| File name: | new 1.js |
| Full analysis: | https://app.any.run/tasks/e1d45298-21f2-46d6-89ca-1251a29fe53c |
| Verdict: | Malicious activity |
| Analysis date: | March 21, 2019, 16:37:31 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/x-c |
| File info: | C source, ASCII text, with CRLF line terminators |
| MD5: | BE3540796CD83AC58DF19411ED3365FA |
| SHA1: | 7F7A3E8F0DDBE733A0563A49586CEAE1036011D4 |
| SHA256: | 863A3D845F81A6FA5FDC56B0C6518F12C1661F5599C6E34FD172E33C4B269F14 |
| SSDEEP: | 24:TBL3g7PZlQfCA899n+4RuWh0uZ+PSQqjf750uqvIDEO0Ypv0KT9:VkZY8RQWP+aQqjf7kwDEO1z9 |
MALICIOUS
Changes settings of System certificates
- WScript.exe (PID: 2824)
SUSPICIOUS
Uses ATTRIB.EXE to modify file attributes
- WScript.exe (PID: 2824)
Adds / modifies Windows certificates
- WScript.exe (PID: 2824)
Creates files in the user directory
- WScript.exe (PID: 2824)
Starts CMD.EXE for commands execution
- WScript.exe (PID: 2824)
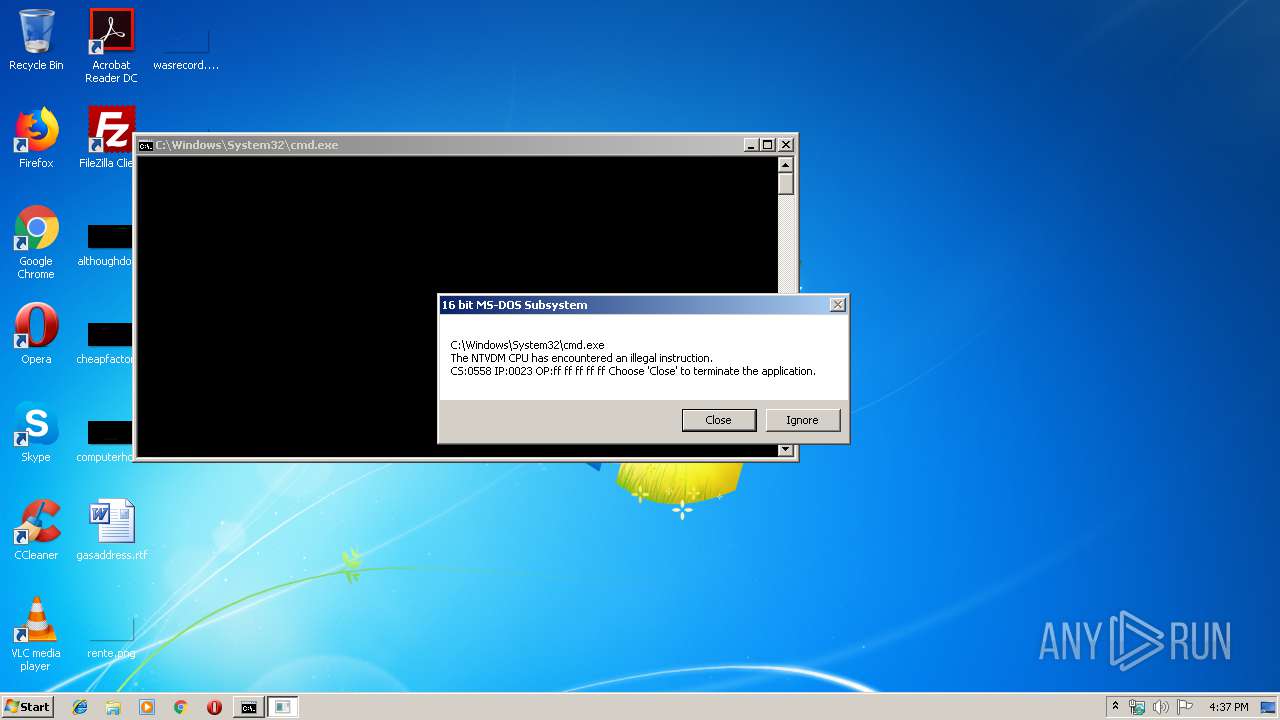
Executes application which crashes
- cmd.exe (PID: 3668)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
37
Monitored processes
5
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2824 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\new 1.js" | C:\Windows\System32\WScript.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 3176 | "C:\Windows\system32\ntvdm.exe" | C:\Windows\system32\ntvdm.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: NTVDM.EXE Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3588 | attrib +H "C:\Users\admin\AppData\Roaming\stub.exe" | C:\Windows\System32\attrib.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Attribute Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3612 | attrib -H "C:\Users\admin\AppData\Roaming\stub.exe" | C:\Windows\System32\attrib.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Attribute Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3668 | cmd /Q /V:OFF /C call "C:\Users\admin\AppData\Roaming\stub.exe" >nul | C:\Windows\System32\cmd.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
93
Read events
59
Write events
32
Delete events
2
Modification events
| (PID) Process: | (2824) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WScript_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2824) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WScript_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2824) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WScript_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2824) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WScript_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2824) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WScript_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2824) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WScript_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (2824) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WScript_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2824) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WScript_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2824) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WScript_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2824) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WScript_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
0
Suspicious files
0
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3176 | ntvdm.exe | C:\Users\admin\AppData\Local\Temp\scsB2D.tmp | — | |
MD5:— | SHA256:— | |||
| 3176 | ntvdm.exe | C:\Users\admin\AppData\Local\Temp\scsB3E.tmp | — | |
MD5:— | SHA256:— | |||
| 2824 | WScript.exe | C:\Users\admin\AppData\Roaming\stub.exe | xml | |
MD5:— | SHA256:— | |||
| 2824 | WScript.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@discordapp[1].txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2824 | WScript.exe | 104.16.10.231:443 | cdn.discordapp.com | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
cdn.discordapp.com |
| shared |