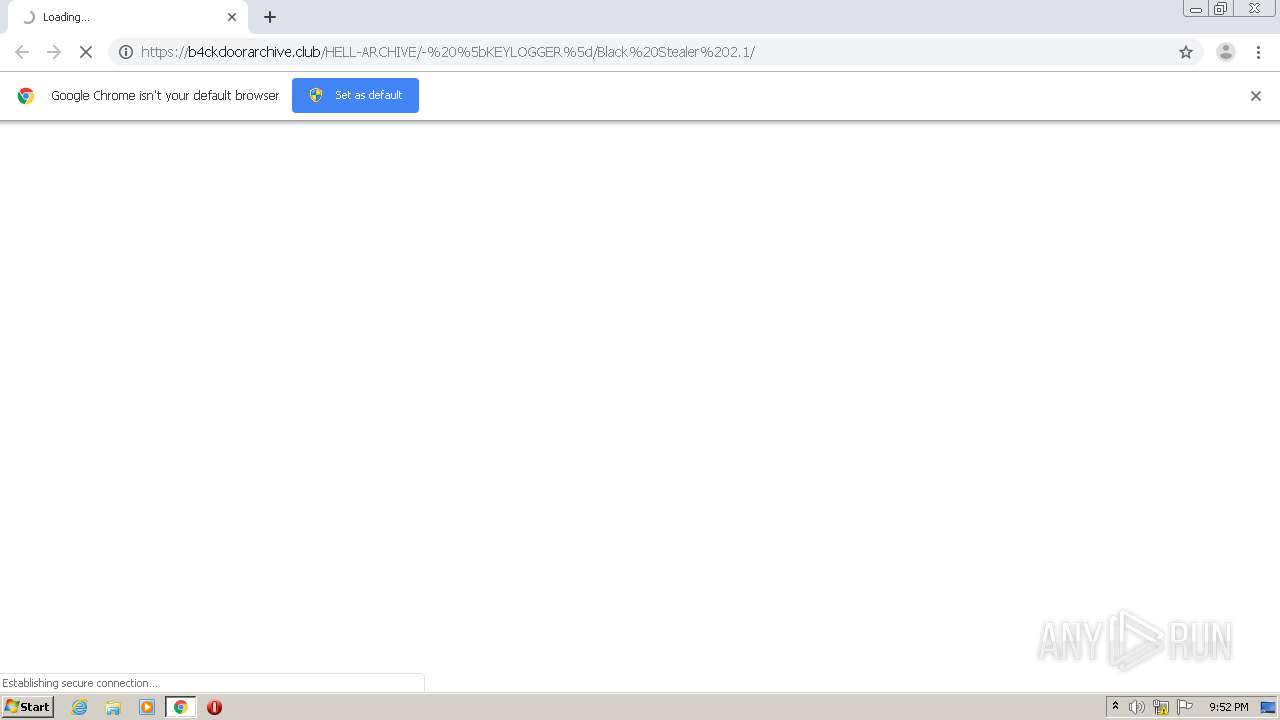
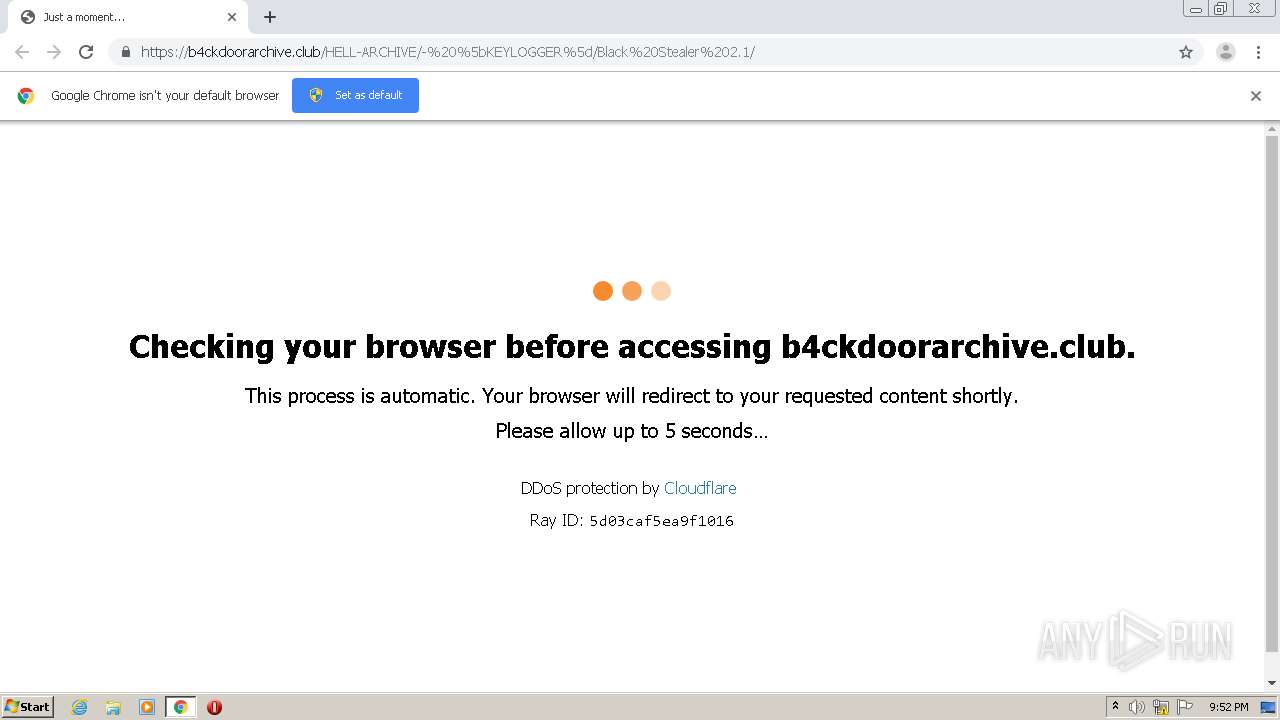
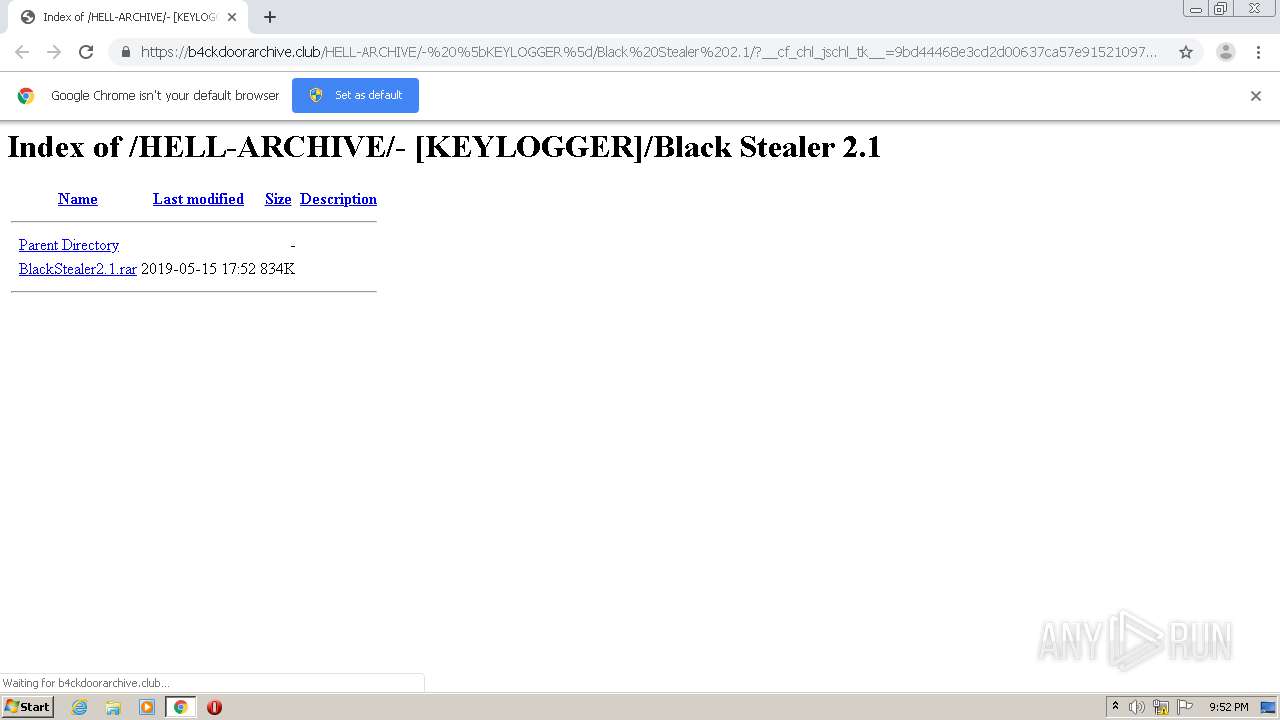
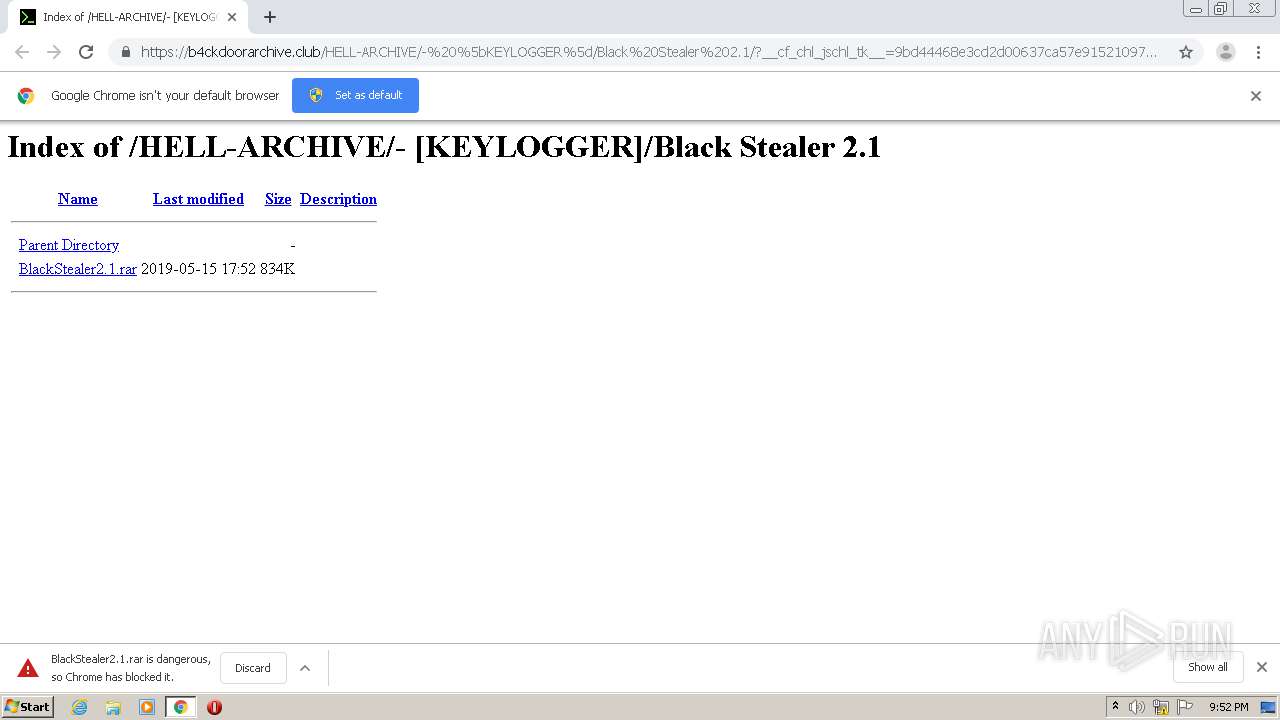
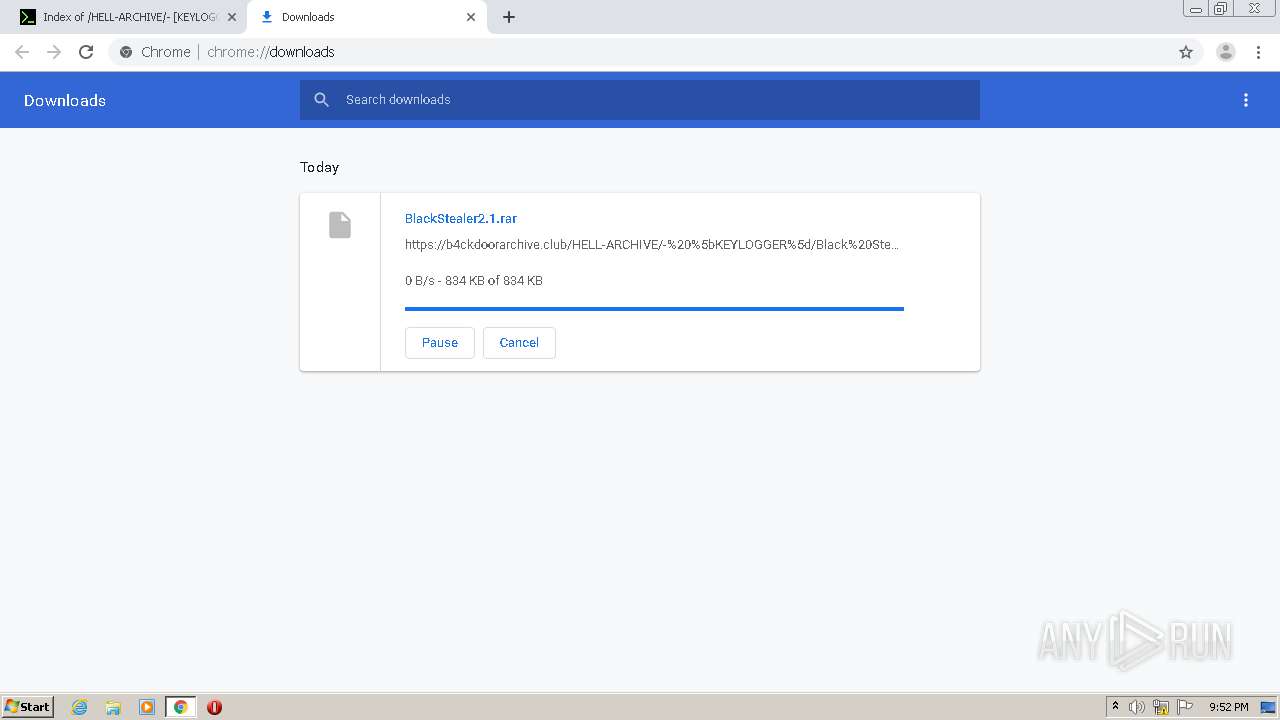
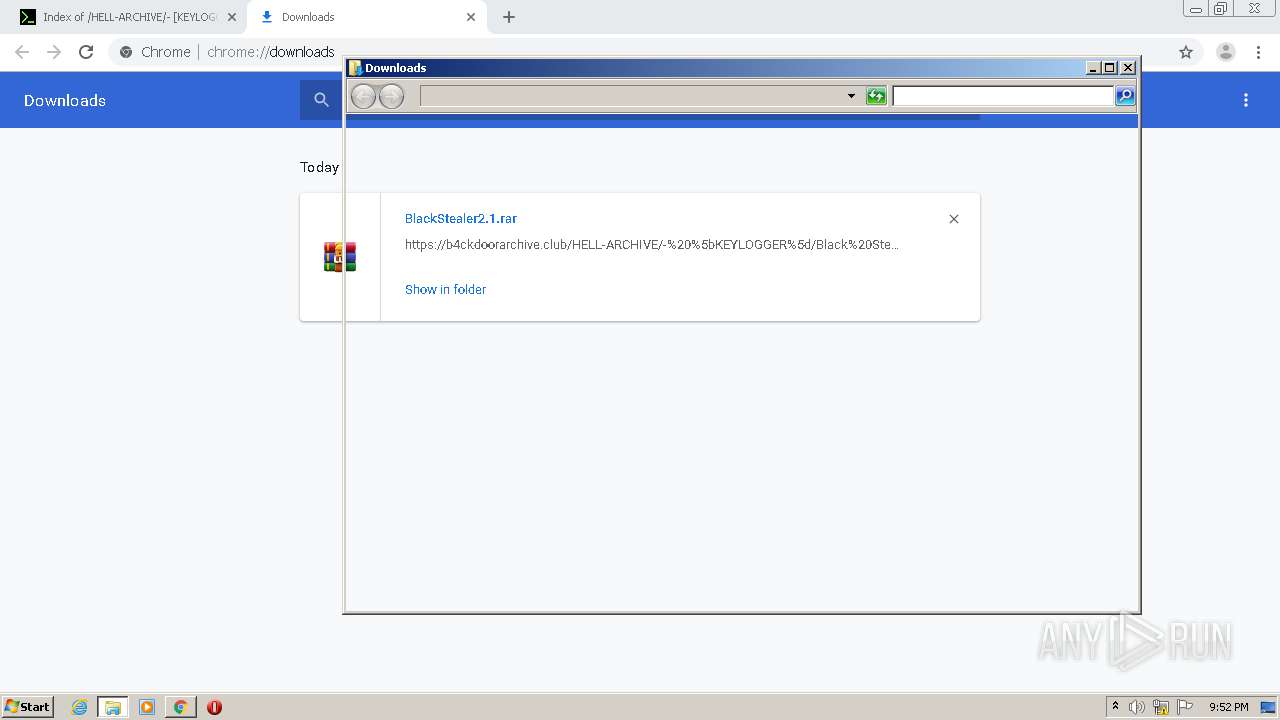
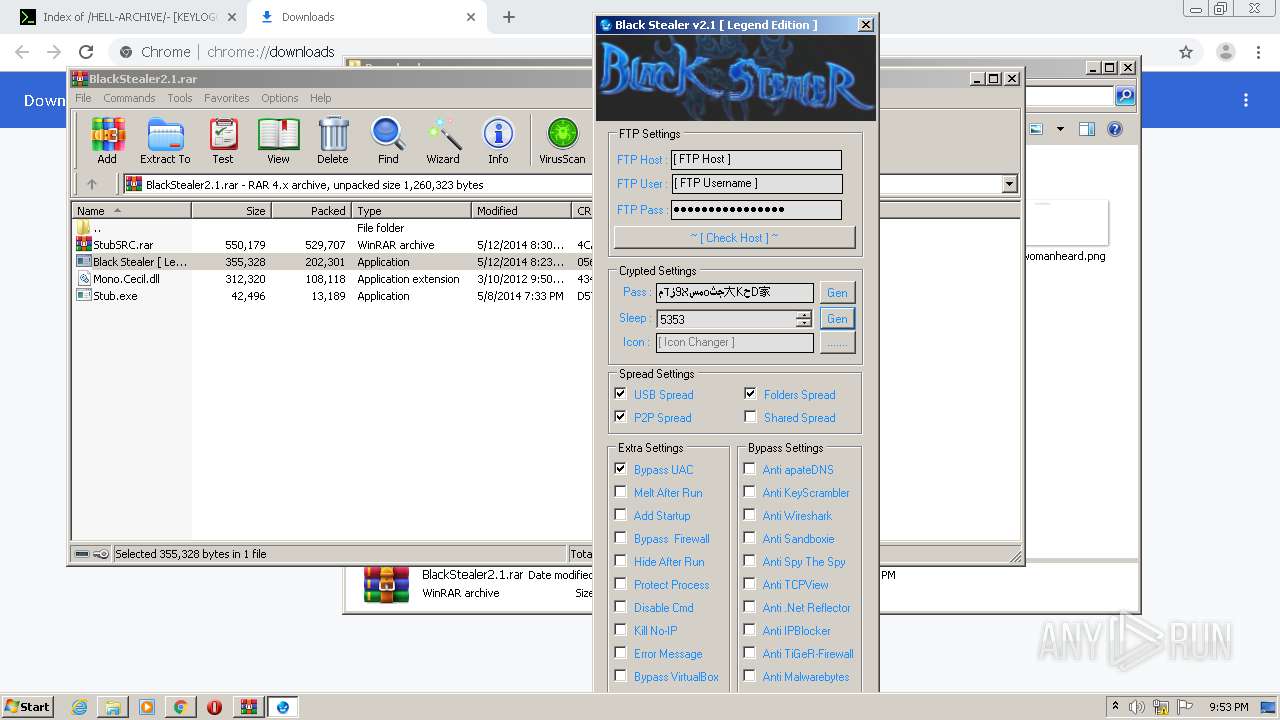
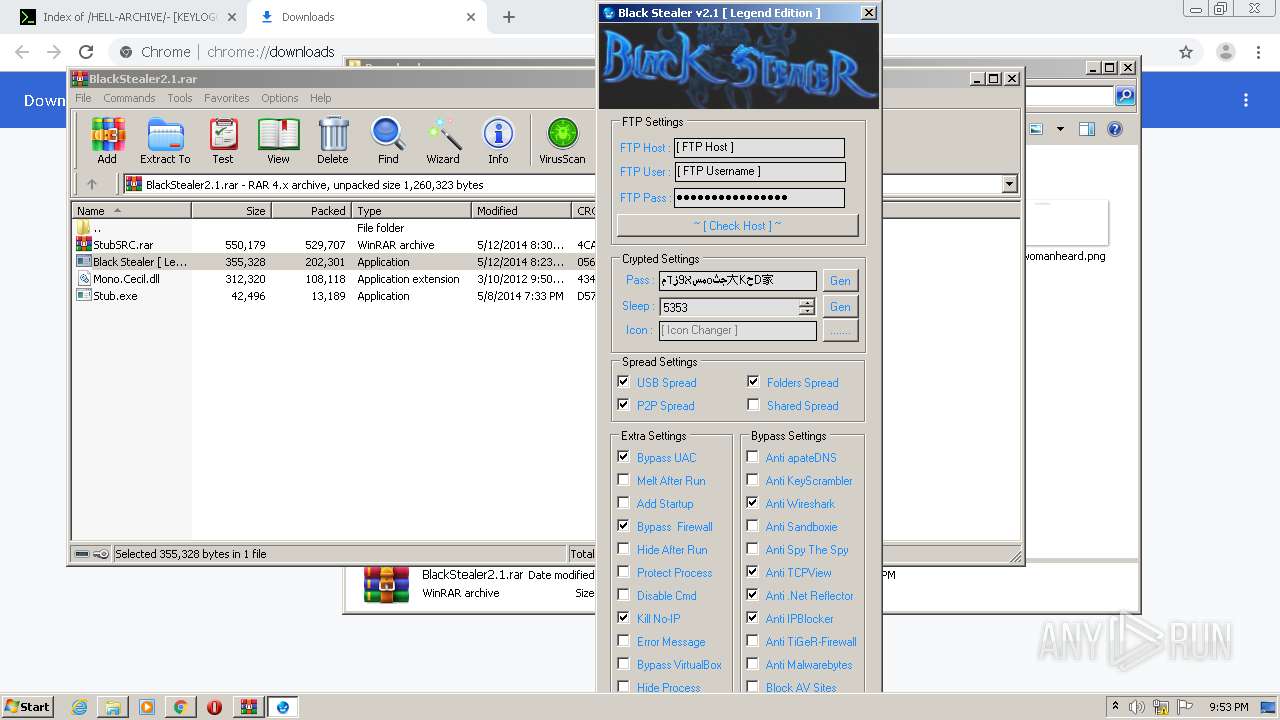
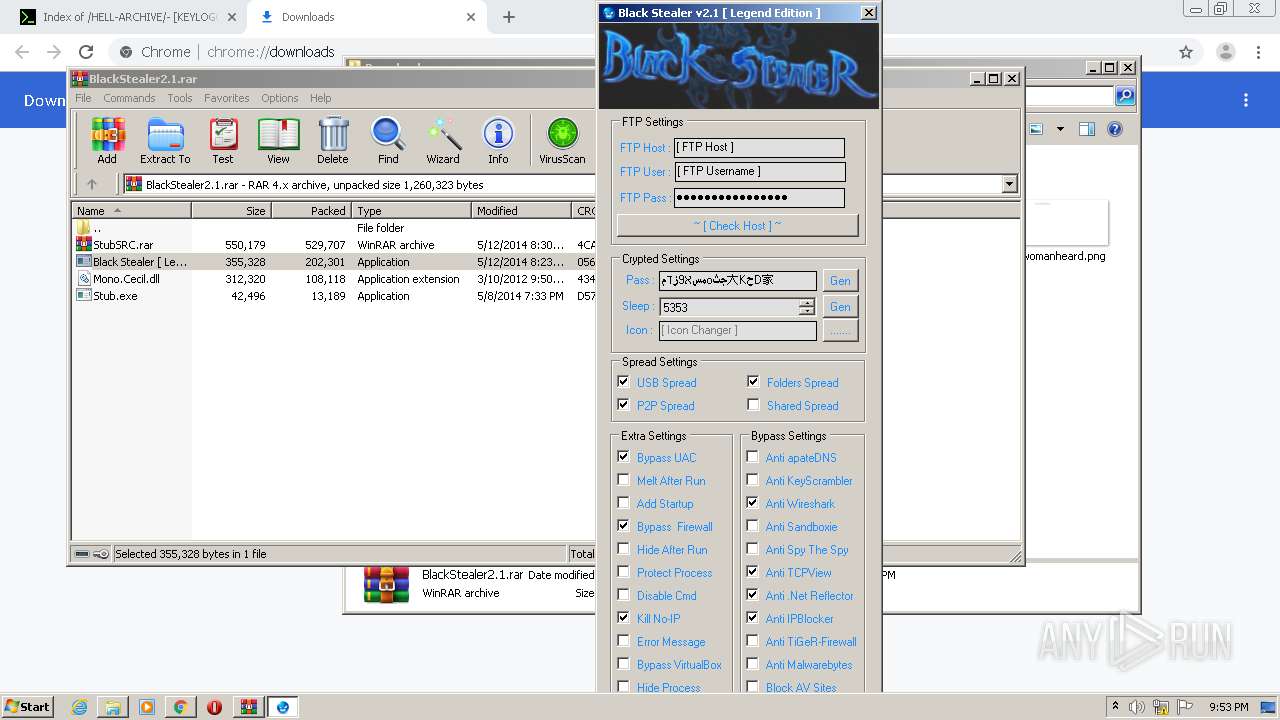
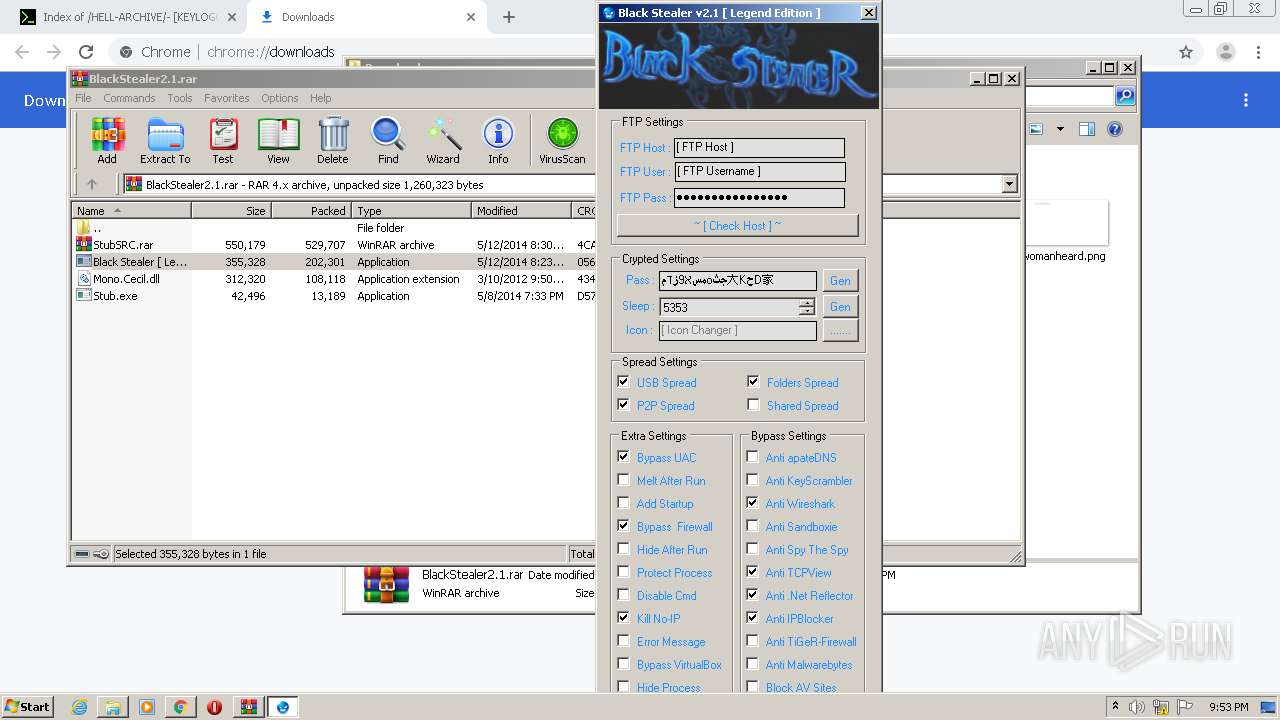
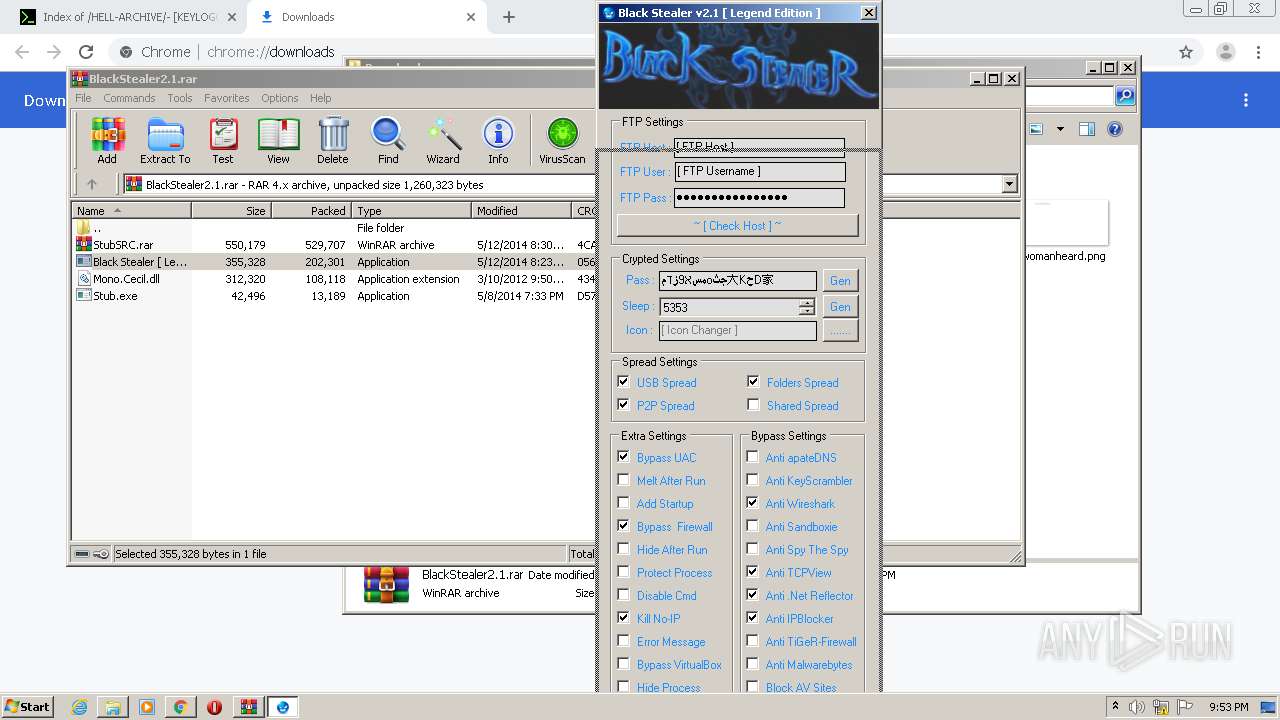
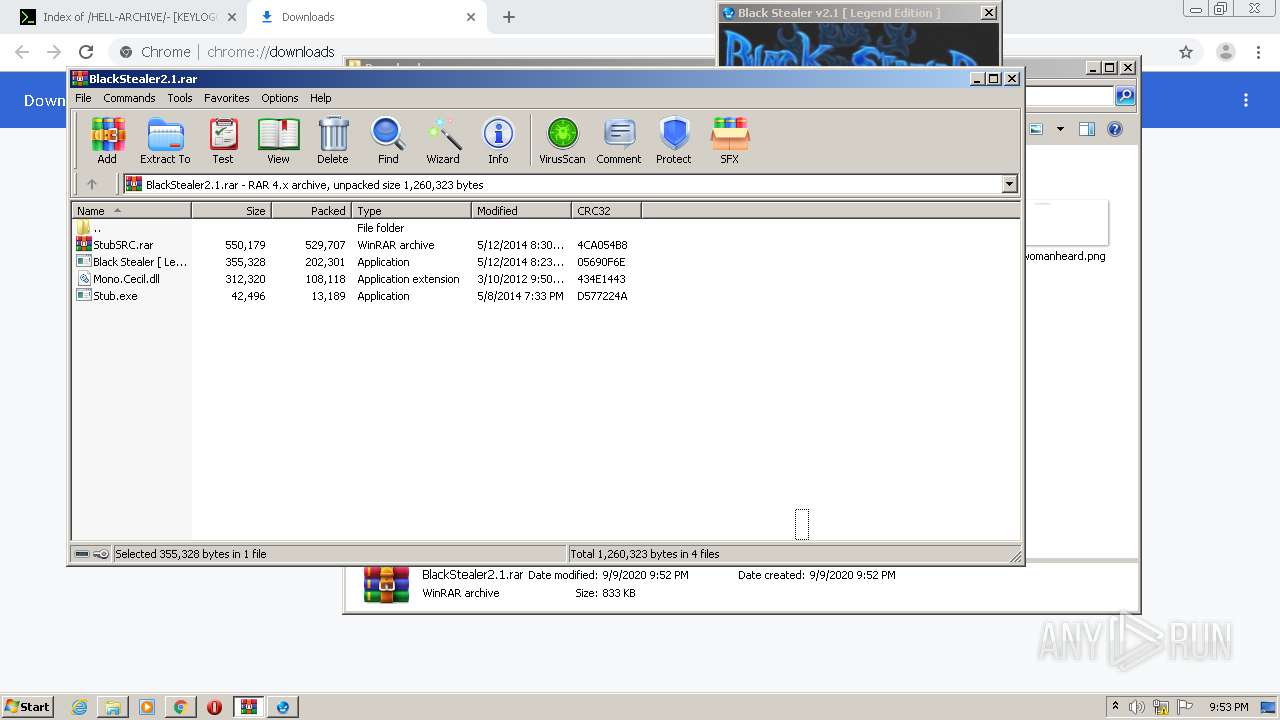
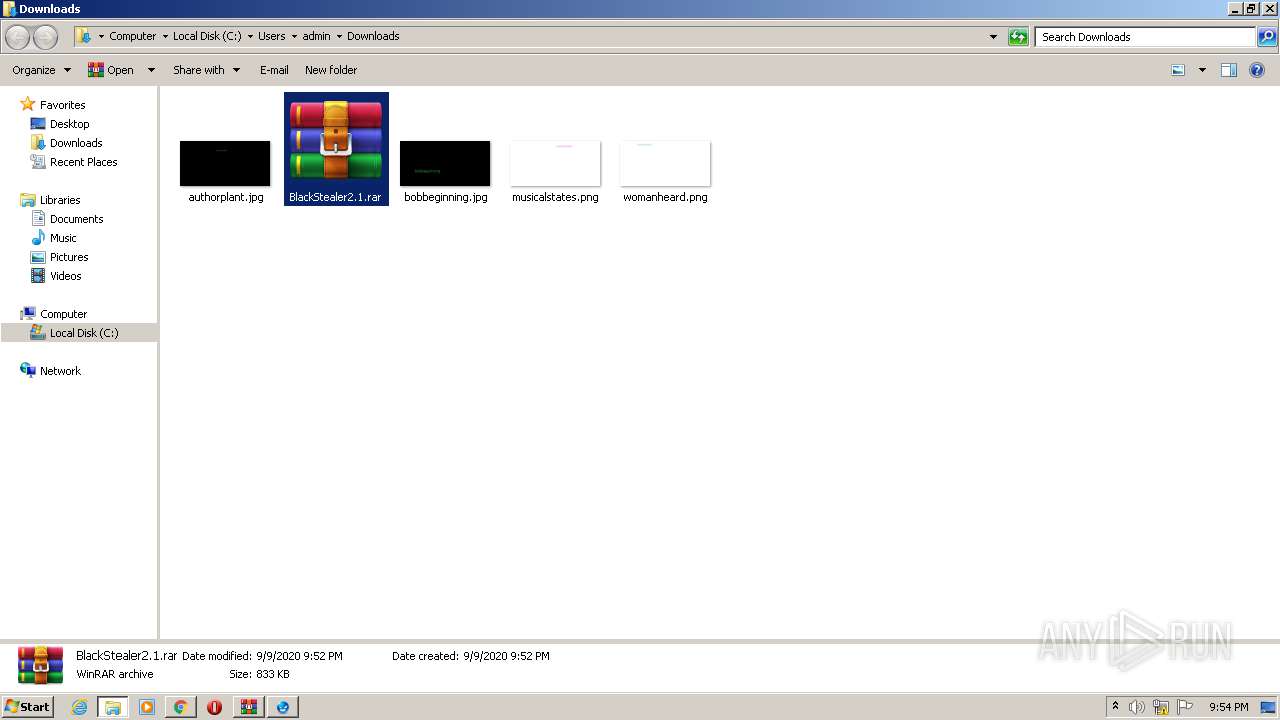
| URL: | https://b4ckdoorarchive.club/HELL-ARCHIVE/-%20%5bKEYLOGGER%5d/Black%20Stealer%202.1/ |
| Full analysis: | https://app.any.run/tasks/9ad000dd-d9da-4f31-ae84-717287afa4c3 |
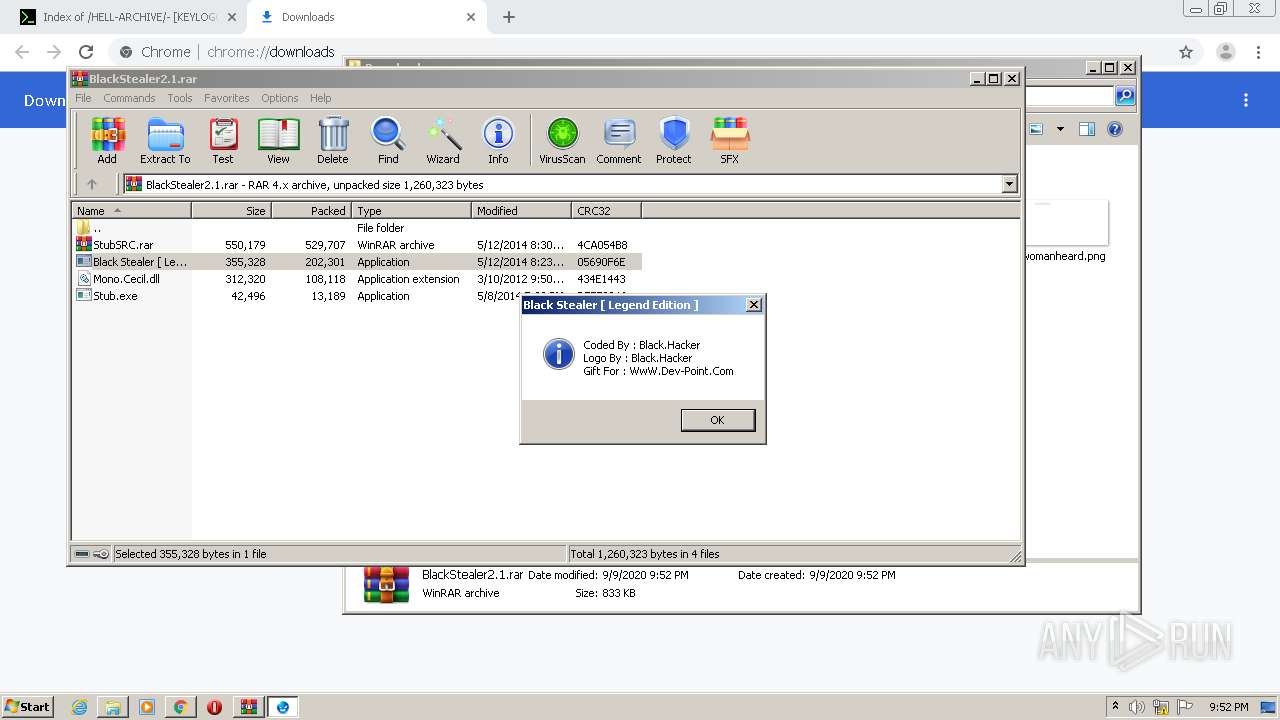
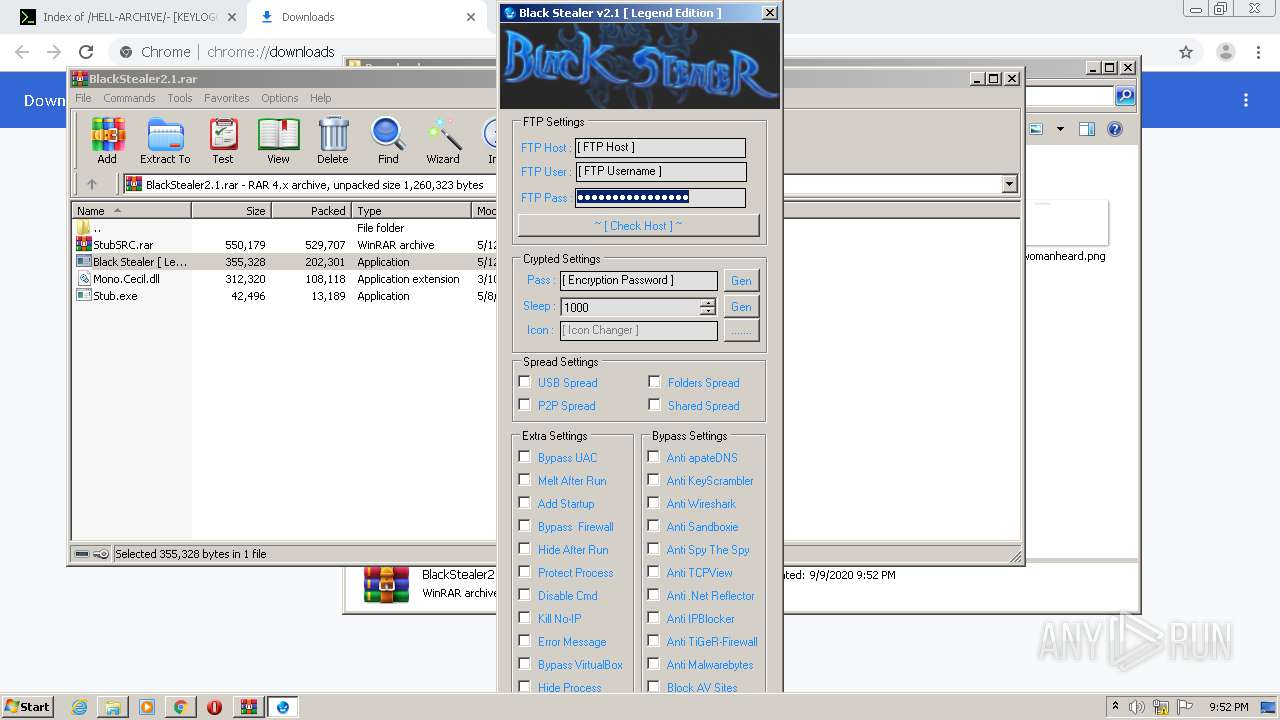
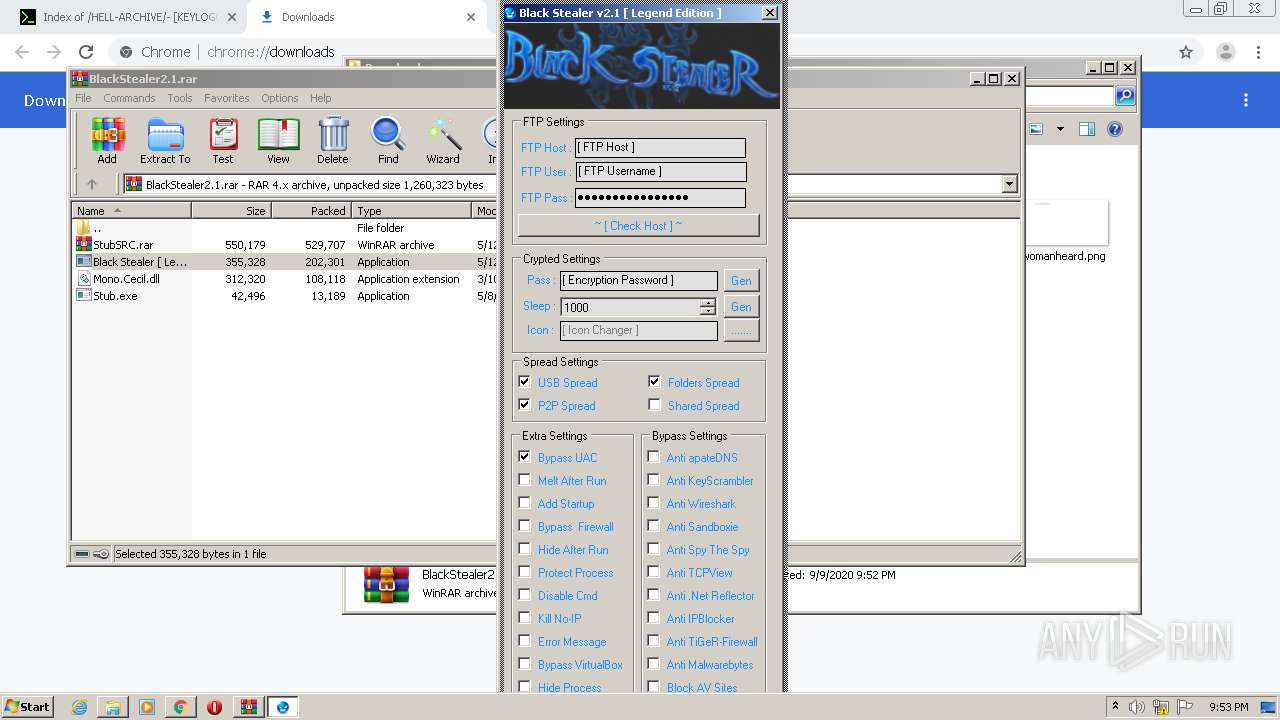
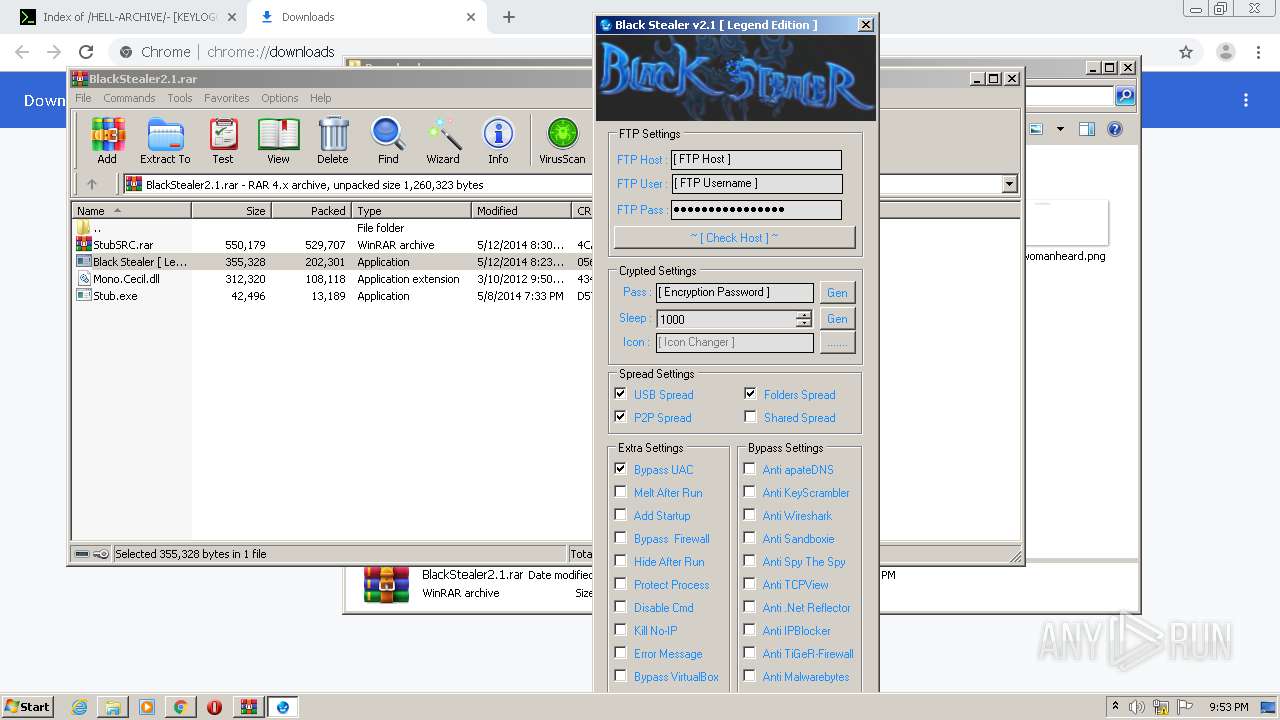
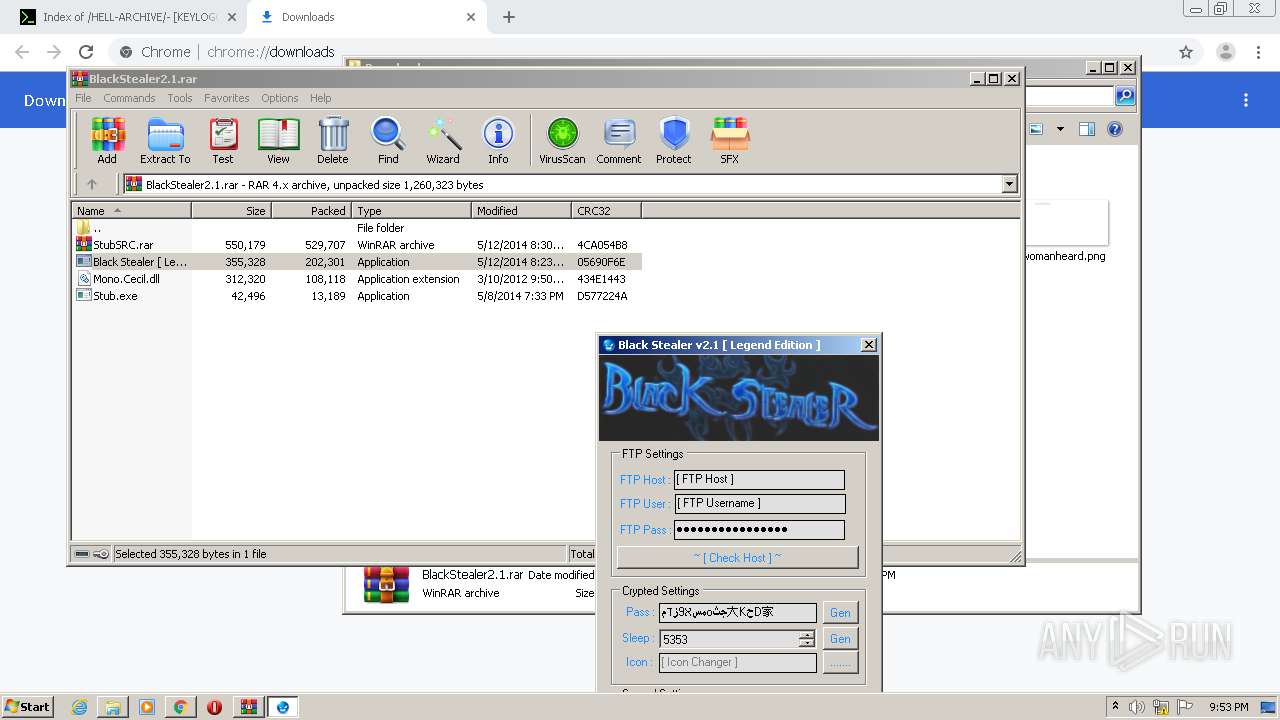
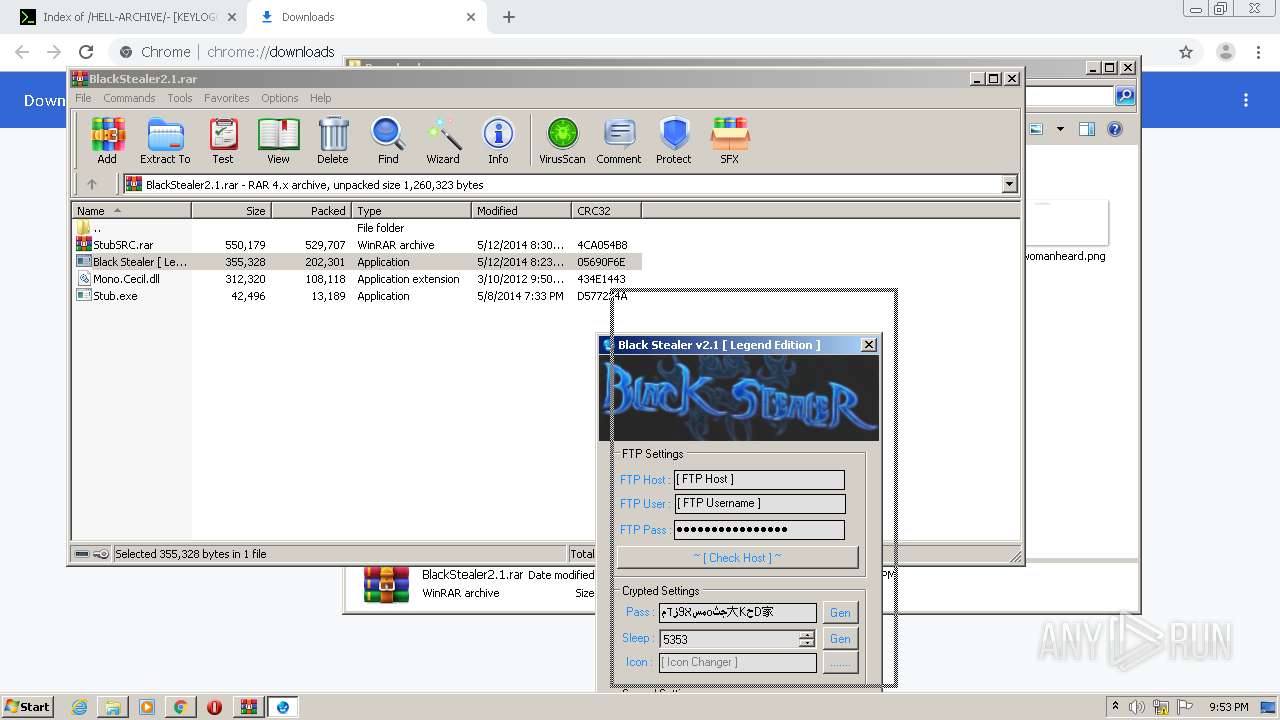
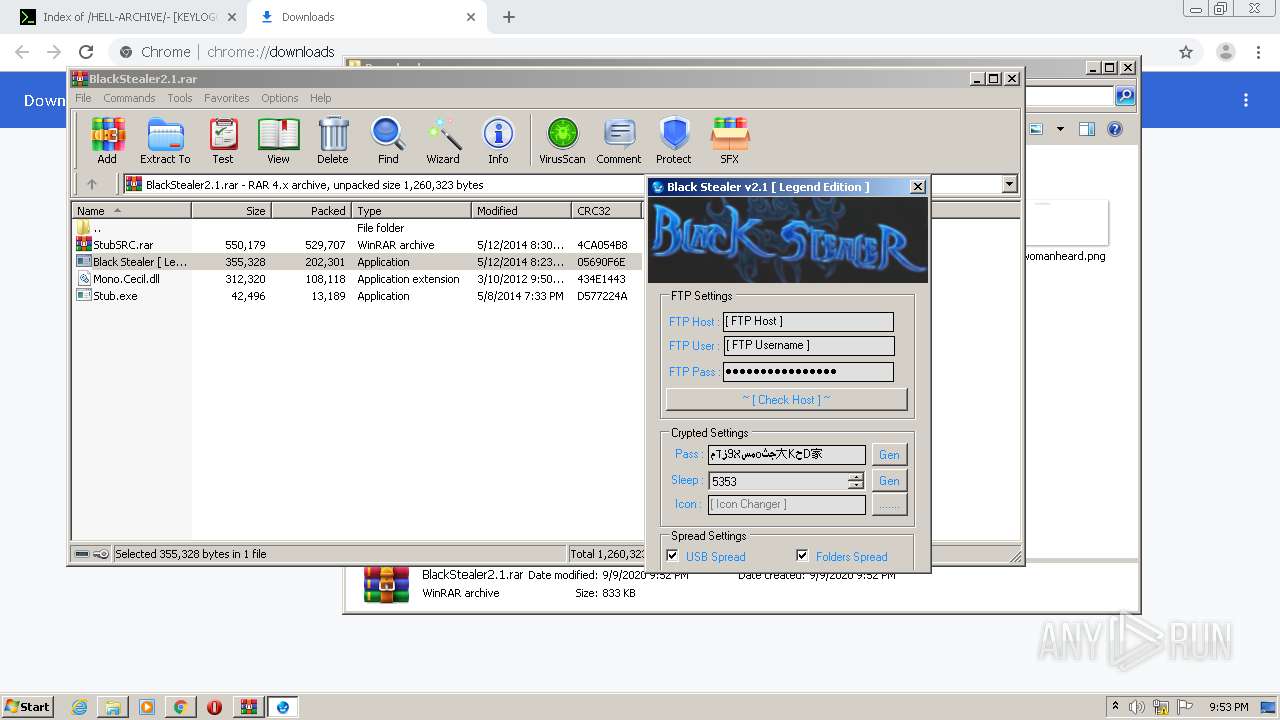
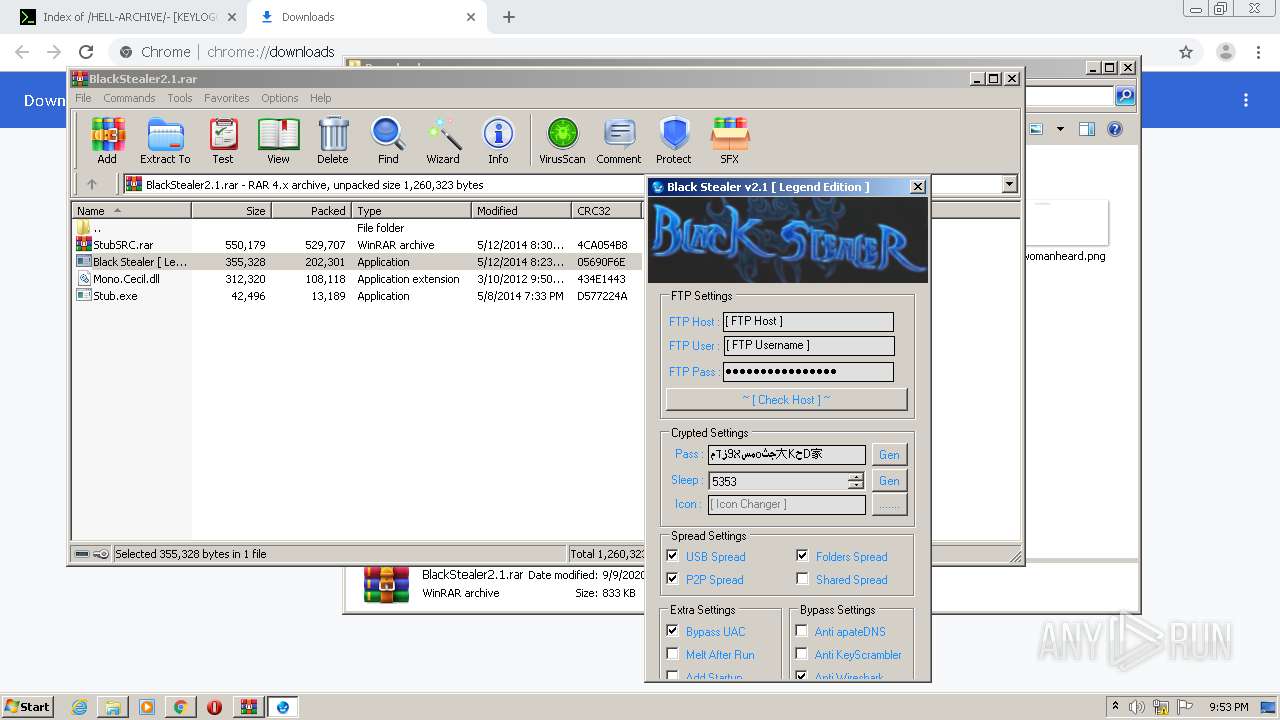
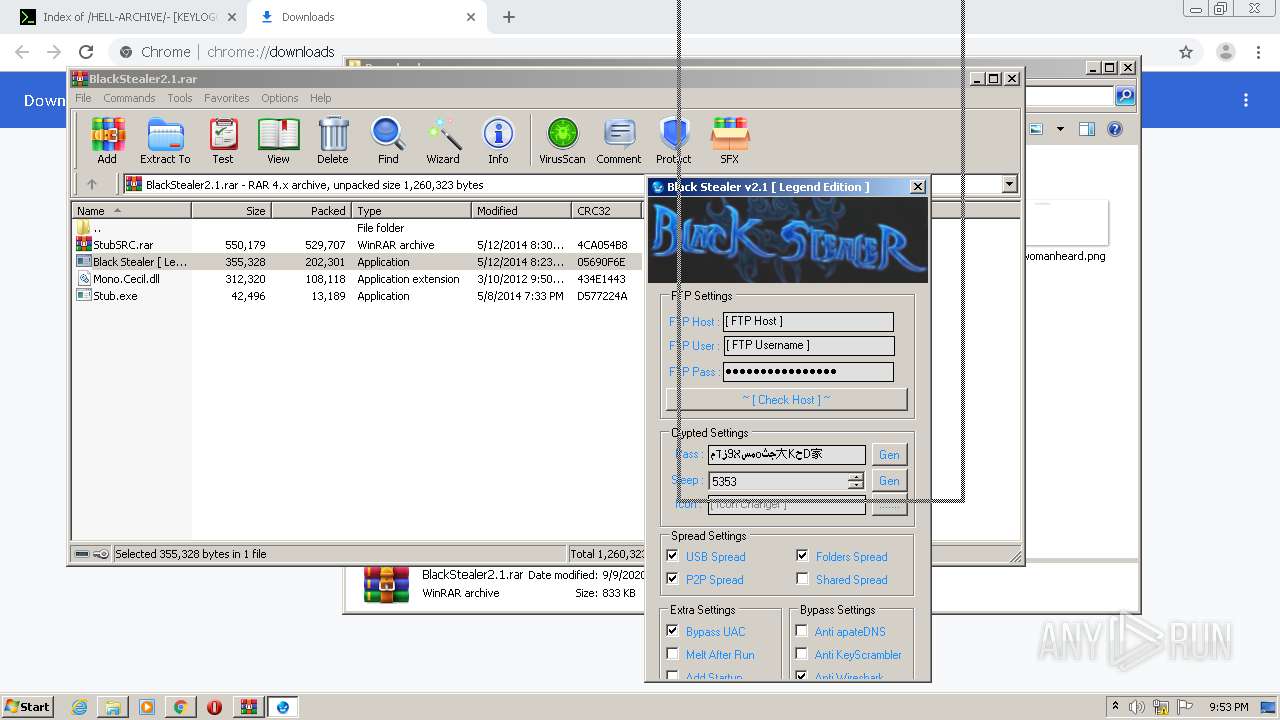
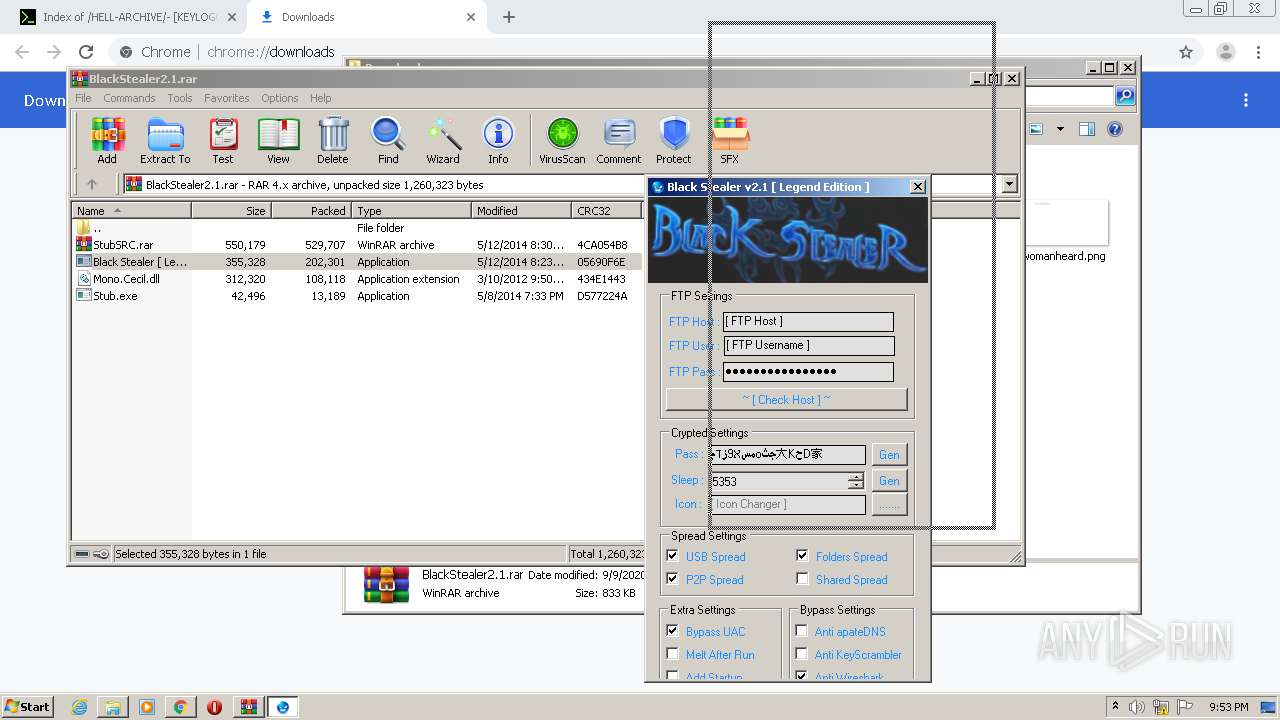
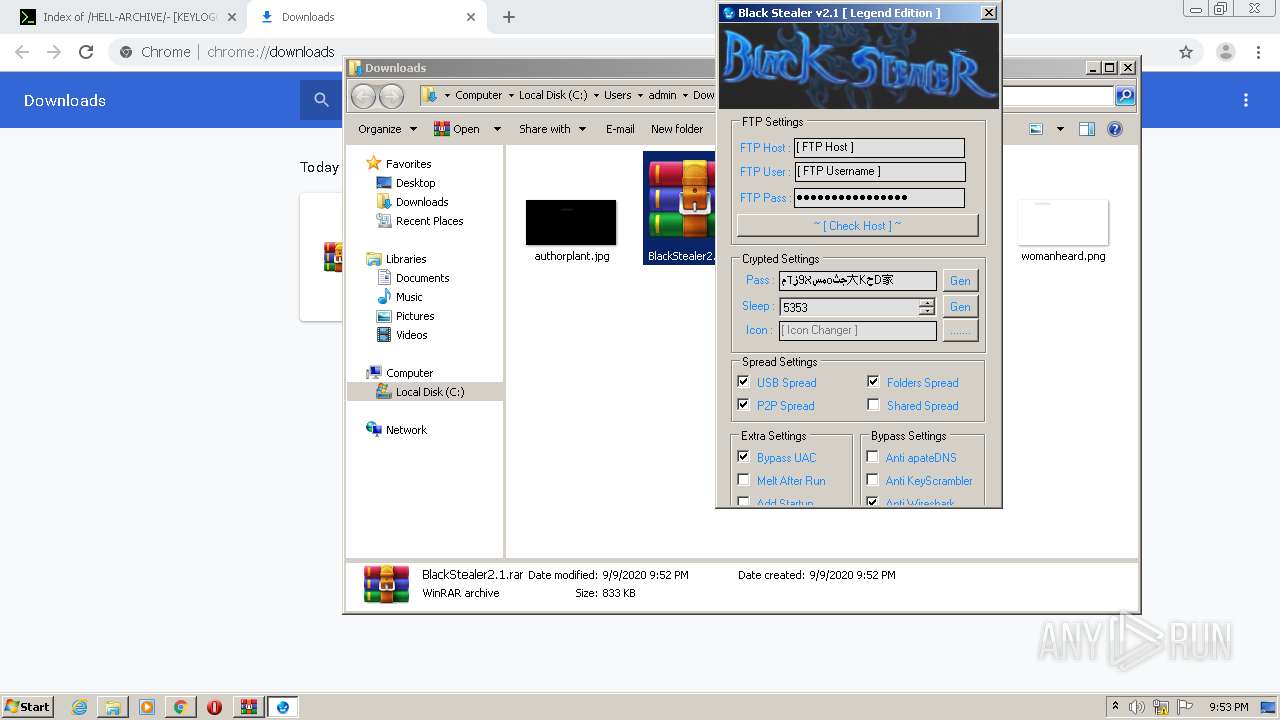
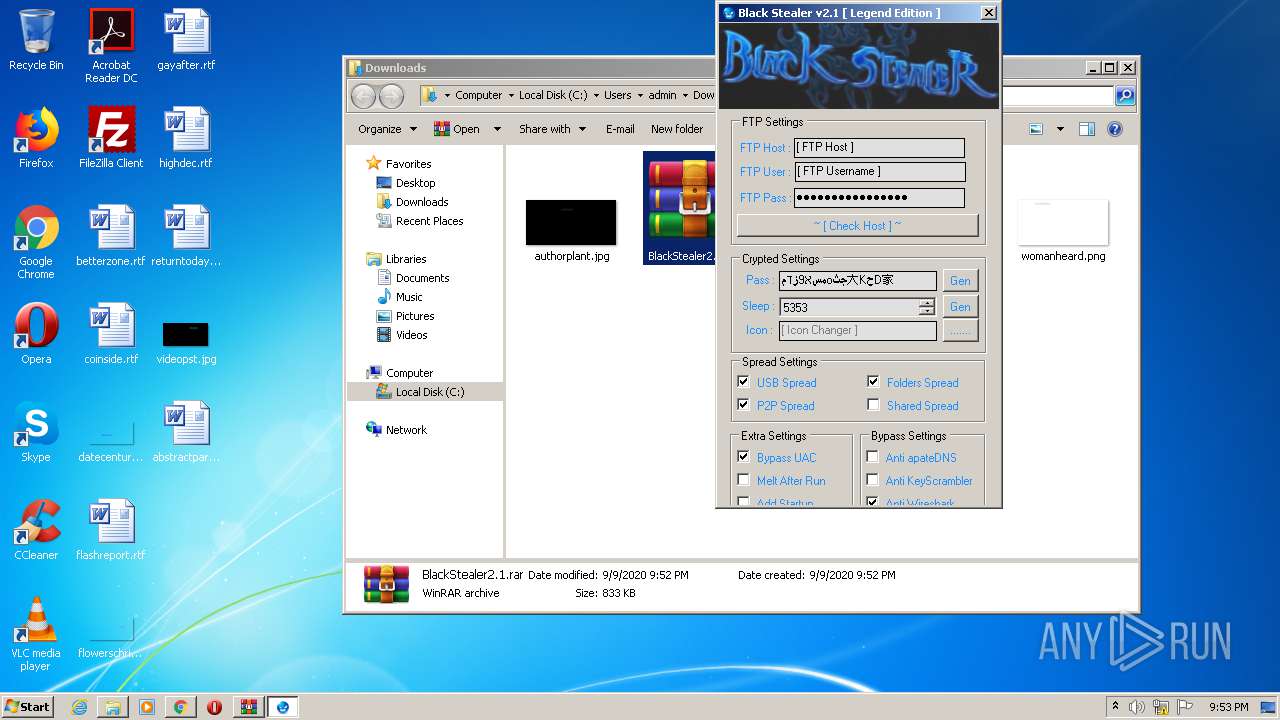
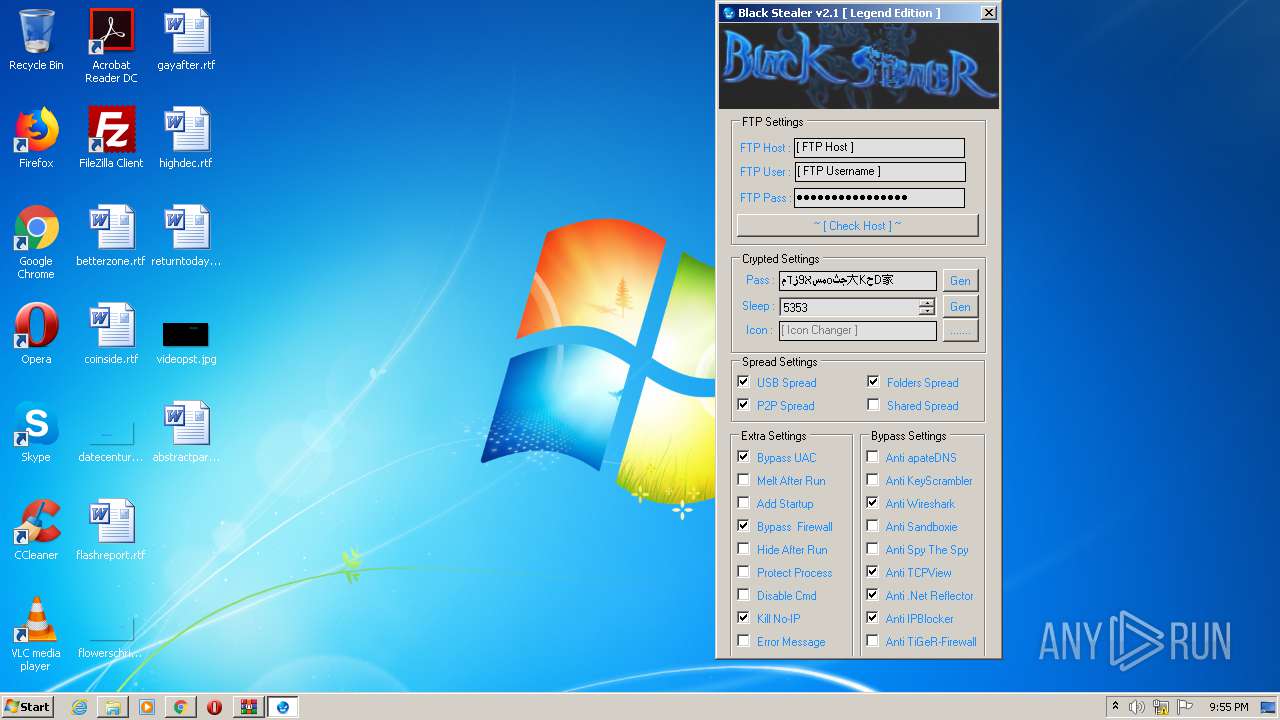
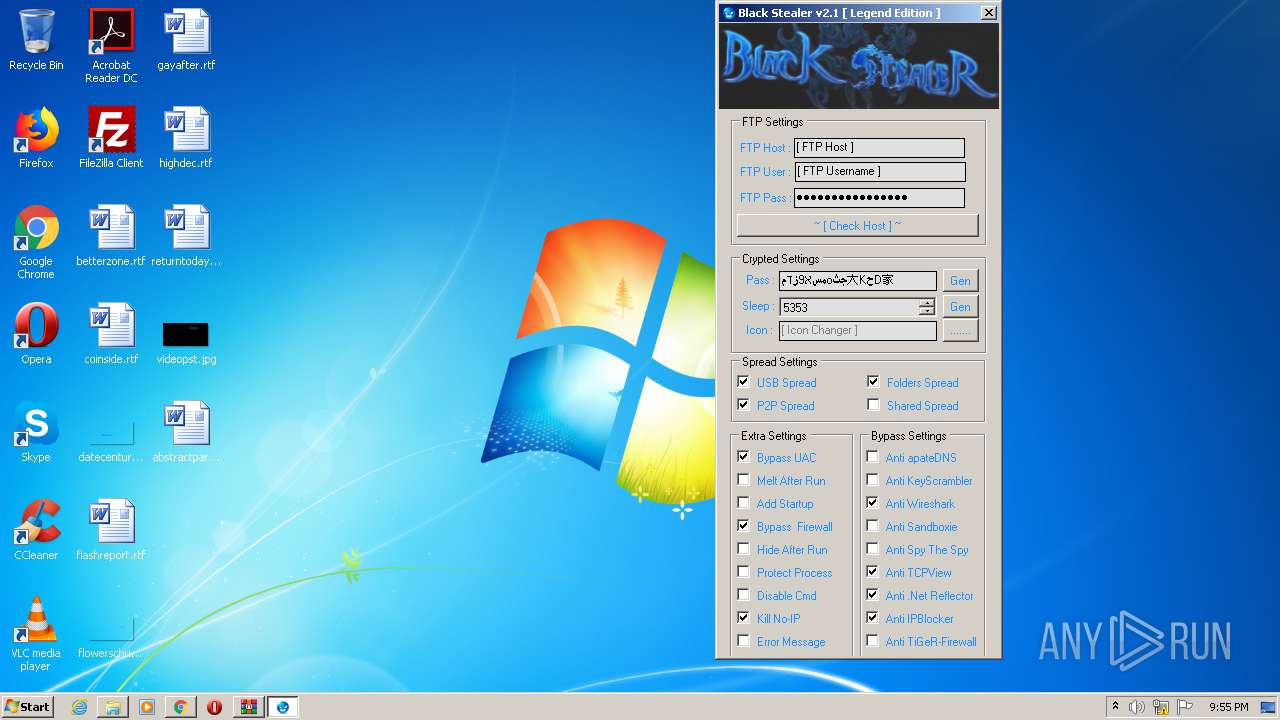
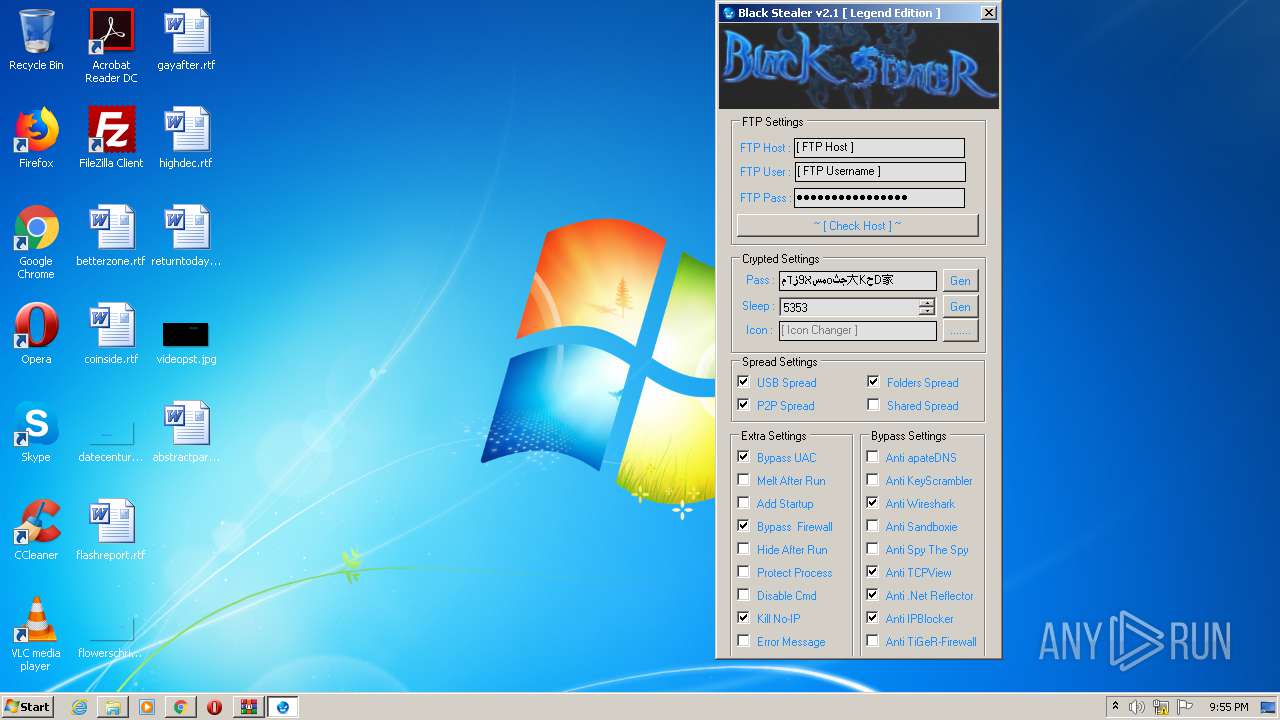
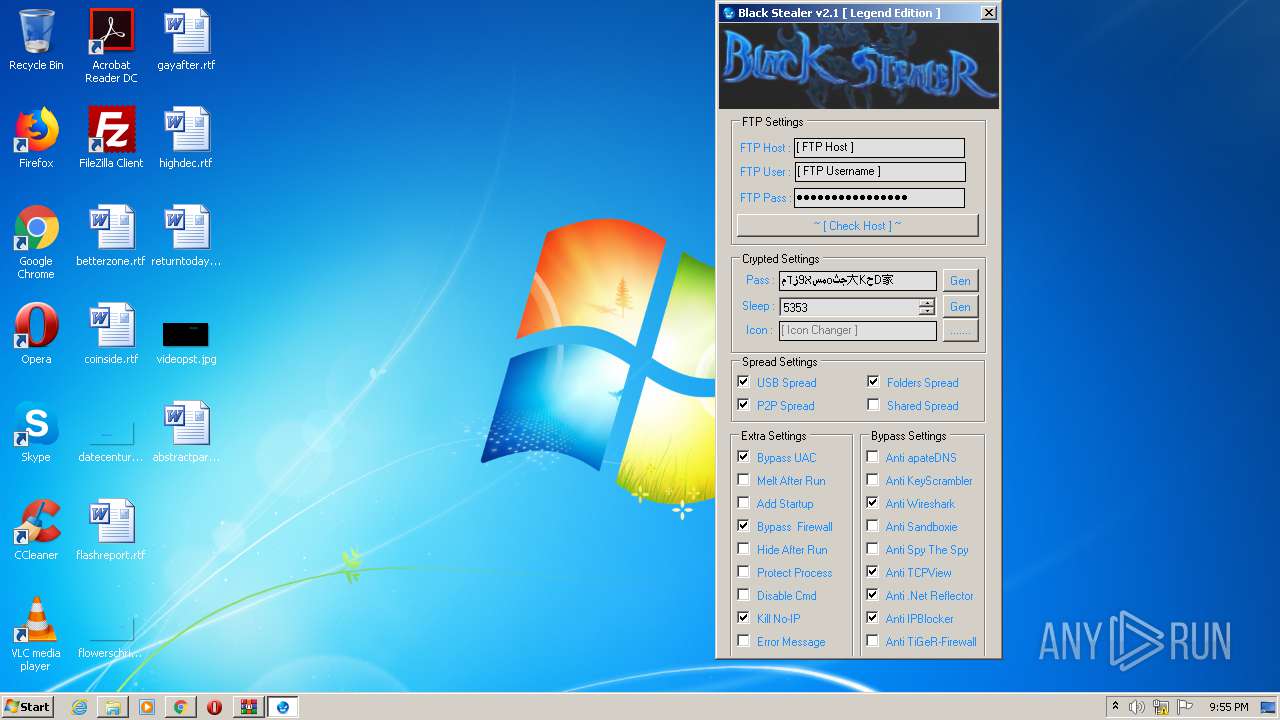
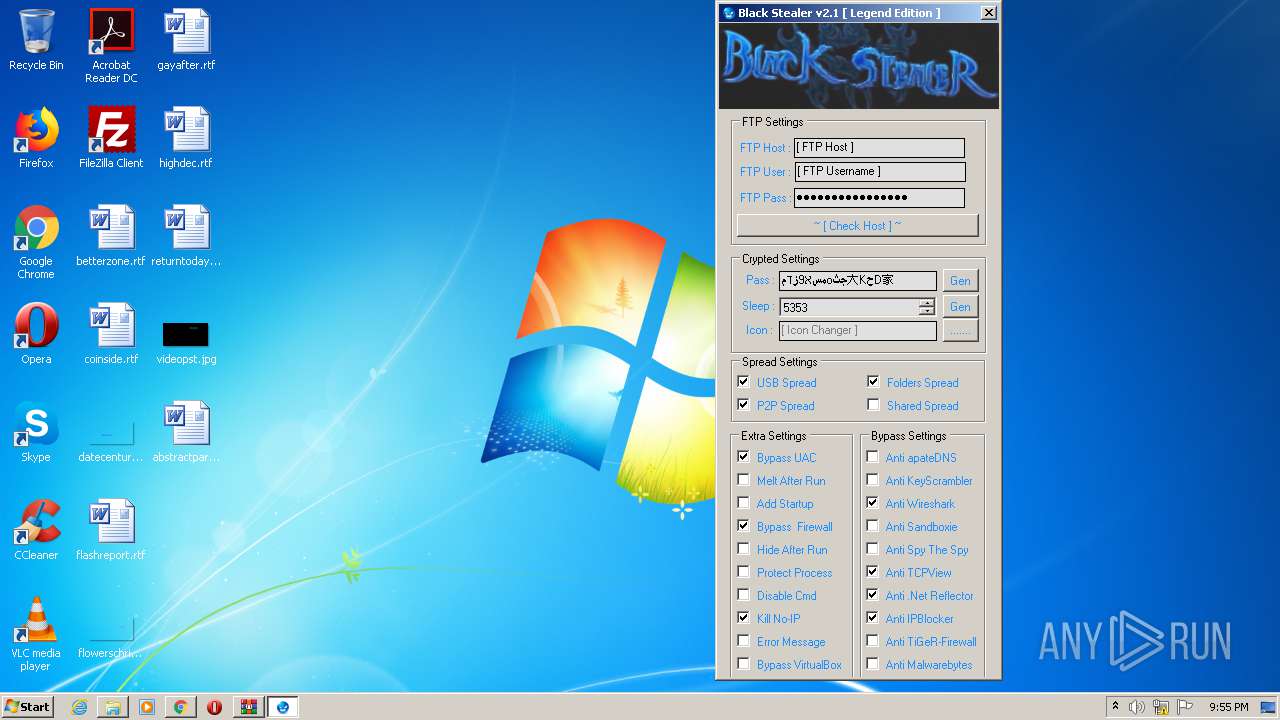
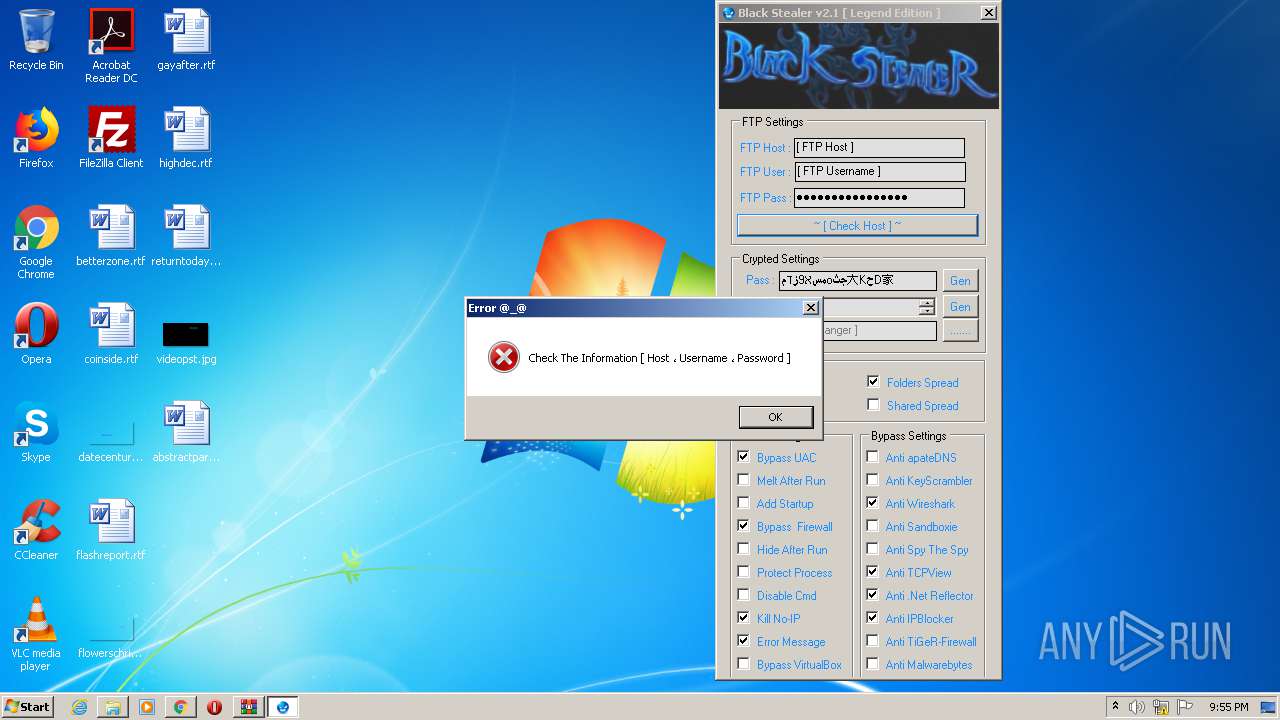
| Verdict: | Malicious activity |
| Analysis date: | September 09, 2020, 20:52:07 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | C77C27990F5187EF4B791F9B78534810 |
| SHA1: | 6CA51B94B195D4FDAC18B7E8A8A8C6BABD1C07E5 |
| SHA256: | 86C9E98F8761063BF26F08B01177E3615B9F1E3400C1E2C89D09233DD2CF667A |
| SSDEEP: | 3:N8/GOBRwTJJzuWezgzQHkpcgwTKGOhRhJAWXLT:2hbwTJJzggzQEpcTTKZhzJA+ |
MALICIOUS
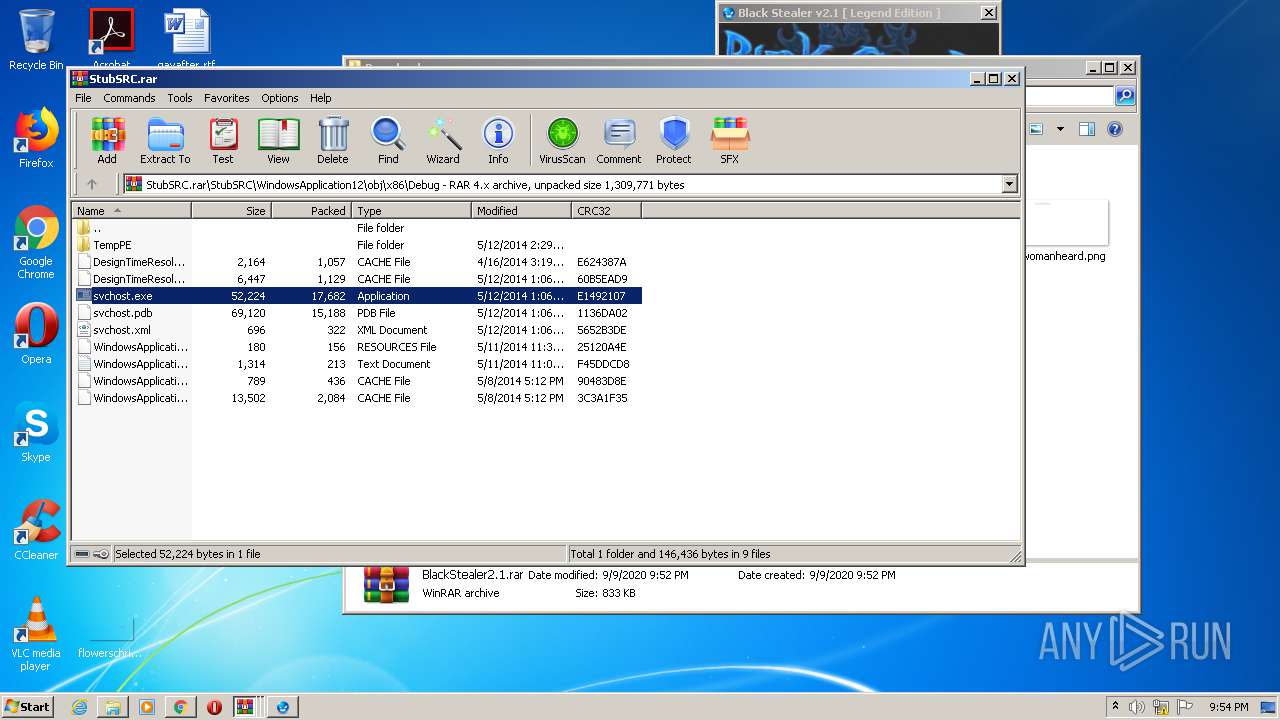
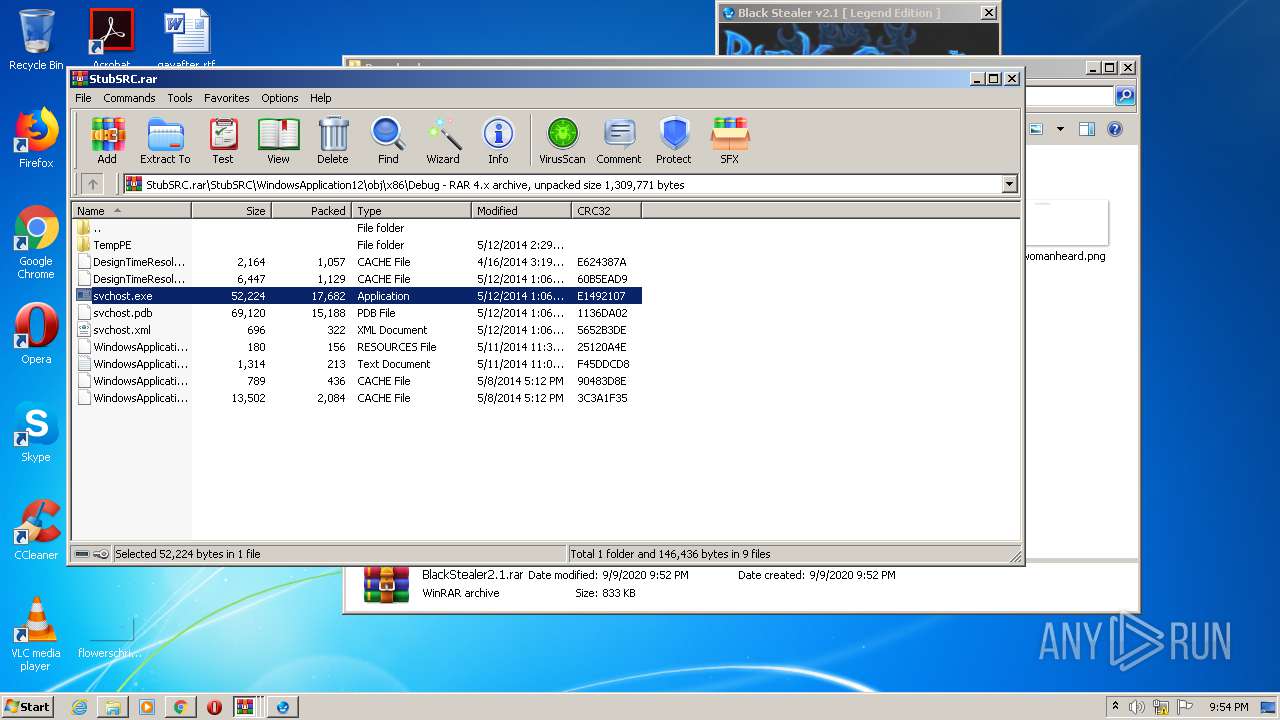
Application was dropped or rewritten from another process
- Black Stealer [ Legend Edition].exe (PID: 3352)
- svchost.exe (PID: 1944)
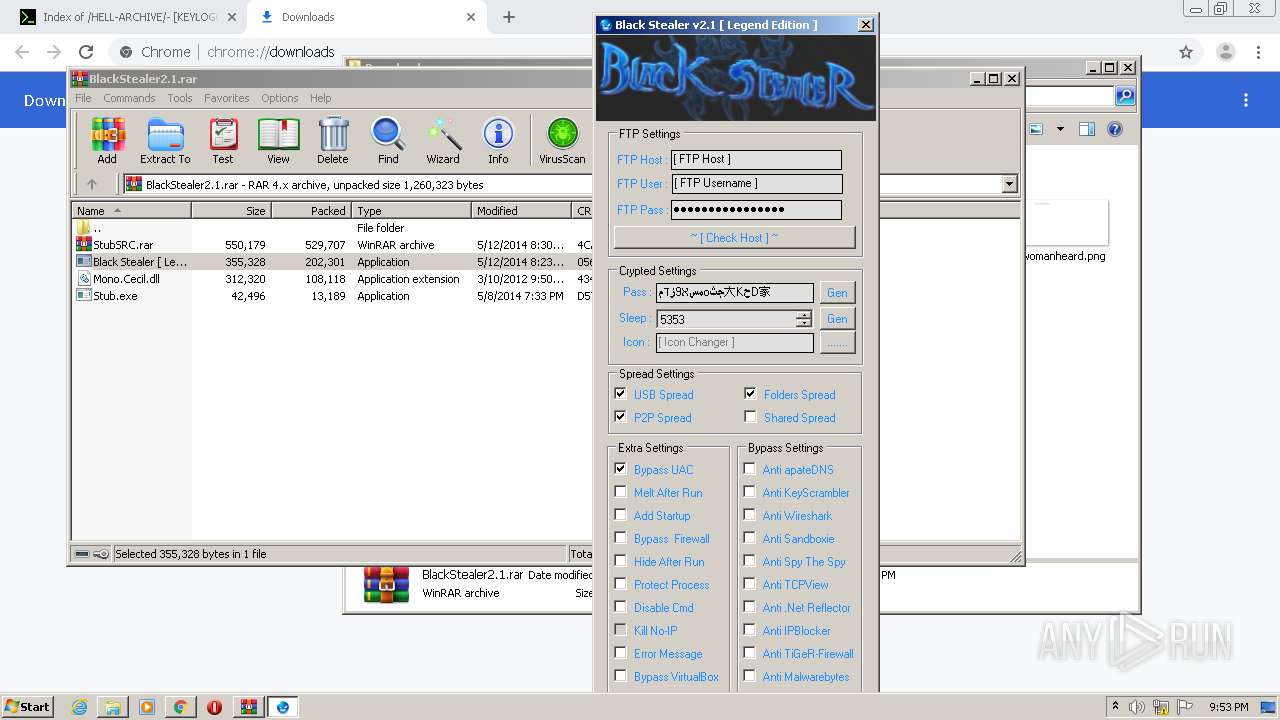
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 1340)
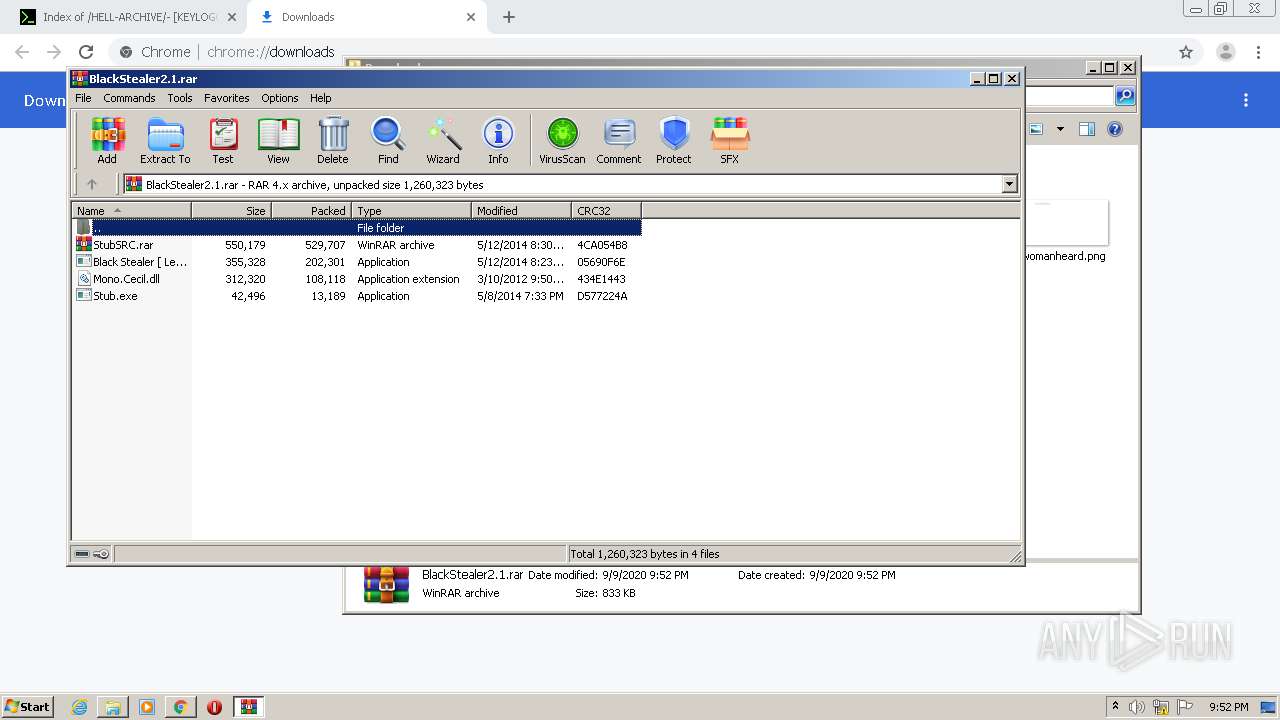
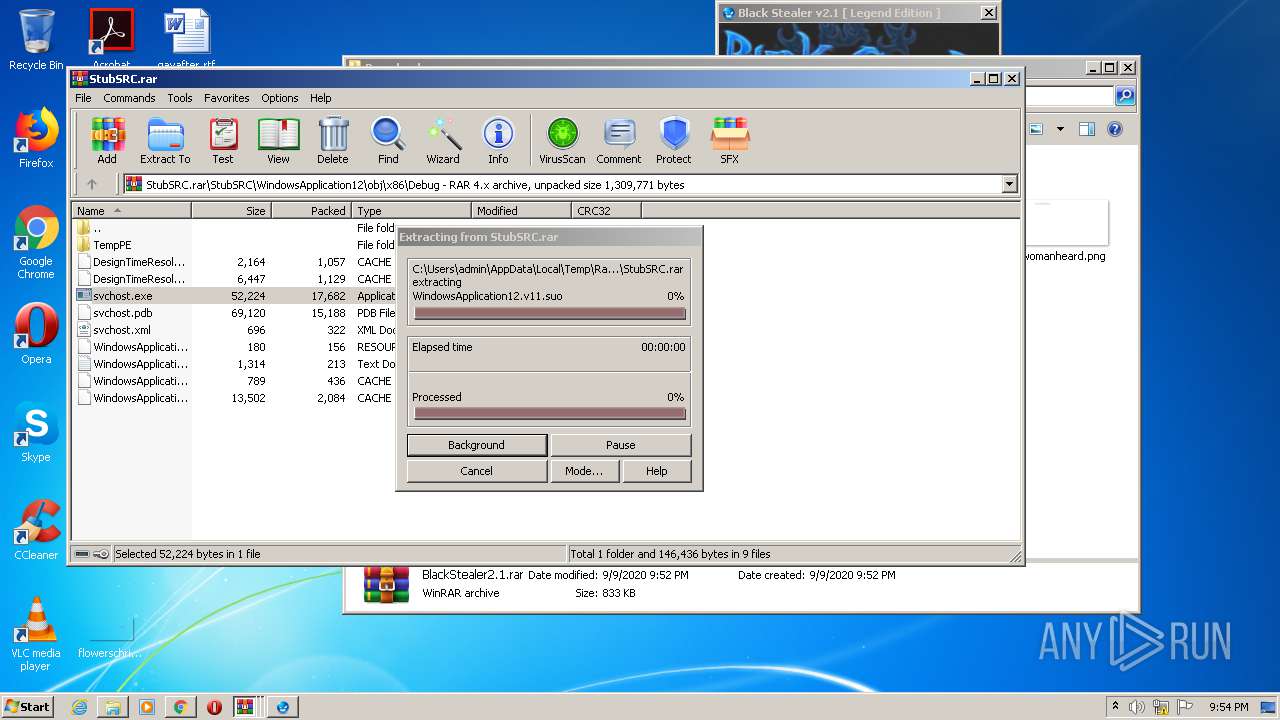
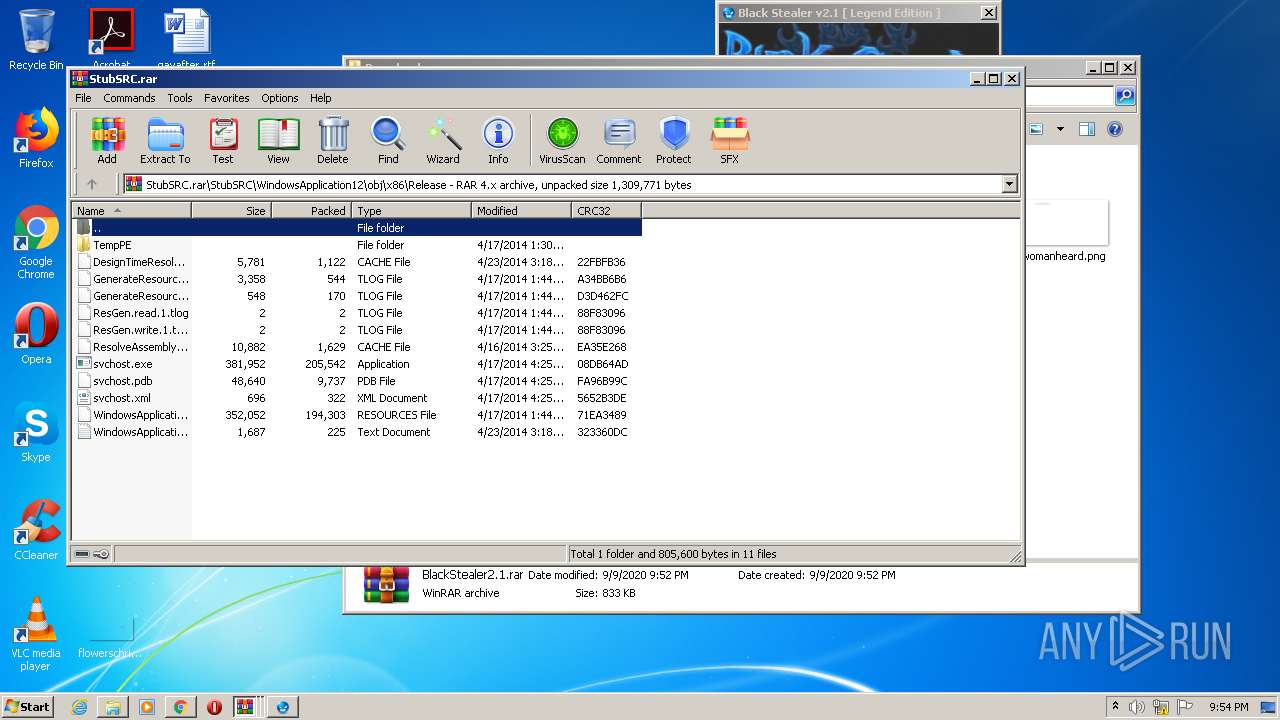
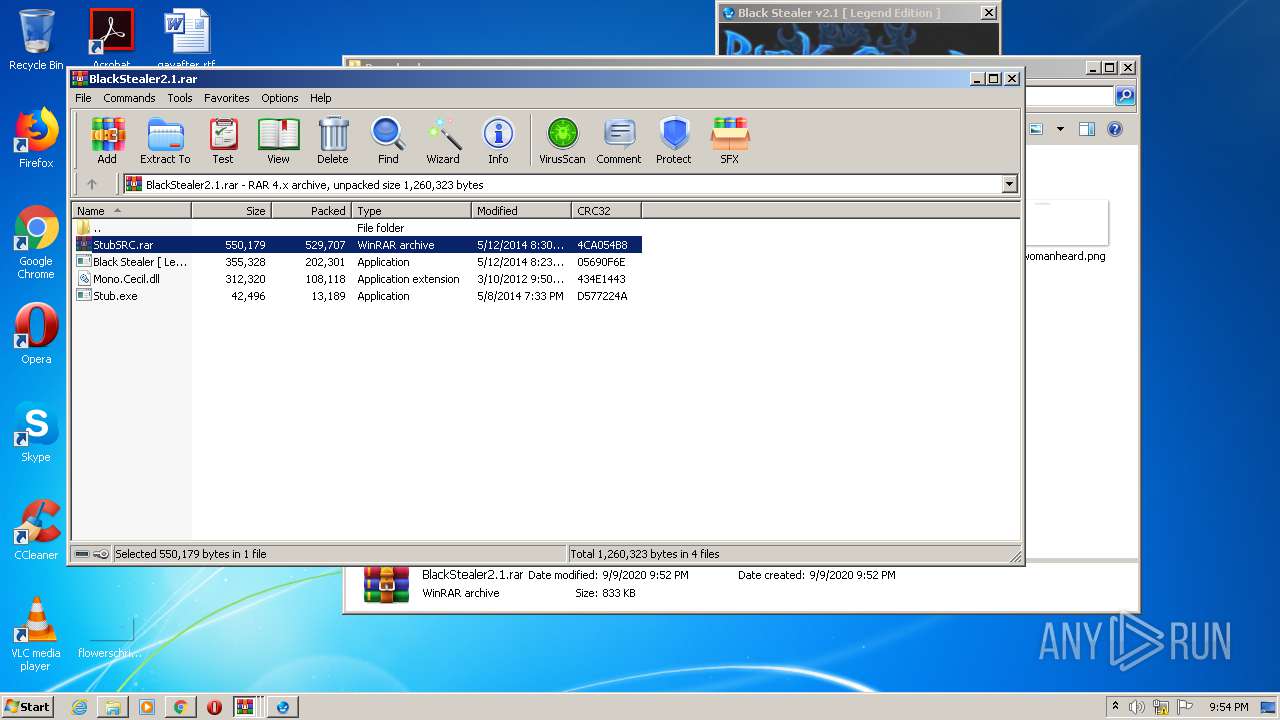
Executable content was dropped or overwritten
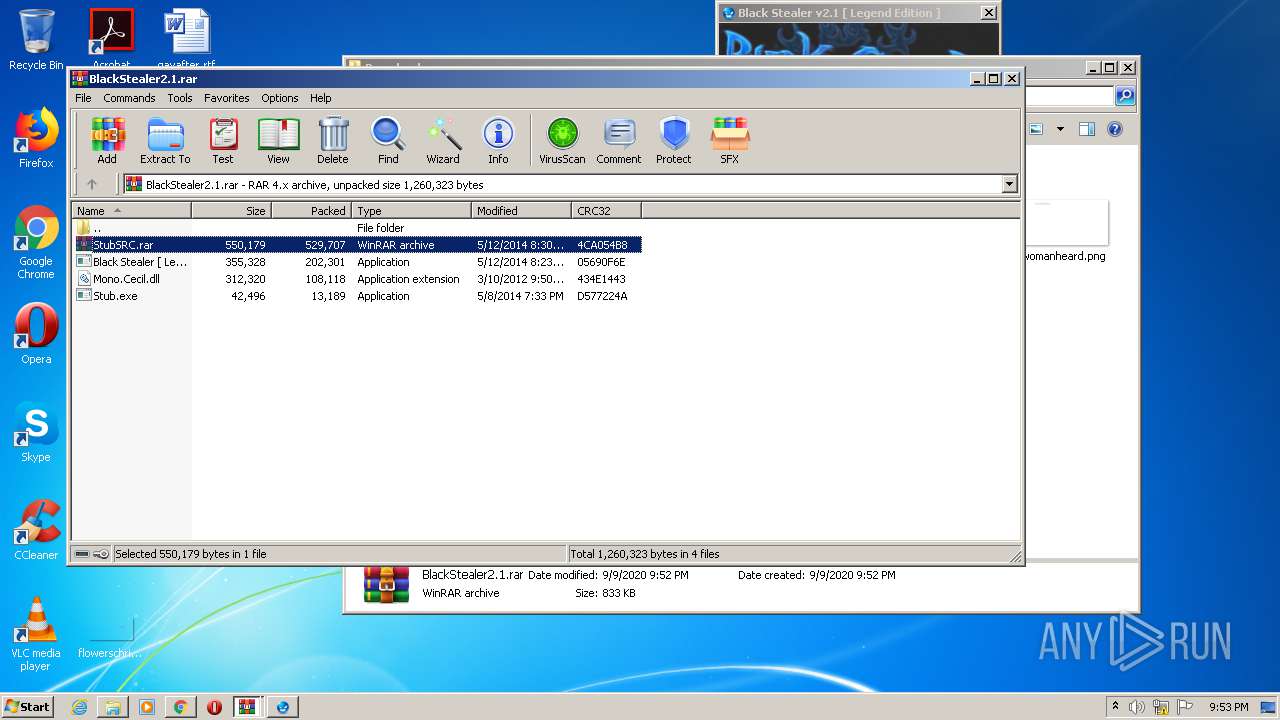
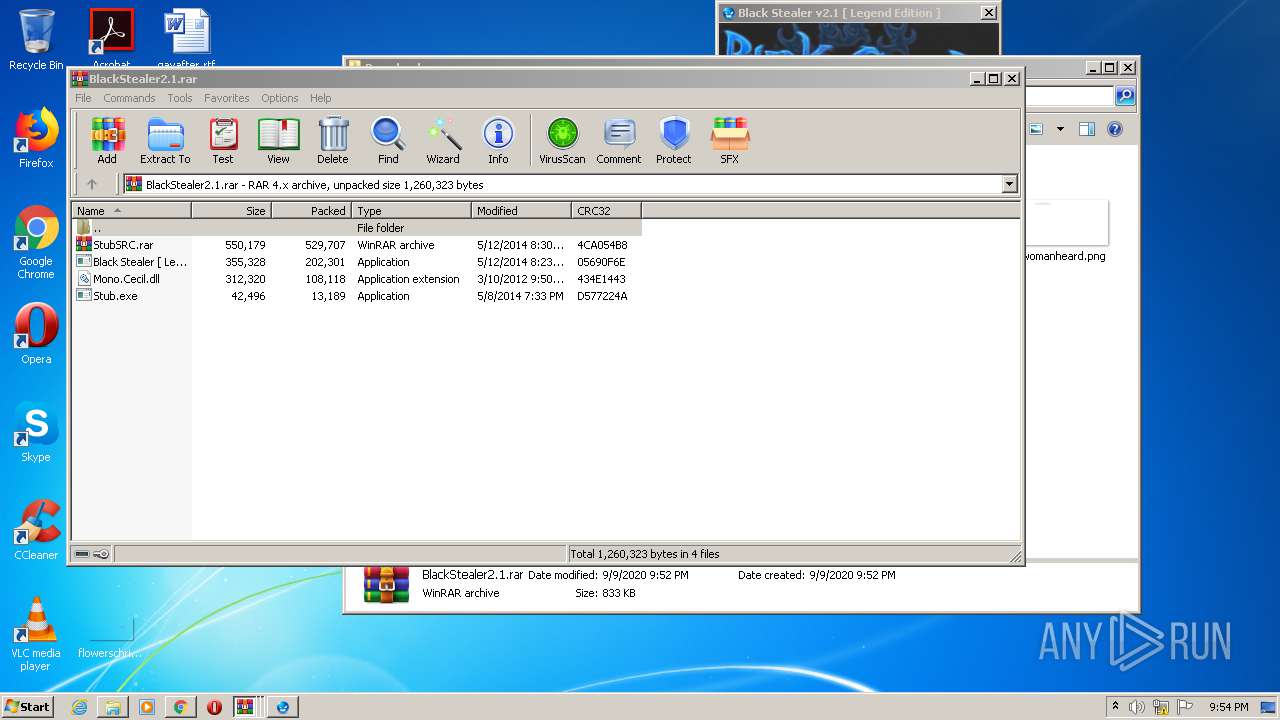
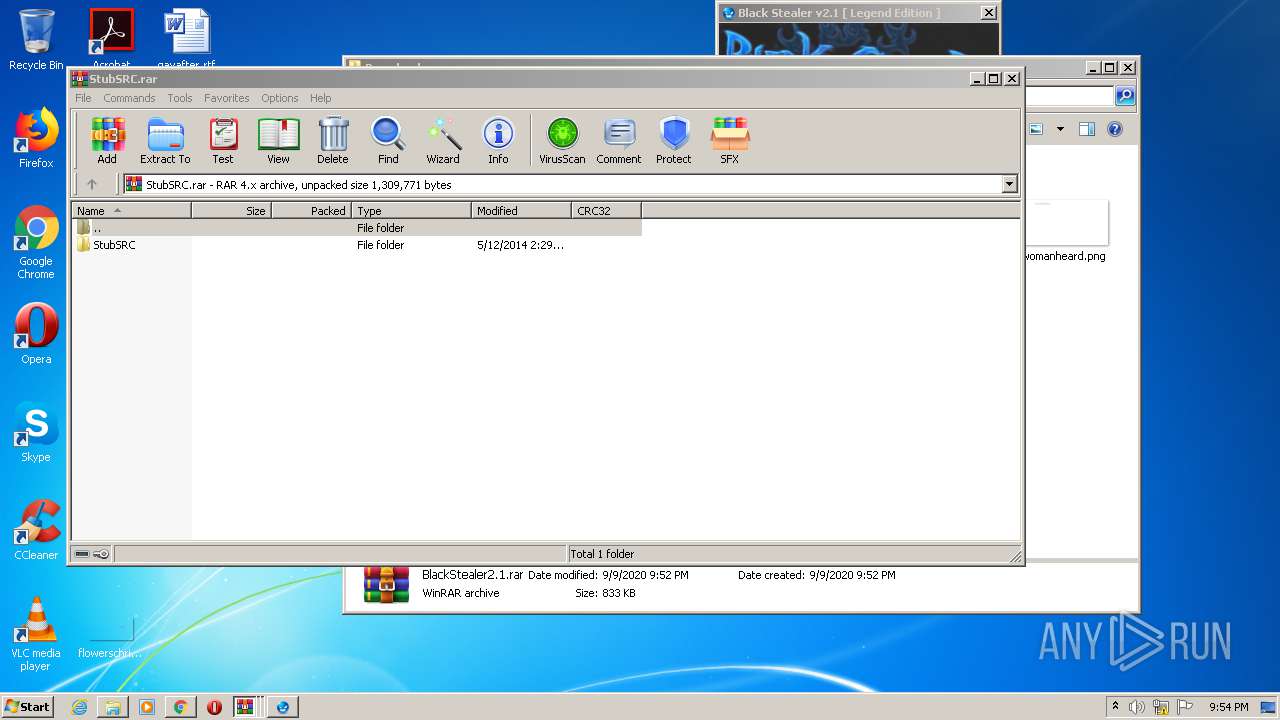
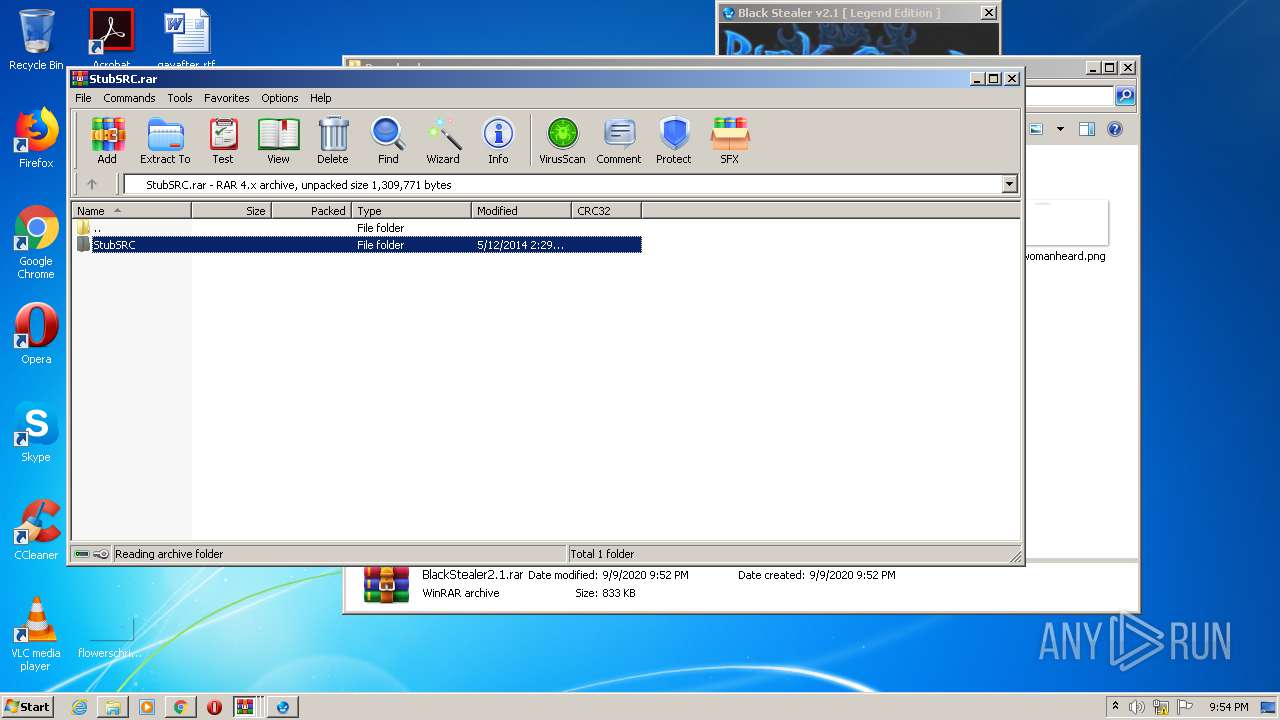
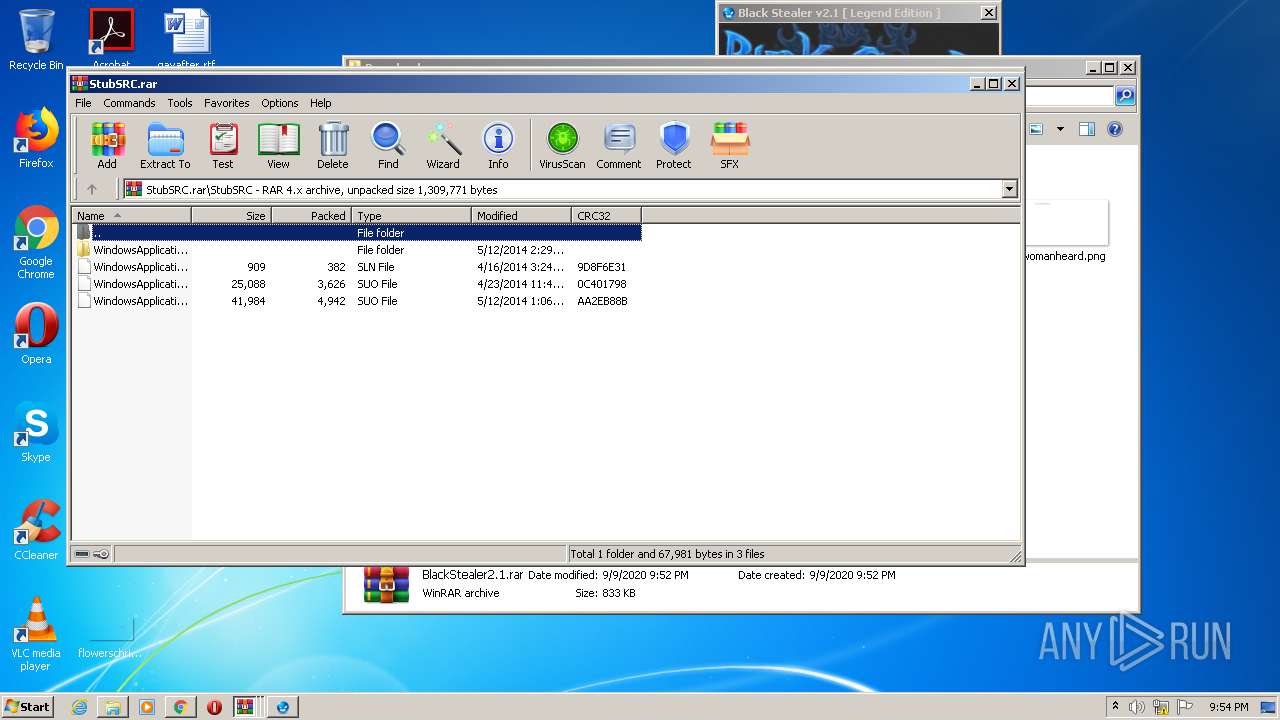
- WinRAR.exe (PID: 3340)
- WinRAR.exe (PID: 1444)
Application launched itself
- WinRAR.exe (PID: 2284)
- WinRAR.exe (PID: 3908)
Creates executable files which already exist in Windows
- WinRAR.exe (PID: 1444)
Checks for external IP
- svchost.exe (PID: 1944)
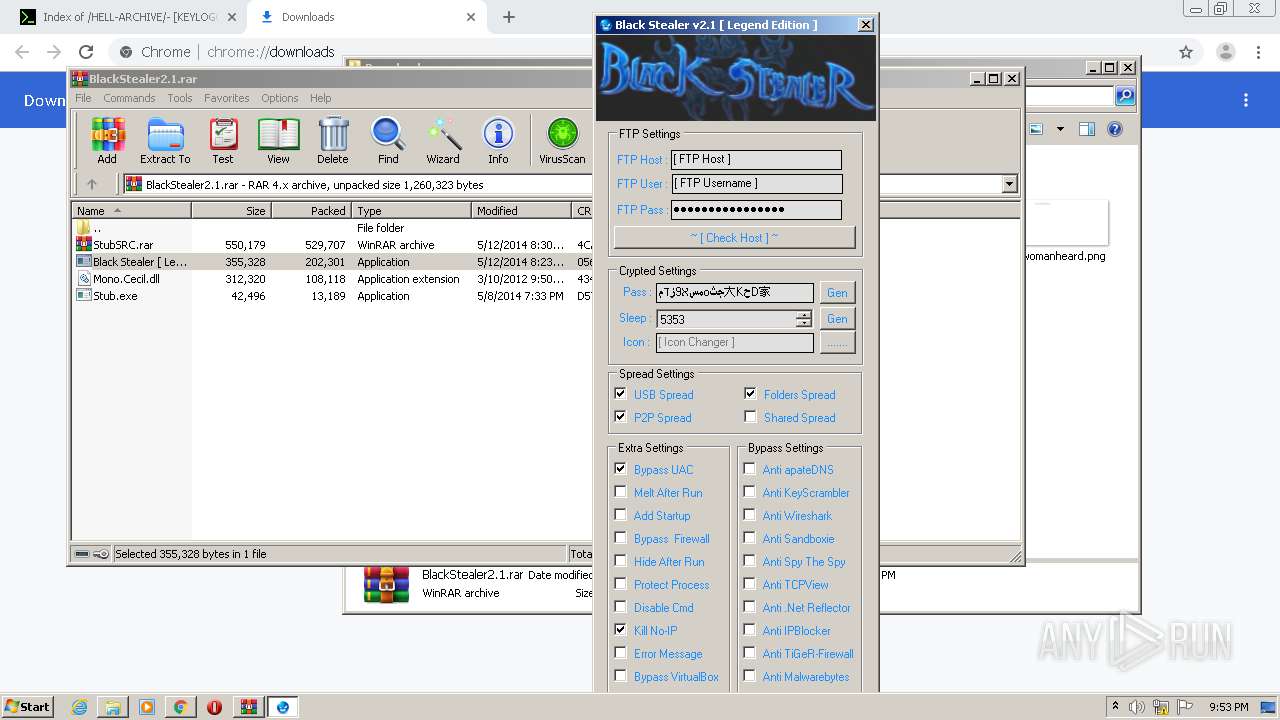
INFO
Reads settings of System Certificates
- chrome.exe (PID: 2944)
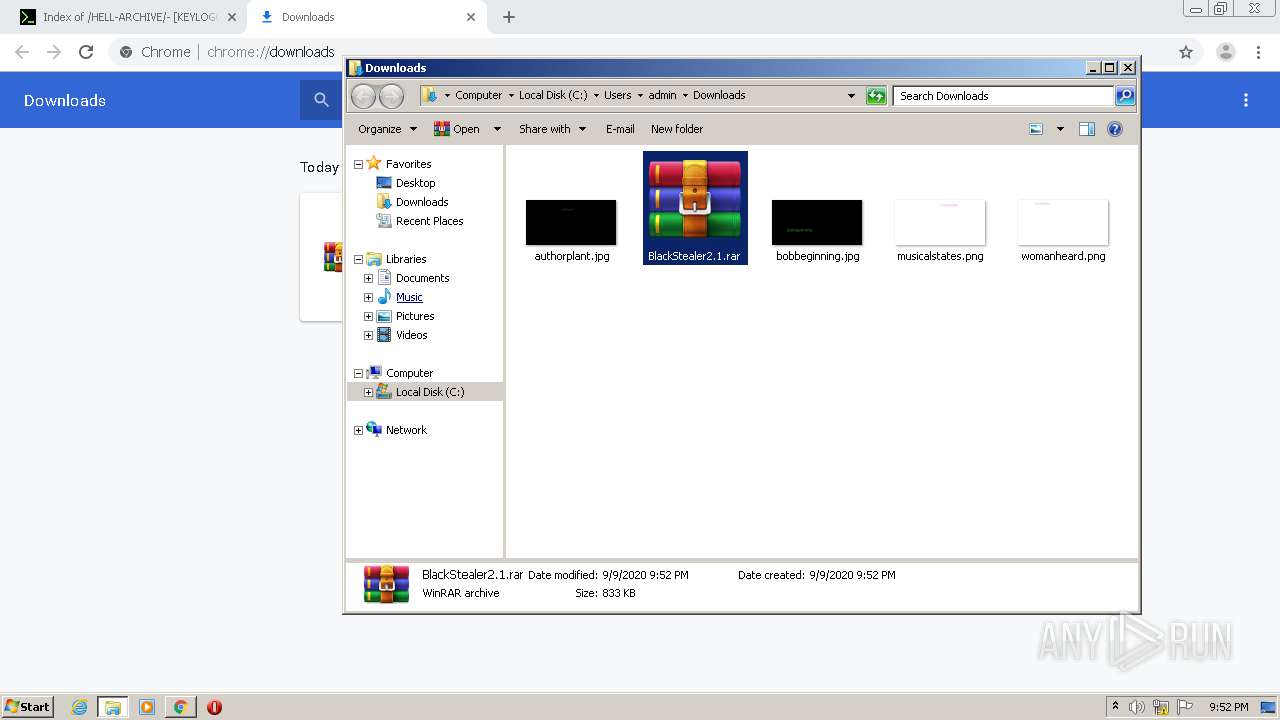
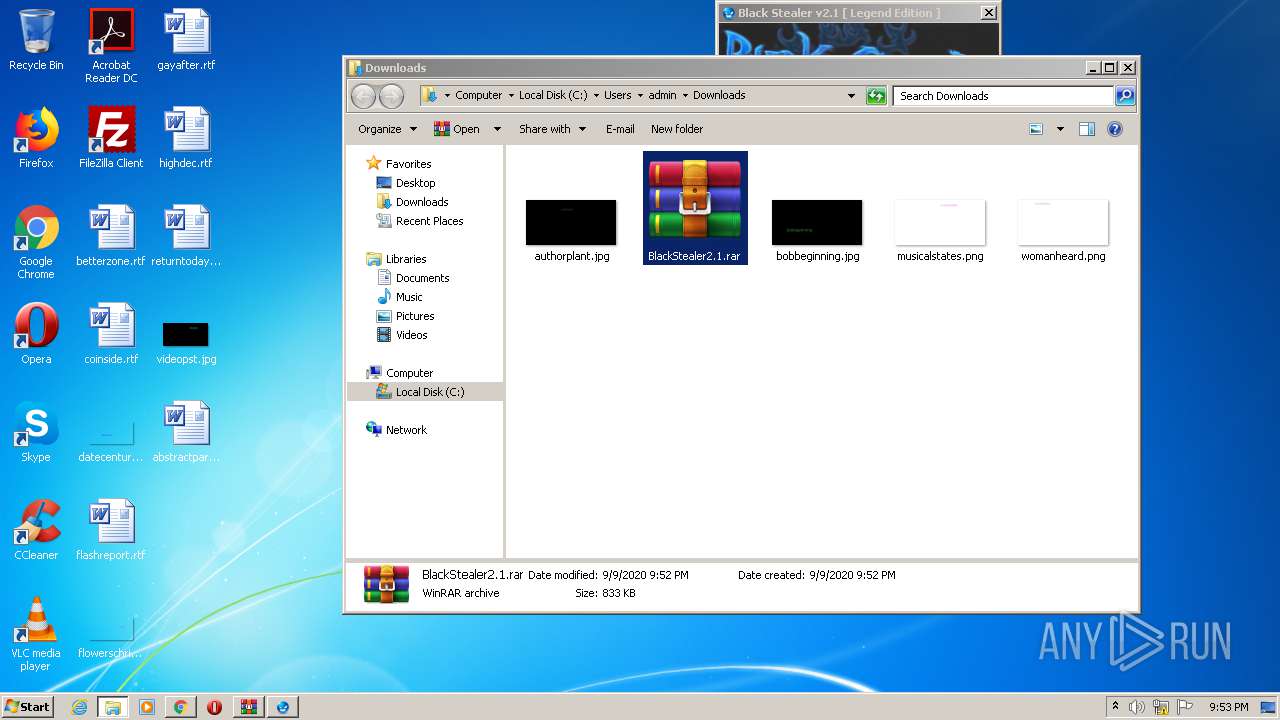
Manual execution by user
- WinRAR.exe (PID: 2284)
- WinRAR.exe (PID: 3908)
- WinRAR.exe (PID: 3340)
Reads Internet Cache Settings
- chrome.exe (PID: 1340)
Reads the hosts file
- chrome.exe (PID: 2944)
- chrome.exe (PID: 1340)
Application launched itself
- chrome.exe (PID: 1340)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
69
Monitored processes
27
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 296 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,1148970200834687375,16750081154089616558,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3166725292982013021 --mojo-platform-channel-handle=3508 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
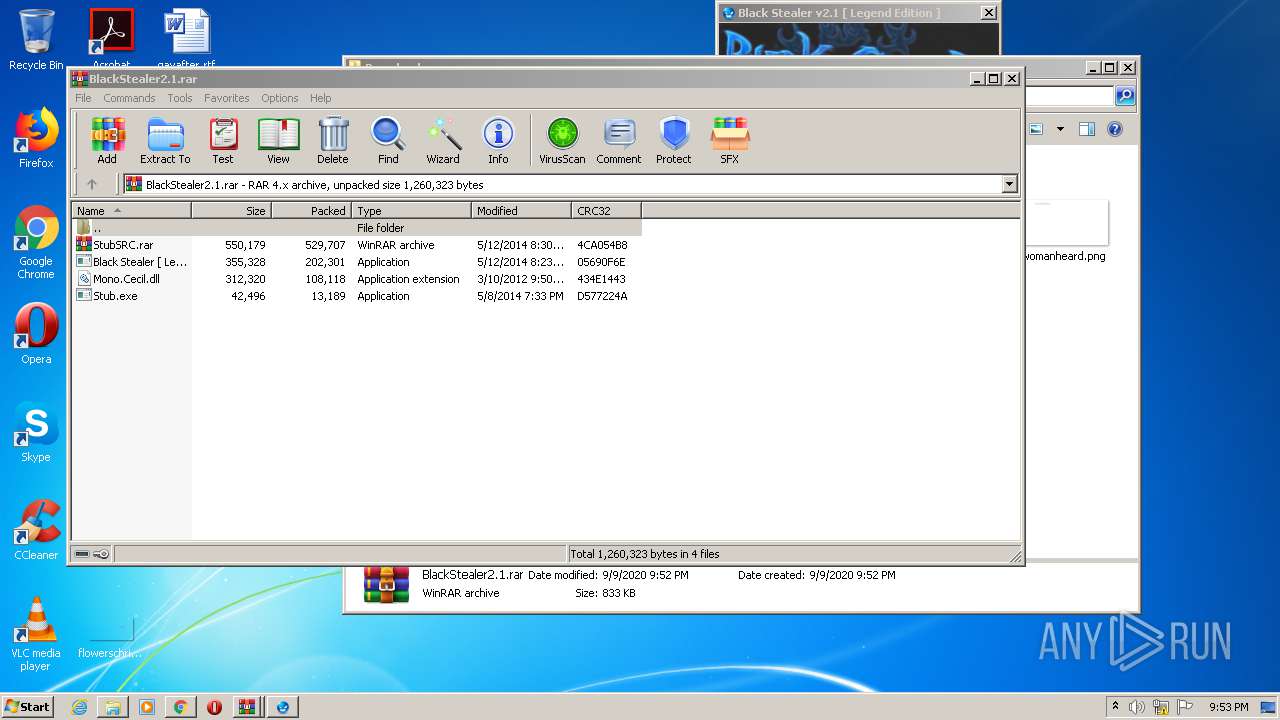
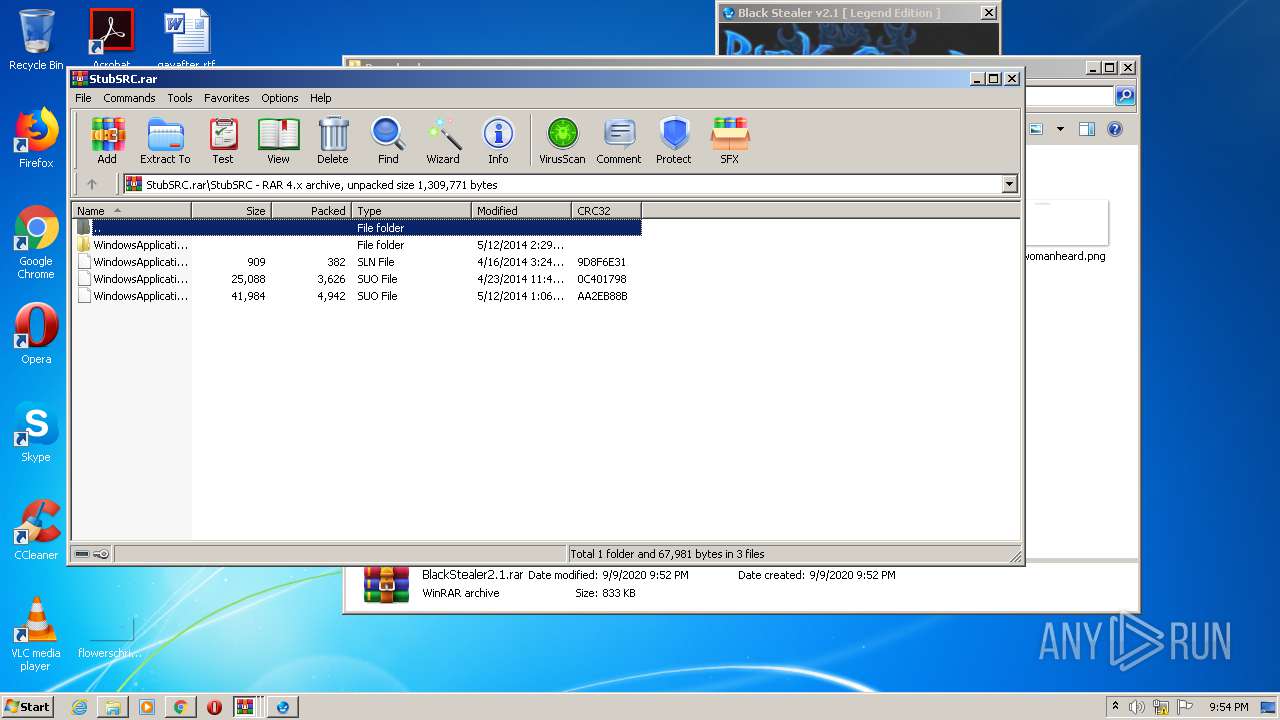
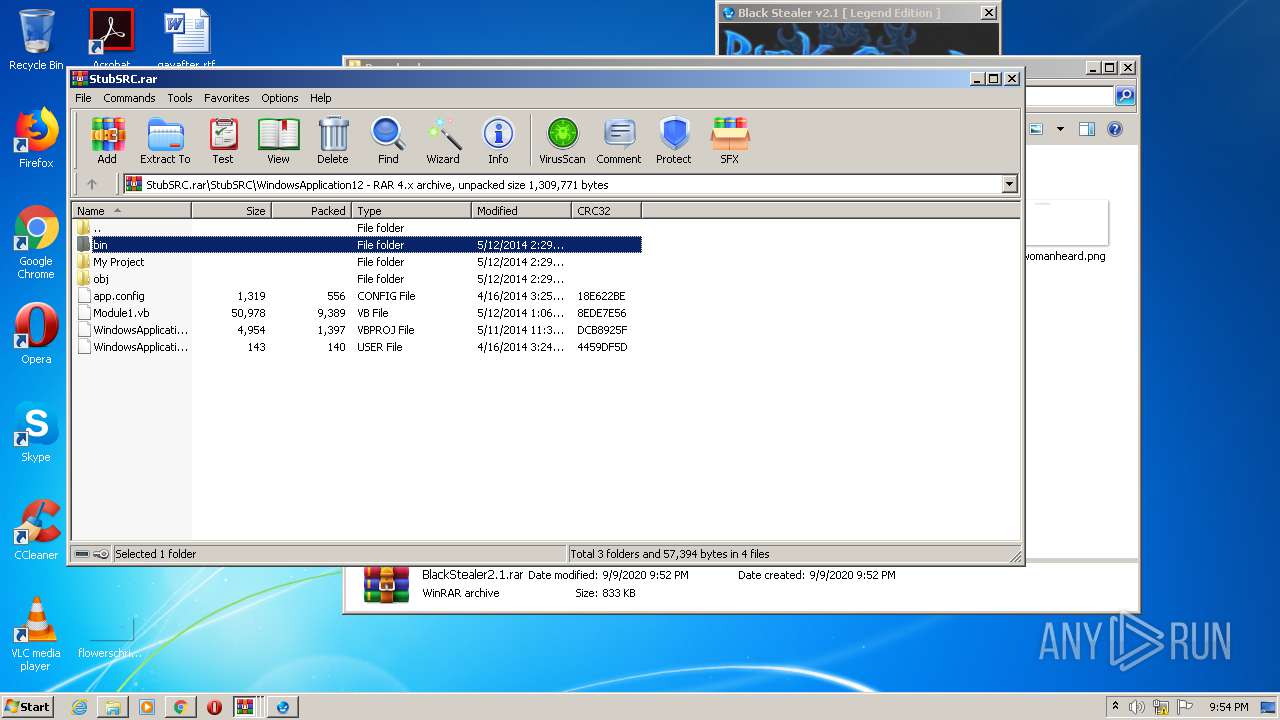
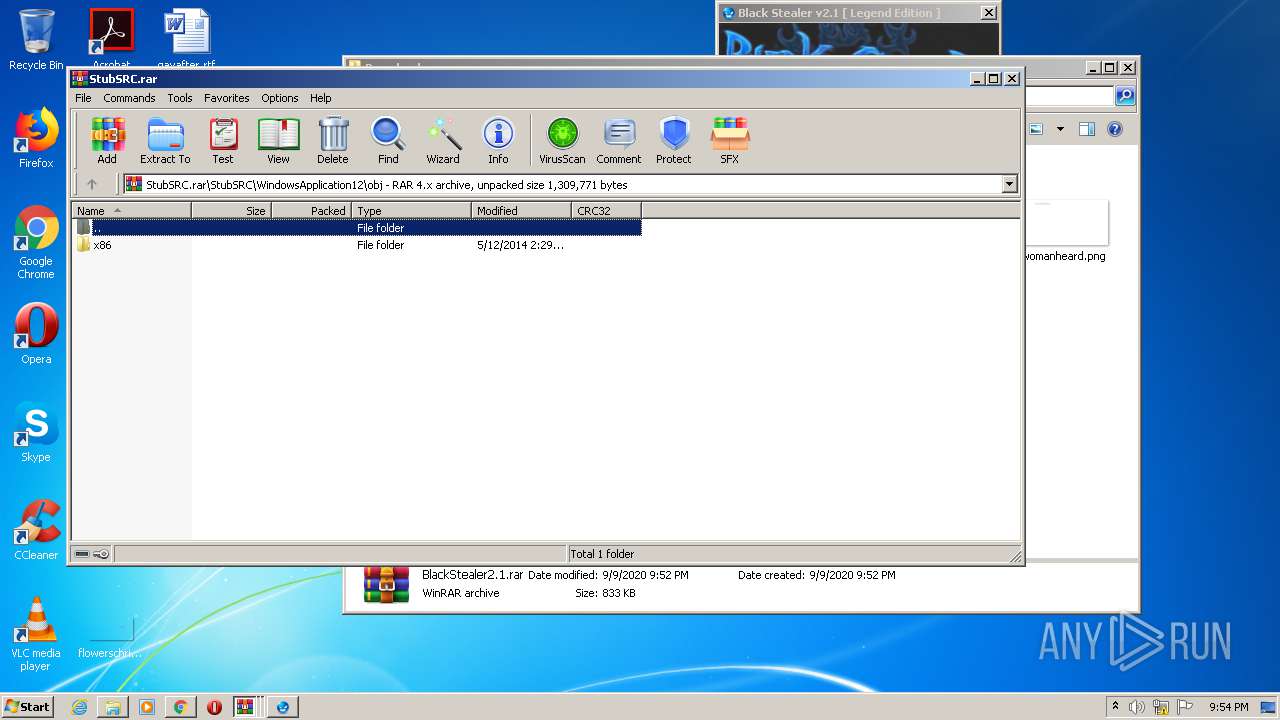
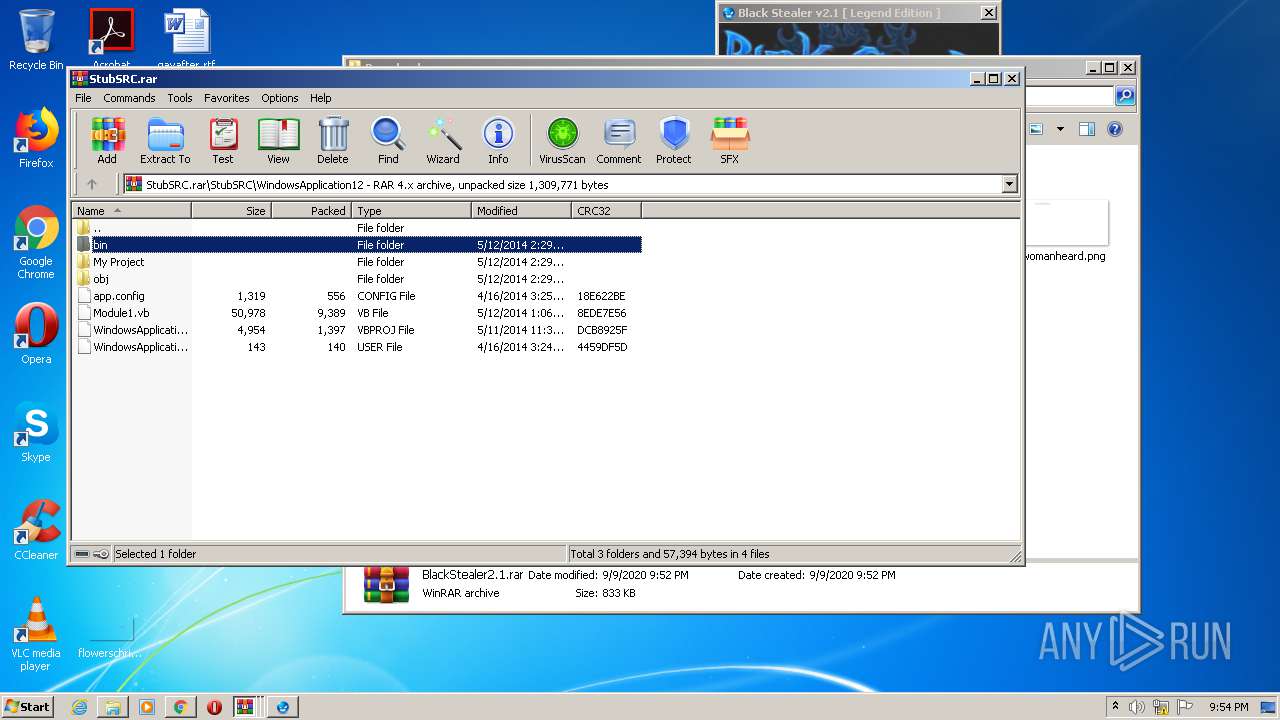
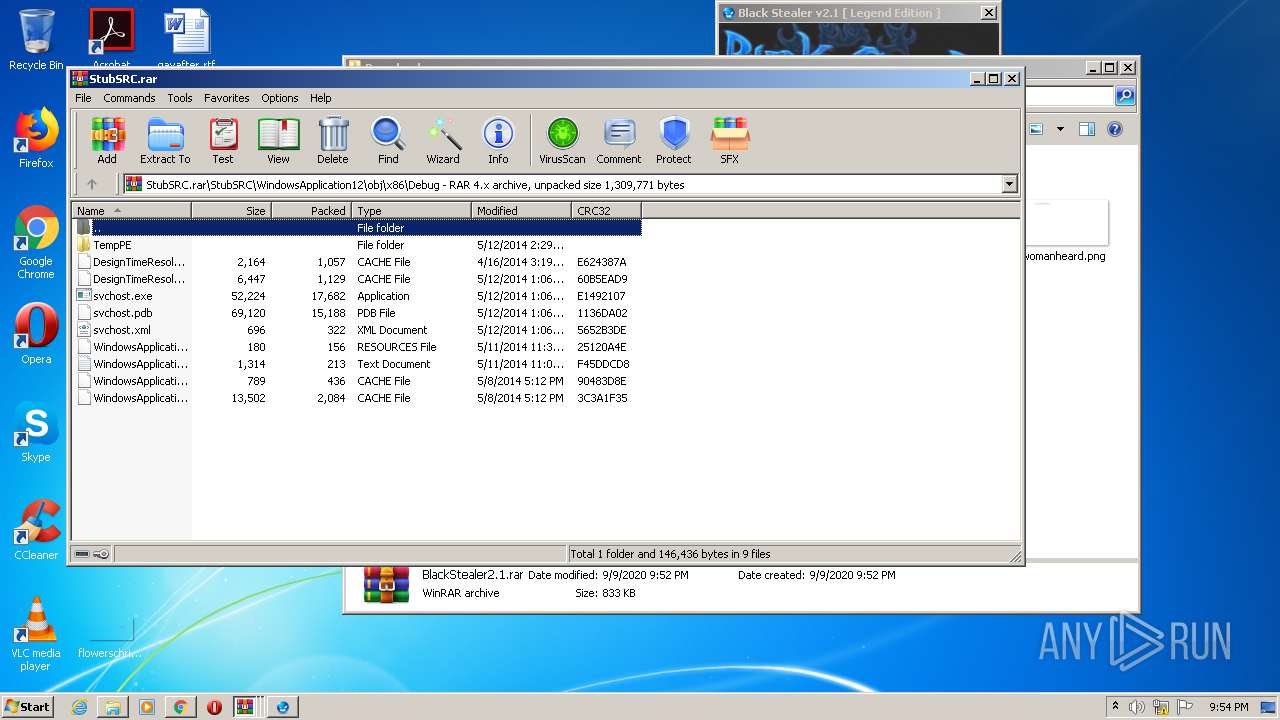
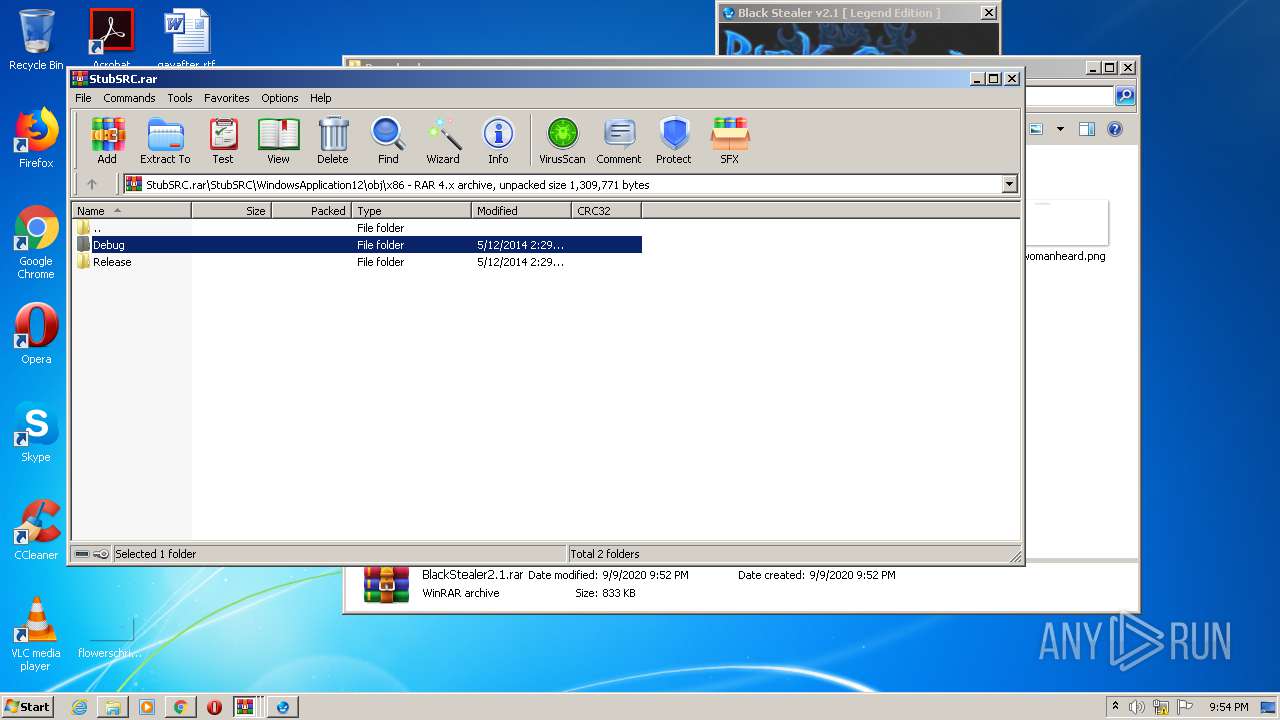
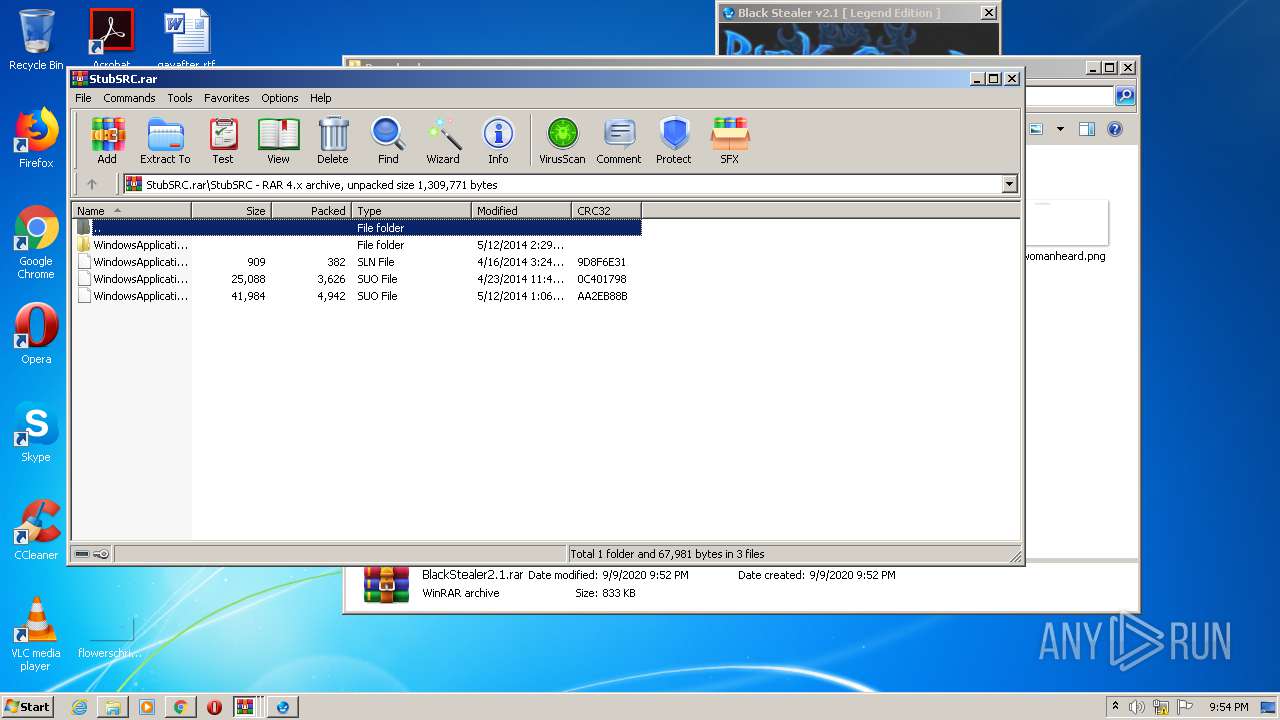
| 624 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\Rar$DIa3908.16865\StubSRC.rar | C:\Program Files\WinRAR\WinRAR.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 840 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,1148970200834687375,16750081154089616558,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13088378696194527204 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2292 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1296 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,1148970200834687375,16750081154089616558,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17802535512301686319 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2272 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1340 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "https://b4ckdoorarchive.club/HELL-ARCHIVE/-%20%5bKEYLOGGER%5d/Black%20Stealer%202.1/" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1444 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\Rar$DIa2284.17437\StubSRC.rar | C:\Program Files\WinRAR\WinRAR.exe | WinRAR.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 1452 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,1148970200834687375,16750081154089616558,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13771384647963668432 --mojo-platform-channel-handle=3608 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1468 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2260 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1516 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1028,1148970200834687375,16750081154089616558,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=1022531878436064460 --mojo-platform-channel-handle=4100 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1936 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,1148970200834687375,16750081154089616558,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=18177992507671244911 --mojo-platform-channel-handle=3516 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
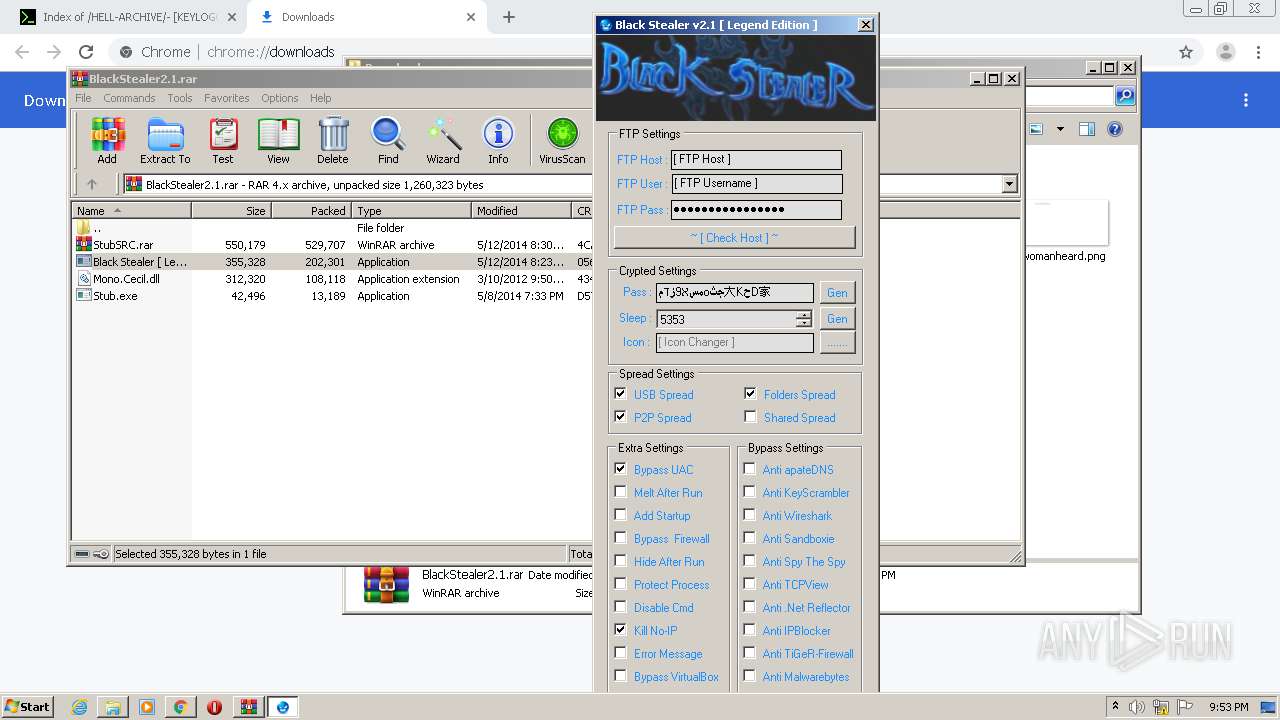
Total events
3 413
Read events
3 190
Write events
218
Delete events
5
Modification events
| (PID) Process: | (1340) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1340) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1340) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1340) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1468) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1340-13244158341805625 |
Value: 259 | |||
| (PID) Process: | (1340) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1340) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1340) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1340) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2832-13239195546717773 |
Value: 0 | |||
| (PID) Process: | (1340) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
9
Suspicious files
34
Text files
179
Unknown types
16
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1340 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1340 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF15c86a.TMP | — | |
MD5:— | SHA256:— | |||
| 1340 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000032.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1340 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF15c7ed.TMP | text | |
MD5:— | SHA256:— | |||
| 1340 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1340 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF15c7ed.TMP | text | |
MD5:— | SHA256:— | |||
| 1340 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Last Tabs | binary | |
MD5:— | SHA256:— | |||
| 1340 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1340 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF15c9a3.TMP | — | |
MD5:— | SHA256:— | |||
| 1340 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF15c7fd.TMP | text | |
MD5:— | SHA256:— | |||
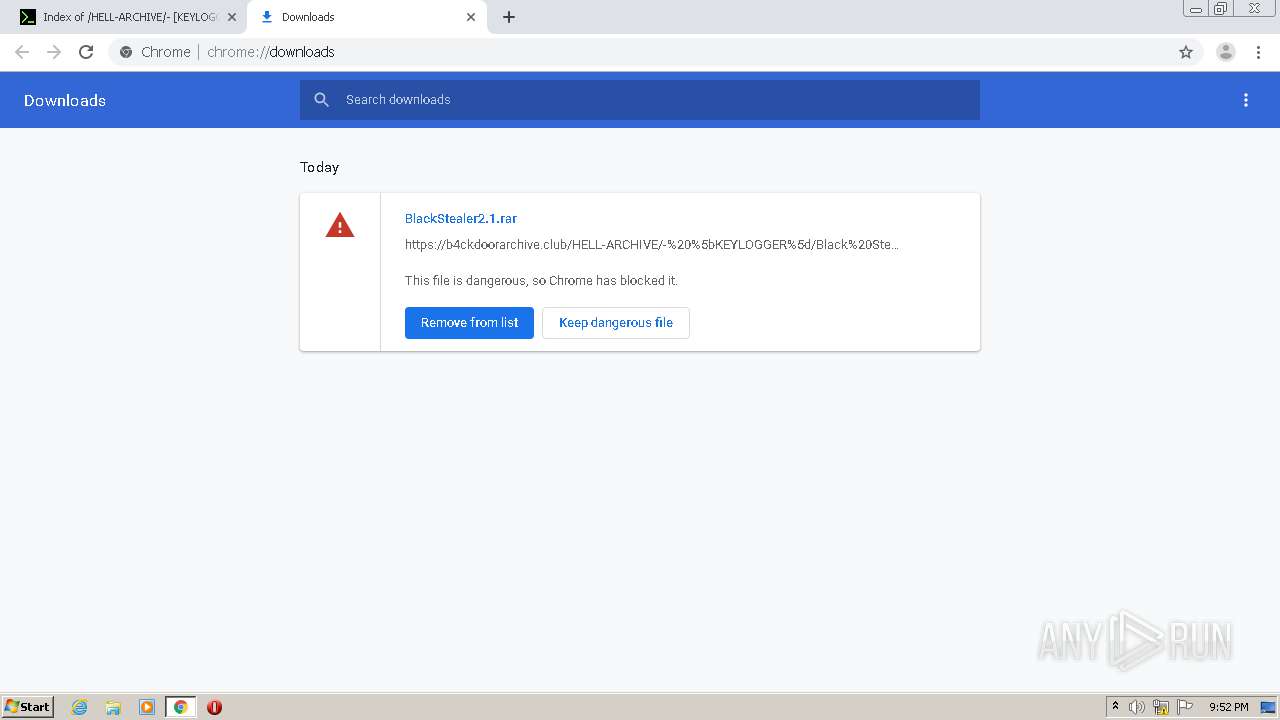
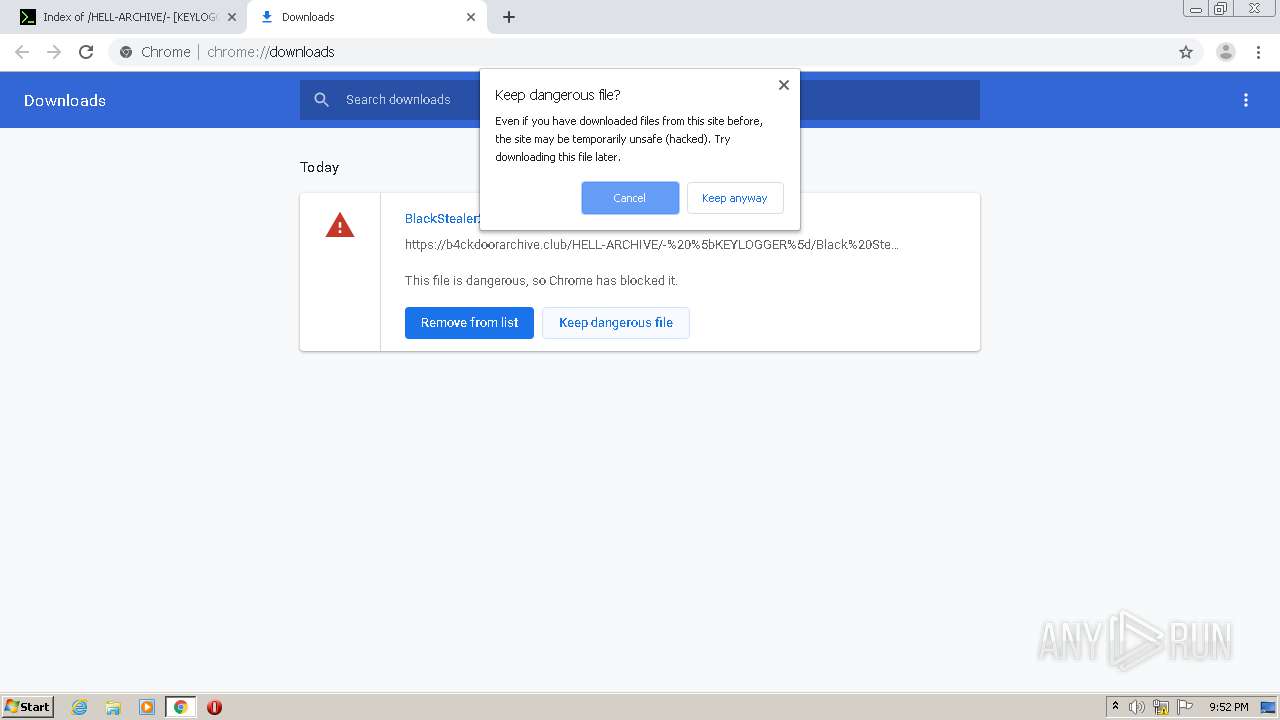
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
17
DNS requests
14
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2944 | chrome.exe | GET | 302 | 216.58.208.46:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWFjQUFXV2lsMkZVdjR5Vk5VZHJTM3E1dw/7919.1028.0.0_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 524 b | whitelisted |
2944 | chrome.exe | GET | 200 | 74.125.173.234:80 | http://r5---sn-4g5ednz7.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWFjQUFXV2lsMkZVdjR5Vk5VZHJTM3E1dw/7919.1028.0.0_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=sX&mip=92.118.13.24&mm=28&mn=sn-4g5ednz7&ms=nvh&mt=1599684629&mv=m&mvi=5&pl=24&shardbypass=yes | US | crx | 834 Kb | whitelisted |
1944 | svchost.exe | GET | 200 | 131.186.161.70:80 | http://checkip.dyndns.org/ | US | html | 104 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2944 | chrome.exe | 172.217.21.195:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2944 | chrome.exe | 104.24.113.46:443 | b4ckdoorarchive.club | Cloudflare Inc | US | suspicious |
2944 | chrome.exe | 216.58.212.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
2944 | chrome.exe | 216.58.212.142:443 | clients2.google.com | Google Inc. | US | whitelisted |
2944 | chrome.exe | 216.58.208.46:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
2944 | chrome.exe | 74.125.173.234:80 | r5---sn-4g5ednz7.gvt1.com | Google Inc. | US | whitelisted |
2944 | chrome.exe | 172.217.23.132:443 | www.google.com | Google Inc. | US | whitelisted |
2944 | chrome.exe | 172.217.22.14:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
2944 | chrome.exe | 172.217.22.46:443 | safebrowsing.google.com | Google Inc. | US | whitelisted |
2944 | chrome.exe | 172.217.22.3:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
b4ckdoorarchive.club |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
clients2.google.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
r5---sn-4g5ednz7.gvt1.com |
| whitelisted |
www.google.com |
| malicious |
sb-ssl.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
safebrowsing.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1044 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.dyndns. Domain |
1044 | svchost.exe | Misc activity | AV INFO Query to checkip.dyndns. Domain |
1944 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup - checkip.dyndns.org |
1944 | svchost.exe | Potential Corporate Privacy Violation | POLICY [PTsecurity] External IP Check checkip.dyndns.org |
1944 | svchost.exe | Potentially Bad Traffic | ET POLICY DynDNS CheckIp External IP Address Server Response |
1 ETPRO signatures available at the full report