| URL: | https://u1595434.ct.sendgrid.net/wf/click?upn=JiZk3D2bHid-2BSoMradmoehlo44qwxC68ms-2F0refP6l7er5Fnxn91KVvCXOPPAfRFsXwMHnFtY85j2yXelOvNBi0wZ0-2BlN-2Ft2ov-2B7Pszu3X-2FC-2Fy0nQST4xlXlNQ3giZ9s9oSD4z-2FVxV0mtXEfPWAexvFZ4IhXJ-2BilPPcoYFfkXomoLjxUfLfWVtasYWIIYkUKcfHuyCT6DmIKZPe-2B4mBE8zIcaQIK4u68lXBsUe7gi5Y-3D_kKLYQ91ZFOe6ryzRU3CXylIFdCdqdvp8zYD6Fhc477KMS4WeR-2Bv2eNKRWGBVMEYzhCNENOkkeDV25zzkLFsw4B89JHqJ5FqlfBtSBlN87wxBze3RDI7RwGYaAN6q1lKan4v1ux5NKcLd3WlYLIdrZtL2nwFmQfsoU-2Ft5BqRzNchu3EPdPnoQyyTbvUj6WkkC6bzok1S5A-2FFXTbazfwzB9PI2LvQ5CBgkn7lP3vbSVxtriQMLZ3e8cJjItFl4Ypu6A3-2FxOaigLLRvHkVqGREKYWcFMRPrBhoLuW6mUE4ncwcYOJraiyWxJFzeFCWwwHLKUyGUNiFdPB-2FZ5EU9HyDAS0KQn-2FfV-2FdFbF3ObdERj4wRcXNwdbJ2reh9akd64J7YYP4RBkYckrTjgkanr7bYdWQiRQNCq-2BE-2F0ylb8RdFhQyDuGNlq1jiLO4eHV-2FWloUxYrdaPYAa4FuatPbH3llEwRg-3D-3D |
| Full analysis: | https://app.any.run/tasks/4528e456-9909-4e87-8448-fe69c3a751a8 |
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2019, 12:21:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | C0DC11F07A03CE6AB0F33645842B9AFE |
| SHA1: | 333C85561CBB6C0E54AEA1052D85A6F273B53AD4 |
| SHA256: | 864455DEBB23BDAB9385B55E98B3979DBD7B02CCA3E24E0FD6DF65861477F85F |
| SSDEEP: | 12:28IDSL+QSqt9rYKR3e0UxhuCNlmu+lFl/dV7IuH1Q/egO5b9Vac3:2jRItOOg4GMx1V7IuH1IeRx9VaO |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 116)
INFO
Reads settings of System Certificates
- chrome.exe (PID: 116)
Application launched itself
- chrome.exe (PID: 116)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
52
Monitored processes
21
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | "C:\Program Files\Google\Chrome\Application\chrome.exe" https://u1595434.ct.sendgrid.net/wf/click?upn=JiZk3D2bHid-2BSoMradmoehlo44qwxC68ms-2F0refP6l7er5Fnxn91KVvCXOPPAfRFsXwMHnFtY85j2yXelOvNBi0wZ0-2BlN-2Ft2ov-2B7Pszu3X-2FC-2Fy0nQST4xlXlNQ3giZ9s9oSD4z-2FVxV0mtXEfPWAexvFZ4IhXJ-2BilPPcoYFfkXomoLjxUfLfWVtasYWIIYkUKcfHuyCT6DmIKZPe-2B4mBE8zIcaQIK4u68lXBsUe7gi5Y-3D_kKLYQ91ZFOe6ryzRU3CXylIFdCdqdvp8zYD6Fhc477KMS4WeR-2Bv2eNKRWGBVMEYzhCNENOkkeDV25zzkLFsw4B89JHqJ5FqlfBtSBlN87wxBze3RDI7RwGYaAN6q1lKan4v1ux5NKcLd3WlYLIdrZtL2nwFmQfsoU-2Ft5BqRzNchu3EPdPnoQyyTbvUj6WkkC6bzok1S5A-2FFXTbazfwzB9PI2LvQ5CBgkn7lP3vbSVxtriQMLZ3e8cJjItFl4Ypu6A3-2FxOaigLLRvHkVqGREKYWcFMRPrBhoLuW6mUE4ncwcYOJraiyWxJFzeFCWwwHLKUyGUNiFdPB-2FZ5EU9HyDAS0KQn-2FfV-2FdFbF3ObdERj4wRcXNwdbJ2reh9akd64J7YYP4RBkYckrTjgkanr7bYdWQiRQNCq-2BE-2F0ylb8RdFhQyDuGNlq1jiLO4eHV-2FWloUxYrdaPYAa4FuatPbH3llEwRg-3D-3D | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 124 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=940,15379422907693368005,9165559896744267503,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17175191762894042813 --mojo-platform-channel-handle=4292 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1332 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=940,15379422907693368005,9165559896744267503,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=7330316508615936354 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7330316508615936354 --renderer-client-id=17 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4844 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1824 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=940,15379422907693368005,9165559896744267503,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=869456481194581229 --mojo-platform-channel-handle=4616 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1936 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=940,15379422907693368005,9165559896744267503,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=66203899630775436 --mojo-platform-channel-handle=956 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2180 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=940,15379422907693368005,9165559896744267503,131072 --enable-features=PasswordImport --service-pipe-token=15540309883557182829 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15540309883557182829 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2032 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2436 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=940,15379422907693368005,9165559896744267503,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17759689092699974751 --mojo-platform-channel-handle=4252 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2496 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3960 --on-initialized-event-handle=308 --parent-handle=312 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2588 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=940,15379422907693368005,9165559896744267503,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=8336621965203225752 --mojo-platform-channel-handle=4824 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2612 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=940,15379422907693368005,9165559896744267503,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17871551985329711548 --mojo-platform-channel-handle=2904 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
579
Read events
488
Write events
86
Delete events
5
Modification events
| (PID) Process: | (116) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (116) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (116) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (116) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (116) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2496) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 116-13202828474274125 |
Value: 259 | |||
| (PID) Process: | (116) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (116) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (116) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (116) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
60
Text files
177
Unknown types
17
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 116 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 116 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 116 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 116 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 116 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 116 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\f83d95c4-d131-4416-aa73-a5e425c33f4d.tmp | — | |
MD5:— | SHA256:— | |||
| 116 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 116 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 116 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 116 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
37
DNS requests
32
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
116 | chrome.exe | GET | 200 | 173.194.5.42:80 | http://r5---sn-aigzrn7e.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=109.169.22.99&mm=28&mn=sn-aigzrn7e&ms=nvh&mt=1558354822&mv=m&pl=22&shardbypass=yes | US | crx | 842 Kb | whitelisted |
116 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRJ9L2KGL92BpjF3kAtaDtxauTmhgQUPdNQpdagre7zSmAKZdMh1Pj41g8CEAbxNUGQezu6vTM9z0AgqpM%3D | US | der | 471 b | whitelisted |
116 | chrome.exe | GET | 200 | 195.138.255.9:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | DE | compressed | 56.1 Kb | whitelisted |
116 | chrome.exe | GET | 302 | 172.217.22.46:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 504 b | whitelisted |
116 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAx5qUSwjBGVIJJhX%2BJrHYM%3D | US | der | 471 b | whitelisted |
116 | chrome.exe | GET | 200 | 52.85.22.245:80 | http://x.ss2.us/x.cer | US | der | 1.27 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
116 | chrome.exe | 172.217.22.67:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
116 | chrome.exe | 167.89.115.54:443 | u1595434.ct.sendgrid.net | SendGrid, Inc. | US | suspicious |
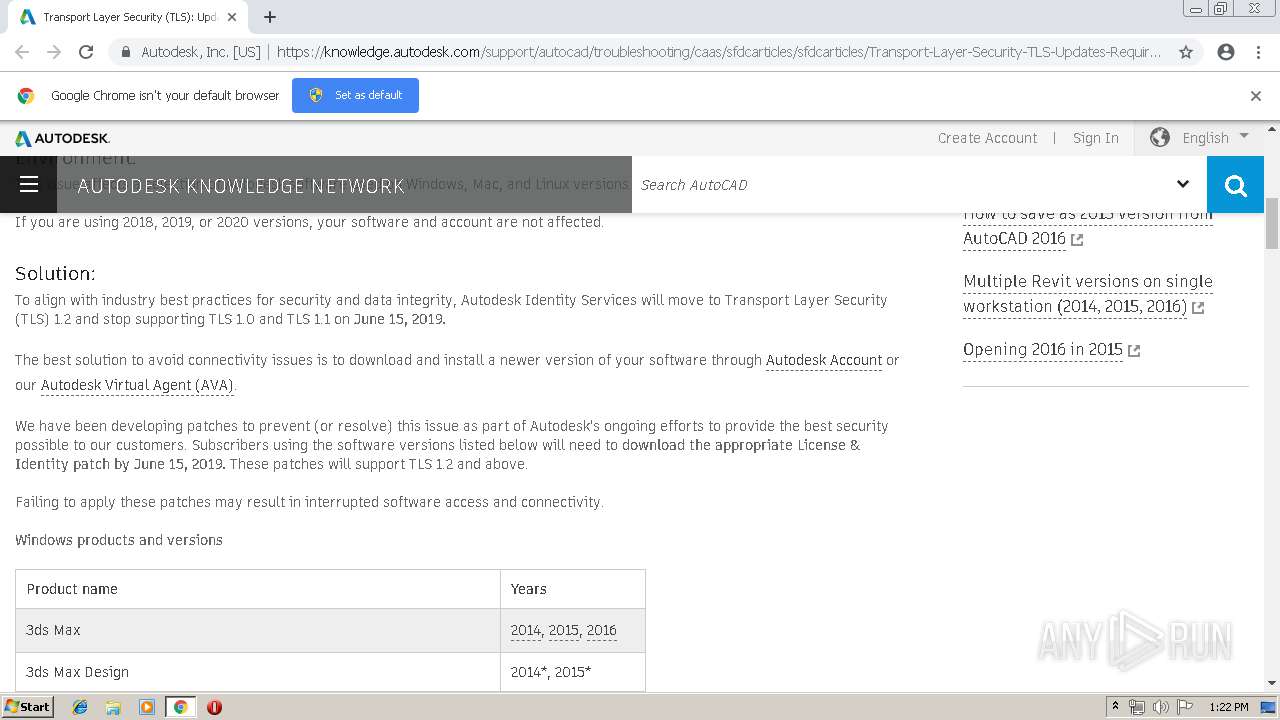
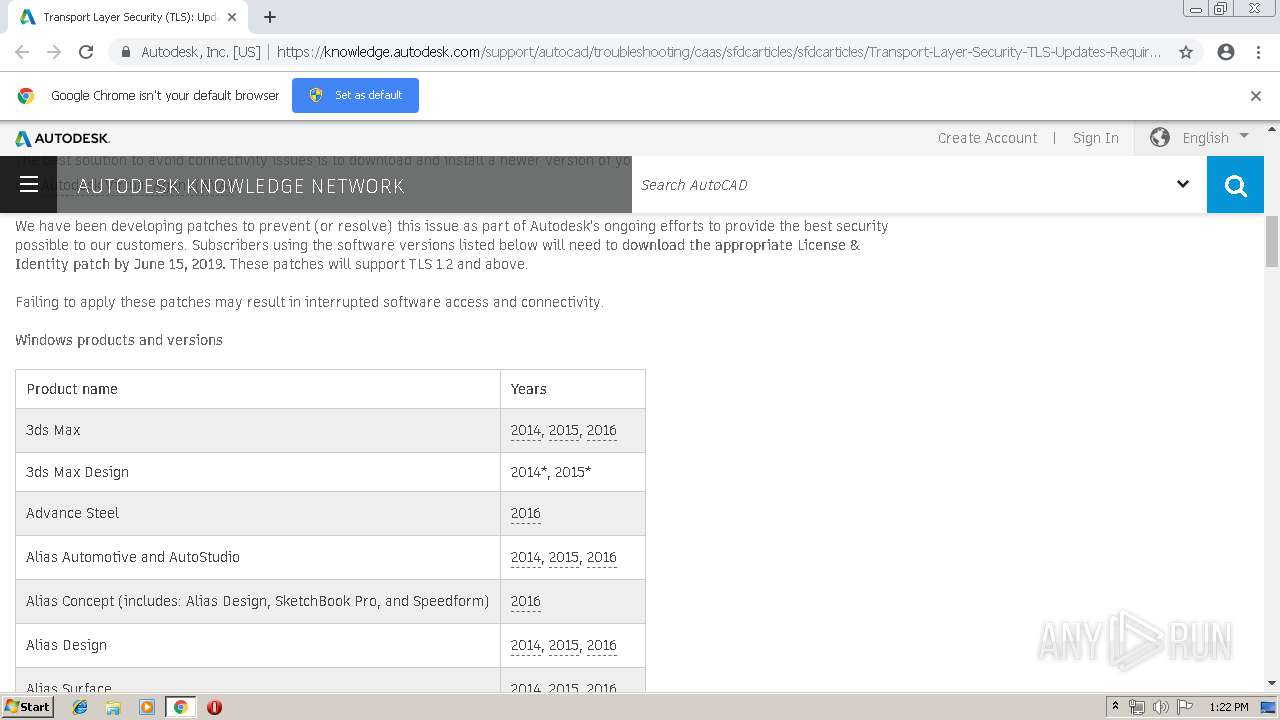
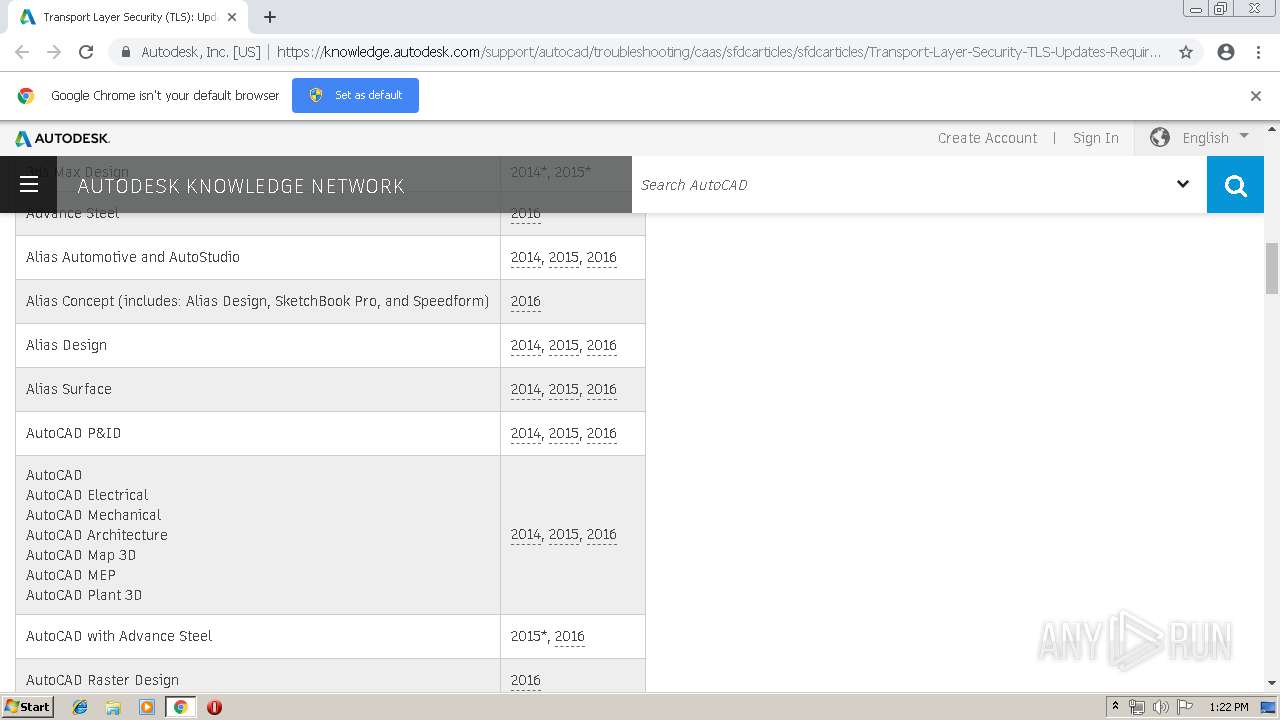
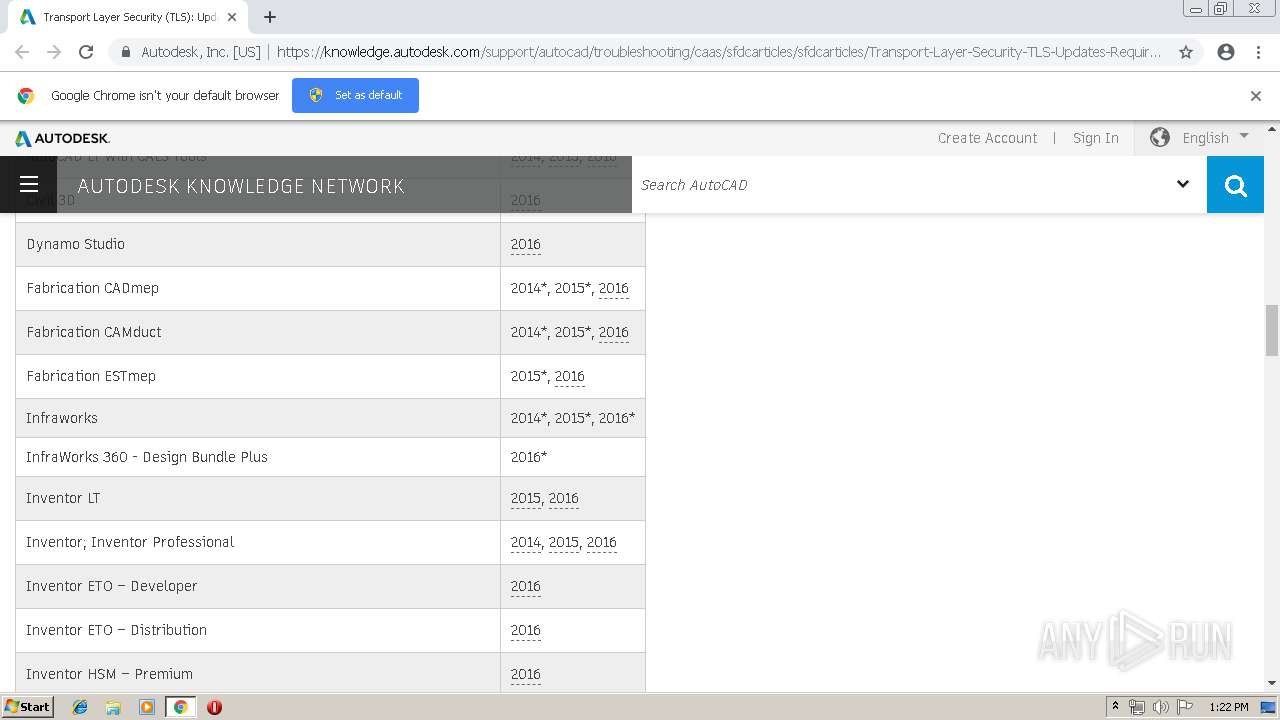
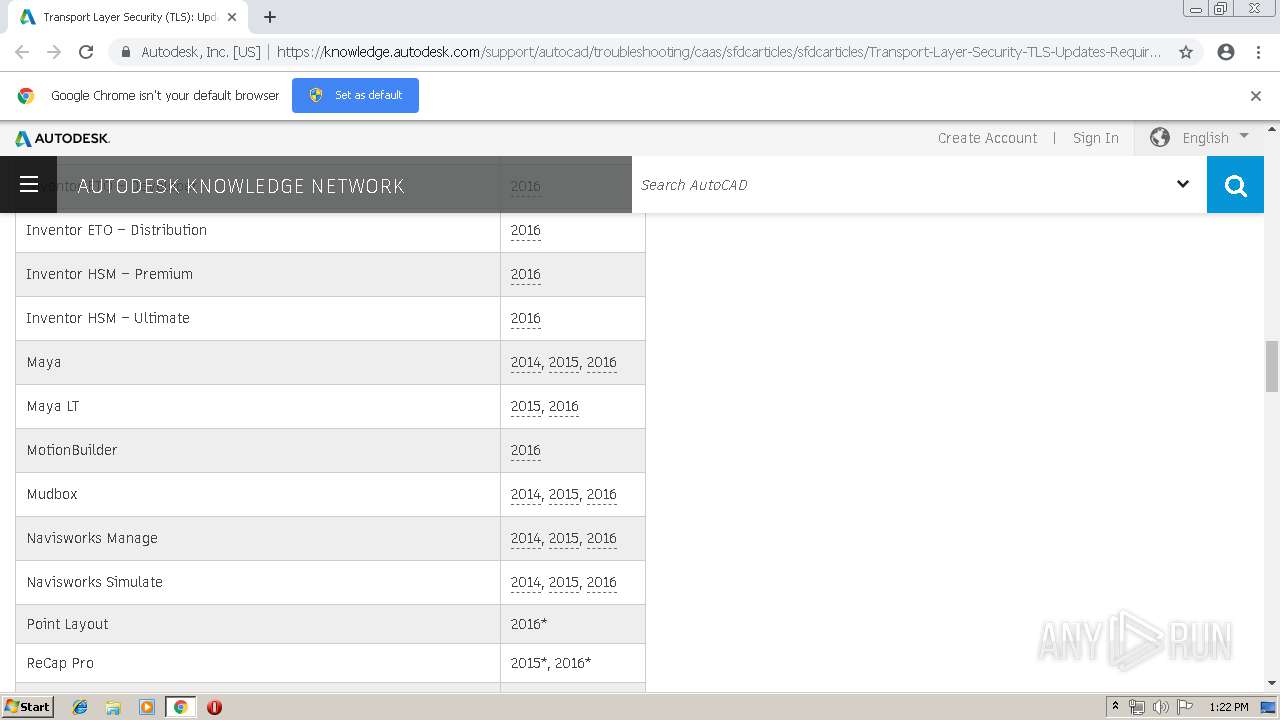
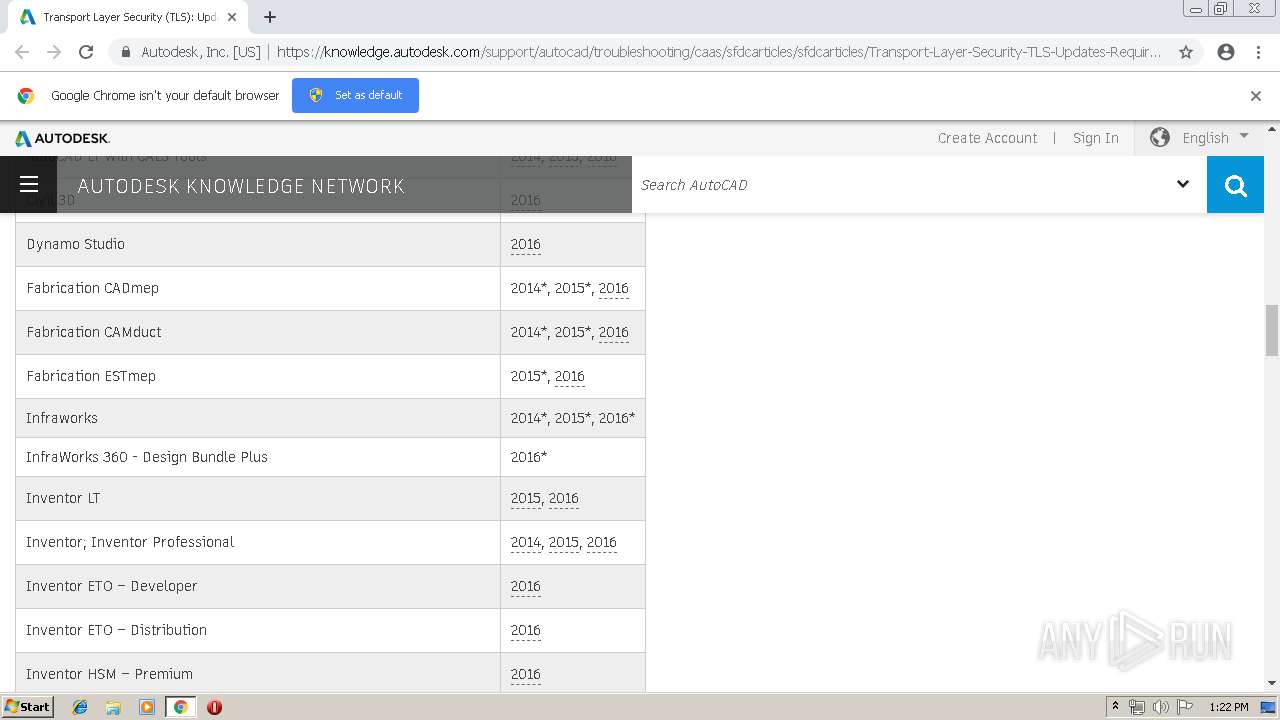
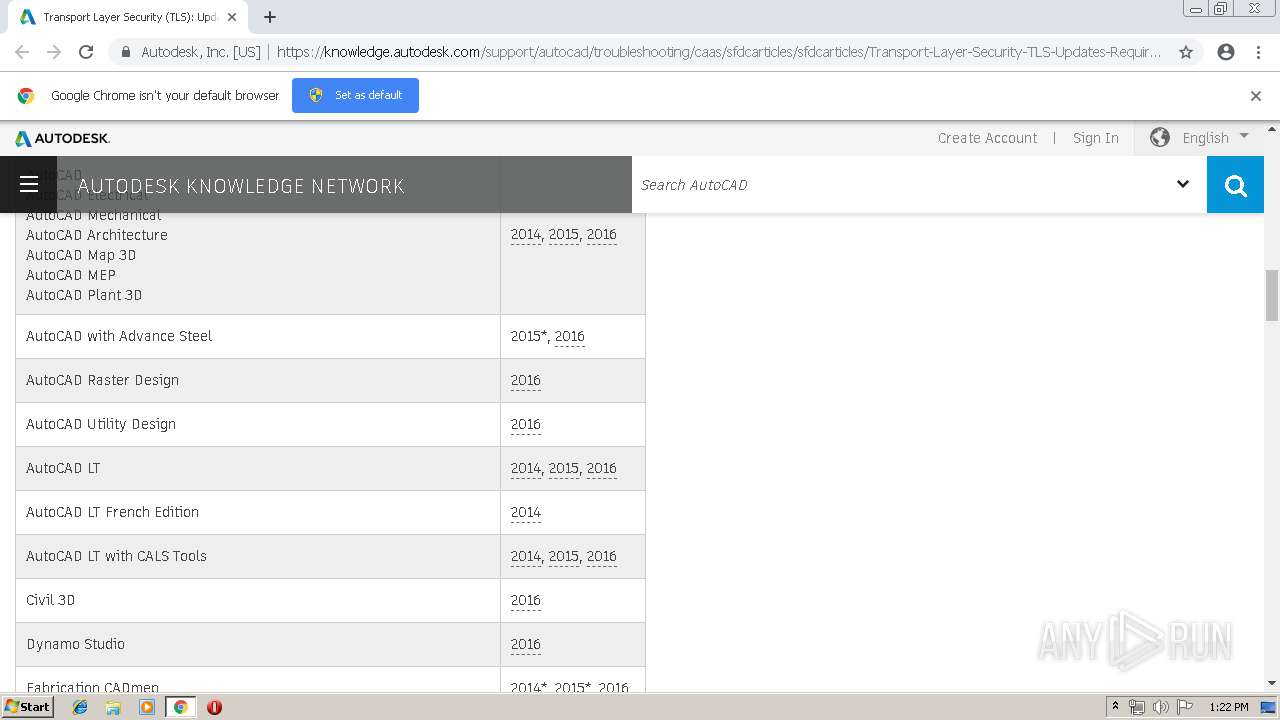
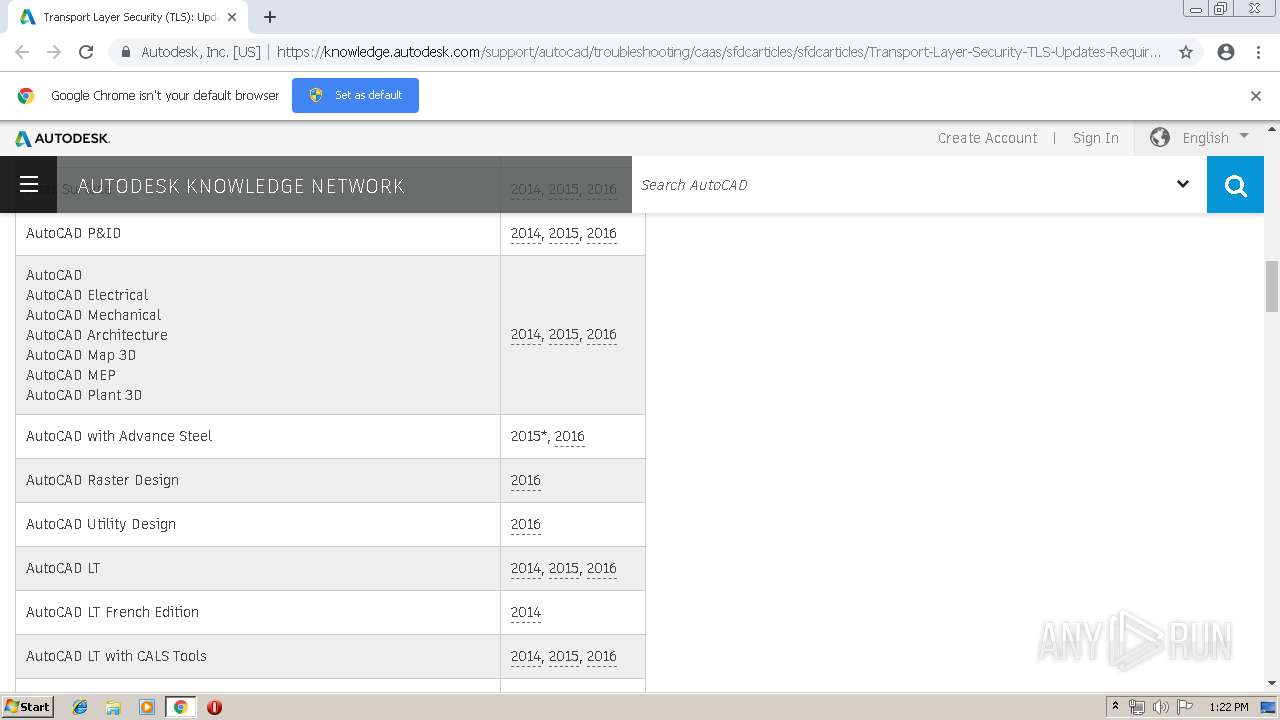
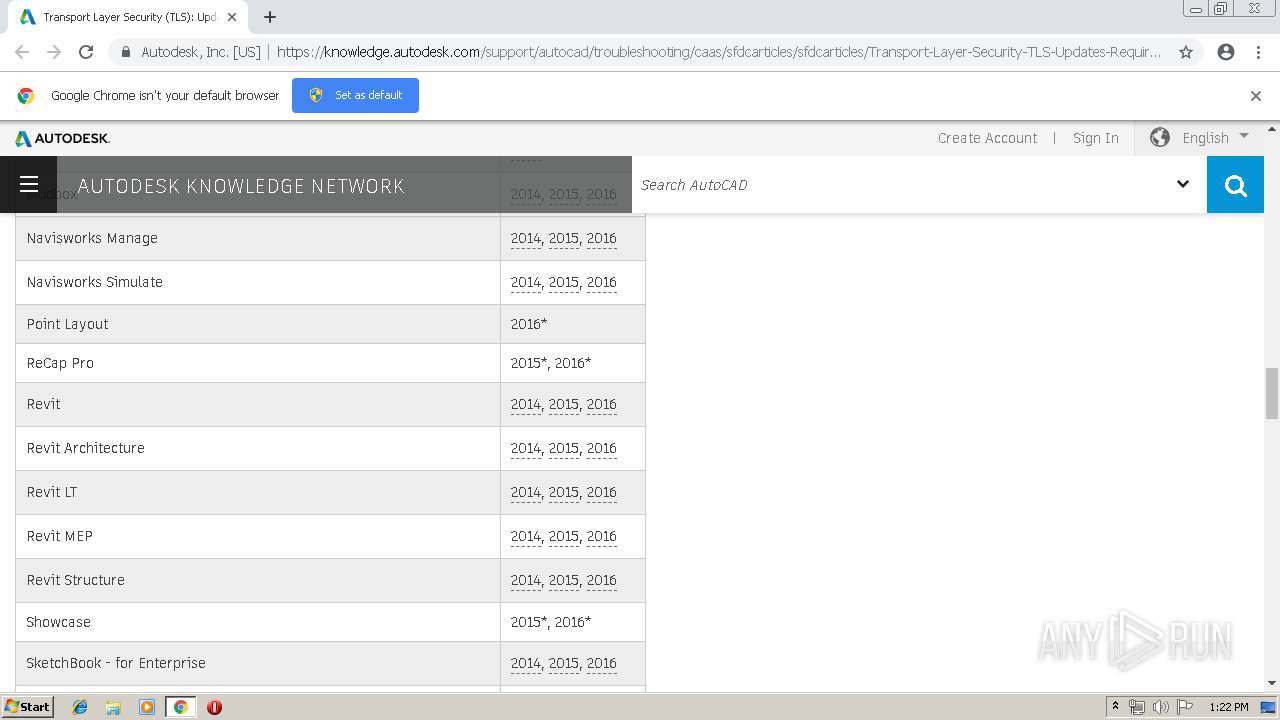
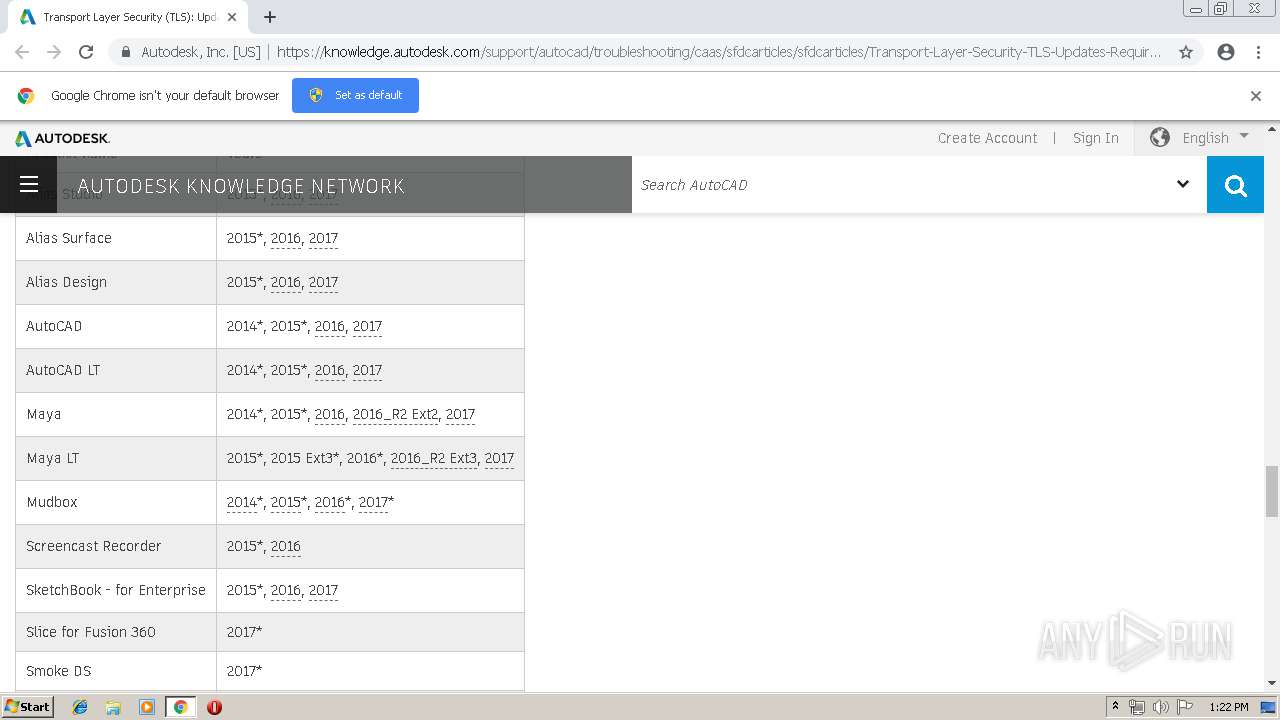
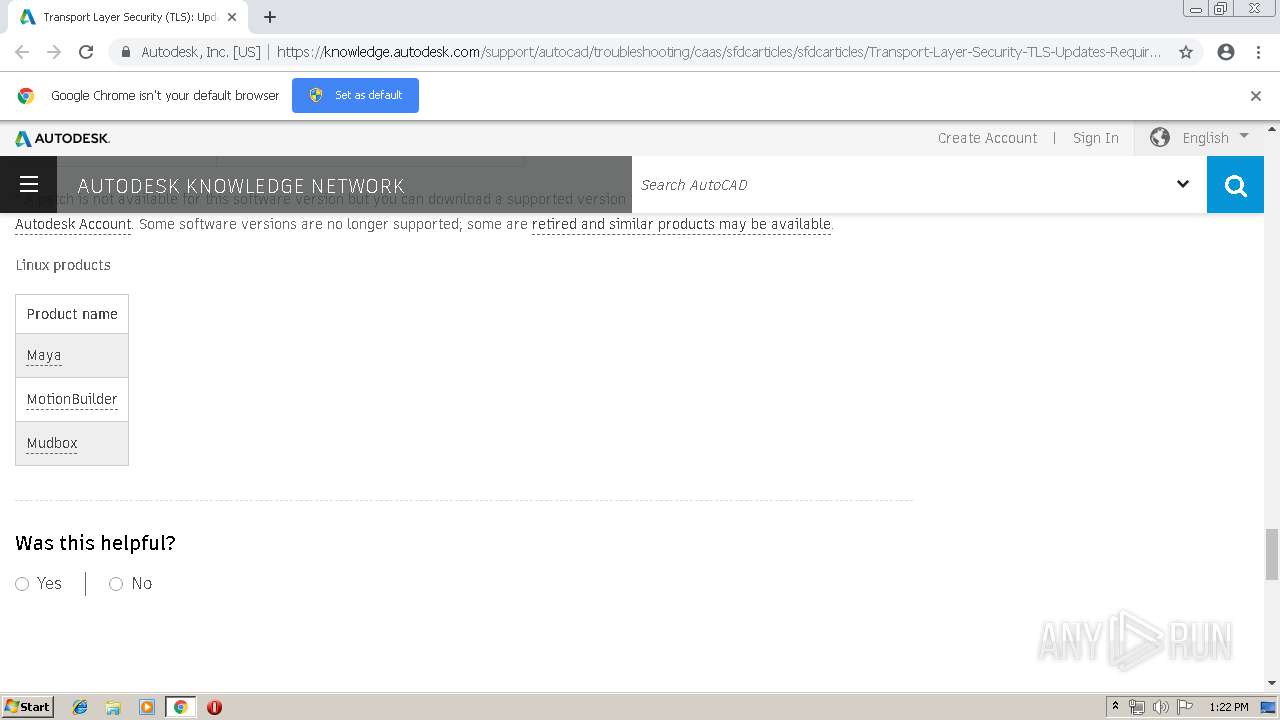
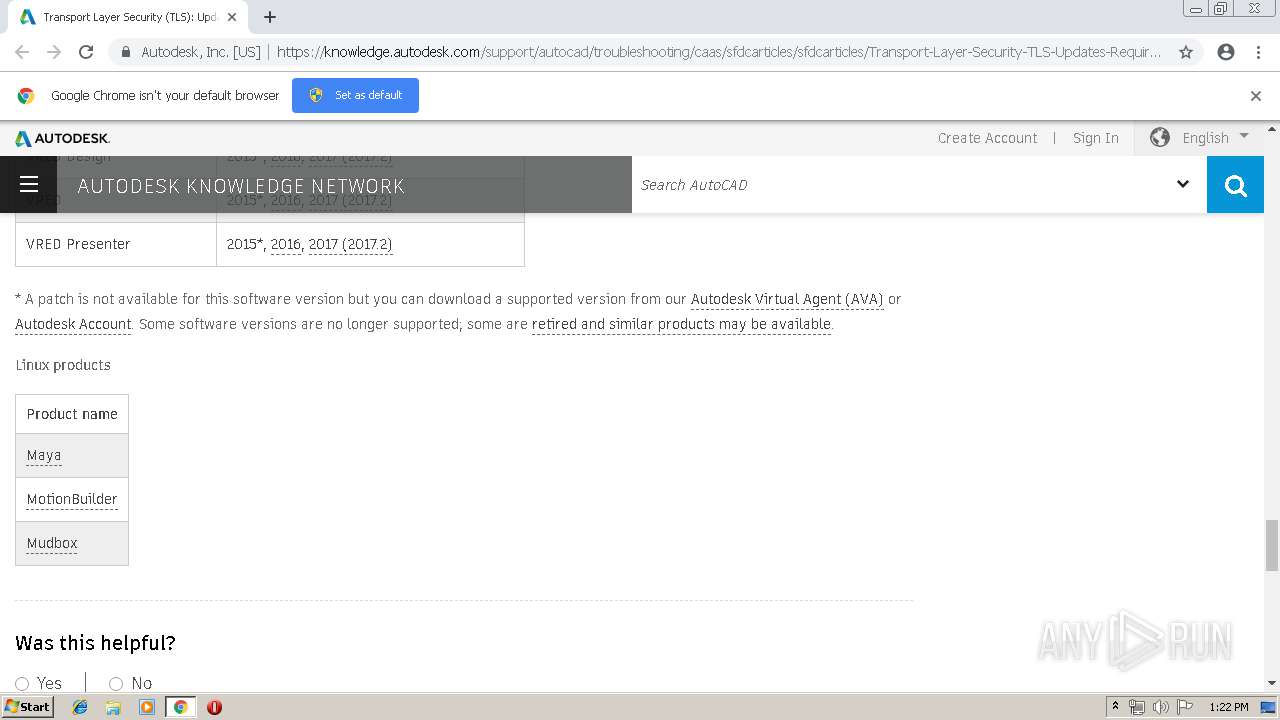
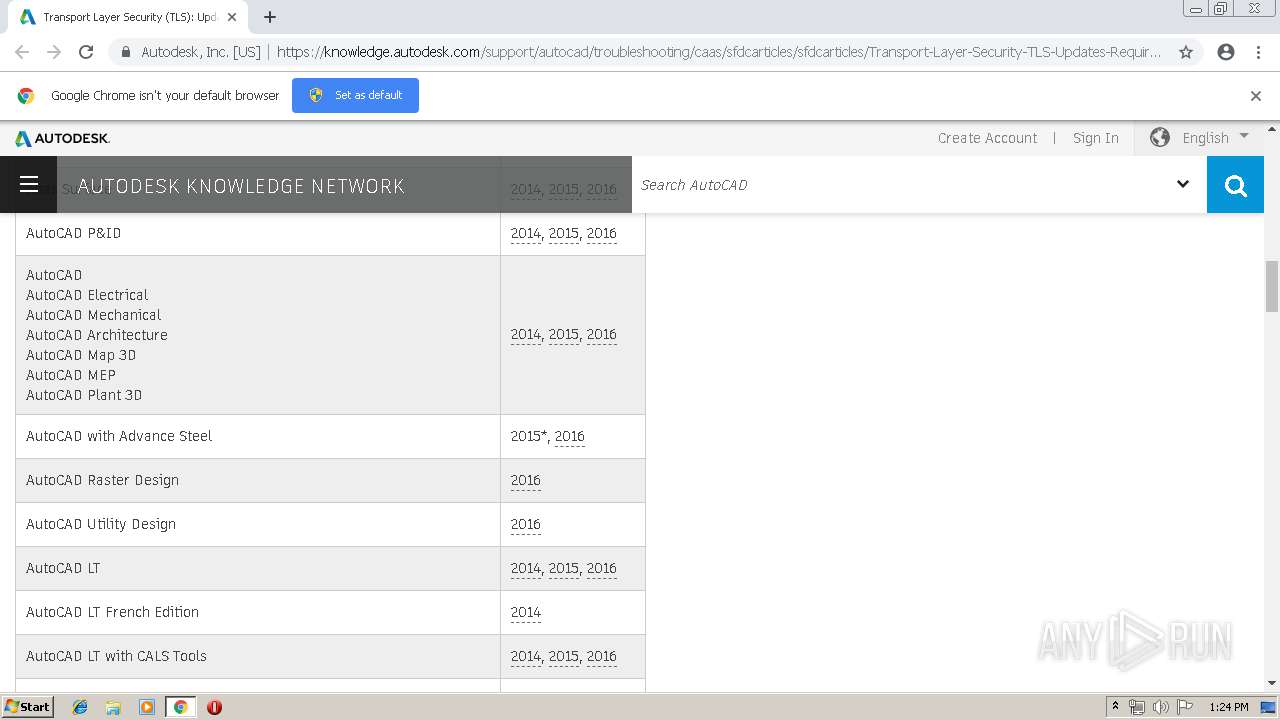
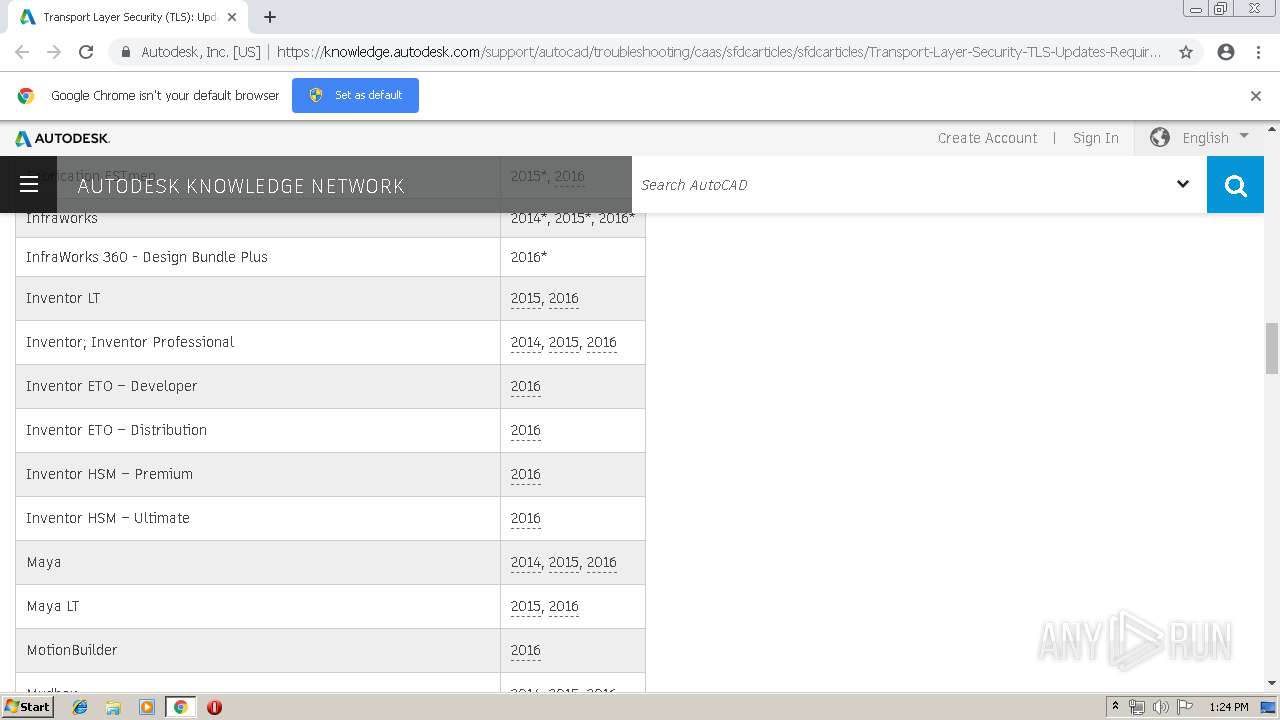
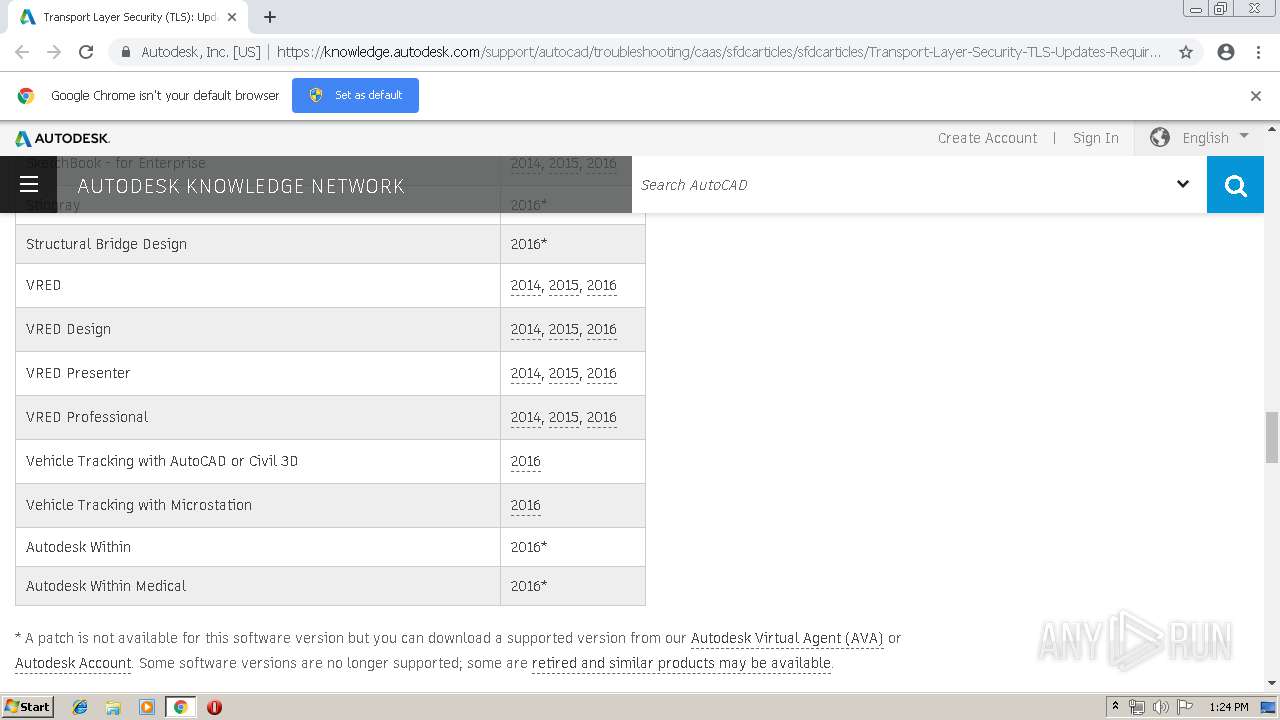
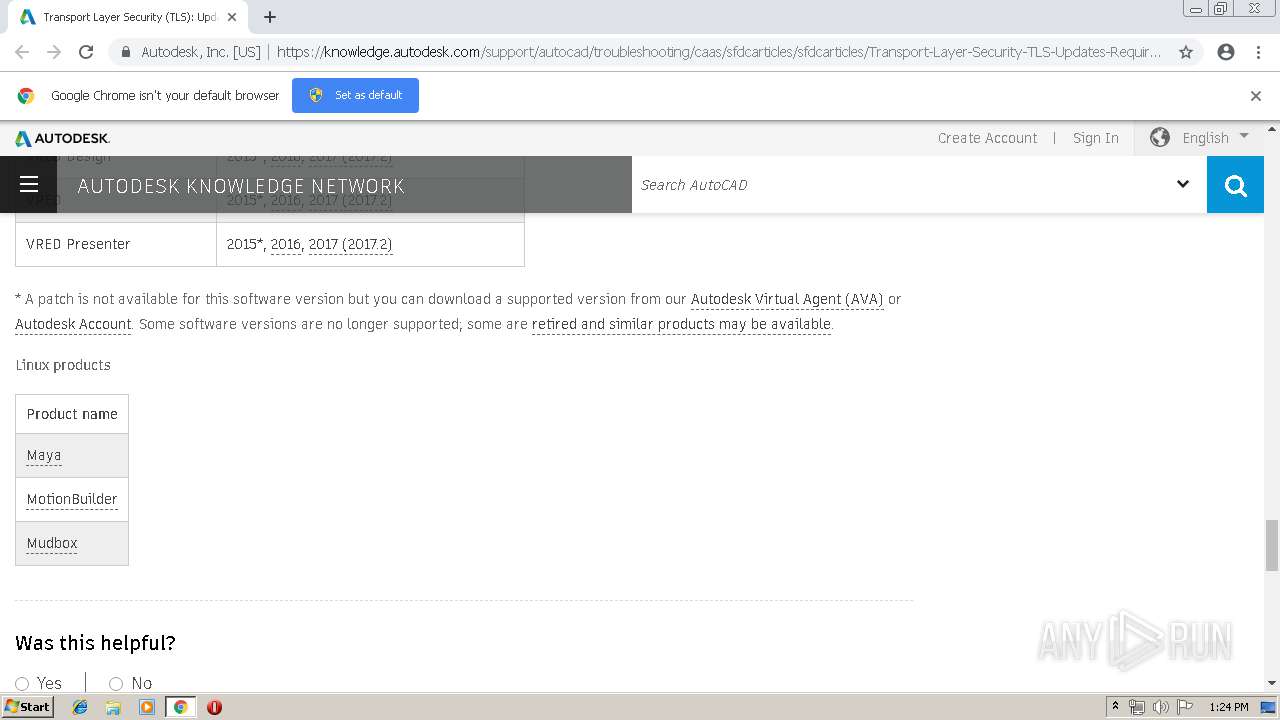
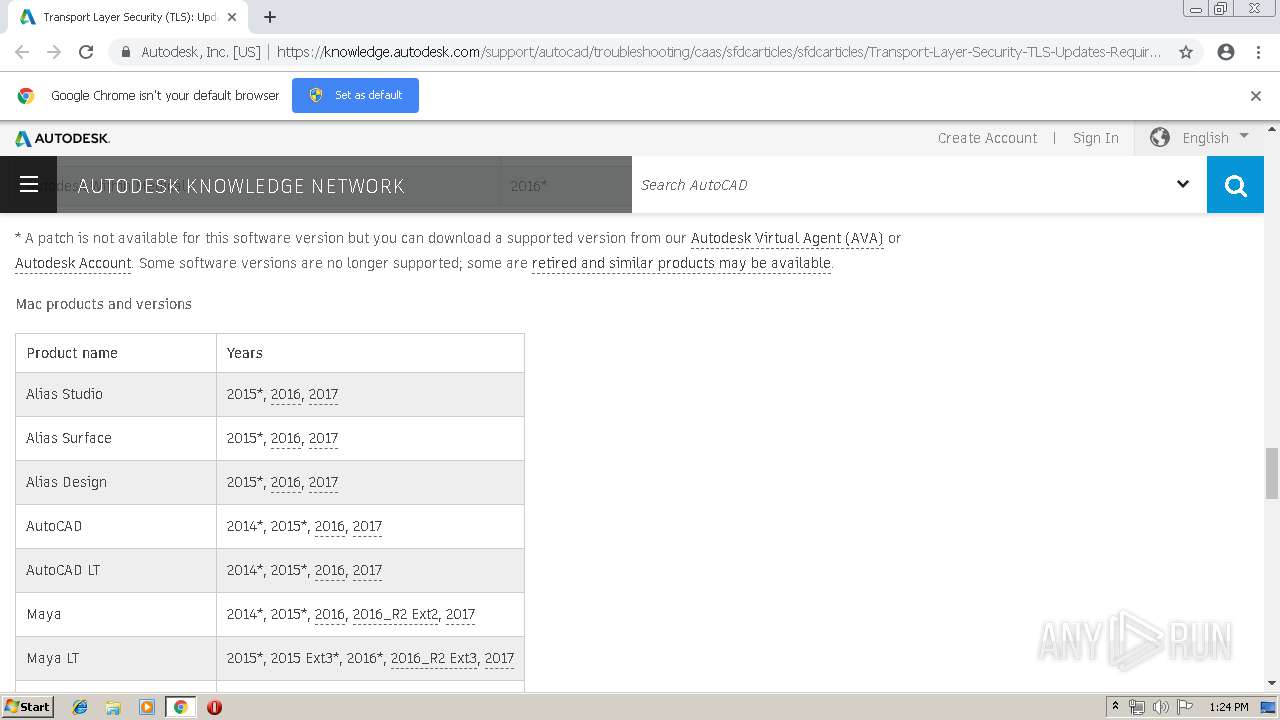
116 | chrome.exe | 104.103.89.178:443 | knowledge.autodesk.com | Akamai Technologies, Inc. | NL | whitelisted |
116 | chrome.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
116 | chrome.exe | 104.19.196.151:443 | cdnjs.cloudflare.com | Cloudflare Inc | US | shared |
116 | chrome.exe | 68.232.35.180:443 | tags.tiqcdn.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
116 | chrome.exe | 54.192.216.144:443 | api.demandbase.com | Amazon.com, Inc. | US | unknown |
116 | chrome.exe | 216.58.205.238:443 | clients1.google.com | Google Inc. | US | whitelisted |
116 | chrome.exe | 104.103.88.251:443 | beehive.autodesk.com | Akamai Technologies, Inc. | NL | whitelisted |
116 | chrome.exe | 54.192.216.13:443 | fonts.autodesk.com | Amazon.com, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
u1595434.ct.sendgrid.net |
| whitelisted |
accounts.google.com |
| shared |
knowledge.autodesk.com |
| unknown |
ocsp.digicert.com |
| whitelisted |
tags.tiqcdn.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
akn.unifiedprofile.autodesk.com |
| unknown |
api.demandbase.com |
| whitelisted |
fonts.autodesk.com |
| shared |