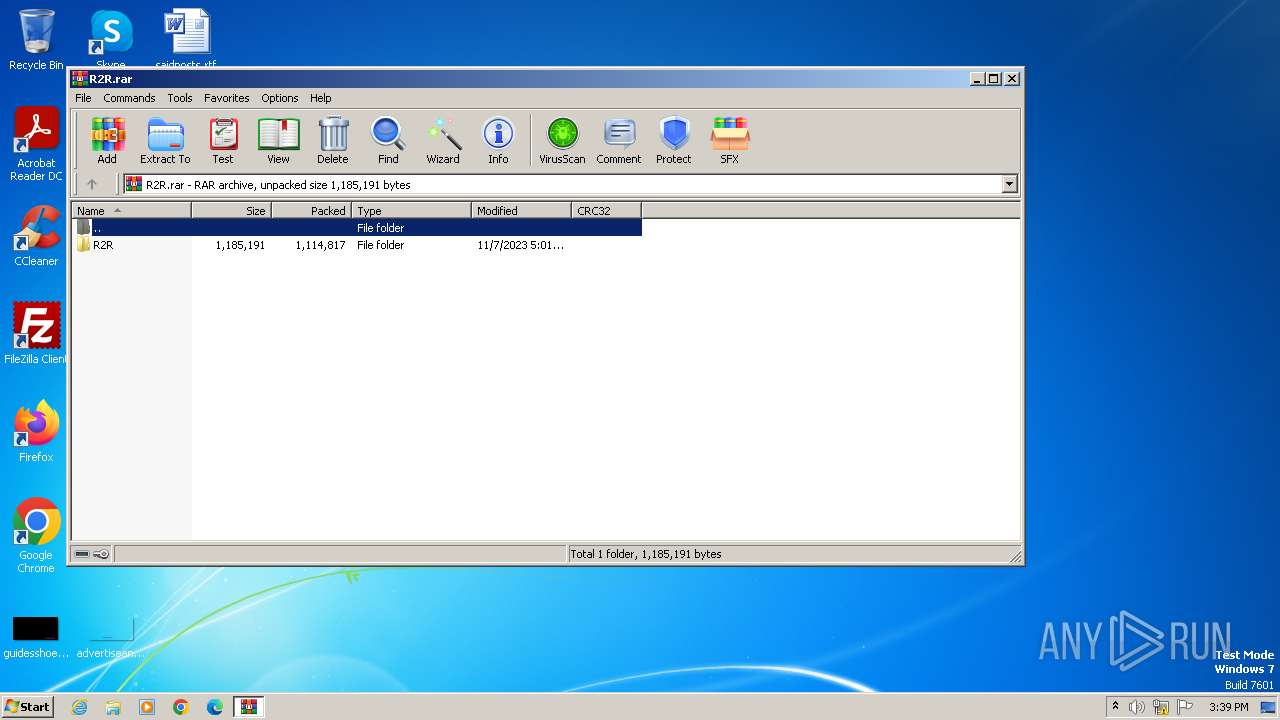
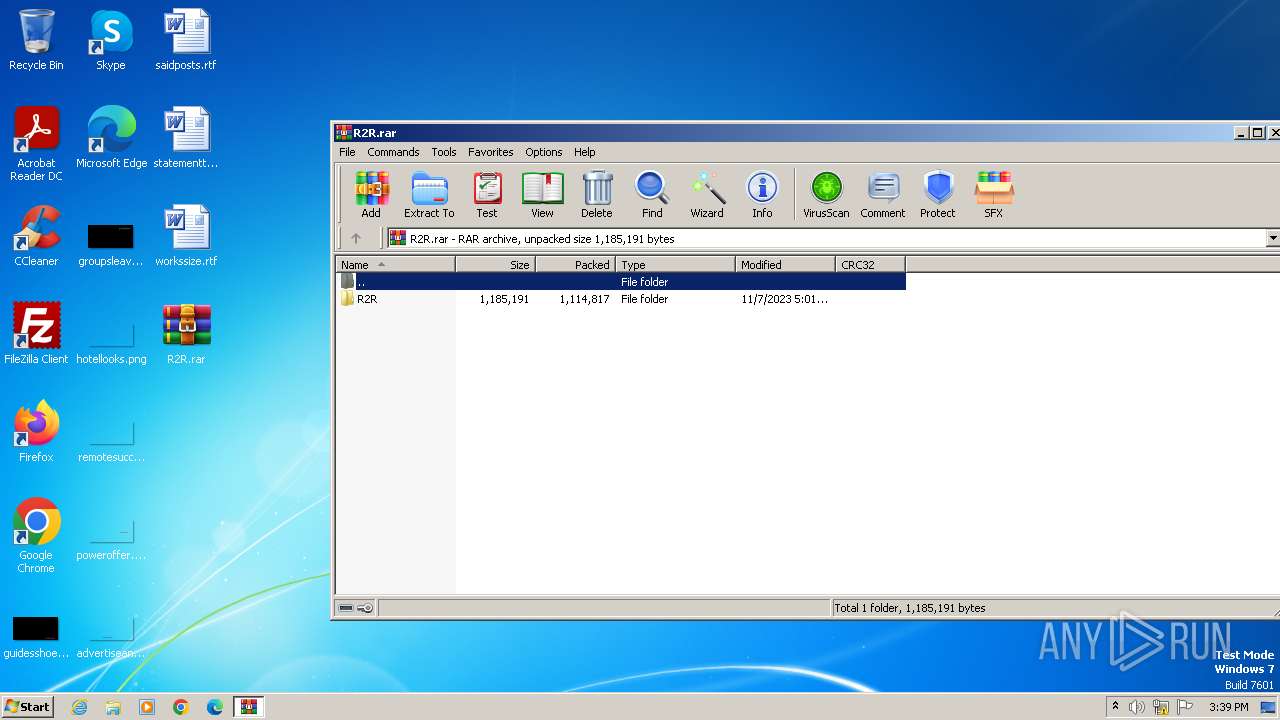
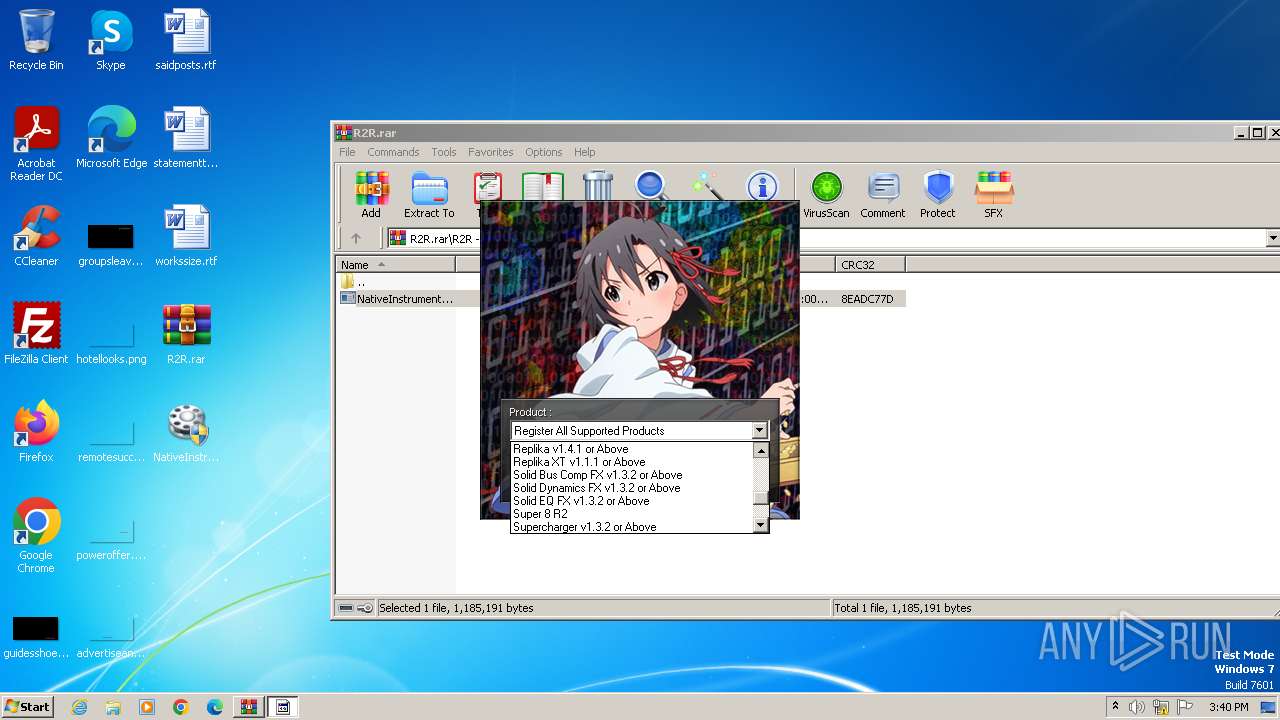
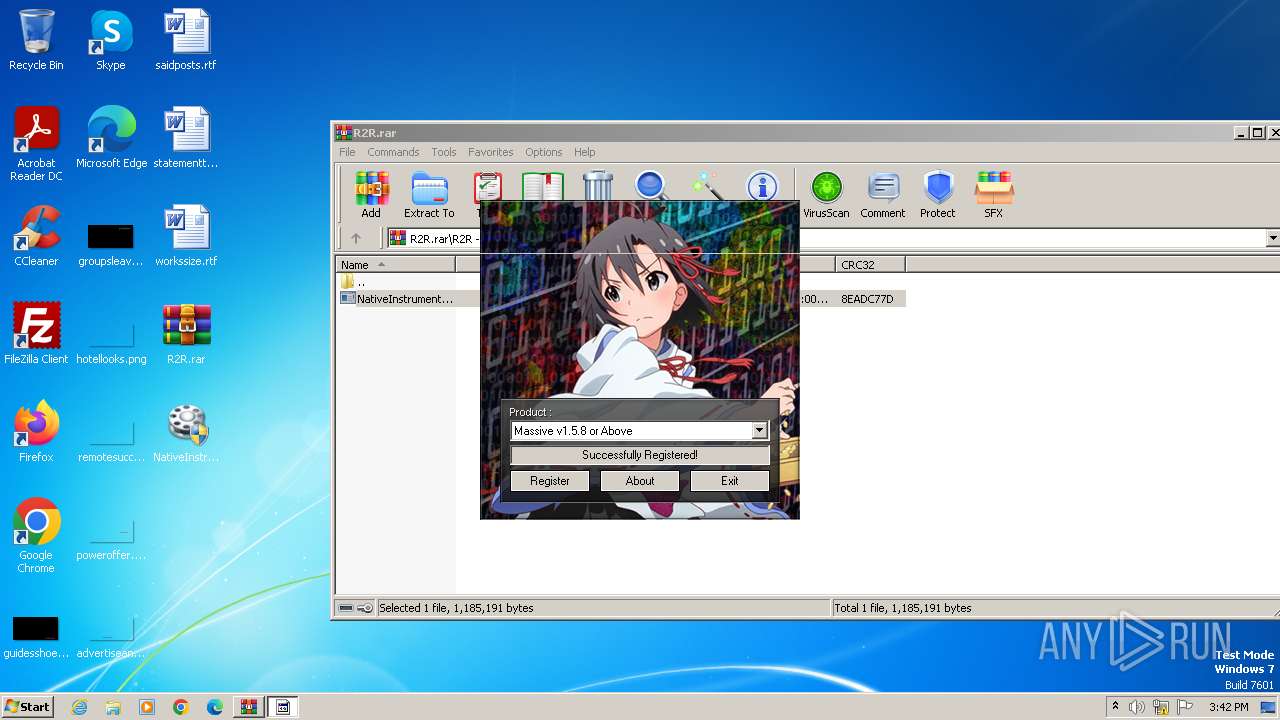
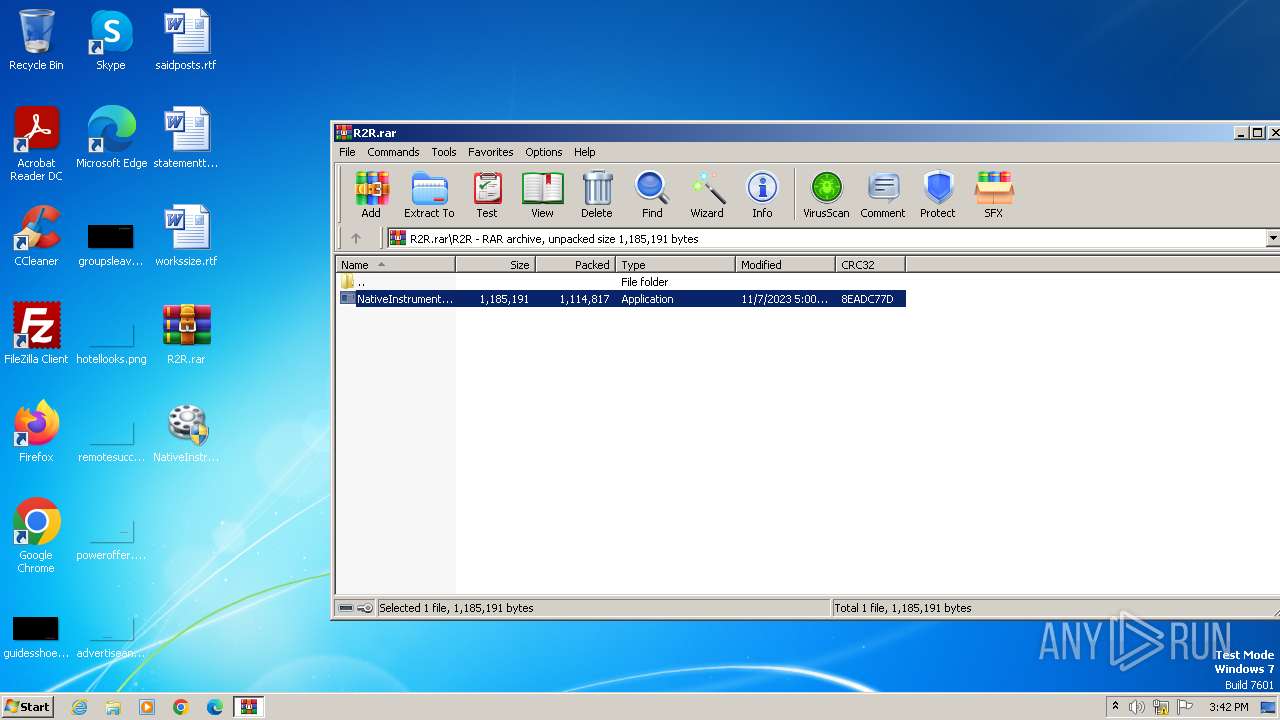
| File name: | R2R.rar |
| Full analysis: | https://app.any.run/tasks/bc4a1543-b717-4813-b000-bc325b3df952 |
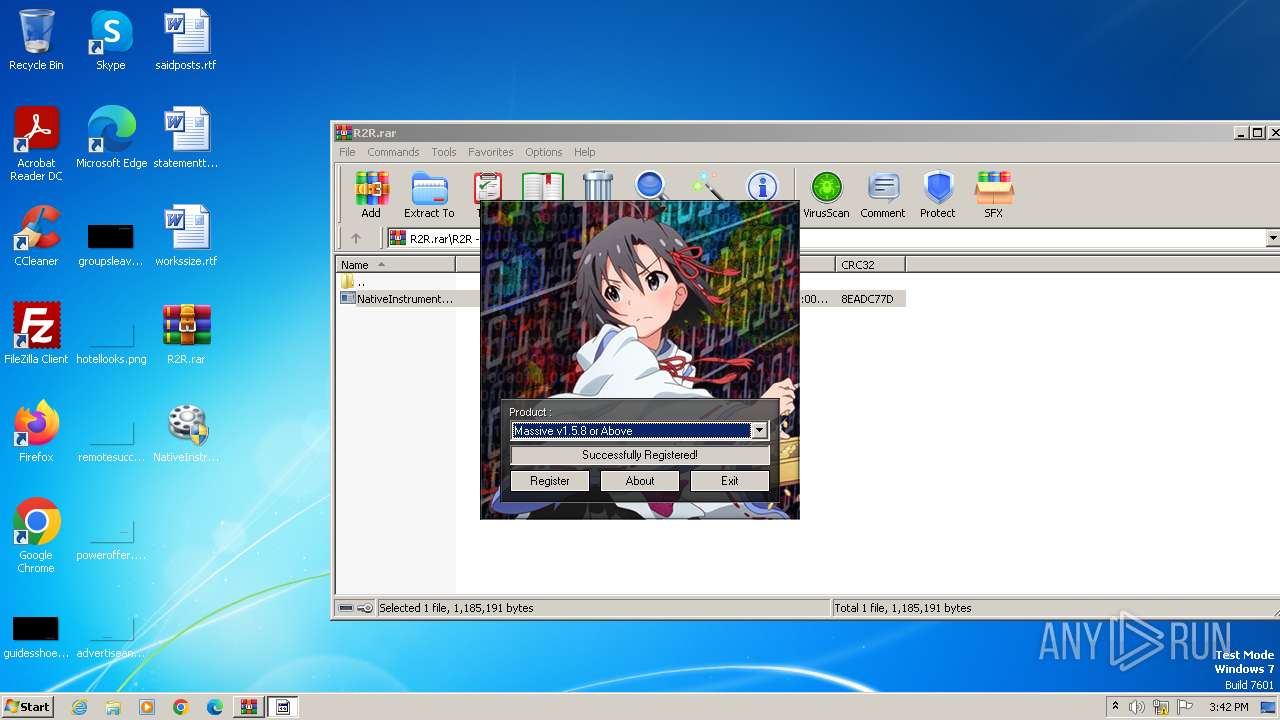
| Verdict: | Malicious activity |
| Analysis date: | November 08, 2023, 15:39:32 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 8D3030F66330B7F7B8F6C7F335E596E7 |
| SHA1: | 723AD7CD880EC8EB95013E9886796BB298D9703A |
| SHA256: | 8650F804B09EE0BA3CC8A7A0EF9A70CCFCE94EC1EBD04FD0267DA279D53DB0D6 |
| SSDEEP: | 49152:ONjKjalCpBtgq+vW6pB4wtcCyRFHG51elt86Y1JzGd8I03RXyRbygE1d6q0Z6XrQ:ONjKjK5q96p2wtIvmXeizI2RAbu1d3oR |
