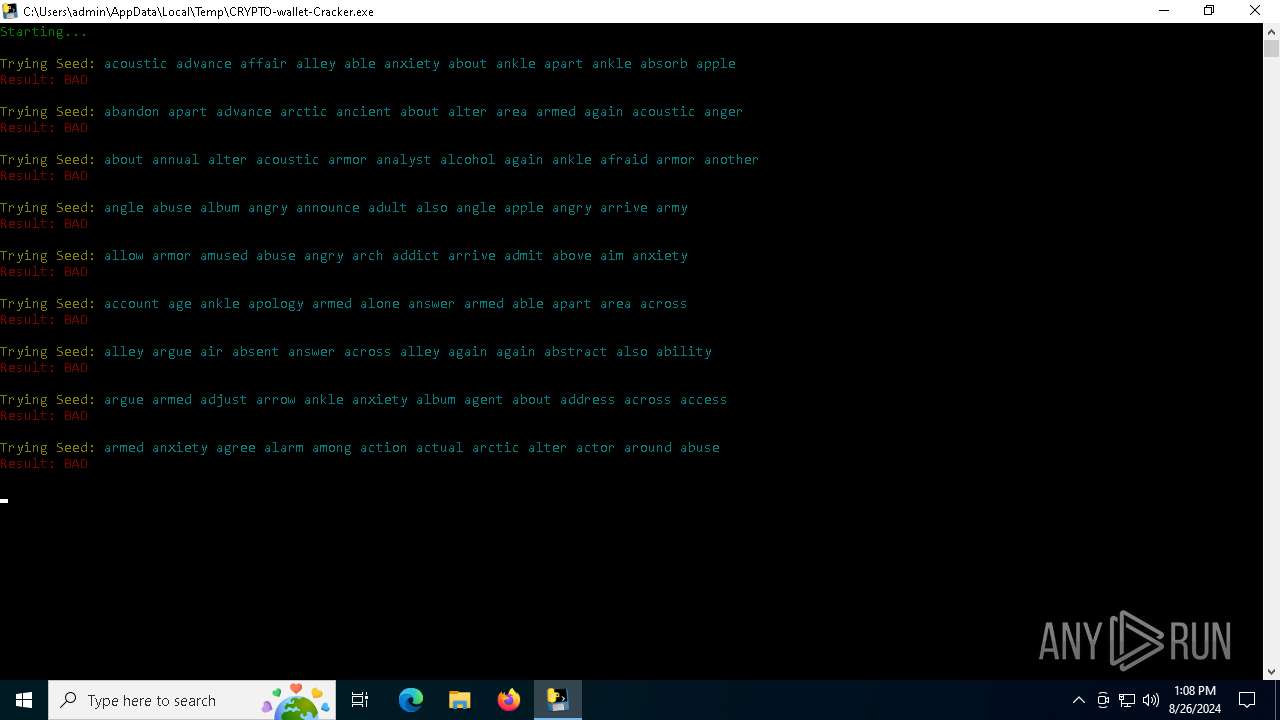
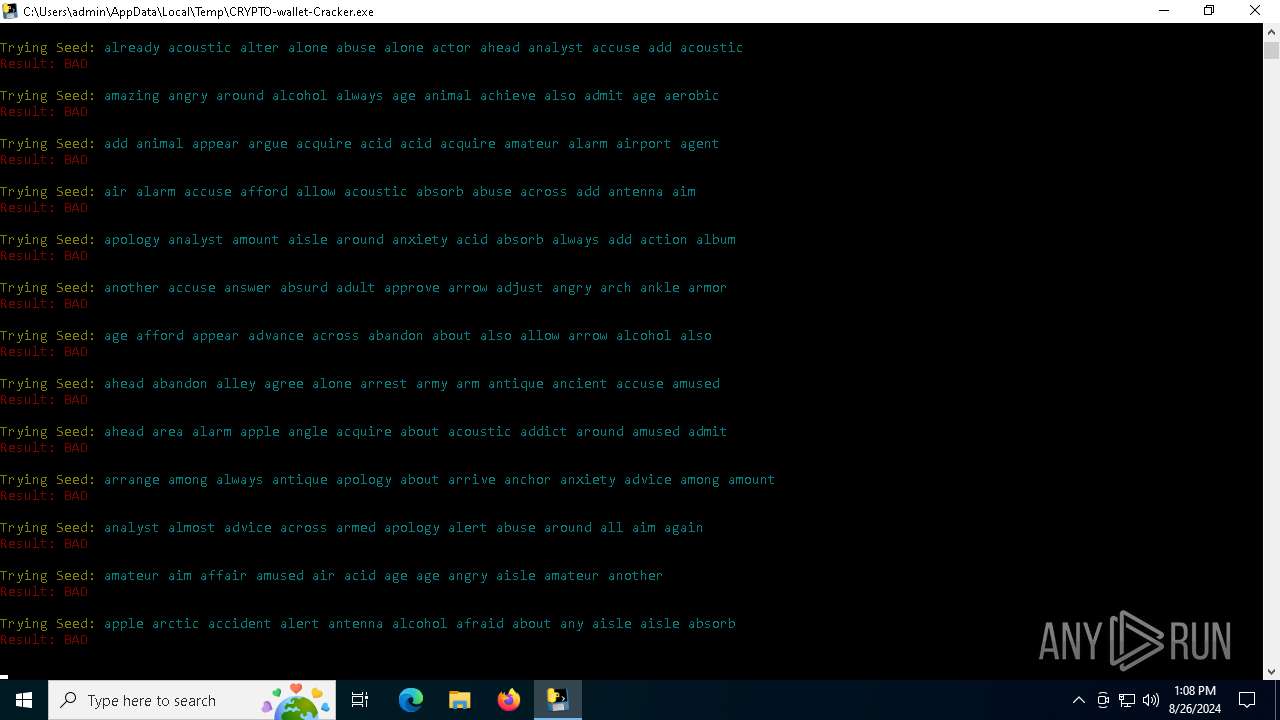
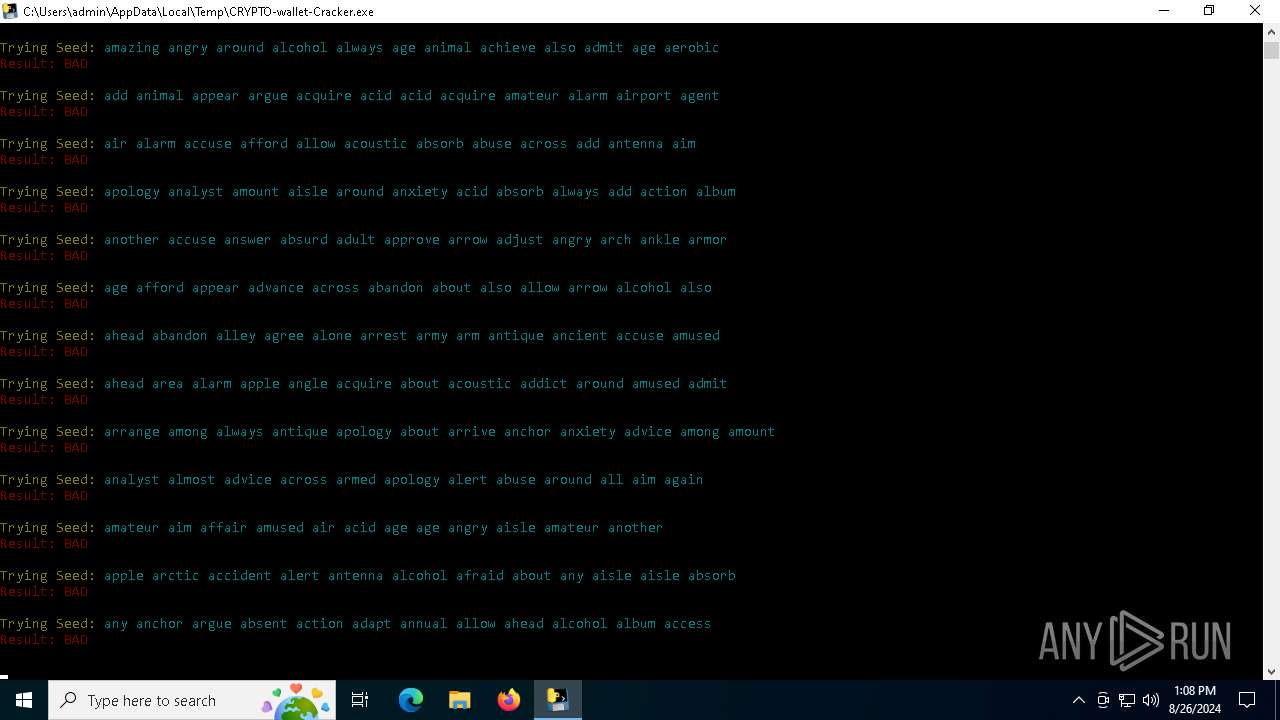
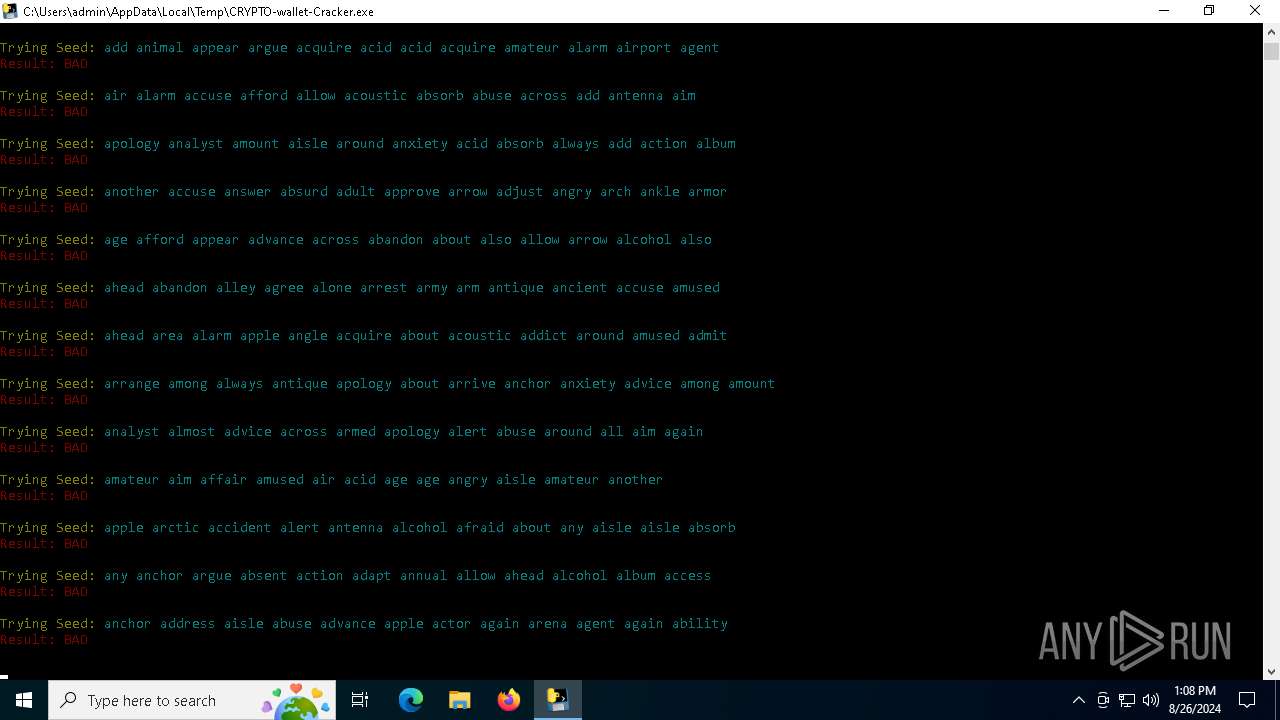
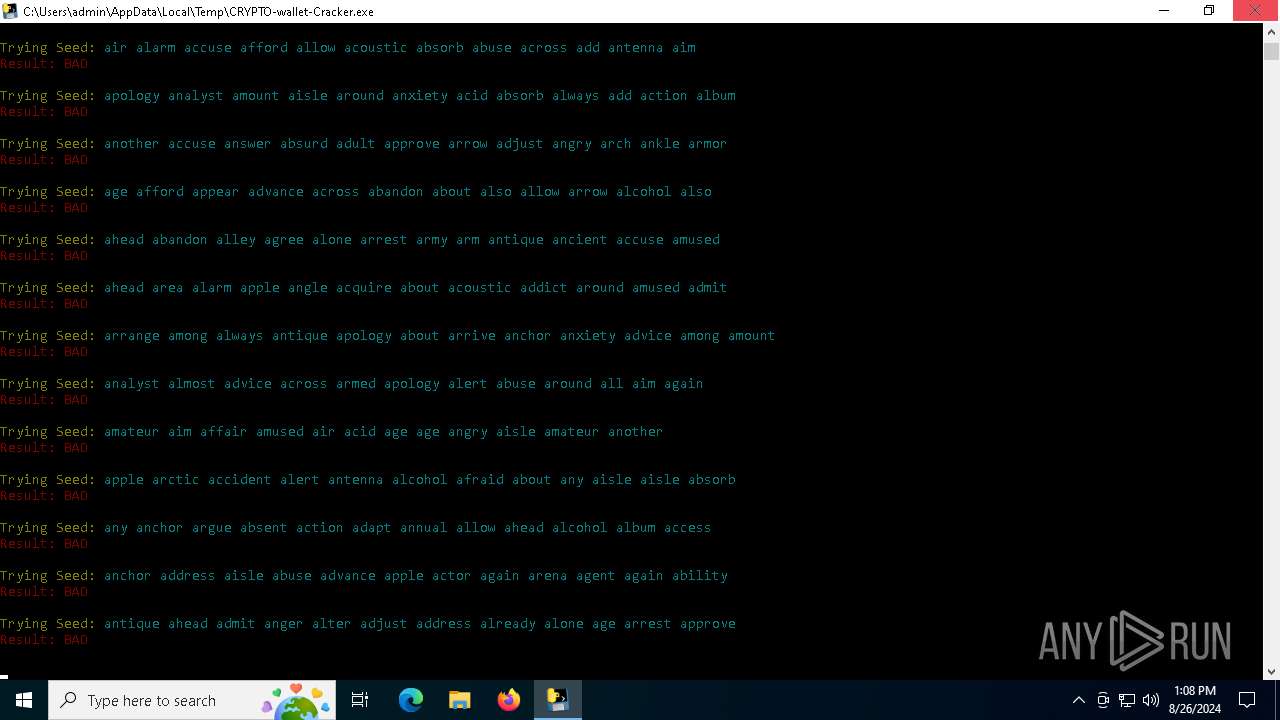
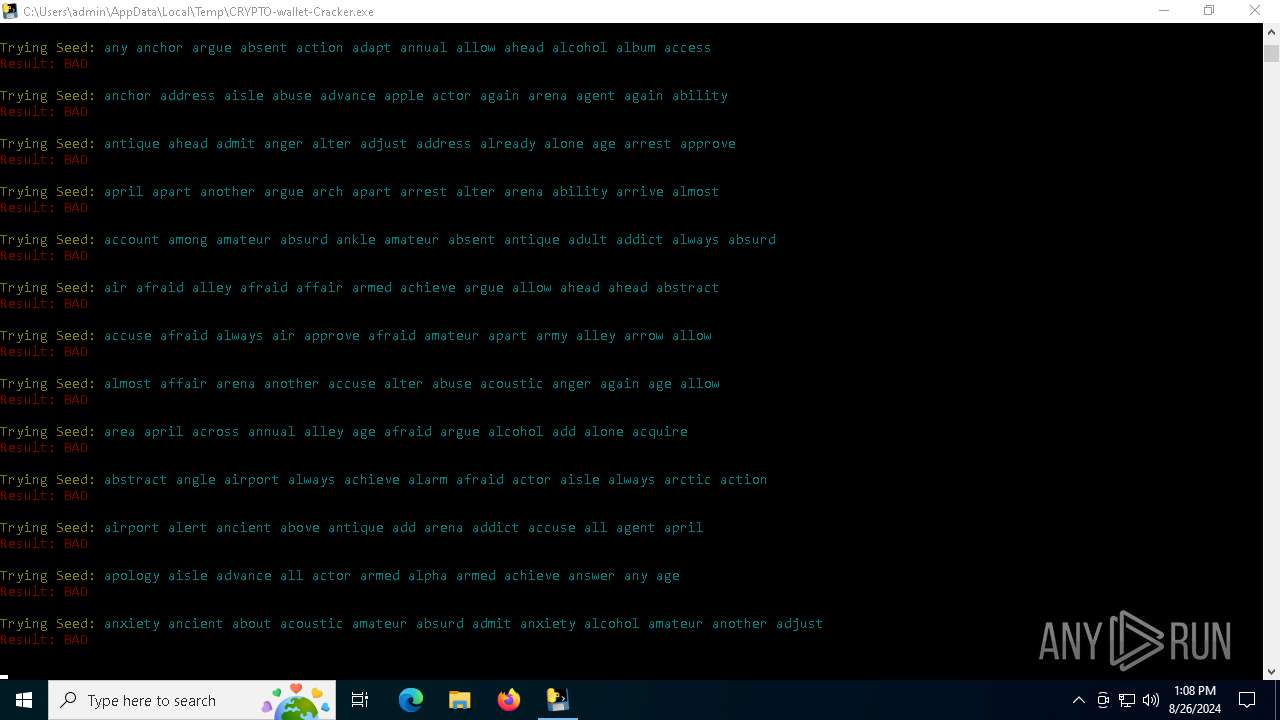
| File name: | CRYPTO-wallet-Cracker.exe |
| Full analysis: | https://app.any.run/tasks/9fefba38-d828-4854-8083-7721b8e63d28 |
| Verdict: | Malicious activity |
| Threats: | A loader is malicious software that infiltrates devices to deliver malicious payloads. This malware is capable of infecting victims’ computers, analyzing their system information, and installing other types of threats, such as trojans or stealers. Criminals usually deliver loaders through phishing emails and links by relying on social engineering to trick users into downloading and running their executables. Loaders employ advanced evasion and persistence tactics to avoid detection. |
| Analysis date: | August 26, 2024, 13:08:07 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32+ executable (console) x86-64, for MS Windows |
| MD5: | 140354A8509F90D76BC2975D5E6A7592 |
| SHA1: | 2FEF012D2C65A84664292B1D3C2A19B33D3A03EF |
| SHA256: | 86A94F3507135A7147F15AF4D81094F0A486B722E4DF72D85FAC74E99380B17B |
| SSDEEP: | 98304:9DZowErFrt0A2qzpZyB4tHfktEzafhOsE+XZ0Nya0TuqTA0PzRYqmh7vSRpl89+m:QGrmCM1boh11Xmts |
MALICIOUS
Create files in the Startup directory
- temp_nik_zbi.exe (PID: 4252)
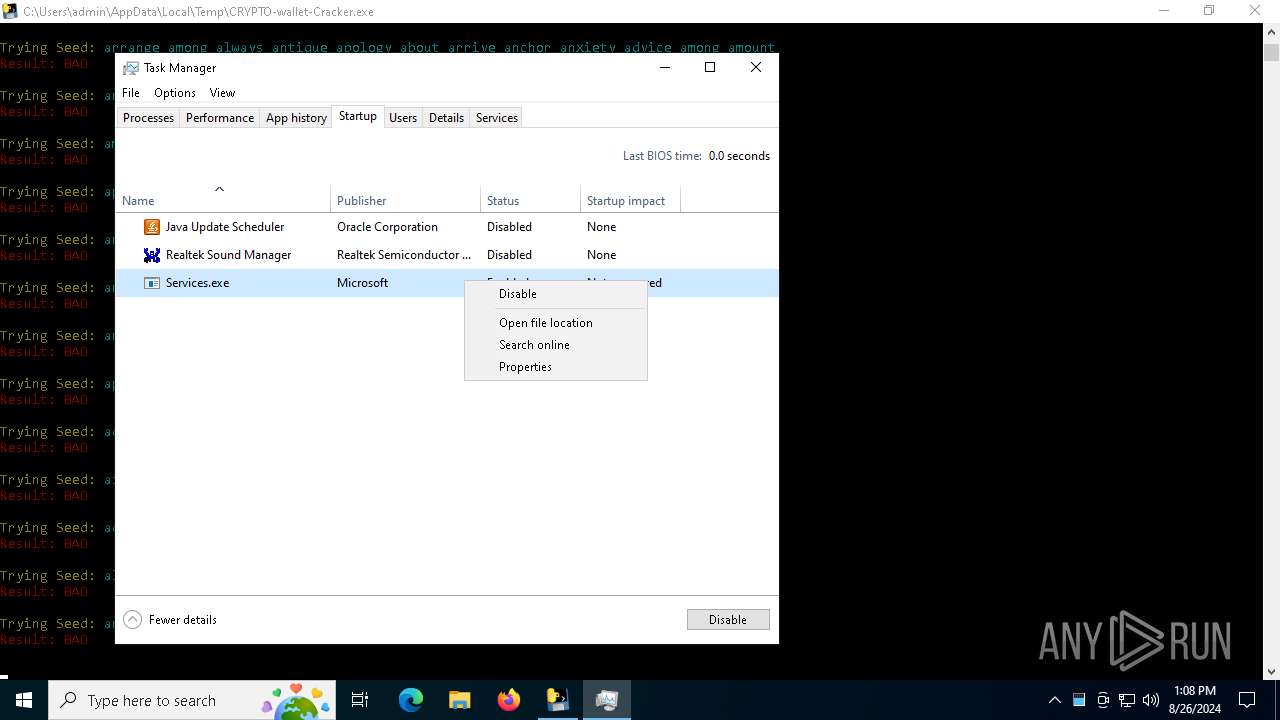
Changes the autorun value in the registry
- svchost.exe (PID: 5128)
- temp_nik_zbi.exe (PID: 4252)
Runs injected code in another process
- svchost.exe (PID: 5128)
Application was injected by another process
- explorer.exe (PID: 4552)
The DLL Hijacking
- WerFault.exe (PID: 4092)
- WerFault.exe (PID: 7076)
SUSPICIOUS
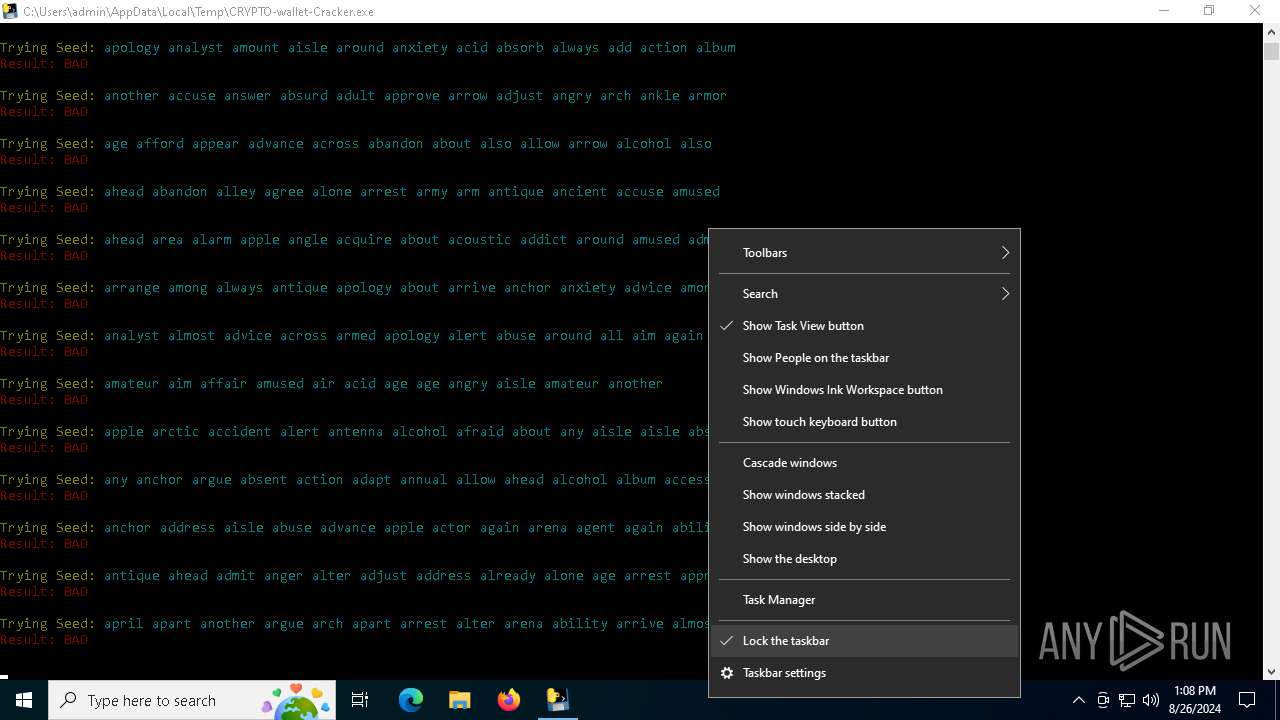
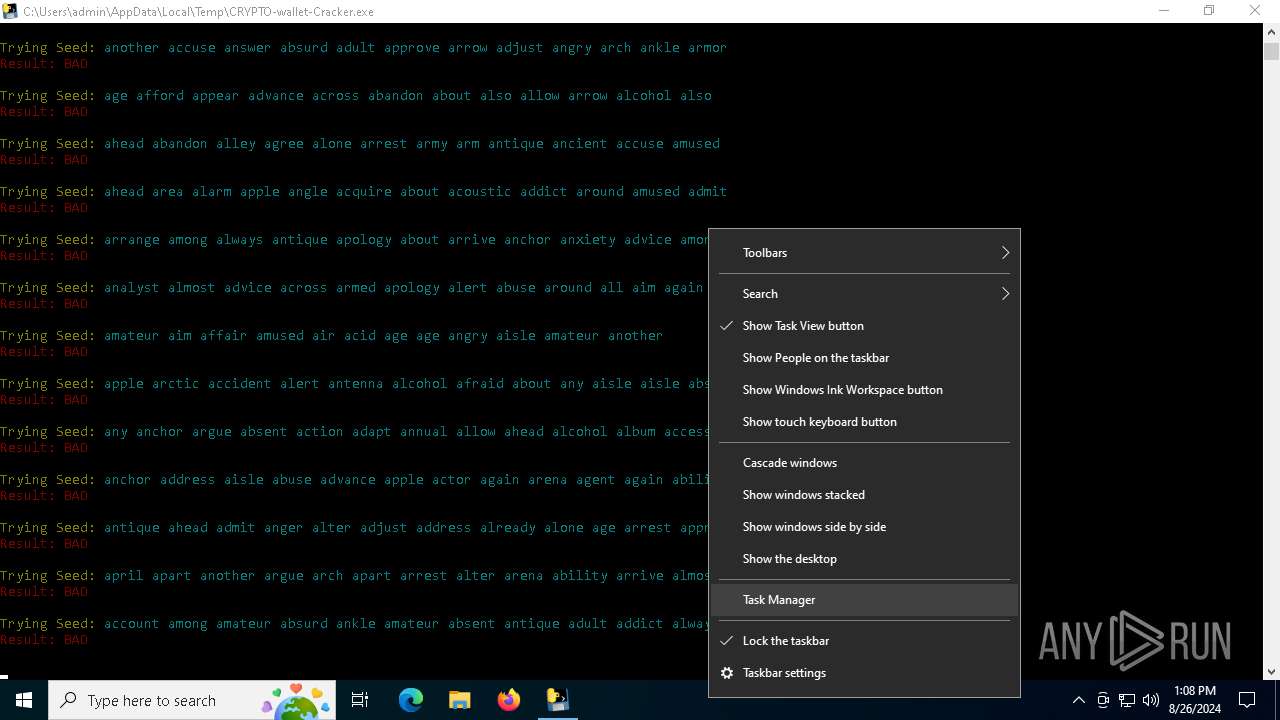
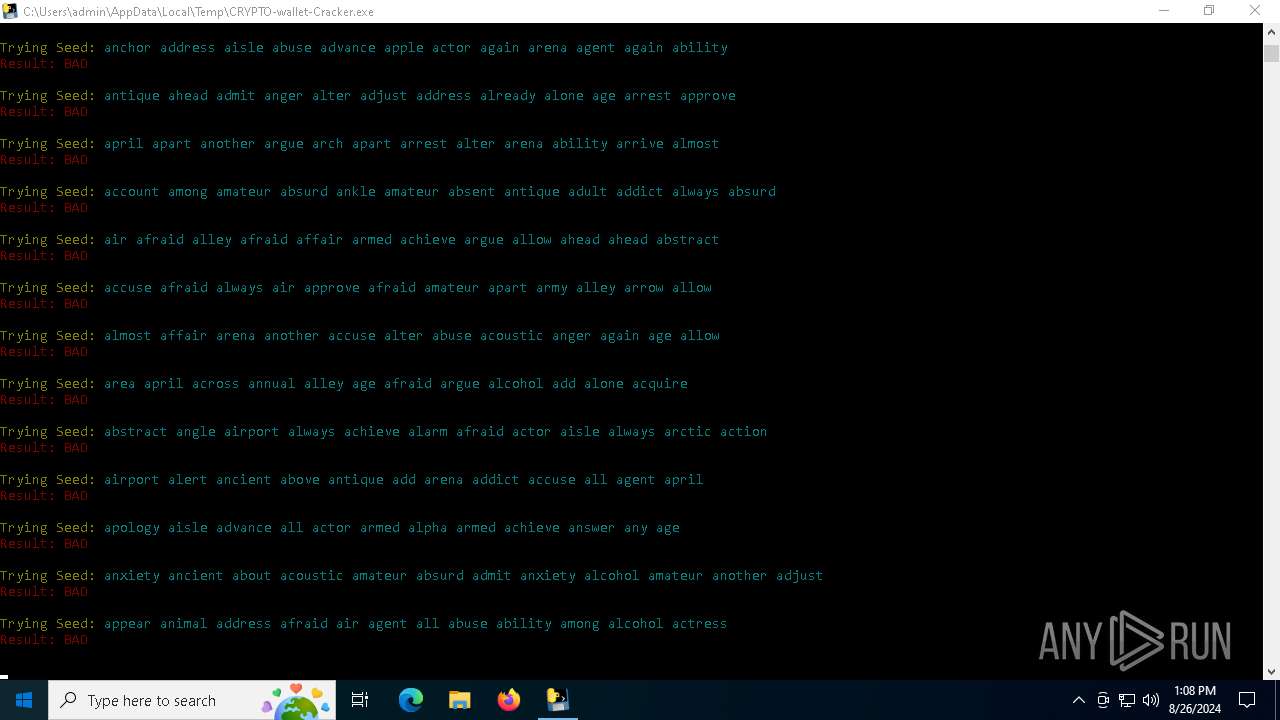
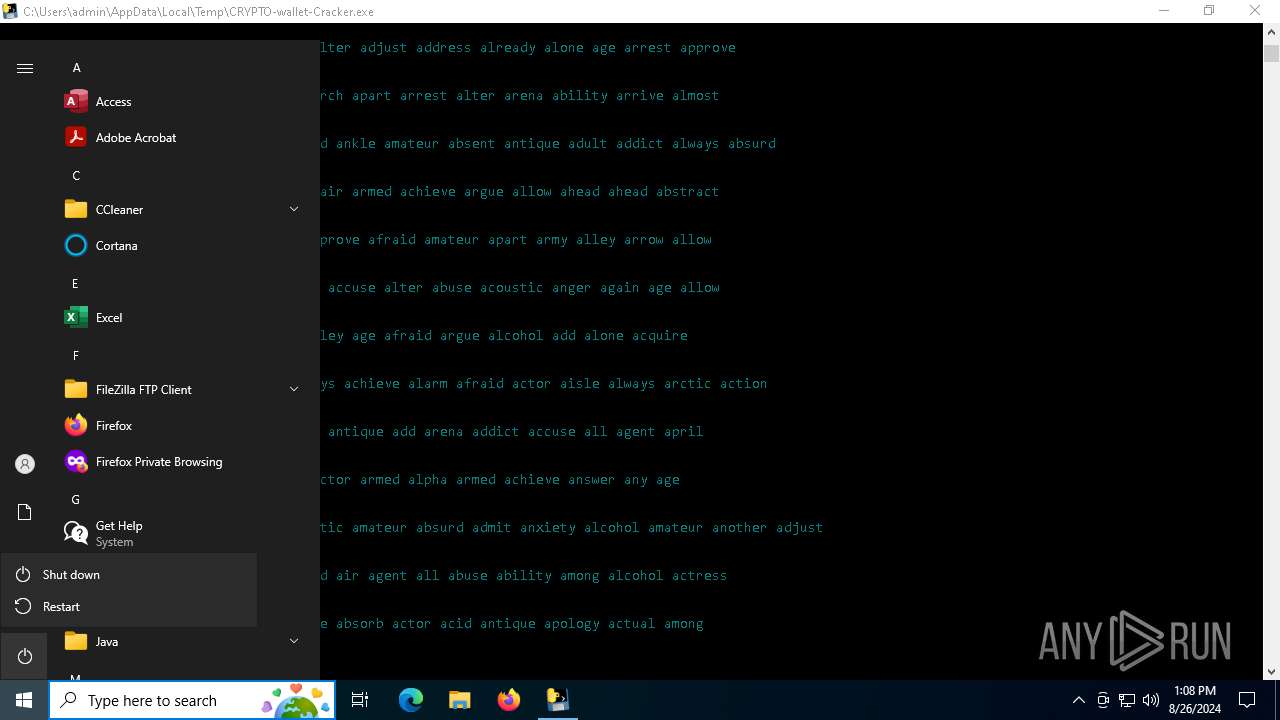
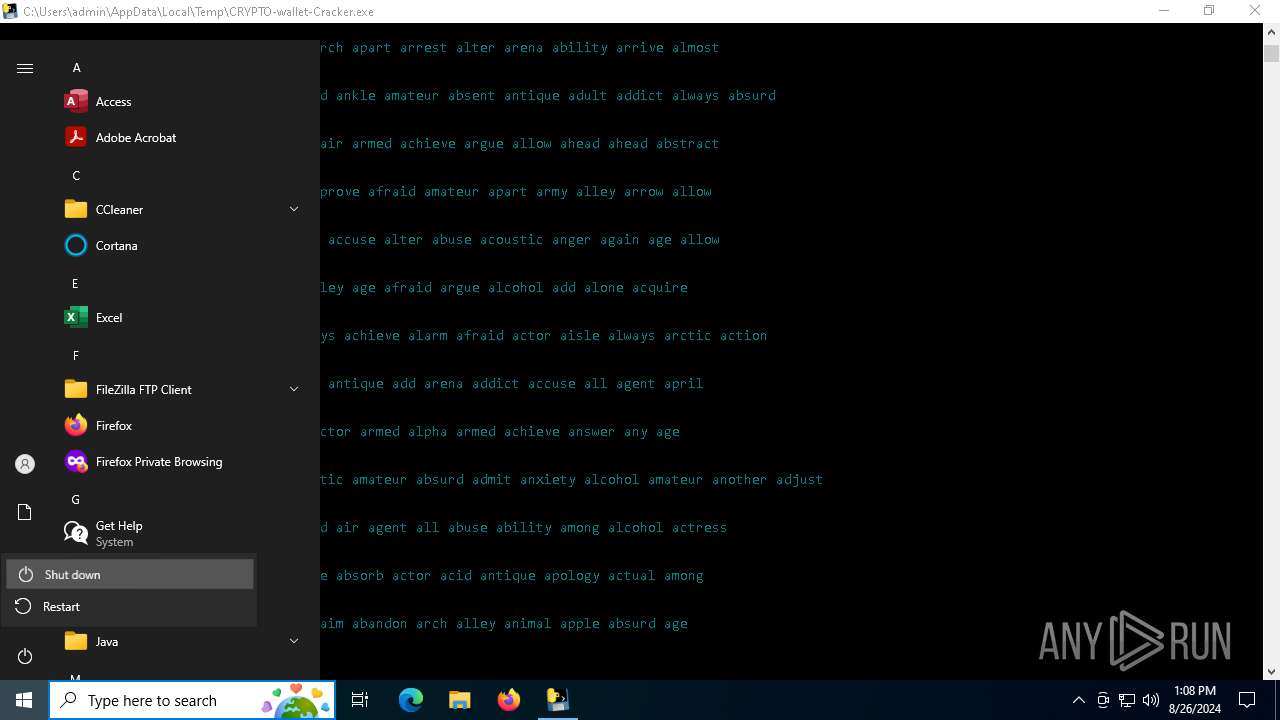
Drops the executable file immediately after the start
- CRYPTO-wallet-Cracker.exe (PID: 508)
- CRYPTO-wallet-Cracker.exe (PID: 5160)
- temp_nik_zbi.exe (PID: 4252)
- CA8C.tmp.nikzbi.exe (PID: 2224)
The process drops C-runtime libraries
- CRYPTO-wallet-Cracker.exe (PID: 508)
- CA8C.tmp.nikzbi.exe (PID: 2224)
Application launched itself
- CRYPTO-wallet-Cracker.exe (PID: 508)
- CA8C.tmp.nikzbi.exe (PID: 2224)
Process drops python dynamic module
- CRYPTO-wallet-Cracker.exe (PID: 508)
- CA8C.tmp.nikzbi.exe (PID: 2224)
Executable content was dropped or overwritten
- CRYPTO-wallet-Cracker.exe (PID: 508)
- CRYPTO-wallet-Cracker.exe (PID: 5160)
- temp_nik_zbi.exe (PID: 4252)
- svchost.exe (PID: 5128)
- CA8C.tmp.nikzbi.exe (PID: 2224)
- explorer.exe (PID: 4552)
Process drops legitimate windows executable
- CRYPTO-wallet-Cracker.exe (PID: 508)
- CA8C.tmp.nikzbi.exe (PID: 2224)
Loads Python modules
- CRYPTO-wallet-Cracker.exe (PID: 5160)
- CA8C.tmp.nikzbi.exe (PID: 2628)
Potential Corporate Privacy Violation
- CRYPTO-wallet-Cracker.exe (PID: 5160)
- svchost.exe (PID: 5128)
- explorer.exe (PID: 4552)
Process requests binary or script from the Internet
- CRYPTO-wallet-Cracker.exe (PID: 5160)
- explorer.exe (PID: 4552)
Connects to the server without a host name
- CRYPTO-wallet-Cracker.exe (PID: 5160)
- explorer.exe (PID: 4552)
Executes application which crashes
- firefox.exe (PID: 6596)
- firefox.exe (PID: 6152)
Loads DLL from Mozilla Firefox
- WerFault.exe (PID: 4092)
- WerFault.exe (PID: 7076)
Found regular expressions for crypto-addresses (YARA)
- svchost.exe (PID: 5128)
INFO
Checks supported languages
- CRYPTO-wallet-Cracker.exe (PID: 508)
- CRYPTO-wallet-Cracker.exe (PID: 5160)
- temp_nik_zbi.exe (PID: 4252)
- CA8C.tmp.nikzbi.exe (PID: 2628)
- CA8C.tmp.nikzbi.exe (PID: 2224)
Create files in a temporary directory
- CRYPTO-wallet-Cracker.exe (PID: 508)
- CRYPTO-wallet-Cracker.exe (PID: 5160)
- svchost.exe (PID: 5128)
- CA8C.tmp.nikzbi.exe (PID: 2224)
- explorer.exe (PID: 4552)
Reads the machine GUID from the registry
- CRYPTO-wallet-Cracker.exe (PID: 5160)
- CA8C.tmp.nikzbi.exe (PID: 2628)
Reads the computer name
- CRYPTO-wallet-Cracker.exe (PID: 508)
- temp_nik_zbi.exe (PID: 4252)
- CA8C.tmp.nikzbi.exe (PID: 2224)
Checks proxy server information
- CRYPTO-wallet-Cracker.exe (PID: 5160)
- svchost.exe (PID: 5128)
- WerFault.exe (PID: 4092)
- WerFault.exe (PID: 7076)
Creates files or folders in the user directory
- temp_nik_zbi.exe (PID: 4252)
- explorer.exe (PID: 4552)
- WerFault.exe (PID: 4092)
- WerFault.exe (PID: 7076)
Reads security settings of Internet Explorer
- svchost.exe (PID: 5128)
- explorer.exe (PID: 4552)
- Taskmgr.exe (PID: 2820)
PyInstaller has been detected (YARA)
- CRYPTO-wallet-Cracker.exe (PID: 508)
- CRYPTO-wallet-Cracker.exe (PID: 5160)
Application launched itself
- firefox.exe (PID: 6580)
- firefox.exe (PID: 4364)
Reads Microsoft Office registry keys
- firefox.exe (PID: 6580)
Changes appearance of the Explorer extensions
- svchost.exe (PID: 5128)
Reads the software policy settings
- WerFault.exe (PID: 4092)
- WerFault.exe (PID: 7076)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2024:08:25 14:46:41+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.4 |
| CodeSize: | 173056 |
| InitializedDataSize: | 151040 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xb4d0 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
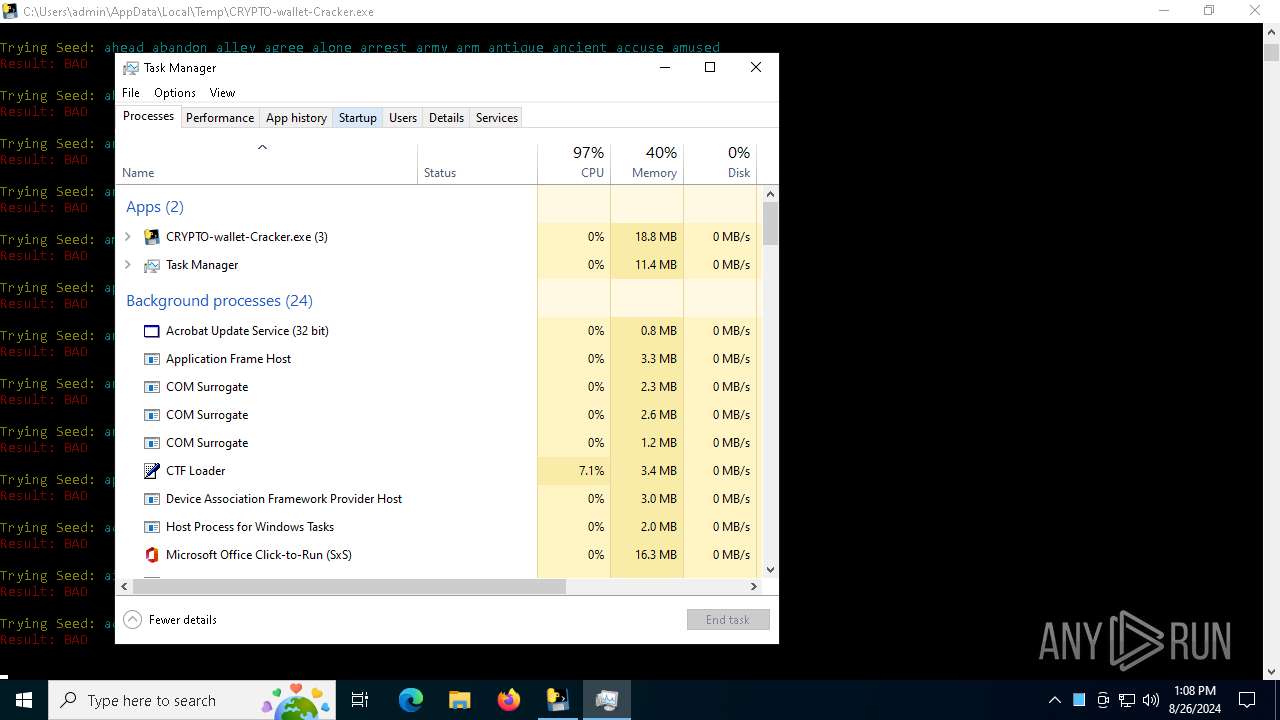
Total processes
154
Monitored processes
22
Malicious processes
8
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 508 | "C:\Users\admin\AppData\Local\Temp\CRYPTO-wallet-Cracker.exe" | C:\Users\admin\AppData\Local\Temp\CRYPTO-wallet-Cracker.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1073807364 Modules
| |||||||||||||||
| 788 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=6000 -childID 5 -isForBrowser -prefsHandle 5696 -prefMapHandle 5596 -prefsLen 31247 -prefMapSize 245487 -jsInitHandle 1360 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {7bf85147-dc9e-42ab-867f-9b23cda2b3f8} 6580 "\\.\pipe\gecko-crash-server-pipe.6580" 1336849b850 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 1480 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | CRYPTO-wallet-Cracker.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2008 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5808 -childID 4 -isForBrowser -prefsHandle 5800 -prefMapHandle 5796 -prefsLen 31255 -prefMapSize 245487 -jsInitHandle 1360 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {15fae2aa-f2bd-4922-8ed1-e3df935f7055} 6580 "\\.\pipe\gecko-crash-server-pipe.6580" 1336849b310 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 2224 | "C:\Users\admin\AppData\Local\Temp\CA8C.tmp.nikzbi.exe" | C:\Users\admin\AppData\Local\Temp\CA8C.tmp.nikzbi.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2628 | "C:\Users\admin\AppData\Local\Temp\CA8C.tmp.nikzbi.exe" | C:\Users\admin\AppData\Local\Temp\CA8C.tmp.nikzbi.exe | — | CA8C.tmp.nikzbi.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
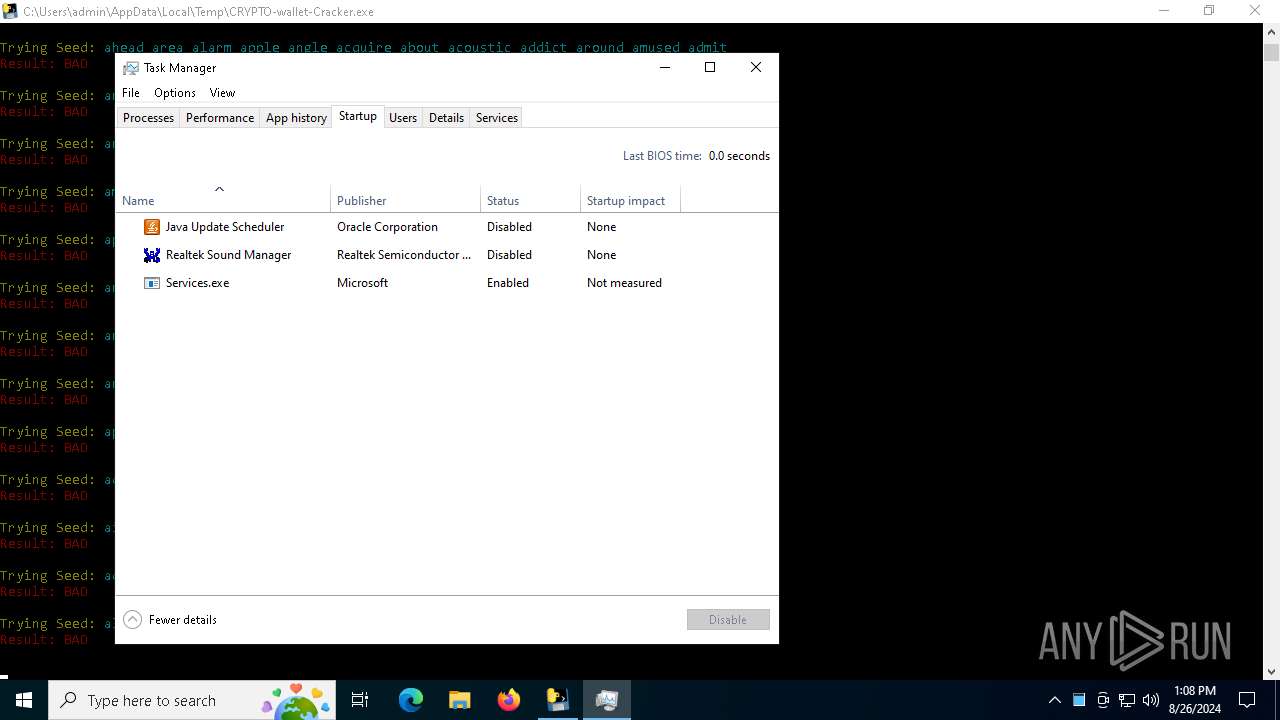
| 2820 | "C:\WINDOWS\system32\taskmgr.exe" /4 | C:\Windows\System32\Taskmgr.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Manager Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3424 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=1924 -parentBuildID 20240213221259 -prefsHandle 1852 -prefMapHandle 1844 -prefsLen 30580 -prefMapSize 245487 -appDir "C:\Program Files\Mozilla Firefox\browser" - {383175f2-6d9a-421f-9205-86950e518f64} 6580 "\\.\pipe\gecko-crash-server-pipe.6580" 1335dee3110 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 1 Version: 123.0 Modules
| |||||||||||||||
| 4092 | C:\WINDOWS\system32\WerFault.exe -u -p 6596 -s 824 | C:\Windows\System32\WerFault.exe | firefox.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4252 | C:\Users\admin\AppData\Local\Temp\temp_nik_zbi.exe | C:\Users\admin\AppData\Local\Temp\temp_nik_zbi.exe | CRYPTO-wallet-Cracker.exe | ||||||||||||
User: admin Company: Microsoft Integrity Level: MEDIUM Description: Services.exe Exit code: 0 Version: 1.2.0.1 Modules
| |||||||||||||||
Total events
37 139
Read events
35 046
Write events
2 083
Delete events
10
Modification events
| (PID) Process: | (4552) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\1\ApplicationViewManagement\W32:00000000000E01E4 |
| Operation: | write | Name: | VirtualDesktop |
Value: 1000000030304456033BCEE44DE41B4E8AEC331E84F566D2 | |||
| (PID) Process: | (4252) temp_nik_zbi.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Services |
Value: C:\Users\admin\AppData\Roaming\{2F33566DA0B91573532102}\{2F33566DA0B91573532102}.exe | |||
| (PID) Process: | (5128) svchost.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (5128) svchost.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (5128) svchost.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (5128) svchost.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (5128) svchost.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Service_Adobe |
Value: C:\Users\admin\AppData\Roaming\Adobe\Service_Adobe.exe | |||
| (PID) Process: | (5128) svchost.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Service_com.adobe.dunamis |
Value: C:\Users\admin\AppData\Roaming\com.adobe.dunamis\Service_com.adobe.dunamis.exe | |||
| (PID) Process: | (5128) svchost.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Service_FileZilla |
Value: C:\Users\admin\AppData\Roaming\FileZilla\Service_FileZilla.exe | |||
| (PID) Process: | (5128) svchost.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Service_Macromedia |
Value: C:\Users\admin\AppData\Roaming\Macromedia\Service_Macromedia.exe | |||
Executable files
120
Suspicious files
148
Text files
18
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 508 | CRYPTO-wallet-Cracker.exe | C:\Users\admin\AppData\Local\Temp\_MEI5082\_bz2.pyd | executable | |
MD5:3DC8AF67E6EE06AF9EEC52FE985A7633 | SHA256:C55821F5FDB0064C796B2C0B03B51971F073140BC210CBE6ED90387DB2BED929 | |||
| 4552 | explorer.exe | C:\Users\admin\AppData\Local\Microsoft\PenWorkspace\DiscoverCacheData.dat | binary | |
MD5:E49C56350AEDF784BFE00E444B879672 | SHA256:A8BD235303668981563DFB5AAE338CB802817C4060E2C199B7C84901D57B7E1E | |||
| 508 | CRYPTO-wallet-Cracker.exe | C:\Users\admin\AppData\Local\Temp\_MEI5082\api-ms-win-core-debug-l1-1-0.dll | executable | |
MD5:33BBECE432F8DA57F17BF2E396EBAA58 | SHA256:7CF0944901F7F7E0D0B9AD62753FC2FE380461B1CCE8CDC7E9C9867C980E3B0E | |||
| 508 | CRYPTO-wallet-Cracker.exe | C:\Users\admin\AppData\Local\Temp\_MEI5082\api-ms-win-core-errorhandling-l1-1-0.dll | executable | |
MD5:EB0978A9213E7F6FDD63B2967F02D999 | SHA256:AB25A1FE836FC68BCB199F1FE565C27D26AF0C390A38DA158E0D8815EFE1103E | |||
| 508 | CRYPTO-wallet-Cracker.exe | C:\Users\admin\AppData\Local\Temp\_MEI5082\api-ms-win-core-file-l2-1-0.dll | executable | |
MD5:BFFFA7117FD9B1622C66D949BAC3F1D7 | SHA256:1EA267A2E6284F17DD548C6F2285E19F7EDB15D6E737A55391140CE5CB95225E | |||
| 508 | CRYPTO-wallet-Cracker.exe | C:\Users\admin\AppData\Local\Temp\_MEI5082\api-ms-win-core-file-l1-2-0.dll | executable | |
MD5:1C58526D681EFE507DEB8F1935C75487 | SHA256:EF13DCE8F71173315DFC64AB839B033AB19A968EE15230E9D4D2C9D558EFEEE2 | |||
| 508 | CRYPTO-wallet-Cracker.exe | C:\Users\admin\AppData\Local\Temp\_MEI5082\api-ms-win-core-handle-l1-1-0.dll | executable | |
MD5:E89CDCD4D95CDA04E4ABBA8193A5B492 | SHA256:1A489E0606484BD71A0D9CB37A1DC6CA8437777B3D67BFC8C0075D0CC59E6238 | |||
| 508 | CRYPTO-wallet-Cracker.exe | C:\Users\admin\AppData\Local\Temp\_MEI5082\api-ms-win-core-heap-l1-1-0.dll | executable | |
MD5:ACCC640D1B06FB8552FE02F823126FF5 | SHA256:332BA469AE84AA72EC8CCE2B33781DB1AB81A42ECE5863F7A3CB5A990059594F | |||
| 508 | CRYPTO-wallet-Cracker.exe | C:\Users\admin\AppData\Local\Temp\_MEI5082\api-ms-win-core-interlocked-l1-1-0.dll | executable | |
MD5:C6024CC04201312F7688A021D25B056D | SHA256:8751D30DF554AF08EF42D2FAA0A71ABCF8C7D17CE9E9FF2EA68A4662603EC500 | |||
| 508 | CRYPTO-wallet-Cracker.exe | C:\Users\admin\AppData\Local\Temp\_MEI5082\api-ms-win-core-localization-l1-2-0.dll | executable | |
MD5:724223109E49CB01D61D63A8BE926B8F | SHA256:4E975F618DF01A492AE433DFF0DD713774D47568E44C377CEEF9E5B34AAD1210 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
35
TCP/UDP connections
66
DNS requests
73
Threats
18
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5160 | CRYPTO-wallet-Cracker.exe | GET | 200 | 176.111.174.140:80 | http://176.111.174.140/nuke.exe | RU | executable | 297 Kb | suspicious |
5128 | svchost.exe | GET | 200 | 176.111.174.140:80 | http://176.111.174.140/vvTBswN.php | RU | executable | 297 Kb | suspicious |
5128 | svchost.exe | GET | 200 | 176.111.174.140:80 | http://176.111.174.140/api/update.pack | RU | executable | 265 Kb | suspicious |
5128 | svchost.exe | GET | 200 | 176.111.174.140:80 | http://176.111.174.140/api/update2.pack | RU | executable | 86.5 Kb | suspicious |
4552 | explorer.exe | POST | 200 | 176.111.174.140:80 | http://176.111.174.140/api.php?{2F33566DA0B91573532102} | RU | text | 345 b | unknown |
4552 | explorer.exe | POST | 200 | 176.111.174.140:80 | http://176.111.174.140/api.php?{2F33566DA0B91573532102} | RU | binary | 37 b | unknown |
4552 | explorer.exe | POST | 200 | 176.111.174.140:80 | http://176.111.174.140/api.php?{2F33566DA0B91573532102} | RU | text | 40 b | suspicious |
2024 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
4552 | explorer.exe | GET | 200 | 176.111.174.140:80 | http://176.111.174.140/nikzbi.exe | RU | executable | 5.57 Mb | suspicious |
6580 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | US | text | 90 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6192 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2120 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3260 | svchost.exe | 40.113.110.67:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5160 | CRYPTO-wallet-Cracker.exe | 176.111.174.140:80 | — | Chang Way Technologies Co. Limited | RU | malicious |
5128 | svchost.exe | 176.111.174.140:80 | — | Chang Way Technologies Co. Limited | RU | malicious |
4552 | explorer.exe | 176.111.174.140:80 | — | Chang Way Technologies Co. Limited | RU | malicious |
2024 | svchost.exe | 20.190.159.75:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2024 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
contile.services.mozilla.com |
| whitelisted |
spocs.getpocket.com |
| whitelisted |
example.org |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5160 | CRYPTO-wallet-Cracker.exe | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
5160 | CRYPTO-wallet-Cracker.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 30 |
5160 | CRYPTO-wallet-Cracker.exe | Misc activity | ET INFO Packed Executable Download |
5160 | CRYPTO-wallet-Cracker.exe | Attempted Information Leak | ET POLICY Python-urllib/ Suspicious User Agent |
5160 | CRYPTO-wallet-Cracker.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
5160 | CRYPTO-wallet-Cracker.exe | Potentially Bad Traffic | ET HUNTING SUSPICIOUS Dotted Quad Host MZ Response |
5128 | svchost.exe | A suspicious filename was detected | ET HUNTING Terse Named Filename EXE Download - Possibly Hostile |
5128 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
5128 | svchost.exe | Potentially Bad Traffic | ET HUNTING SUSPICIOUS Dotted Quad Host MZ Response |
5128 | svchost.exe | Misc activity | ET INFO EXE - Served Inline HTTP |