| File name: | RamCapturer.zip |
| Full analysis: | https://app.any.run/tasks/6b41d8ee-e355-4e71-861d-1c169e70d52c |
| Verdict: | Malicious activity |
| Analysis date: | May 05, 2020, 21:32:40 |
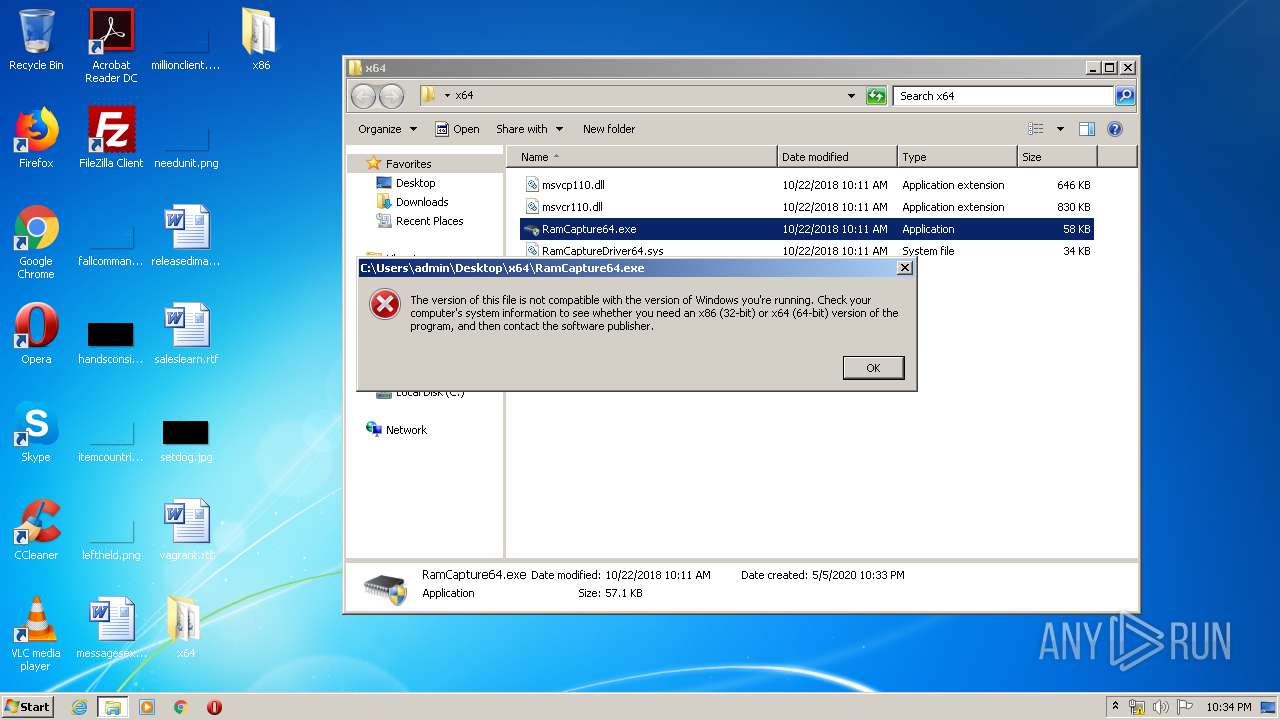
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 2527D00C1F1BFFABBC975B20CF2FEE29 |
| SHA1: | A2C0EED4F9FBD885AC1E1A5CC0543B125DD291A6 |
| SHA256: | 8673BDC896C8E8B4FBC992D9883A17281773F109A92C9A7FFBDBB63E8608E435 |
| SSDEEP: | 24576:8aQeIJN2EKZm+DWodEEt2R+9BbHqWVFlB7s2ncm9NBrqWJgS0wzsYmyy6OTz6LHS:uLI9d7M3nS0wSEHnhr6fBbuCWakNc |
MALICIOUS
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 2460)
- RamCapture.exe (PID: 1604)
