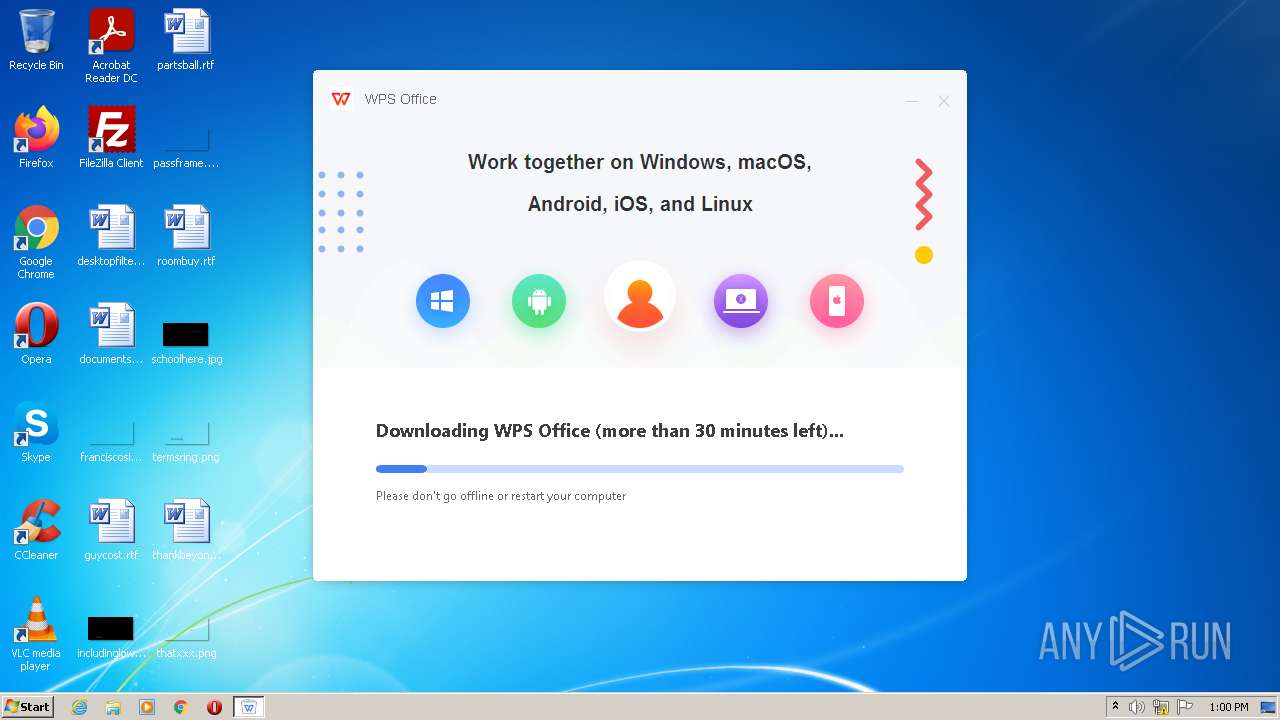
| File name: | C:\Users\admin\Downloads\wps_wid.cid-90329163.1657539443.exe |
| Full analysis: | https://app.any.run/tasks/363a767b-2d42-49f9-aa6d-3a23407b0d88 |
| Verdict: | Malicious activity |
| Analysis date: | July 11, 2022, 11:55:50 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 38E2093E23BD40B29A27F2345BE1D0EB |
| SHA1: | 4896DB450C850A875CBB2C59362305F617BADF97 |
| SHA256: | 86B326141A85A3B808697C39E0E77CD1A14E4F60C696F1AE3327B23FEF0A843A |
| SSDEEP: | 98304:KWG+aDovMcnK9Hj80rr4pqaVQnGtKOQ+l4SmYB4DlnF/5Eye:KBoEcnkj807aywXMYODlla |
MALICIOUS
No malicious indicators.SUSPICIOUS
Checks supported languages
- wps_wid.cid-90329163.1657539443.exe (PID: 3284)
Reads the computer name
- wps_wid.cid-90329163.1657539443.exe (PID: 3284)
Creates files in the user directory
- wps_wid.cid-90329163.1657539443.exe (PID: 3284)
INFO
Reads settings of System Certificates
- wps_wid.cid-90329163.1657539443.exe (PID: 3284)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (18) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (2.9) |
| .exe | | | Generic Win/DOS Executable (1.3) |
| .exe | | | DOS Executable Generic (1.3) |
EXIF
EXE
| MIMEType: | - |
|---|---|
| ProductVersion: | 11,2,0,11134 |
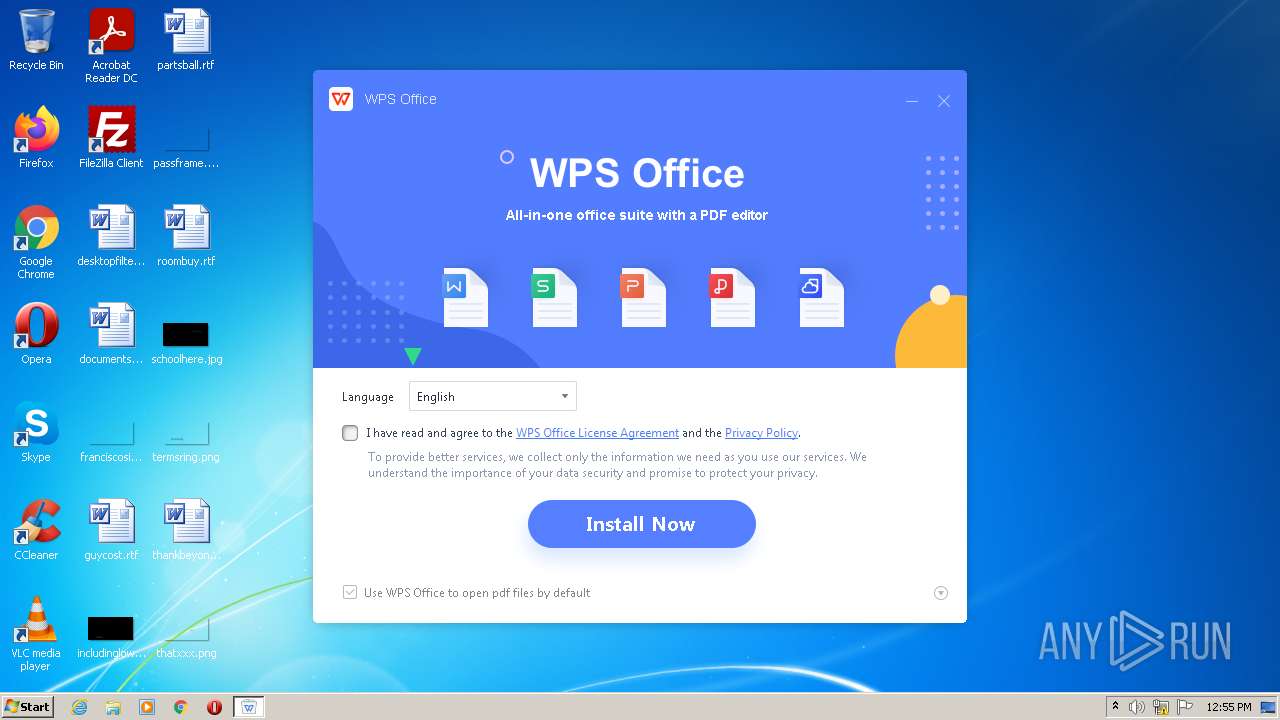
| ProductName: | WPS Office |
| OriginalFileName: | konlinesetup_xa.exe |
| LegalCopyright: | Copyright©2022 Kingsoft Corporation. All rights reserved. |
| InternalName: | konlinesetup_xa |
| FileVersion: | 11,2,0,11134 |
| FileDescription: | WPS Office Setup |
| CompanyName: | Zhuhai Kingsoft Office Software Co.,Ltd |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Unknown |
| FileOS: | Windows NT 32-bit |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 11.2.0.11134 |
| FileVersionNumber: | 11.2.0.11134 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 5.1 |
| ImageVersion: | - |
| OSVersion: | 5.1 |
| EntryPoint: | 0x175d98 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 1302016 |
| CodeSize: | 3679744 |
| LinkerVersion: | 14.24 |
| PEType: | PE32 |
| TimeStamp: | 2022:05:12 01:20:40+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 11-May-2022 23:20:40 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Zhuhai Kingsoft Office Software Co.,Ltd |
| FileDescription: | WPS Office Setup |
| FileVersion: | 11,2,0,11134 |
| InternalName: | konlinesetup_xa |
| LegalCopyright: | Copyright©2022 Kingsoft Corporation. All rights reserved. |
| OriginalFilename: | konlinesetup_xa.exe |
| ProductName: | WPS Office |
| ProductVersion: | 11,2,0,11134 |
| MIMEType: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000138 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 11-May-2022 23:20:40 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x003825CA | 0x00382600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.73825 |
.rdata | 0x00384000 | 0x000C4834 | 0x000C4A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.0596 |
.data | 0x00449000 | 0x0001586C | 0x0000CE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.72308 |
.rsrc | 0x0045F000 | 0x00046404 | 0x00046600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.73118 |
.reloc | 0x004A6000 | 0x00025EDC | 0x00026000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.61355 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.27658 | 1044 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 4.16635 | 67624 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
3 | 4.21424 | 38056 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
4 | 4.43466 | 16936 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
5 | 4.46225 | 9640 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
6 | 4.70335 | 4264 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
7 | 4.83778 | 2440 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
8 | 5.23684 | 1128 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
101 | 7.96308 | 117205 | Latin 1 / Western European | Chinese - PRC | ZIPRES |
102 | 2.97321 | 118 | Latin 1 / Western European | Chinese - PRC | RT_GROUP_ICON |
Imports
KERNEL32.dll |
SHLWAPI.dll (delay-loaded) |
Total processes
34
Monitored processes
1
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 3284 | "C:\Users\admin\AppData\Local\Temp\wps_wid.cid-90329163.1657539443.exe" | C:\Users\admin\AppData\Local\Temp\wps_wid.cid-90329163.1657539443.exe | Explorer.EXE | |
User: admin Company: Zhuhai Kingsoft Office Software Co.,Ltd Integrity Level: MEDIUM Description: WPS Office Setup Exit code: 0 Version: 11,2,0,11134 | ||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
19
DNS requests
3
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3284 | wps_wid.cid-90329163.1657539443.exe | 34.89.231.242:443 | event.wps.com | — | US | unknown |
3284 | wps_wid.cid-90329163.1657539443.exe | 104.17.187.189:443 | wdl1.pcfg.cache.wpscdn.com | Cloudflare Inc | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
event.wps.com |
| suspicious |
wdl1.pcfg.cache.wpscdn.com |
| malicious |