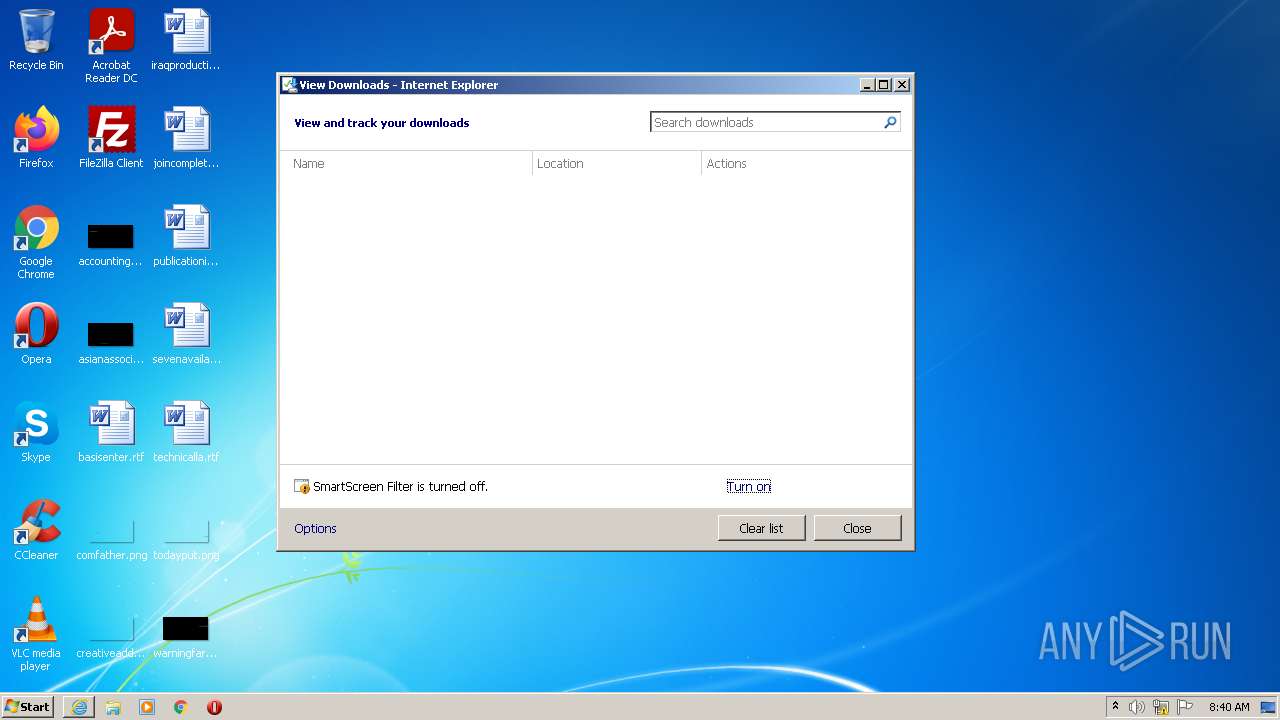
| URL: | https://www.lunkr.cn/dl?p=mail&arch_type=win32.exe |
| Full analysis: | https://app.any.run/tasks/8937d258-ac07-4d03-9a07-2b3b518f1553 |
| Verdict: | Malicious activity |
| Analysis date: | April 01, 2022, 07:38:18 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 197FB4B3C99947C82FAE008BCF438A2B |
| SHA1: | 75F53628C7842E58DC2B02241005A78AE8A578B3 |
| SHA256: | 8642534E5836B61C717CCA11F1B87D21C4FC72026B4CAD28E04A08533DDCC14F |
| SSDEEP: | 3:N8DSLU4yLKREwNXkAn:2OLSLmE8XkA |
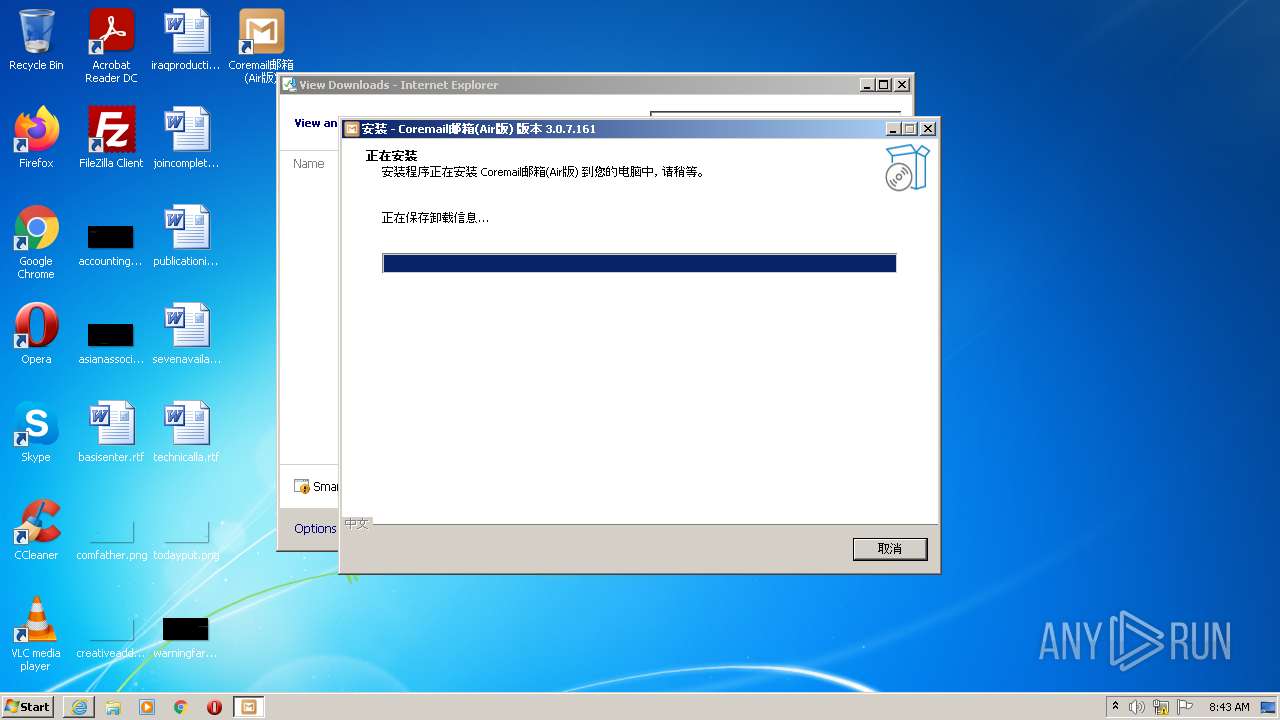
MALICIOUS
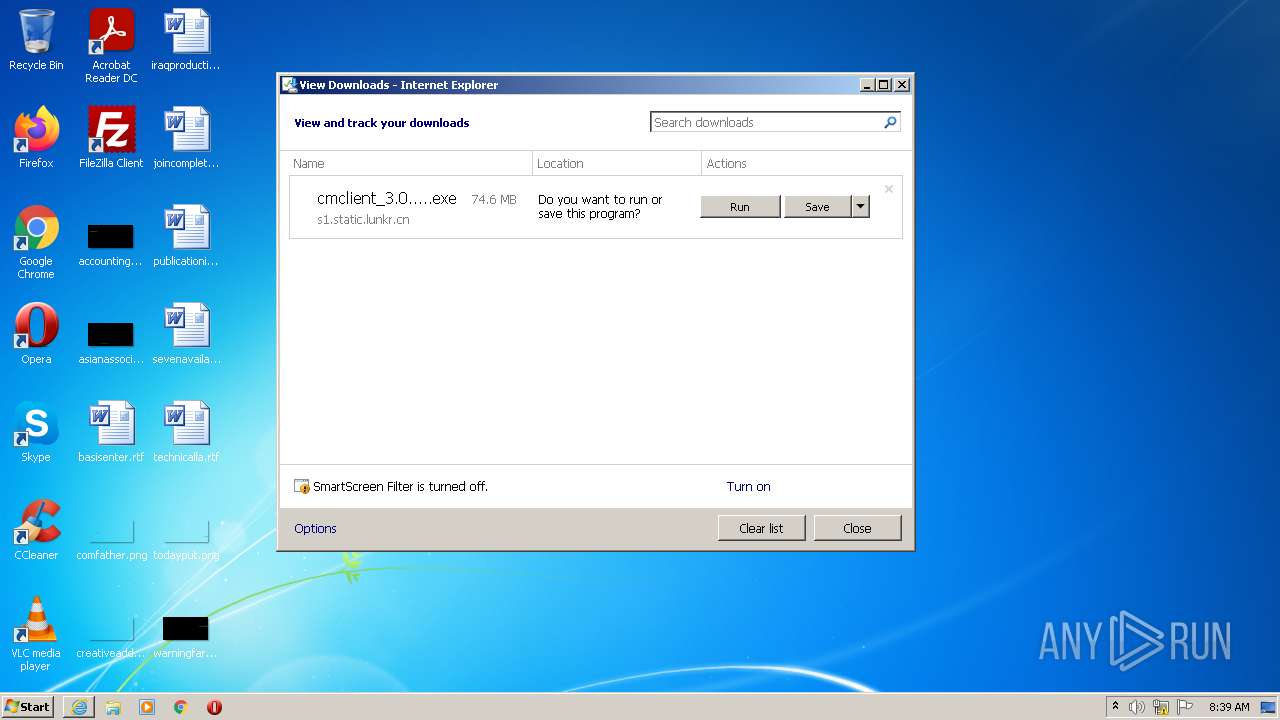
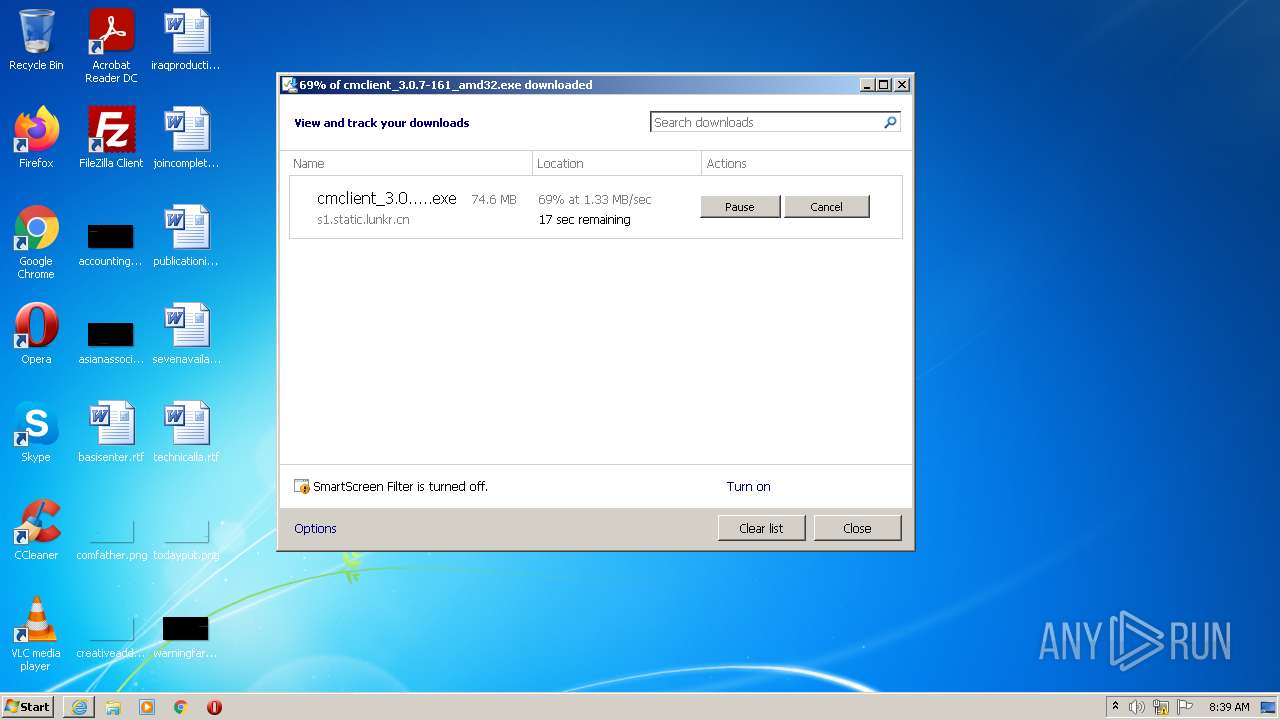
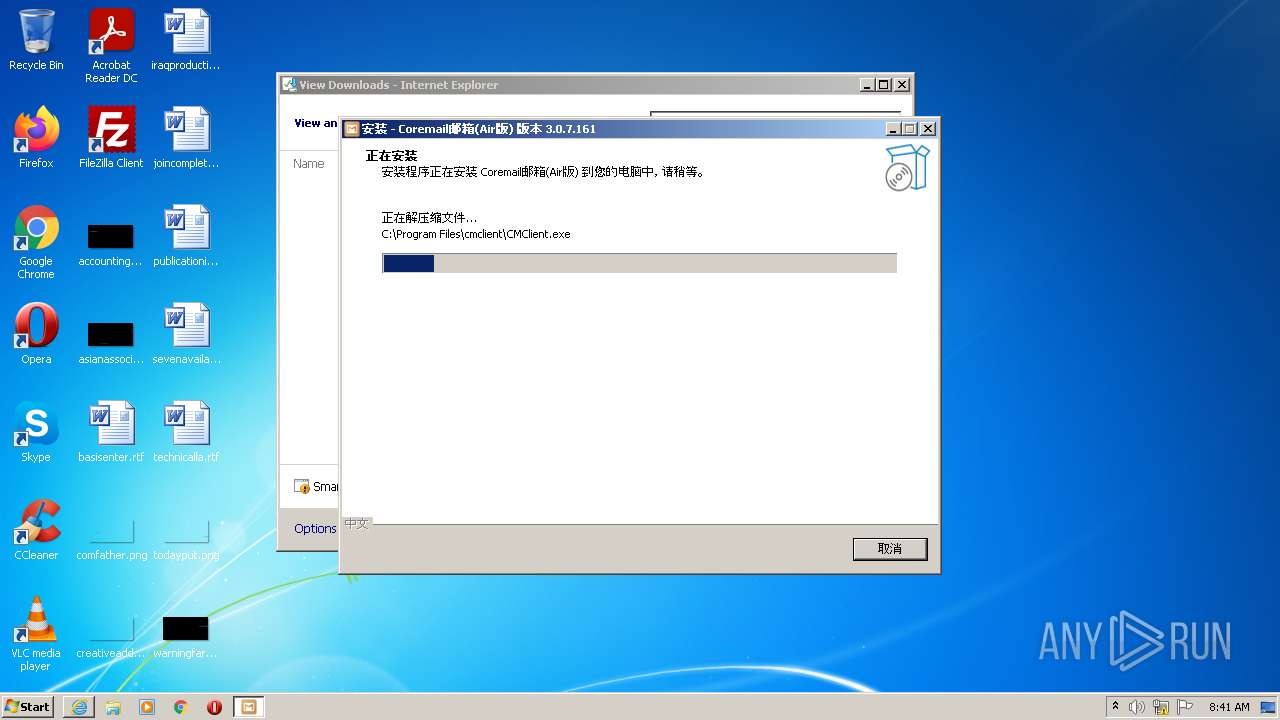
Drops executable file immediately after starts
- cmclient_3.0.7-161_amd32.exe (PID: 2980)
- cmclient_3.0.7-161_amd32.exe (PID: 3848)
Application was dropped or rewritten from another process
- CMClient.exe (PID: 3884)
- CMCefApp.exe (PID: 4016)
- CMCefApp.exe (PID: 2792)
- CMCefApp.exe (PID: 1964)
- CMCefApp.exe (PID: 2640)
- CMCefApp.exe (PID: 3864)
- CMCefApp.exe (PID: 3348)
- CMCefApp.exe (PID: 2364)
Loads dropped or rewritten executable
- CMClient.exe (PID: 3884)
- CMCefApp.exe (PID: 4016)
- CMCefApp.exe (PID: 2792)
- CMCefApp.exe (PID: 1964)
- CMCefApp.exe (PID: 2640)
- CMCefApp.exe (PID: 3864)
- CMCefApp.exe (PID: 3348)
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2148)
Executable content was dropped or overwritten
- iexplore.exe (PID: 2148)
- cmclient_3.0.7-161_amd32.exe (PID: 2980)
- cmclient_3.0.7-161_amd32.exe (PID: 3848)
- cmclient_3.0.7-161_amd32.tmp (PID: 2288)
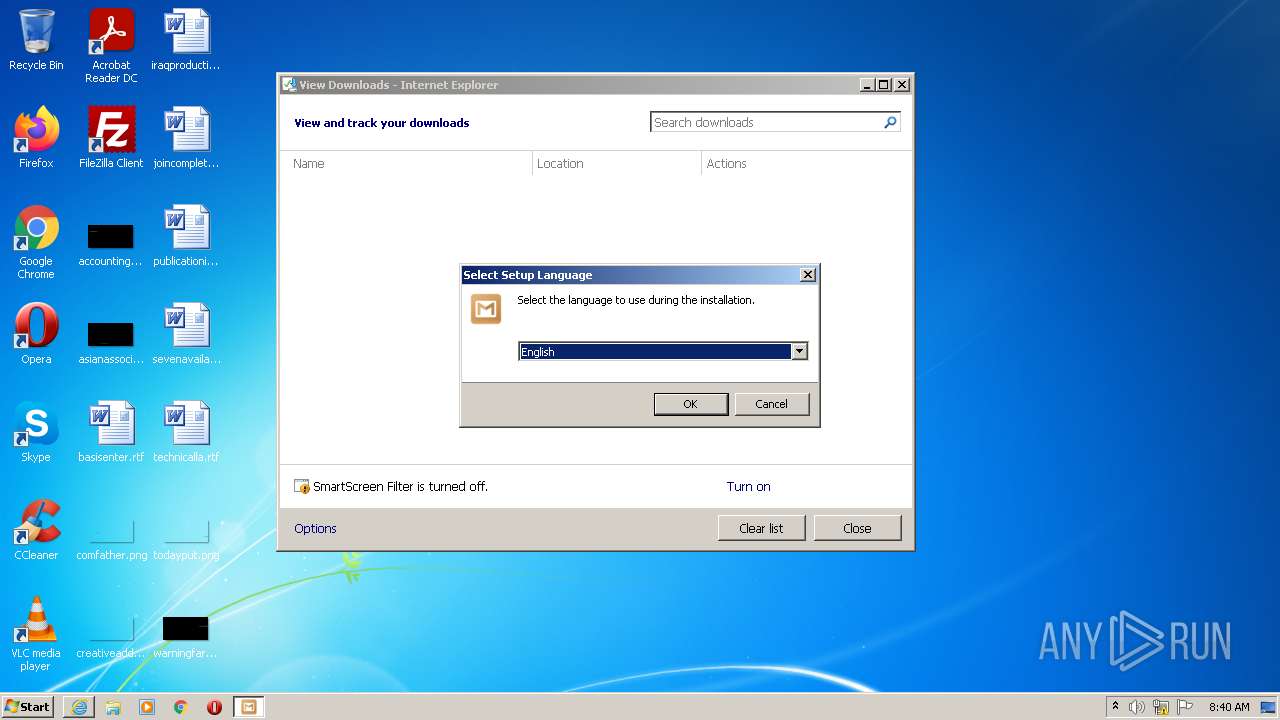
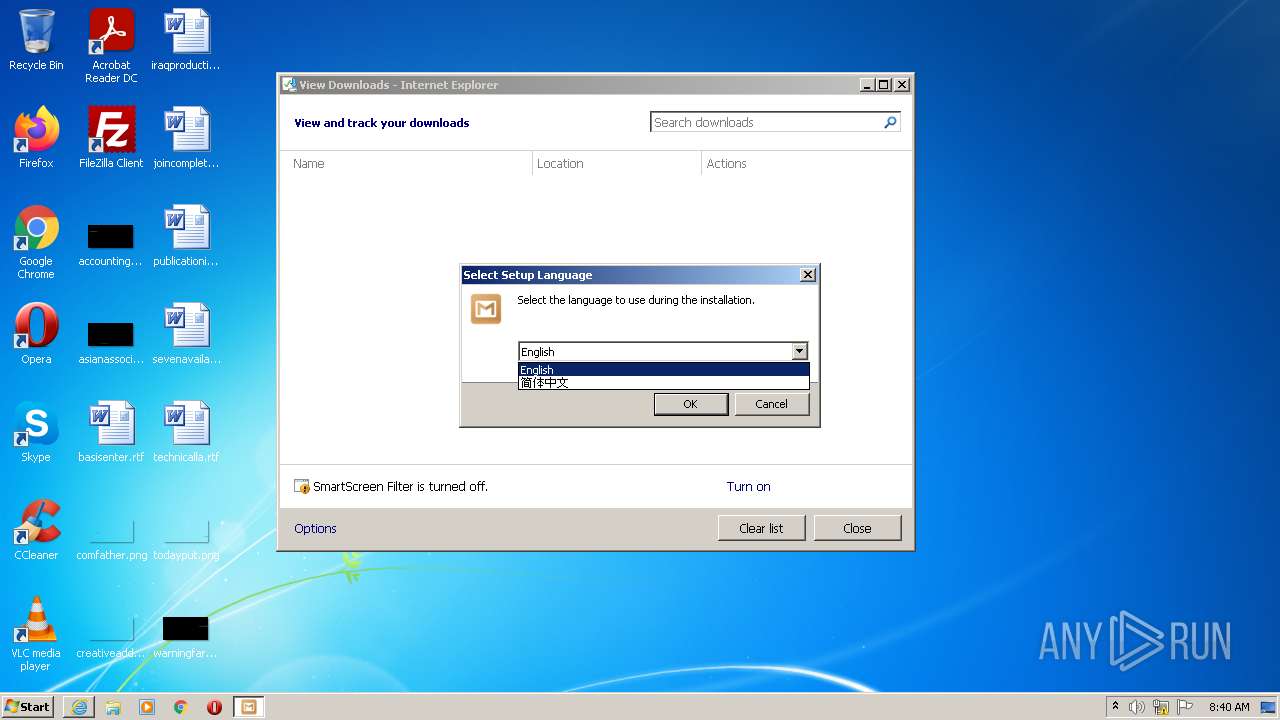
Checks supported languages
- cmclient_3.0.7-161_amd32.exe (PID: 2980)
- cmclient_3.0.7-161_amd32.tmp (PID: 3860)
- cmclient_3.0.7-161_amd32.exe (PID: 3848)
- cmclient_3.0.7-161_amd32.tmp (PID: 2288)
- CMClient.exe (PID: 3884)
- CMCefApp.exe (PID: 4016)
- wmic.exe (PID: 4028)
- CMCefApp.exe (PID: 2792)
- CMCefApp.exe (PID: 1964)
- wmic.exe (PID: 3788)
- CMCefApp.exe (PID: 2640)
- cmd.exe (PID: 1332)
- CMCefApp.exe (PID: 3348)
- CMCefApp.exe (PID: 3864)
Reads the computer name
- cmclient_3.0.7-161_amd32.tmp (PID: 3860)
- cmclient_3.0.7-161_amd32.tmp (PID: 2288)
- CMClient.exe (PID: 3884)
- wmic.exe (PID: 4028)
- CMCefApp.exe (PID: 2792)
- wmic.exe (PID: 3788)
Reads Windows owner or organization settings
- cmclient_3.0.7-161_amd32.tmp (PID: 2288)
Reads the Windows organization settings
- cmclient_3.0.7-161_amd32.tmp (PID: 2288)
Drops a file with a compile date too recent
- cmclient_3.0.7-161_amd32.tmp (PID: 2288)
Drops a file with too old compile date
- cmclient_3.0.7-161_amd32.tmp (PID: 2288)
Drops a file that was compiled in debug mode
- cmclient_3.0.7-161_amd32.tmp (PID: 2288)
Creates files in the user directory
- cmclient_3.0.7-161_amd32.tmp (PID: 2288)
- CMClient.exe (PID: 3884)
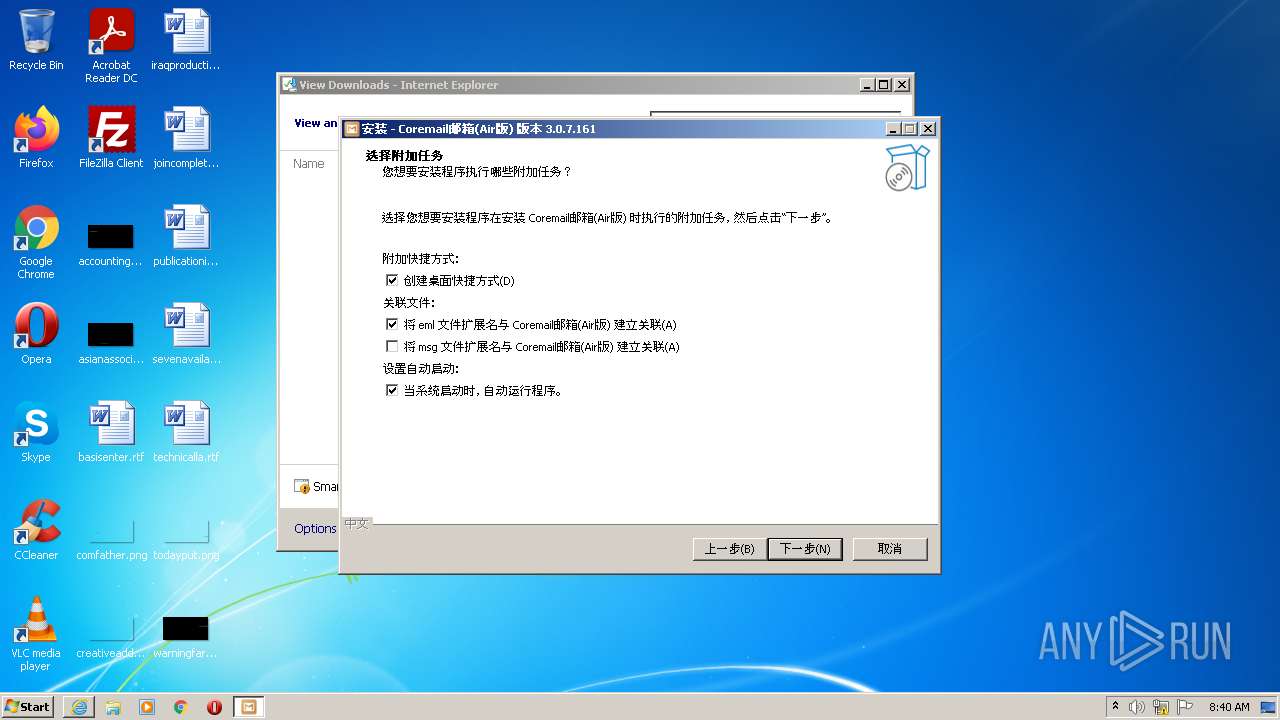
Changes default file association
- cmclient_3.0.7-161_amd32.tmp (PID: 2288)
Uses NETSH.EXE for network configuration
- cmclient_3.0.7-161_amd32.tmp (PID: 2288)
Reads Environment values
- netsh.exe (PID: 1728)
- netsh.exe (PID: 336)
Uses WMIC.EXE to obtain a system information
- CMClient.exe (PID: 3884)
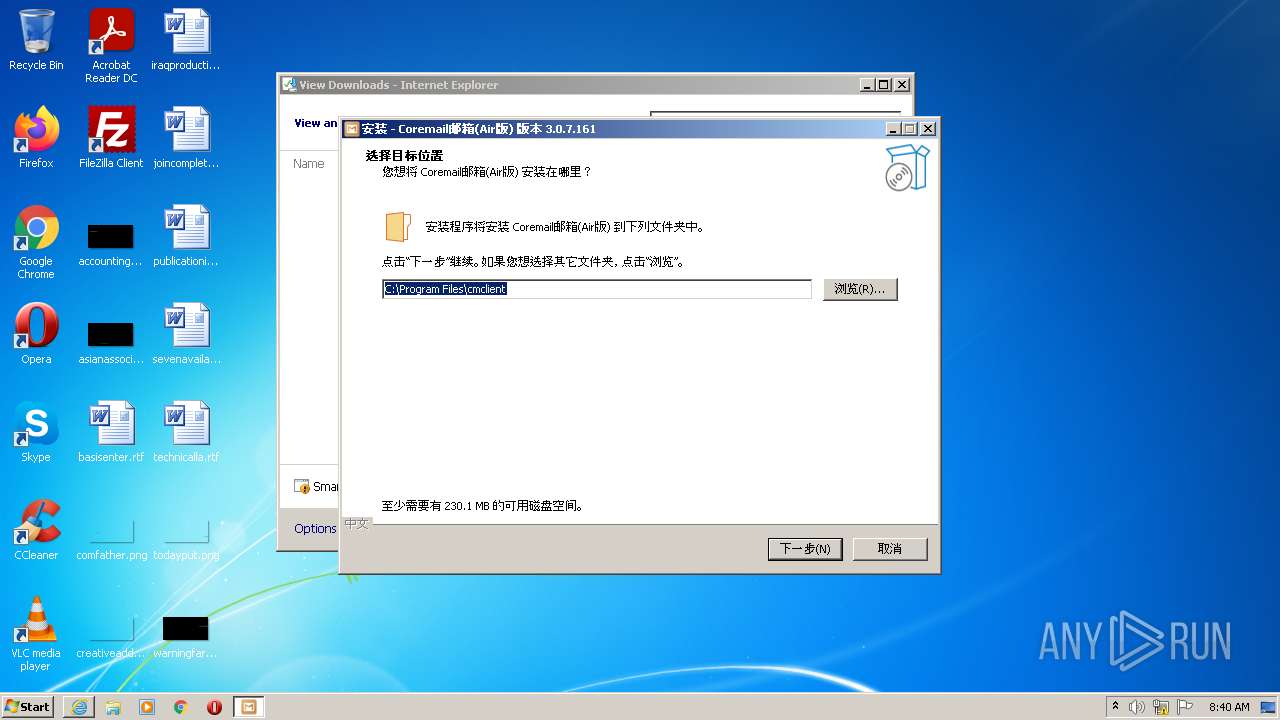
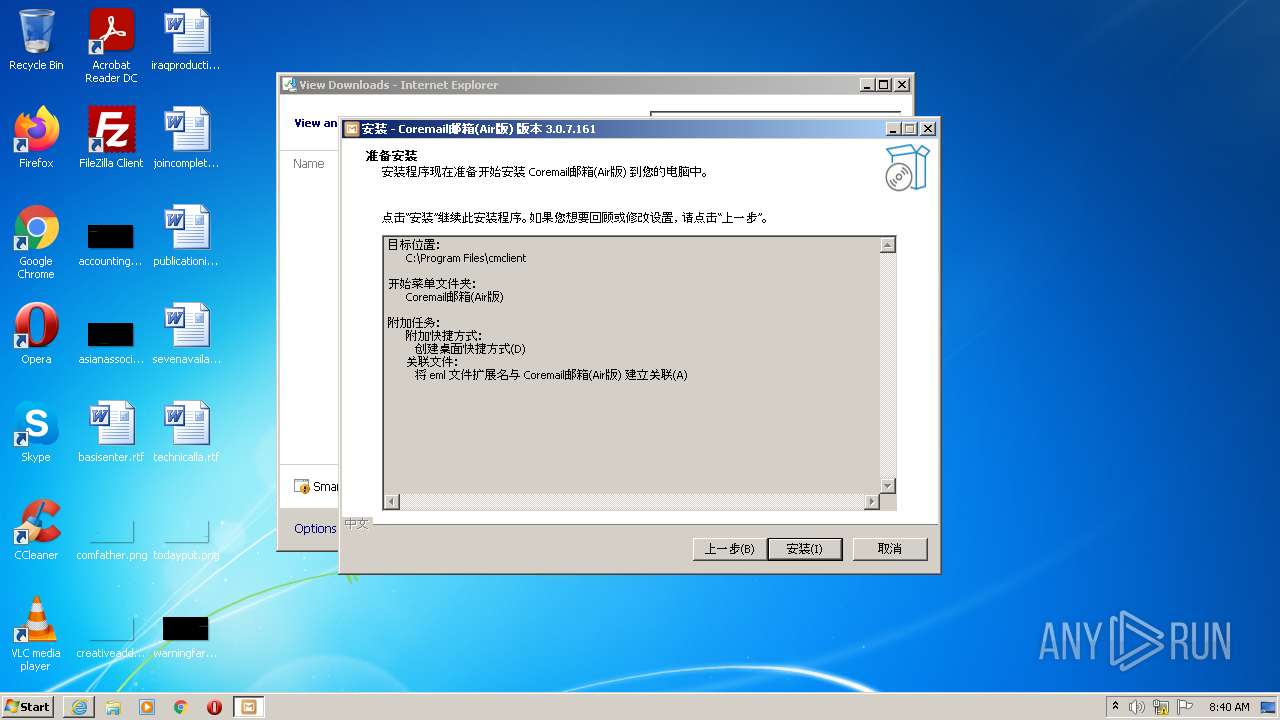
Creates a directory in Program Files
- cmclient_3.0.7-161_amd32.tmp (PID: 2288)
Starts CMD.EXE for commands execution
- CMClient.exe (PID: 3884)
INFO
Checks supported languages
- iexplore.exe (PID: 2228)
- iexplore.exe (PID: 2148)
- netsh.exe (PID: 1728)
- netsh.exe (PID: 336)
Reads the computer name
- iexplore.exe (PID: 2228)
- iexplore.exe (PID: 2148)
- netsh.exe (PID: 1728)
- netsh.exe (PID: 336)
Changes internet zones settings
- iexplore.exe (PID: 2228)
Application launched itself
- iexplore.exe (PID: 2228)
Checks Windows Trust Settings
- iexplore.exe (PID: 2228)
- iexplore.exe (PID: 2148)
Reads settings of System Certificates
- iexplore.exe (PID: 2228)
- iexplore.exe (PID: 2148)
Reads internet explorer settings
- iexplore.exe (PID: 2148)
Modifies the phishing filter of IE
- iexplore.exe (PID: 2228)
Reads the date of Windows installation
- iexplore.exe (PID: 2228)
Creates files in the user directory
- iexplore.exe (PID: 2228)
Changes settings of System certificates
- iexplore.exe (PID: 2228)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2228)
Application was dropped or rewritten from another process
- cmclient_3.0.7-161_amd32.tmp (PID: 3860)
- cmclient_3.0.7-161_amd32.tmp (PID: 2288)
Dropped object may contain Bitcoin addresses
- cmclient_3.0.7-161_amd32.tmp (PID: 2288)
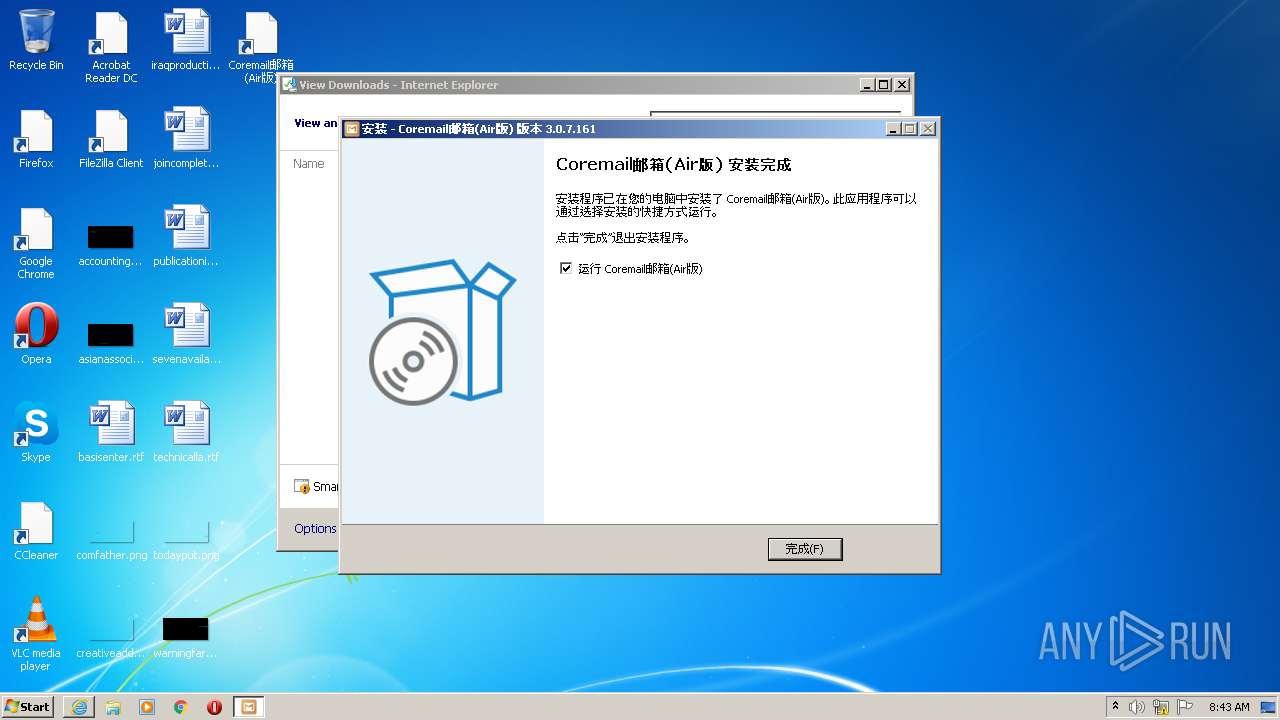
Creates a software uninstall entry
- cmclient_3.0.7-161_amd32.tmp (PID: 2288)
Reads the hosts file
- CMClient.exe (PID: 3884)
- CMCefApp.exe (PID: 2792)
Creates files in the program directory
- cmclient_3.0.7-161_amd32.tmp (PID: 2288)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
64
Monitored processes
19
Malicious processes
10
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 336 | "C:\Windows\system32\netsh.exe" advfirewall firewall add rule name="Coremail邮箱(Air版)" dir=in action=allow program="C:\Program Files\cmclient\CMClient.exe" enable=yes | C:\Windows\system32\netsh.exe | — | cmclient_3.0.7-161_amd32.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1332 | C:\Windows\system32\cmd.exe /c cat /proc/cpuinfo | C:\Windows\system32\cmd.exe | — | CMClient.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1728 | "C:\Windows\system32\netsh.exe" advfirewall firewall delete rule name="Coremail邮箱(Air版)" | C:\Windows\system32\netsh.exe | — | cmclient_3.0.7-161_amd32.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1964 | "C:\Program Files\cmclient\CMCefApp.exe" --type=gpu-process --field-trial-handle=1076,15696172974399878226,15148709402540830937,131072 --disable-features=CalculateNativeWinOcclusion,WinUseBrowserSpellChecker --no-sandbox --locales-dir-path="C:\Program Files\cmclient\cef\locales" --log-severity=warning --resources-dir-path="C:\Program Files\cmclient\cef" --lang=zh-cn --user-data-dir="C:\Users\admin\AppData\Local\CEF\User