Application was dropped or rewritten from another process
- RamCapture.exe (PID: 1604)
- RamCapture.exe (PID: 3444)
SUSPICIOUS
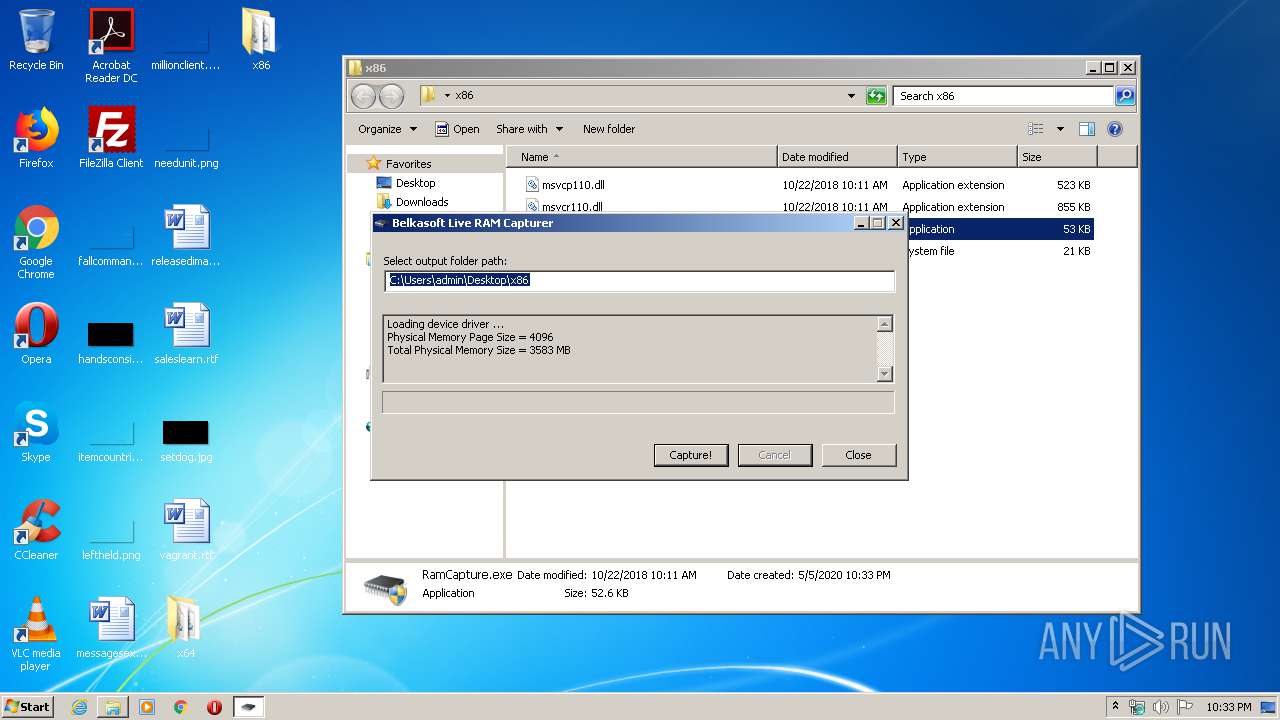
Creates or modifies windows services
- RamCapture.exe (PID: 1604)
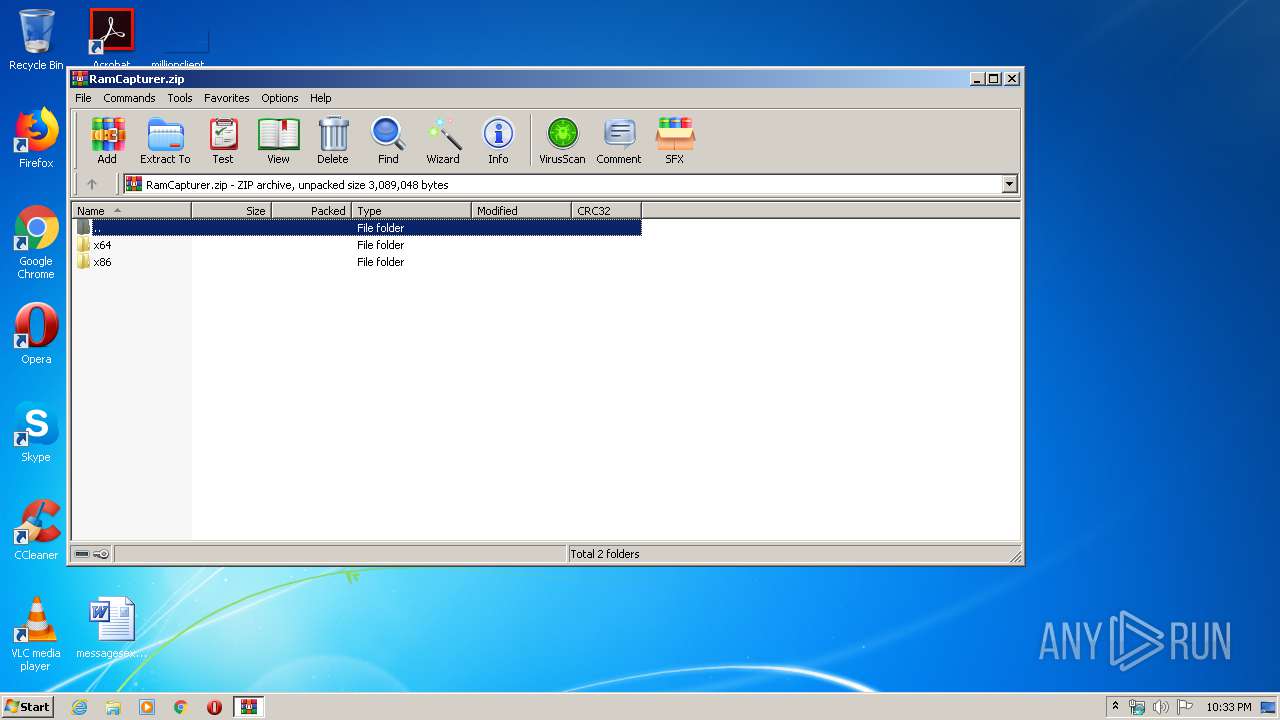
Executable content was dropped or overwritten
- WinRAR.exe (PID: 332)
INFO
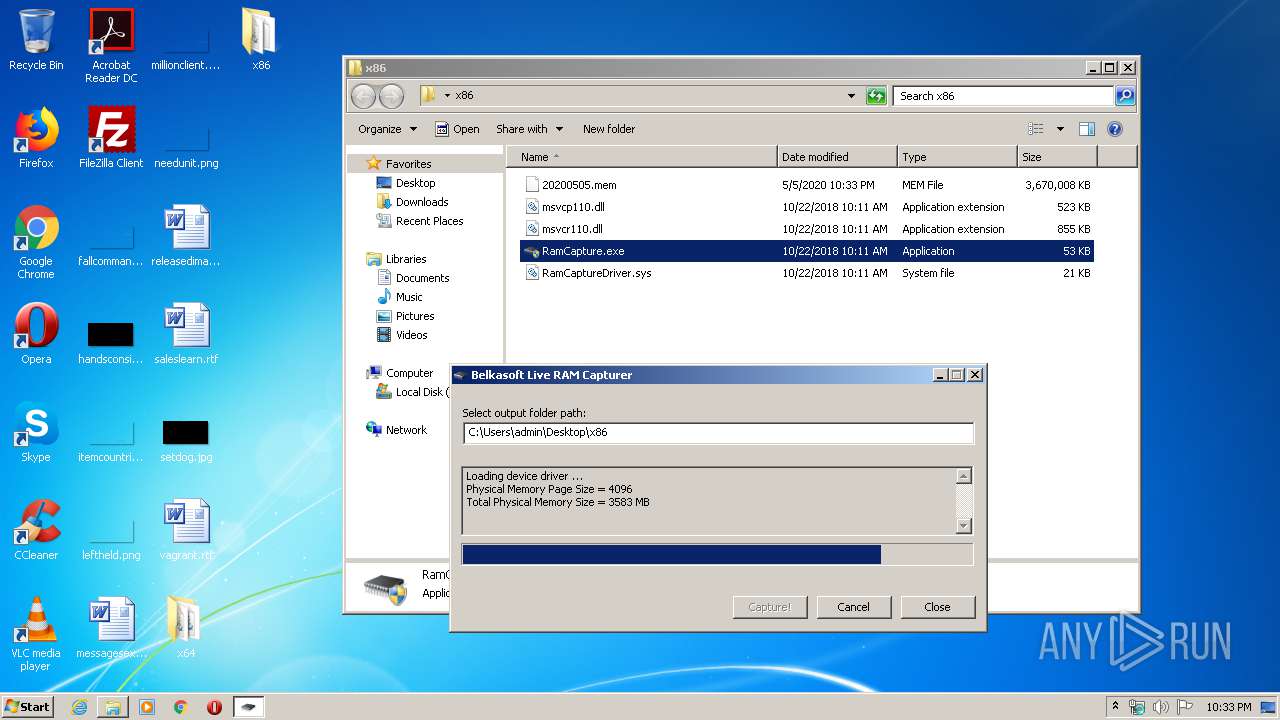
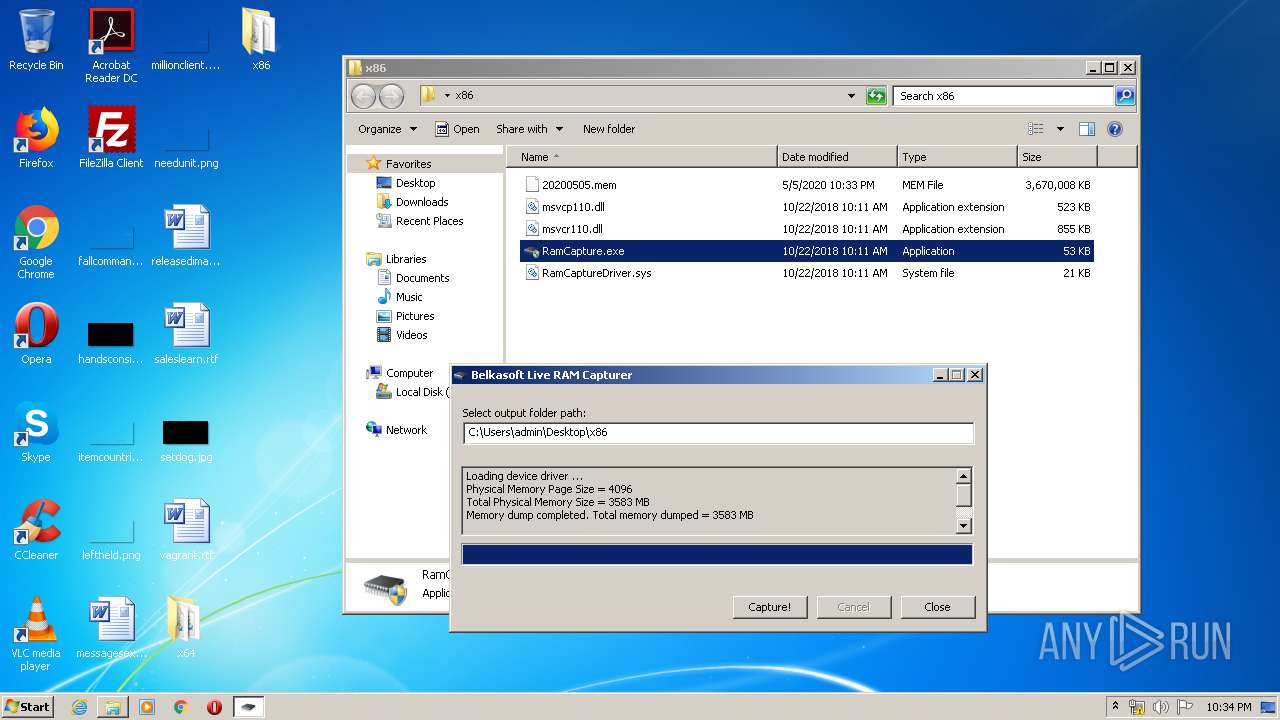
Manual execution by user
- RamCapture.exe (PID: 1604)
- rundll32.exe (PID: 3164)
- RamCapture.exe (PID: 3444)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0008 |
| ZipCompression: | None |
| ZipModifyDate: | 2018:10:22 10:11:02 |
| ZipCRC: | 0xaf095826 |
| ZipCompressedSize: | 661456 |
| ZipUncompressedSize: | 661456 |
| ZipFileName: | x64/msvcp110.dll |
Total processes
47
Monitored processes
5
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 332 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\RamCapturer.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
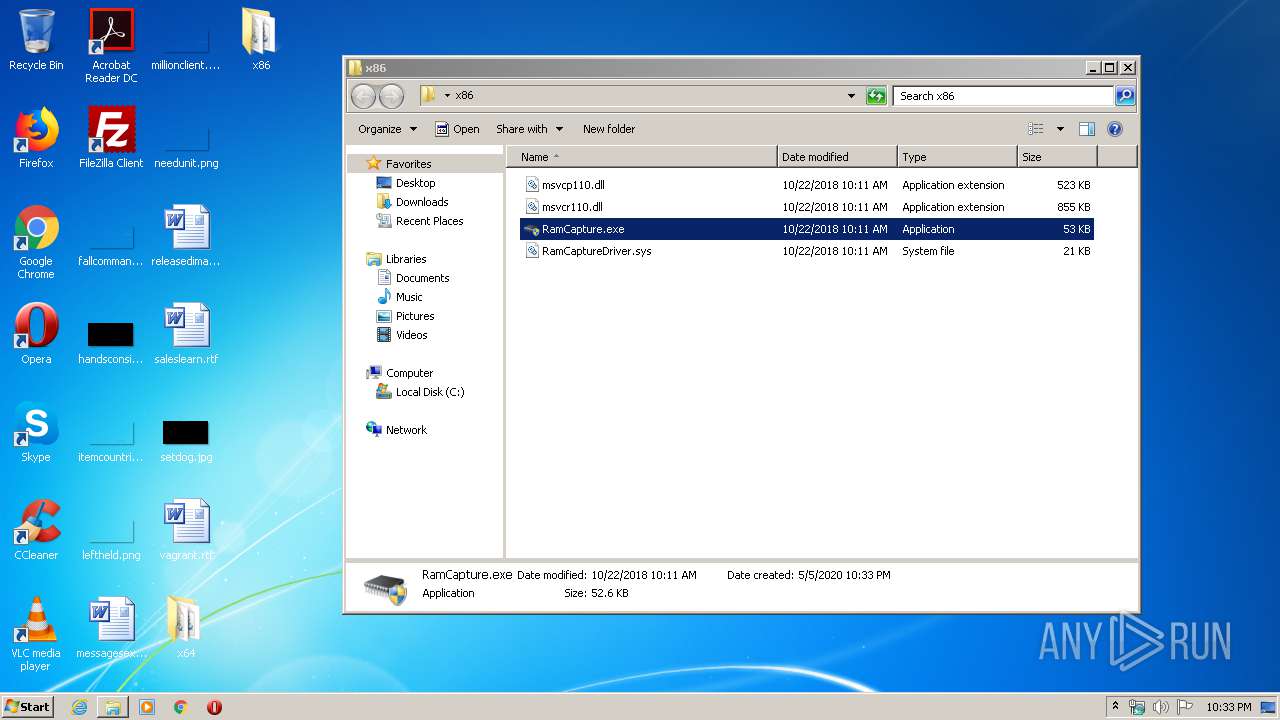
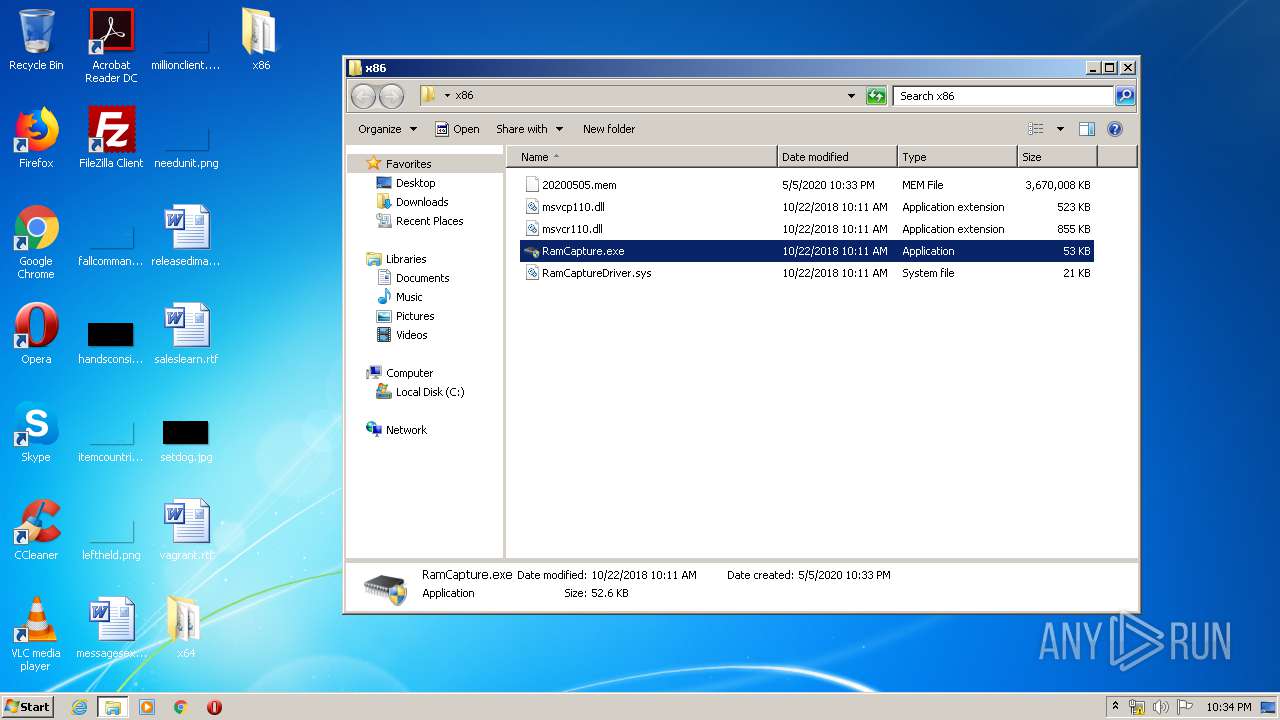
| 1604 | "C:\Users\admin\Desktop\x86\RamCapture.exe" | C:\Users\admin\Desktop\x86\RamCapture.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
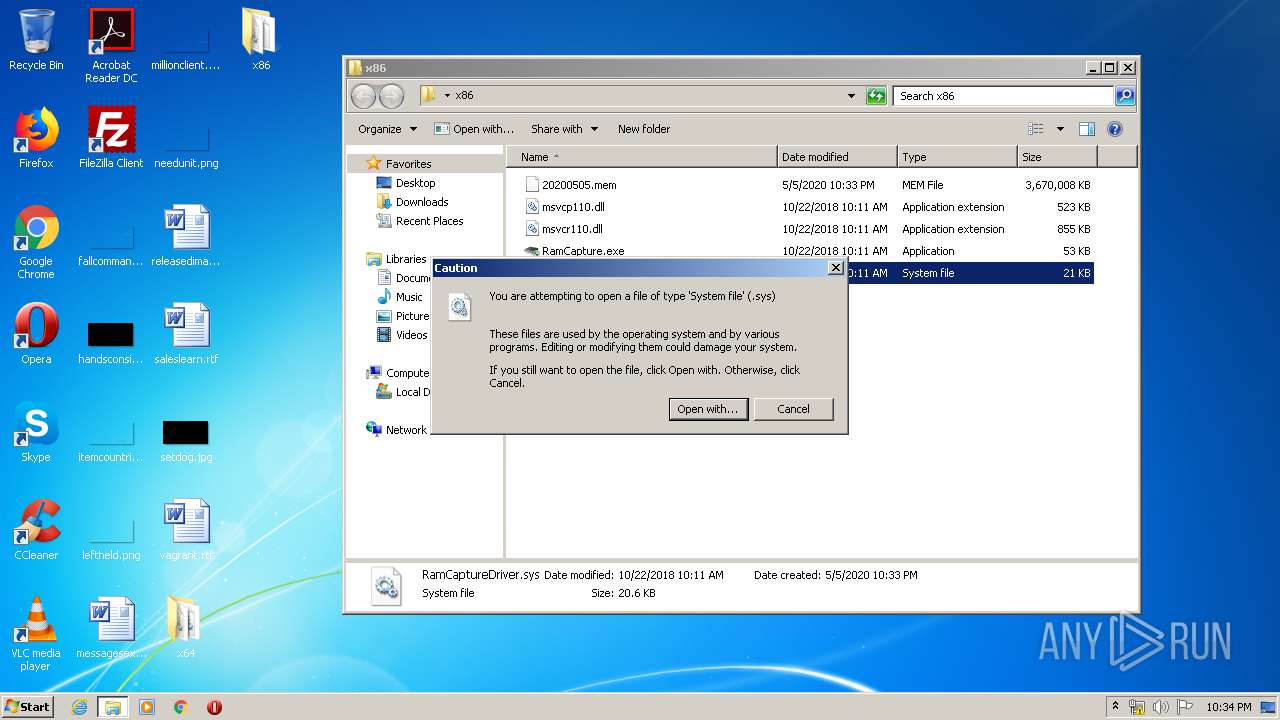
