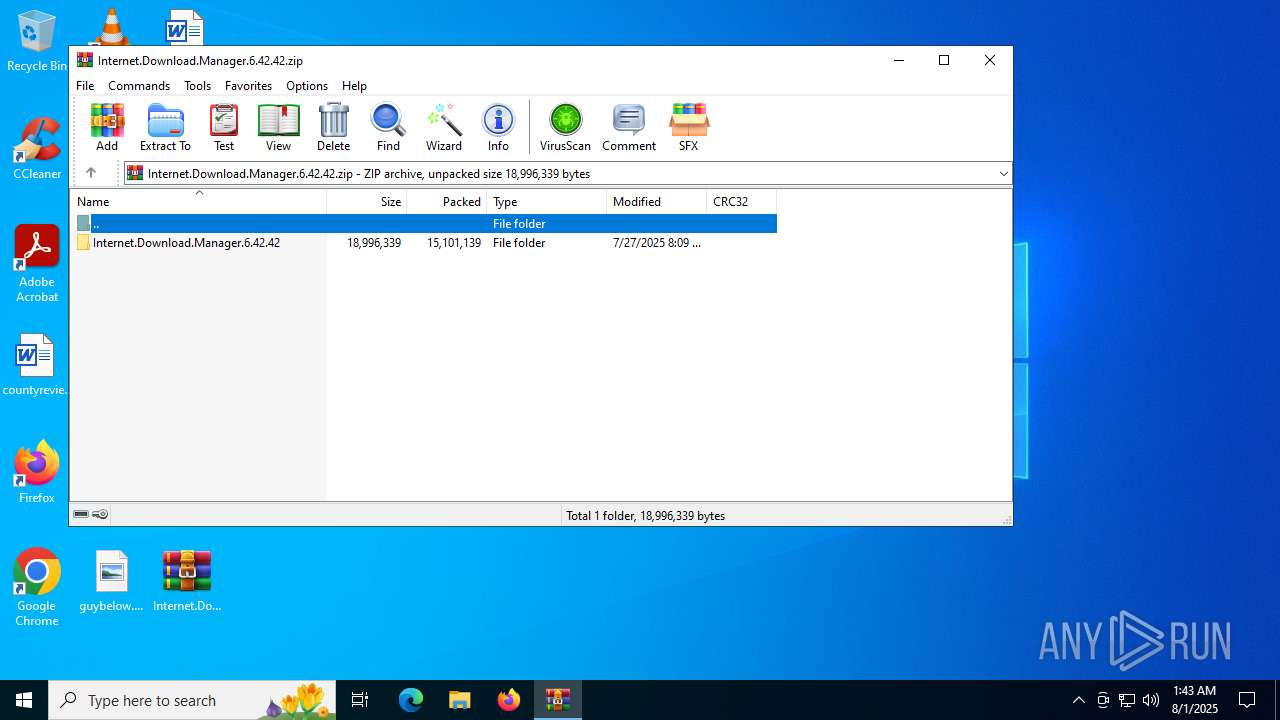
| File name: | Internet.Download.Manager.6.42.42.zip |
| Full analysis: | https://app.any.run/tasks/23bf8e1f-b15e-4f4d-af90-50dbe36a4b7a |
| Verdict: | Malicious activity |
| Analysis date: | August 01, 2025, 01:43:20 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=store |
| MD5: | 3F339D87D18C3DA925BFB17937DFC06A |
| SHA1: | 945110C404A694256827AF6470E81973B946EC22 |
| SHA256: | 86EB4CBABEED92E4244C37BA29B1FCACBFB09D768B78AFF1ECCEDE100B1C5DA5 |
| SSDEEP: | 98304:sNyDEdwM5PO2ZpaQQTkrcLYqjWK/ru6Kl7GscZKcPqBDdlLQldnPF8emWijo9ZL8:HMWGzApGdyzOC0GS5EN+vxt454tlnB |
MALICIOUS
Creates internet connection object (SCRIPT)
- wscript.exe (PID: 5548)
Opens an HTTP connection (SCRIPT)
- wscript.exe (PID: 5548)
Sends HTTP request (SCRIPT)
- wscript.exe (PID: 5548)
Deletes a file (SCRIPT)
- wscript.exe (PID: 5548)
SUSPICIOUS
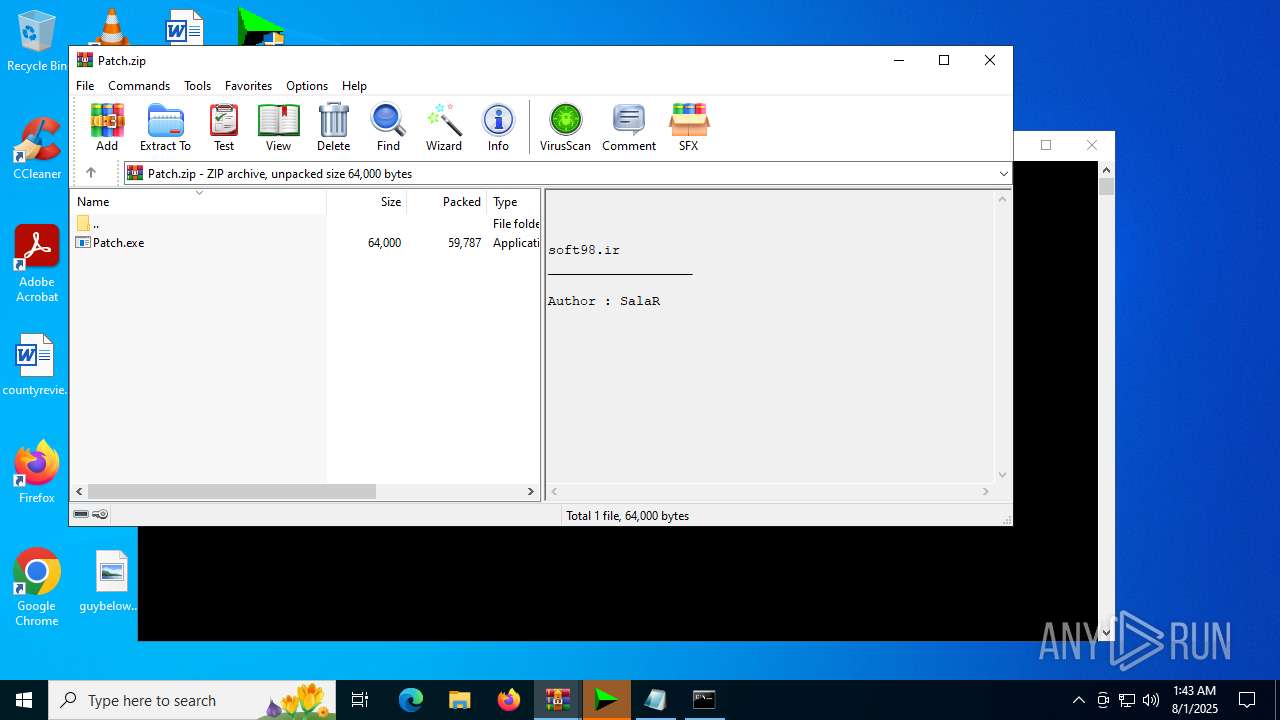
The process executes VB scripts
- Patch.exe (PID: 2112)
Starts NET.EXE to display or manage information about active sessions
- cmd.exe (PID: 7004)
- net.exe (PID: 7124)
- net.exe (PID: 5372)
- cmd.exe (PID: 4912)
