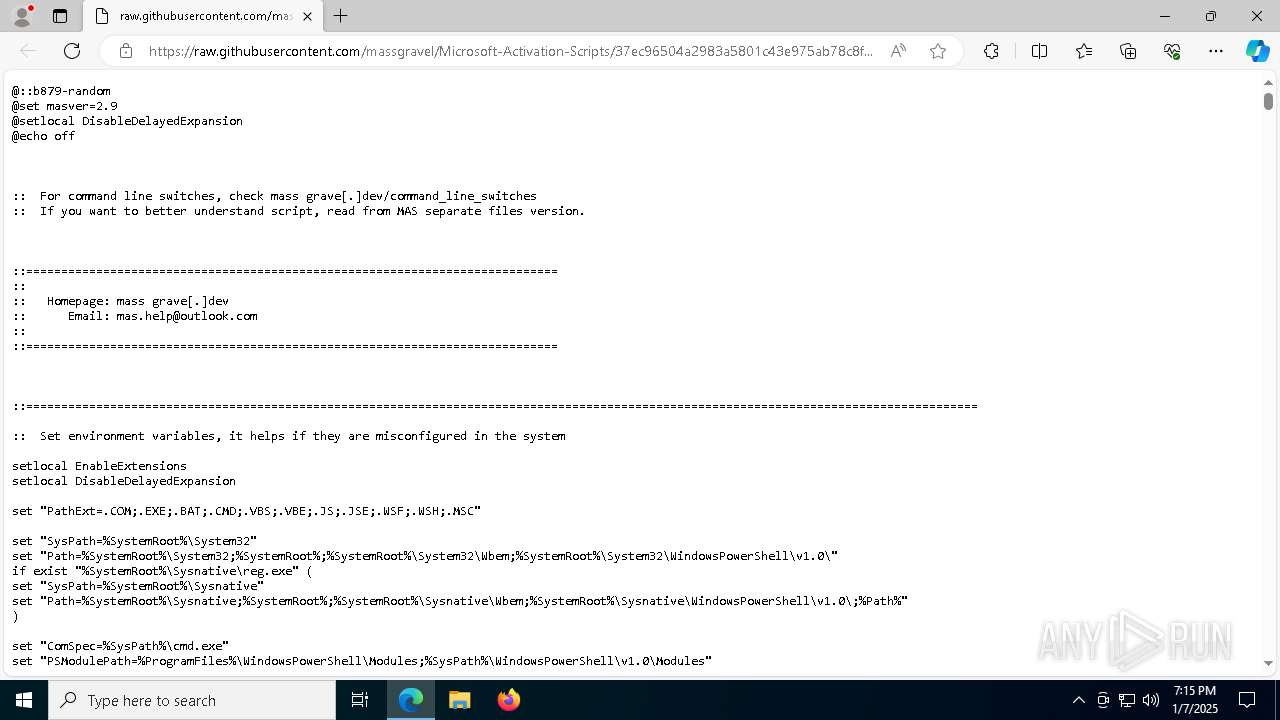
| URL: | https://raw.githubusercontent.com/massgravel/Microsoft-Activation-Scripts/37ec96504a2983a5801c43e975ab78c8f9315d2a/MAS/All-In-One-Version-KL/MAS_AIO.cmd |
| Full analysis: | https://app.any.run/tasks/8cbe3c2d-44bd-4264-9d76-8362c2be69e2 |
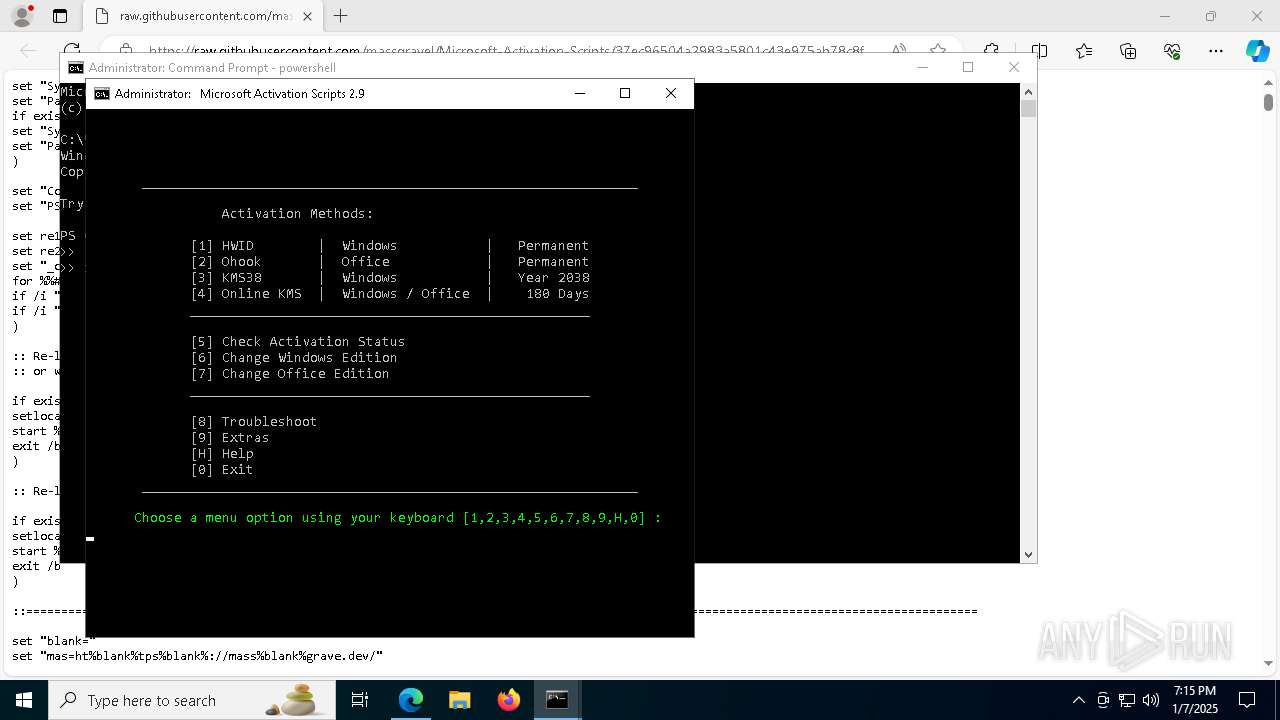
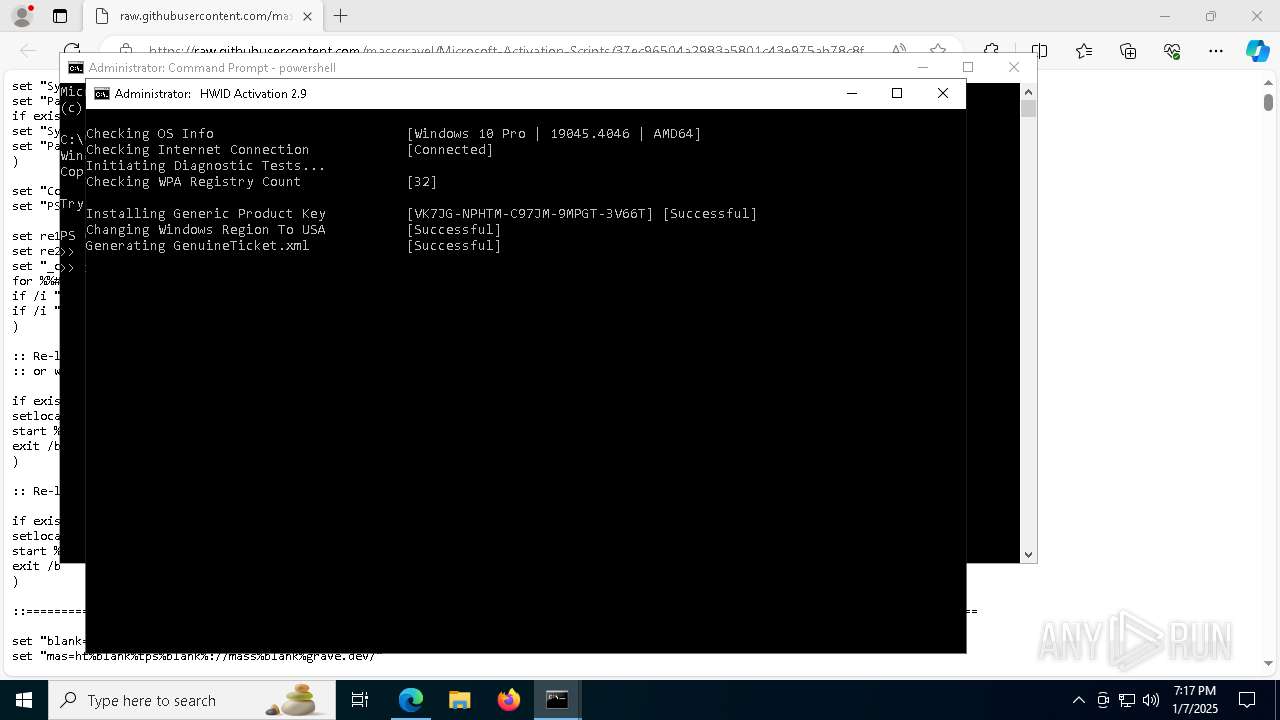
| Verdict: | Malicious activity |
| Threats: | A loader is malicious software that infiltrates devices to deliver malicious payloads. This malware is capable of infecting victims’ computers, analyzing their system information, and installing other types of threats, such as trojans or stealers. Criminals usually deliver loaders through phishing emails and links by relying on social engineering to trick users into downloading and running their executables. Loaders employ advanced evasion and persistence tactics to avoid detection. |
| Analysis date: | January 07, 2025, 19:14:57 |
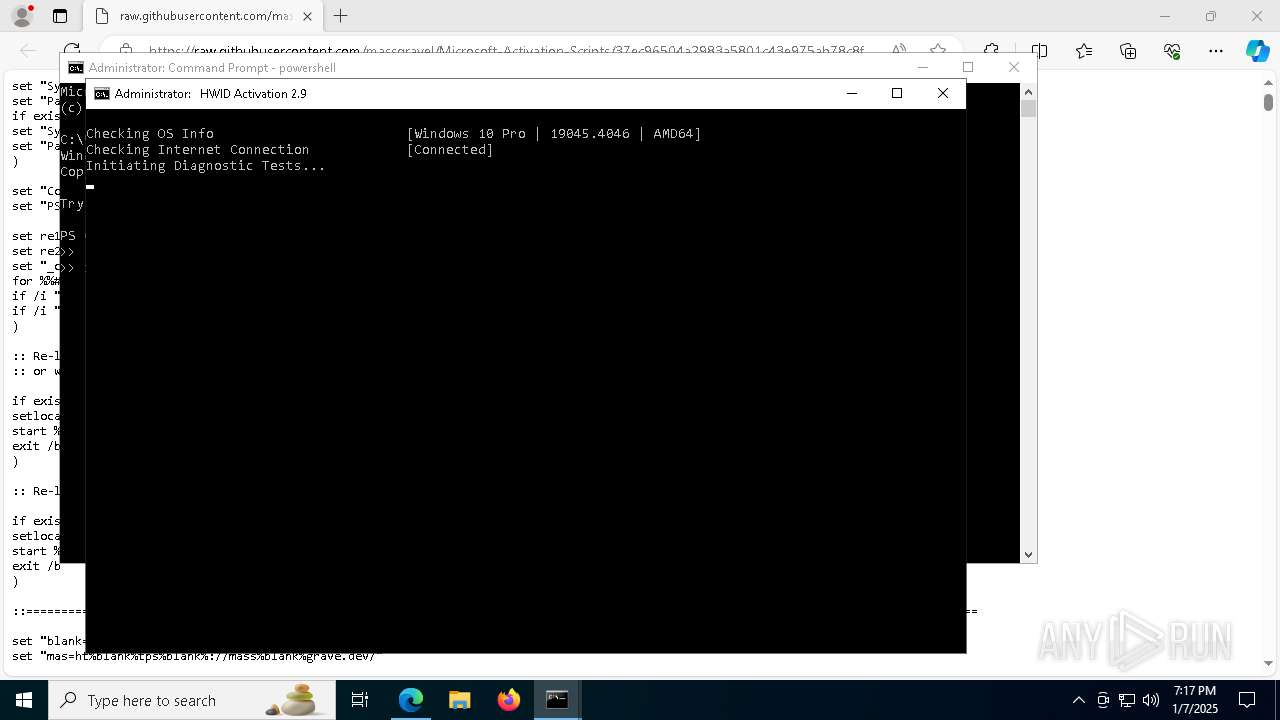
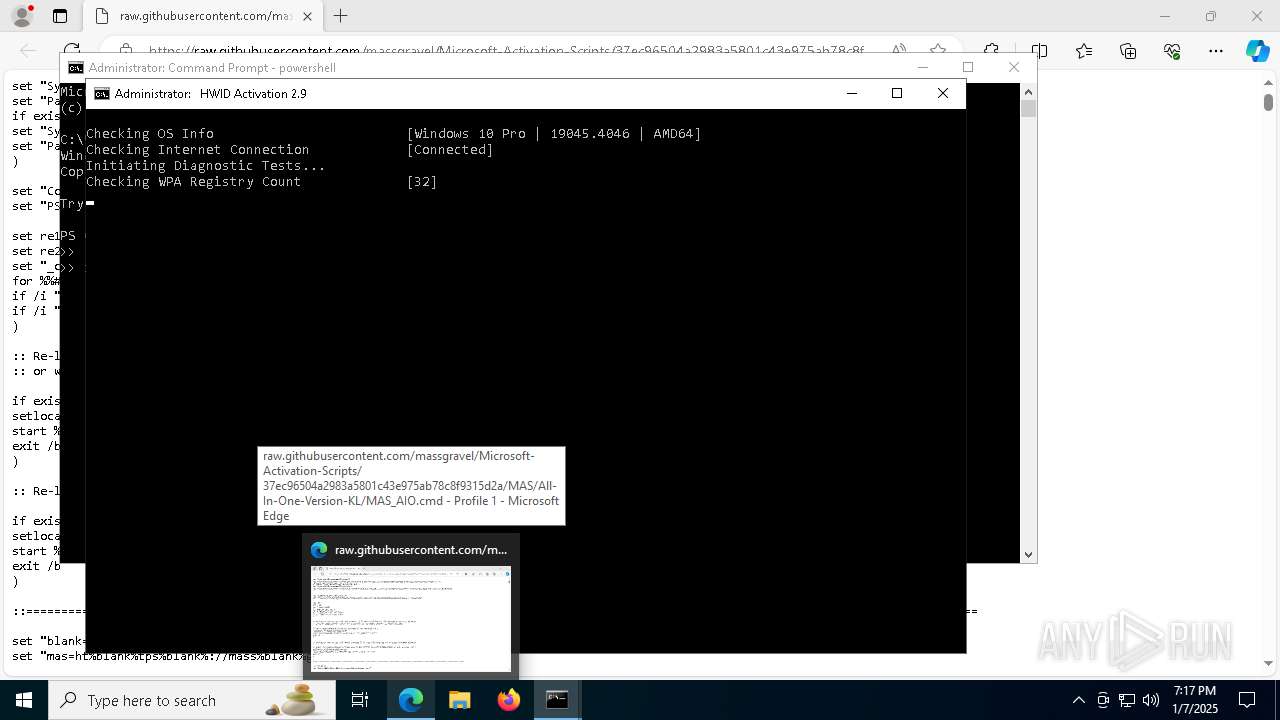
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 23A571C2CE09FE11D11CE4973FA05824 |
| SHA1: | EB21FC1EF33F894615A9A4073F39CED1740236AF |
| SHA256: | 86A7819467EEFE8E7CA32B53A60E19B3666C2E2755BBF2B62CE6BE83F1978C45 |
| SSDEEP: | 3:N8SGfALtGTzKoHXuukGR3RLLLGXUezQPUE35J6PXj8tIqLAOAh9wln:2FMGnKzukGv/LGXUezQM4J6Q0vDG |
MALICIOUS
No malicious indicators.SUSPICIOUS
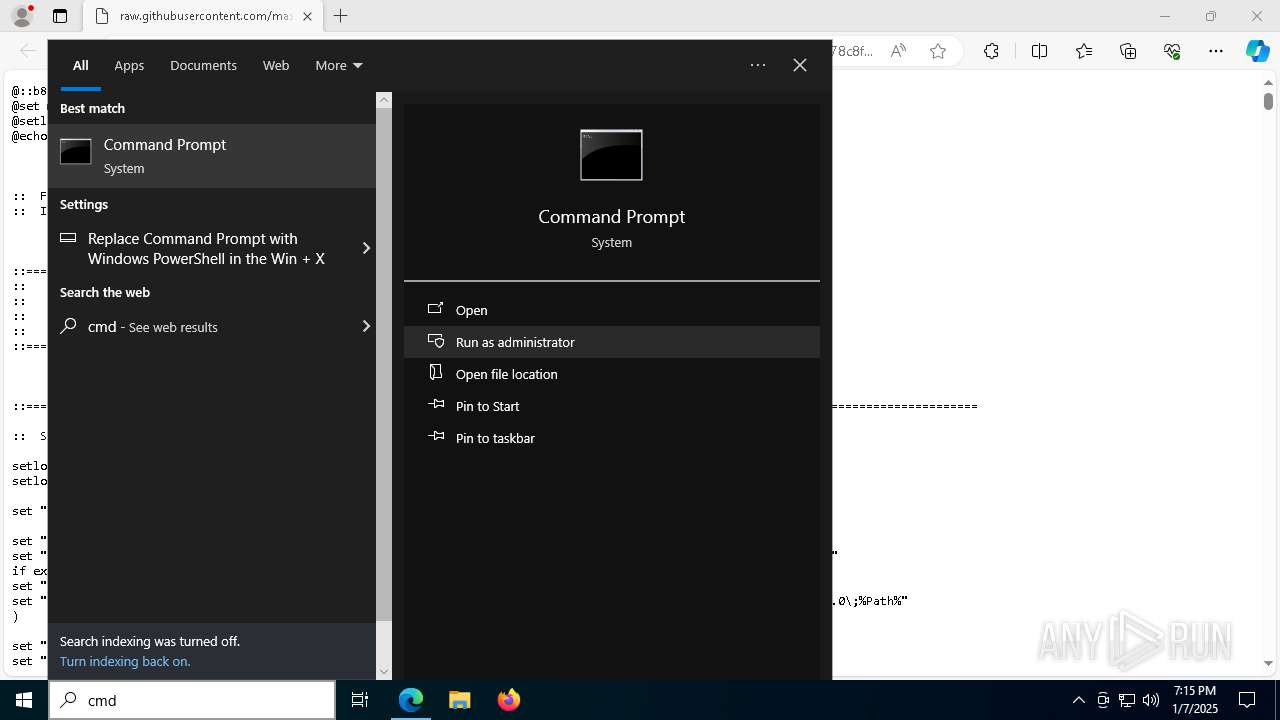
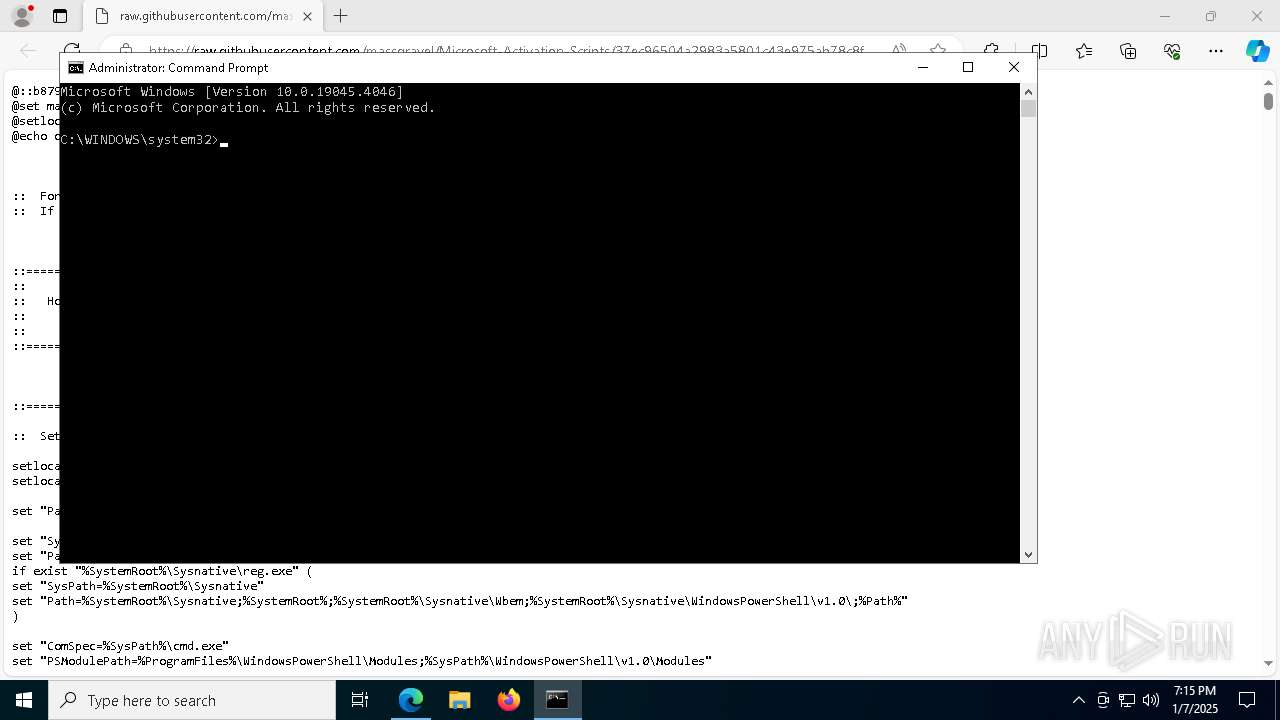
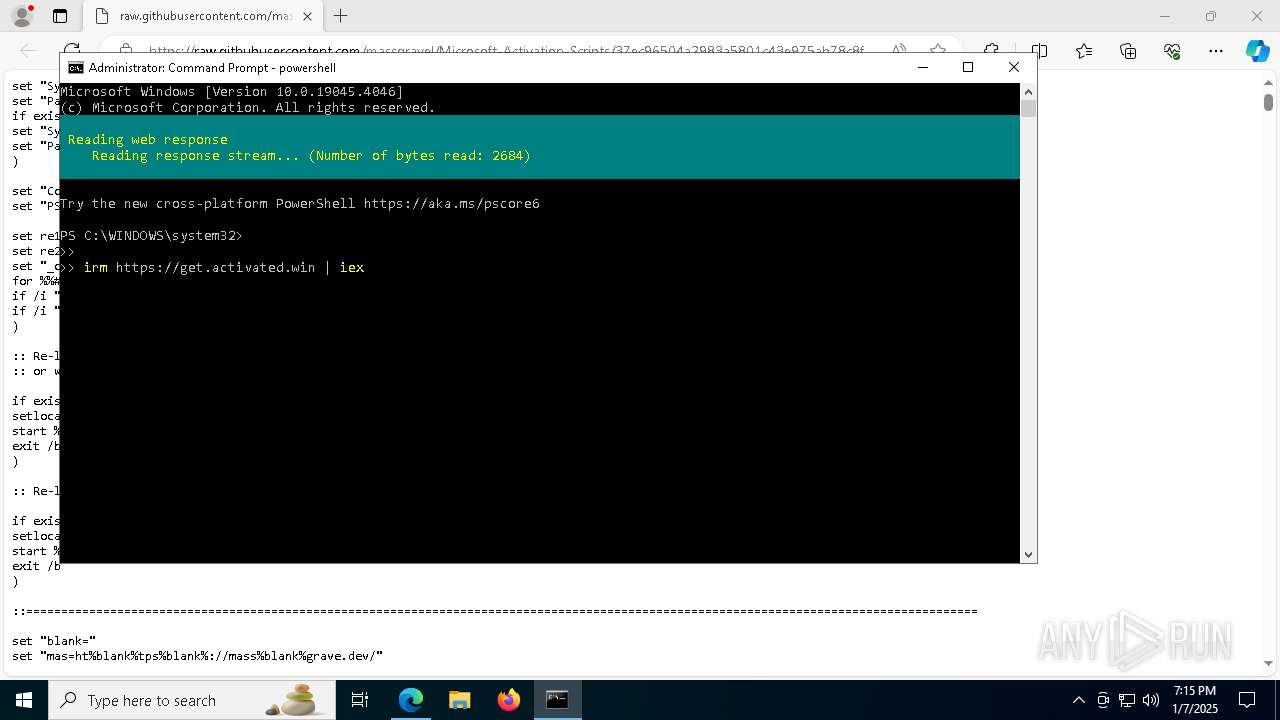
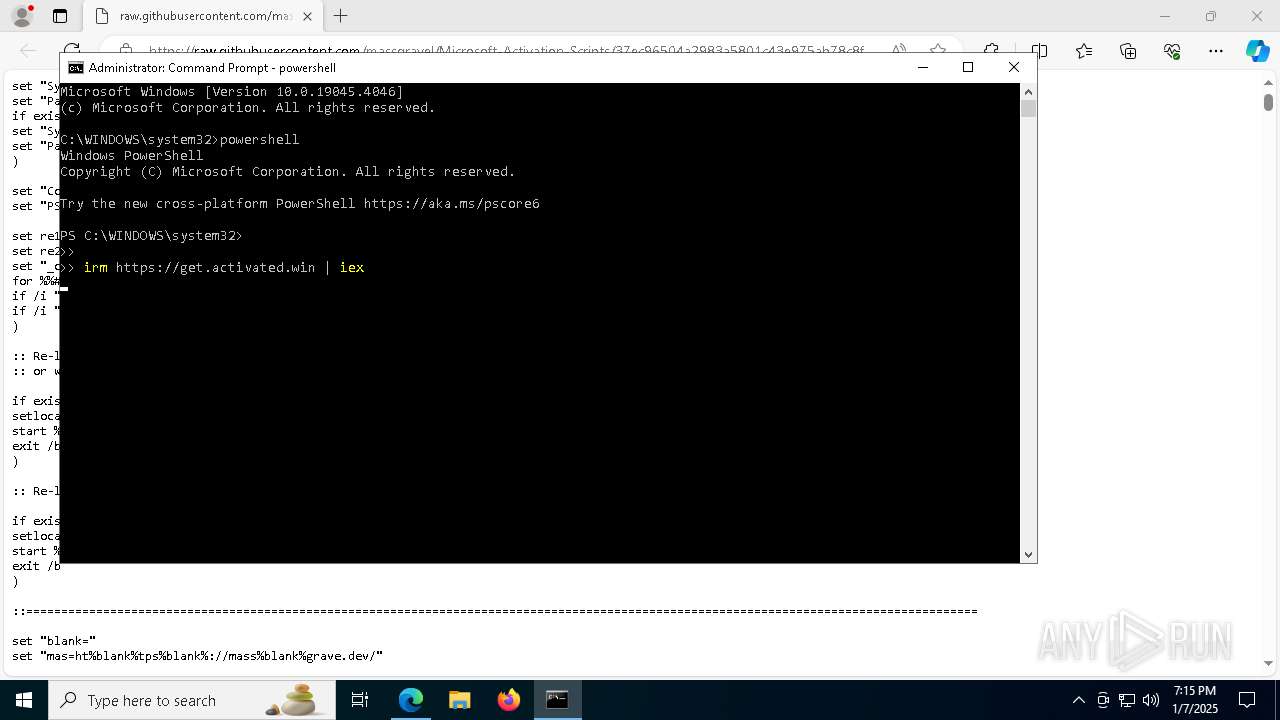
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 6004)
- cmd.exe (PID: 8072)
- cmd.exe (PID: 6376)
- cmd.exe (PID: 7740)
- cmd.exe (PID: 5556)
- cmd.exe (PID: 6252)
- cmd.exe (PID: 7916)
- powershell.exe (PID: 7964)
- cmd.exe (PID: 6464)
- cmd.exe (PID: 7868)
- powershell.exe (PID: 1156)
- cmd.exe (PID: 7244)
- cmd.exe (PID: 5880)
- powershell.exe (PID: 5592)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 7228)
Gets content of a file (POWERSHELL)
- powershell.exe (PID: 7228)
- powershell.exe (PID: 8108)
- powershell.exe (PID: 7832)
- powershell.exe (PID: 7848)
- powershell.exe (PID: 7816)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 7228)
- powershell.exe (PID: 7832)
- powershell.exe (PID: 8108)
- powershell.exe (PID: 7848)
- powershell.exe (PID: 7816)
- powershell.exe (PID: 1304)
Creates new GUID (POWERSHELL)
- powershell.exe (PID: 7228)
Starts CMD.EXE for commands execution
- powershell.exe (PID: 7228)
- cmd.exe (PID: 7740)
- cmd.exe (PID: 7972)
- cmd.exe (PID: 5556)
- cmd.exe (PID: 7648)
- powershell.exe (PID: 2436)
Executing commands from ".cmd" file
- powershell.exe (PID: 7228)
- cmd.exe (PID: 7740)
- powershell.exe (PID: 2436)
- cmd.exe (PID: 5556)
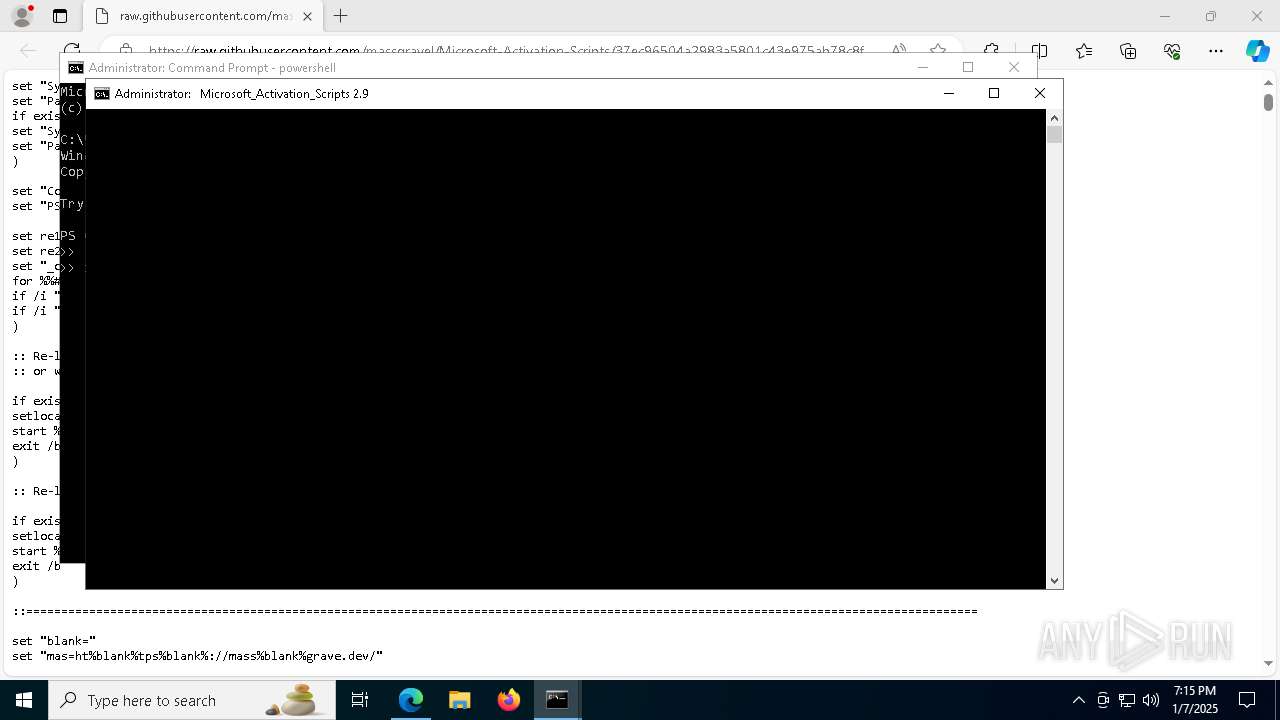
Application launched itself
- cmd.exe (PID: 7740)
- cmd.exe (PID: 7972)
- cmd.exe (PID: 5556)
- cmd.exe (PID: 7648)
- powershell.exe (PID: 7964)
- powershell.exe (PID: 1156)
- ClipUp.exe (PID: 7120)
- powershell.exe (PID: 5592)
Windows service management via SC.EXE
- sc.exe (PID: 7800)
- sc.exe (PID: 4668)
- sc.exe (PID: 7724)
- sc.exe (PID: 7944)
- sc.exe (PID: 8008)
- sc.exe (PID: 6012)
- sc.exe (PID: 2972)
- sc.exe (PID: 3832)
- sc.exe (PID: 8168)
- sc.exe (PID: 8184)
- sc.exe (PID: 5308)
- sc.exe (PID: 3172)
- sc.exe (PID: 6948)
- sc.exe (PID: 2124)
- sc.exe (PID: 6076)
- sc.exe (PID: 7860)
- sc.exe (PID: 8140)
- sc.exe (PID: 4992)
- sc.exe (PID: 7656)
- sc.exe (PID: 7660)
- sc.exe (PID: 6248)
- sc.exe (PID: 7776)
- sc.exe (PID: 7552)
- sc.exe (PID: 5028)
- sc.exe (PID: 7596)
- sc.exe (PID: 7372)
- sc.exe (PID: 7400)
- sc.exe (PID: 7900)
- sc.exe (PID: 3224)
- sc.exe (PID: 7848)
- sc.exe (PID: 7912)
- sc.exe (PID: 4548)
- sc.exe (PID: 7996)
- sc.exe (PID: 7896)
- sc.exe (PID: 4244)
- sc.exe (PID: 7444)
Starts SC.EXE for service management
- cmd.exe (PID: 7740)
- cmd.exe (PID: 5556)
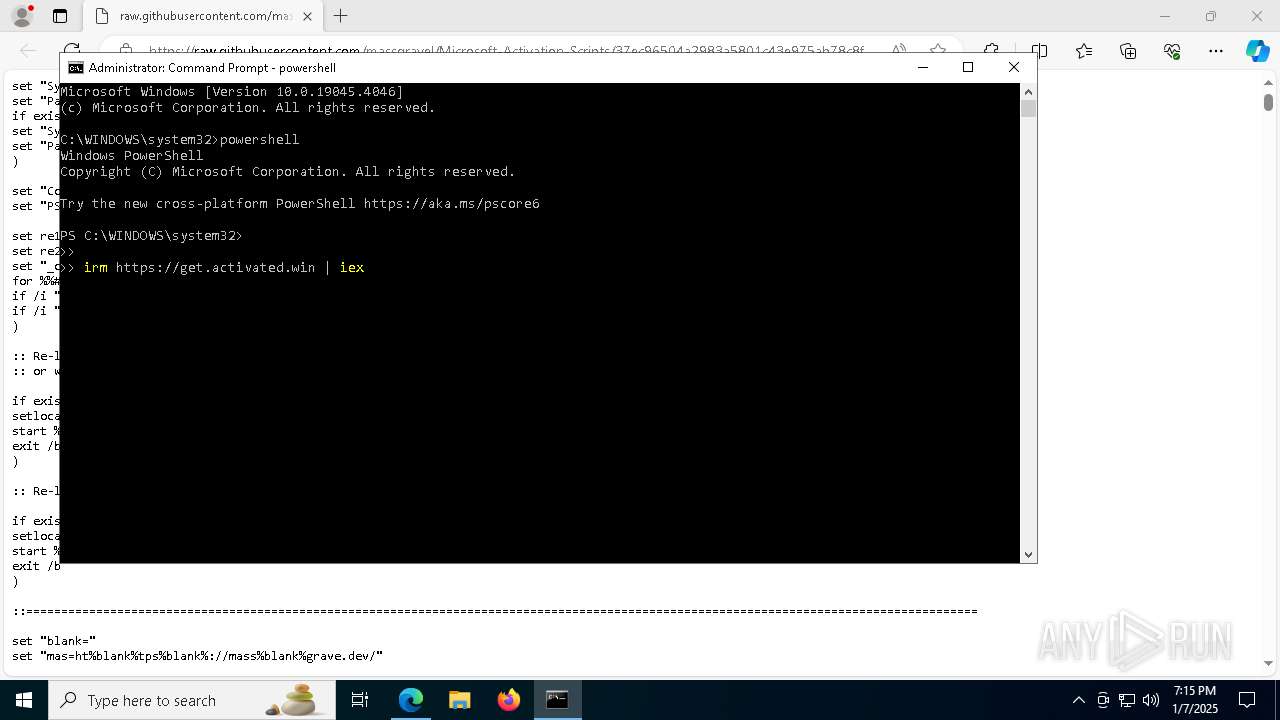
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 8072)
- cmd.exe (PID: 6376)
- cmd.exe (PID: 5556)
- cmd.exe (PID: 6464)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 8072)
- cmd.exe (PID: 6376)
- cmd.exe (PID: 5556)
- cmd.exe (PID: 6464)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 7740)
- cmd.exe (PID: 5556)
Detects reflection assembly loader (YARA)
- powershell.exe (PID: 7228)
- powershell.exe (PID: 2436)
Uses WMIC.EXE to obtain computer system information
- cmd.exe (PID: 2496)
- cmd.exe (PID: 5556)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 5556)
Hides command output
- cmd.exe (PID: 7648)
- cmd.exe (PID: 7640)
- cmd.exe (PID: 6464)
- cmd.exe (PID: 3736)
- cmd.exe (PID: 8152)
- cmd.exe (PID: 7392)
- cmd.exe (PID: 7896)
- cmd.exe (PID: 8008)
- cmd.exe (PID: 5880)
- cmd.exe (PID: 3864)
- cmd.exe (PID: 7244)
Uses WMIC.EXE to obtain operating system information
- cmd.exe (PID: 7648)
The process hides Powershell's copyright startup banner
- powershell.exe (PID: 7964)
- powershell.exe (PID: 1156)
- powershell.exe (PID: 5592)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 5556)
- cmd.exe (PID: 8152)
- cmd.exe (PID: 7392)
- cmd.exe (PID: 3864)
The process bypasses the loading of PowerShell profile settings
- powershell.exe (PID: 7964)
- powershell.exe (PID: 1156)
- powershell.exe (PID: 5592)
Uses WMIC.EXE to obtain service application data
- cmd.exe (PID: 5556)
INFO
Checks supported languages
- identity_helper.exe (PID: 3128)
- mode.com (PID: 1556)
Application launched itself
- msedge.exe (PID: 4052)
Reads the computer name
- identity_helper.exe (PID: 3128)
Reads security settings of Internet Explorer
- powershell.exe (PID: 7228)
- WMIC.exe (PID: 4668)
- WMIC.exe (PID: 7352)
- WMIC.exe (PID: 5728)
- WMIC.exe (PID: 5208)
- WMIC.exe (PID: 5096)
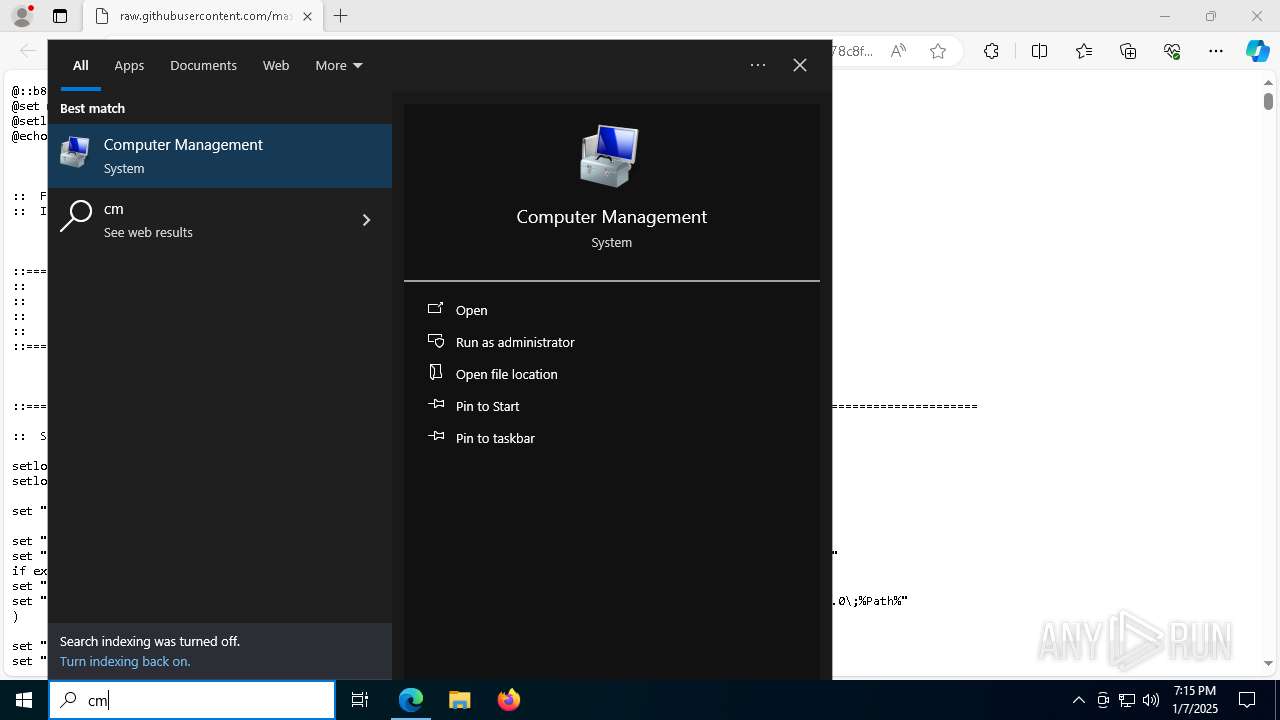
Manual execution by a user
- cmd.exe (PID: 6004)
Reads Environment values
- identity_helper.exe (PID: 3128)
Creates files or folders in the user directory
- powershell.exe (PID: 7228)
Checks current location (POWERSHELL)
- powershell.exe (PID: 7228)
Disables trace logs
- powershell.exe (PID: 7228)
Create files in a temporary directory
- powershell.exe (PID: 7228)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 7228)
- powershell.exe (PID: 8108)
- powershell.exe (PID: 7832)
- powershell.exe (PID: 7848)
- powershell.exe (PID: 7816)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 7228)
- powershell.exe (PID: 8108)
- powershell.exe (PID: 7832)
- powershell.exe (PID: 7848)
- powershell.exe (PID: 7816)
Gets a random number, or selects objects randomly from a collection (POWERSHELL)
- powershell.exe (PID: 7228)
- powershell.exe (PID: 8108)
- powershell.exe (PID: 7832)
- powershell.exe (PID: 7848)
- powershell.exe (PID: 7816)
Reads the software policy settings
- powershell.exe (PID: 7228)
The process uses the downloaded file
- powershell.exe (PID: 7228)
Checks operating system version
- cmd.exe (PID: 7740)
- cmd.exe (PID: 5556)
Starts MODE.COM to configure console settings
- mode.com (PID: 8096)
- mode.com (PID: 1556)
Executable content was dropped or overwritten
- msedge.exe (PID: 7840)
The sample compiled with english language support
- msedge.exe (PID: 7840)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 7384)
Creates files in the program directory
- cmd.exe (PID: 5556)
- ClipUp.exe (PID: 5872)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
452
Monitored processes
314
Malicious processes
5
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.Extractor --lang=en-US --service-sandbox-type=entity_extraction --onnx-enabled-for-ee --no-appcompat-clear --mojo-platform-channel-handle=5216 --field-trial-handle=2300,i,573171969310311341,11254640645279915988,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 236 | reg query HKLM\SYSTEM\CurrentControlSet\Services\wlidsvc /v ObjectName | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 308 | reg query "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\ClipSVC\Volatile\PersistedSystemState" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 420 | choice /C:10 /N /M "> [1] Activate Anyway [0] Go back : " | C:\Windows\System32\choice.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Offers the user a choice Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 444 | reg query HKLM\SYSTEM\CurrentControlSet\Services\sppsvc /v ImagePath | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 768 | reg query "HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Setup\State" /v ImageState | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 836 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6432 --field-trial-handle=2300,i,573171969310311341,11254640645279915988,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 836 | reg query HKLM\SYSTEM\CurrentControlSet\Services\sppsvc /v Description | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 848 | reg query HKLM\SYSTEM\CurrentControlSet\Services\sppsvc /v ObjectName | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 848 | reg query "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\SppExtComObj.exe" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
132 592
Read events
132 572
Write events
18
Delete events
2
Modification events
| (PID) Process: | (4052) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (4052) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (4052) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (4052) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (4052) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 6CAE63D8B8892F00 | |||
| (PID) Process: | (4052) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: DC7777D8B8892F00 | |||
| (PID) Process: | (4052) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459456 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {01029764-25ED-4E14-A2B3-A748B21E954F} | |||
| (PID) Process: | (4052) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459456 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {31CD7708-8CF6-41C4-B02F-4B937F427083} | |||
| (PID) Process: | (4052) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 6D4EC4D8B8892F00 | |||
| (PID) Process: | (4052) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
Executable files
9
Suspicious files
509
Text files
154
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4052 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF13574b.TMP | — | |
MD5:— | SHA256:— | |||
| 4052 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4052 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF13575a.TMP | — | |
MD5:— | SHA256:— | |||
| 4052 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF13575a.TMP | — | |
MD5:— | SHA256:— | |||
| 4052 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4052 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4052 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF13575a.TMP | — | |
MD5:— | SHA256:— | |||
| 4052 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4052 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF13575a.TMP | — | |
MD5:— | SHA256:— | |||
| 4052 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
60
TCP/UDP connections
76
DNS requests
75
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2324 | svchost.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2324 | svchost.exe | GET | 200 | 184.30.230.103:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 184.30.230.103:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.230.103:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
432 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9cf951df-e7db-4d00-b0fc-02131f5ca303?P1=1736821430&P2=404&P3=2&P4=EJ05ELsNKPT44i%2fYKPmhA85%2fZxVts10hqKrZcm1cBKa%2fliHINX76byi5RUGylAB0CiWayH%2fFNpEmyl1L%2f70CRg%3d%3d | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
5432 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2324 | svchost.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 184.30.230.103:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
2324 | svchost.exe | 184.30.230.103:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
— | — | 184.30.230.103:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
5064 | SearchApp.exe | 2.23.227.208:443 | www.bing.com | Ooredoo Q.S.C. | QA | whitelisted |
5064 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
raw.githubusercontent.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6456 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
6456 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |