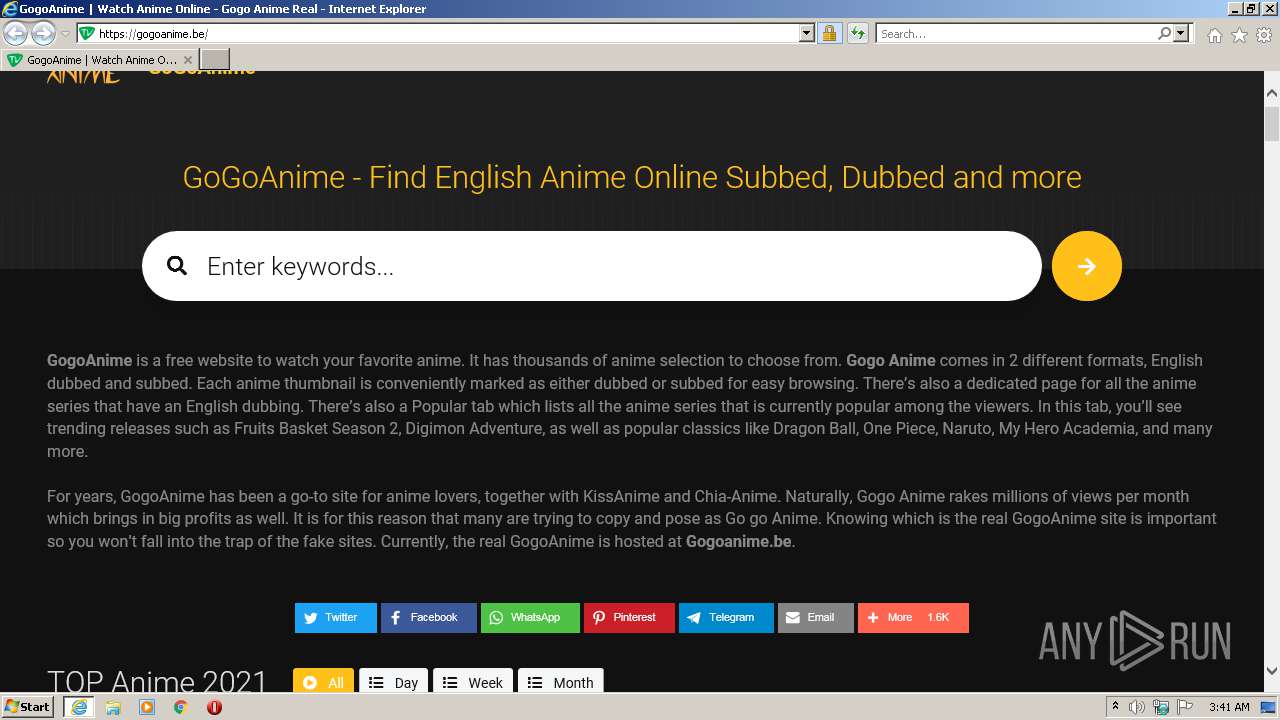
| URL: | https://gogoanime.be/ |
| Full analysis: | https://app.any.run/tasks/a1f75d22-bee6-4be1-8605-e1a486b7cb65 |
| Verdict: | Malicious activity |
| Analysis date: | September 25, 2021, 02:41:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | BE6D1C14A969F6C64EB9F3A0F9FB375C |
| SHA1: | FF077E96335D5A5A68B331592D1E374F541D0C29 |
| SHA256: | 86AD07DABF34F8F3418F18949DE114FBAEBA8A09270133E48303C6E819A50107 |
| SSDEEP: | 3:N8r2Azv:2Lzv |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3404)
INFO
Reads the computer name
- iexplore.exe (PID: 268)
- iexplore.exe (PID: 3404)
Changes internet zones settings
- iexplore.exe (PID: 268)
Checks supported languages
- iexplore.exe (PID: 3404)
- iexplore.exe (PID: 268)
Checks Windows Trust Settings
- iexplore.exe (PID: 3404)
- iexplore.exe (PID: 268)
Reads settings of System Certificates
- iexplore.exe (PID: 3404)
- iexplore.exe (PID: 268)
Creates files in the user directory
- iexplore.exe (PID: 3404)
Application launched itself
- iexplore.exe (PID: 268)
Reads internet explorer settings
- iexplore.exe (PID: 3404)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 3404)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
37
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 268 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://gogoanime.be/" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3404 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:268 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
13 097
Read events
12 956
Write events
141
Delete events
0
Modification events
| (PID) Process: | (268) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (268) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (268) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30912950 | |||
| (PID) Process: | (268) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (268) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30912950 | |||
| (PID) Process: | (268) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (268) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (268) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (268) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (268) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
17
Text files
51
Unknown types
23
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3404 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\PNP6V7Y0.htm | html | |
MD5:BC51C15C38327DDC8F2A49D10952EBD6 | SHA256:5A86FE2051088FEC43F326D4021F5DC9067B8DBC11BCCE2BADD6B11C08AB6606 | |||
| 3404 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\82CB34DD3343FE727DF8890D352E0D8F | der | |
MD5:19C8BD1F7F069C31D8A9412682934CE0 | SHA256:CF990EE1D98C55B75623544876F4406A01D380A45B0D9C413C6F7AE26D1A3E48 | |||
| 3404 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\82CB34DD3343FE727DF8890D352E0D8F | binary | |
MD5:9B95489944EED4EC0A01A2263CFD6ABC | SHA256:12433E793CD1603730F327CBF45F2D58AADB2BAF69C5D4A5BB317C2BF133D1C5 | |||
| 3404 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\app[1].js | text | |
MD5:AF6A0A6D2AD99376CE44F92F9E8C2BE2 | SHA256:C14625AA2D337169C2F67E8C73CE8ED513C9A9629A6DFD35D03021634F8FF847 | |||
| 3404 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:B670E633B3C40F959F47F166D17DC1AC | SHA256:2D632A866BB2CDBC7BD71996E6CE6E107494BC4B478C9B211CEC8CC41F6B2BE9 | |||
| 3404 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | der | |
MD5:B427405B9F9C3B3F6FC20ABD795ED404 | SHA256:F9372CEF3A72E0F34644CDA109F4B4A9DC03FA7401267B885A2790DB0A8CC7D7 | |||
| 3404 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\7423F88C7F265F0DEFC08EA88C3BDE45_D975BBA8033175C8D112023D8A7A8AD6 | binary | |
MD5:ED2EF754108AC0A918965902FE1141EB | SHA256:993E24F98B7398727D439A89286314A9E003EE62F3B70B46B0DCC92BF8C14ED9 | |||
| 3404 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7423F88C7F265F0DEFC08EA88C3BDE45_D975BBA8033175C8D112023D8A7A8AD6 | der | |
MD5:0C723FE38623CCC678C94D75CCFBC44E | SHA256:DE857B5C12A7198B8CDA871BF60DFDA46FB17CCF2BA419EC680ABB982752926C | |||
| 3404 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\style[1].css | text | |
MD5:DBDBCB892233541E65E868514A9BB38A | SHA256:55290977B81530E5B939073D6563715638AB3DEE7C274B1B020D5B1B985CA019 | |||
| 3404 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\libs[1].js | text | |
MD5:A3EA43F2653AD916D5F96D69D3F18EBC | SHA256:ADD3097638829FACC98A6AF35A35EDD223C717CA87F2F45F4A606D181D2203D4 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
18
TCP/UDP connections
60
DNS requests
27
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3404 | iexplore.exe | GET | 200 | 142.250.184.195:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQD%2FlD3sEhDdGAoAAAAA%2FPSV | US | der | 472 b | whitelisted |
3404 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://crl3.digicert.com/Omniroot2025.crl | US | der | 7.68 Kb | whitelisted |
3404 | iexplore.exe | GET | 200 | 92.123.195.116:80 | http://crl.identrust.com/DSTROOTCAX3CRL.crl | unknown | der | 1.16 Kb | whitelisted |
3404 | iexplore.exe | GET | 200 | 142.250.184.195:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDc6ok2a4jVfAoAAAAA%2FPgi | US | der | 472 b | whitelisted |
3404 | iexplore.exe | GET | 200 | 92.123.195.35:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgODa63V0kCbvBIAmBV2ZK3rKA%3D%3D | unknown | der | 503 b | shared |
268 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
268 | iexplore.exe | GET | 304 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?891218c58222d0b1 | US | — | — | whitelisted |
3404 | iexplore.exe | GET | 200 | 104.89.32.83:80 | http://x1.c.lencr.org/ | NL | der | 717 b | whitelisted |
3404 | iexplore.exe | GET | 200 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?b6f55517897bfb55 | US | compressed | 4.70 Kb | whitelisted |
3404 | iexplore.exe | GET | 200 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?d811fe331798fe31 | US | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3404 | iexplore.exe | 172.67.157.73:443 | gogoanime.be | — | US | suspicious |
3404 | iexplore.exe | 209.197.3.8:80 | ctldl.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
3404 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
268 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
268 | iexplore.exe | 209.197.3.8:80 | ctldl.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
3404 | iexplore.exe | 142.250.185.136:443 | www.googletagmanager.com | Google Inc. | US | suspicious |
— | — | 172.67.157.73:443 | gogoanime.be | — | US | suspicious |
3404 | iexplore.exe | 104.16.18.94:443 | cdnjs.cloudflare.com | Cloudflare Inc | US | unknown |
3404 | iexplore.exe | 142.250.186.68:443 | www.google.com | Google Inc. | US | whitelisted |
— | — | 142.250.186.68:443 | www.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
gogoanime.be |
| suspicious |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
crl3.digicert.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
www.google.com |
| malicious |
s7.addthis.com |
| whitelisted |