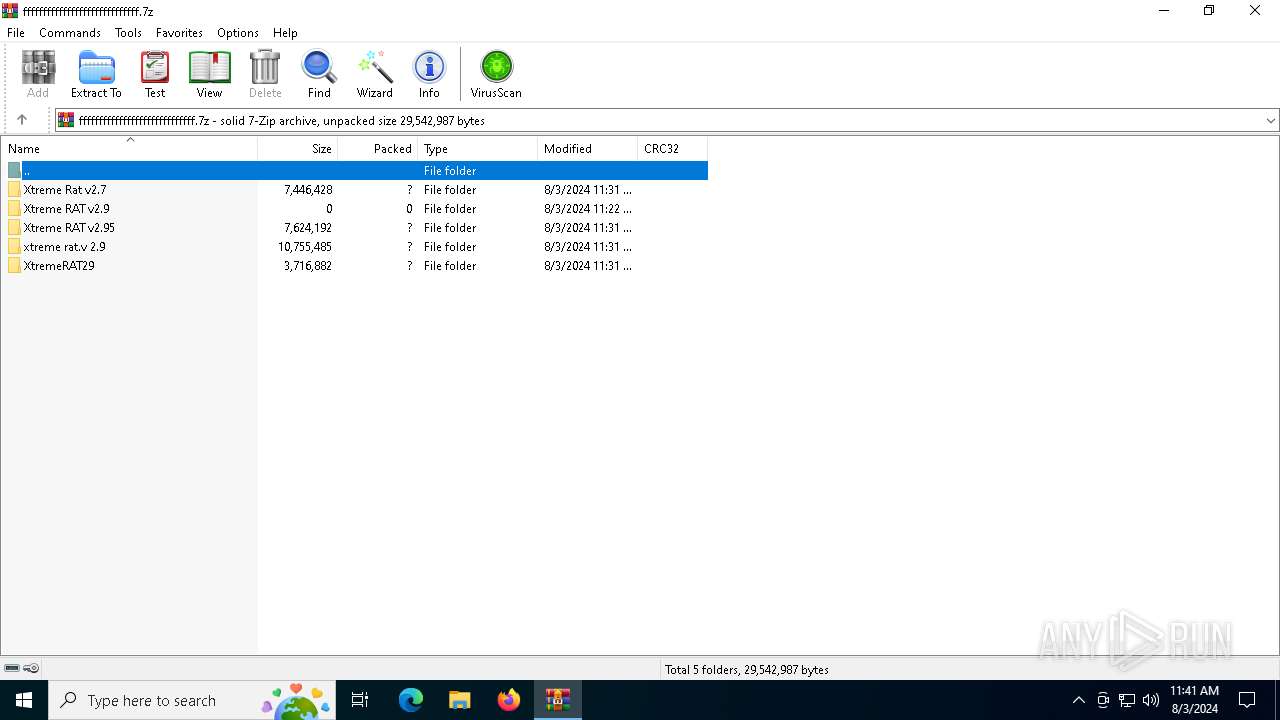
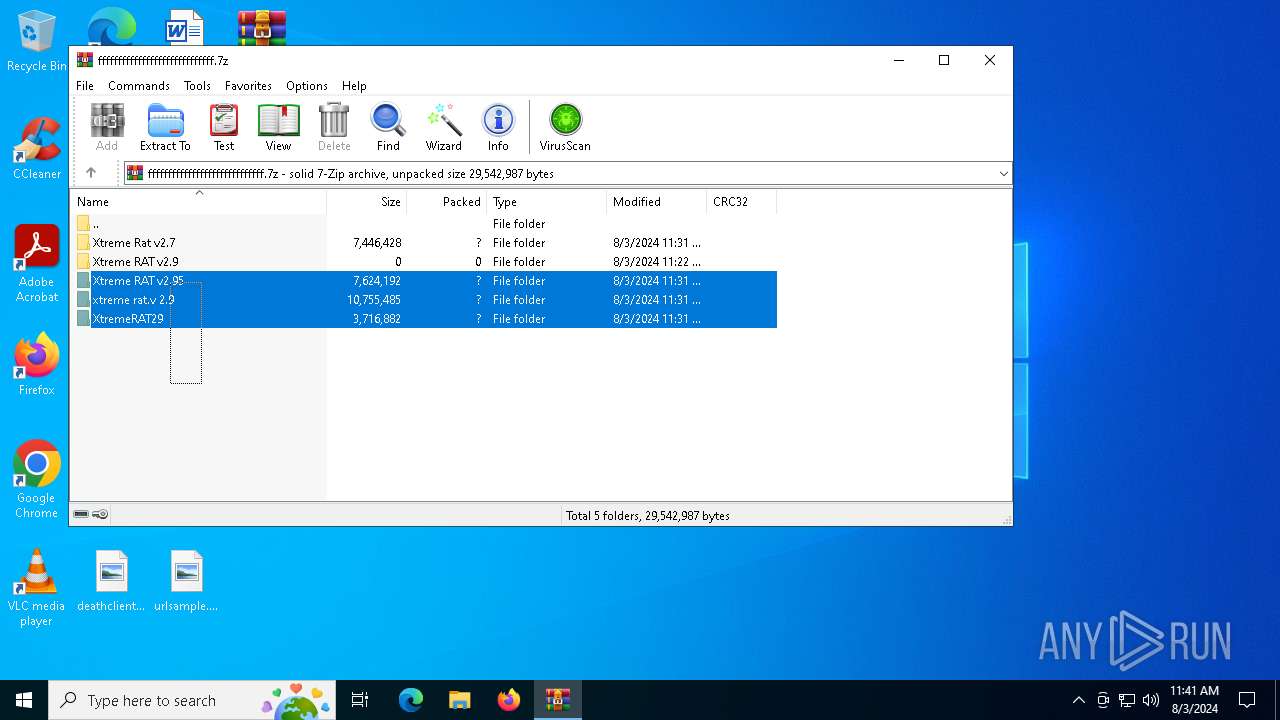
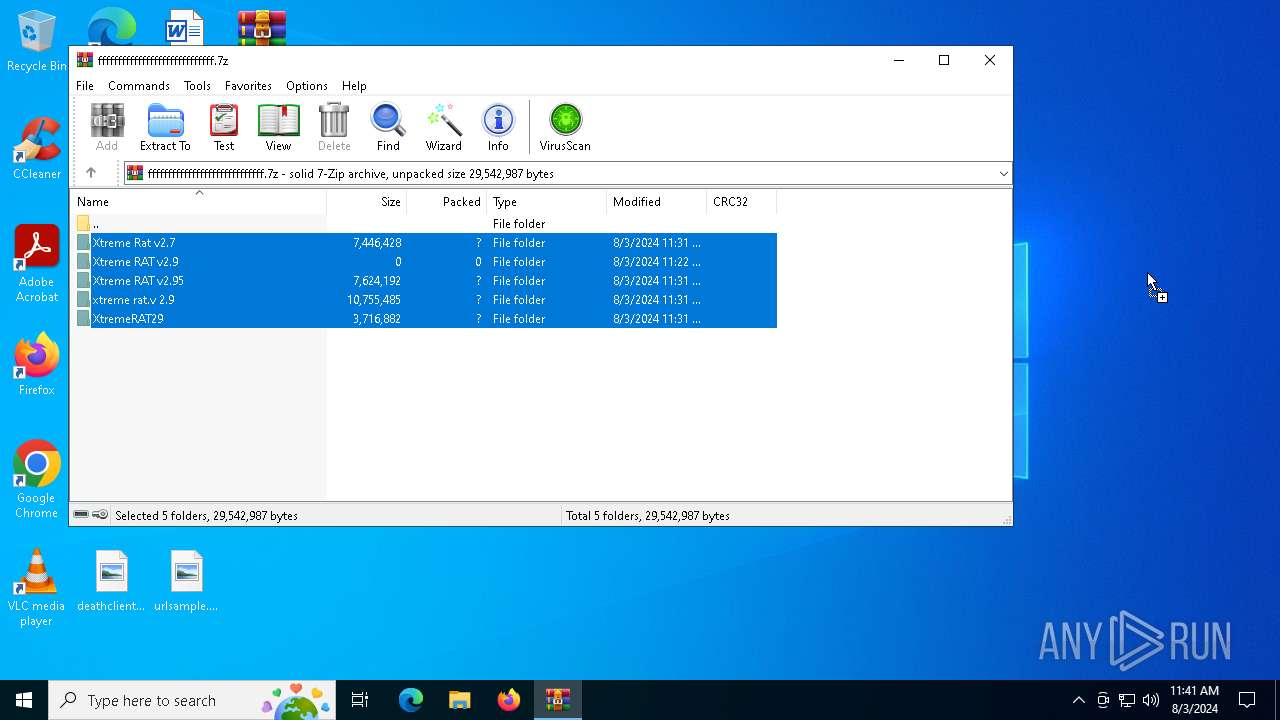
| File name: | fffffffffffffffffffffffffffff.7z |
| Full analysis: | https://app.any.run/tasks/704fb003-2f7f-47c8-8d36-c23728feeec7 |
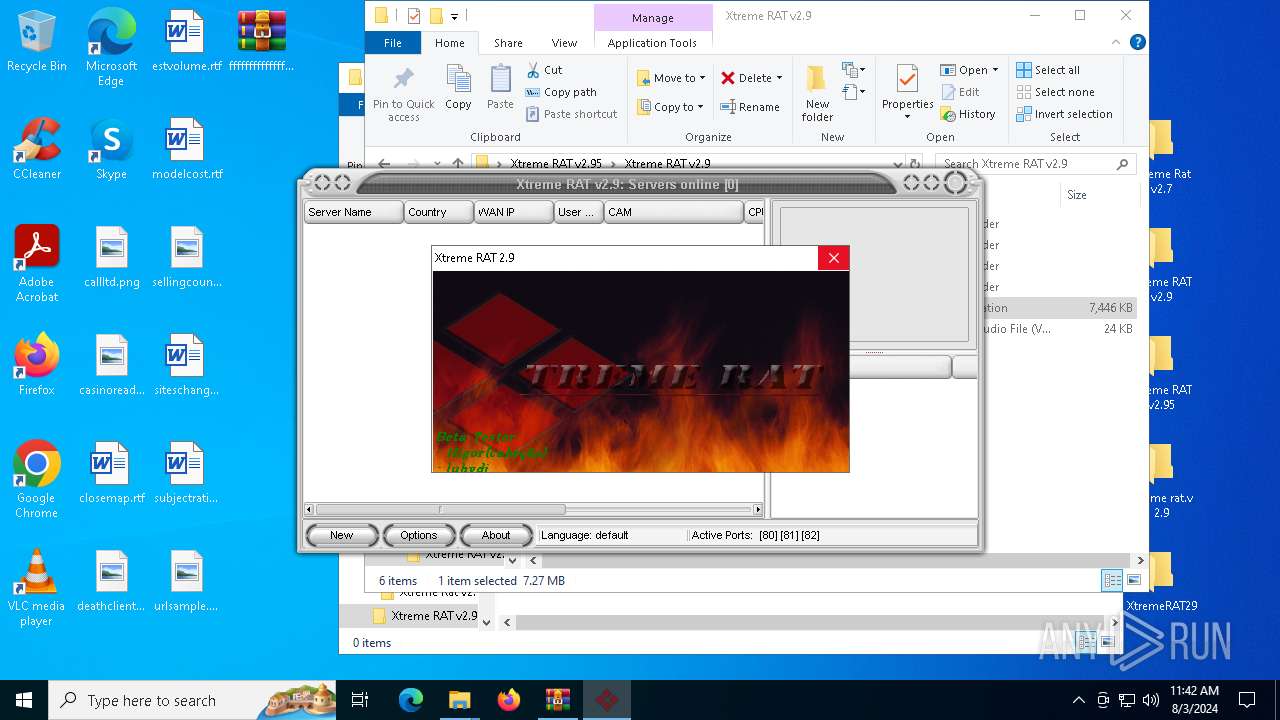
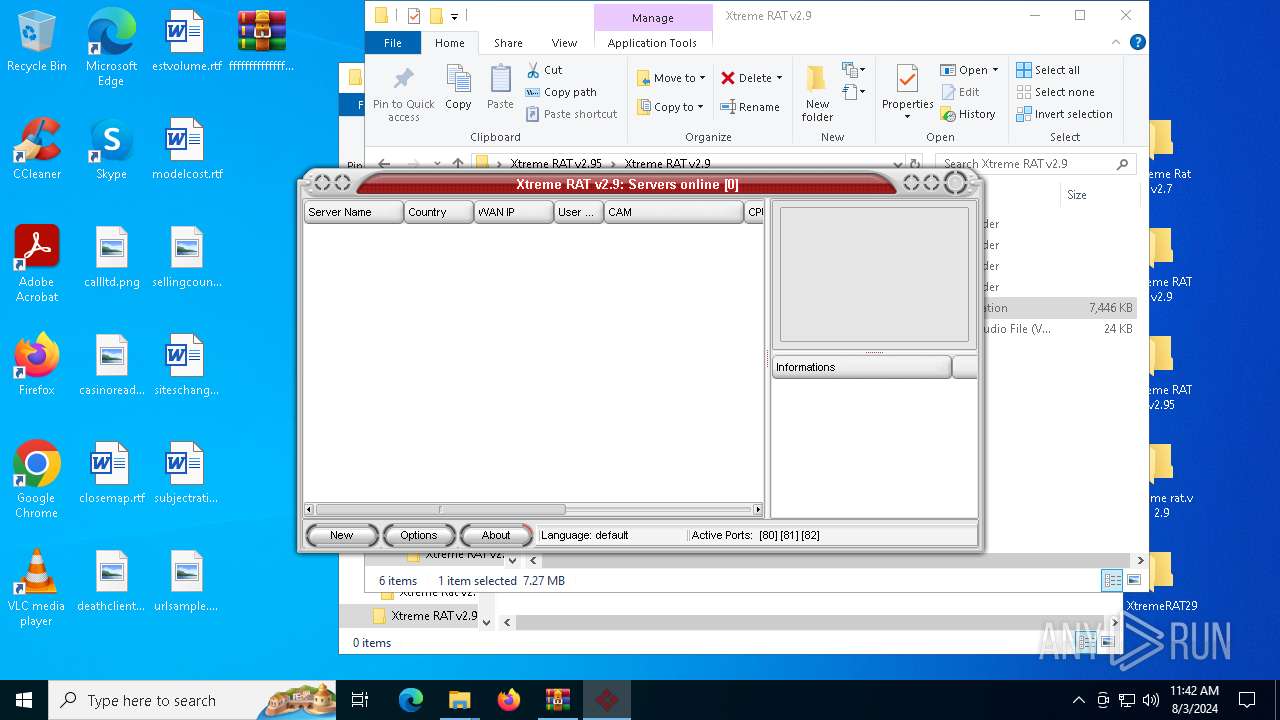
| Verdict: | Malicious activity |
| Analysis date: | August 03, 2024, 11:41:28 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | F727CB1C363A77583BA80A882D63703D |
| SHA1: | 8F878D149FF61144B9224086CE8DBEE032D2E004 |
| SHA256: | 86D4984F7252AA4C84BAD7207ADE4230A1FA8FDF2E9CEEA4441997F0543BC676 |
| SSDEEP: | 98304:HwhPZbrLlZLdLwnCpf6fNqGMcMYAjgXhsKzakEtEwkYW+XOTeWu73oKuvS5++pD+:Gwud+9rgsrAWbESQmSS0xbK |
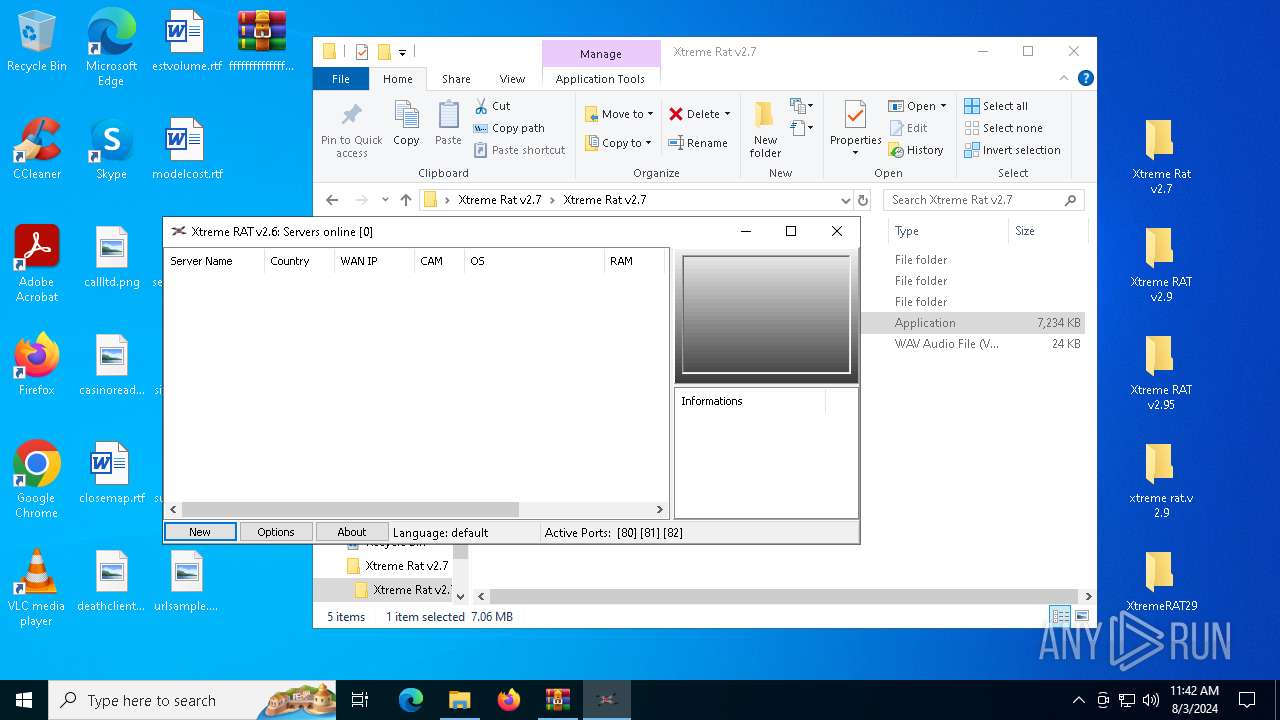
MALICIOUS
Drops the executable file immediately after the start
- Cliente.exe (PID: 1964)
SUSPICIOUS
Reads security settings of Internet Explorer
- Cliente.exe (PID: 1964)
Executable content was dropped or overwritten
- Cliente.exe (PID: 1964)
Reads the date of Windows installation
- Cliente.exe (PID: 1964)