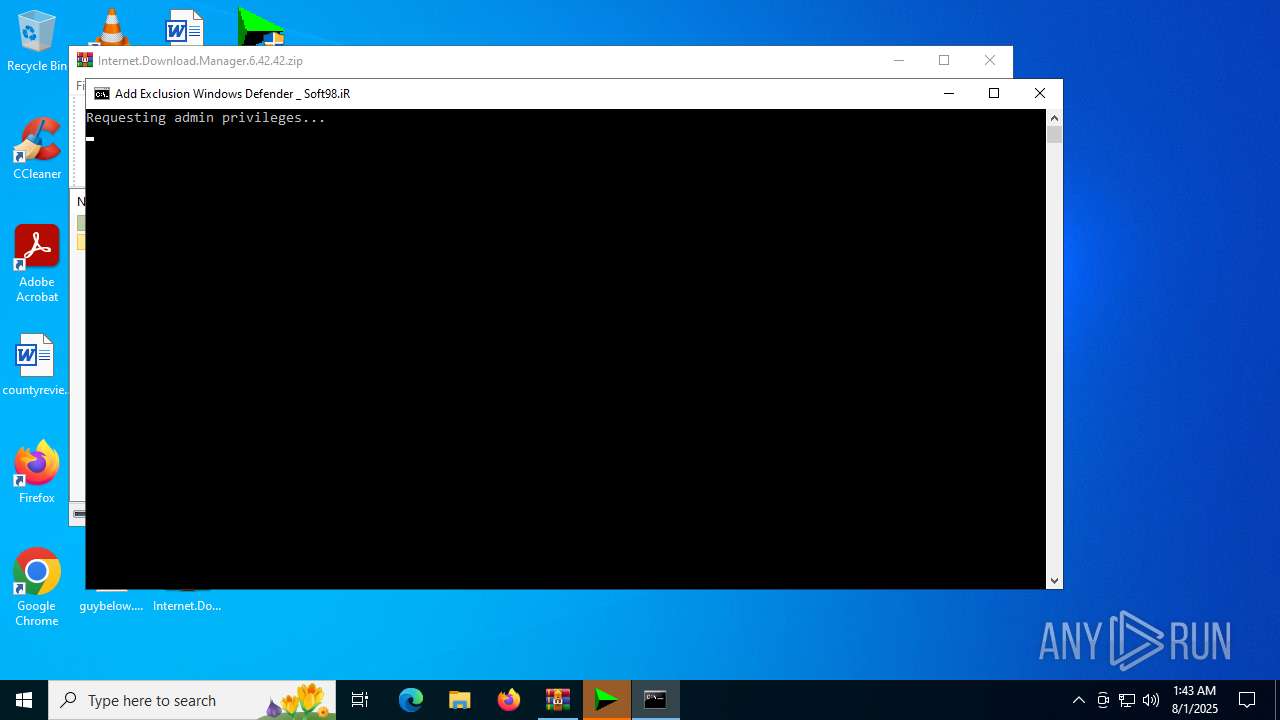
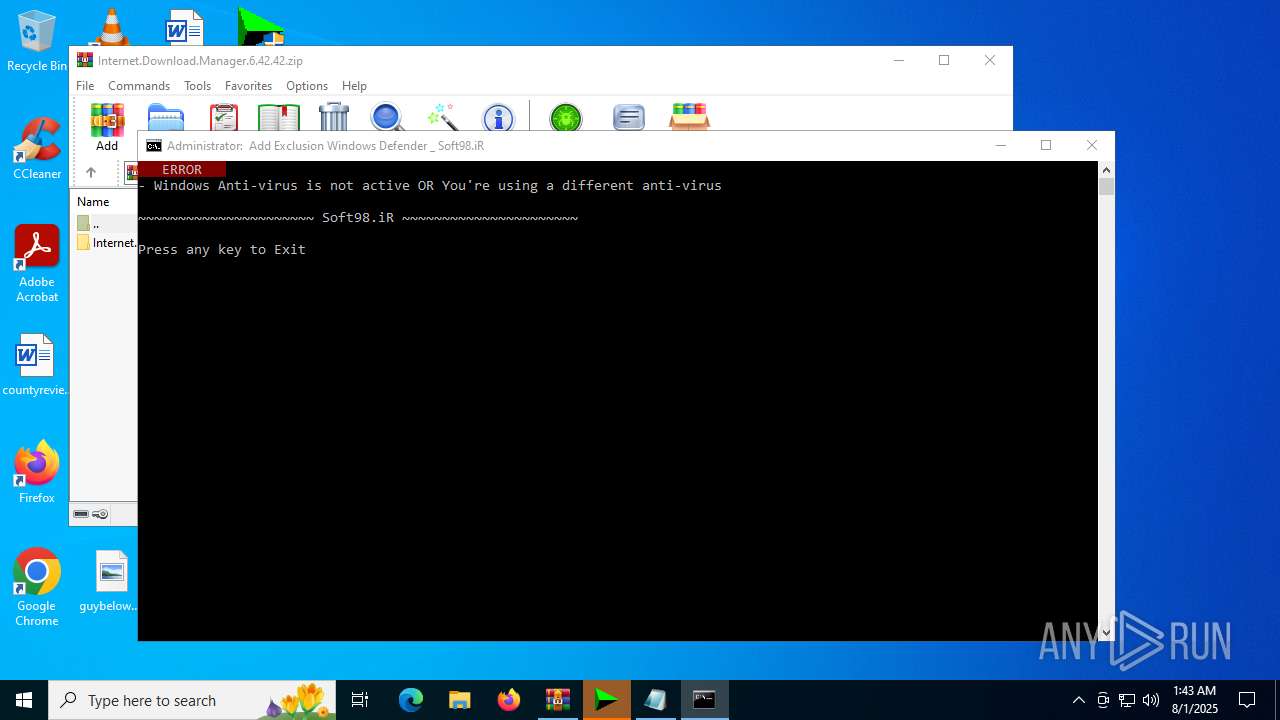
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 7004)
Starts process via Powershell
- powershell.exe (PID: 5928)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 5548)
Adds, changes, or deletes HTTP request header (SCRIPT)
- wscript.exe (PID: 5548)
Gets full path of the running script (SCRIPT)
- wscript.exe (PID: 5548)
Sets XML DOM element text (SCRIPT)
- wscript.exe (PID: 5548)
Starts CMD.EXE for commands execution
- powershell.exe (PID: 5928)
- cmd.exe (PID: 4912)
Found strings related to reading or modifying Windows Defender settings
- powershell.exe (PID: 5928)
Executing commands from ".cmd" file
- powershell.exe (PID: 5928)
Starts SC.EXE for service management
- cmd.exe (PID: 320)
Application launched itself
- cmd.exe (PID: 4912)
Windows service management via SC.EXE
- sc.exe (PID: 7032)
INFO
Manual execution by a user
- Patch.exe (PID: 2112)
- Patch.exe (PID: 6980)
- cmd.exe (PID: 7004)
- notepad.exe (PID: 1244)
- IDMGrHlp.exe (PID: 1880)
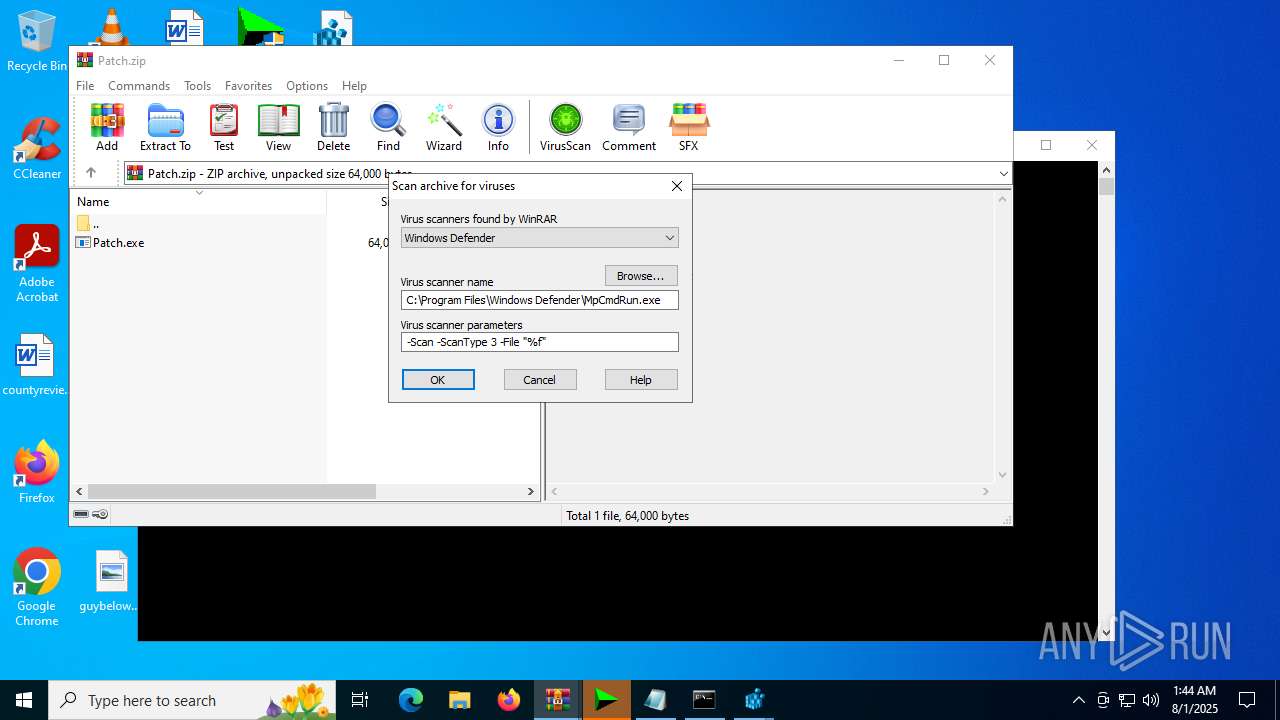
- WinRAR.exe (PID: 620)
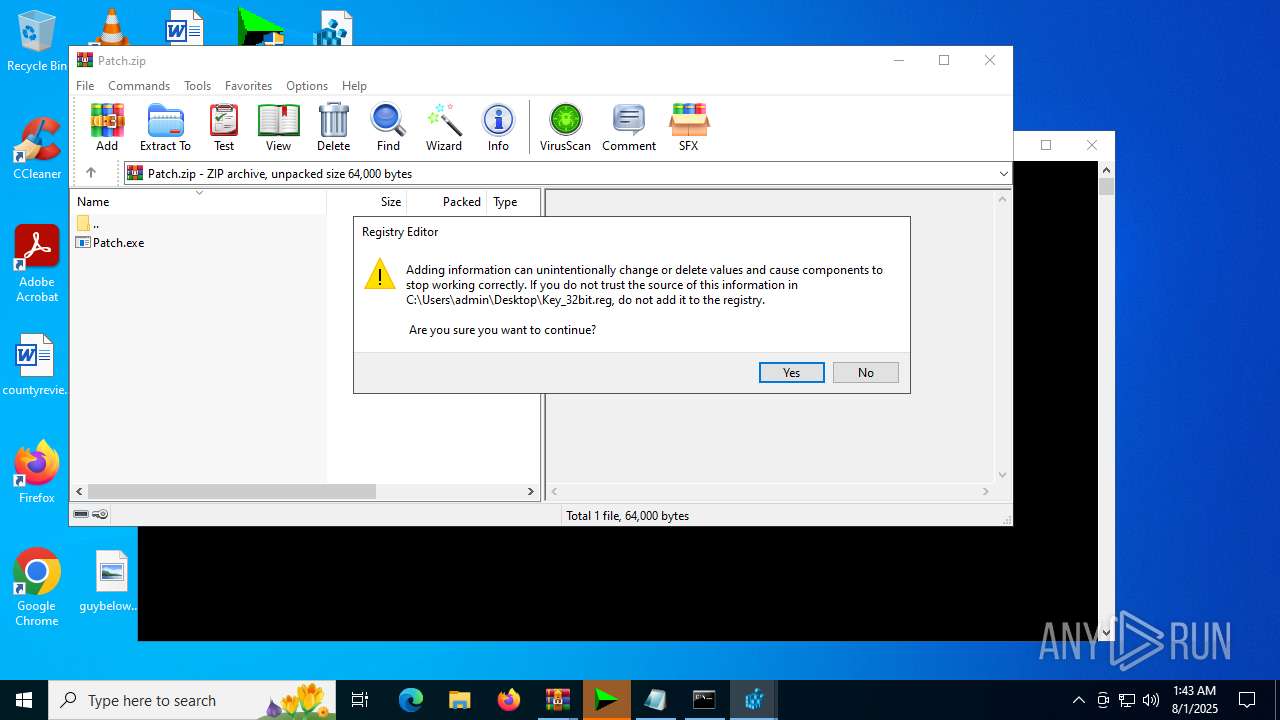
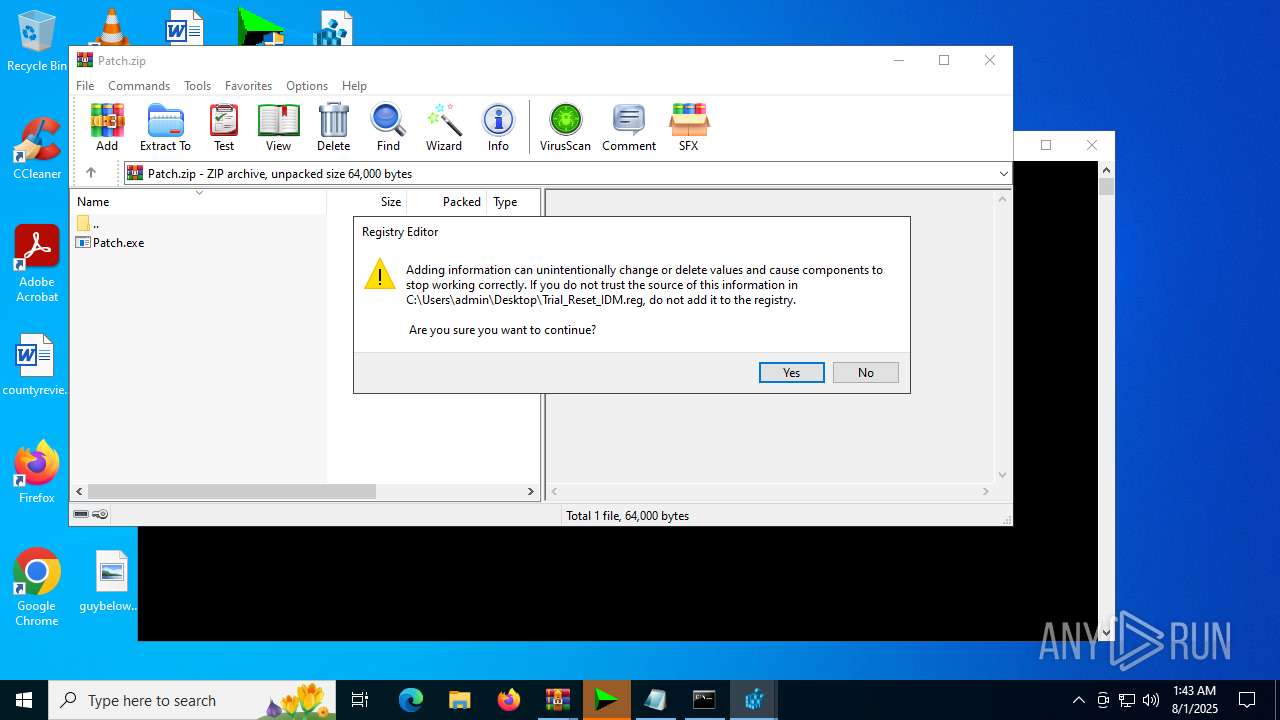
- regedit.exe (PID: 6452)
- regedit.exe (PID: 1100)
- regedit.exe (PID: 5240)
- regedit.exe (PID: 3396)
- regedit.exe (PID: 2964)
- regedit.exe (PID: 3644)
The sample compiled with english language support
- WinRAR.exe (PID: 1508)
Checks supported languages
- Patch.exe (PID: 2112)
- IDMGrHlp.exe (PID: 1880)
Reads the computer name
- Patch.exe (PID: 2112)
Create files in a temporary directory
- Patch.exe (PID: 2112)
Creates files or folders in the user directory
- Patch.exe (PID: 2112)
Reads security settings of Internet Explorer
- notepad.exe (PID: 1244)
Checks operating system version
- cmd.exe (PID: 4912)
Checks proxy server information
- wscript.exe (PID: 5548)
- slui.exe (PID: 1800)
Reads the software policy settings
- slui.exe (PID: 1800)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2025:07:27 16:09:30 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | Internet.Download.Manager.6.42.42/ |
Total processes
163
Monitored processes
27
Malicious processes
2