Data" --gpu-preferences=UAAAAAAAAADgAAAIAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAHgAAAAAAAAAeAAAAAAAAAAoAAAABAAAACAAAAAAAAAAKAAAAAAAAAAwAAAAAAAAADgAAAAAAAAAEAAAAAAAAAAAAAAADQAAABAAAAAAAAAAAQAAAA0AAAAQAAAAAAAAAAQAAAANAAAAEAAAAAAAAAAHAAAADQAAAAgAAAAAAAAACAAAAAAAAAA= --use-gl=disabled --log-file="C:\Users\admin\AppData\Roaming\Cm\CMClient\logs\cmcef.log" --mojo-platform-channel-handle=1448 /prefetch:2 | C:\Program Files\cmclient\CMCefApp.exe | CMClient.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2148 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2228 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2228 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://www.lunkr.cn/dl?p=mail&arch_type=win32.exe" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2288 | "C:\Users\admin\AppData\Local\Temp\is-O293B.tmp\cmclient_3.0.7-161_amd32.tmp" /SL5="$301D4,77324702,970752,C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\cmclient_3.0.7-161_amd32.exe" /SPAWNWND=$201D2 /NOTIFYWND=$301B0 | C:\Users\admin\AppData\Local\Temp\is-O293B.tmp\cmclient_3.0.7-161_amd32.tmp | cmclient_3.0.7-161_amd32.exe | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 2364 | "C:\Program Files\cmclient\CMCefApp.exe" --type=renderer --locales-dir-path="C:\Program Files\cmclient\cef\locales" --log-severity=warning --resources-dir-path="C:\Program Files\cmclient\cef" --user-data-dir="C:\Users\admin\AppData\Local\CEF\User Data" --no-sandbox --log-file="C:\Users\admin\AppData\Roaming\Cm\CMClient\logs\cmcef.log" --field-trial-handle=1076,15696172974399878226,15148709402540830937,131072 --disable-features=CalculateNativeWinOcclusion,WinUseBrowserSpellChecker --disable-gpu-compositing --lang=zh-CN --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --mojo-platform-channel-handle=1788 /prefetch:1 | C:\Program Files\cmclient\CMCefApp.exe | — | CMClient.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2640 | "C:\Program Files\cmclient\CMCefApp.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --field-trial-handle=1076,15696172974399878226,15148709402540830937,131072 --disable-features=CalculateNativeWinOcclusion,WinUseBrowserSpellChecker --lang=zh-CN --service-sandbox-type=utility --no-sandbox --locales-dir-path="C:\Program Files\cmclient\cef\locales" --log-severity=warning --resources-dir-path="C:\Program Files\cmclient\cef" --lang=zh-cn --user-data-dir="C:\Users\admin\AppData\Local\CEF\User Data" --log-file="C:\Users\admin\AppData\Roaming\Cm\CMClient\logs\cmcef.log" --mojo-platform-channel-handle=1552 /prefetch:8 | C:\Program Files\cmclient\CMCefApp.exe | — | CMClient.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2792 | "C:\Program Files\cmclient\CMCefApp.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --field-trial-handle=1076,15696172974399878226,15148709402540830937,131072 --disable-features=CalculateNativeWinOcclusion,WinUseBrowserSpellChecker --lang=zh-CN --service-sandbox-type=none --no-sandbox --locales-dir-path="C:\Program Files\cmclient\cef\locales" --log-severity=warning --resources-dir-path="C:\Program Files\cmclient\cef" --lang=zh-cn --user-data-dir="C:\Users\admin\AppData\Local\CEF\User Data" --log-file="C:\Users\admin\AppData\Roaming\Cm\CMClient\logs\cmcef.log" --mojo-platform-channel-handle=1456 /prefetch:8 | C:\Program Files\cmclient\CMCefApp.exe | — | CMClient.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
16 925
Read events
16 577
Write events
337
Delete events
11
Modification events
| (PID) Process: | (2228) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2228) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (2228) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30950811 | |||
| (PID) Process: | (2228) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (2228) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30950811 | |||
| (PID) Process: | (2228) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2228) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2228) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2228) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2228) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
31
Suspicious files
51
Text files
2 148
Unknown types
139
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2228 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:8DBD94926E329FE0F281EB101ED00A94 | SHA256:BA5180596984FA37637A613EB784708A353E063AC7662EE1D7210E83FA8BEDB3 | |||
| 2228 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | der | |
MD5:5D9ED3BEAA5AE1284AD83A14CF40BD33 | SHA256:DAFAAA654CE112151E48E971475B52B7A1D5BFFBFFB51C0871AFFA769A73AF0F | |||
| 2228 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | binary | |
MD5:EF5C614994A94999E551C7631774FF9C | SHA256:04829A7B2A43737DD5C41733608B942E734664809993B704C94A6FC89988C051 | |||
| 2228 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | der | |
MD5:D563DAA43DC3727DF0768A4DD45E83EB | SHA256:F4E7AE620324BEAE96EB8DFC636A3DE527A4DFF22C0422419EB6A2A39D53BFED | |||
| 2228 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | binary | |
MD5:3C4F77887EDC7C7ECBBC9E14914681D0 | SHA256:6D50C4AB44C4F89234FAF3B3BA98677A361375C617B70829B45072D97A82E401 | |||
| 2148 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\EB2C4AB8B68FFA4B7733A9139239A396_D76DB901EE986B889F30D8CC06229E2D | der | |
MD5:50A650524BE3141472BE5A0AB033A032 | SHA256:9F53FECDD88B70A3F64686FF471B9AD21E356883B11CE36C39335C9403D0703D | |||
| 2148 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\EB2C4AB8B68FFA4B7733A9139239A396_D76DB901EE986B889F30D8CC06229E2D | binary | |
MD5:BF5F0C120BDD69F058FFB728F7710B6D | SHA256:A08D6DCF52AC648EE8921339A107833EB030A03BCDD663331591E383D5C4CE4B | |||
| 2148 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\49ACF97526F8EF0EA415F477BF7C57D6_D1960FCE1FB9773851CAD7EEC7E8FB08 | der | |
MD5:AD8A8BD436D9F5D95230D85C73509D15 | SHA256:D89E16F8125A438850D7B8E811B744994623A6543DFA47800B0449CC6B70EE61 | |||
| 2148 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\49ACF97526F8EF0EA415F477BF7C57D6_D1960FCE1FB9773851CAD7EEC7E8FB08 | binary | |
MD5:CC372A3119201B2EA2708482E86CCC44 | SHA256:CF1CC32389C5C7D359D5BFDCE13913A1B671EA03C081A7E8C8B07CFA407E5EAE | |||
| 2148 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\998D5166E87A5DE92945A6C9666CE9B4_D08DD7032E776E5399105071A78B868E | der | |
MD5:1D83E2BEAC1D16E35F6728DA92C3D145 | SHA256:854770CDC3971CBC5AB67A49220A5355FA96EF8A82B35D3890634C53772824C7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
25
DNS requests
18
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2148 | iexplore.exe | GET | 200 | 192.124.249.22:80 | http://ocsp.godaddy.com//MEQwQjBAMD4wPDAJBgUrDgMCGgUABBTkIInKBAzXkF0Qh0pel3lfHJ9GPAQU0sSw0pHUTBFxs2HLPaH%2B3ahq1OMCAxvnFQ%3D%3D | US | der | 1.66 Kb | whitelisted |
2228 | iexplore.exe | GET | 200 | 41.63.96.128:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?f3d59a9156b46f04 | ZA | compressed | 4.70 Kb | whitelisted |
2228 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
2228 | iexplore.exe | GET | 200 | 41.63.96.128:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?e7edb64a7e80a60a | ZA | compressed | 4.70 Kb | whitelisted |
2228 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
2148 | iexplore.exe | GET | 200 | 192.124.249.22:80 | http://ocsp.godaddy.com//MEIwQDA%2BMDwwOjAJBgUrDgMCGgUABBQdI2%2BOBkuXH93foRUj4a7lAr4rGwQUOpqFBxBnKLbv9r0FQW4gwZTaD94CAQc%3D | US | der | 1.69 Kb | whitelisted |
2148 | iexplore.exe | GET | 200 | 192.124.249.22:80 | http://ocsp.godaddy.com//MEkwRzBFMEMwQTAJBgUrDgMCGgUABBS2CA1fbGt26xPkOKX4ZguoUjM0TgQUQMK9J47MNIMwojPX%2B2yz8LQsgM4CCEri1hp%2BSeeI | US | der | 1.74 Kb | whitelisted |
2148 | iexplore.exe | GET | 200 | 192.124.249.22:80 | http://ocsp.godaddy.com//MEkwRzBFMEMwQTAJBgUrDgMCGgUABBS2CA1fbGt26xPkOKX4ZguoUjM0TgQUQMK9J47MNIMwojPX%2B2yz8LQsgM4CCBsNFxOjhLyH | US | der | 1.74 Kb | whitelisted |
2228 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA177el9ggmWelJjG4vdGL0%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2148 | iexplore.exe | 152.32.174.138:443 | www.lunkr.cn | MCNC | US | unknown |
2228 | iexplore.exe | 131.253.33.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2228 | iexplore.exe | 41.63.96.128:80 | ctldl.windowsupdate.com | Limelight Networks, Inc. | ZA | suspicious |
2228 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2228 | iexplore.exe | 152.199.19.161:443 | r20swj13mr.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2148 | iexplore.exe | 192.124.249.22:80 | ocsp.godaddy.com | Sucuri | US | suspicious |
