| File name: | Rz_Laun v_3.43 Setup.exe |
| Full analysis: | https://app.any.run/tasks/c1da47b1-d91f-4022-9bc4-9189b2175413 |
| Verdict: | Malicious activity |
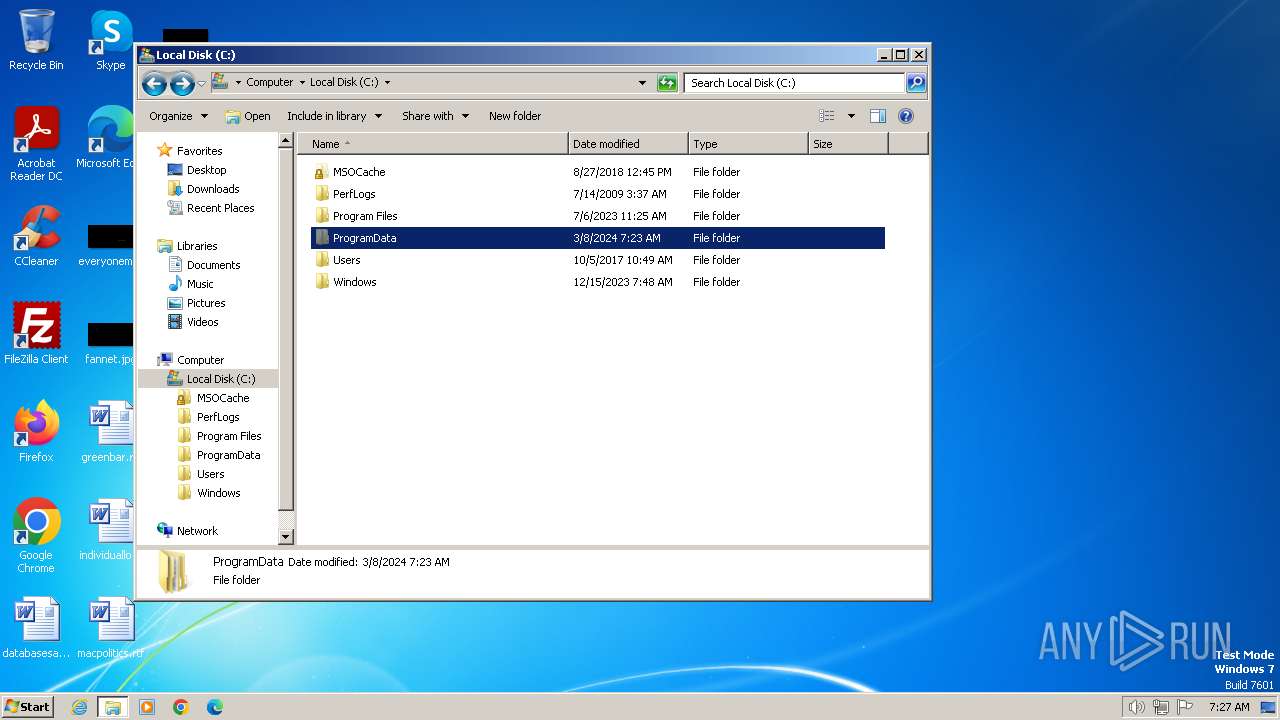
| Analysis date: | March 08, 2024, 07:23:43 |
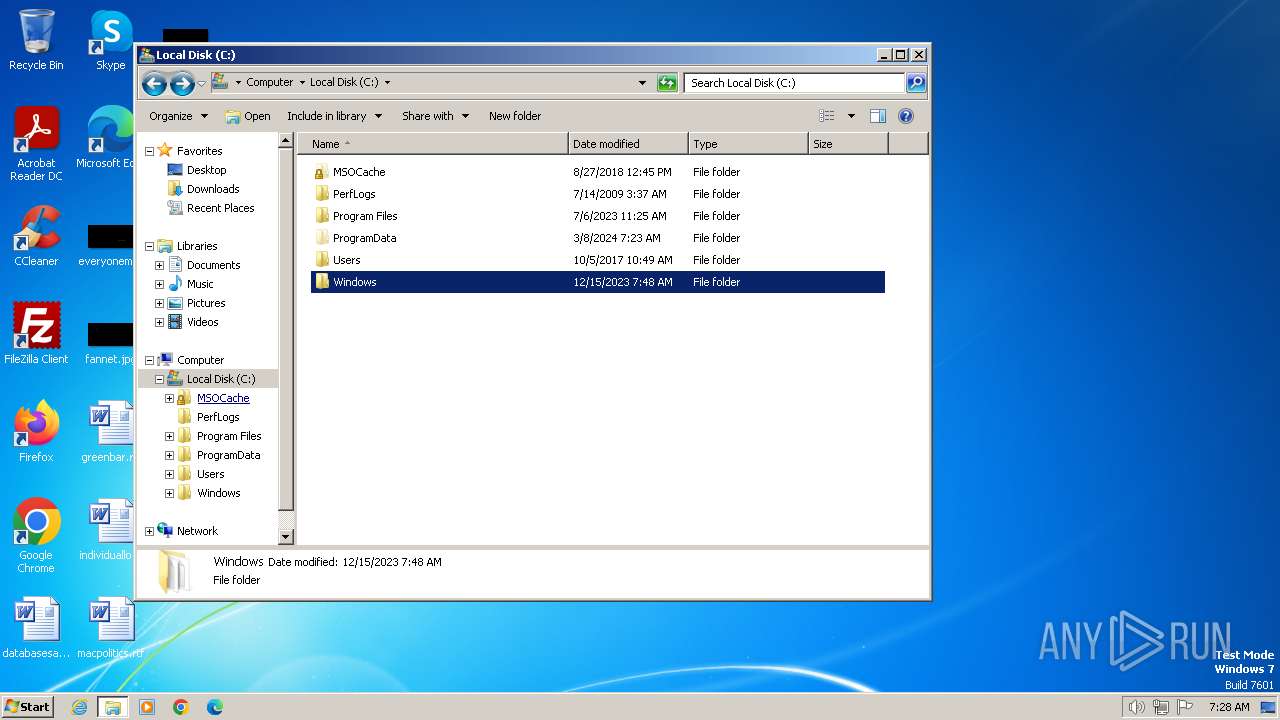
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 231D907F0BE80F1DB15CE824B39E34F1 |
| SHA1: | 25E89B9BEFE180B7D71B9E16D9F5858FD72E98EC |
| SHA256: | 867A6F31E58A0BD2F070B0812A5E898DB19C220B0BD4EC8AFC273319D9059F71 |
| SSDEEP: | 24576:Q3HzLnqOaNMCFJ6kPvOxrcg0i7uFZXls9:Q3HzLnqOaNMCFJ6kPvO1cg0i72ls9 |
MALICIOUS
Drops the executable file immediately after the start
- Rz_Laun v_3.43 Setup.exe (PID: 3772)
Changes the autorun value in the registry
- Rz_Laun v_3.43 Setup.exe (PID: 3772)
Connects to the CnC server
- Synaptics.exe (PID: 3460)
SUSPICIOUS
Reads security settings of Internet Explorer
- Rz_Laun v_3.43 Setup.exe (PID: 3772)
- Synaptics.exe (PID: 3460)
Reads the date of Windows installation
- Rz_Laun v_3.43 Setup.exe (PID: 3772)
Reads the Internet Settings
- Rz_Laun v_3.43 Setup.exe (PID: 3772)
- Synaptics.exe (PID: 3460)
Executable content was dropped or overwritten
- Rz_Laun v_3.43 Setup.exe (PID: 3772)
Checks for Java to be installed
- ._cache_Rz_Laun v_3.43 Setup.exe (PID: 3848)
Reads settings of System Certificates
- Synaptics.exe (PID: 3460)
Connects to unusual port
- Synaptics.exe (PID: 3460)
Checks Windows Trust Settings
- Synaptics.exe (PID: 3460)
INFO
Checks supported languages
- javaw.exe (PID: 3948)
