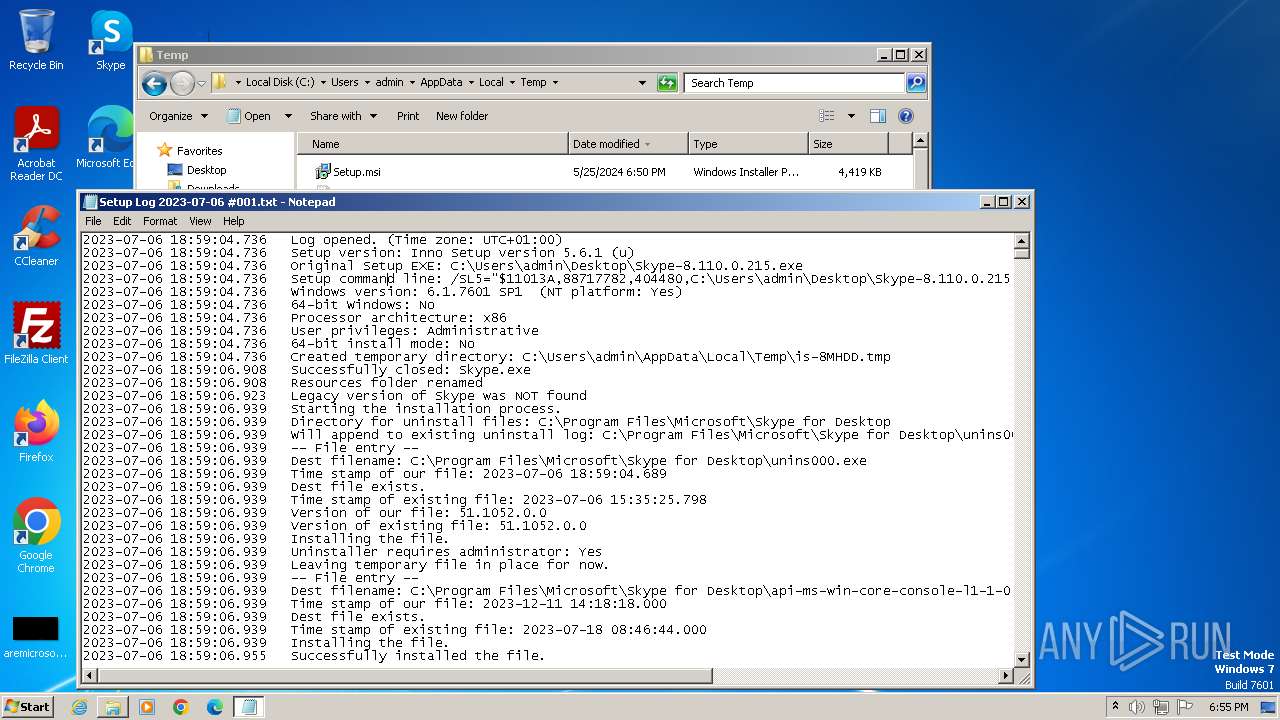
| File name: | Setup.msi |
| Full analysis: | https://app.any.run/tasks/3c4cd4b2-92c6-403f-b81d-bafa3120b4a8 |
| Verdict: | Malicious activity |
| Analysis date: | May 25, 2024, 17:50:42 |
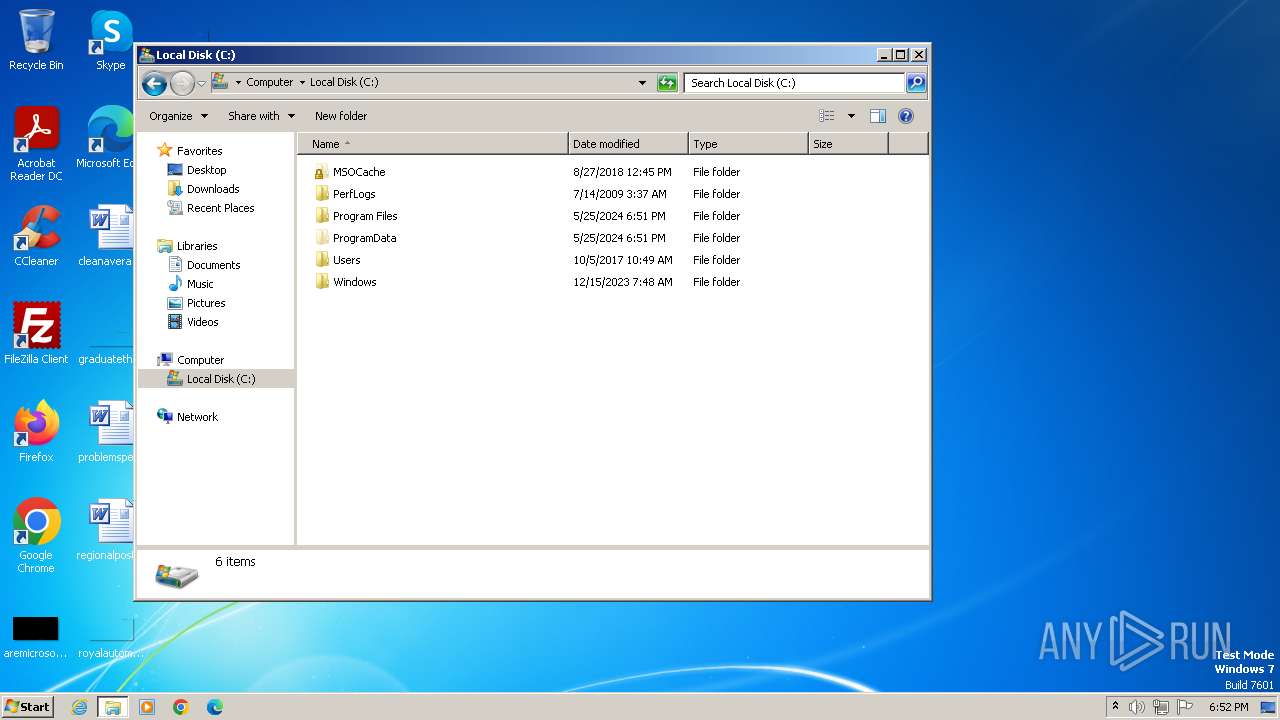
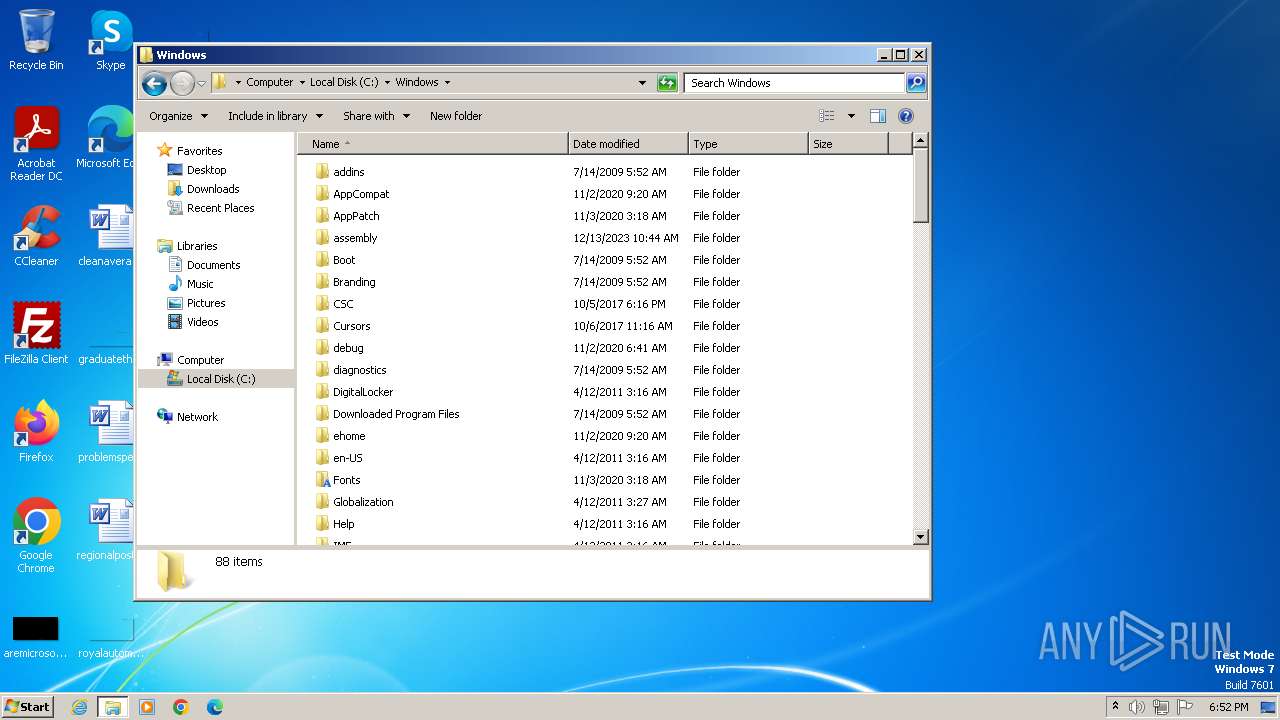
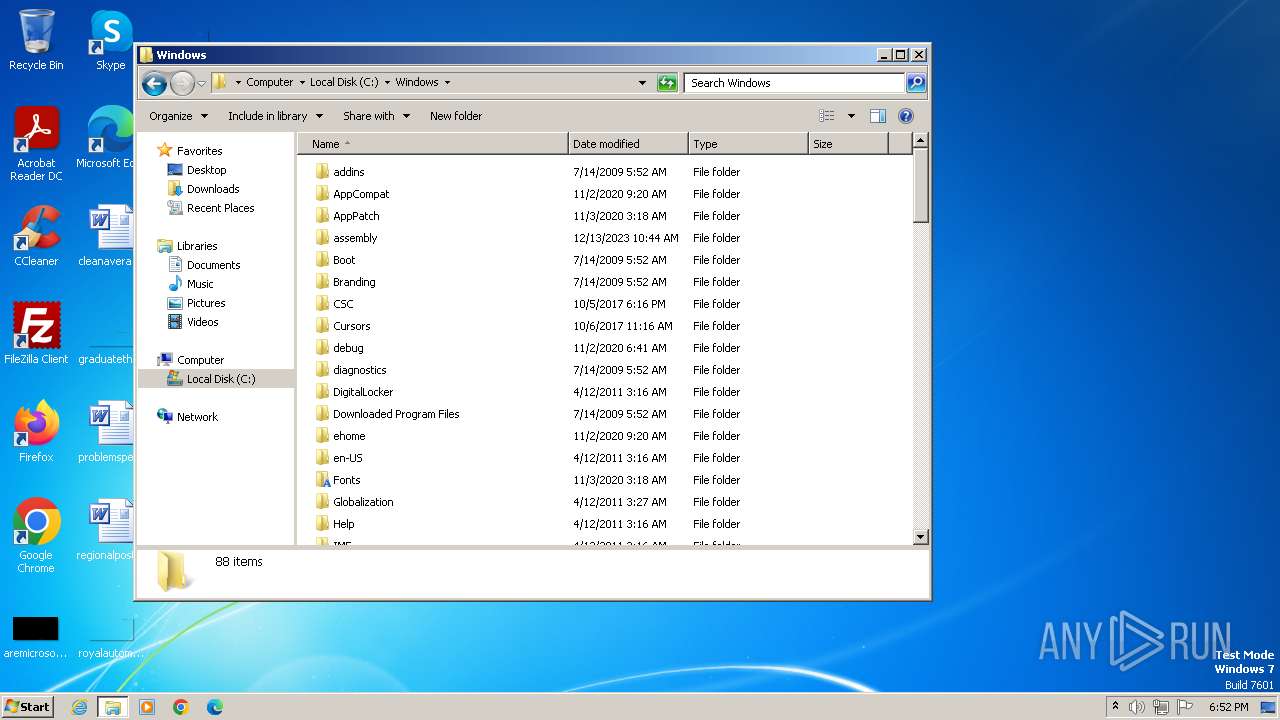
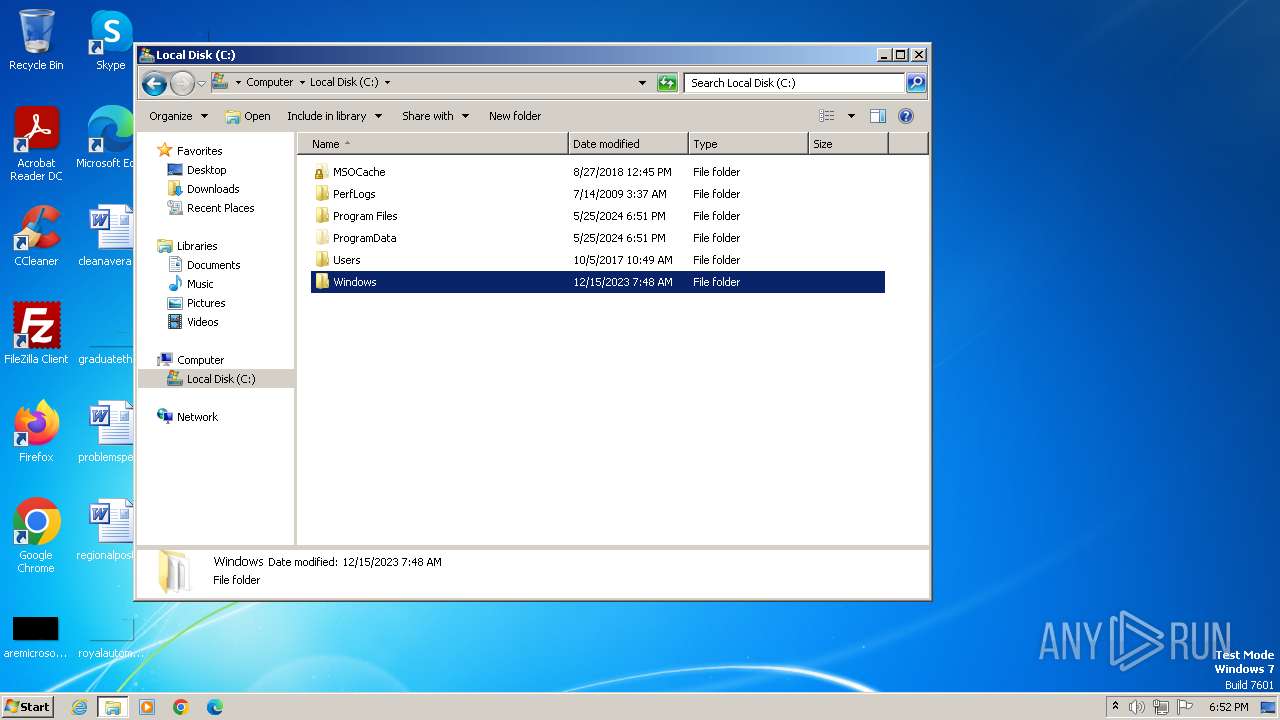
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, MSI Installer, Security: 0, Code page: 1252, Revision Number: {C1B83721-FE99-46B4-B042-617BDFBC06F6}, Number of Words: 2, Subject: World Wide Web, Author: World Wide Solutions, Name of Creating Application: World Wide Web, Template: ;1033, Title: Installation Database, Keywords: Installer, MSI, Database, Create Time/Date: Fri May 24 14:47:38 2024, Last Saved Time/Date: Fri May 24 14:47:38 2024, Last Printed: Fri May 24 14:47:38 2024, Number of Pages: 450 |
| MD5: | 0507DF0A33368A93328C6DECABDFB577 |
| SHA1: | 40187F34E3C097812B53BF9C8B760362BC2B5F50 |
| SHA256: | 8614615B67BAC60F0460A8DF17B504076B5A9A39DC249CC9BF7B34ED7685A09B |
| SSDEEP: | 98304:J9ILoiSpk+fom2xYqr0V5RZlTvJ9jwCdJbXjs18a0IX6C4ORbn6u18j0kOjLqPmS:3G |
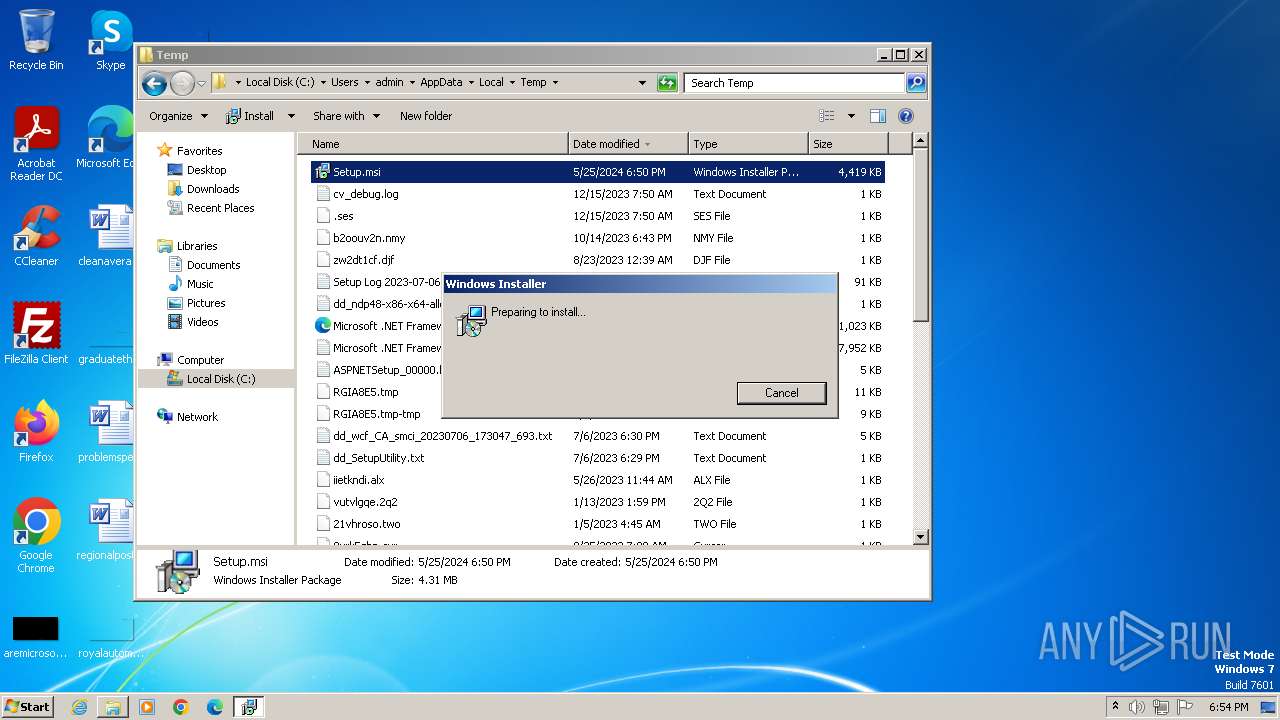
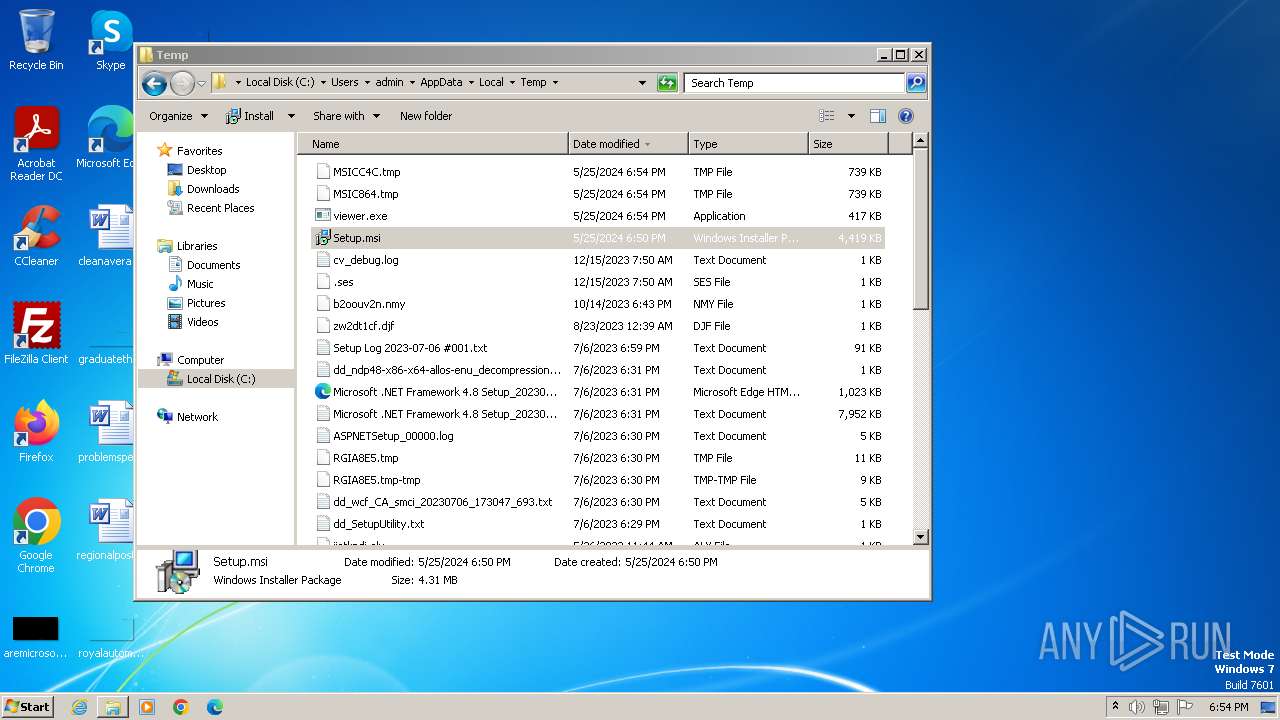
MALICIOUS
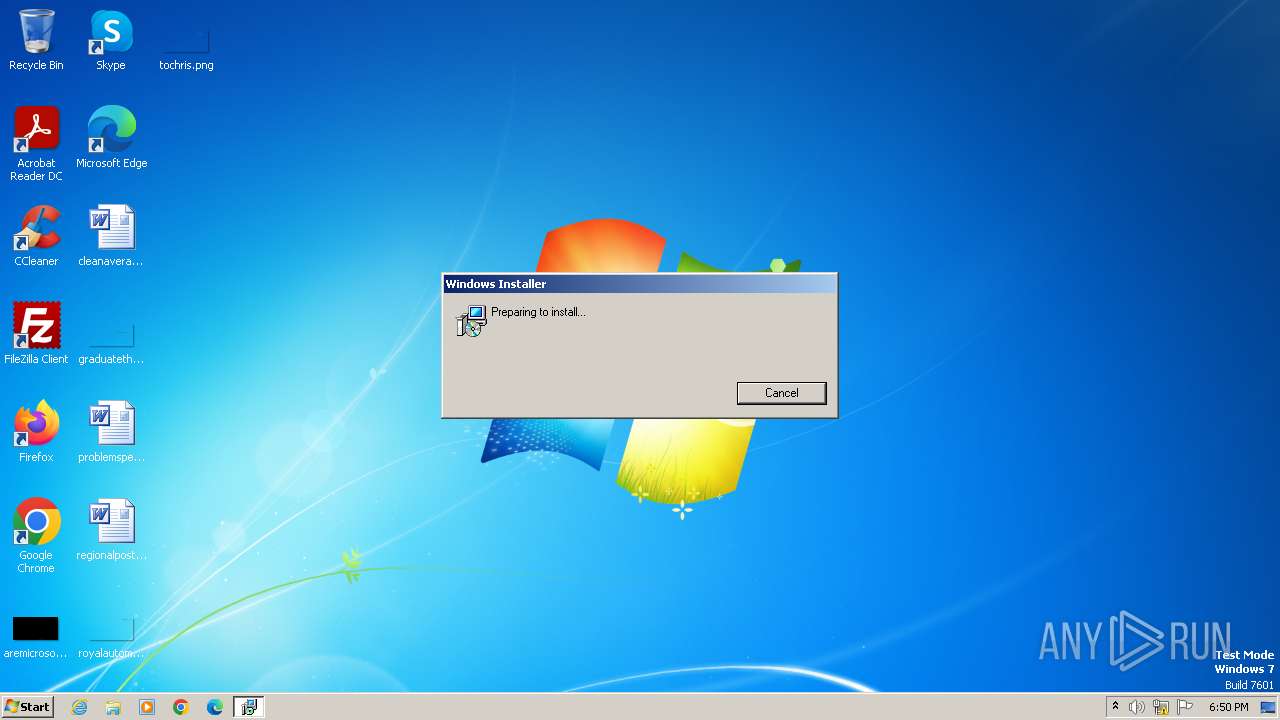
Drops the executable file immediately after the start
- msiexec.exe (PID: 1200)
- msiexec.exe (PID: 4060)
- msiexec.exe (PID: 3120)
- msiexec.exe (PID: 3820)
SUSPICIOUS
Reads the Internet Settings
- msiexec.exe (PID: 3980)
- msiexec.exe (PID: 1200)
- viewer.exe (PID: 2312)
- WorldWideWeb.exe (PID: 2320)
- viewer.exe (PID: 1944)
- msiexec.exe (PID: 3120)
- WorldWideWeb.exe (PID: 3408)
- msiexec.exe (PID: 3820)
- viewer.exe (PID: 1396)
- WorldWideWeb.exe (PID: 1136)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 1200)
- viewer.exe (PID: 2312)
- msiexec.exe (PID: 1840)
- WorldWideWeb.exe (PID: 2320)
- msiexec.exe (PID: 3120)
- viewer.exe (PID: 1944)
- msiexec.exe (PID: 1032)
- WorldWideWeb.exe (PID: 3408)
- viewer.exe (PID: 1396)
- msiexec.exe (PID: 3820)
- msiexec.exe (PID: 2448)
- WorldWideWeb.exe (PID: 1136)
Reads settings of System Certificates
- viewer.exe (PID: 2312)
- WorldWideWeb.exe (PID: 2320)
- viewer.exe (PID: 1944)
- WorldWideWeb.exe (PID: 3408)
- viewer.exe (PID: 1396)
- WorldWideWeb.exe (PID: 1136)
Adds/modifies Windows certificates
- viewer.exe (PID: 2312)
Checks Windows Trust Settings
- msiexec.exe (PID: 1200)
- msiexec.exe (PID: 1840)
- viewer.exe (PID: 2312)
- msiexec.exe (PID: 4060)
- WorldWideWeb.exe (PID: 2320)
- msiexec.exe (PID: 3120)
- viewer.exe (PID: 1944)
- msiexec.exe (PID: 1032)
- WorldWideWeb.exe (PID: 3408)
- msiexec.exe (PID: 3820)
- viewer.exe (PID: 1396)
- msiexec.exe (PID: 2448)
- WorldWideWeb.exe (PID: 1136)
Executes as Windows Service
- VSSVC.exe (PID: 2068)
- VSSVC.exe (PID: 2868)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 4060)
The process executes via Task Scheduler
- WorldWideWeb.exe (PID: 2320)
- WorldWideWeb.exe (PID: 3408)
- WorldWideWeb.exe (PID: 1136)
INFO
Checks supported languages
- msiexec.exe (PID: 4060)
- msiexec.exe (PID: 1200)
- viewer.exe (PID: 2312)
- wmpnscfg.exe (PID: 1640)
- msiexec.exe (PID: 1332)
- msiexec.exe (PID: 1840)
- WorldWideWeb.exe (PID: 2320)
- msiexec.exe (PID: 1976)
- msiexec.exe (PID: 3120)
- viewer.exe (PID: 1944)
- msiexec.exe (PID: 1032)
- msiexec.exe (PID: 2756)
- msiexec.exe (PID: 3208)
- WorldWideWeb.exe (PID: 3408)
- msiexec.exe (PID: 3820)
- viewer.exe (PID: 1396)
- msiexec.exe (PID: 2332)
- msiexec.exe (PID: 2196)
- msiexec.exe (PID: 2448)
- WorldWideWeb.exe (PID: 1136)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 3980)
- msiexec.exe (PID: 304)
- msiexec.exe (PID: 1296)
- msiexec.exe (PID: 3116)
- msiexec.exe (PID: 3536)
- msiexec.exe (PID: 1292)
Reads the software policy settings
- msiexec.exe (PID: 3980)
- msiexec.exe (PID: 1200)
- msiexec.exe (PID: 304)
- viewer.exe (PID: 2312)
- msiexec.exe (PID: 1840)
- msiexec.exe (PID: 4060)
- WorldWideWeb.exe (PID: 2320)
- msiexec.exe (PID: 1296)
- msiexec.exe (PID: 3120)
- viewer.exe (PID: 1944)
- msiexec.exe (PID: 3116)
- msiexec.exe (PID: 1032)
- WorldWideWeb.exe (PID: 3408)
- msiexec.exe (PID: 3536)
- viewer.exe (PID: 1396)
- msiexec.exe (PID: 3820)
- msiexec.exe (PID: 2448)
- msiexec.exe (PID: 1292)
- WorldWideWeb.exe (PID: 1136)
An automatically generated document
- msiexec.exe (PID: 3980)
Reads the computer name
- msiexec.exe (PID: 4060)
- viewer.exe (PID: 2312)
- msiexec.exe (PID: 1200)
- msiexec.exe (PID: 1840)
- wmpnscfg.exe (PID: 1640)
- WorldWideWeb.exe (PID: 2320)
- msiexec.exe (PID: 1976)
- msiexec.exe (PID: 1332)
- msiexec.exe (PID: 3120)
- viewer.exe (PID: 1944)
- msiexec.exe (PID: 1032)
- msiexec.exe (PID: 2756)
- msiexec.exe (PID: 3208)
- WorldWideWeb.exe (PID: 3408)
- msiexec.exe (PID: 3820)
- viewer.exe (PID: 1396)
- msiexec.exe (PID: 2448)
- msiexec.exe (PID: 2332)
- WorldWideWeb.exe (PID: 1136)
- msiexec.exe (PID: 2196)
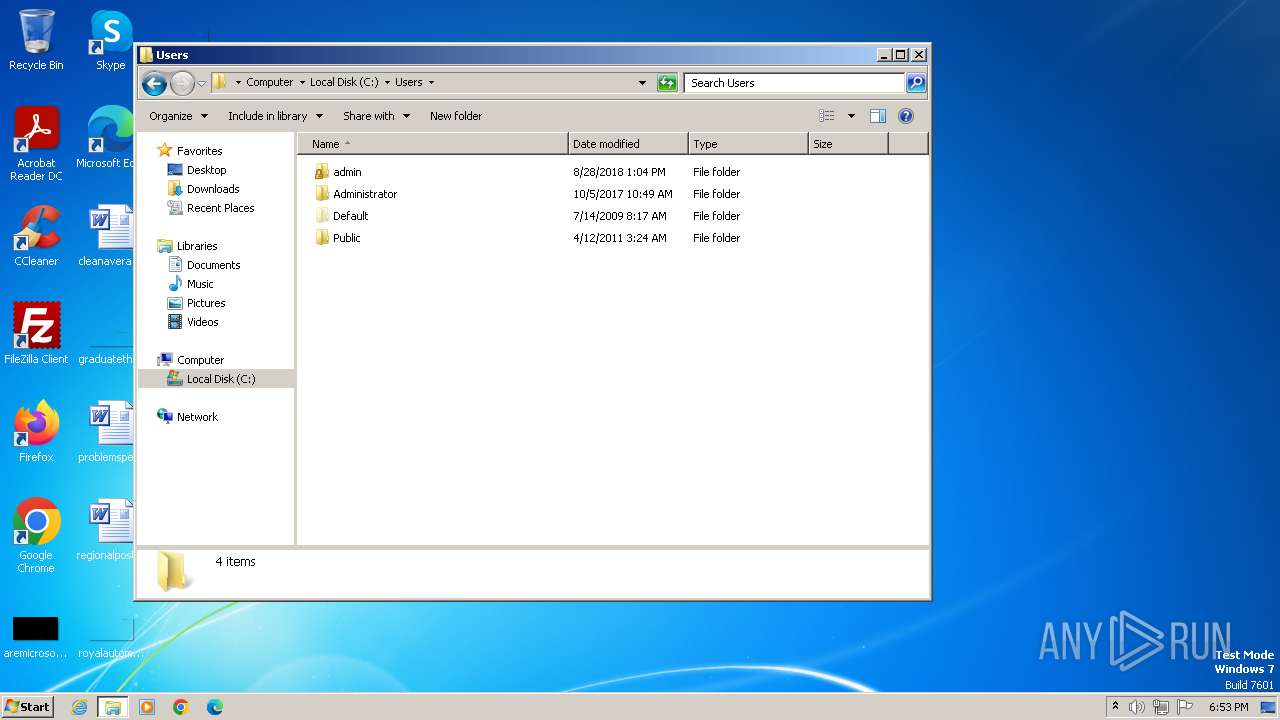
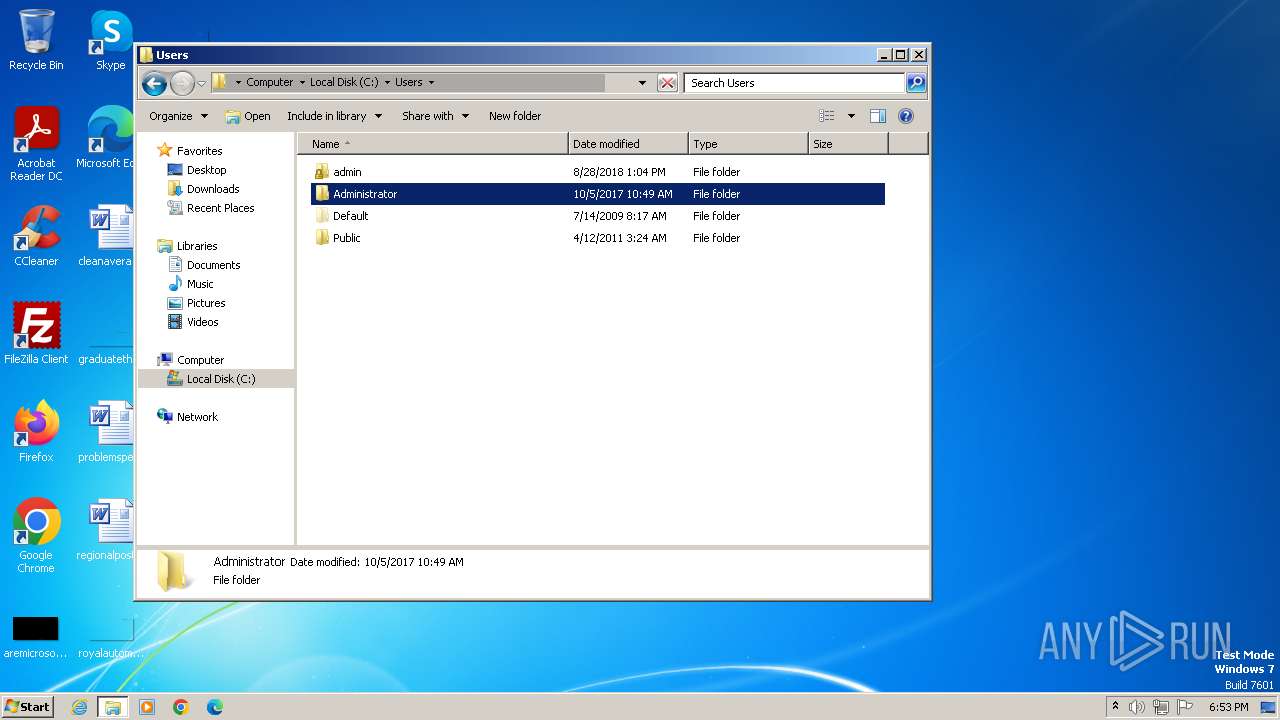
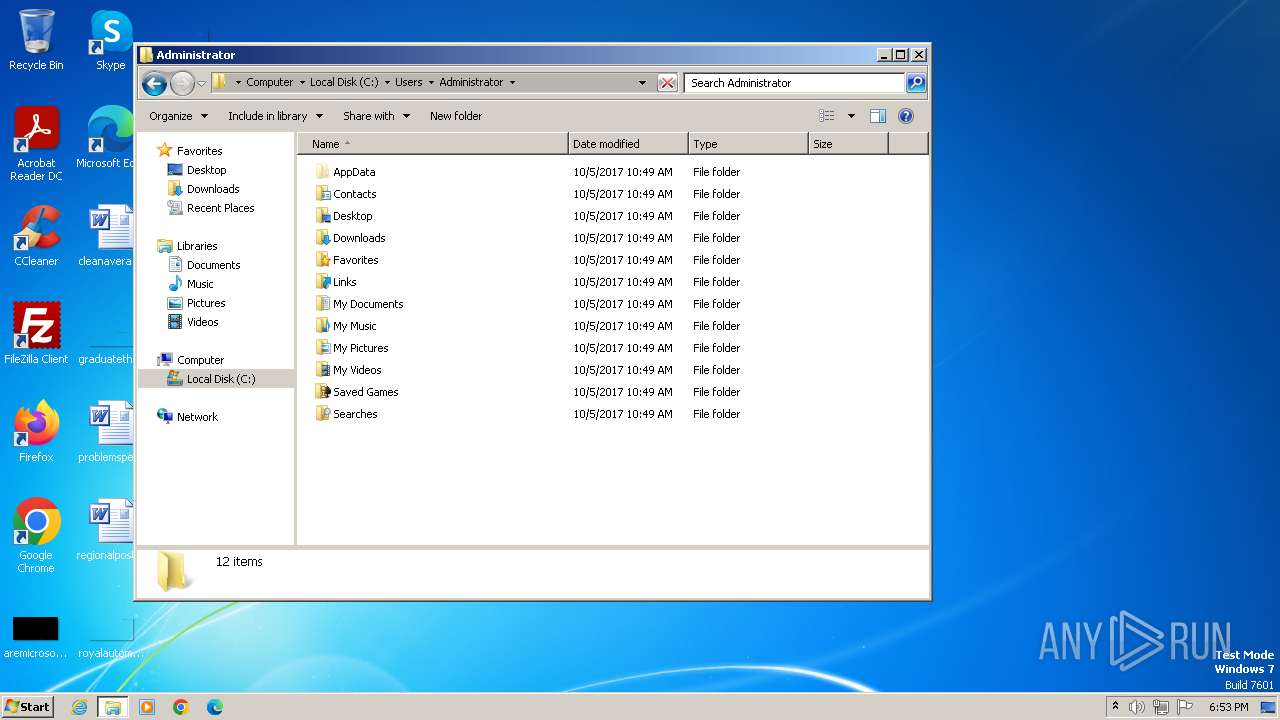
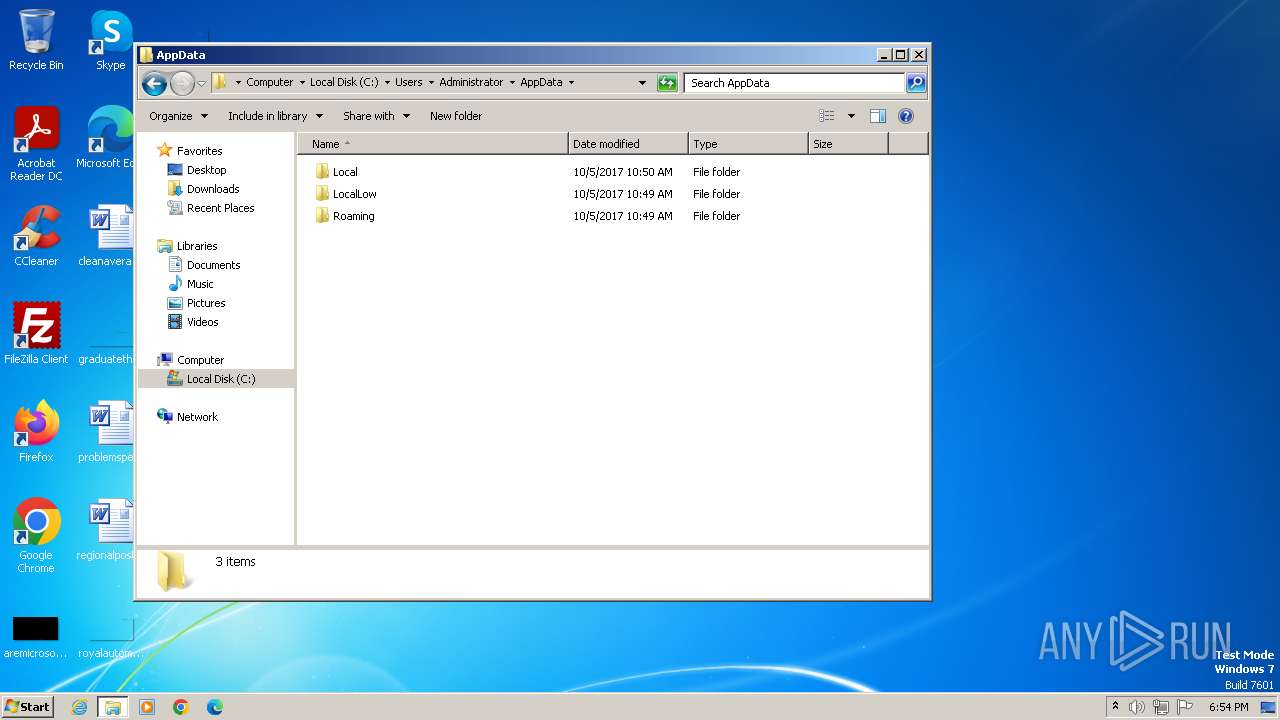
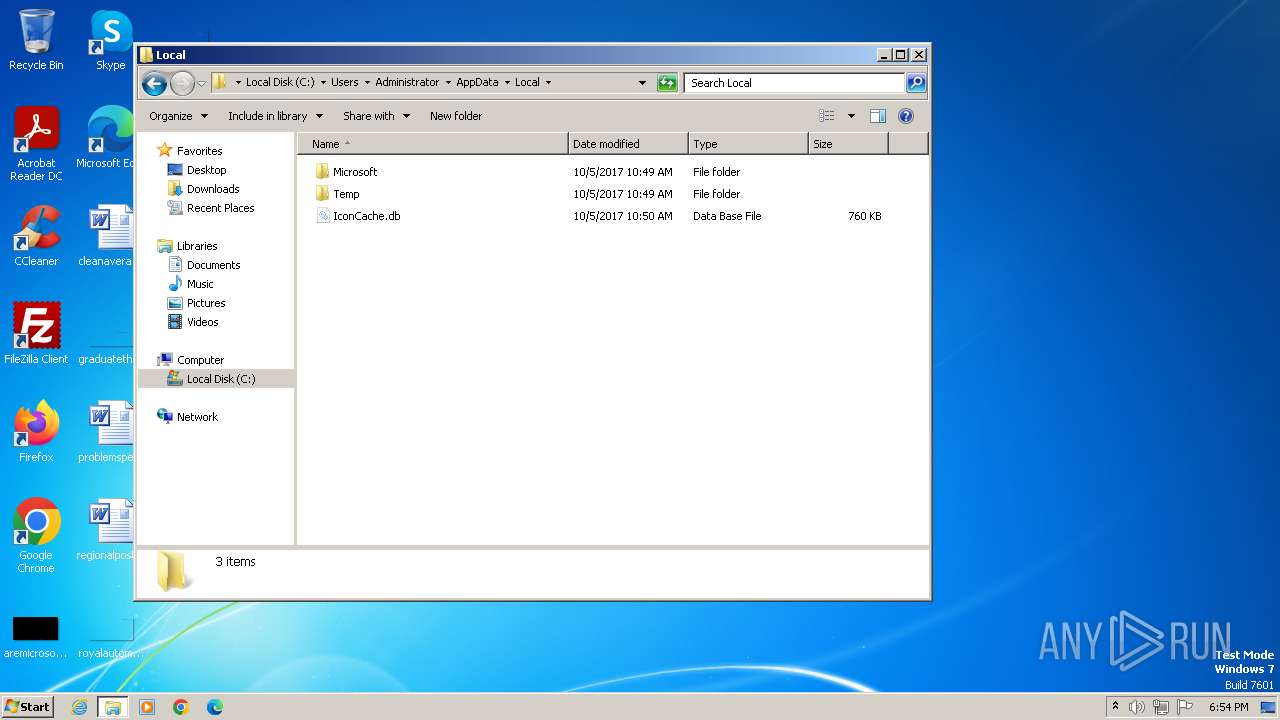
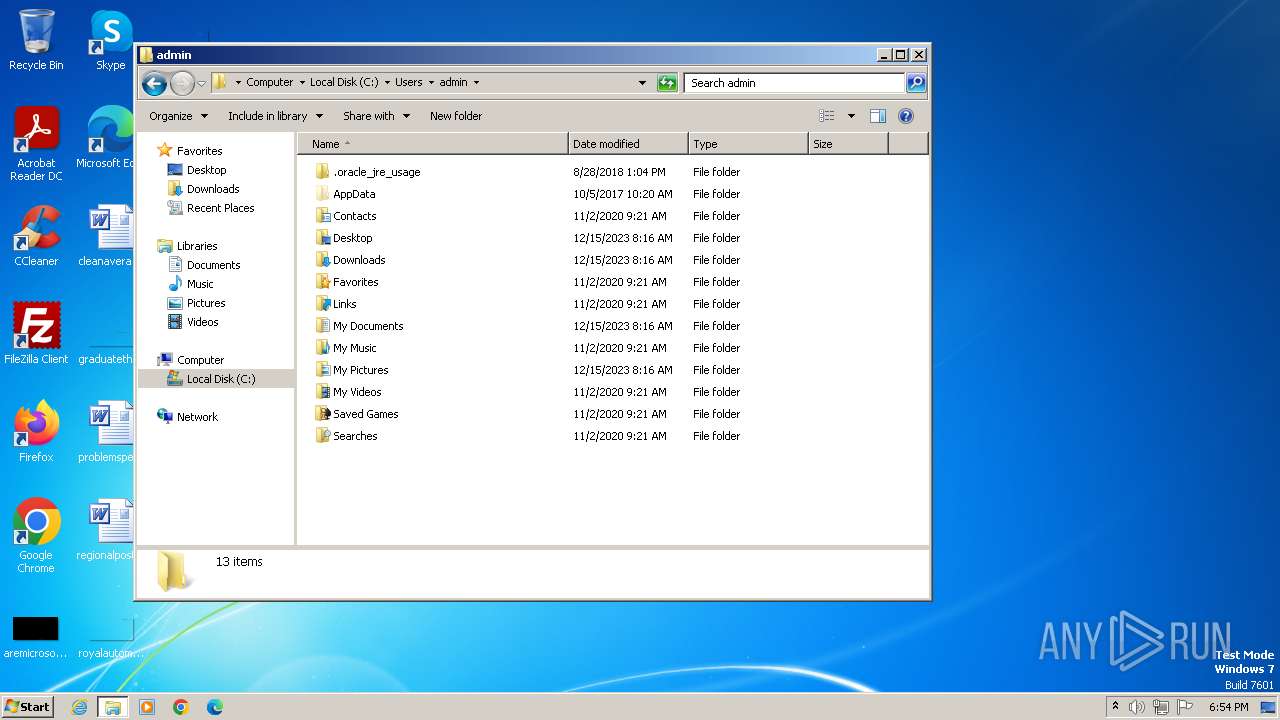
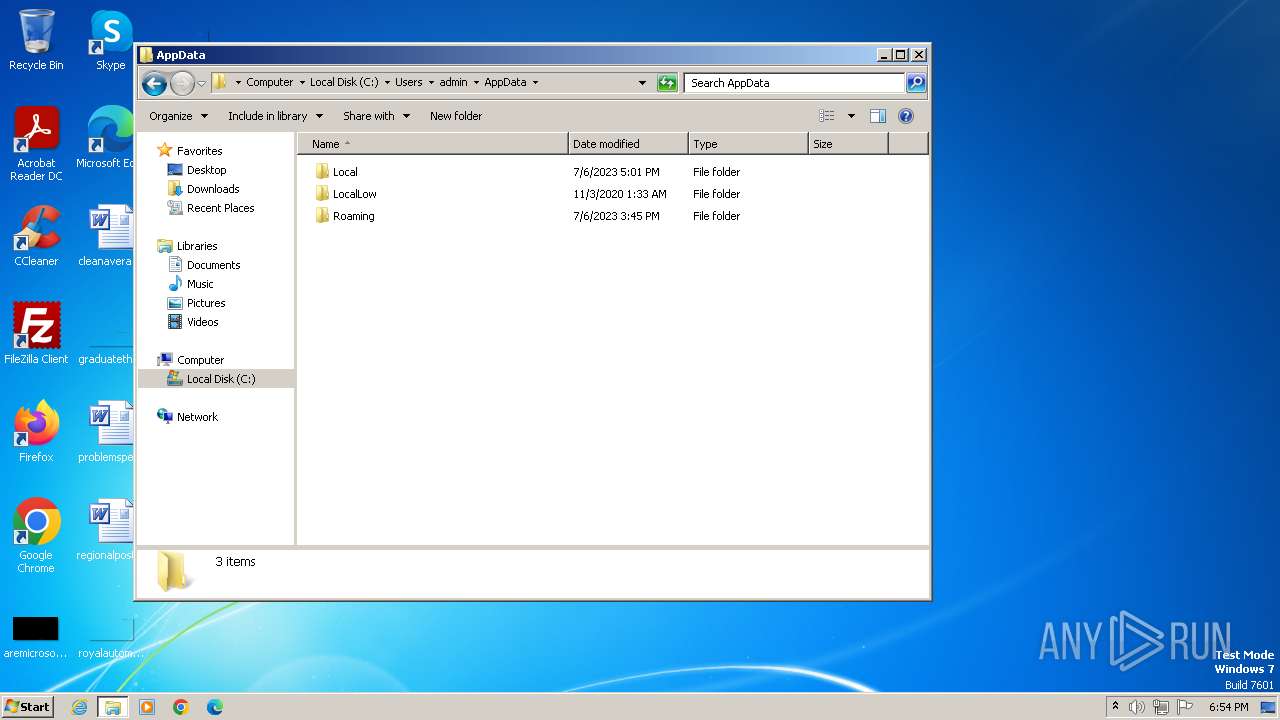
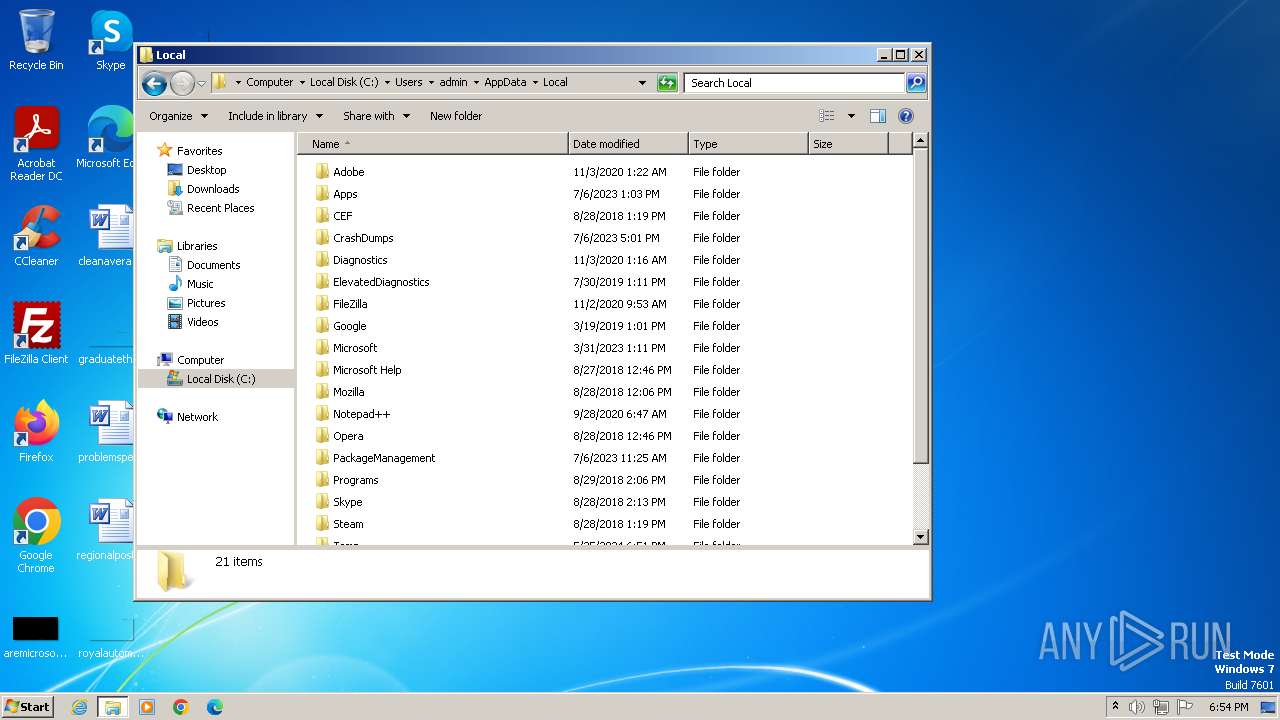
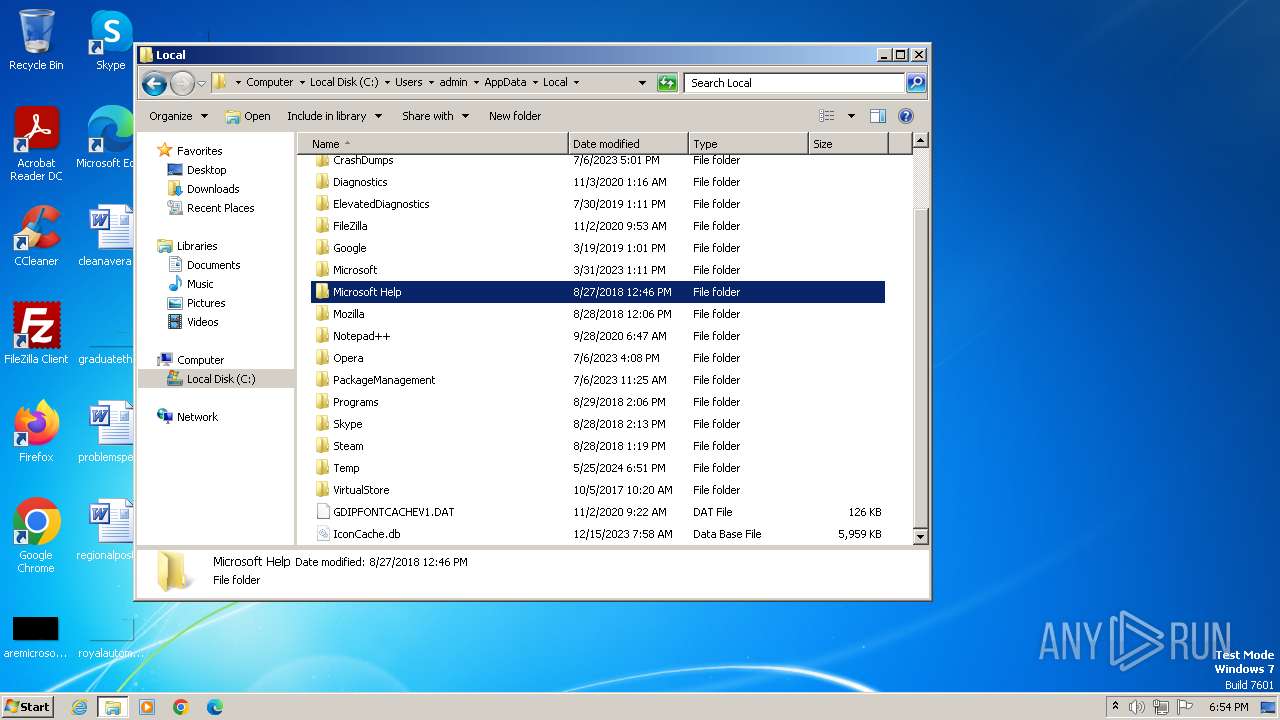
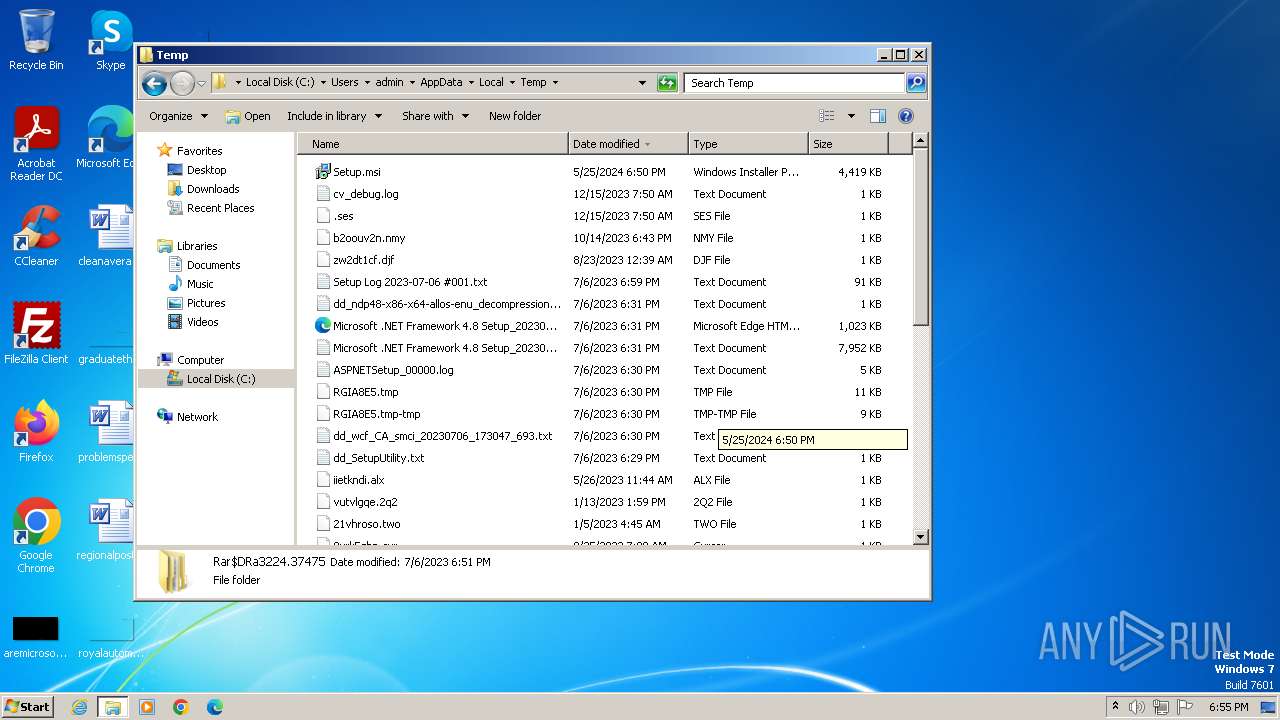
Creates files or folders in the user directory
- msiexec.exe (PID: 3980)
- WorldWideWeb.exe (PID: 2320)
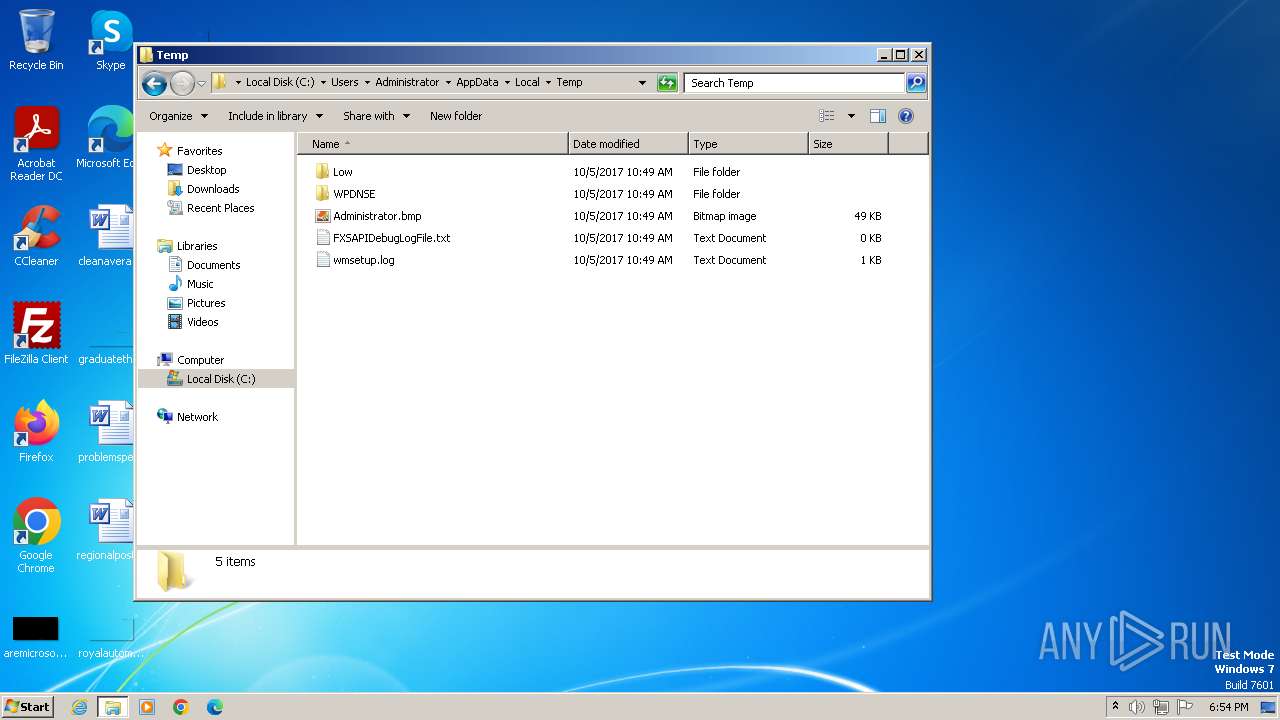
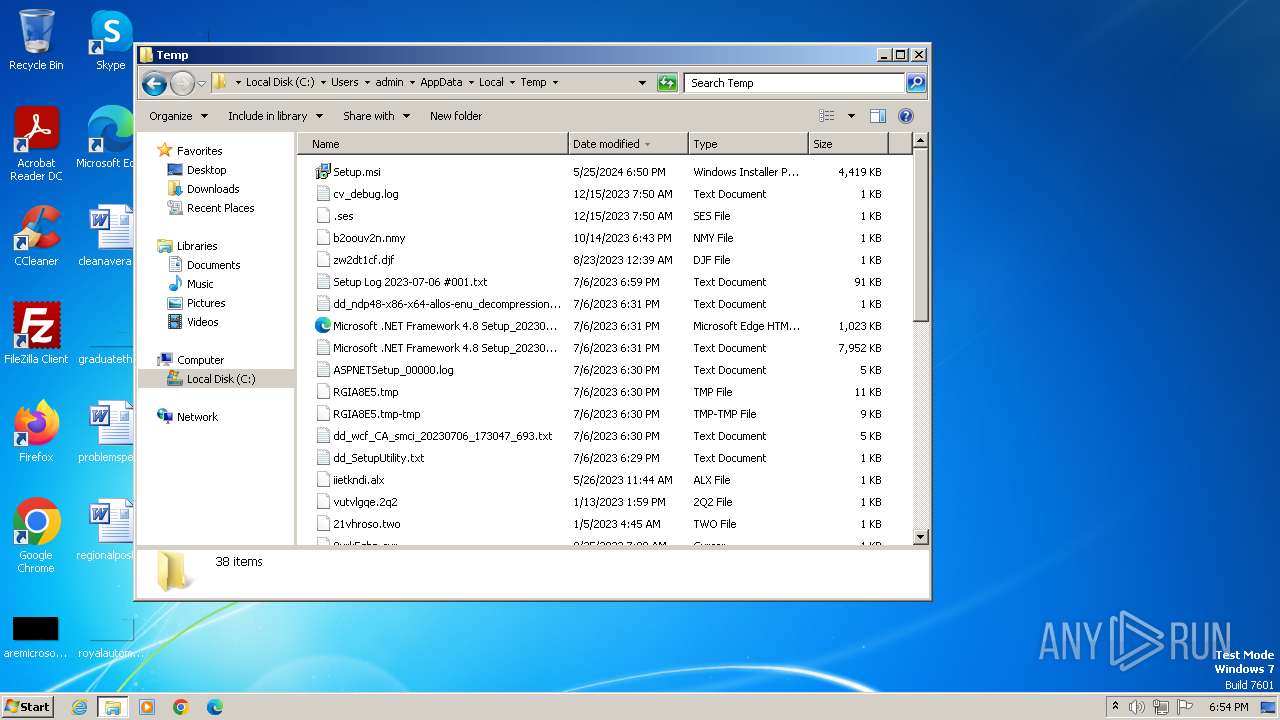
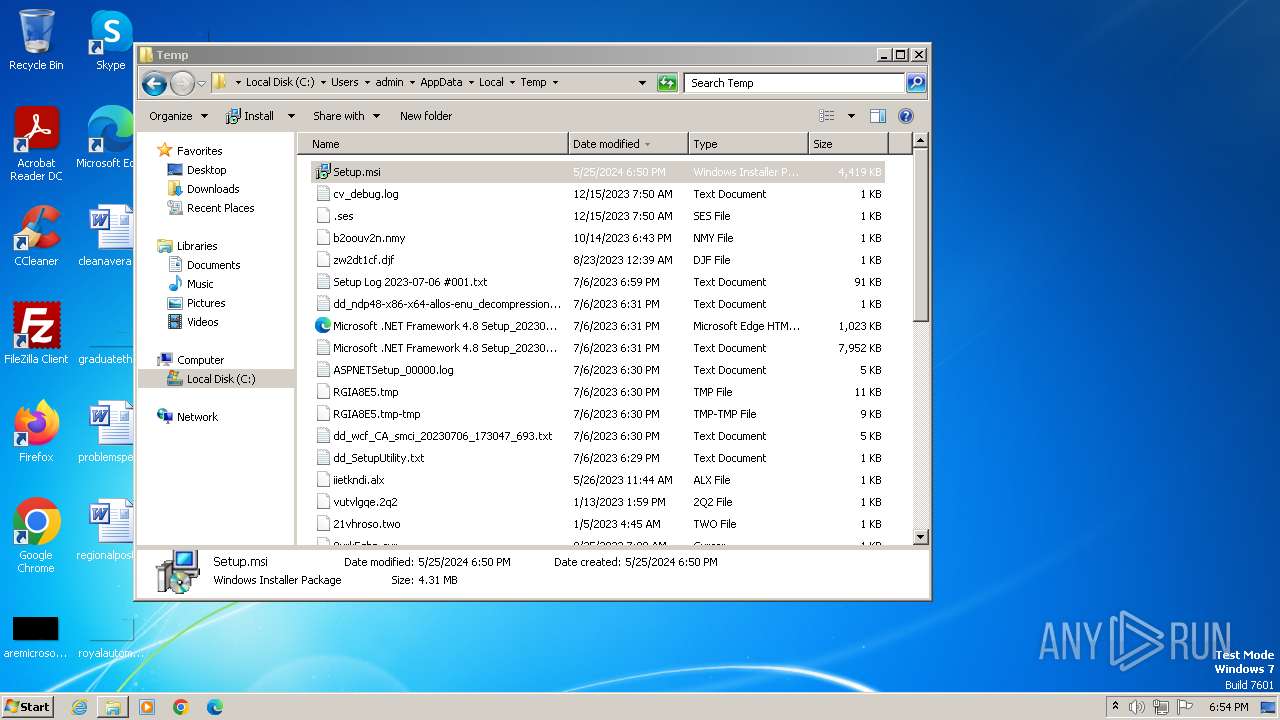
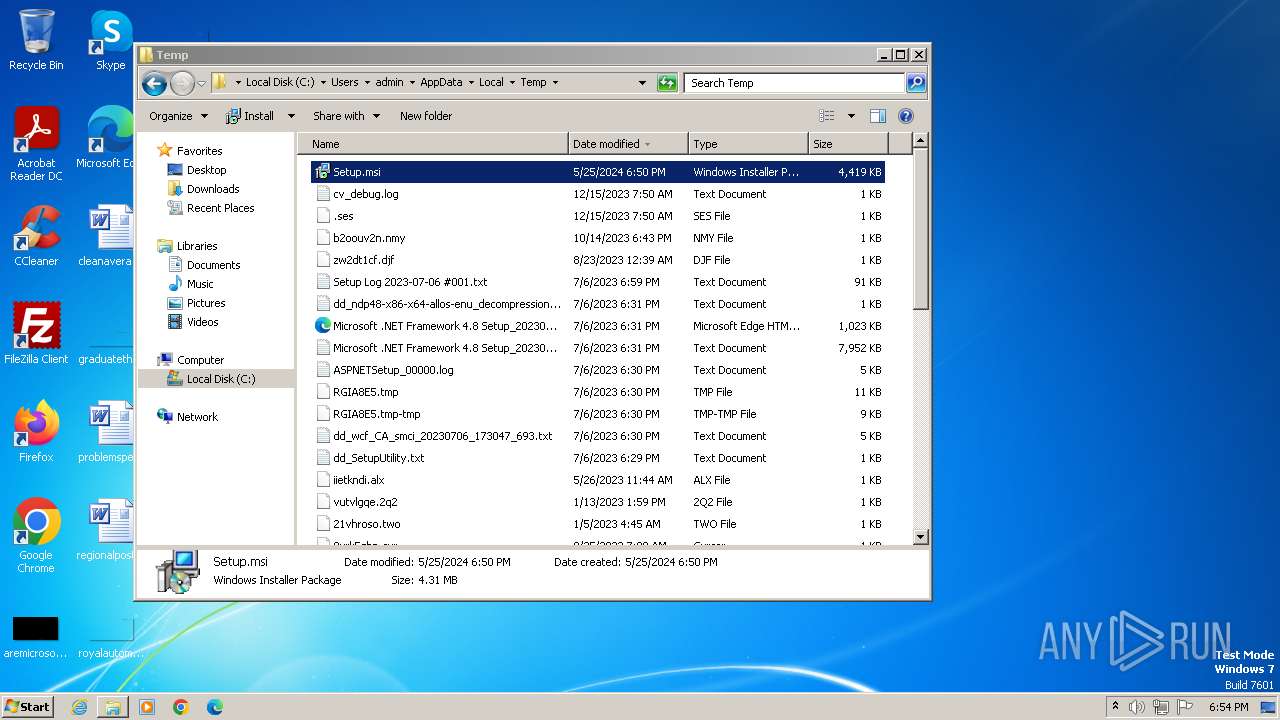
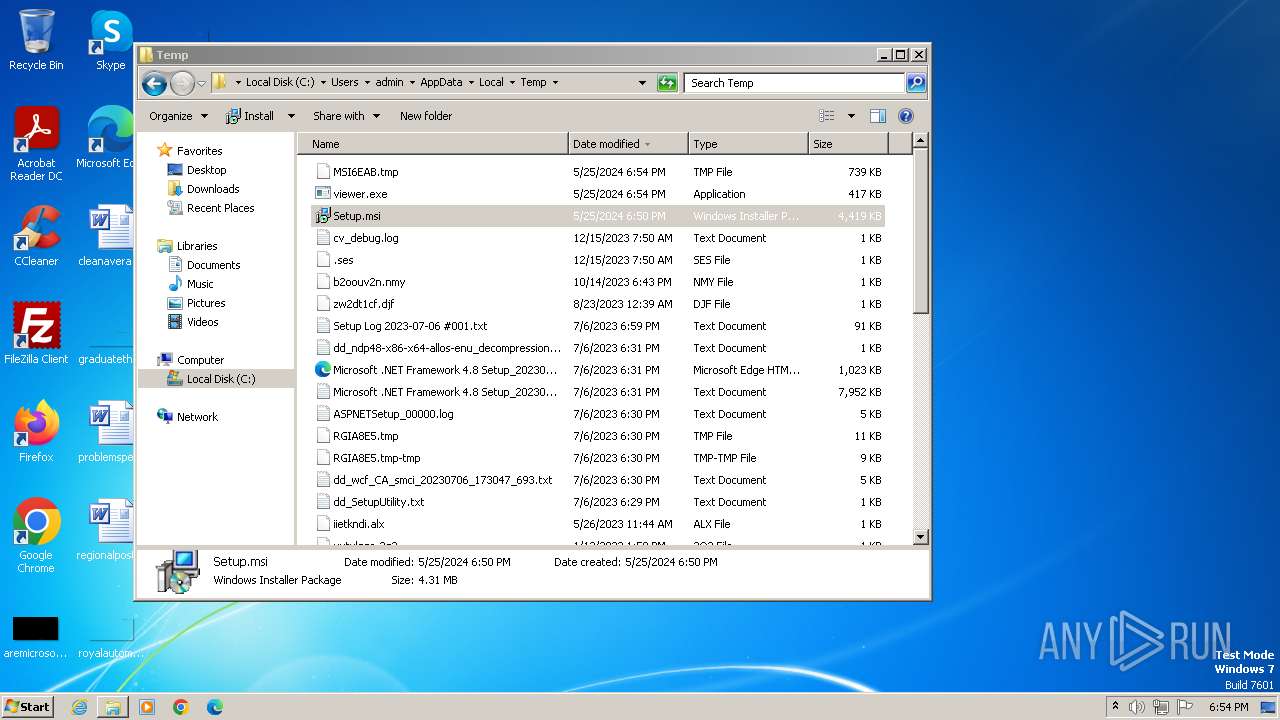
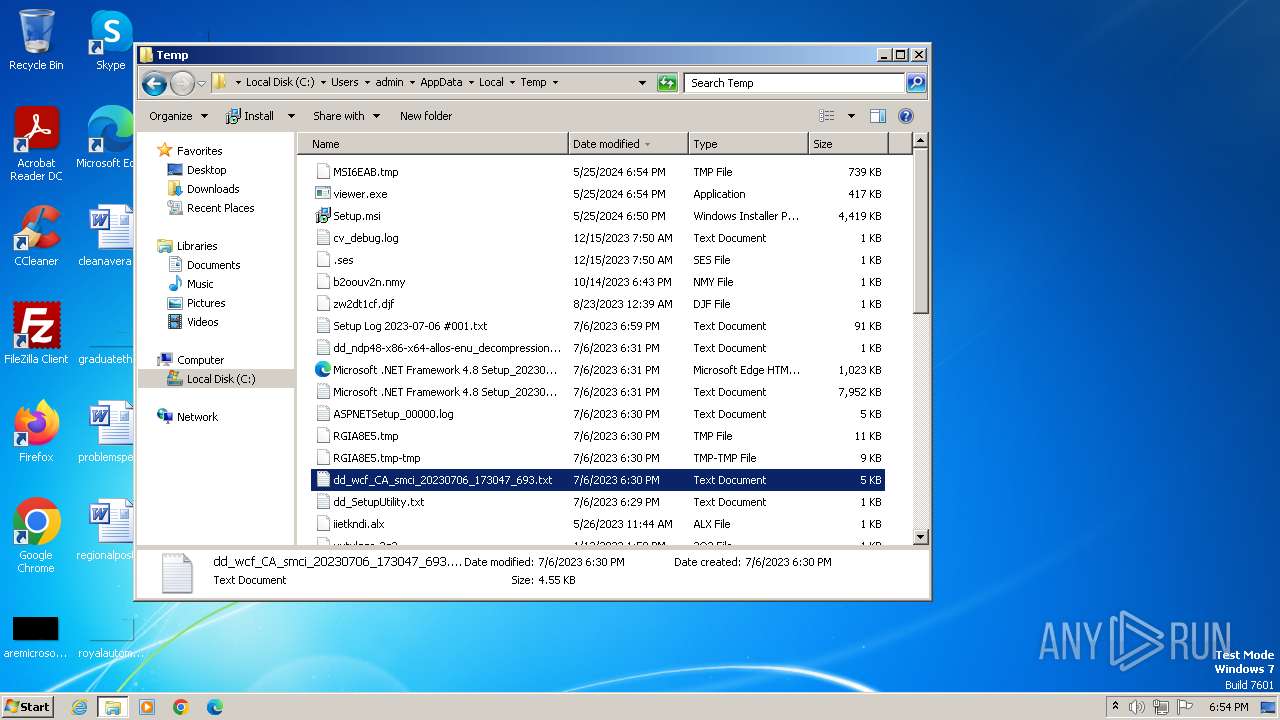
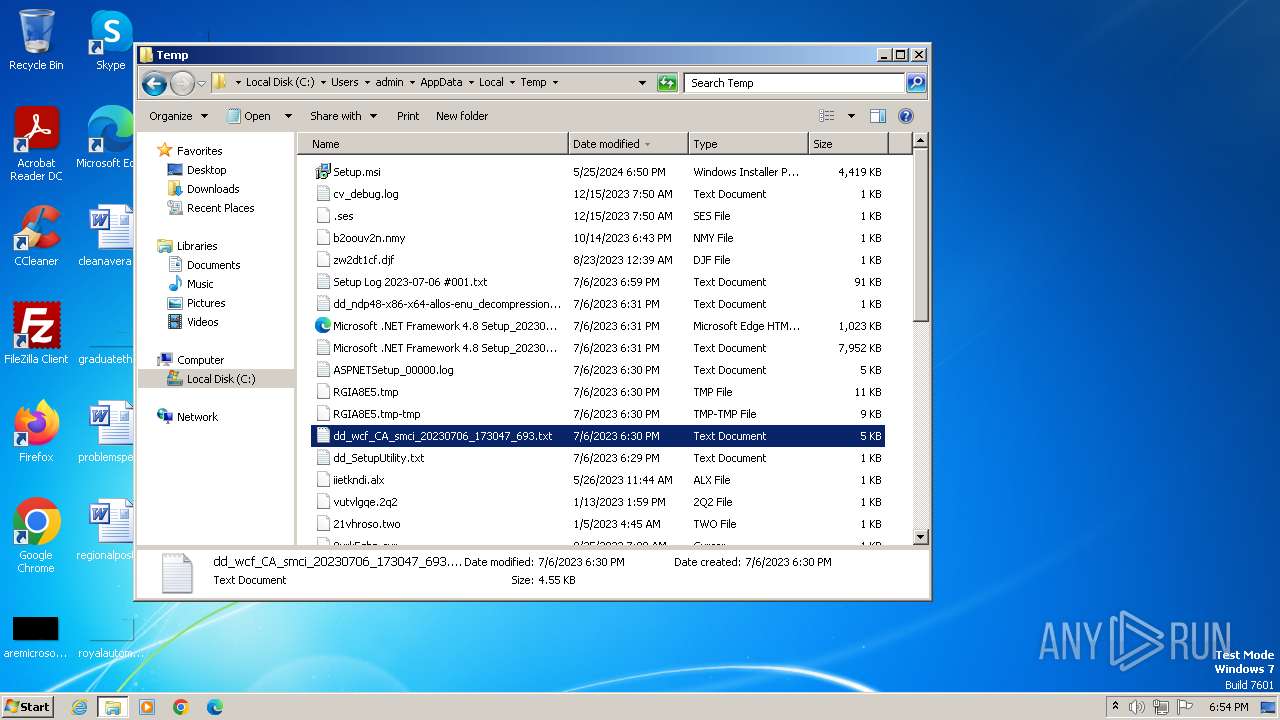
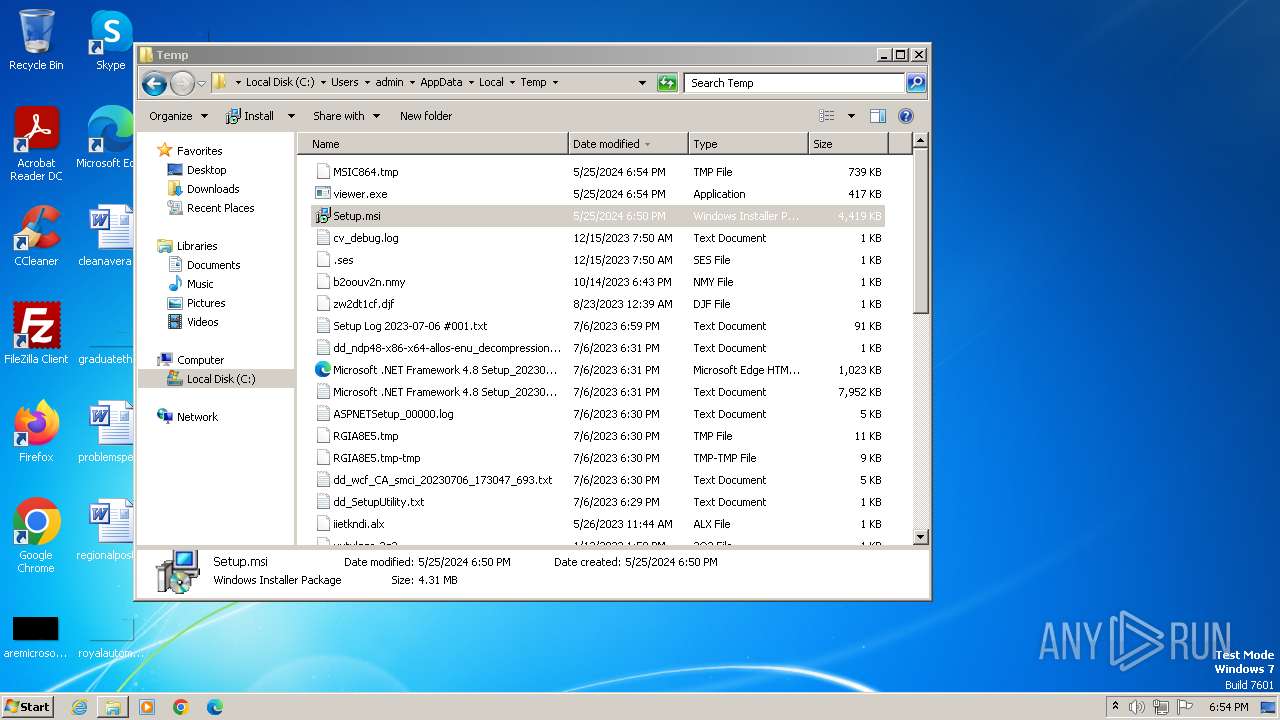
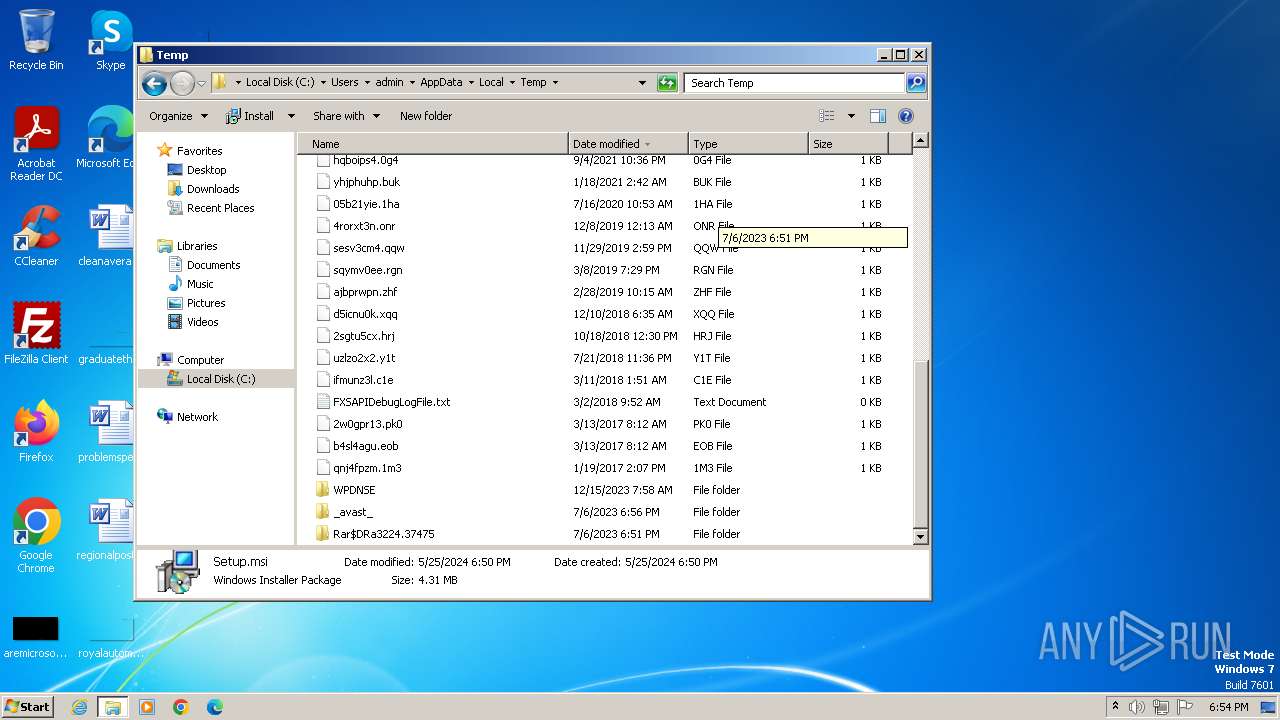
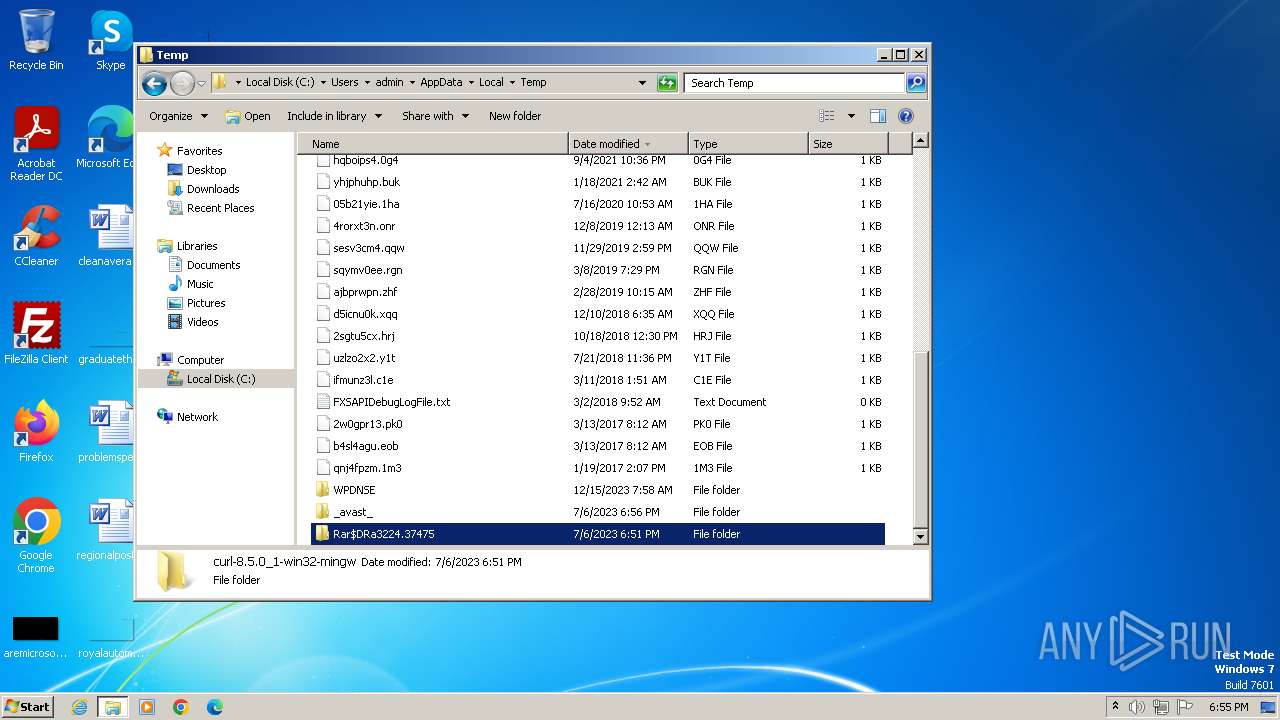
Create files in a temporary directory
- msiexec.exe (PID: 3980)
- msiexec.exe (PID: 1200)
- msiexec.exe (PID: 4060)
- msiexec.exe (PID: 1332)
- msiexec.exe (PID: 3120)
- msiexec.exe (PID: 2756)
- msiexec.exe (PID: 3820)
- msiexec.exe (PID: 2332)
Reads the machine GUID from the registry
- msiexec.exe (PID: 4060)
- msiexec.exe (PID: 1200)
- viewer.exe (PID: 2312)
- msiexec.exe (PID: 1840)
- msiexec.exe (PID: 1332)
- WorldWideWeb.exe (PID: 2320)
- msiexec.exe (PID: 1976)
- msiexec.exe (PID: 3120)
- viewer.exe (PID: 1944)
- msiexec.exe (PID: 1032)
- msiexec.exe (PID: 2756)
- msiexec.exe (PID: 3208)
- WorldWideWeb.exe (PID: 3408)
- msiexec.exe (PID: 3820)
- viewer.exe (PID: 1396)
- msiexec.exe (PID: 2332)
- msiexec.exe (PID: 2448)
- WorldWideWeb.exe (PID: 1136)
- msiexec.exe (PID: 2196)
Executable content was dropped or overwritten
- msiexec.exe (PID: 3980)
- msiexec.exe (PID: 1200)
- msiexec.exe (PID: 4060)
- msiexec.exe (PID: 304)
- msiexec.exe (PID: 3120)
- msiexec.exe (PID: 3116)
- msiexec.exe (PID: 3536)
- msiexec.exe (PID: 3820)
- msiexec.exe (PID: 1292)
- msiexec.exe (PID: 1296)
Drops the executable file immediately after the start
- msiexec.exe (PID: 3980)
- msiexec.exe (PID: 304)
- msiexec.exe (PID: 1296)
- msiexec.exe (PID: 3116)
- msiexec.exe (PID: 3536)
- msiexec.exe (PID: 1292)
Application launched itself
- msiexec.exe (PID: 4060)
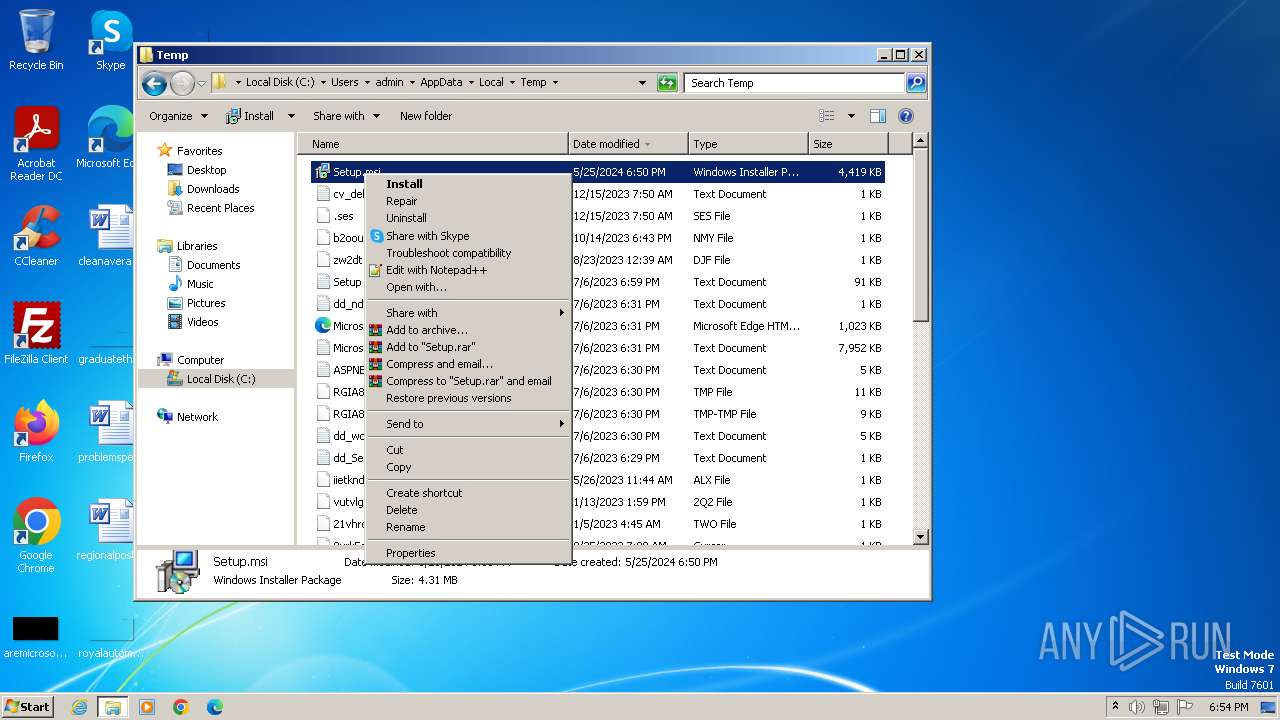
Manual execution by a user
- wmpnscfg.exe (PID: 1640)
- msiexec.exe (PID: 1296)
- explorer.exe (PID: 948)
- msiexec.exe (PID: 3536)
- notepad.exe (PID: 2544)
Reads Environment values
- msiexec.exe (PID: 1332)
- msiexec.exe (PID: 2756)
- msiexec.exe (PID: 2332)
Checks proxy server information
- WorldWideWeb.exe (PID: 2320)
- WorldWideWeb.exe (PID: 3408)
- WorldWideWeb.exe (PID: 1136)
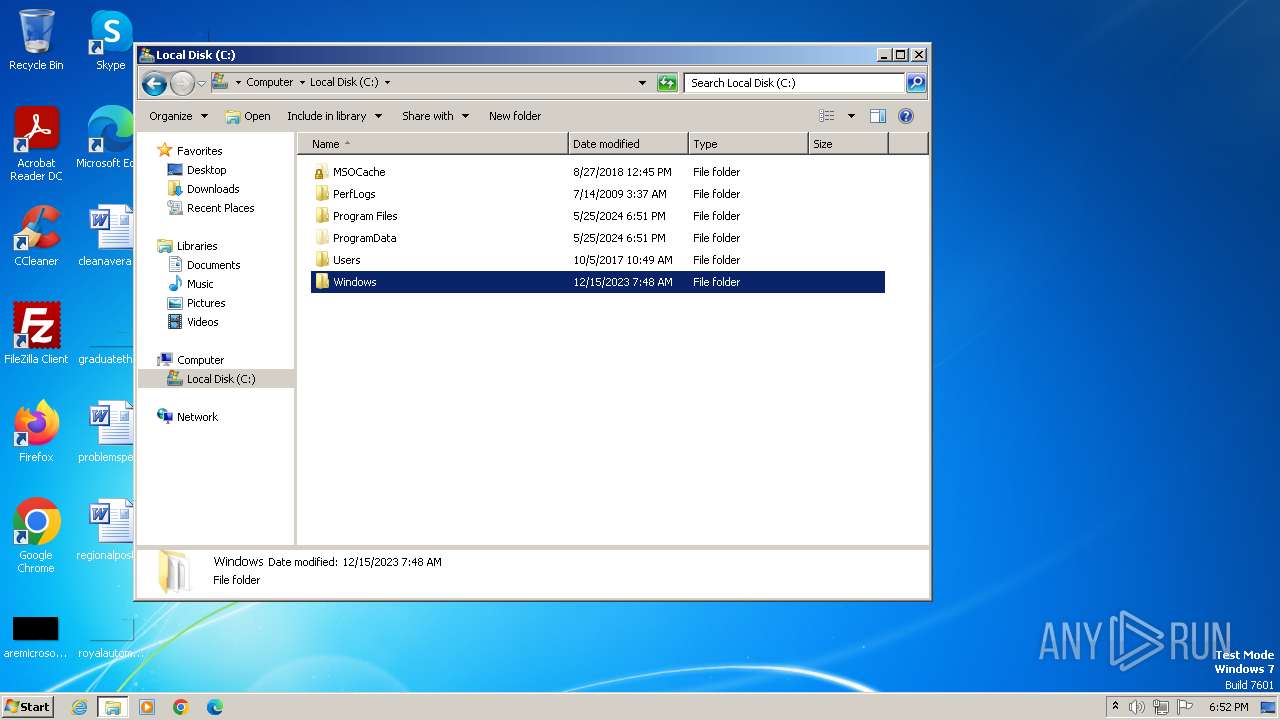
Creates files in the program directory
- WorldWideWeb.exe (PID: 2320)
- WorldWideWeb.exe (PID: 3408)
- WorldWideWeb.exe (PID: 1136)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (81.9) |
|---|---|---|
| .mst | | | Windows SDK Setup Transform Script (9.2) |
| .msp | | | Windows Installer Patch (7.6) |
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| Security: | None |
|---|---|
| CodePage: | Windows Latin 1 (Western European) |
| RevisionNumber: | {C1B83721-FE99-46B4-B042-617BDFBC06F6} |
| Words: | 2 |
| Subject: | World Wide Web |
| Author: | World Wide Solutions |
| LastModifiedBy: | - |
| Software: | World Wide Web |
| Template: | ;1033 |
| Comments: | - |
| Title: | Installation Database |
| Keywords: | Installer, MSI, Database |
| CreateDate: | 2024:05:24 14:47:38 |
| ModifyDate: | 2024:05:24 14:47:38 |
| LastPrinted: | 2024:05:24 14:47:38 |
| Pages: | 450 |
Total processes
90
Monitored processes
31
Malicious processes
10
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
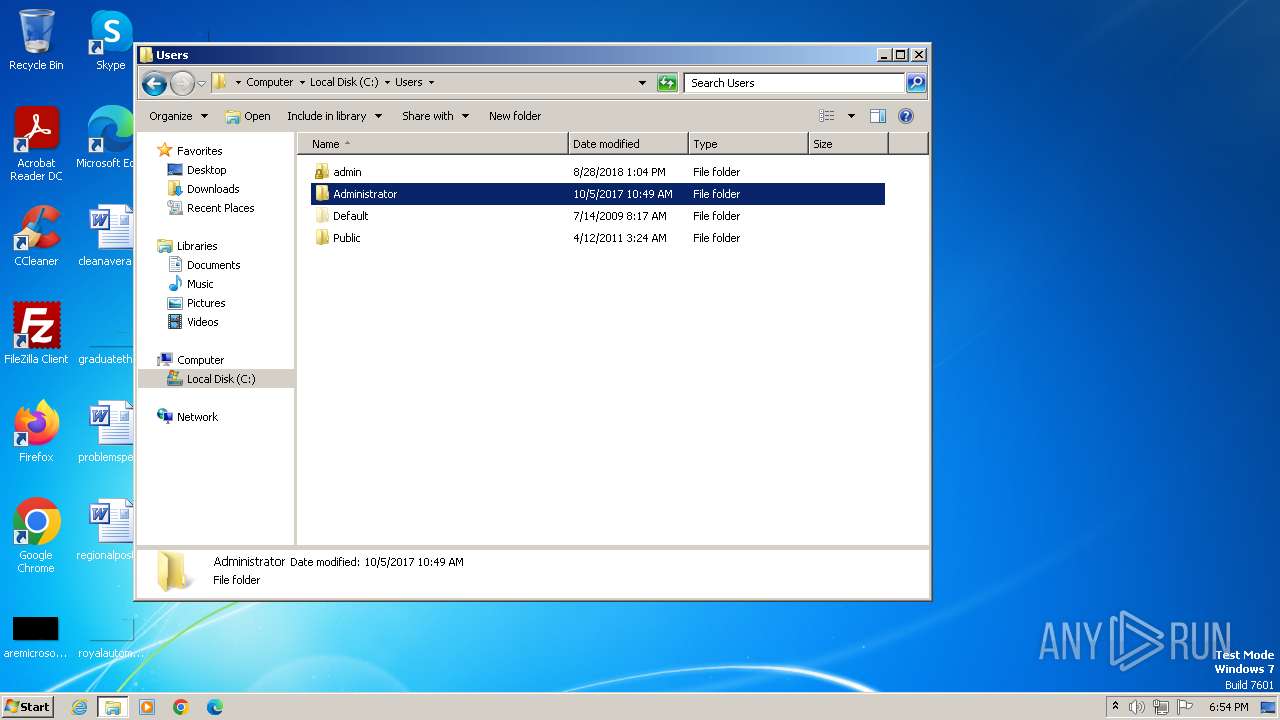
| 304 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\AppData\Local\Temp\Setup.msi" | C:\Windows\System32\msiexec.exe | viewer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 948 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1032 | C:\Windows\system32\MsiExec.exe -Embedding 557E3C08C0C7E1E97D209F15A85C0523 C | C:\Windows\System32\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
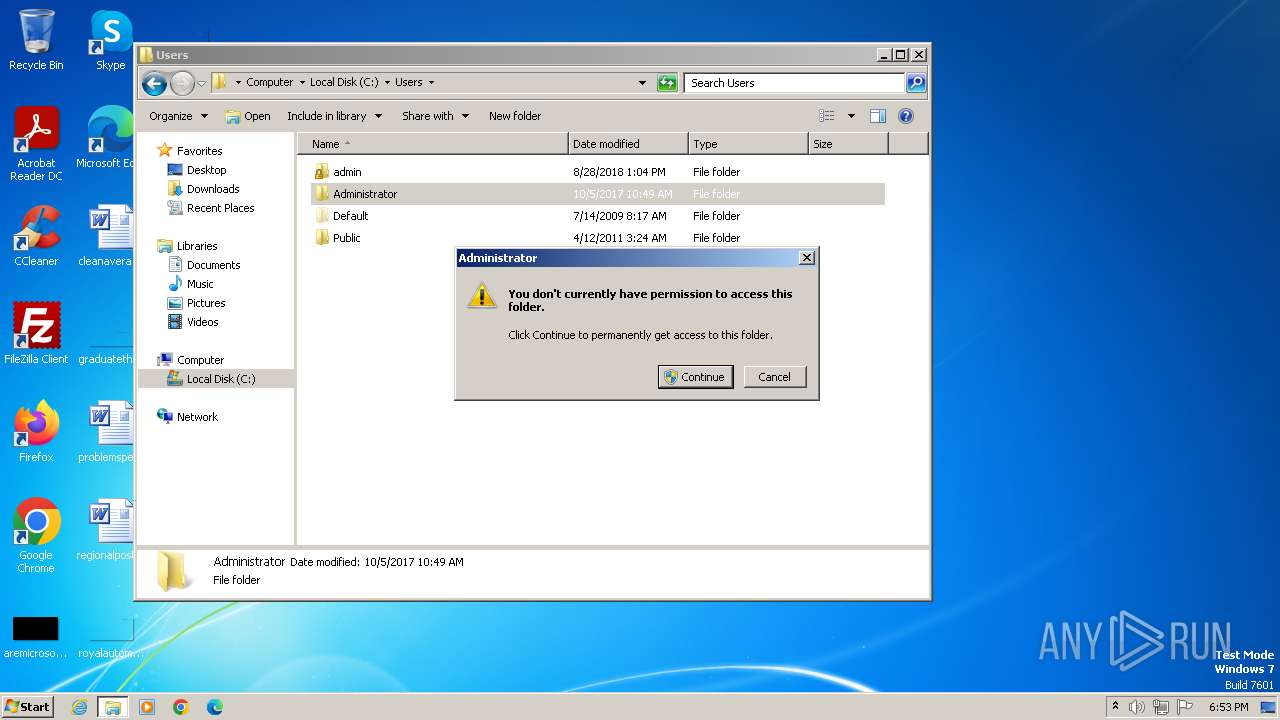
| 1136 | "C:\Program Files\World Wide Solutions\World Wide Web\WorldWideWeb.exe" /silentall -nogui -nofreqcheck | C:\Program Files\World Wide Solutions\World Wide Web\WorldWideWeb.exe | taskeng.exe | ||||||||||||
User: admin Company: World Wide Solutions Integrity Level: HIGH Description: WorldWideWeb 1.0.0.0 Exit code: 3758096401 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1200 | C:\Windows\system32\MsiExec.exe -Embedding 00864D27BAF44E315F0EE1685E572746 C | C:\Windows\System32\msiexec.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1292 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\AppData\Local\Temp\Setup.msi" | C:\Windows\System32\msiexec.exe | viewer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1296 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\AppData\Local\Temp\Setup.msi" | C:\Windows\System32\msiexec.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 1602 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1332 | C:\Windows\system32\MsiExec.exe -Embedding AAC151F5964503DBFB86B6CF2917DD34 | C:\Windows\System32\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1396 | "C:\Users\admin\AppData\Local\Temp\viewer.exe" /RunAsAdmin "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\AppData\Local\Temp\Setup.msi" | C:\Users\admin\AppData\Local\Temp\viewer.exe | msiexec.exe | ||||||||||||
User: admin Company: Caphyon LTD Integrity Level: HIGH Description: File that launches another file Exit code: 0 Version: 21.7.1.0 Modules
| |||||||||||||||
| 1640 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
93 499
Read events
92 490
Write events
941
Delete events
68
Modification events
| (PID) Process: | (3980) msiexec.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1200) msiexec.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1200) msiexec.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1200) msiexec.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1200) msiexec.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1200) msiexec.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2312) viewer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2312) viewer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates |
| Operation: | delete value | Name: | 4EFC31460C619ECAE59C1BCE2C008036D94C84B8 |
Value: | |||
| (PID) Process: | (2312) viewer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\4EFC31460C619ECAE59C1BCE2C008036D94C84B8 |
| Operation: | write | Name: | Blob |
Value: 0F0000000100000030000000C130BBA37B8B350E89FD5ED76B4F78777FEEE220D3B9E729042BEF6AF46E8E4C1B252E32B3080C681BC9A8A1AFDD0A3C0B000000010000004200000047006C006F00620061006C005300690067006E00200043006F006400650020005300690067006E0069006E006700200052006F006F007400200052003400350000006200000001000000200000007B9D553E1C92CB6E8803E137F4F287D4363757F5D44B37D52F9FCA22FB97DF8653000000010000001F000000301D301B060567810C010330123010060A2B0601040182373C0101030200C01400000001000000140000001F00BF46800AFC7839B7A5B443D95650BBCE963B1D00000001000000100000005467B0ADDE8D858E30EE517B1A19ECD909000000010000000C000000300A06082B060105050703030300000001000000140000004EFC31460C619ECAE59C1BCE2C008036D94C84B8200000000100000076050000308205723082035AA00302010202107653FEAC75464893F5E5D74A483A4EF8300D06092A864886F70D01010C05003053310B300906035504061302424531193017060355040A1310476C6F62616C5369676E206E762D73613129302706035504031320476C6F62616C5369676E20436F6465205369676E696E6720526F6F7420523435301E170D3230303331383030303030305A170D3435303331383030303030305A3053310B300906035504061302424531193017060355040A1310476C6F62616C5369676E206E762D73613129302706035504031320476C6F62616C5369676E20436F6465205369676E696E6720526F6F742052343530820222300D06092A864886F70D01010105000382020F003082020A0282020100B62DC530DD7AE8AB903D0372B03A4B991661B2E5FFA5671D371CE57EEC9383AA84F5A3439B98458AB863575D9B00880425E9F868924B82D84BC94A03F3A87F6A8F8A6127BDA144D0FDF53F22C2A34F918DB305B22882915DFB5988050B9706C298F82CA73324EE503A41CCF0A0B07B1D4DD2A8583896E9DFF91B91BB8B102CD2C7431DA20974A180AF7BE6330A0C596B8EBCF4AB5A977B7FAE55FB84F080FE844CD7E2BABDC475A16FBD61107444B29807E274ABFF68DC6C263EE91FE5E00487AD30D30C8D037C55B816705C24782025EB676788ABBA4E34986B7011DE38CAD4BEA1C09CE1DF1E0201D83BE1674384B6CFFC74B72F84A3BFBA09373D676CB1455C1961AB4183F5AC1DEB770D464773CEBFBD9595ED9D2B8810FEFA58E8A757E1B3CFA85AE907259B12C49E80723D93DC8C94DF3B44E62680FCD2C303F08C0CD245D62EE78F989EE604EE426E677E42167162E704F960C664A1B69C81214E2BC66D689486C699747367317A91F2D48C796E7CA6BB7E466F4DC585122BCF9A224408A88537CE07615706171224C0C43173A1983557477E103A45D92DA4519098A9A00737C4651AAA1C6B1677F7A797EC3F1930996F31FBEA40B2E7D2C4FAC9D0F050767459FA8D6D1732BEF8E97E03F4E787759AD44A912C850313022B4280F2896A36CFC84CA0CE9EF8CB8DAD16A7D3DED59B18A7C6923AF18263F12E0E2464DF0203010001A3423040300E0603551D0F0101FF040403020186300F0603551D130101FF040530030101FF301D0603551D0E041604141F00BF46800AFC7839B7A5B443D95650BBCE963B300D06092A864886F70D01010C050003820201005E2BBA749734445F764828408493EE016EE9A1B3D68025E67BE4BC09913D0FFC76ADD7D43020BB8F60D091D61CF29CEF781A2B943202C12496525202D0F3D1FCF29B396E99E11F8E43417D9A1E5BC95D9A84FC26E687F3747226ADA41BD93D3B6A52A03C091E2F1E7BB333B445C7F7ACB1AF9360AD76AEB8B21578EB836AEBFFDB46AB24E5EE02FA901F59C02F5DD6B75DA45C10B77253F8414ECCFA781A254ACAFE85624361C3B437AA81D2F4D63A0FBD8D597E3047DE2B6BE72150335FD4679BD4B8679F3C279903FF85438E7312CA20CDE861D5B166DC17D6396D0FDBCF2337A182894E1C6B3FD6A0CDAA079D3E4226AAD70CEEFA47BF1A527ED17581D3C98A62176D4F88A021A0263EAF6DD962301FE99828AE6E8DD58E4C726693808D2AE355C760679042565C22510FB3DC4E39EE4DDDD91D7810543B6ED0976F03B51EB22373C612B29A64D0FC958524A8FFDFA1B0DC9140AEDF0933ABB9DD92B7F1CC91743B69EB67971B90BFE7C7A06F71BB57BFB78F5AED7A406A16CD80842D2FE102D4249443B315FC0C2B1BFD716FFCCBBC75173A5E83D2C9B32F1BD59C8D7F54FE7E7EE456A387A79DE1595294418F6D5BBE86959AFF1A76DD40D2514A70B41F336323773FEC271E59E40887ED34824A0F3FFEA01DC1F56773458678F4AA29E92787C619DBC61314C33949874DA097E06513F59D7756E9DAB358C73AF2C0CD82 | |||
| (PID) Process: | (2312) viewer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\EnterpriseCertificates\Root\Certificates |
| Operation: | delete value | Name: | 9F6134C5FA75E4FDDE631B232BE961D6D4B97DB6 |
Value: | |||
Executable files
48
Suspicious files
38
Text files
13
Unknown types
0
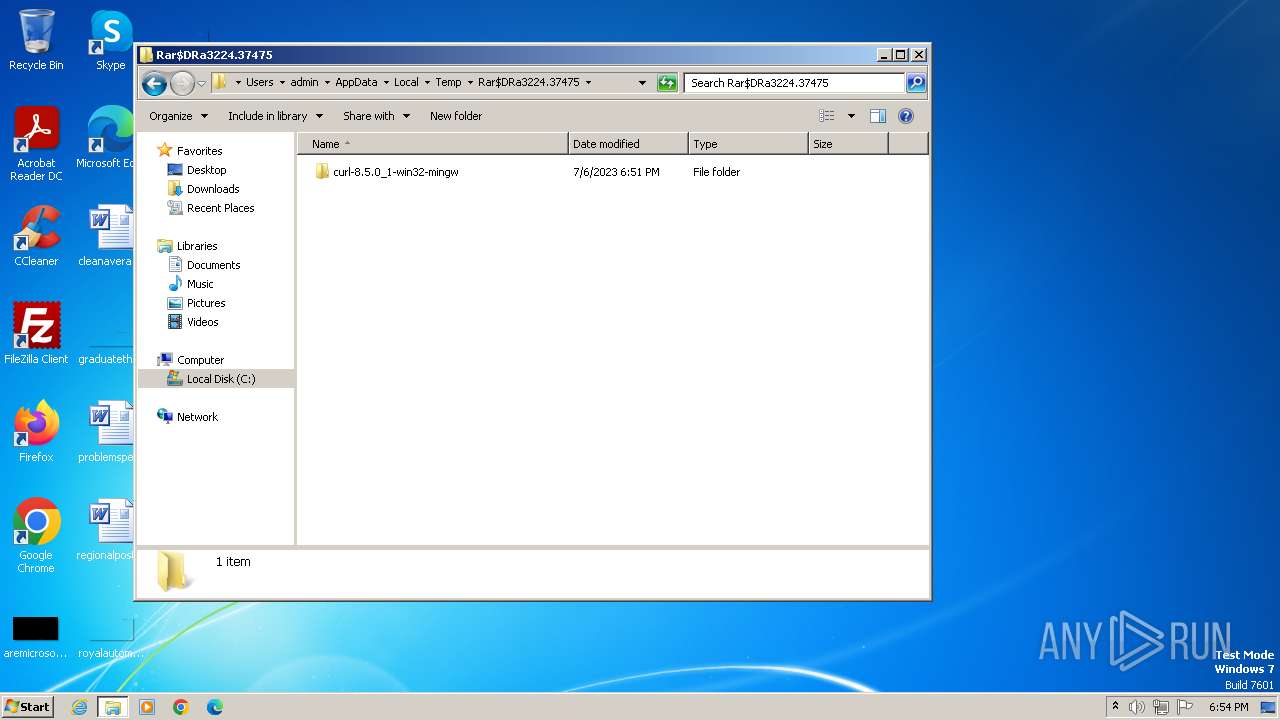
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4060 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 4060 | msiexec.exe | C:\Windows\Installer\105a37.msi | — | |
MD5:— | SHA256:— | |||
| 3980 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\C5C8CC0A7FE31816B4641D0465402560 | binary | |
MD5:E94FB54871208C00DF70F708AC47085B | SHA256:7B9D553E1C92CB6E8803E137F4F287D4363757F5D44B37D52F9FCA22FB97DF86 | |||
| 3980 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI34CF.tmp | executable | |
MD5:EE45C6DFFAF86ED2A76D8F969C390C08 | SHA256:118A551EEF23BF842ED470316AA1A50BF17B6D656652879802D4ACC0184608CA | |||
| 304 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI3D0F.tmp | executable | |
MD5:E6D26B10972BC3B58CCD535E1278CC32 | SHA256:3DBB46EE1950B828C53F2C5DEE3371559327F8C6932E549C3543EAF16846A5DE | |||
| 3980 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\C5C8CC0A7FE31816B4641D0465402560 | binary | |
MD5:4989BD64F26B9B5DD55BDFD5E2E5E4A0 | SHA256:8005FB442BB155357651C78936B49637A88DD8F9236EB38A24DDC70250E958F2 | |||
| 304 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI3B94.tmp | executable | |
MD5:EE45C6DFFAF86ED2A76D8F969C390C08 | SHA256:118A551EEF23BF842ED470316AA1A50BF17B6D656652879802D4ACC0184608CA | |||
| 1200 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\viewer.exe | executable | |
MD5:A71081C3731B6BB7E9784C45B100DD9B | SHA256:10B01AFAF5B7AAD16C6289ACE237BAA9CB7C3B0C254D07383A79BEC189B56B16 | |||
| 1332 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\msi60EE.txt | — | |
MD5:— | SHA256:— | |||
| 1332 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\scr60EF.ps1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
11
DNS requests
4
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3980 | msiexec.exe | GET | 200 | 104.18.21.226:80 | http://secure.globalsign.com/cacert/codesigningrootr45.crt | unknown | — | — | unknown |
3980 | msiexec.exe | GET | 200 | 23.50.131.205:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?440ced30b185b4f4 | unknown | — | — | unknown |
2320 | WorldWideWeb.exe | GET | 200 | 142.250.186.35:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | unknown | — | — | unknown |
2320 | WorldWideWeb.exe | GET | 200 | 142.250.186.35:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFCjJ1PwkYAi7fE%3D | unknown | — | — | unknown |
2320 | WorldWideWeb.exe | GET | 304 | 23.50.131.205:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?39c7a4e1e6501a40 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | unknown |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
3980 | msiexec.exe | 104.18.21.226:80 | secure.globalsign.com | CLOUDFLARENET | — | shared |
3980 | msiexec.exe | 23.50.131.205:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
1088 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2320 | WorldWideWeb.exe | 104.21.23.145:443 | worldwidewebuniverse.com | CLOUDFLARENET | — | unknown |
2320 | WorldWideWeb.exe | 23.50.131.205:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
2320 | WorldWideWeb.exe | 142.250.186.35:80 | ocsp.pki.goog | GOOGLE | US | unknown |
3408 | WorldWideWeb.exe | 104.21.23.145:443 | worldwidewebuniverse.com | CLOUDFLARENET | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
secure.globalsign.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
worldwidewebuniverse.com |
| unknown |
ocsp.pki.goog |
| whitelisted |
Threats
Process | Message |
|---|---|
WorldWideWeb.exe | Logger::SetLogFile( C:\ProgramData\World Wide Solutions\World Wide Web\updates\updater.log ) while OLD path is: |
WorldWideWeb.exe | Logger::SetLogFile( C:\ProgramData\World Wide Solutions\World Wide Web\updates\updater.log ) while OLD path is: |
WorldWideWeb.exe | Logger::SetLogFile( C:\ProgramData\World Wide Solutions\World Wide Web\updates\updater.log ) while OLD path is: |