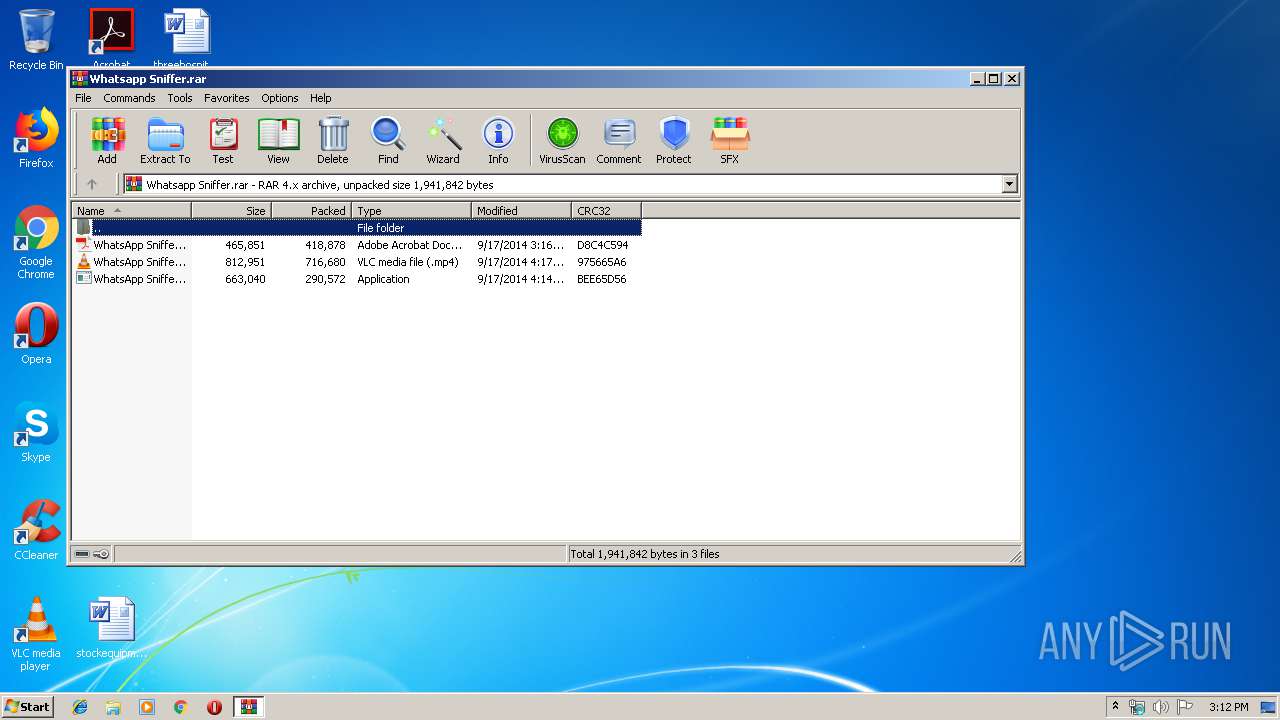
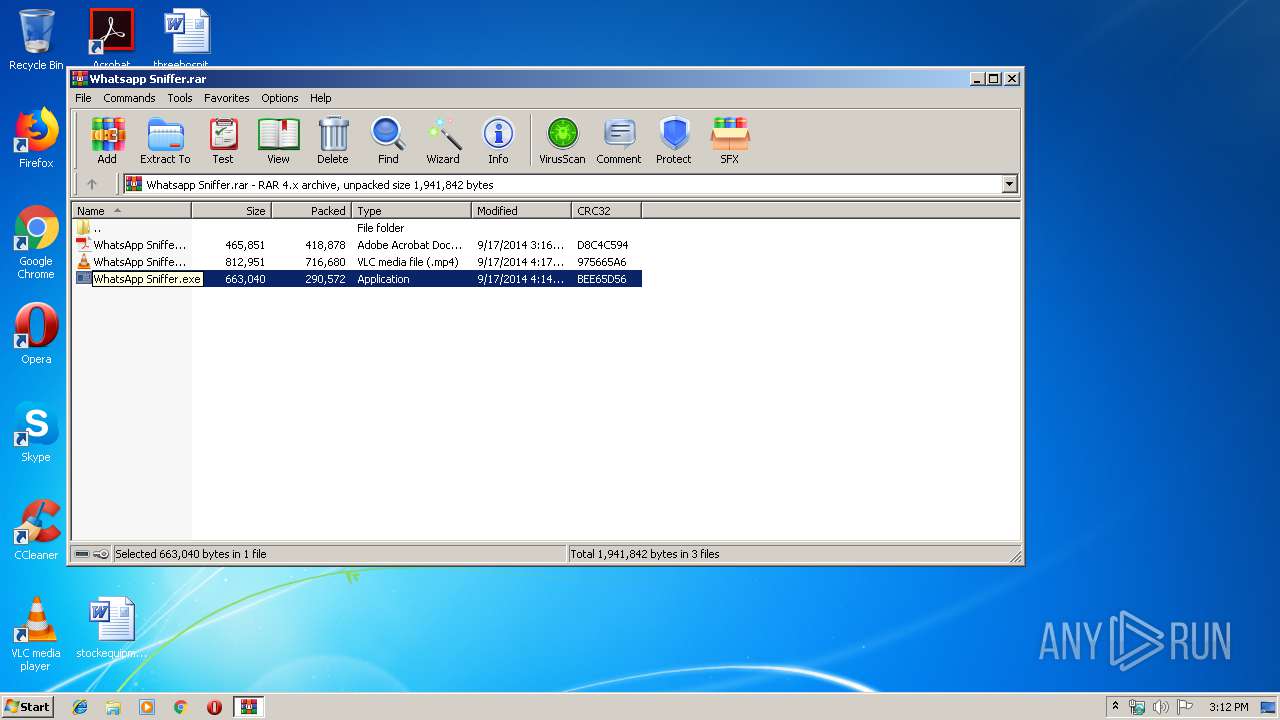
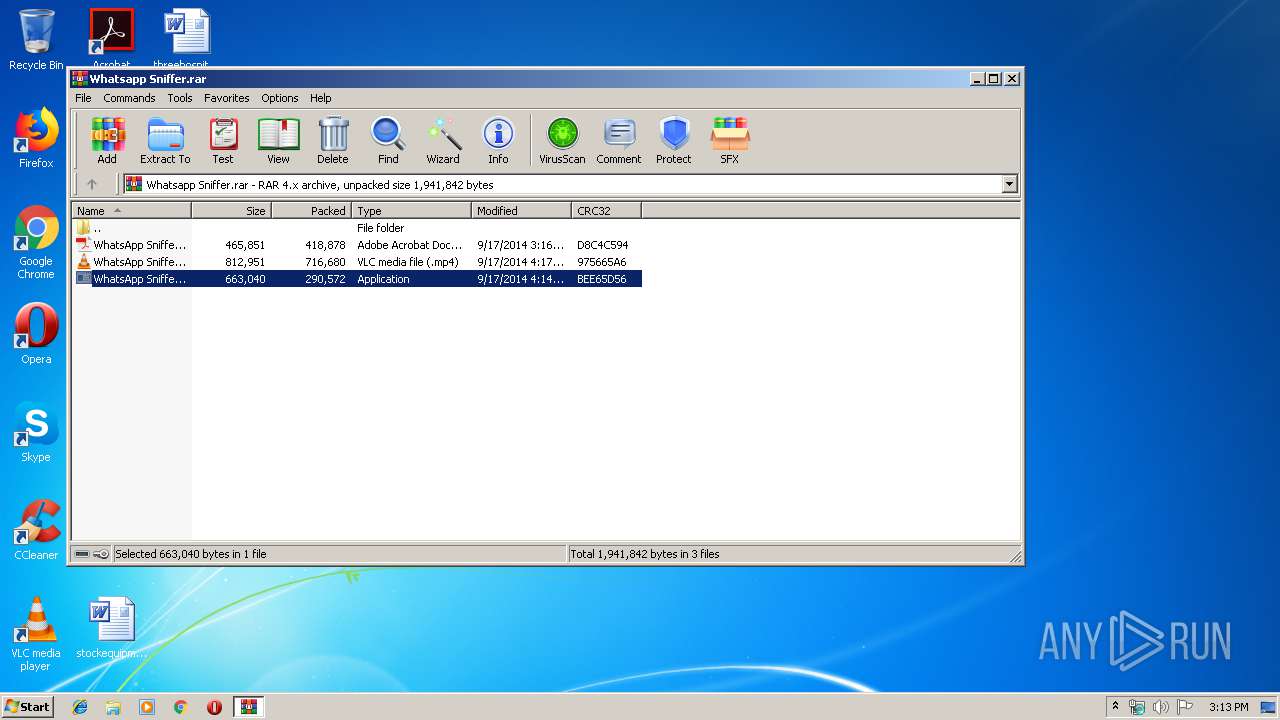
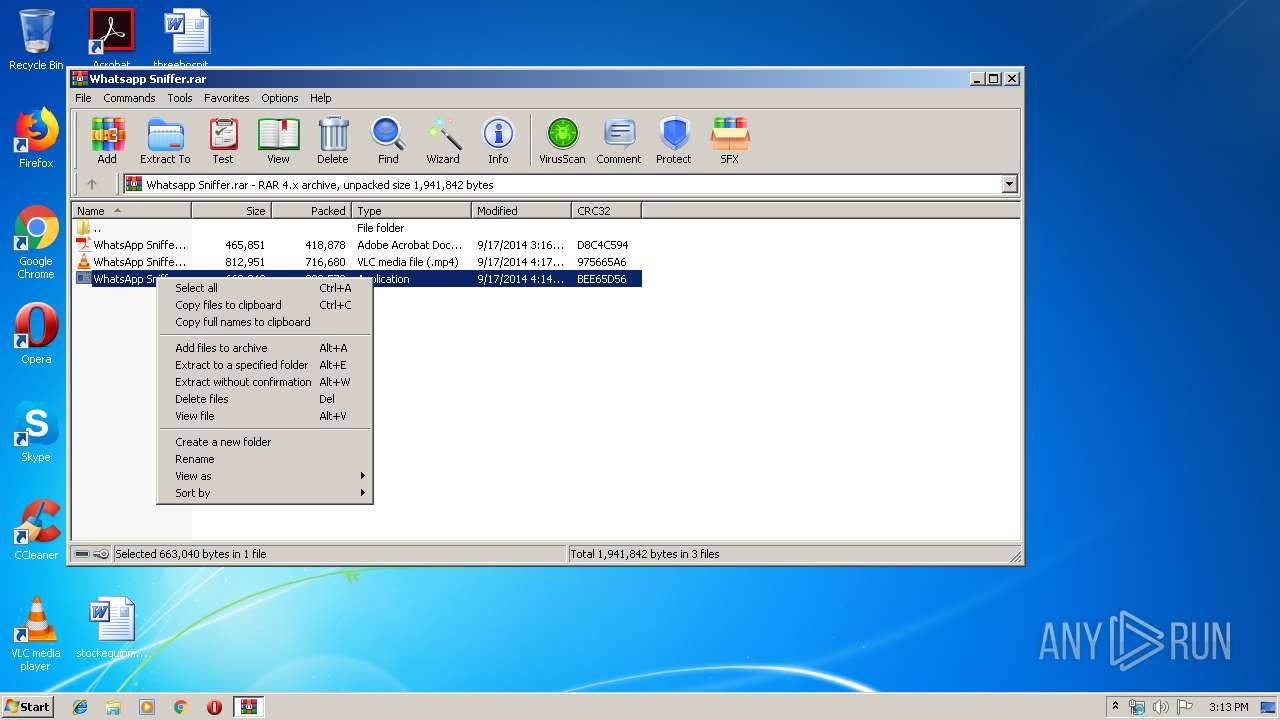
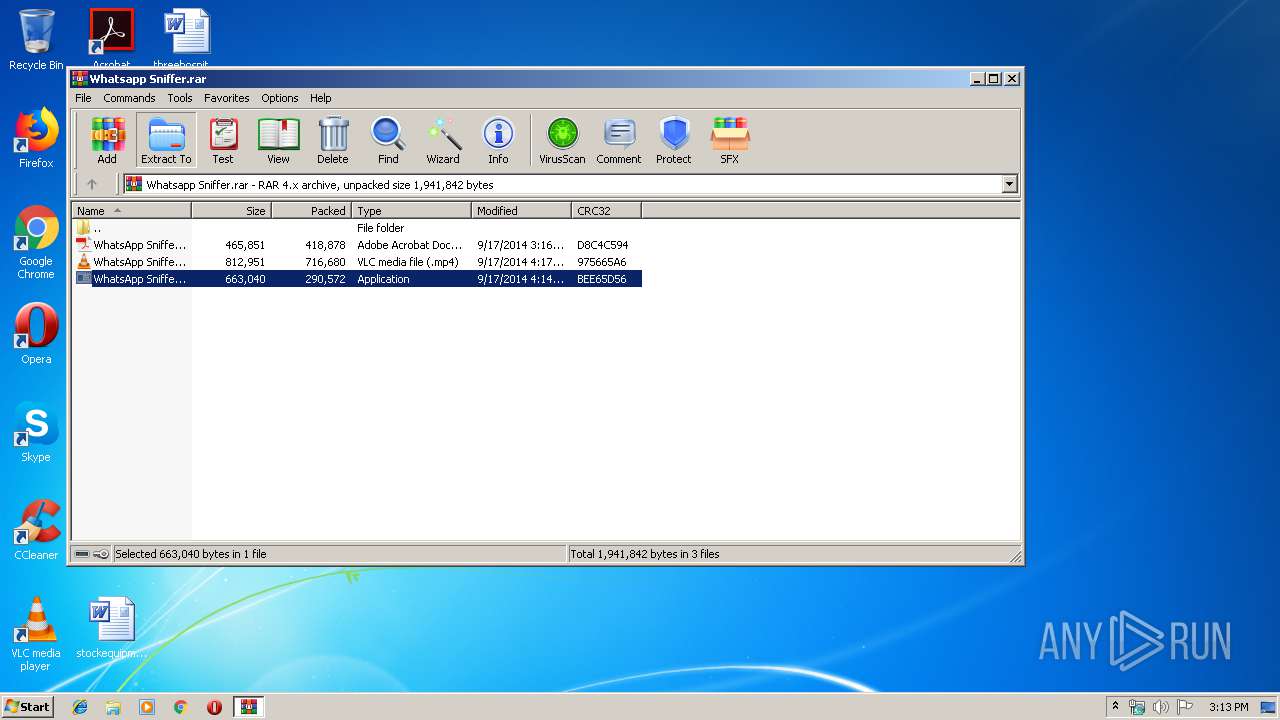
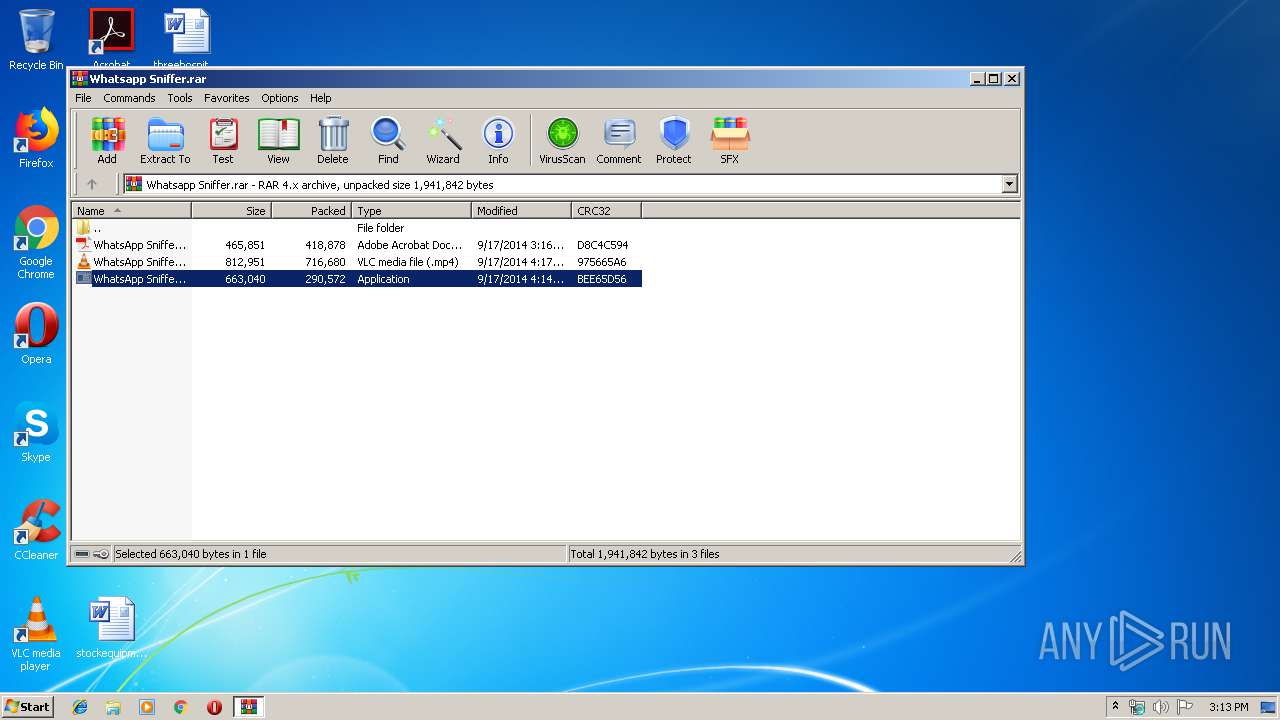
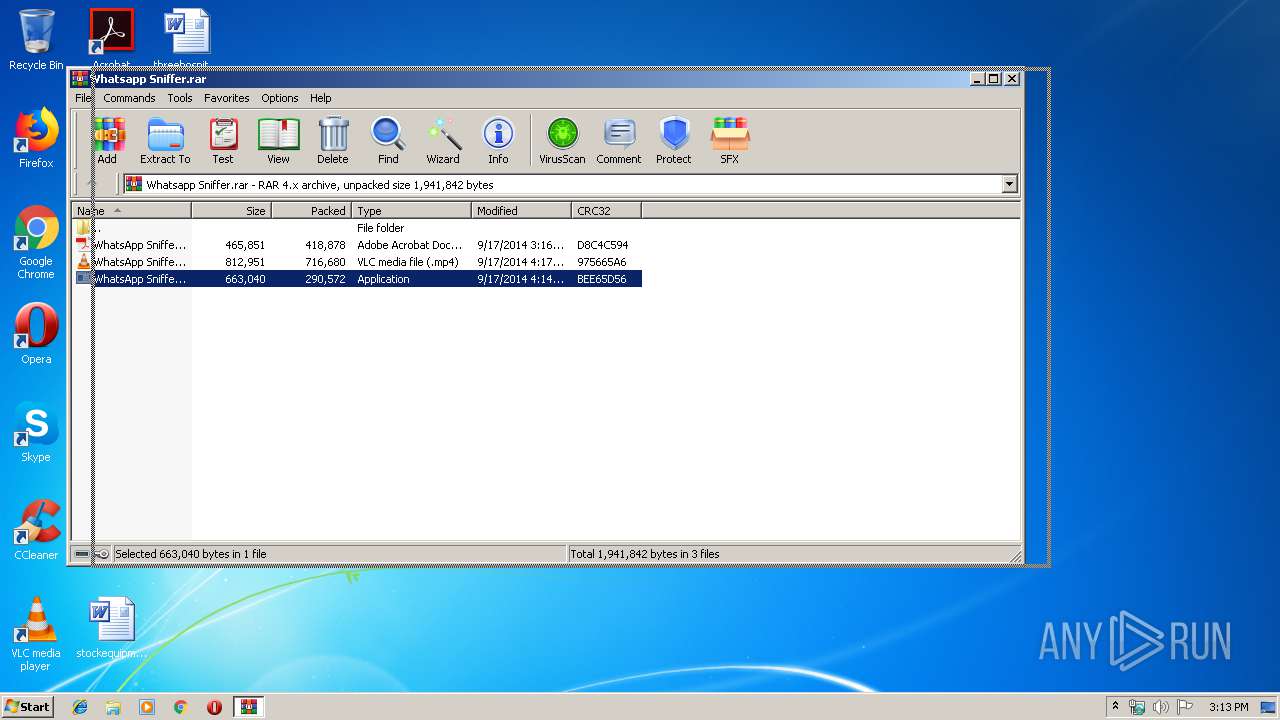
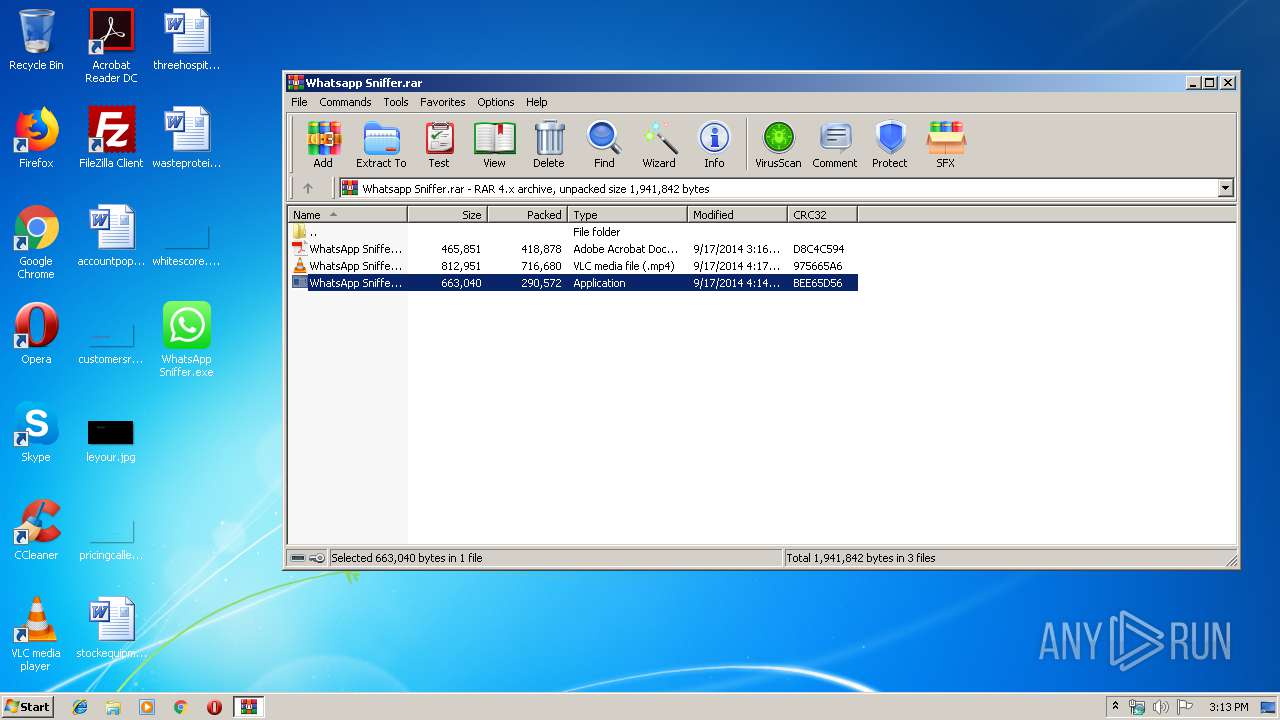
| File name: | Whatsapp Sniffer.rar |
| Full analysis: | https://app.any.run/tasks/5f9f5414-c315-4887-8cda-4a2de80ae74f |
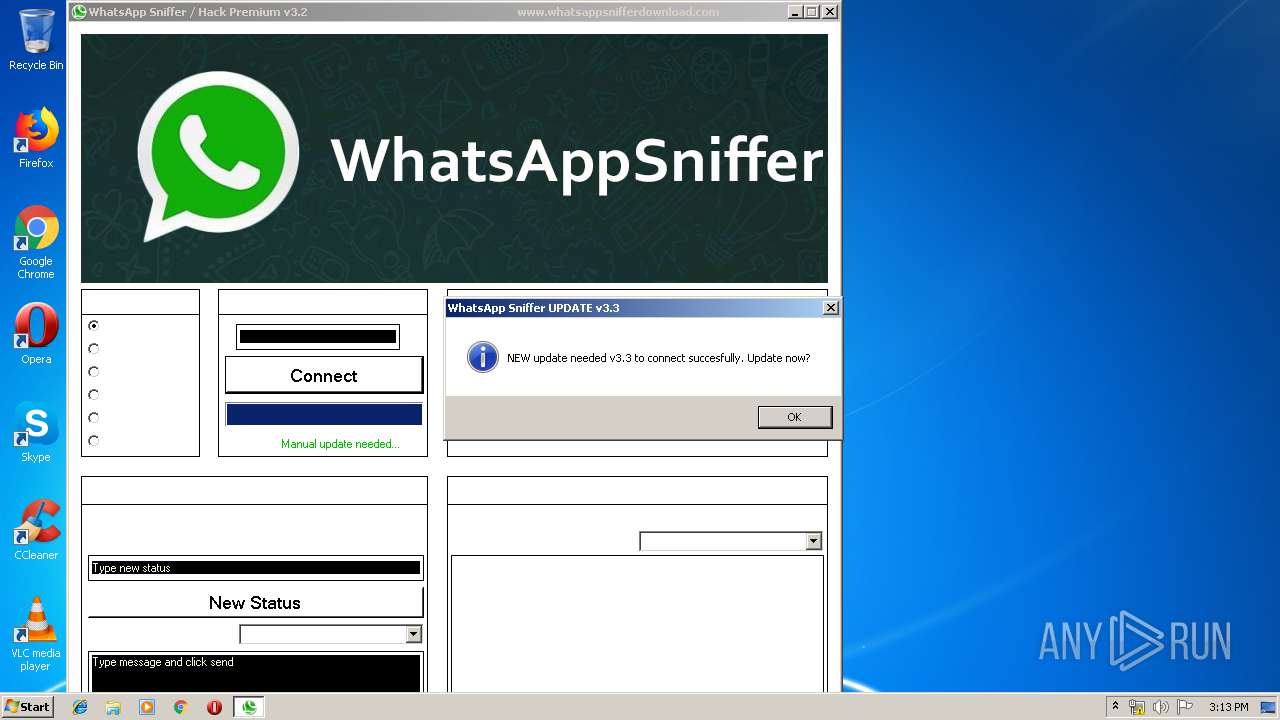
| Verdict: | Malicious activity |
| Analysis date: | July 09, 2019, 14:12:29 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v4, os: Win32 |
| MD5: | 60CBF8F2296CB0C6E87574F75E6193AC |
| SHA1: | 8ACDBA3002CA715CFD9B103DD1A76B9D4D1411A3 |
| SHA256: | 860E08CFABBCF10AF48ED75B4B5E23214C2F7F5DB45C4A07C93B04D60F75BAF3 |
| SSDEEP: | 24576:kZIbVtLsF7frWV/X8hvNeXgCIpbT3awk8qqDxJbYoOimljffA8N+2l1NXl21Y/tA:kZ5r4Qv8wzbTlB/YogljjxnFl21ytb1O |
MALICIOUS
Application was dropped or rewritten from another process
- WhatsApp Sniffer.exe (PID: 3104)
- WhatsApp Sniffer.exe (PID: 3936)
SUSPICIOUS
Creates files in the user directory
- WhatsApp Sniffer.exe (PID: 3936)
Executable content was dropped or overwritten
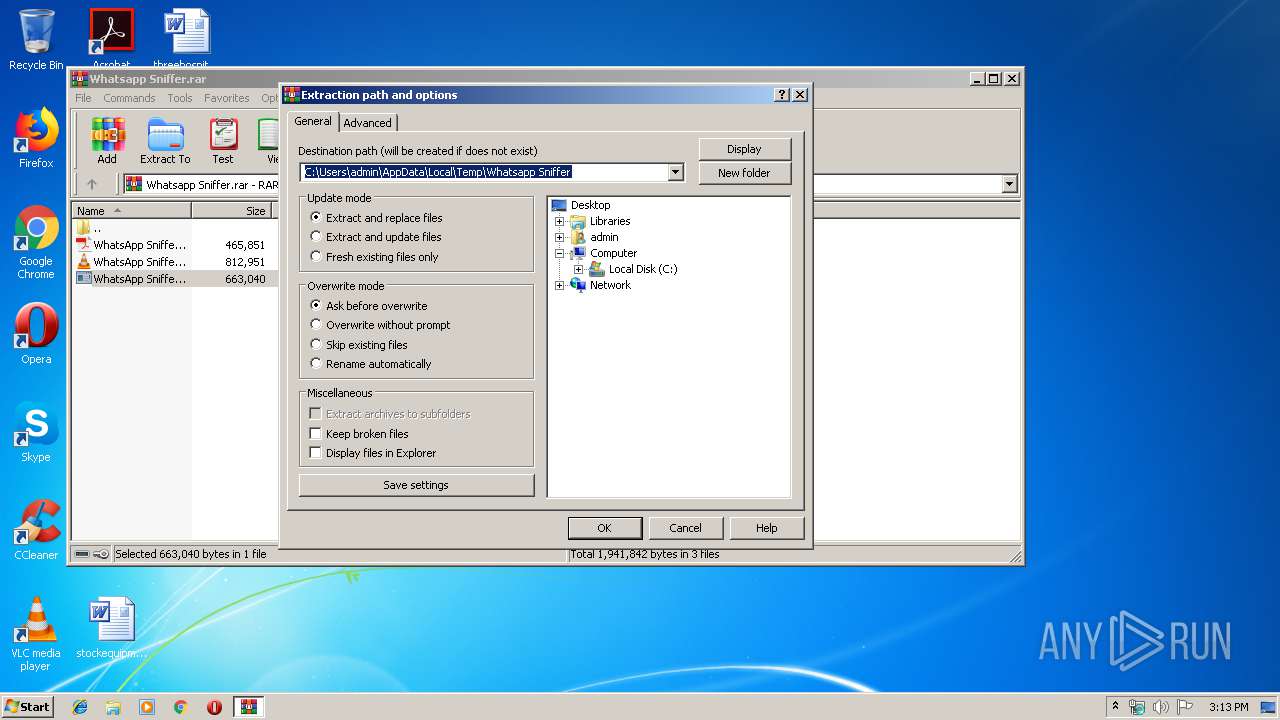
- WinRAR.exe (PID: 3108)
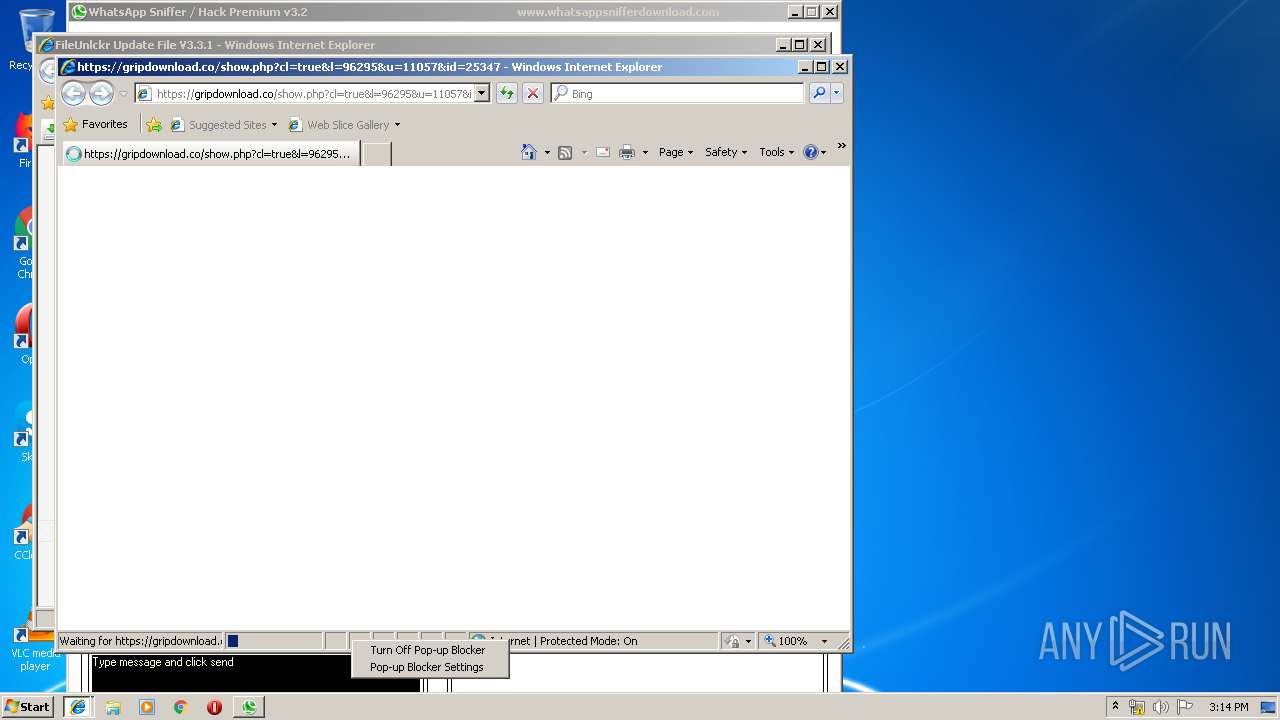
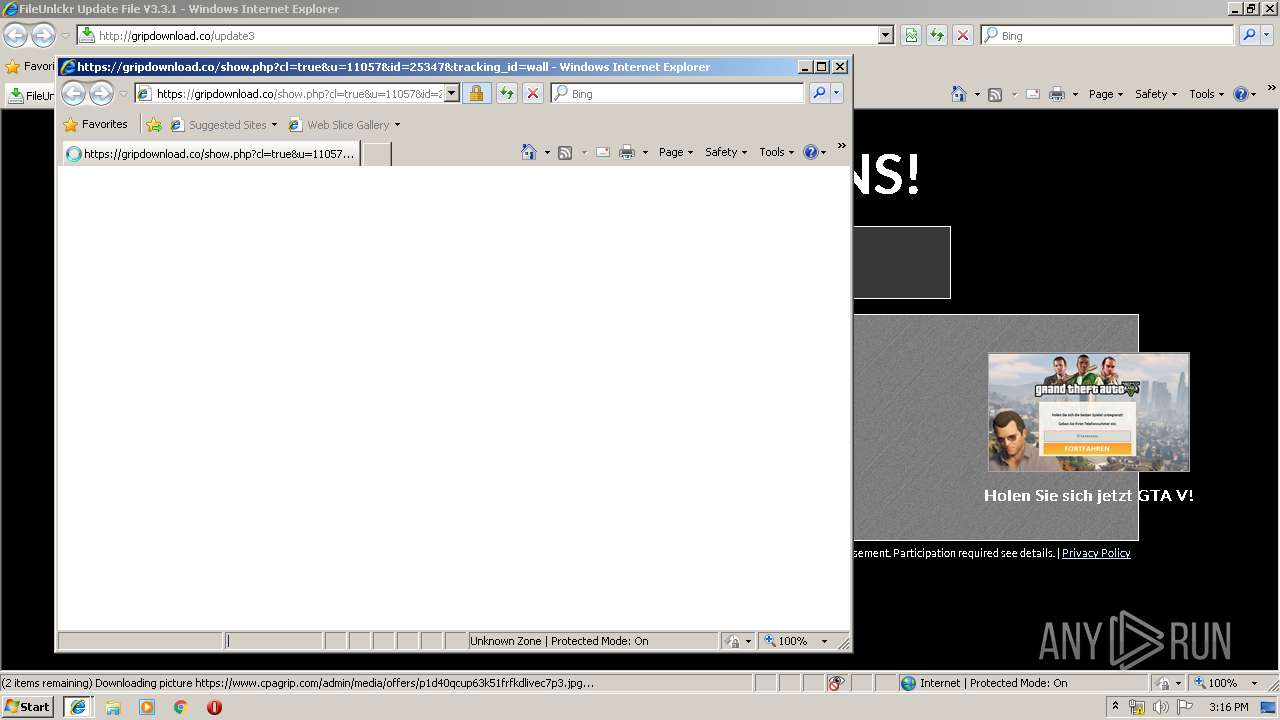
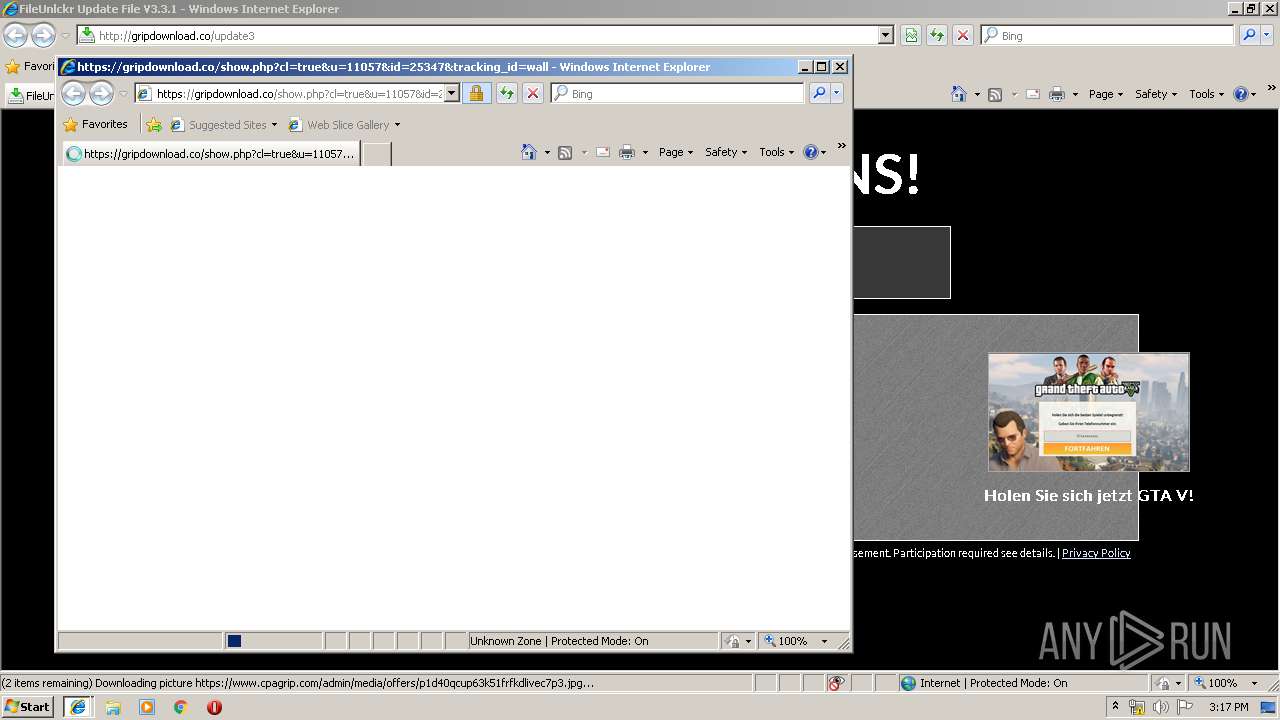
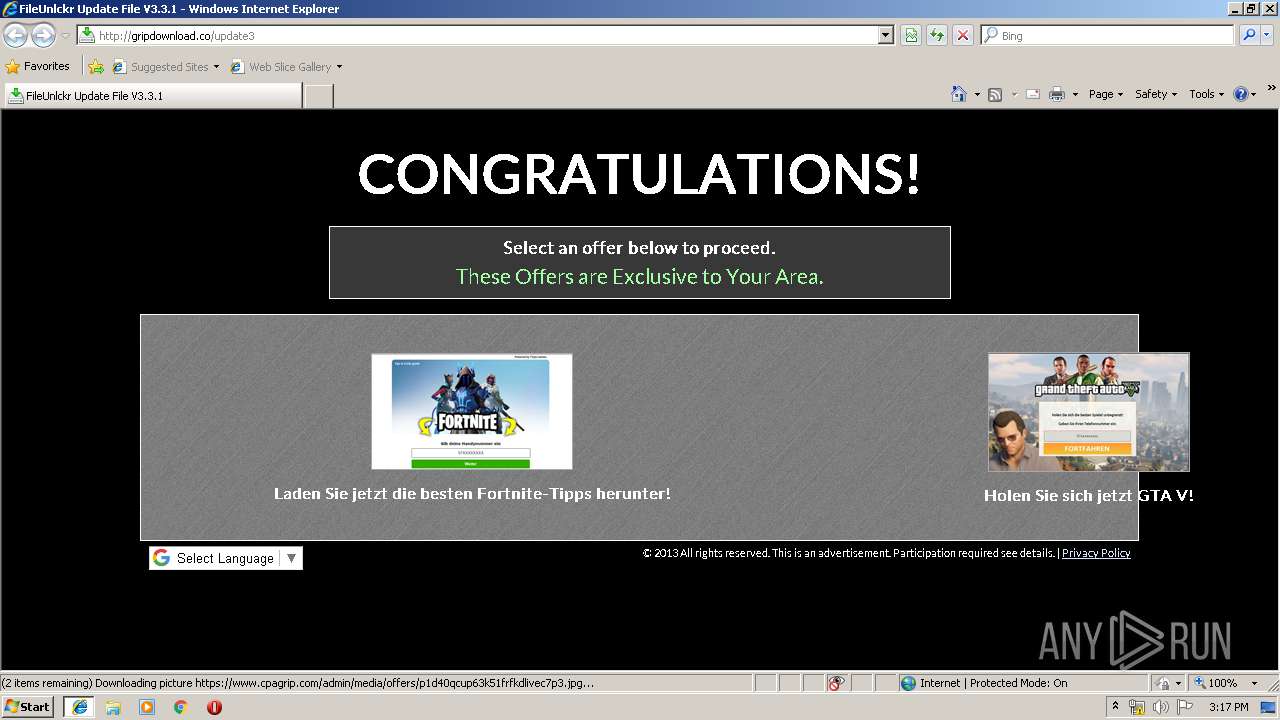
Starts Internet Explorer
- WhatsApp Sniffer.exe (PID: 3936)
Reads Internet Cache Settings
- WhatsApp Sniffer.exe (PID: 3936)
INFO
Manual execution by user
- WhatsApp Sniffer.exe (PID: 3936)
Changes internet zones settings
- iexplore.exe (PID: 3580)
Application launched itself
- iexplore.exe (PID: 3580)
Creates files in the user directory
- iexplore.exe (PID: 3612)
- iexplore.exe (PID: 3580)
- iexplore.exe (PID: 840)
Reads internet explorer settings
- iexplore.exe (PID: 3612)
- iexplore.exe (PID: 840)
- iexplore.exe (PID: 2620)
Reads Internet Cache Settings
- iexplore.exe (PID: 840)
- iexplore.exe (PID: 3612)
- iexplore.exe (PID: 2620)
Reads settings of System Certificates
- iexplore.exe (PID: 3612)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v-4.x) (58.3) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (41.6) |
EXIF
ZIP
| CompressedSize: | 290618 |