- ._cache_Rz_Laun v_3.43 Setup.exe (PID: 3848)
- Rz_Laun v_3.43 Setup.exe (PID: 3772)
- Synaptics.exe (PID: 3460)
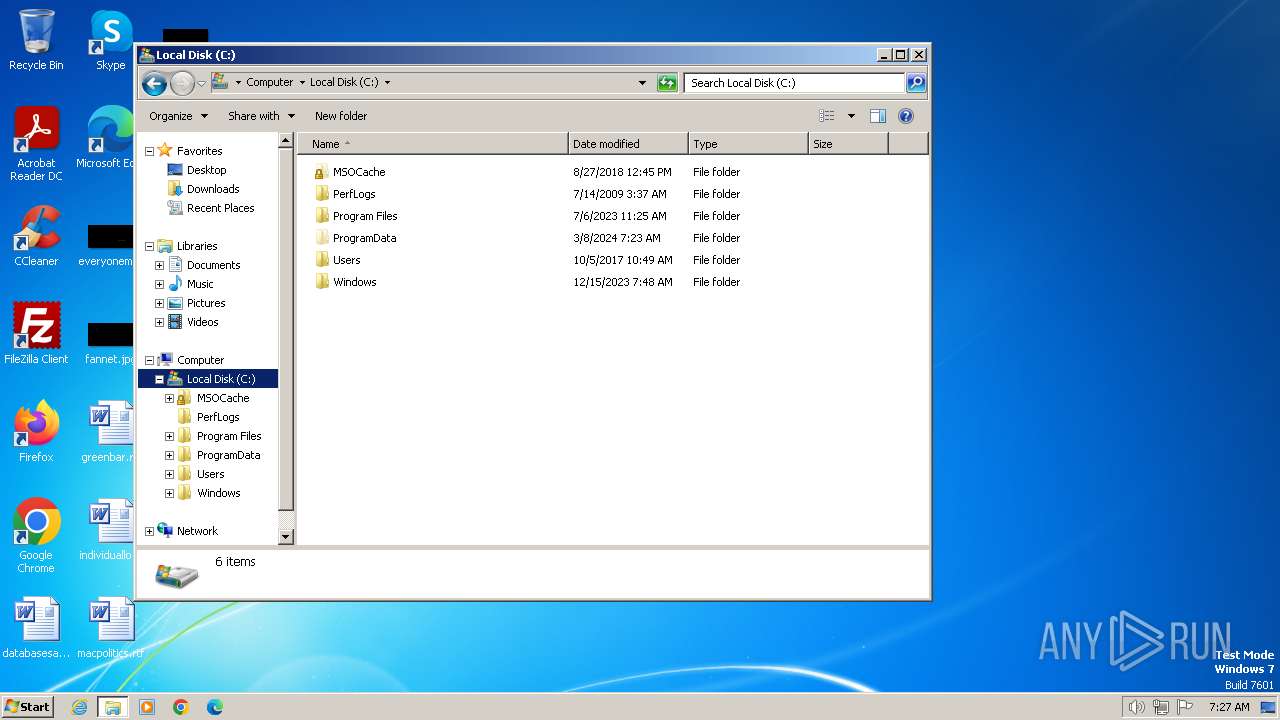
Creates files in the program directory
- Rz_Laun v_3.43 Setup.exe (PID: 3772)
- javaw.exe (PID: 3948)
- Synaptics.exe (PID: 3460)
Reads the machine GUID from the registry
- Rz_Laun v_3.43 Setup.exe (PID: 3772)
- Synaptics.exe (PID: 3460)
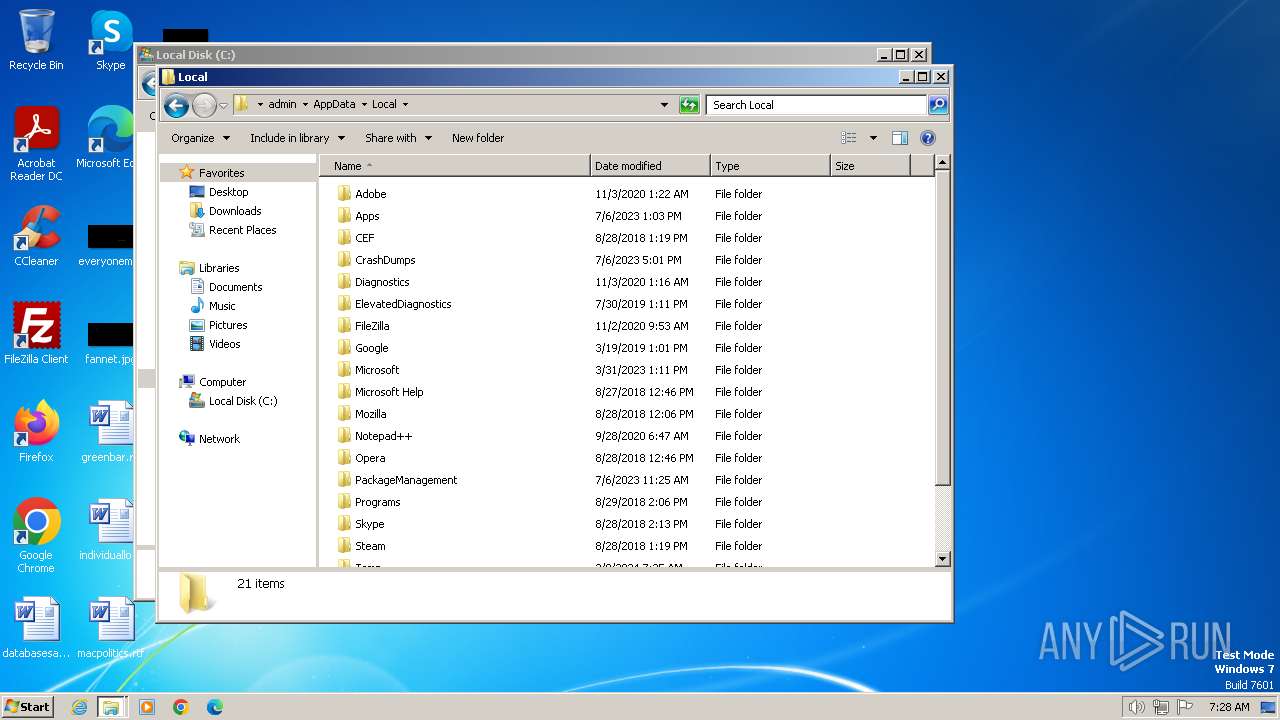
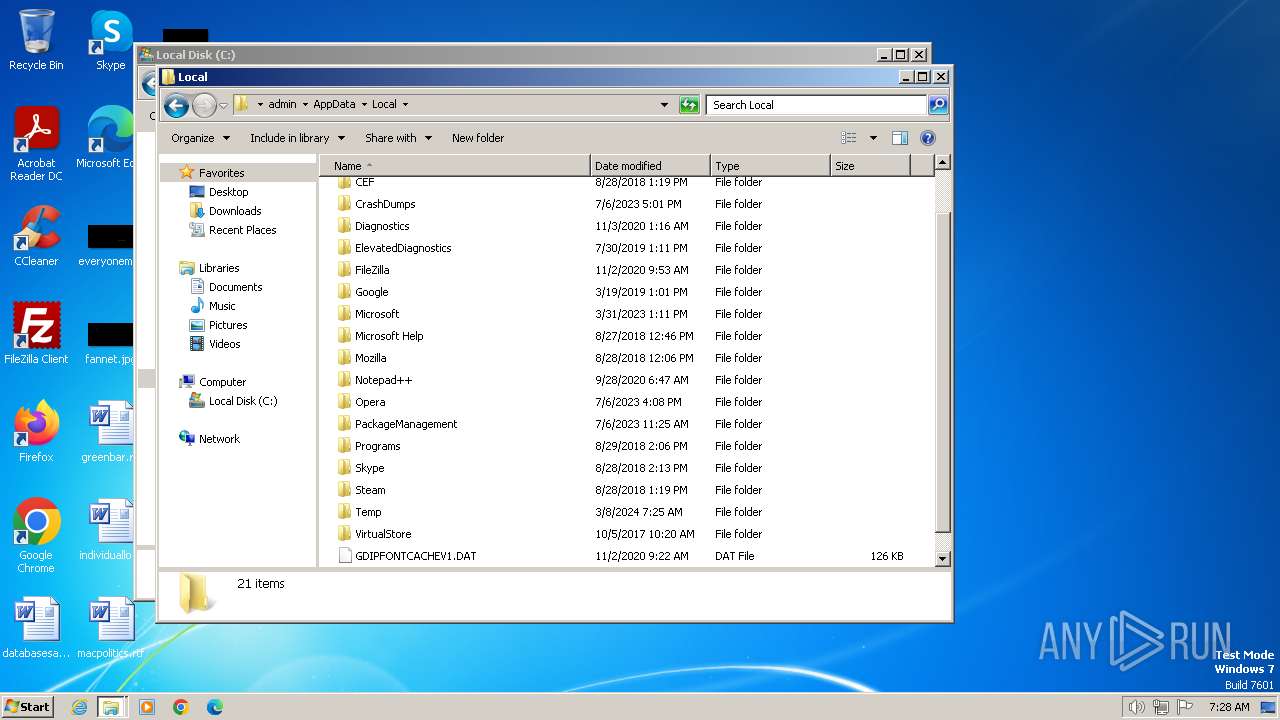
Create files in a temporary directory
- Rz_Laun v_3.43 Setup.exe (PID: 3772)
- javaw.exe (PID: 3948)
- Synaptics.exe (PID: 3460)
Reads the computer name
- Rz_Laun v_3.43 Setup.exe (PID: 3772)
- Synaptics.exe (PID: 3460)
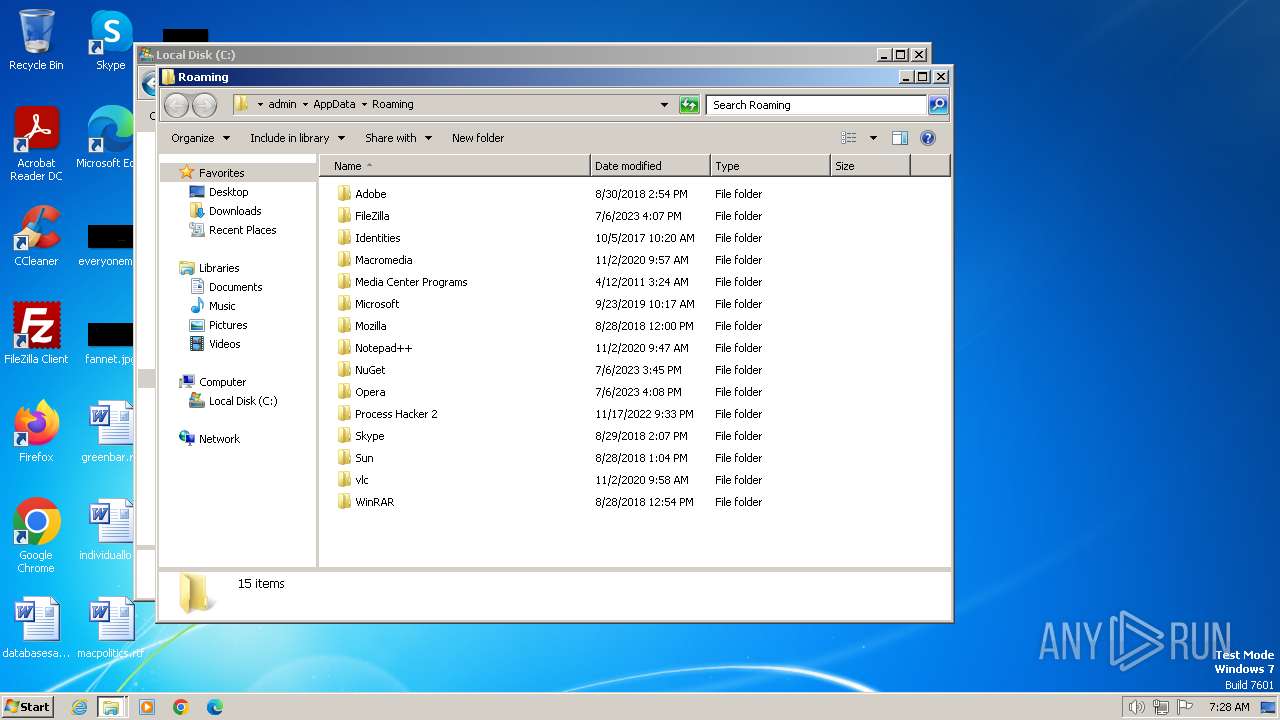
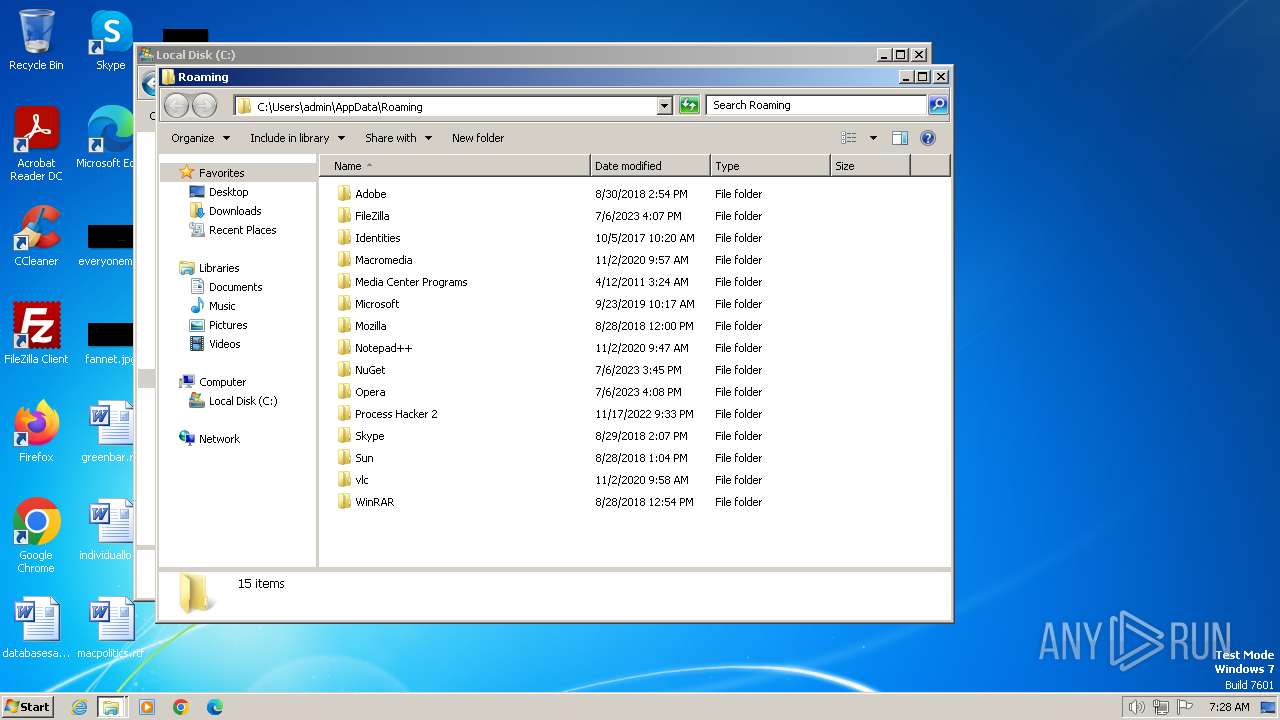
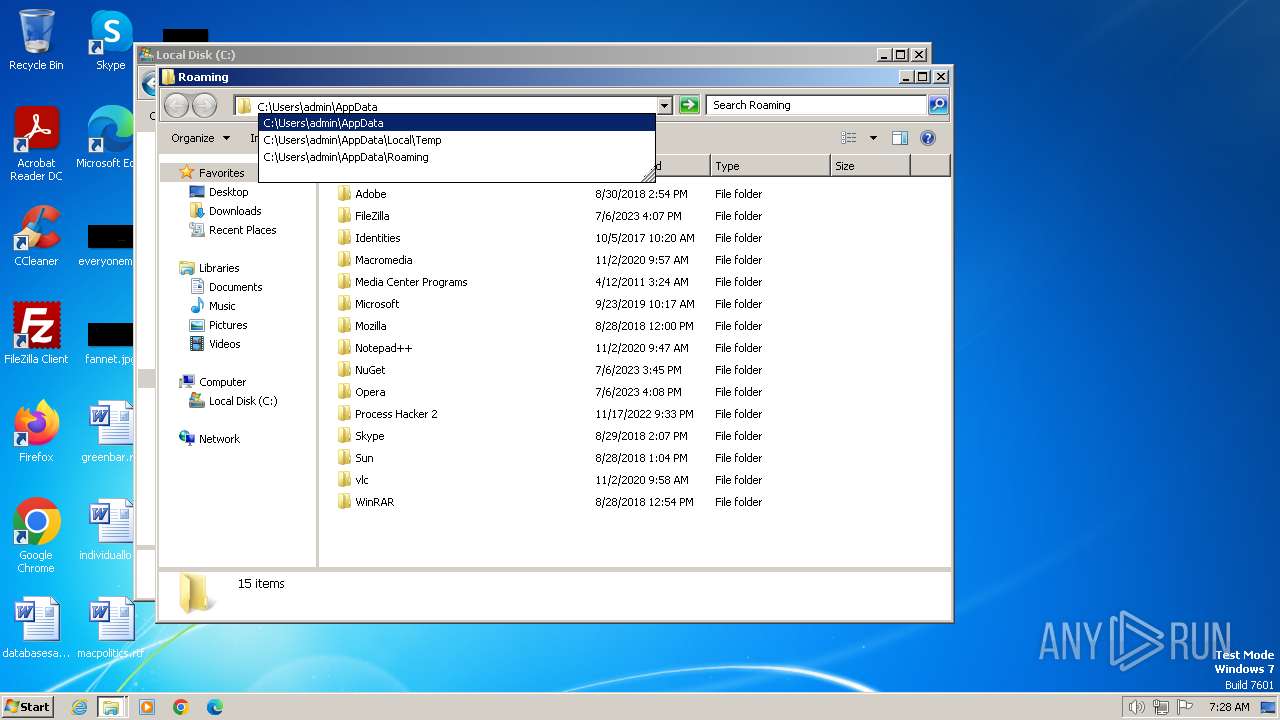
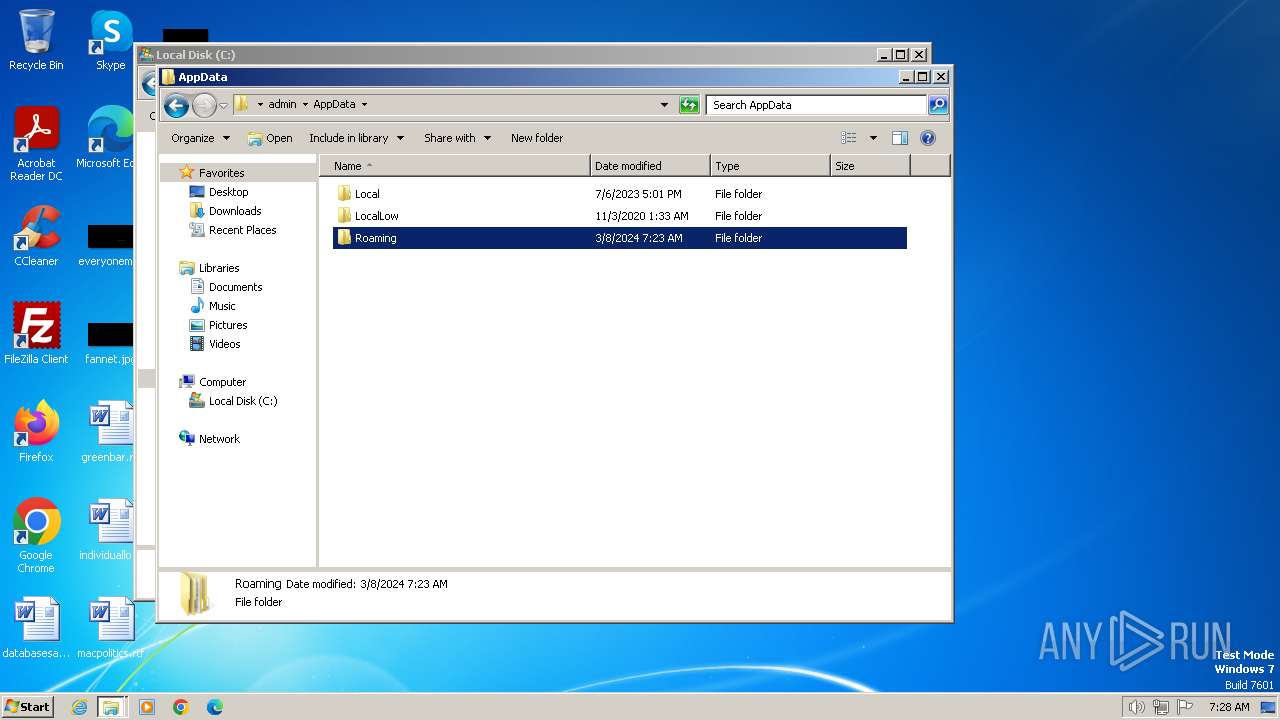
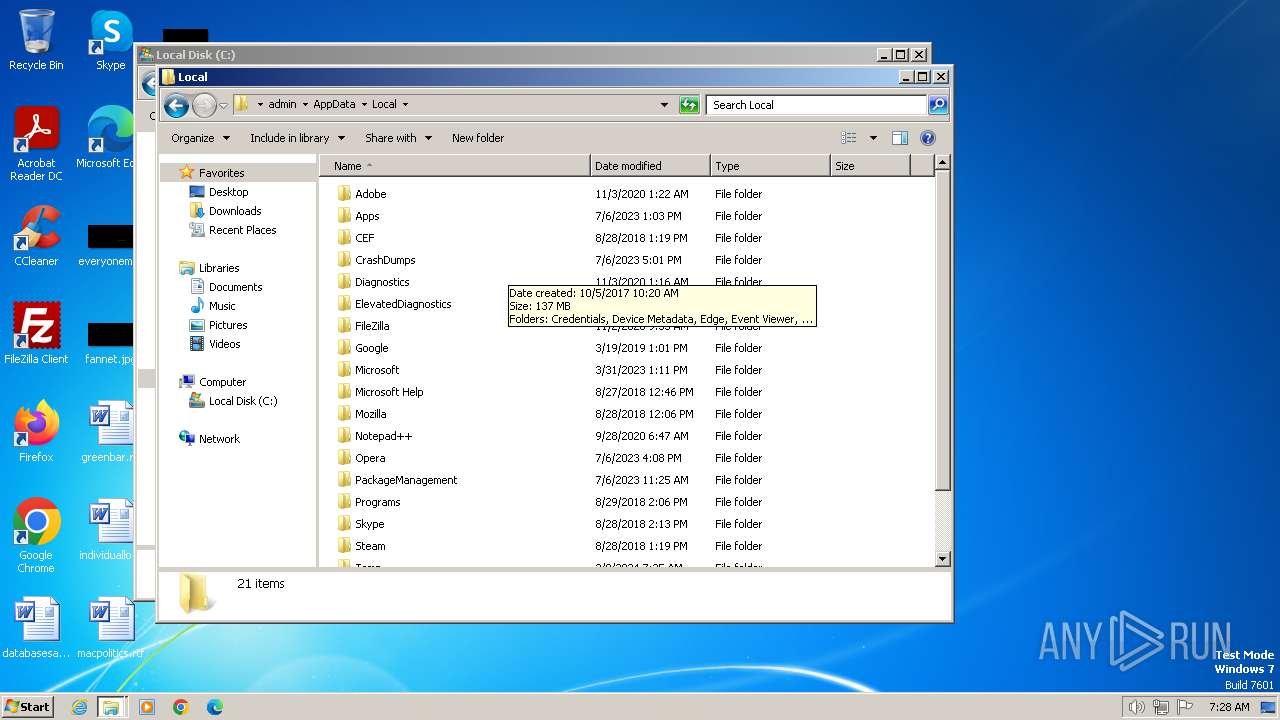
Creates files or folders in the user directory
- Synaptics.exe (PID: 3460)
Checks proxy server information
- Synaptics.exe (PID: 3460)
Reads the software policy settings
- Synaptics.exe (PID: 3460)
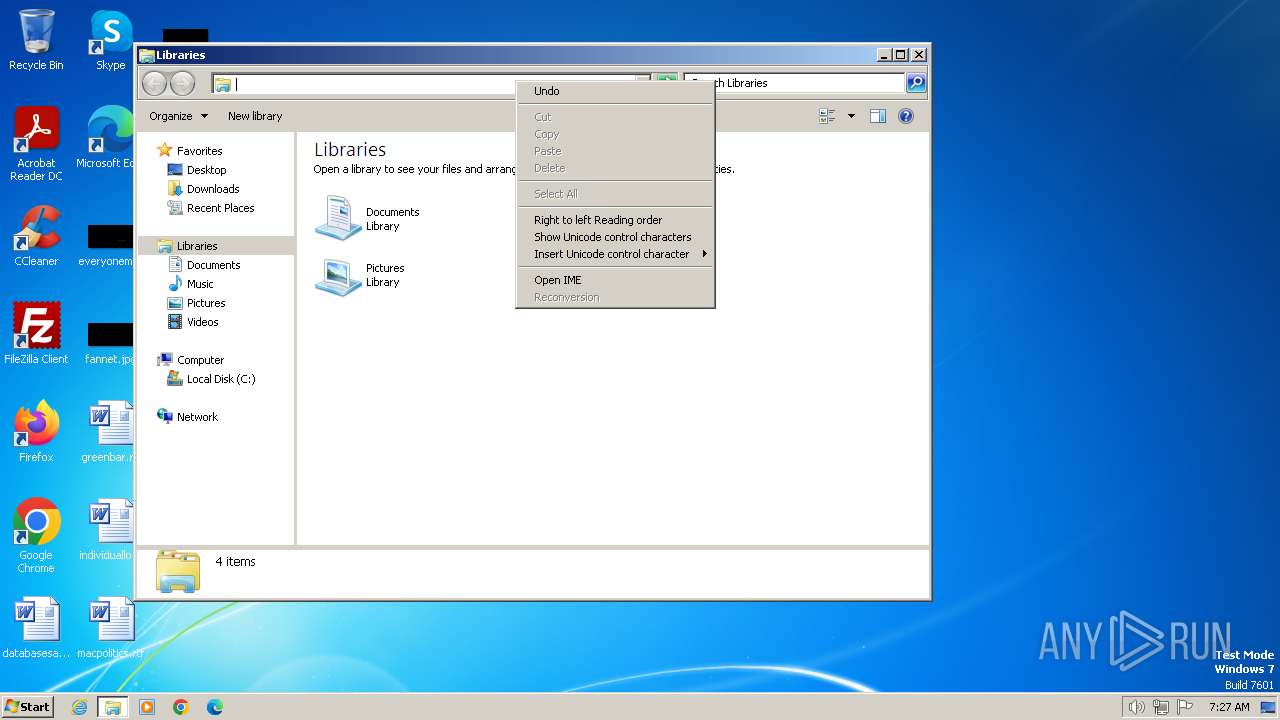
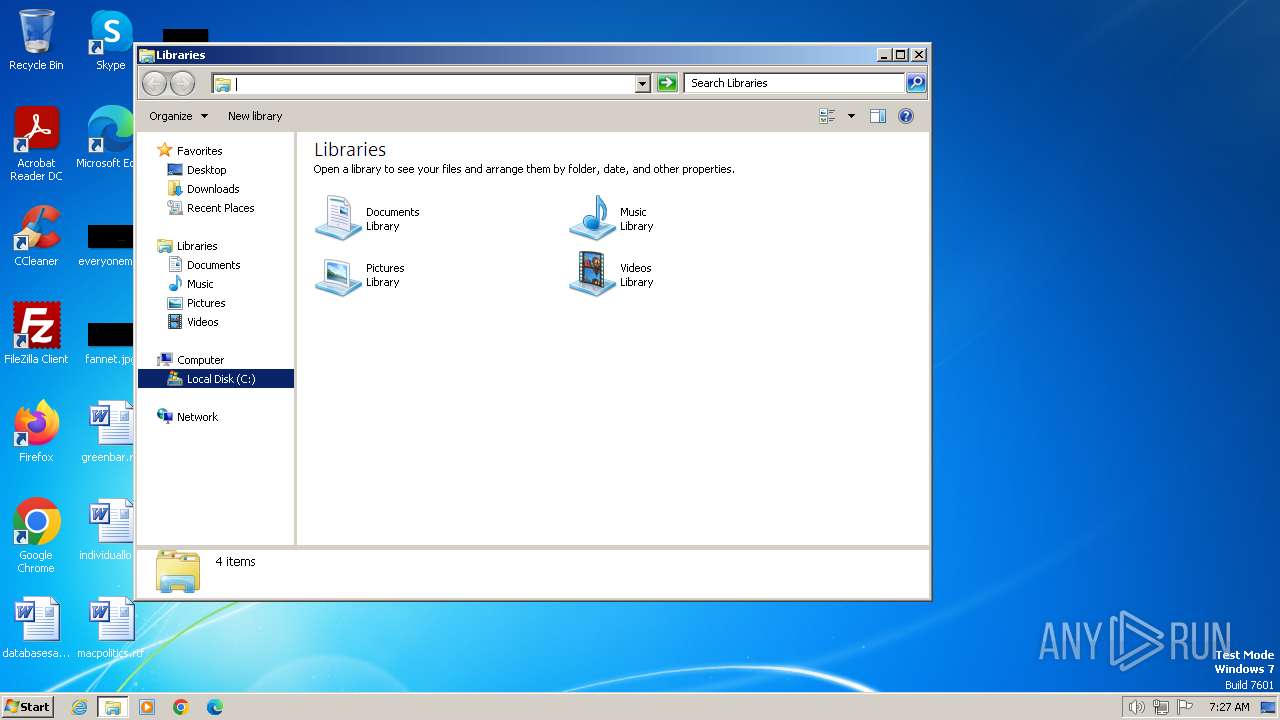
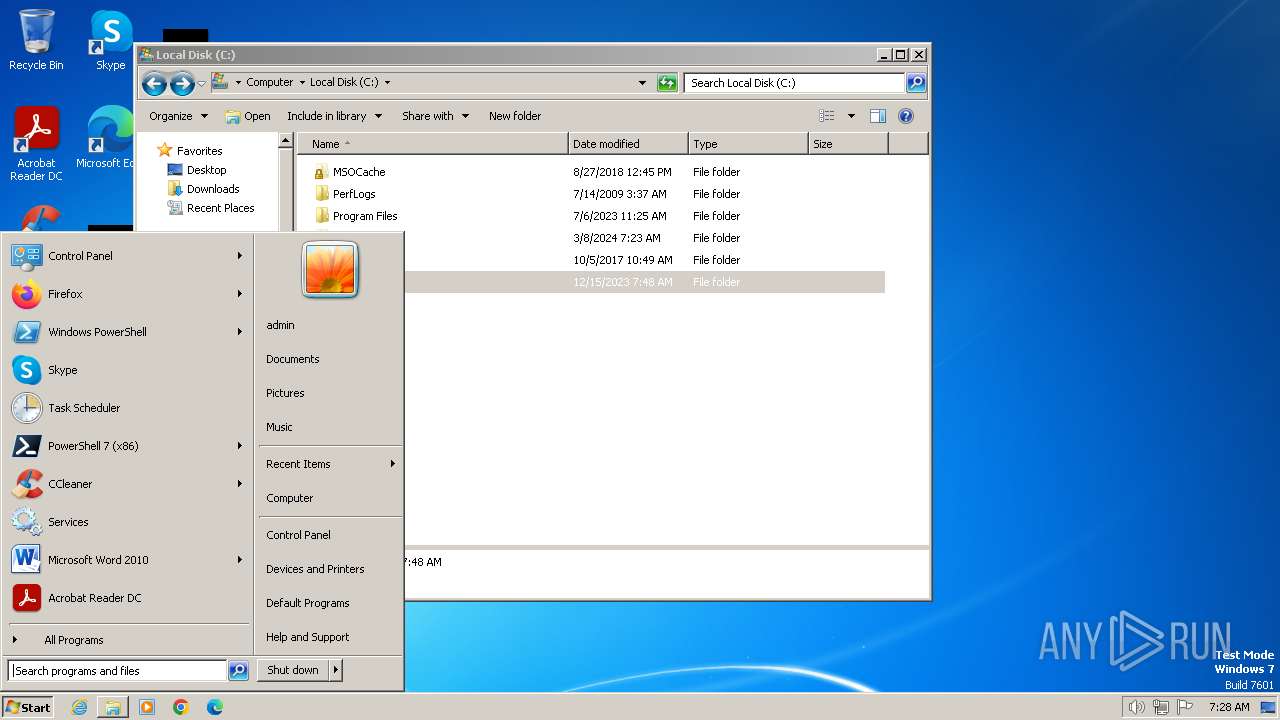
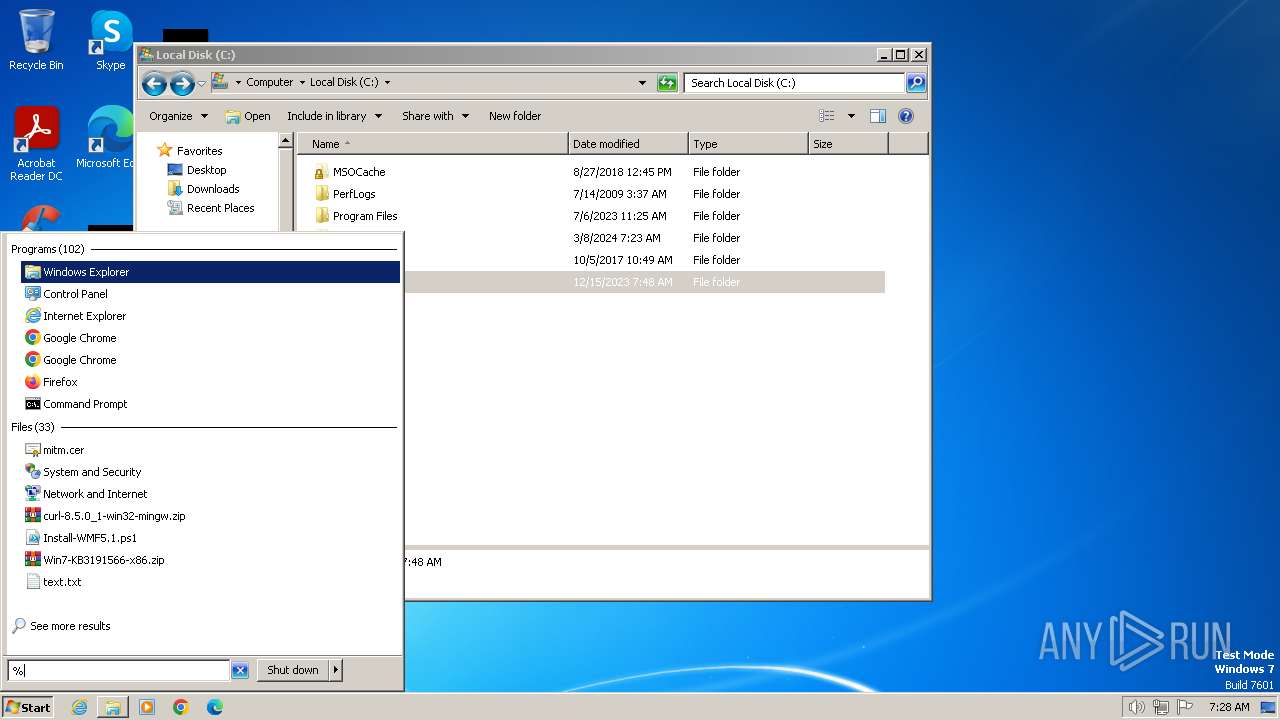
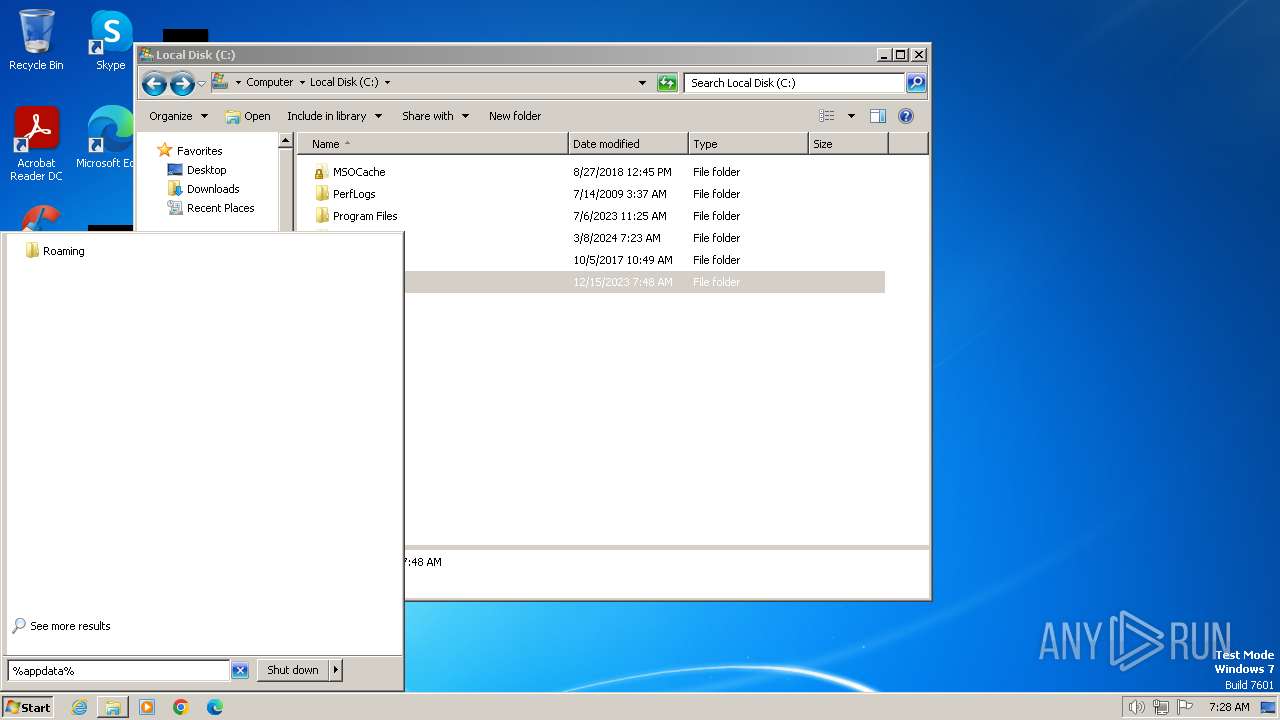
Manual execution by a user
- explorer.exe (PID: 2904)
- verclsid.exe (PID: 752)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Borland Delphi 7 (96.4) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (2) |
| .exe | | | Win32 Executable (generic) (0.6) |
| .exe | | | Win16/32 Executable Delphi generic (0.3) |
| .exe | | | Generic Win/DOS Executable (0.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:19 22:22:17+00:00 |
| ImageFileCharacteristics: | Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 629760 |
| InitializedDataSize: | 459776 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x9ab80 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.4 |
| ProductVersionNumber: | 1.0.0.4 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Turkish |
| CharacterSet: | Windows, Turkish |
| CompanyName: | Synaptics |
| FileDescription: | Synaptics Pointing Device Driver |
| FileVersion: | 1.0.0.4 |
| InternalName: | - |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFileName: | - |
| ProductName: | Synaptics Pointing Device Driver |
| ProductVersion: | 1.0.0.0 |
| Comments: | - |
Total processes
51
Monitored processes
8
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
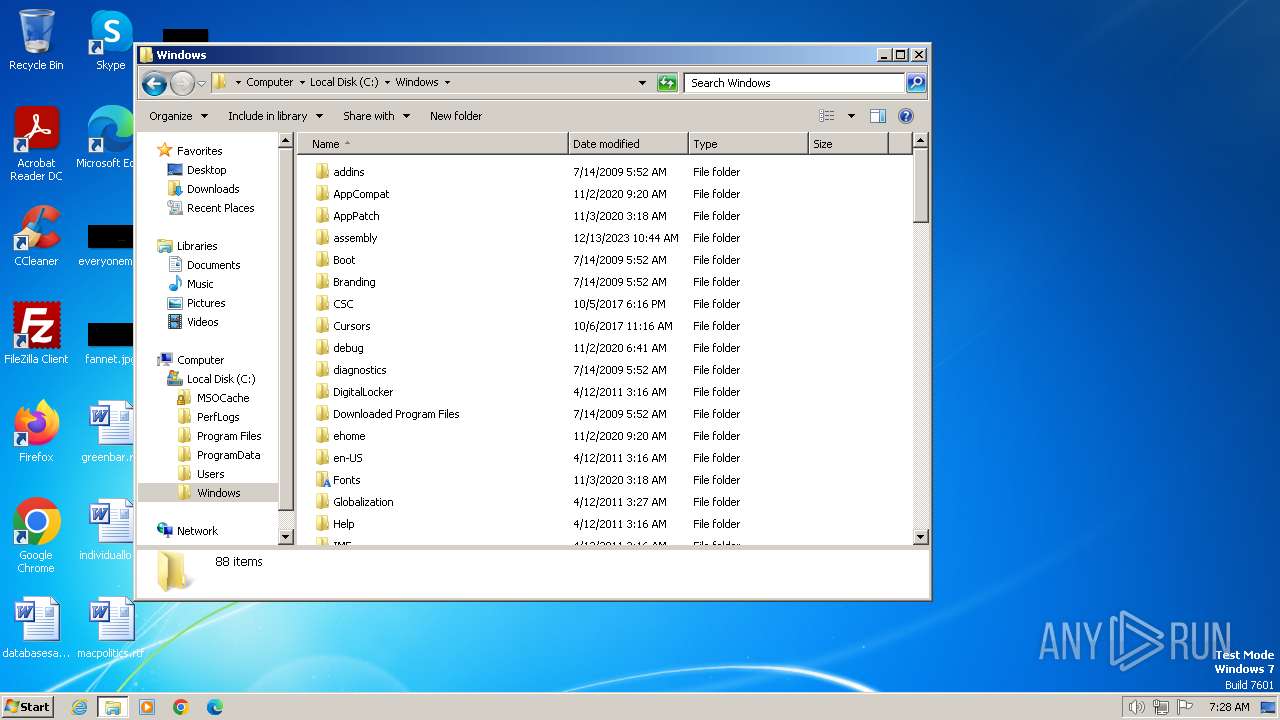
| 752 | "C:\Windows\system32\verclsid.exe" /S /C {0B2C9183-C9FA-4C53-AE21-C900B0C39965} /I {0C733A8A-2A1C-11CE-ADE5-00AA0044773D} /X 0x401 | C:\Windows\System32\verclsid.exe | — | explorer.exe | |||||||||||
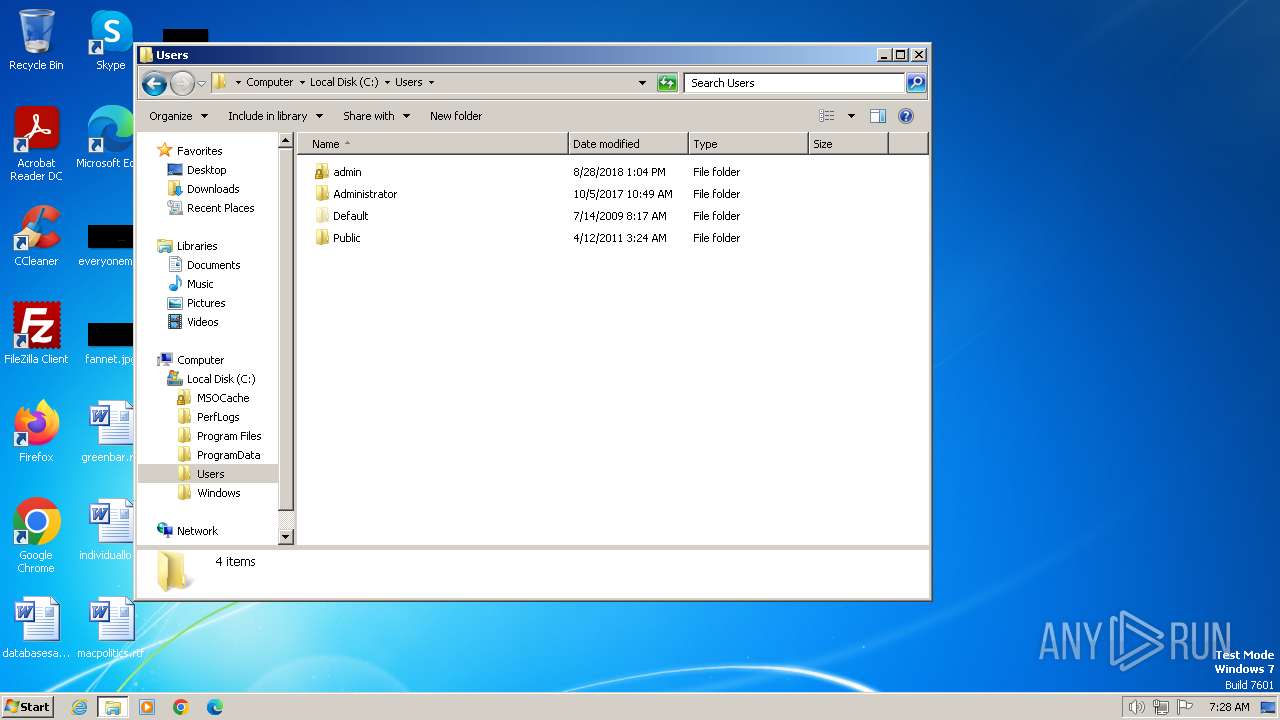
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Extension CLSID Verification Host Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2904 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
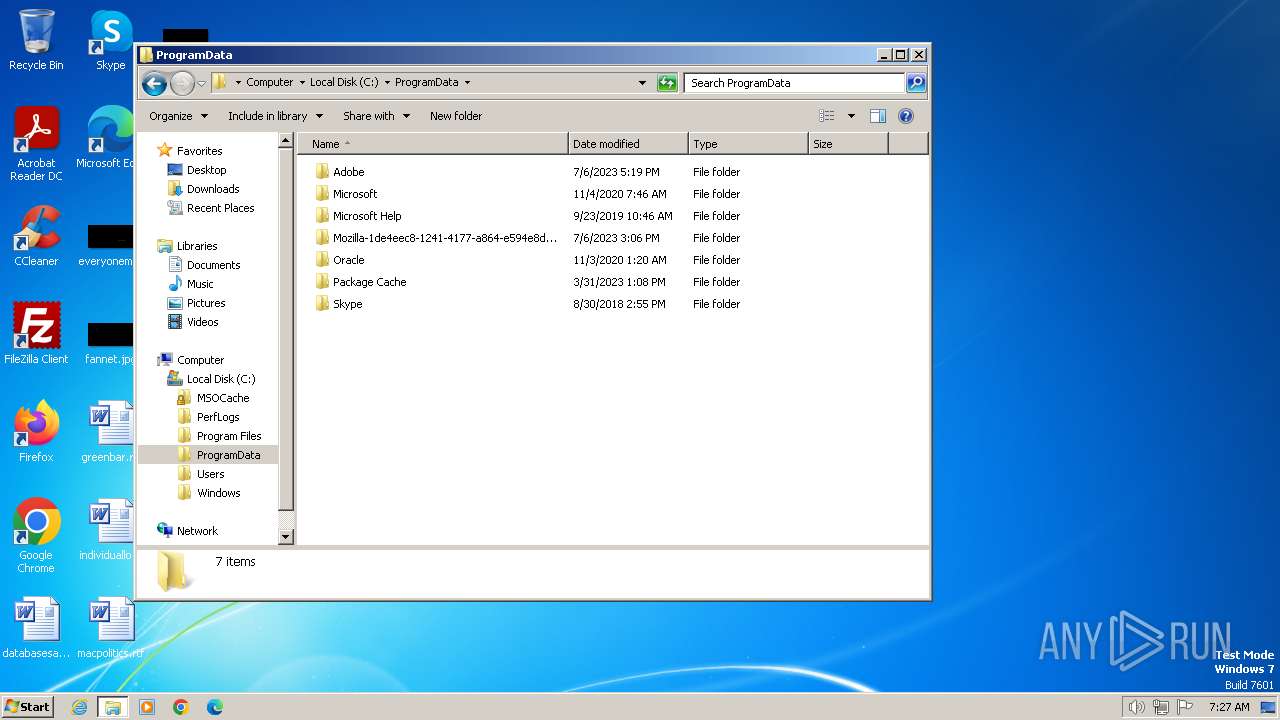
