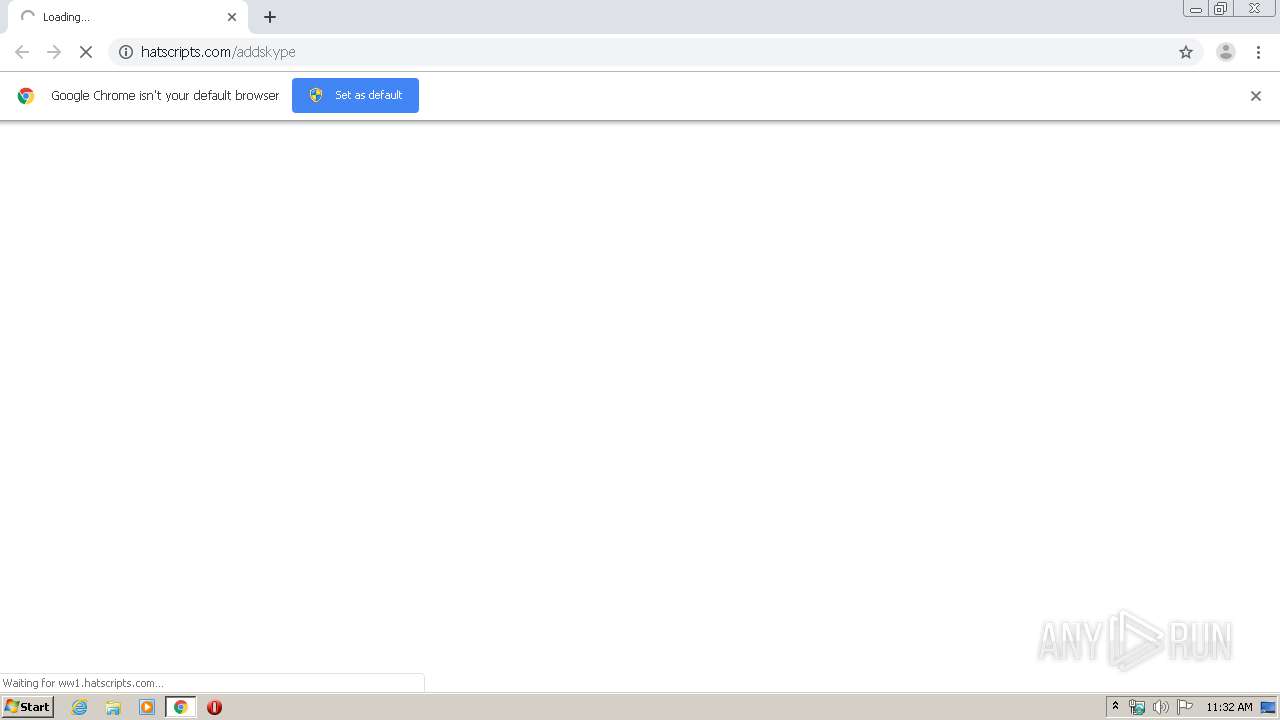
| URL: | http://hatscripts.com/addskype |
| Full analysis: | https://app.any.run/tasks/cc627545-c383-4cef-85d7-1c13c9b820a5 |
| Verdict: | Malicious activity |
| Analysis date: | March 31, 2020, 10:32:27 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 1A53DA15EC82B6E1E30C4BDDDD5F1DAA |
| SHA1: | B0D6CF3E24F2B919D00F13A794C2134074AC1E59 |
| SHA256: | 86AA15EABC8172D6E42E9DCB7508603FA56457F57AAF8C10BE8F1E8BF8DE196B |
| SSDEEP: | 3:N1KWE7MVRqIKEH:CW0M7q0H |
MALICIOUS
No malicious indicators.SUSPICIOUS
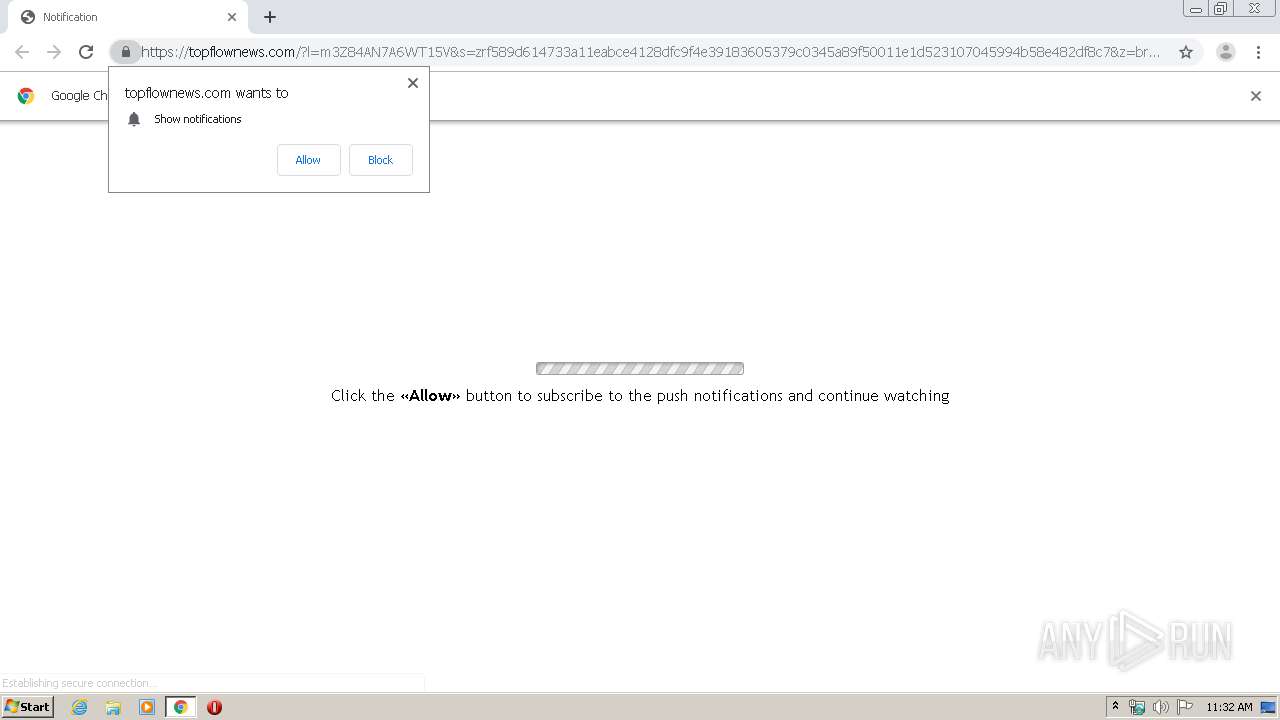
Modifies files in Chrome extension folder
- chrome.exe (PID: 2524)
INFO
Reads the hosts file
- chrome.exe (PID: 2524)
- chrome.exe (PID: 2756)
Changes settings of System certificates
- chrome.exe (PID: 2756)
Application launched itself
- chrome.exe (PID: 2524)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
65
Monitored processes
29
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 820 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=996,14134417760950761469,12088534520466632996,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=8618211905672259000 --mojo-platform-channel-handle=1016 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 852 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,14134417760950761469,12088534520466632996,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16367582066488449964 --mojo-platform-channel-handle=3648 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1720 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,14134417760950761469,12088534520466632996,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4014916732779768553 --renderer-client-id=24 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3668 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1872 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,14134417760950761469,12088534520466632996,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7019092710916555561 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3356 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2116 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,14134417760950761469,12088534520466632996,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15265564269956165826 --mojo-platform-channel-handle=4168 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2424 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=996,14134417760950761469,12088534520466632996,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=993146008740231017 --mojo-platform-channel-handle=3956 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2488 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6fa8a9d0,0x6fa8a9e0,0x6fa8a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2520 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,14134417760950761469,12088534520466632996,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12561573826824994316 --mojo-platform-channel-handle=4276 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2524 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "http://hatscripts.com/addskype" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2548 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,14134417760950761469,12088534520466632996,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17552309250871821331 --mojo-platform-channel-handle=4172 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
604
Read events
520
Write events
79
Delete events
5
Modification events
| (PID) Process: | (2524) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2524) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2524) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2524) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2524) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2884) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2524-13230124362946750 |
Value: 259 | |||
| (PID) Process: | (2524) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2524) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2524) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (2524) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
92
Text files
233
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2524 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5E831C4B-9DC.pma | — | |
MD5:— | SHA256:— | |||
| 2524 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\572f84f0-023b-4b64-a4d8-51ca31aec777.tmp | — | |
MD5:— | SHA256:— | |||
| 2524 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2524 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2524 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2524 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2524 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\metadata\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2524 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RFa66b55.TMP | text | |
MD5:— | SHA256:— | |||
| 2524 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2524 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFa66ceb.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
89
DNS requests
59
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
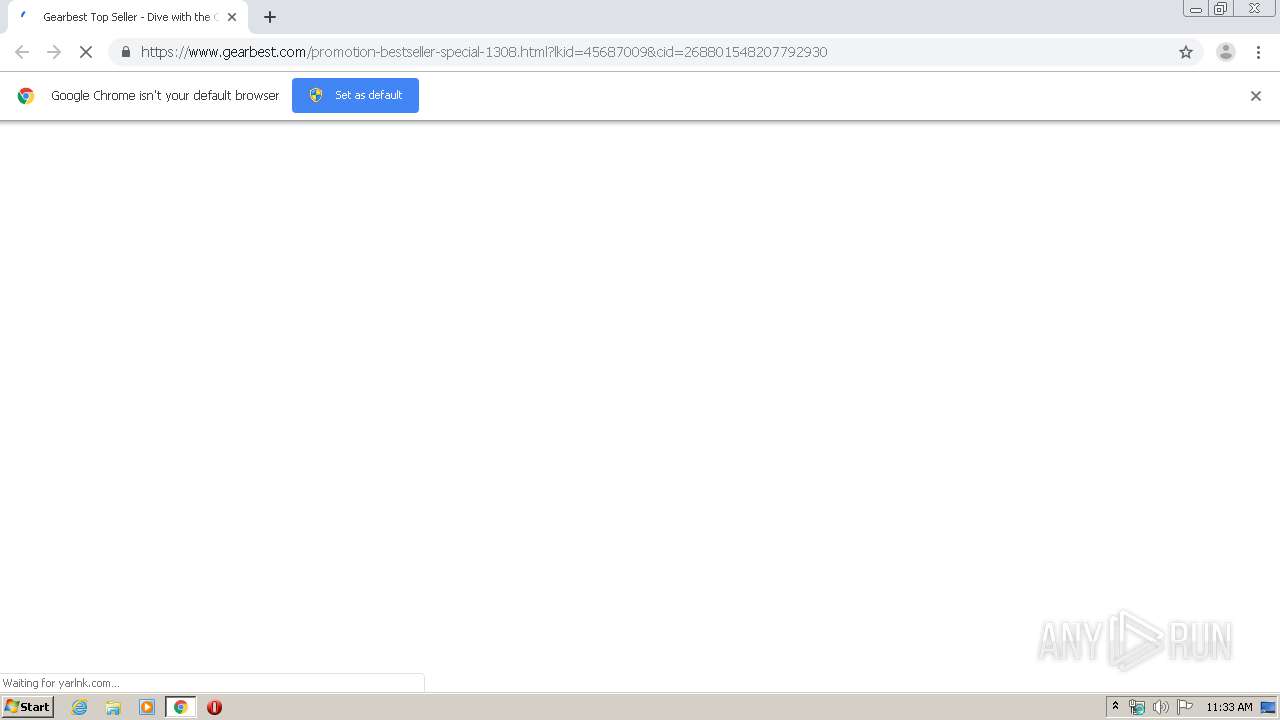
2756 | chrome.exe | GET | 302 | 69.16.230.42:80 | http://hatscripts.com/addskype | US | — | — | malicious |
2756 | chrome.exe | GET | — | 35.169.74.130:80 | http://usd.alwilda-ram.com/favicon.ico | US | — | — | shared |
2756 | chrome.exe | GET | 200 | 91.195.240.136:80 | http://ww1.hatscripts.com/ | DE | html | 2.77 Kb | malicious |
2756 | chrome.exe | GET | 302 | 91.195.240.136:80 | http://ww1.hatscripts.com/search/redirect.php?f=http%3A%2F%2Fusd.alwilda-ram.com%2Fzcvisitor%2Ff589d614-733a-11ea-bce4-128dfc9f4e39%3Fcampaignid%3Dd9eea150-702f-11ea-a9db-0a06ea97c507&v=ZTMxNGM3ZTEzZjZjNTM0ODNkYjI2MWZkNDE2ODUzMTQJMQl3dzEuaGF0c2NyaXB0cy5jb201ZTgzMWM0ZDFkMTY2OS43NTQ5MzUwMwl3dzEuaGF0c2NyaXB0cy5jb201ZTgzMWM0ZDFkMWE1Mi4yNDkxMjM4NQkxNTg1NjUwNzY2CWFkXzMxXzA=&l=OAk4ZWU5ZTU5MGViYzY2NmJmZGY3NWExYjkzMzY3NDg2ZQkwCTIwCTAJMmE5Yzc2MmEwMjBmYzAyYTkxN2YwMDhiNjAxZGRlOTkJMzM1NjM4Njg4CWhhdHNjcmlwdHMJMTEwMQkzMQkxCTE1CTE1ODU2NTA3NjYJMC4wMDA1NglOCTAJMQkwCTEyMDUJMzEzNDQyNjcwCTE4NS4xODMuMTA3LjIzNgkw | DE | compressed | 2.77 Kb | malicious |
2756 | chrome.exe | GET | 200 | 91.195.240.136:80 | http://ww1.hatscripts.com/search/tsc.php?200=MzM1NjM4Njg4&21=MTg1LjE4My4xMDcuMjM2&681=MTU4NTY1MDc2NjUyNTQ4ODBlM2U2NzgzMGIxNTRmMzcyYWU3ODFlOTM2&crc=6823e60aa7cd09c96992089e23b1245f1e5811c6&cv=1 | DE | compressed | 2.77 Kb | malicious |
2756 | chrome.exe | GET | 200 | 35.169.74.130:80 | http://usd.alwilda-ram.com/zcvisitor/f589d614-733a-11ea-bce4-128dfc9f4e39?campaignid=d9eea150-702f-11ea-a9db-0a06ea97c507 | US | html | 1008 b | shared |
2756 | chrome.exe | GET | 302 | 91.195.240.136:80 | http://ww1.hatscripts.com/search/tcerider.php?f=http%3A%2F%2Fusd.alwilda-ram.com%2Fzcvisitor%2Ff589d614-733a-11ea-bce4-128dfc9f4e39%3Fcampaignid%3Dd9eea150-702f-11ea-a9db-0a06ea97c507&v=ZTMxNGM3ZTEzZjZjNTM0ODNkYjI2MWZkNDE2ODUzMTQJMQl3dzEuaGF0c2NyaXB0cy5jb201ZTgzMWM0ZDFkMTY2OS43NTQ5MzUwMwl3dzEuaGF0c2NyaXB0cy5jb201ZTgzMWM0ZDFkMWE1Mi4yNDkxMjM4NQkxNTg1NjUwNzY2CWFkXzMxXzA=&l=OAk4ZWU5ZTU5MGViYzY2NmJmZGY3NWExYjkzMzY3NDg2ZQkwCTIwCTAJMmE5Yzc2MmEwMjBmYzAyYTkxN2YwMDhiNjAxZGRlOTkJMzM1NjM4Njg4CWhhdHNjcmlwdHMJMTEwMQkzMQkxCTE1CTE1ODU2NTA3NjYJMC4wMDA1NglOCTAJMQkwCTEyMDUJMzEzNDQyNjcwCTE4NS4xODMuMTA3LjIzNgkw | DE | html | 465 b | malicious |
2756 | chrome.exe | GET | 200 | 35.169.74.130:80 | http://usd.alwilda-ram.com/zcredirect?visitid=f589d614-733a-11ea-bce4-128dfc9f4e39&type=js&browserWidth=1280&browserHeight=572&iframeDetected=false | US | html | 482 b | shared |
2756 | chrome.exe | GET | 302 | 216.58.205.238:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 539 b | whitelisted |
2756 | chrome.exe | GET | 302 | 216.58.205.238:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 544 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2756 | chrome.exe | 172.217.23.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
2756 | chrome.exe | 91.195.240.136:80 | ww1.hatscripts.com | SEDO GmbH | DE | malicious |
2756 | chrome.exe | 205.234.175.175:80 | img.sedoparking.com | CacheNetworks, Inc. | US | suspicious |
2756 | chrome.exe | 35.169.74.130:80 | usd.alwilda-ram.com | Amazon.com, Inc. | US | malicious |
2756 | chrome.exe | 188.42.160.69:443 | my.rtmark.net | Webzilla B.V. | NL | unknown |
2756 | chrome.exe | 88.85.66.186:443 | blacurlik.com | Webzilla B.V. | NL | unknown |
2756 | chrome.exe | 88.85.66.227:443 | choogeet.net | Webzilla B.V. | NL | unknown |
— | — | 216.58.208.36:443 | www.google.com | Google Inc. | US | whitelisted |
2756 | chrome.exe | 216.58.205.238:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
2756 | chrome.exe | 172.217.23.174:443 | clients2.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
hatscripts.com |
| malicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
ww1.hatscripts.com |
| malicious |
img.sedoparking.com |
| whitelisted |
usd.alwilda-ram.com |
| shared |
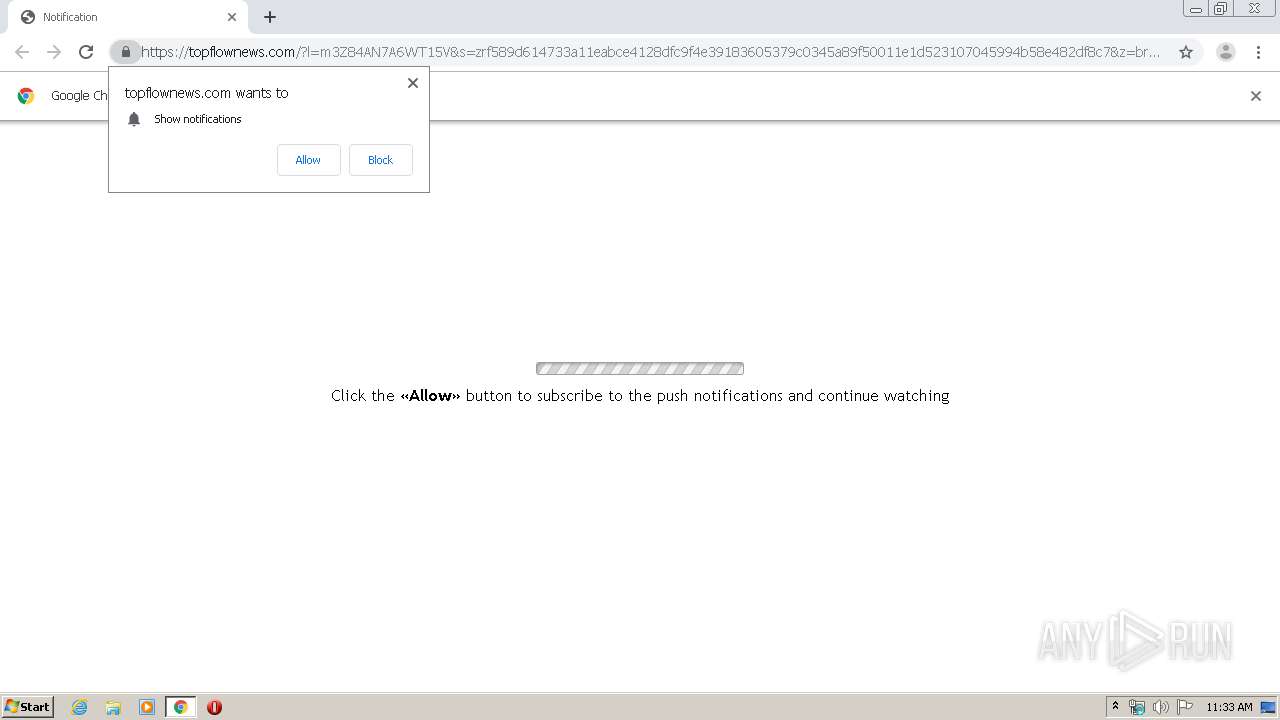
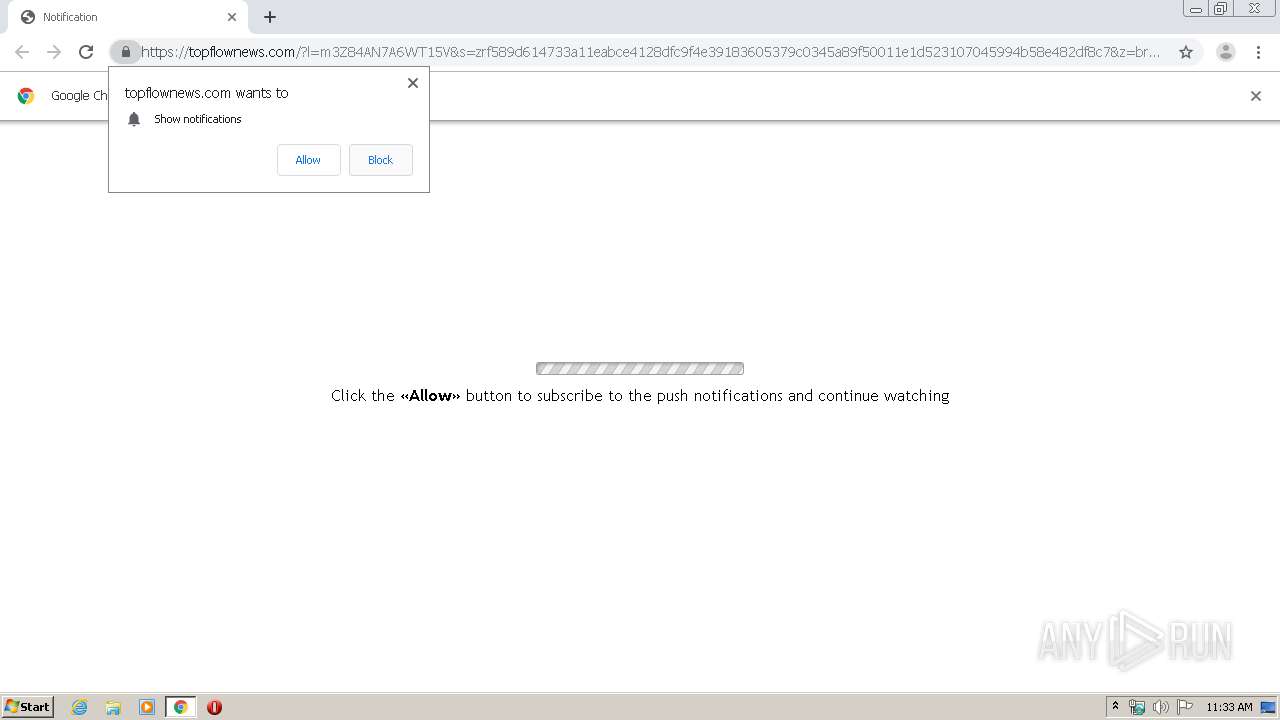
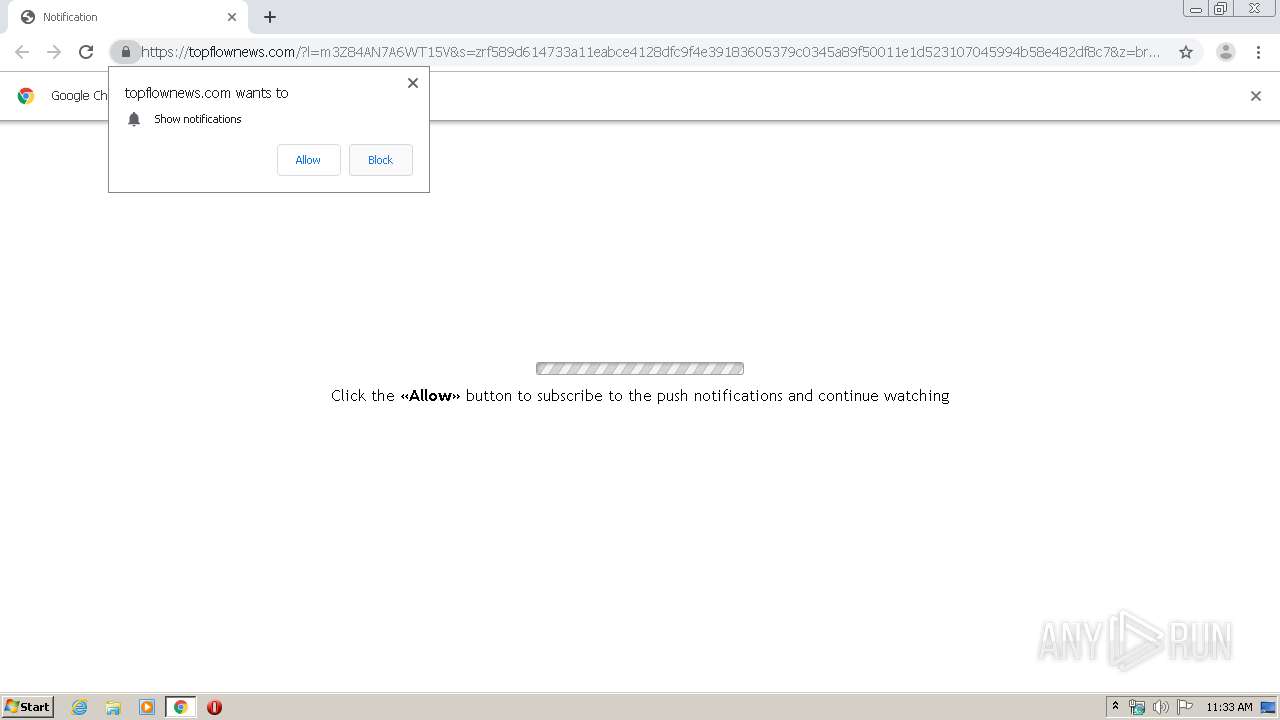
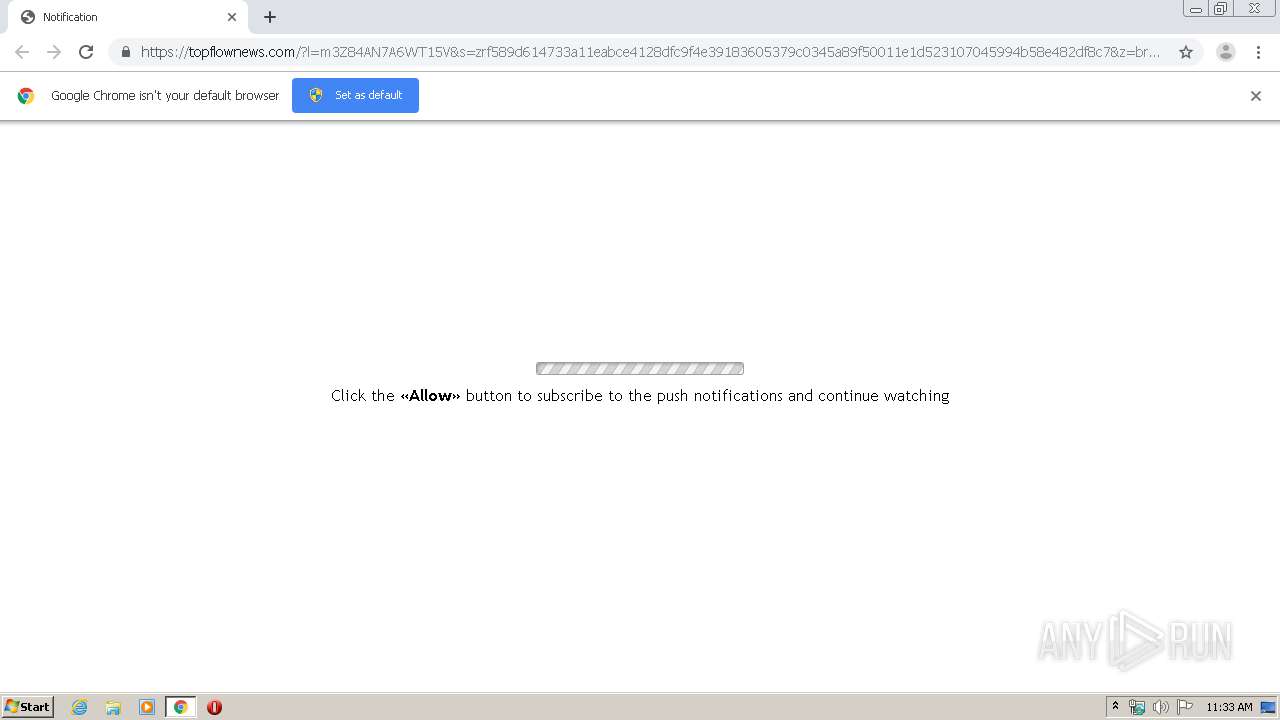
topflownews.com |
| whitelisted |
blacurlik.com |
| malicious |
choogeet.net |
| suspicious |
my.rtmark.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2756 | chrome.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |