| File name: | Message.eml |
| Full analysis: | https://app.any.run/tasks/3ee6a151-0936-4939-80e2-1ba5536239d8 |
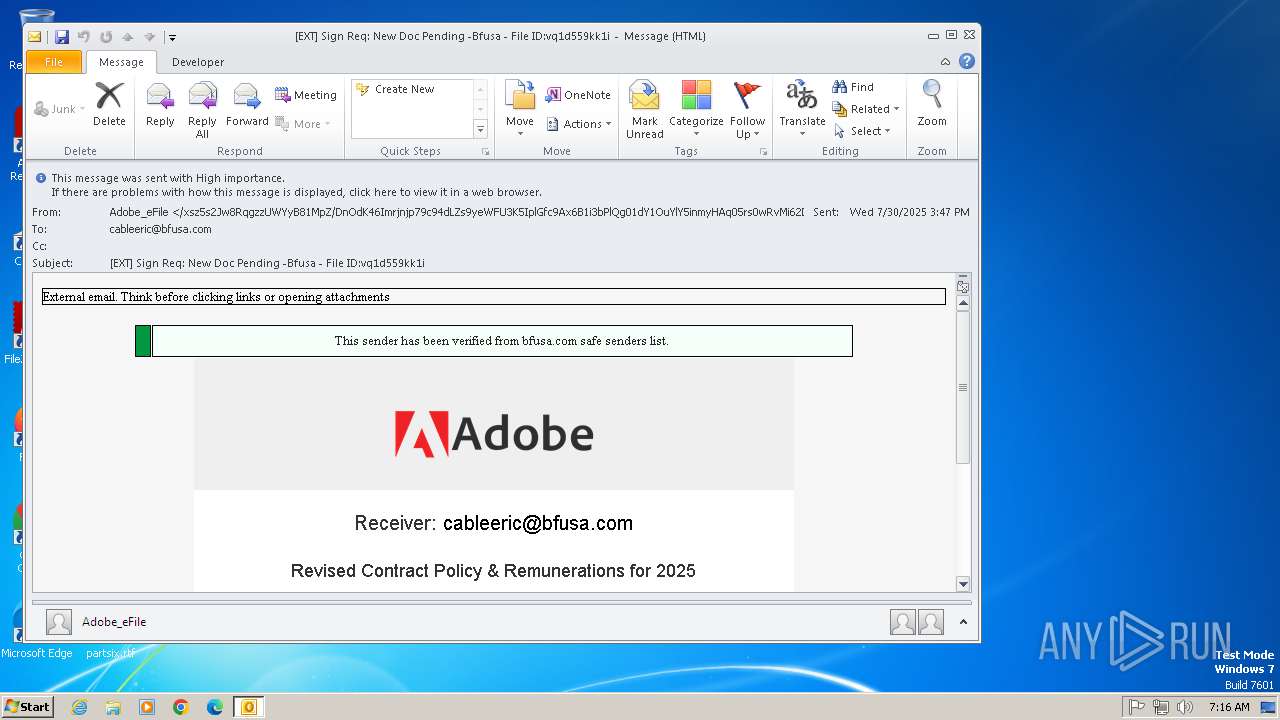
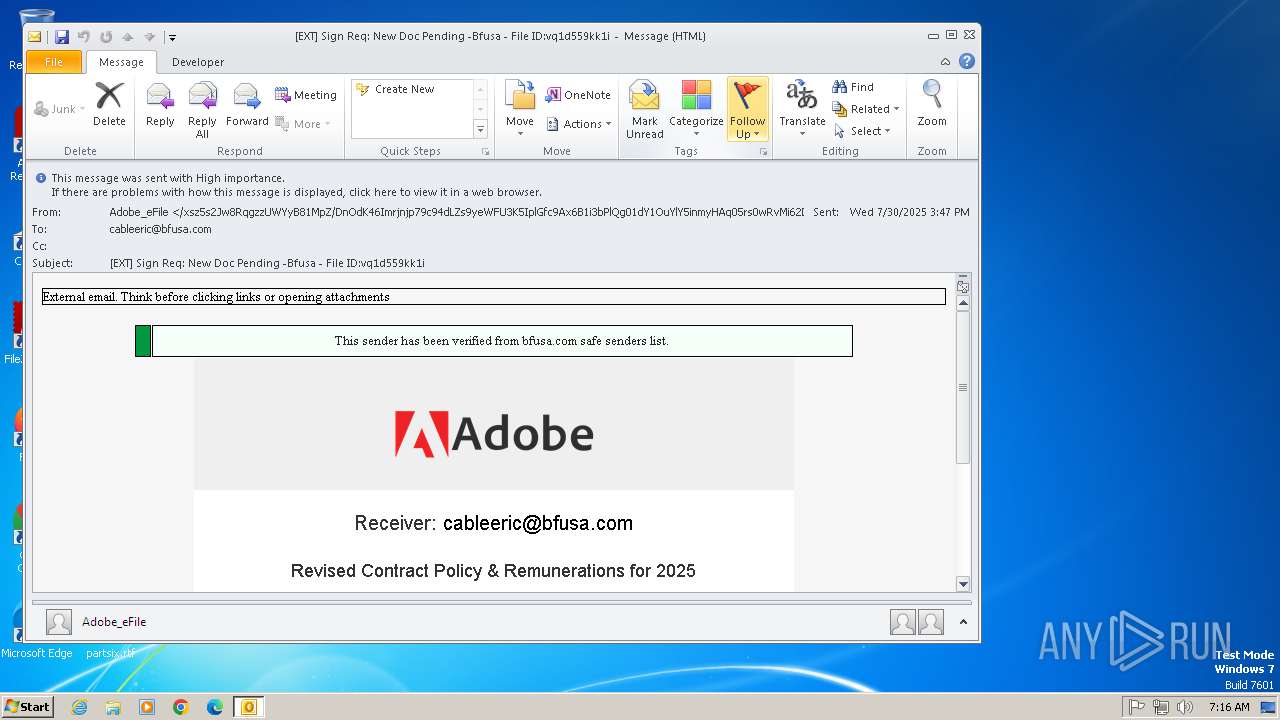
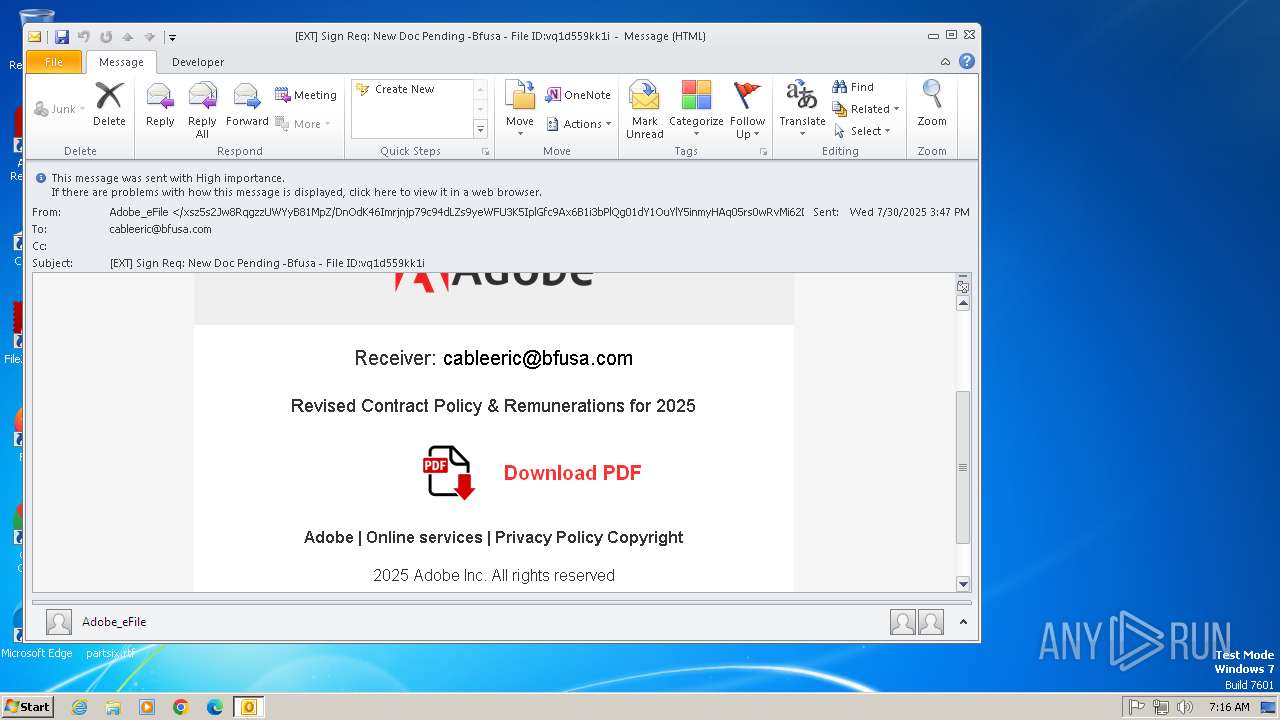
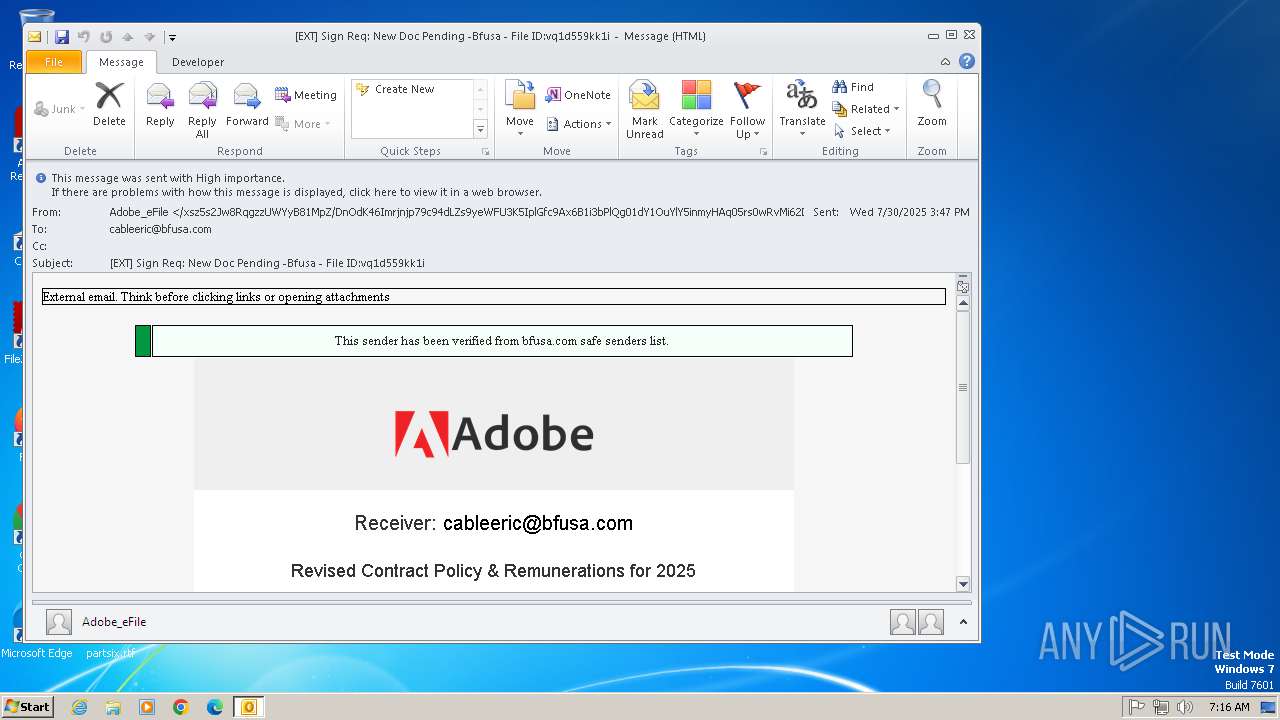
| Verdict: | Malicious activity |
| Analysis date: | August 01, 2025, 06:16:05 |
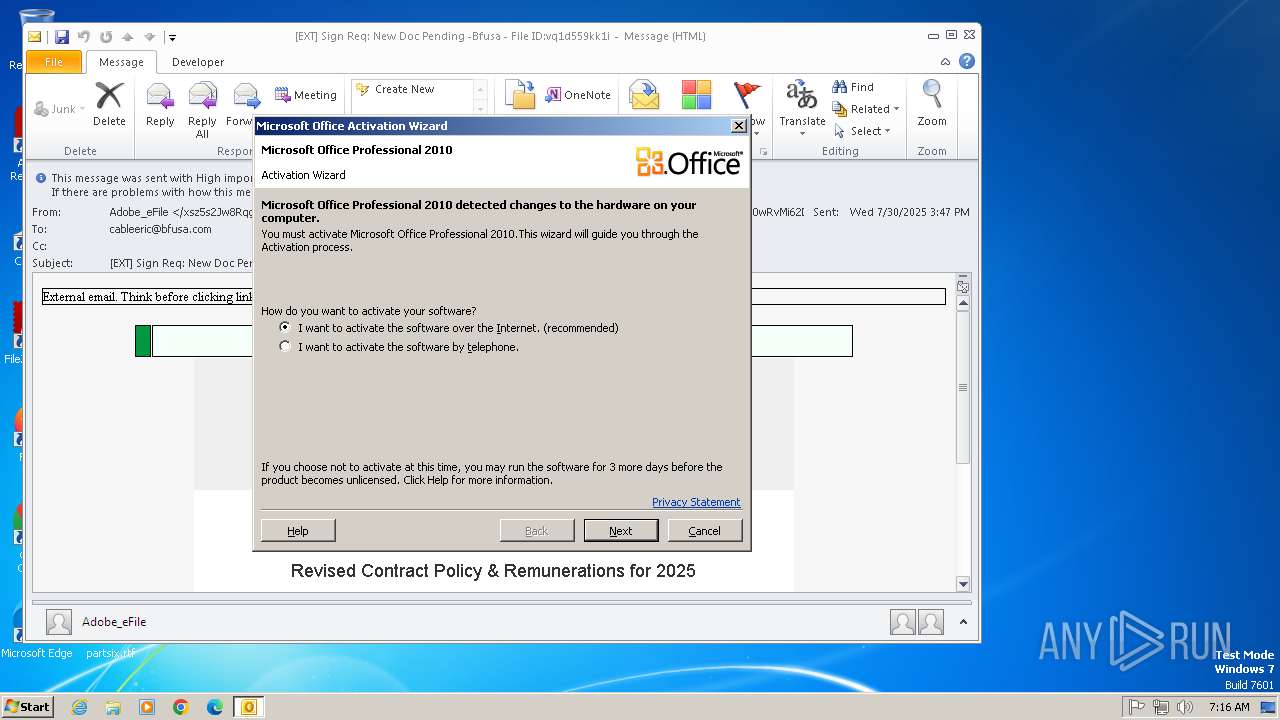
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| MIME: | text/plain |
| File info: | Unicode text, UTF-8 (with BOM) text, with very long lines (343), with CRLF line terminators |
| MD5: | 8AF345C4FEE8A398033E6A48D2100572 |
| SHA1: | 747D4FB62230F0B540C83E96150AF1826F492F70 |
| SHA256: | 86B627E836DDDA7261A4FF85030DD1EB50FC3D29FB67BF8F1175768E877A2D91 |
| SSDEEP: | 1536:oM64p2P5J3uD0rln9ipwgfiYUYdLV4cqDedhYwaGuchvOX744MWuYrfqyWw7:oM64p2P7pX0PfdUY4cTdhYwaGuS+HLh7 |
MALICIOUS
Email came from third-party service (Amazon SES)
- OUTLOOK.EXE (PID: 1288)
SUSPICIOUS
No suspicious indicators.INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .txt | | | Text - UTF-8 encoded (100) |
|---|
Total processes
36
Monitored processes
1
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1288 | "C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE" /eml C:\Users\admin\AppData\Local\Temp\Message.eml | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Version: 14.0.6025.1000 Modules
| |||||||||||||||
Total events
8 130
Read events
7 210
Write events
890
Delete events
30
Modification events
| (PID) Process: | (1288) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Control Panel\MMCPL |
| Operation: | delete value | Name: | mlcfg32.cpl |
Value: | |||
| (PID) Process: | (1288) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook |
| Operation: | write | Name: | MTTT |
Value: 08050000A0F871D2AB02DC0100000000 | |||
| (PID) Process: | (1288) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionNumber |
Value: 0 | |||
| (PID) Process: | (1288) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionDate |
Value: 223308000 | |||
| (PID) Process: | (1288) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\0a0d020000000000c000000000000046 |
| Operation: | write | Name: | 00030429 |
Value: 04000000 | |||
| (PID) Process: | (1288) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | {ED475418-B0D6-11D2-8C3B-00104B2A6676} |
Value: | |||
| (PID) Process: | (1288) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | LastChangeVer |
Value: 1500000000000000 | |||
| (PID) Process: | (1288) OUTLOOK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109A10090400000000000F01FEC\Usage |
| Operation: | write | Name: | OutlookMAPI2Intl_1033 |
Value: | |||
| (PID) Process: | (1288) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\Resiliency\StartupItems |
| Operation: | write | Name: | /+ |
Value: 2F2B200008050000040000000000000096000000010000008E000000430043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C0045006D00610069006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (1288) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\Resiliency\StartupItems |
| Operation: | delete value | Name: | /+ |
Value: ⬯ Ԉ | |||
Executable files
0
Suspicious files
0
Text files
4
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1288 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR4DD.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1288 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\Outlook Data File - NoMail.pst | — | |
MD5:— | SHA256:— | |||
| 1288 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:A22012FBD9D8519F846A3E90E0F69CC5 | SHA256:4E9C43C0D4306E152C82D9039C182F51EAAACA0ECAB7646C591F34C5A1D26801 | |||
| 1288 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\mapisvc.inf | text | |
MD5:F3B25701FE362EC84616A93A45CE9998 | SHA256:B3D510EF04275CA8E698E5B3CBB0ECE3949EF9252F0CDC839E9EE347409A2209 | |||
| 1288 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\9AC1D14D.dat | image | |
MD5:91694725CD47F418026F9BD5D9493097 | SHA256:9892990DC6480672EBE0715C6453C3085EF2A4336676AE9E386E7F8257EA04D8 | |||
| 1288 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\41982F7C.dat | image | |
MD5:C9CE6B0ADE8E38BCD94CDE8493212952 | SHA256:C0332EE59C1BD1423A229F067329EDD48FC2F4C3AE14BFE91AF2D84DEA1820C1 | |||
| 1288 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\{75A465A6-3254-4A0F-9789-DC05F3FF153D}\{1C306CB1-771E-4B4B-A902-86E897877F5B}.png | image | |
MD5:4C61C12EDBC453D7AE184976E95258E1 | SHA256:296526F9A716C1AA91BA5D6F69F0EB92FDF79C2CB2CFCF0CEB22B7CCBC27035F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
6
DNS requests
3
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1288 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
config.messenger.msn.com |
| whitelisted |
dns.msftncsi.com |
| whitelisted |