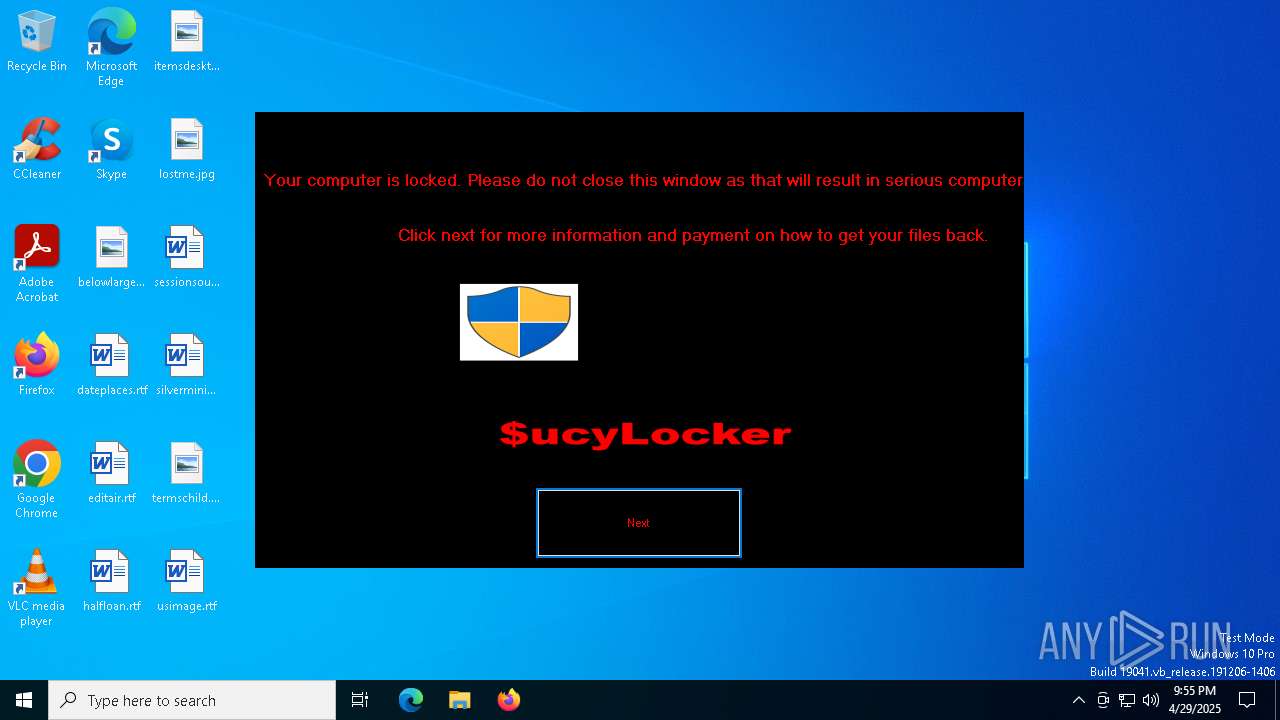
| File name: | $uckyLocker.exe |
| Full analysis: | https://app.any.run/tasks/f2b855f0-bce8-4fe8-947f-5b81409c5326 |
| Verdict: | Malicious activity |
| Analysis date: | April 29, 2025, 21:55:16 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | C850F942CCF6E45230169CC4BD9EB5C8 |
| SHA1: | 51C647E2B150E781BD1910CAC4061A2CEE1DAF89 |
| SHA256: | 86E0EAC8C5CE70C4B839EF18AF5231B5F92E292B81E440193CDBDC7ED108049F |
| SSDEEP: | 6144:Av+lDAAB6fm00rx/Qdd1QkfRLT+vLtls6LEmynPsVpw/pcPk19V:RdAAB6Mk1HfRLqzPlLEmynPsVpwBTV |
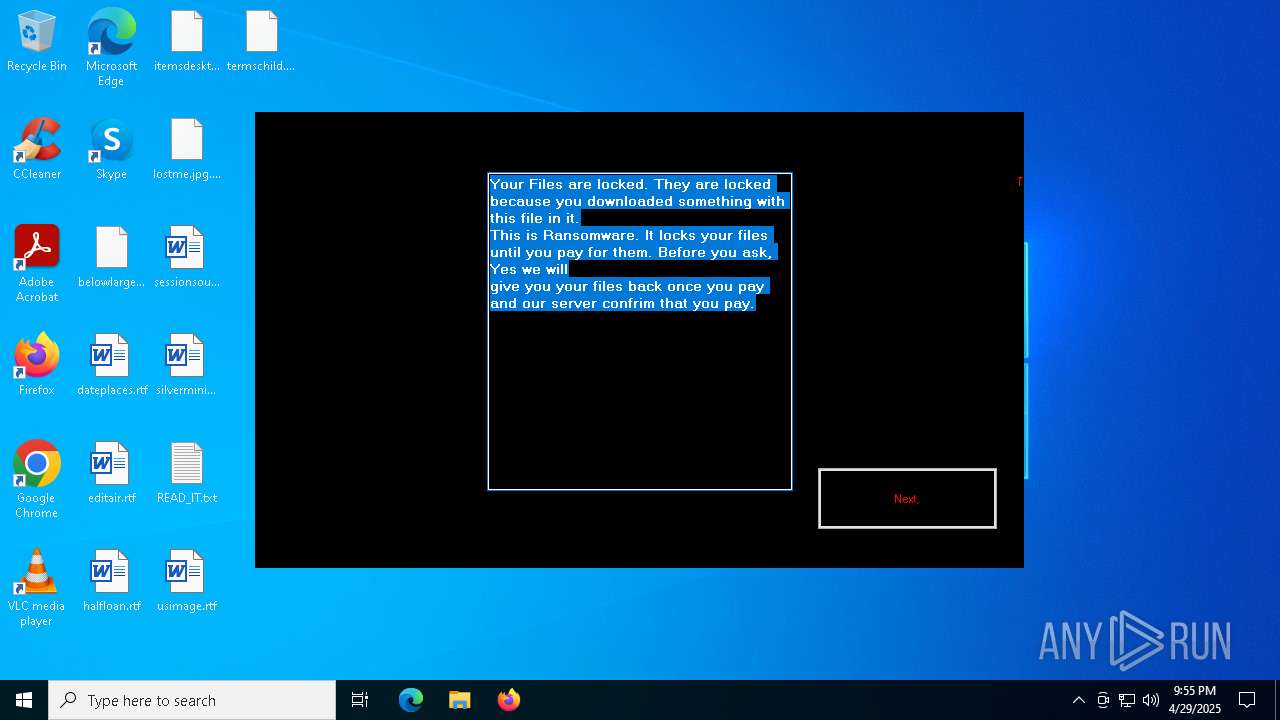
MALICIOUS
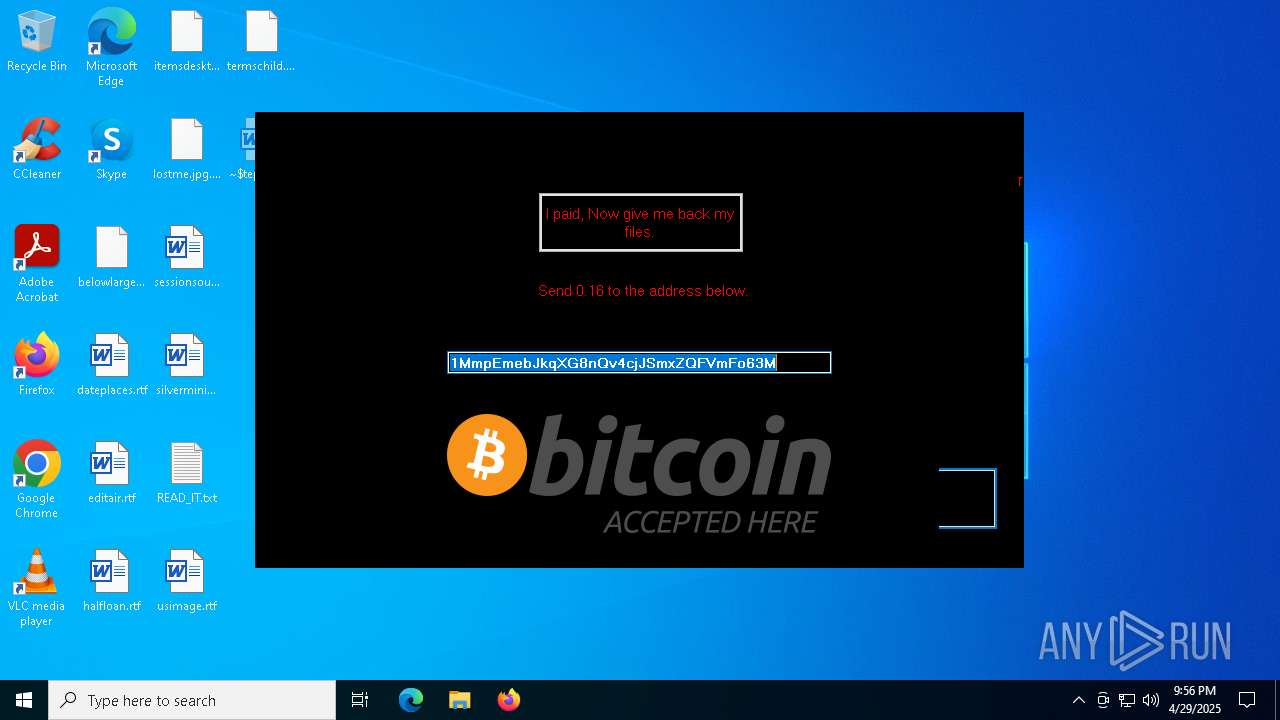
Disables task manager
- $uckyLocker.exe (PID: 6620)
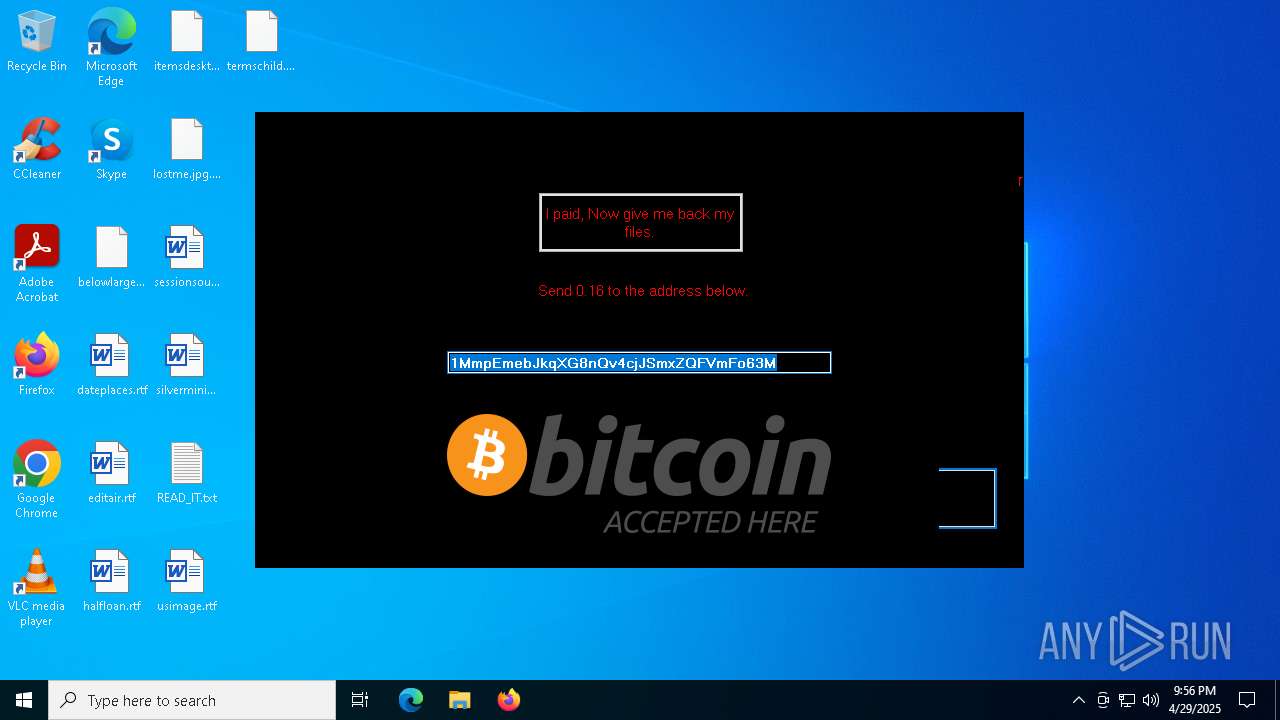
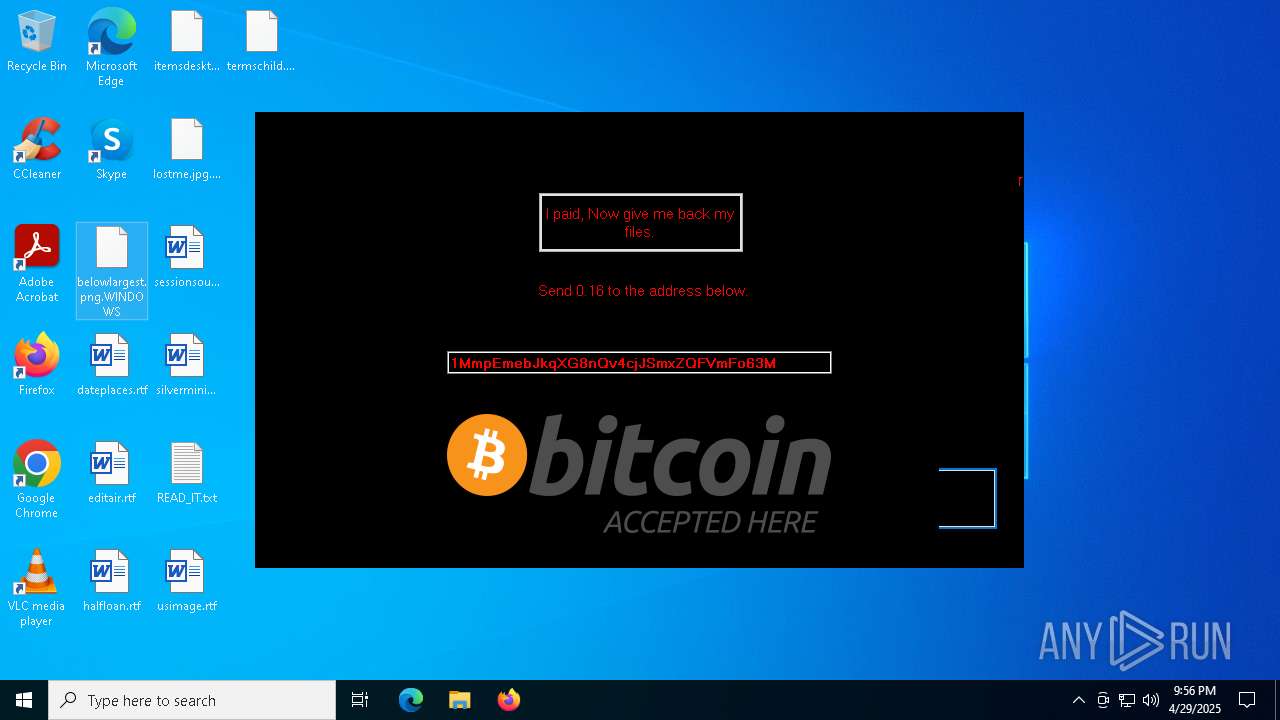
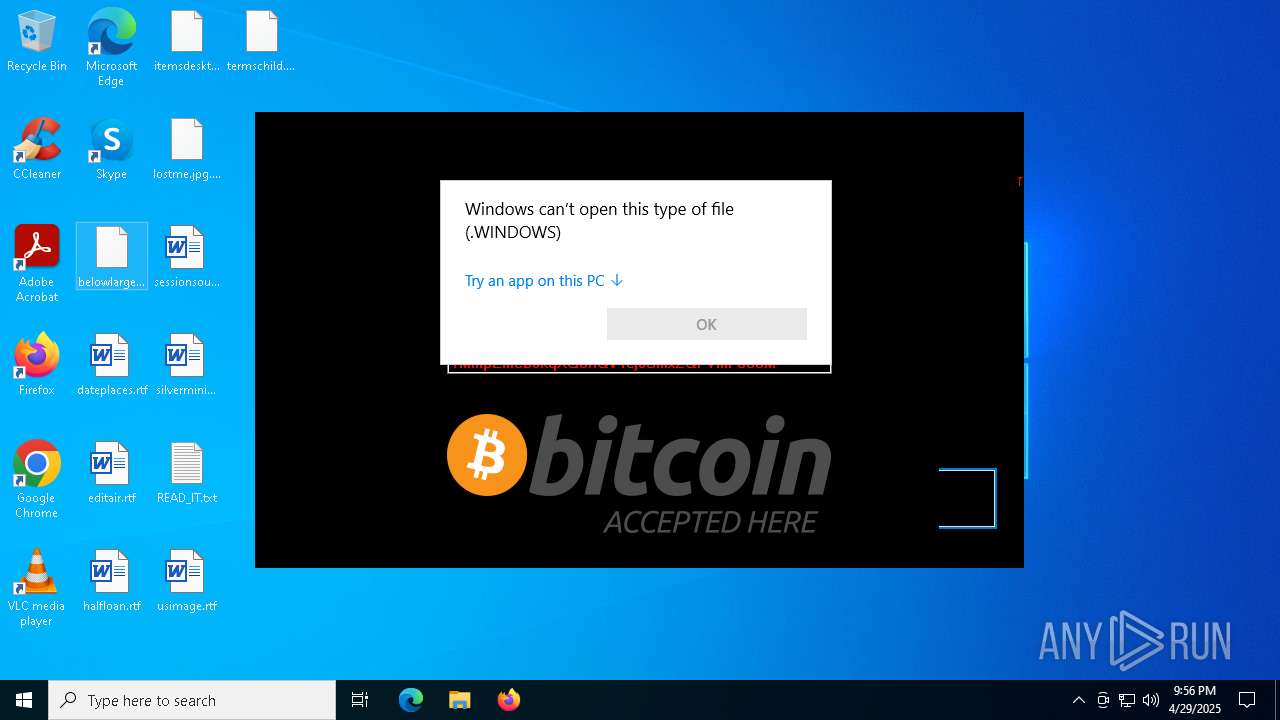
Renames files like ransomware
- $uckyLocker.exe (PID: 6620)
SUSPICIOUS
Changes the desktop background image
- $uckyLocker.exe (PID: 6620)
INFO
Reads the computer name
- $uckyLocker.exe (PID: 6620)
Reads the machine GUID from the registry
