| download: | index.html |
| Full analysis: | https://app.any.run/tasks/2e812ff6-2dfc-4930-b10f-11ebd0da6703 |
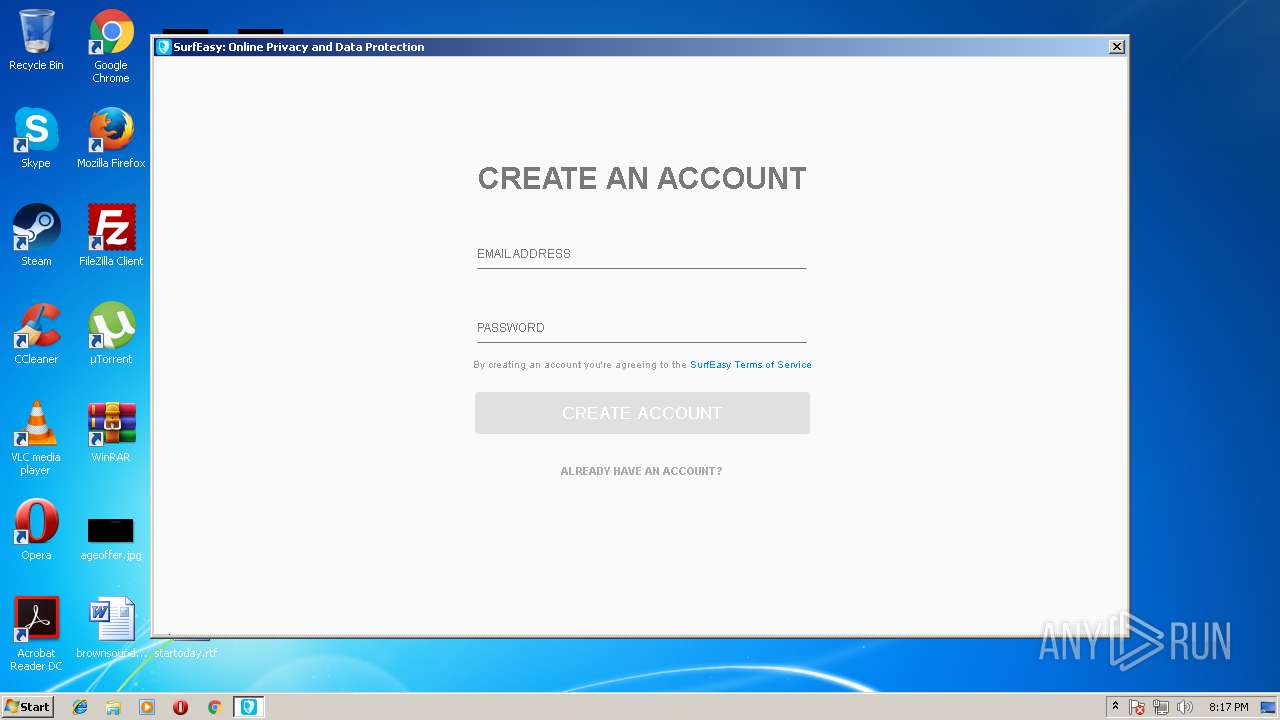
| Verdict: | Malicious activity |
| Analysis date: | September 04, 2018, 19:14:29 |
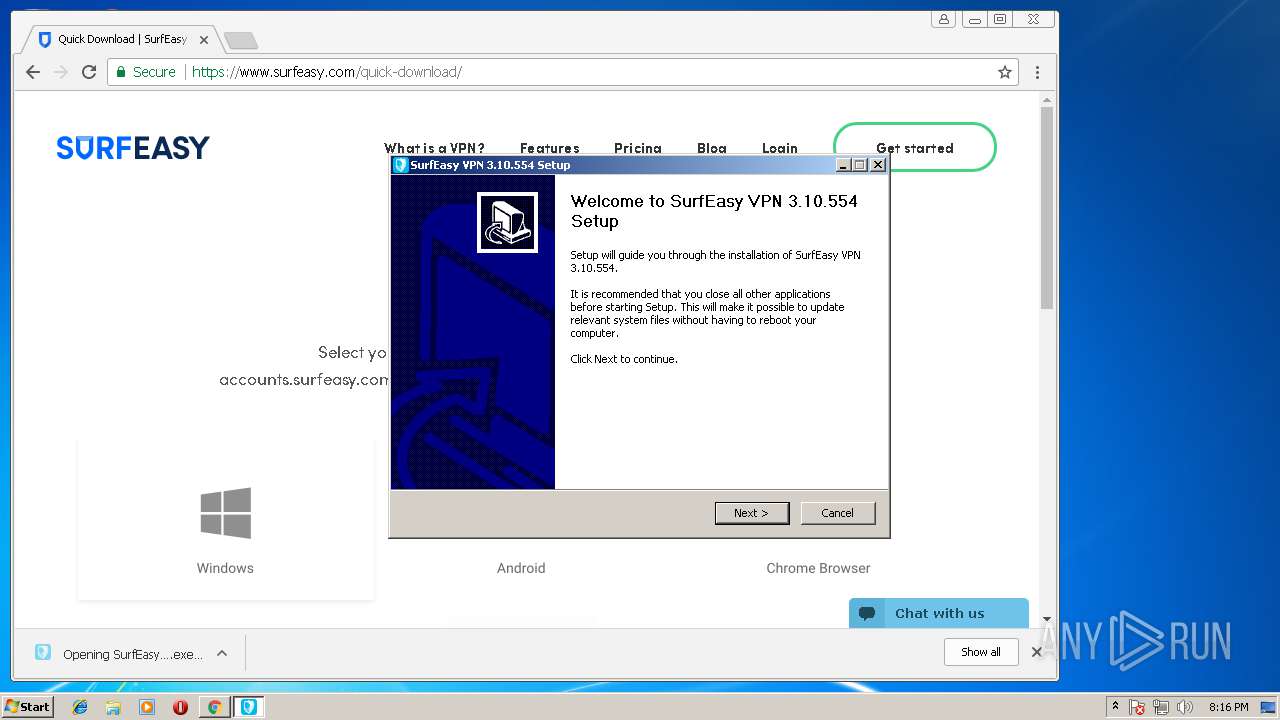
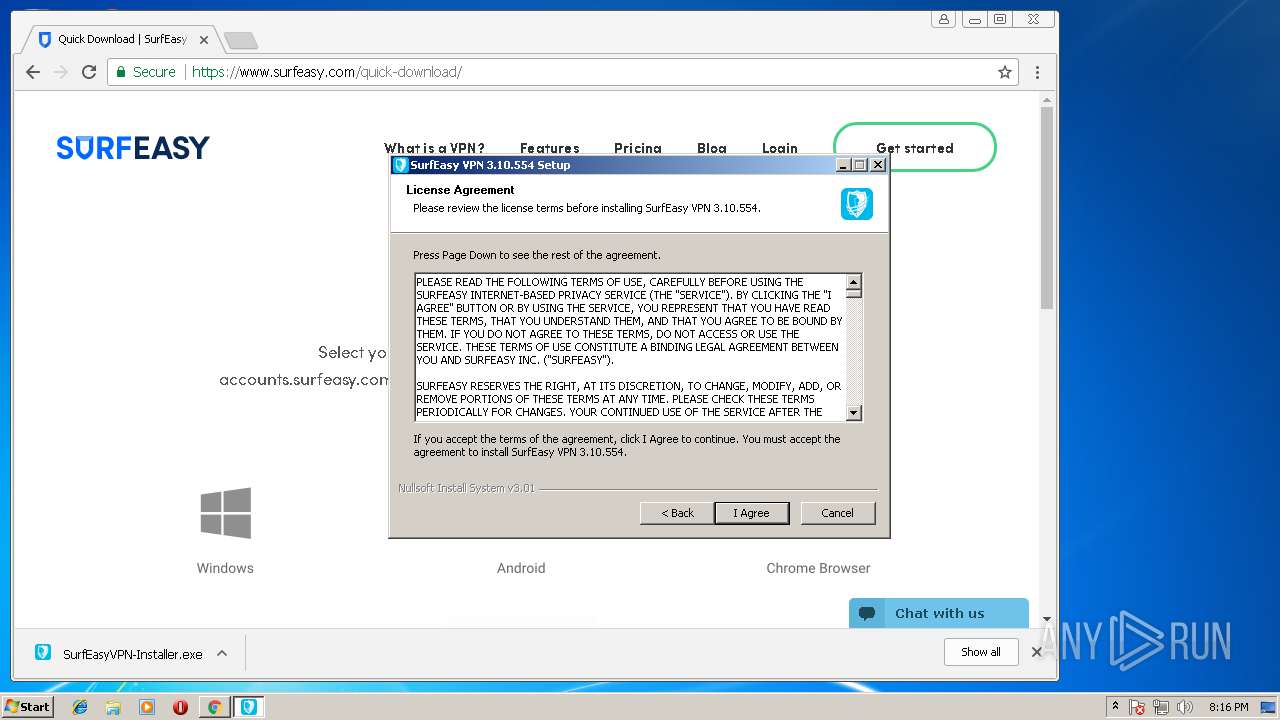
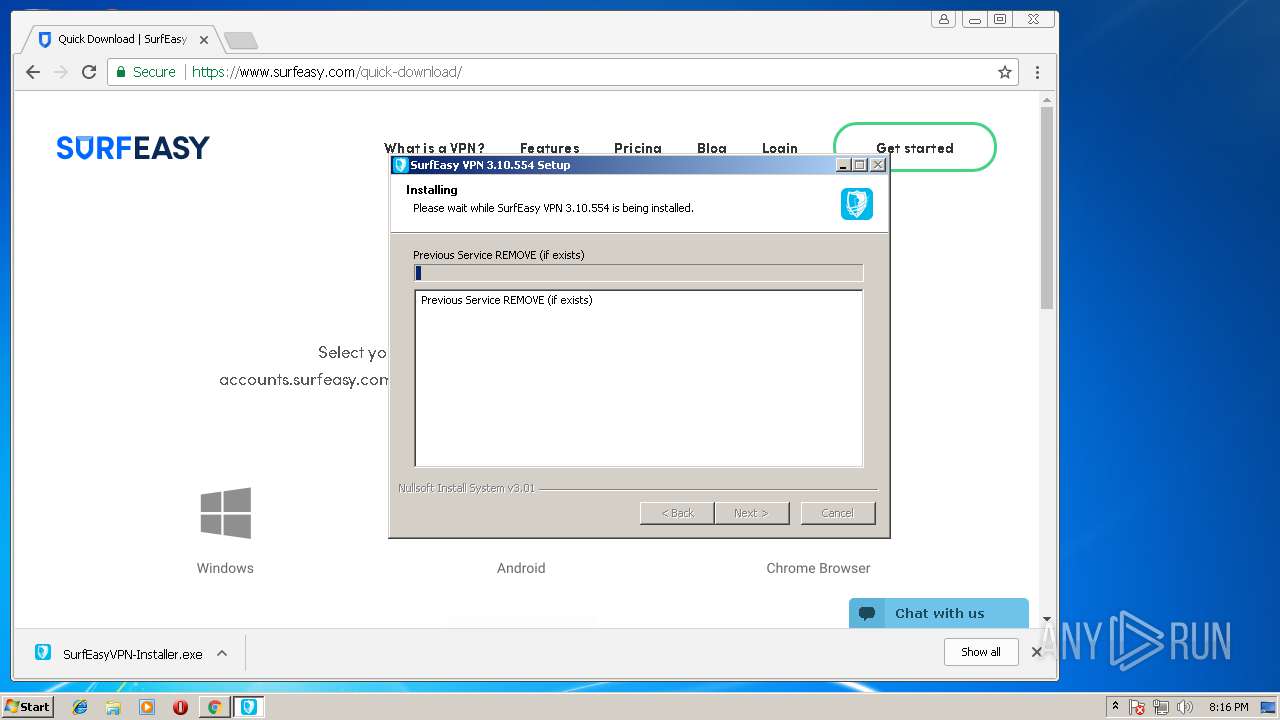
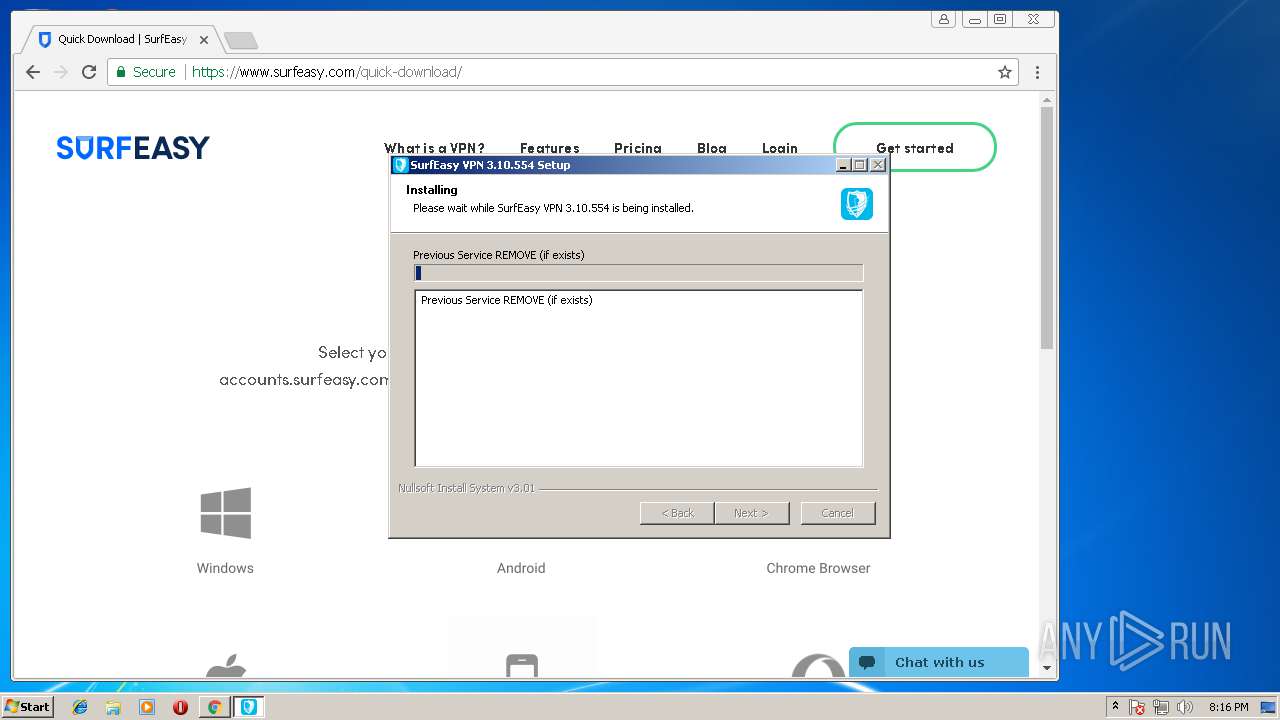
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, UTF-8 Unicode text, with very long lines |
| MD5: | 25C199B21360C62A36A80B9D60C4F35B |
| SHA1: | C20C28B3340CE9DD7E1E2C8B1A5530BCF068CD60 |
| SHA256: | 8607E66ED97C0BC3EDB114E69F507767889A5223199E19097BBAFDA7D50EA11A |
| SSDEEP: | 768:qW7sbUGQU9WbteiGJcRcl1D3IsRxvDCMY6eTNM9wNX5vHuwW:qFQU9WJjGMcLYmxvvY6etNVW |
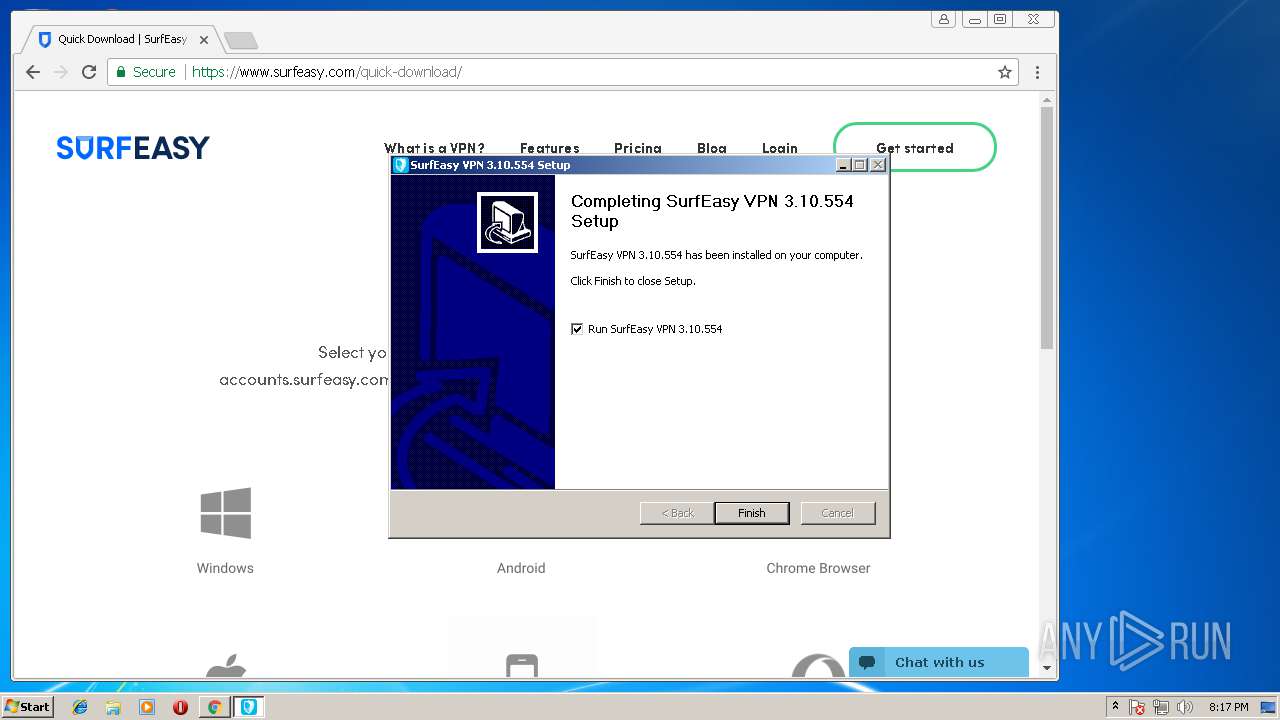
MALICIOUS
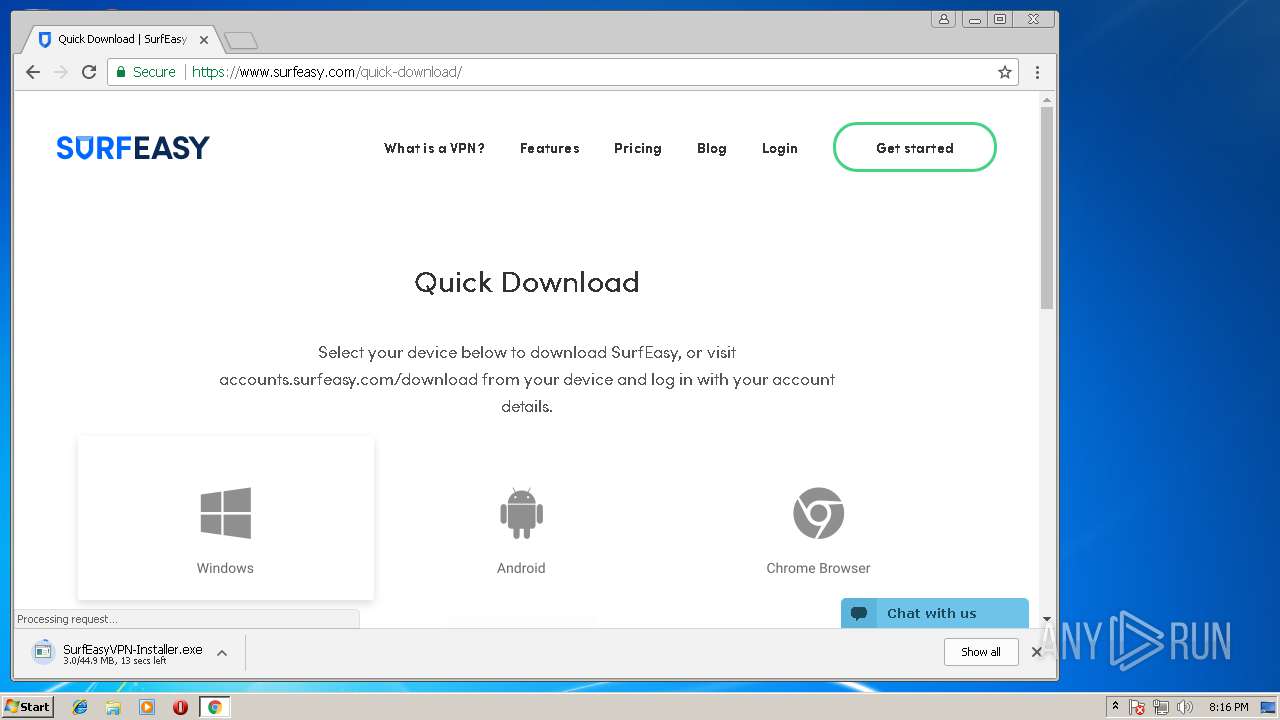
Application was dropped or rewritten from another process
- SurfEasyVPN-Installer.exe (PID: 2624)
- SurfEasyVPN-Installer.exe (PID: 2688)
- ns48AD.tmp (PID: 3016)
- ns5AAF.tmp (PID: 1548)
- ns6466.tmp (PID: 2892)
- ns65BF.tmp (PID: 2148)
- ns5CF2.tmp (PID: 3656)
- ns6020.tmp (PID: 2708)
- SurfEasyService.exe (PID: 2112)
- SurfEasyService.exe (PID: 3716)
Loads dropped or rewritten executable
- SurfEasyVPN-Installer.exe (PID: 2688)
- SurfEasyVPN.exe (PID: 3552)
- SurfEasyService.exe (PID: 2112)
- SurfEasyService.exe (PID: 3716)
Starts NET.EXE for service management
- ns5CF2.tmp (PID: 3656)
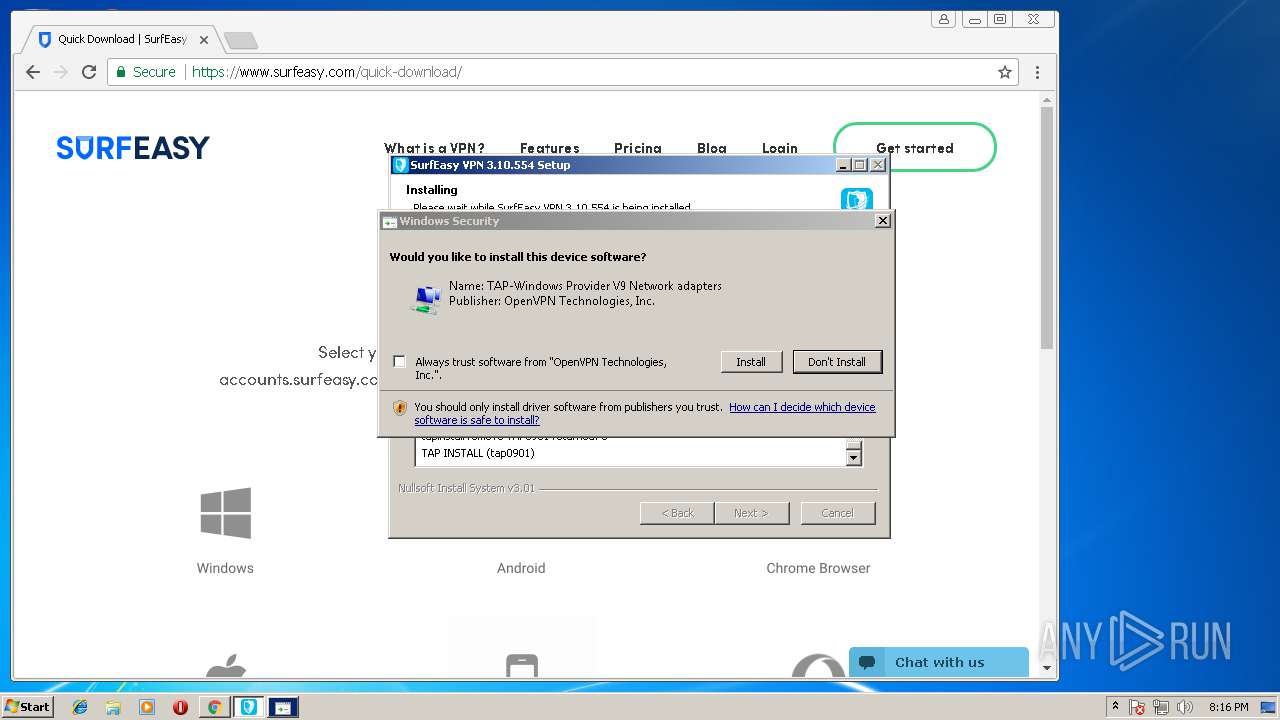
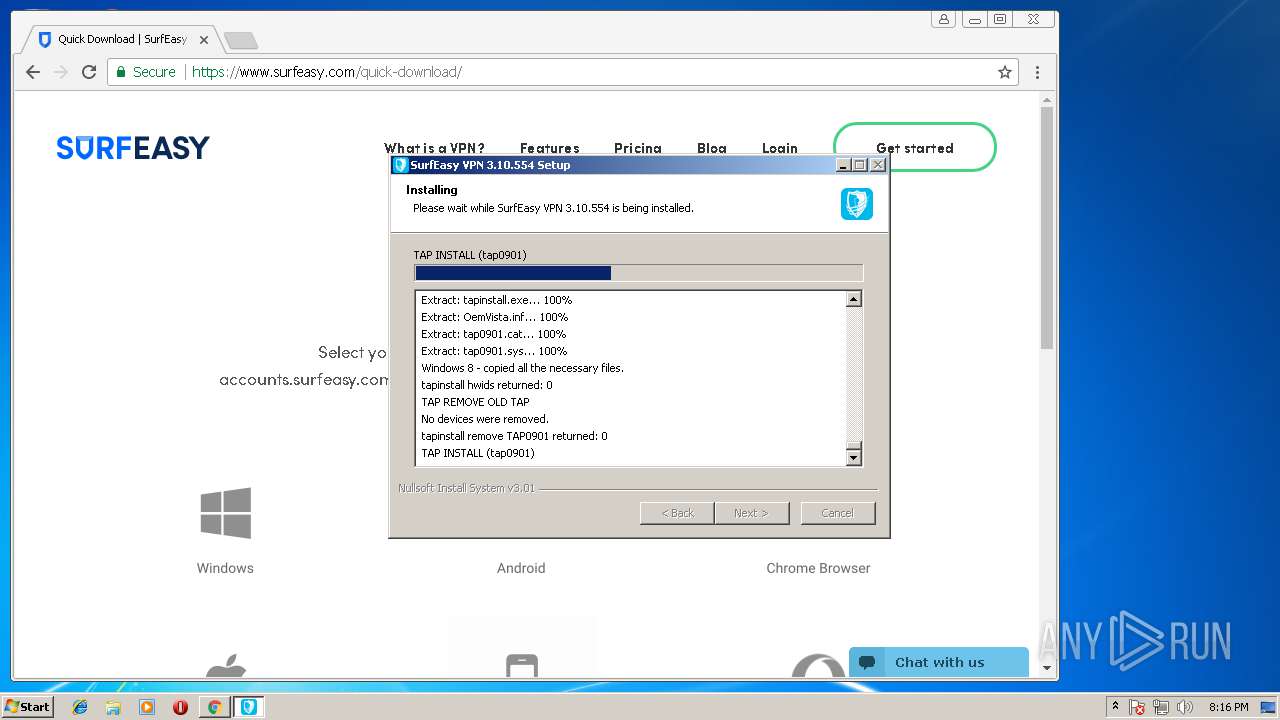
Changes settings of System certificates
- tapinstall.exe (PID: 2224)
Changes the autorun value in the registry
- SurfEasyVPN.exe (PID: 3552)
SUSPICIOUS
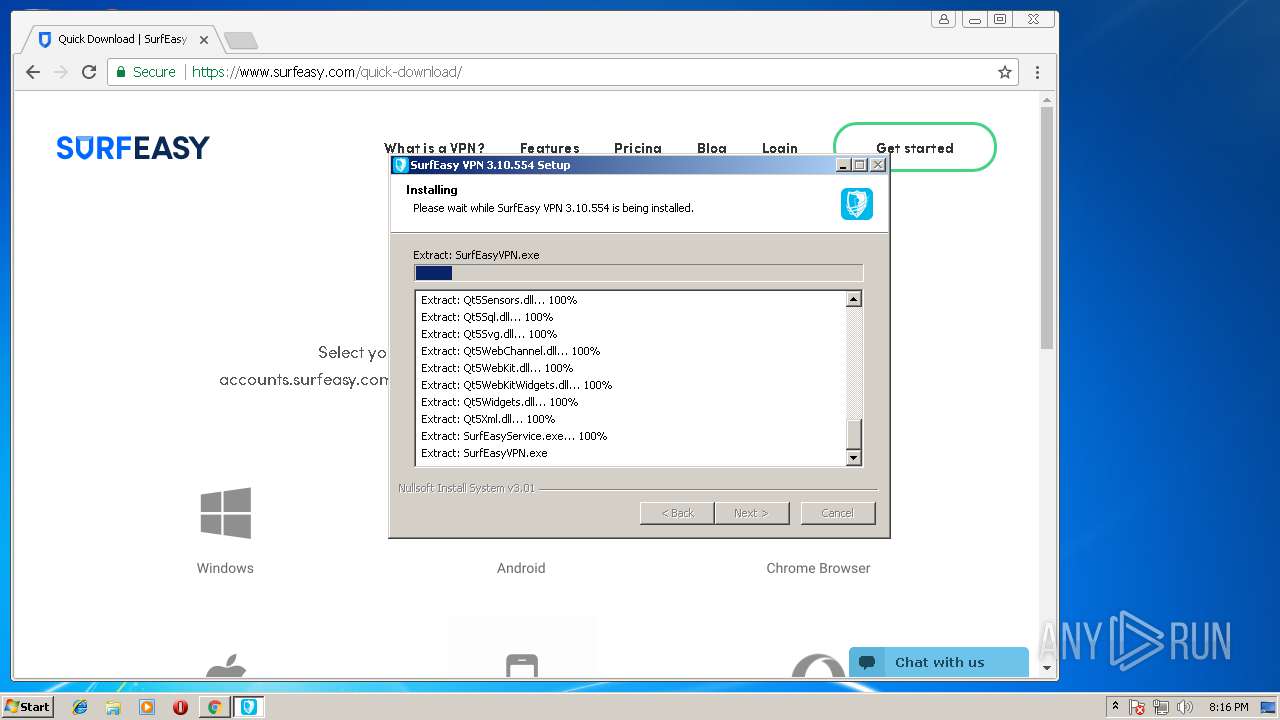
Executable content was dropped or overwritten
- chrome.exe (PID: 1124)
- SurfEasyVPN-Installer.exe (PID: 2688)
- tapinstall.exe (PID: 2224)
Starts application with an unusual extension