| 2460 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe5_ Global\UsGthrCtrlFltPipeMssGthrPipe5 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3164 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\Desktop\x86\RamCaptureDriver.sys | C:\Windows\system32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3444 | "C:\Users\admin\Desktop\x86\RamCapture.exe" | C:\Users\admin\Desktop\x86\RamCapture.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
Total events
829
Read events
793
Write events
33
Delete events
3
Modification events
| (PID) Process: | (332) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (332) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (332) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (332) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\RamCapturer.zip | |||
| (PID) Process: | (332) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (332) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (332) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (332) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
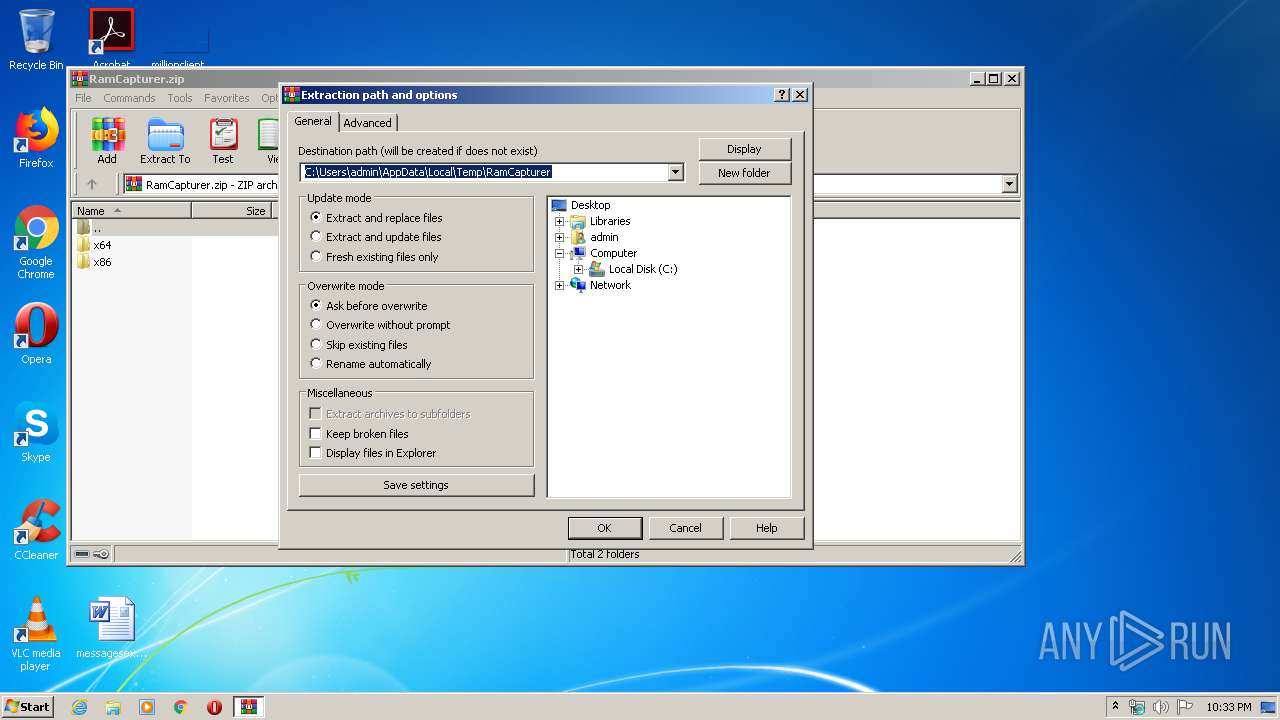
| (PID) Process: | (332) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop | |||
| (PID) Process: | (332) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
Executable files
8
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
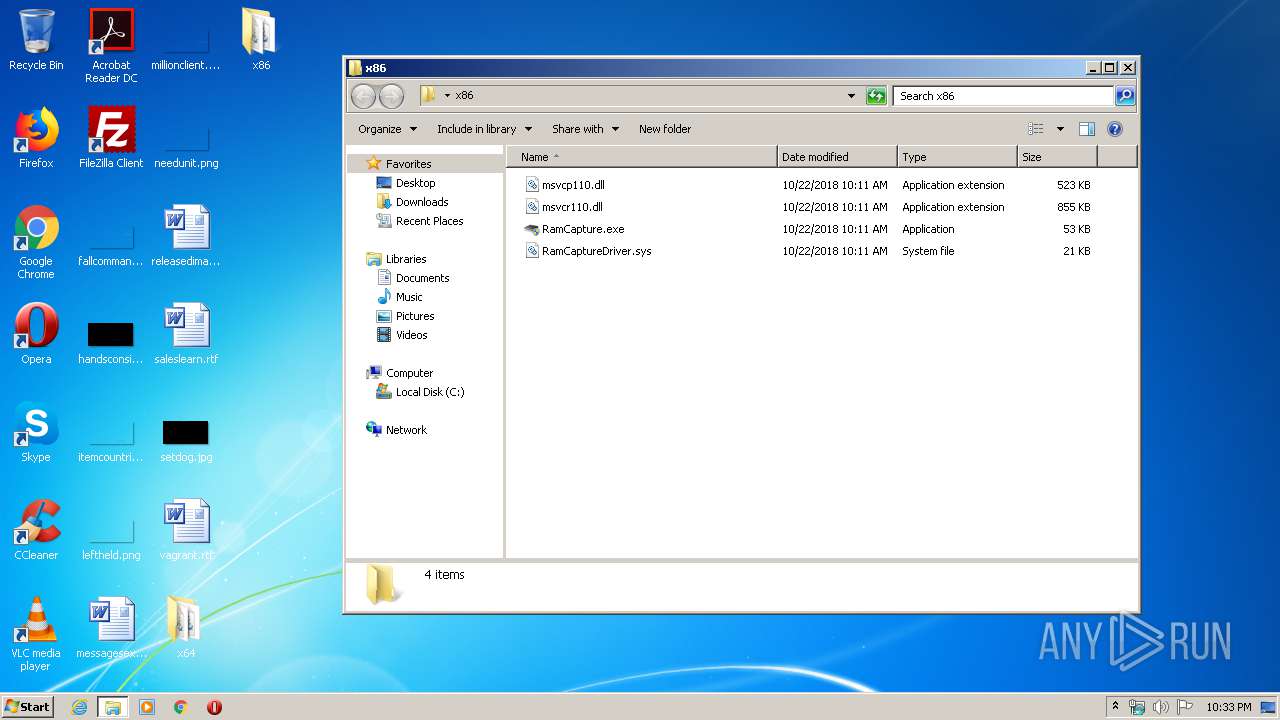
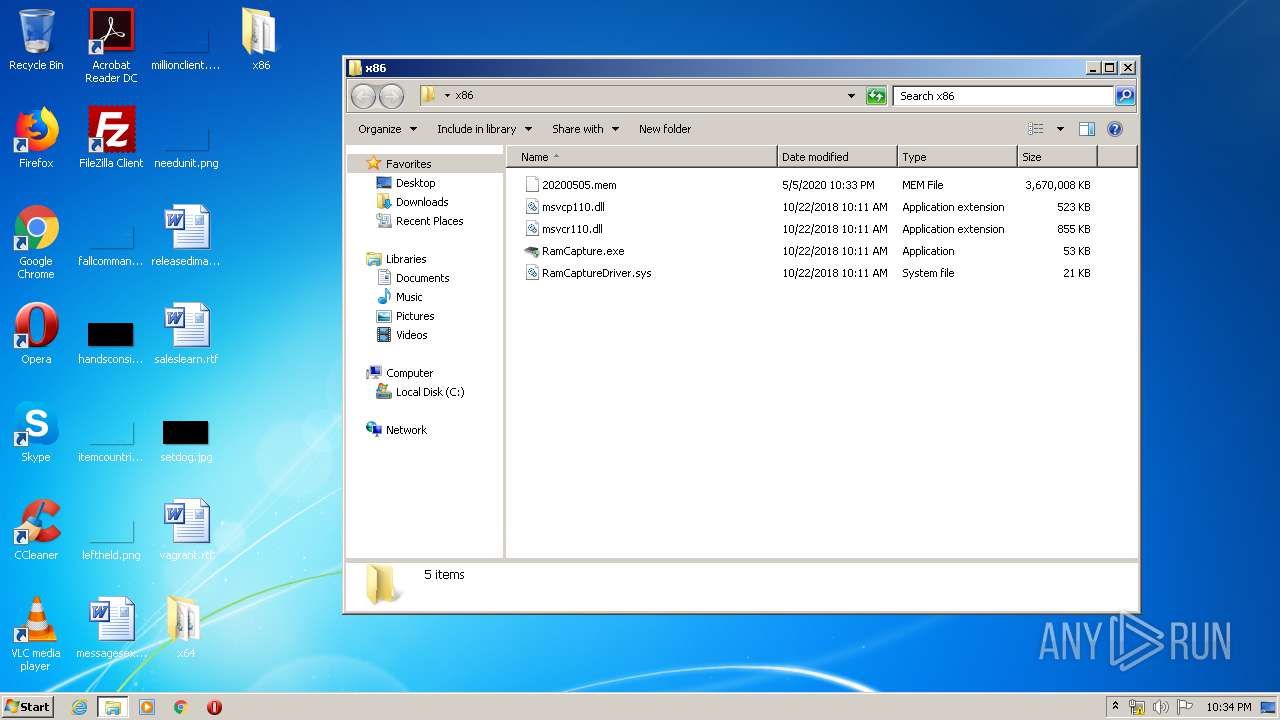
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1604 | RamCapture.exe | C:\Users\admin\Desktop\x86\20200505.mem | — | |
MD5:— | SHA256:— | |||
| 332 | WinRAR.exe | C:\Users\admin\Desktop\x86\RamCapture.exe | executable | |
MD5:FCA60980F235B4EFB3C3119EF4584FFF | SHA256:6E2C3E0CE3ABBD8D027E77D210891F2F835400856F36BB70AEA47598F1C5B131 | |||
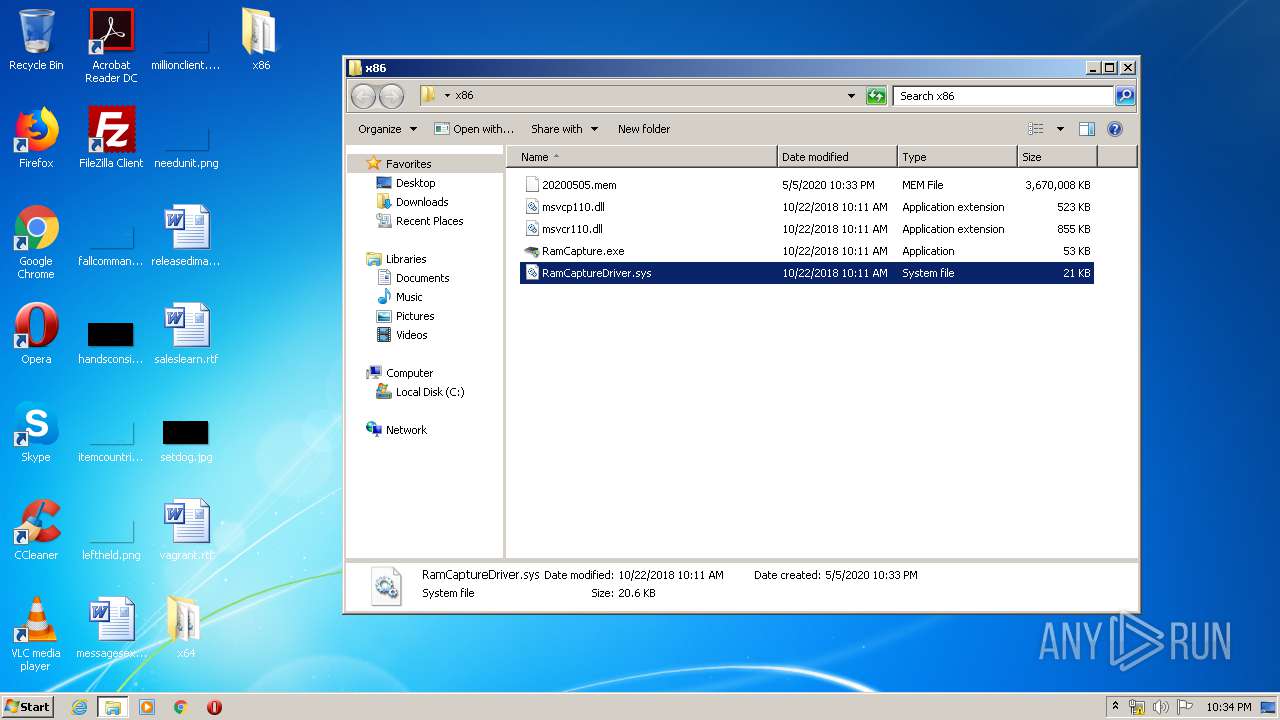
| 332 | WinRAR.exe | C:\Users\admin\Desktop\x86\RamCaptureDriver.sys | executable | |
MD5:AA29BD60087B4A389F56A580F3528929 | SHA256:01FE877949230562936203255773139F8604E1B2991790E6376E488D5A4FB5B9 | |||