INFO
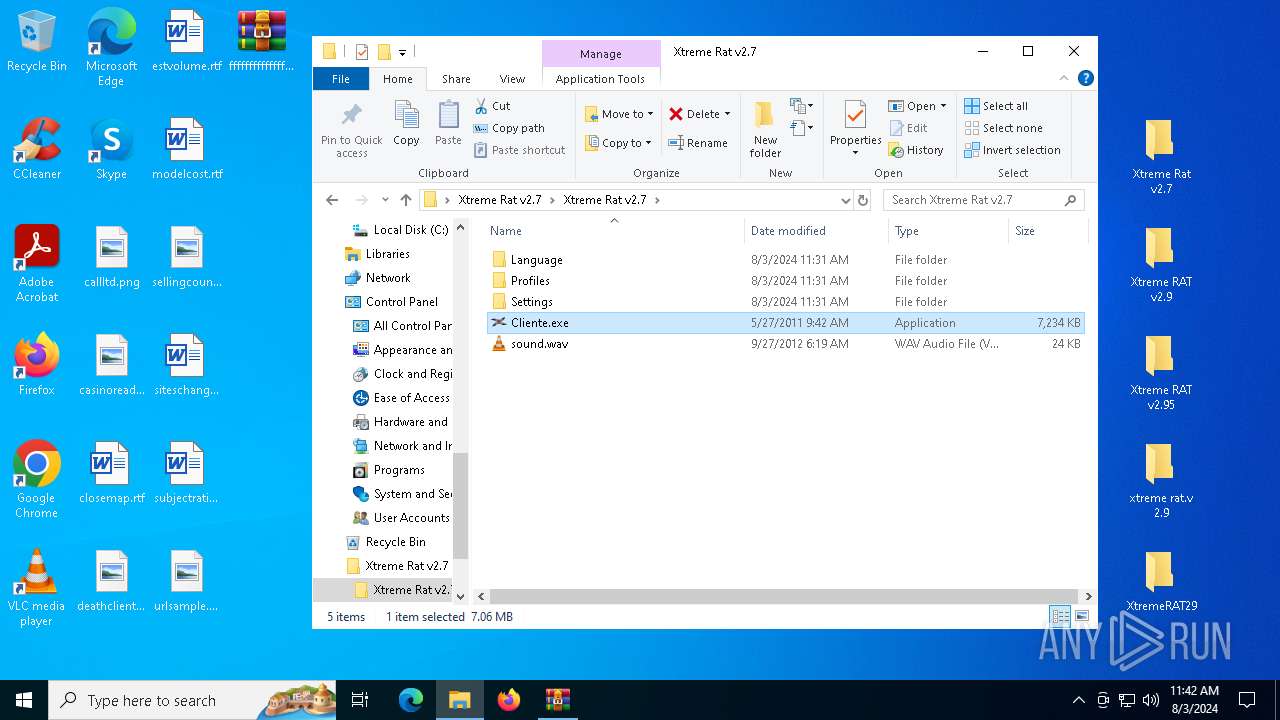
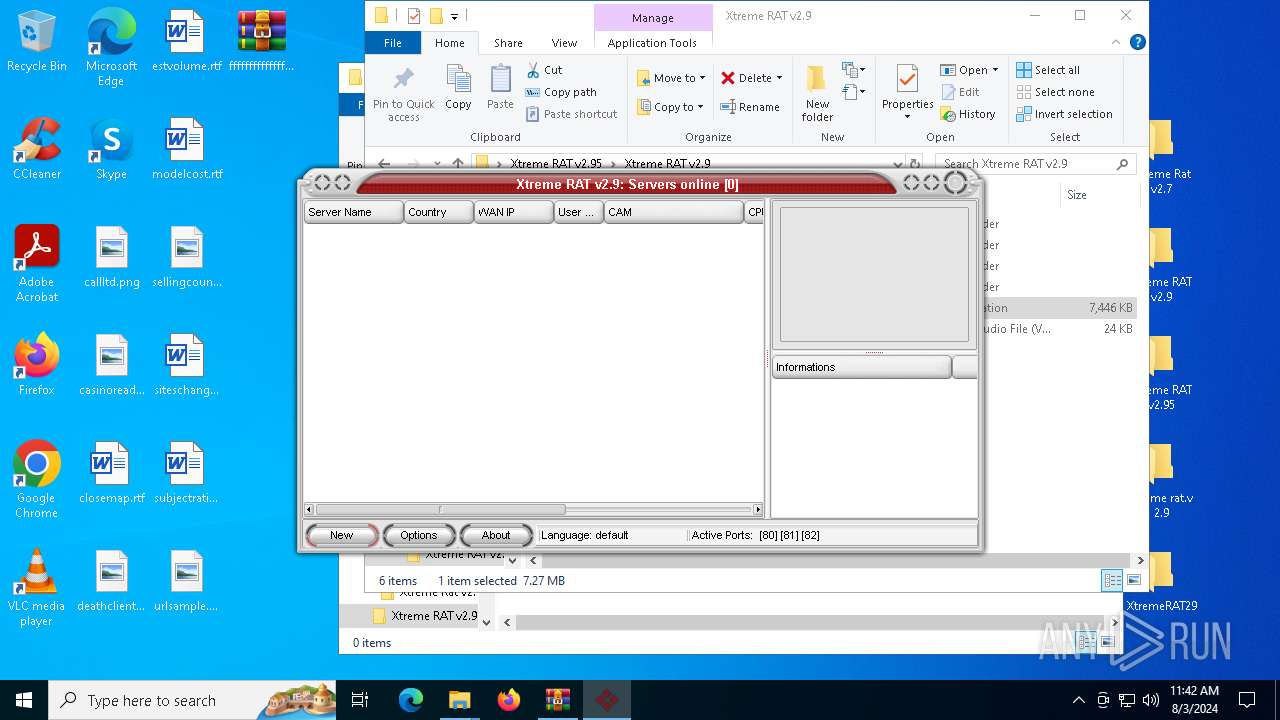
Manual execution by a user
- Cliente.exe (PID: 6204)
- Cliente.exe (PID: 6236)
- Cliente.exe (PID: 1964)
- Cliente.exe (PID: 6996)
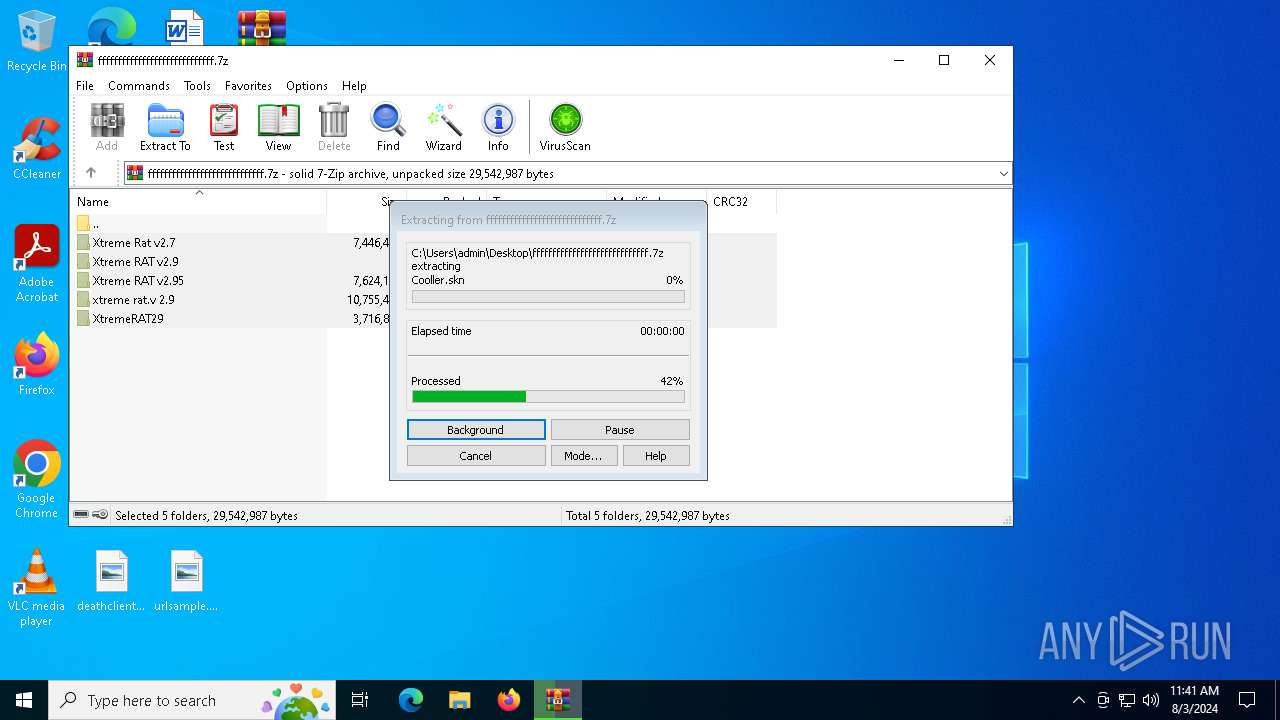
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6488)
Drops the executable file immediately after the start
- WinRAR.exe (PID: 6488)
Checks supported languages
- Cliente.exe (PID: 6236)
- Cliente.exe (PID: 6204)
- Cliente.exe (PID: 1964)
- 6576807.exe (PID: 7104)
- Cliente.exe (PID: 6996)
- 4113995.exe (PID: 6200)
Reads the computer name
- Cliente.exe (PID: 6204)
- Cliente.exe (PID: 6236)
- Cliente.exe (PID: 1964)
- 4113995.exe (PID: 6200)
- Cliente.exe (PID: 6996)
Create files in a temporary directory
- Cliente.exe (PID: 6204)
- Cliente.exe (PID: 1964)
- 4113995.exe (PID: 6200)
- Cliente.exe (PID: 6996)
Process checks computer location settings
- Cliente.exe (PID: 1964)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
Total processes
138
Monitored processes
8
Malicious processes
0
Suspicious processes
1
