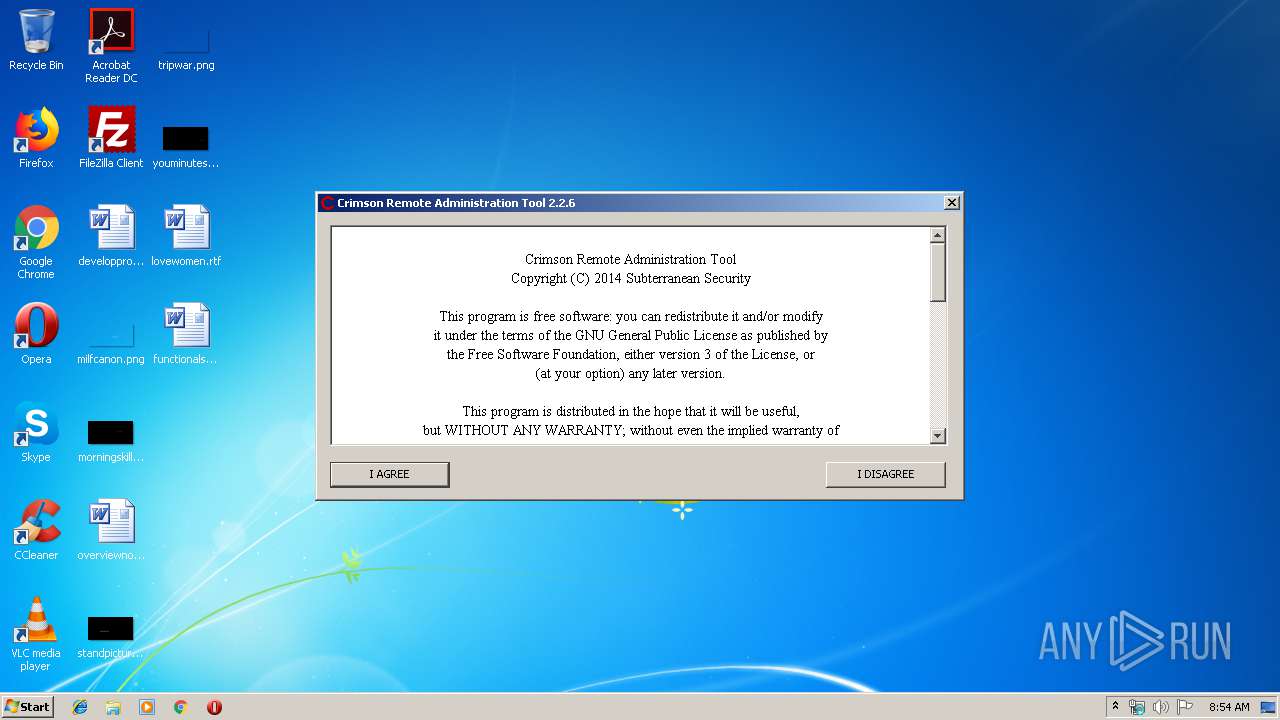
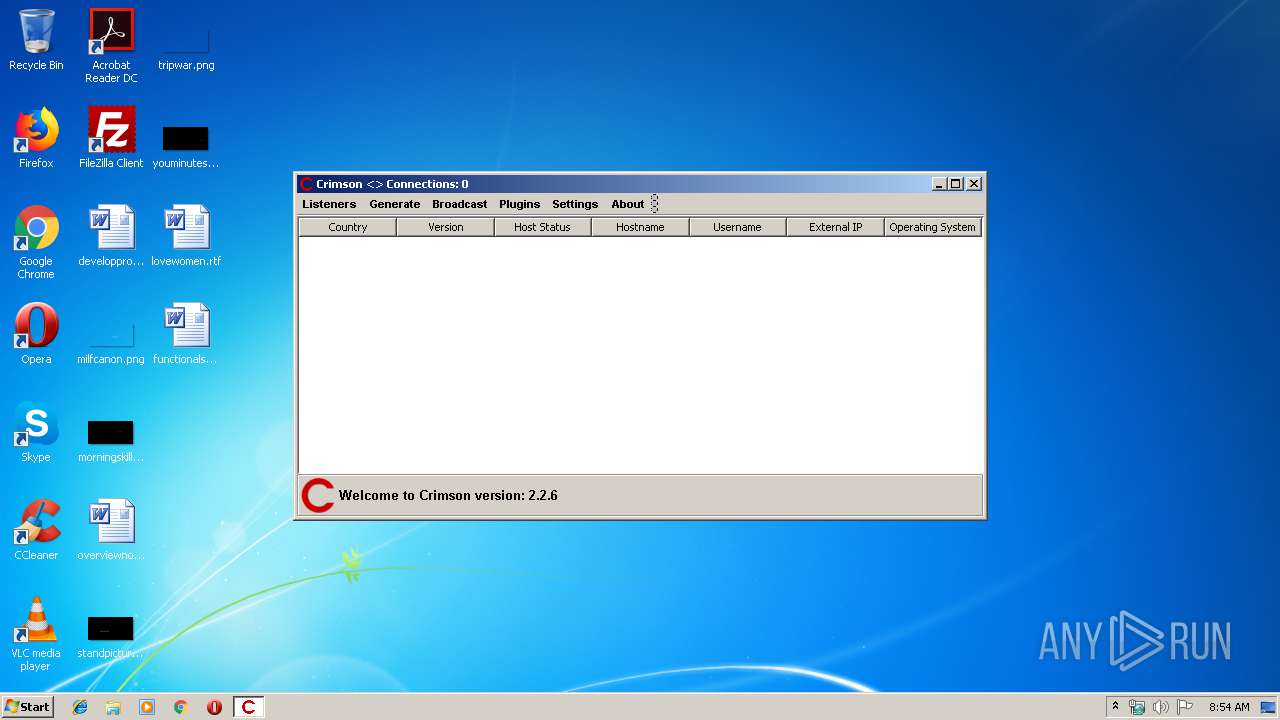
| File name: | crimsonRAT2.2.6.jar |
| Full analysis: | https://app.any.run/tasks/60cda609-4a63-4f31-958c-ad5731849641 |
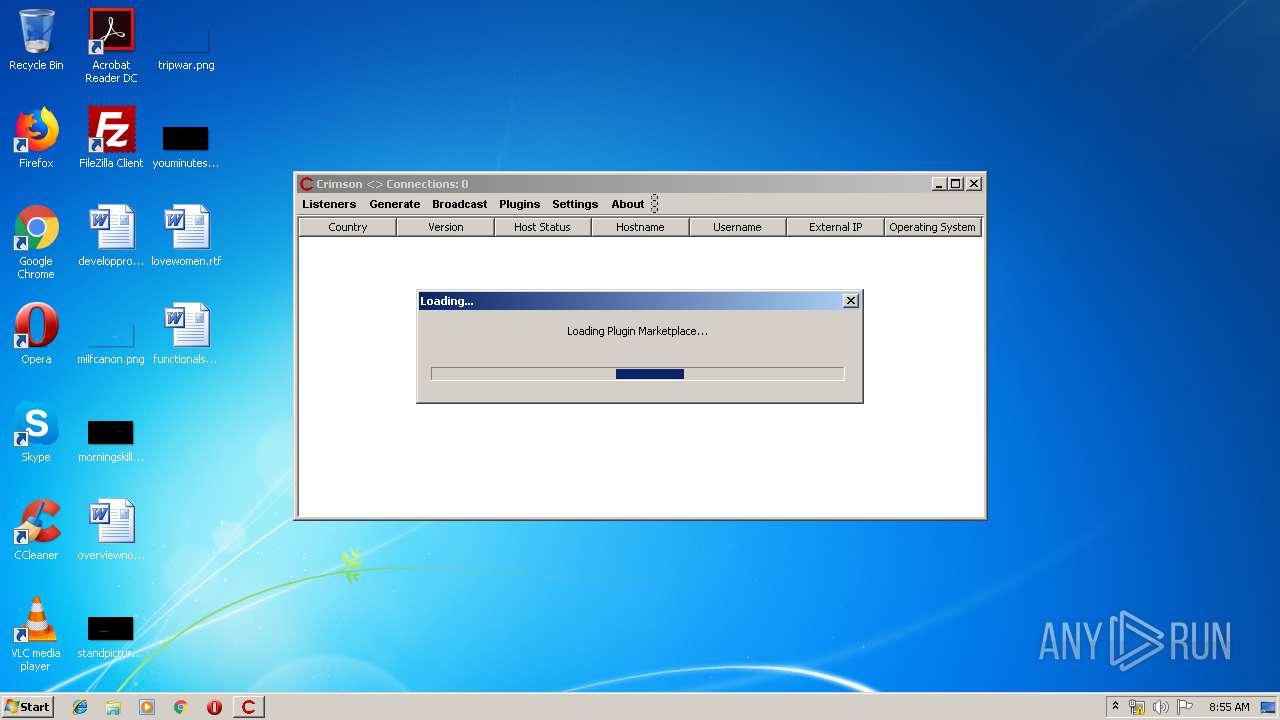
| Verdict: | Malicious activity |
| Analysis date: | November 16, 2019, 08:53:46 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | A6324CDB52C0182CCB6E991E53B8B024 |
| SHA1: | F5E338B12A461BE8B5F21EEABD6981B60A5B916C |
| SHA256: | 86592DA5B0F1FB41F2F12DA15EA754BAFA0011FDDBA02065984B164CF4623D4B |
| SSDEEP: | 98304:6N+aNpG8rJwoOXd6ERkkn/jpwaMInQd7nMRd:qpGcJEX9NwCQdrMb |
MALICIOUS
Actions looks like stealing of personal data
- javaw.exe (PID: 892)
SUSPICIOUS