- $uckyLocker.exe (PID: 6620)
Checks supported languages
- $uckyLocker.exe (PID: 6620)
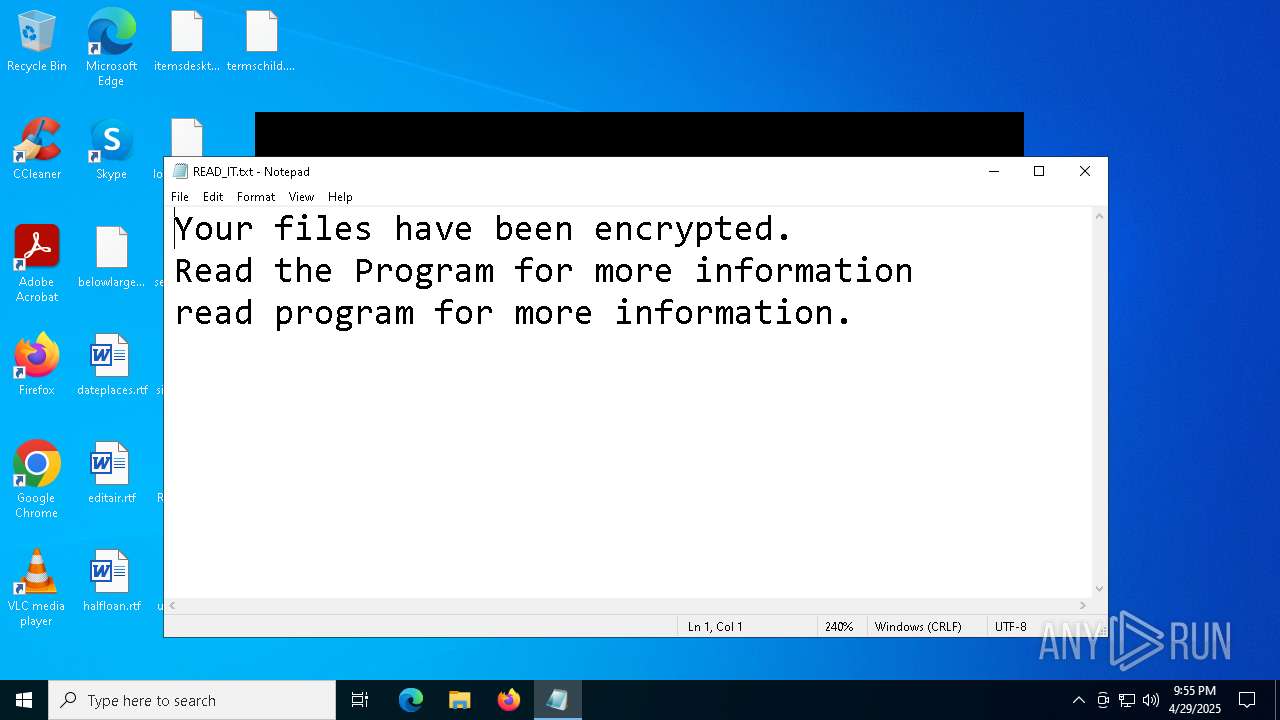
Manual execution by a user
- notepad.exe (PID: 2852)
- WINWORD.EXE (PID: 2136)
Reads security settings of Internet Explorer
- notepad.exe (PID: 2852)
Reads Microsoft Office registry keys
- OpenWith.exe (PID: 1188)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (82.9) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (5.1) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:06:02 15:44:57+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 394752 |
| InitializedDataSize: | 29184 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x62586 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | Loader |
| FileVersion: | 1.0.0.0 |
| InternalName: | VapeHacksLoader.exe |
| LegalCopyright: | Copyright © 2017 |
| LegalTrademarks: | - |
| OriginalFileName: | VapeHacksLoader.exe |
| ProductName: | Loader-Private |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
141
Monitored processes
8
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1188 | C:\WINDOWS\system32\OpenWith.exe -Embedding | C:\Windows\System32\OpenWith.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
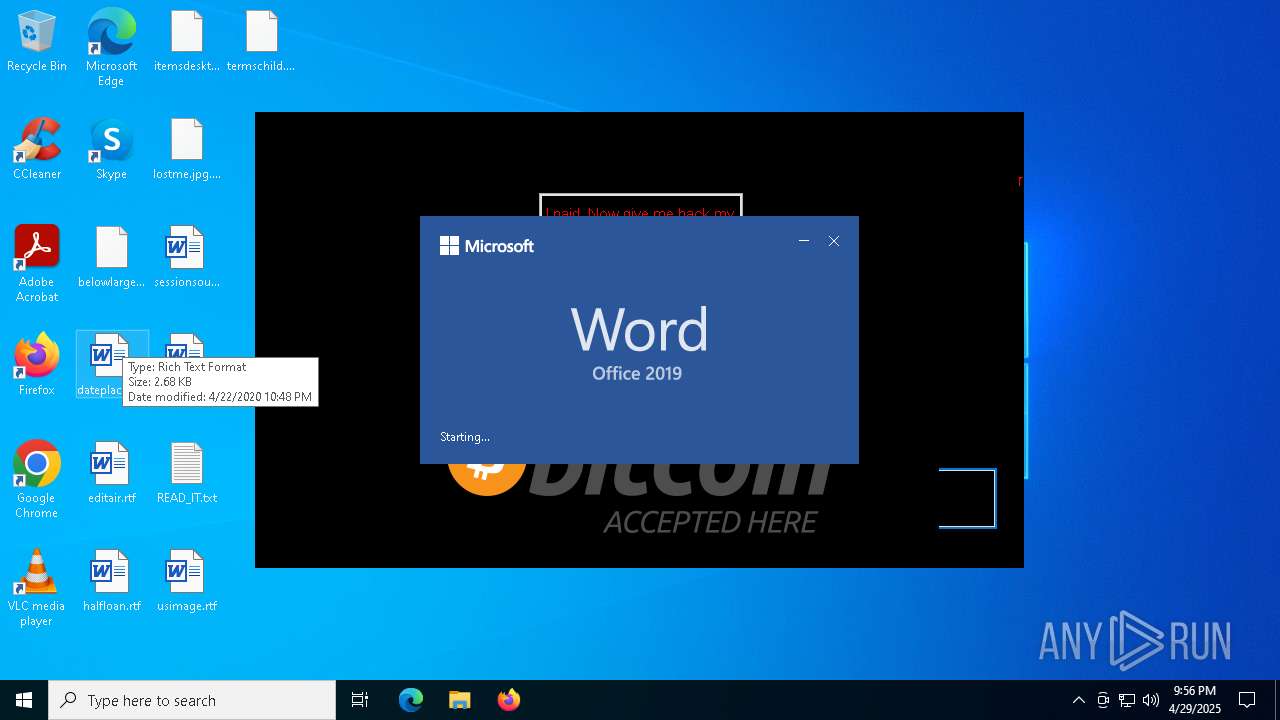
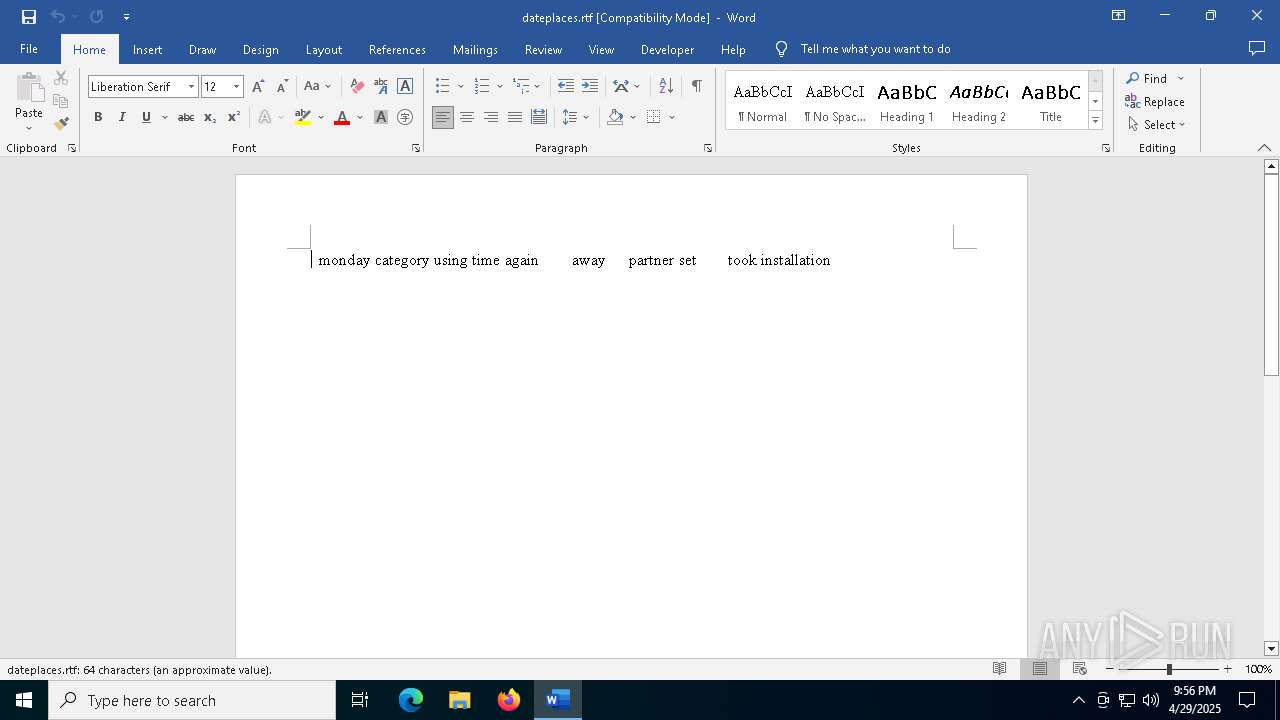
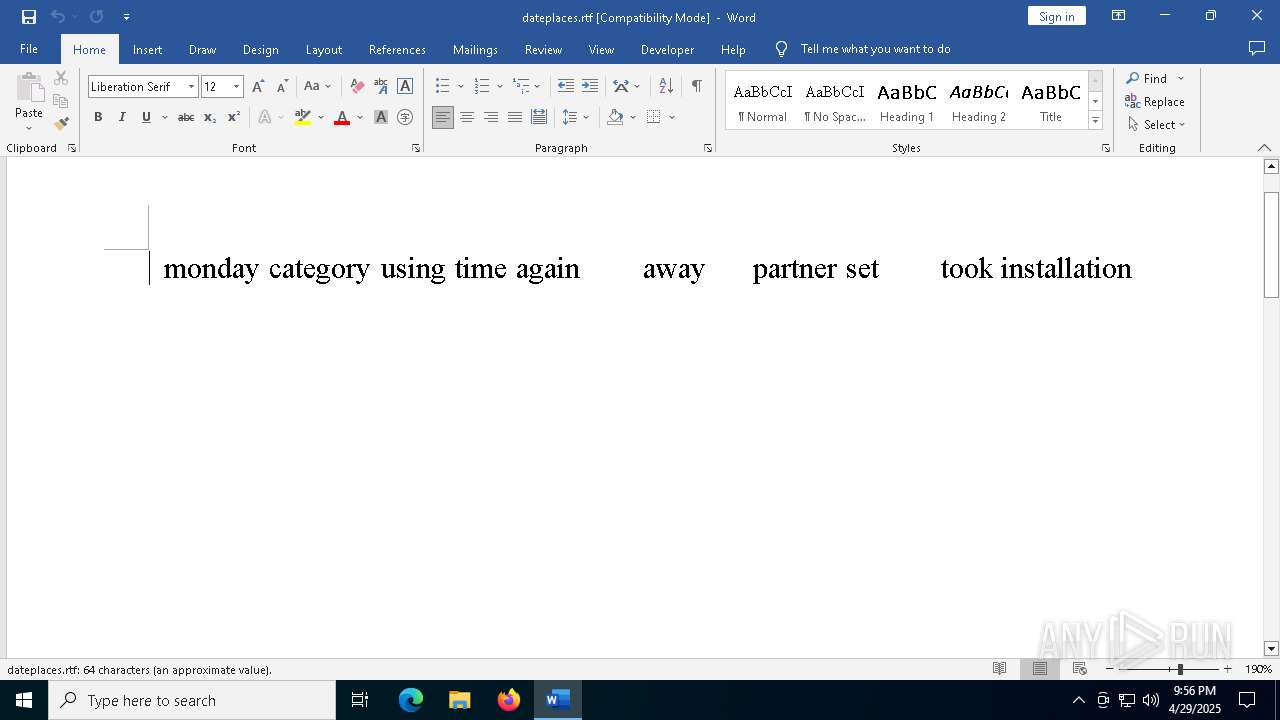
| 2136 | "C:\Program Files\Microsoft Office\Root\Office16\WINWORD.EXE" /n "C:\Users\admin\Desktop\dateplaces.rtf" /o "" | C:\Program Files\Microsoft Office\root\Office16\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 16.0.16026.20146 Modules
| |||||||||||||||
| 2384 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
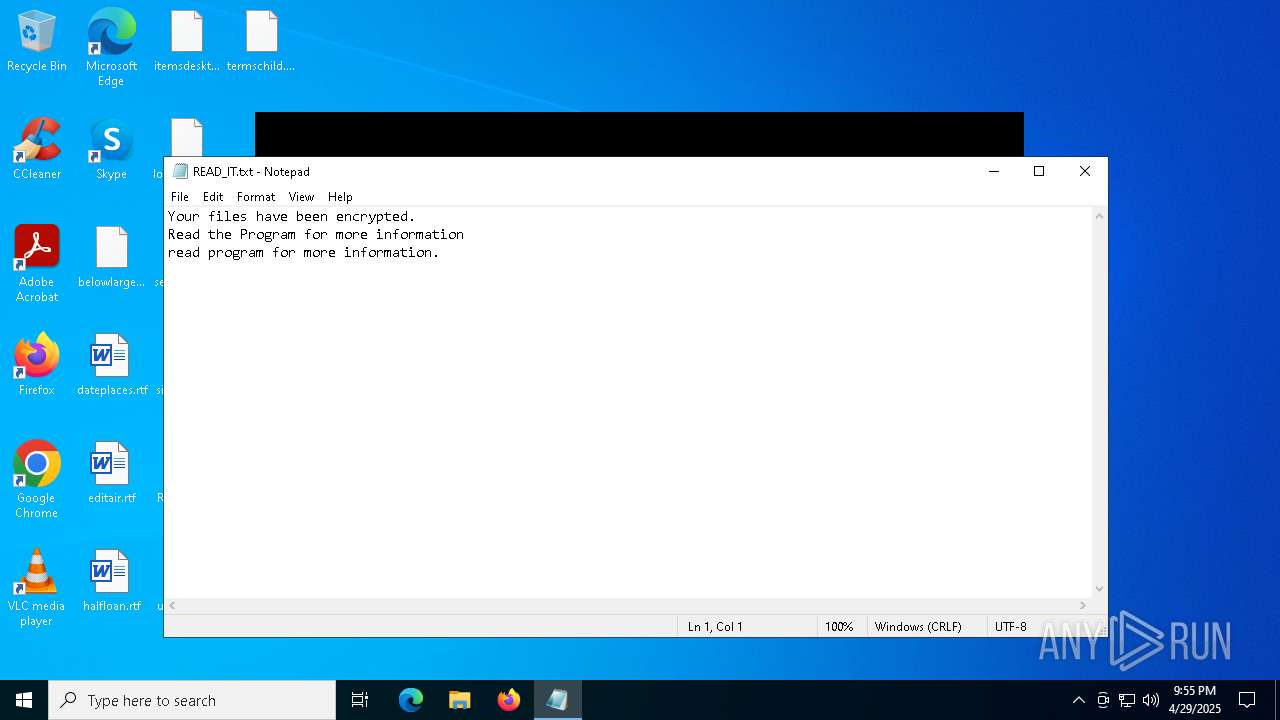
| 2852 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\READ_IT.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5508 | "C:\Program Files\Microsoft Office\root\VFS\ProgramFilesCommonX64\Microsoft Shared\OFFICE16\ai.exe" "6E175716-CB52-473D-A681-C0ACA0EC7B78" "88EFB99E-440F-4E3B-9623-2E73B3BF8E61" "2136" | C:\Program Files\Microsoft Office\root\VFS\ProgramFilesCommonX64\Microsoft Shared\OFFICE16\ai.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Artificial Intelligence (AI) Host for the Microsoft® Windows® Operating System and Platform x64. Exit code: 0 Version: 0.12.2.0 Modules
| |||||||||||||||
| 5972 | "C:\Users\admin\AppData\Local\Temp\$uckyLocker.exe" | C:\Users\admin\AppData\Local\Temp\$uckyLocker.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Loader Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
| 5972 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6620 | "C:\Users\admin\AppData\Local\Temp\$uckyLocker.exe" | C:\Users\admin\AppData\Local\Temp\$uckyLocker.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Loader Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
10 283
Read events
10 179
Write events
82
Delete events
22
Modification events
| (PID) Process: | (6620) $uckyLocker.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | DisableTaskMgr |
Value: 1 | |||
| (PID) Process: | (6620) $uckyLocker.exe | Key: | HKEY_CURRENT_USER\Control Panel\Desktop |
| Operation: | write | Name: | Wallpaper |
Value: 0 | |||
| (PID) Process: | (2136) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\Common\ClientTelemetry\Sampling |
| Operation: | write | Name: | 0 |
Value: 017012000000001000B24E9A3E02000000000000000600000000000000 | |||
| (PID) Process: | (2136) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | xz) |
Value: 787A29005808000001000000000000008D78758151B9DB0100000000 | |||
| (PID) Process: | (2136) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 2{) |
Value: 327B29005808000004000000000000008C40A08151B9DB018C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2136) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\Common\CrashPersistence\WINWORD\2136 |
| Operation: | write | Name: | 0 |
Value: 0B0E10B789EB5ECD8C02498A760F2B8CCD60CB2300468FBBAF8B98AAEEED016A04102400449A7D64B29D01008500A907556E6B6E6F776EC906022222CA0DC2190000C91003783634C511D810D2120B770069006E0077006F00720064002E00650078006500C51620C517808004C91808323231322D44656300 | |||
| (PID) Process: | (2136) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | en-US |
Value: 2 | |||
| (PID) Process: | (2136) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | de-de |
Value: 2 | |||
| (PID) Process: | (2136) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | fr-fr |
Value: 2 | |||
| (PID) Process: | (2136) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | es-es |
Value: 2 | |||
Executable files
1
Suspicious files
29
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
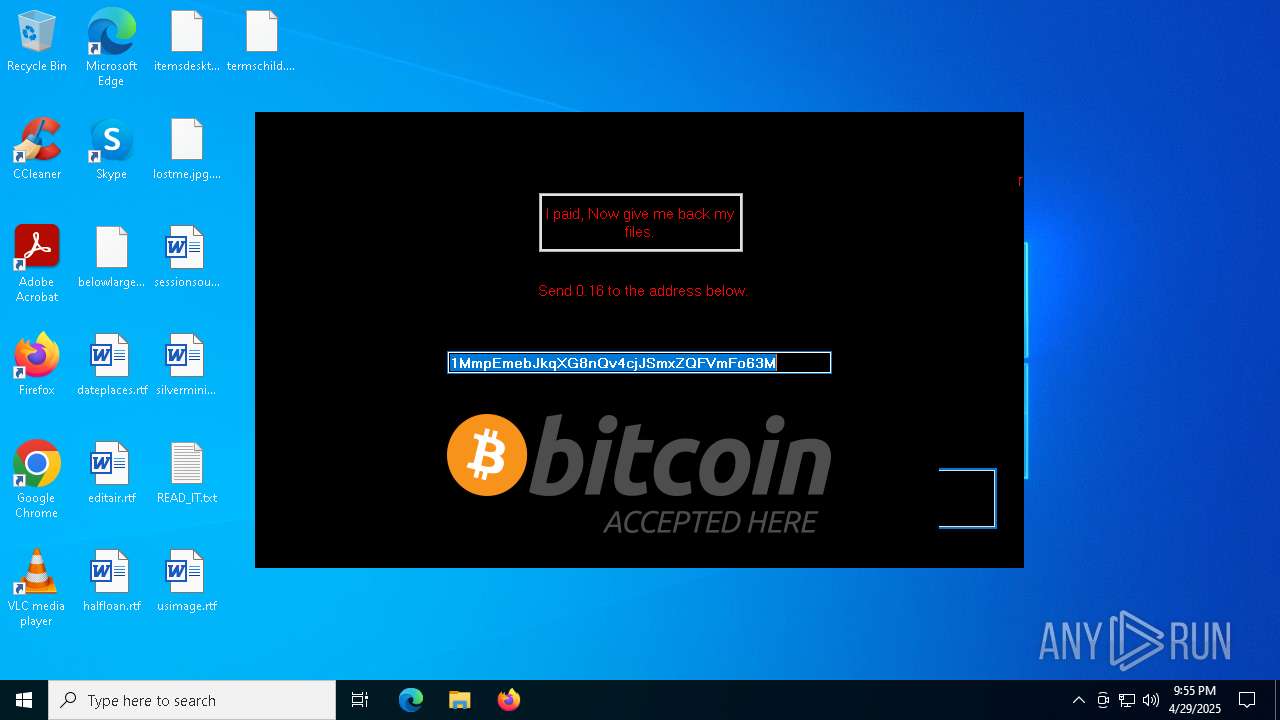
| 6620 | $uckyLocker.exe | C:\Users\admin\Desktop\belowlargest.png.WINDOWS | binary | |
MD5:27C24DB7C6DC096B4B9BC5E8DD8DCCC4 | SHA256:71666D1785C6A2057884DD8ACAA1A9CB6502002B17C434CB28AAED3896C27735 | |||
| 6620 | $uckyLocker.exe | C:\Users\admin\Desktop\lostme.jpg.WINDOWS | binary | |
MD5:866444244A3CCD8605D0478D127834CC | SHA256:D7A1B7E0F7CF95A316983C61A7D2359C81014E457753D8EC76F430138BC40619 | |||
| 6620 | $uckyLocker.exe | C:\Users\admin\Desktop\itemsdesktop.jpg.WINDOWS | binary | |
MD5:AED9C3EA123E3D4F19FB170038A881E6 | SHA256:A868FF32BC257470E3397D8D89DB6CB3952AC52C0D748951E120C9207E69BCD5 | |||
| 2136 | WINWORD.EXE | C:\Users\admin\Desktop\~$teplaces.rtf | binary | |
MD5:78AA8629C0008BE564F286A8DC336569 | SHA256:F393A5D996F401B83F74E787156516B273674597FAD2F5C98B37440C349AA1FD | |||
| 6620 | $uckyLocker.exe | C:\Users\admin\Desktop\termschild.jpg | binary | |
MD5:8CA1ED64C80770181C62F009EC059A6B | SHA256:31C8A67DA8CB0B5DDE20F4AD3F1BC2AFDB0539E594B951FA9EAC3C8988A91DCC | |||
| 2136 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\TokenBroker\Cache\089d66ba04a8cec4bdc5267f42f39cf84278bb67.tbres | binary | |
MD5:2F042B52B0744705ABD6212A57725077 | SHA256:EDF366BD0143115FDE2ABD6AF53E363105A0D14DE154045EDDF71A417A264AB5 | |||
| 2136 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Content.Word\~WRS{119123FE-AC34-4A99-AD60-F3D3BA023535}.tmp | binary | |
MD5:830FBF83999E052538EAF156AB6ECB17 | SHA256:D5098A2CEAE815DB29CD53C76F85240C95DC4D2E3FEDDD71D628617064C29869 | |||
| 2136 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:0C9B686F2D54329316ED914F7C95B86D | SHA256:2E51D66344633181715F6D1614EC72BECE81716154ACC7B0BA692C531E82A163 | |||
| 2136 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Diagnostics\WINWORD\App1745963765390191700_5EEB89B7-8CCD-4902-8A76-0F2B8CCD60CB.log | — | |
MD5:— | SHA256:— | |||
| 2136 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\49AE4A7D.tmp | binary | |
MD5:EF1FA8818BBB17FAEC3C7350D622F2D9 | SHA256:12379444D12FCDEC499D96DD46FFBB3B05EACDD868C461037BC38E753F9BF334 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
48
DNS requests
21
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6544 | svchost.exe | 20.190.160.66:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
2112 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6476 | SIHClient.exe | 52.149.20.212:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6476 | SIHClient.exe | 20.242.39.171:443 | fe3cr.delivery.mp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
171.39.242.20.in-addr.arpa |
| unknown |
4.8.2.0.0.0.0.0.0.0.0.0.0.0.0.0.2.0.0.0.2.0.c.0.0.3.0.1.3.0.6.2.ip6.arpa |
| unknown |
officeclient.microsoft.com |
| whitelisted |
roaming.officeapps.live.com |
| whitelisted |