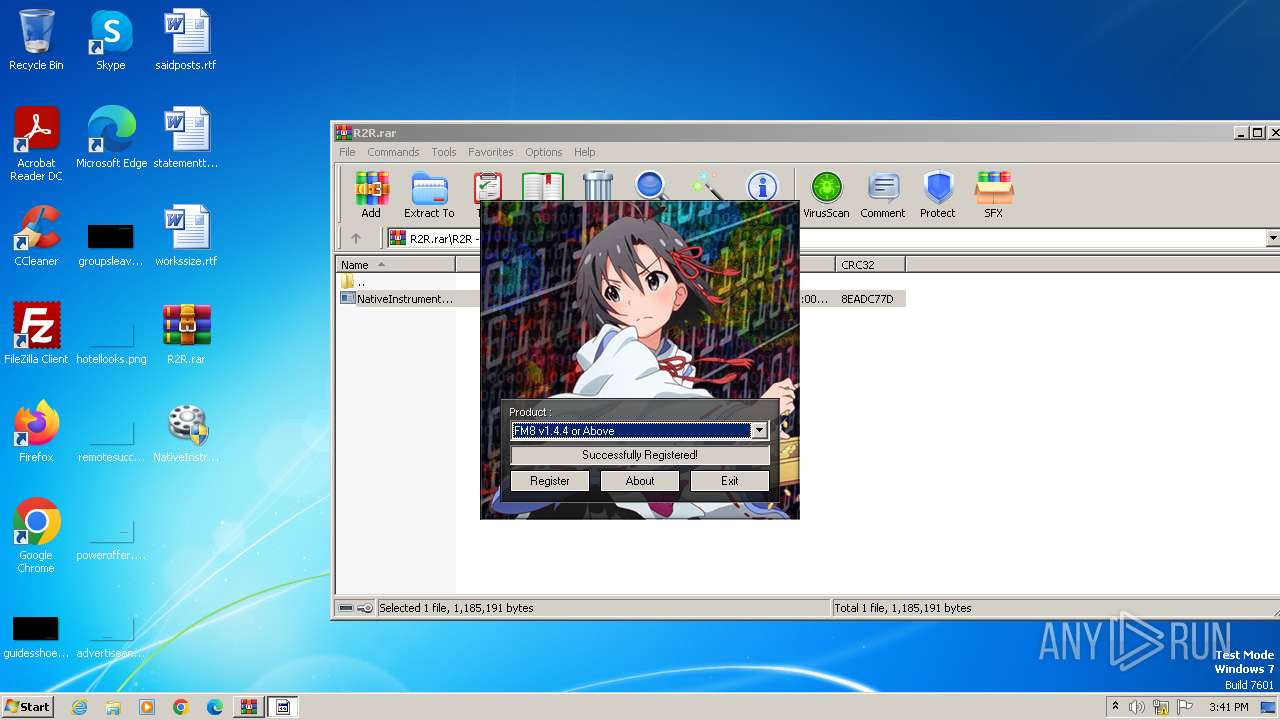
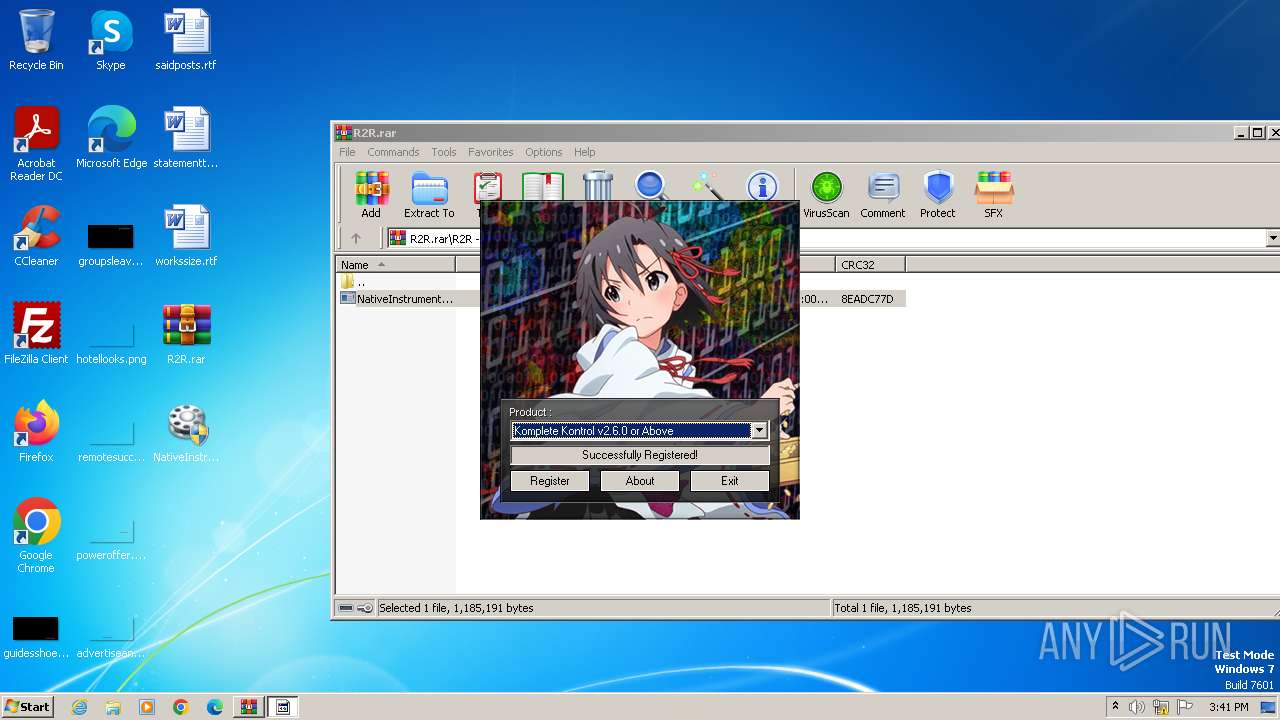
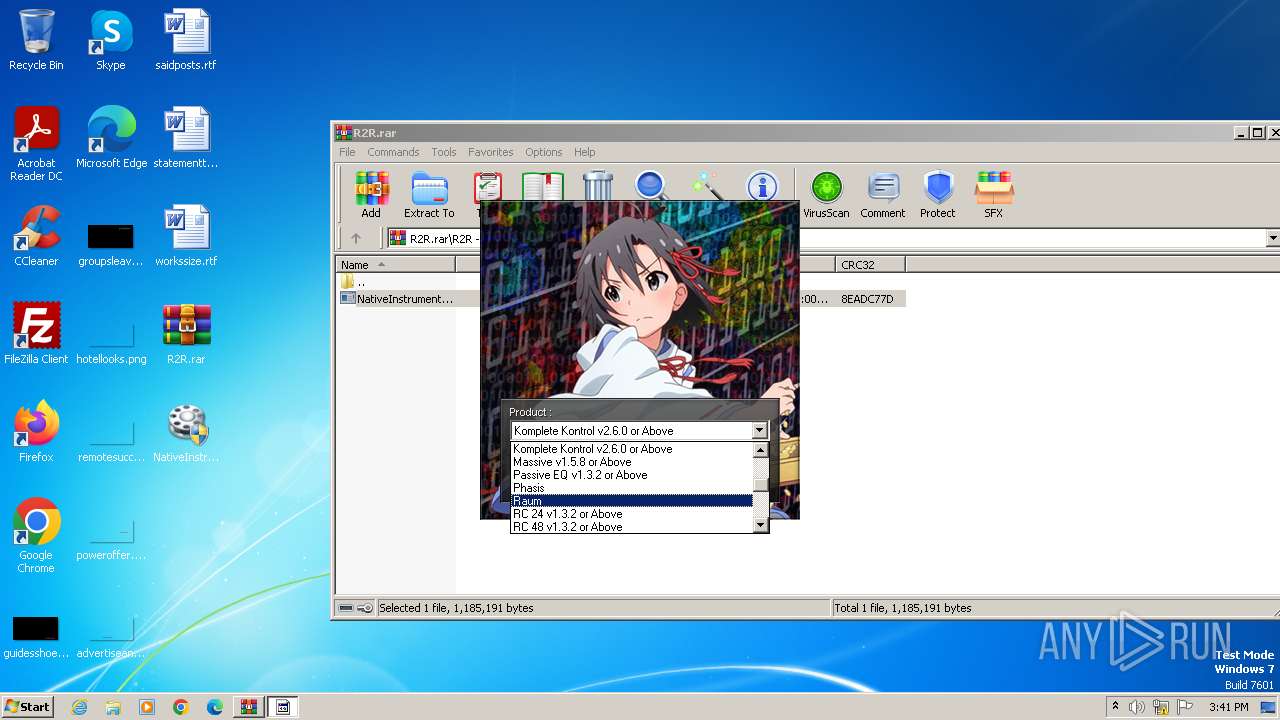
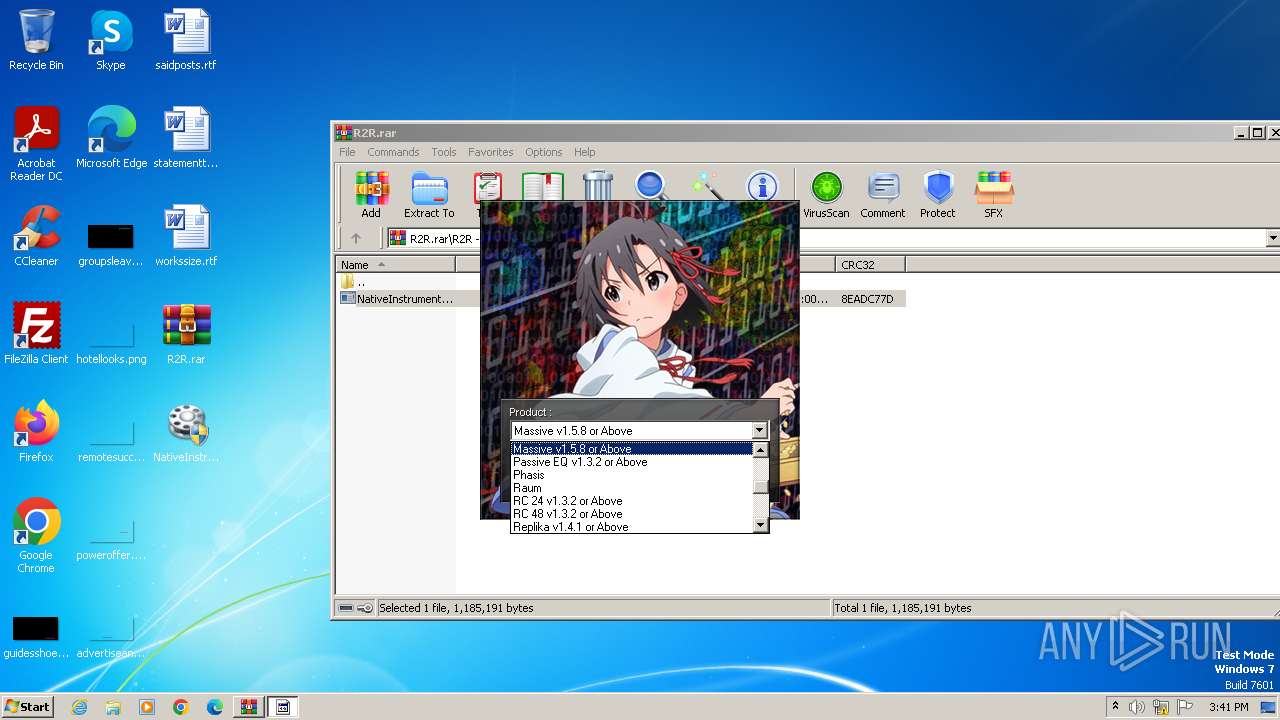
MALICIOUS
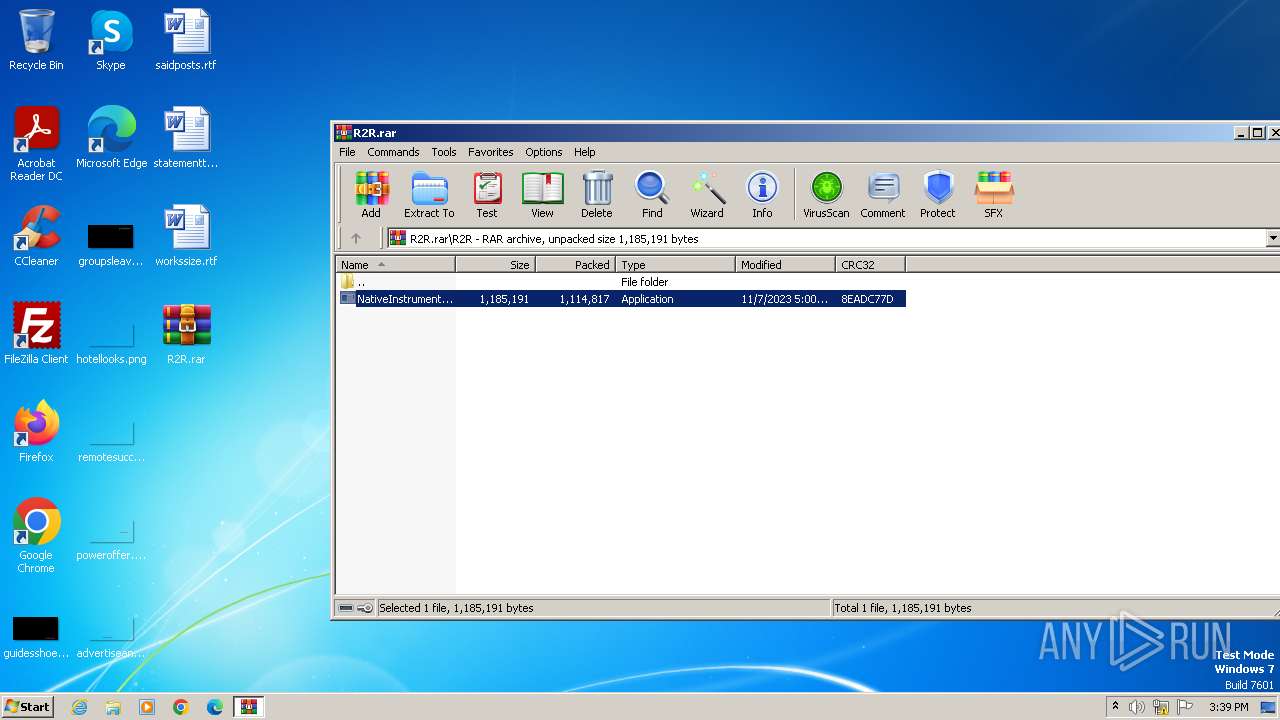
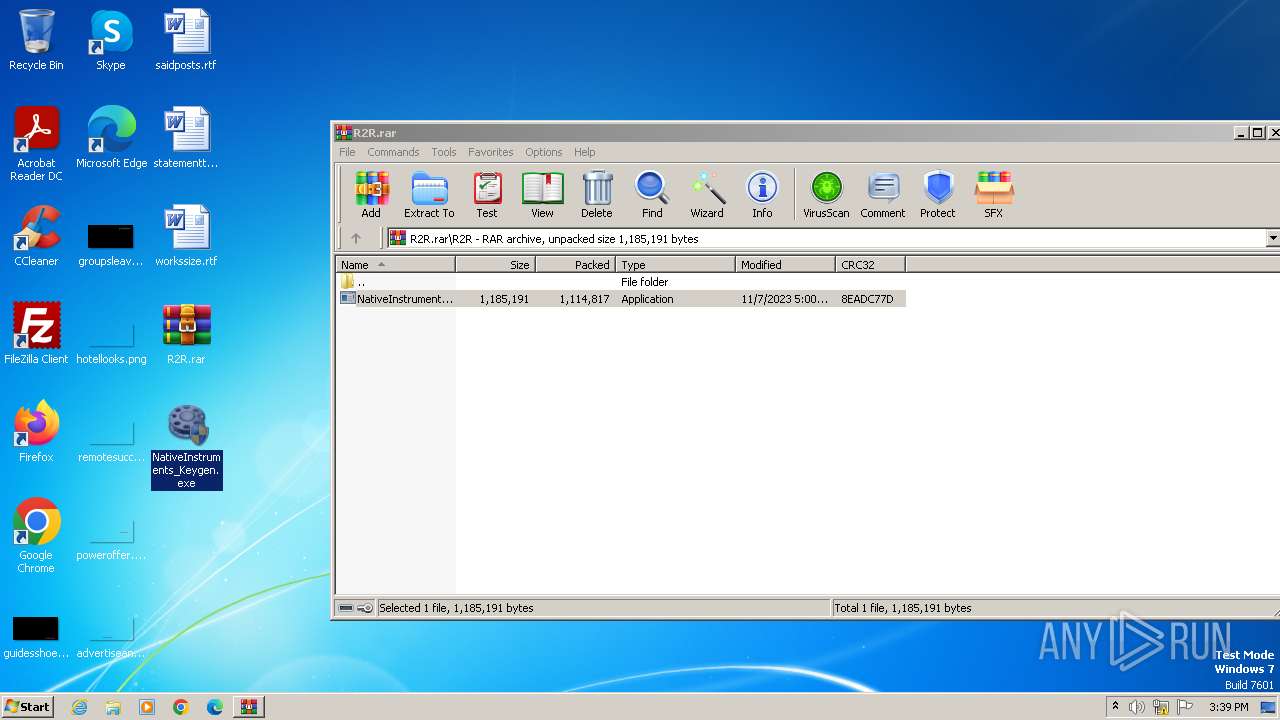
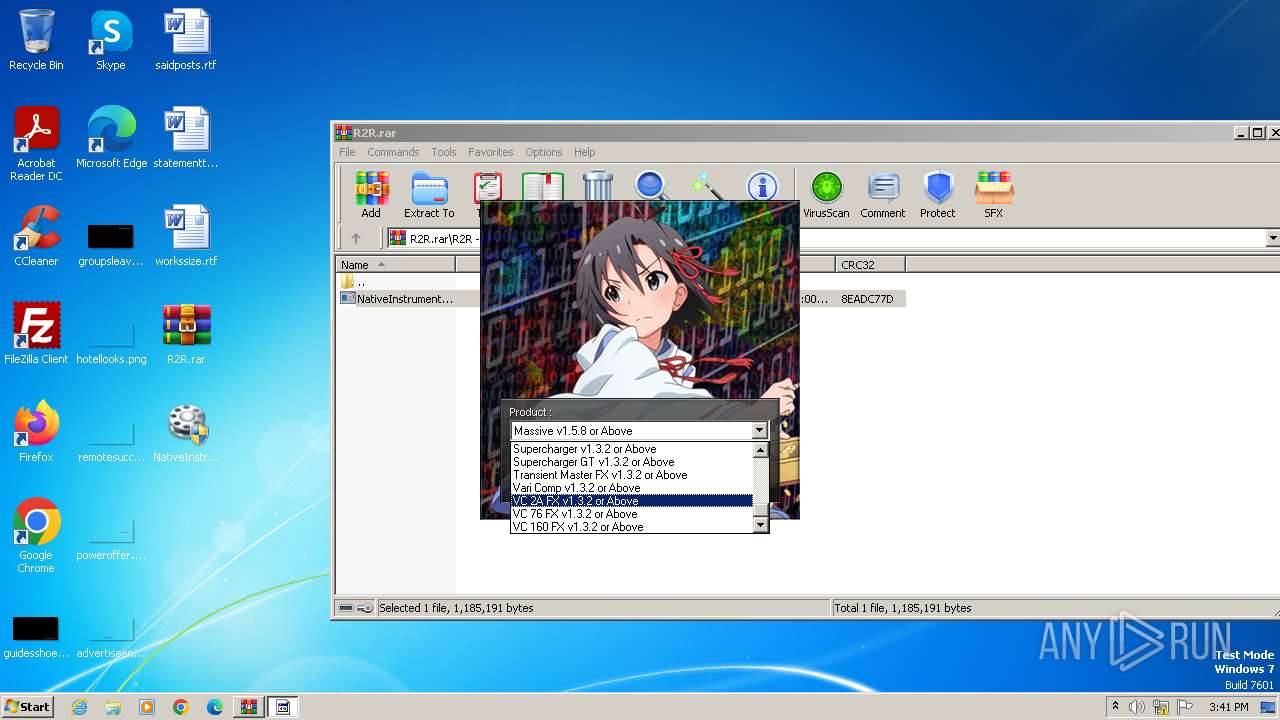
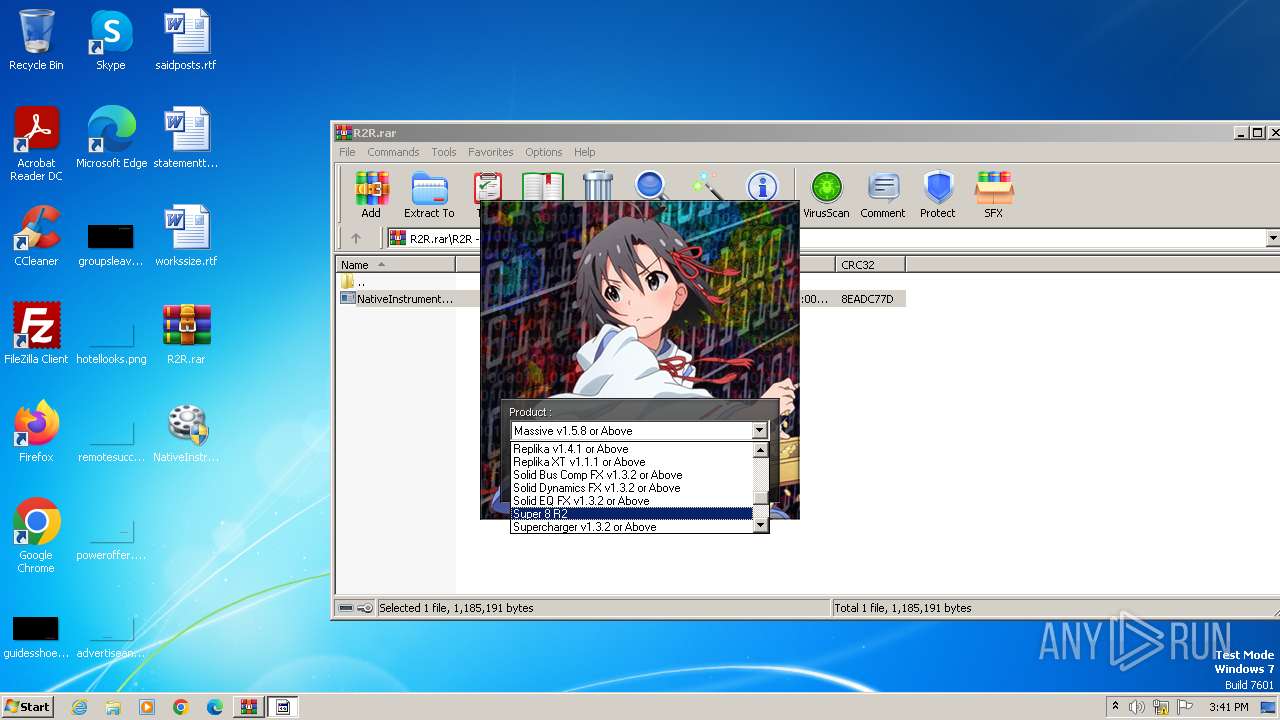
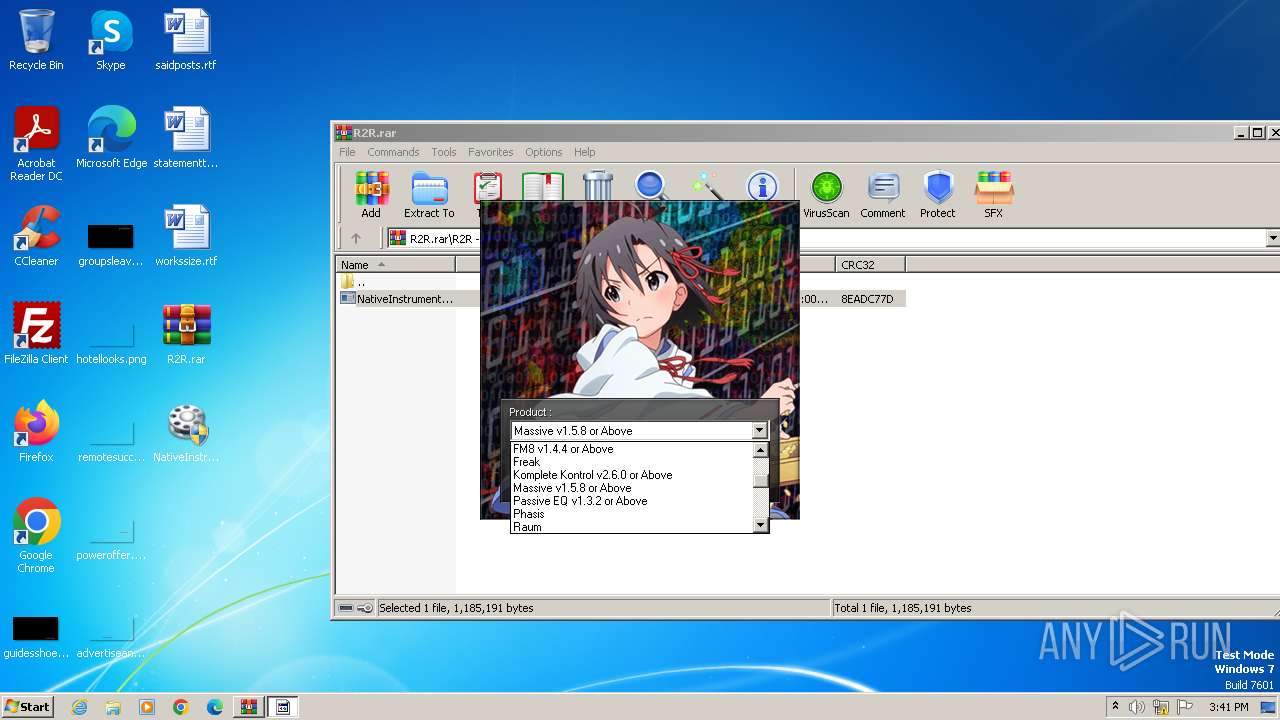
Drops the executable file immediately after the start
- NativeInstruments_Keygen.exe (PID: 3880)
SUSPICIOUS
No suspicious indicators.INFO
Checks supported languages
- NativeInstruments_Keygen.exe (PID: 3880)
- keygen.exe (PID: 3836)
Reads the computer name
- NativeInstruments_Keygen.exe (PID: 3880)
- keygen.exe (PID: 3836)
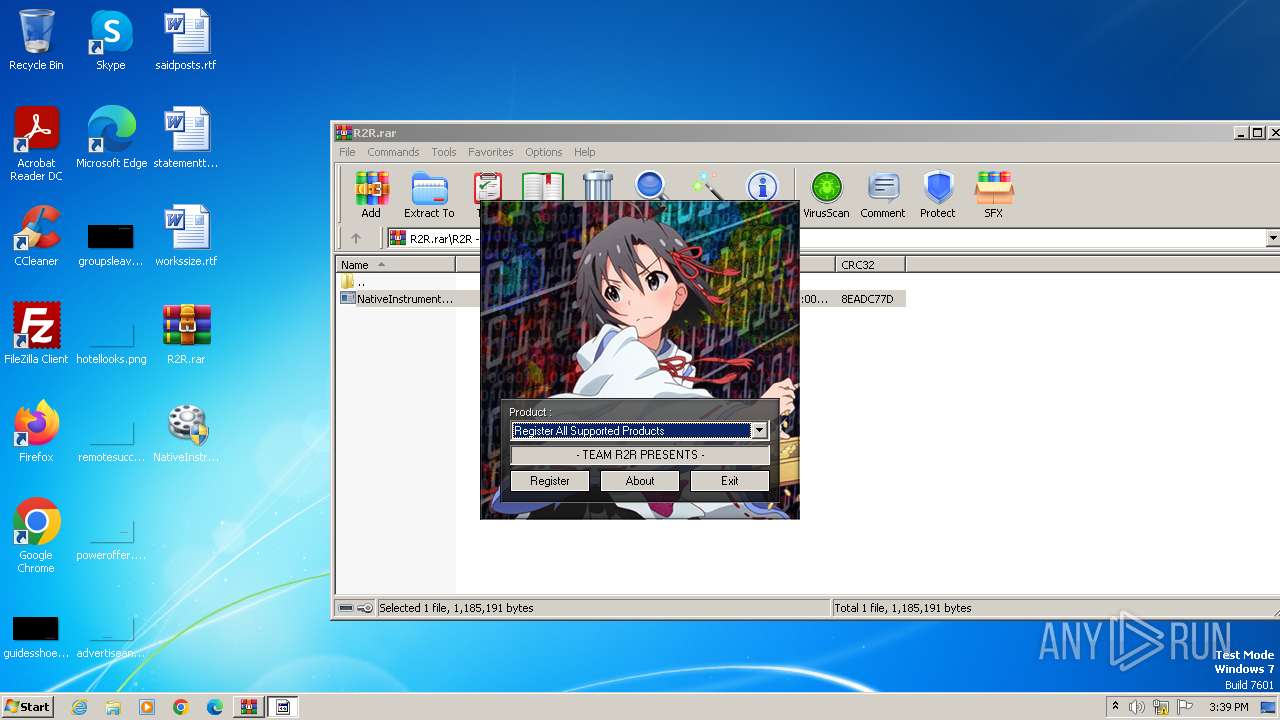
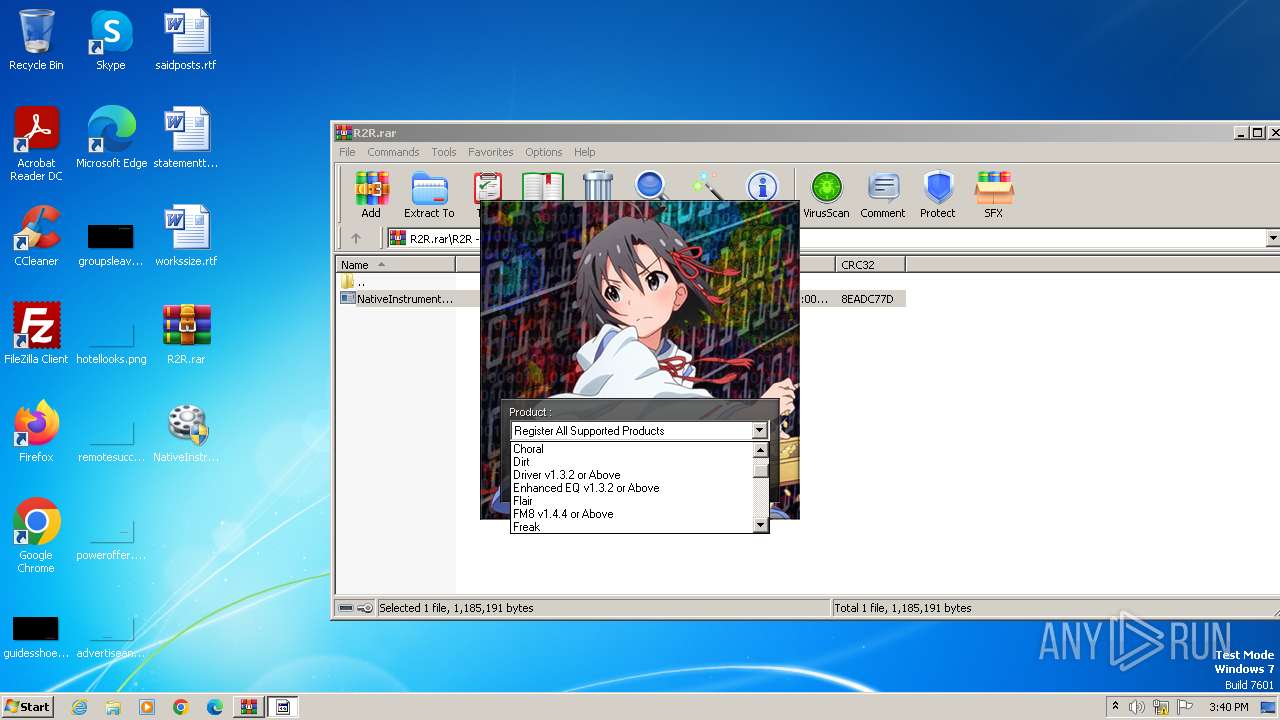
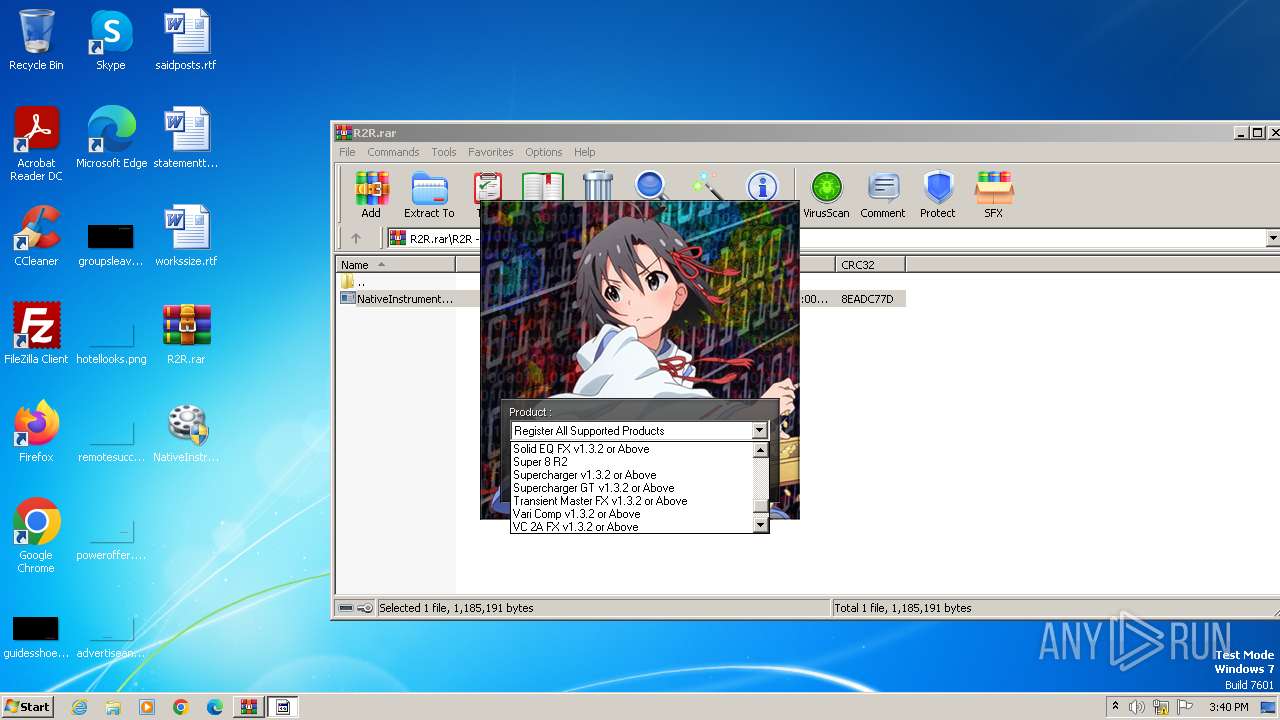
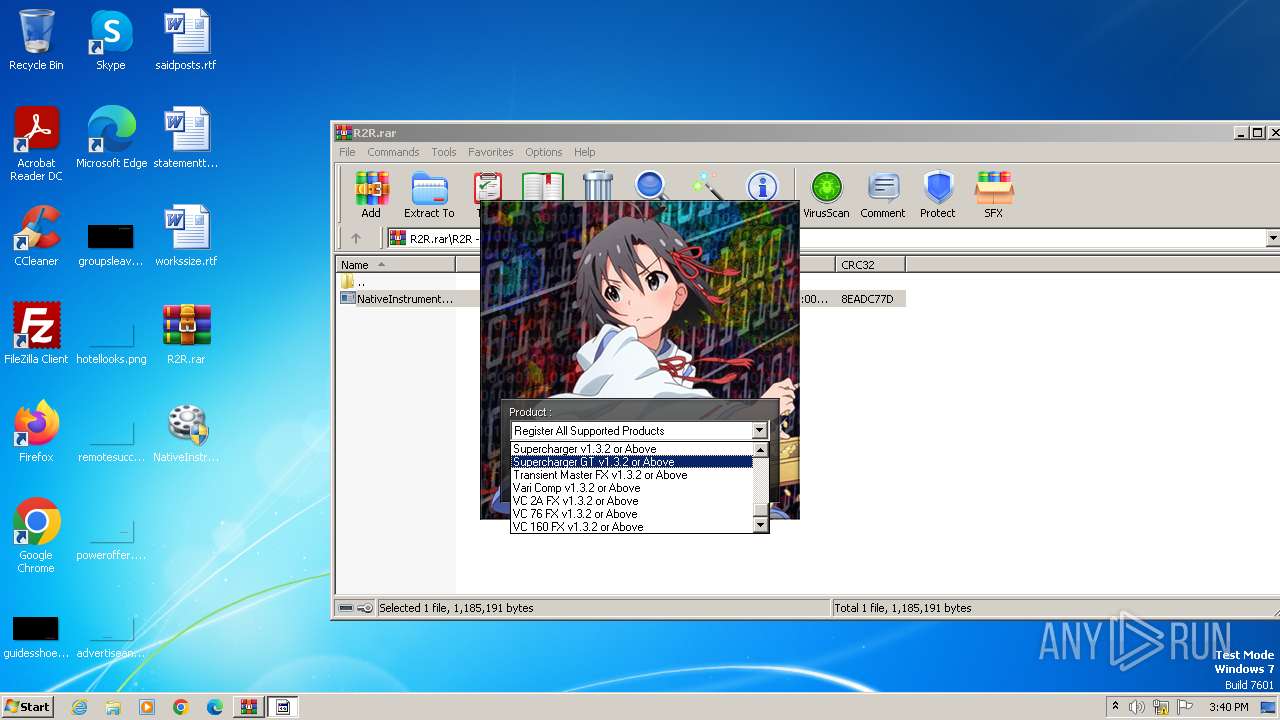
Manual execution by a user
- NativeInstruments_Keygen.exe (PID: 3516)
- NativeInstruments_Keygen.exe (PID: 3880)
Drops the executable file immediately after the start
- WinRAR.exe (PID: 3220)
Create files in a temporary directory
- keygen.exe (PID: 3836)
- NativeInstruments_Keygen.exe (PID: 3880)
Reads the machine GUID from the registry
- keygen.exe (PID: 3836)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
43
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3220 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\R2R.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 3516 | "C:\Users\admin\Desktop\NativeInstruments_Keygen.exe" | C:\Users\admin\Desktop\NativeInstruments_Keygen.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 3836 | C:\Users\admin\AppData\Local\Temp\keygen.exe | C:\Users\admin\AppData\Local\Temp\keygen.exe | — | NativeInstruments_Keygen.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3880 | "C:\Users\admin\Desktop\NativeInstruments_Keygen.exe" | C:\Users\admin\Desktop\NativeInstruments_Keygen.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
1 169
Read events
1 161
Write events
8
Delete events
0
Modification events
| (PID) Process: | (3220) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\17A\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3220) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (3220) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (3220) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (3220) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3220) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3220) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3220) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
4
Suspicious files
3
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3880 | NativeInstruments_Keygen.exe | C:\Users\admin\AppData\Local\Temp\BASSMOD.dll | executable | |
MD5:E4EC57E8508C5C4040383EBE6D367928 | SHA256:8AD9E47693E292F381DA42DDC13724A3063040E51C26F4CA8E1F8E2F1DDD547F | |||
| 3880 | NativeInstruments_Keygen.exe | C:\Users\admin\AppData\Local\Temp\keygen.exe | executable | |
MD5:F973101B44AE0CF7725391CAE0406962 | SHA256:0C0708E13D9FA85A4FA66B5A31766198E0F6D7CD0FA4A980B94AC992FFD3043C | |||
| 3836 | keygen.exe | C:\Users\Public\Documents\Native Instruments\Native Access\ras3\f1e4c3f3-300a-413f-983e-cb8fb758397e.jwt | text | |
MD5:300F86395CB98A508DDA8C23C41803A3 | SHA256:D4A9EF8F64FA8055D7B9591A804EAB02727FED184A165B3F60E99FDC9037E1E1 | |||
| 3836 | keygen.exe | C:\Users\Public\Documents\Native Instruments\Native Access\ras3\00b224af-b357-4dfe-9929-414bbdf97d6f.jwt | text | |
MD5:B2E555F3C71F55F1A2DD6233C9A3D965 | SHA256:335C19A1348F431598EA7E203D63028F81F0789B6199421C296EE3064596461F | |||
| 3880 | NativeInstruments_Keygen.exe | C:\Users\admin\AppData\Local\Temp\bgm.xm | binary | |
MD5:89E24756B8A453F3F3014AE6D1780498 | SHA256:929C62454CC0002FEC0E05E740DB6DBDE9C786CE41C8DF4CAE4AF7F59B19867D | |||
| 3836 | keygen.exe | C:\Users\admin\AppData\Local\Temp\~DF002F37913948C47A.TMP | binary | |
MD5:FA027E886606CF73AFC52FC6AD77C147 | SHA256:788C07F9C76CB477B39650E74379049F7A3233903760B8D6B7A24AF11AACEE8C | |||
| 3836 | keygen.exe | C:\Users\Public\Documents\Native Instruments\Native Access\ras3\cf11c1f6-1d76-432f-aece-52ef5305a14d.jwt | text | |
MD5:2260671FF5A04D5E76B95667CEFECA30 | SHA256:F5E95593F59BE85144AF26AA7C26E16566D4BD91445BC08A6BB4781A0477FC1C | |||
| 3836 | keygen.exe | C:\Users\Public\Documents\Native Instruments\Native Access\ras3\02cf2683-8802-4ccc-b7c4-78c89f7d3fad.jwt | text | |
MD5:153BF2842E76359A9D6F9824AEE12468 | SHA256:0470C8FAC00D50338C16E48AD72015FA0F20C0FDCA4B4829D15DEA7E35BFEDC3 | |||
| 3220 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3220.47490\R2R\NativeInstruments_Keygen.exe | executable | |
MD5:A5285B2F373FA2F61A4F95C13CC9F9A9 | SHA256:3E277411E31D818D7276565CDA7B11FDF18D2E4547DABF75E4A0E826A127A042 | |||
| 3880 | NativeInstruments_Keygen.exe | C:\Users\admin\AppData\Local\Temp\R2RNIKG3.dll | executable | |
MD5:0B60071BC47CCCE73BA68738F8F8C9CA | SHA256:C759B35280C1DDFC5BFEB9160D0D8B0649496488DB8B6D640F11AF2AA7C4C1F0 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
3
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
868 | svchost.exe | 23.218.208.137:80 | armmf.adobe.com | AKAMAI-AS | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
armmf.adobe.com |
| whitelisted |