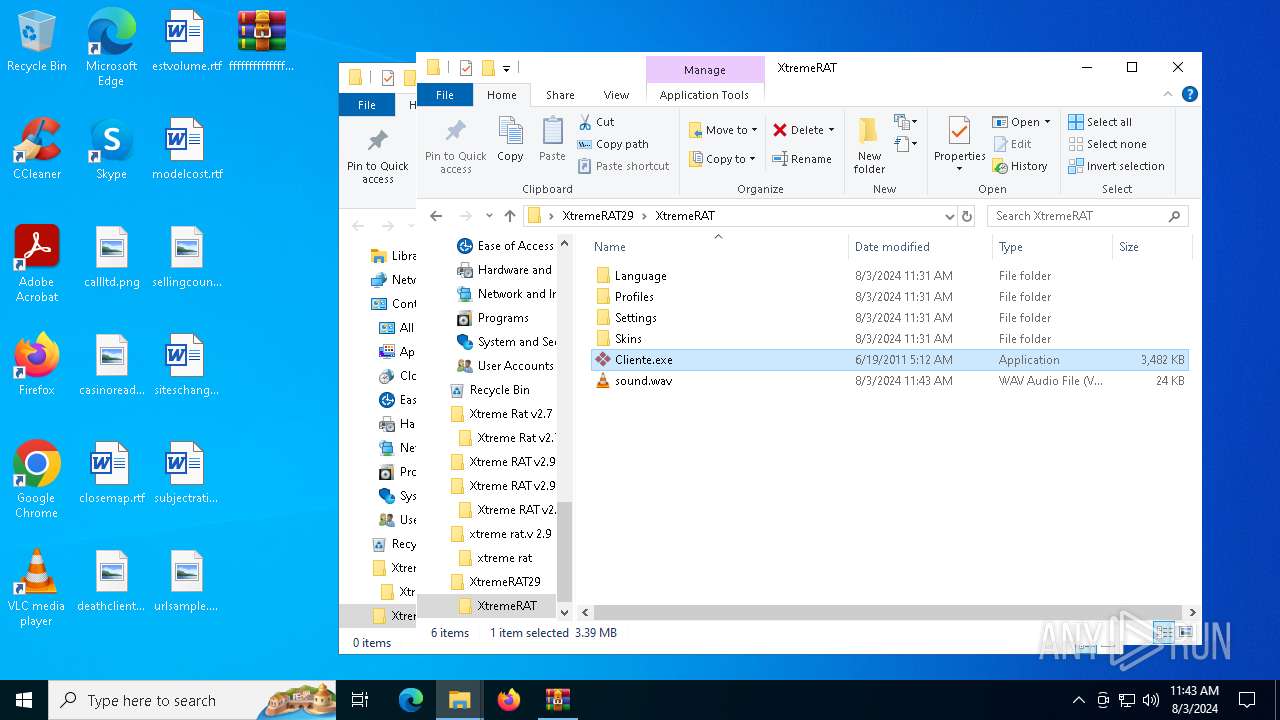
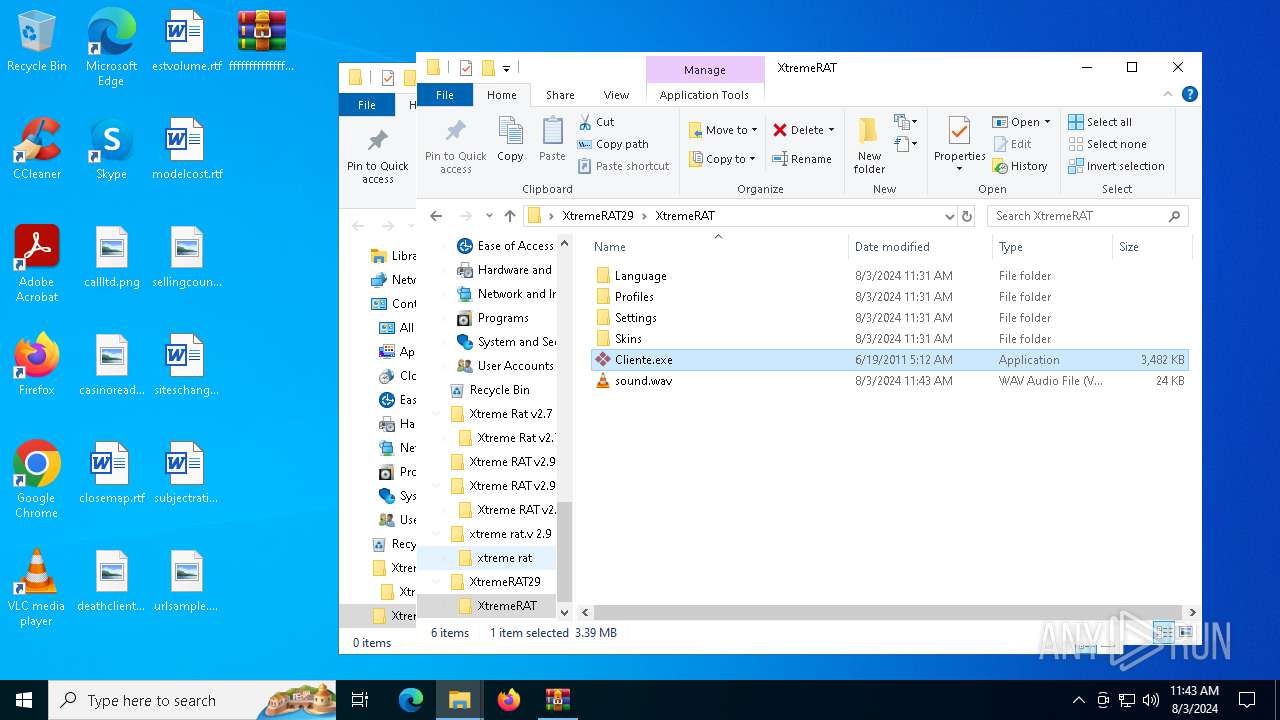
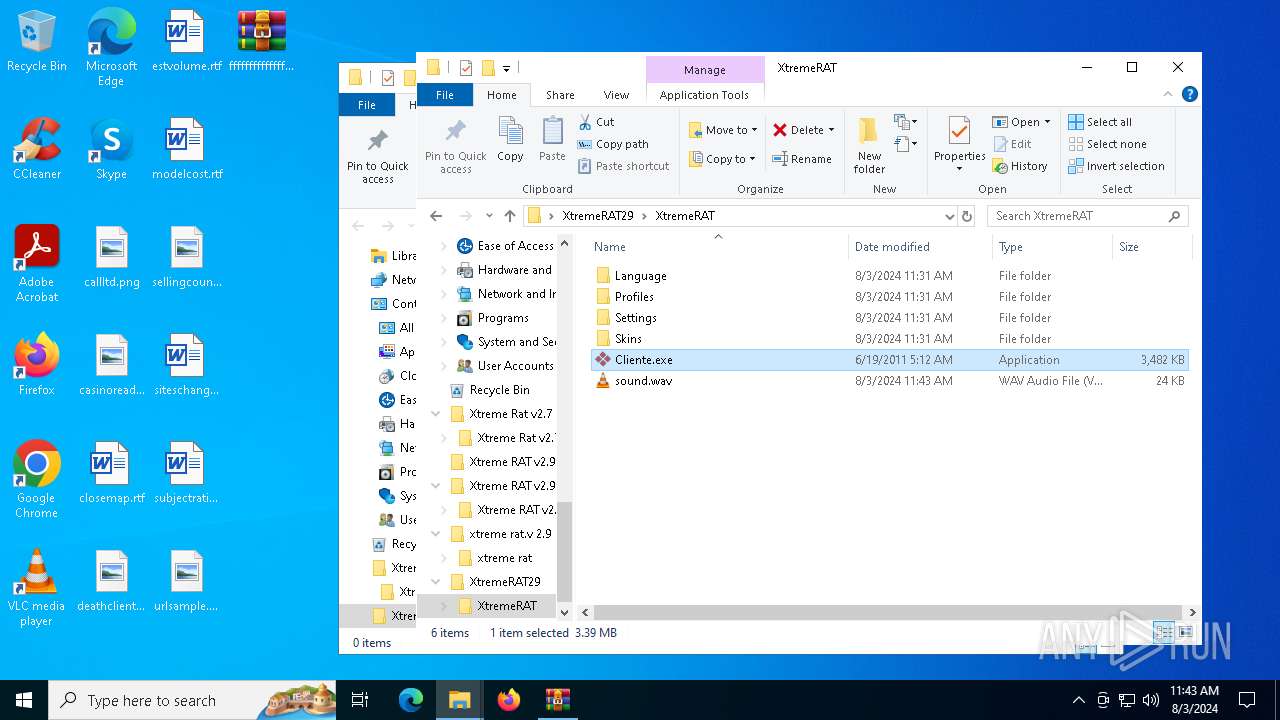
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
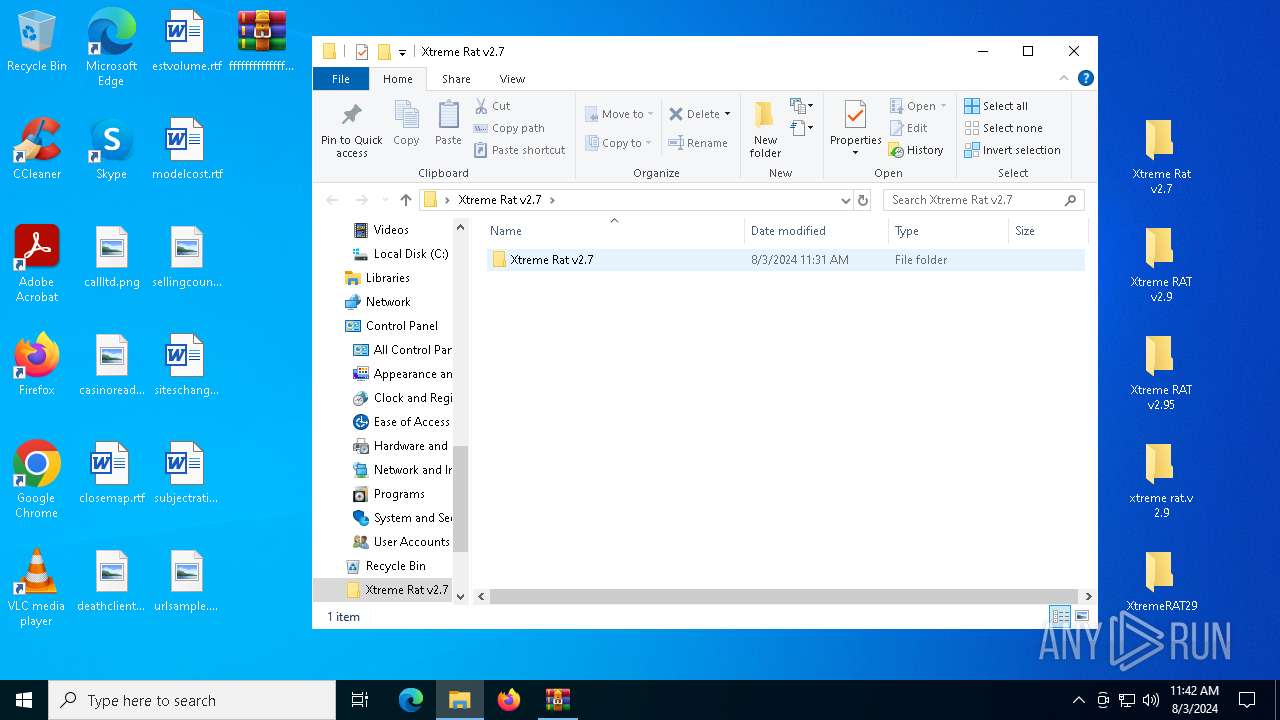
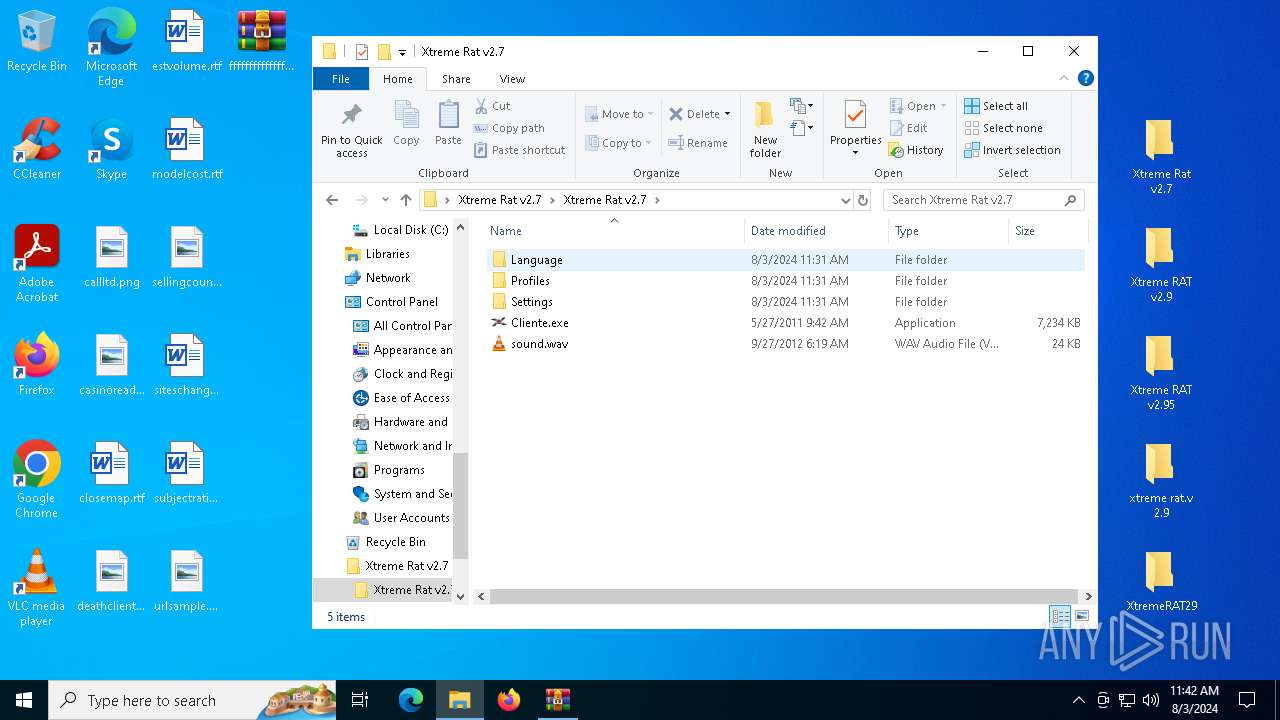
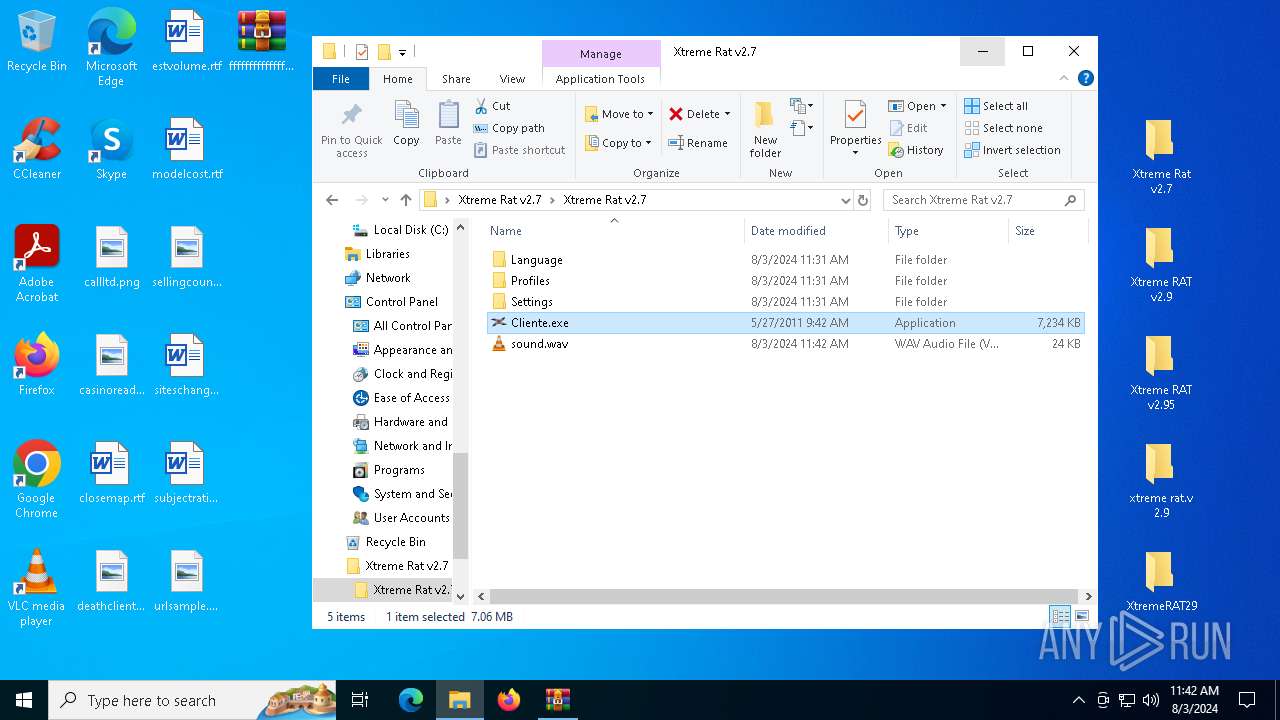
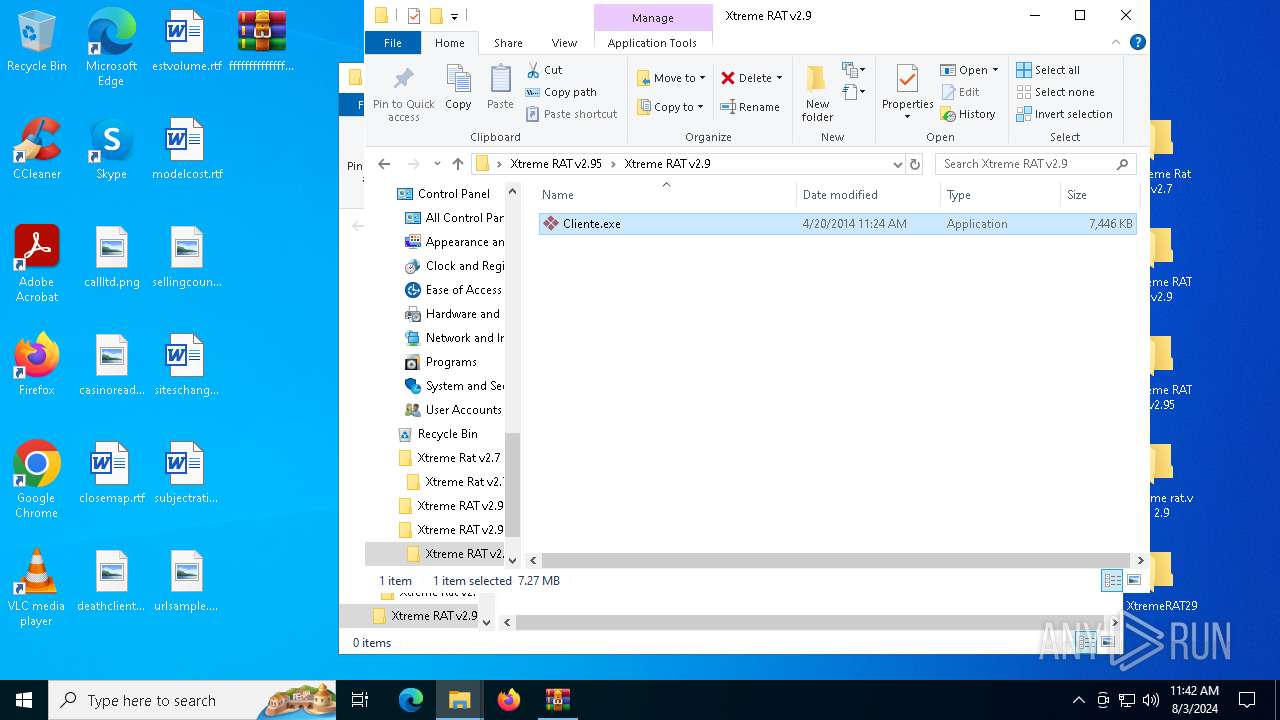
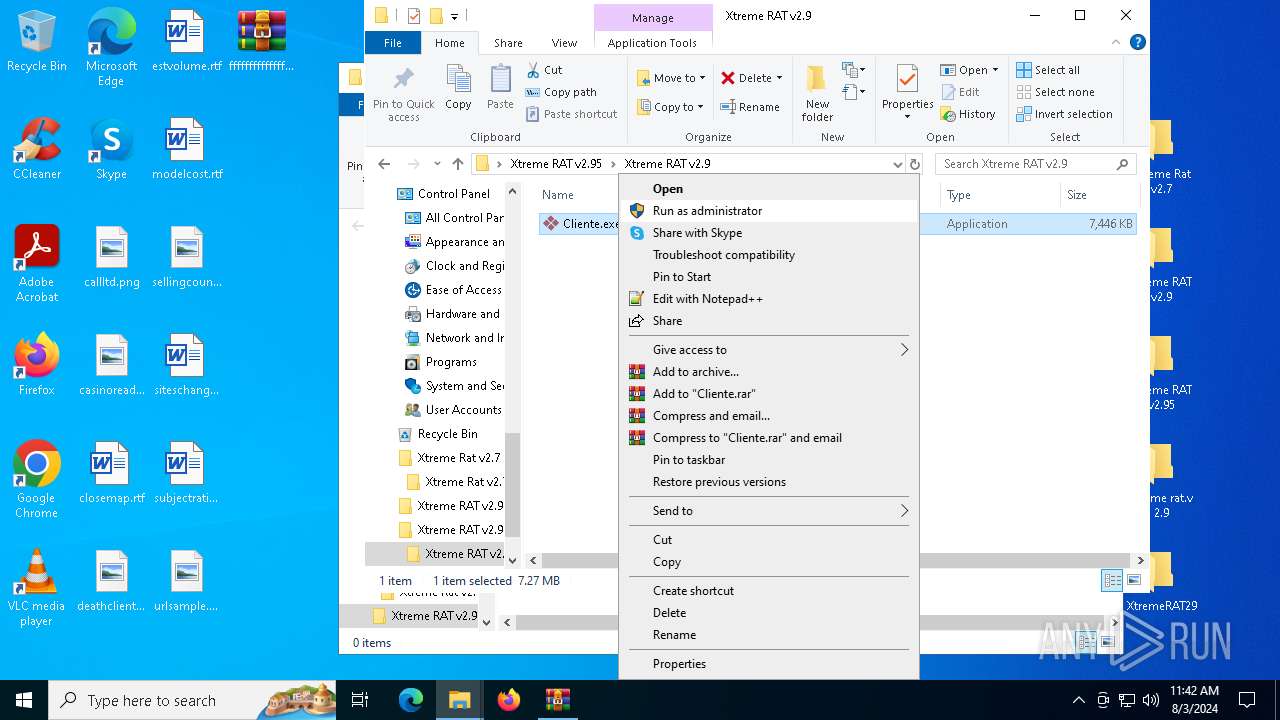
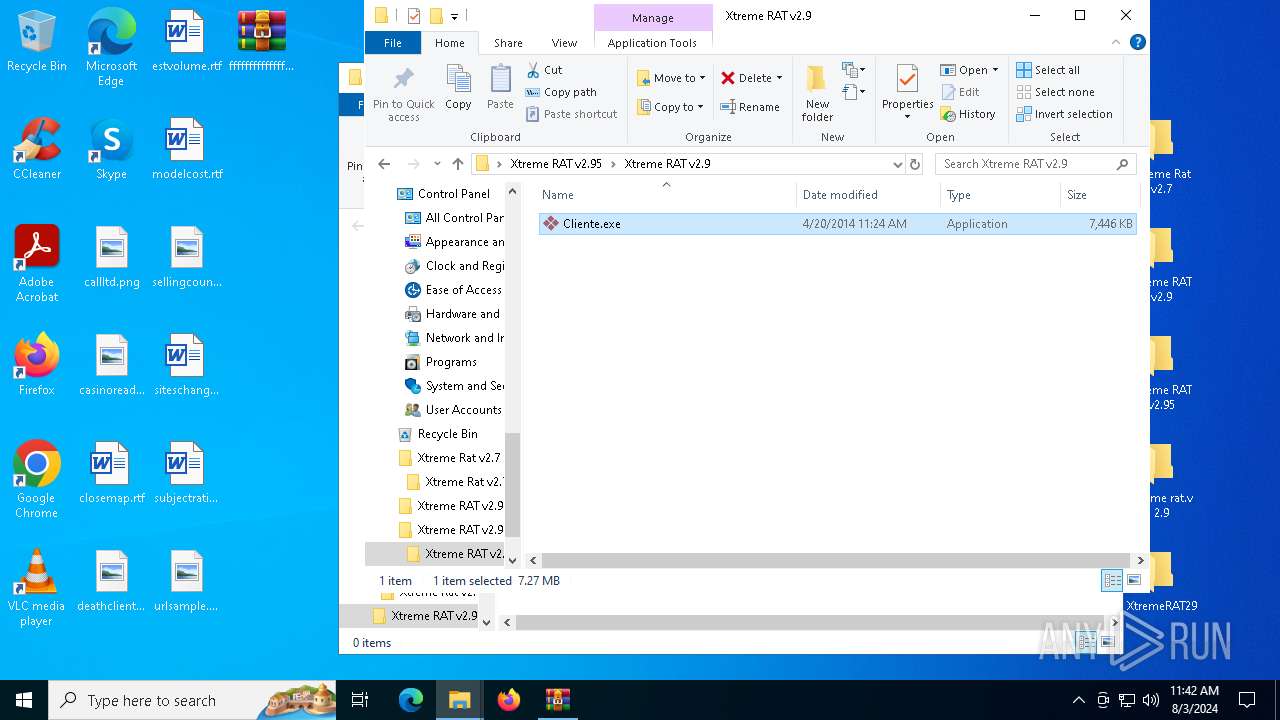
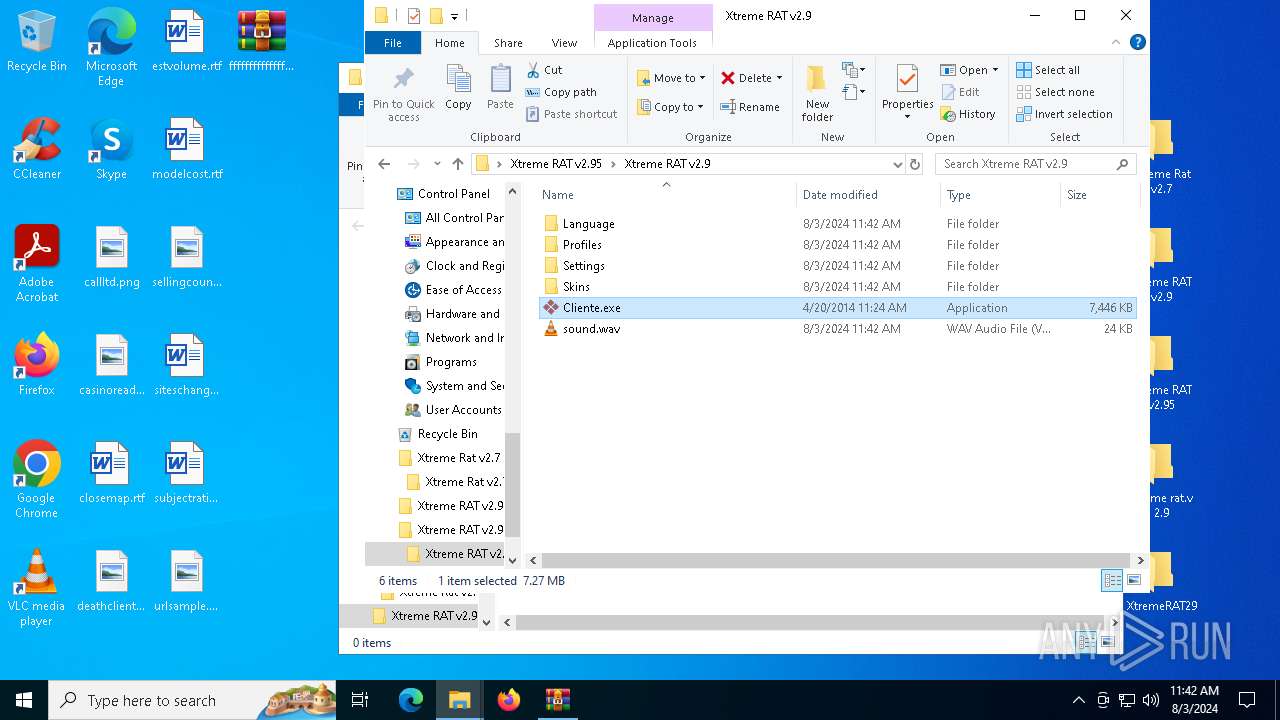
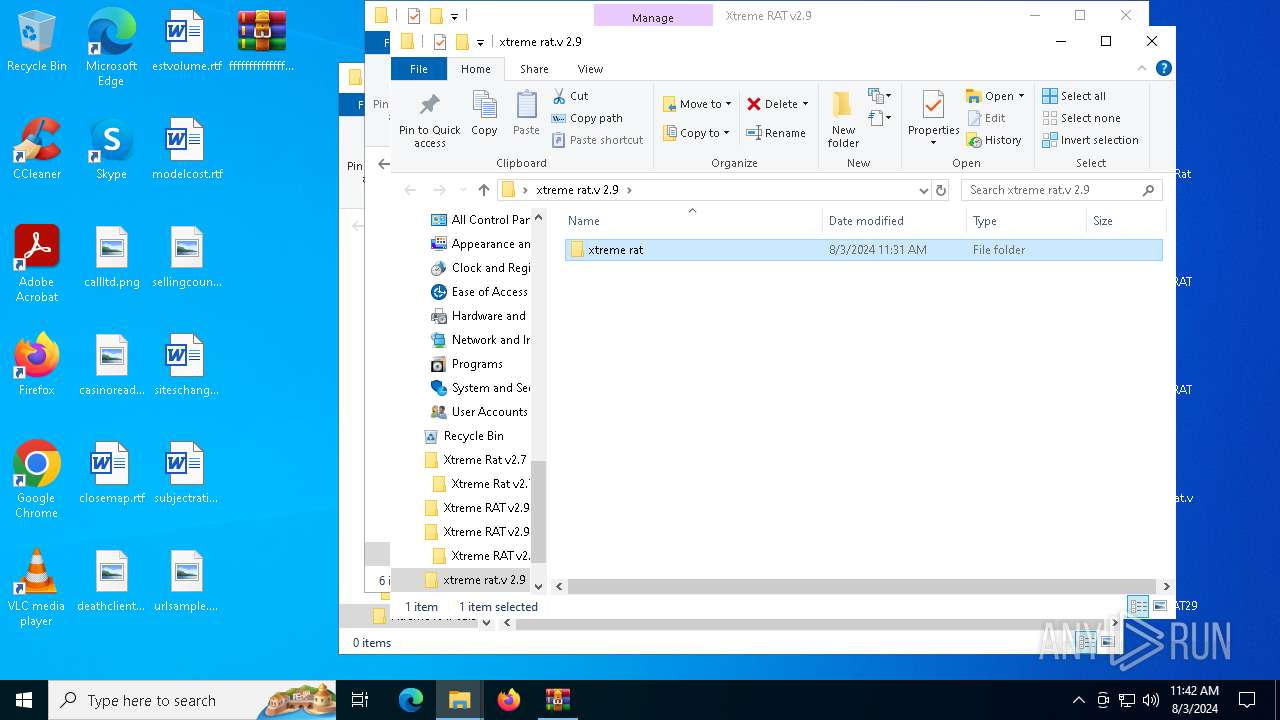
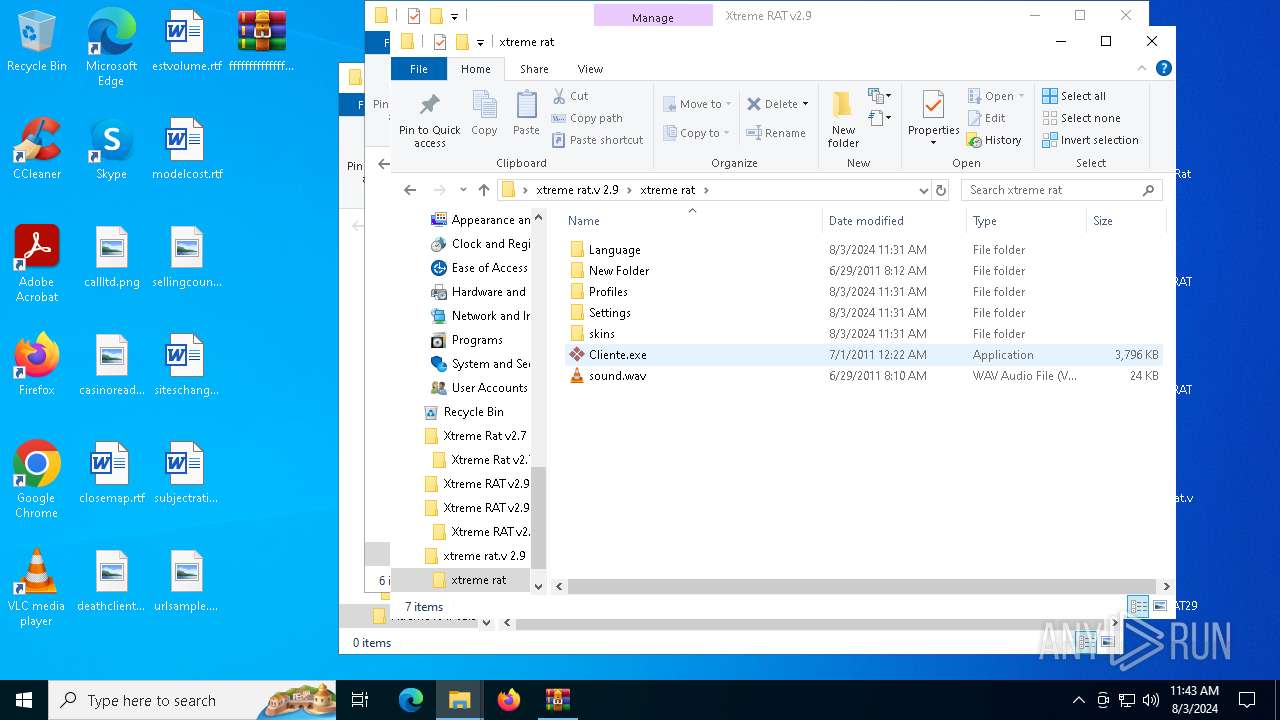
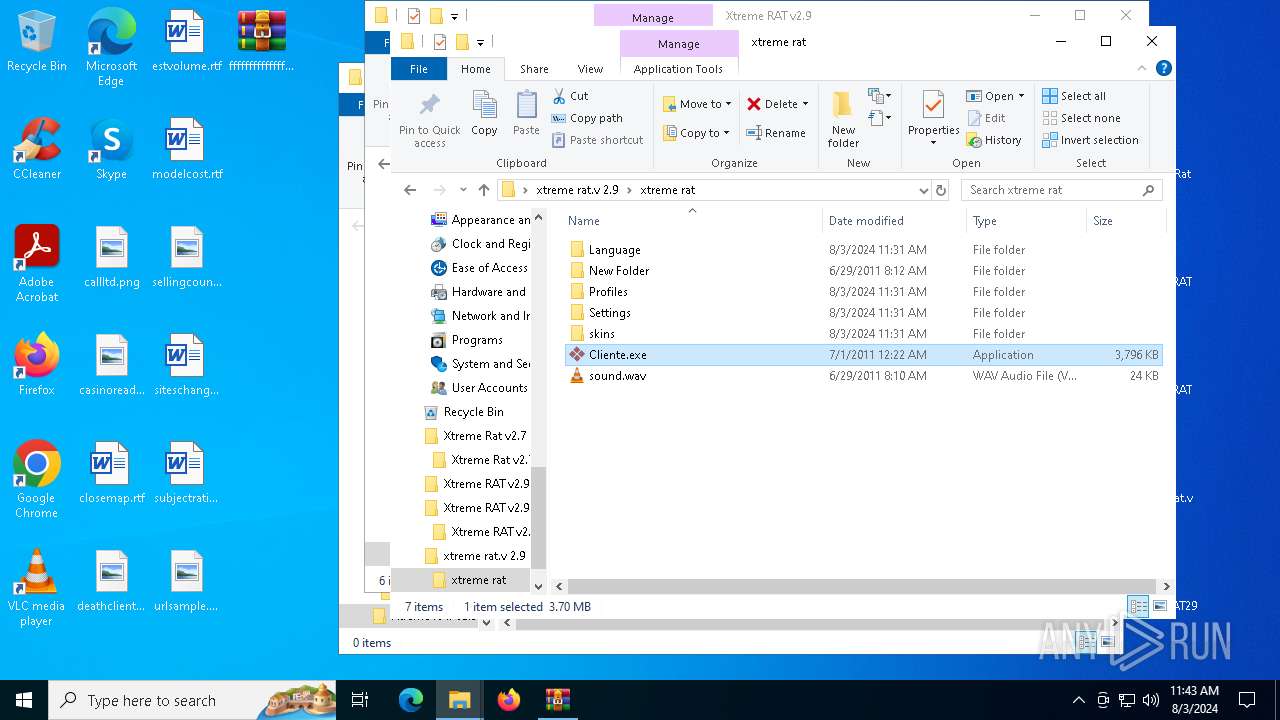
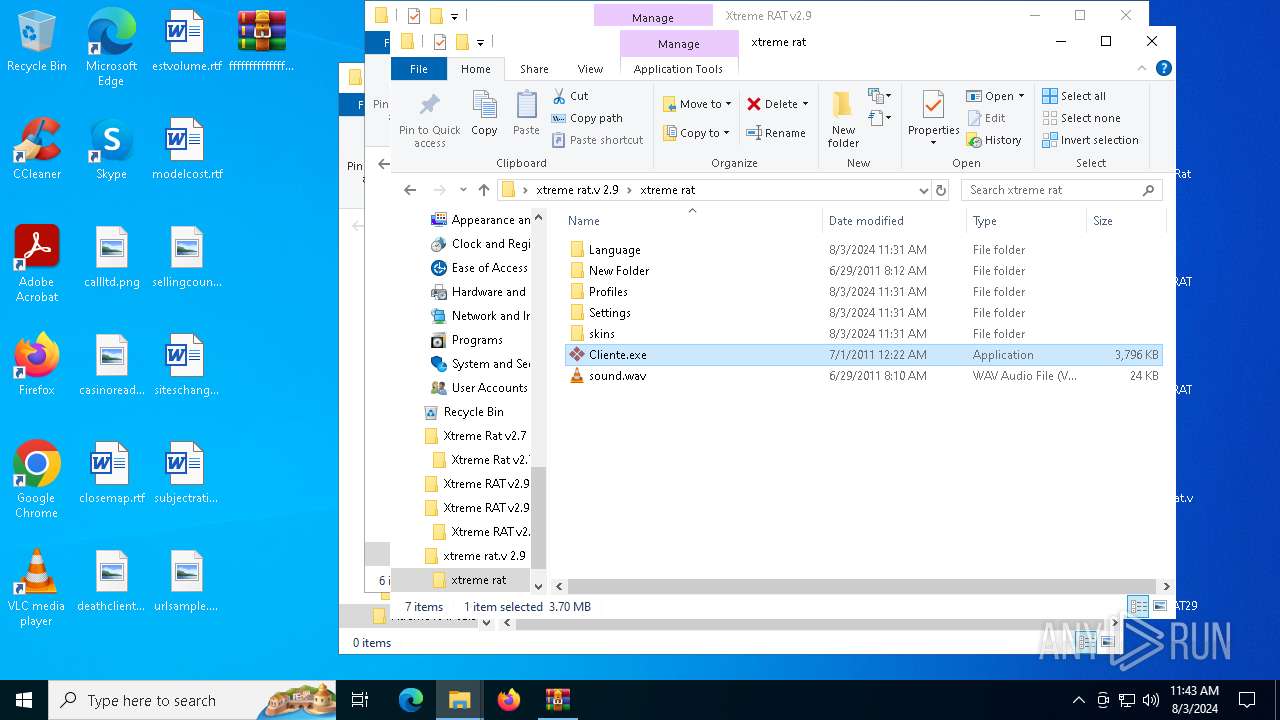
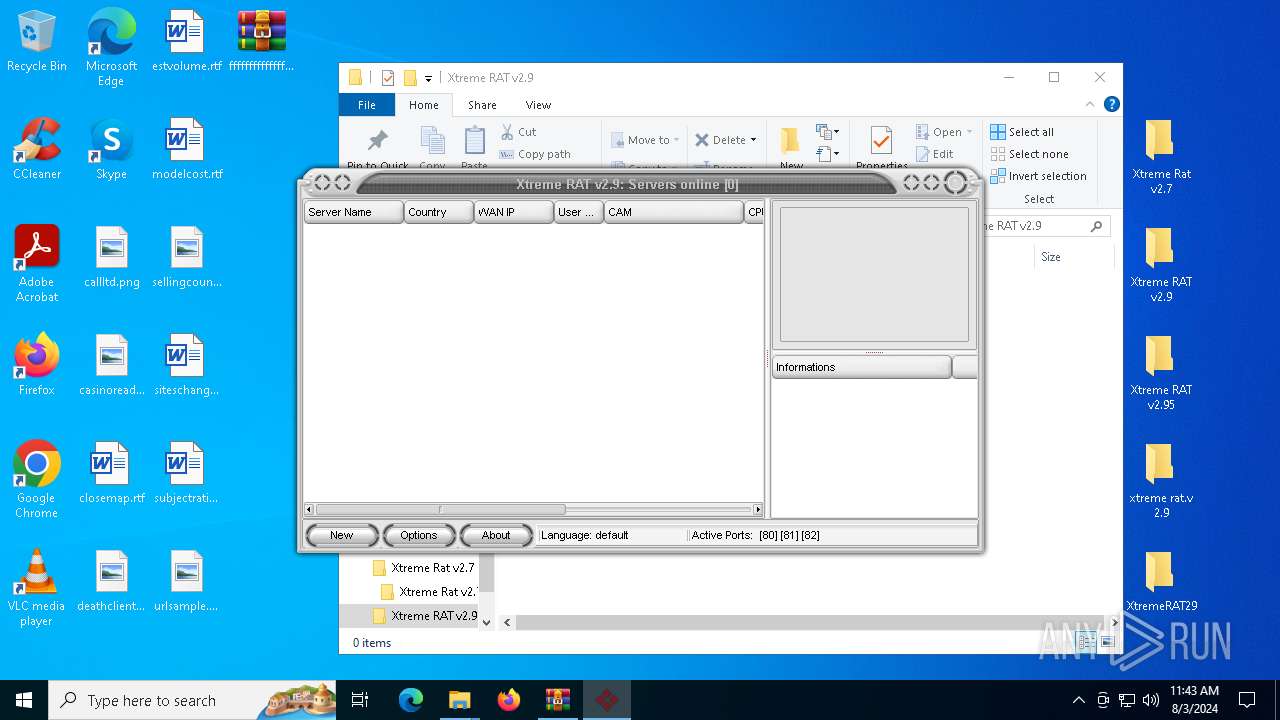
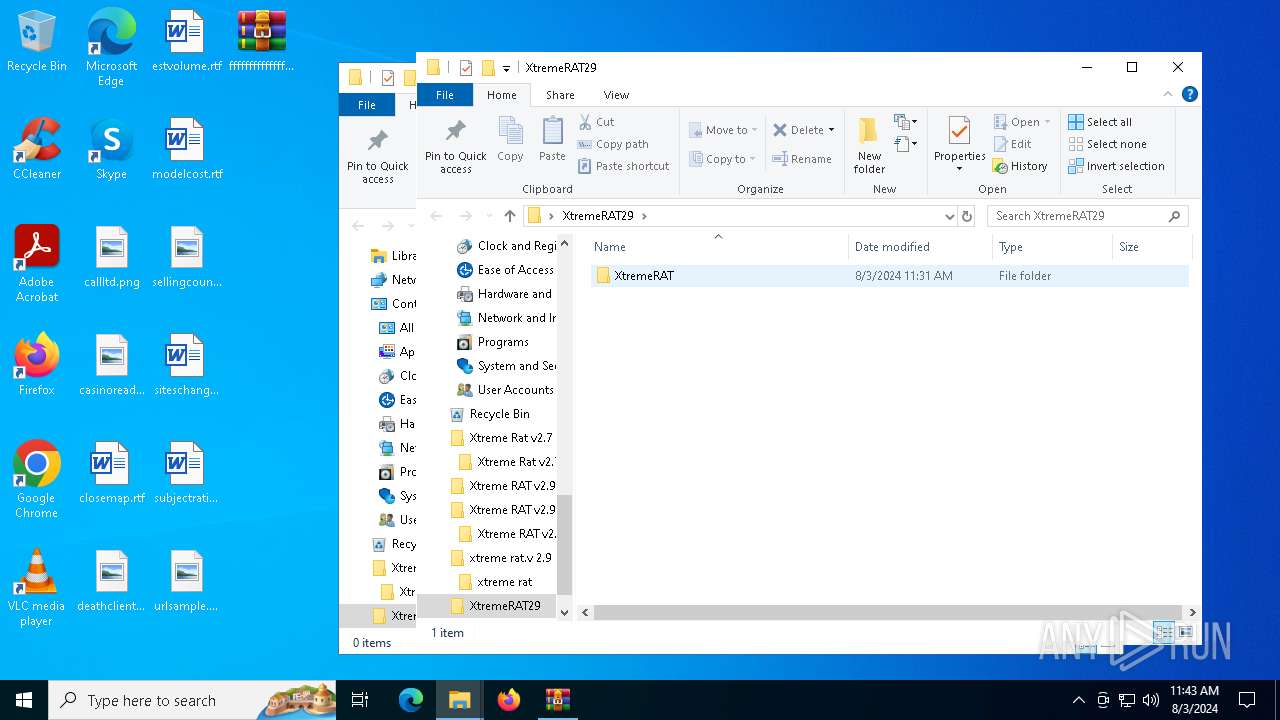
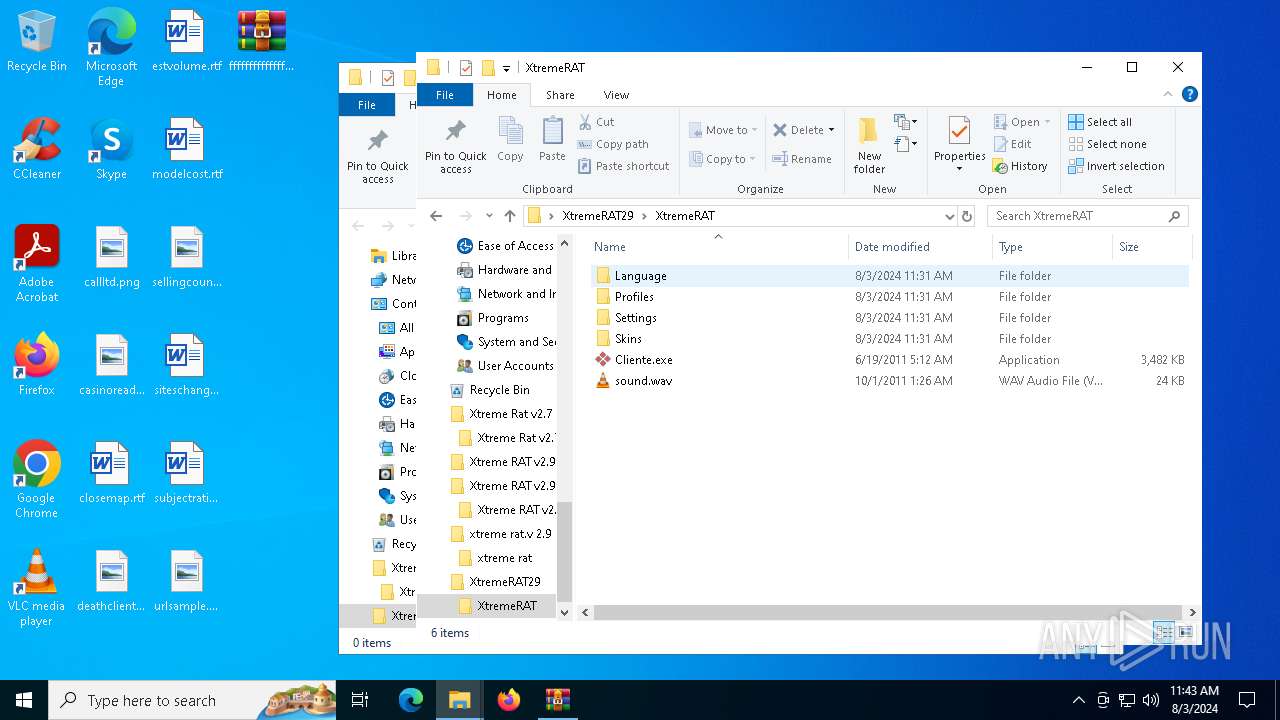
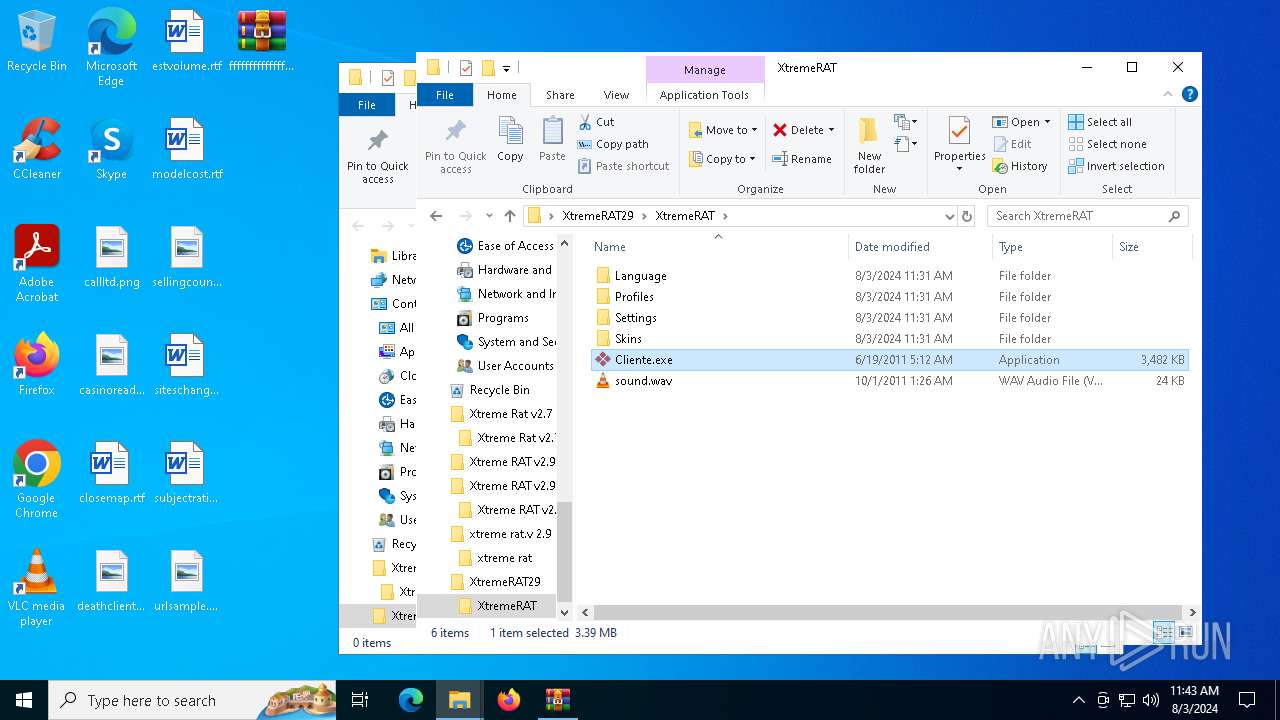
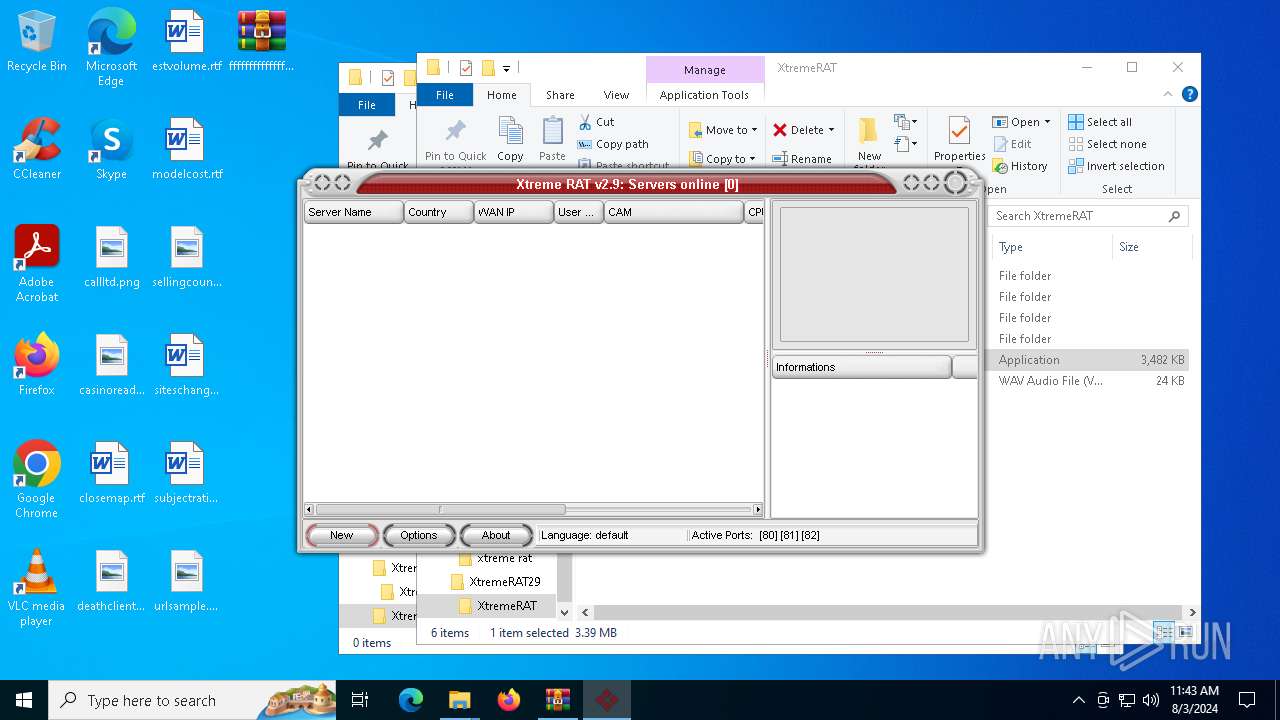
| 1964 | "C:\Users\admin\Desktop\xtreme rat.v 2.9\xtreme rat\Cliente.exe" | C:\Users\admin\Desktop\xtreme rat.v 2.9\xtreme rat\Cliente.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 2.9 Modules
| |||||||||||||||