|---|---|
| UncompressedSize: | 663040 |
| OperatingSystem: | Win32 |
| ModifyDate: | 2014:09:17 16:14:09 |
| PackingMethod: | Normal |
| ArchivedFileName: | WhatsApp Sniffer.exe |
Total processes
43
Monitored processes
7
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 840 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3580 CREDAT:203010 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2620 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3580 CREDAT:203009 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3104 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3108.7472\WhatsApp Sniffer.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3108.7472\WhatsApp Sniffer.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: WhatsApp Sniffer Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3108 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Whatsapp Sniffer.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3580 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | WhatsApp Sniffer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3612 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3580 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
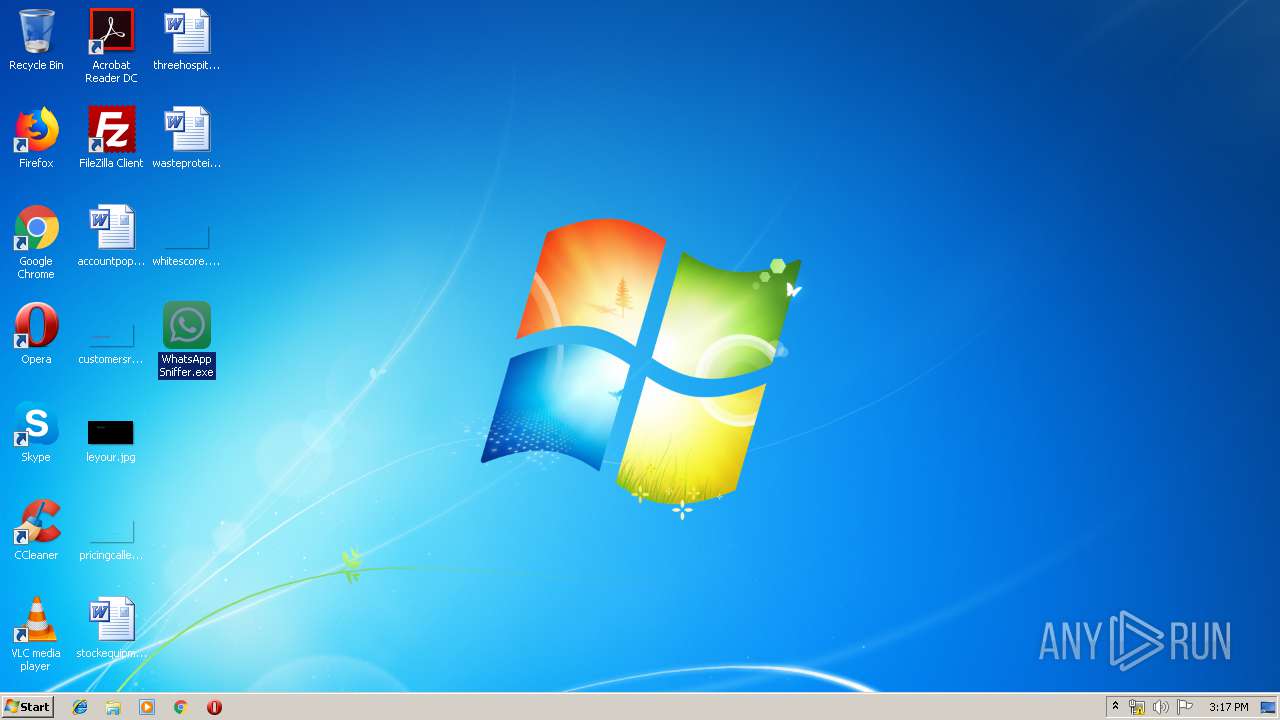
| 3936 | "C:\Users\admin\Desktop\WhatsApp Sniffer.exe" | C:\Users\admin\Desktop\WhatsApp Sniffer.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: WhatsApp Sniffer Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
1 527
Read events
1 317
Write events
207
Delete events
3
Modification events
| (PID) Process: | (3108) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3108) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3108) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\70\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3108) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Whatsapp Sniffer.rar | |||
| (PID) Process: | (3108) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3108) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3108) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3108) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3108) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3108) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
2
Suspicious files
26
Text files
56
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3580 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3580 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
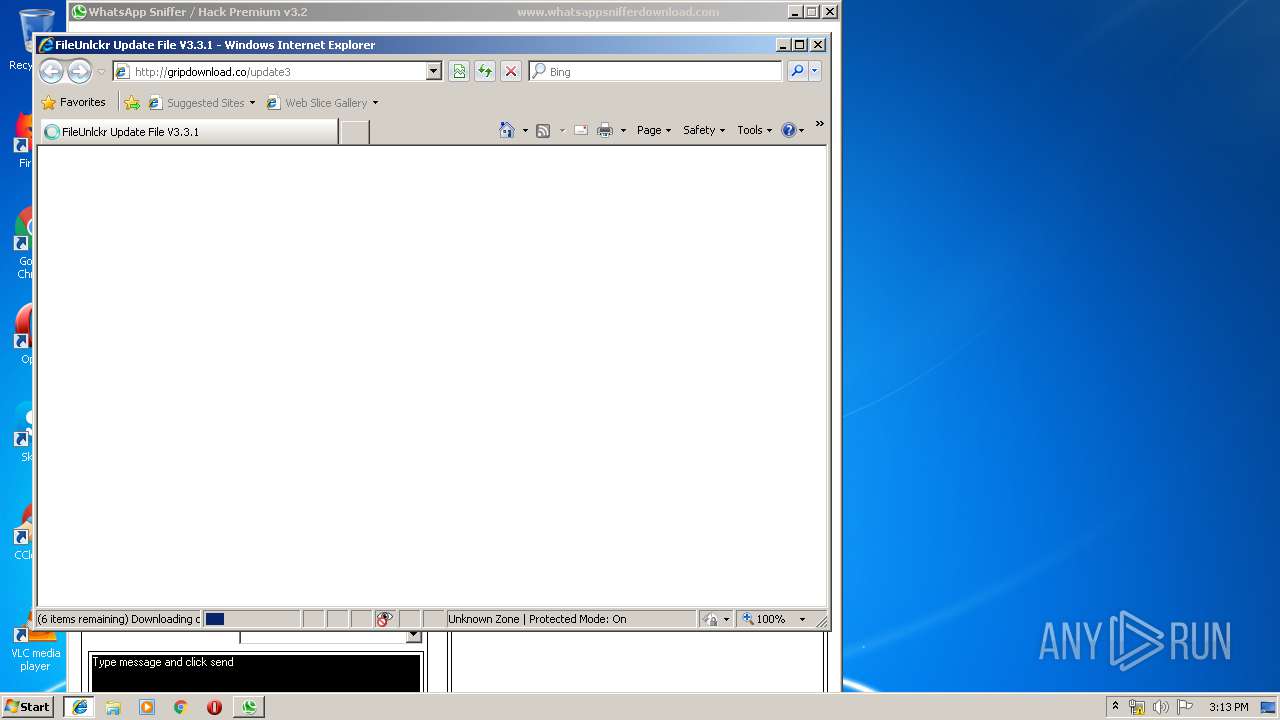
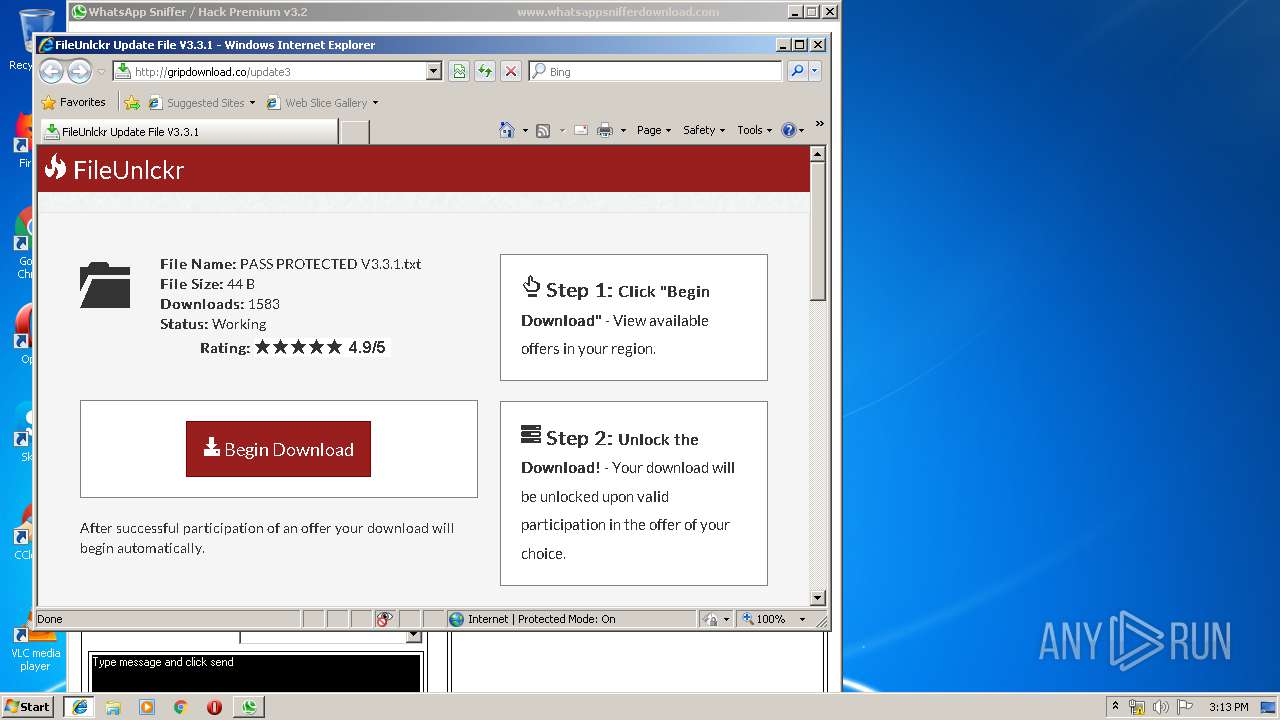
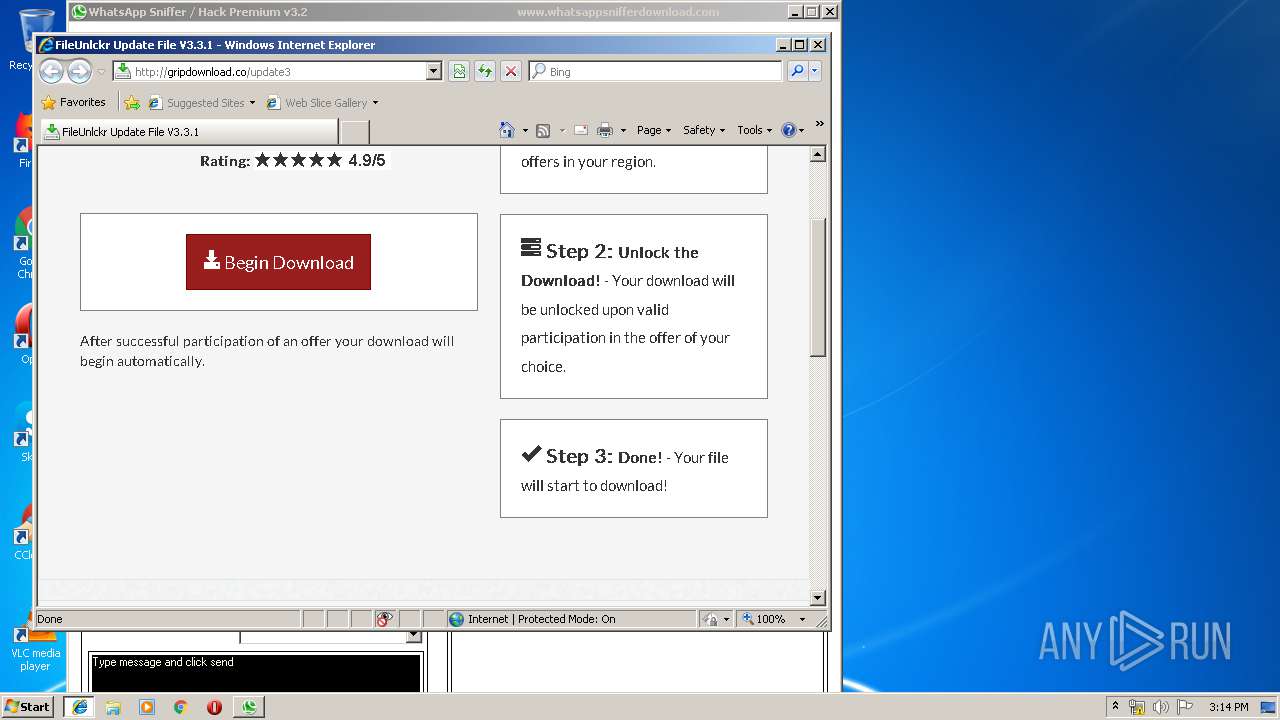
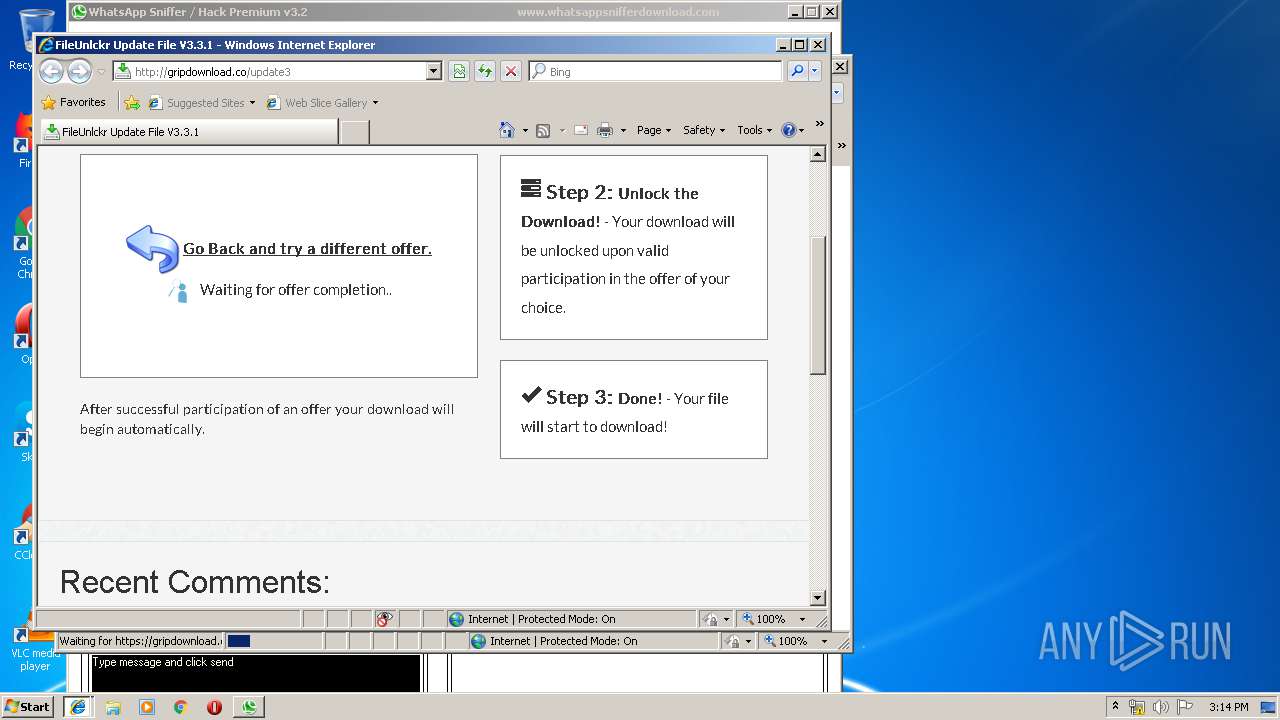
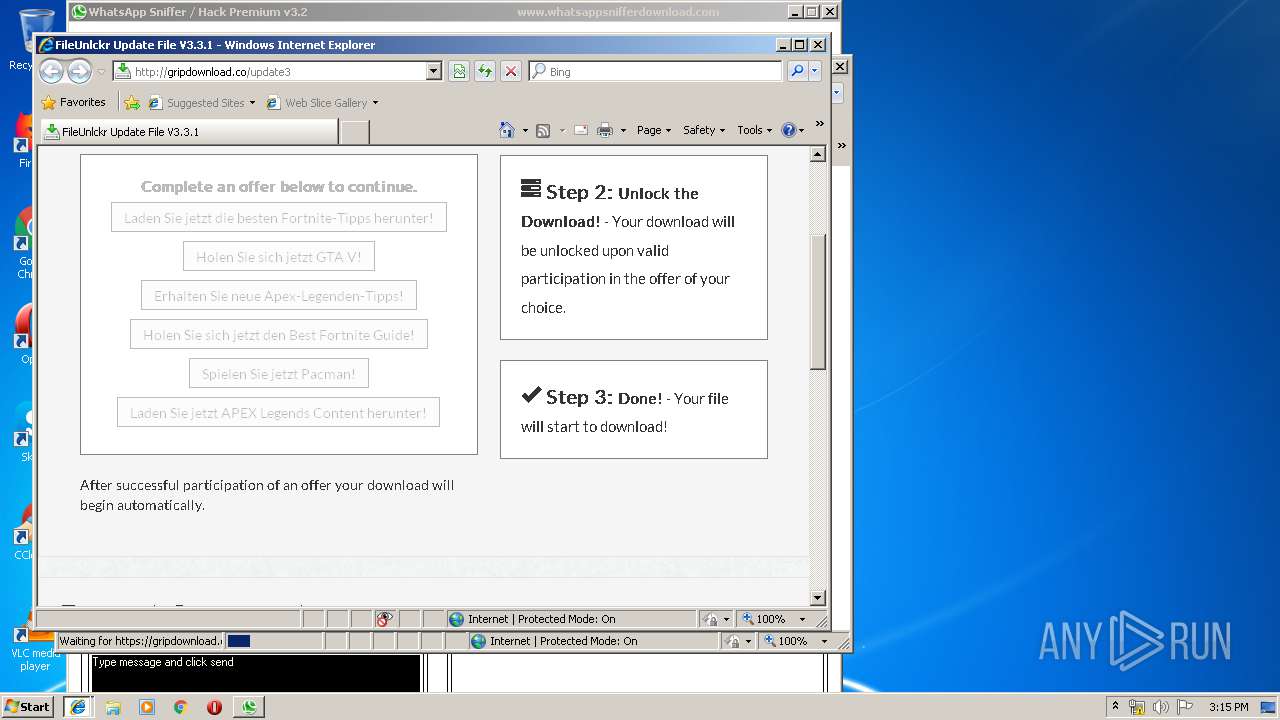
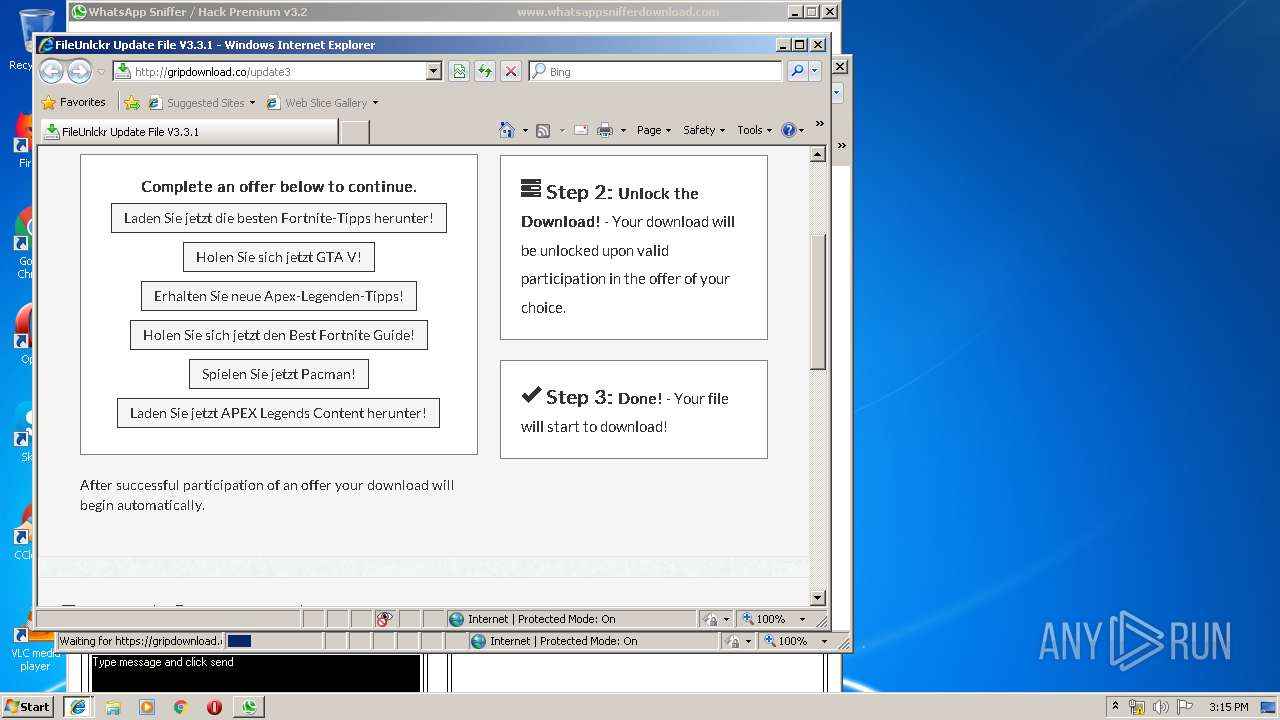
| 3612 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\86MOZ83J\update3[1].txt | — | |
MD5:— | SHA256:— | |||
| 3108 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3108.7472\WhatsApp Sniffer.exe | executable | |
MD5:— | SHA256:— | |||
| 3612 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 3108 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3108.7472\WhatsApp Sniffer - Read Me.pdf | ||
MD5:— | SHA256:— | |||
| 3108 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3108.7472\WhatsApp Sniffer Tutorial.mp4 | m4v | |
MD5:— | SHA256:— | |||
| 3612 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\86MOZ83J\update3[1].htm | html | |
MD5:— | SHA256:— | |||
| 3108 | WinRAR.exe | C:\Users\admin\Desktop\WhatsApp Sniffer.exe | executable | |
MD5:— | SHA256:— | |||
| 3612 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\Low\History.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
35
DNS requests
21
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
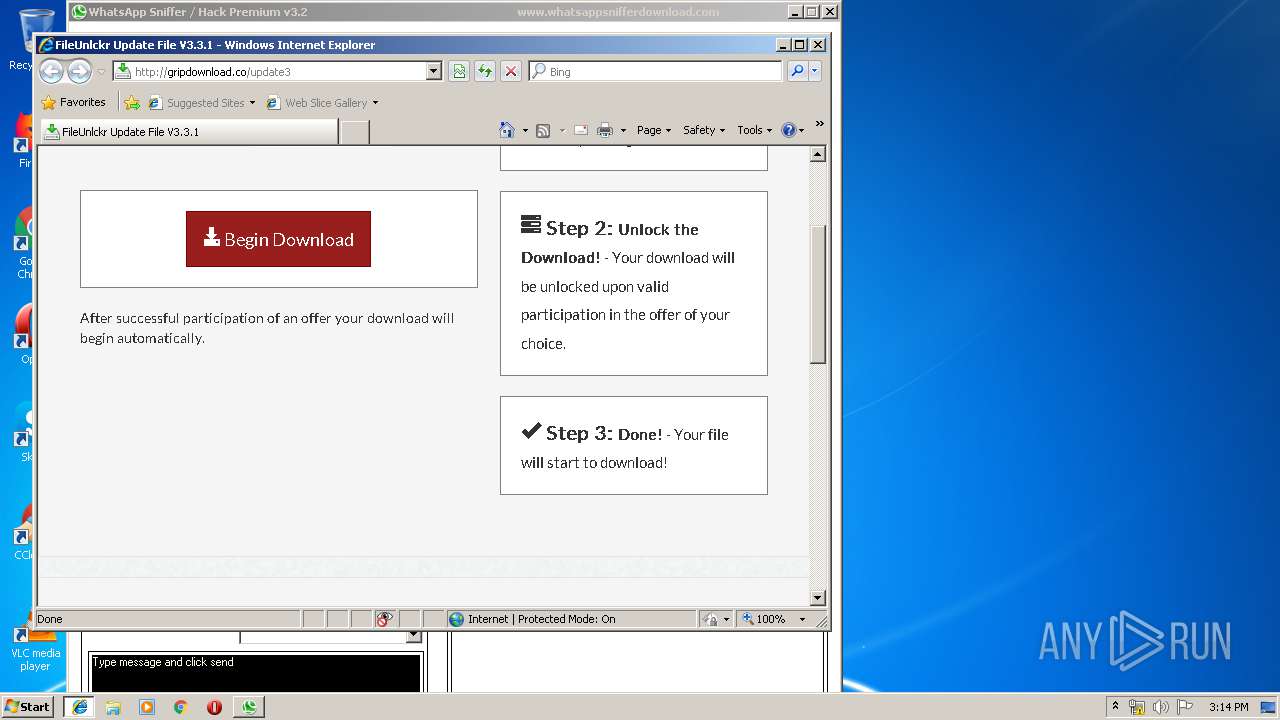
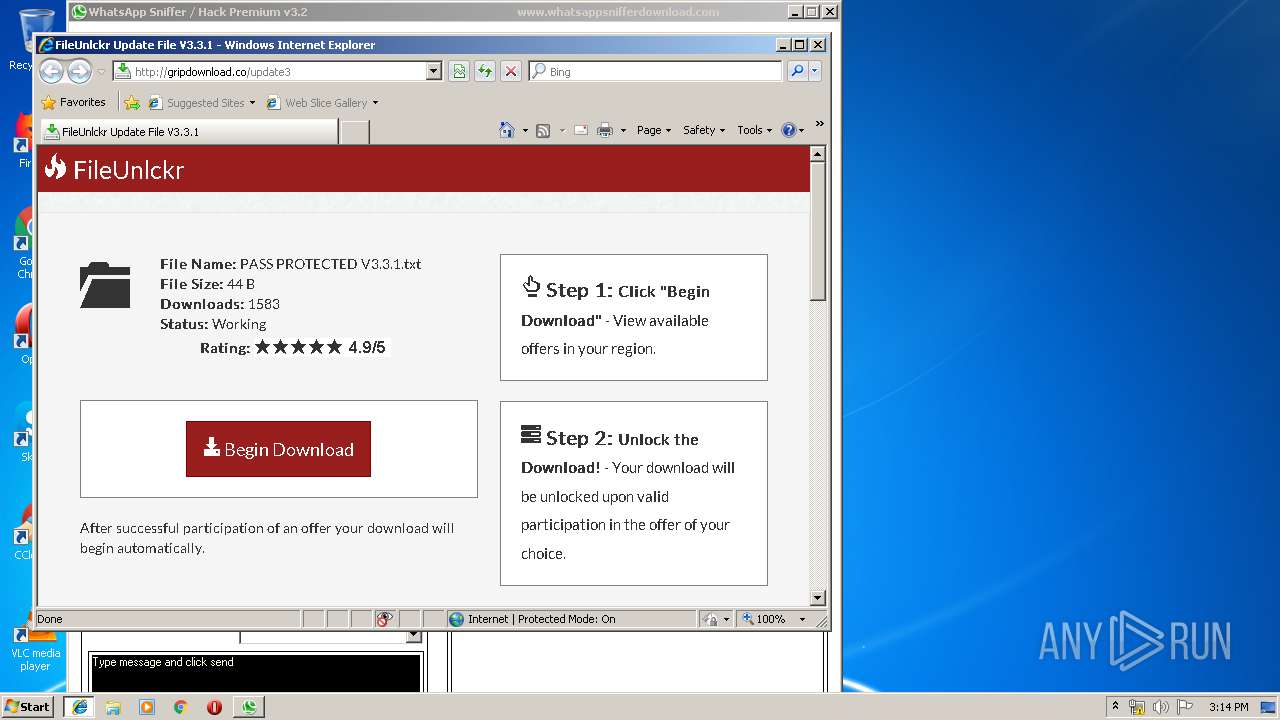
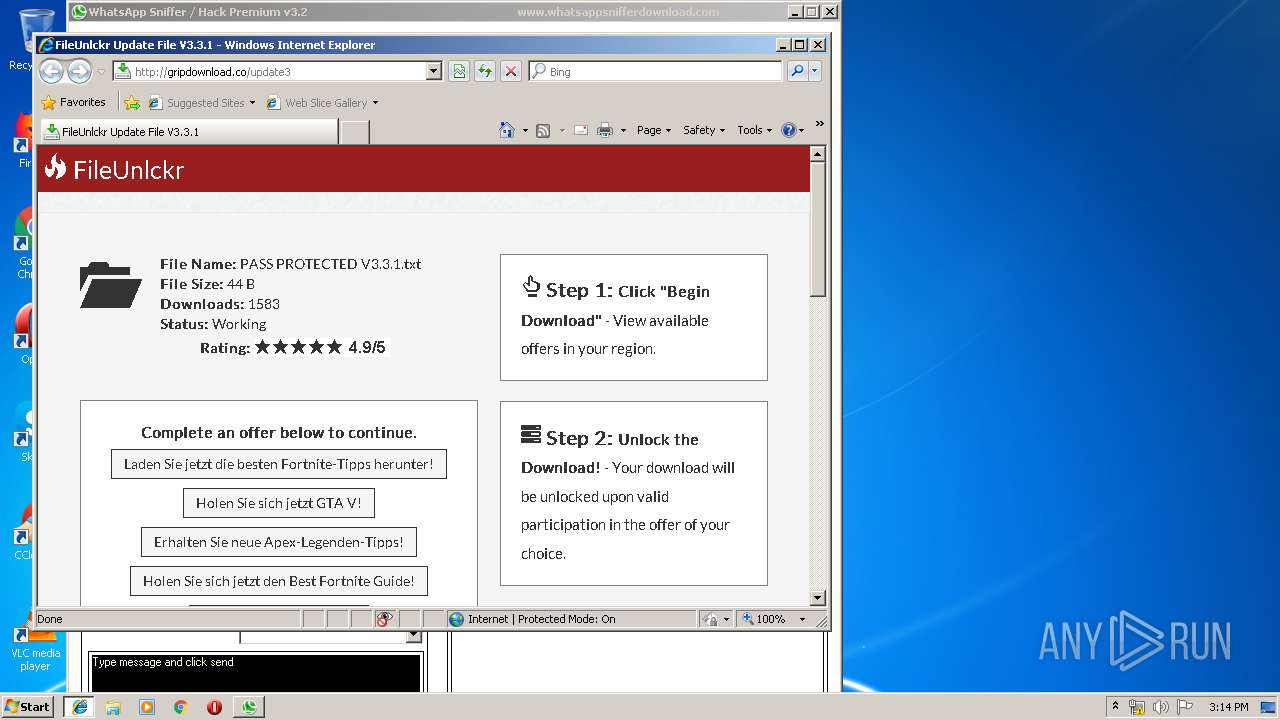
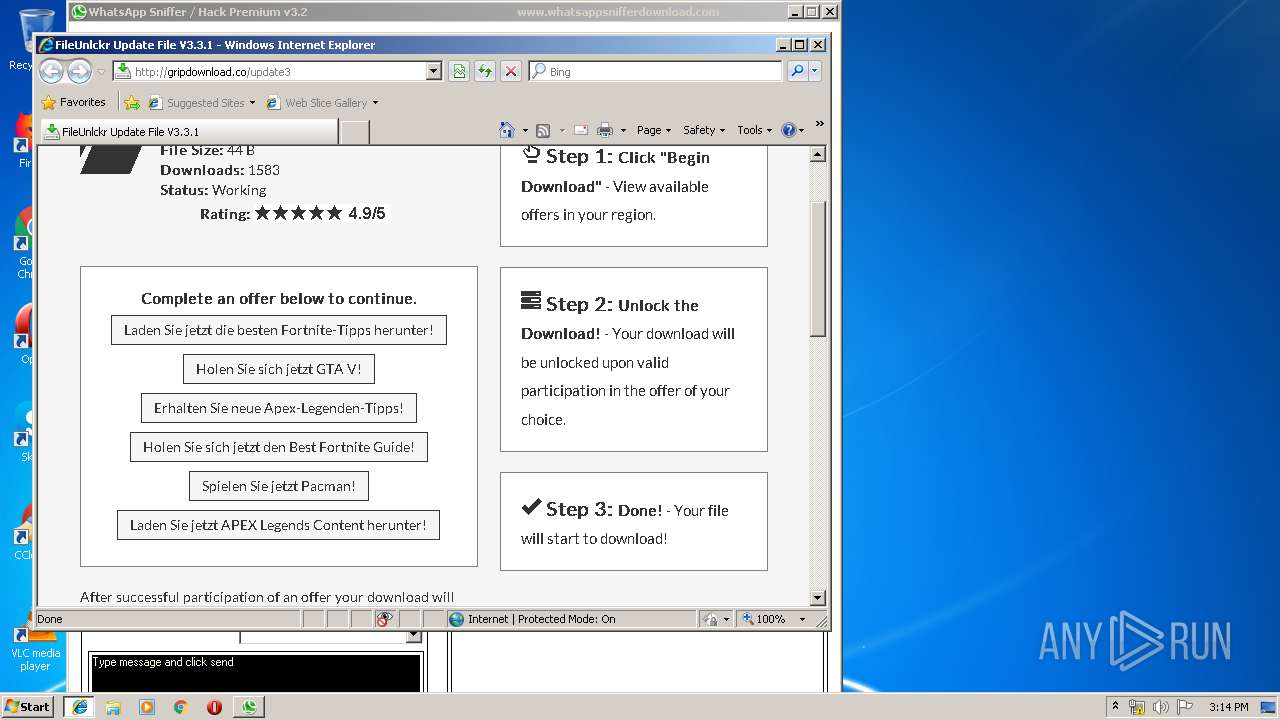
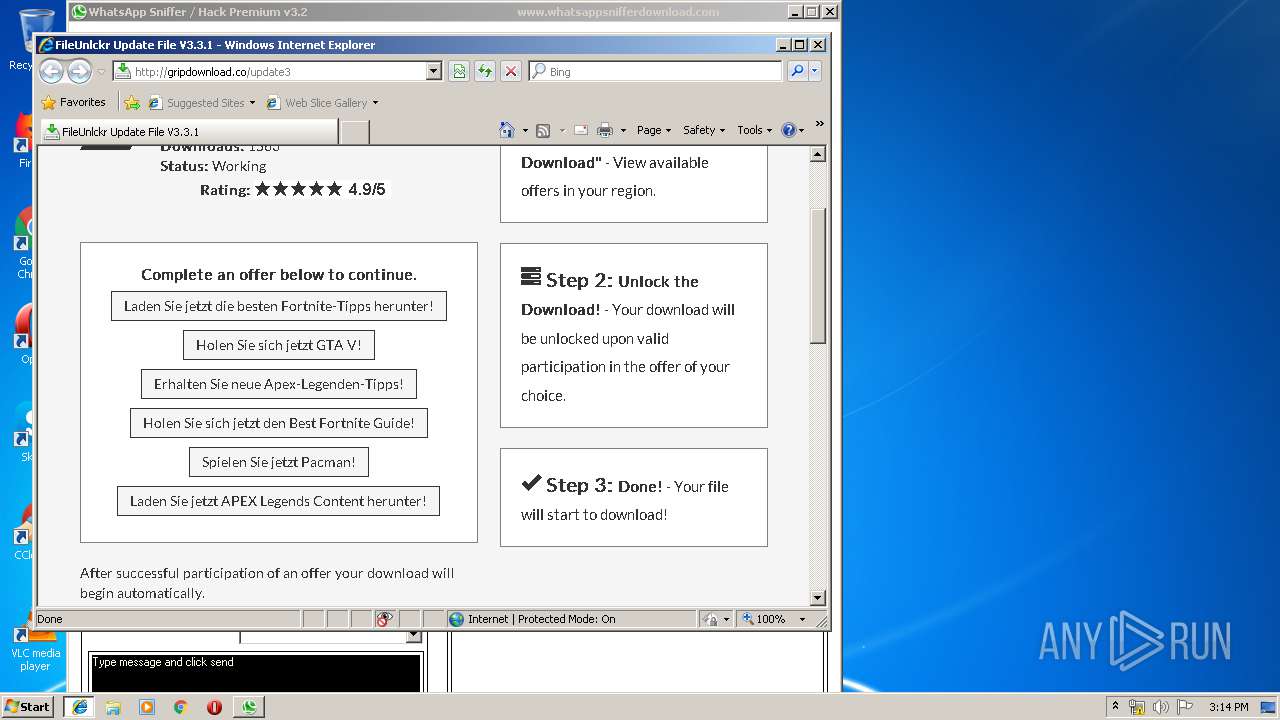
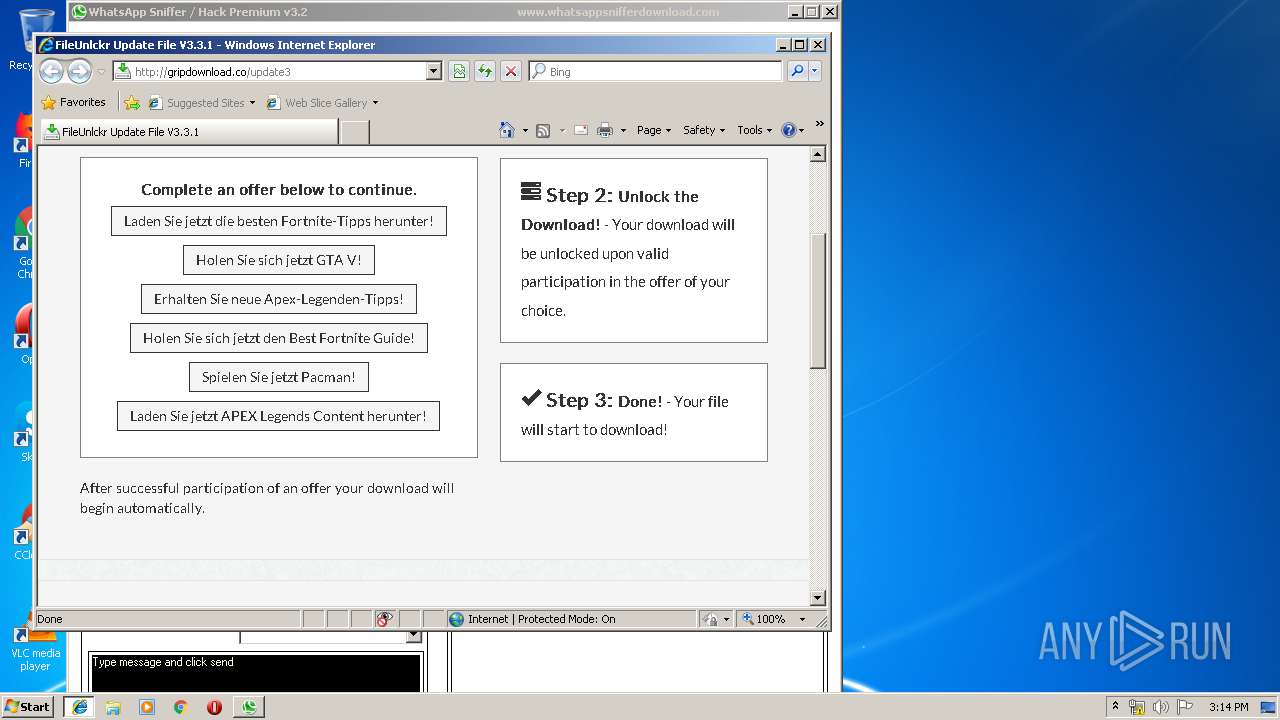
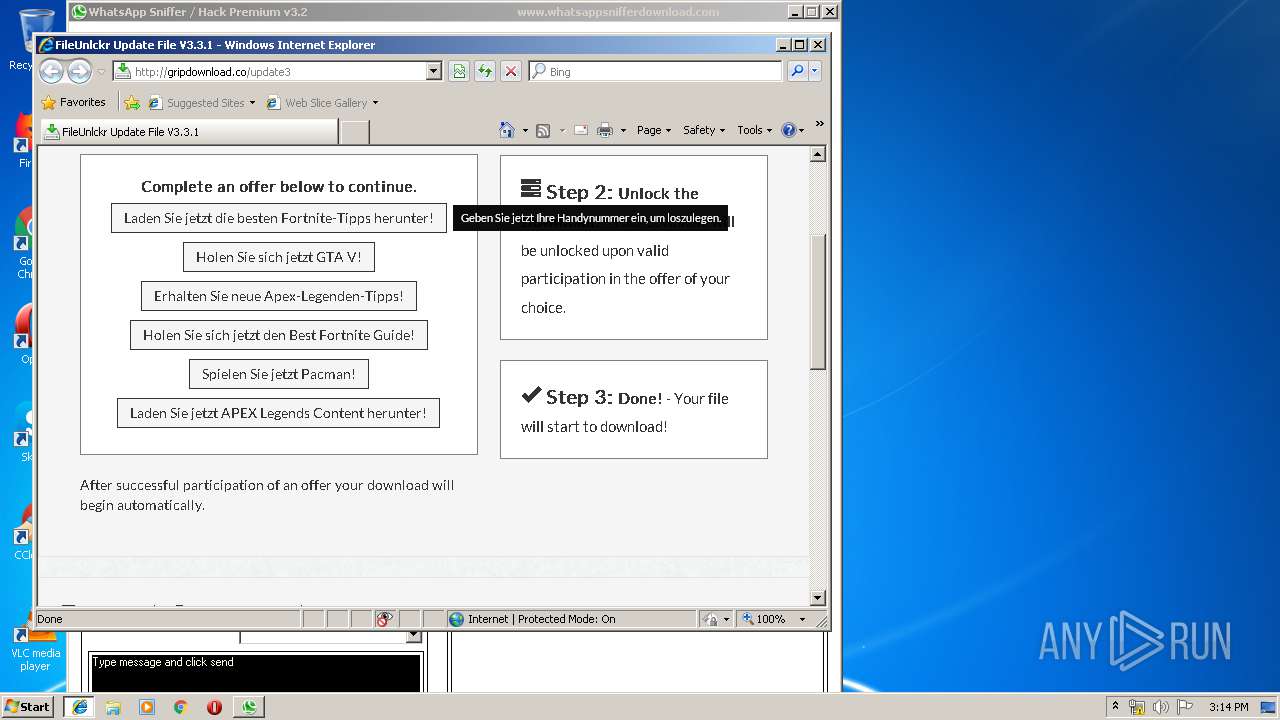
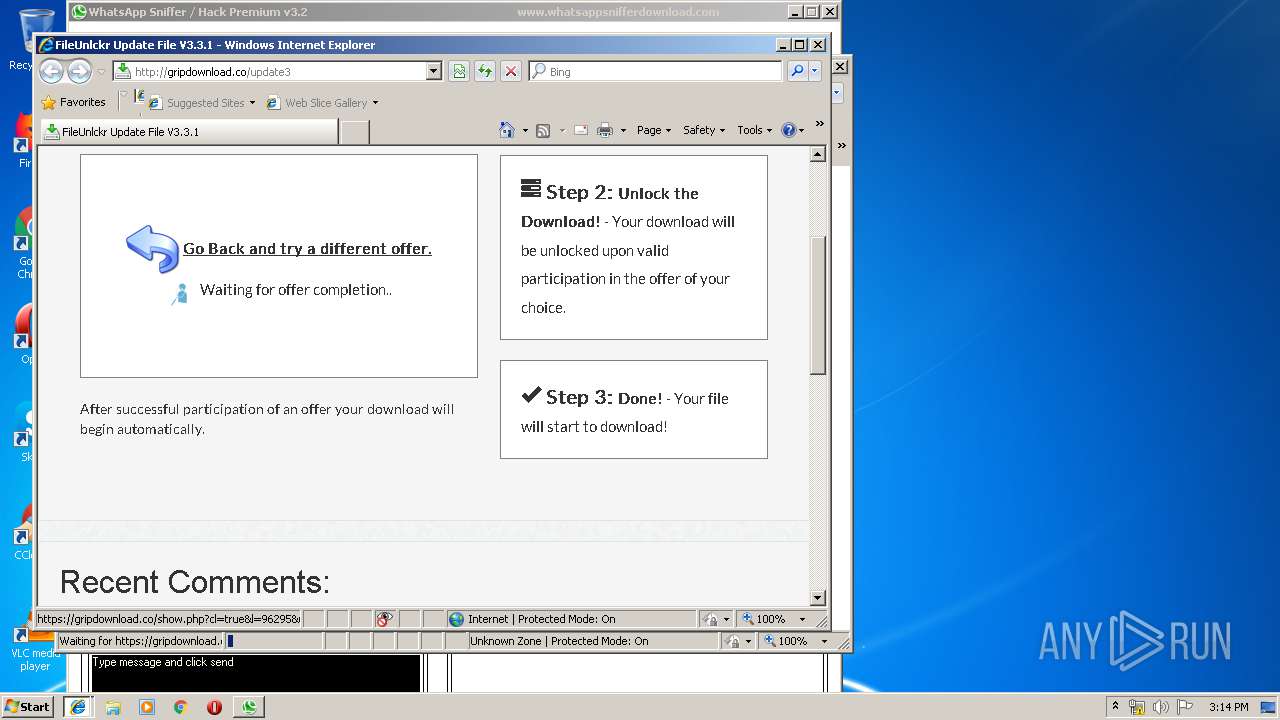
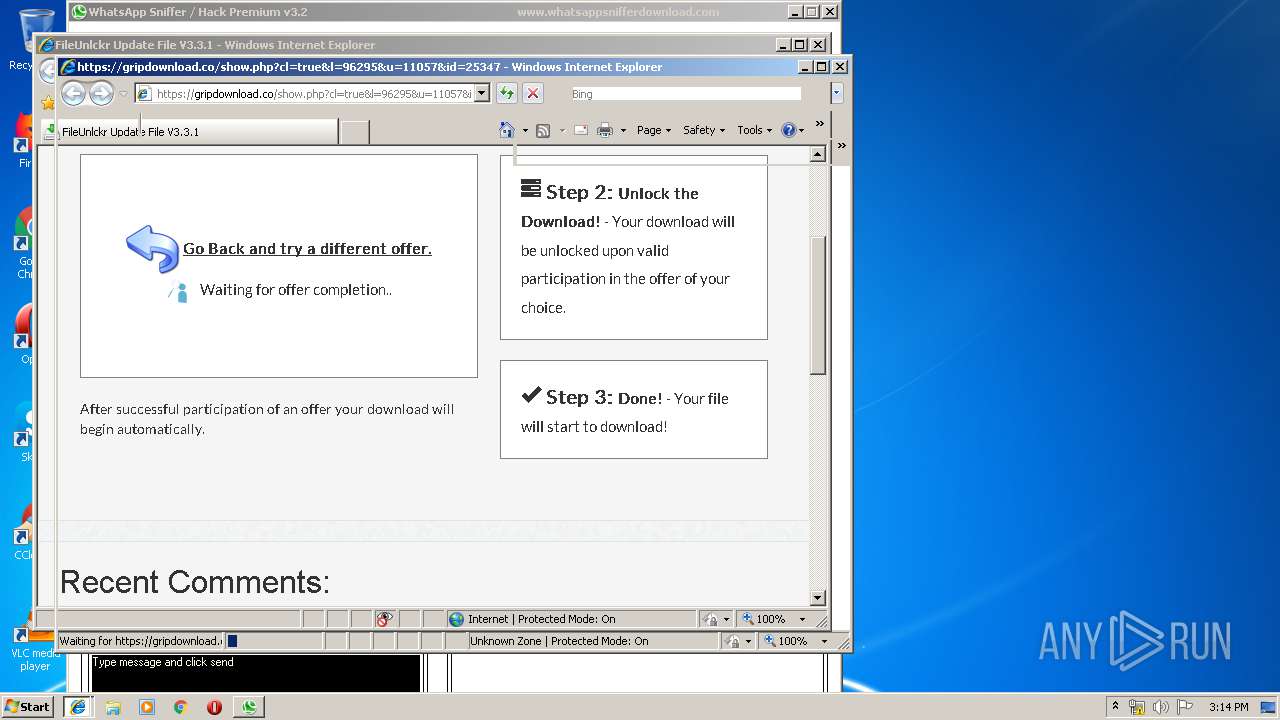
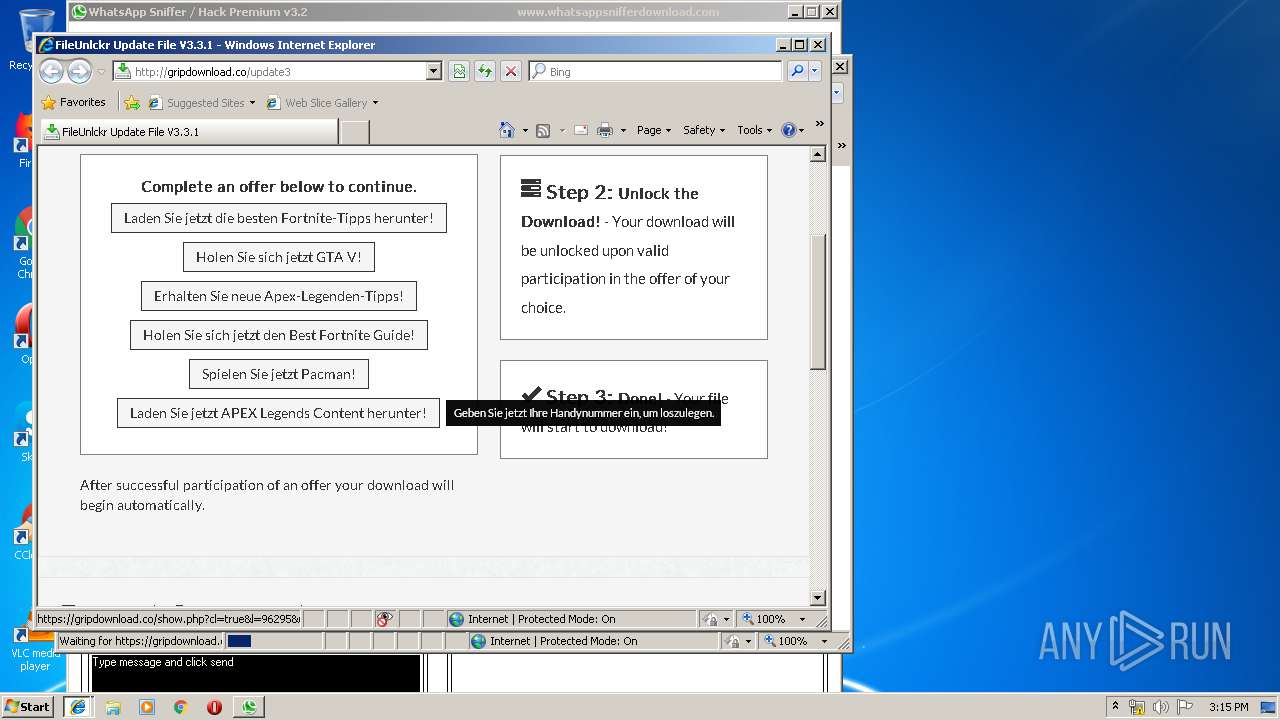
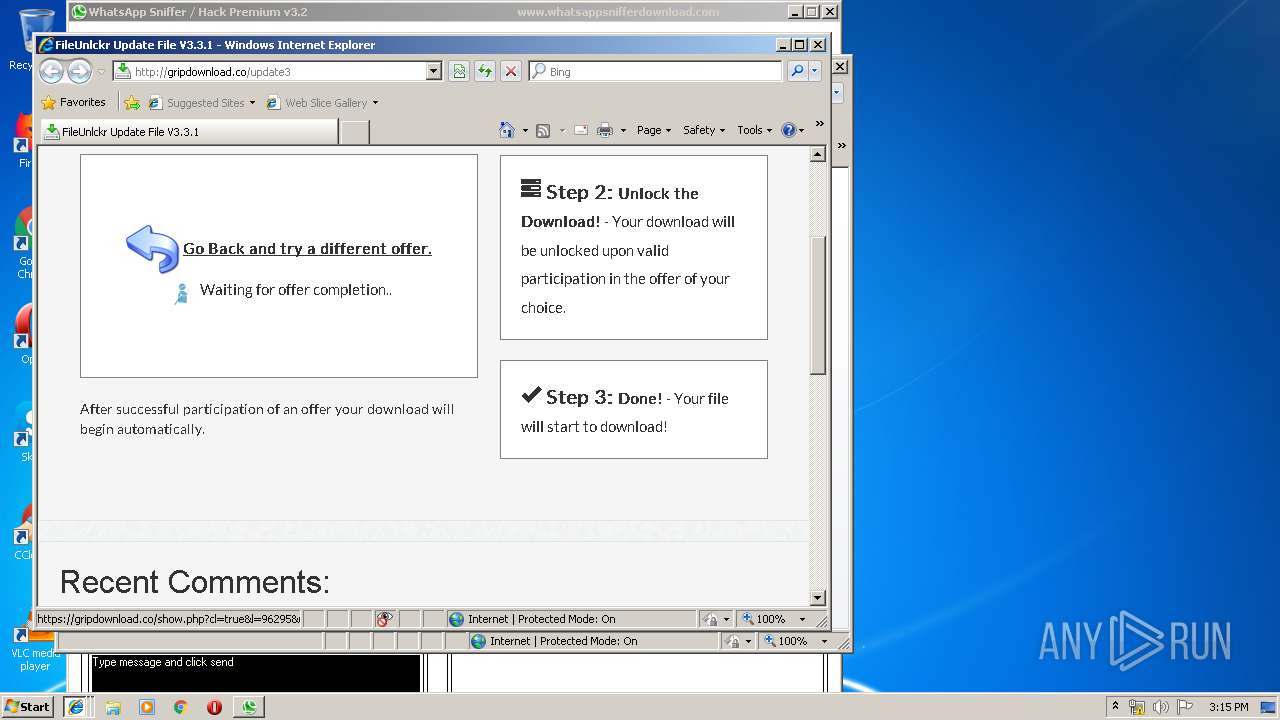
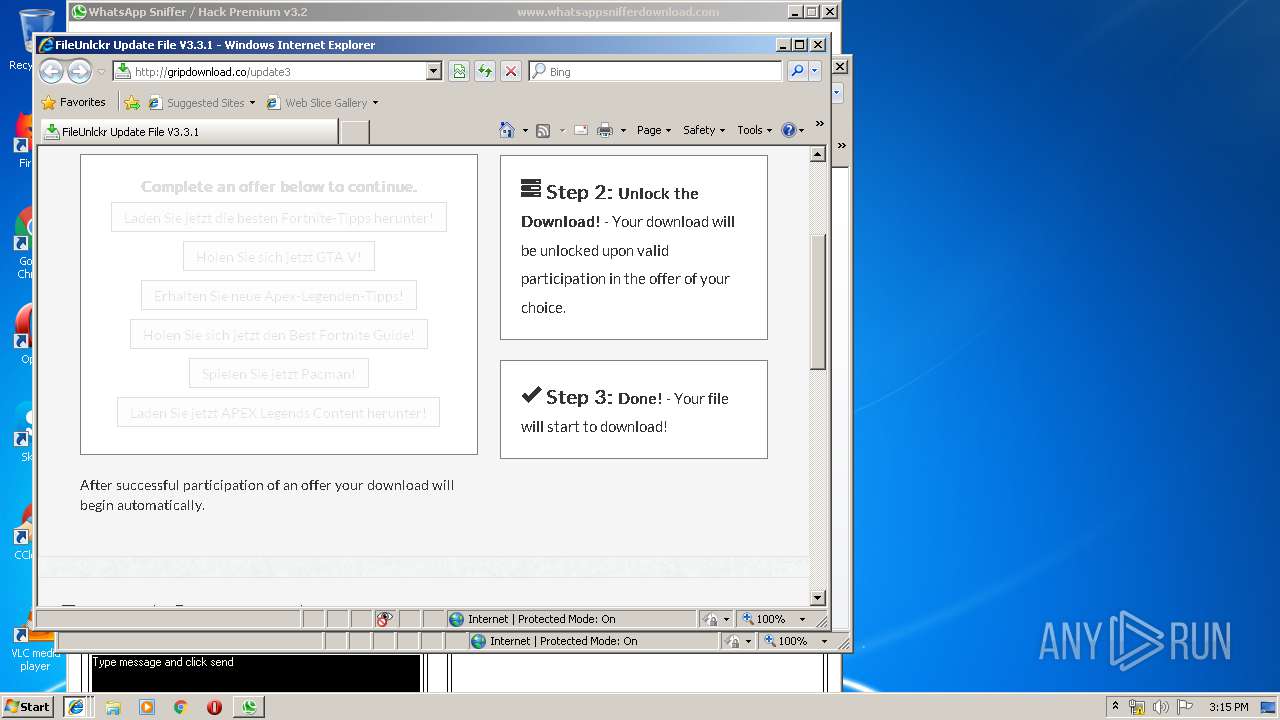
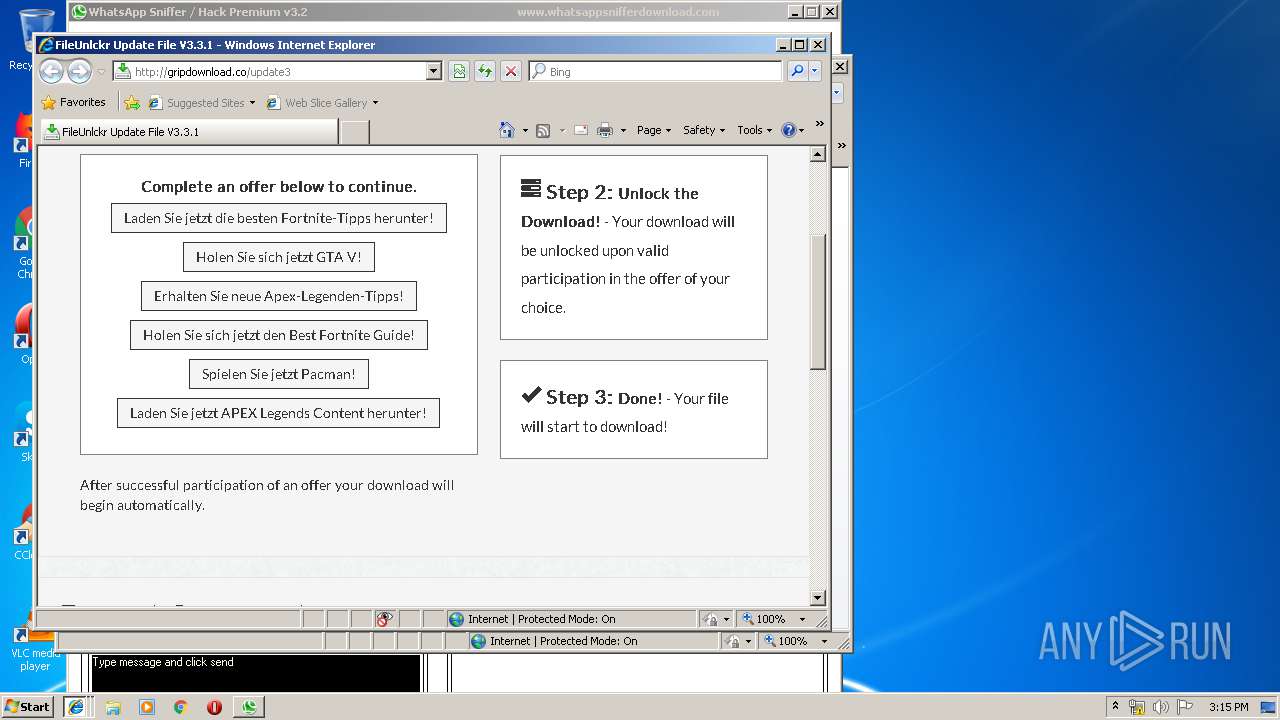
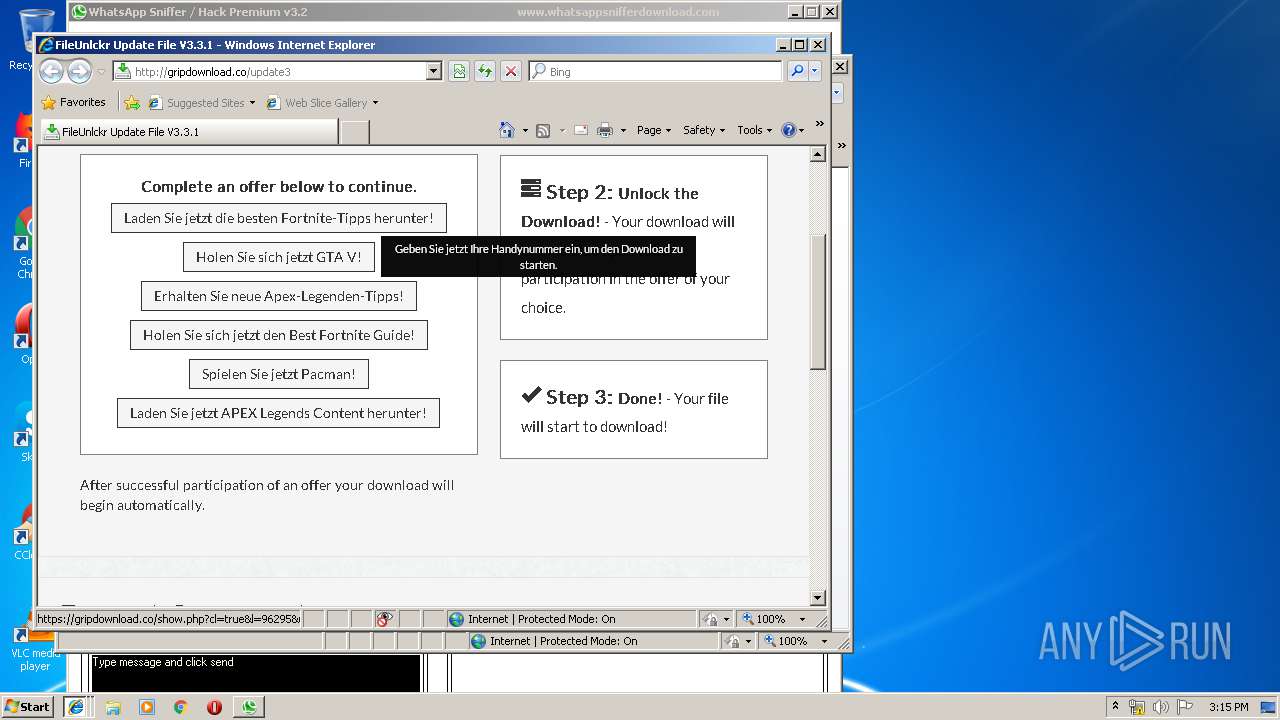
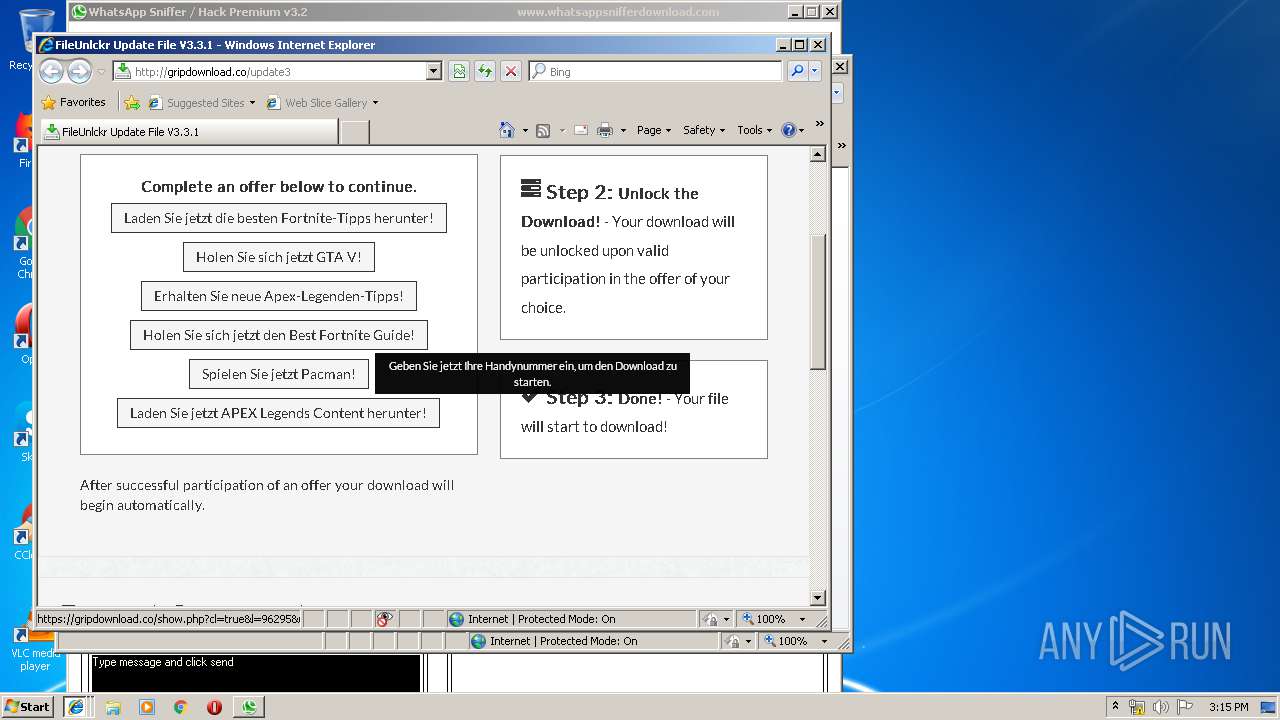
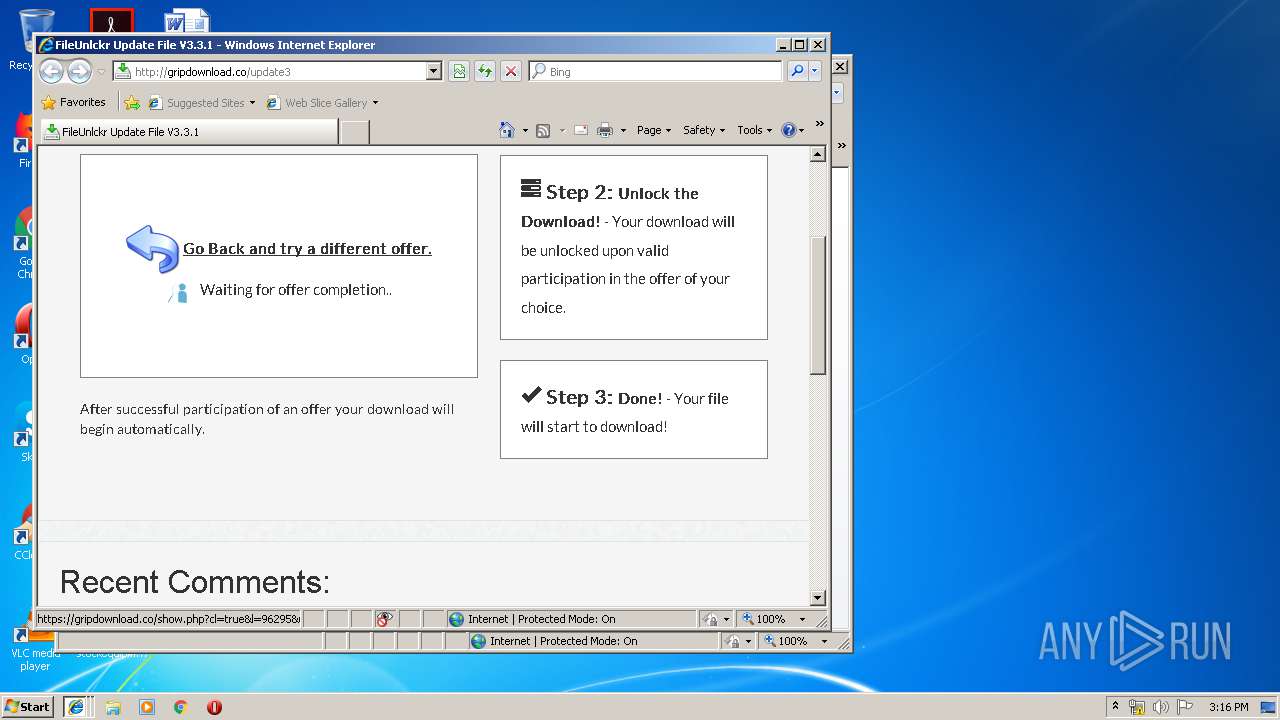
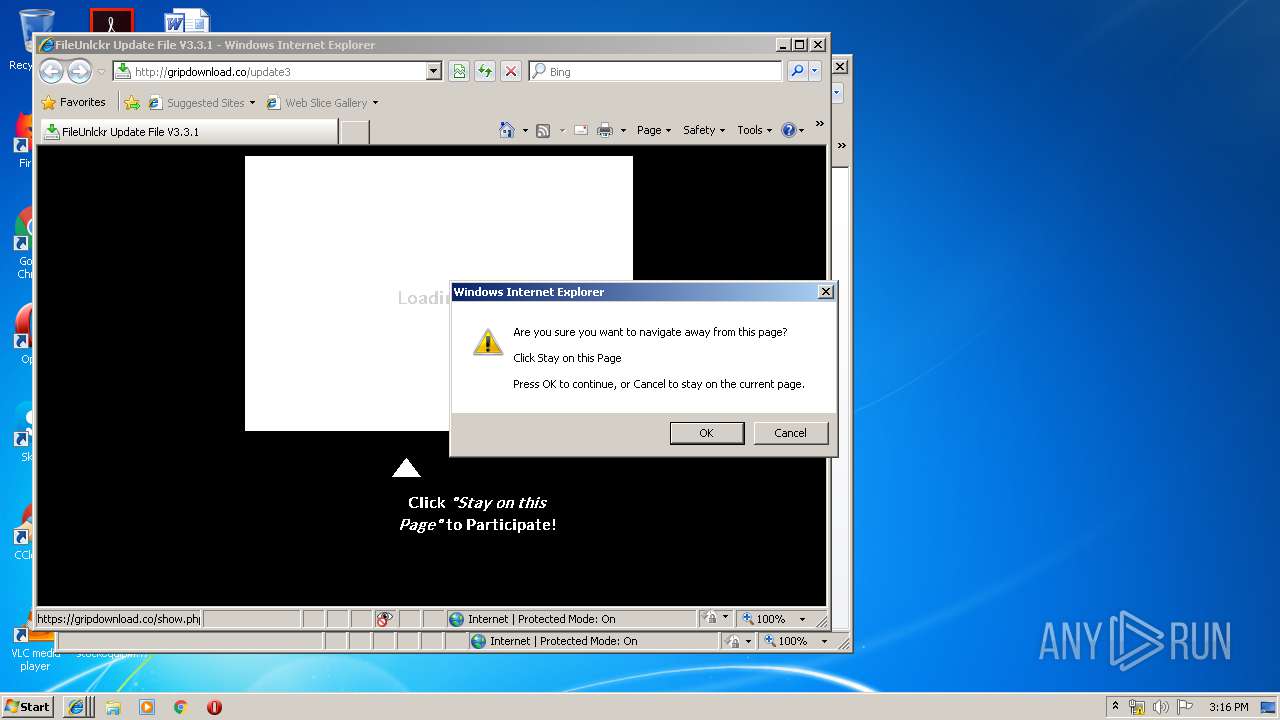
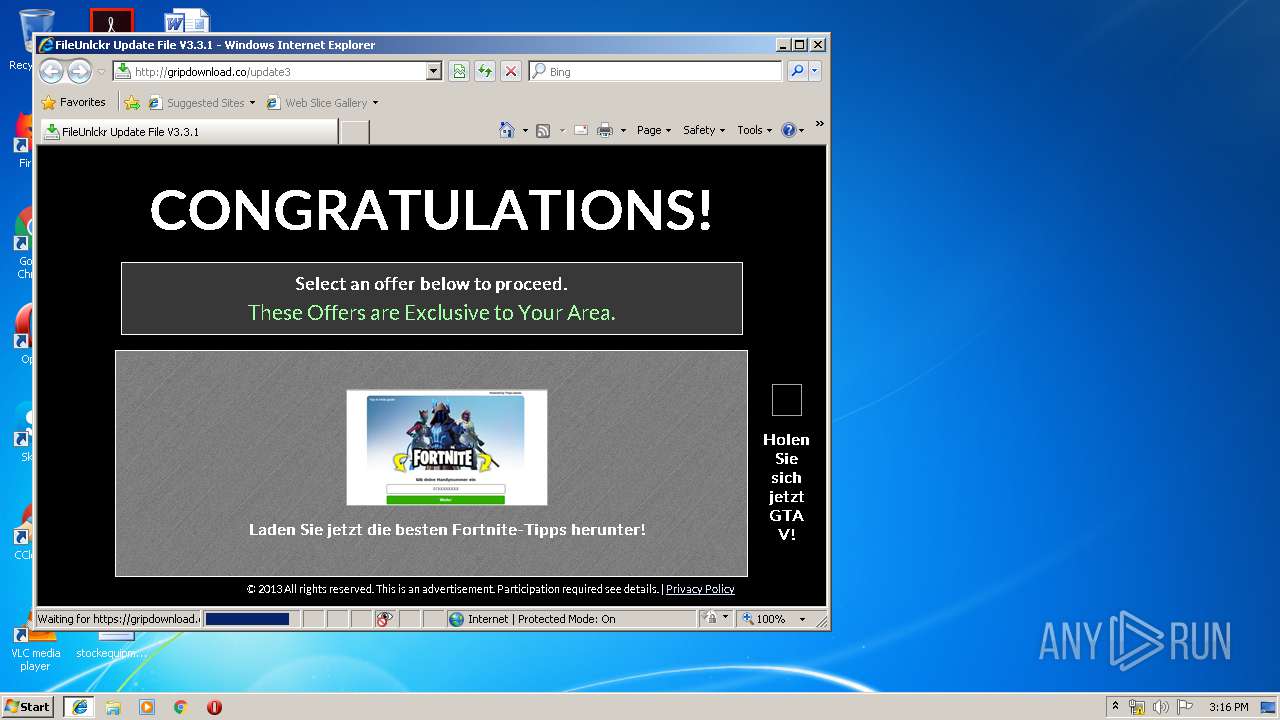
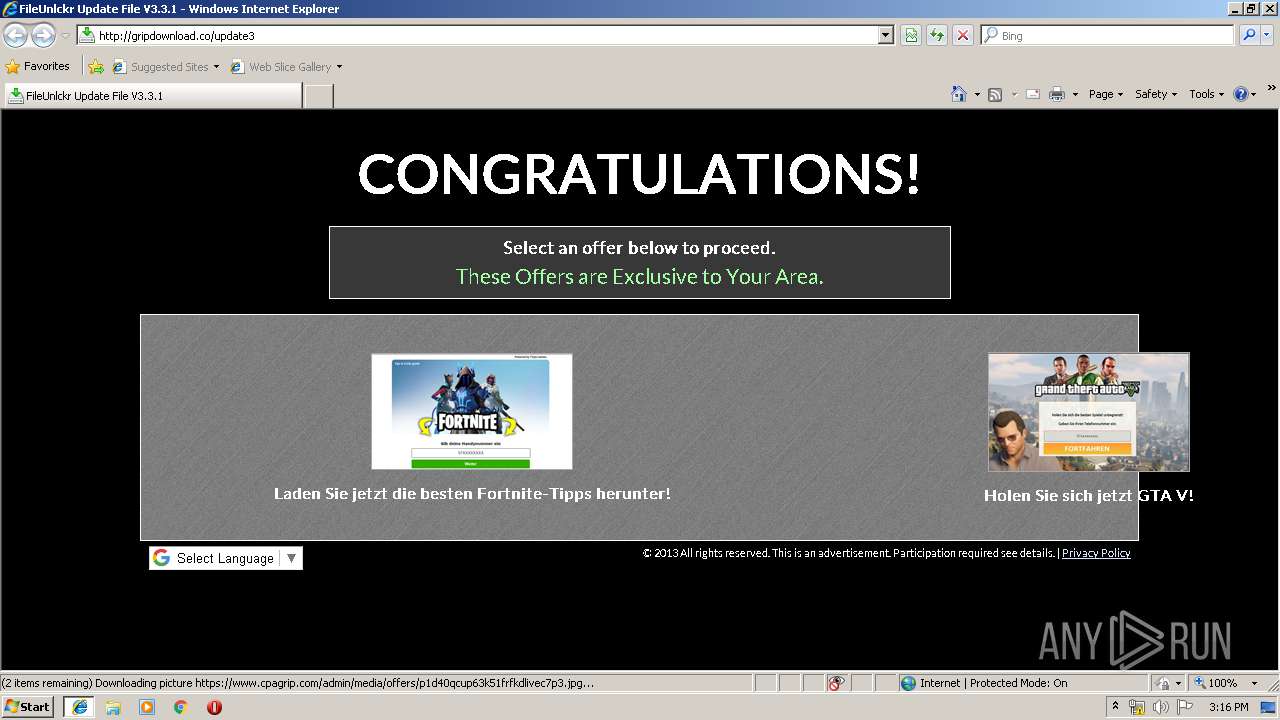
3612 | iexplore.exe | GET | 200 | 104.26.3.131:80 | http://gripdownload.co/update3 | US | html | 8.08 Kb | shared |
840 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 56.2 Kb | whitelisted |
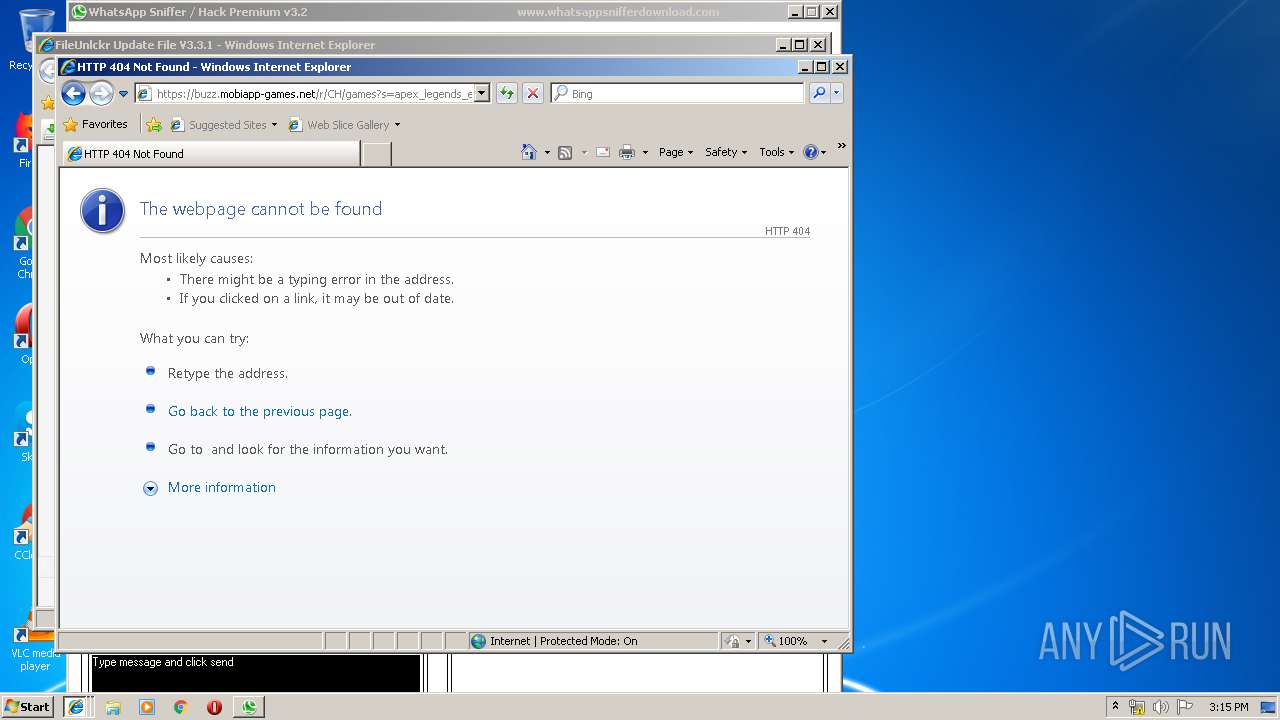
840 | iexplore.exe | GET | 200 | 5.79.75.10:80 | http://track.buzz-track.com/click?offer_id=7410&aff_id=612&click_id=102eb9737f36415159eaaa3313465f&pub_id=11057&sub_id=949721208 | NL | html | 250 b | suspicious |
3612 | iexplore.exe | GET | 200 | 104.28.21.63:80 | http://lokhlp.com/images/blankuser.png | US | image | 979 b | shared |
3612 | iexplore.exe | GET | 200 | 104.26.3.131:80 | http://gripdownload.co/bootstrap3/fonts/glyphiconshalflings-regular.eot? | US | eot | 18.6 Kb | shared |
3612 | iexplore.exe | GET | 200 | 104.26.3.131:80 | http://gripdownload.co/bootstrap3/css/bootstrap-glyphicons.css | US | text | 1.50 Kb | shared |
3580 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
3612 | iexplore.exe | GET | 200 | 104.27.176.100:80 | http://fileunlckr.com/img/bg1.png | US | image | 72.3 Kb | shared |
3612 | iexplore.exe | GET | 200 | 209.197.3.15:80 | http://netdna.bootstrapcdn.com/bootstrap/3.0.0-rc1/css/bootstrap.min.css | US | text | 11.4 Kb | whitelisted |
3580 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3580 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3612 | iexplore.exe | 104.26.3.131:80 | gripdownload.co | Cloudflare Inc | US | shared |
3612 | iexplore.exe | 209.197.3.15:80 | netdna.bootstrapcdn.com | Highwinds Network Group, Inc. | US | whitelisted |
3612 | iexplore.exe | 216.58.208.42:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
3612 | iexplore.exe | 216.58.207.74:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
3612 | iexplore.exe | 104.26.3.131:443 | gripdownload.co | Cloudflare Inc | US | shared |
3612 | iexplore.exe | 172.217.23.131:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3612 | iexplore.exe | 104.28.21.63:80 | lokhlp.com | Cloudflare Inc | US | shared |
3612 | iexplore.exe | 104.27.176.100:80 | fileunlckr.com | Cloudflare Inc | US | shared |
3580 | iexplore.exe | 104.26.3.131:80 | gripdownload.co | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
gripdownload.co |
| unknown |
netdna.bootstrapcdn.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
lokhlp.com |
| unknown |
fonts.gstatic.com |
| whitelisted |
fileunlckr.com |
| unknown |
t.trackingrace.online |
| unknown |
x.ss2.us |
| whitelisted |