2148 | iexplore.exe | 58.215.145.29:443 | s1.static.lunkr.cn | AS Number for CHINANET jiangsu province backbone | CN | suspicious |
2228 | iexplore.exe | 204.79.197.200:443 | ieonline.microsoft.com | Microsoft Corporation | US | whitelisted |
2228 | iexplore.exe | 96.16.143.41:443 | go.microsoft.com | Akamai International B.V. | US | whitelisted |
2228 | iexplore.exe | 131.253.33.203:443 | www.msn.com | Microsoft Corporation | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.lunkr.cn |
| unknown |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
ocsp.godaddy.com |
| whitelisted |
s1.static.lunkr.cn |
| unknown |
ieonline.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
CMCefApp.exe | [0401/084309.442:ERROR:angle_platform_impl.cc(44)] RendererVk.cpp:122 (VerifyExtensionsPresent): Extension not supported: VK_KHR_surface
|
CMCefApp.exe | [0401/084309.442:ERROR:angle_platform_impl.cc(44)] RendererVk.cpp:122 (VerifyExtensionsPresent): Extension not supported: VK_KHR_win32_surface
|
CMCefApp.exe | [0401/084309.442:ERROR:angle_platform_impl.cc(44)] Display.cpp:894 (initialize): ANGLE Display::initialize error 0: Internal Vulkan error (-7): A requested extension is not supported, in ../../third_party/angle/src/libANGLE/renderer/vulkan/RendererVk.cpp, initialize:997.
|
CMCefApp.exe | [0401/084309.442:ERROR:gl_surface_egl.cc(780)] EGL Driver message (Critical) eglInitialize: Internal Vulkan error (-7): A requested extension is not supported, in ../../third_party/angle/src/libANGLE/renderer/vulkan/RendererVk.cpp, initialize:997.
|
CMCefApp.exe | [0401/084309.442:ERROR:gl_surface_egl.cc(1375)] eglInitialize SwANGLE failed with error EGL_NOT_INITIALIZED
|
CMCefApp.exe | [0401/084309.442:ERROR:gl_initializer_win.cc(141)] GLSurfaceEGL::InitializeOneOff failed.
|
CMCefApp.exe | [0401/084309.458:ERROR:viz_main_impl.cc(161)] Exiting GPU process due to errors during initialization
|
CMCefApp.exe | [0401/084309.598:ERROR:gpu_init.cc(453)] Passthrough is not supported, GL is disabled, ANGLE is
|