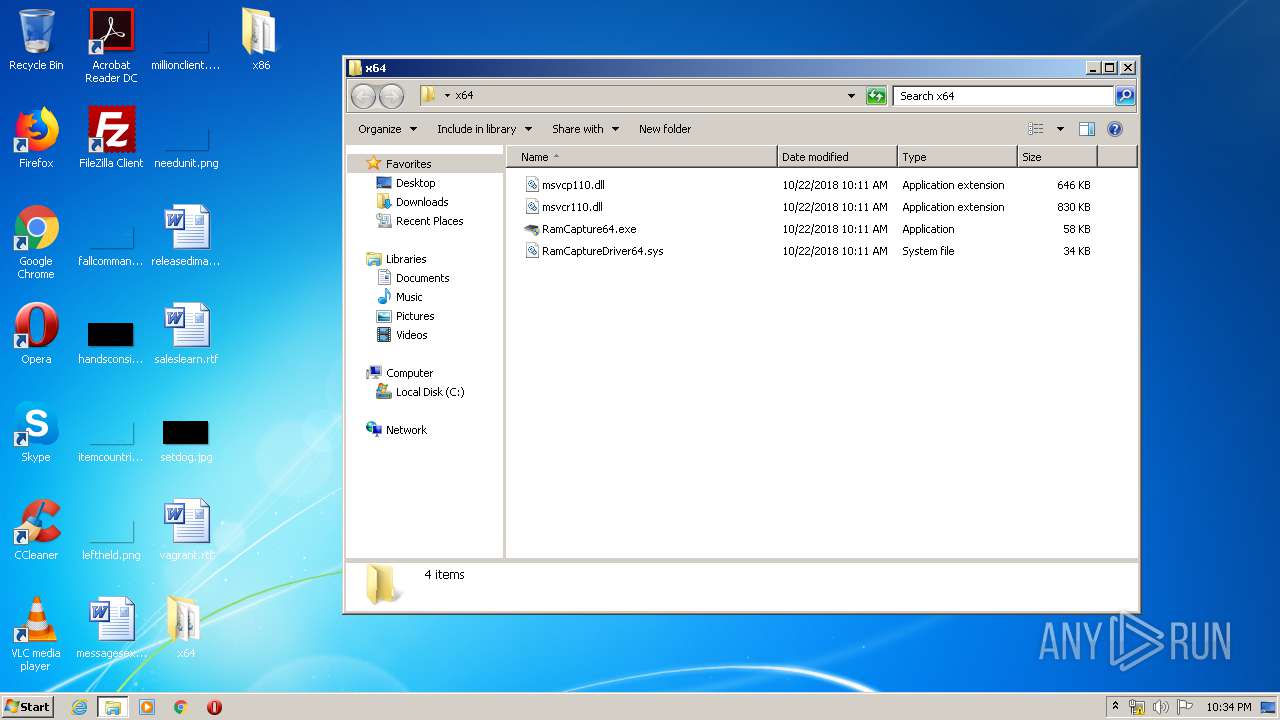
| 332 | WinRAR.exe | C:\Users\admin\Desktop\x64\RamCaptureDriver64.sys | executable | |
MD5:A3ED45520B17E910794EDD8D946E0F18 | SHA256:154B93EDD85F39059175C0709371D1F73D3F8D7DCFFB8CD4907D885E62EC83FC | |||
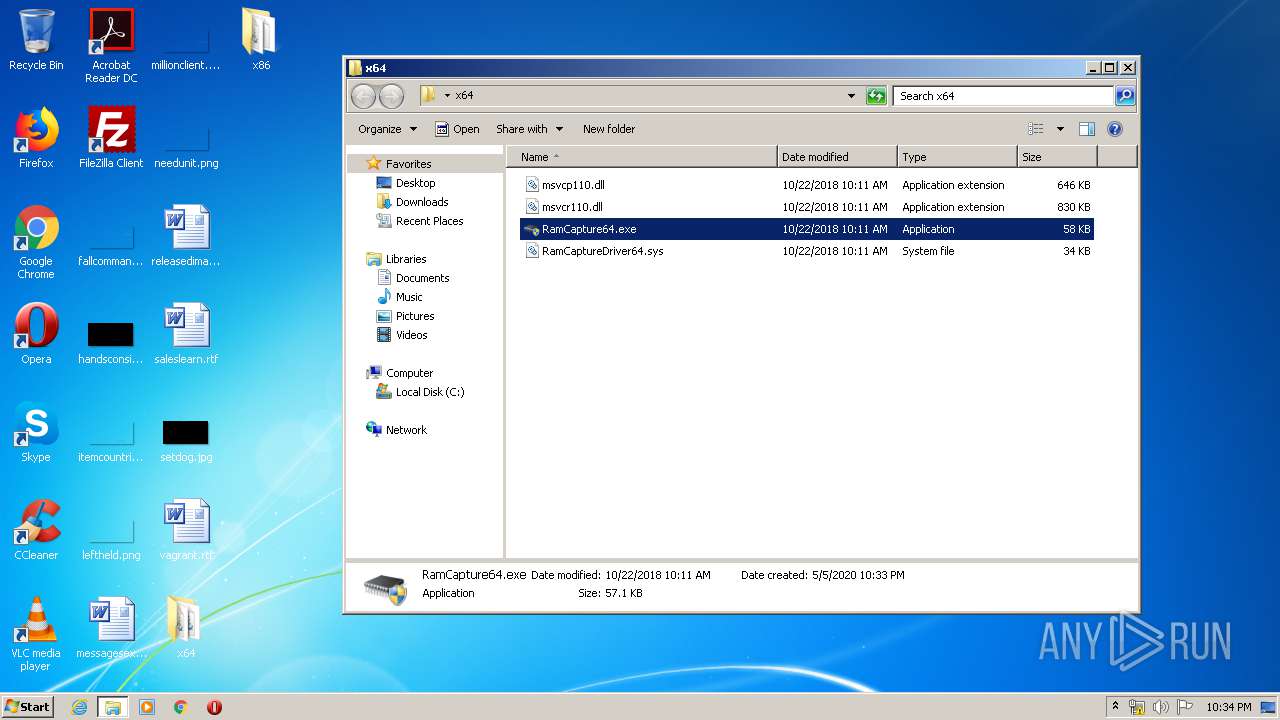
| 332 | WinRAR.exe | C:\Users\admin\Desktop\x64\RamCapture64.exe | executable | |
MD5:E331F960CDBA675DEA9218EFDED56A5F | SHA256:3F934019C46763B518C90E9D66088A301BD50FFC7F90D447FF1B54AF96AB9E4E | |||
| 332 | WinRAR.exe | C:\Users\admin\Desktop\x64\msvcp110.dll | executable | |
MD5:7CAA1B97A3311EB5A695E3C9028616E7 | SHA256:27F394AE01D12F851F1DEE3632DEE3C5AFA1D267F7A96321D35FD43105B035AD | |||
| 332 | WinRAR.exe | C:\Users\admin\Desktop\x86\msvcr110.dll | executable | |
MD5:4BA25D2CBE1587A841DCFB8C8C4A6EA6 | SHA256:B30160E759115E24425B9BCDF606EF6EBCE4657487525EDE7F1AC40B90FF7E49 | |||
| 332 | WinRAR.exe | C:\Users\admin\Desktop\x64\msvcr110.dll | executable | |
MD5:7C3B449F661D99A9B1033A14033D2987 | SHA256:AE996EDB9B050677C4F82D56092EFDC75F0ADDC97A14E2C46753E2DB3F6BD732 | |||
| 332 | WinRAR.exe | C:\Users\admin\Desktop\x86\msvcp110.dll | executable | |
MD5:3E29914113EC4B968BA5EB1F6D194A0A | SHA256:C8D5572CA8D7624871188F0ACABC3AE60D4C5A4F6782D952B9038DE3BC28B39A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report