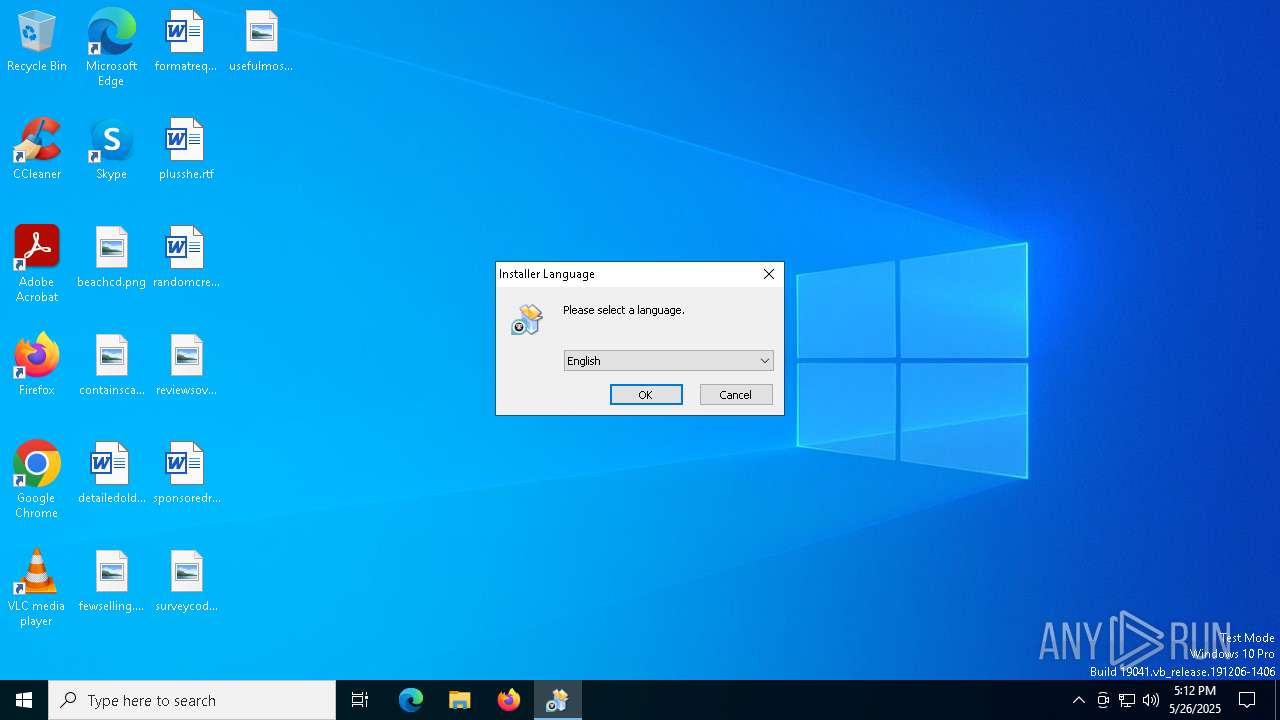
Checks supported languages
- 86ee53c7d42f9187b734d69bdcde0869932b85992e5fa635ecf0040a933acc96.exe (PID: 7012)
- TNODUP.exe (PID: 4696)
- TNODUP.exe (PID: 1096)
Reads the computer name
- 86ee53c7d42f9187b734d69bdcde0869932b85992e5fa635ecf0040a933acc96.exe (PID: 7012)
- TNODUP.exe (PID: 4696)
- TNODUP.exe (PID: 1096)
Launch of the file from Registry key
- 86ee53c7d42f9187b734d69bdcde0869932b85992e5fa635ecf0040a933acc96.exe (PID: 7012)
Creates files in the program directory
- 86ee53c7d42f9187b734d69bdcde0869932b85992e5fa635ecf0040a933acc96.exe (PID: 7012)
Create files in a temporary directory
- 86ee53c7d42f9187b734d69bdcde0869932b85992e5fa635ecf0040a933acc96.exe (PID: 7012)
Checks proxy server information
- TNODUP.exe (PID: 4696)
- TNODUP.exe (PID: 1096)
Manual execution by a user
- TNODUP.exe (PID: 1096)
Reads the software policy settings
- slui.exe (PID: 3884)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (94.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.7) |
| .exe | | | Win32 Executable (generic) (0.5) |
| .exe | | | Generic Win/DOS Executable (0.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:12:05 22:50:46+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 23552 |
| InitializedDataSize: | 119808 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x323c |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.4.0.15 |
| ProductVersionNumber: | 1.4.0.15 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Windows, Latin1 |
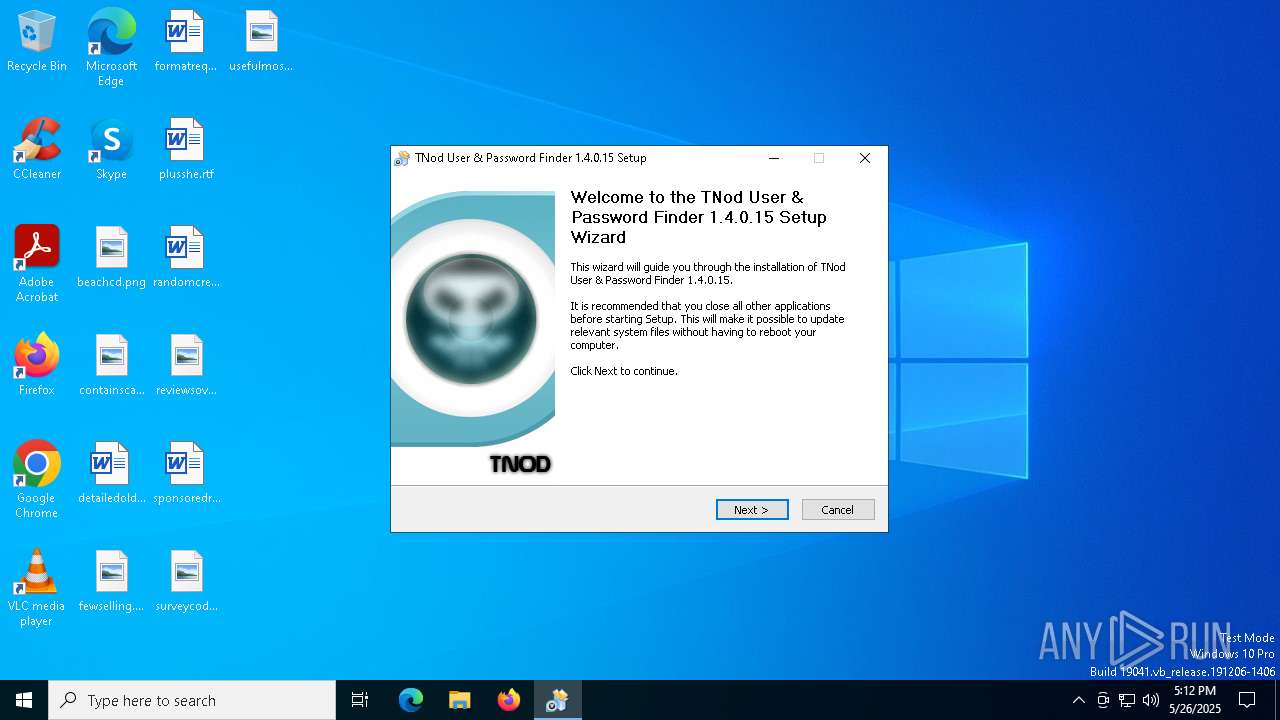
| CompanyName: | Tukero[X]Team |
| FileDescription: | Installer. NSIS |
| FileVersion: | 1.4.0.15 |
| LegalCopyright: | © Tukero |
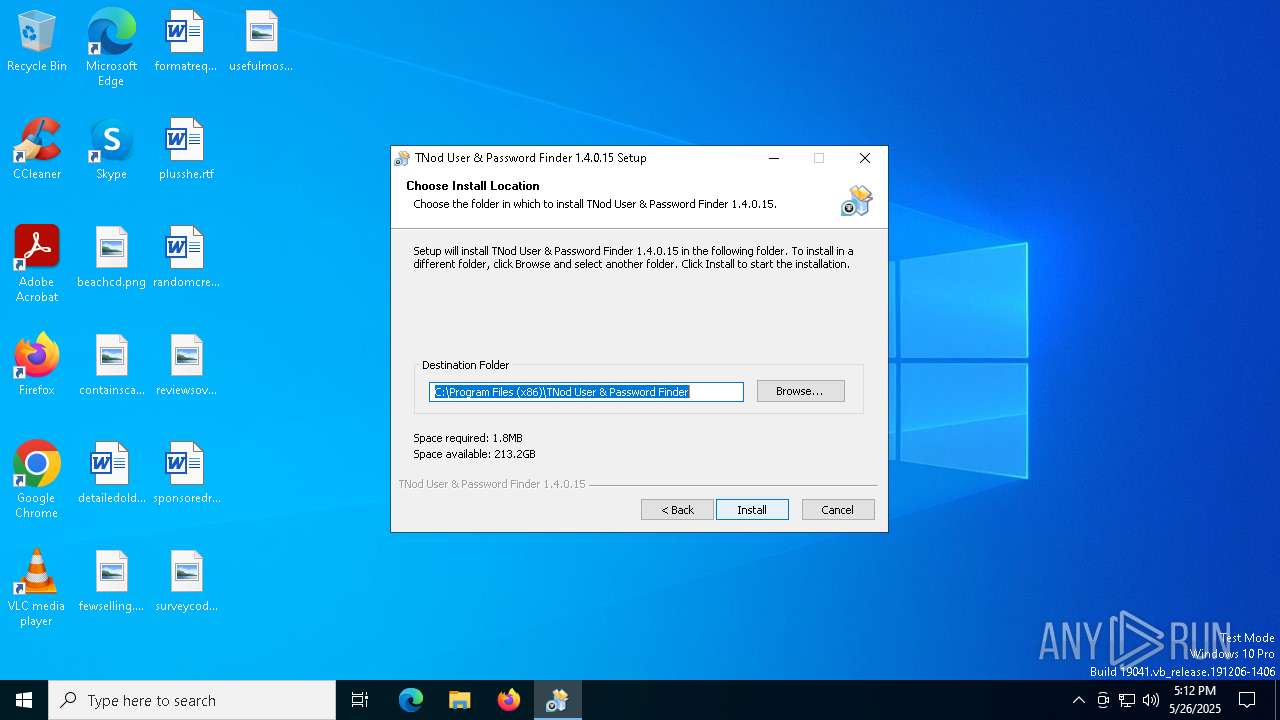
| ProductName: | TNod User & Password Finder |
| ProductVersion: | 1.4.0.15 |
Total processes
138
Monitored processes
7
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1096 | "C:\Program Files (x86)\TNod User & Password Finder\TNODUP.exe" | C:\Program Files (x86)\TNod User & Password Finder\TNODUP.exe | — | explorer.exe | |||||||||||
User: admin Company: Tukero[X]Team Integrity Level: MEDIUM Description: TNod User & Password Finder Exit code: 0 Version: 1, 4, 0, 15 Modules
| |||||||||||||||
| 3884 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3896 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4696 | "C:\Program Files (x86)\TNod User & Password Finder\TNODUP.exe" | C:\Program Files (x86)\TNod User & Password Finder\TNODUP.exe | — | 86ee53c7d42f9187b734d69bdcde0869932b85992e5fa635ecf0040a933acc96.exe | |||||||||||
User: admin Company: Tukero[X]Team Integrity Level: HIGH Description: TNod User & Password Finder Exit code: 0 Version: 1, 4, 0, 15 Modules
| |||||||||||||||
| 6808 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7012 | "C:\Users\admin\AppData\Local\Temp\86ee53c7d42f9187b734d69bdcde0869932b85992e5fa635ecf0040a933acc96.exe" | C:\Users\admin\AppData\Local\Temp\86ee53c7d42f9187b734d69bdcde0869932b85992e5fa635ecf0040a933acc96.exe | — | explorer.exe | |||||||||||
User: admin Company: Tukero[X]Team Integrity Level: MEDIUM Description: Installer. NSIS Exit code: 3221226540 Version: 1.4.0.15 Modules
| |||||||||||||||
| 7012 | "C:\Users\admin\AppData\Local\Temp\86ee53c7d42f9187b734d69bdcde0869932b85992e5fa635ecf0040a933acc96.exe" | C:\Users\admin\AppData\Local\Temp\86ee53c7d42f9187b734d69bdcde0869932b85992e5fa635ecf0040a933acc96.exe | explorer.exe | ||||||||||||
User: admin Company: Tukero[X]Team Integrity Level: HIGH Description: Installer. NSIS Exit code: 0 Version: 1.4.0.15 Modules
| |||||||||||||||
Total events
1 540
Read events
1 471
Write events
69
Delete events
0
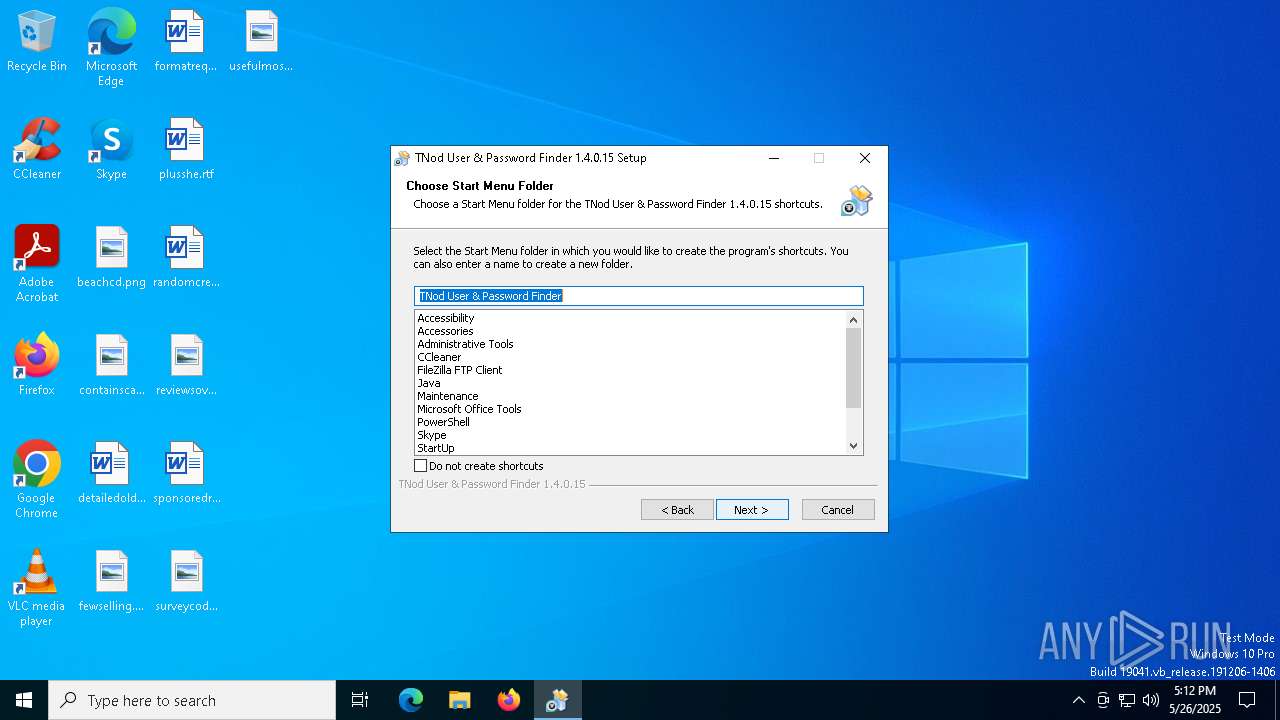
Modification events
| (PID) Process: | (7012) 86ee53c7d42f9187b734d69bdcde0869932b85992e5fa635ecf0040a933acc96.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Tukero[X]Team |
| Operation: | write | Name: | TNod StartMenuFolder |
Value: TNod User & Password Finder | |||
| (PID) Process: | (7012) 86ee53c7d42f9187b734d69bdcde0869932b85992e5fa635ecf0040a933acc96.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Tukero[X]Team\TNod User & Password Finder |
| Operation: | write | Name: | Language |
Value: 56 | |||
| (PID) Process: | (7012) 86ee53c7d42f9187b734d69bdcde0869932b85992e5fa635ecf0040a933acc96.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Tukero[X]Team |
| Operation: | write | Name: | TNod InstallDir |
Value: C:\Program Files (x86)\TNod User & Password Finder | |||
| (PID) Process: | (7012) 86ee53c7d42f9187b734d69bdcde0869932b85992e5fa635ecf0040a933acc96.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Tukero[X]Team\TNod User & Password Finder |
| Operation: | write | Name: | NewVersions |
Value: 1 | |||
| (PID) Process: | (7012) 86ee53c7d42f9187b734d69bdcde0869932b85992e5fa635ecf0040a933acc96.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | TNOD UP |