- SurfEasyVPN-Installer.exe (PID: 2688)
Creates files in the user directory
- SurfEasyVPN-Installer.exe (PID: 2688)
Creates files in the Windows directory
- DrvInst.exe (PID: 2396)
- DrvInst.exe (PID: 3132)
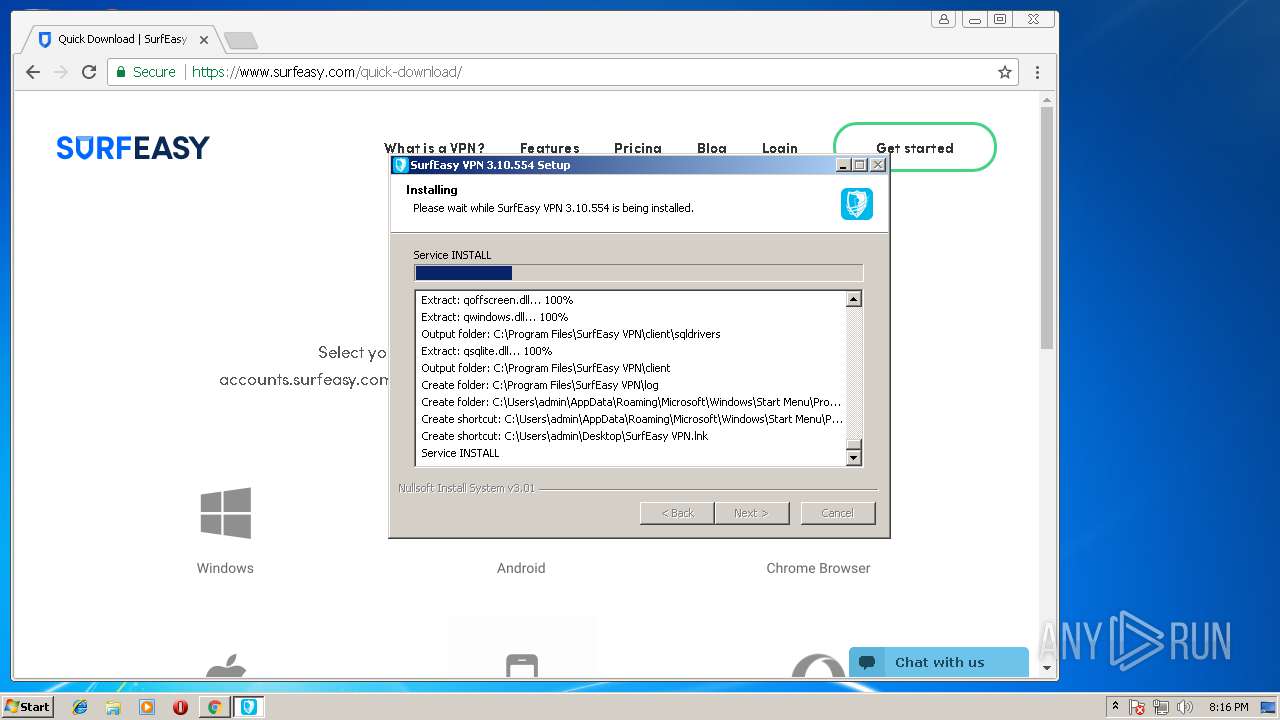
Creates or modifies windows services
- SurfEasyVPN-Installer.exe (PID: 2688)
- DrvInst.exe (PID: 2396)
- DrvInst.exe (PID: 3132)
Adds / modifies Windows certificates
- tapinstall.exe (PID: 2224)
Creates files in the program directory
- SurfEasyVPN-Installer.exe (PID: 2688)
- SurfEasyService.exe (PID: 3716)
- SurfEasyVPN.exe (PID: 3552)
Removes files from Windows directory
- DrvInst.exe (PID: 2396)
- DrvInst.exe (PID: 3132)
Creates files in the driver directory
- DrvInst.exe (PID: 2396)
- DrvInst.exe (PID: 3132)
Modifies files in Chrome extension folder
- chrome.exe (PID: 1124)
Searches for installed software
- DrvInst.exe (PID: 2396)
Creates a software uninstall entry
- SurfEasyVPN-Installer.exe (PID: 2688)
Starts CMD.EXE for commands execution
- SurfEasyVPN.exe (PID: 3552)
INFO
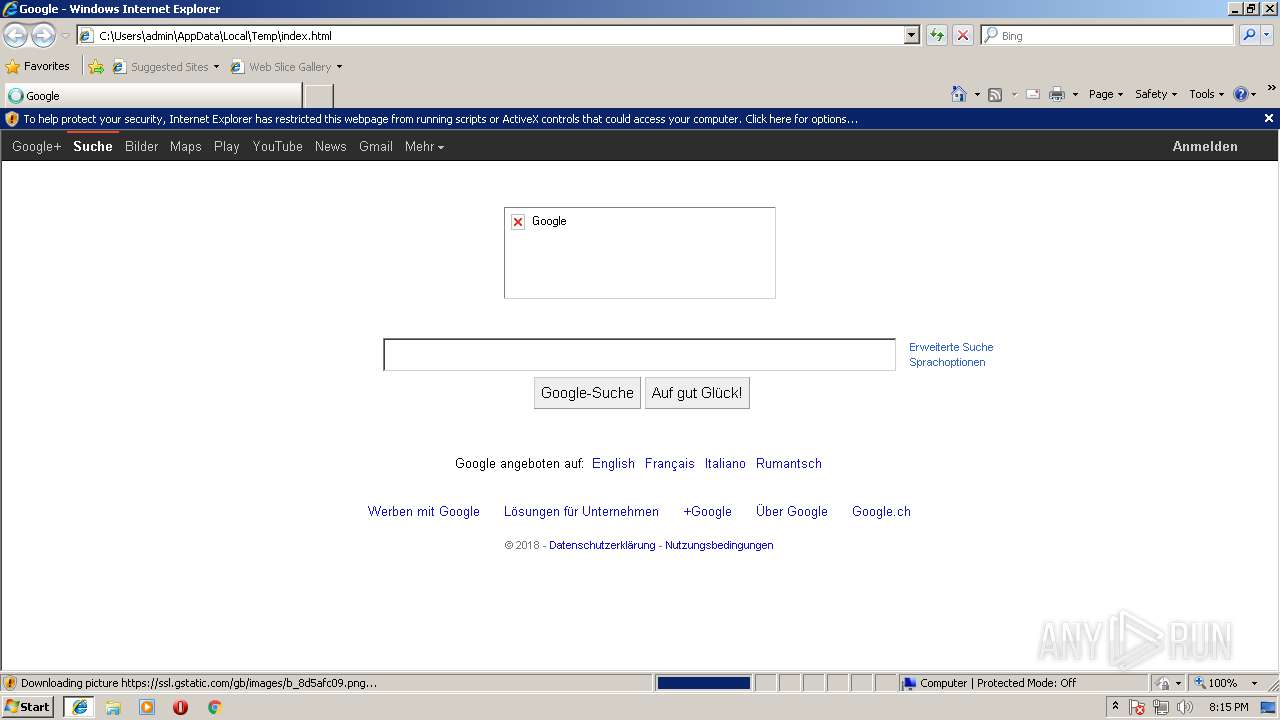
Changes internet zones settings
- iexplore.exe (PID: 3636)
Application launched itself
- iexplore.exe (PID: 3636)
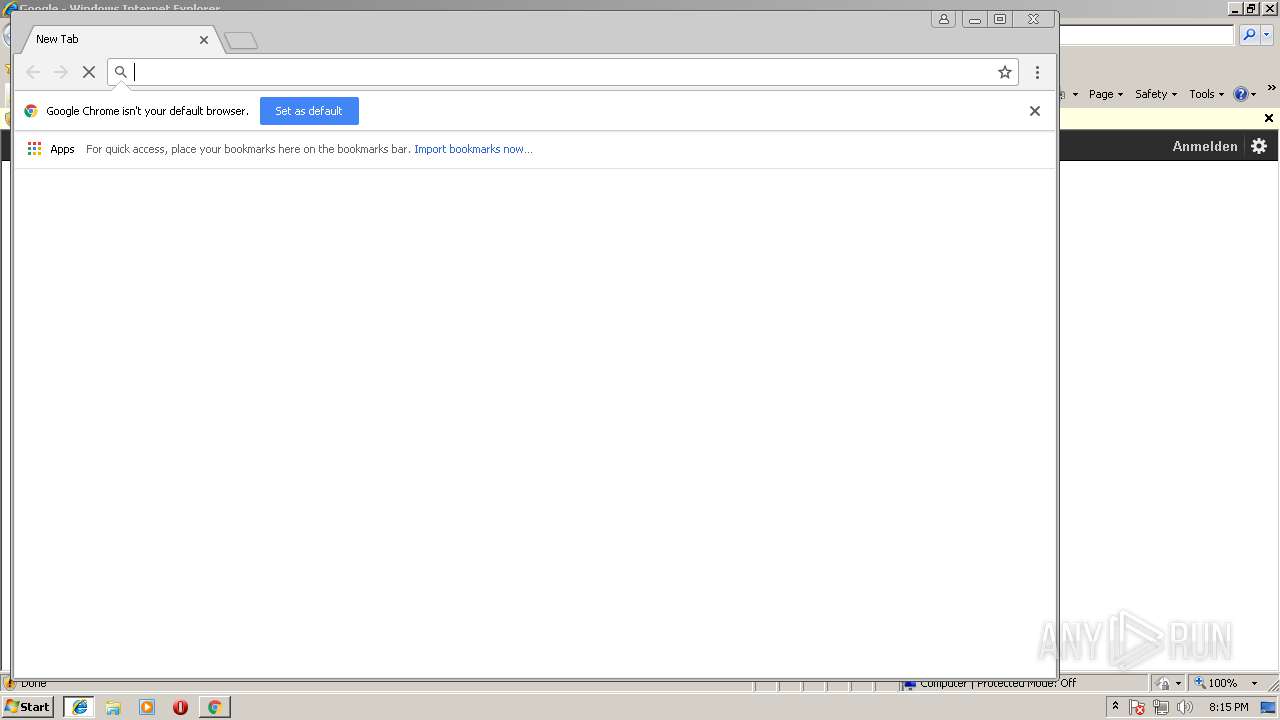
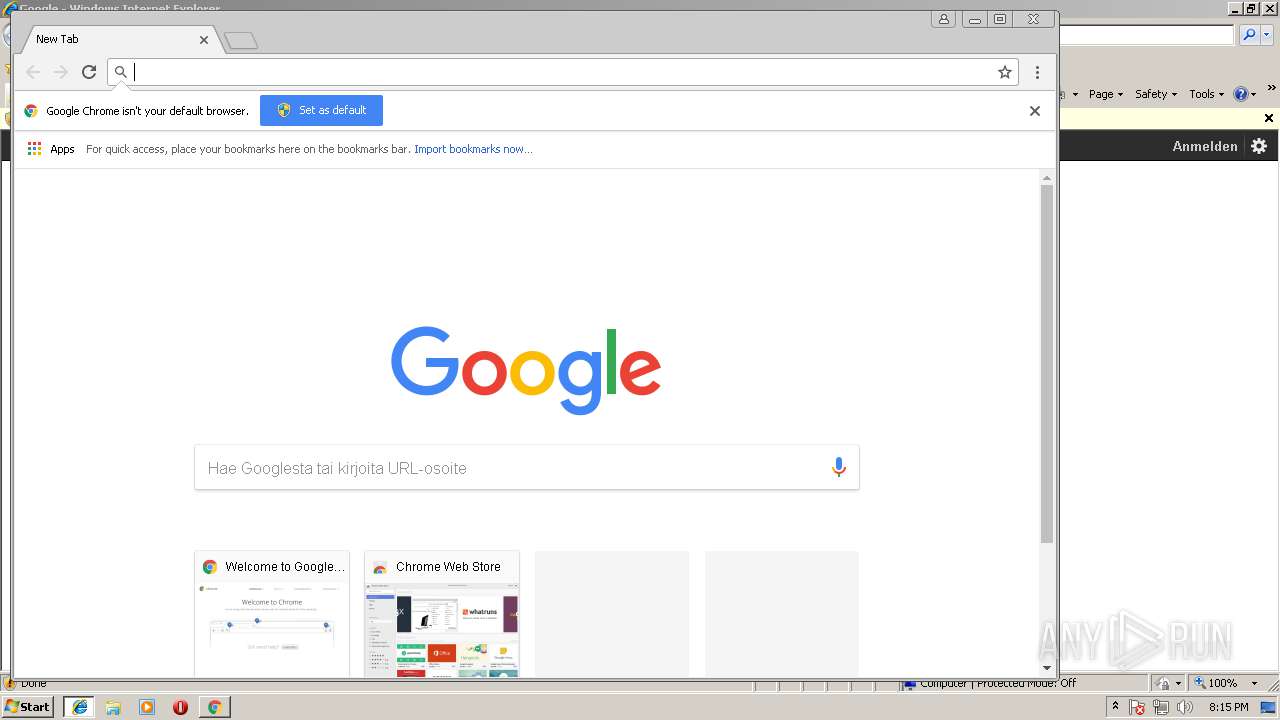
- chrome.exe (PID: 1124)
Reads Internet Cache Settings
- iexplore.exe (PID: 2096)
- chrome.exe (PID: 1124)
Creates files in the user directory
- iexplore.exe (PID: 2096)
Reads internet explorer settings
- iexplore.exe (PID: 2096)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2096)
Changes settings of System certificates
- iexplore.exe (PID: 2096)
Reads settings of System Certificates
- chrome.exe (PID: 1124)
Dropped object may contain Bitcoin addresses
- SurfEasyVPN-Installer.exe (PID: 2688)
Dropped object may contain URL's
- tapinstall.exe (PID: 2224)
- SurfEasyVPN-Installer.exe (PID: 2688)
- chrome.exe (PID: 3628)