| 3460 | "C:\ProgramData\Synaptics\Synaptics.exe" InjUpdate | C:\ProgramData\Synaptics\Synaptics.exe | Rz_Laun v_3.43 Setup.exe | ||||||||||||
User: admin Company: Synaptics Integrity Level: HIGH Description: Synaptics Pointing Device Driver Exit code: 0 Version: 1.0.0.4 Modules
| |||||||||||||||
| 3500 | C:\Windows\system32\icacls.exe C:\ProgramData\Oracle\Java\.oracle_jre_usage /grant "everyone":(OI)(CI)M | C:\Windows\System32\icacls.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3668 | "C:\Users\admin\AppData\Local\Temp\Rz_Laun v_3.43 Setup.exe" | C:\Users\admin\AppData\Local\Temp\Rz_Laun v_3.43 Setup.exe | — | explorer.exe | |||||||||||
User: admin Company: Synaptics Integrity Level: MEDIUM Description: Synaptics Pointing Device Driver Exit code: 3221226540 Version: 1.0.0.4 Modules
| |||||||||||||||
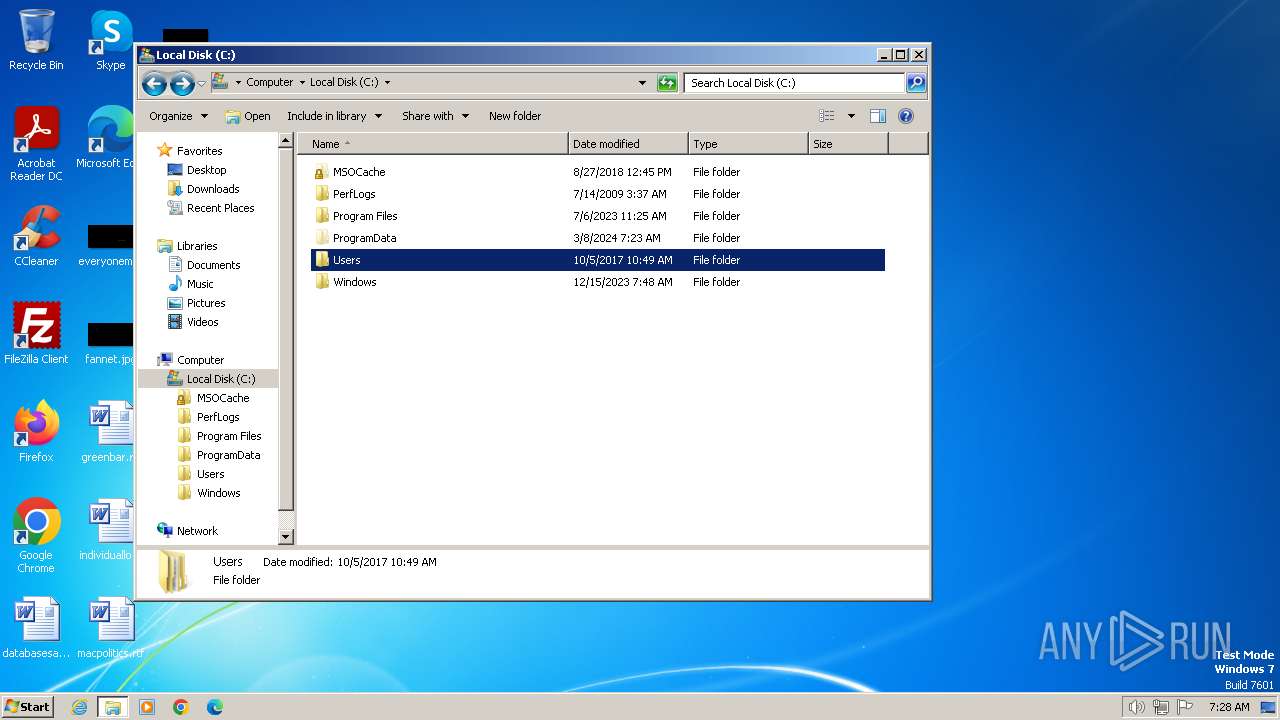
| 3772 | "C:\Users\admin\AppData\Local\Temp\Rz_Laun v_3.43 Setup.exe" | C:\Users\admin\AppData\Local\Temp\Rz_Laun v_3.43 Setup.exe | explorer.exe | ||||||||||||
User: admin Company: Synaptics Integrity Level: HIGH Description: Synaptics Pointing Device Driver Exit code: 0 Version: 1.0.0.4 Modules
| |||||||||||||||
| 3848 | "C:\Users\admin\AppData\Local\Temp\._cache_Rz_Laun v_3.43 Setup.exe" | C:\Users\admin\AppData\Local\Temp\._cache_Rz_Laun v_3.43 Setup.exe | — | Rz_Laun v_3.43 Setup.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3948 | "C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe" -Dfile.encoding=UTF-8 -classpath " org.develnext.jphp.ext.javafx.FXLauncher | C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe | — | ._cache_Rz_Laun v_3.43 Setup.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: HIGH Description: Java(TM) Platform SE binary Exit code: 1 Version: 8.0.2710.9 Modules
| |||||||||||||||
Total events
9 566
Read events
9 454
Write events
103
Delete events
9
Modification events
| (PID) Process: | (3772) Rz_Laun v_3.43 Setup.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3772) Rz_Laun v_3.43 Setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3772) Rz_Laun v_3.43 Setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3772) Rz_Laun v_3.43 Setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3772) Rz_Laun v_3.43 Setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3772) Rz_Laun v_3.43 Setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Synaptics Pointing Device Driver |
Value: C:\ProgramData\Synaptics\Synaptics.exe | |||
| (PID) Process: | (3460) Synaptics.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3460) Synaptics.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | ProxyServer |
Value: | |||
| (PID) Process: | (3460) Synaptics.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | ProxyOverride |
Value: | |||
| (PID) Process: | (3460) Synaptics.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | AutoConfigURL |
Value: | |||
Executable files
4
Suspicious files
5
Text files
3
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3772 | Rz_Laun v_3.43 Setup.exe | C:\ProgramData\Synaptics\RCXF5F8.tmp | executable | |
MD5:2600C3DBB5DCD181749CBD948D3C5C96 | SHA256:438A3EF647E0575C55CEACD4E3AC73048507D8F6927223719E1A6AB869D0641F | |||
| 3460 | Synaptics.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CAF4703619713E3F18D8A9D5D88D6288_A7725538C46DE2D0088EE44974E2CEBA | der | |
MD5:AC89A852C2AAA3D389B2D2DD312AD367 | SHA256:0B720E19270C672F9B6E0EC40B468AC49376807DE08A814573FE038779534F45 | |||
| 3460 | Synaptics.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\F07644E38ED7C9F37D11EEC6D4335E02_08872284D8414653D8A6B617C1164F2D | binary | |
MD5:A9F0DC2701BFEA7F8FB647F2F488C1E5 | SHA256:8678DA3170A66E3868AEB00D696C43113F77BBD1861C9BD95A81CF29C6DF2A29 | |||
| 3772 | Rz_Laun v_3.43 Setup.exe | C:\ProgramData\Synaptics\Synaptics.exe | executable | |
MD5:231D907F0BE80F1DB15CE824B39E34F1 | SHA256:867A6F31E58A0BD2F070B0812A5E898DB19C220B0BD4EC8AFC273319D9059F71 | |||
| 3460 | Synaptics.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:4E6B8A831FBA627932D0505E9179AA6A | SHA256:40A0D6B4AAB1E3ED3C786E3A73BD76AE48F2064748C7D0DEA6D288320753A332 | |||
| 3460 | Synaptics.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\F07644E38ED7C9F37D11EEC6D4335E02_08872284D8414653D8A6B617C1164F2D | der | |
MD5:E709DAFA6EAA93971B4685D2BE653E6A | SHA256:D001FF5E362CD5625E417E9A08E54F5A0775F49C7A56DE5CAAD9731ED3ECAA58 | |||
| 3460 | Synaptics.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | der | |
MD5:5ECFEF2DF434C73C08D36275DDBA5749 | SHA256:84491AB7F3FB1E79AF631892913ABF4EC95DE721C4F940300D69093AE1E689DD | |||
| 3460 | Synaptics.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\F2DDCD2B5F37625B82E81F4976CEE400_2517452929F0CAF6449847D40B7C277D | binary | |
MD5:FD7284B206B8C0B5315286E5D9A13BAB | SHA256:DF0AB521F07DF5ADF2EDCCF181D1938FC743C930E626F9A3EA002CFF2CFA066B | |||
| 3772 | Rz_Laun v_3.43 Setup.exe | C:\Users\admin\AppData\Local\Temp\._cache_Rz_Laun v_3.43 Setup.exe | executable | |
MD5:E44D7AA359A13D3B757D635DA9BBFCA9 | SHA256:CD78ADE636555E668FD38C6DD9644FD1F53BBD93EE0DD16B692567CEA0579345 | |||
| 3948 | javaw.exe | C:\ProgramData\Oracle\Java\.oracle_jre_usage\17dfc292991c8061.timestamp | text | |
MD5:AA262D67E8873137D81B255D3A680BE0 | SHA256:B1C68E3CC2AB7890B5598C6E81E96B4D1BC65C8705E4189C1116DE525C5D894B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
14
DNS requests
10
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3460 | Synaptics.exe | GET | 200 | 69.42.215.252:80 | http://freedns.afraid.org/api/?action=getdyndns&sha=a30fa98efc092684e8d1c5cff797bcc613562978 | unknown | text | 31 b | unknown |
3460 | Synaptics.exe | GET | — | 96.17.194.184:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?fd81cbc265c122d4 | unknown | — | — | unknown |
3460 | Synaptics.exe | GET | 200 | 142.250.186.67:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | unknown | binary | 1.41 Kb | unknown |
3460 | Synaptics.exe | GET | 200 | 142.250.186.67:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | unknown | binary | 724 b | unknown |
3460 | Synaptics.exe | GET | 200 | 142.250.186.67:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCRd4hKrA6aBAnnS3UYBsso | unknown | binary | 472 b | unknown |
1080 | svchost.exe | GET | — | 96.17.194.170:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?3e412f7b4eff0943 | unknown | — | — | unknown |
3460 | Synaptics.exe | GET | 200 | 142.250.186.67:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCECzpBwEAqmZNCdn%2B9lFcFjc%3D | unknown | binary | 471 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3460 | Synaptics.exe | 49.13.77.253:1199 | xred.mooo.com | Hetzner Online GmbH | DE | unknown |
3460 | Synaptics.exe | 69.42.215.252:80 | freedns.afraid.org | AWKNET | US | unknown |
3460 | Synaptics.exe | 216.58.212.142:443 | docs.google.com | GOOGLE | US | whitelisted |
3460 | Synaptics.exe | 96.17.194.184:80 | ctldl.windowsupdate.com | Akamai International B.V. | IN | unknown |
3460 | Synaptics.exe | 142.250.186.67:80 | ocsp.pki.goog | GOOGLE | US | whitelisted |
1080 | svchost.exe | 96.17.194.170:80 | ctldl.windowsupdate.com | Akamai International B.V. | IN | unknown |
3460 | Synaptics.exe | 142.250.185.129:443 | drive.usercontent.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
xred.mooo.com |
| unknown |
freedns.afraid.org |
| whitelisted |
docs.google.com |
| shared |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
drive.usercontent.google.com |
| unknown |
dns.msftncsi.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to Abused Domain *.mooo.com |
3 ETPRO signatures available at the full report