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 320 | C:\WINDOWS\system32\cmd.exe /c sc query WinDefend | find "STATE" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 620 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\Patch.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 1100 | "C:\Windows\regedit.exe" C:\Users\admin\Desktop\Key_64bit.reg | C:\Windows\regedit.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Editor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1244 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\Serial.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1508 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\Internet.Download.Manager.6.42.42.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 1800 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1880 | "C:\Users\admin\Desktop\IDMGrHlp.exe" | C:\Users\admin\Desktop\IDMGrHlp.exe | — | explorer.exe | |||||||||||
User: admin Company: Tonec Inc. Integrity Level: MEDIUM Description: Internet Download Manager module Exit code: 0 Version: 6, 35, 9, 1 Modules
| |||||||||||||||
| 2112 | "C:\Users\admin\Desktop\Patch.exe" | C:\Users\admin\Desktop\Patch.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 2964 | "C:\Windows\regedit.exe" C:\Users\admin\Desktop\Trial_Reset_IDM.reg | C:\Windows\regedit.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Editor Exit code: 3221226540 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3396 | "C:\Windows\regedit.exe" C:\Users\admin\Desktop\Key_32bit.reg | C:\Windows\regedit.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Editor Exit code: 3221226540 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
16 456
Read events
16 420
Write events
36
Delete events
0
Modification events
| (PID) Process: | (1508) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1508) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1508) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (1508) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (1508) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (1508) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\Internet.Download.Manager.6.42.42.zip | |||
| (PID) Process: | (1508) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1508) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1508) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1508) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