Value: "C:\Program Files (x86)\TNod User & Password Finder\TNODUP.exe" /i | |||
| (PID) Process: | (7012) 86ee53c7d42f9187b734d69bdcde0869932b85992e5fa635ecf0040a933acc96.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Tukero[X]Team\TNod User & Password Finder |
| Operation: | write | Name: | UseIEProxy |
Value: 1 | |||
| (PID) Process: | (7012) 86ee53c7d42f9187b734d69bdcde0869932b85992e5fa635ecf0040a933acc96.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\TNod |
| Operation: | write | Name: | UninstallString |
Value: "C:\Program Files (x86)\TNod User & Password Finder\uninst-TNod.exe" | |||
| (PID) Process: | (7012) 86ee53c7d42f9187b734d69bdcde0869932b85992e5fa635ecf0040a933acc96.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\TNod |
| Operation: | write | Name: | DisplayName |
Value: TNod User & Password Finder | |||
| (PID) Process: | (7012) 86ee53c7d42f9187b734d69bdcde0869932b85992e5fa635ecf0040a933acc96.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\TNod |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Program Files (x86)\TNod User & Password Finder\TNODUP.exe,0 | |||
| (PID) Process: | (7012) 86ee53c7d42f9187b734d69bdcde0869932b85992e5fa635ecf0040a933acc96.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\TNod |
| Operation: | write | Name: | DisplayVersion |
Value: 1.4.0.15 | |||
Executable files
8
Suspicious files
10
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7012 | 86ee53c7d42f9187b734d69bdcde0869932b85992e5fa635ecf0040a933acc96.exe | C:\Users\admin\AppData\Local\Temp\nscBBD2.tmp\modern-wizard.bmp | image | |
MD5:A4CAFA206193CA77110D2BBB750D602C | SHA256:43C16E75A065787EC73318FD1BBEDA30377662533F4B42461A8AFF174C436AA9 | |||
| 7012 | 86ee53c7d42f9187b734d69bdcde0869932b85992e5fa635ecf0040a933acc96.exe | C:\Program Files (x86)\TNod User & Password Finder\tnodicons.icl | executable | |
MD5:49D13D0454EA8FBC278A026686011803 | SHA256:F2643CE646F2C5A69ADFA271C2C88033FCBBE2DE037AD01DDB5BCA076A380084 | |||
| 7012 | 86ee53c7d42f9187b734d69bdcde0869932b85992e5fa635ecf0040a933acc96.exe | C:\Users\admin\AppData\Local\Temp\nscBBD2.tmp\StartMenu.dll | executable | |
MD5:A4173B381625F9F12AADB4E1CDAEFDB8 | SHA256:7755FF2707CA19344D489A5ACEC02D9E310425FA6E100D2F13025761676B875B | |||
| 7012 | 86ee53c7d42f9187b734d69bdcde0869932b85992e5fa635ecf0040a933acc96.exe | C:\Program Files (x86)\TNod User & Password Finder\TNODUP.exe | executable | |
MD5:E268C7C2716E33F91DD988E38D2973FD | SHA256:F83589F99374767795A49DA0F66A3F95D827D742D4E0E339548AA0E1B9D026C9 | |||
| 7012 | 86ee53c7d42f9187b734d69bdcde0869932b85992e5fa635ecf0040a933acc96.exe | C:\Program Files (x86)\TNod User & Password Finder\LEEME.txt | text | |
MD5:BAA3F5327B241FBB28B887CD072A057D | SHA256:AE3031E677BA295D732F7CC1C91786AB5FBE649ED8B0CF41AF090146F1826C9B | |||
| 7012 | 86ee53c7d42f9187b734d69bdcde0869932b85992e5fa635ecf0040a933acc96.exe | C:\Users\admin\AppData\Local\Temp\nscBBD2.tmp\System.dll | executable | |
MD5:C17103AE9072A06DA581DEC998343FC1 | SHA256:DC58D8AD81CACB0C1ED72E33BFF8F23EA40B5252B5BB55D393A0903E6819AE2F | |||
| 7012 | 86ee53c7d42f9187b734d69bdcde0869932b85992e5fa635ecf0040a933acc96.exe | C:\Program Files (x86)\TNod User & Password Finder\CREDITOS.txt | text | |
MD5:AF3204ACE9EAAC65558E07F3A25A5DE7 | SHA256:50367C77AE12A4BE1D33FBC914493117E655D28E33E6F32D230289302520960D | |||
| 7012 | 86ee53c7d42f9187b734d69bdcde0869932b85992e5fa635ecf0040a933acc96.exe | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\TNod User & Password Finder\Open Settings.lnk | binary | |
MD5:01D551801659C585480ACAA1E27BFB19 | SHA256:487520362C2A14902B0A401E87B4F5A841D648374D43663BB1D3C8643A0DA1A1 | |||
| 7012 | 86ee53c7d42f9187b734d69bdcde0869932b85992e5fa635ecf0040a933acc96.exe | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\TNod User & Password Finder\Update license.lnk | binary | |
MD5:66B2F693D56E2360BC8A384B74977672 | SHA256:6305EA9106AA18362ADB677A812FF601228879DF892194EBD472FCEDA4E9A9BC | |||
| 7012 | 86ee53c7d42f9187b734d69bdcde0869932b85992e5fa635ecf0040a933acc96.exe | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\TNod User & Password Finder\Run hidden.lnk | binary | |
MD5:C19444036D59FF9EB7D21171724AB5C2 | SHA256:2C16D978FCC88B0F10EB28B677CE5F6610FD5BAC711ED0E48BAF288ED373EF62 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
21
DNS requests
15
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.168.124:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
960 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.16.168.124:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
960 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.168.124:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
— | — | 2.16.168.124:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
— | — | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.159.130:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |