| File name: | order.zip |
| Full analysis: | https://app.any.run/tasks/68f6f8fc-81a5-4ac4-99be-60e67b397d50 |
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2019, 08:41:47 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 5CF4E1E90288D2BC24268A401D130053 |
| SHA1: | F9B7C24D613792B55B5E4B0054C74DB286B9348A |
| SHA256: | 861795CC12AE6CA9C6031859AB2A772CB73186774B9DECC6BEB4D2A6D8D927CD |
| SSDEEP: | 6:5jVhtCXyv3F4GjeH3DXOe8AovgvhmYy4YClN/dTEXugiUNtK0OFMnotn3VhtmQ+f:5jpCiv3MH3DXOeovuJdLNVI+sK0dnoVE |
MALICIOUS
No malicious indicators.SUSPICIOUS
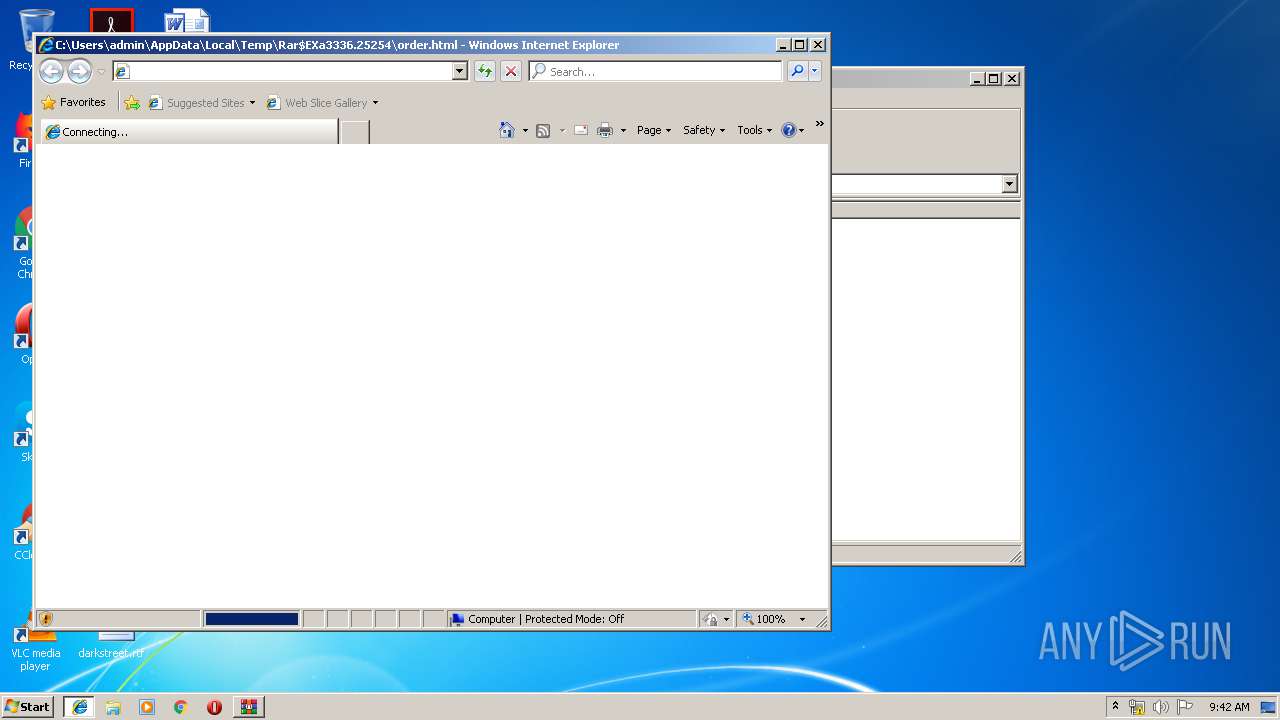
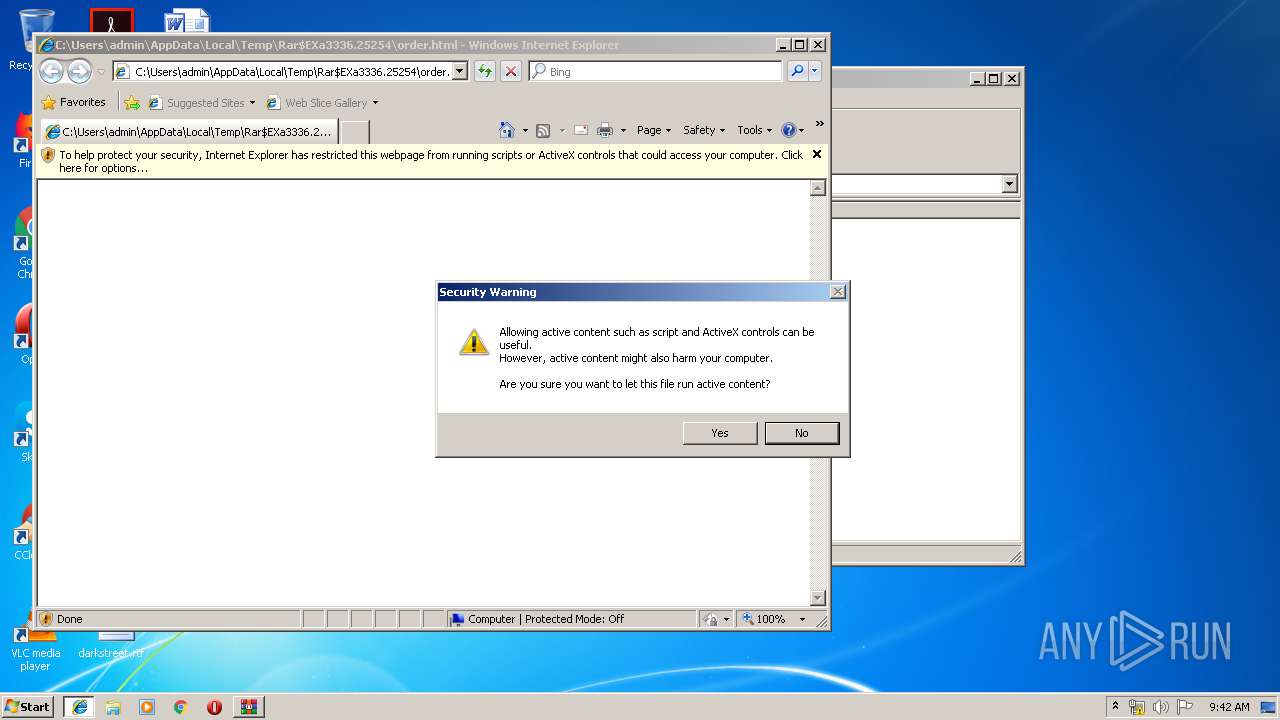
Starts Internet Explorer
- WinRAR.exe (PID: 3336)
INFO
Reads Microsoft Office registry keys
- WinRAR.exe (PID: 3336)
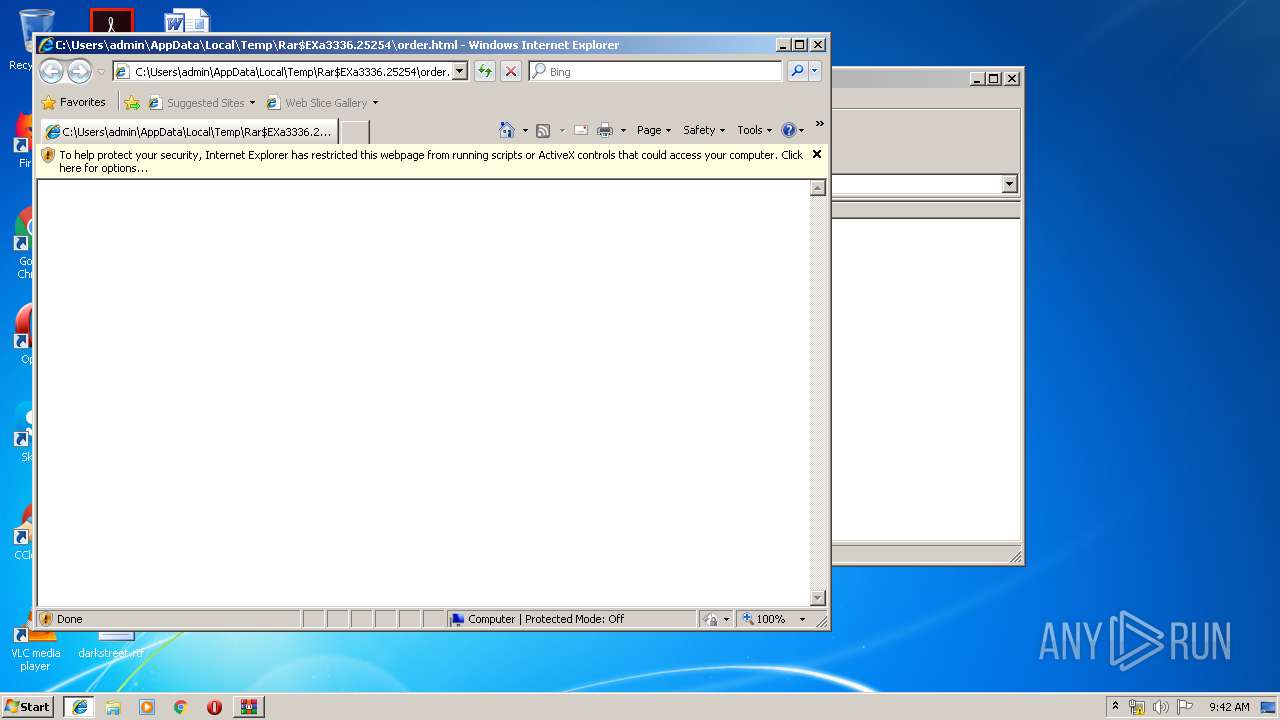
Changes internet zones settings
- iexplore.exe (PID: 3068)
Reads Internet Cache Settings
- iexplore.exe (PID: 3720)
- iexplore.exe (PID: 3068)
- iexplore.exe (PID: 3972)
Reads internet explorer settings
- iexplore.exe (PID: 3720)
- iexplore.exe (PID: 3972)
Application launched itself
- iexplore.exe (PID: 3068)
Creates files in the user directory
- iexplore.exe (PID: 3972)
- iexplore.exe (PID: 3068)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
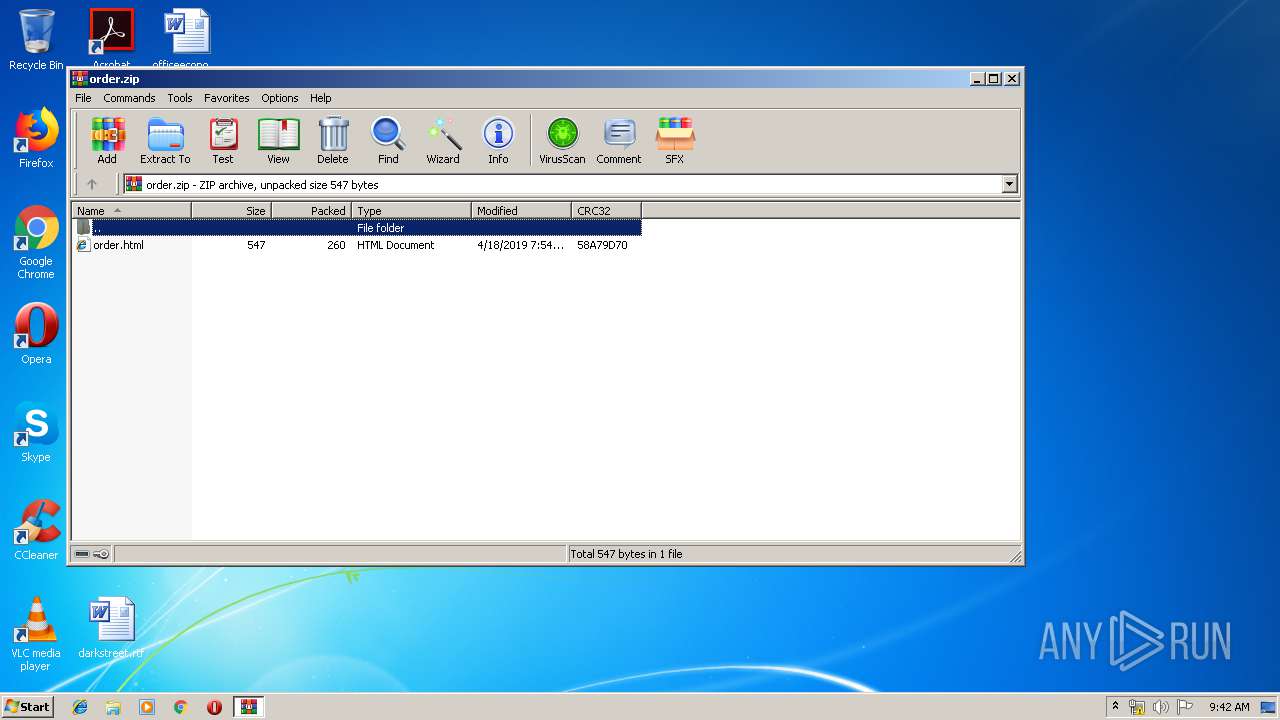
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:04:18 07:54:08 |
| ZipCRC: | 0x58a79d70 |
| ZipCompressedSize: | 260 |
| ZipUncompressedSize: | 547 |
| ZipFileName: | order.html |
Total processes
38
Monitored processes
4
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3068 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\admin\AppData\Local\Temp\Rar$EXa3336.25254\order.html | C:\Program Files\Internet Explorer\iexplore.exe | WinRAR.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3336 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\order.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3720 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3068 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3972 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3068 CREDAT:137473 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
985
Read events
887
Write events
96
Delete events
2
Modification events
| (PID) Process: | (3336) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3336) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3336) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3336) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\order.zip | |||
| (PID) Process: | (3336) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3336) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3336) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3336) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3336) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\ieframe.dll,-912 |
Value: HTML Document | |||
| (PID) Process: | (3068) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
Executable files
0
Suspicious files
1
Text files
40
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3068 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3068 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3972 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\R0XV3039\ltdg_mywebcommunity_org[1].txt | — | |
MD5:— | SHA256:— | |||
| 3068 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF886B1361597169D7.TMP | — | |
MD5:— | SHA256:— | |||
| 3972 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\R0XV3039\cjkelechi_mywebcommunity_org[1].txt | — | |
MD5:— | SHA256:— | |||
| 3336 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3336.25254\order.html | html | |
MD5:— | SHA256:— | |||
| 3972 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\HHPUJS74\ltdg_mywebcommunity_org[1].htm | html | |
MD5:— | SHA256:— | |||
| 3972 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\Low\History.IE5\MSHist012019052020190521\index.dat | dat | |
MD5:— | SHA256:— | |||
| 3720 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\History.IE5\MSHist012019052020190521\index.dat | dat | |
MD5:— | SHA256:— | |||
| 3972 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\UVWZT6VL\cjkelechi_mywebcommunity_org[1].htm | html | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
19
TCP/UDP connections
26
DNS requests
8
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
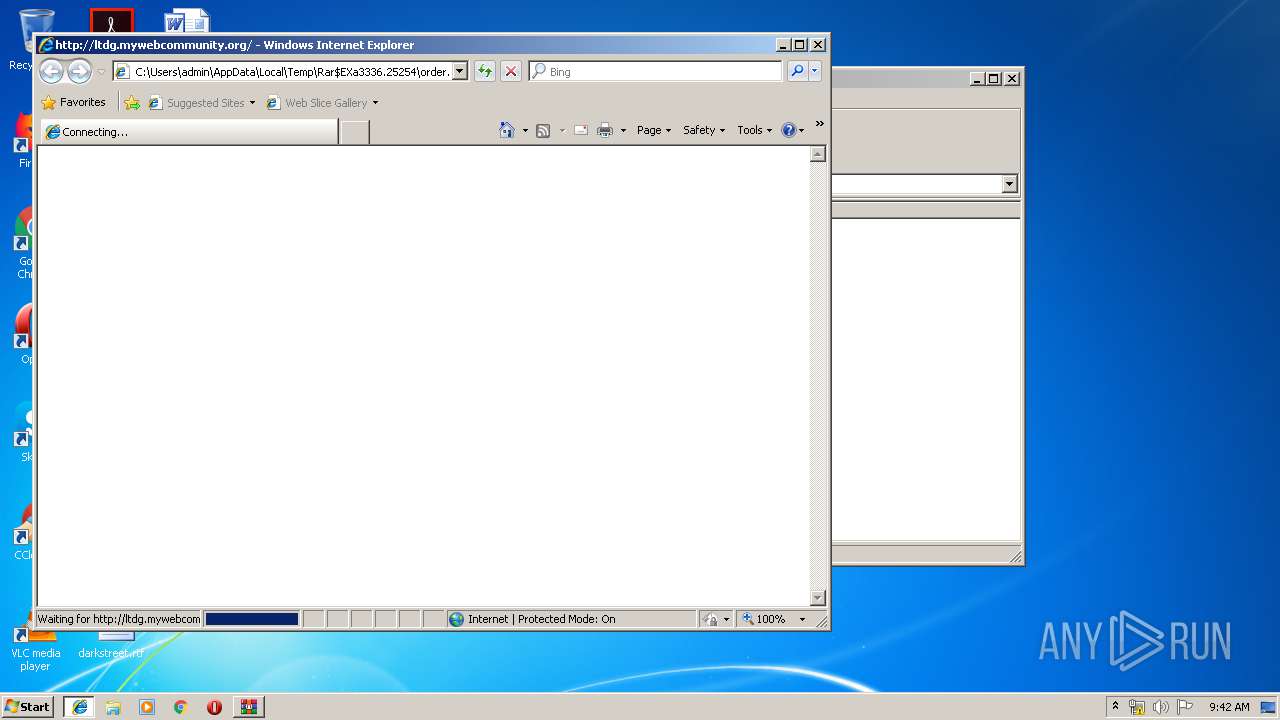
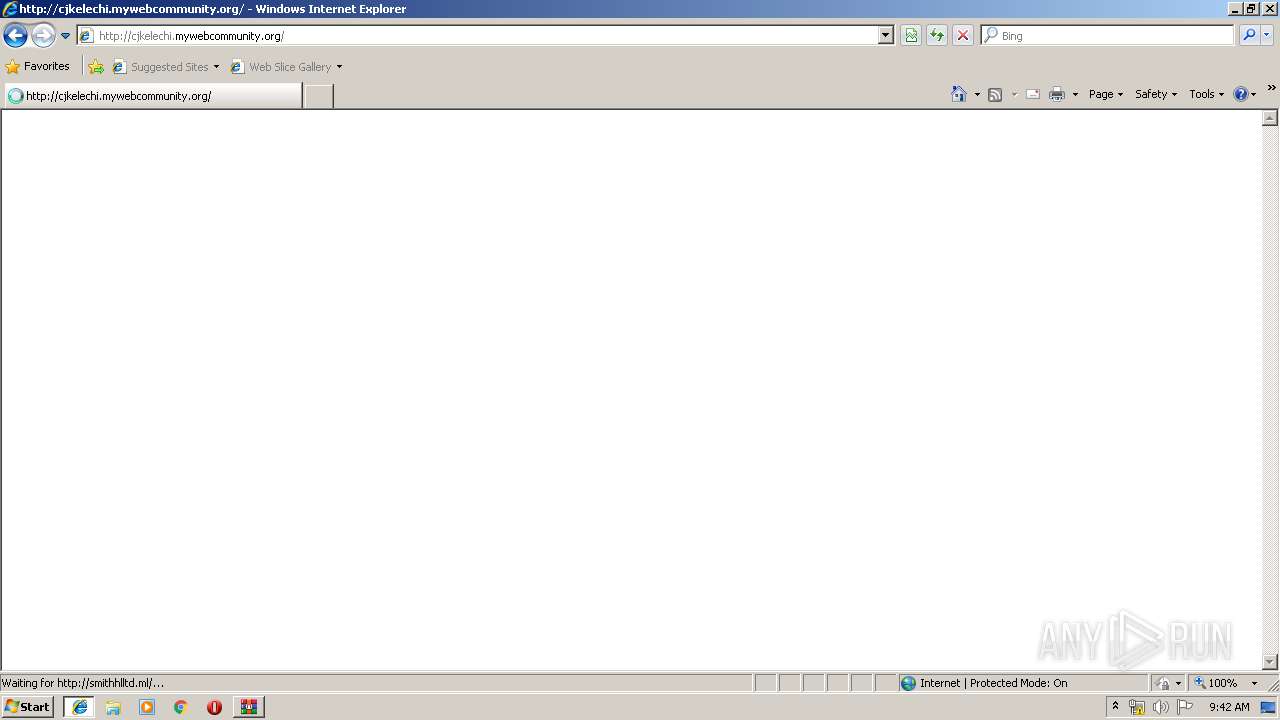
3972 | iexplore.exe | GET | 200 | 185.176.43.92:80 | http://ltdg.mywebcommunity.org/ | BG | html | 160 b | malicious |
3068 | iexplore.exe | GET | 404 | 185.176.43.92:80 | http://ltdg.mywebcommunity.org/favicon.ico | BG | html | 118 b | malicious |
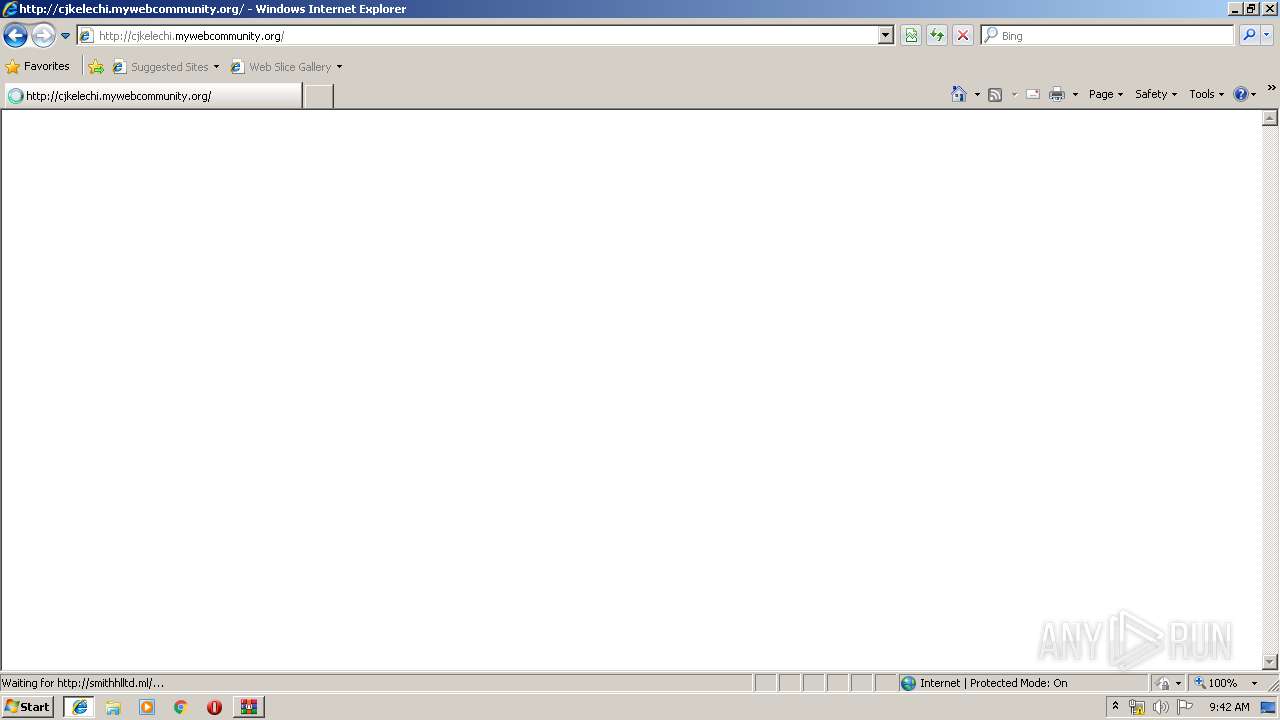
3972 | iexplore.exe | GET | 200 | 185.176.43.92:80 | http://cjkelechi.mywebcommunity.org/ | BG | html | 145 b | malicious |
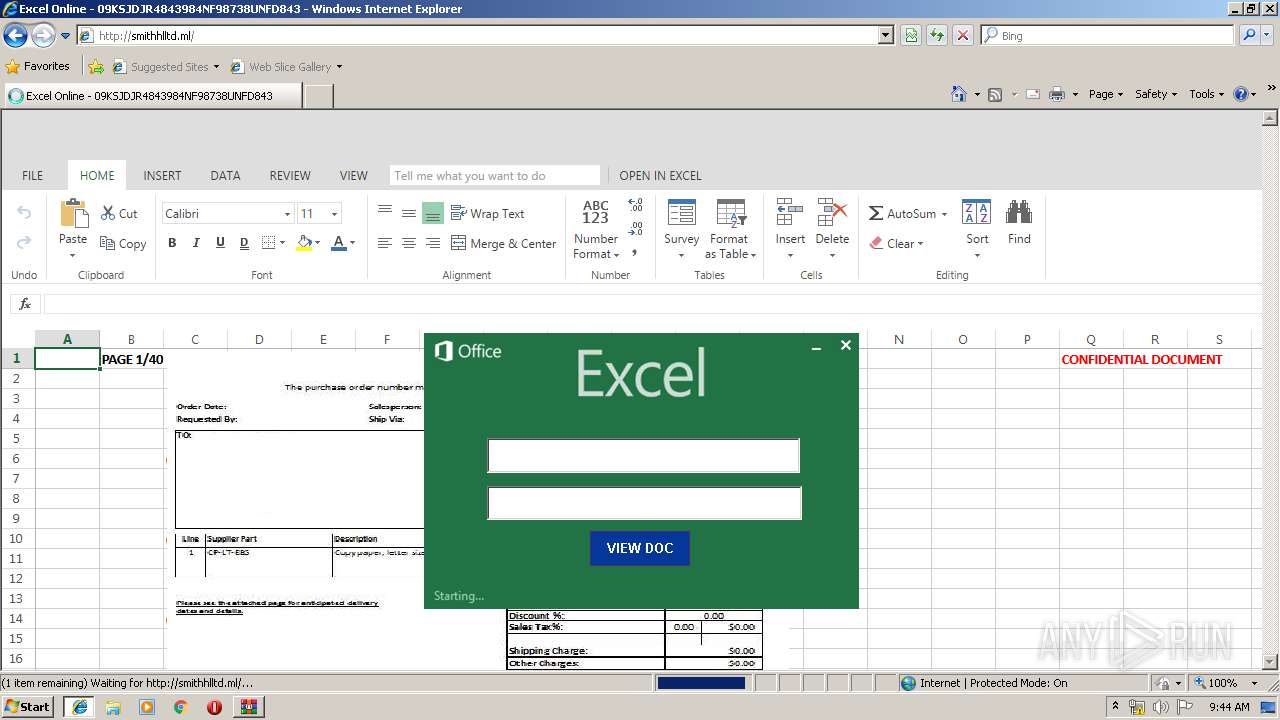
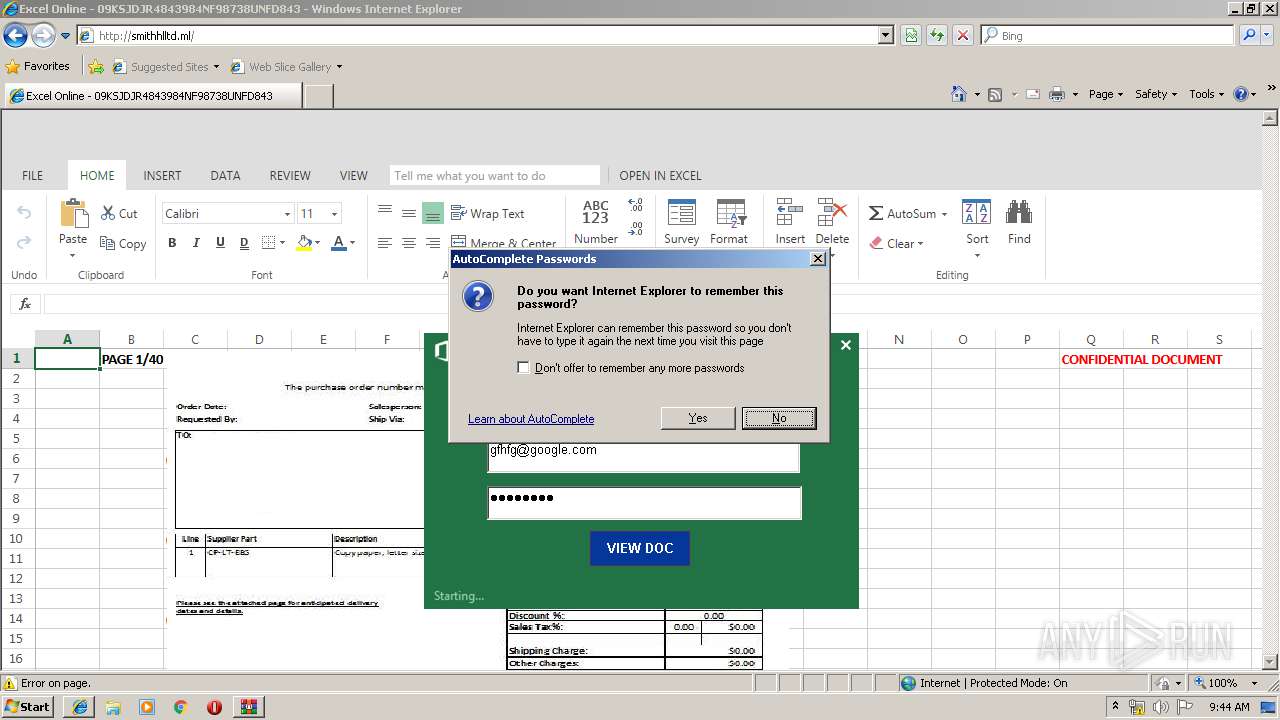
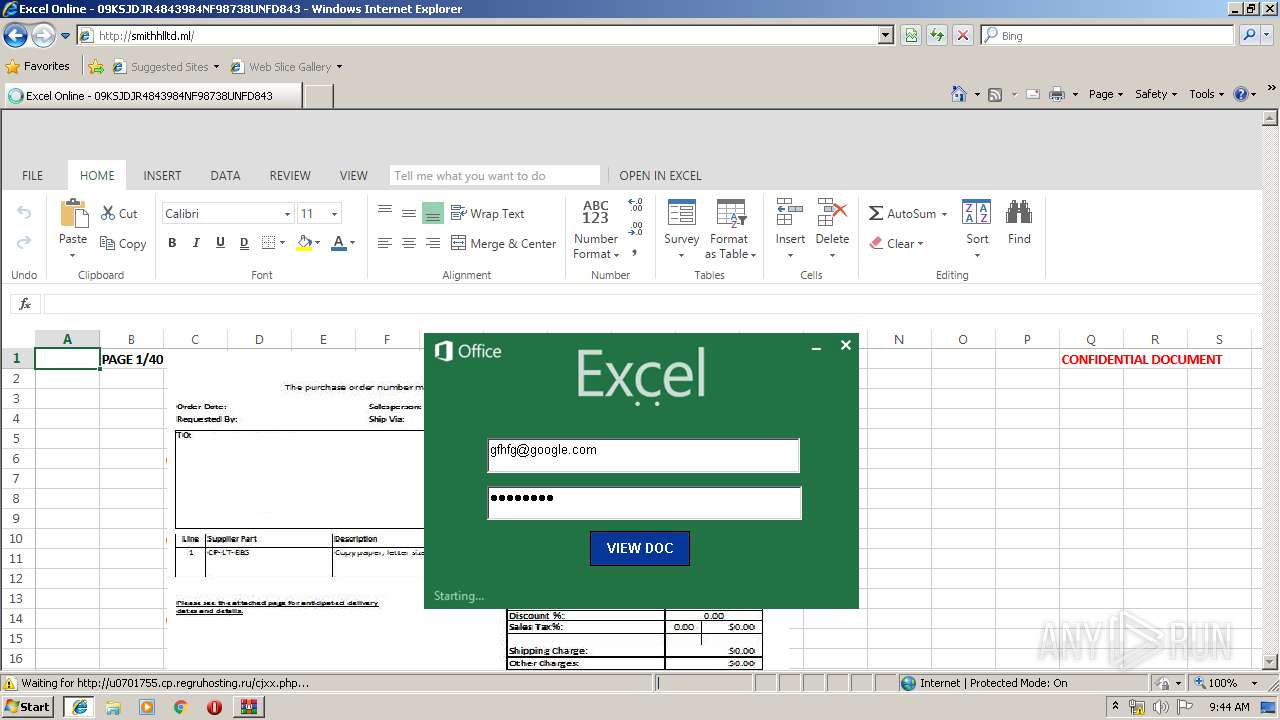
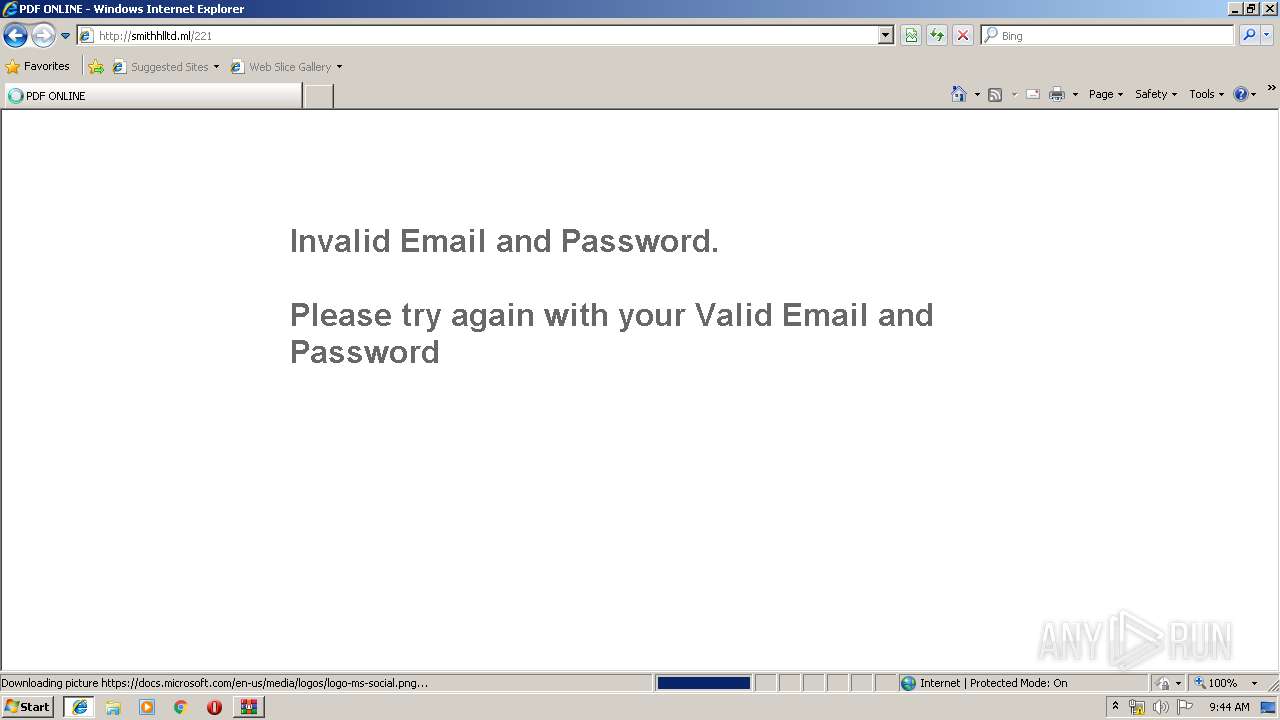
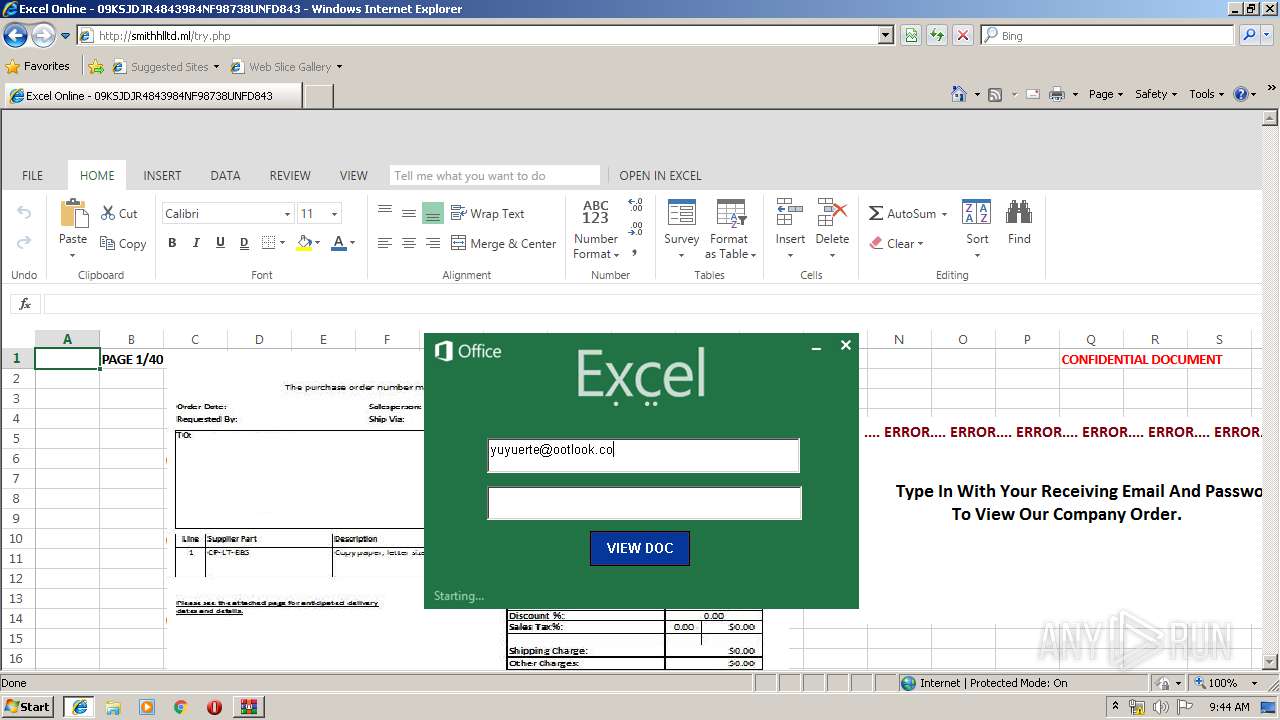
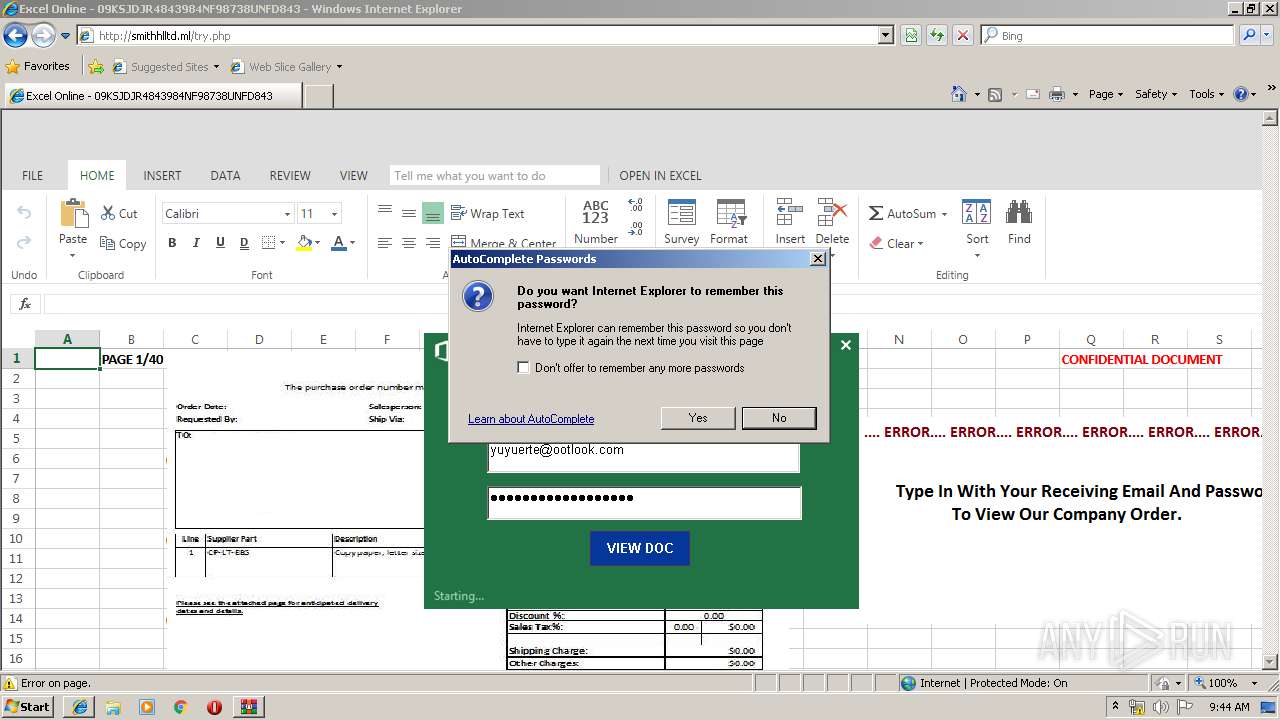
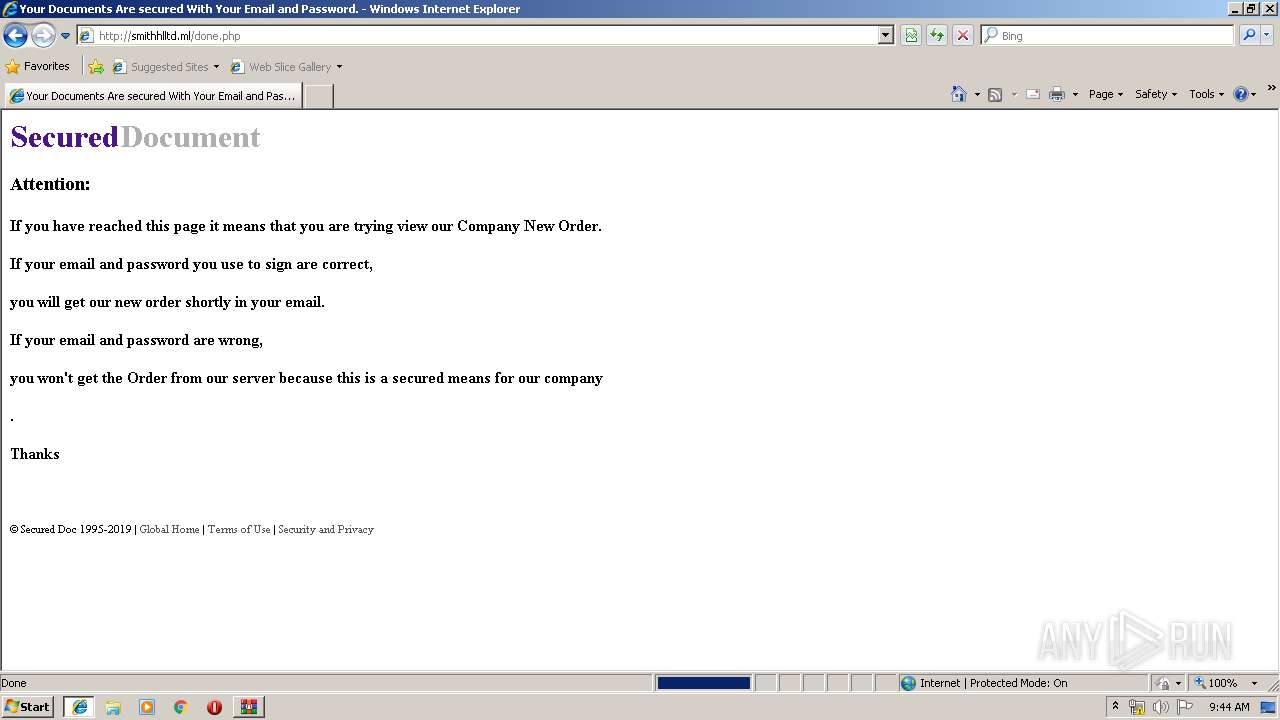
3972 | iexplore.exe | GET | 200 | 31.31.196.197:80 | http://smithhlltd.ml/221 | RU | html | 2.30 Kb | malicious |
3068 | iexplore.exe | GET | 404 | 31.31.196.197:80 | http://smithhlltd.ml/favicon.ico | RU | html | 1.19 Kb | malicious |
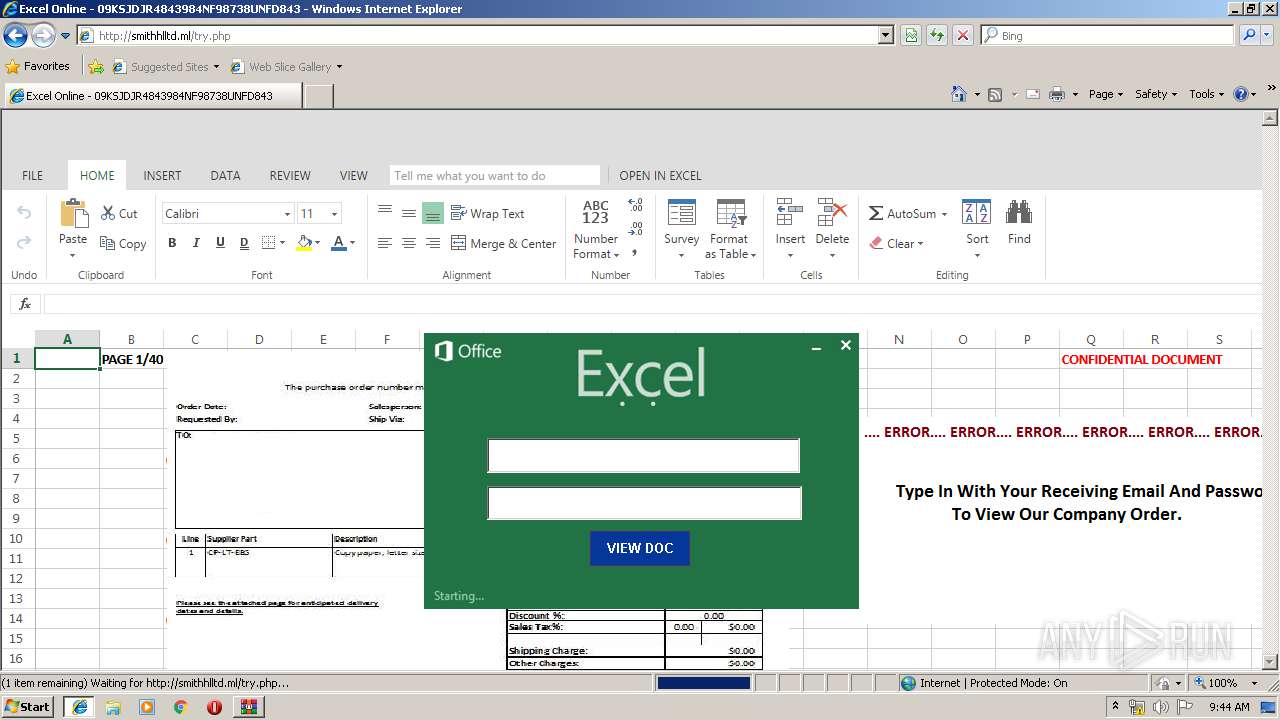
3972 | iexplore.exe | GET | 200 | 31.31.196.197:80 | http://smithhlltd.ml/try.php | RU | html | 922 b | malicious |
3068 | iexplore.exe | GET | 404 | 31.31.196.197:80 | http://u0701755.cp.regruhosting.ru/favicon.ico | RU | html | 1.19 Kb | malicious |
3068 | iexplore.exe | GET | 404 | 31.31.196.197:80 | http://smithhlltd.ml/favicon.ico | RU | html | 1.19 Kb | malicious |
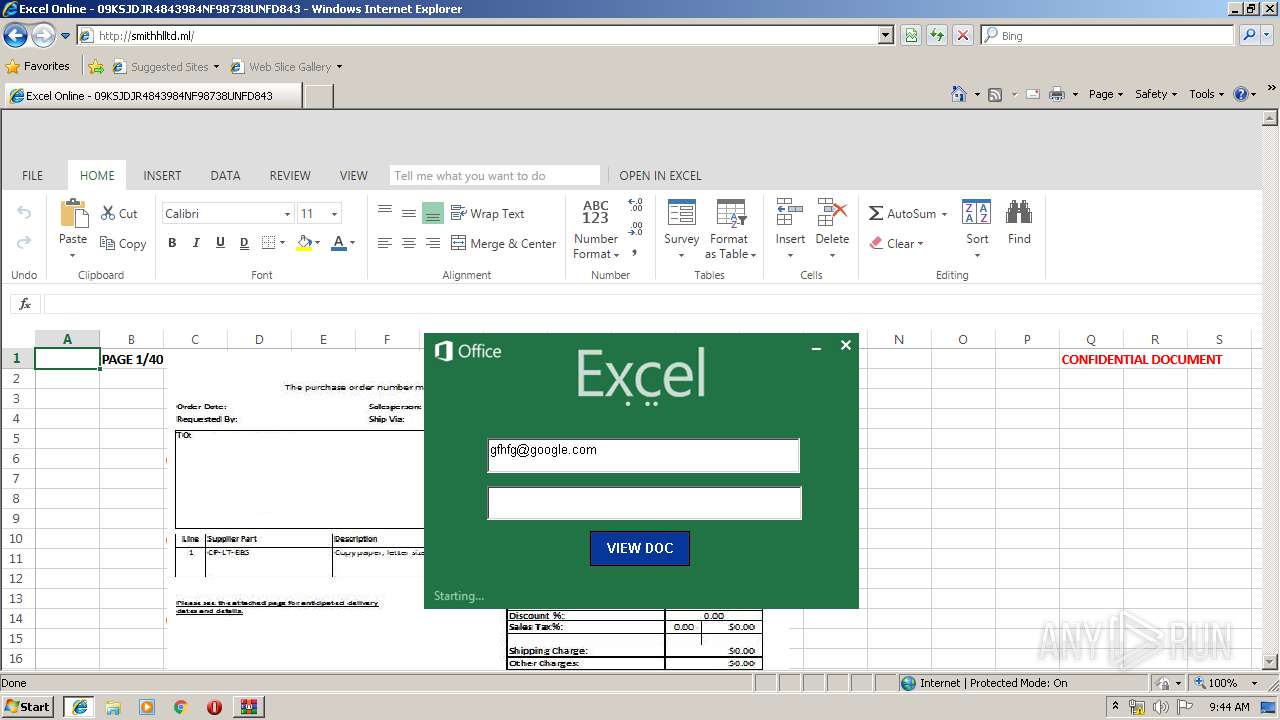
3972 | iexplore.exe | POST | 200 | 31.31.196.197:80 | http://u0701755.cp.regruhosting.ru/cfi.php | RU | text | 92 b | malicious |
3972 | iexplore.exe | GET | 200 | 31.31.196.197:80 | http://u0701754.cp.regruhosting.ru/exl1.png | RU | image | 167 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3068 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3972 | iexplore.exe | 185.176.43.92:80 | ltdg.mywebcommunity.org | Zetta Hosting Solutions LLC. | BG | malicious |
3068 | iexplore.exe | 185.176.43.92:80 | ltdg.mywebcommunity.org | Zetta Hosting Solutions LLC. | BG | malicious |
3972 | iexplore.exe | 31.31.196.197:80 | smithhlltd.ml | Domain names registrar REG.RU, Ltd | RU | malicious |
3068 | iexplore.exe | 31.31.196.197:80 | smithhlltd.ml | Domain names registrar REG.RU, Ltd | RU | malicious |
— | — | 31.31.196.197:80 | smithhlltd.ml | Domain names registrar REG.RU, Ltd | RU | malicious |
3972 | iexplore.exe | 104.109.84.249:443 | docs.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 104.109.84.249:443 | docs.microsoft.com | Akamai International B.V. | NL | whitelisted |
3068 | iexplore.exe | 104.109.84.249:443 | docs.microsoft.com | Akamai International B.V. | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
ltdg.mywebcommunity.org |
| malicious |
cjkelechi.mywebcommunity.org |
| malicious |
smithhlltd.ml |
| malicious |
u0701754.cp.regruhosting.ru |
| malicious |
u0701755.cp.regruhosting.ru |
| malicious |
docs.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1056 | svchost.exe | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .ml Domain |
3972 | iexplore.exe | A Network Trojan was detected | ET CURRENT_EVENTS Excel/Adobe Online Phishing Landing Nov 25 2015 |
3972 | iexplore.exe | Potentially Bad Traffic | ET CURRENT_EVENTS Possible Excel Online Phishing Landing - Title over non SSL |
3972 | iexplore.exe | A Network Trojan was detected | MALWARE [PTsecurity] Possible Successful Generic Phish |
3972 | iexplore.exe | A Network Trojan was detected | ET CURRENT_EVENTS Excel/Adobe Online Phishing Landing Nov 25 2015 |
3972 | iexplore.exe | Potentially Bad Traffic | ET CURRENT_EVENTS Possible Excel Online Phishing Landing - Title over non SSL |
3972 | iexplore.exe | A Network Trojan was detected | MALWARE [PTsecurity] Possible Successful Generic Phish |
2 ETPRO signatures available at the full report