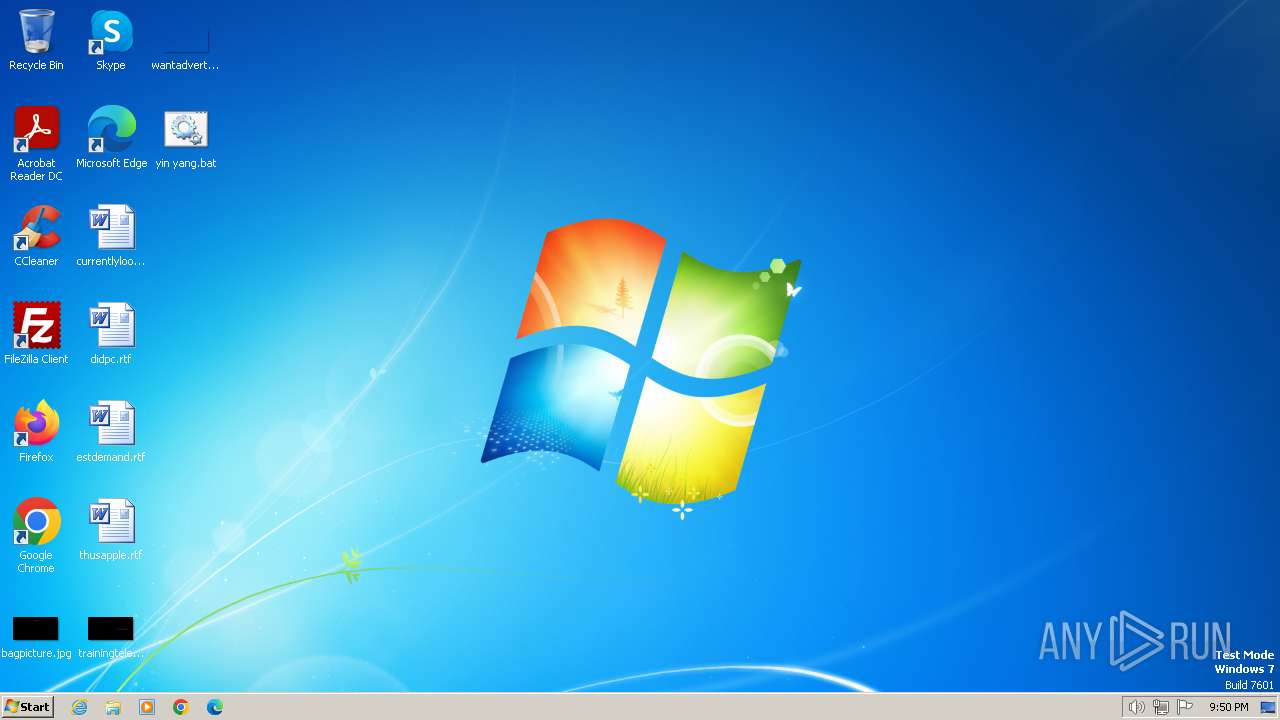
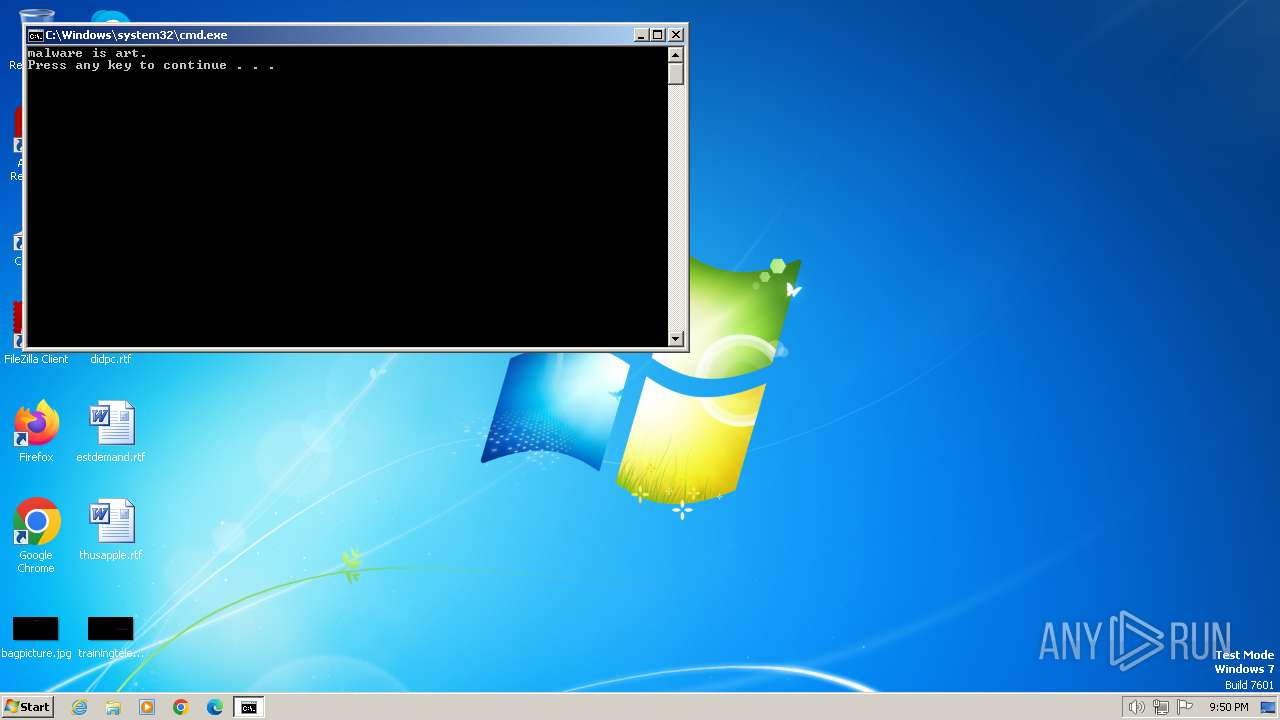
| File name: | yin yang.bat |
| Full analysis: | https://app.any.run/tasks/3e87fe9e-095c-44c8-a3f3-7900273b5915 |
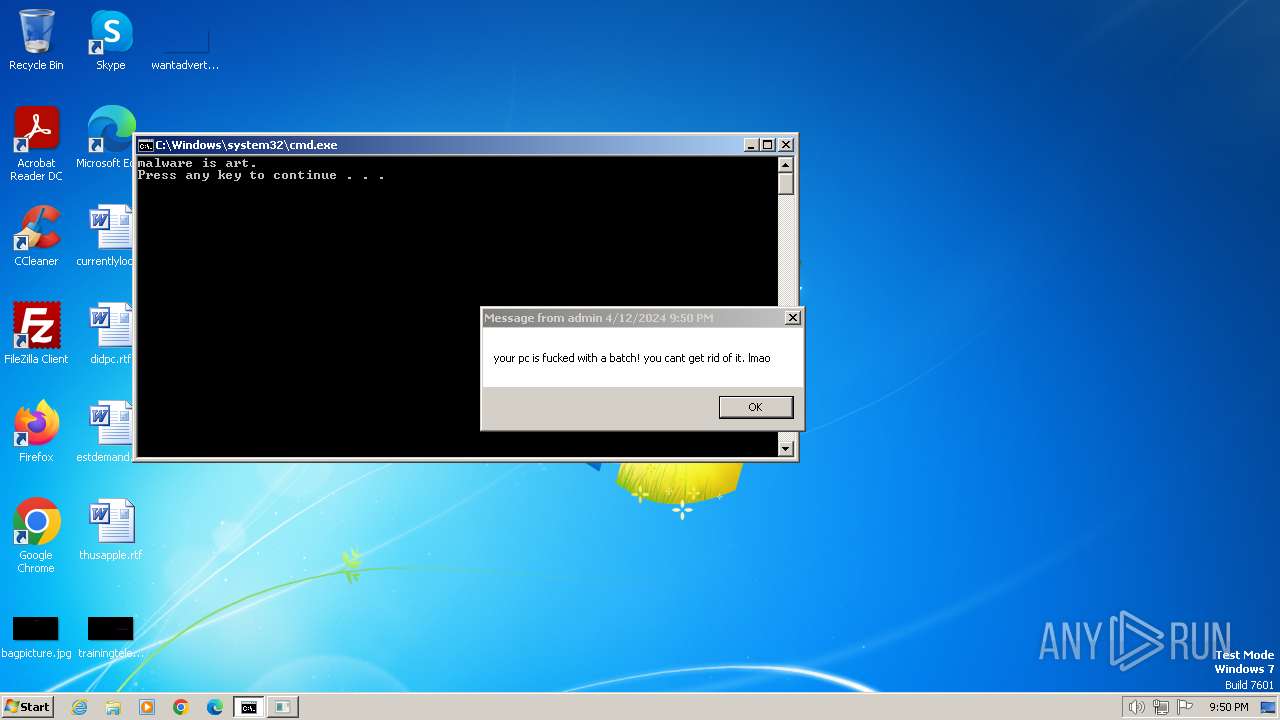
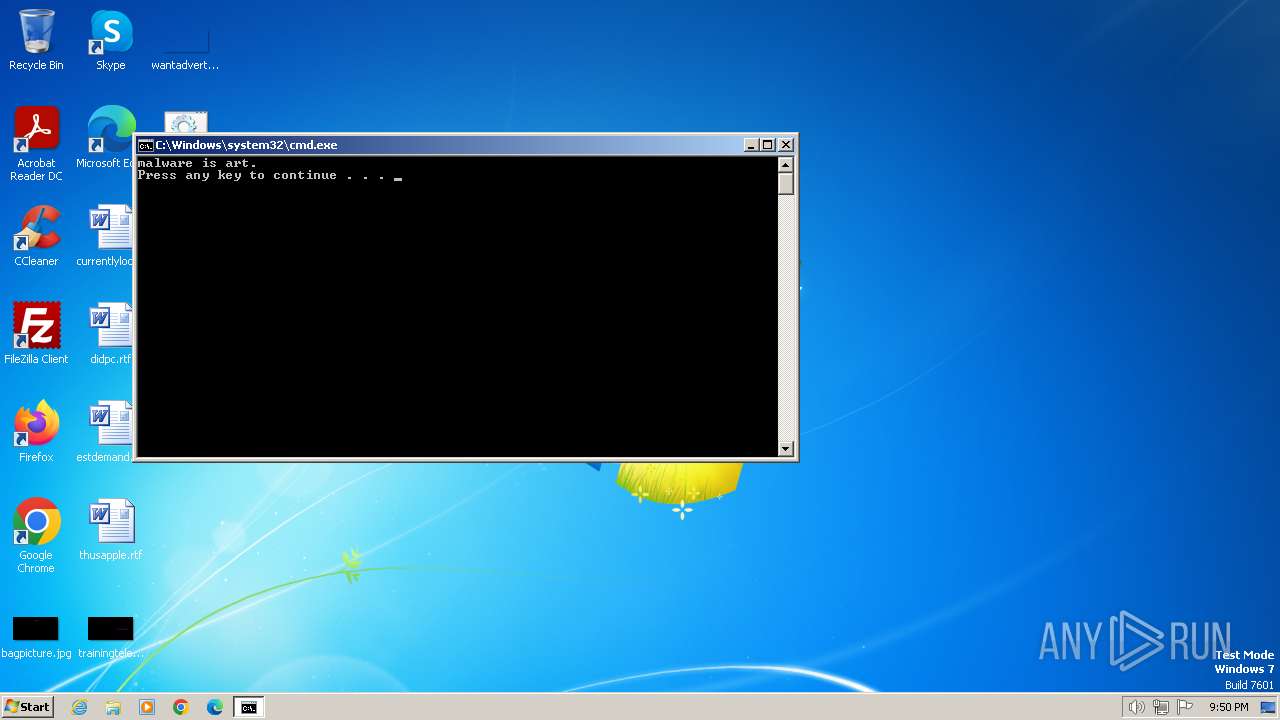
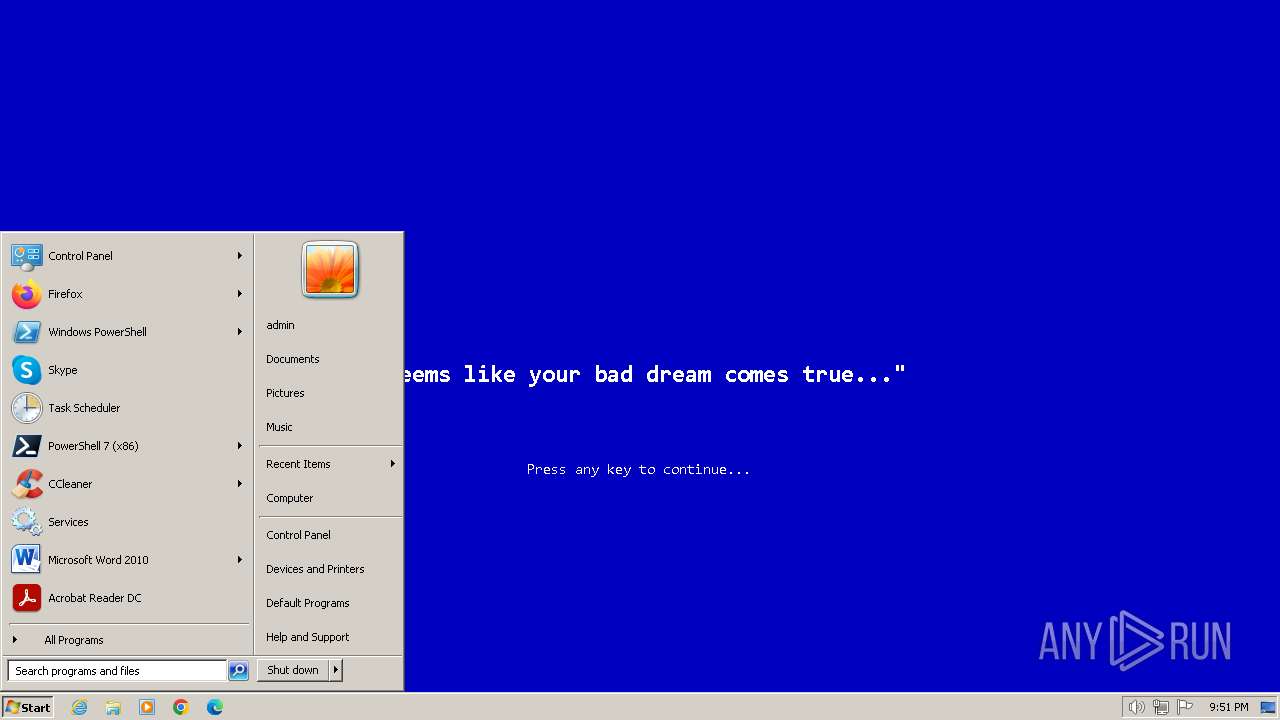
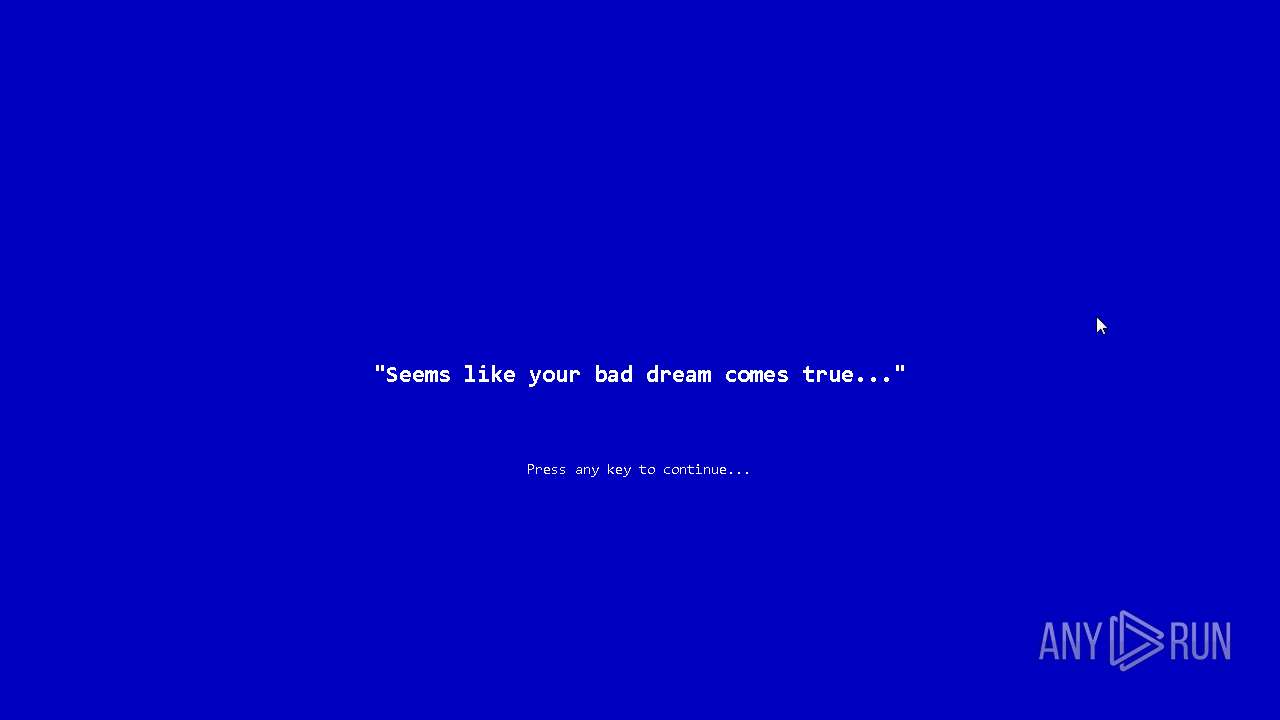
| Verdict: | Malicious activity |
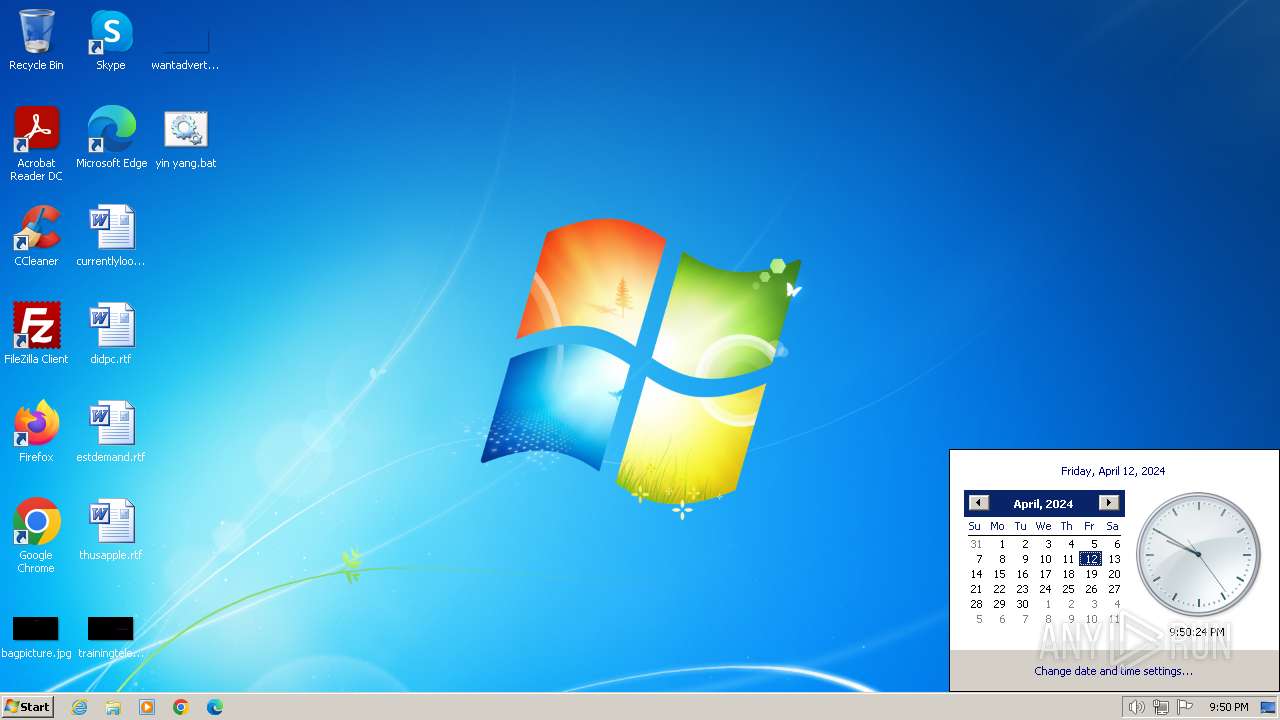
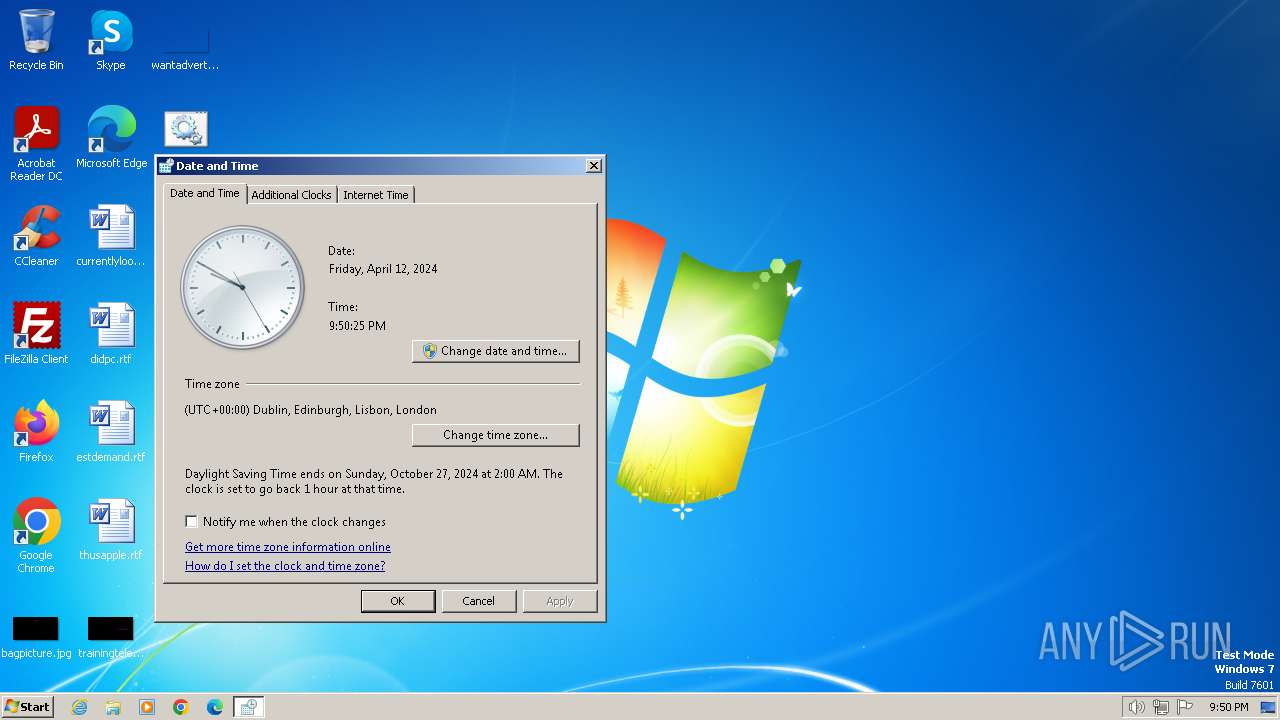
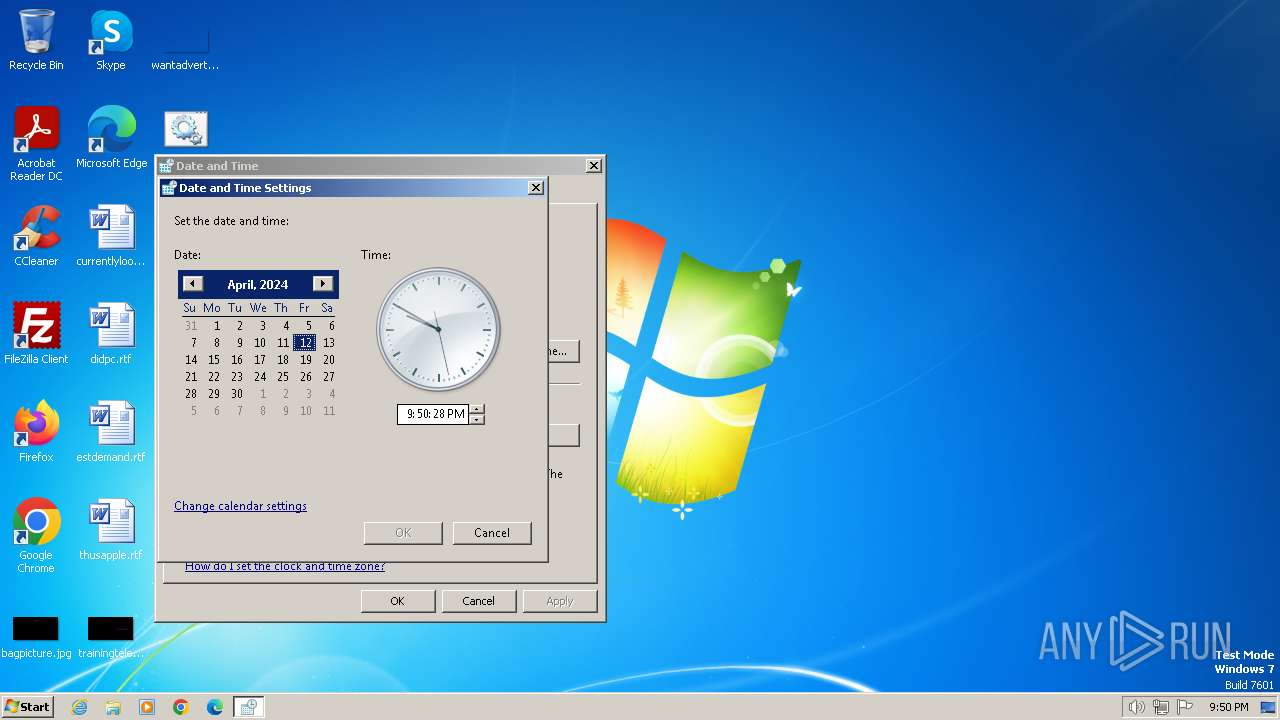
| Analysis date: | April 12, 2024, 20:50:04 |
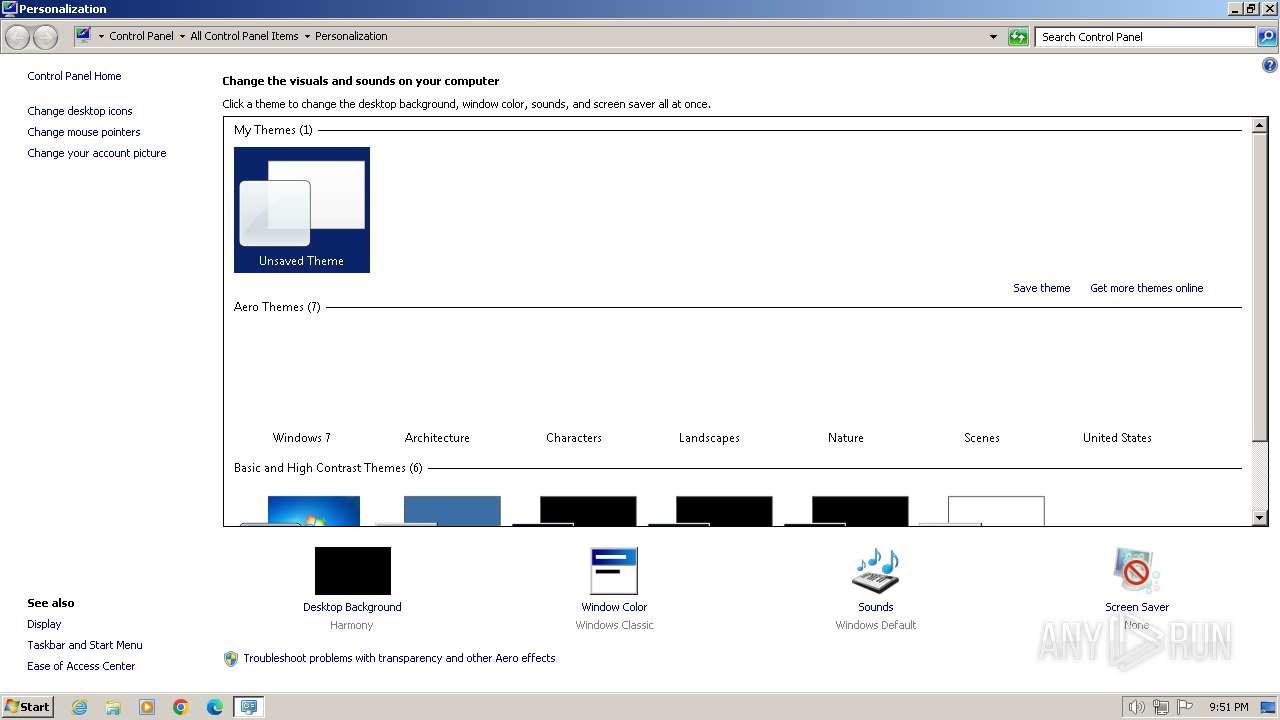
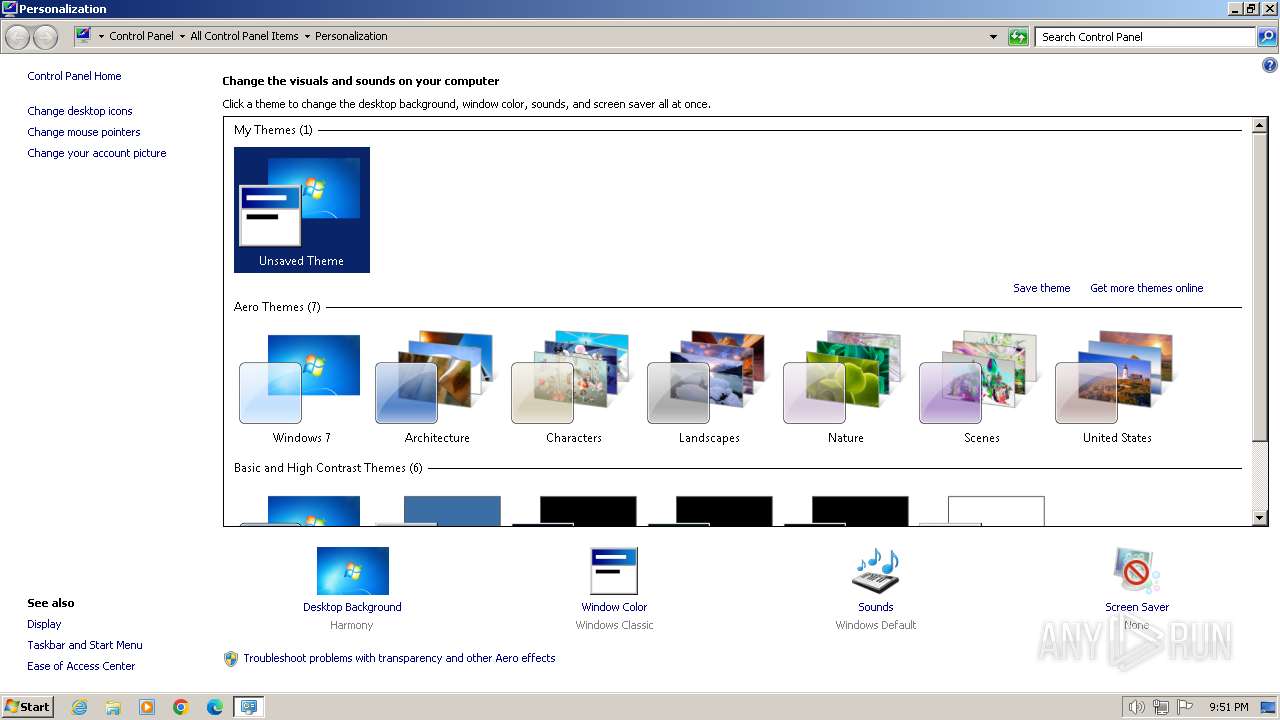
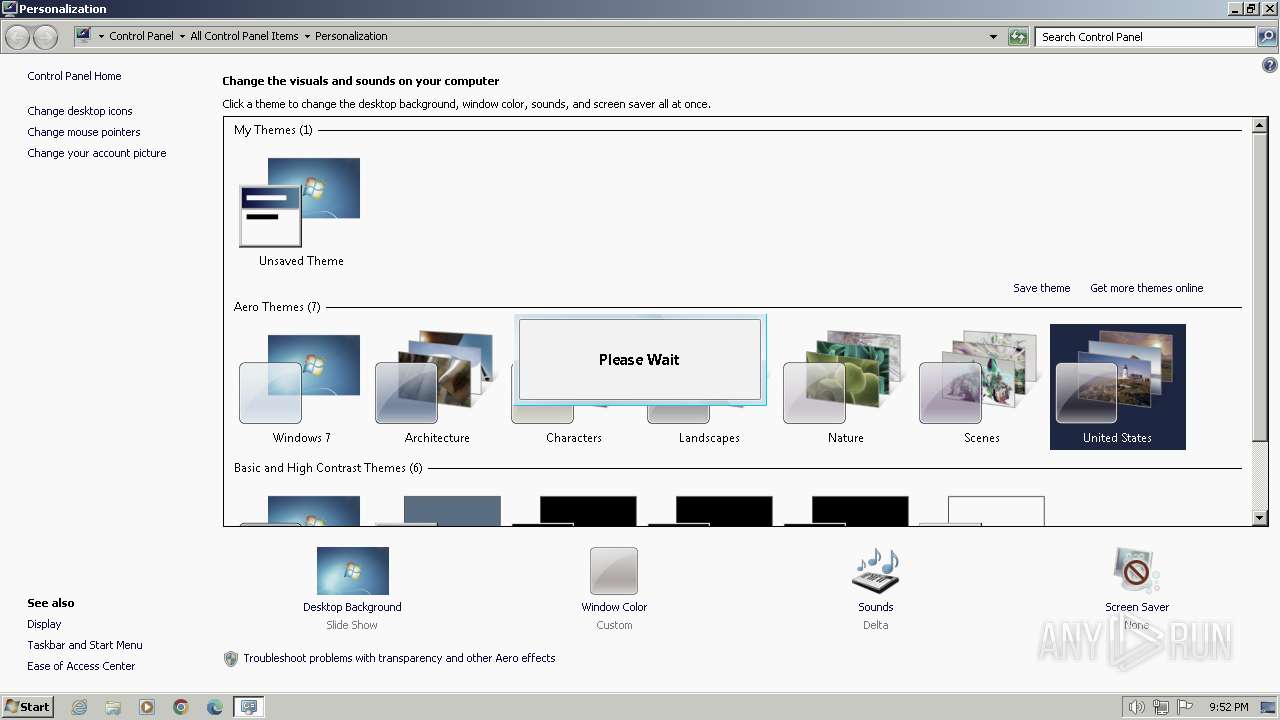
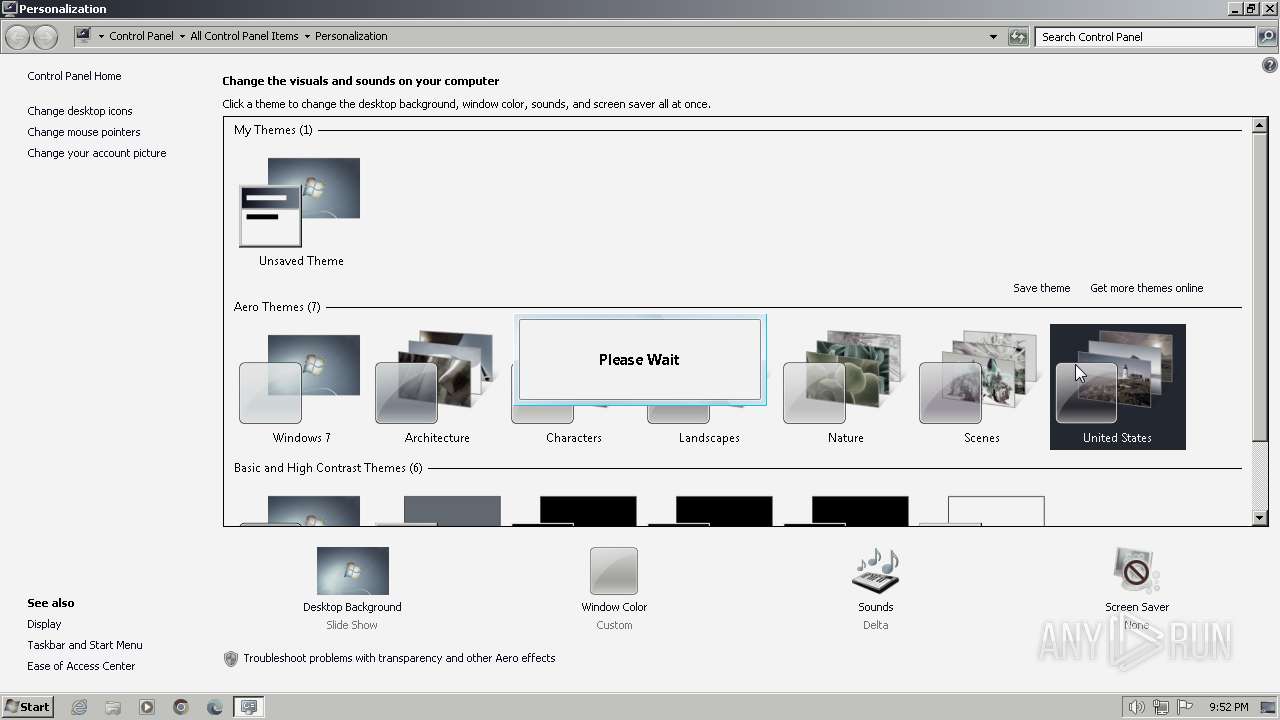
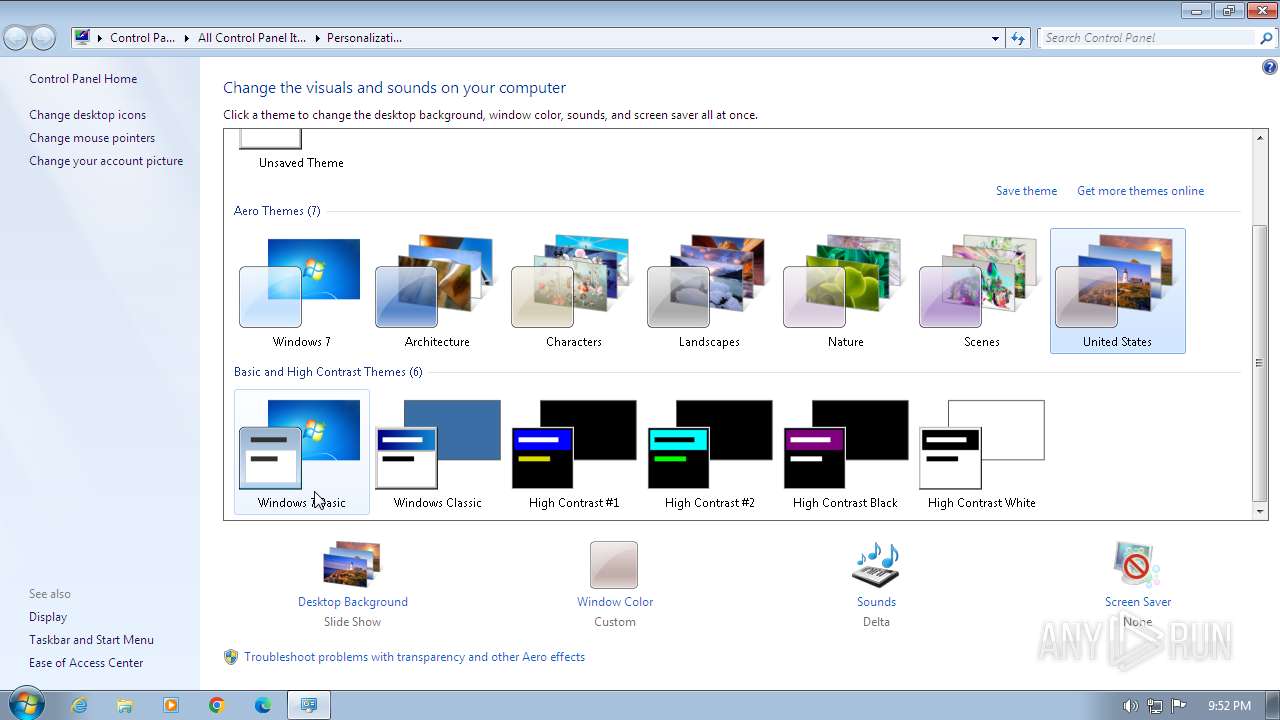
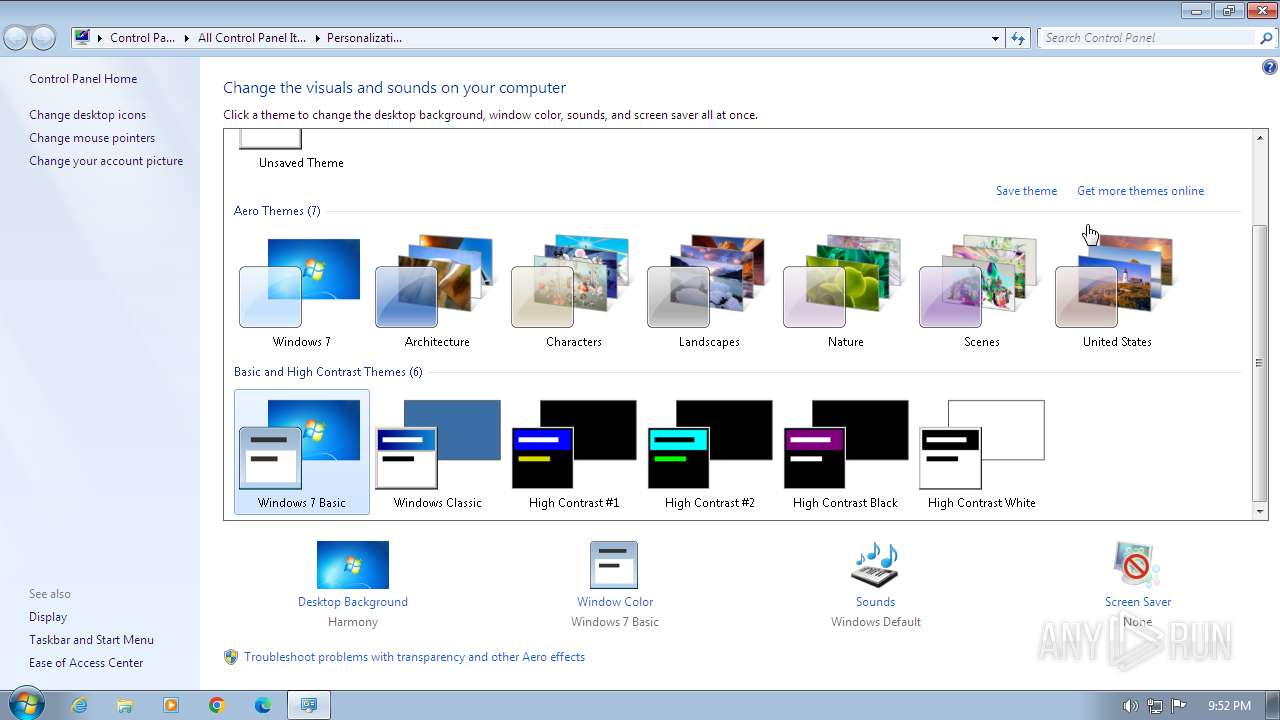
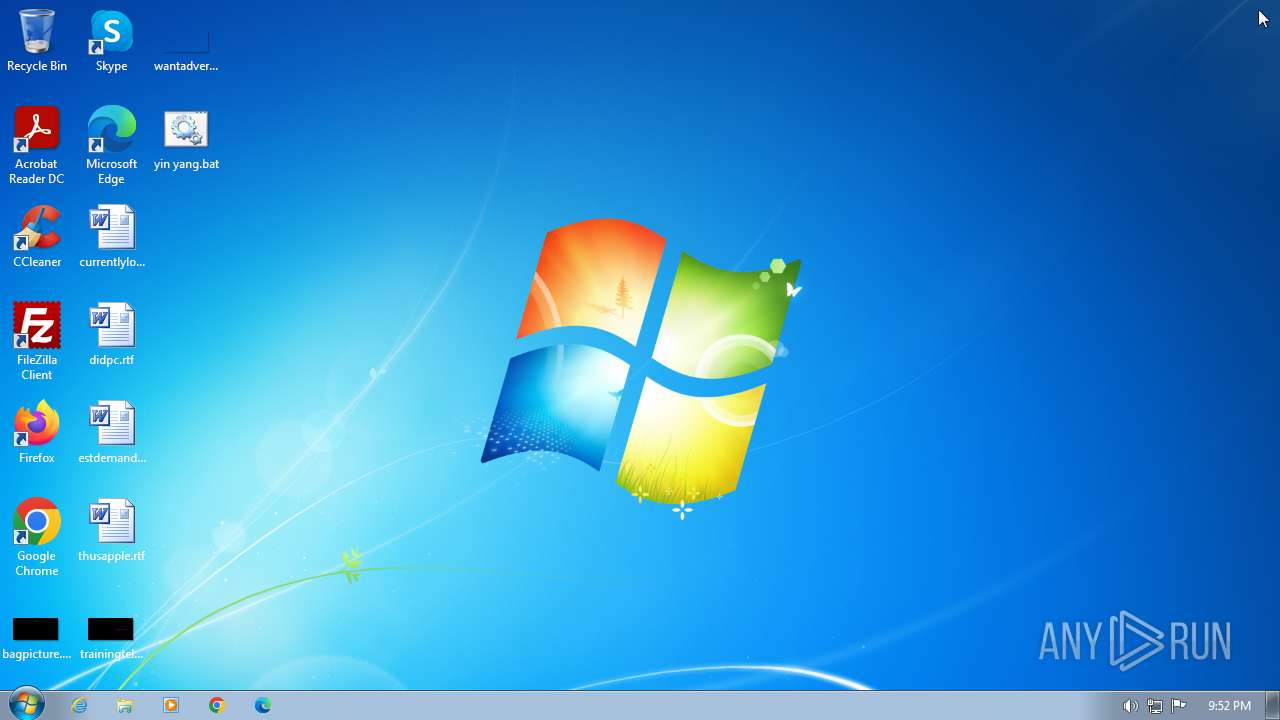
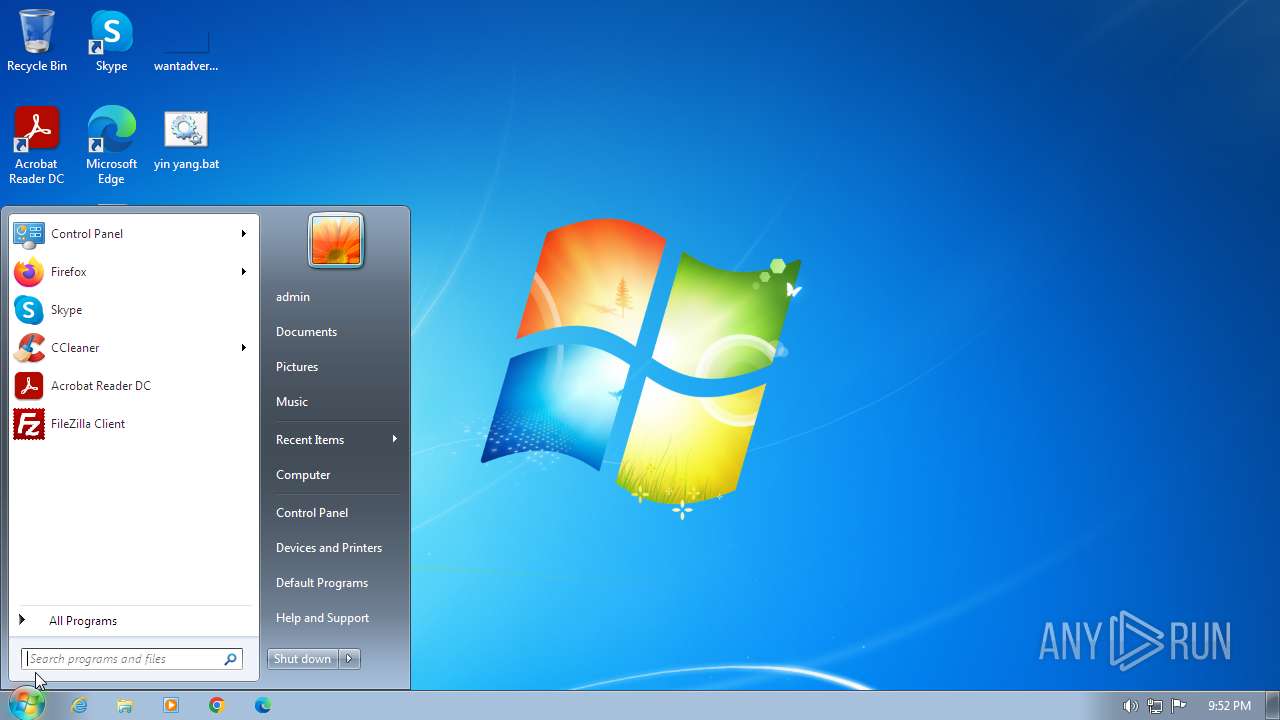
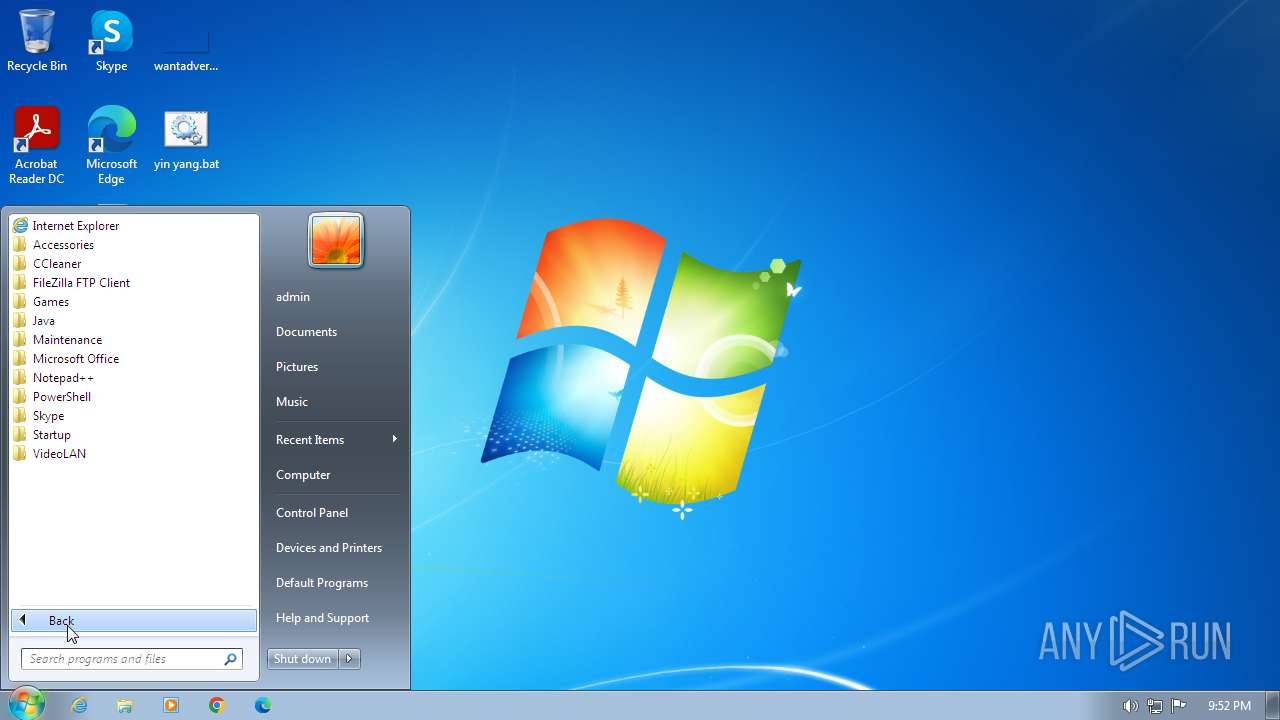
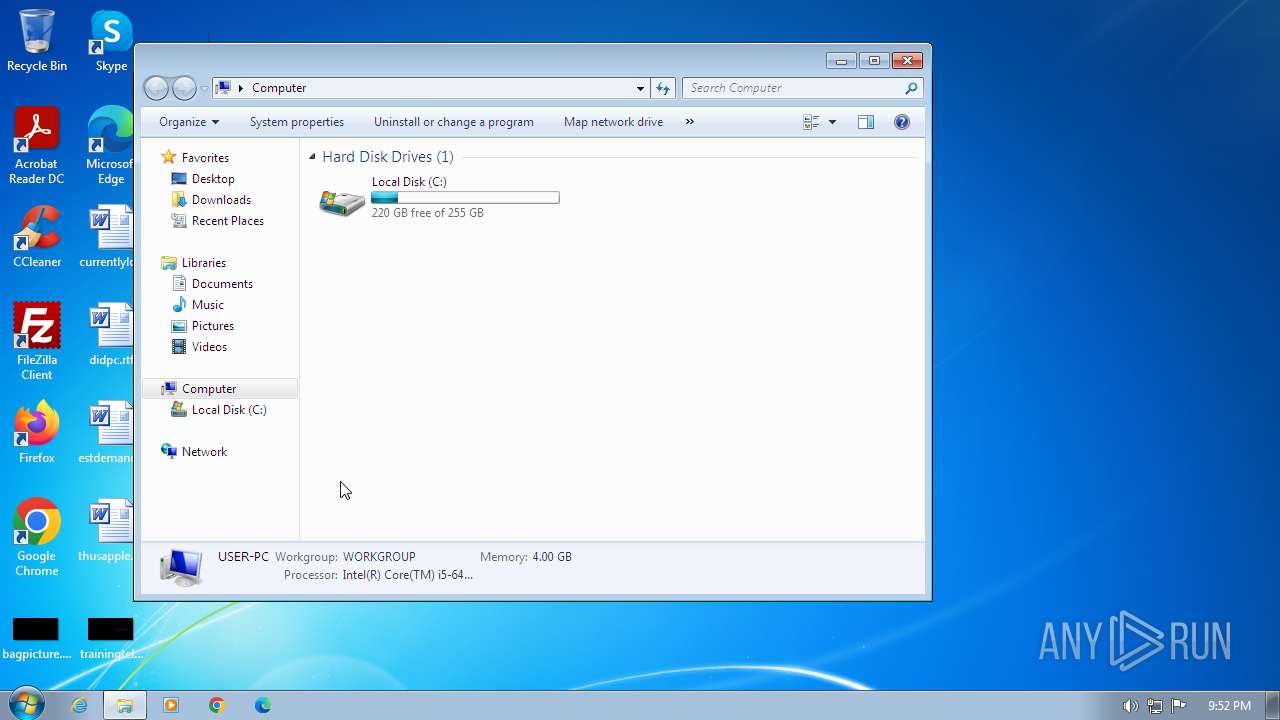
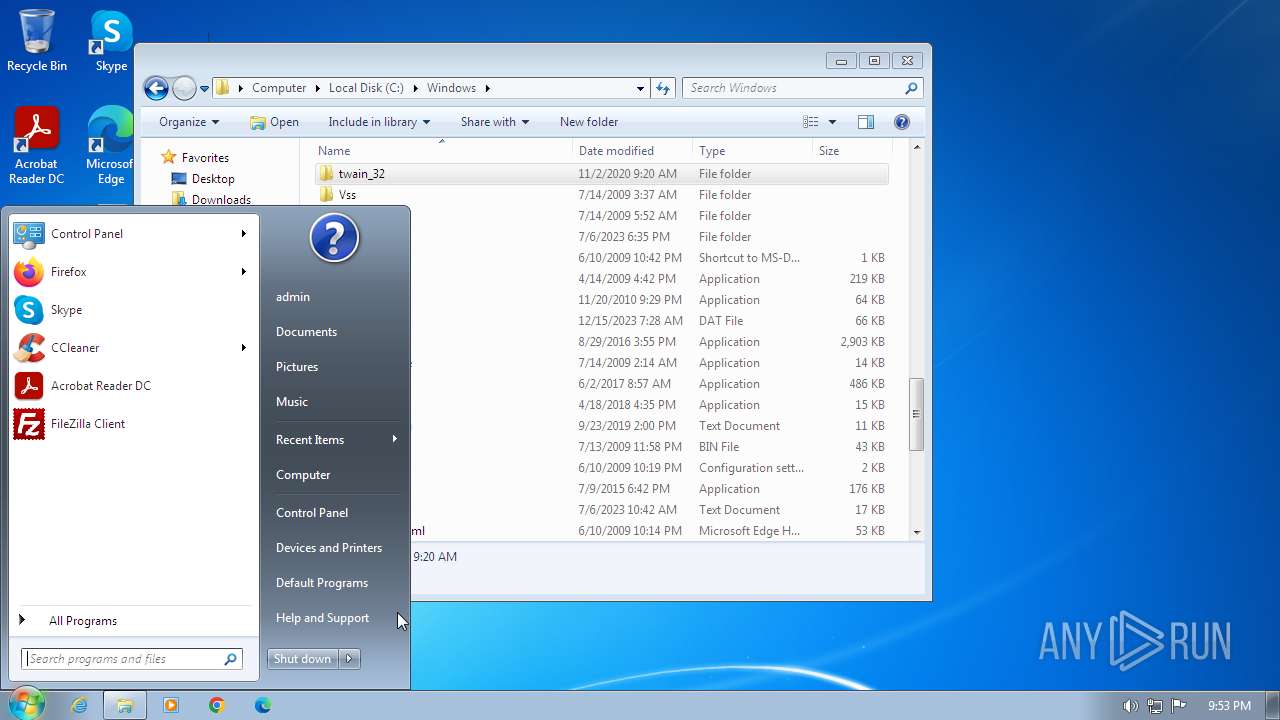
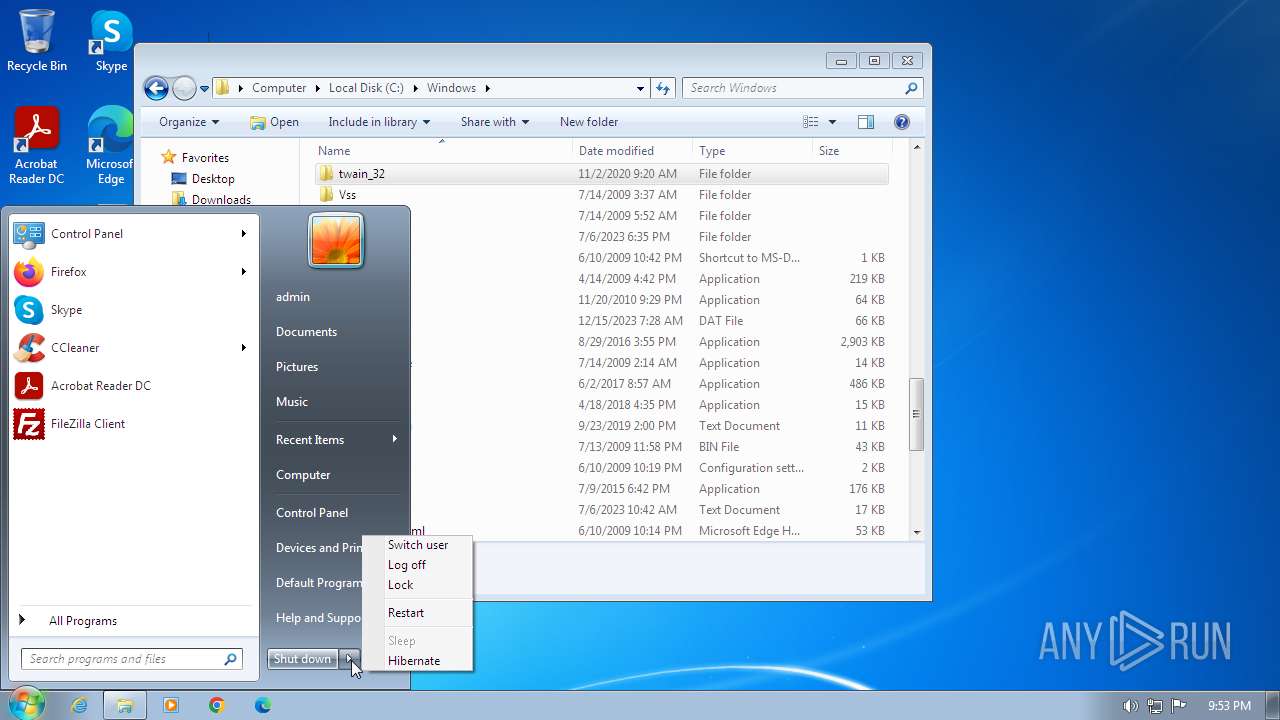
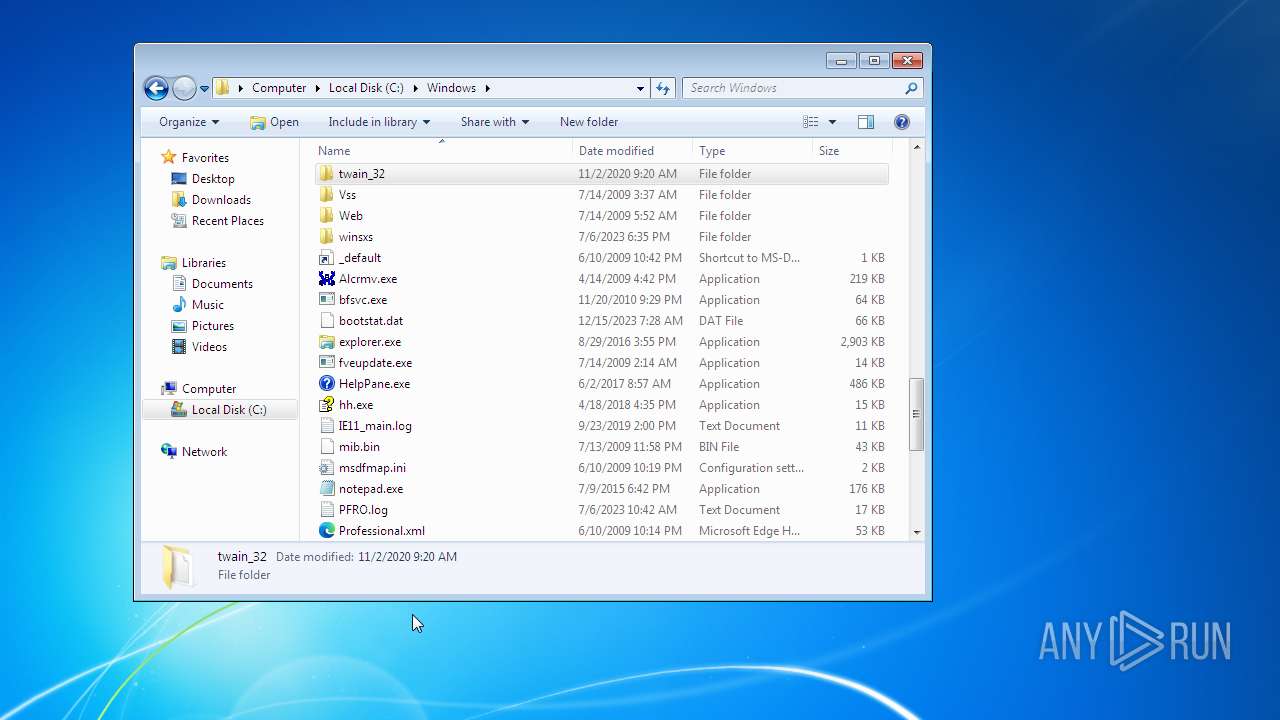
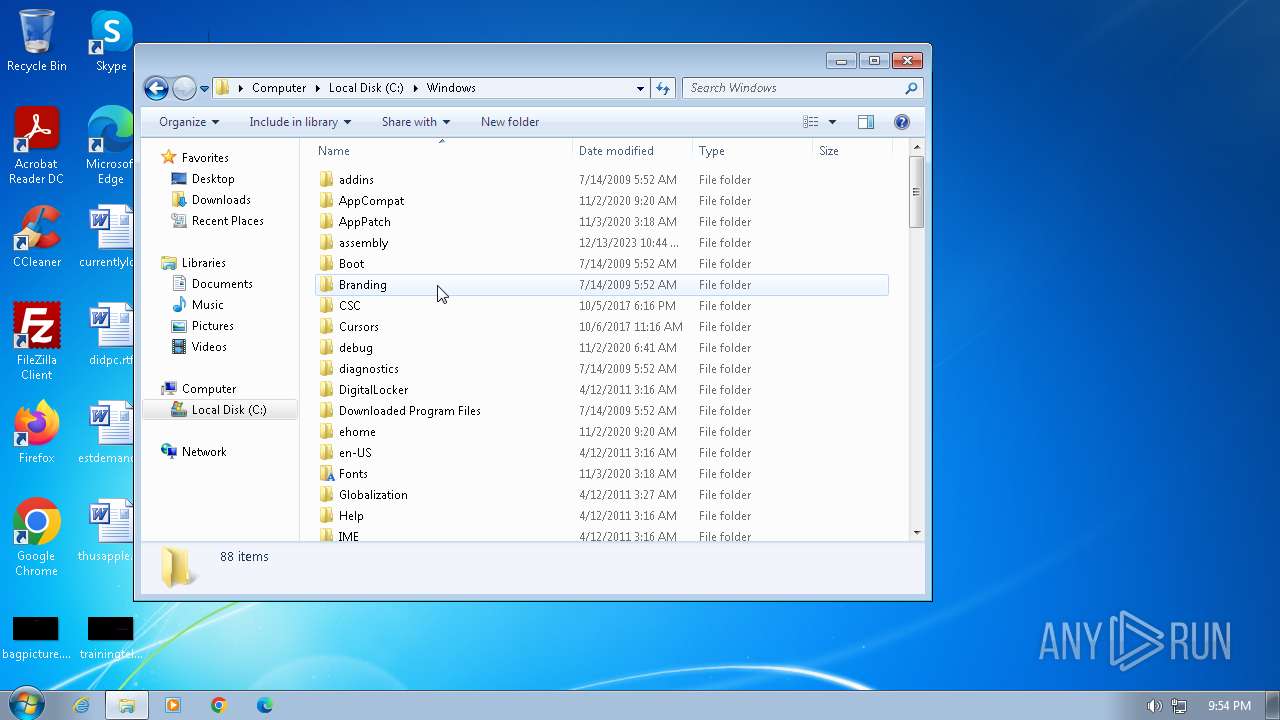
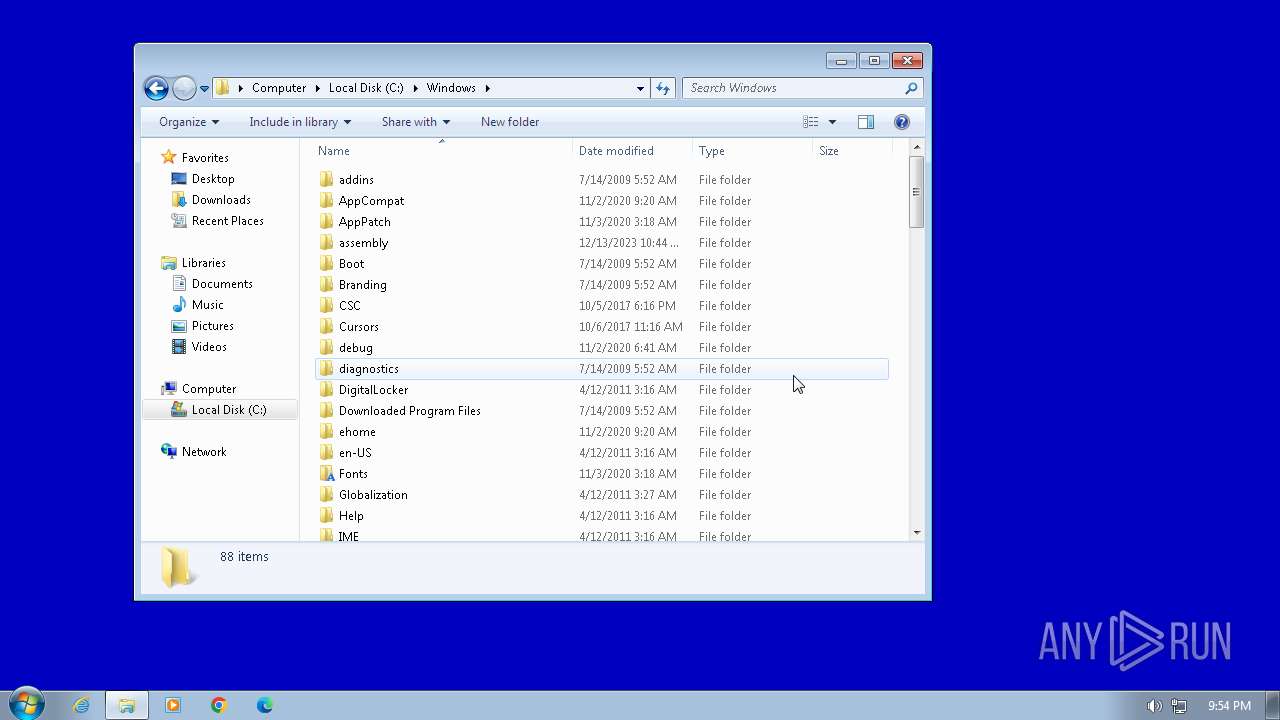
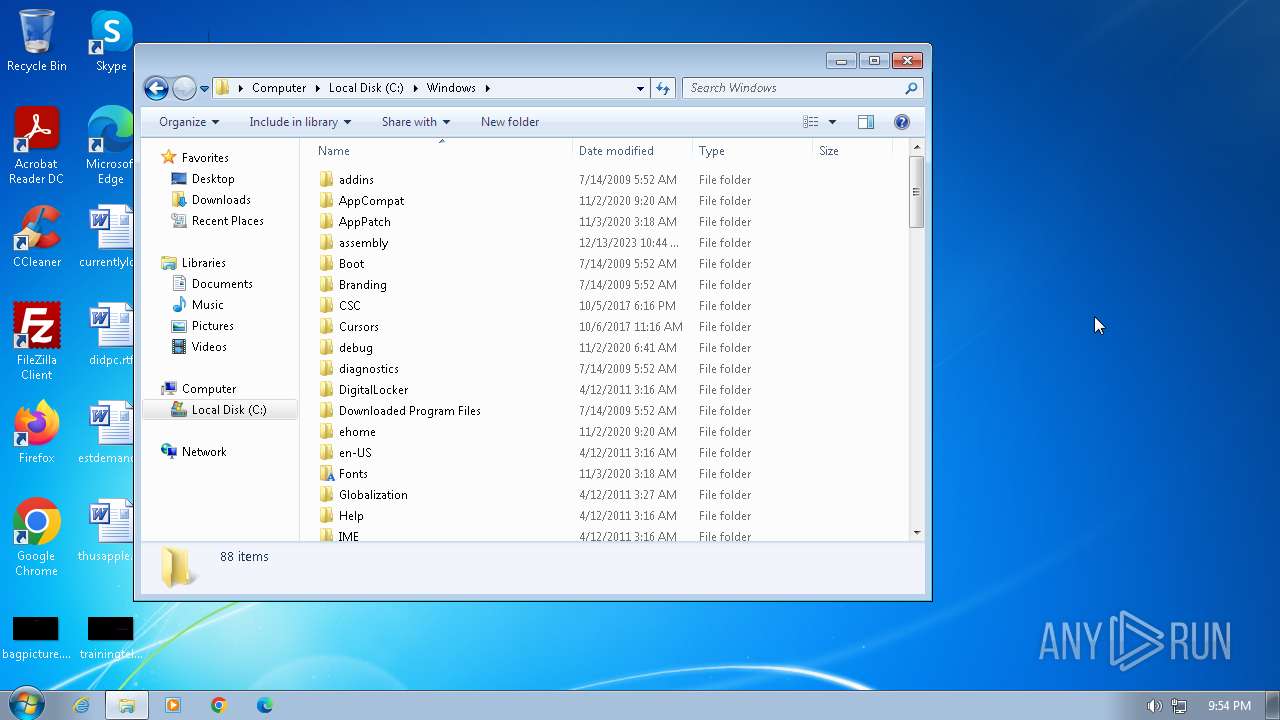
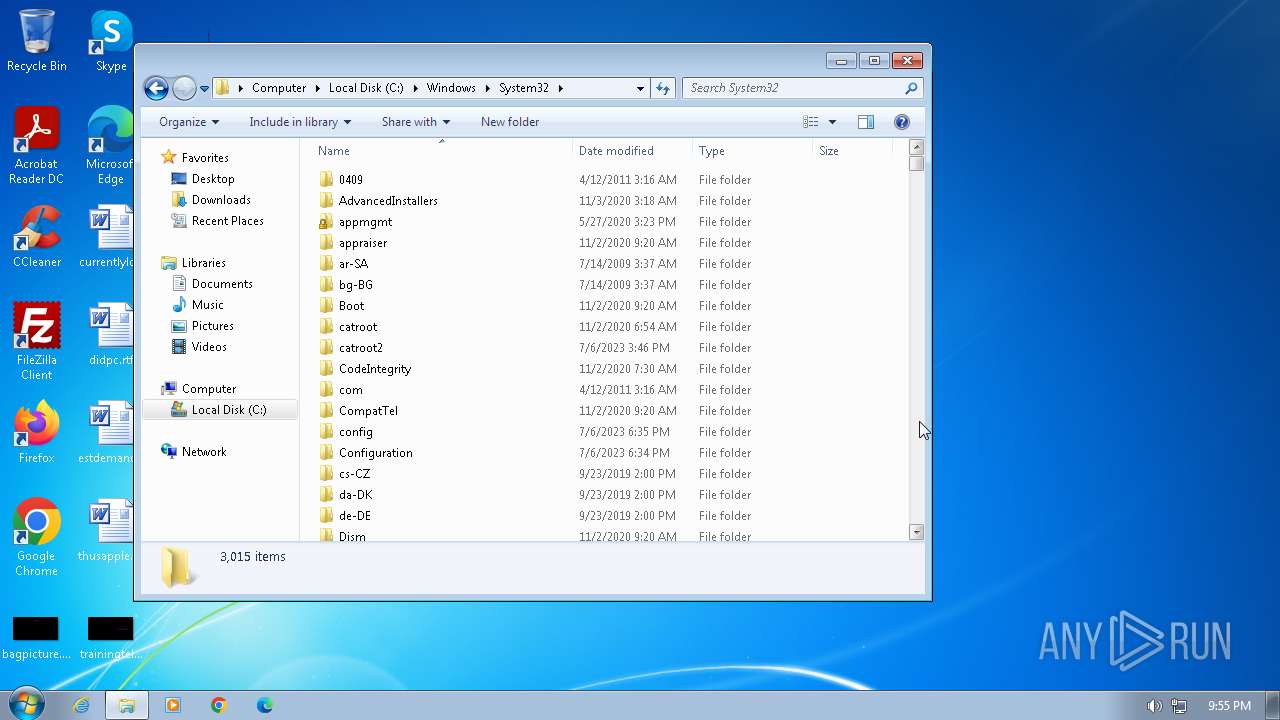
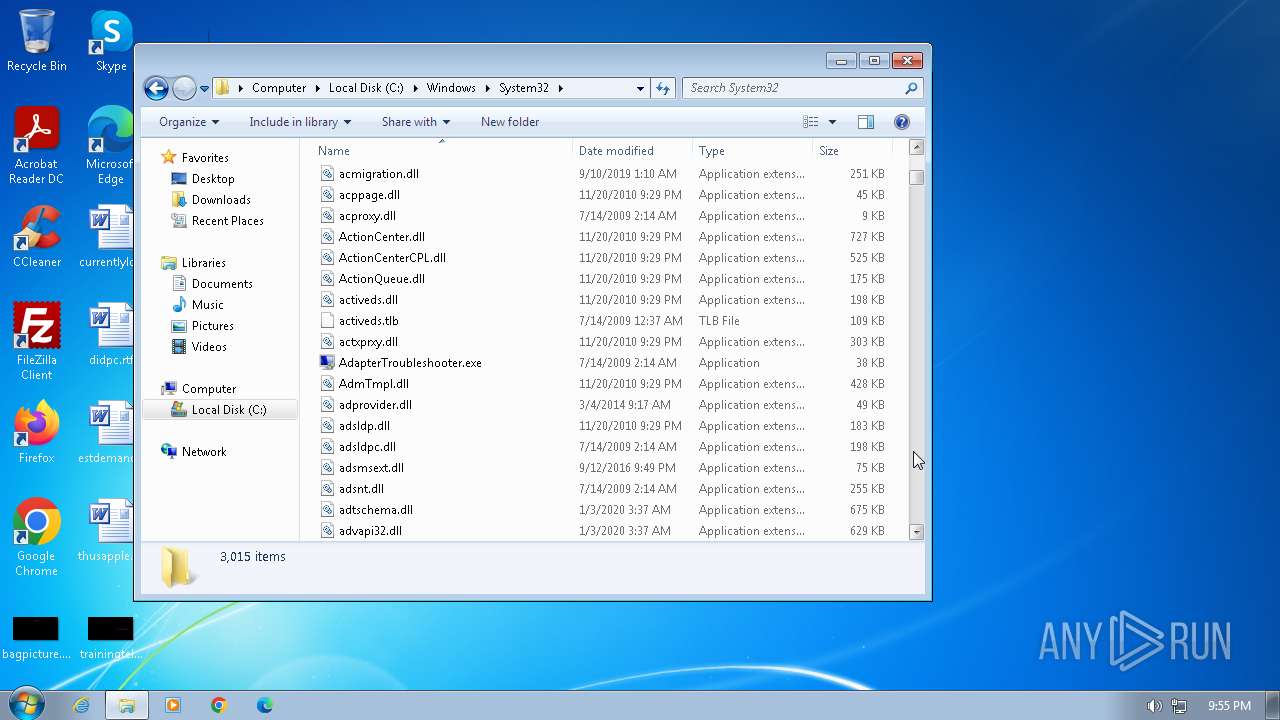
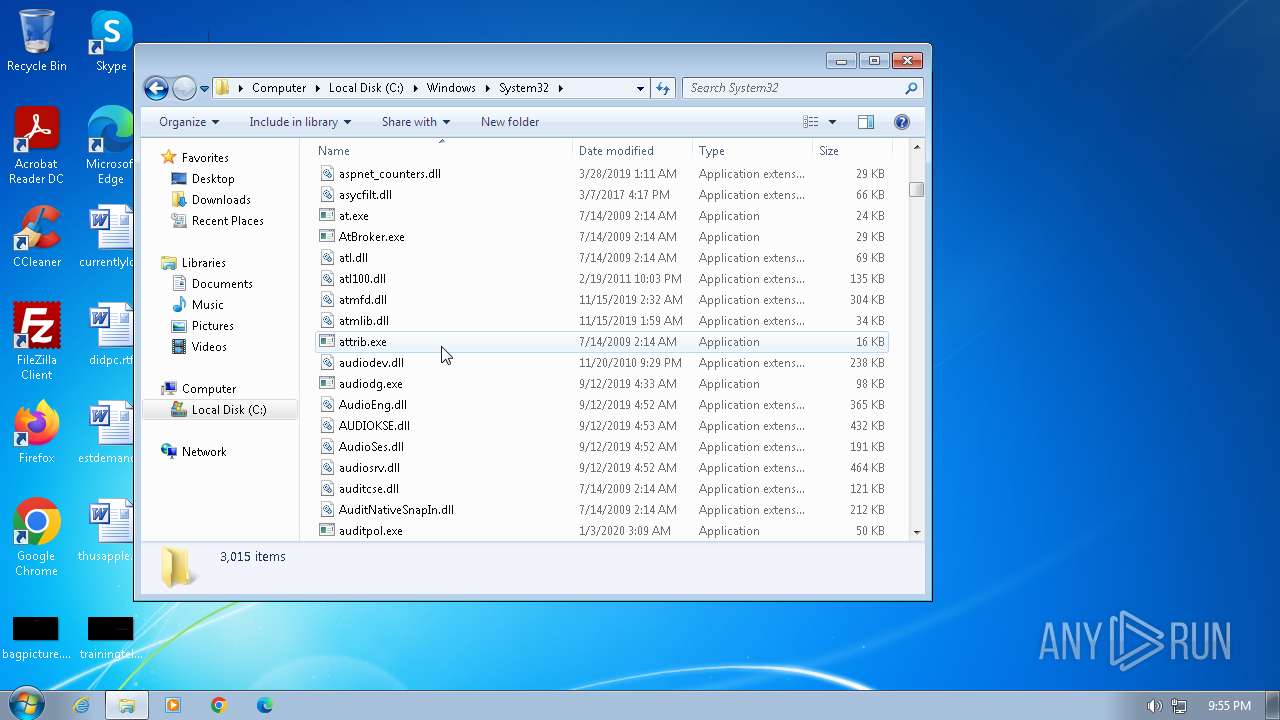
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines (31424), with CRLF line terminators |
| MD5: | DC7885C57316E39E0D7B29922D2ED9D0 |
| SHA1: | A8A5C67480CF13B5BB72F4C099650C3F5EDE65A8 |
| SHA256: | 86806F07D86CA6D01D408DE609ED1E3738E4E41FA91769BA713E8C98311FBFE2 |
| SSDEEP: | 768:3CF8vW8Oh8aLlCGi1Cj1G2M4bTjRhGlwQJg8y8+M4bTjRhGlwQJFoRT9Rllj:3F+8aLI/gI2MGTjewQJgNrMGTjewQJFi |
MALICIOUS
Detects the decoding of a binary file from Base64 (SCRIPT)
- cscript.exe (PID: 1844)
- cscript.exe (PID: 2856)
Uses base64 encoding (SCRIPT)
- cscript.exe (PID: 2856)
- cscript.exe (PID: 1844)
Gets path to any of the special folders (SCRIPT)
- cscript.exe (PID: 1844)
- cscript.exe (PID: 2856)
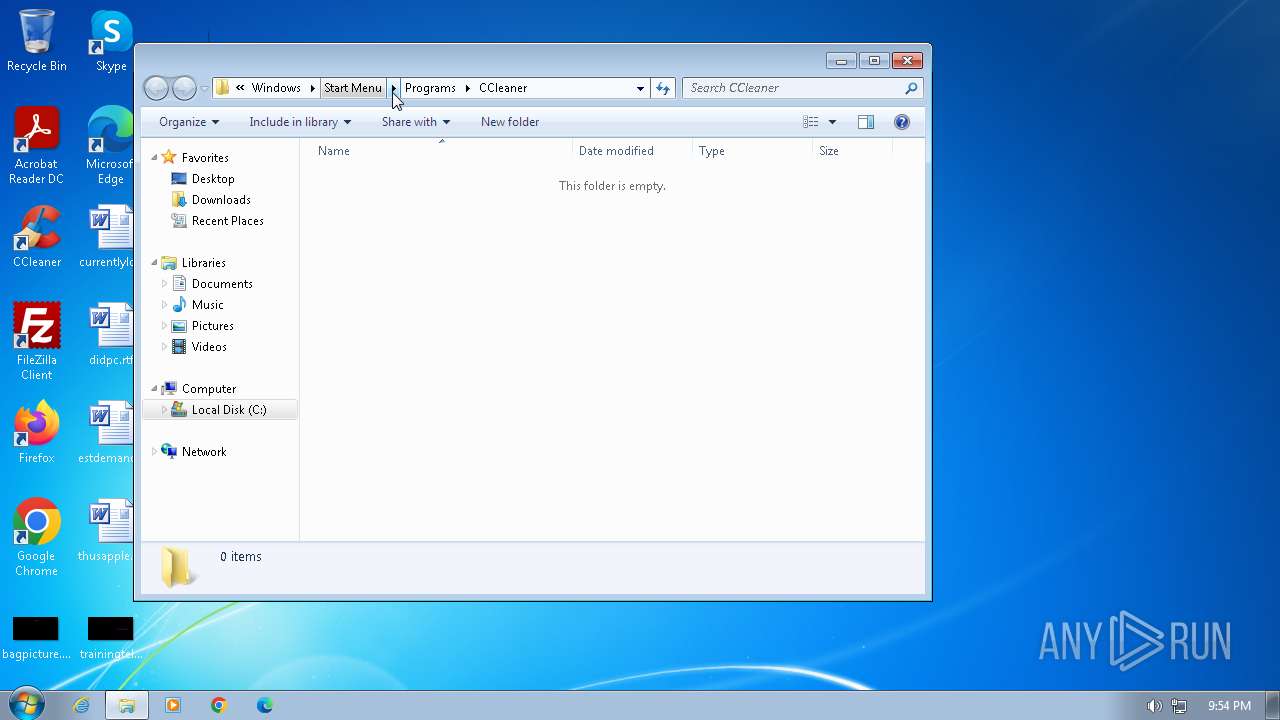
Changes the autorun value in the registry
- file.exe (PID: 3392)
Actions looks like stealing of personal data
- file.exe (PID: 3392)
Drops the executable file immediately after the start
- autumn.exe (PID: 2076)
SUSPICIOUS
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 2100)
- cmd.exe (PID: 3936)
The process executes VB scripts
- cmd.exe (PID: 2100)
- cmd.exe (PID: 3936)
Creates XML DOM element (SCRIPT)
- cscript.exe (PID: 1844)
- cscript.exe (PID: 2856)
Creates FileSystem object to access computer's file system (SCRIPT)
- cscript.exe (PID: 1844)
- cscript.exe (PID: 2856)
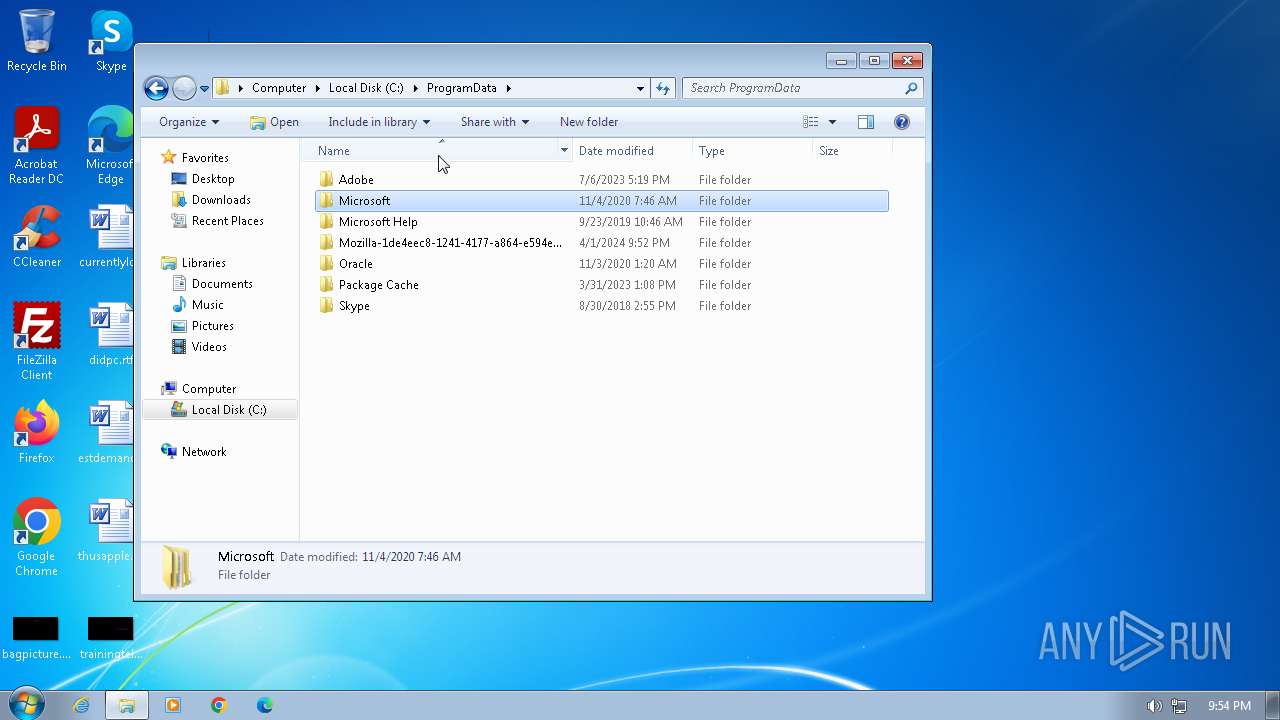
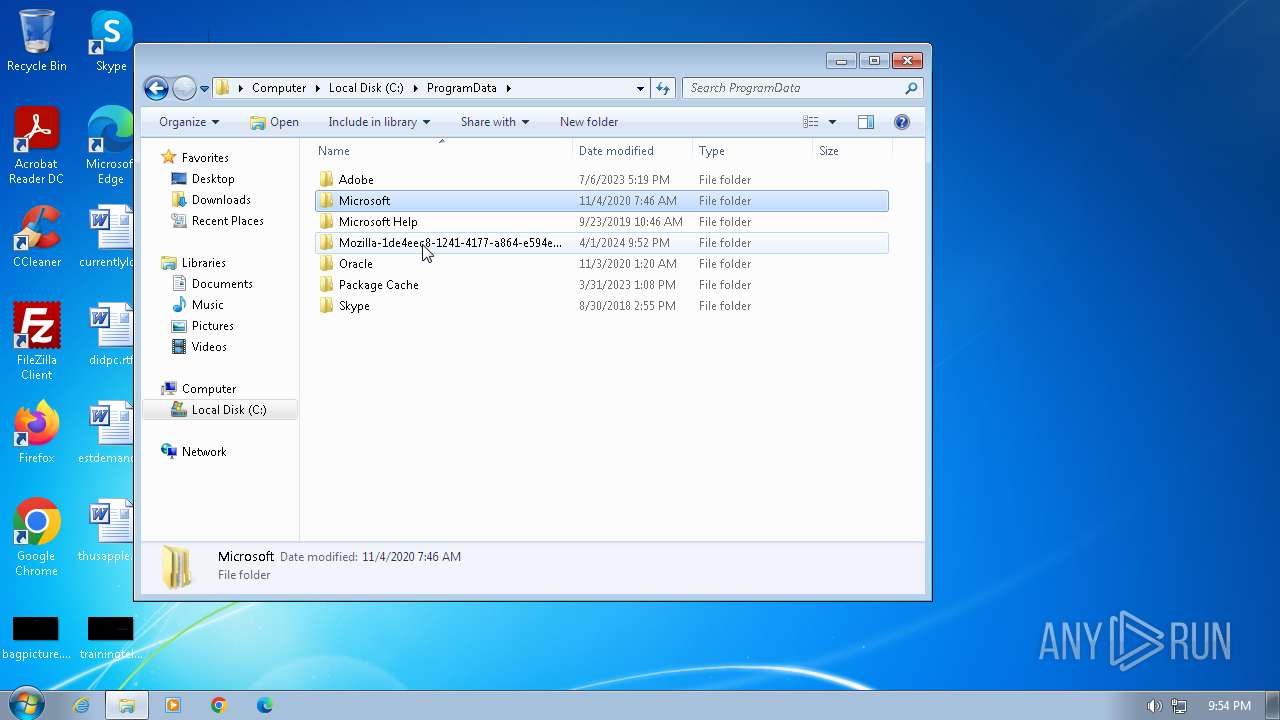
Executable content was dropped or overwritten
- file.exe (PID: 2968)
- autumn.exe (PID: 2076)
- cscript.exe (PID: 2856)
The process executes via Task Scheduler
- ctfmon.exe (PID: 1460)
- sipnotify.exe (PID: 1680)
Reads the Internet Settings
- sipnotify.exe (PID: 1680)
- control.exe (PID: 796)
Reads settings of System Certificates
- sipnotify.exe (PID: 1680)
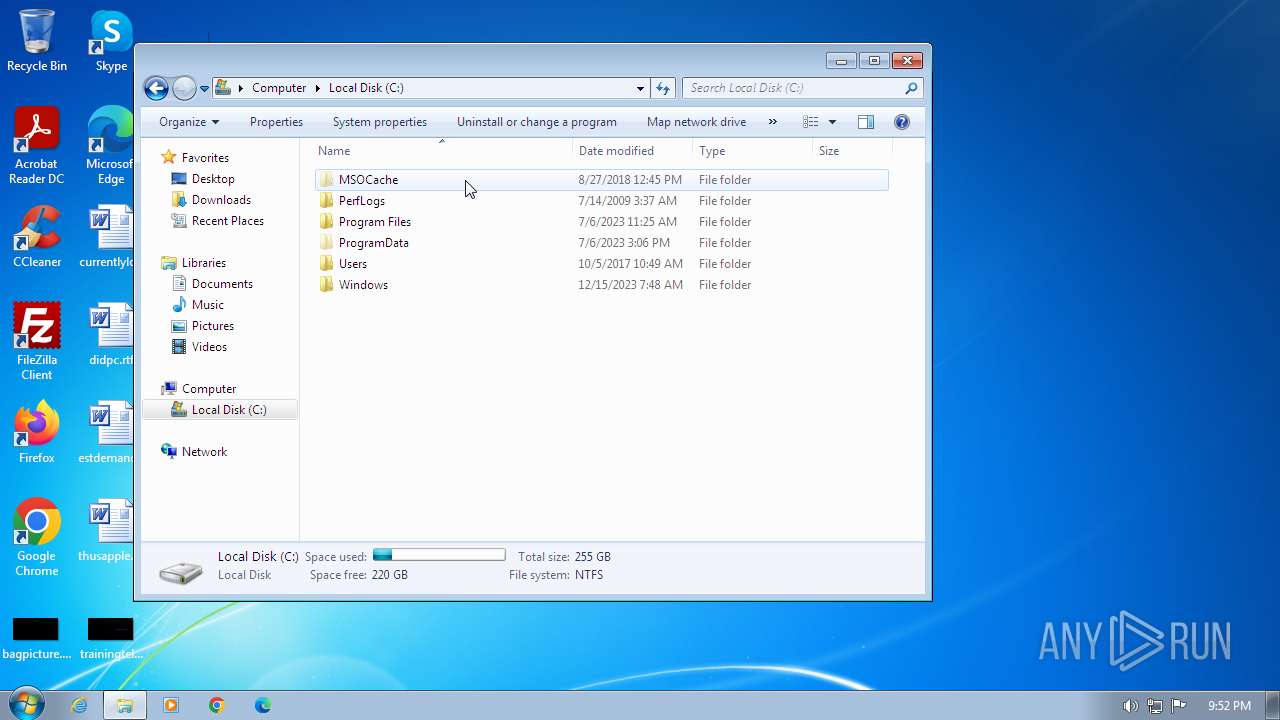
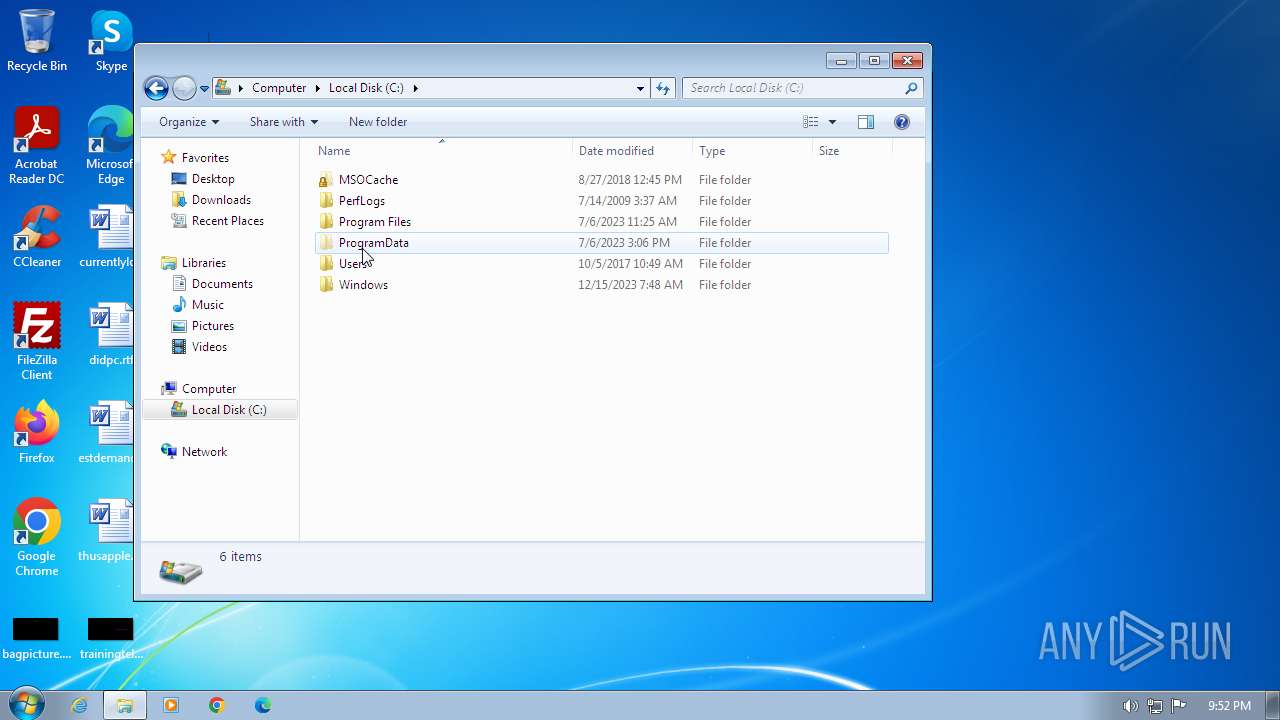
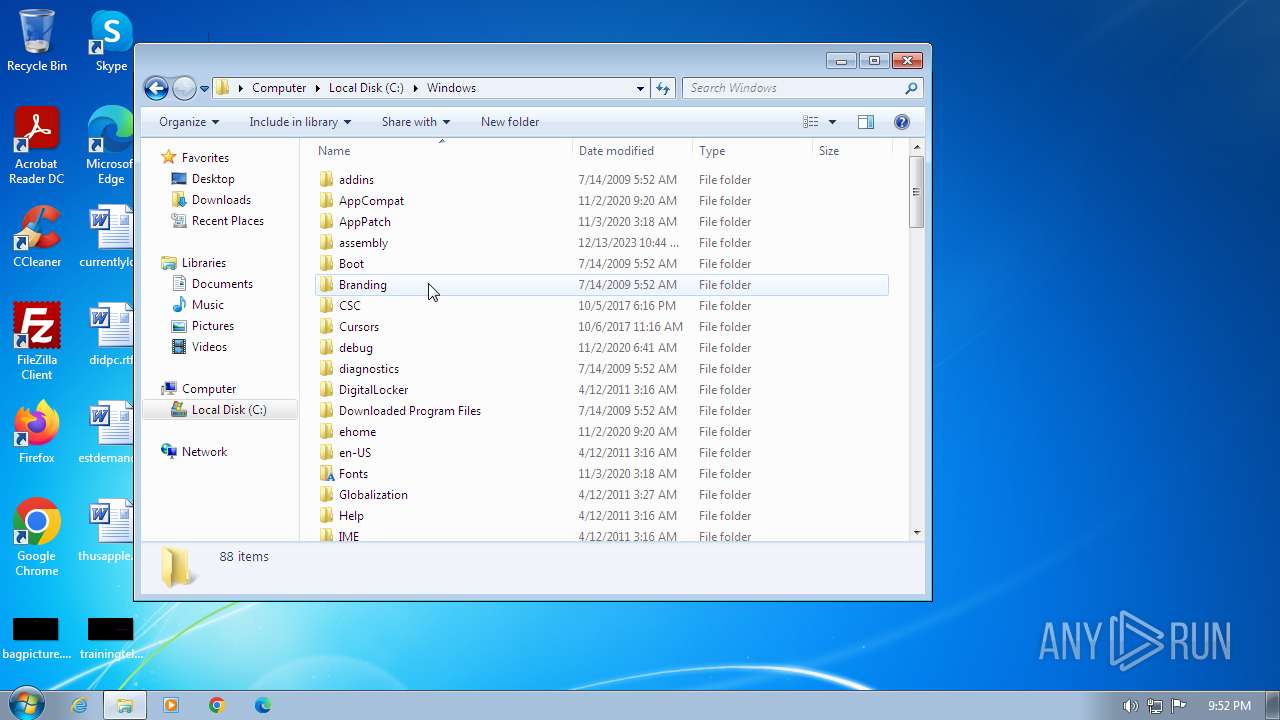
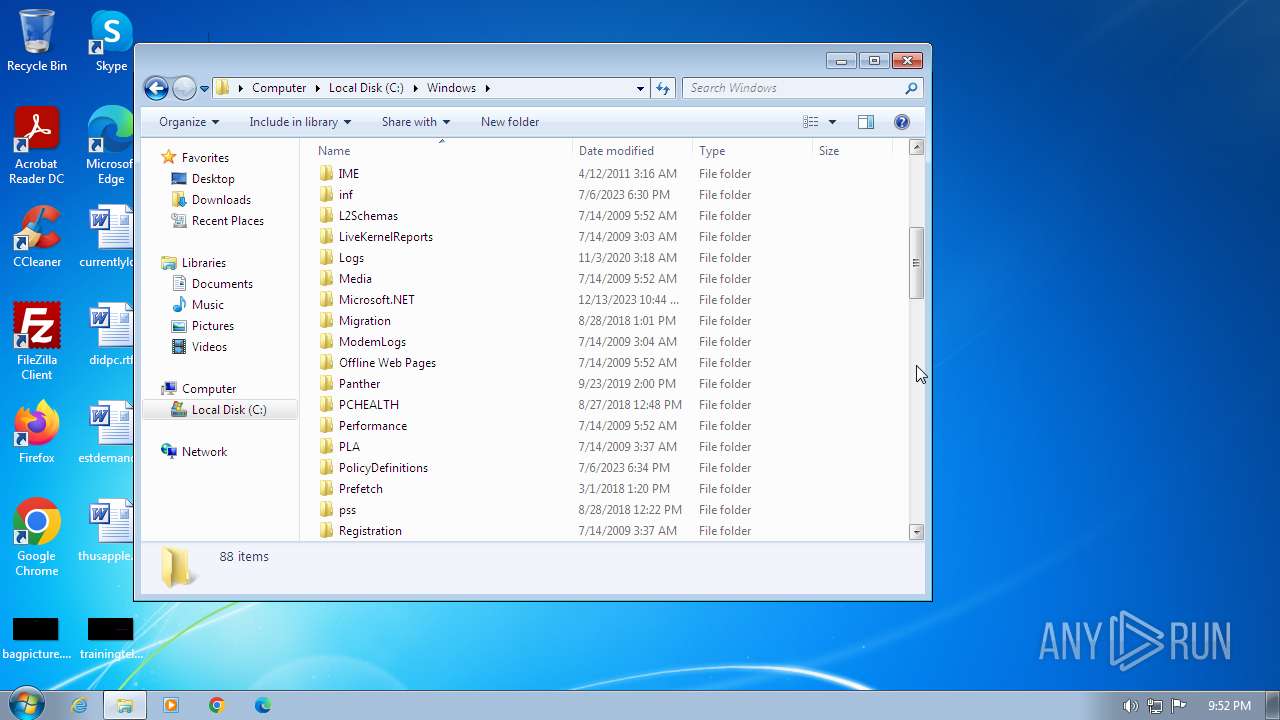
Creates file in the systems drive root
- autumn.exe (PID: 2076)
- file.exe (PID: 3392)
Writes binary data to a Stream object (SCRIPT)
- cscript.exe (PID: 1844)
- cscript.exe (PID: 2856)
Sets XML DOM element text (SCRIPT)
- cscript.exe (PID: 1844)
- cscript.exe (PID: 2856)
The executable file from the user directory is run by the CMD process
- file.exe (PID: 3392)
Creates a Stream, which may work with files, input/output devices, pipes, or TCP/IP sockets (SCRIPT)
- cscript.exe (PID: 2856)
- cscript.exe (PID: 1844)
Saves data to a binary file (SCRIPT)
- cscript.exe (PID: 1844)
- cscript.exe (PID: 2856)
Uses RUNDLL32.EXE to load library
- control.exe (PID: 796)
INFO
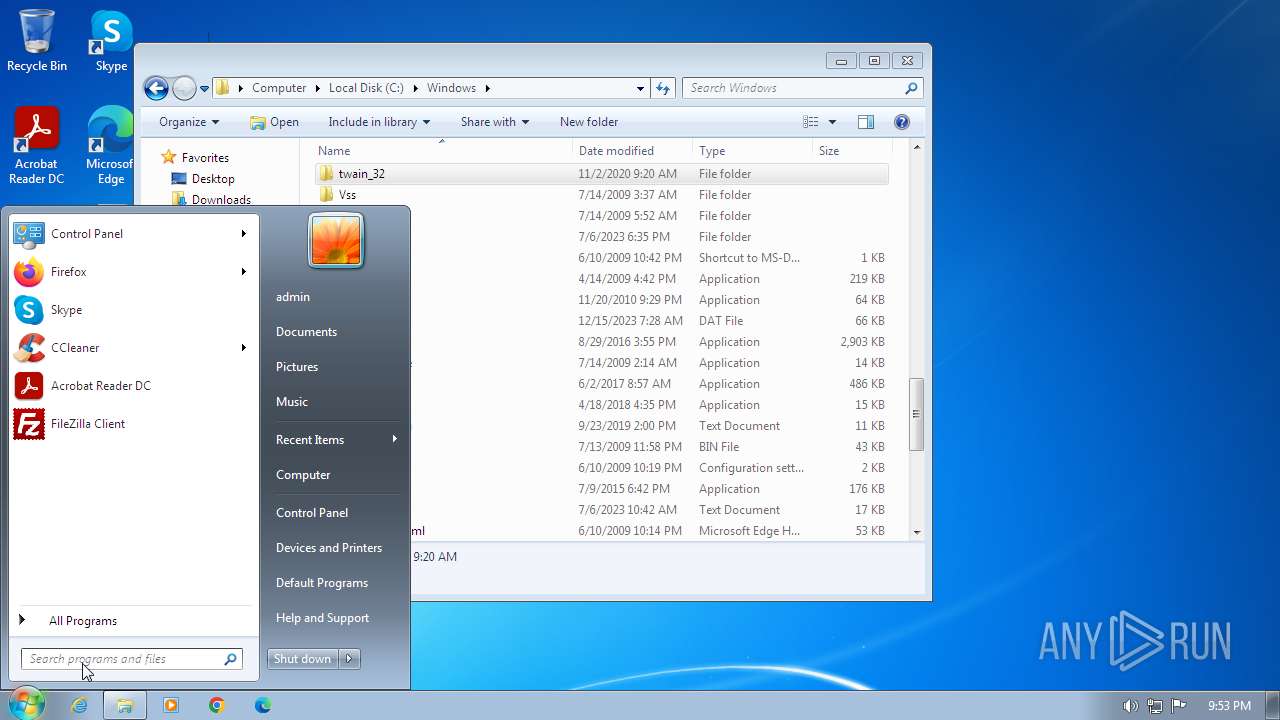
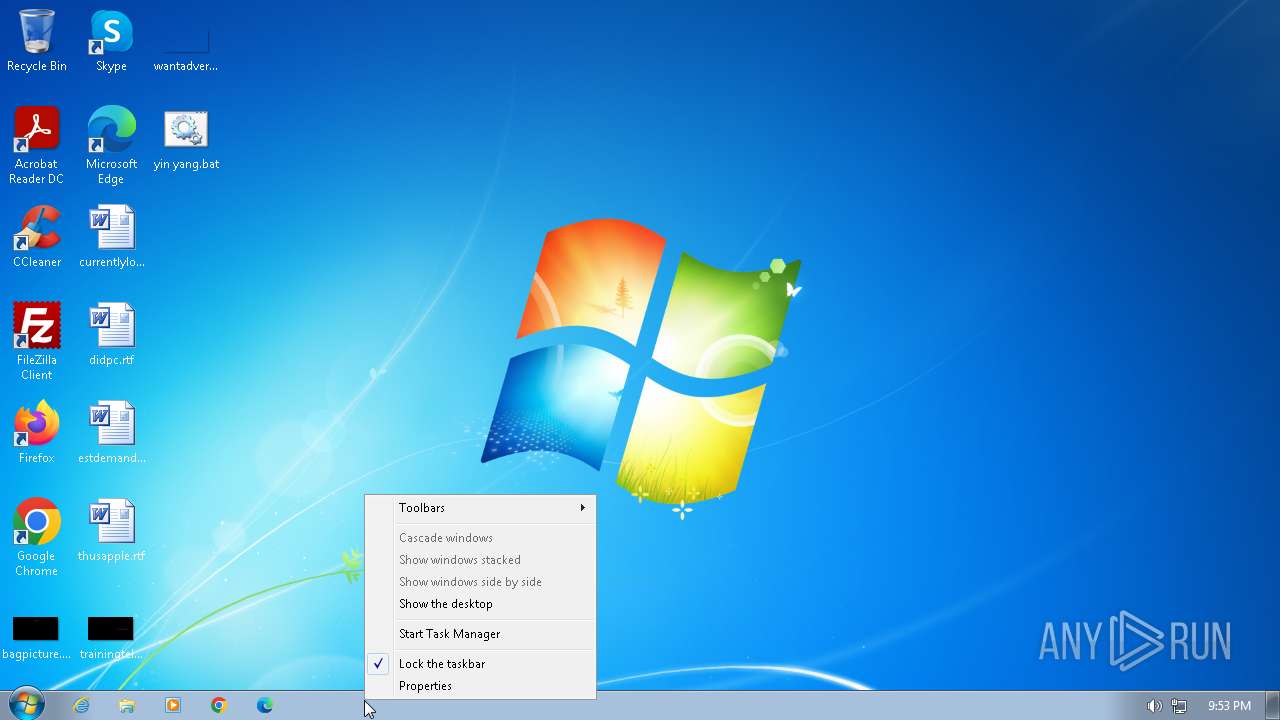
Manual execution by a user
- IMEKLMG.EXE (PID: 1952)
- IMEKLMG.EXE (PID: 2056)
- autumn.exe (PID: 2076)
- wmpnscfg.exe (PID: 2328)
- wmpnscfg.exe (PID: 2348)
- taskmgr.exe (PID: 2528)
- control.exe (PID: 796)
Reads security settings of Internet Explorer
- sipnotify.exe (PID: 1680)
- cscript.exe (PID: 2856)
- control.exe (PID: 796)
Reads the computer name
- IMEKLMG.EXE (PID: 1952)
- IMEKLMG.EXE (PID: 2056)
- wmpnscfg.exe (PID: 2348)
- autumn.exe (PID: 2076)
- wmpnscfg.exe (PID: 2328)
- file.exe (PID: 3392)
Checks supported languages
- IMEKLMG.EXE (PID: 1952)
- IMEKLMG.EXE (PID: 2056)
- autumn.exe (PID: 2076)
- wmpnscfg.exe (PID: 2328)
- wmpnscfg.exe (PID: 2348)
- file.exe (PID: 3392)
Process checks whether UAC notifications are on
- IMEKLMG.EXE (PID: 2056)
- IMEKLMG.EXE (PID: 1952)
Reads the machine GUID from the registry
- autumn.exe (PID: 2076)
- file.exe (PID: 3392)
Reads the software policy settings
- sipnotify.exe (PID: 1680)
Creates files or folders in the user directory
- autumn.exe (PID: 2076)
Create files in a temporary directory
- cscript.exe (PID: 2856)
Reads the time zone
- rundll32.exe (PID: 1740)
Checks transactions between databases Windows and Oracle
- rundll32.exe (PID: 1740)
Drops the executable file immediately after the start
- cscript.exe (PID: 2856)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
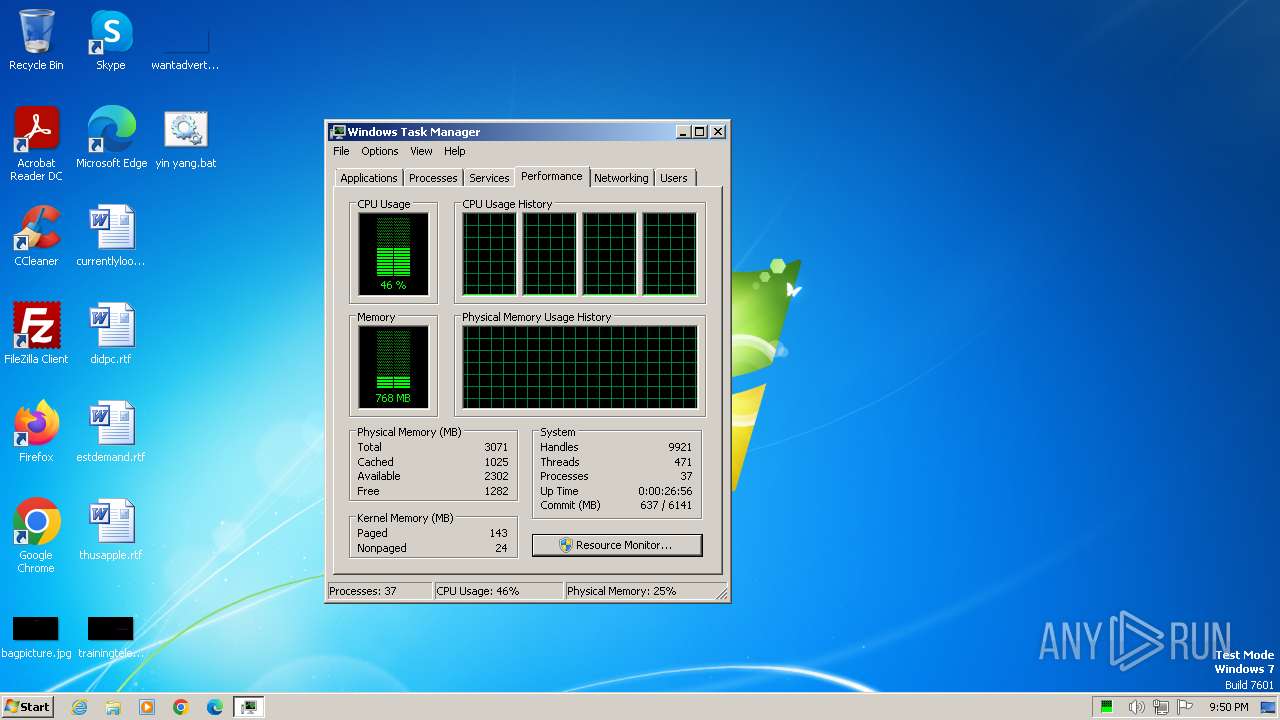
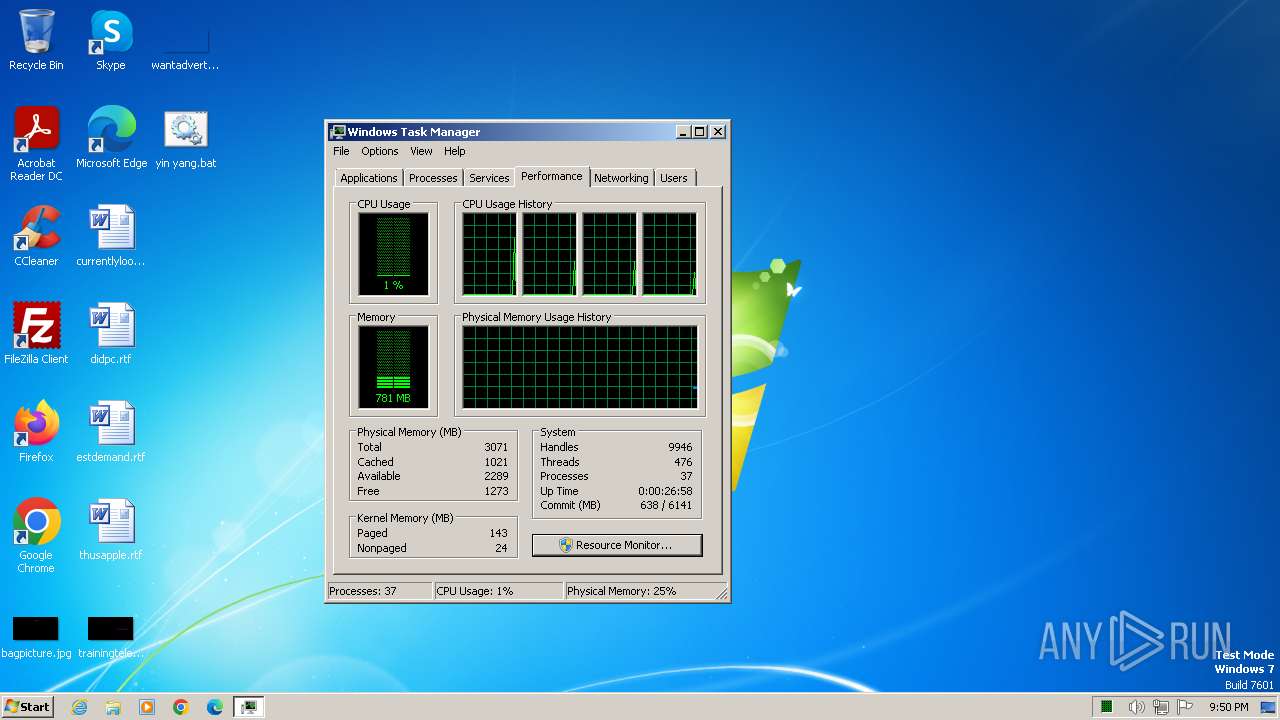
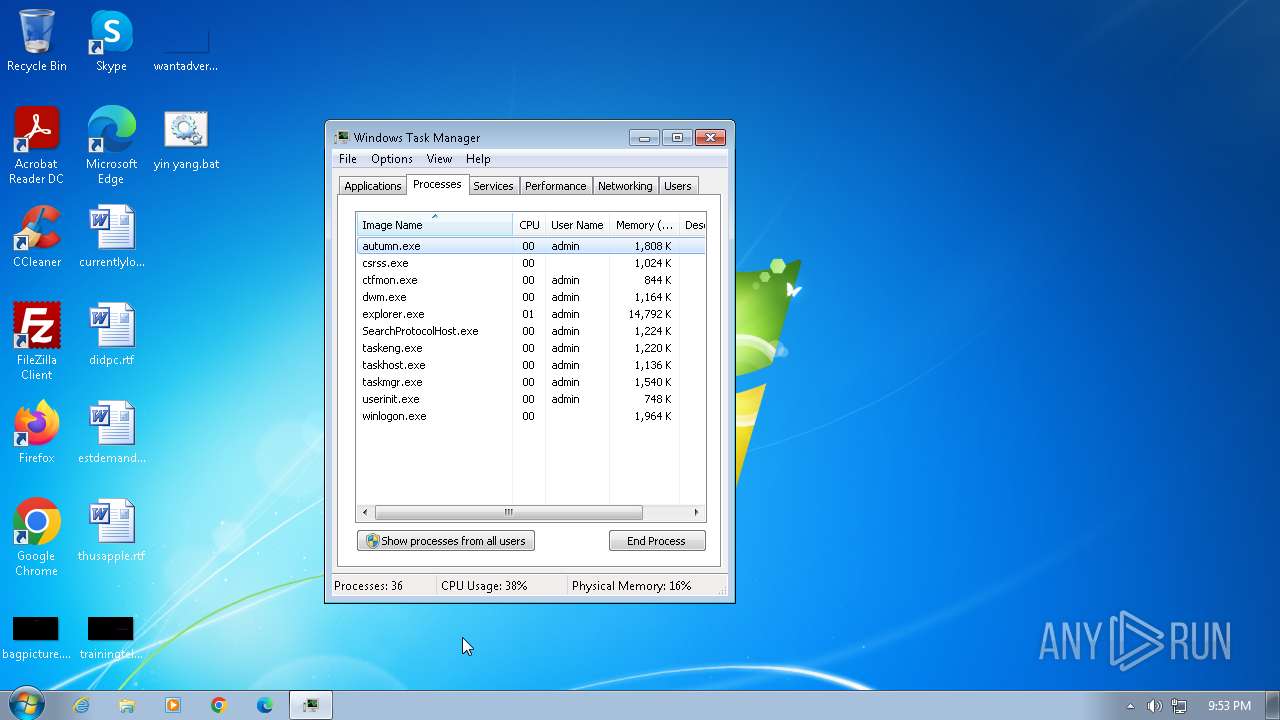
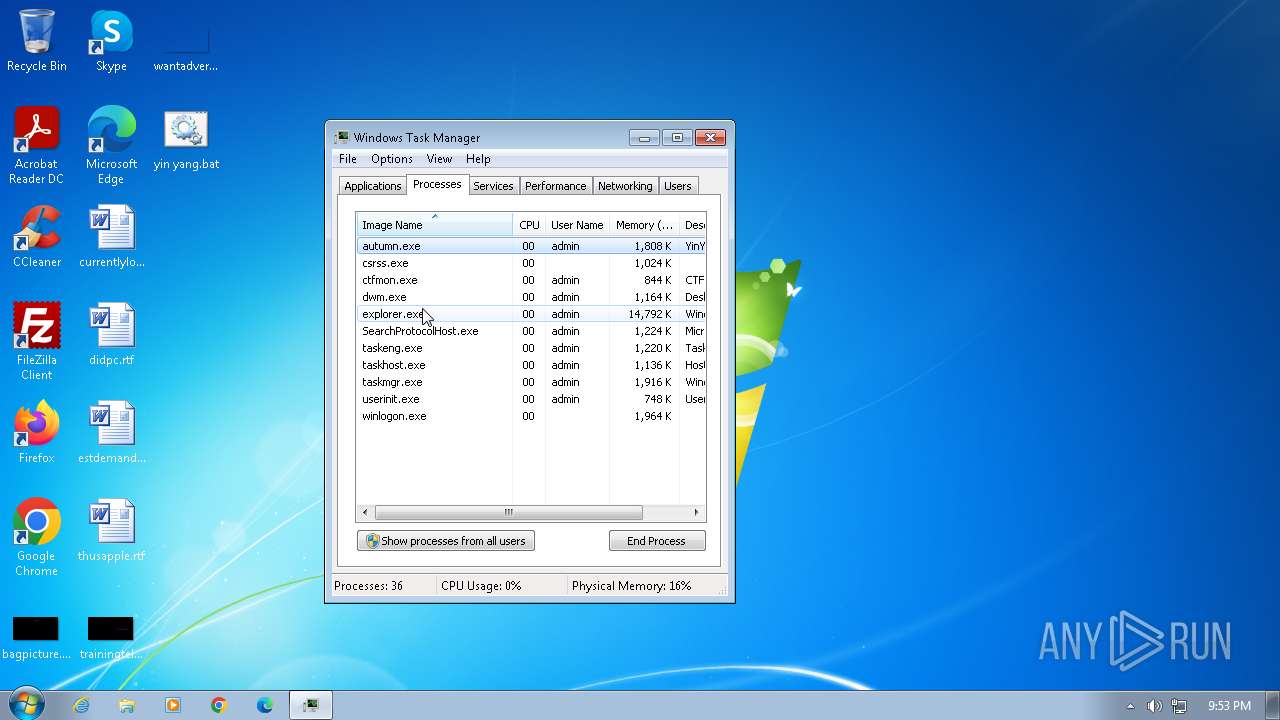
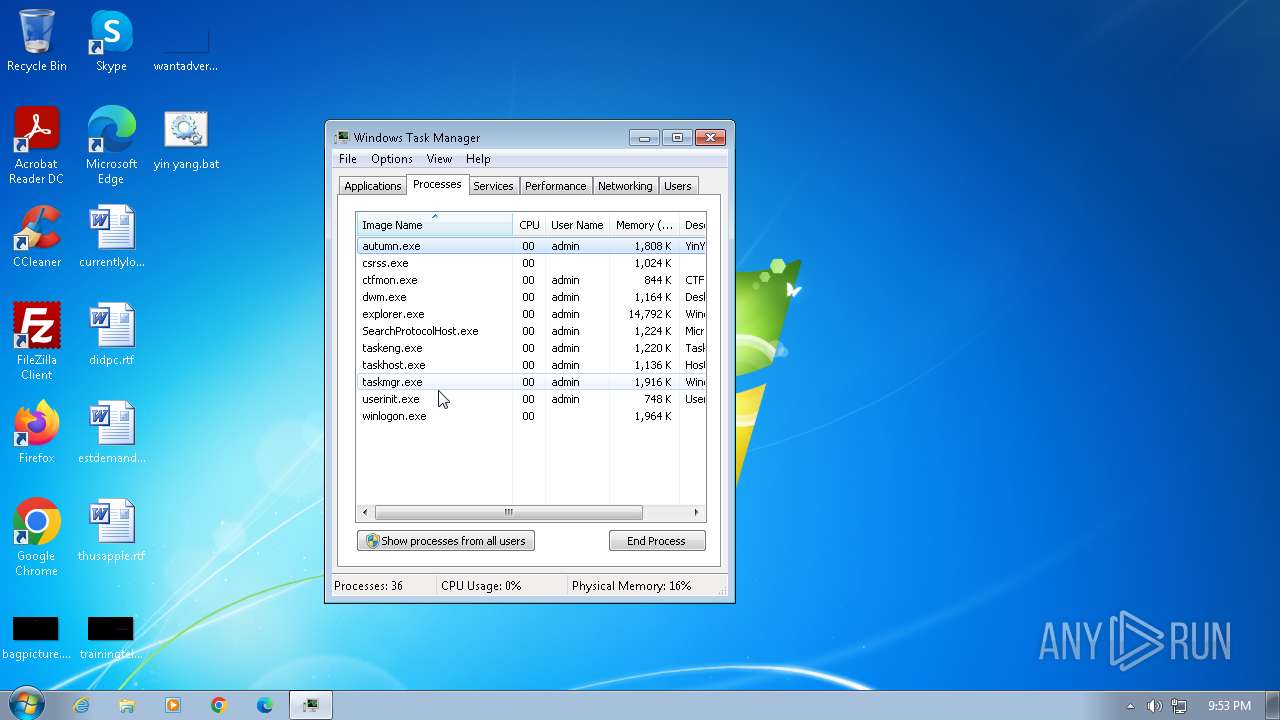
Total processes
119
Monitored processes
22
Malicious processes
7
Suspicious processes
1
Behavior graph
Click at the process to see the details
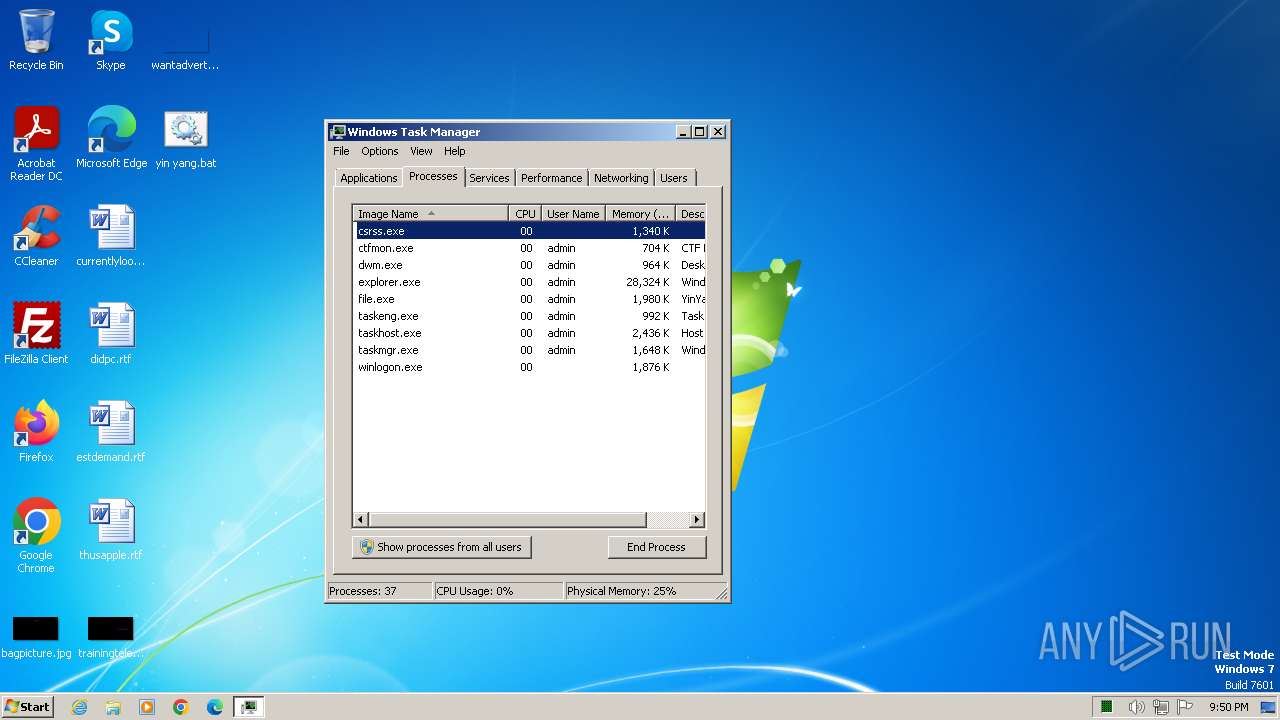
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 796 | "C:\Windows\System32\control.exe" "C:\Windows\system32\timedate.cpl", | C:\Windows\System32\control.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Control Panel Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1340 | FINDSTR /E "'VBS" "C:\Users\admin\Desktop\yin yang.bat" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1460 | C:\Windows\System32\ctfmon.exe | C:\Windows\System32\ctfmon.exe | — | taskeng.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: CTF Loader Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1680 | C:\Windows\system32\sipnotify.exe -LogonOrUnlock | C:\Windows\System32\sipnotify.exe | taskeng.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: sipnotify Exit code: 0 Version: 6.1.7602.20480 (win7sp1_ldr_escrow.191010-1716) Modules
| |||||||||||||||
| 1740 | "C:\Windows\system32\rundll32.exe" Shell32.dll,Control_RunDLL "C:\Windows\system32\timedate.cpl", | C:\Windows\System32\rundll32.exe | — | control.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1844 | cscript //nologo "C:\Users\admin\AppData\Local\Temp\bbin.vbs" | C:\Windows\System32\cscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
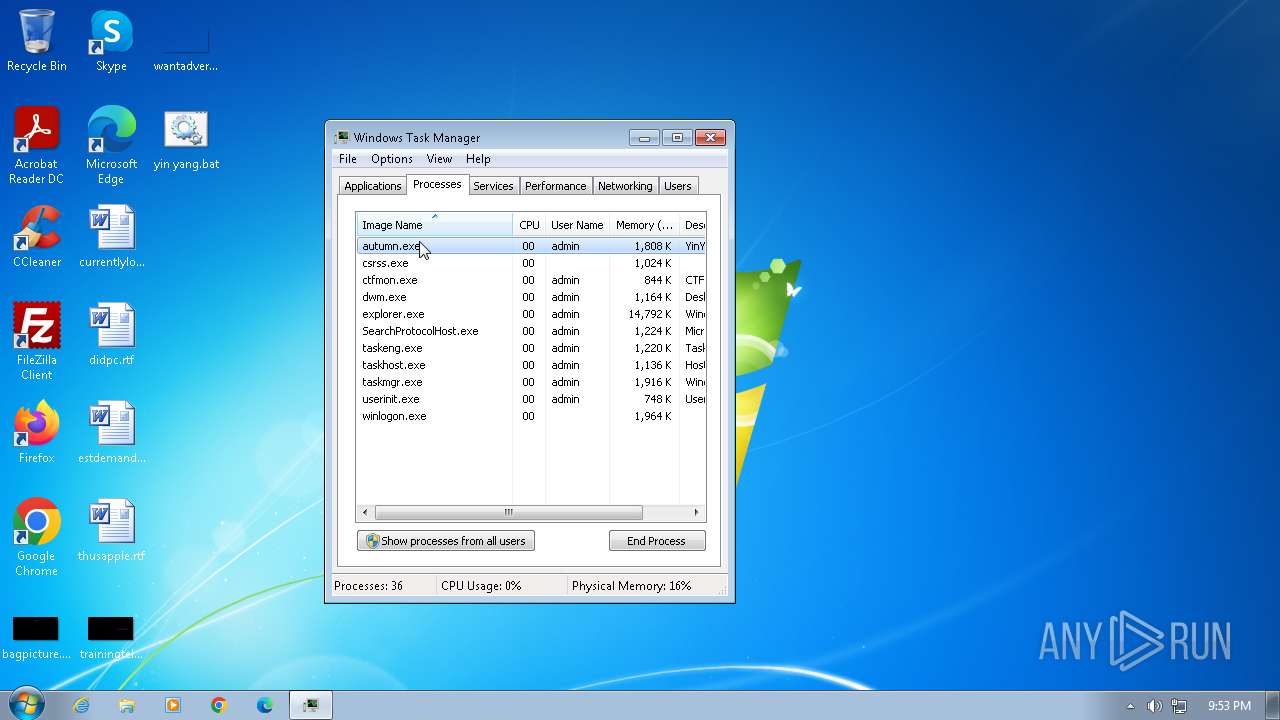
| 1848 | "C:\Windows\system32\taskmgr.exe" /4 | C:\Windows\System32\taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1952 | "C:\Program Files\Common Files\microsoft shared\IME14\SHARED\IMEKLMG.EXE" /SetPreload /JPN /Log | C:\Program Files\Common Files\microsoft shared\IME14\SHARED\IMEKLMG.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Office IME 2010 Exit code: 1 Version: 14.0.4734.1000 Modules
| |||||||||||||||
| 2056 | "C:\Program Files\Common Files\microsoft shared\IME14\SHARED\IMEKLMG.EXE" /SetPreload /KOR /Log | C:\Program Files\Common Files\microsoft shared\IME14\SHARED\IMEKLMG.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Office IME 2010 Exit code: 1 Version: 14.0.4734.1000 Modules
| |||||||||||||||
| 2076 | "C:\Users\admin\autumn.exe" | C:\Users\admin\autumn.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Integrity Level: MEDIUM Description: YinYang Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
5 106
Read events
5 060
Write events
33
Delete events
13
Modification events
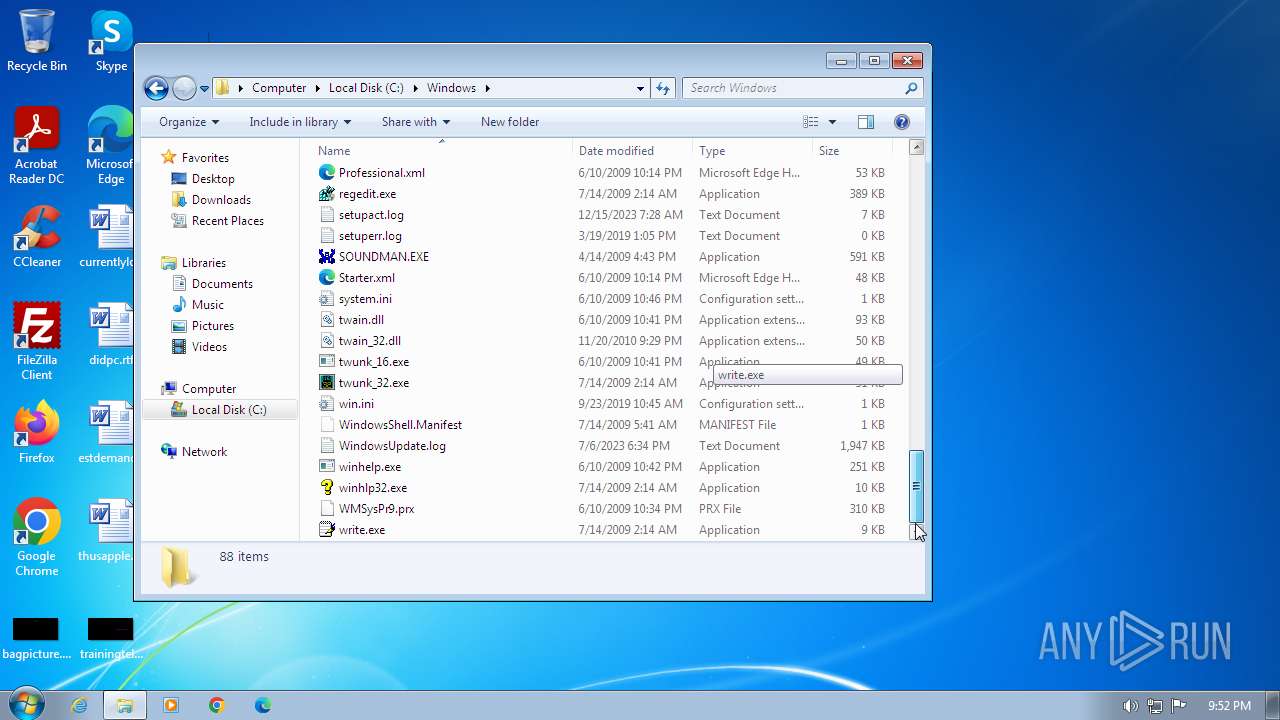
| (PID) Process: | (3392) file.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | WinDoctor |
Value: C:\Users\admin\autumn.exe | |||
| (PID) Process: | (796) control.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (796) control.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (796) control.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (796) control.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1460) ctfmon.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | internat.exe |
Value: | |||
| (PID) Process: | (1952) IMEKLMG.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\IMEJP\14.0 |
| Operation: | write | Name: | SetPreload |
Value: 1 | |||
| (PID) Process: | (2056) IMEKLMG.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\IMEKR\14.0 |
| Operation: | write | Name: | SetPreload |
Value: 1 | |||
| (PID) Process: | (1680) sipnotify.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1680) sipnotify.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\EnterpriseCertificates\Root\Certificates |
| Operation: | delete value | Name: | 9F6134C5FA75E4FDDE631B232BE961D6D4B97DB6 |
Value: | |||
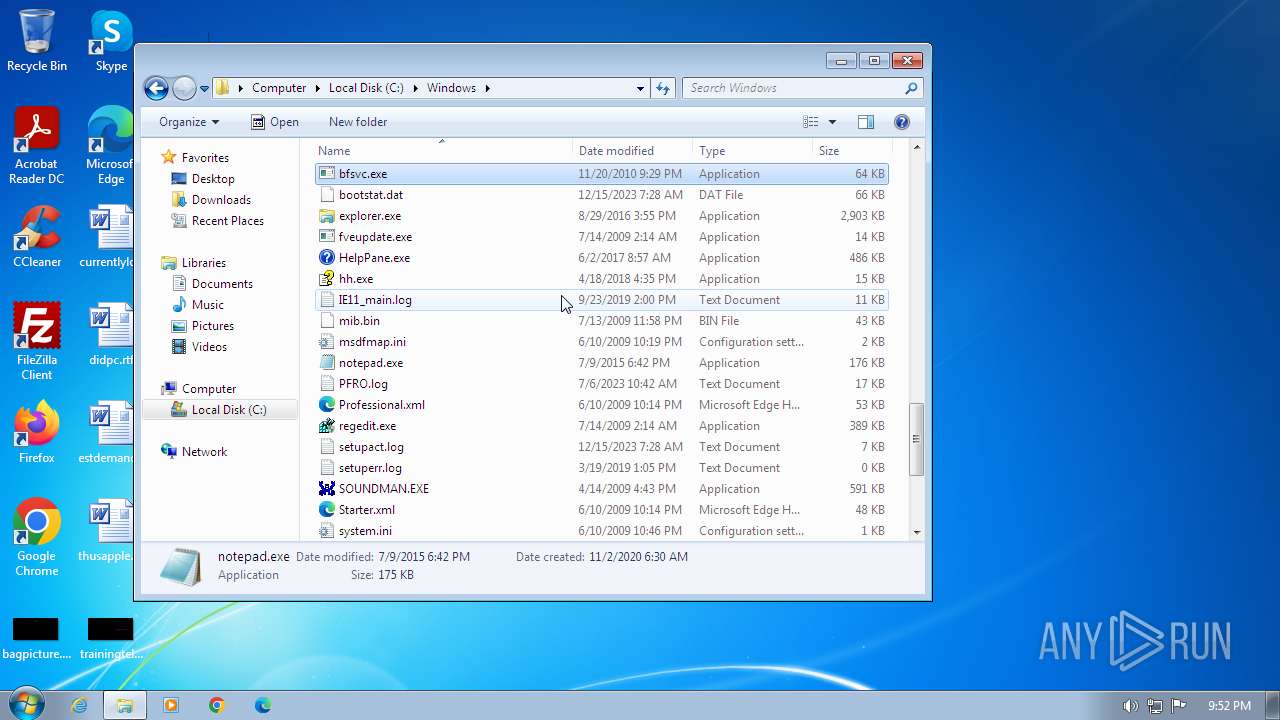
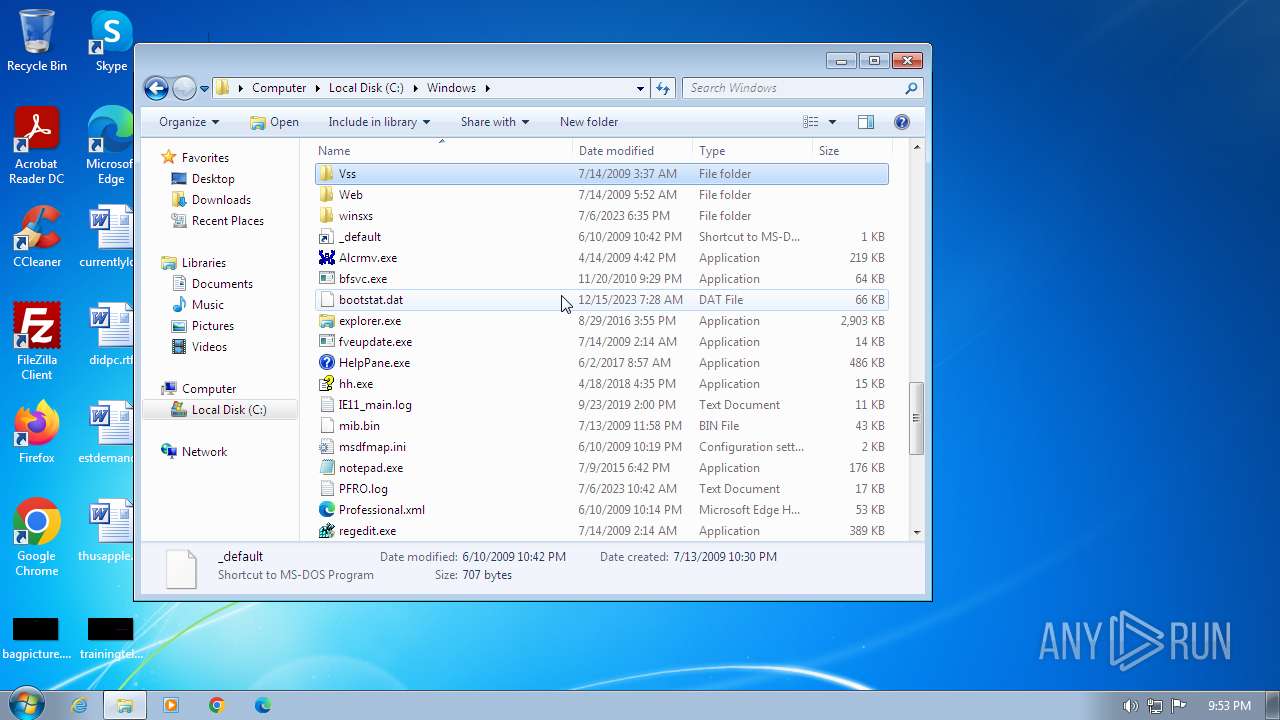
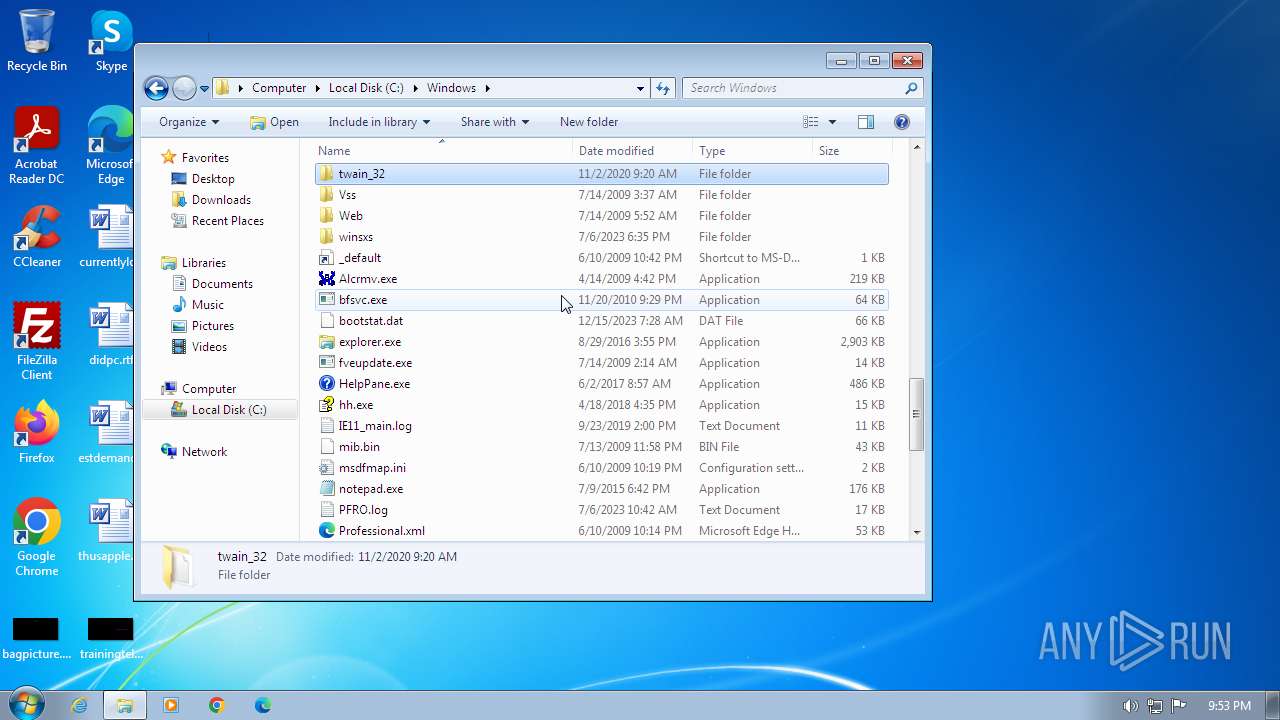
Executable files
2 816
Suspicious files
1
Text files
6
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
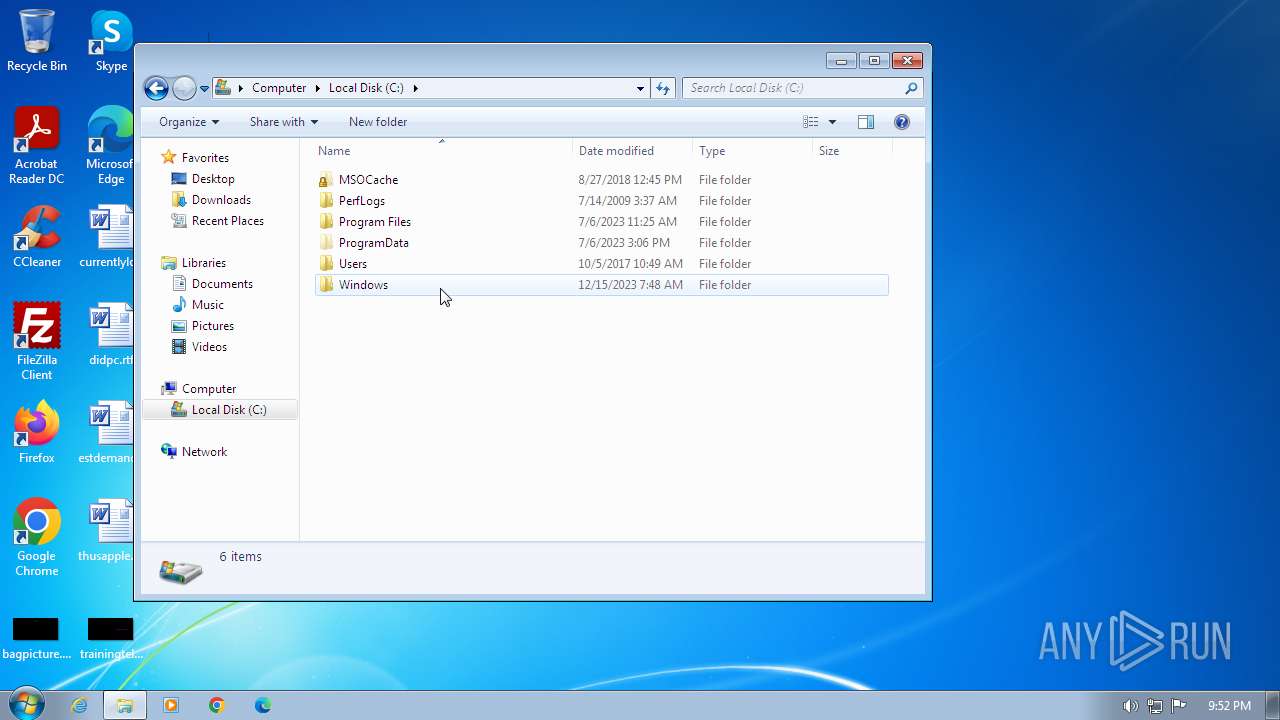
| 2968 | file.exe | C:\$Recycle.Bin\S-1-5-21-1302019708-1500728564-335382590-1000\desktop.ini.exe | executable | |
MD5:— | SHA256:— | |||
| 2968 | file.exe | C:\MSOCache\All Users\{90140000-0015-0407-0000-0000000FF1CE}-C\AccessMUI.msi.exe | executable | |
MD5:— | SHA256:— | |||
| 2968 | file.exe | C:\MSOCache\All Users\{90140000-0015-0407-0000-0000000FF1CE}-C\AccessMUI.xml.exe | executable | |
MD5:— | SHA256:— | |||
| 2968 | file.exe | C:\MSOCache\All Users\{90140000-0015-0407-0000-0000000FF1CE}-C\AccLR.cab.exe | executable | |
MD5:— | SHA256:— | |||
| 2968 | file.exe | C:\MSOCache\All Users\{90140000-0015-0407-0000-0000000FF1CE}-C\branding.xml.exe | executable | |
MD5:— | SHA256:— | |||
| 2968 | file.exe | C:\MSOCache\All Users\{90140000-0015-0407-0000-0000000FF1CE}-C\Setup.xml.exe | executable | |
MD5:— | SHA256:— | |||
| 2968 | file.exe | C:\MSOCache\All Users\{90140000-0015-040C-0000-0000000FF1CE}-C\AccessMUI.msi.exe | executable | |
MD5:— | SHA256:— | |||
| 2968 | file.exe | C:\MSOCache\All Users\{90140000-0015-040C-0000-0000000FF1CE}-C\AccessMUI.xml.exe | executable | |
MD5:— | SHA256:— | |||
| 2968 | file.exe | C:\MSOCache\All Users\{90140000-0015-040C-0000-0000000FF1CE}-C\AccLR.cab.exe | executable | |
MD5:— | SHA256:— | |||
| 2968 | file.exe | C:\MSOCache\All Users\{90140000-0015-040C-0000-0000000FF1CE}-C\branding.xml.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
9
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1680 | sipnotify.exe | HEAD | 200 | 88.221.61.151:80 | http://query.prod.cms.rt.microsoft.com/cms/api/am/binary/RE2JgkA?v=133564820178120000 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | unknown |
4 | System | 192.168.100.255:137 | — | — | — | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1680 | sipnotify.exe | 88.221.61.151:80 | query.prod.cms.rt.microsoft.com | AKAMAI-AS | DE | unknown |
1132 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
query.prod.cms.rt.microsoft.com |
| whitelisted |