- chrome.exe (PID: 1124)
- chrome.exe (PID: 4020)
- DrvInst.exe (PID: 2396)
Low-level read access rights to disk partition
- vssvc.exe (PID: 992)
Creates or modifies windows services
- vssvc.exe (PID: 992)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .html | | | HyperText Markup Language (100) |
|---|
Total processes
85
Monitored processes
41
Malicious processes
8
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 616 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=4044 --on-initialized-event-handle=296 --parent-handle=300 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 61.0.3163.91 Modules
| |||||||||||||||
| 828 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1768,17624026540415479484,12161071306157314895,131072 --lang=en-US --no-sandbox --service-request-channel-token=95176D31CCF8D8A3B9692FF387B5F12A --mojo-platform-channel-handle=796 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 61.0.3163.91 Modules
| |||||||||||||||
| 956 | C:\Windows\system32\net1 START "SurfEasyVPN" | C:\Windows\system32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 992 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1124 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 61.0.3163.91 Modules
| |||||||||||||||
| 1208 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1768,17624026540415479484,12161071306157314895,131072 --service-pipe-token=FCB3BEB2F6C484C1D234B6A3675486D5 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --enable-pinch --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --content-image-texture-target=0,0,3553;0,1,3553;0,2,3553;0,3,3553;0,4,3553;0,5,3553;0,6,3553;0,7,3553;0,8,3553;0,9,3553;0,10,3553;0,11,3553;0,12,3553;0,13,3553;0,14,3553;0,15,3553;0,16,3553;0,17,3553;1,0,3553;1,1,3553;1,2,3553;1,3,3553;1,4,3553;1,5,3553;1,6,3553;1,7,3553;1,8,3553;1,9,3553;1,10,3553;1,11,3553;1,12,3553;1,13,3553;1,14,3553;1,15,3553;1,16,3553;1,17,3553;2,0,3553;2,1,3553;2,2,3553;2,3,3553;2,4,3553;2,5,3553;2,6,3553;2,7,3553;2,8,3553;2,9,3553;2,10,3553;2,11,3553;2,12,3553;2,13,3553;2,14,3553;2,15,3553;2,16,3553;2,17,3553;3,0,3553;3,1,3553;3,2,3553;3,3,3553;3,4,3553;3,5,3553;3,6,3553;3,7,3553;3,8,3553;3,9,3553;3,10,3553;3,11,3553;3,12,3553;3,13,3553;3,14,3553;3,15,3553;3,16,3553;3,17,3553;4,0,3553;4,1,3553;4,2,3553;4,3,3553;4,4,3553;4,5,3553;4,6,3553;4,7,3553;4,8,3553;4,9,3553;4,10,3553;4,11,3553;4,12,3553;4,13,3553;4,14,3553;4,15,3553;4,16,3553;4,17,3553 --disable-accelerated-video-decode --disable-gpu-compositing --enable-gpu-async-worker-context --service-request-channel-token=FCB3BEB2F6C484C1D234B6A3675486D5 --renderer-client-id=15 --mojo-platform-channel-handle=4252 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 61.0.3163.91 Modules
| |||||||||||||||
| 1336 | "C:\Program Files\SurfEasy VPN\driver6\win32\tapinstall.exe" remove TAP0901 | C:\Program Files\SurfEasy VPN\driver6\win32\tapinstall.exe | — | ns6466.tmp | |||||||||||
User: admin Company: SurfEasy Inc. Integrity Level: HIGH Description: SurfEasy TapInstall Exit code: 0 Version: 9.9.2 built by: WinDDK Modules
| |||||||||||||||
| 1548 | "C:\Users\admin\AppData\Local\Temp\nsb3AE0.tmp\ns5AAF.tmp" "C:\Program Files\SurfEasy VPN\client\SurfEasyService.exe" install | C:\Users\admin\AppData\Local\Temp\nsb3AE0.tmp\ns5AAF.tmp | — | SurfEasyVPN-Installer.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1624 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1768,17624026540415479484,12161071306157314895,131072 --service-pipe-token=6F040A5D550BDA14F693DE428C87FF0D --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --enable-pinch --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --content-image-texture-target=0,0,3553;0,1,3553;0,2,3553;0,3,3553;0,4,3553;0,5,3553;0,6,3553;0,7,3553;0,8,3553;0,9,3553;0,10,3553;0,11,3553;0,12,3553;0,13,3553;0,14,3553;0,15,3553;0,16,3553;0,17,3553;1,0,3553;1,1,3553;1,2,3553;1,3,3553;1,4,3553;1,5,3553;1,6,3553;1,7,3553;1,8,3553;1,9,3553;1,10,3553;1,11,3553;1,12,3553;1,13,3553;1,14,3553;1,15,3553;1,16,3553;1,17,3553;2,0,3553;2,1,3553;2,2,3553;2,3,3553;2,4,3553;2,5,3553;2,6,3553;2,7,3553;2,8,3553;2,9,3553;2,10,3553;2,11,3553;2,12,3553;2,13,3553;2,14,3553;2,15,3553;2,16,3553;2,17,3553;3,0,3553;3,1,3553;3,2,3553;3,3,3553;3,4,3553;3,5,3553;3,6,3553;3,7,3553;3,8,3553;3,9,3553;3,10,3553;3,11,3553;3,12,3553;3,13,3553;3,14,3553;3,15,3553;3,16,3553;3,17,3553;4,0,3553;4,1,3553;4,2,3553;4,3,3553;4,4,3553;4,5,3553;4,6,3553;4,7,3553;4,8,3553;4,9,3553;4,10,3553;4,11,3553;4,12,3553;4,13,3553;4,14,3553;4,15,3553;4,16,3553;4,17,3553 --disable-accelerated-video-decode --disable-gpu-compositing --enable-gpu-async-worker-context --service-request-channel-token=6F040A5D550BDA14F693DE428C87FF0D --renderer-client-id=6 --mojo-platform-channel-handle=2936 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 61.0.3163.91 Modules
| |||||||||||||||
| 2096 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3636 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 696
Read events
1 910
Write events
725
Delete events
61
Modification events
| (PID) Process: | (3636) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3636) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3636) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3636) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (3636) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3636) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000048000000010000000000000000000000000000000000000000000000B096B68868EBD301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000D8BFD602040000000000000000000000000000000000000000000000F4BFD602040000000000000000000000000000000000000000000000D8372A0000000000FFFFFFFF000000000000000000000000010000002E00000000000000000000000000000002000000C0A801640000000000000000D84ED505AC02000005000000010000000000000000000000010000000000000000000000BF060000000000000000000000000000000000001000000088C0D60204000000000000000000000000000000000000000000000000000000C8E40C00000000000C0000000000000000000000 | |||
| (PID) Process: | (3636) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {E664E3E5-B076-11E8-ACE5-5254004AAD11} |
Value: 0 | |||
| (PID) Process: | (3636) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (3636) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 10 | |||
| (PID) Process: | (3636) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E20709000200040013000F0024006002 | |||
Executable files
80
Suspicious files
92
Text files
126
Unknown types
17
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3636 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\HHUAAB7W\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3636 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 1124 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000008.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1124 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\80f79c1f-0c58-4d35-8b69-22bffc3fd77b.tmp | — | |
MD5:— | SHA256:— | |||
| 1124 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\CacheStorage\e6622492fa163609ddd4212f54512baa07929ed3\0b424357-803d-4002-a471-5e43f4cbfdf1\index-dir\temp-index | — | |
MD5:— | SHA256:— | |||
| 2096 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\History.IE5\MSHist012018090420180905\index.dat | dat | |
MD5:— | SHA256:— | |||
| 1124 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF4c7c91.TMP | text | |
MD5:— | SHA256:— | |||
| 1124 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:— | SHA256:— | |||
| 1124 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3636 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\HHUAAB7W\favicon[2].png | image | |
MD5:9FB559A691078558E77D6848202F6541 | SHA256:6D8A01DC7647BC218D003B58FE04049E24A9359900B7E0CEBAE76EDF85B8B914 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
164
DNS requests
126
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1124 | chrome.exe | GET | 200 | 87.245.198.17:80 | http://r6---sn-gxuog0-axqe.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOGZmQUFWZDVabUx2XzNSUmJXZUVFZWhQQQ/6317.1002.0.5_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=185.117.118.94&mm=28&mn=sn-gxuog0-axqe&ms=nvh&mt=1536088424&mv=u&pl=26&shardbypass=yes | RU | crx | 877 Kb | whitelisted |
3552 | SurfEasyVPN.exe | GET | 200 | 2.16.186.26:80 | http://www.msftncsi.com/ncsi.txt | unknown | text | 14 b | whitelisted |
3552 | SurfEasyVPN.exe | GET | 200 | 2.16.186.17:80 | http://www.msftncsi.com/ncsi.txt | unknown | text | 14 b | whitelisted |
1124 | chrome.exe | GET | 302 | 216.58.212.206:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOGZmQUFWZDVabUx2XzNSUmJXZUVFZWhQQQ/6317.1002.0.5_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 512 b | whitelisted |
1124 | chrome.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 53.8 Kb | whitelisted |
1124 | chrome.exe | GET | 200 | 143.204.208.196:80 | http://x.ss2.us/x.cer | US | der | 1.27 Kb | whitelisted |
3636 | iexplore.exe | GET | 200 | 131.253.33.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3636 | iexplore.exe | 131.253.33.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
1124 | chrome.exe | 172.217.17.67:443 | www.google.de | Google Inc. | US | whitelisted |
1124 | chrome.exe | 216.58.212.206:443 | apis.google.com | Google Inc. | US | whitelisted |
1124 | chrome.exe | 216.58.212.195:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
1124 | chrome.exe | 172.217.20.99:443 | id.google.fi | Google Inc. | US | whitelisted |
1124 | chrome.exe | 172.217.23.132:443 | www.google.com | Google Inc. | US | whitelisted |
1124 | chrome.exe | 172.217.17.66:443 | www.googleadservices.com | Google Inc. | US | whitelisted |
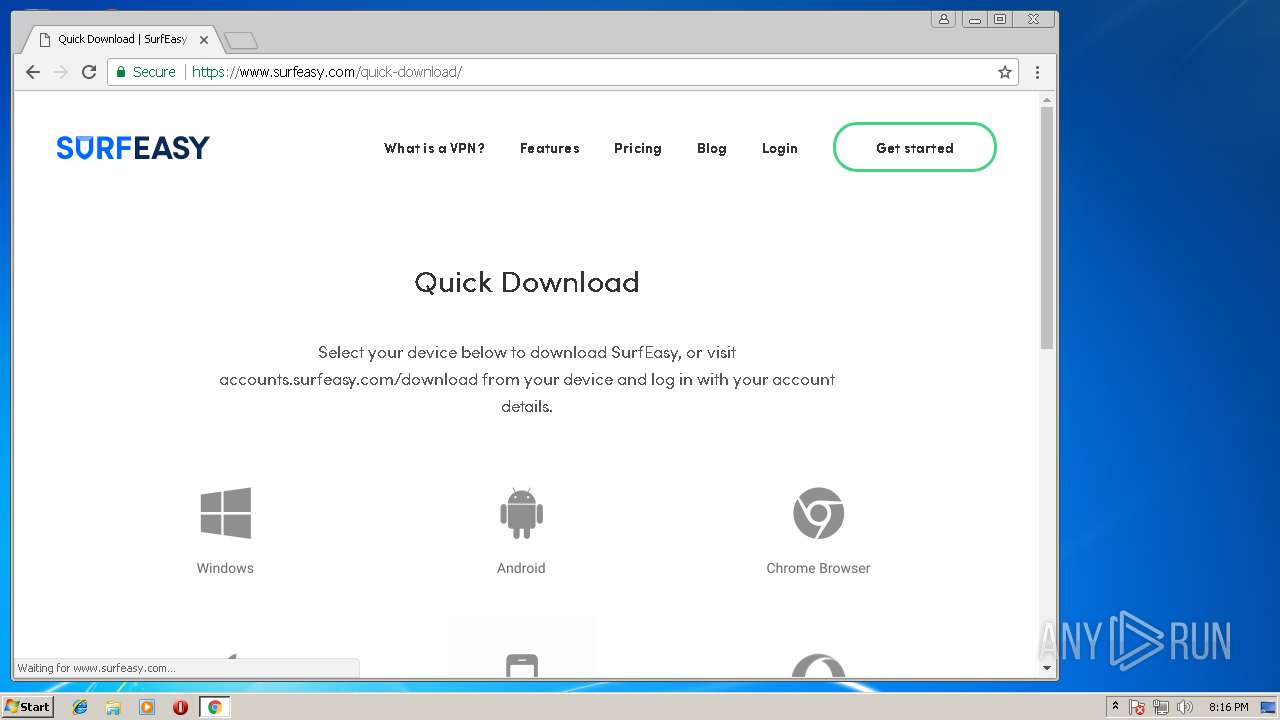
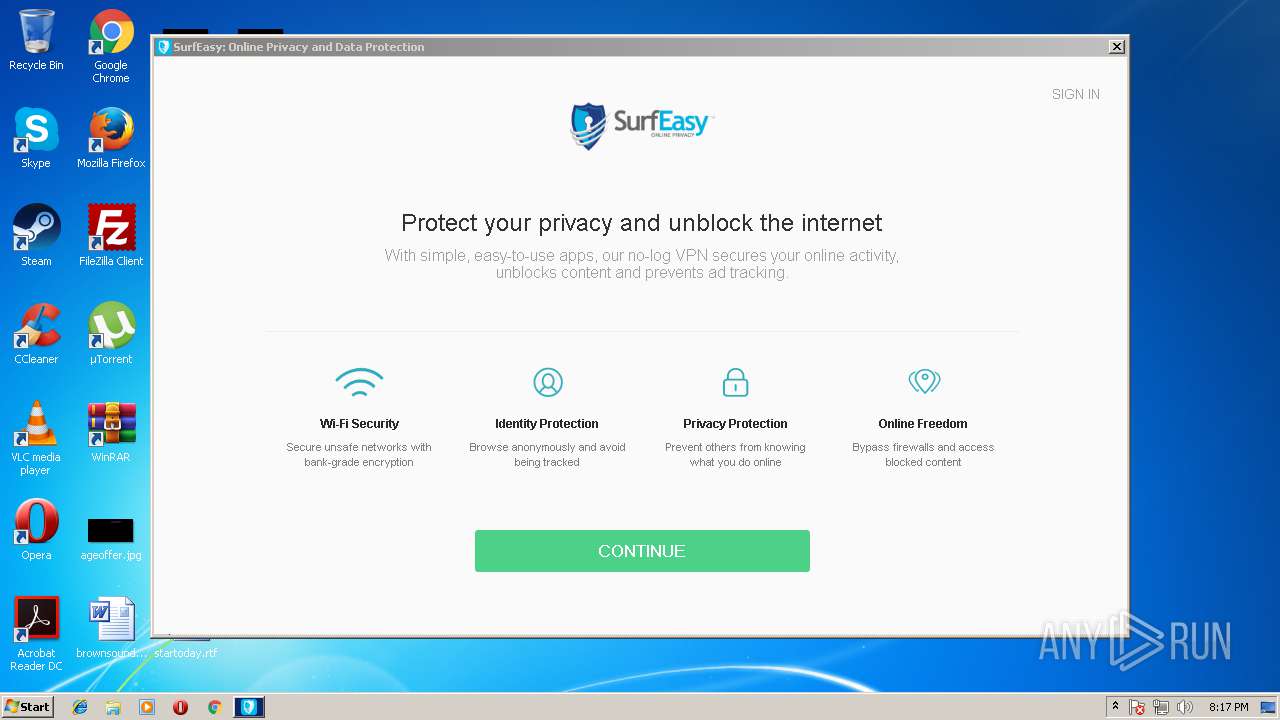
1124 | chrome.exe | 104.25.38.106:443 | www.surfeasy.com | Cloudflare Inc | US | shared |
1124 | chrome.exe | 104.19.198.151:443 | cdnjs.cloudflare.com | Cloudflare Inc | US | shared |
2096 | iexplore.exe | 216.58.212.195:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ssl.gstatic.com |
| whitelisted |
www.bing.com |
| whitelisted |
www.google.de |
| whitelisted |
apis.google.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
translate.googleapis.com |
| whitelisted |
www.google.com |
| malicious |
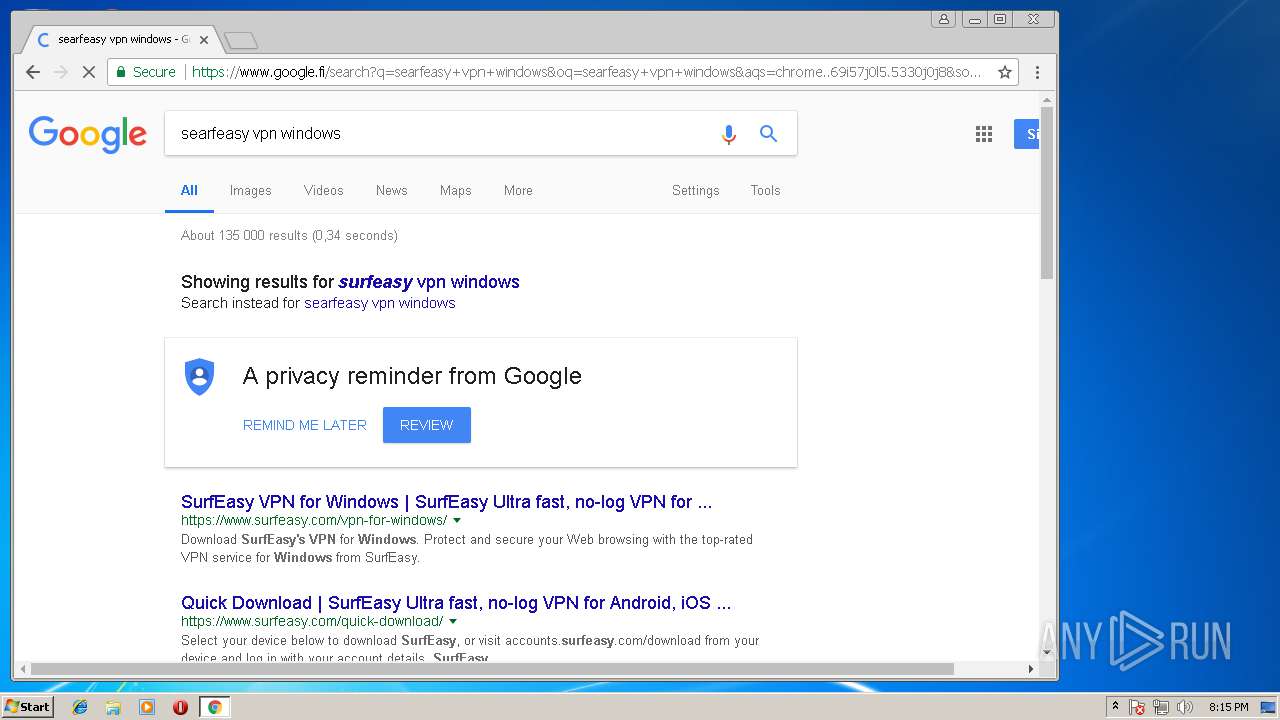
www.google.fi |
| whitelisted |
consent.google.com |
| shared |
Threats
Process | Message |
|---|---|
SurfEasyVPN.exe | QObject::connect: No such signal seUI::FacebookLoginDialog::cancelClicked() in C:\jenkins\workspace\windows-VPN-master\ui\seUIFacebookLoginDialog.cpp:61
|
SurfEasyVPN.exe | QObject::connect: No such signal seUI::OnboardingDialog::cancelClicked() in C:\jenkins\workspace\windows-VPN-master\ui\seUIOnboardingDialog.cpp:181
|
SurfEasyVPN.exe | QMetaObject::connectSlotsByName: No matching signal for on_free_reward_facebook_like_clicked()
|
SurfEasyVPN.exe | QMetaObject::connectSlotsByName: No matching signal for on_free_reward_generic_clicked(int)
|
SurfEasyVPN.exe | QMetaObject::connectSlotsByName: No matching signal for on_free_rewards_add_device_v3()
|
SurfEasyVPN.exe | QMetaObject::connectSlotsByName: No matching signal for on_free_rewards_update_email()
|
SurfEasyVPN.exe | "C:\\Program Files\\SurfEasy VPN\\surfeasy_on.mbtiles"
|
SurfEasyVPN.exe | Using "surfeasy_on.mbtiles"
|
SurfEasyVPN.exe | "C:\\Program Files\\SurfEasy VPN\\surfeasy_off.mbtiles"
|
SurfEasyVPN.exe | Using "surfeasy_off.mbtiles"
|