| 6200 | "C:\Users\admin\AppData\Local\Temp\4113995.exe" | C:\Users\admin\AppData\Local\Temp\4113995.exe | — | Cliente.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
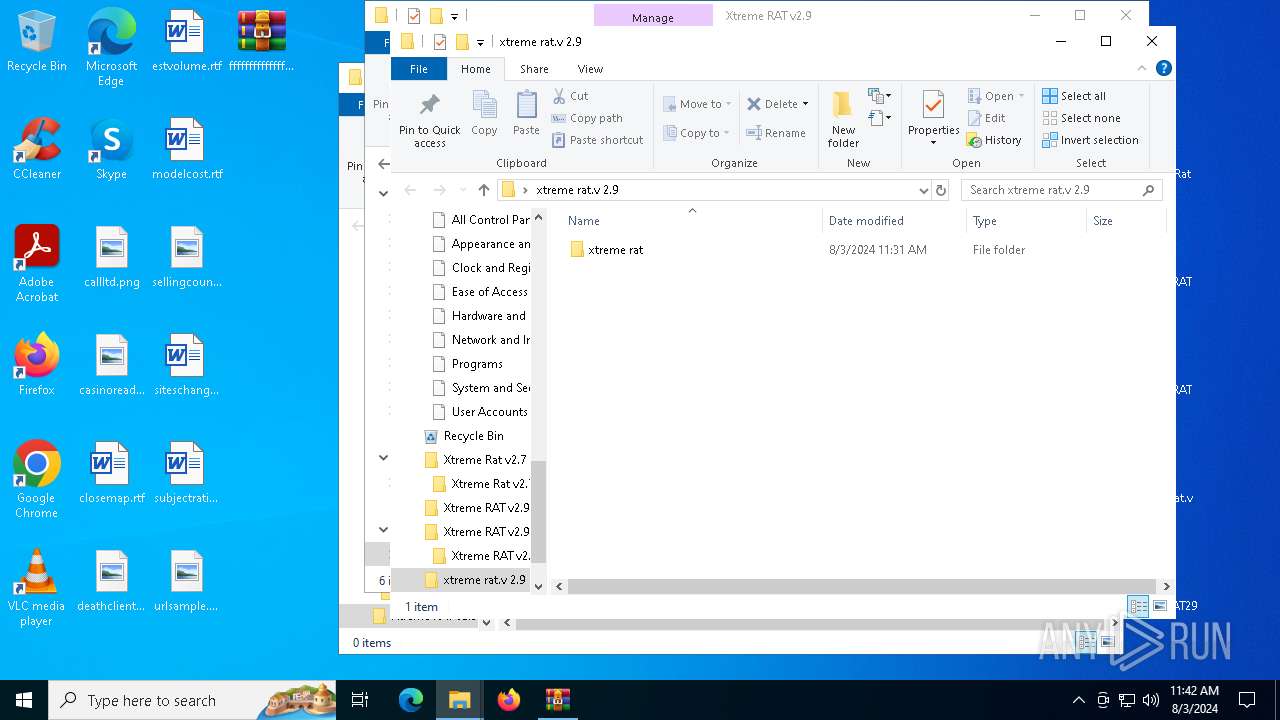
| 6204 | "C:\Users\admin\Desktop\Xtreme Rat v2.7\Xtreme Rat v2.7\Cliente.exe" | C:\Users\admin\Desktop\Xtreme Rat v2.7\Xtreme Rat v2.7\Cliente.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
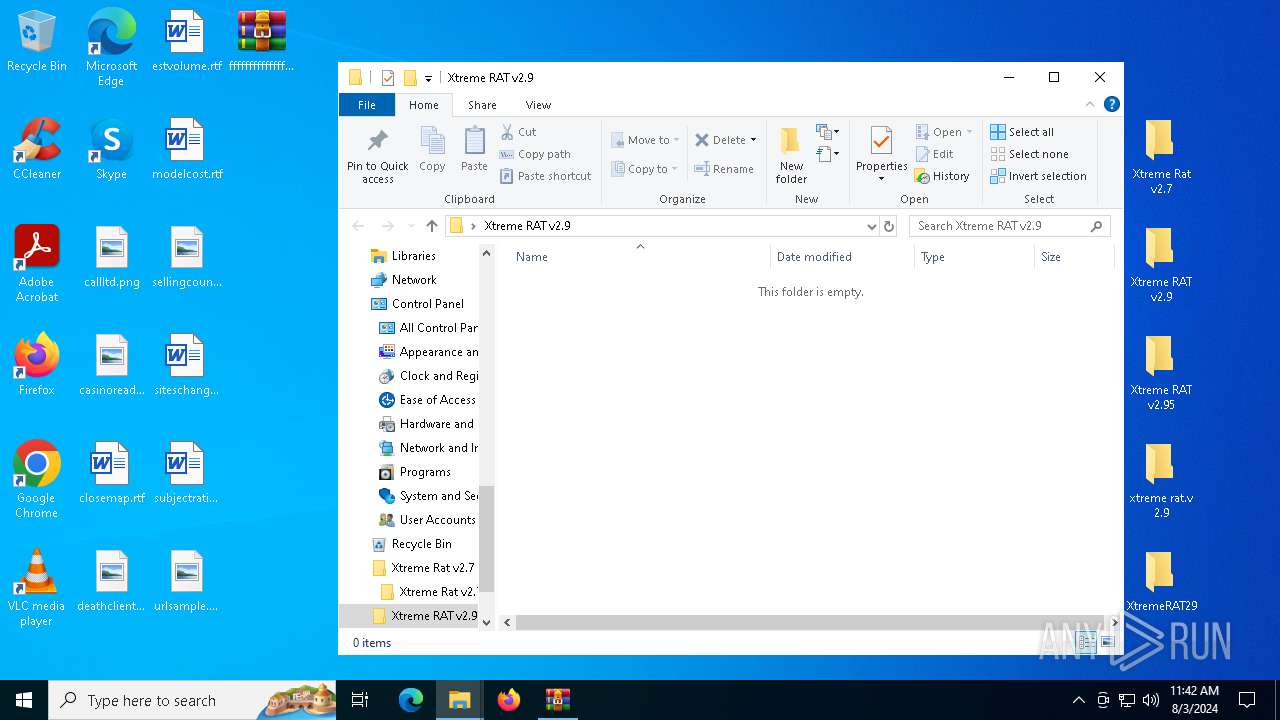
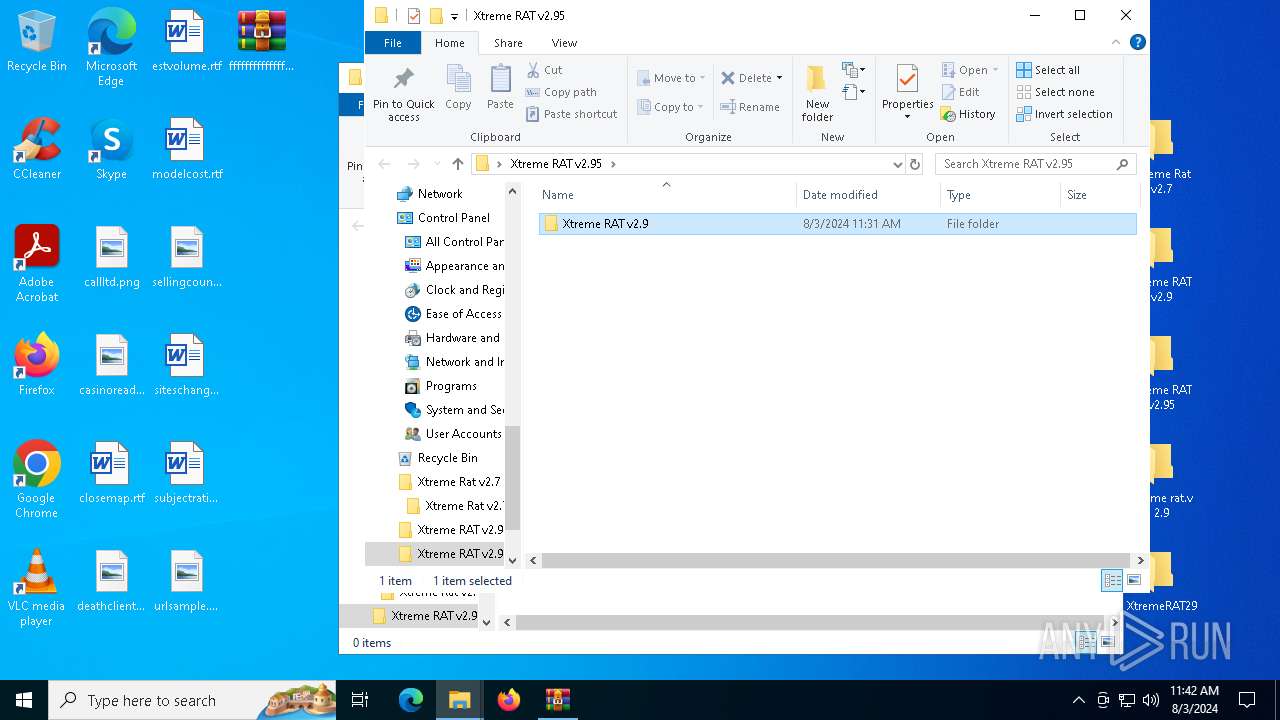
| 6236 | "C:\Users\admin\Desktop\Xtreme RAT v2.95\Xtreme RAT v2.9\Cliente.exe" | C:\Users\admin\Desktop\Xtreme RAT v2.95\Xtreme RAT v2.9\Cliente.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 6488 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\fffffffffffffffffffffffffffff.7z | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 6812 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6996 | "C:\Users\admin\Desktop\XtremeRAT29\XtremeRAT\Cliente.exe" | C:\Users\admin\Desktop\XtremeRAT29\XtremeRAT\Cliente.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
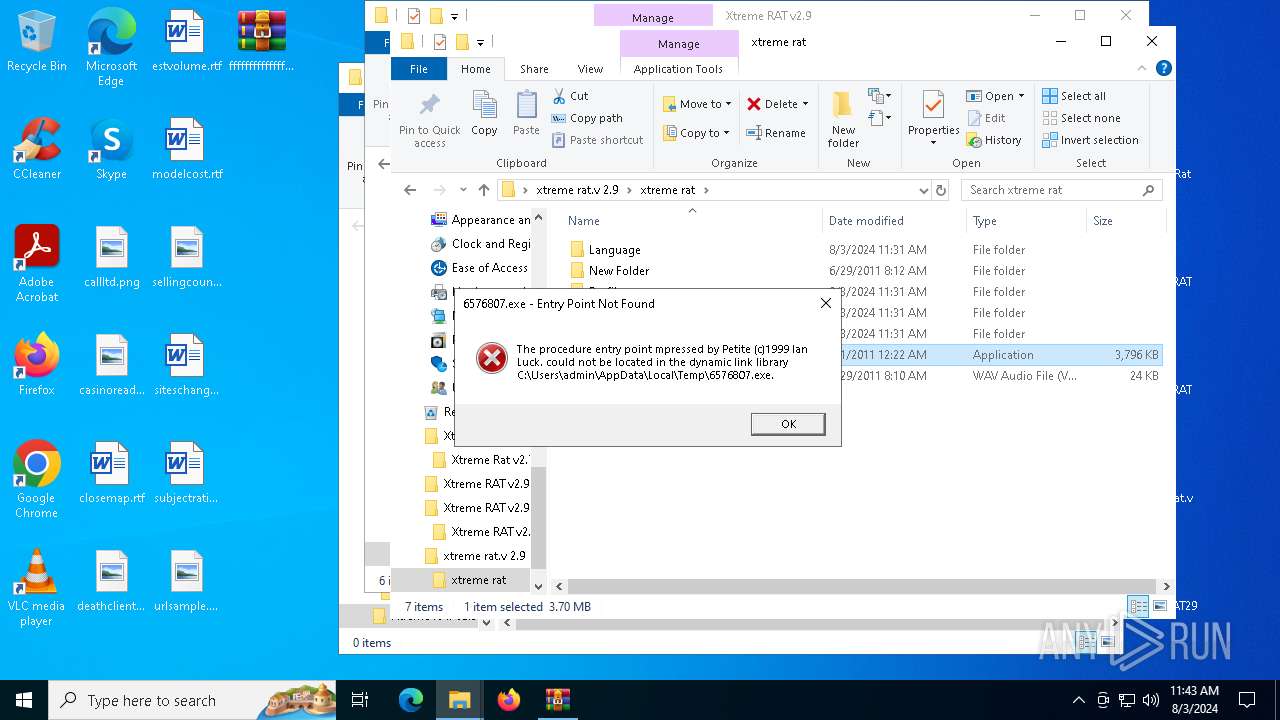
| 7104 | "C:\Users\admin\AppData\Local\Temp\6576807.exe" | C:\Users\admin\AppData\Local\Temp\6576807.exe | — | Cliente.exe | |||||||||||
User: admin Company: NBCripter Integrity Level: MEDIUM Exit code: 3221225785 Version: 1.00.0013 Modules
| |||||||||||||||
Total events
9 937
Read events
9 921
Write events
16
Delete events
0
Modification events
| (PID) Process: | (6488) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (6488) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (6488) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (6488) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\fffffffffffffffffffffffffffff.7z | |||
| (PID) Process: | (6488) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6488) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6488) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6488) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1964) Cliente.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1964) Cliente.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
Executable files
6
Suspicious files
102
Text files
16
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6488 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6488.12312\Xtreme Rat v2.7\Xtreme Rat v2.7\Language\default.ini | text | |
MD5:4F04A2713B7B7E2E8D2467A0813C5489 | SHA256:78E0BEE9272C5095E28A711BC617686027FE64935B2674077CBC9E24700FF731 | |||
| 6488 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6488.12312\Xtreme Rat v2.7\Xtreme Rat v2.7\Settings\settings.ini | text | |
MD5:A505EC1817AE944E8E5AED7F159E0ADB | SHA256:639331BBA420E3E5C71BB33C41221C04FEB4DBE913D2D73A37E6F3B3E51D79D8 | |||
| 6488 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6488.12312\xtreme rat.v 2.9\xtreme rat\Language\default.ini | text | |
MD5:E6AE7B5E7E0BB2D737B1FDCEF56410C3 | SHA256:7046863817CB5EEABABB641CFF1262915B13BB5DEE9BD1B6EA10C51929424956 | |||
| 6488 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6488.12312\xtreme rat.v 2.9\xtreme rat\Profiles\samuca.ini | text | |
MD5:D9969D0719B129EA8B7C9A0BF79B82A1 | SHA256:D6861E6AB78F21AD39FE2FD41BB28FFD4DEBC9F41622962CF1770A8A9FA82B05 | |||
| 6488 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6488.12312\xtreme rat.v 2.9\xtreme rat\skins\2010Black_Ext.skn | dbf | |
MD5:E2698F6740C3769F5A005BBFA3A69EDC | SHA256:BC58A9F627E71B01D96A426B5B48F1BCA54487422F706769677B81EDAC0A6933 | |||
| 6488 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6488.12312\xtreme rat.v 2.9\xtreme rat\skins\2010Black_Aero.skn | dbf | |
MD5:98626B9138F8112F6D1171055BC36752 | SHA256:14F40C72244119C2163892A536E3A054A69023F08E530136F3C1460891C11129 | |||
| 6488 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6488.12312\xtreme rat.v 2.9\xtreme rat\skins\2010Blue_Aero.skn | dbf | |
MD5:50903ED4D83B95B36B2007BB5F2C8C5F | SHA256:C77E0F222DBB43484D19F26CED16E293CDB1CDDEAACAB29DDC1DC81ECE75CFC6 | |||
| 6488 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6488.12312\Xtreme Rat v2.7\Xtreme Rat v2.7\Profiles\Profile.ini | text | |
MD5:247BE0A58C3104FC179D6E4F1EF87950 | SHA256:DE354CF8263B3E25579277EB8171BC2D0632CF10A5CA8653A08196E85449CDBB | |||
| 6488 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6488.12312\xtreme rat.v 2.9\xtreme rat\skins\Amazing_Aero.skn | dbf | |
MD5:88A5F8E0B3649943EE2423926C752E32 | SHA256:387E2000C5209FAEDDFBE2D7B544F765E4016E5B119AEA69BECF69F78D8EE0C7 | |||
| 6488 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6488.12312\xtreme rat.v 2.9\xtreme rat\skins\2010Silver_Aero.skn | binary | |
MD5:6586B0BC38BE5A97385B0984615047DD | SHA256:4F242125BAB3808379934B1B23396147D0439A182258C5F3AD9184DB745E6DF3 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
37
DNS requests
15
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
2456 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6916 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6892 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4084 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2388 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5336 | SearchApp.exe | 104.126.37.153:443 | www.bing.com | Akamai International B.V. | DE | unknown |
5336 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
3260 | svchost.exe | 40.113.110.67:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2456 | svchost.exe | 20.190.160.14:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
th.bing.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |