| URL: | http://www.xxgasm.com |
| Full analysis: | https://app.any.run/tasks/223c14c3-5c54-4530-9824-c1abbd5be3df |
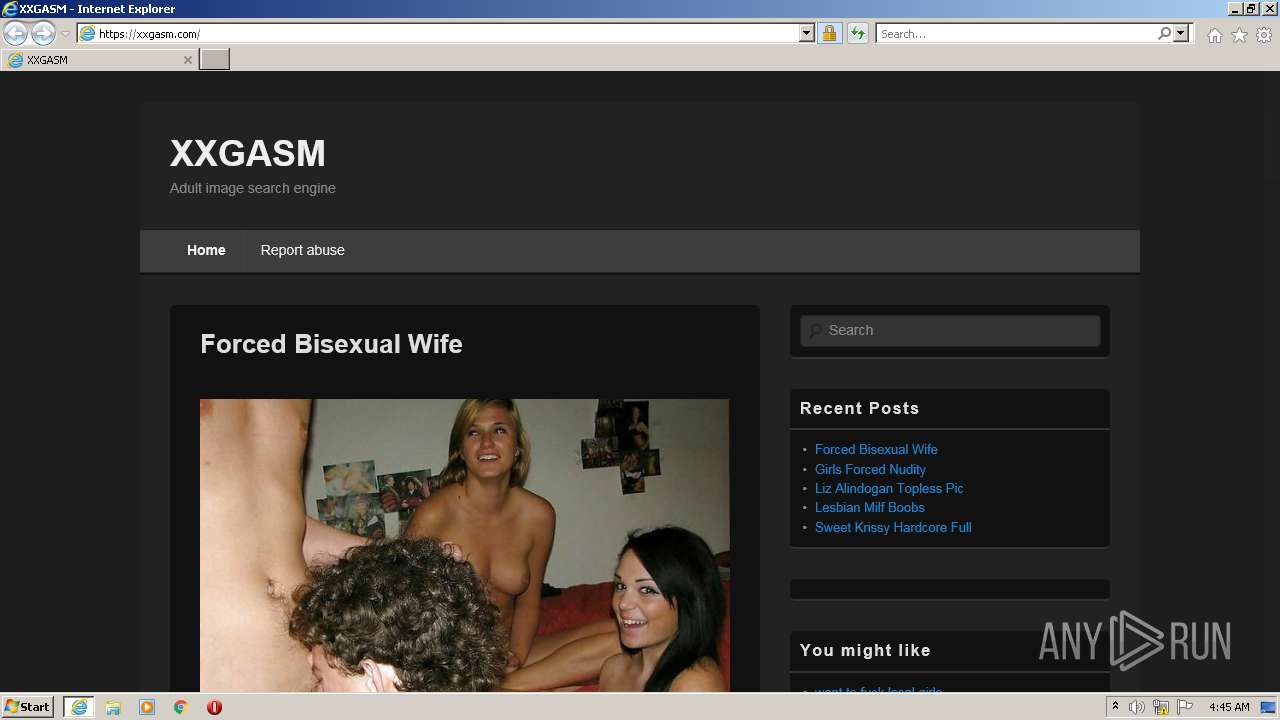
| Verdict: | Malicious activity |
| Analysis date: | February 15, 2022, 04:44:48 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 59AE7E0FB271AAD1E8EFFFCF2CA0CBED |
| SHA1: | AAF189BA7DADC4FFF004721A072CBCD86C32DB1C |
| SHA256: | 8611E87714C41C66277EB07DACA0104A78BDA45124DE9ACD3E36F2715F031964 |
| SSDEEP: | 3:N1KJS4/W2dIn:Cc4/On |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3788)
Checks supported languages
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 2304)
Executed via COM
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 2304)
Reads the computer name
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 2304)
Creates files in the user directory
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 2304)
INFO
Checks supported languages
- iexplore.exe (PID: 3788)
- iexplore.exe (PID: 2188)
Changes internet zones settings
- iexplore.exe (PID: 2188)
Reads the computer name
- iexplore.exe (PID: 2188)
- iexplore.exe (PID: 3788)
Reads settings of System Certificates
- iexplore.exe (PID: 2188)
- iexplore.exe (PID: 3788)
Application launched itself
- iexplore.exe (PID: 2188)
Reads internet explorer settings
- iexplore.exe (PID: 3788)
Creates files in the user directory
- iexplore.exe (PID: 2188)
- iexplore.exe (PID: 3788)
Checks Windows Trust Settings
- iexplore.exe (PID: 3788)
- iexplore.exe (PID: 2188)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2188)
Changes settings of System certificates
- iexplore.exe (PID: 2188)
Reads CPU info
- iexplore.exe (PID: 3788)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
39
Monitored processes
3
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2188 | "C:\Program Files\Internet Explorer\iexplore.exe" "http://www.xxgasm.com" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2304 | C:\Windows\system32\Macromed\Flash\FlashUtil32_32_0_0_453_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_32_0_0_453_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Integrity Level: MEDIUM Description: Adobe� Flash� Player Installer/Uninstaller 32.0 r0 Exit code: 0 Version: 32,0,0,453 Modules
| |||||||||||||||
| 3788 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2188 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
26 643
Read events
26 408
Write events
231
Delete events
4
Modification events
| (PID) Process: | (2188) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2188) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (2188) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30941734 | |||
| (PID) Process: | (2188) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (2188) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30941734 | |||
| (PID) Process: | (2188) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2188) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2188) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2188) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2188) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
39
Text files
147
Unknown types
43
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2188 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | der | |
MD5:0EDB00115298FCB1B0861694D7C2AC93 | SHA256:AC01D5DB93DA4BAE25175BAB4BC8A7DD18FE5643EB6969F17FE8AFA0884EF1EB | |||
| 3788 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:4EE0F8E5EE003DD498FC11558E14EAB3 | SHA256:43E983B92DEBAC4BCAE4E260D246C42044A334DE7F23560D3DF491CDFF52B2BA | |||
| 2188 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | binary | |
MD5:25D531B053A7A7AA407F6903ED53FC79 | SHA256:6F90FC79B6686F17D31E6094620F9728A0B903087A0538FB8D964DE417D3280D | |||
| 2188 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:C1845CEC77F0BA7419C571DCF0DB7654 | SHA256:B71C03985D9F86E965A120398820E2EE195FB3D62BC7D77DF3C9B980E366F752 | |||
| 2188 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 2188 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\favicon[2].ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 2188 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\favicon[1].ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 3788 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:ACAEDA60C79C6BCAC925EEB3653F45E0 | SHA256:6B0CECCF0103AFD89844761417C1D23ACC41F8AEBF3B7230765209B61EEE5658 | |||
| 3788 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\YA6TB67W.htm | html | |
MD5:CD2E0E43980A00FB6A2742D3AFD803B8 | SHA256:BD9DF047D51943ACC4BC6CF55D88EDB5B6785A53337EE2A0F74DD521AEDDE87D | |||
| 3788 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab80E4.tmp | compressed | |
MD5:ACAEDA60C79C6BCAC925EEB3653F45E0 | SHA256:6B0CECCF0103AFD89844761417C1D23ACC41F8AEBF3B7230765209B61EEE5658 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
38
TCP/UDP connections
125
DNS requests
53
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2188 | iexplore.exe | GET | 200 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?70fbc2ab68232dfb | US | compressed | 4.70 Kb | whitelisted |
2188 | iexplore.exe | GET | 200 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?d5a6dd4f3e8c7a9c | US | compressed | 4.70 Kb | whitelisted |
2188 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
3788 | iexplore.exe | GET | 301 | 173.208.189.242:80 | http://www.xxgasm.com/ | US | html | 178 b | suspicious |
3788 | iexplore.exe | GET | 200 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?4e266d7008046ca9 | US | compressed | 59.9 Kb | whitelisted |
3788 | iexplore.exe | GET | 200 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?69331fd87d7f6d72 | US | compressed | 59.9 Kb | whitelisted |
3788 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
3788 | iexplore.exe | GET | 200 | 95.101.89.74:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgMGYx6B%2BgoU9bj5eHy5%2FnvFVA%3D%3D | unknown | der | 503 b | shared |
3788 | iexplore.exe | GET | 200 | 104.89.32.83:80 | http://x1.c.lencr.org/ | NL | der | 717 b | whitelisted |
3788 | iexplore.exe | GET | 200 | 142.250.185.99:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEHI5G%2Bbavp8MCgAAAAEz%2BiM%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3788 | iexplore.exe | 142.250.184.225:443 | 4.bp.blogspot.com | Google Inc. | US | whitelisted |
3788 | iexplore.exe | 173.208.189.242:80 | www.xxgasm.com | WholeSale Internet, Inc. | US | suspicious |
2188 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2188 | iexplore.exe | 209.197.3.8:80 | ctldl.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
2188 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3788 | iexplore.exe | 173.208.189.242:443 | www.xxgasm.com | WholeSale Internet, Inc. | US | suspicious |
3788 | iexplore.exe | 209.197.3.8:80 | ctldl.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
3788 | iexplore.exe | 104.89.32.83:80 | x1.c.lencr.org | Akamai Technologies, Inc. | NL | suspicious |
3788 | iexplore.exe | 185.94.236.244:443 | adserver.juicyads.com | Mojohost B.v. | NL | unknown |
3788 | iexplore.exe | 143.204.2.47:443 | js.juicyads.com | — | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.xxgasm.com |
| unknown |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
xxgasm.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
r3.o.lencr.org |
| shared |
js.juicyads.com |
| whitelisted |
adserver.juicyads.com |
| suspicious |