Uses ATTRIB.EXE to modify file attributes
- javaw.exe (PID: 892)
Creates files in the user directory
- javaw.exe (PID: 892)
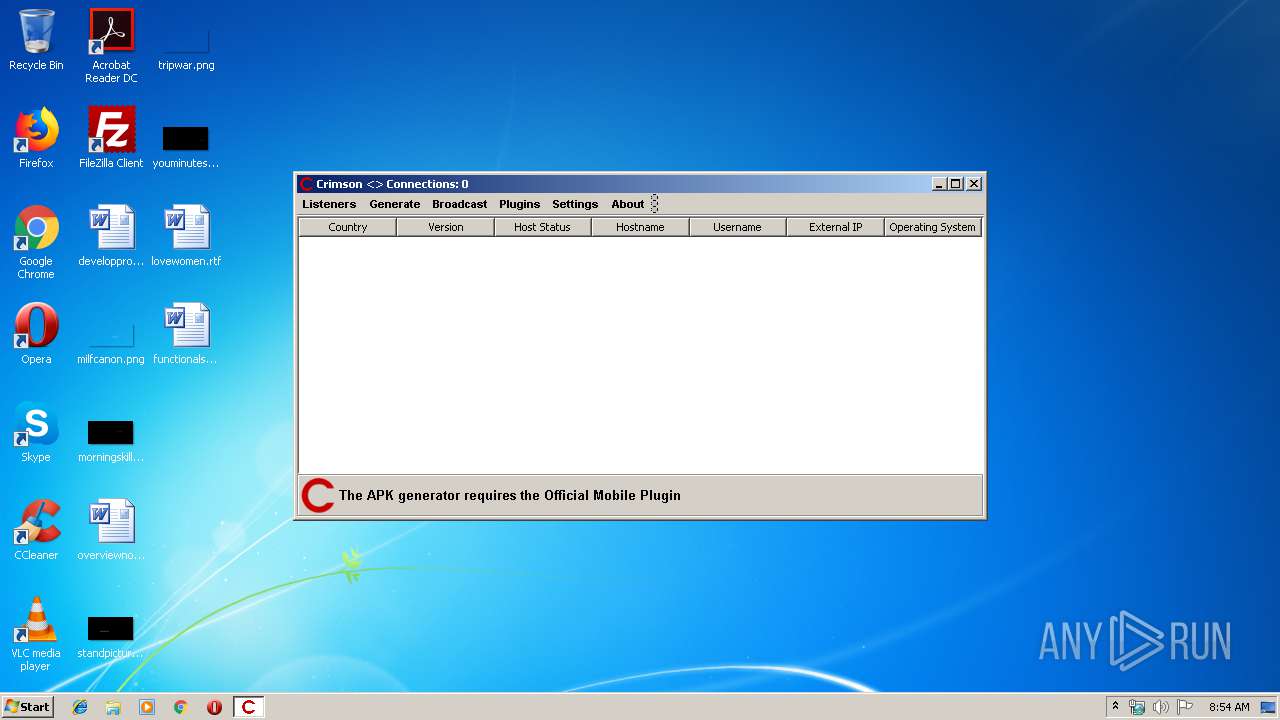
Checks for external IP
- javaw.exe (PID: 892)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (36.3) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0808 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2014:09:06 19:35:06 |
| ZipCRC: | 0x0e51b6b7 |
| ZipCompressedSize: | 213 |
| ZipUncompressedSize: | 368 |
| ZipFileName: | .classpath |
Total processes
36
Monitored processes
2
Malicious processes
1
Suspicious processes
0
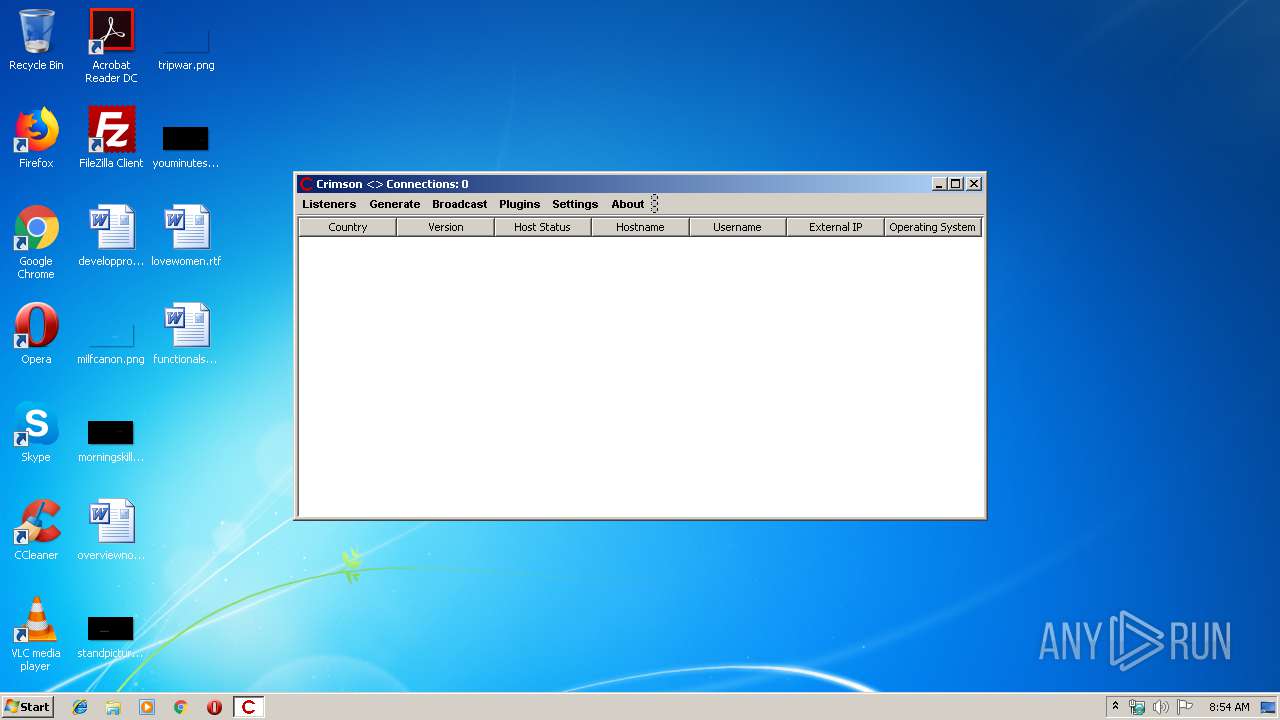
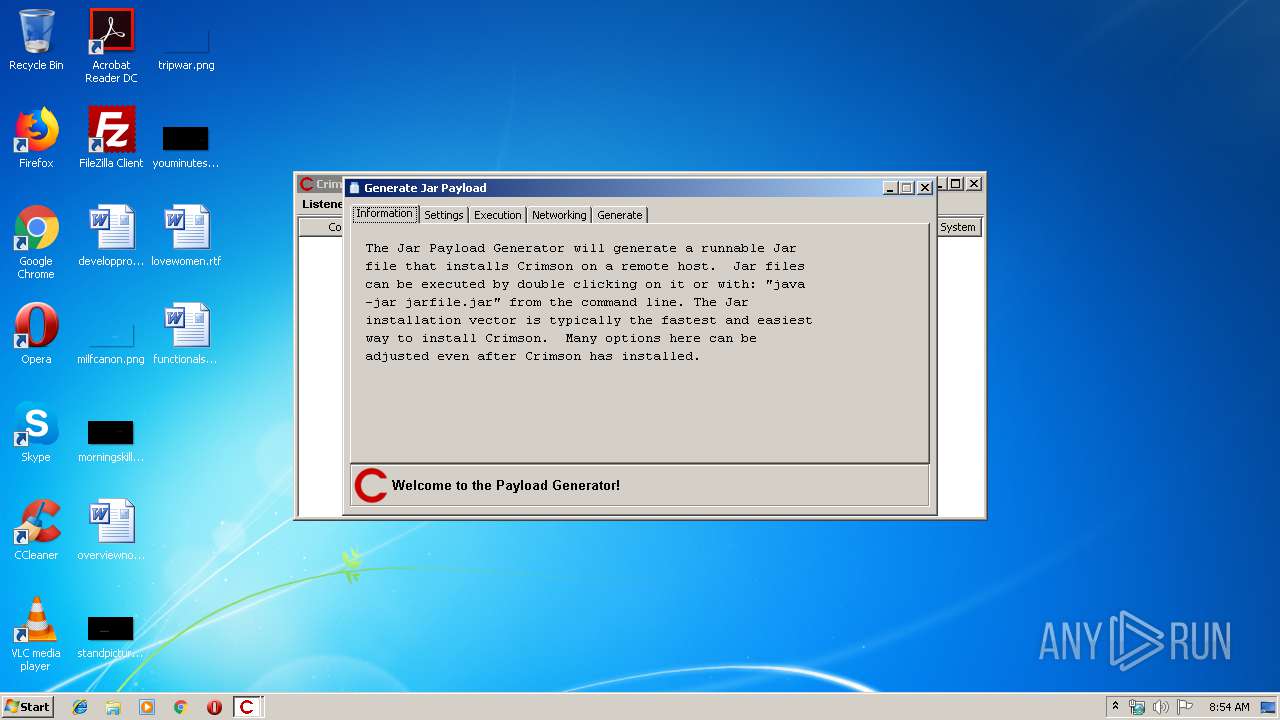
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 892 | "C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe" -jar "C:\Users\admin\AppData\Local\Temp\crimsonRAT2.2.6.jar" | C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe | explorer.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
| 4076 | attrib +h .Ssettings.properties | C:\Windows\system32\attrib.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Attribute Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
413
Read events
410
Write events
3
Delete events
0
Modification events
| (PID) Process: | (892) javaw.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: javaw.exe | |||
| (PID) Process: | (892) javaw.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
0
Suspicious files
0
Text files
1
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 892 | javaw.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | text | |
MD5:— | SHA256:— | |||
| 892 | javaw.exe | C:\Users\admin\AppData\Roaming\Microsoft\Crypto\RSA\S-1-5-21-1302019708-1500728564-335382590-1000\83aa4cc77f591dfc2374580bbd95f6ba_90059c37-1320-41a4-b58d-2b75a9850d2f | dbf | |
MD5:C8366AE350E7019AEFC9D1E6E6A498C6 | SHA256:11E6ACA8E682C046C83B721EEB5C72C5EF03CB5936C60DF6F4993511DDC61238 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
3
DNS requests
3
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
892 | javaw.exe | GET | 301 | 104.26.14.73:80 | http://freegeoip.net/xml/185.183.107.236 | US | — | — | malicious |
892 | javaw.exe | GET | 200 | 52.44.169.135:80 | http://checkip.amazonaws.com/ | US | text | 16 b | malicious |
892 | javaw.exe | GET | 403 | 104.26.14.73:80 | http://freegeoip.net/shutdown | US | text | 1.51 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
892 | javaw.exe | 52.44.169.135:80 | checkip.amazonaws.com | Amazon.com, Inc. | US | shared |
— | — | 104.26.14.73:80 | freegeoip.net | Cloudflare Inc | US | shared |
892 | javaw.exe | 104.26.14.73:80 | freegeoip.net | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
checkip.amazonaws.com |
| malicious |
freegeoip.net |
| malicious |
crimsonrat.org |
| unknown |
Threats
4 ETPRO signatures available at the full report