0
Suspicious files
1
Text files
6
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2112 | Patch.exe | C:\Users\admin\AppData\Local\Temp\CRK_UPDT.vbs | text | |
MD5:B91C1157D6F1E605CC965D092551B307 | SHA256:92FE72CCEB630C7EFF3B2D3BED9C6969F53E5B9DFF1F481888754E59B3C76AB7 | |||
| 2112 | Patch.exe | C:\Users\admin\AppData\Roaming\WinRAR\rarreg.key | text | |
MD5:CC72935D4E4BD54DB0ED6BF4701FDC9E | SHA256:2ABE74BB821BA46762AFDB23EAC95454EC7155D5379E3CD56385D900C34CB1BF | |||
| 5928 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_sgrkamdf.j3c.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5548 | wscript.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\E4DJRUXW\JW71I8Q1.xml | text | |
MD5:4578E6452BA4B6DB8F26638BEF27CD85 | SHA256:6F03D6B5FC6A2CA8F3B8683848C0F16A14ABF316156AECD7606D047A651CD3F6 | |||
| 5928 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:4E11E0164898650C23B98C34689DE261 | SHA256:73CB92072D25A71D45CC41101C10B182139A2F5CE52E1ABEC0F7909A34F161FB | |||
| 2112 | Patch.exe | C:\Users\admin\AppData\Local\Temp\IDM_UPDT.vbs | text | |
MD5:B91C1157D6F1E605CC965D092551B307 | SHA256:92FE72CCEB630C7EFF3B2D3BED9C6969F53E5B9DFF1F481888754E59B3C76AB7 | |||
| 5928 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_2bfzigrf.bji.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
22
DNS requests
9
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | POST | 500 | 40.91.76.224:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1636 | RUXIMICS.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2940 | svchost.exe | GET | 200 | 69.192.161.44:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
— | — | POST | 500 | 20.83.72.98:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1636 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5944 | MoUsoCoreWorker.exe | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1636 | RUXIMICS.exe | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5548 | wscript.exe | 188.114.97.3:443 | idm.0dy.ir | CLOUDFLARENET | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
idm.0dy.ir |
| unknown |
self.events.data.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |