| File name: | GLP_installer_1000218865_com.vng.pubgmobile.exe |
| Full analysis: | https://app.any.run/tasks/884ff36d-3bc8-4e49-9467-2ff22a1ed5ef |
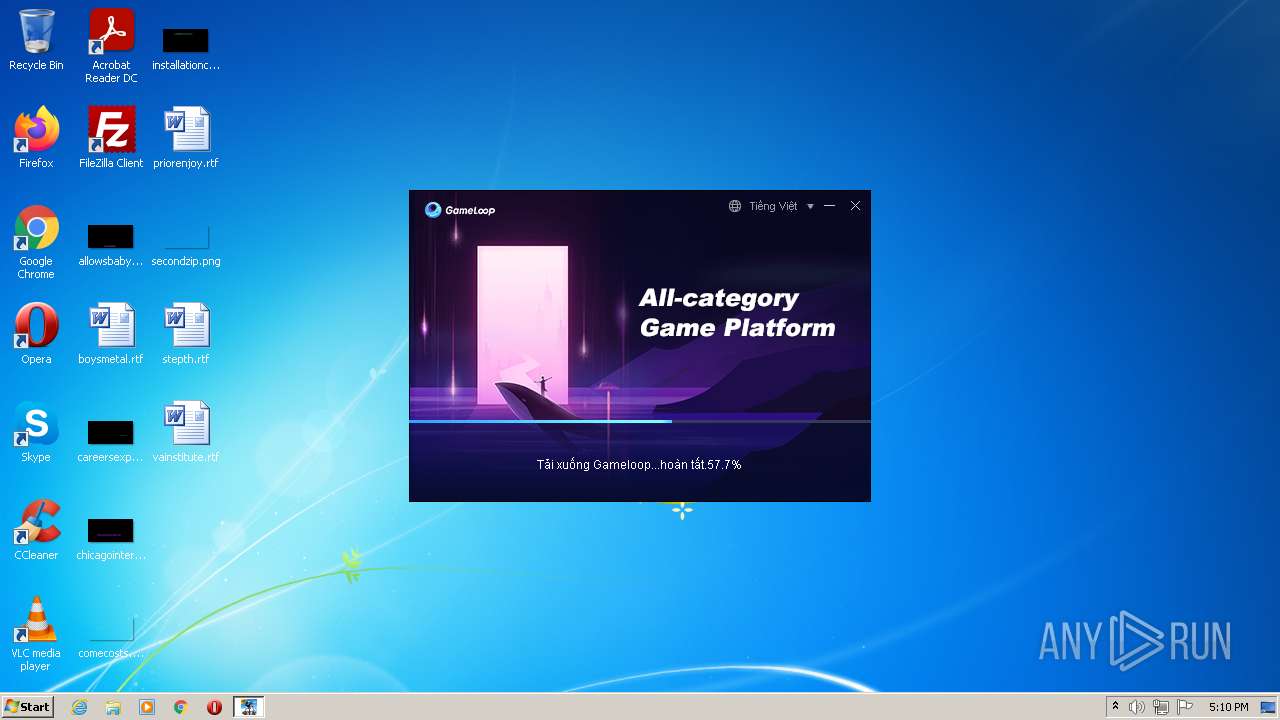
| Verdict: | Malicious activity |
| Analysis date: | January 30, 2022, 17:09:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 393F3017E884959F5F4674DB92C35023 |
| SHA1: | C8A7C779A94A95710884CF4BC0AB91F0071C6E63 |
| SHA256: | 86BE57D527628376CA74C0B7EB4C4F0993E490183C9A64D33709798142EC10F2 |
| SSDEEP: | 49152:E08OhxtUg9OUi82w6aQp9dgS1GUL38XhCOYc3iJXe9emEPGKOPkQThMYRVnm7LBY:E08vdsGaQNgS1C6evnsRMqq |
MALICIOUS
Loads dropped or rewritten executable
- GLP_installer_1000218865_com.vng.pubgmobile.exe (PID: 3168)
Drops executable file immediately after starts
- GLP_installer_1000218865_com.vng.pubgmobile.exe (PID: 3168)
SUSPICIOUS
Checks supported languages
- GLP_installer_1000218865_com.vng.pubgmobile.exe (PID: 3168)
Reads the computer name
- GLP_installer_1000218865_com.vng.pubgmobile.exe (PID: 3168)
Creates files in the user directory
- GLP_installer_1000218865_com.vng.pubgmobile.exe (PID: 3168)
Drops a file that was compiled in debug mode
- GLP_installer_1000218865_com.vng.pubgmobile.exe (PID: 3168)
Executable content was dropped or overwritten
- GLP_installer_1000218865_com.vng.pubgmobile.exe (PID: 3168)
INFO
Reads settings of System Certificates
- GLP_installer_1000218865_com.vng.pubgmobile.exe (PID: 3168)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (3.6) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (1.6) |
| .exe | | | DOS Executable Generic (1.5) |
EXIF
EXE
| ProductVersion: | 1, 0, 0, 1 |
|---|---|
| ProductName: | Tencent Game Downloader |
| OriginalFileName: | TGBDownloader.exe |
| LegalCopyright: | Copyright ? 2020 Tencent. All Rights Reserved. |
| InternalName: | TGBDownloader.exe |
| FileVersion: | 1, 0, 0, 1 |
| FileDescription: | Tencent Game Downloader |
| CompanyName: | Tencent |
| CharacterSet: | Windows, Latin1 |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 1.0.0.1 |
| FileVersionNumber: | 1.0.0.1 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 5.1 |
| ImageVersion: | - |
| OSVersion: | 5.1 |
| EntryPoint: | 0x220be4 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 1211392 |
| CodeSize: | 2604544 |
| LinkerVersion: | 14 |
| PEType: | PE32 |
| TimeStamp: | 2021:09:20 06:42:01+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 20-Sep-2021 04:42:01 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Tencent |
| FileDescription: | Tencent Game Downloader |
| FileVersion: | 1, 0, 0, 1 |
| InternalName: | TGBDownloader.exe |
| LegalCopyright: | Copyright ? 2020 Tencent. All Rights Reserved. |
| OriginalFilename: | TGBDownloader.exe |
| ProductName: | Tencent Game Downloader |
| ProductVersion: | 1, 0, 0, 1 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000130 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 20-Sep-2021 04:42:01 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0027BC4A | 0x0027BE00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.70671 |
.rdata | 0x0027D000 | 0x00084486 | 0x00084600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.43551 |
.data | 0x00302000 | 0x000149D4 | 0x00010200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.13707 |
.gfids | 0x00317000 | 0x00001108 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.98895 |
.tls | 0x00319000 | 0x00000009 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.0203931 |
.QMGuid | 0x0031A000 | 0x00000014 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0031B000 | 0x0006FFC8 | 0x00070000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.78608 |
.reloc | 0x0038B000 | 0x0001D480 | 0x0001D600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.59191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.06216 | 651 | UNKNOWN | English - United States | RT_MANIFEST |
7 | 2.32128 | 84 | UNKNOWN | Chinese - PRC | RT_STRING |
107 | 1.91924 | 20 | UNKNOWN | Chinese - PRC | RT_GROUP_ICON |
109 | 3.24529 | 80 | UNKNOWN | Chinese - PRC | RT_MENU |
133 | 7.99534 | 360872 | UNKNOWN | Chinese - PRC | ZIPRES |
135 | 6.34869 | 9662 | UNKNOWN | Chinese - PRC | CUSTOM |
136 | 5.81636 | 76168 | UNKNOWN | Chinese - PRC | CUSTOM |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
IMM32.dll |
KERNEL32.dll |
NETAPI32.dll |
PSAPI.DLL |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
Total processes
39
Monitored processes
2
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3168 | "C:\Users\admin\AppData\Local\Temp\GLP_installer_1000218865_com.vng.pubgmobile.exe" | C:\Users\admin\AppData\Local\Temp\GLP_installer_1000218865_com.vng.pubgmobile.exe | Explorer.EXE | ||||||||||||
User: admin Company: Tencent Integrity Level: HIGH Description: Tencent Game Downloader Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 3548 | "C:\Users\admin\AppData\Local\Temp\GLP_installer_1000218865_com.vng.pubgmobile.exe" | C:\Users\admin\AppData\Local\Temp\GLP_installer_1000218865_com.vng.pubgmobile.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Tencent Integrity Level: MEDIUM Description: Tencent Game Downloader Exit code: 3221226540 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
Total events
2 940
Read events
2 921
Write events
19
Delete events
0
Modification events
| (PID) Process: | (3168) GLP_installer_1000218865_com.vng.pubgmobile.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: GLP_installer_1000218865_com.vng.pubgmobile.exe | |||
| (PID) Process: | (3168) GLP_installer_1000218865_com.vng.pubgmobile.exe | Key: | HKEY_CURRENT_USER\Software\Tencent\MobileGamePC\Beacon |
| Operation: | write | Name: | Last_Sid_GLP_installer_1000218865_com.vng.pubgmobile.exe |
Value: FA14F45A-7E05-4A7F-89CC-006C58D92B47 | |||
| (PID) Process: | (3168) GLP_installer_1000218865_com.vng.pubgmobile.exe | Key: | HKEY_CURRENT_USER\Software\Tencent\MobileGamePC |
| Operation: | write | Name: | TempPath |
Value: C:\Temp\TxGameDownload\Component\ | |||
| (PID) Process: | (3168) GLP_installer_1000218865_com.vng.pubgmobile.exe | Key: | HKEY_CURRENT_USER\Software\Tencent\MobileGamePC |
| Operation: | write | Name: | UserLanguage |
Value: vi | |||
| (PID) Process: | (3168) GLP_installer_1000218865_com.vng.pubgmobile.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3168) GLP_installer_1000218865_com.vng.pubgmobile.exe | Key: | HKEY_CURRENT_USER\Software\Tencent\MobileGamePC |
| Operation: | write | Name: | abtestid |
Value: {"Component":"0"} | |||
Executable files
1
Suspicious files
2
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3168 | GLP_installer_1000218865_com.vng.pubgmobile.exe | C:\test.tmp | binary | |
MD5:— | SHA256:— | |||
| 3168 | GLP_installer_1000218865_com.vng.pubgmobile.exe | C:\Users\admin\AppData\Roaming\Tencent\DeskUpdate\GlobalMgr.db | text | |
MD5:— | SHA256:— | |||
| 3168 | GLP_installer_1000218865_com.vng.pubgmobile.exe | C:\Users\admin\AppData\Local\Tencent\TxGameAssistant\TGBDownloader\dr.dll | executable | |
MD5:2814ACBD607BA47BDBCDF6AC3076EE95 | SHA256:5904A7E4D97EEAC939662C3638A0E145F64FF3DD0198F895C4BF0337595C6A67 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
9
DNS requests
4
Threats
9
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3168 | GLP_installer_1000218865_com.vng.pubgmobile.exe | 58.251.106.185:443 | master.etl.desktop.qq.com | China Unicom Guangdong IP network | CN | malicious |
3168 | GLP_installer_1000218865_com.vng.pubgmobile.exe | 150.109.28.54:443 | unifiedaccess.gameloop.com | — | US | unknown |
3168 | GLP_installer_1000218865_com.vng.pubgmobile.exe | 101.33.47.206:8081 | oth.eve.mdt.qq.com | — | CN | unknown |
— | — | 101.33.47.206:8081 | oth.eve.mdt.qq.com | — | CN | unknown |
3168 | GLP_installer_1000218865_com.vng.pubgmobile.exe | 43.132.67.41:443 | down.gameloop.com | — | JP | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
master.etl.desktop.qq.com |
| whitelisted |
oth.eve.mdt.qq.com |
| unknown |
unifiedaccess.gameloop.com |
| suspicious |
down.gameloop.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3168 | GLP_installer_1000218865_com.vng.pubgmobile.exe | Generic Protocol Command Decode | SURICATA TLS error message encountered |
3168 | GLP_installer_1000218865_com.vng.pubgmobile.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
3168 | GLP_installer_1000218865_com.vng.pubgmobile.exe | Generic Protocol Command Decode | SURICATA TLS error message encountered |
3168 | GLP_installer_1000218865_com.vng.pubgmobile.exe | Generic Protocol Command Decode | SURICATA TLS error message encountered |
3168 | GLP_installer_1000218865_com.vng.pubgmobile.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
3168 | GLP_installer_1000218865_com.vng.pubgmobile.exe | Generic Protocol Command Decode | SURICATA TLS error message encountered |
3168 | GLP_installer_1000218865_com.vng.pubgmobile.exe | Generic Protocol Command Decode | SURICATA TLS error message encountered |
3168 | GLP_installer_1000218865_com.vng.pubgmobile.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
3168 | GLP_installer_1000218865_com.vng.pubgmobile.exe | Generic Protocol Command Decode | SURICATA TLS error message encountered |
Process | Message |
|---|---|
GLP_installer_1000218865_com.vng.pubgmobile.exe | Standard VGA Graphics Adapter |