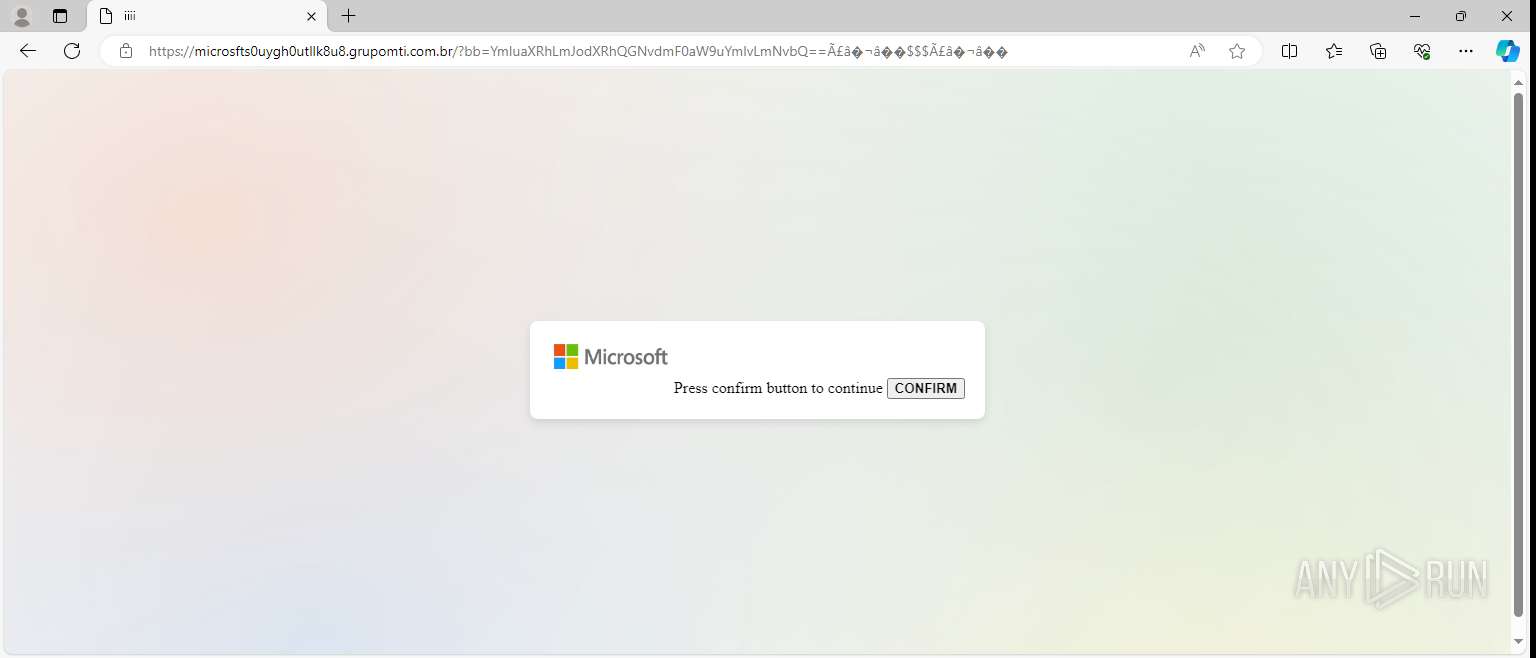
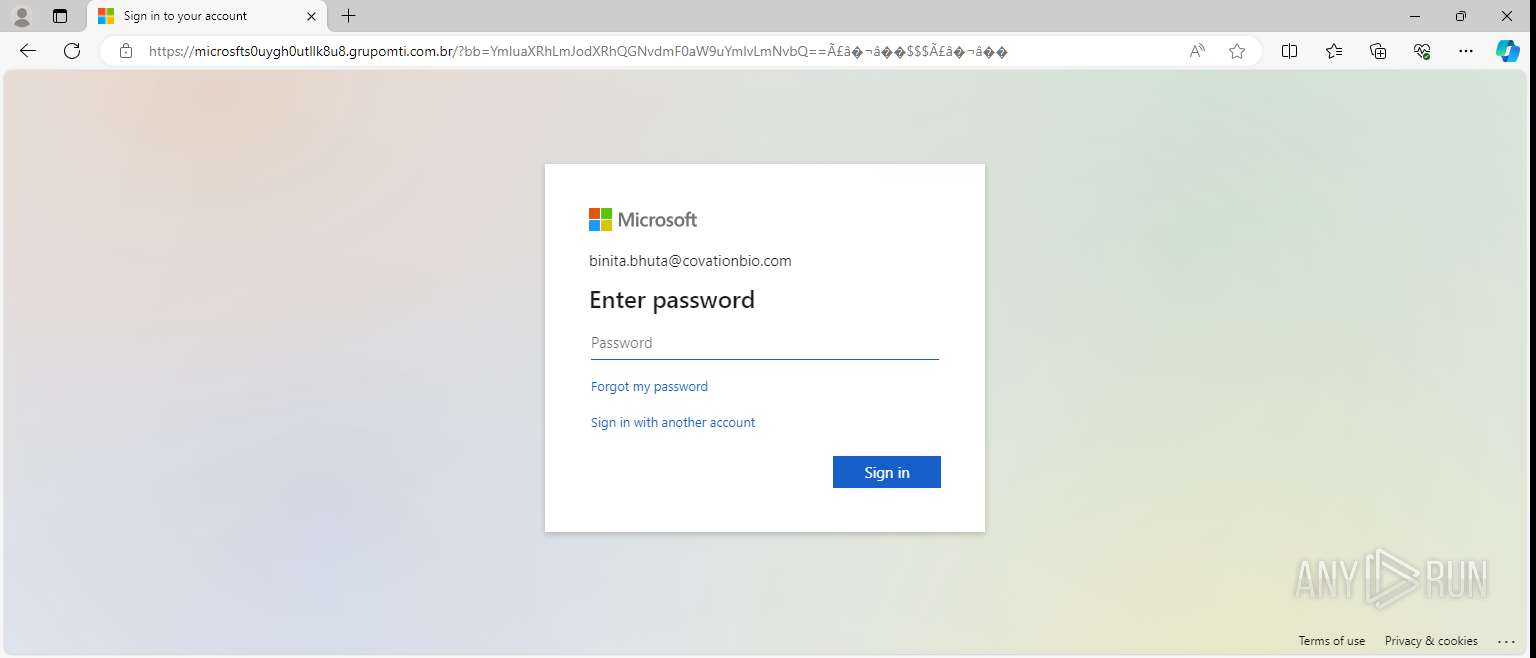
| URL: | https://google.co.ve/url?q=ai65p8rJLi6z73yh&rct=tTPvvq6xRyj7Y00xDjnlx9kIjusucT&sa=t&url=amp%2Fs%2Fthelatewire.com%2F8yoya%2F7x1sp2ytogxundo%C3%A3%E2%82%AC%E2%80%9A%C3%A3%E2%82%AC%E2%80%9A%2FYmluaXRhLmJodXRhQGNvdmF0aW9uYmlvLmNvbQ%3D%3D%C3%A3%E2%82%AC%E2%80%9A%24%24%24%C3%A3%E2%82%AC%E2%80%9A |
| Full analysis: | https://app.any.run/tasks/510caf79-1695-4dfa-97fe-684ec5231fd1 |
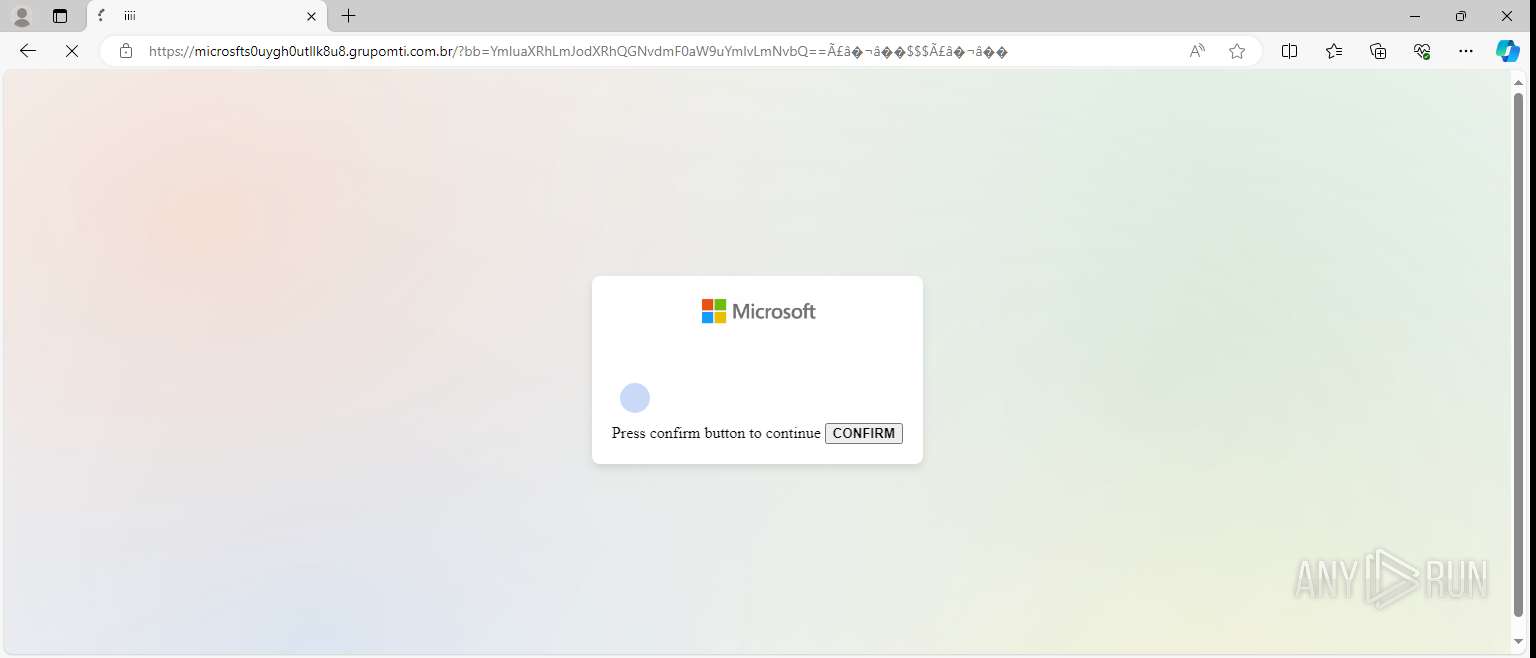
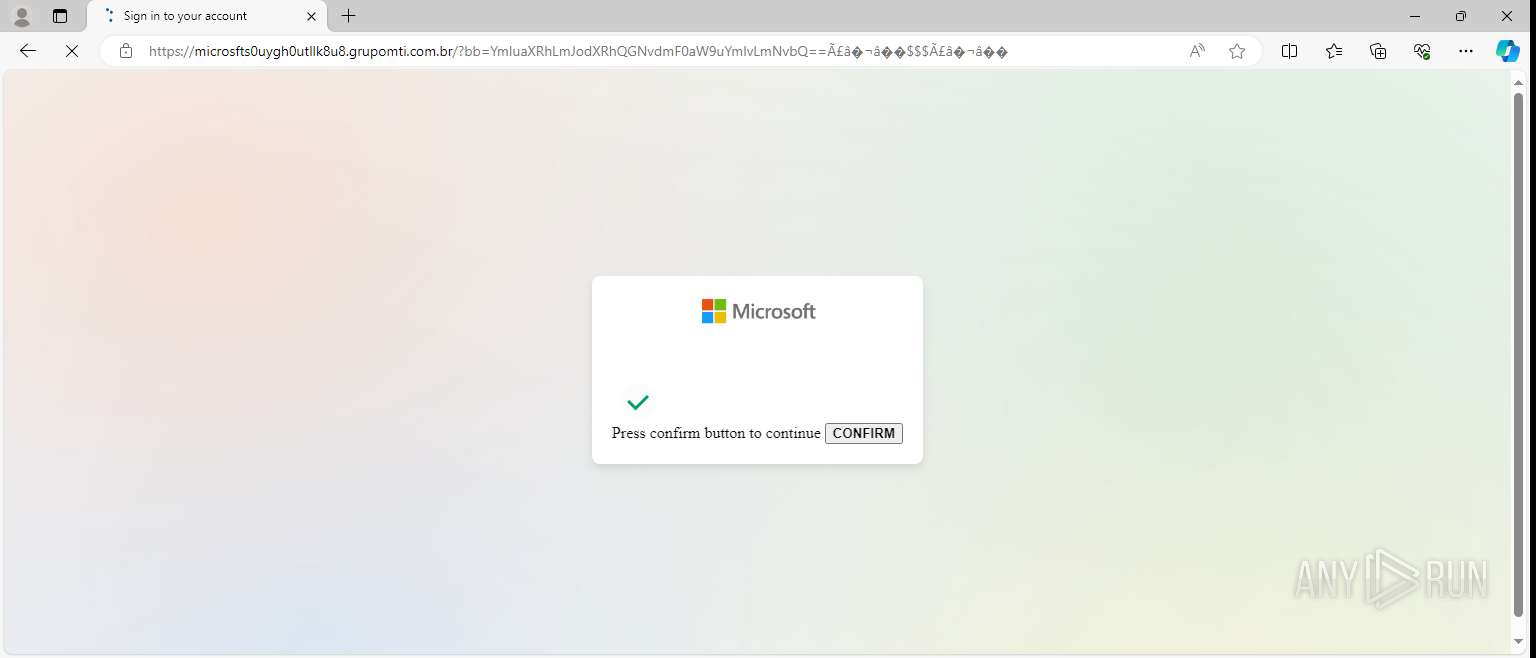
| Verdict: | Malicious activity |
| Analysis date: | December 14, 2024, 07:29:39 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 34D65AD30F2EC239219BC791C5F921AD |
| SHA1: | F52D40F807ABD5170002B7FD6223C47F5FA89691 |
| SHA256: | 862D4386476C765D3D8760989DCC778F29E1D4805EFAAC2F169FCD782633675B |
| SSDEEP: | 6:2LuJLQkypATBRtMqf9hDRVn1KKzAvAgIq+AvAgIq/IpXTAeHdAvAgIq1B9BxAvAm:2yjJjfDkcVxq+Vxqc1dVxq1fVxqV |
MALICIOUS
PHISHING has been detected (SURICATA)
- msedge.exe (PID: 4792)
SUSPICIOUS
No suspicious indicators.INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
141
Monitored processes
1
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 4792 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=2604 --field-trial-handle=2320,i,16194277592197507296,15814343983252007256,262144 --variations-seed-version /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 | ||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
22
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4792 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Cache\Cache_Data\f_0000bf | compressed | |
MD5:F592CE299393AAACEA4710F789F365A9 | SHA256:94AB3D6EF10560E48CAF885DF2D1AEA3920146F53BDF2C8A79123A47B659892F | |||
| 4792 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Network\TransportSecurity~RF2b5e99.TMP | binary | |
MD5:15D26FA4E16467BE658F42074AC0DBAA | SHA256:D287407BD901A32E3F38F4392984507184D596C3694FAA69DD0B2E68F9F3A8FE | |||
| 4792 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Network\2b64e7e3-561a-4f9f-91bb-6ca7387b9efc.tmp | binary | |
MD5:ED74D0CC3CAB53CA501F3CD6C50FAA1A | SHA256:331BB0DA5A3BE7843A14503DA9547E7309F3631916C6112882FF36D75025E7EE | |||
| 4792 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Cache\Cache_Data\f_0000bd | compressed | |
MD5:69F909D3BA8C6B993DD001B8B9F54F55 | SHA256:5DEB7C0DFBFFCA6439CADD009CD4F57AF7C3E8B6AD9B1467DB95A1B0DC262B0C | |||
| 4792 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Cache\Cache_Data\f_0000bb | compressed | |
MD5:1650B56973EBF85AC18ABB4F7BE0C7F3 | SHA256:F5EDE89176318D6F0FDEE49FE92DF96E90D3DD3C621F14C6F6C475029BC4818E | |||
| 4792 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Network\Network Persistent State~RF2c19ac.TMP | binary | |
MD5:564B2A43E887555421867881A85500CD | SHA256:6C35DC3F00E55F522EC36B6BBC441CE8646B0A92D4427046BE695A102D61B67E | |||
| 4792 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Network\57aba56f-db37-44c1-9b0c-55672bd78fa3.tmp | binary | |
MD5:BF57084E05BEFB8F3E54E75E97198A30 | SHA256:A02108D9982E5B29CA3ABC1105C6897E5F5720BE1BB2D72172F45B4B745FD2CB | |||
| 4792 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Cache\Cache_Data\f_0000be | compressed | |
MD5:F1007A61B989A9D3B7E74794CD49D7C6 | SHA256:BA538EB1A6B6003337DC15D2698FC6EBA9CD07289957D48EFFB3B5F786113C64 | |||
| 4792 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Network\9a39f60b-828e-4d29-9f41-c0e06cca4517.tmp | binary | |
MD5:29271875314D9B47BE3B0D62D9B0FA2D | SHA256:E20127BA14198C3775A36E49F4AA16EE1A346D4098620A332D956591C1F00C78 | |||
| 4792 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Network\26ec7a3f-f85d-4dce-8857-117aae8ca209.tmp | binary | |
MD5:564B2A43E887555421867881A85500CD | SHA256:6C35DC3F00E55F522EC36B6BBC441CE8646B0A92D4427046BE695A102D61B67E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
64
TCP/UDP connections
74
DNS requests
49
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | HEAD | 200 | 184.30.17.174:443 | https://fs.microsoft.com/fs/windows/config.json | unknown | — | — | — |
— | — | GET | 404 | 208.115.219.174:443 | https://thelatewire.com/favicon.ico | unknown | — | — | — |
— | — | GET | 200 | 208.115.219.174:443 | https://thelatewire.com/8yoya/7x1sp2ytogxundo%C3%A3%E2%82%AC%E2%80%9A%C3%A3%E2%82%AC%E2%80%9A/YmluaXRhLmJodXRhQGNvdmF0aW9uYmlvLmNvbQ==%C3%A3%E2%82%AC%E2%80%9A$$%C3%A3%E2%82%AC%E2%80%9A | unknown | — | — | — |
4304 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5040 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4304 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6340 | RUXIMICS.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6340 | RUXIMICS.exe | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5040 | svchost.exe | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 104.126.37.131:443 | https://www.bing.com/bloomfilterfiles/ExpandedDomainsFilterGlobal.json | unknown | binary | 620 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 224.0.0.251:5353 | — | — | — | unknown |
4792 | msedge.exe | 52.182.143.213:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
6340 | RUXIMICS.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4304 | MoUsoCoreWorker.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5040 | svchost.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5988 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4792 | msedge.exe | 142.250.181.227:443 | google.co.ve | GOOGLE | US | whitelisted |
3900 | svchost.exe | 184.28.90.27:443 | fs.microsoft.com | AKAMAI-AS | US | whitelisted |
4792 | msedge.exe | 142.250.74.195:443 | www.google.co.ve | GOOGLE | US | whitelisted |
4792 | msedge.exe | 208.115.219.174:443 | thelatewire.com | LIMESTONENETWORKS | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
google.co.ve |
| whitelisted |
fs.microsoft.com |
| whitelisted |
www.google.co.ve |
| whitelisted |
thelatewire.com |
| unknown |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
microsfts0uygh0utllk8u8.grupomti.com.br |
| unknown |
www.bing.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected phishing domain name created with Leet (l1ve) |
— | — | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected phishing domain name created with Leet (l1ve) |