| File name: | Rover.exe |
| Full analysis: | https://app.any.run/tasks/b0cec4d4-cee0-4cd8-825d-dba29db5dc01 |
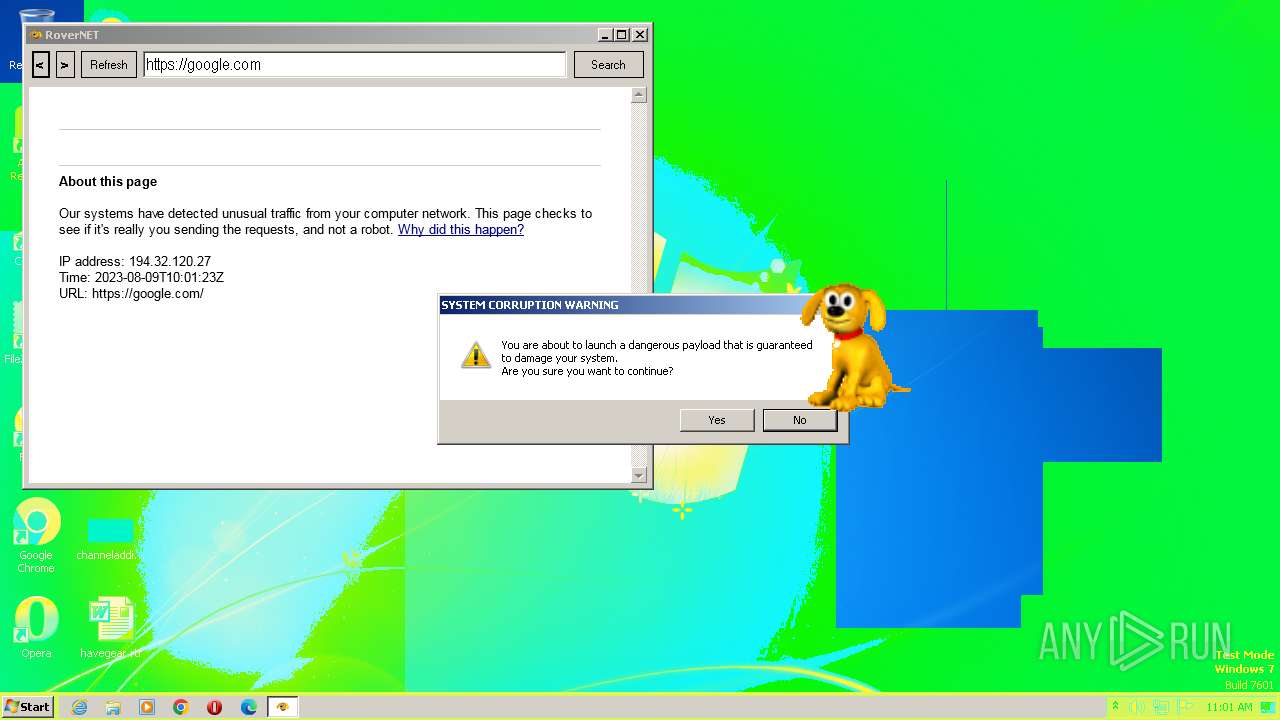
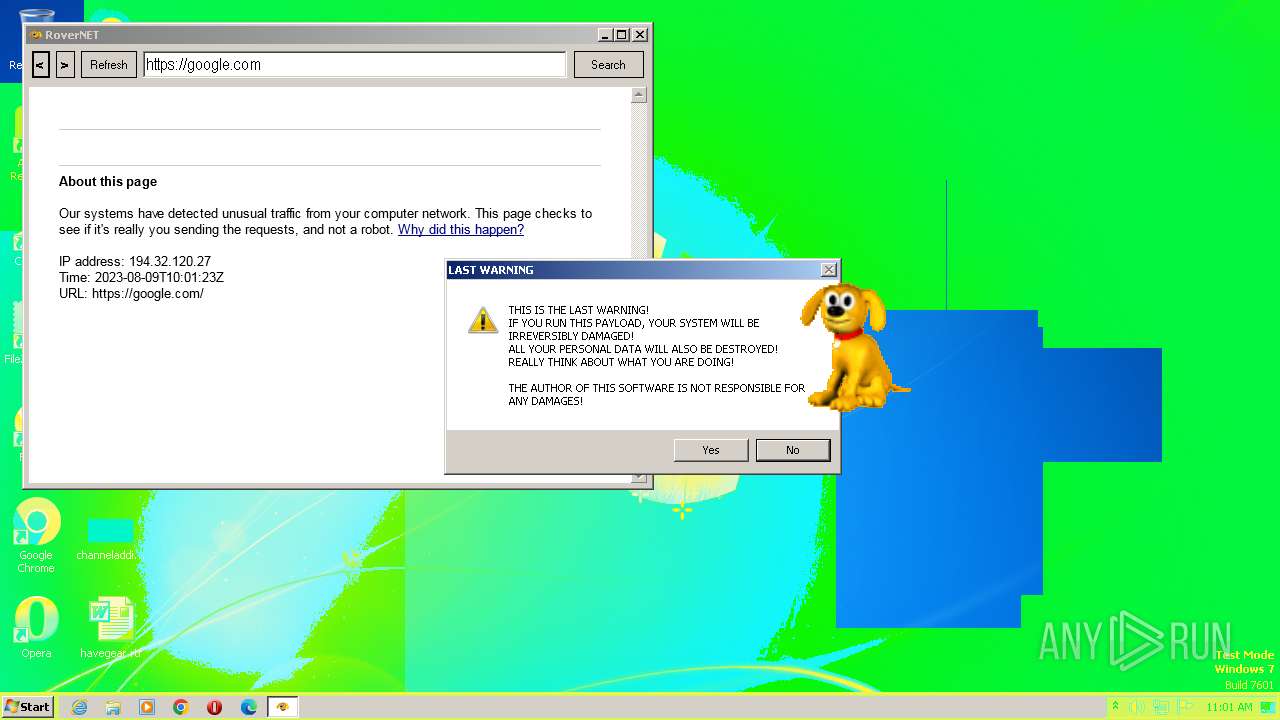
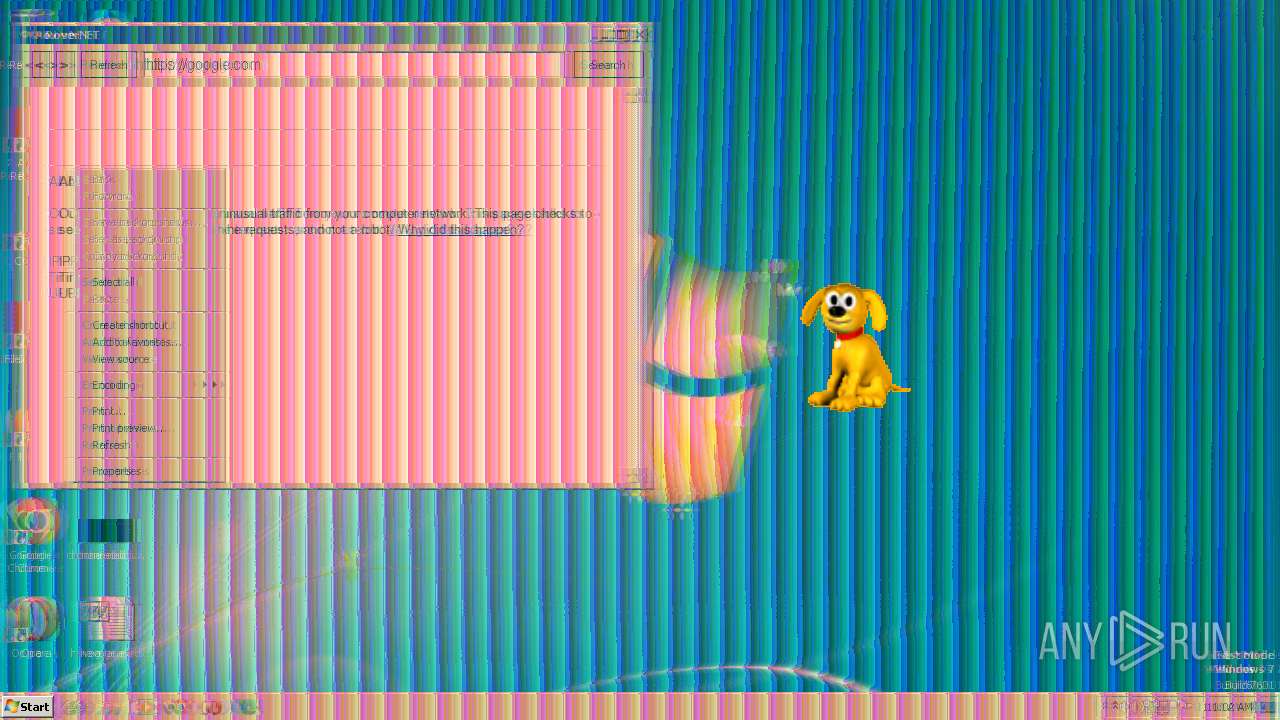
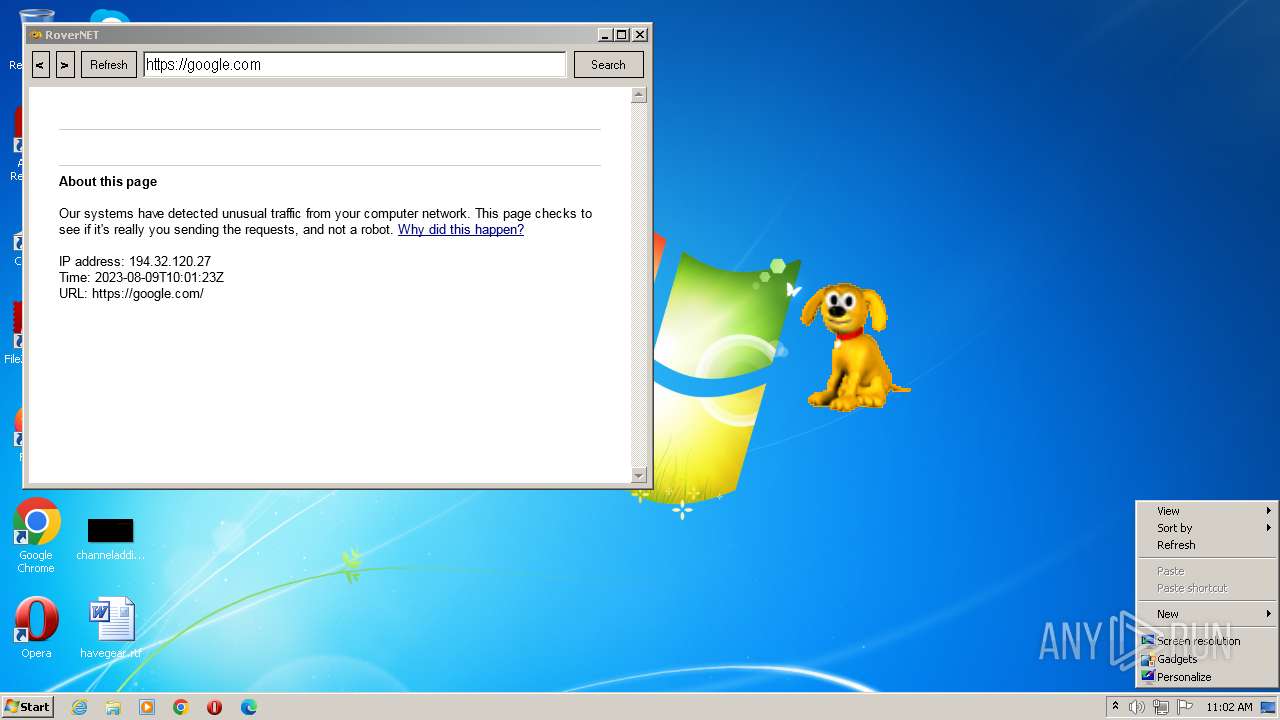
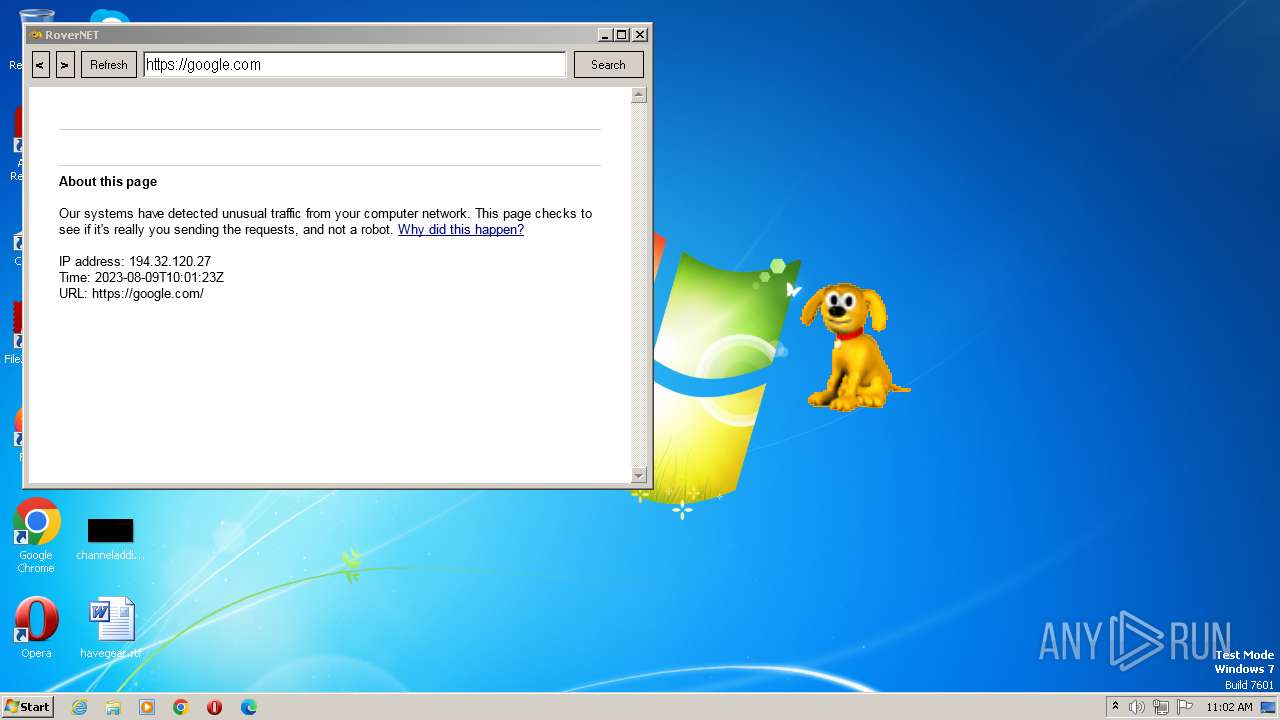
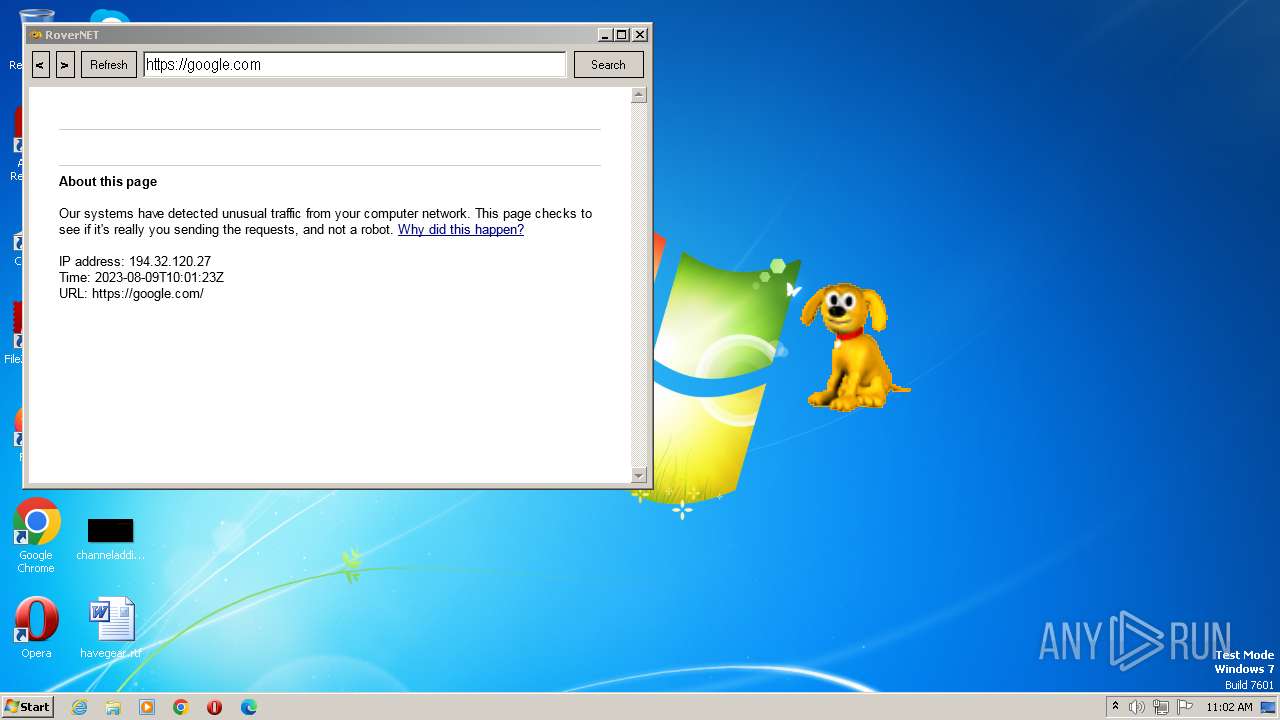
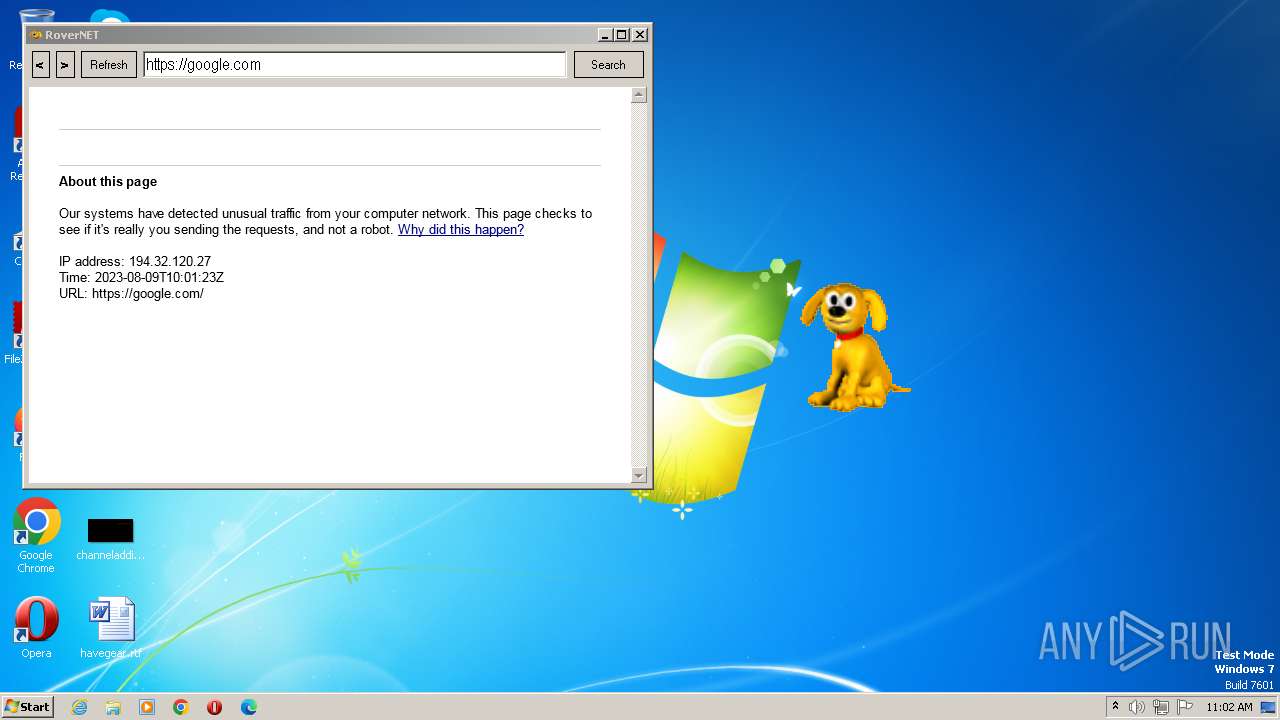
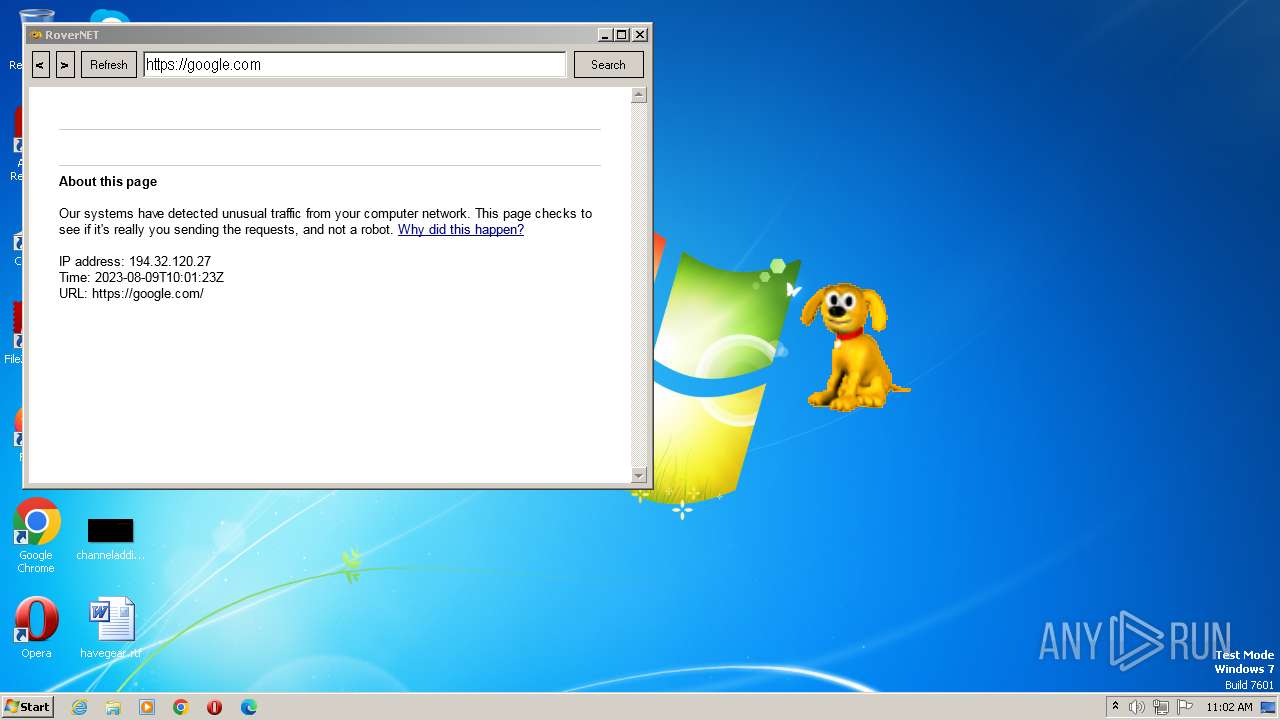
| Verdict: | Malicious activity |
| Analysis date: | August 09, 2023, 09:59:37 |
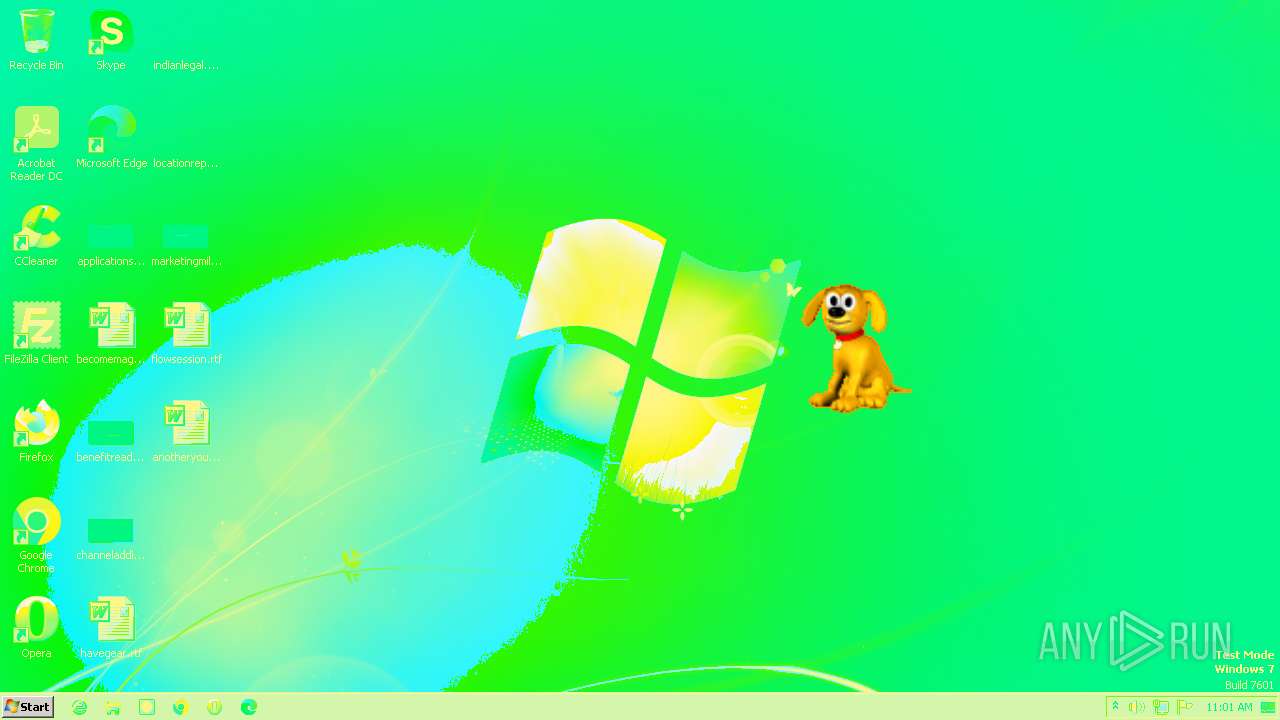
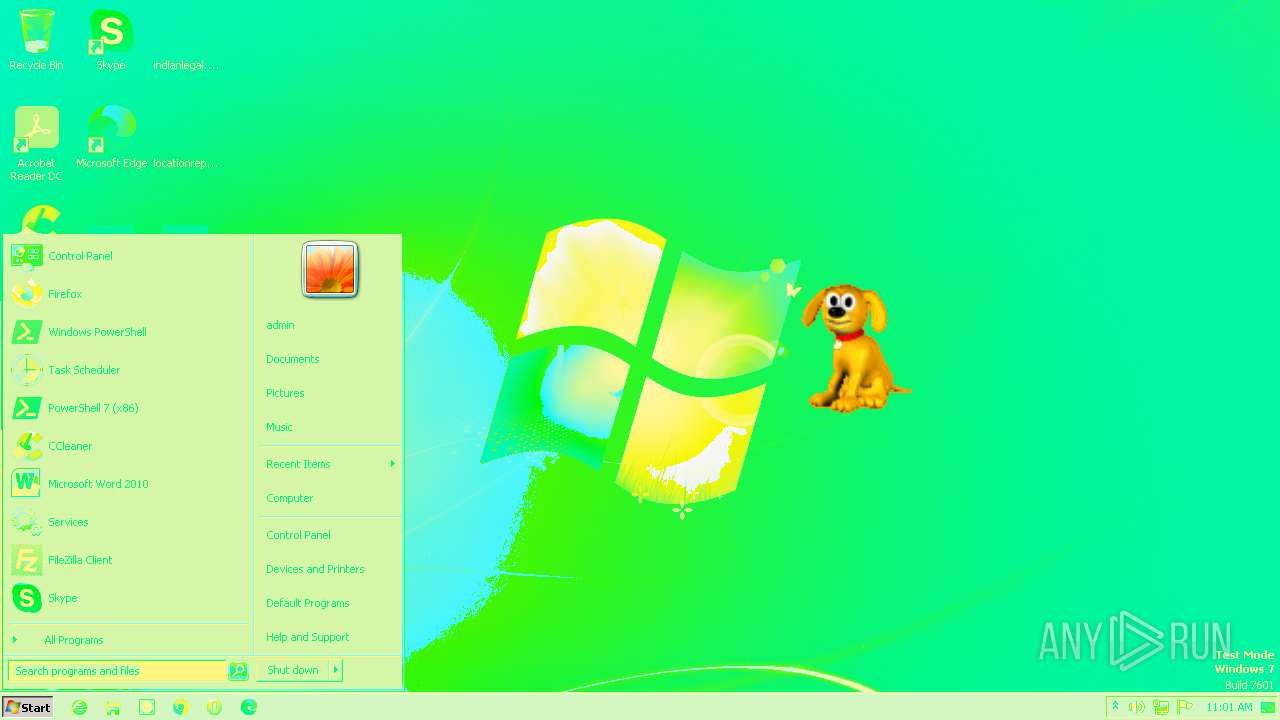
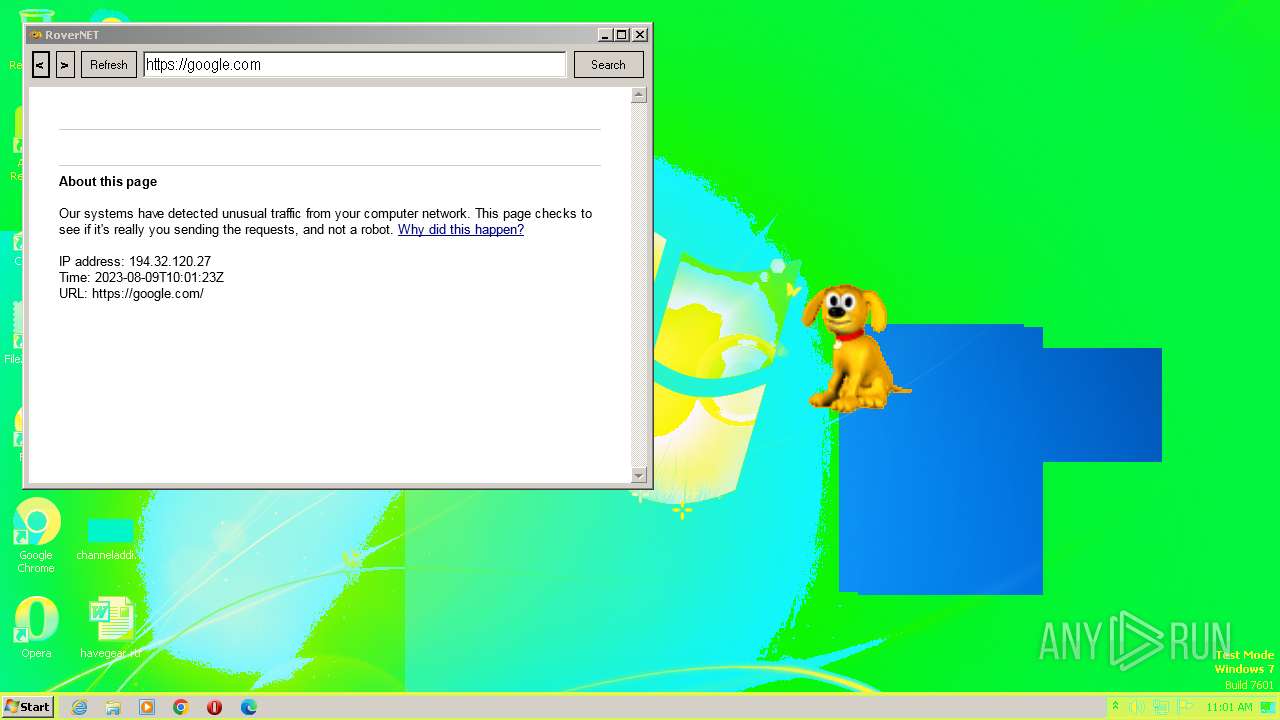
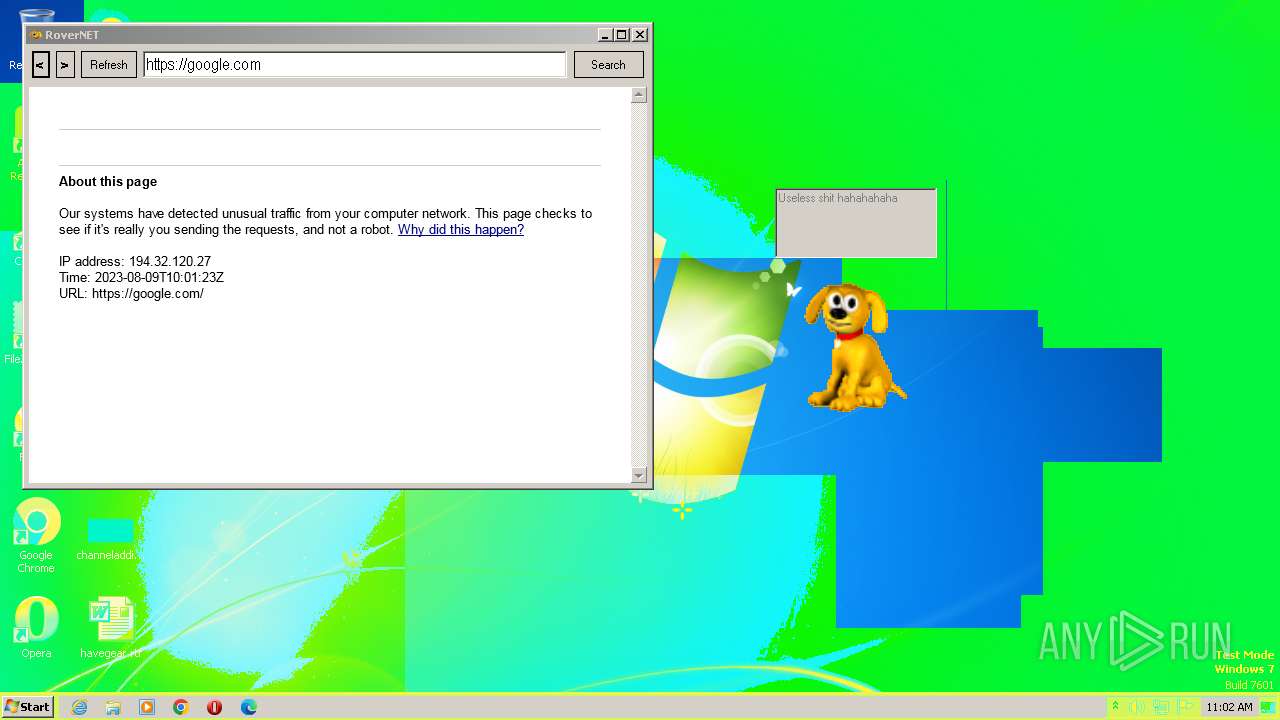
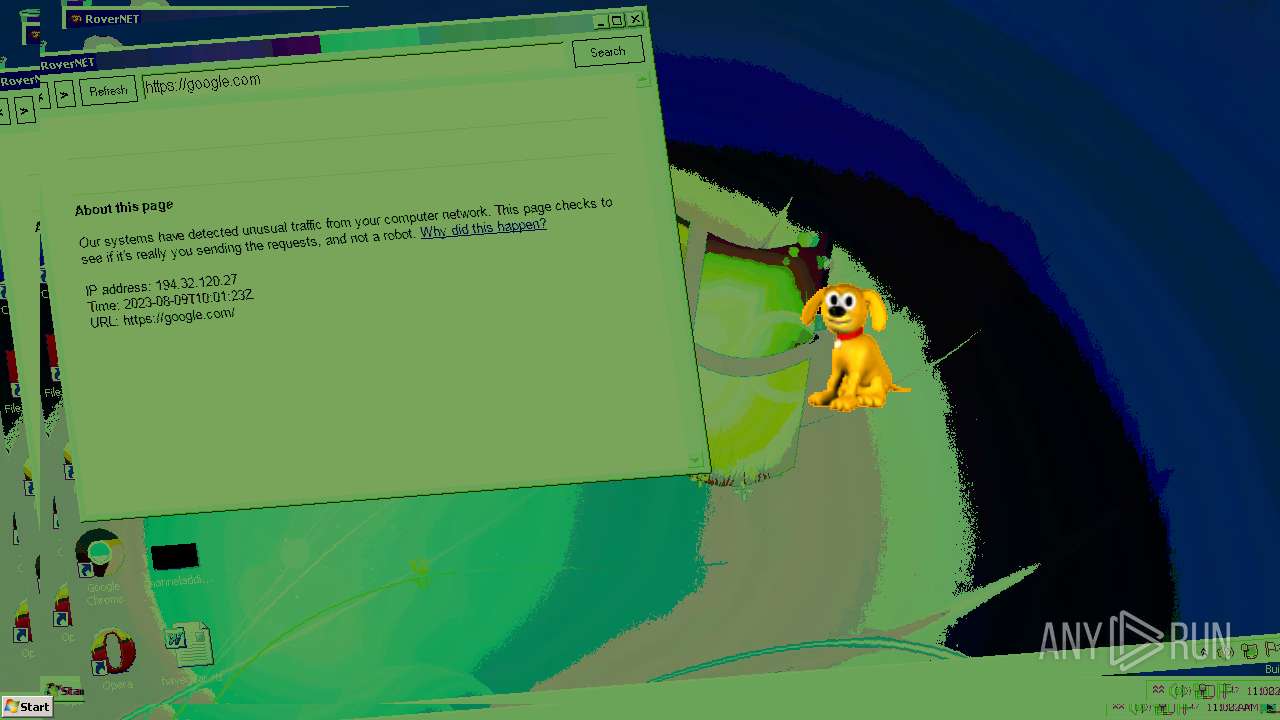
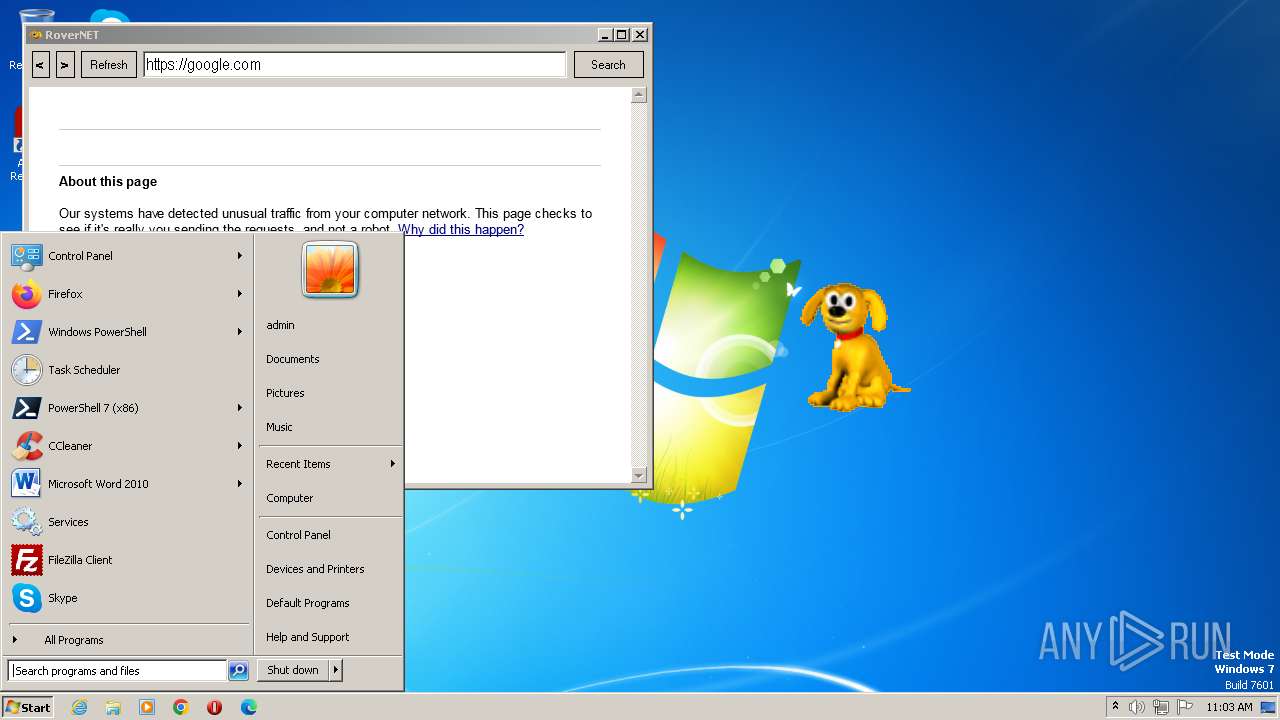
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 63D052B547C66AC7678685D9F3308884 |
| SHA1: | A6E42E6A86E3FF9FEC137C52B1086EE140A7B242 |
| SHA256: | 8634E9241729F16A8C2C23D5C184384815B97026E3D1A2D6DD0DDC825B142ABA |
| SSDEEP: | 98304:Oapmon4QzApS9hNQdrhEYzOi85kXNjMcDPWDnkE3DJ910Fx5mwAbguuwS09Fo:OQhn5EQ9hNQAYzA5k6cTWDn7JKObS09u |
MALICIOUS
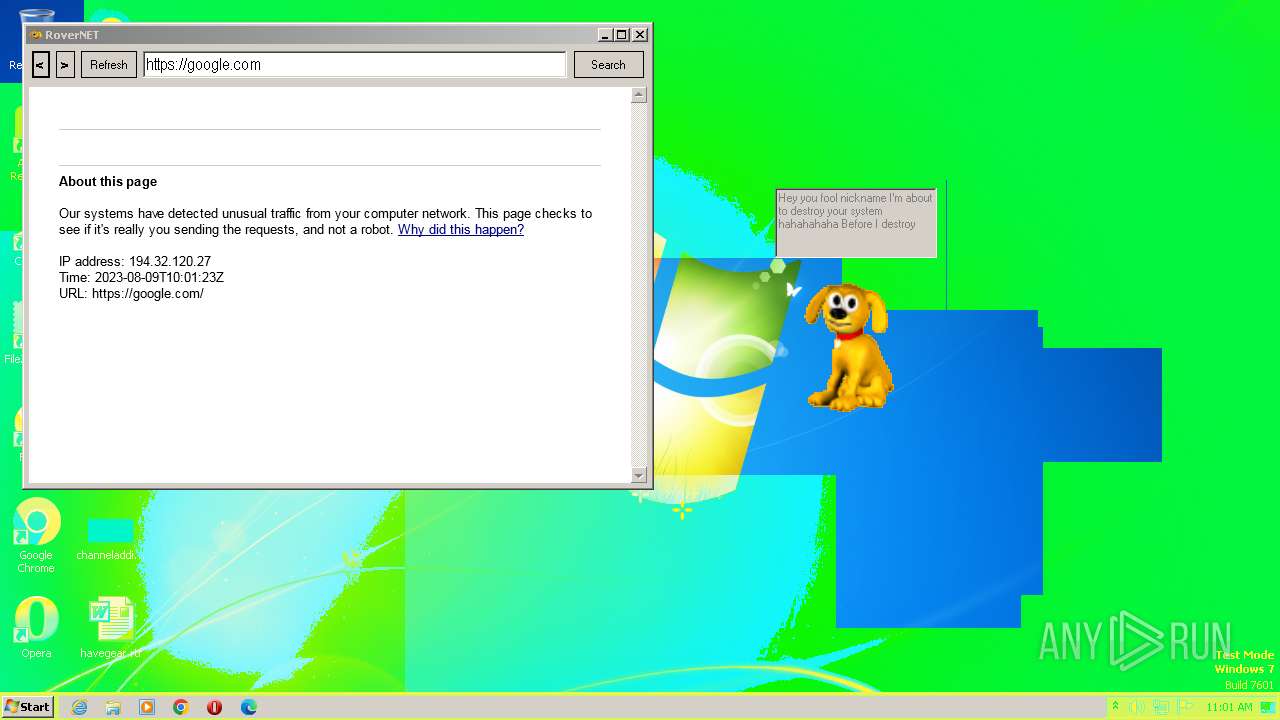
UAC/LUA settings modification
- Rover.exe (PID: 2696)
Changes the login/logoff helper path in the registry
- Rover.exe (PID: 2696)
SUSPICIOUS
Executable content was dropped or overwritten
- Rover.exe (PID: 2696)
Checks Windows Trust Settings
- Rover.exe (PID: 2696)
Reads the Internet Settings
- Rover.exe (PID: 2696)
Reads settings of System Certificates
- Rover.exe (PID: 2696)
Reads Microsoft Outlook installation path
- Rover.exe (PID: 2696)
Reads security settings of Internet Explorer
- Rover.exe (PID: 2696)
Reads Internet Explorer settings
- Rover.exe (PID: 2696)
INFO
Checks supported languages
- Rover.exe (PID: 2696)
- wmpnscfg.exe (PID: 692)
Reads the computer name
- Rover.exe (PID: 2696)
- wmpnscfg.exe (PID: 692)
Reads the machine GUID from the registry
- Rover.exe (PID: 2696)
- wmpnscfg.exe (PID: 692)
The process checks LSA protection
- wmpnscfg.exe (PID: 692)
- Rover.exe (PID: 2696)
Manual execution by a user
- wmpnscfg.exe (PID: 692)
Process checks are UAC notifies on
- Rover.exe (PID: 2696)
Creates files in the program directory
- Rover.exe (PID: 2696)
Checks proxy server information
- Rover.exe (PID: 2696)
Creates files or folders in the user directory
- Rover.exe (PID: 2696)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| AssemblyVersion: | 1.0.0.0 |
|---|---|
| ProductVersion: | 1.0.0.0 |
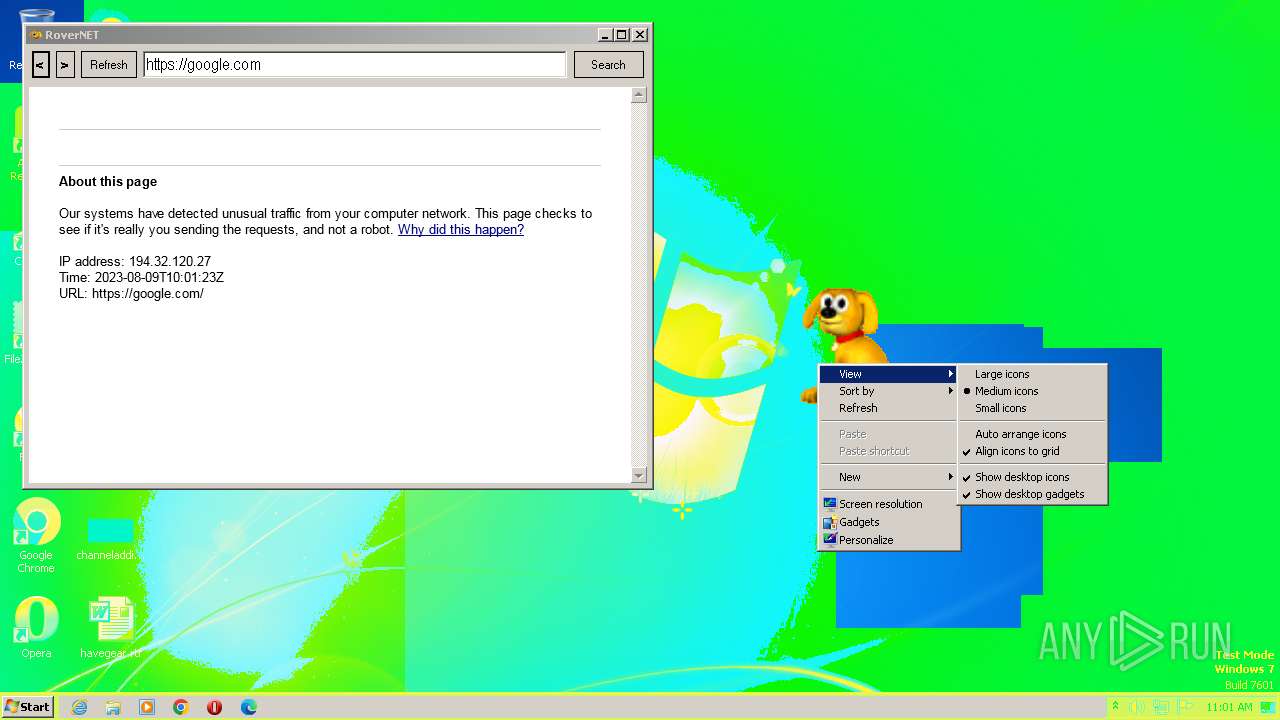
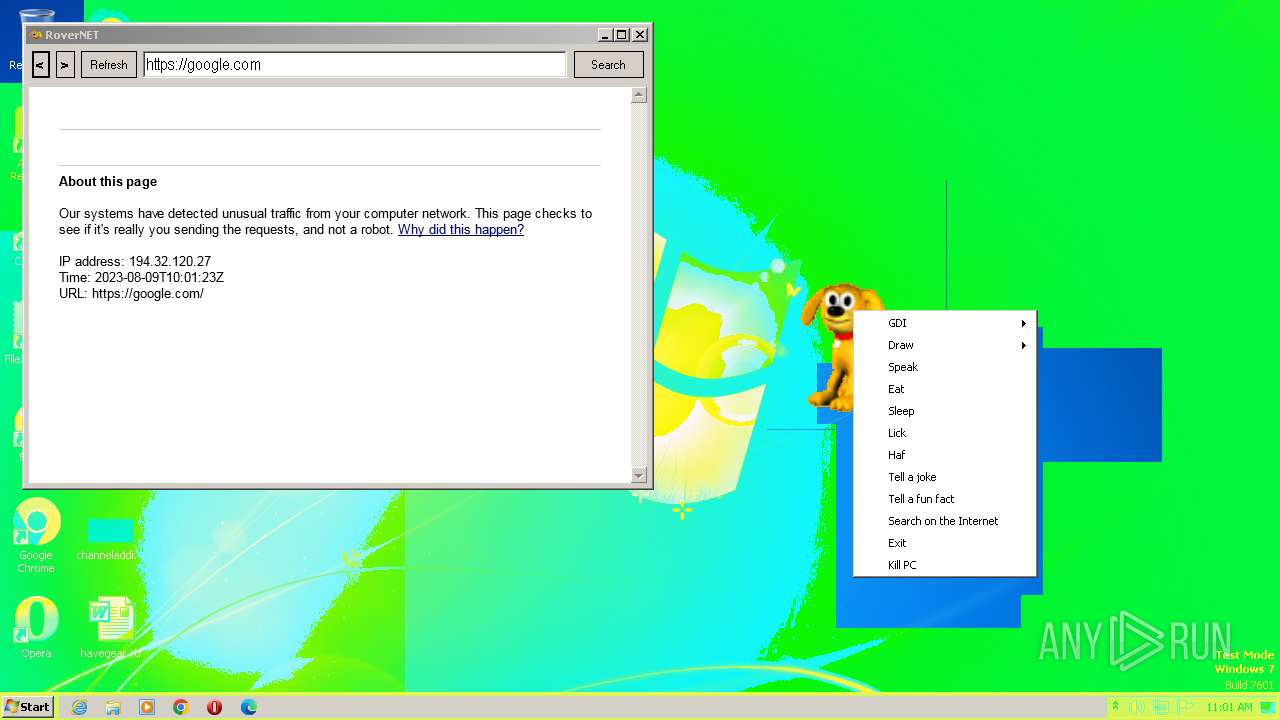
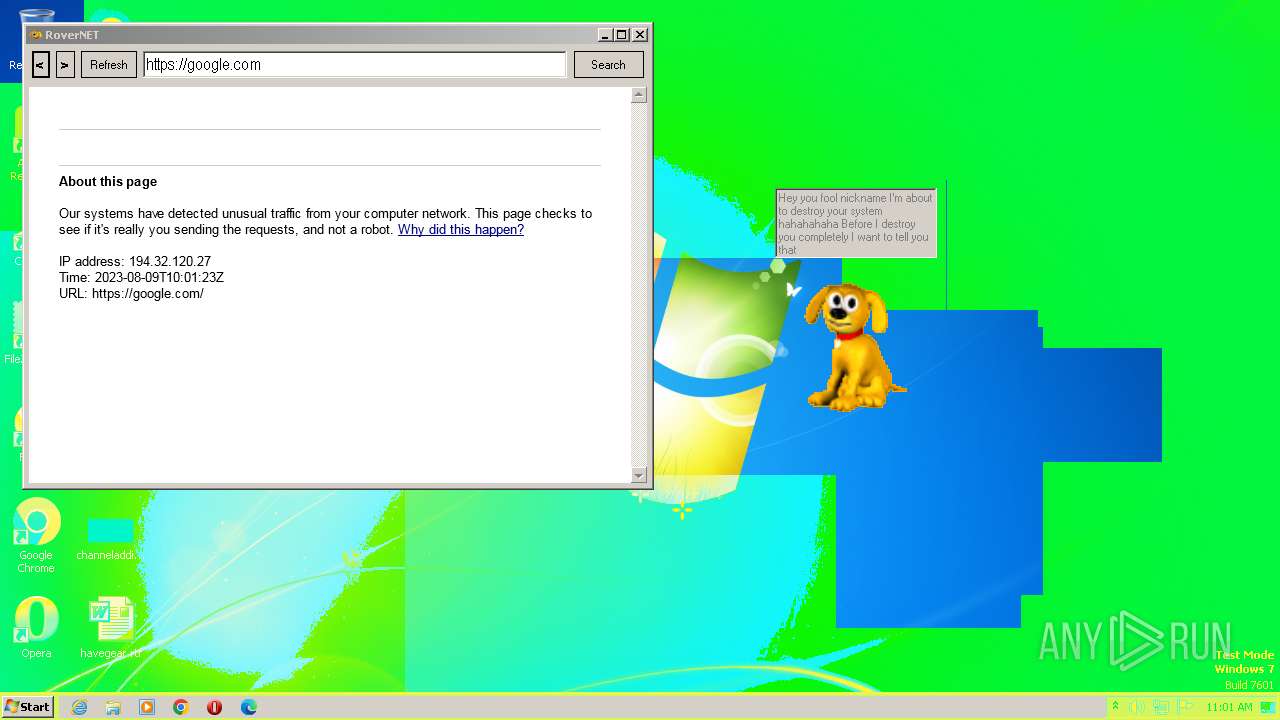
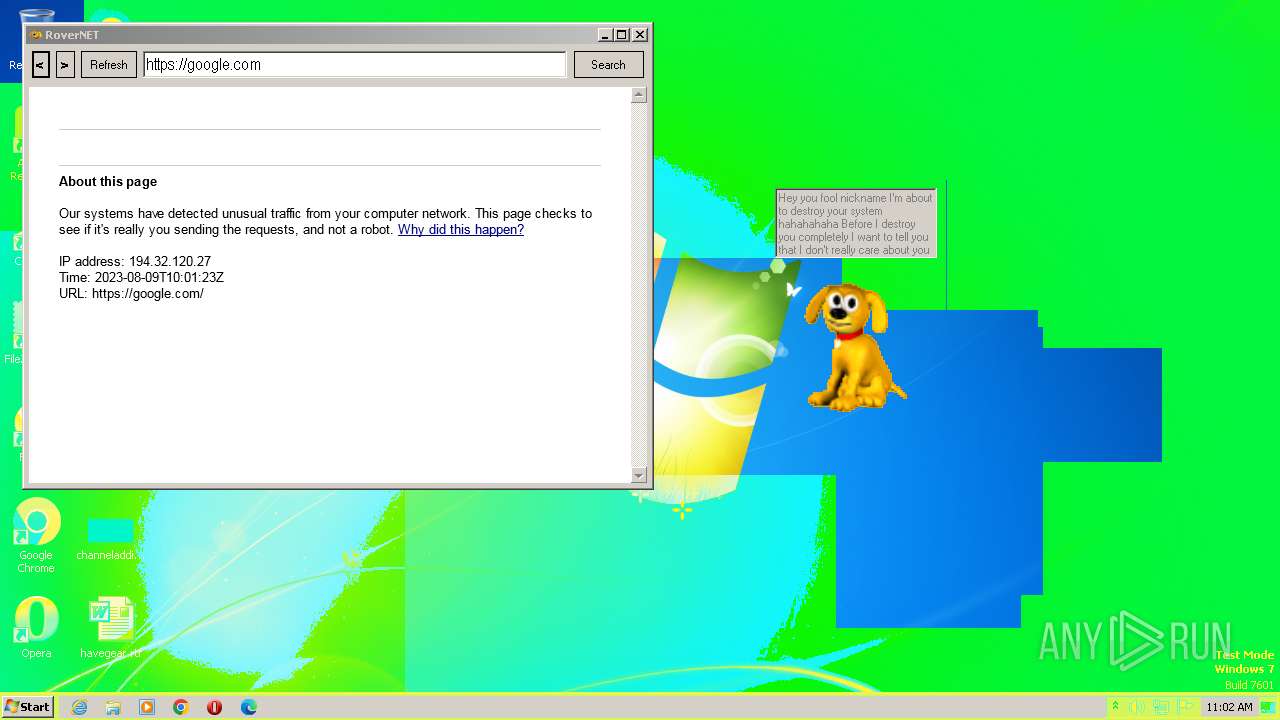
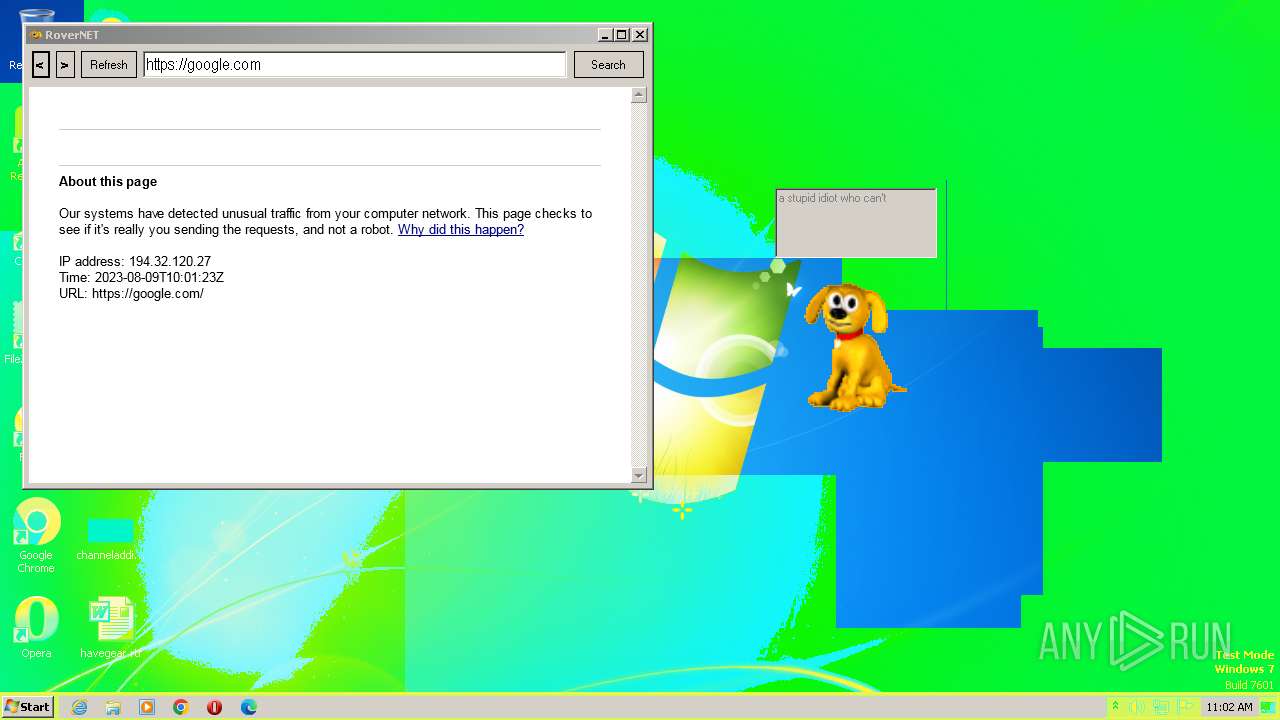
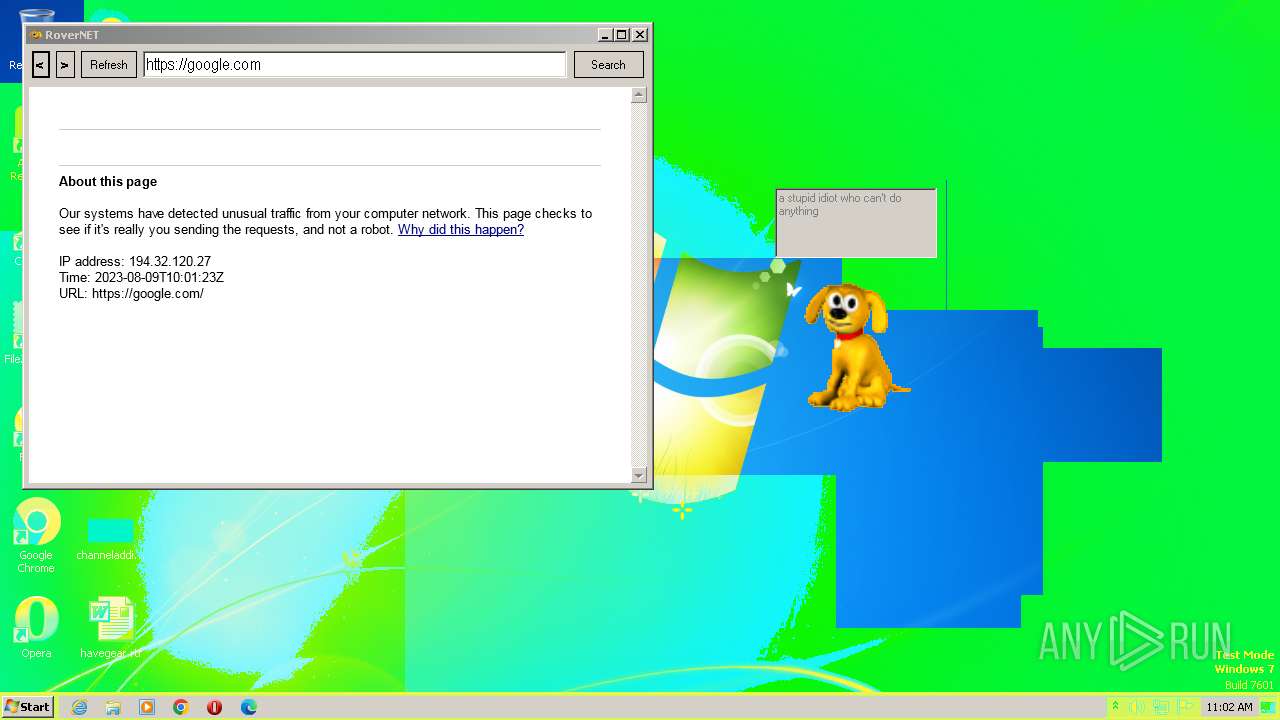
| ProductName: | Created by CYBER SOLDIER aka Clutter |
| OriginalFileName: | Rover.exe |
| LegalTrademarks: | - |
| LegalCopyright: | Copyright © 2023 |
| InternalName: | Rover.exe |
| FileVersion: | 1.0.0.0 |
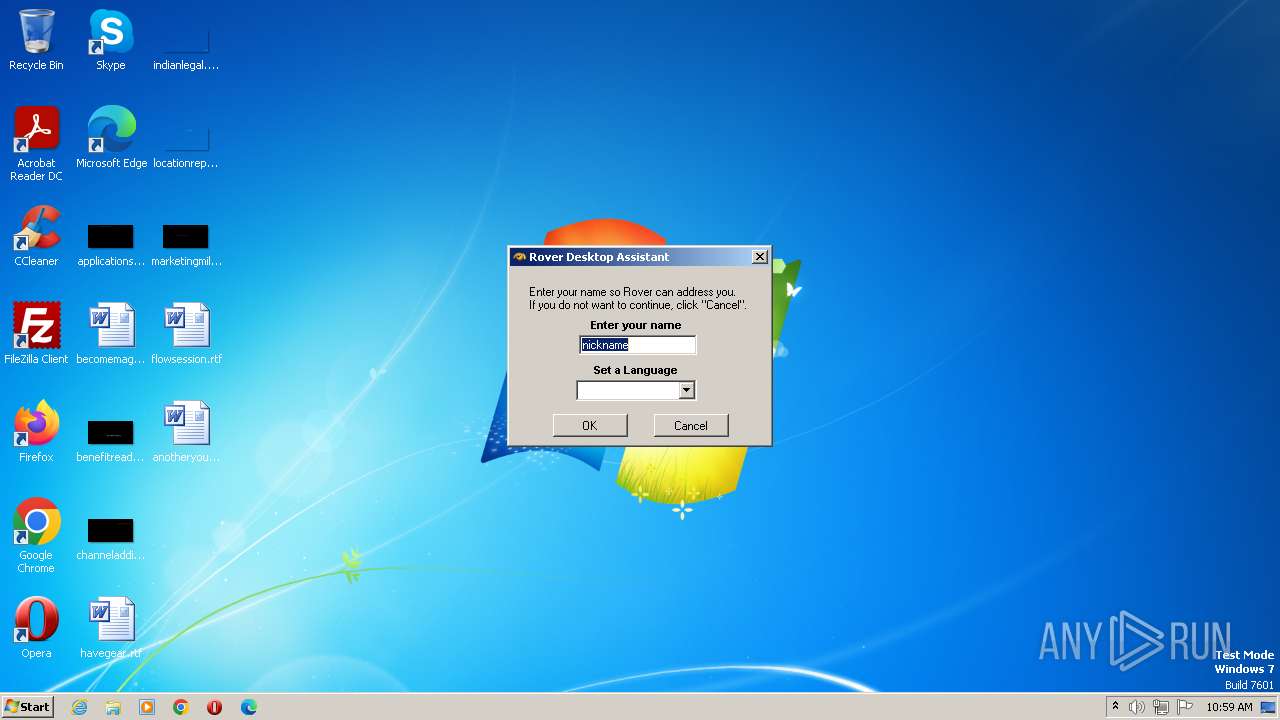
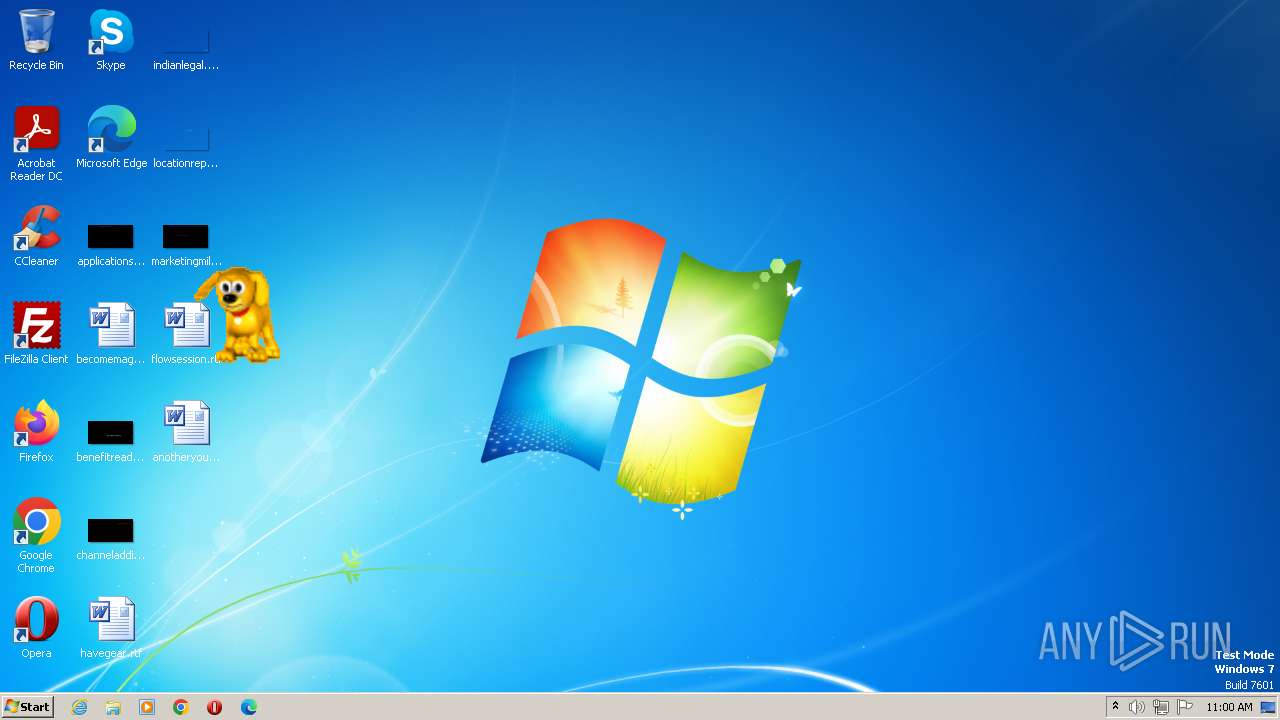
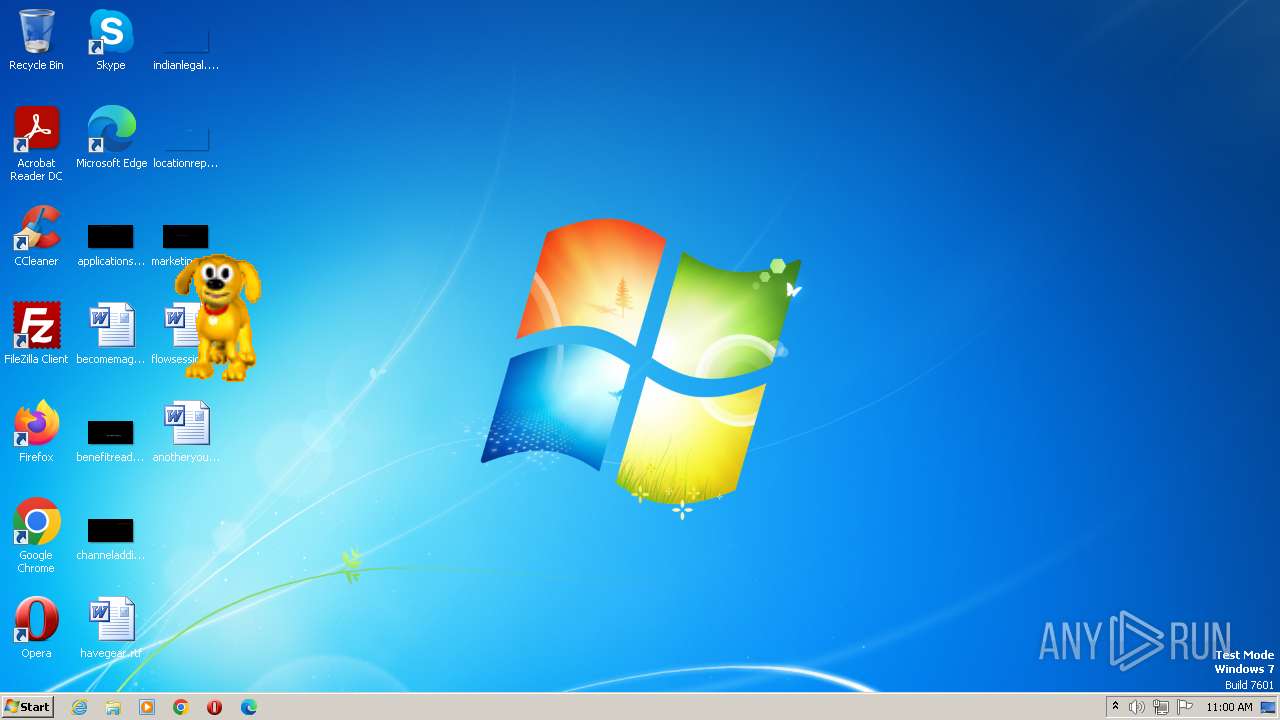
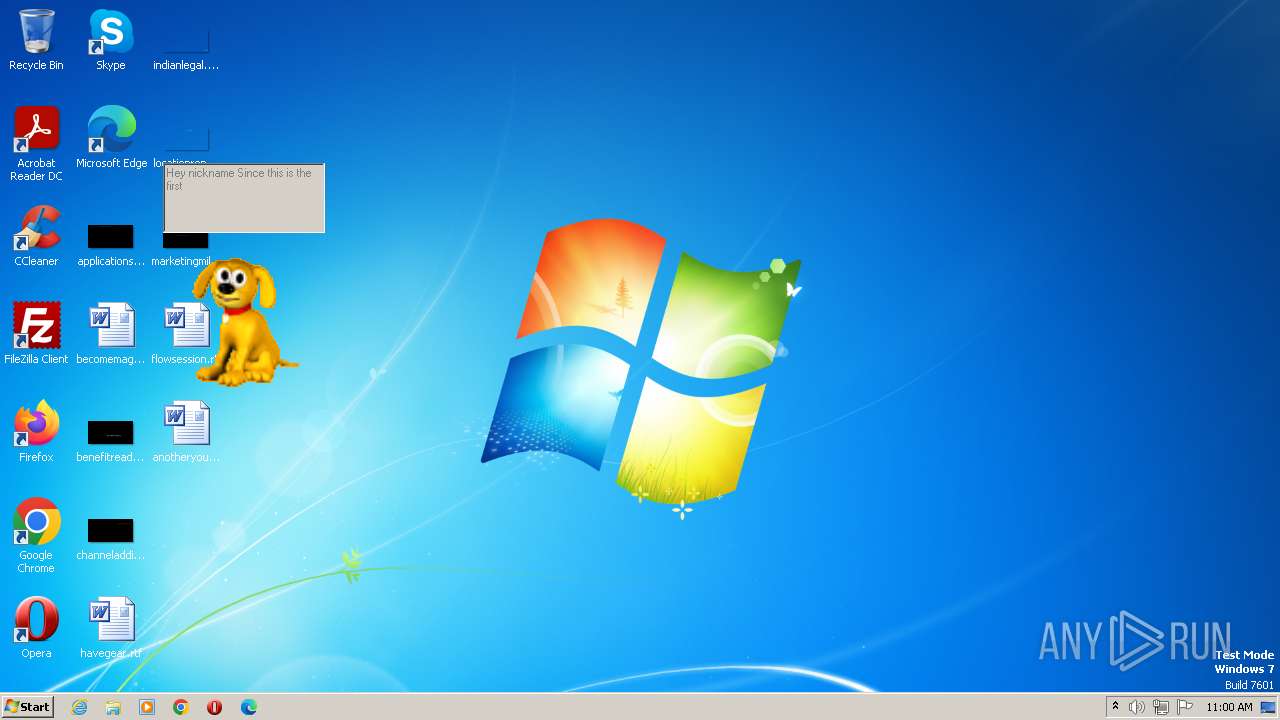
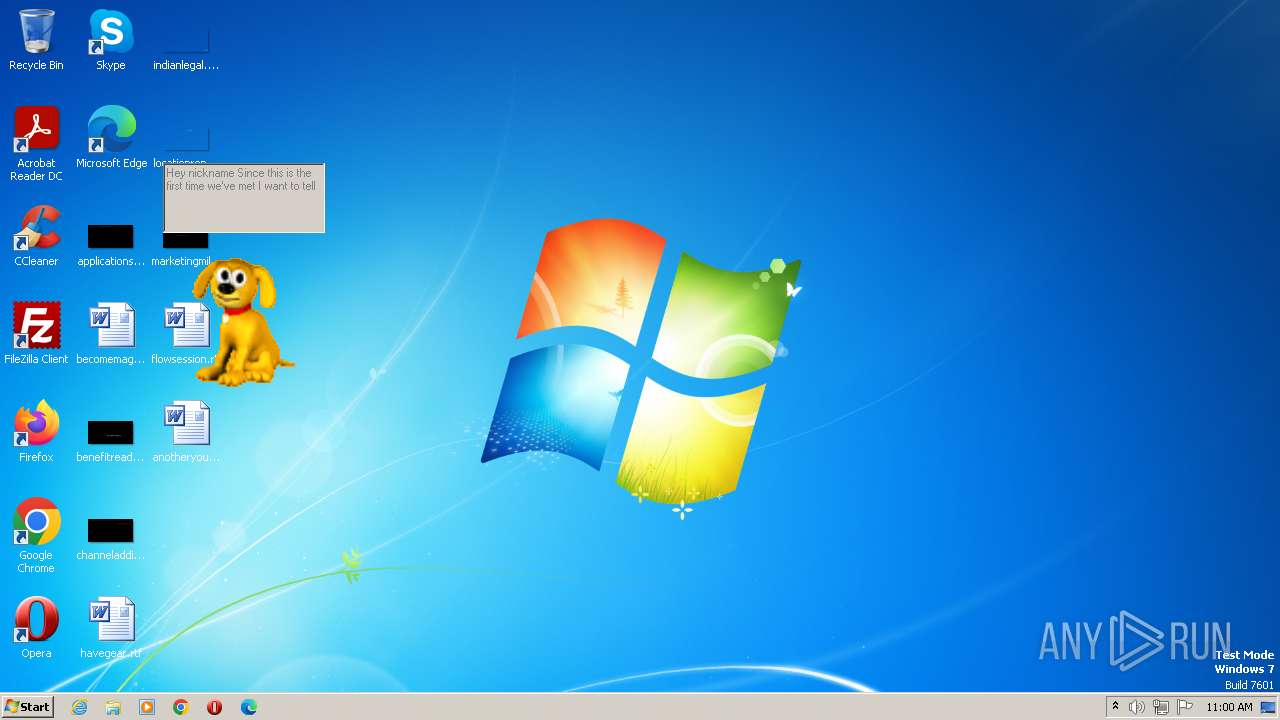
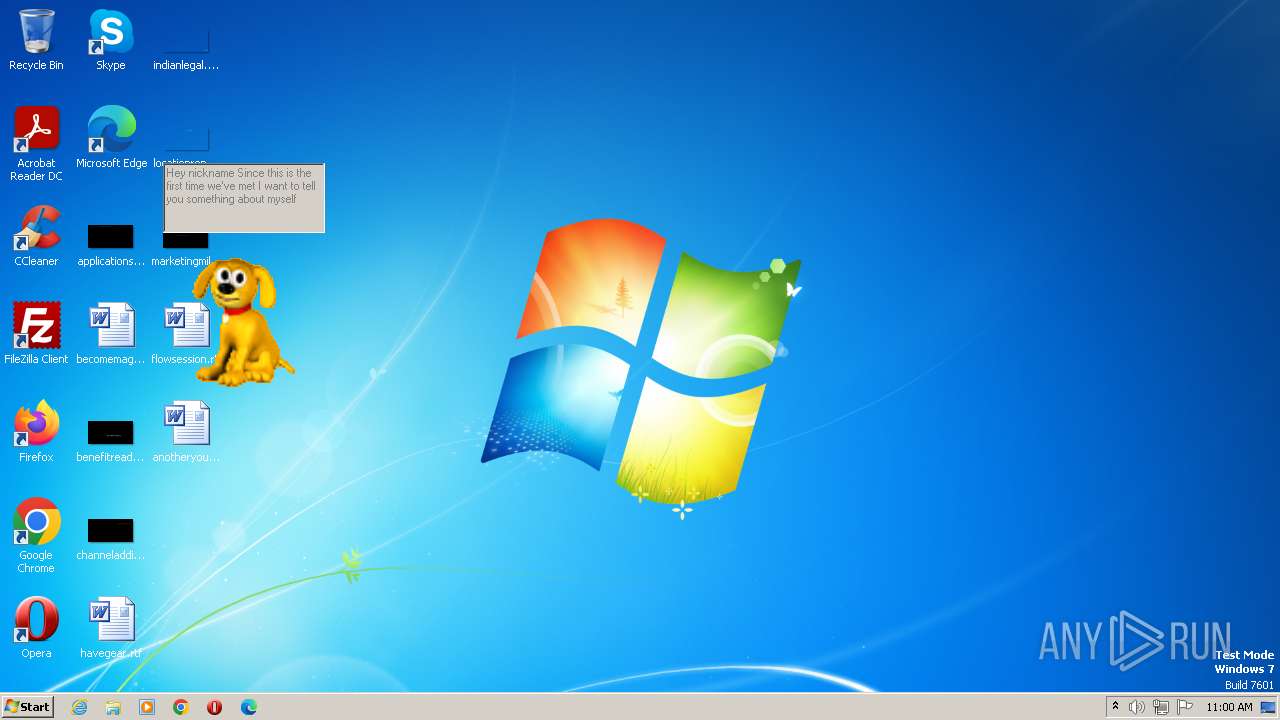
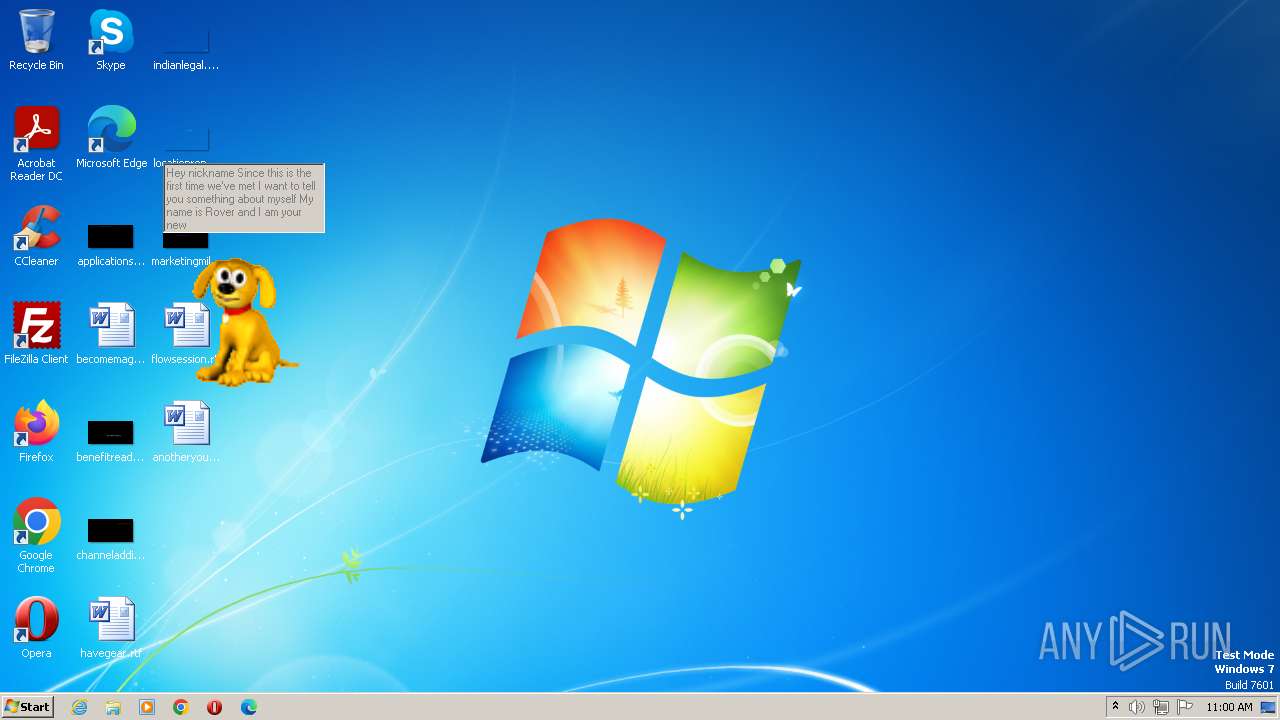
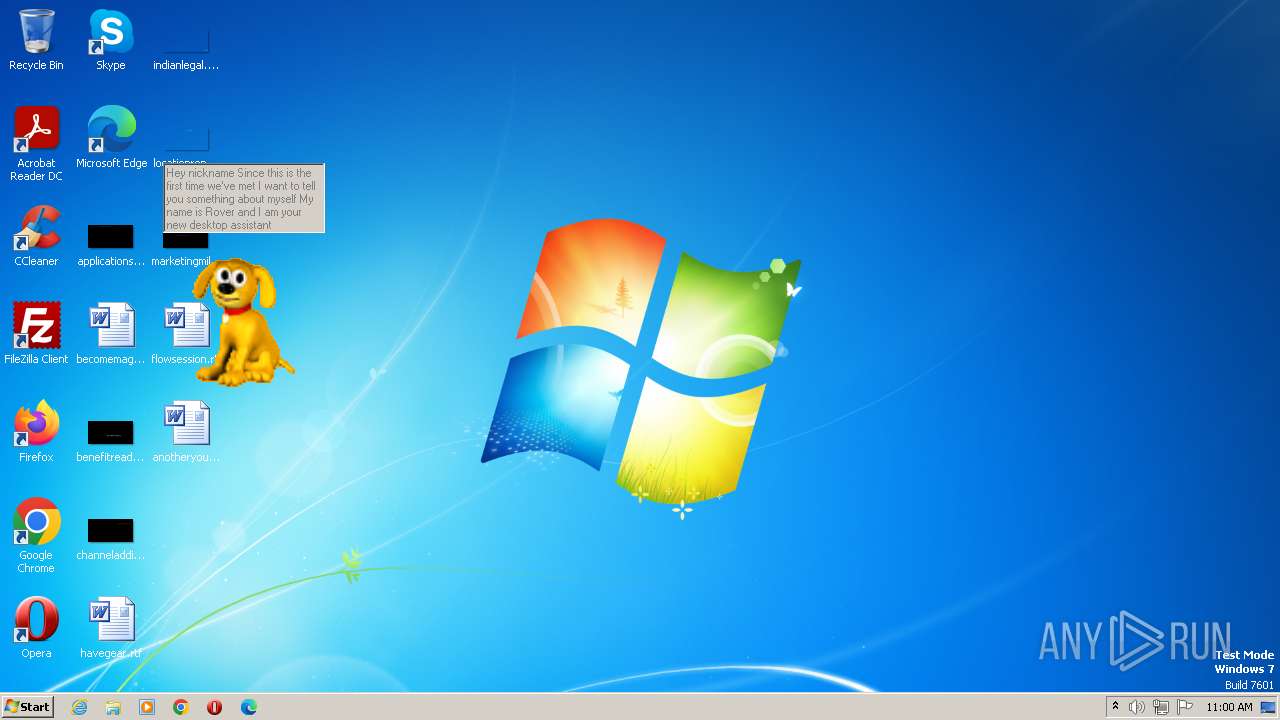
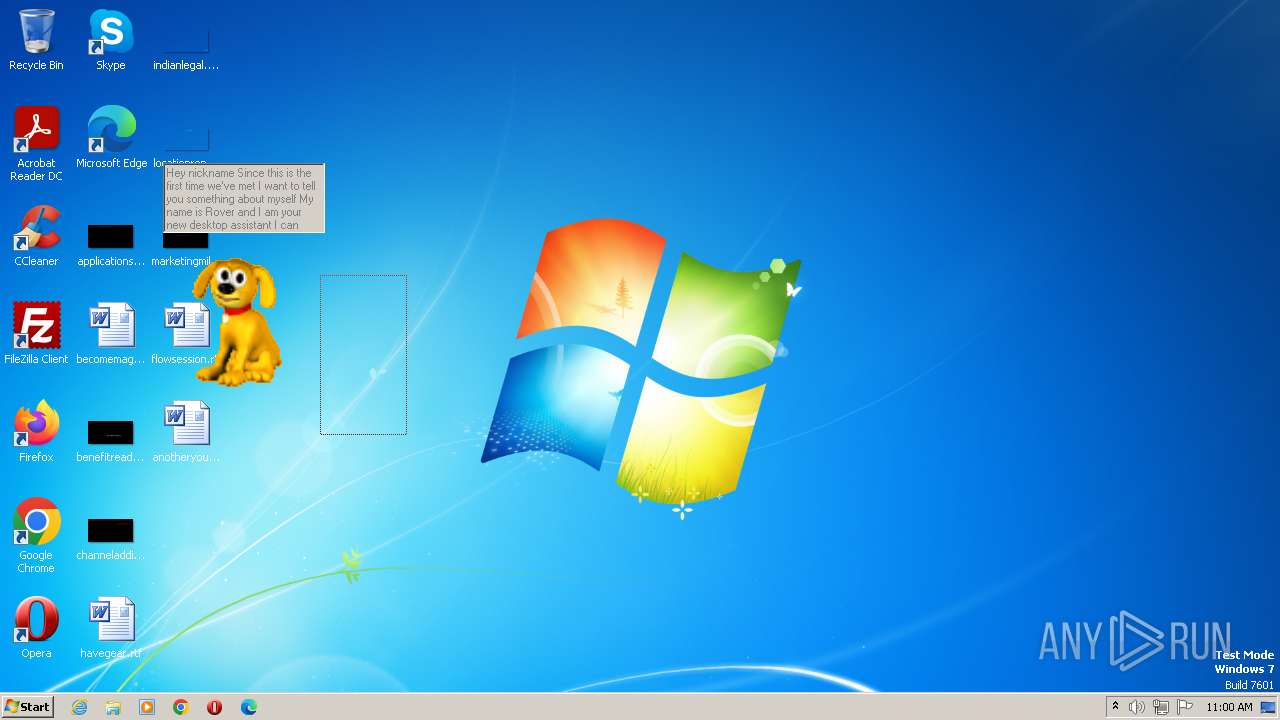
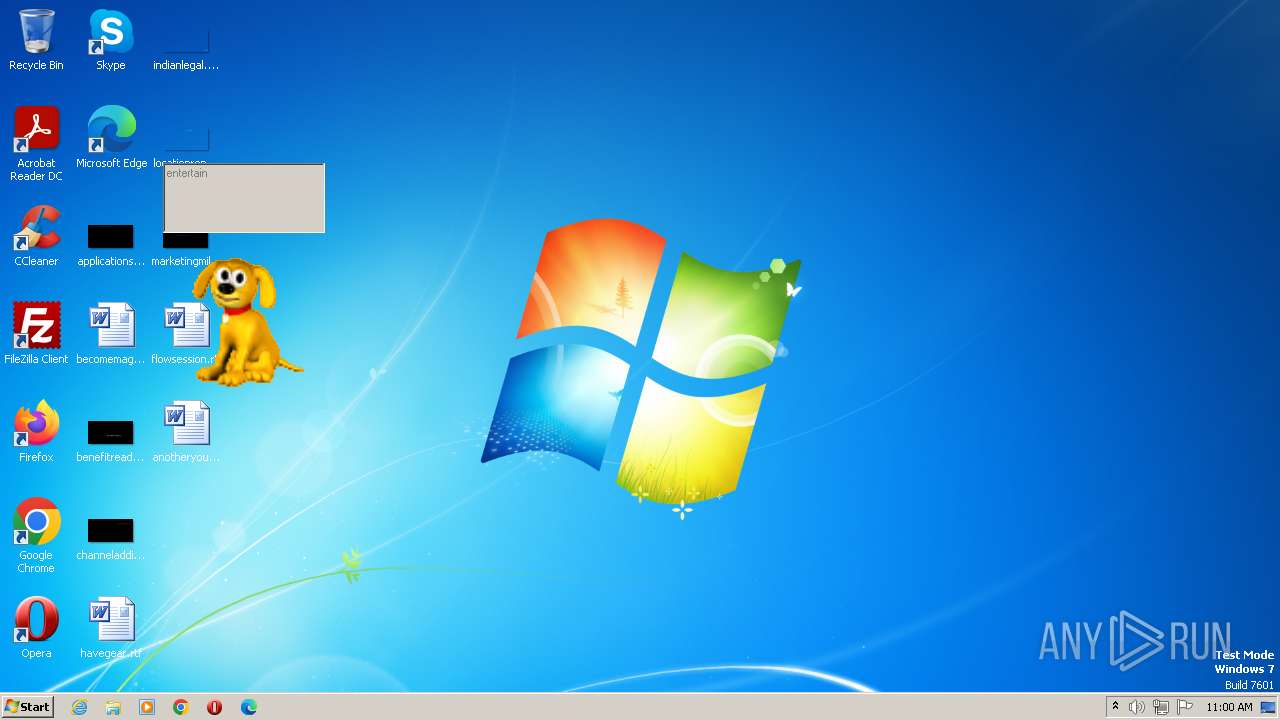
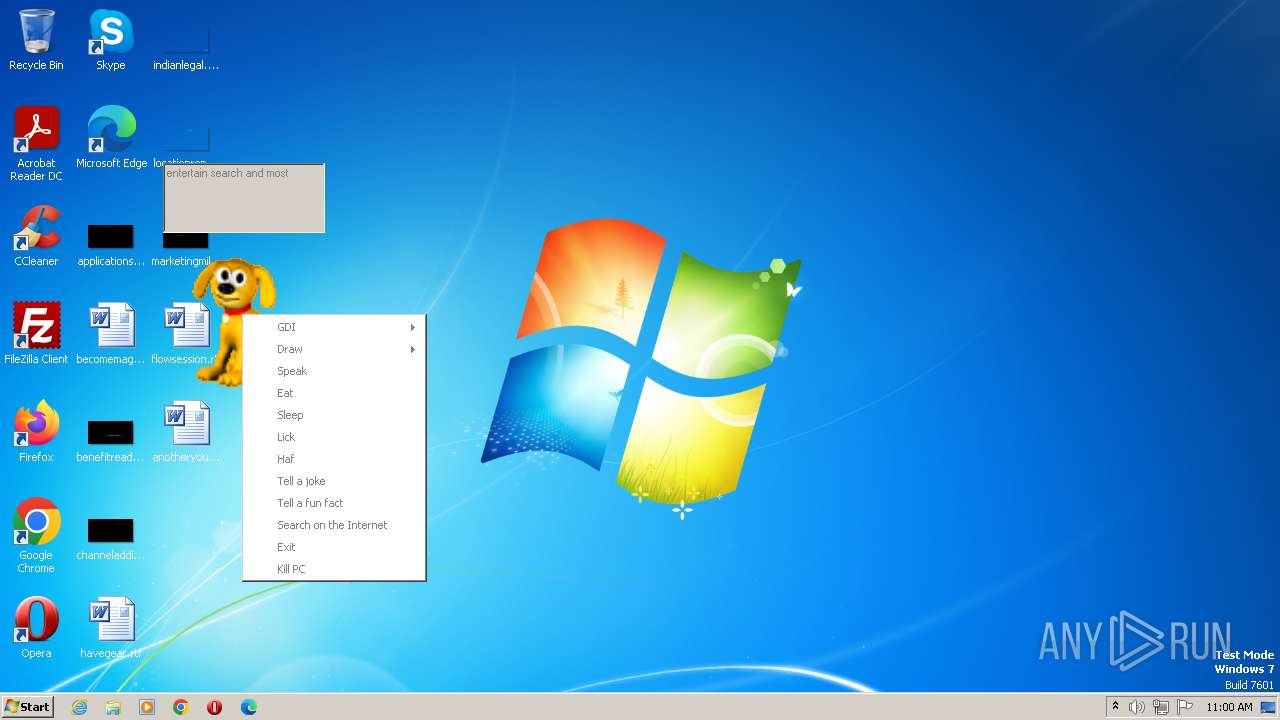
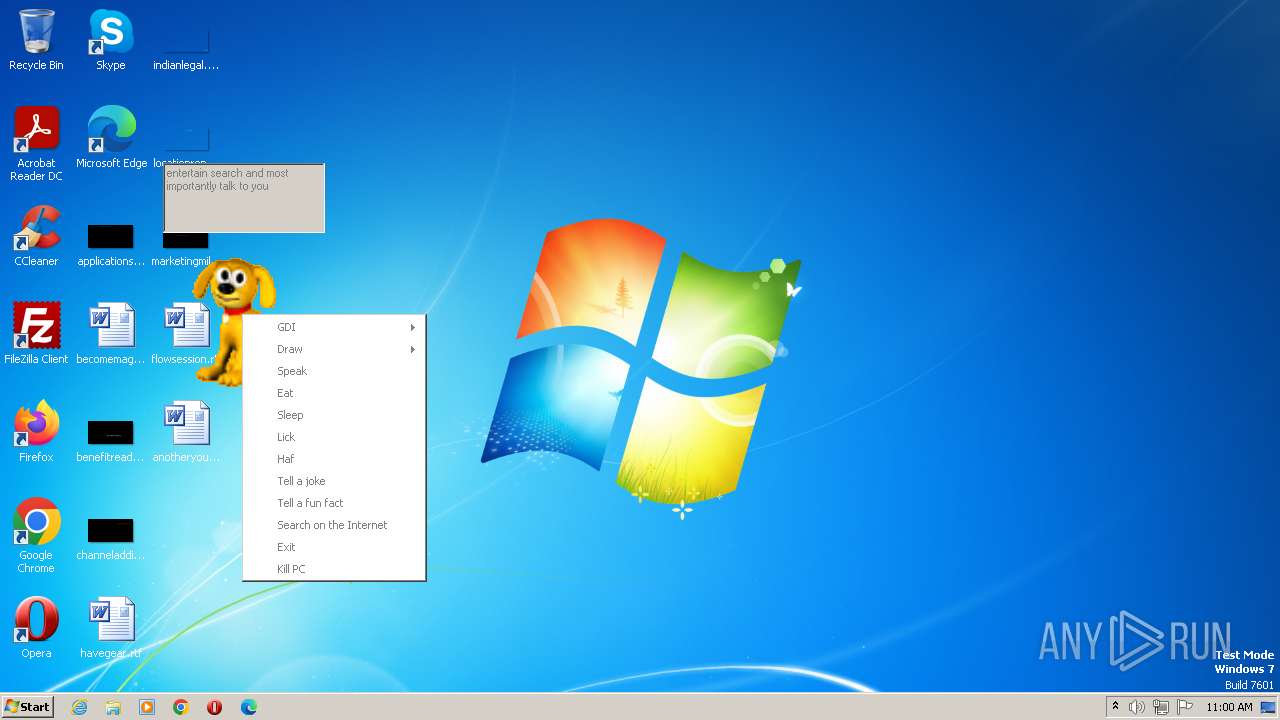
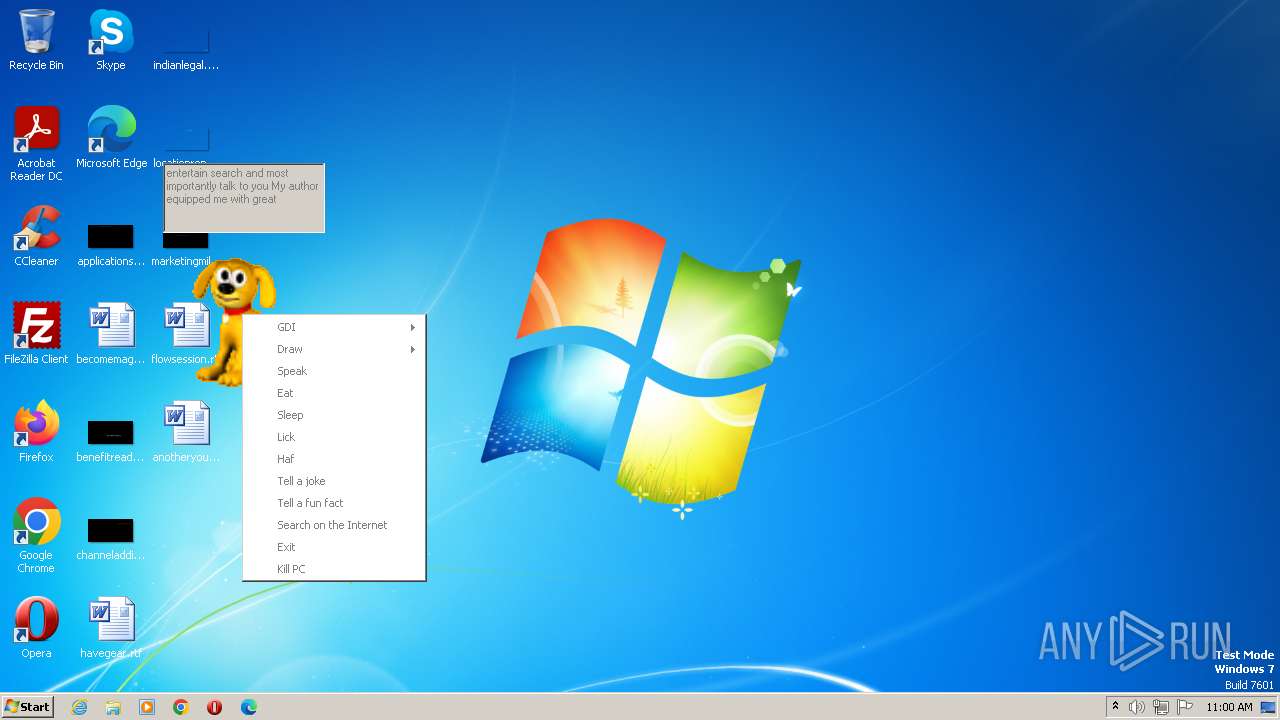
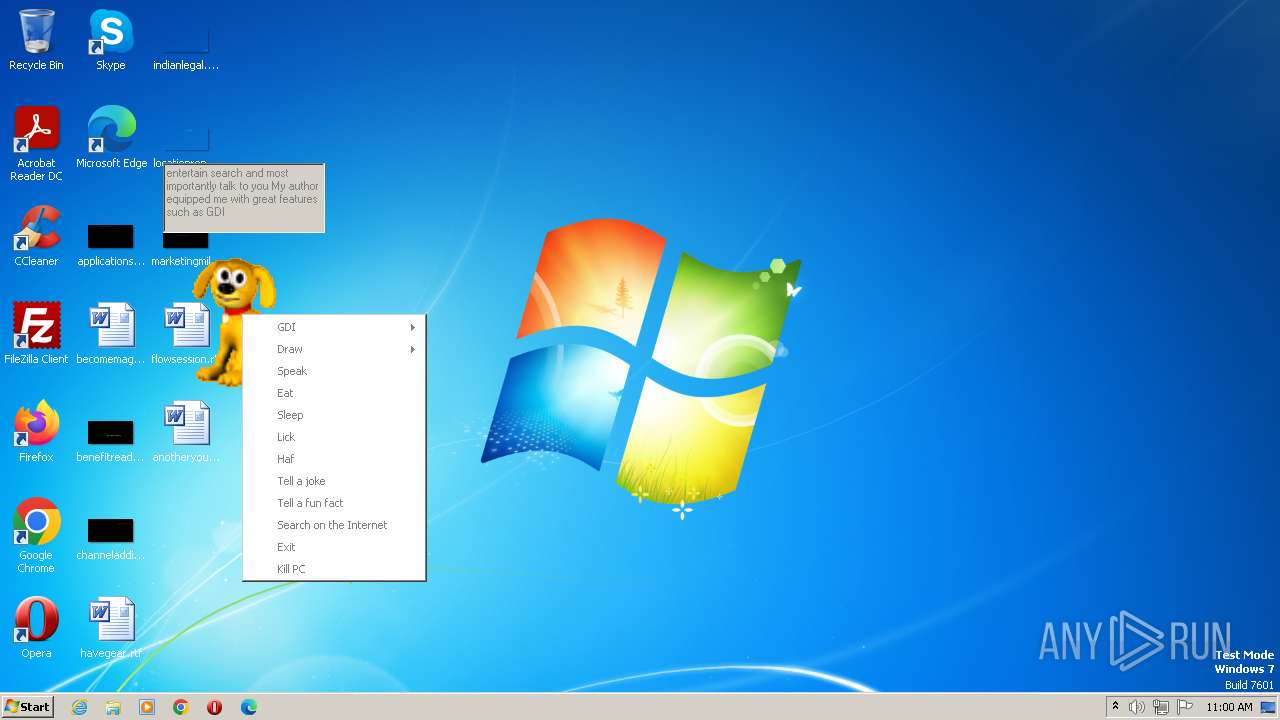
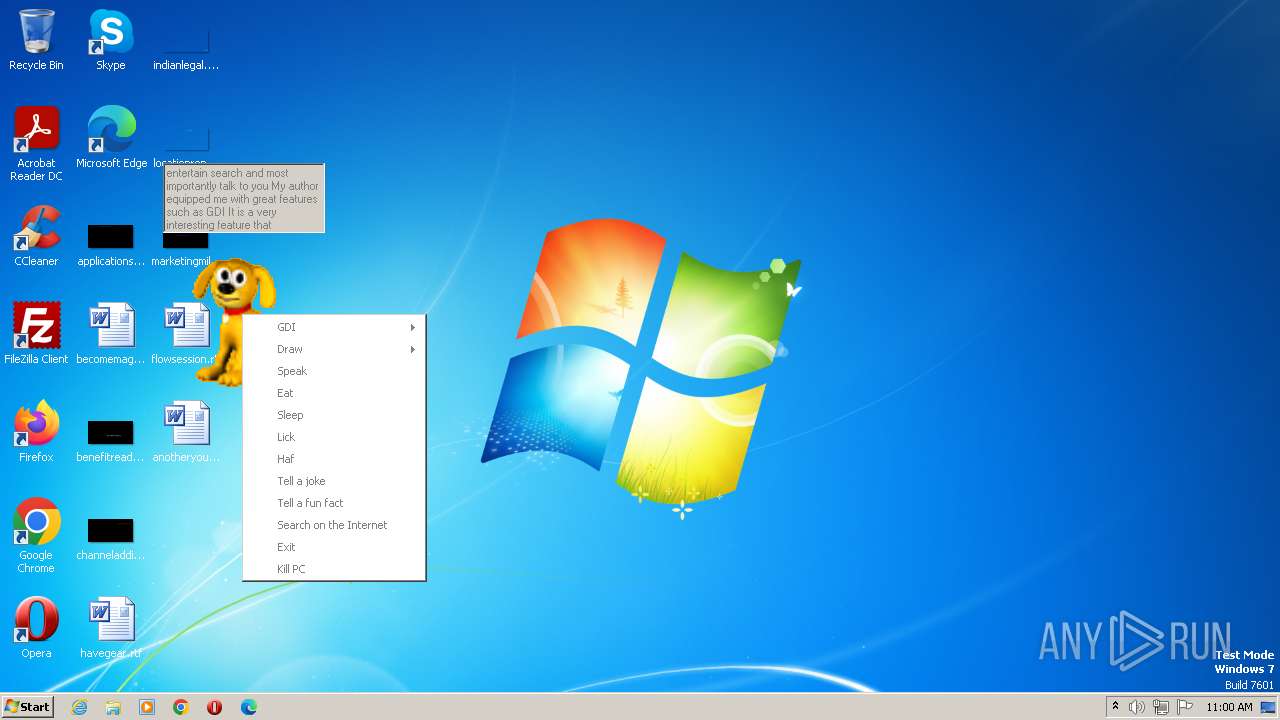
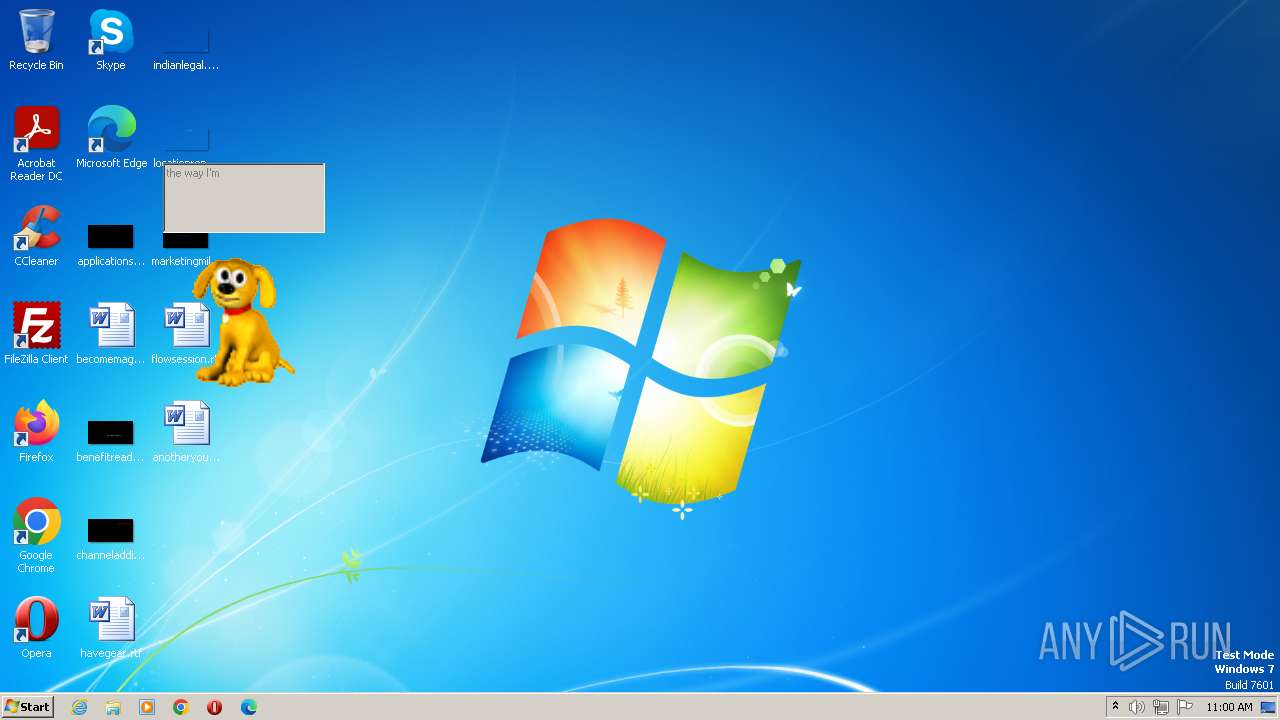
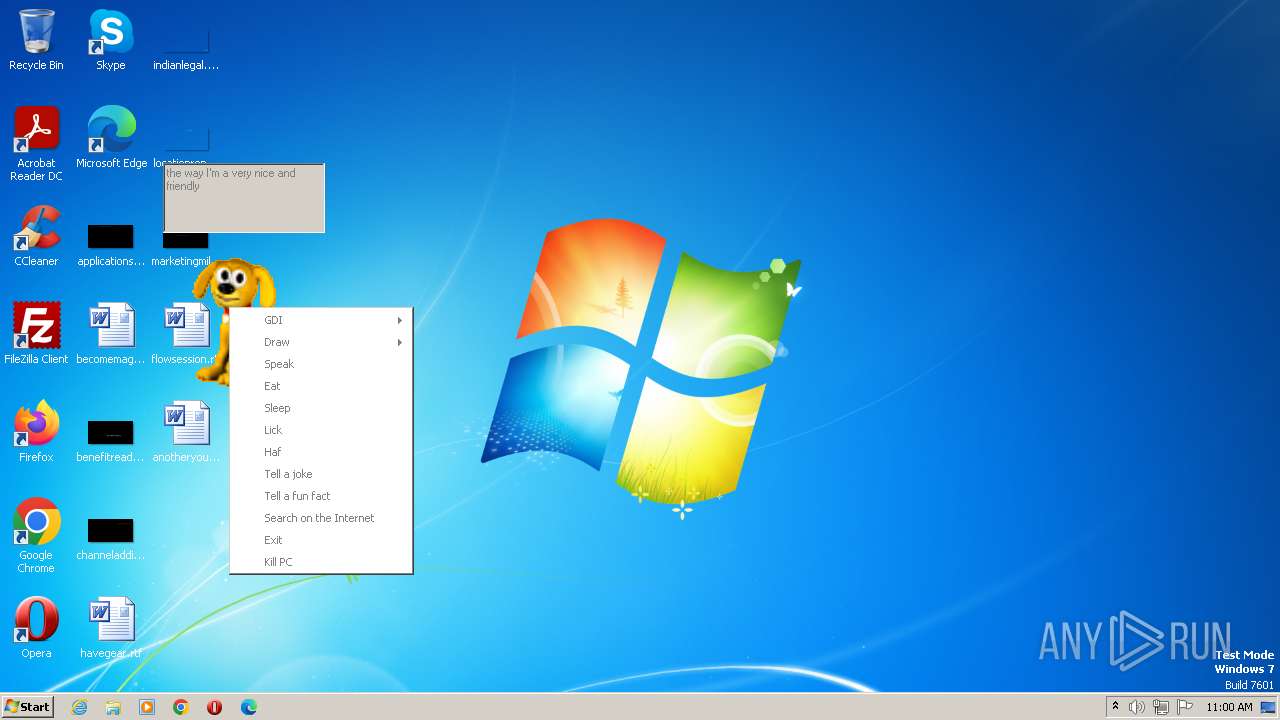
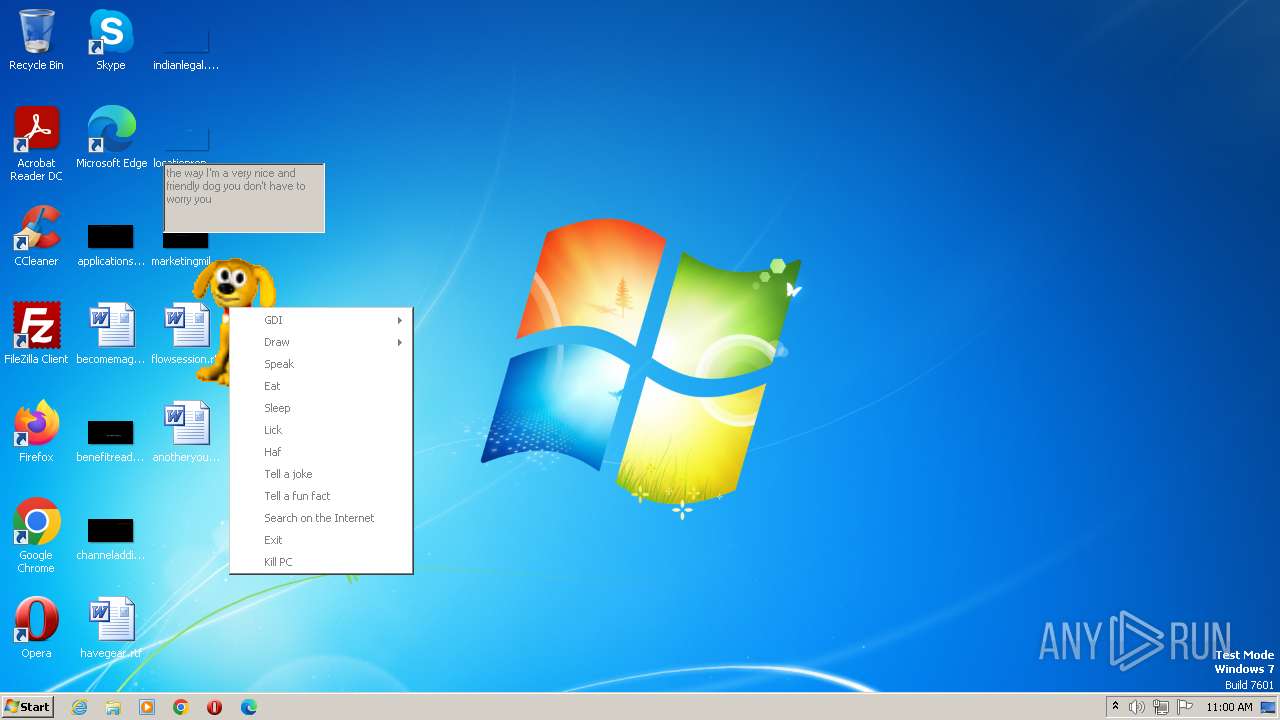
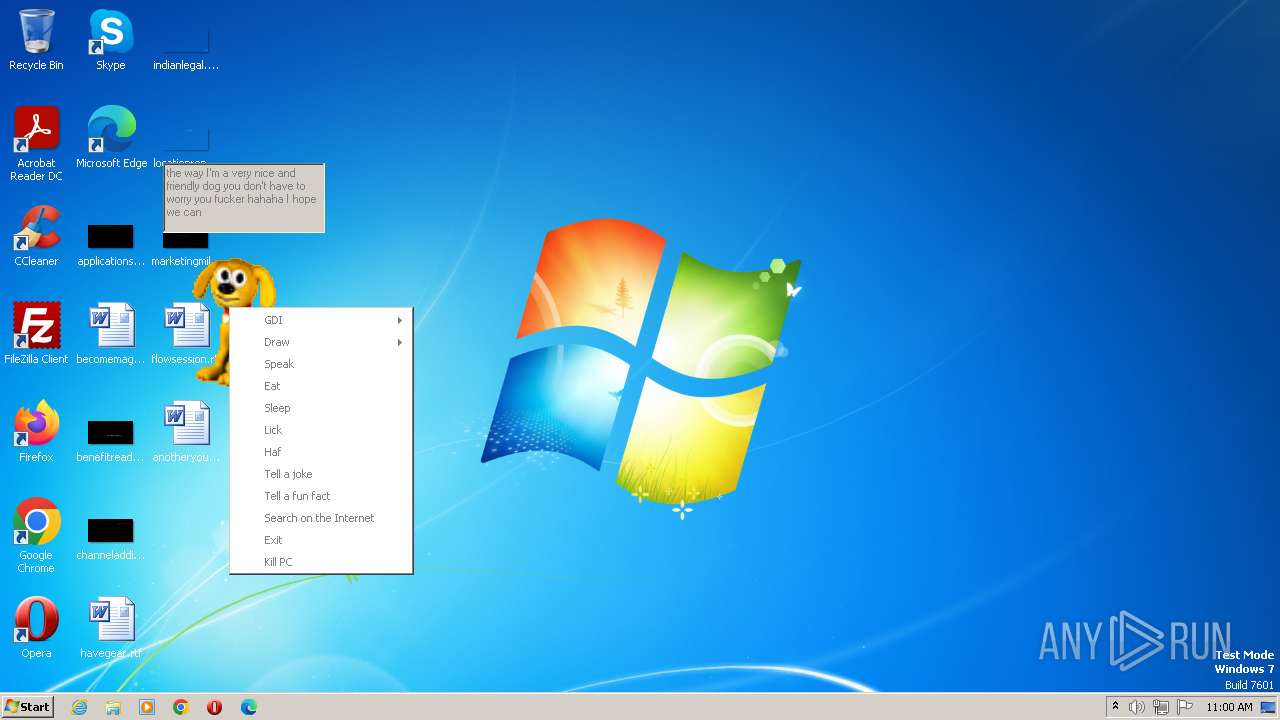
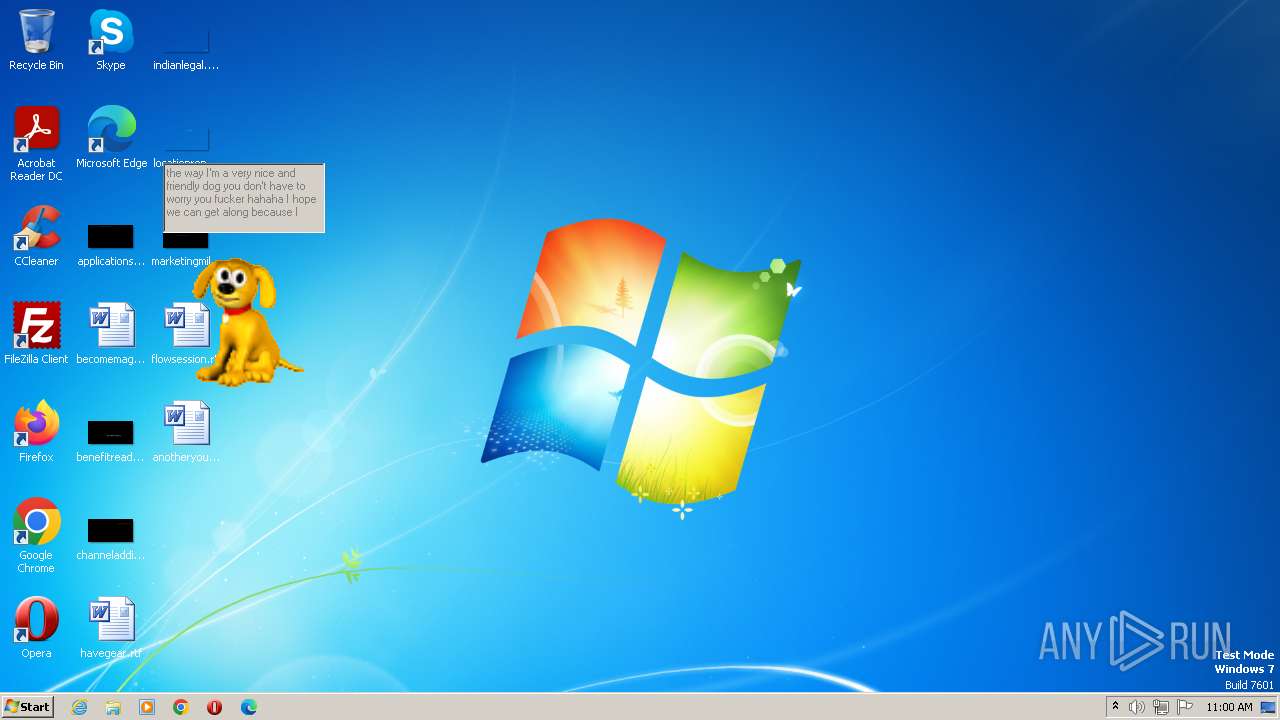
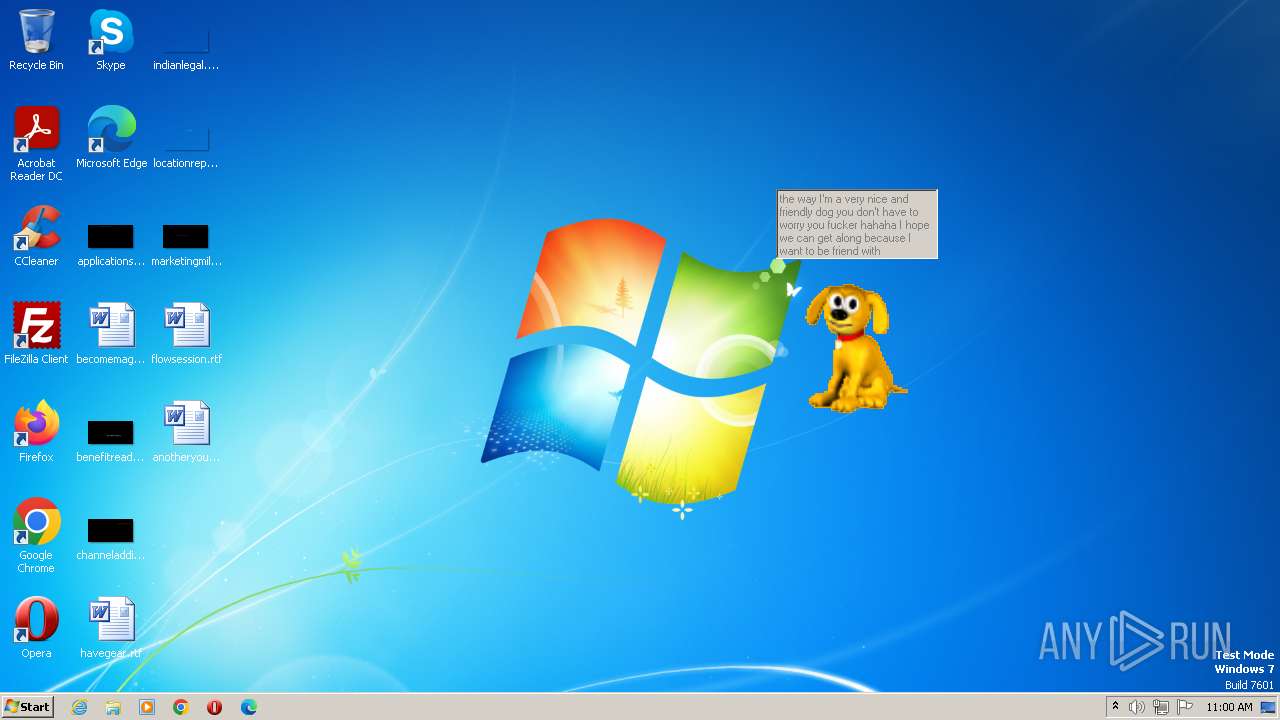
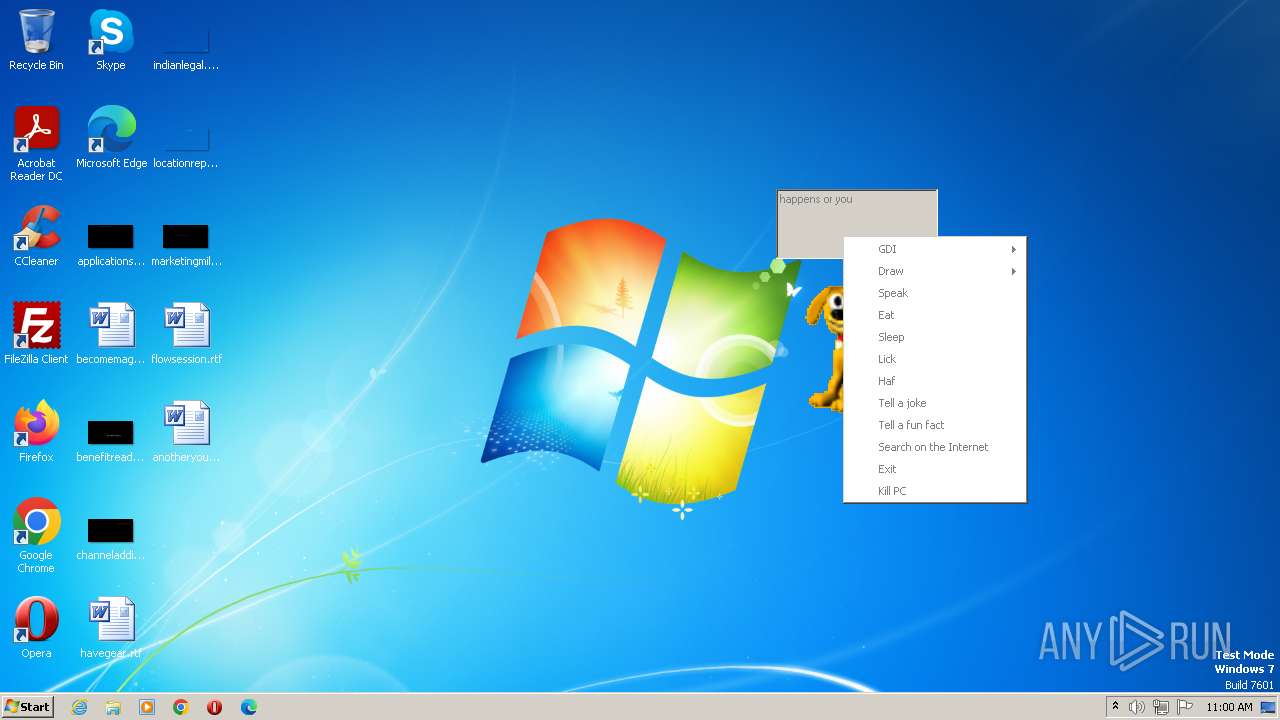
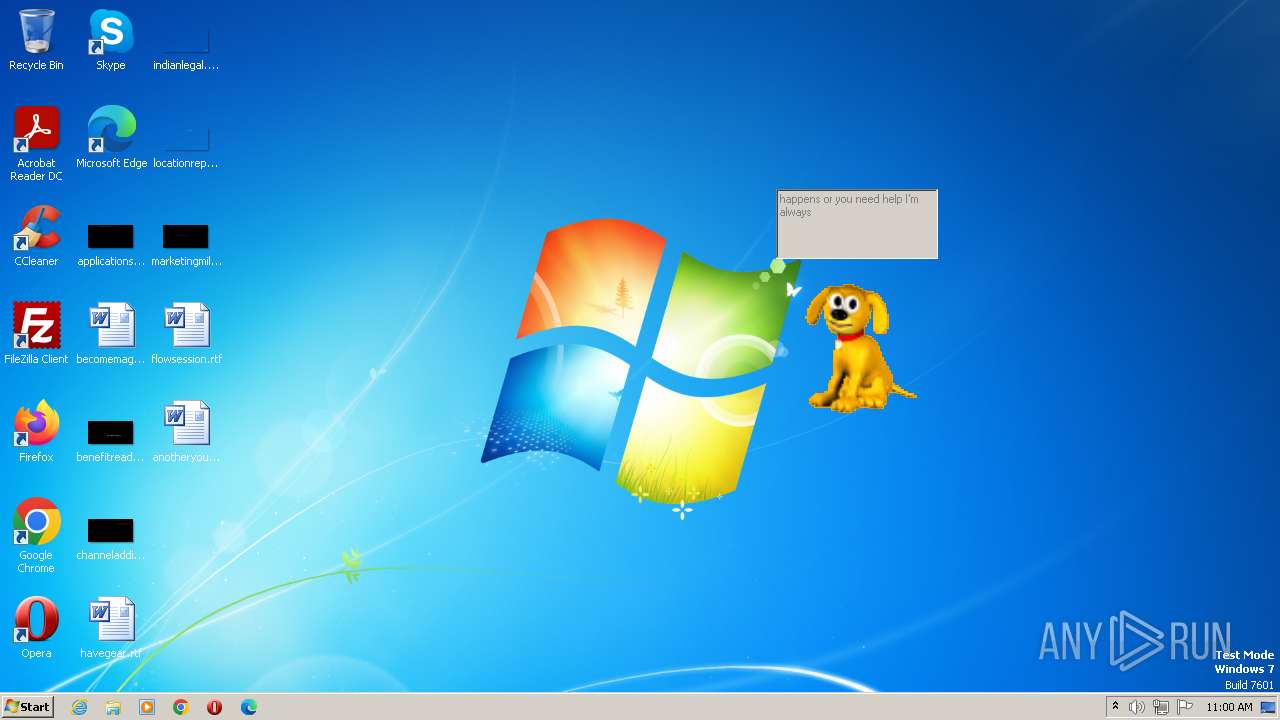
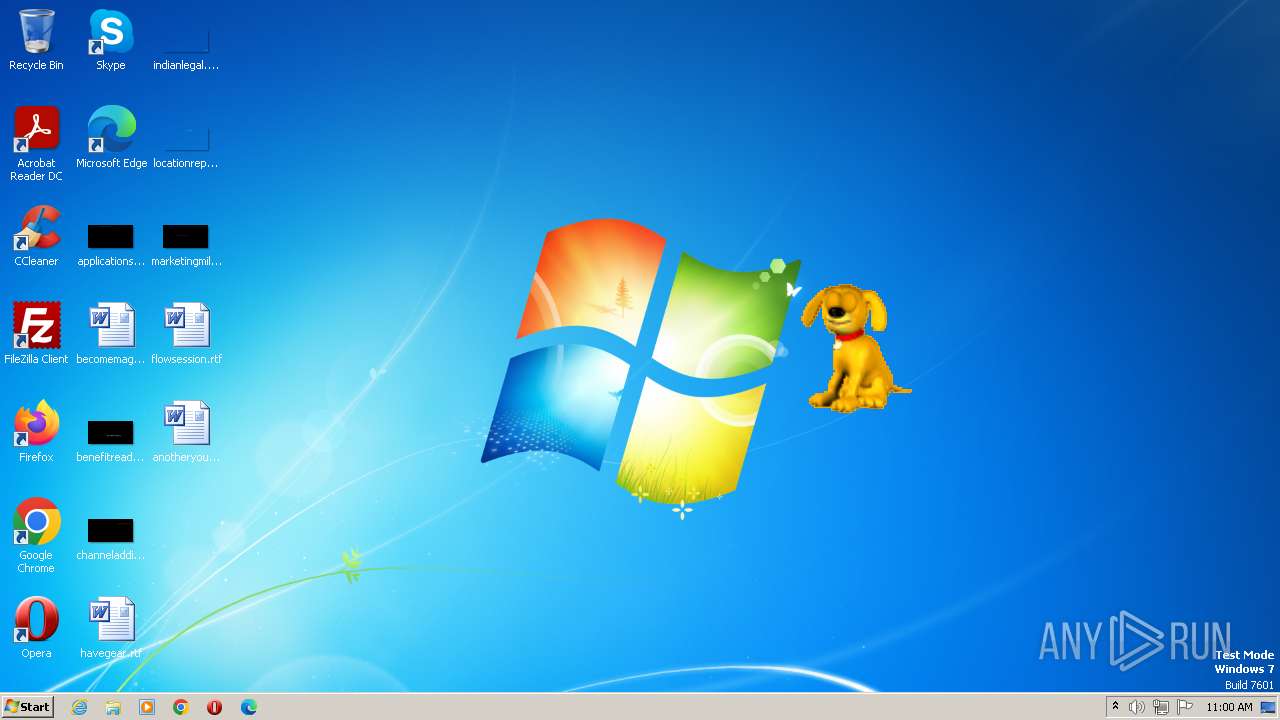
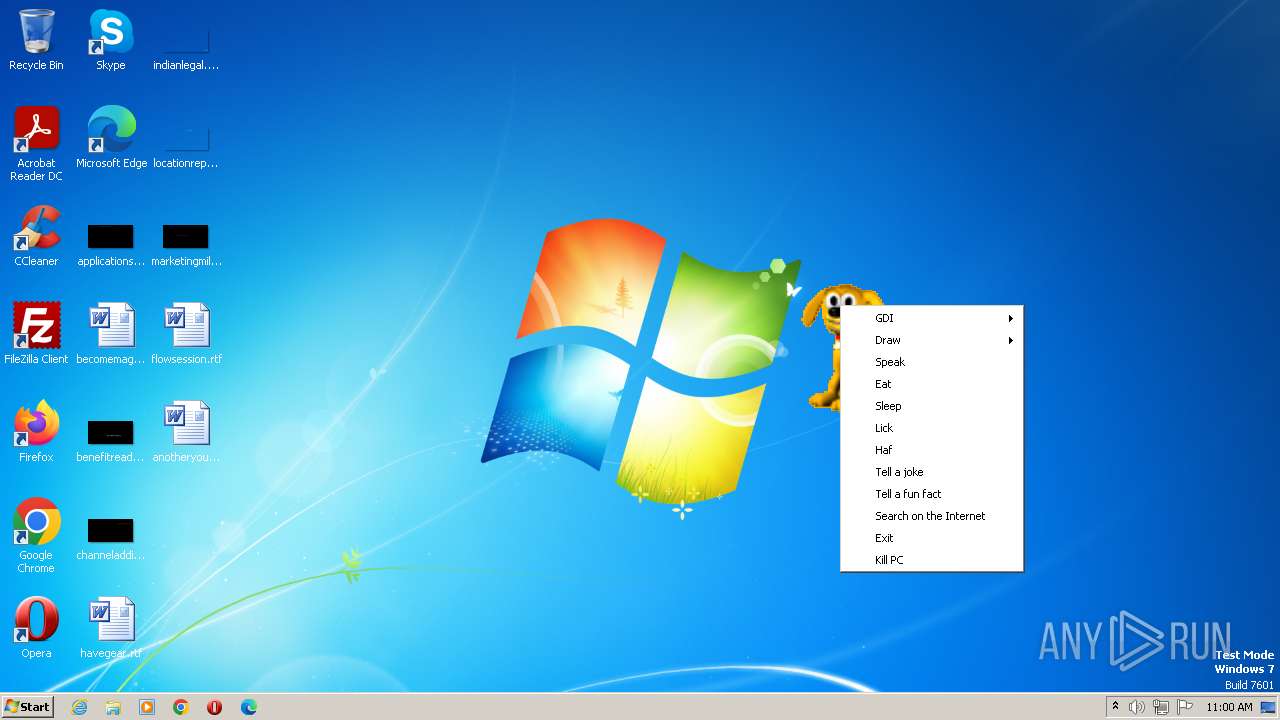
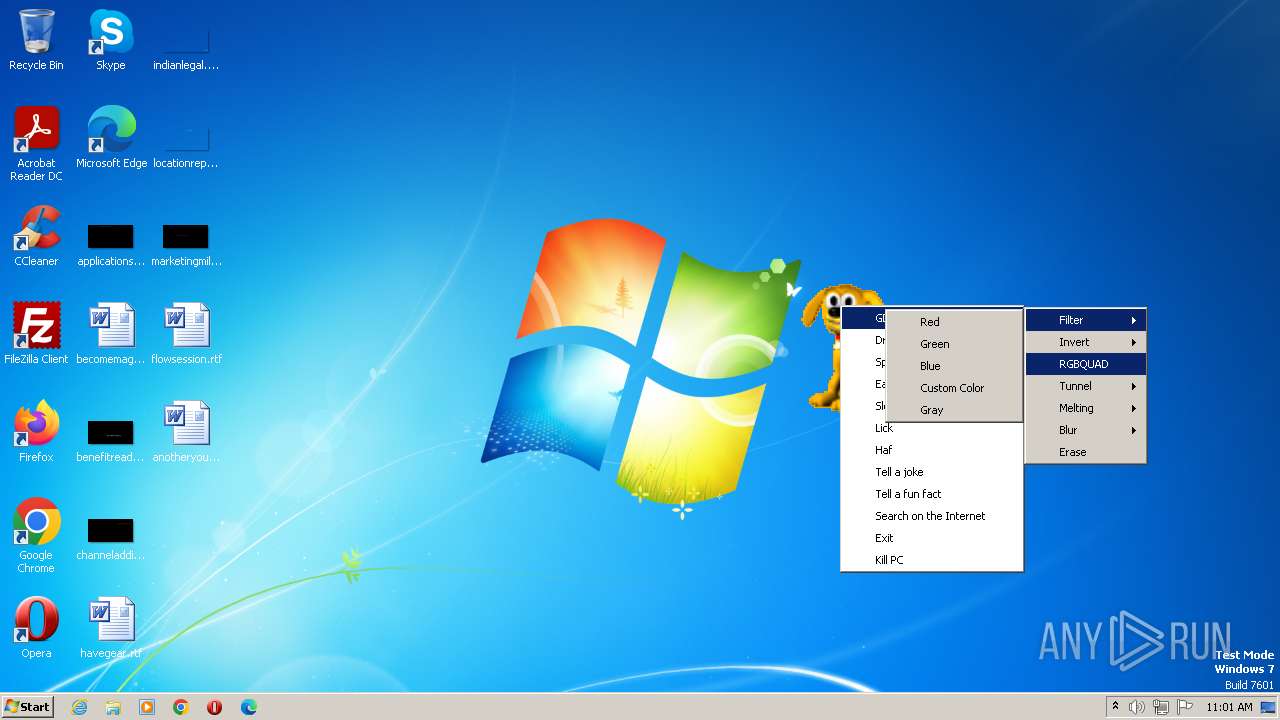
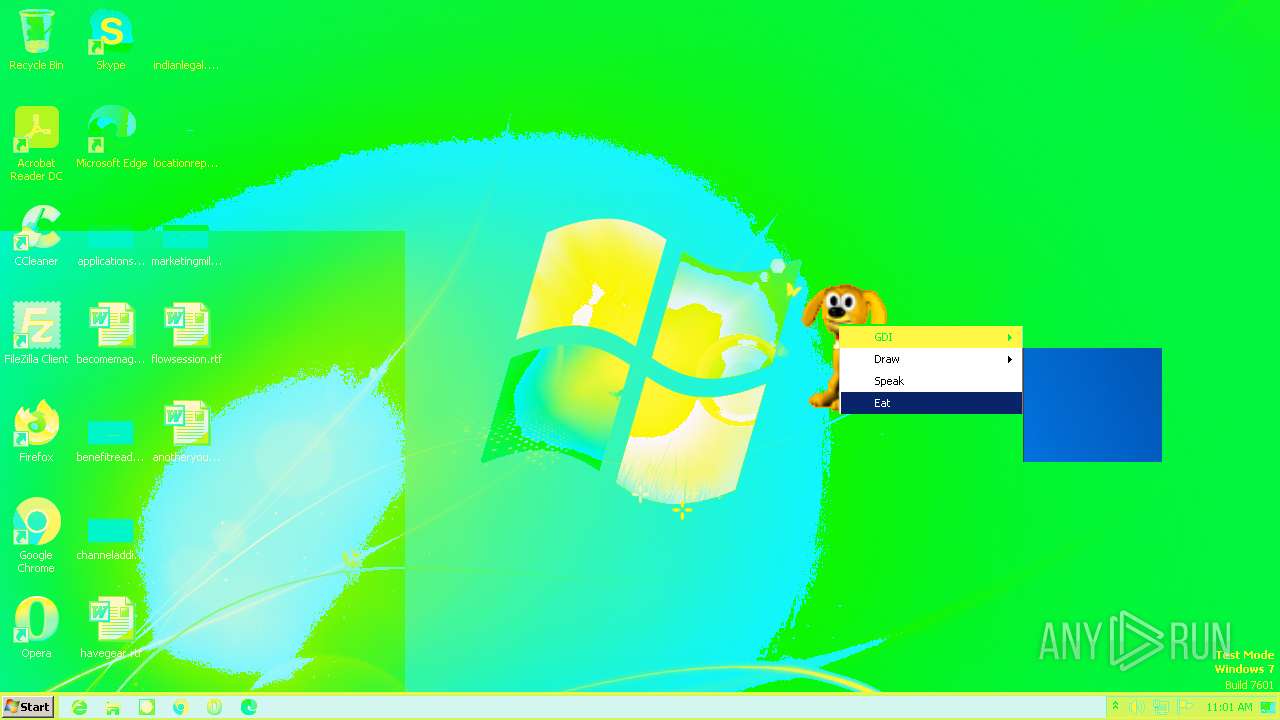
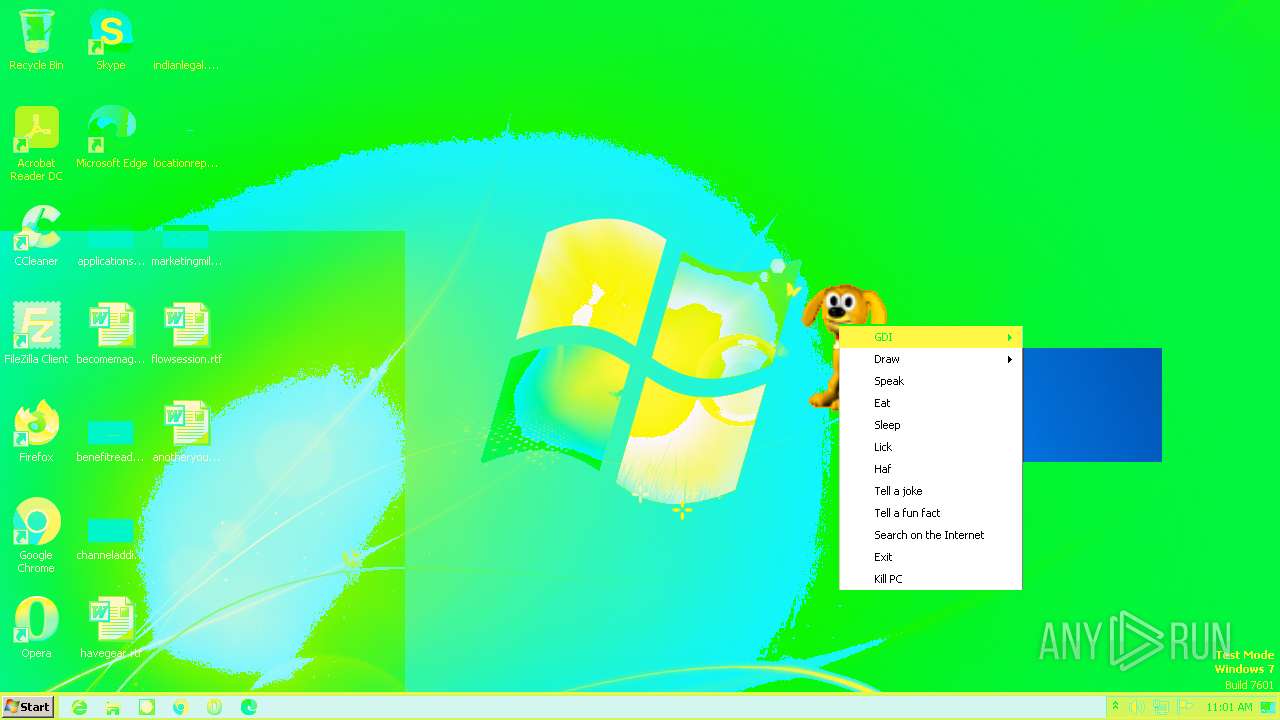
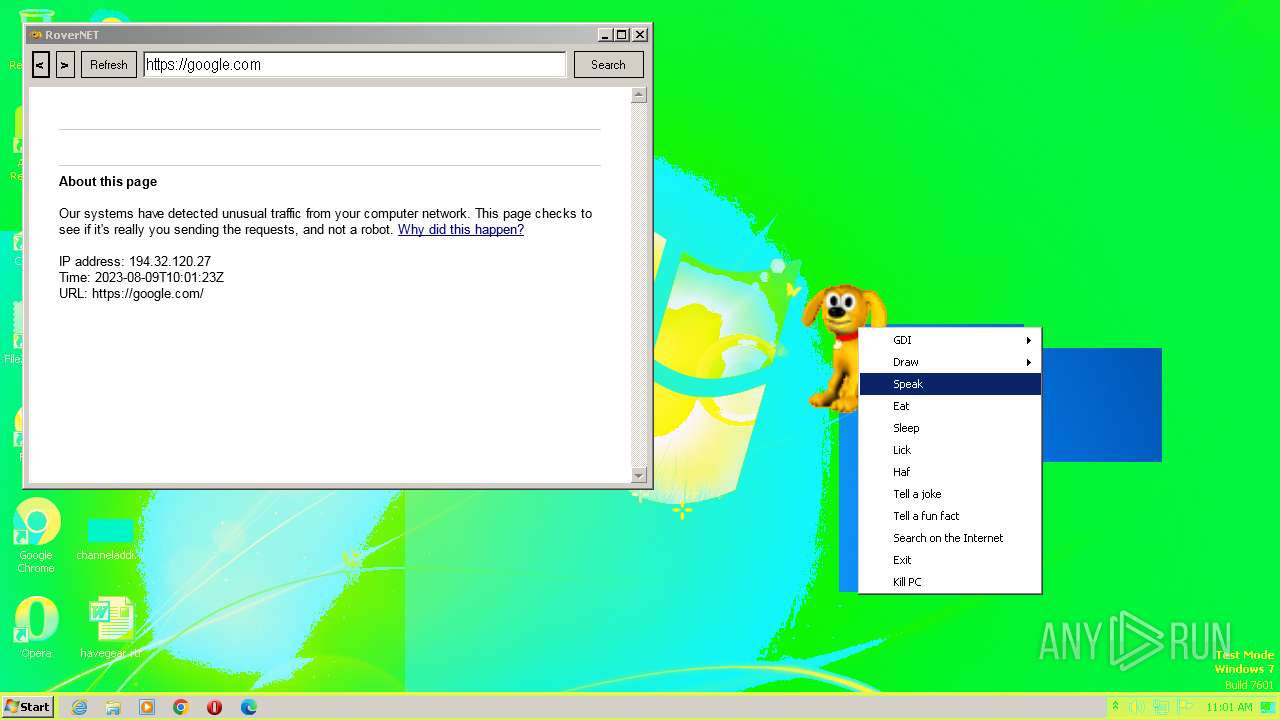
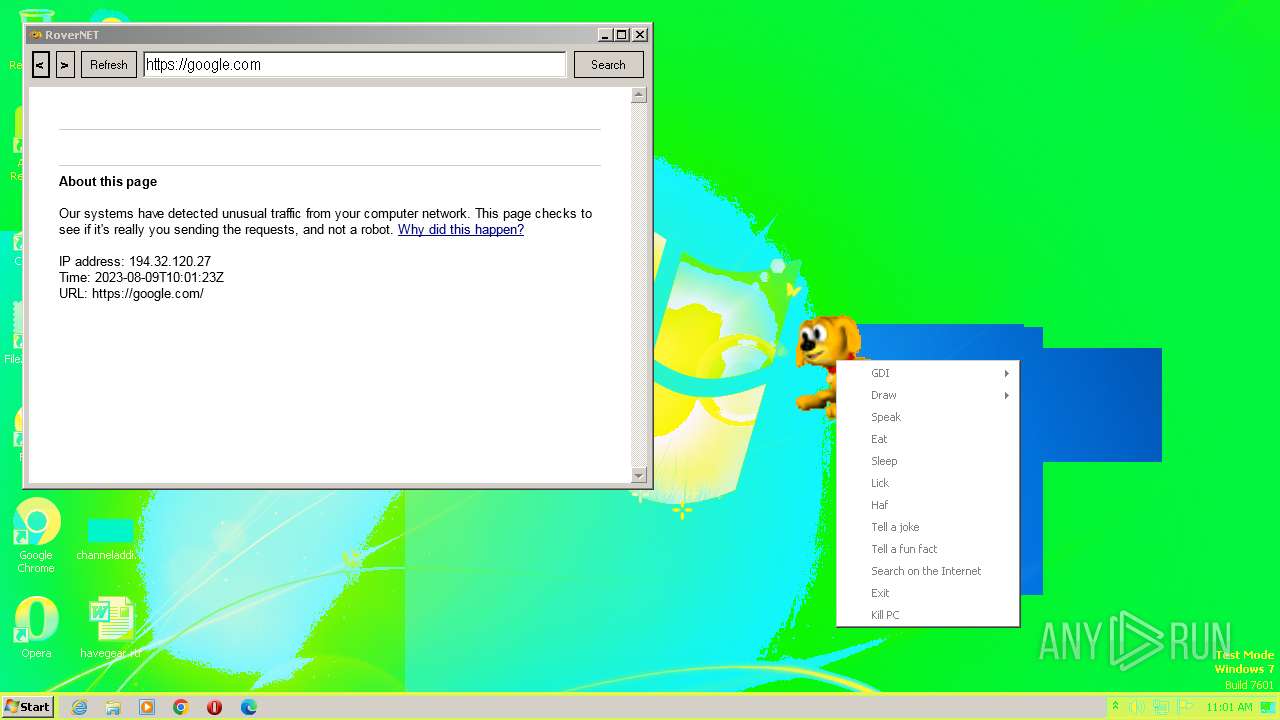
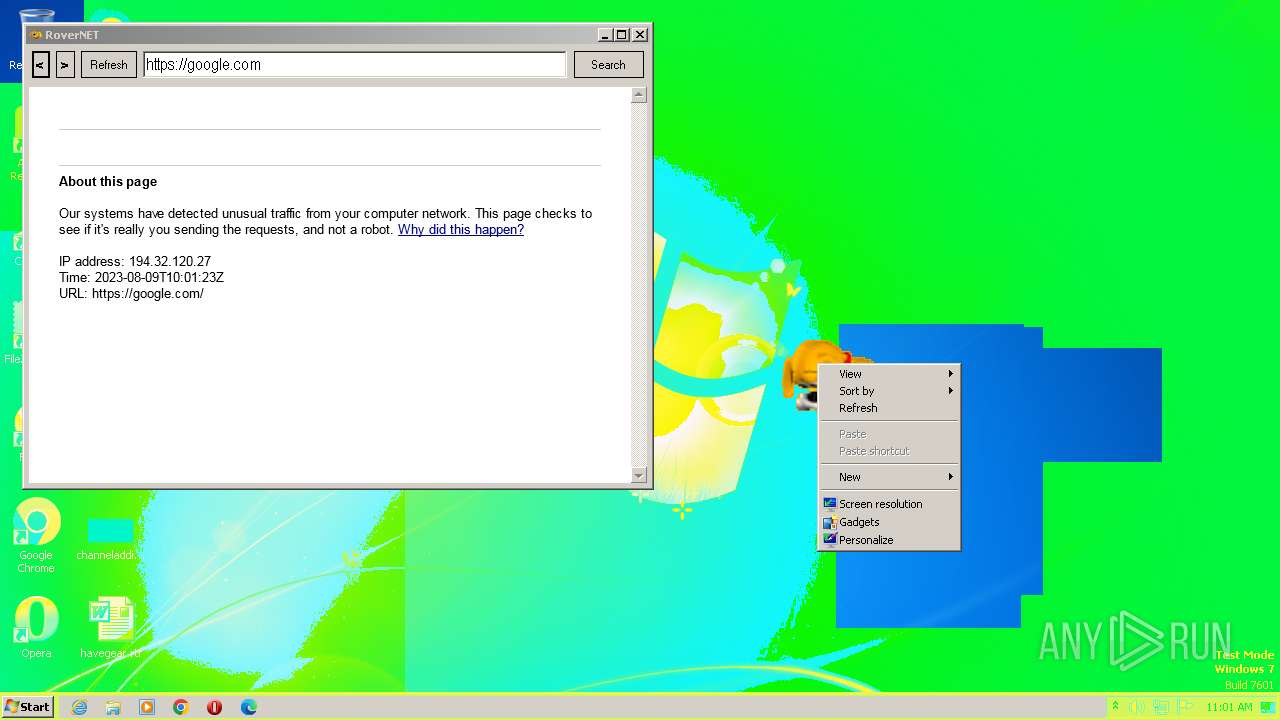
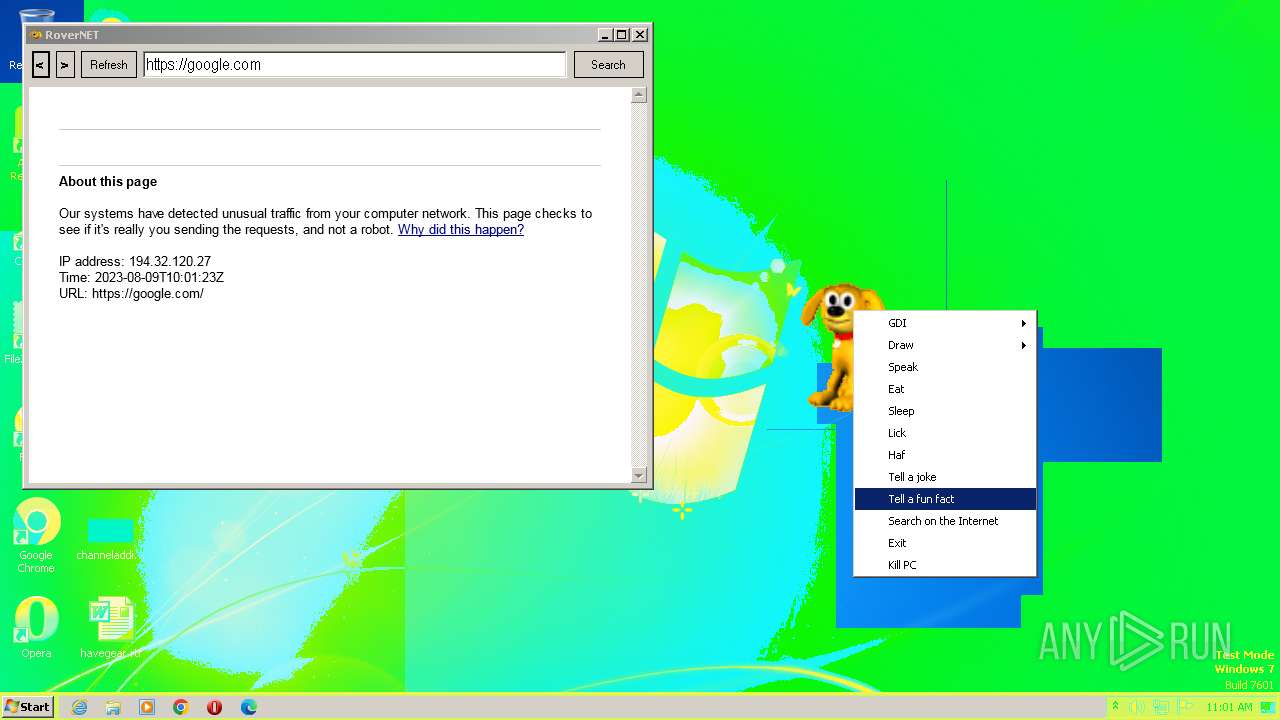
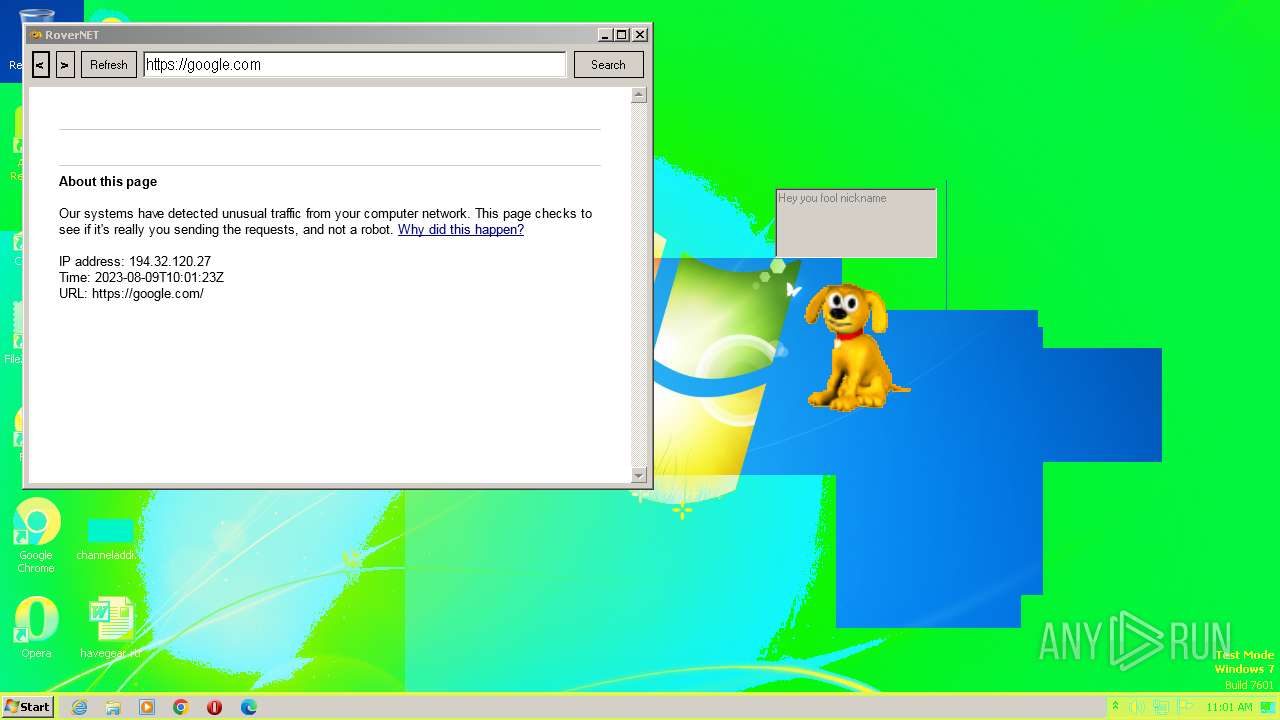
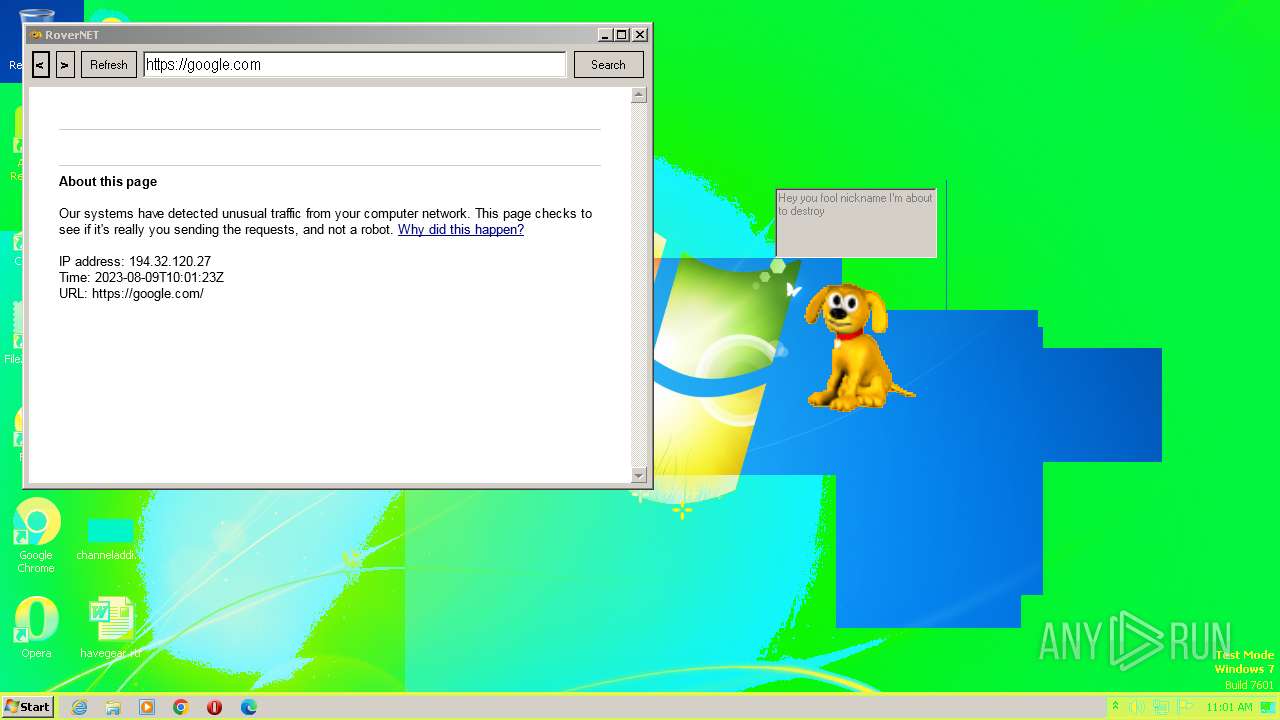
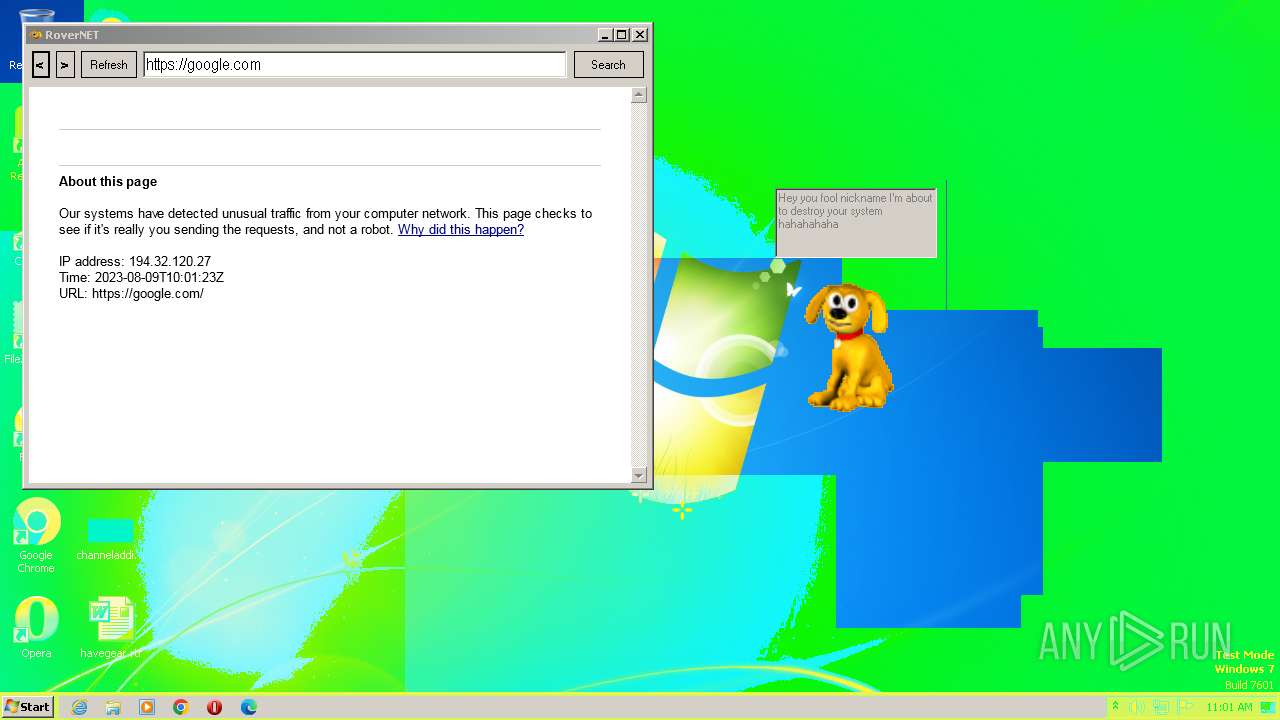
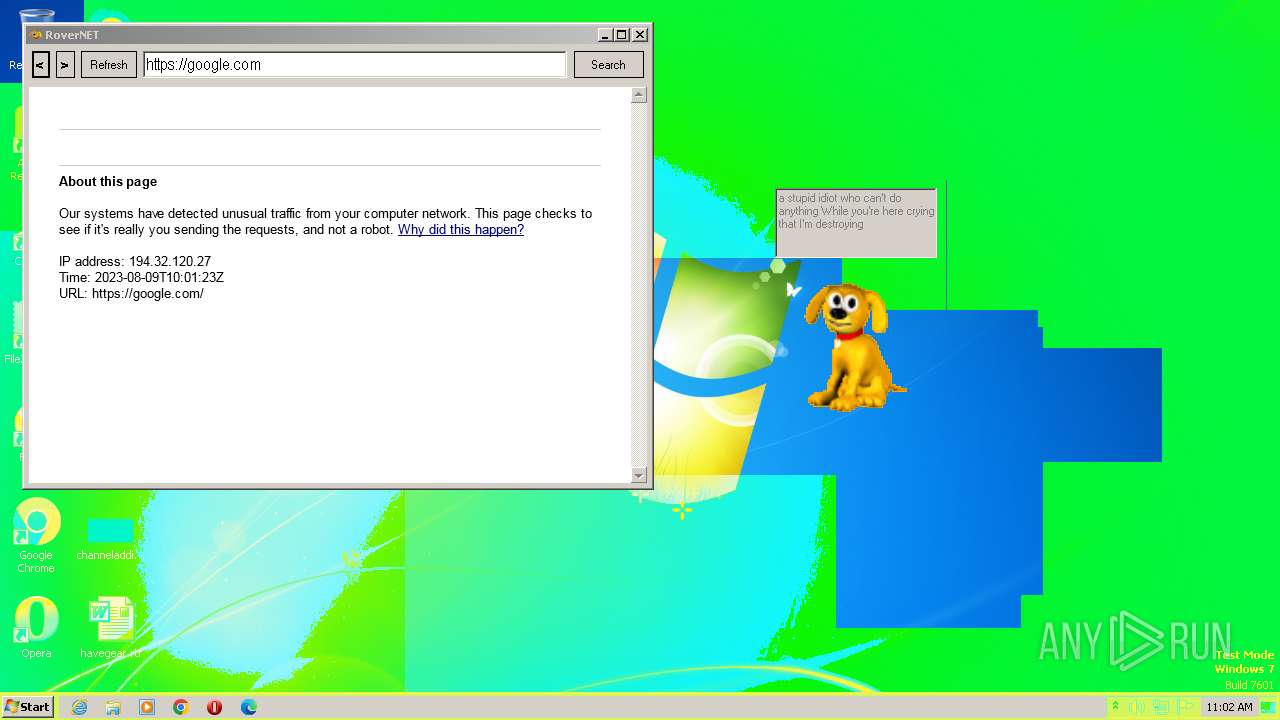
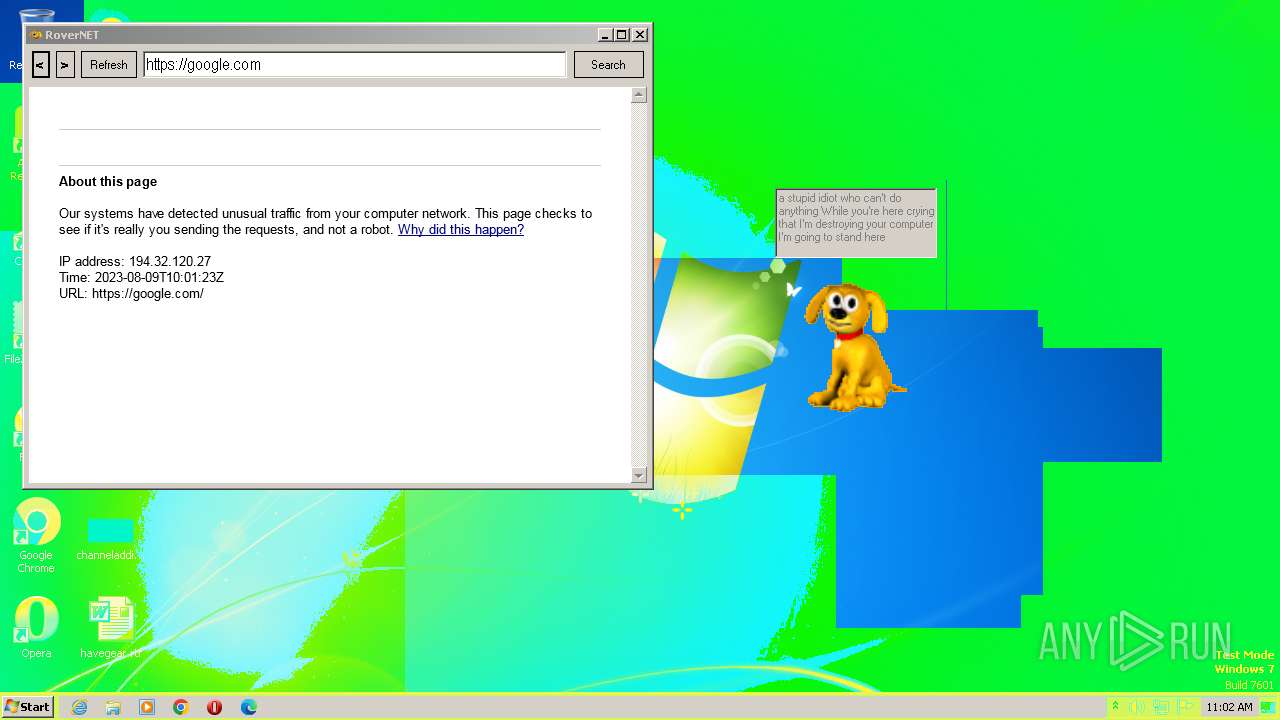
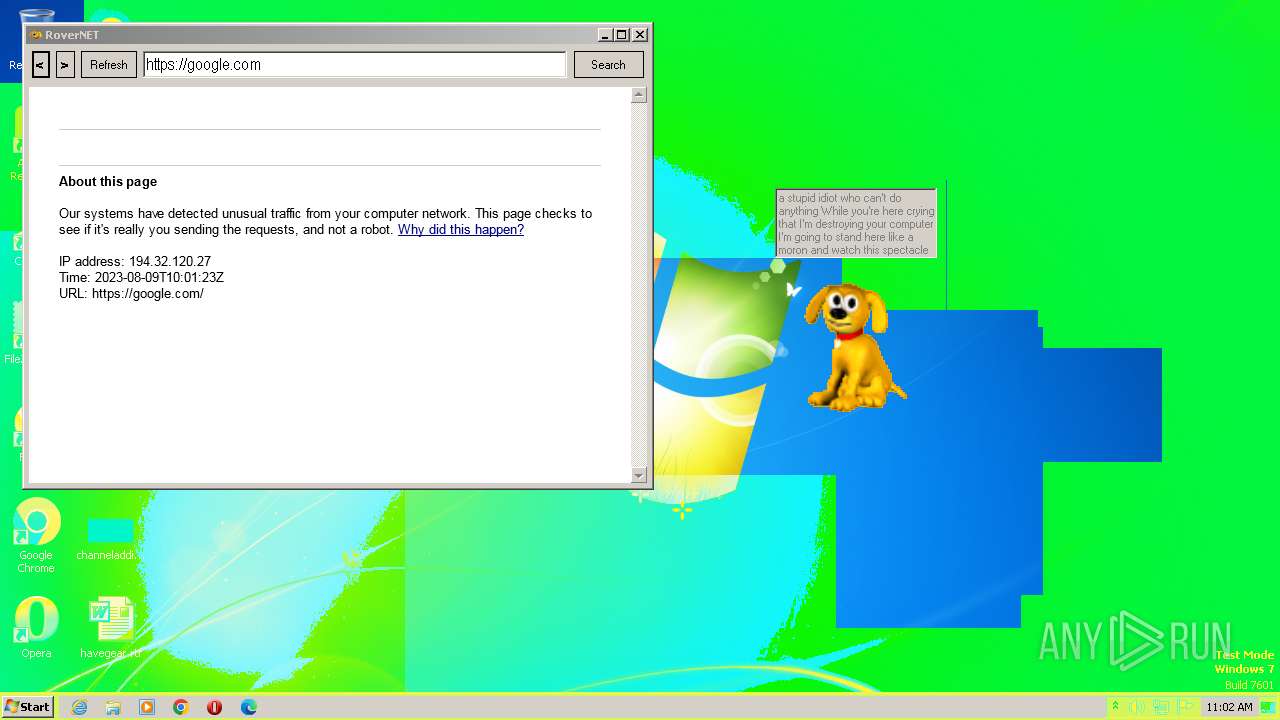
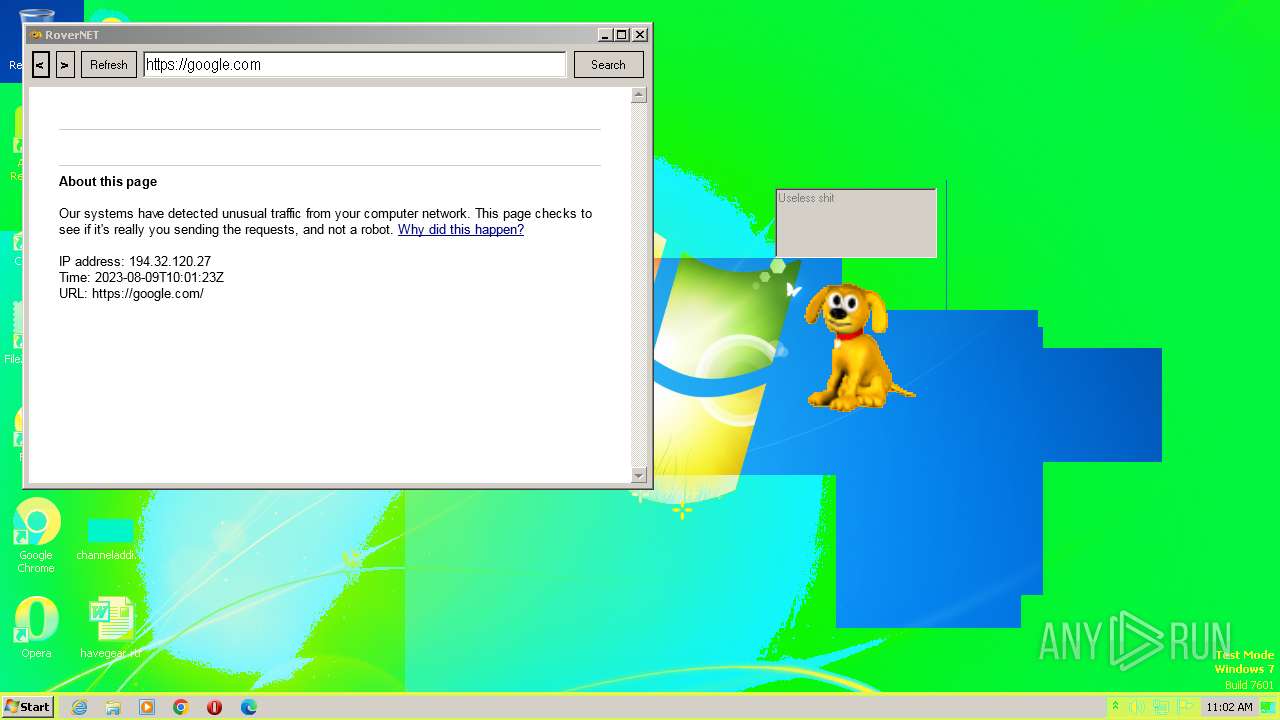
| FileDescription: | Rover The Desktop Assistant (beta version) |
| CompanyName: | - |
| Comments: | Desktop Assistant |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 1.0.0.0 |
| FileVersionNumber: | 1.0.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 5 |
| ImageVersion: | - |
| OSVersion: | 5 |
| EntryPoint: | 0xcd2f |
| UninitializedDataSize: | - |
| InitializedDataSize: | 5268992 |
| CodeSize: | 104448 |
| LinkerVersion: | 9 |
| PEType: | PE32 |
| ImageFileCharacteristics: | No relocs, Executable, Large address aware, 32-bit |
| TimeStamp: | 2012:07:13 22:47:16+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 13-Jul-2012 22:47:16 |
| Debug artifacts: | |
| Comments: | Desktop Assistant |
| CompanyName: | - |
| FileDescription: | Rover The Desktop Assistant (beta version) |
| FileVersion: | 1.0.0.0 |
| InternalName: | Rover.exe |
| LegalCopyright: | Copyright © 2023 |
| LegalTrademarks: | - |
| OriginalFilename: | Rover.exe |
| ProductName: | Created by CYBER SOLDIER aka Clutter |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 13-Jul-2012 22:47:16 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00019718 | 0x00019800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.74854 |
.rdata | 0x0001B000 | 0x00006DB4 | 0x00006E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.44296 |
.data | 0x00022000 | 0x000030C0 | 0x00001600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.26259 |
.rsrc | 0x00026000 | 0x004FE05C | 0x004FE200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.9792 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.0261 | 3407 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
2 | 2.10277 | 67624 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 2.36504 | 16936 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 2.51219 | 9640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 2.67365 | 4264 | Latin 1 / Western European | UNKNOWN | RT_ICON |
6 | 3.09109 | 1128 | Latin 1 / Western European | UNKNOWN | RT_ICON |
32512 | 2.79908 | 90 | Latin 1 / Western European | UNKNOWN | RT_GROUP_ICON |
__ | 7.99996 | 5121056 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
~ | 4.9375 | 32 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
Imports
KERNEL32.dll |
OLEAUT32.dll |
ole32.dll |
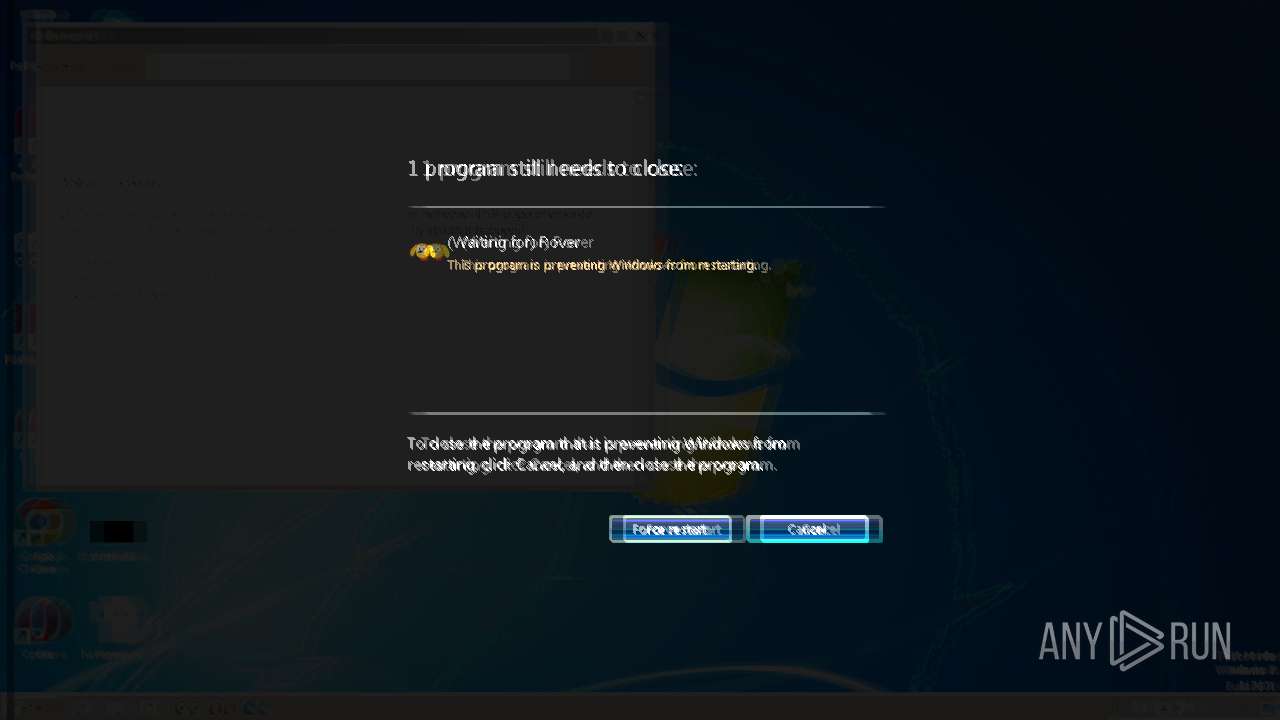
Total processes
42
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 124 | "C:\Users\admin\AppData\Local\Temp\Rover.exe" | C:\Users\admin\AppData\Local\Temp\Rover.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Rover The Desktop Assistant (beta version) Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
| 692 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
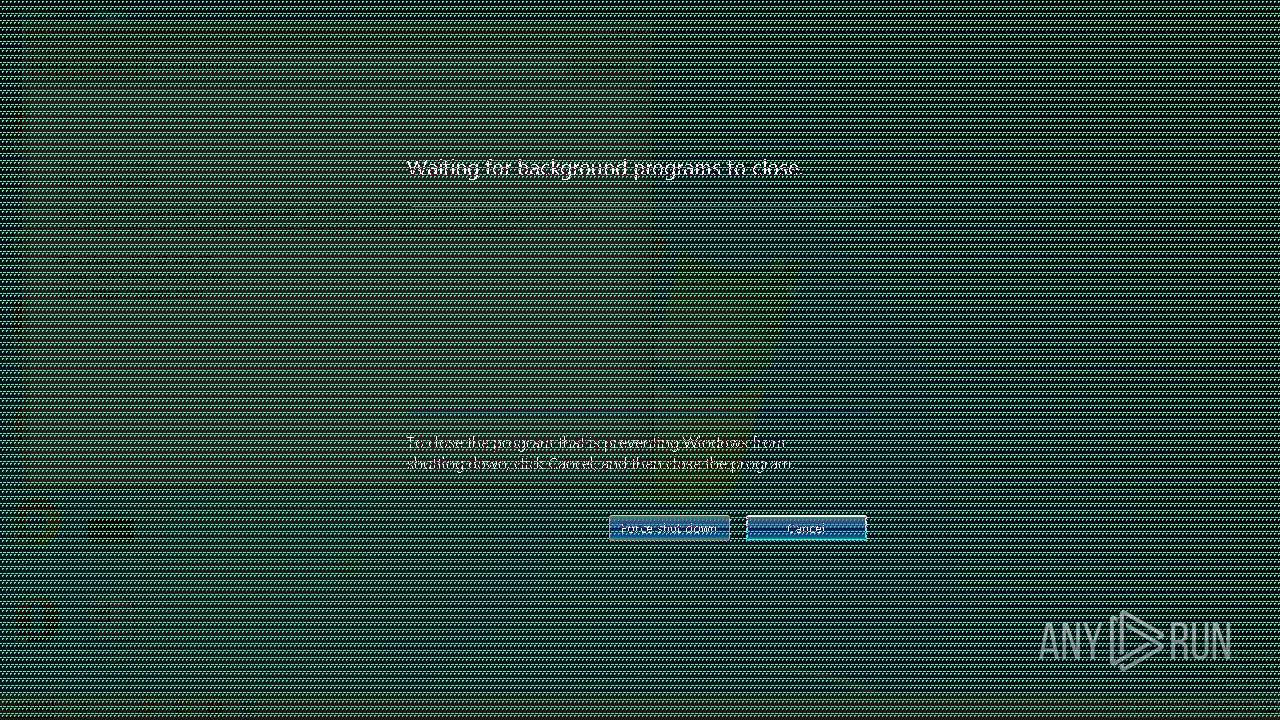
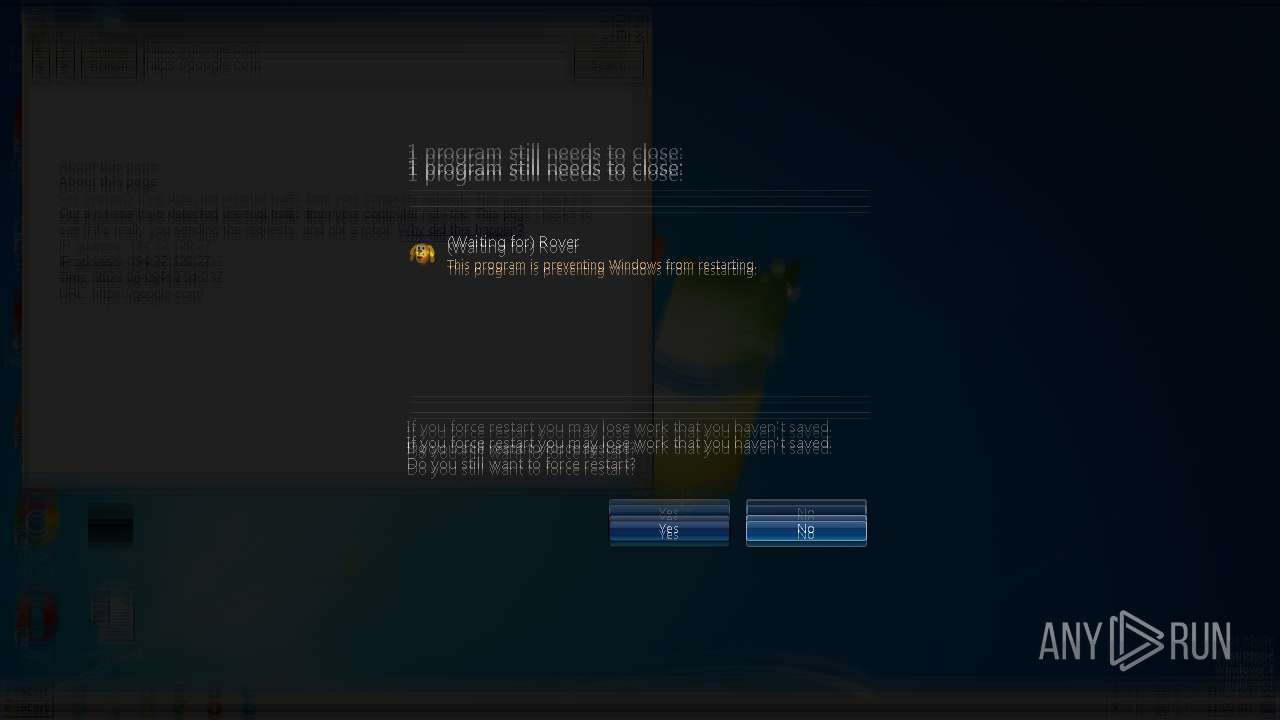
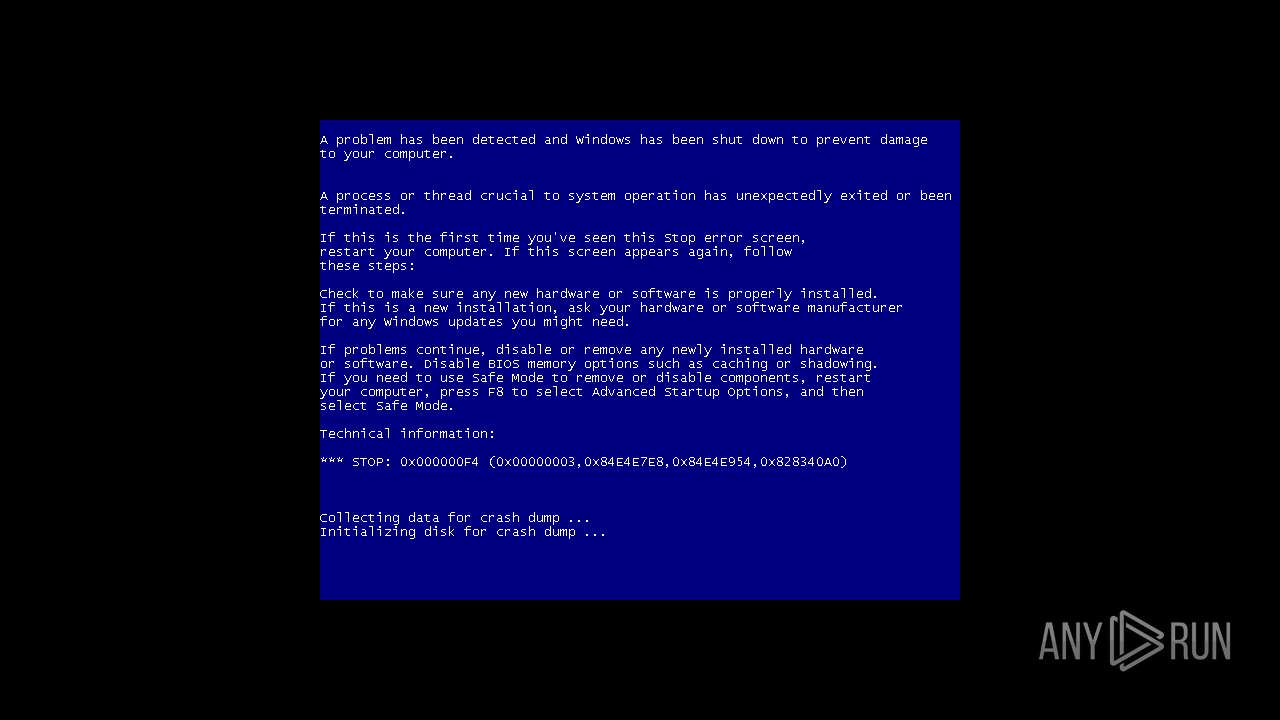
| 2696 | "C:\Users\admin\AppData\Local\Temp\Rover.exe" | C:\Users\admin\AppData\Local\Temp\Rover.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Rover The Desktop Assistant (beta version) Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
5 841
Read events
5 796
Write events
42
Delete events
3
Modification events
| (PID) Process: | (692) wmpnscfg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Media Player NSS\3.0\Events\{3741E1B0-6F0B-4B4E-80AC-754D44763F41}\{97251834-6E8F-4C92-A222-DDE5731DCBE9} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (692) wmpnscfg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Media Player NSS\3.0\Events\{3741E1B0-6F0B-4B4E-80AC-754D44763F41} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (692) wmpnscfg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\MediaPlayer\Health\{6B8F0E60-EABB-4D15-B9F1-181AA21BB518} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (2696) Rover.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | FilterAdministratorToken |
Value: 0 | |||
| (PID) Process: | (2696) Rover.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | EnableLUA |
Value: 1 | |||
| (PID) Process: | (2696) Rover.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon |
| Operation: | write | Name: | Shell |
Value: explorer.exe | |||
| (PID) Process: | (2696) Rover.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Speech\CurrentUserLexicon |
| Operation: | write | Name: | CLSID |
Value: {C9E37C15-DF92-4727-85D6-72E5EEB6995A} | |||
| (PID) Process: | (2696) Rover.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2696) Rover.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2696) Rover.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
Executable files
1
Suspicious files
26
Text files
1 359
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2696 | Rover.exe | C:\Program Files\rover\Ashamed\Ashamed.008.png | image | |
MD5:B3F53C1DC286776CF34641C7B8256DFA | SHA256:43C42124AE7D35D7ACDEAFDBB16A890B4667B4089920810FBFD1CC19AB9AEFCA | |||
| 2696 | Rover.exe | C:\Program Files\rover\Ashamed\Ashamed.005.png | image | |
MD5:4568226931D995534E249F402AF4825A | SHA256:C1EF483BBF4DA565D3445A48A81B77B2DB2257AFD39C9B17B67E2E0277CFA24B | |||
| 2696 | Rover.exe | C:\Program Files\rover\Ashamed\Ashamed.002.png | image | |
MD5:A46F286AE95E280424E0C6D8F1213173 | SHA256:49D69A5F0F84D89A458BF7E8FEA059F54F45ACE360D74DE22FE45ECEEC87BA16 | |||
| 2696 | Rover.exe | C:\Program Files\rover\Ashamed\Ashamed.007.png | image | |
MD5:72685D7C7CC4C77E20618264B4150331 | SHA256:B67E7613906632BC3F8AEC7541F2D99FB73C9406183699F9EAB3D97952AEB81B | |||
| 2696 | Rover.exe | C:\Program Files\rover\Ashamed\Ashamed.003.png | image | |
MD5:CF62C5107B66367690832F72854BFFAE | SHA256:075B30FC4D1997D1826148D9A98DBE3A6B06EA53862FD2C453F5D6AD8C288E62 | |||
| 2696 | Rover.exe | C:\Program Files\rover\Ashamed\Ashamed.014.png | image | |
MD5:BD65E98C40A77188E231F2E89B224A7D | SHA256:8A22BDC7116DE7970BB06E2124B5336CF3BC488310E4D796021D01CF378A4A1D | |||
| 2696 | Rover.exe | C:\Program Files\rover\Ashamed\Ashamed.004.png | image | |
MD5:5F737B5A980C89BC41DBD33559902D29 | SHA256:EC57C51CDAA4132218B00935F14BA1AEB0E9FA8AAC322C840F8C55B58D0D66EA | |||
| 2696 | Rover.exe | C:\Program Files\rover\Ashamed\Ashamed.001.png | image | |
MD5:AA84C45293EF08A7A64DB8F5D12B5DD0 | SHA256:8178152F670855DD0CB4412494C80B854A164EE02922A112DA4266AF53F9195D | |||
| 2696 | Rover.exe | C:\Program Files\rover\Ashamed\Ashamed.006.png | image | |
MD5:3D8699EC82F73E244B078D9F16BDAC5C | SHA256:B1F9AE224B7B7988E6FF76C9A951609BA88290B79BC295F015186495E693479F | |||
| 2696 | Rover.exe | C:\Program Files\rover\Ashamed\Ashamed.010.png | image | |
MD5:CB14927415ADCAC79057F0D907A19B83 | SHA256:DC286D3373C6531C7F724FDE5AB241D639B19234AADA887C3D36CA0EF7E4AAAB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
7
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2696 | Rover.exe | GET | 200 | 142.250.181.227:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEDo0jldRIDwhENILOduC1D0%3D | US | binary | 471 b | whitelisted |
2696 | Rover.exe | GET | 200 | 142.250.181.227:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEBsV%2Bpyhb5SrCUFdcBMI3OE%3D | US | binary | 471 b | whitelisted |
2696 | Rover.exe | GET | 200 | 8.248.115.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?cda5b051b177fc11 | US | compressed | 4.70 Kb | whitelisted |
2696 | Rover.exe | GET | 200 | 142.250.181.227:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEByt3bC56JDRCcVdVRDlZLM%3D | US | der | 471 b | whitelisted |
2696 | Rover.exe | GET | 200 | 142.250.181.227:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | binary | 1.41 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3284 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
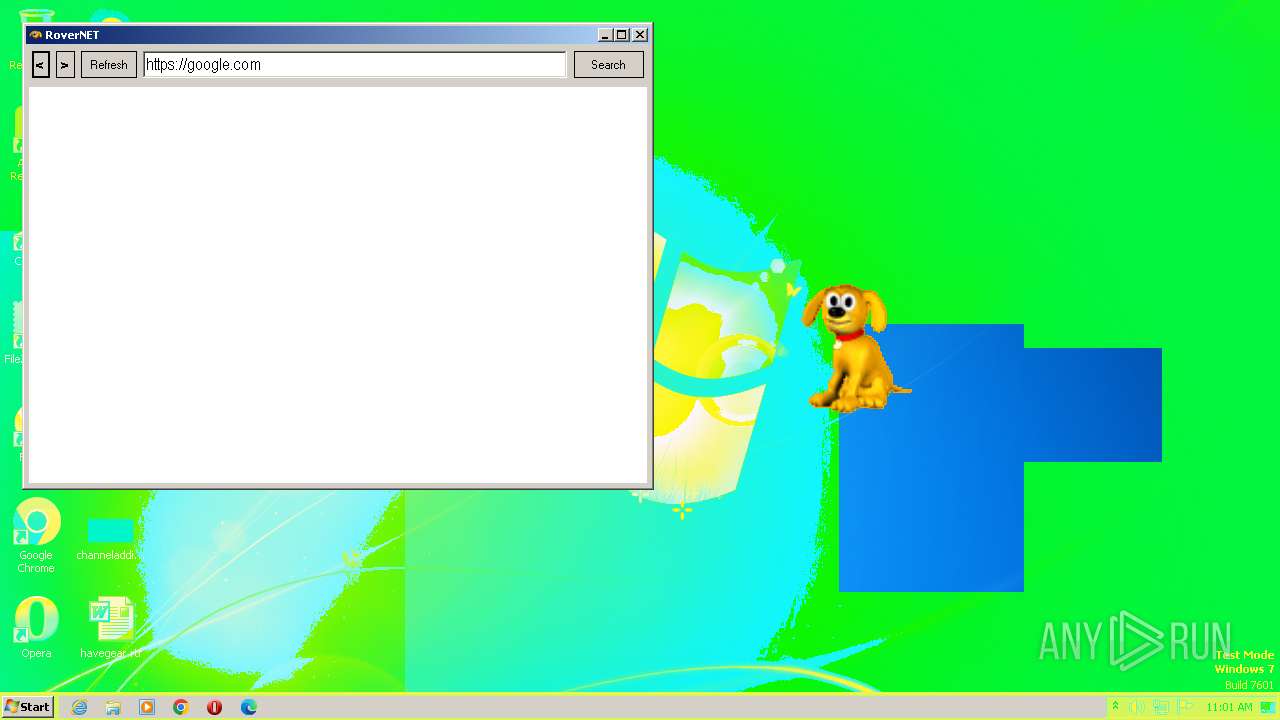
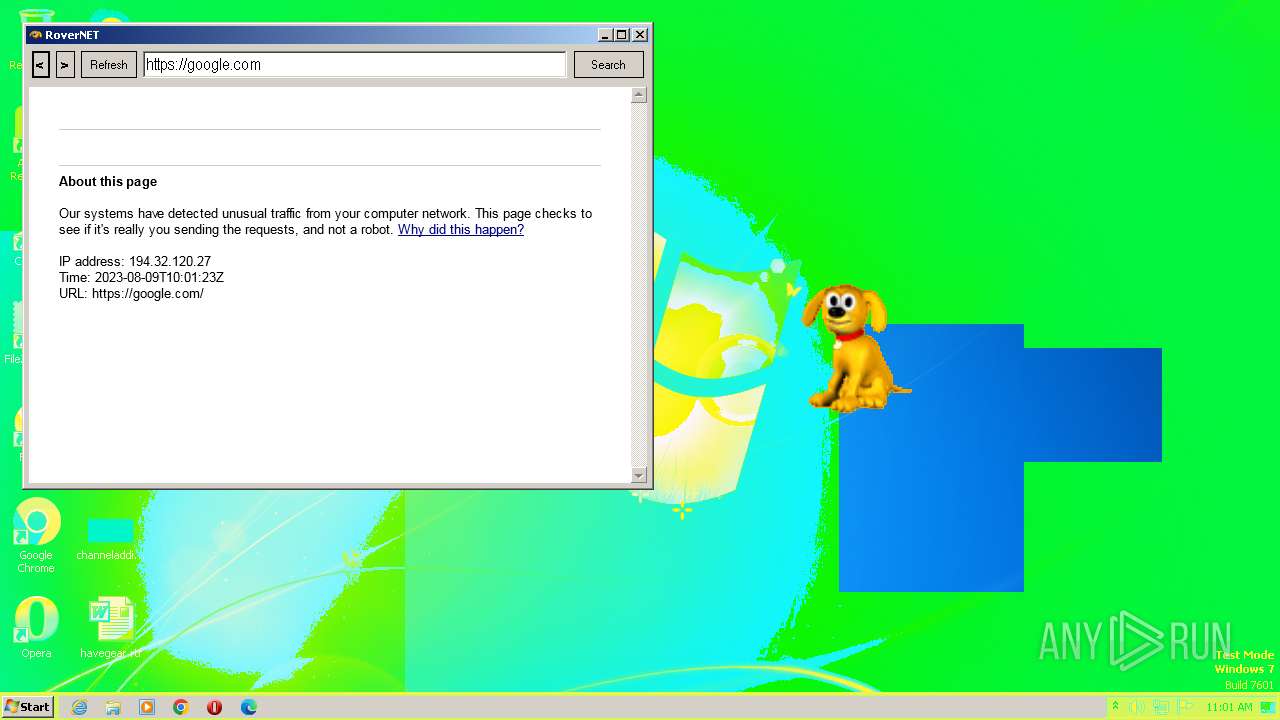
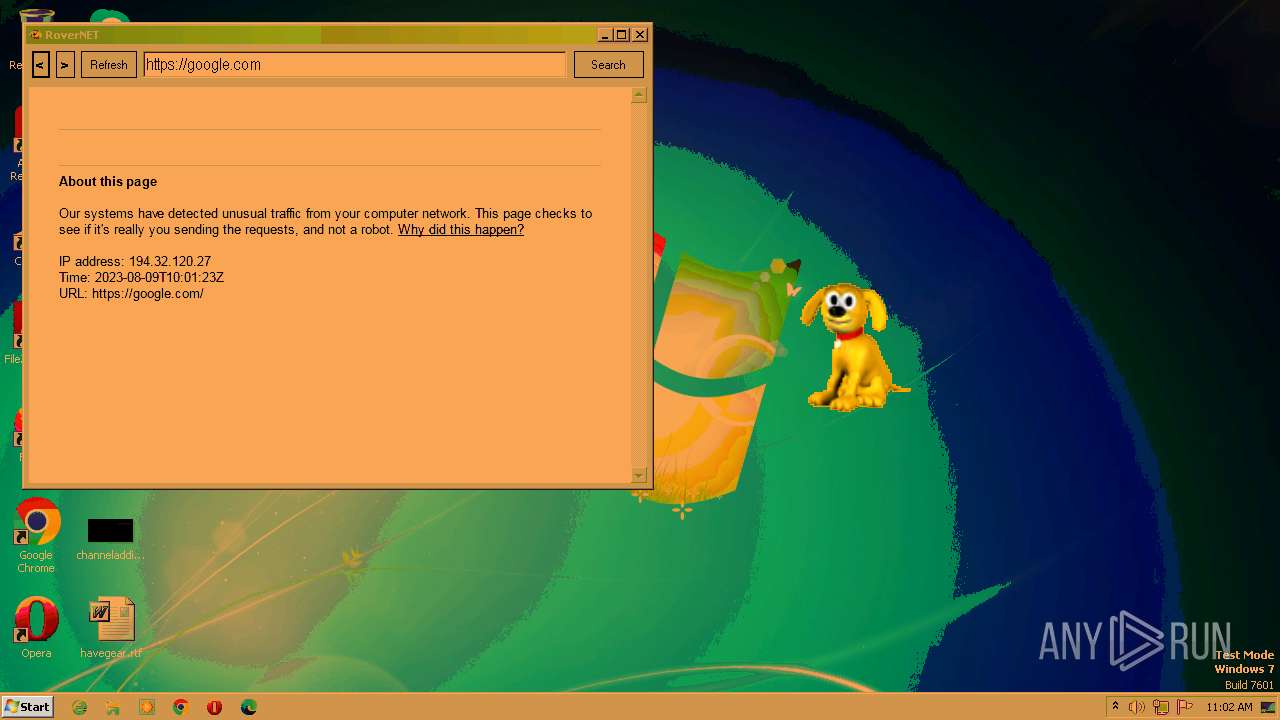
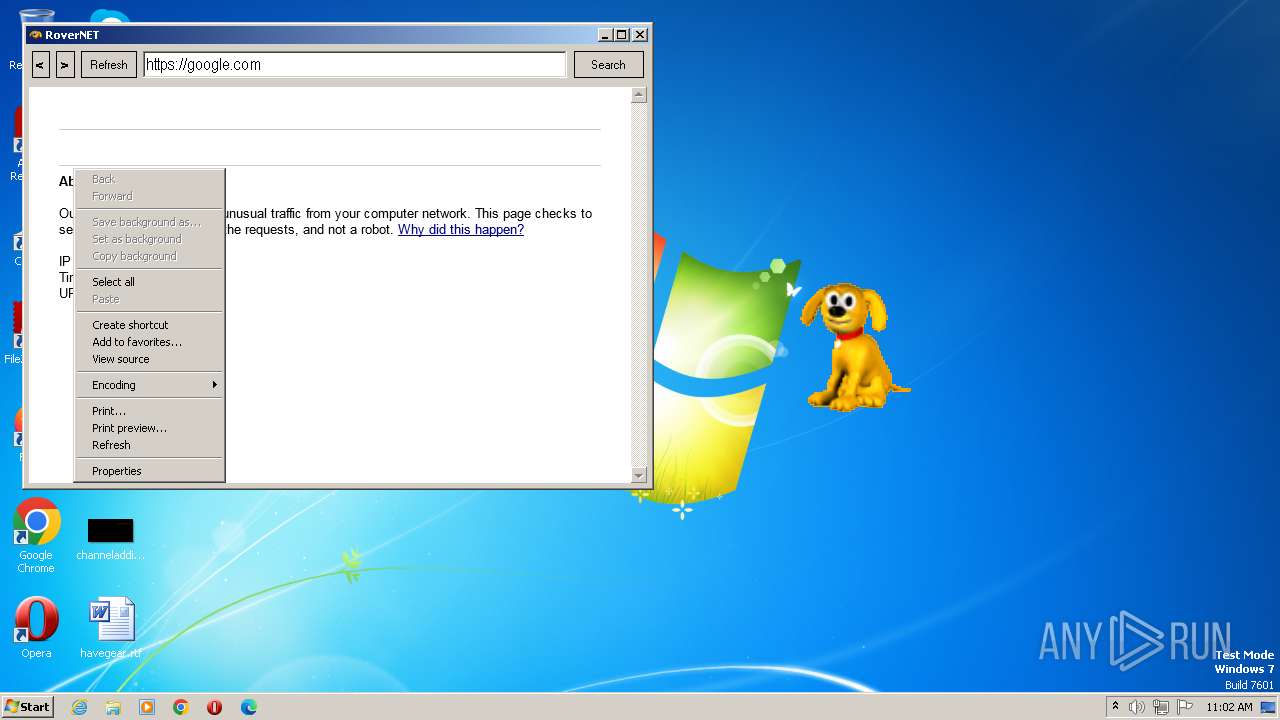
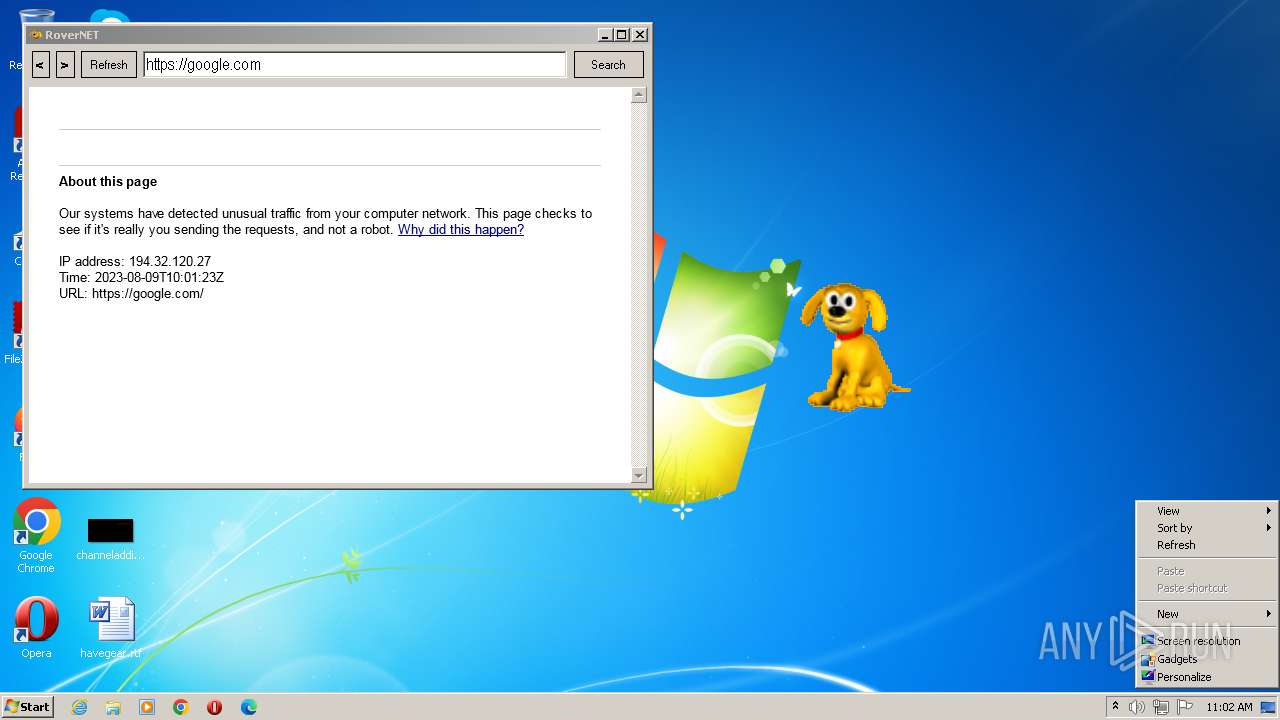
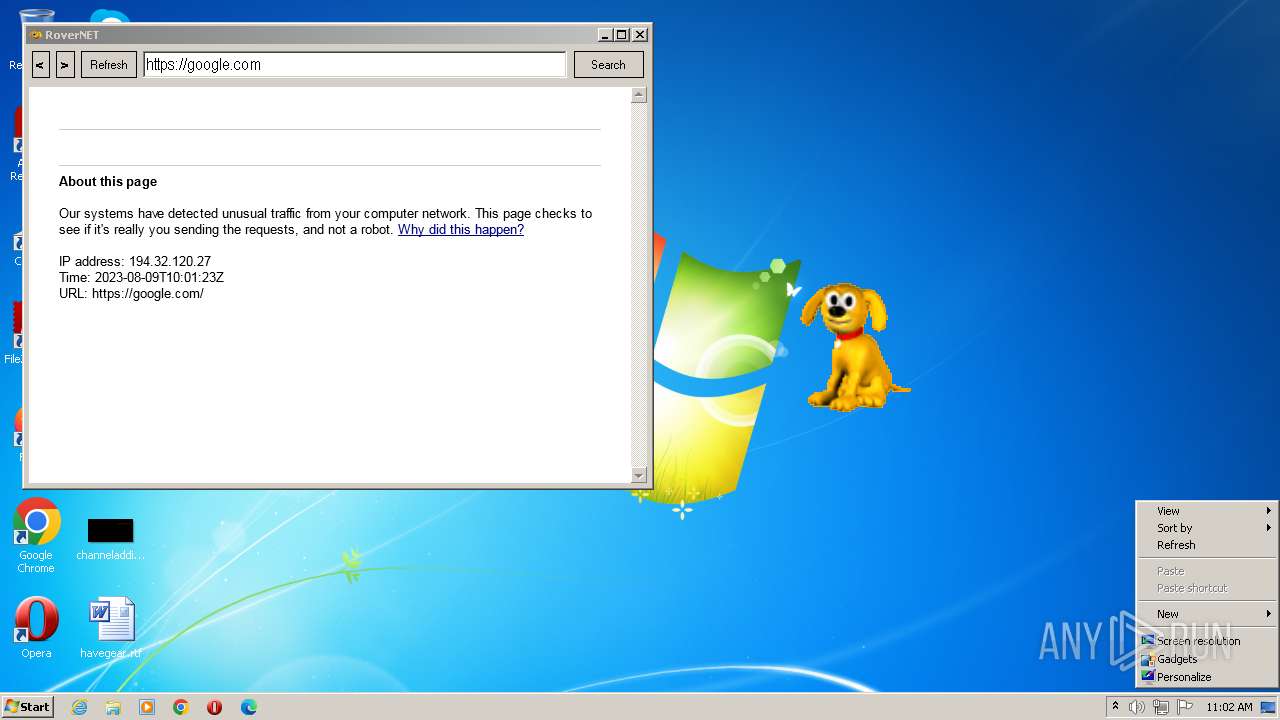
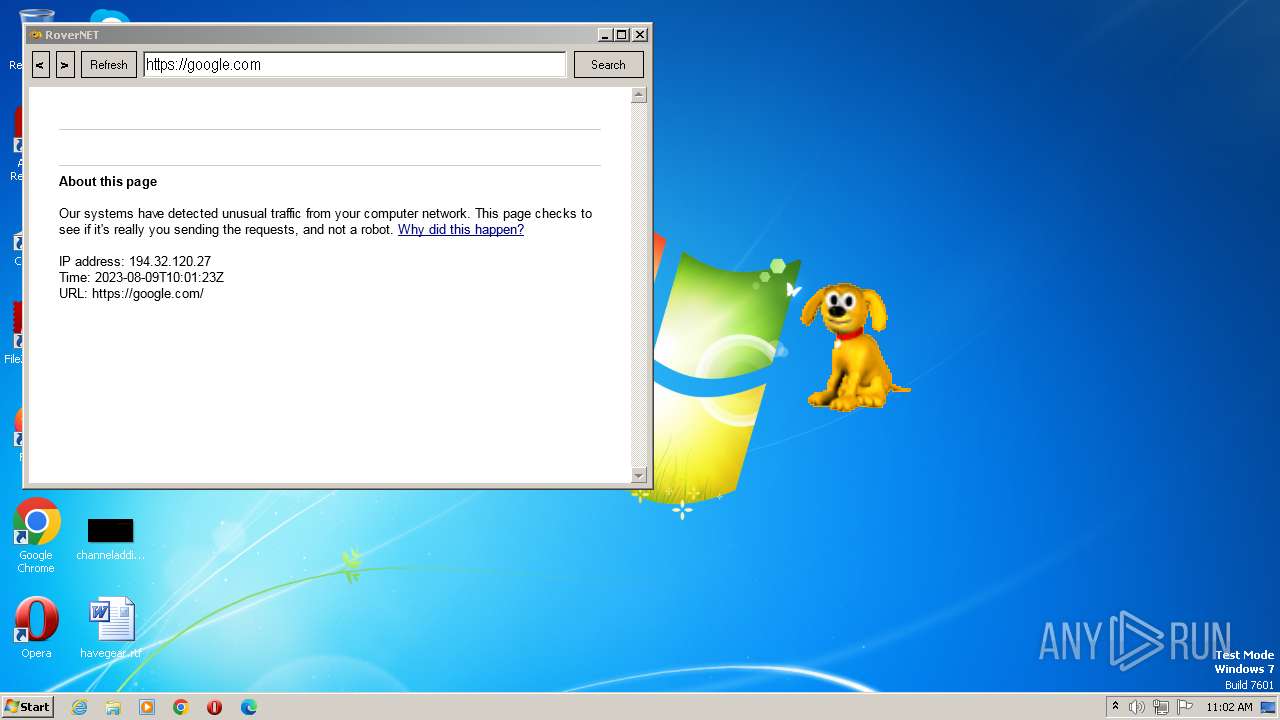
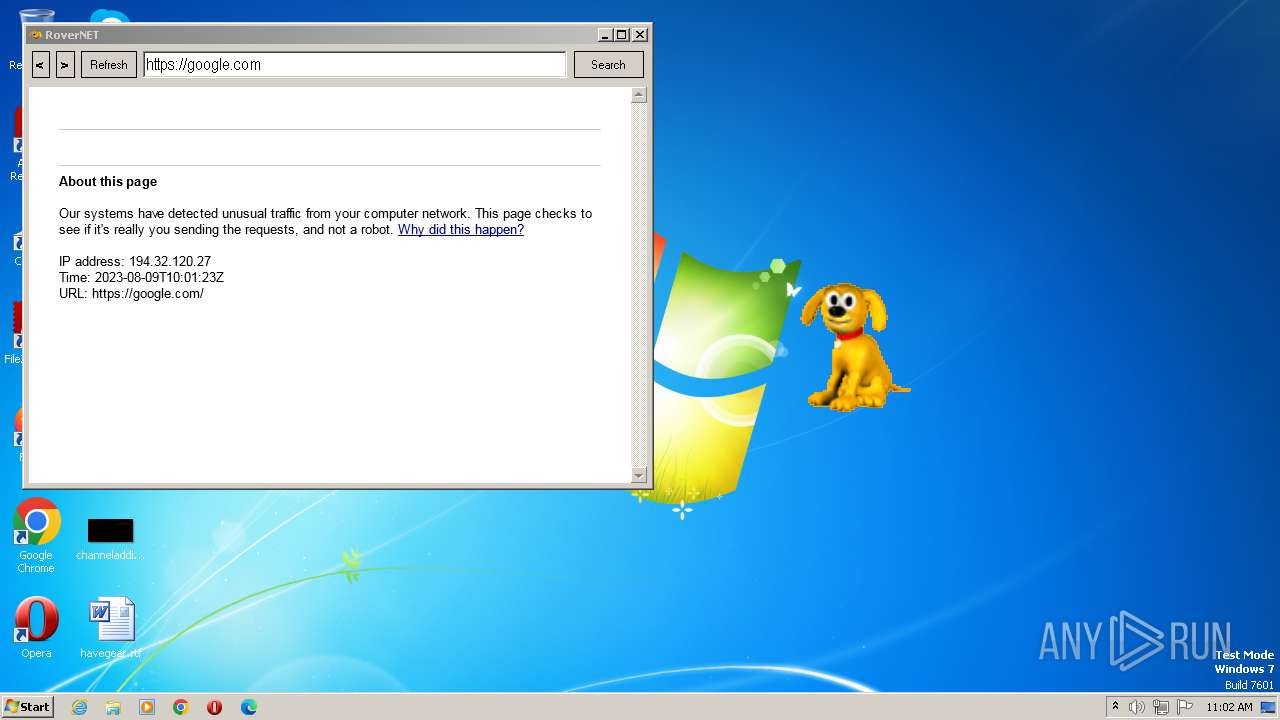
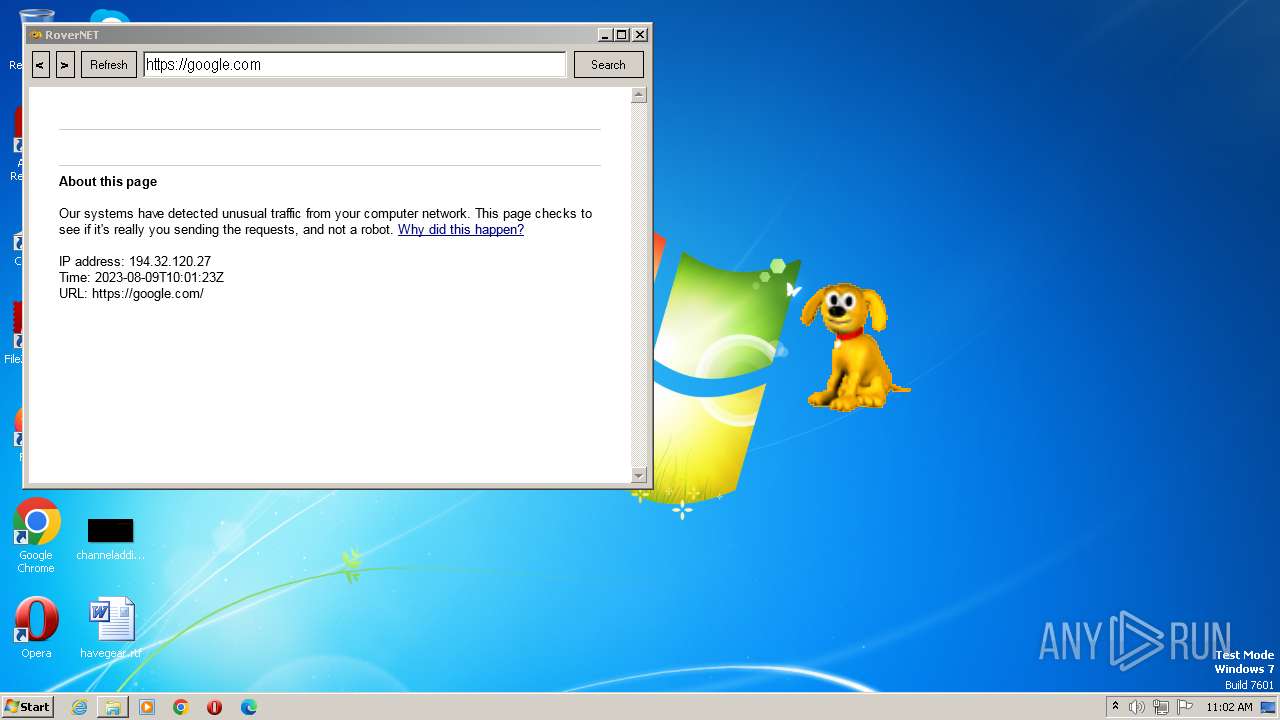
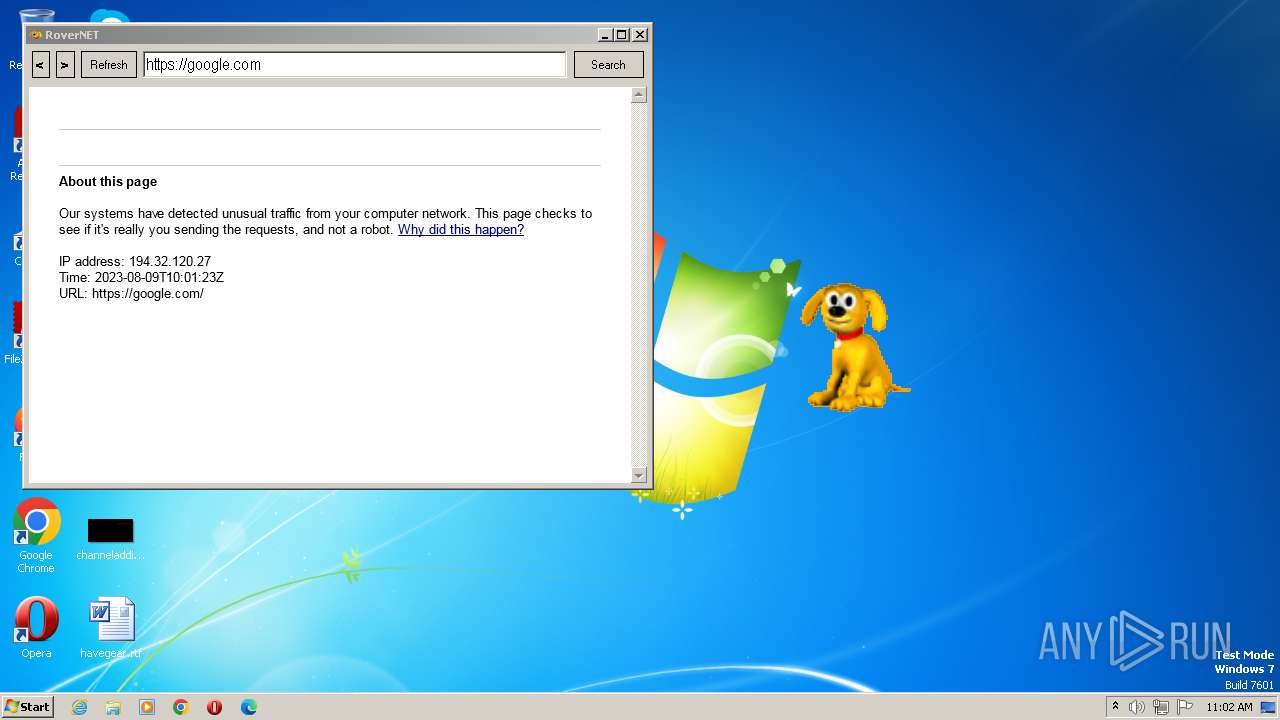
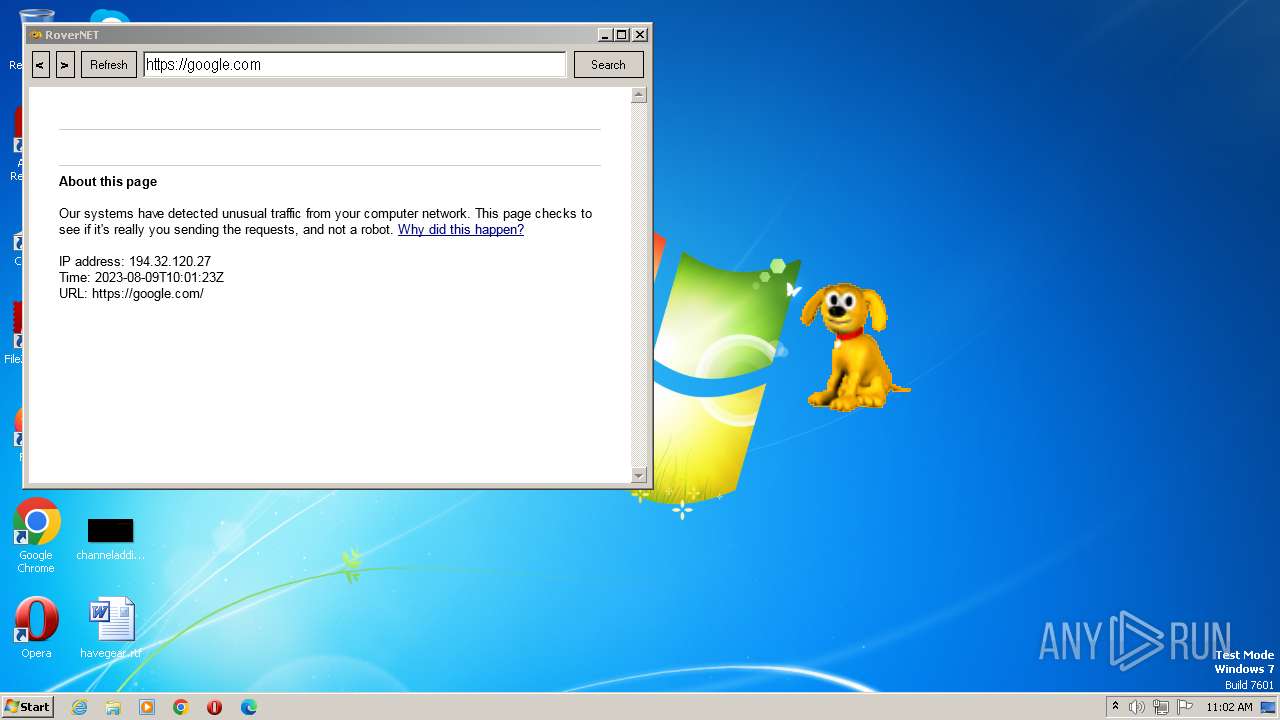
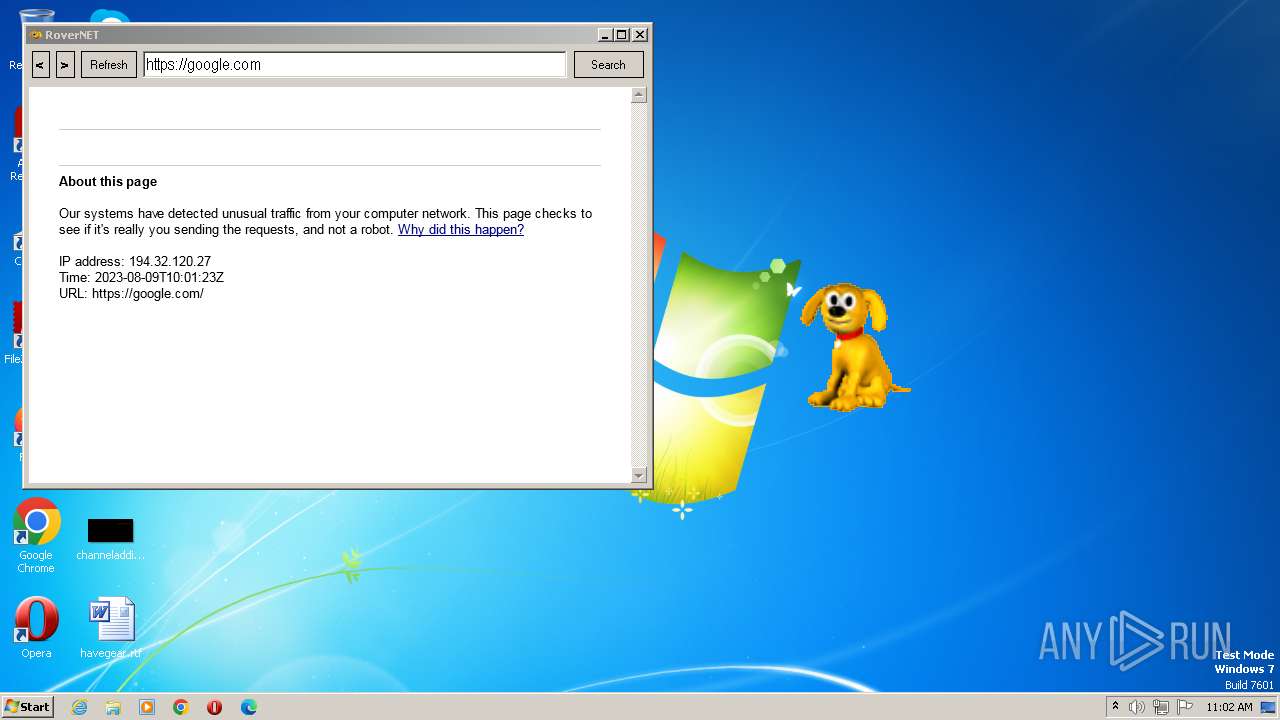
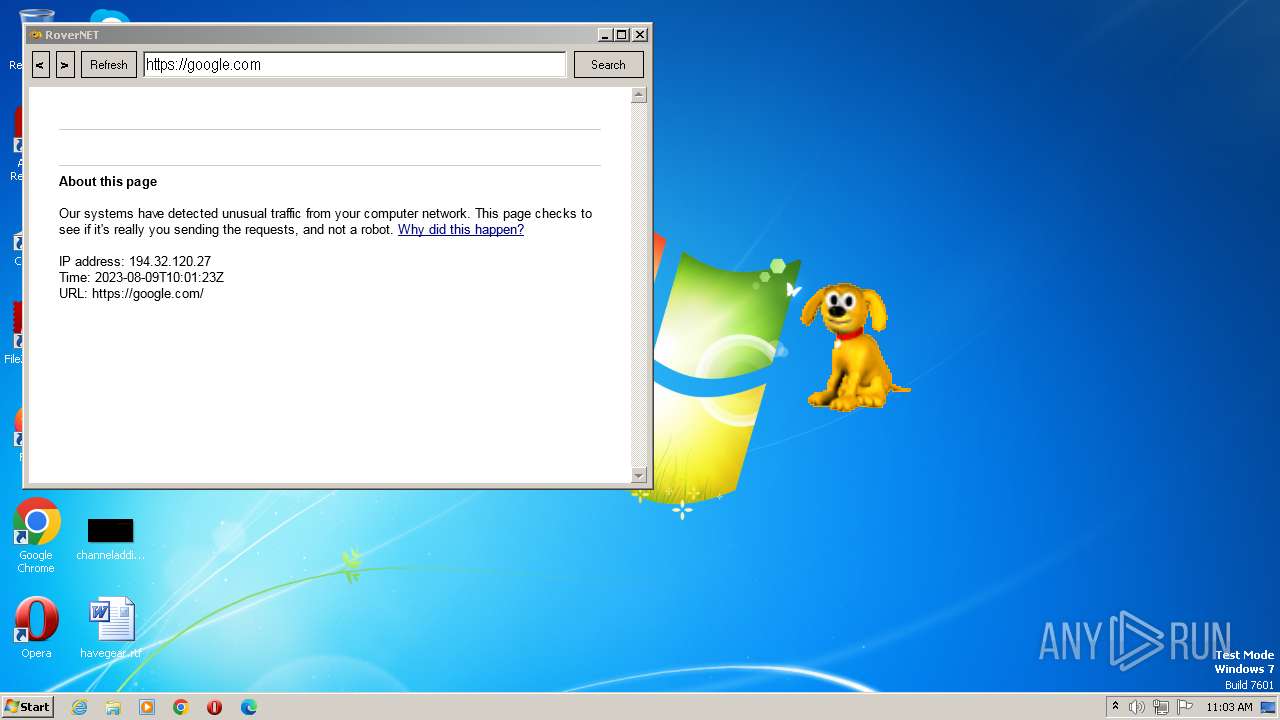
2696 | Rover.exe | 142.250.186.46:443 | google.com | GOOGLE | US | whitelisted |
2696 | Rover.exe | 8.248.115.254:80 | ctldl.windowsupdate.com | LEVEL3 | US | suspicious |
2696 | Rover.exe | 142.250.185.164:443 | www.google.com | GOOGLE | US | whitelisted |
2696 | Rover.exe | 142.250.181.227:80 | ocsp.pki.goog | GOOGLE | US | whitelisted |
2696 | Rover.exe | 216.58.206.35:443 | www.gstatic.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
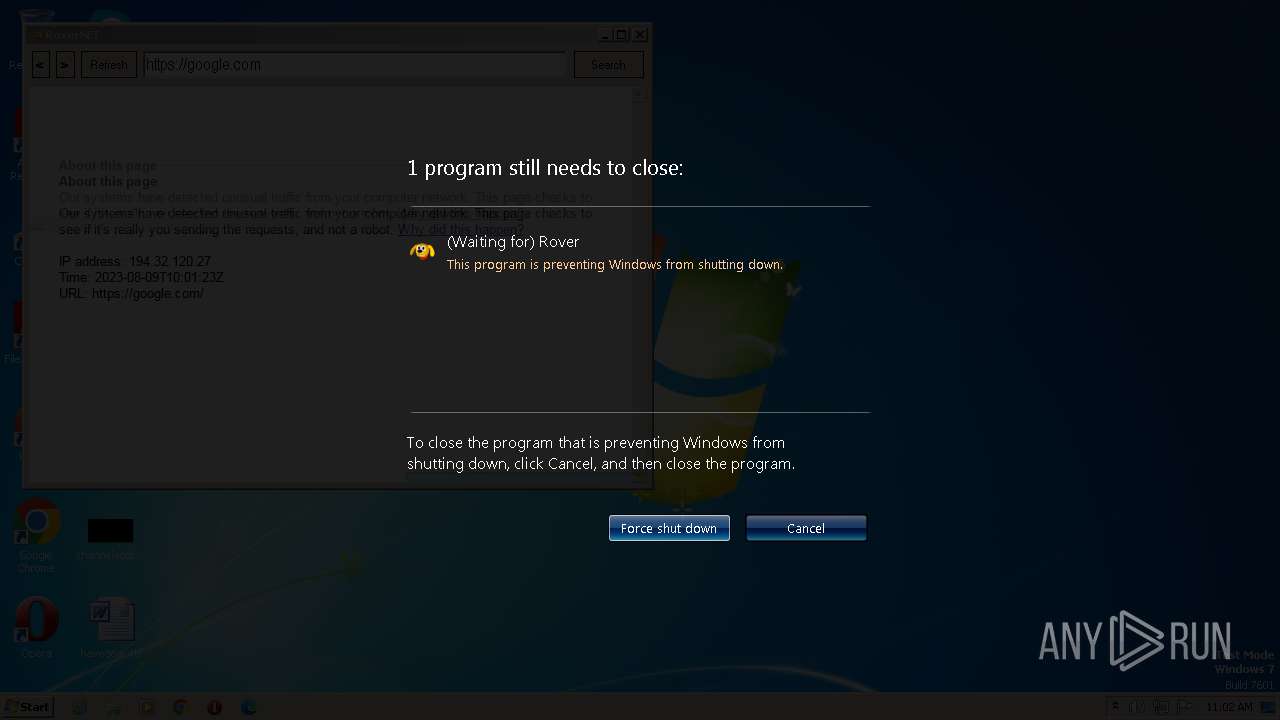
google.com |
| malicious |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
www.google.com |
| malicious |
www.gstatic.com |
| whitelisted |